mirror of
https://github.com/LCTT/TranslateProject.git
synced 2025-02-28 01:01:09 +08:00
commit
dfaf4d865f
@ -1,500 +0,0 @@
|
||||
2q1w2007翻译中
|
||||
搭建并运行OpenVPN,享受你的隐私生活
|
||||
================================================================================
|
||||

|
||||
|
||||
> 我们支持保护隐私,不为我们有自己的秘密需要保护,只是我们认为保护隐私应该成为一项基本人权。所以我们坚信无论谁在什么时候行使这项权利,都应该不受拘束的获取必须的工具和服务。OpenVPN就是这样一种服务并且有多种工具(客户端) 来让我们利用并享受这种服务。
|
||||
|
||||
By establishing a connection to an [OpenVPN][1] server, we basically create a secure communications channel between our device and the remote host OpenVPN runs on. Although traffic flowing between these two end-points can be intercepted, it is strongly encrypted and thus practically useless to the interceptor. In addition to the OpenVPN acting as the facilitator of this encrypted channel (or tunnel), we may configure the server to also play the role of our Internet gateway. By doing so, we can for example hook up to any open, inherently insecure WiFi network, then immediately connect to the remote OpenVPN server and start using any Internet-enabled application without worrying of prying eyes or bored administrators. (Note though that we still need to trust any administrator in the vicinity of the OpenVPN server. But more on that towards the end of the post.)
|
||||
|
||||
This article is a step-by-step guide on how to setup OpenVPN on [Ubuntu Server 14.04 LTS][2]. The OpenVPN host computer may be a VPS in the cloud, a virtual machine running on one of our computers at home, or even that somewhat aged box we tend to forget we have.
|
||||
|
||||
### Step 01 -- System Preparation ###
|
||||
|
||||
We gain access to a command shell in the Ubuntu Server host, for example by remotely connecting to it via SSH, and immediately refresh the local repository database:
|
||||
|
||||
sub0@delta:~$ sudo apt-get update
|
||||
|
||||
To perform any upgrades for all installed packages and the operating system itself, we type:
|
||||
|
||||
sub0@delta:~$ sudo apt-get dist-upgrade
|
||||
|
||||
If a new kernel gets pulled in, a system reboot will be required. After refreshing and upgrading, it’s time to install OpenVPN:
|
||||
|
||||
sub0@delta:~$ sudo apt-get -y install openvpn easy-rsa dnsmasq
|
||||
|
||||
Notice that we installed three packages with apt-get:
|
||||
|
||||
- openvpn provides the core of OpenVPN
|
||||
- easy-rsa contains some handy scripts for key management
|
||||
- dnsmasq is the name server we’ll be using later on, when our OpenVPN server box/VM will assume the role of a router for all OpenVPN clients`
|
||||
|
||||
### Step 02 -- Master certificate and private key for the Certificate Authority ###
|
||||
|
||||
The most important –and admittedly the most crucial– step during the setup of an OpenVPN server, is the establishment of a corresponding Public Key Infrastructure (PKI). This infrastructure comprises the following:
|
||||
|
||||
- A certificate (public key) and a private key for the OpenVPN server
|
||||
- A certificate and a private key for any OpenVPN client
|
||||
- A master certificate and a private key for the Certificate Authority (CA). This private key is used for signing the OpenVPN certificate as well as the client certificates.
|
||||
|
||||
Beginning with the latter, we create a convenient working directory
|
||||
|
||||
sub0@delta:~$ sudo mkdir /etc/openvpn/easy-rsa
|
||||
|
||||
and then copy easy-rsa’s files to it:
|
||||
|
||||
sub0@delta:~$ sudo cp -r /usr/share/easy-rsa/* /etc/openvpn/easy-rsa
|
||||
|
||||
Before we actually create the keys for the CA, we open /etc/openvpn/easy-rsa/vars for editing (we like the nano text editor but this is just our preference):
|
||||
|
||||
sub0@delta:~$ sudo nano /etc/openvpn/easy-rsa/vars
|
||||
|
||||
Towards the end of the file we assign values to a set of variables which are read during the creation of the master certificate and private key. Take a look at the variables we assigned values to:
|
||||
|
||||
export KEY_COUNTRY="GR"
|
||||
export KEY_PROVINCE="Central Macedonia"
|
||||
export KEY_CITY="Thessaloniki"
|
||||
export KEY_ORG="Parabing Creations"
|
||||
export KEY_EMAIL="nobody@parabing.com"
|
||||
export KEY_CN="VPNsRUS"
|
||||
export KEY_NAME="VPNsRUS"
|
||||
export KEY_OU="Parabing"
|
||||
export KEY_ALTNAMES="VPNsRUS"
|
||||
|
||||
It goes without saying that you may assign different values, more appropriate for your case. Also take particular note of the last line, in which we set a value to the KEY_ALTNAMES variable. This line is not part of the original vars file but we nevertheless append it at the end of said file, or the build-ca script we’re going to run next will fail.
|
||||
|
||||
To save the changes in vars we hit [CTRL+O] followed by the [Enter] key. To quit nano we hit [CTRL+X]. Now, we gain access to the root account and move on to building of the master certificate and private key:
|
||||
|
||||
sub0@delta:~$ sudo su
|
||||
root@delta:/home/sub0# cd /etc/openvpn/easy-rsa
|
||||
root@delta:/etc/openvpn/easy-rsa# source vars
|
||||
NOTE: If you run ./clean-all, I will be doing a rm -rf on /etc/openvpn/easy-rsa/keys
|
||||
root@delta:/etc/openvpn/easy-rsa# sh clean-all
|
||||
root@delta:/etc/openvpn/easy-rsa# sh build-ca
|
||||
Generating a 1024 bit RSA private key
|
||||
...++++++
|
||||
................++++++
|
||||
writing new private key to 'ca.key'
|
||||
-----
|
||||
You are about to be asked to enter information that will be incorporated
|
||||
into your certificate request.
|
||||
What you are about to enter is what is called a Distinguished Name or a DN.
|
||||
There are quite a few fields but you can leave some blank
|
||||
For some fields there will be a default value,
|
||||
If you enter '.', the field will be left blank.
|
||||
-----
|
||||
Country Name (2 letter code) [GR]:
|
||||
State or Province Name (full name) [Central Macedonia]:
|
||||
Locality Name (eg, city) [Thessaloniki]:
|
||||
Organization Name (eg, company) [Parabing Creations]:
|
||||
Organizational Unit Name (eg, section) [Parabing]:
|
||||
Common Name (eg, your name or your server's hostname) [VPNsRUS]:
|
||||
Name [VPNsRUS]:
|
||||
Email Address [nobody@parabing.com]:
|
||||
root@delta:/etc/openvpn/easy-rsa#
|
||||
|
||||
In our example the default answers were used for all the questions. After the build-ca script finishes we have the file for the master certificate (keys/ca.crt) and also the file for the private key (keys/ca.key). The latter must be kept secret at all costs.
|
||||
|
||||
### Step 03 -- Certificate and private key for the OpenVPN server ###
|
||||
|
||||
Before we make a certificate and private key for our OpenVPN server, we need to pick a name for it. We decided to name ours “delta” and then ran the build-key-server script to get the keys:
|
||||
|
||||
root@delta:/etc/openvpn/easy-rsa# sh build-key-server delta
|
||||
Generating a 1024 bit RSA private key
|
||||
....++++++
|
||||
...++++++
|
||||
writing new private key to 'delta.key'
|
||||
-----
|
||||
You are about to be asked to enter information that will be incorporated
|
||||
into your certificate request.
|
||||
What you are about to enter is what is called a Distinguished Name or a DN.
|
||||
There are quite a few fields but you can leave some blank
|
||||
For some fields there will be a default value,
|
||||
If you enter '.', the field will be left blank.
|
||||
-----
|
||||
Country Name (2 letter code) [GR]:
|
||||
State or Province Name (full name) [Central Macedonia]:
|
||||
Locality Name (eg, city) [Thessaloniki]:
|
||||
Organization Name (eg, company) [Parabing Creations]:
|
||||
Organizational Unit Name (eg, section) [Parabing]:
|
||||
Common Name (eg, your name or your server's hostname) [delta]:
|
||||
Name [VPNsRUS]:deltaVPN
|
||||
Email Address [nobody@parabing.com]:
|
||||
|
||||
Please enter the following 'extra' attributes
|
||||
to be sent with your certificate request
|
||||
A challenge password []:
|
||||
An optional company name []:
|
||||
Using configuration from /etc/openvpn/easy-rsa/openssl-1.0.0.cnf
|
||||
Check that the request matches the signature
|
||||
Signature ok
|
||||
The Subject's Distinguished Name is as follows
|
||||
countryName :PRINTABLE:'GR'
|
||||
stateOrProvinceName :PRINTABLE:'Central Macedonia'
|
||||
localityName :PRINTABLE:'Thessaloniki'
|
||||
organizationName :PRINTABLE:'Parabing Creations'
|
||||
organizationalUnitName:PRINTABLE:'Parabing'
|
||||
commonName :PRINTABLE:'delta'
|
||||
name :PRINTABLE:'deltaVPN'
|
||||
emailAddress :IA5STRING:'nobody@parabing.com'
|
||||
Certificate is to be certified until Apr 7 08:06:02 2024 GMT (3650 days)
|
||||
Sign the certificate? [y/n]:y
|
||||
|
||||
1 out of 1 certificate requests certified, commit? [y/n]y
|
||||
Write out database with 1 new entries
|
||||
Data Base Updated
|
||||
root@delta:/etc/openvpn/easy-rsa#
|
||||
|
||||
The script successfully finished and we got a certificate (keys/delta.crt) as well as a private key (keys/delta.key) for our server. Note that the server certificate is signed by the CA’s private key.
|
||||
|
||||
### Step 04 -- Diffie-Hellman parameters ###
|
||||
|
||||
The secure passing of keys over an insecure communications channel is made possible thanks to a well-known technique involving the so called Diffie-Hellman parameters. To generate those we just type
|
||||
|
||||
root@delta:/etc/openvpn/easy-rsa# sh build-dh
|
||||
Generating DH parameters, 2048 bit long safe prime, generator 2
|
||||
This is going to take a long time
|
||||
.......................+.....................................+..
|
||||
...........................+..+.....................+...........
|
||||
..............................................+.................
|
||||
.......................+........................................
|
||||
................................................+...............
|
||||
.......................................++*++*++*
|
||||
root@delta:/etc/openvpn/easy-rsa#
|
||||
|
||||
The certificates, private keys and the file containing the Diffie-Hellman parameters we just generated, are all stored into the /etc/openvpn/easy-rsa/keys directory. So up until now we have five files in total and in our case they are as follows:
|
||||
|
||||
1. **ca.crt** – the certificate of the Certificate Authority
|
||||
2. **ca.key** – the private key of the CA
|
||||
3. **delta.crt** – the certificate of the OpenVPN server
|
||||
4. **delta.key** – the private key of the OpenVPN server
|
||||
5. **dh2048.pem** – the Diffie-Hellman parameters file
|
||||
|
||||
In all likelihood, the keys for your own OpenVPN server are named differently. We now need to copy all files but the ca.key over to the /etc/openvpn directory:
|
||||
|
||||
root@delta:/etc/openvpn/easy-rsa# cd keys
|
||||
root@delta:/etc/openvpn/easy-rsa/keys# cp ca.crt delta.crt delta.key dh2048.pem /etc/openvpn
|
||||
root@delta:/etc/openvpn/easy-rsa/keys# cd ..
|
||||
root@delta:/etc/openvpn/easy-rsa#
|
||||
|
||||
### Step 05 -- Certificates and private keys for the OpenVPN clients ###
|
||||
|
||||
Let’s assume we’d like to connect to the OpenVPN server from our laptop. That’s actually a very common scenario and in order to be able to do so we first need to generate a certificate as well as a private key for the client, i.e. our laptop. There’s a script for that and it lives in the /etc/openvpn/easy-rsa directory:
|
||||
|
||||
root@delta:/etc/openvpn/easy-rsa# source vars
|
||||
NOTE: If you run ./clean-all, I will be doing a rm -rf on /etc/openvpn/easy-rsa/keys
|
||||
root@delta:/etc/openvpn/easy-rsa# ./build-key laptop
|
||||
Generating a 1024 bit RSA private key
|
||||
.......................................++++++
|
||||
...................................................................................................++++++
|
||||
writing new private key to 'laptop.key'
|
||||
-----
|
||||
You are about to be asked to enter information that will be incorporated
|
||||
into your certificate request.
|
||||
What you are about to enter is what is called a Distinguished Name or a DN.
|
||||
There are quite a few fields but you can leave some blank
|
||||
For some fields there will be a default value,
|
||||
If you enter '.', the field will be left blank.
|
||||
-----
|
||||
Country Name (2 letter code) [GR]:
|
||||
State or Province Name (full name) [Central Macedonia]:
|
||||
Locality Name (eg, city) [Thessaloniki]:
|
||||
Organization Name (eg, company) [Parabing Creations]:
|
||||
Organizational Unit Name (eg, section) [Parabing]:
|
||||
Common Name (eg, your name or your server's hostname) [laptop]:
|
||||
Name [VPNsRUS]:
|
||||
Email Address [nobody@parabing.com]:
|
||||
|
||||
Please enter the following 'extra' attributes
|
||||
to be sent with your certificate request
|
||||
A challenge password []:
|
||||
An optional company name []:
|
||||
Using configuration from /etc/openvpn/easy-rsa/openssl-1.0.0.cnf
|
||||
Check that the request matches the signature
|
||||
Signature ok
|
||||
The Subject's Distinguished Name is as follows
|
||||
countryName :PRINTABLE:'GR'
|
||||
stateOrProvinceName :PRINTABLE:'Central Macedonia'
|
||||
localityName :PRINTABLE:'Thessaloniki'
|
||||
organizationName :PRINTABLE:'Parabing Creations'
|
||||
organizationalUnitName:PRINTABLE:'Parabing'
|
||||
commonName :PRINTABLE:'laptop'
|
||||
name :PRINTABLE:'VPNsRUS'
|
||||
emailAddress :IA5STRING:'nobody@parabing.com'
|
||||
Certificate is to be certified until Apr 7 18:00:51 2024 GMT (3650 days)
|
||||
Sign the certificate? [y/n]:y
|
||||
|
||||
1 out of 1 certificate requests certified, commit? [y/n]y
|
||||
Write out database with 1 new entries
|
||||
Data Base Updated
|
||||
root@delta:/etc/openvpn/easy-rsa#
|
||||
|
||||
The base name we chose for the keys was “laptop”, so after the build-key finished we got keys/laptop.crt (certificate) and keys/laptop.key (private key). Those two keys for the particular client along with the CA’s certificate file go together, and it’s a good idea to copy them to a directory where our user (sub0) has full access to. We can, for example, create a new directory in the user’s home directory and copy those three files there:
|
||||
|
||||
root@delta:/etc/openvpn/easy-rsa# mkdir /home/sub0/ovpn-client
|
||||
root@delta:/etc/openvpn/easy-rsa# cd keys
|
||||
root@delta:/etc/openvpn/easy-rsa/keys# cp ca.crt laptop.crt laptop.key /home/sub0/ovpn-client
|
||||
root@delta:/etc/openvpn/easy-rsa/keys# chown -R sub0:sub0 /home/sub0/ovpn-client
|
||||
root@delta:/etc/openvpn/easy-rsa/keys# cd ..
|
||||
root@delta:/etc/openvpn/easy-rsa#
|
||||
|
||||
The directory ovpn-client must be securely copied to our laptop. We are allowed to distribute those three files to more than one clients, as long as they are all ours. Of course, should we need a different certificate-private key couple, we run the build-key script again.
|
||||
|
||||
### Step 06 -- OpenVPN server configuration ###
|
||||
|
||||
In a little while our OpenVPN server will be up and running. But first, there are some configuration changes that need to be made. There’s a sample configuration file in /usr/share/doc/openvpn/examples/sample-config-files which is excellent for our setup. That file is named server.conf.gz:
|
||||
|
||||
root@delta:/etc/openvpn/easy-rsa# cd /etc/openvpn
|
||||
root@delta:/etc/openvpn# cp /usr/share/doc/openvpn/examples/sample-config-files/server.conf.gz .
|
||||
root@delta:/etc/openvpn# gunzip -d server.conf.gz
|
||||
root@delta:/etc/openvpn# mv server.conf delta.conf
|
||||
root@delta:/etc/openvpn#
|
||||
|
||||
As you can see, we copied server.conf.gz into the /etc/openvpn directory, uncompressed it and renamed it to delta.conf. You may choose any name you like for your OpenVPN server’s configuration file, as long as it has the “.conf” extension. Whatever the base name, we now open the configuration file with nano:
|
||||
|
||||
root@delta:/etc/openvpn# nano delta.conf
|
||||
|
||||
Here are the changes and additions we should make.
|
||||
|
||||
- First, we locate the lines
|
||||
|
||||
cert server.crt
|
||||
key server.key
|
||||
|
||||
and make sure they reflect the names of our OpenVPN server’s certificate and private key. In our case, those lines were changed into
|
||||
|
||||
cert delta.crt
|
||||
key delta.key
|
||||
|
||||
- We locate the line
|
||||
|
||||
dh dh1024.pem
|
||||
|
||||
and replace “1024″ with “2048″:
|
||||
|
||||
dh dh2048.pem
|
||||
|
||||
- At the end of the configuration file we add the following two lines:
|
||||
|
||||
push "redirect-gateway def1"
|
||||
push "dhcp-option DNS 10.8.0.1"
|
||||
|
||||
Those last two lines instruct the clients to use OpenVPN as the default gateway to the Internet, and also use 10.8.0.1 as the server to deal with DNS requests. Notice that 10.8.0.1 is the IP address of the tunnel network interface OpenVPN automatically creates upon startup. If the clients were to use any other server for name resolution, then we would have a situation in which all DNS requests were served from a possibly untrustworthy server. To avoid such DNS leaks, we instruct all OpenVPN clients to use 10.8.0.1 as the DNS server.
|
||||
|
||||
We start our OpenVPN server like this:
|
||||
|
||||
root@delta:/etc/openvpn# service openvpn start
|
||||
|
||||
By default, OpenVPN listens for connections on port 1194/UDP. One way to see that is with the netstat tool:
|
||||
|
||||
root@delta:/etc/openvpn# netstat -anup
|
||||
Active Internet connections (servers and established)
|
||||
Proto Recv-Q Send-Q Local Address Foreign Address State PID/Program name
|
||||
udp 0 0 0.0.0.0:54149 0.0.0.0:* 555/dhclient
|
||||
udp 0 0 0.0.0.0:1194 0.0.0.0:* 3024/openvpn
|
||||
udp 0 0 0.0.0.0:53 0.0.0.0:* 2756/dnsmasq
|
||||
udp 0 0 0.0.0.0:68 0.0.0.0:* 555/dhclient
|
||||
udp6 0 0 :::60622 :::* 555/dhclient
|
||||
udp6 0 0 :::53 :::* 2756/dnsmasq
|
||||
|
||||
All is well, though we have no properly configured DNS server for the clients yet.
|
||||
|
||||
### Step 07 -- A DNS service for OpenVPN clients ###
|
||||
|
||||
That’s why we’ve installed dnsmasq for. We open up its configuration file
|
||||
|
||||
root@delta:/etc/openvpn# nano /etc/dnsmasq.conf
|
||||
|
||||
locate this line
|
||||
|
||||
#listen-address=
|
||||
|
||||
and change it into the following one:
|
||||
|
||||
listen-address=127.0.0.1, 10.8.0.1
|
||||
|
||||
We also locate this line
|
||||
|
||||
#bind-interfaces
|
||||
|
||||
and delete the hash character on the left:
|
||||
|
||||
bind-interfaces
|
||||
|
||||
To make dnsmasq take these changes into account, we just restart the service:
|
||||
|
||||
root@delta:/etc/openvpn# service dnsmasq restart
|
||||
* Restarting DNS forwarder and DHCP server dnsmasq [ OK ]
|
||||
root@delta:/etc/openvpn#
|
||||
|
||||
As it is now, dnsmasq listens for DNS requests from the loopback (lo) and also from the tunnel (tun0) interface. The output of netstat confirms that:
|
||||
|
||||
root@delta:/etc/openvpn# netstat -anup
|
||||
Active Internet connections (servers and established)
|
||||
Proto Recv-Q Send-Q Local Address Foreign Address State PID/Program name
|
||||
udp 0 0 0.0.0.0:57219 0.0.0.0:* 638/dhclient
|
||||
udp 0 0 0.0.0.0:1194 0.0.0.0:* 911/openvpn
|
||||
udp 0 0 127.0.0.1:53 0.0.0.0:* 1385/dnsmasq
|
||||
udp 0 0 10.8.0.1:53 0.0.0.0:* 1385/dnsmasq
|
||||
udp 0 0 0.0.0.0:68 0.0.0.0:* 638/dhclient
|
||||
udp6 0 0 :::39148 :::* 638/dhclient
|
||||
|
||||
### Step 08 -- Router functionality ###
|
||||
|
||||
We want the VM/box our OpenVPN server runs on to behave like a router, and that means that IP forwarding must be enabled. To enable it right now, from the root account we just type
|
||||
|
||||
root@delta:/etc/openvpn# echo "1" > /proc/sys/net/ipv4/ip_forward
|
||||
|
||||
To make this setting persistent across reboots we open up /etc/sysctl.conf
|
||||
|
||||
root@delta:/etc/openvpn# nano /etc/sysctl.conf
|
||||
|
||||
locate the line
|
||||
|
||||
#net.ipv4.ip_forward=1
|
||||
|
||||
and remove the hash character on the left:
|
||||
|
||||
net.ipv4.ip_forward=1
|
||||
|
||||
There are also some iptables-related rules we should activate:
|
||||
|
||||
root@delta:/etc/openvpn# iptables -A FORWARD -m state --state RELATED,ESTABLISHED -j ACCEPT
|
||||
root@delta:/etc/openvpn# iptables -A FORWARD -s 10.8.0.0/24 -j ACCEPT
|
||||
root@delta:/etc/openvpn# iptables -A FORWARD -j REJECT
|
||||
root@delta:/etc/openvpn# iptables -t nat -A POSTROUTING -s 10.8.0.0/24 -o eth0 -j MASQUERADE
|
||||
root@delta:/etc/openvpn#
|
||||
|
||||
And of course we want these rules activated every time Ubuntu boots up, so we add them inside /etc/rc.local:
|
||||
|
||||
#!/bin/sh -e
|
||||
#
|
||||
# rc.local
|
||||
#
|
||||
# This script is executed at the end of each multiuser runlevel.
|
||||
# Make sure that the script will "exit 0" on success or any other
|
||||
# value on error.
|
||||
#
|
||||
# In order to enable or disable this script just change the execution
|
||||
# bits.
|
||||
#
|
||||
# By default this script does nothing.
|
||||
|
||||
iptables -A FORWARD -m state --state RELATED,ESTABLISHED -j ACCEPT
|
||||
iptables -A FORWARD -s 10.8.0.0/24 -j ACCEPT
|
||||
iptables -A FORWARD -j REJECT
|
||||
iptables -t nat -A POSTROUTING -s 10.8.0.0/24 -o eth0 -j MASQUERADE
|
||||
|
||||
service dnsmasq restart
|
||||
|
||||
exit 0
|
||||
|
||||
Please notice the line before the last one:
|
||||
|
||||
service dnsmasq restart
|
||||
|
||||
> This is crucial: During system startup dnsmasq tries to come up before OpenVPN does. But without OpenVPN there is no tunnel interface (tun0) present so naturally dnsmasq fails. A bit later, when /etc/rc.local is read the tun0 interface is present, so at this point we restart dnsmasq and everything is as it's supposed to be.
|
||||
|
||||
### Step 09 -- Client configuration ###
|
||||
|
||||
In Step 05 we created the directory ovpn-client inside our user’s home directory (/home/sub0, in our example). In there we have the CA certificate plus the client certificate and private key. There’s only one file missing and that’s the configuration file for the client. A sample file we can use is inside /usr/share/doc/openvpn/examples/sample-config-files:
|
||||
|
||||
root@delta:/etc/openvpn# exit
|
||||
exit
|
||||
sub0@delta:~$ cd ~/ovpn-client
|
||||
sub0@delta:~/ovpn-client$ cp /usr/share/doc/openvpn/examples/sample-config-files/client.conf .
|
||||
sub0@delta:~/ovpn-client$
|
||||
|
||||
We open up client.conf for editing and immediately locate the following line:
|
||||
|
||||
remote my-server-1 1194
|
||||
|
||||
This “my-server-1″ string is a placeholder and we are now going to replace it for our server’s public domain name or public IP. If we do have a public domain name already assigned to the server, then there’s nothing more to do than put it in place of my-server-1. Things get a tiny bit more involved if there’s no public domain name for our server. What’s the public IP for it? One way to find out is by typing the following:
|
||||
|
||||
sub0@delta:~/ovpn-client$ curl ipecho.net/plain ; echo
|
||||
|
||||
(If instead of a numeric IP address you get an error, just wait a few seconds and try again.) So now we know our server’s public IP, but is it static or dynamic? Well, if we’re dealing with a server at home or even at the office, chances are it has a dynamic IP address. In that case it is advisable to use a free dynamic DNS service, such as the one provided by http://www.noip.com. In the case of NoIP, assuming we have chosen the free domain dnsalias.net then we may end up with a line like this
|
||||
|
||||
remote ovpn.dnsalias.net 1194
|
||||
|
||||
where “ovpn” is the hostname we’ve given to the server. On the other hand, if our server is hosted in the cloud then it probably has a static public IP address. In that case, the remote directive inside client.conf will look like the following:
|
||||
|
||||
remote 1.2.3.4 1194
|
||||
|
||||
There are two more lines we need to modify:
|
||||
|
||||
cert client.crt
|
||||
key client.key
|
||||
|
||||
In our case, the certificate and private key files for the client are named laptop.crt and laptop.key respectively, so our client.conf contains these two lines:
|
||||
|
||||
cert laptop.crt
|
||||
key laptop.key
|
||||
|
||||
After making sure the changes to client.conf are saved, we need to securely transfer the whole ovpn-client directory to the client. One way to do so is by using the scp command (secure copy or copy over SSH). An alternative is provided by the excellent and free FileZilla, which supports FTP over SSH connections (SFTP).
|
||||
|
||||
### Step 10 -- Connecting and testing ###
|
||||
|
||||

|
||||
|
||||
|
||||
So how do we actually connect to the remote OpenVPN server? It all depends on the type of the device we have in hand and of course on the operating system is runs. In a bit we are going to examine the cases of four different OS families — or OS categories, if you will: Linux, Windows, OS X and iOS/Android. Note though that no matter the device or the OS, for the connection to be successful we need to be outside of the OpenVPN server’s local network. In addition, if there’s a firewall in front of the server –and it probably is– then we ought to put a new rule in place which essentially states something like this:
|
||||
|
||||
*Redirect all incoming UDP packets for port 1194 to port 1194/UDP of the server’s public-facing network interface.*
|
||||
|
||||
That’s some simple firewall rule, don’t you think? And without further ado, let’s establish our first connection to the fabulous OpenVPN server of ours.
|
||||
|
||||
**Linux**. All we need is the openvpn package installed. One way to connect to the remote OpenVPN server is to fire up a terminal, change to the ovpn-client directory and from the root user account –or with the assistance of sudo– type something like this:
|
||||
|
||||
/usr/sbin/openvpn --config client.conf
|
||||
|
||||
Anytime we want to terminate the connection we just hit [CTRL+C].
|
||||
|
||||
**Windows**. A free OpenVPN client is the so called [OpenVPN Desktop Client][3]. The configuration file client.conf must be renamed to client.ovpn and that’s the file we should give to the OpenVPN Desktop Client. The application will read client.ovpn and create a new connection profile for the OpenVPN server.
|
||||
|
||||

|
||||
|
||||
**OS X**. A free OpenVPN client for OS X is [tunnelblick][4]. There is also [Viscosity][5] which is commercial and happens to be our favorite. Viscosity will read client.conf and create a new connection profile for the remote server.
|
||||
|
||||
iOS/Android. An excellent choice is OpenVPN connect. It is free of charge and available from the [App Store][6] as well as the Google [Play store][7].
|
||||
|
||||
Regardless of the computing platform, sometimes we’d like to check if we’re actually using the OpenVPN server we think we’re using. One way to do that is by following this simple 4-step procedure:
|
||||
|
||||
Prior to connecting to the OpenVPN server we…
|
||||
|
||||
- visit a site such as [whatip.com][8] and take note of our public IP
|
||||
- visit [dnsleaktest.com][10, perform the standard test, take note of the name servers we’re using
|
||||
|
||||

|
||||
|
||||
After connecting to the OpenVPN server we repeat the above two steps. If we get two different public IPs, this means we do go out on the net through the remote OpenVPN server. In addition, if we get two different sets of name servers, then there are no DNS leaks.
|
||||
|
||||
### Final thoughts ###
|
||||
|
||||
I use three different OpenVPN servers, all custom-made. One of them runs on the pfSense router at my home office in Thessaloniki, Greece. I use this server when I’m out of office and want secure access to the home LAN. The other two OpenVPN servers are hosted on two different VPSes, one in Reykjavik, Iceland, and the other in New Jersey, USA. Whenever I’m out and about and feel like using a random WiFi hotspot, I don’t even have to think of the security implications: I simply connect to the Reykjavik server and start surfing the web normally. There are also some times when I want to casually check out a service which is geographically restricted to the US. In these not-so-common cases the New Jersey server comes in handy, for when I connect to it I get a public IP from the U, S of A and hence access to that otherwise restricted service. It is worth noting that some service providers maintain blacklists with numerous well-known VPN companies. And that’s *exactly* one of the advantages of setting up your own OpenVPN server on a VPS provider of your choosing: It’s unlikely that this provider is blacklisted.
|
||||
|
||||
No matter where the physical location of your server is, OpenVPN ensures that the traffic flow between the client and the server is strongly encrypted. What happens to the traffic leaving the OpenVPN server is another story. Depending on the application-layer protocol it may still be encrypted, but it could be unencrypted as well. So unless you have absolute control of the OpenVPN server and of the local network it belongs to, you cannot fully trust the administrator at the other end. The moral of this is apparent: If you really care about your privacy, then you should keep in mind that your own behavior may indeed undermine it.
|
||||
|
||||
One example will hopefully get the point across. You have a well configured OpenVPN server in the cloud. You use any random WiFi hotspot anytime you feel like it and without the slightest bit of worry, thanks to that heroic OpenVPN server. Then you fire up your favorite mail client to get your email from this good, old mail server which still uses plain SMTP. Guess what? Your username and password leave the OpenVPN server in plain text, i.e. unencrypted. At the same time a bored administrator in the vicinity of the OpenVPN server could be easily sniffing-out your credentials and storing them in their ever-growing list named “random happy people.txt”.
|
||||
|
||||
So what do you do? Simple. You continue using your OpenVPN server, but refrain from using applications which talk old and/or insecure protocols.
|
||||
|
||||
Enjoy your brand new OpenVPN server!
|
||||
|
||||
--------------------------------------------------------------------------------
|
||||
|
||||
via: http://parabing.com/2014/06/openvpn-on-ubuntu/
|
||||
|
||||
译者:[译者ID](https://github.com/译者ID) 校对:[校对者ID](https://github.com/校对者ID)
|
||||
|
||||
本文由 [LCTT](https://github.com/LCTT/TranslateProject) 原创翻译,[Linux中国](http://linux.cn/) 荣誉推出
|
||||
|
||||
[1]:http://en.wikipedia.org/wiki/Openvpn
|
||||
[2]:http://www.ubuntu.com/server
|
||||
[3]:http://swupdate.openvpn.net/downloads/openvpn-client.msi
|
||||
[4]:https://code.google.com/p/tunnelblick
|
||||
[5]:https://www.sparklabs.com/viscosity
|
||||
[6]:https://itunes.apple.com/us/app/openvpn-connect/id590379981?mt=8
|
||||
[7]:https://play.google.com/store/apps/details?id=net.openvpn.openvpn
|
||||
[8]:http://www.whatip.com/
|
||||
[9]:https://dnsleaktest.com/
|
||||
@ -1,89 +0,0 @@
|
||||
How to access SoundCloud from the command line in Linux
|
||||
================================================================================
|
||||
If you enjoy music streaming and originally-created sounds, you cannot have missed [SoundCloud][1]. Based in Germany, this cloud streaming service is now famous and well-established for any music adventurer. And naturally, as a Linux enthusiast, you might wonder how to join your passion for Linux with your love for music. As a solution, I advise you to check out Soundcloud2000, **a command line client for SoundCloud** born out of the [Music Hack Day Stockholm '13][2].
|
||||
|
||||
### Installation ###
|
||||
|
||||
For Debian or Ubuntu users, install via:
|
||||
|
||||
$ sudo apt-get install portaudio19-dev libmpg123-dev libncurses-dev ruby1.9.1-dev
|
||||
$ sudo gem install soundcloud2000
|
||||
|
||||
For Archlinux users, the package is available in [AUR][3].
|
||||
|
||||
For Fedora users, install via:
|
||||
|
||||
$ sudo yum install portaudio-devel libmpg123-devel ncurses-devel ruby-devel
|
||||
$ sudo gem install soundcloud2000
|
||||
|
||||
For CentOS users, install or upgrade to the [latest Ruby/RubyGems][4] (1.9 and higher), enable [Repoforge repo][5], and install via:
|
||||
|
||||
$ sudo yum install portaudio-devel mpg123-devel
|
||||
$ sudo gem install curses soundcloud2000
|
||||
|
||||
And finally, go to the official github page for the sources.
|
||||
|
||||
### Usage ###
|
||||
|
||||
Soundcloud2000 is very easy to pick up. Some might even say simplistic. I like it for that sobriety and the effort of the three authors and contributors. Launch it via:
|
||||
|
||||
$ soundcloud2000
|
||||
|
||||
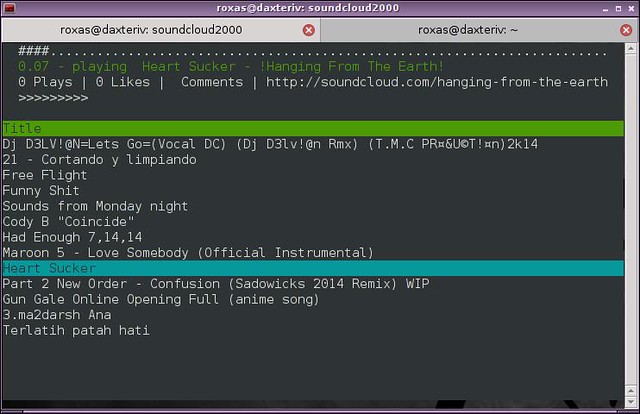
From there, you will be welcomed with a splash screen:
|
||||
|
||||

|
||||
|
||||
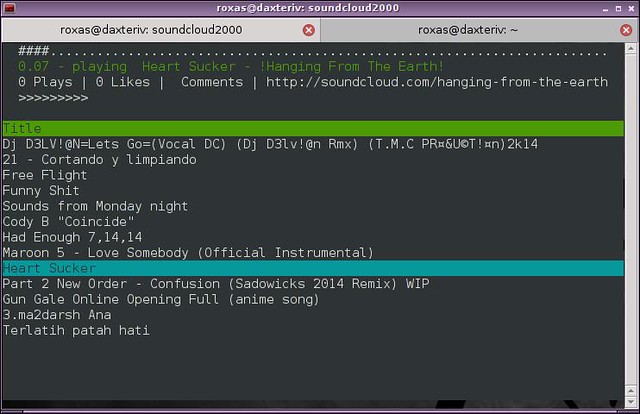
and then a list of songs:
|
||||
|
||||
|
||||
|
||||
You can scroll through the list via the up and down keys, play a song with enter, pause/resume with the space bar, and fast forward/rewind with the right and left arrow keys. As you can see, nothing groundbreaking but definitely ergonomic.
|
||||
|
||||
If the random list is too long to scroll through, you have an option to see all the tracks for a particular user by hitting the 'u' key and then typing his name.
|
||||
|
||||

|
||||
|
||||
That is probably one of the major defaults of Soundcloud2000. While the navigation is not optimized, I have high hopes for improvements and support as the software is still very young.
|
||||
|
||||
### Bonus ###
|
||||
|
||||
Another alternative as a bonus: if you like the idea of using SoundCloud from a terminal, but do not want to install any additional software (or maybe you cannot), I advise you to go to [cmd.fm][6]. The website is a kind of camouflage for SoundCloud, as it hides it behind a shell interface.
|
||||
|
||||
[][7]
|
||||
|
||||
Type "help" for a list of commands, which is a lot longer than for Soundcloud2000. As examples, I noticed:
|
||||
|
||||
- _genres to list all genres
|
||||
- _play random to play a random track
|
||||
- _pause to pause the current track
|
||||
- _playlist new to make a new playlist
|
||||
- _loop to loop current track
|
||||
- _cinema to watch and ASCII version of Star Wars which completely blew my mind.
|
||||
|
||||
And it even supports auto-completion via the tabulation key for genres.
|
||||
|
||||
To conclude, Soundcloud2000 is a neat program that does exactly what it is supposed to. We can forgive its current flaws as they are surely tied to its youth. I really hope that it will grow and include more features (and potentially get inspiration from cmd.fm).
|
||||
|
||||
If you like the idea, I invite you to support the programmers, and if you like these kinds of initiatives, support [Music Hack Day][8] which mixes software development and music.
|
||||
|
||||
What do you think of using SoundCloud from the command line? Please let us know in the comments.
|
||||
|
||||
--------------------------------------------------------------------------------
|
||||
|
||||
via: http://xmodulo.com/2014/07/access-soundcloud-command-line-linux.html
|
||||
|
||||
原文作者:[Adrien Brochard][a]
|
||||
|
||||
译者:[译者ID](https://github.com/译者ID) 校对:[校对者ID](https://github.com/校对者ID)
|
||||
|
||||
本文由 [LCTT](https://github.com/LCTT/TranslateProject) 原创翻译,[Linux中国](http://linux.cn/) 荣誉推出
|
||||
|
||||
[a]:http://xmodulo.com/author/adrien
|
||||
[1]:https://soundcloud.com/
|
||||
[2]:https://www.hackerleague.org/hackathons/music-hack-day-stockholm-13/
|
||||
[3]:https://aur.archlinux.org/packages/ruby-soundcloud2000/
|
||||
[4]:http://ask.xmodulo.com/upgrade-ruby-centos.html
|
||||
[5]:http://xmodulo.com/2013/01/how-to-set-up-rpmforge-repoforge-repository-on-centos.html
|
||||
[6]:https://cmd.fm/
|
||||
[7]:https://www.flickr.com/photos/xmodulo/14494448218/
|
||||
[8]:http://new.musichackday.org/
|
||||
@ -0,0 +1,500 @@
|
||||
2q1w2007翻译中
|
||||
搭建并运行OpenVPN,享受你的隐私生活
|
||||
================================================================================
|
||||

|
||||
|
||||
> 我们支持保护隐私,不为我们有自己的秘密需要保护,只是我们认为保护隐私应该成为一项基本人权。所以我们坚信无论谁在什么时候行使这项权利,都应该不受拘束的获取必须的工具和服务。OpenVPN就是这样一种服务并且有多种工具(客户端) 来让我们利用并享受这种服务。
|
||||
|
||||
通过与一个[OpenVPN][1]服务器建立连接,我们基本上在我们的设备和远端运行OpenVPN的主机之间建立了一个安全的通信通道。尽管在两个端点之间的通信可能被截获,但是信息是经过高强度加密的所以实际上它对于攻击者没什么用。OpenVPN除了扮演加密通信通道的调解人,我们也可以通过设置使服务器扮演因特网网管的角色。通过这种方式,我们可以连接任何不安全的Wifi,然后迅速的链接到远程的OpenVPN服务器并在不需要考虑偷窥的人或者无聊的管理员的情况下运行需要上网的程序。(注意:OpenVPN服务器旁还是需要信任的管理员的。)
|
||||
|
||||
这篇文章将一步一步的教会你如何在[Ubuntu Server 14.04 LTS][2]上安装OpenVPN。OpenVPN所在的主机可能是云上的一台VPS,一台在我们家里某台电脑上运行的虚拟机,或者是一个老到你都快忘了的设备。
|
||||
|
||||
### 第一步 -- 准备系统 ###
|
||||
|
||||
我们需要Ubuntu Server主机的一个命令行终端,比如通过SSH从远程访问它。首先需要更新它的本地仓库数据:
|
||||
|
||||
sub0@delta:~$ sudo apt-get update
|
||||
|
||||
进行操作系统和已安装的包的升级,输入:
|
||||
|
||||
sub0@delta:~$ sudo apt-get dist-upgrade
|
||||
|
||||
如果升级了新内核,那就需要重启。当更新完成后,就该安装OpenVPN了:
|
||||
|
||||
sub0@delta:~$ sudo apt-get -y install openvpn easy-rsa dnsmasq
|
||||
|
||||
注意,我们用apt-get安装了三个包:
|
||||
|
||||
- openvpn提供了OpenVPN的核心
|
||||
- easy-rsa包含了一些有用的密钥管理脚本
|
||||
- dnsmasq是当我们的OpenVPN所在的主机将扮演客户端的路由器时会用到的域名服务器
|
||||
|
||||
### 第二步 -- 生成证书和私钥 ###
|
||||
|
||||
这是安装OpenVPN中最重要和最关键的一步,目的是建立公钥基础设施(PKI)。包括如下内容:
|
||||
|
||||
- 为OpenVPN服务器创建一个证书(公钥)和一个私钥
|
||||
- 为每个OpenVPN客户端创建证书和私钥
|
||||
- 建立一个证书颁发机构(CA)并创建证书和私钥。这个私钥用来给OpenVPN服务器和客户端的证书签名
|
||||
|
||||
从最后一个做起,我们先建立一个目录:
|
||||
|
||||
sub0@delta:~$ sudo mkdir /etc/openvpn/easy-rsa
|
||||
|
||||
然后把easy-rsa的文件拷过去:
|
||||
|
||||
sub0@delta:~$ sudo cp -r /usr/share/easy-rsa/* /etc/openvpn/easy-rsa
|
||||
|
||||
在我们创建CA的私钥之前,我们先编辑/etc/openvpn/easy-rsa/vars(我们喜欢用nano,不过这只是我们的喜好,你爱用什么用什么):
|
||||
|
||||
sub0@delta:~$ sudo nano /etc/openvpn/easy-rsa/vars
|
||||
|
||||
在文件的尾部,我们设置主证书和密钥的信息:
|
||||
|
||||
export KEY_COUNTRY="GR"
|
||||
export KEY_PROVINCE="Central Macedonia"
|
||||
export KEY_CITY="Thessaloniki"
|
||||
export KEY_ORG="Parabing Creations"
|
||||
export KEY_EMAIL="nobody@parabing.com"
|
||||
export KEY_CN="VPNsRUS"
|
||||
export KEY_NAME="VPNsRUS"
|
||||
export KEY_OU="Parabing"
|
||||
export KEY_ALTNAMES="VPNsRUS"
|
||||
|
||||
你可以根据自己的情况设置不同的值。特别注意最后KEY_ALTNAMES这一行,尽管这不是原本vars文件中有的但是我们还是把它加到文件的尾部,不然build-ca脚本会运行失败。
|
||||
|
||||
保存更改,我们得按[CTRL+O]然后按[Enter]。想退出nano,请按[CTRL+X]。现在,我们要获得root访问权限,继续生成主证书和私钥(LCTT译注:请注意命令行账户发生了改变):
|
||||
|
||||
sub0@delta:~$ sudo su
|
||||
root@delta:/home/sub0# cd /etc/openvpn/easy-rsa
|
||||
root@delta:/etc/openvpn/easy-rsa# source vars
|
||||
NOTE: If you run ./clean-all, I will be doing a rm -rf on /etc/openvpn/easy-rsa/keys
|
||||
root@delta:/etc/openvpn/easy-rsa# sh clean-all
|
||||
root@delta:/etc/openvpn/easy-rsa# sh build-ca
|
||||
Generating a 1024 bit RSA private key
|
||||
...++++++
|
||||
................++++++
|
||||
writing new private key to 'ca.key'
|
||||
-----
|
||||
You are about to be asked to enter information that will be incorporated
|
||||
into your certificate request.
|
||||
What you are about to enter is what is called a Distinguished Name or a DN.
|
||||
There are quite a few fields but you can leave some blank
|
||||
For some fields there will be a default value,
|
||||
If you enter '.', the field will be left blank.
|
||||
-----
|
||||
Country Name (2 letter code) [GR]:
|
||||
State or Province Name (full name) [Central Macedonia]:
|
||||
Locality Name (eg, city) [Thessaloniki]:
|
||||
Organization Name (eg, company) [Parabing Creations]:
|
||||
Organizational Unit Name (eg, section) [Parabing]:
|
||||
Common Name (eg, your name or your server's hostname) [VPNsRUS]:
|
||||
Name [VPNsRUS]:
|
||||
Email Address [nobody@parabing.com]:
|
||||
root@delta:/etc/openvpn/easy-rsa#
|
||||
|
||||
在我们的实例中,所有问题的答案都选择了默认的。在运行了build-ca脚本后,我们就获得了主证书文件(keys/ca.crt)和对应的私钥(keys/ca.key)。私钥必须不计代价的保密。
|
||||
|
||||
### 第三步 -- 生成OpenVPN服务器的证书和私钥 ###
|
||||
|
||||
在我们为OpenVPN服务器生成证书和密钥之前,我们得给他起个名。我决定把它叫"delta",然后运行build-key-server脚本来获取证书和密钥:
|
||||
|
||||
root@delta:/etc/openvpn/easy-rsa# sh build-key-server delta
|
||||
Generating a 1024 bit RSA private key
|
||||
....++++++
|
||||
...++++++
|
||||
writing new private key to 'delta.key'
|
||||
-----
|
||||
You are about to be asked to enter information that will be incorporated
|
||||
into your certificate request.
|
||||
What you are about to enter is what is called a Distinguished Name or a DN.
|
||||
There are quite a few fields but you can leave some blank
|
||||
For some fields there will be a default value,
|
||||
If you enter '.', the field will be left blank.
|
||||
-----
|
||||
Country Name (2 letter code) [GR]:
|
||||
State or Province Name (full name) [Central Macedonia]:
|
||||
Locality Name (eg, city) [Thessaloniki]:
|
||||
Organization Name (eg, company) [Parabing Creations]:
|
||||
Organizational Unit Name (eg, section) [Parabing]:
|
||||
Common Name (eg, your name or your server's hostname) [delta]:
|
||||
Name [VPNsRUS]:deltaVPN
|
||||
Email Address [nobody@parabing.com]:
|
||||
|
||||
Please enter the following 'extra' attributes
|
||||
to be sent with your certificate request
|
||||
A challenge password []:
|
||||
An optional company name []:
|
||||
Using configuration from /etc/openvpn/easy-rsa/openssl-1.0.0.cnf
|
||||
Check that the request matches the signature
|
||||
Signature ok
|
||||
The Subject's Distinguished Name is as follows
|
||||
countryName :PRINTABLE:'GR'
|
||||
stateOrProvinceName :PRINTABLE:'Central Macedonia'
|
||||
localityName :PRINTABLE:'Thessaloniki'
|
||||
organizationName :PRINTABLE:'Parabing Creations'
|
||||
organizationalUnitName:PRINTABLE:'Parabing'
|
||||
commonName :PRINTABLE:'delta'
|
||||
name :PRINTABLE:'deltaVPN'
|
||||
emailAddress :IA5STRING:'nobody@parabing.com'
|
||||
Certificate is to be certified until Apr 7 08:06:02 2024 GMT (3650 days)
|
||||
Sign the certificate? [y/n]:y
|
||||
|
||||
1 out of 1 certificate requests certified, commit? [y/n]y
|
||||
Write out database with 1 new entries
|
||||
Data Base Updated
|
||||
root@delta:/etc/openvpn/easy-rsa#
|
||||
|
||||
当脚本成功运行完的时候,我们就得到了服务器的证书(keys/delta.crt)和私钥(keys/delta.key)。注意服务器证书被CA的私钥签名了。
|
||||
|
||||
### 第四步 -- 生成Diffie-Hellman参数 ###
|
||||
|
||||
幸亏有了Diffie-Hellman参数,我们才能在不安全的通信通道里安全的交换密钥。为了生成它我们需要键入:
|
||||
|
||||
root@delta:/etc/openvpn/easy-rsa# sh build-dh
|
||||
Generating DH parameters, 2048 bit long safe prime, generator 2
|
||||
This is going to take a long time
|
||||
.......................+.....................................+..
|
||||
...........................+..+.....................+...........
|
||||
..............................................+.................
|
||||
.......................+........................................
|
||||
................................................+...............
|
||||
.......................................++*++*++*
|
||||
root@delta:/etc/openvpn/easy-rsa#
|
||||
|
||||
证书,私钥和包含Diffie-Hellman参数的文件已生成,它们都储存在/etc/openvpn/easy-rsa/keys,所以我们到现在为止已经有如下五个文件了:
|
||||
|
||||
1. **ca.crt** – 证书颁发机构(CA)的证书
|
||||
2. **ca.key** – CA的私钥
|
||||
3. **delta.crt** – OpenVPN服务器的证书
|
||||
4. **delta.key** – OpenVPN服务器的私钥
|
||||
5. **dh2048.pem** – Diffie-Hellman参数文件
|
||||
|
||||
你自己的OpenVPN服务器命名可能和我们的不同。现在我们需要拷贝除了ca.key的文件到/etc/openvpn:
|
||||
|
||||
root@delta:/etc/openvpn/easy-rsa# cd keys
|
||||
root@delta:/etc/openvpn/easy-rsa/keys# cp ca.crt delta.crt delta.key dh2048.pem /etc/openvpn
|
||||
root@delta:/etc/openvpn/easy-rsa/keys# cd ..
|
||||
root@delta:/etc/openvpn/easy-rsa#
|
||||
|
||||
### 第五步 -- 为OpenVPN客户端生成证书和私钥 ###
|
||||
|
||||
试想我们的笔记本要连接OpenVPN服务器。为了实现这个很常见的情况,我们首先需要为客户端(比如:我们的笔记本)生成证书和私钥,在/etc/openvpn/easy-rsa有一个脚本帮我们完成这项工作:
|
||||
|
||||
root@delta:/etc/openvpn/easy-rsa# source vars
|
||||
NOTE: If you run ./clean-all, I will be doing a rm -rf on /etc/openvpn/easy-rsa/keys
|
||||
root@delta:/etc/openvpn/easy-rsa# ./build-key laptop
|
||||
Generating a 1024 bit RSA private key
|
||||
.......................................++++++
|
||||
...................................................................................................++++++
|
||||
writing new private key to 'laptop.key'
|
||||
-----
|
||||
You are about to be asked to enter information that will be incorporated
|
||||
into your certificate request.
|
||||
What you are about to enter is what is called a Distinguished Name or a DN.
|
||||
There are quite a few fields but you can leave some blank
|
||||
For some fields there will be a default value,
|
||||
If you enter '.', the field will be left blank.
|
||||
-----
|
||||
Country Name (2 letter code) [GR]:
|
||||
State or Province Name (full name) [Central Macedonia]:
|
||||
Locality Name (eg, city) [Thessaloniki]:
|
||||
Organization Name (eg, company) [Parabing Creations]:
|
||||
Organizational Unit Name (eg, section) [Parabing]:
|
||||
Common Name (eg, your name or your server's hostname) [laptop]:
|
||||
Name [VPNsRUS]:
|
||||
Email Address [nobody@parabing.com]:
|
||||
|
||||
Please enter the following 'extra' attributes
|
||||
to be sent with your certificate request
|
||||
A challenge password []:
|
||||
An optional company name []:
|
||||
Using configuration from /etc/openvpn/easy-rsa/openssl-1.0.0.cnf
|
||||
Check that the request matches the signature
|
||||
Signature ok
|
||||
The Subject's Distinguished Name is as follows
|
||||
countryName :PRINTABLE:'GR'
|
||||
stateOrProvinceName :PRINTABLE:'Central Macedonia'
|
||||
localityName :PRINTABLE:'Thessaloniki'
|
||||
organizationName :PRINTABLE:'Parabing Creations'
|
||||
organizationalUnitName:PRINTABLE:'Parabing'
|
||||
commonName :PRINTABLE:'laptop'
|
||||
name :PRINTABLE:'VPNsRUS'
|
||||
emailAddress :IA5STRING:'nobody@parabing.com'
|
||||
Certificate is to be certified until Apr 7 18:00:51 2024 GMT (3650 days)
|
||||
Sign the certificate? [y/n]:y
|
||||
|
||||
1 out of 1 certificate requests certified, commit? [y/n]y
|
||||
Write out database with 1 new entries
|
||||
Data Base Updated
|
||||
root@delta:/etc/openvpn/easy-rsa#
|
||||
|
||||
我们为密钥选取的名字是"laptop",当build-key脚本运行完之后,我们就得到了在keys/laptop.crt的证书和在keys/laptop.key的私钥。有了这两个文件和CA的证书,我们得把这三个文件拷贝到用户有(比如用户sub0)权访问的地方。比如我们可以在用户的home目录中新建一个目录并把三个文件拷贝过去:
|
||||
|
||||
root@delta:/etc/openvpn/easy-rsa# mkdir /home/sub0/ovpn-client
|
||||
root@delta:/etc/openvpn/easy-rsa# cd keys
|
||||
root@delta:/etc/openvpn/easy-rsa/keys# cp ca.crt laptop.crt laptop.key /home/sub0/ovpn-client
|
||||
root@delta:/etc/openvpn/easy-rsa/keys# chown -R sub0:sub0 /home/sub0/ovpn-client
|
||||
root@delta:/etc/openvpn/easy-rsa/keys# cd ..
|
||||
root@delta:/etc/openvpn/easy-rsa#
|
||||
|
||||
ovpn-client文件夹必须安全的拷贝到我们的笔记本电脑上。我们可以给多个客户端分发这三个文件。当然了,等我们需要一个不一样的证书-私钥对的时候只要再次运行build-key脚本即可。
|
||||
|
||||
### 第六步 -- OpenVPN服务器设置 ###
|
||||
|
||||
等会我们的OpenVPN服务器就要启动并运行了。但是开始的时候,我们需要更改一些设置。在/usr/share/doc/openvpn/examples/sample-config-files中有一个示例配置文件,它很适合我们的教程,这个文件叫server.conf.gz:
|
||||
|
||||
root@delta:/etc/openvpn/easy-rsa# cd /etc/openvpn
|
||||
root@delta:/etc/openvpn# cp /usr/share/doc/openvpn/examples/sample-config-files/server.conf.gz .
|
||||
root@delta:/etc/openvpn# gunzip -d server.conf.gz
|
||||
root@delta:/etc/openvpn# mv server.conf delta.conf
|
||||
root@delta:/etc/openvpn#
|
||||
|
||||
如你所见,我们把server.conf.gz拷贝到/etc/openvpn,解压并重命名到delta.conf。你可以按个人喜好给OpenVPN服务器配置文件取名字,但是它必须有".conf"扩展名。我们现在用nano打开配置文件:
|
||||
|
||||
root@delta:/etc/openvpn# nano delta.conf
|
||||
|
||||
下面是我们应该做出的更改。
|
||||
|
||||
- 首先,定位到这一行
|
||||
|
||||
cert server.crt
|
||||
key server.key
|
||||
|
||||
确认OpenVPN服务器证书和私钥的位置和名称,在我们的例子中,这两行要改成
|
||||
|
||||
cert delta.crt
|
||||
key delta.key
|
||||
|
||||
- 然后定位到这一行
|
||||
|
||||
dh dh1024.pem
|
||||
|
||||
用"2048"代替"1024":
|
||||
|
||||
dh dh2048.pem
|
||||
|
||||
- 在配置文件的末尾,我们添加下面这两行:
|
||||
|
||||
push "redirect-gateway def1"
|
||||
push "dhcp-option DNS 10.8.0.1"
|
||||
|
||||
最后这两行指示客户端用OpenVPN作为默认的网关,并用10.8.0.1作为DNS服务器。注意10.8.0.1是OpenVPN启动时自动创建的隧道接口的IP。如果客户用别的域名解析服务,那么我们就得提防不安全的DNS服务器。为了避免这种泄露,我们建议所有OpenVPN客户端使用10.8.0.1作为DNS服务器。
|
||||
|
||||
我们以这种方式来开始运行OpenVPN服务器:
|
||||
|
||||
root@delta:/etc/openvpn# service openvpn start
|
||||
|
||||
默认的,OpenVPN服务器监听1194/UDP端口。一种查看的方法是使用netstat工具:
|
||||
|
||||
root@delta:/etc/openvpn# netstat -anup
|
||||
Active Internet connections (servers and established)
|
||||
Proto Recv-Q Send-Q Local Address Foreign Address State PID/Program name
|
||||
udp 0 0 0.0.0.0:54149 0.0.0.0:* 555/dhclient
|
||||
udp 0 0 0.0.0.0:1194 0.0.0.0:* 3024/openvpn
|
||||
udp 0 0 0.0.0.0:53 0.0.0.0:* 2756/dnsmasq
|
||||
udp 0 0 0.0.0.0:68 0.0.0.0:* 555/dhclient
|
||||
udp6 0 0 :::60622 :::* 555/dhclient
|
||||
udp6 0 0 :::53 :::* 2756/dnsmasq
|
||||
|
||||
看起来一切运行的不错,但是我们还没设置DNS服务器呢。
|
||||
|
||||
### 第七步 -- 为OpenVPN客户端搭建DNS ###
|
||||
|
||||
这就是为什么我们要安装dnsmasq,打开它的配置文件。
|
||||
|
||||
root@delta:/etc/openvpn# nano /etc/dnsmasq.conf
|
||||
|
||||
定位到这行:
|
||||
|
||||
#listen-address=
|
||||
|
||||
把它换成下面这样:
|
||||
|
||||
listen-address=127.0.0.1, 10.8.0.1
|
||||
|
||||
然后定位到这行:
|
||||
|
||||
#bind-interfaces
|
||||
|
||||
把"#"删了:
|
||||
|
||||
bind-interfaces
|
||||
|
||||
为了让dnsmasq应用这些更改,我们重启它:
|
||||
|
||||
root@delta:/etc/openvpn# service dnsmasq restart
|
||||
* Restarting DNS forwarder and DHCP server dnsmasq [ OK ]
|
||||
root@delta:/etc/openvpn#
|
||||
|
||||
现在,dnamasq在本地回环(lo)和隧道(tun0)接口监听DNS请求。netstat的输出看起来是这个样子的:
|
||||
|
||||
root@delta:/etc/openvpn# netstat -anup
|
||||
Active Internet connections (servers and established)
|
||||
Proto Recv-Q Send-Q Local Address Foreign Address State PID/Program name
|
||||
udp 0 0 0.0.0.0:57219 0.0.0.0:* 638/dhclient
|
||||
udp 0 0 0.0.0.0:1194 0.0.0.0:* 911/openvpn
|
||||
udp 0 0 127.0.0.1:53 0.0.0.0:* 1385/dnsmasq
|
||||
udp 0 0 10.8.0.1:53 0.0.0.0:* 1385/dnsmasq
|
||||
udp 0 0 0.0.0.0:68 0.0.0.0:* 638/dhclient
|
||||
udp6 0 0 :::39148 :::* 638/dhclient
|
||||
|
||||
### 第八步 -- 路由功能 ###
|
||||
|
||||
我们希望在一些"盒子"或虚拟机上运行的OpneVPN有路由的功能,这意味着要开启IP转发.为了打开它,我们用root账户键入:
|
||||
|
||||
root@delta:/etc/openvpn# echo "1" > /proc/sys/net/ipv4/ip_forward
|
||||
|
||||
为了让这个设置重启也好用,我们编辑 /etc/sysctl.conf:
|
||||
|
||||
root@delta:/etc/openvpn# nano /etc/sysctl.conf
|
||||
|
||||
编辑这行:
|
||||
|
||||
#net.ipv4.ip_forward=1
|
||||
|
||||
把"#"删了:
|
||||
|
||||
net.ipv4.ip_forward=1
|
||||
|
||||
还需要激活一些iptables相关的规则:
|
||||
|
||||
root@delta:/etc/openvpn# iptables -A FORWARD -m state --state RELATED,ESTABLISHED -j ACCEPT
|
||||
root@delta:/etc/openvpn# iptables -A FORWARD -s 10.8.0.0/24 -j ACCEPT
|
||||
root@delta:/etc/openvpn# iptables -A FORWARD -j REJECT
|
||||
root@delta:/etc/openvpn# iptables -t nat -A POSTROUTING -s 10.8.0.0/24 -o eth0 -j MASQUERADE
|
||||
root@delta:/etc/openvpn#
|
||||
|
||||
当然了,我们希望每次Ubuntu启动的时候,这些规则都好用。所以我们得把它们加到/etc/rc.local里:
|
||||
|
||||
#!/bin/sh -e
|
||||
#
|
||||
# rc.local
|
||||
#
|
||||
# This script is executed at the end of each multiuser runlevel.
|
||||
# Make sure that the script will "exit 0" on success or any other
|
||||
# value on error.
|
||||
#
|
||||
# In order to enable or disable this script just change the execution
|
||||
# bits.
|
||||
#
|
||||
# By default this script does nothing.
|
||||
|
||||
iptables -A FORWARD -m state --state RELATED,ESTABLISHED -j ACCEPT
|
||||
iptables -A FORWARD -s 10.8.0.0/24 -j ACCEPT
|
||||
iptables -A FORWARD -j REJECT
|
||||
iptables -t nat -A POSTROUTING -s 10.8.0.0/24 -o eth0 -j MASQUERADE
|
||||
|
||||
service dnsmasq restart
|
||||
|
||||
exit 0
|
||||
|
||||
请注意倒数第二行:
|
||||
|
||||
service dnsmasq restart
|
||||
|
||||
> 这非常重要:在系统启动时,dnsmasq会尝试在OpenVPN之前启动。但是OpenVPN启动之前是没有隧道(tun0)接口的,所以dnsmasq自然就挂了。过了一阵,当/etc/rc.local读到隧道(tun0)接口出现时,它会在这时重启dnsmasq然后就一切如你所愿了。
|
||||
|
||||
### 第九步 -- 客户端设置 ###
|
||||
|
||||
在第五步,我们在用户的home目录里我们建立了ovpn-client文件夹(在我们的例子里是/home/sub0)。在哪里有CA的证书和客户端证书和私钥。现在只缺客户端配置文件了,在/usr/share/doc/openvpn/examples/sample-config-files有一个示例配置文件:
|
||||
|
||||
root@delta:/etc/openvpn# exit
|
||||
exit
|
||||
sub0@delta:~$ cd ~/ovpn-client
|
||||
sub0@delta:~/ovpn-client$ cp /usr/share/doc/openvpn/examples/sample-config-files/client.conf .
|
||||
sub0@delta:~/ovpn-client$
|
||||
|
||||
我们编需要辑client.conf,定位到这一行:
|
||||
|
||||
remote my-server-1 1194
|
||||
|
||||
"my-server-1"是一个占位符,现在我们要把它换成我们自己服务器的公网域名或IP。如果我们已经给服务器分配域名了,那只要把它填到my-server-1的位置。如果没有域名,那么得获取公网IP。如何获取呢?一种方式是键入下列命令:
|
||||
|
||||
sub0@delta:~/ovpn-client$ curl ipecho.net/plain ; echo
|
||||
|
||||
(如果不是一个数字的IP地址, 或是发生错误,那就等会再试。)所以我们现在知道我们的服务器公网IP了,但是它是动态的还是静态的呢?当我们把服务器架设在家或者办公室的时候,极有可能就是动态IP。如果是动态IP的话,可以用免费的动态域名服务(DDNS),比如[No-IP](http://www.noip.com)的服务。如果使用No-IP,假设我们选择了免费的域名dnsalias.net,那么这一行应该像这样填写:
|
||||
|
||||
remote ovpn.dnsalias.net 1194
|
||||
|
||||
"ovpn"是我们给服务器起的主机名。如果我们的服务器在云上,那么它可能有一个静态IP。如果有静态IP的话,那么这一行应该是这样的:
|
||||
|
||||
remote 1.2.3.4 1194
|
||||
|
||||
还要修改两行:
|
||||
|
||||
cert client.crt
|
||||
key client.key
|
||||
|
||||
在我们的例子里,客户端的证书和密钥的名字分别是laptop.crt和laptop.key所以我们的client.conf要包含下面这两行:
|
||||
|
||||
cert laptop.crt
|
||||
key laptop.key
|
||||
|
||||
在确认保存client.conf的修改之后,我们需要安全的把整个ovpn-client文件夹传输到客户端。一种方式是使用scp命令(安全拷贝或在SSH上拷贝)。另一种方式由优秀而免费的软件FileZilla提供,使用在SSH上运行的FTP(SFTP)。
|
||||
|
||||
### 第十步 -- 连接并测试 ###
|
||||
|
||||

|
||||
|
||||
|
||||
所以我们到底怎么样才能链接到远程的OpenVPN服务器的呢?它完全取决于我们手中现有的设备类型,当然也取决于所运行的操作系统。我们将在四种不同类别的操作系统上运行,Linux, Windows, OS X和iOS/Android。注意,无论在什么设备和系统上,我们都得在OpenVPN服务器的本地网络外才能连接成功。此外,如果在服务器前有防火墙,我们需要增加一条这样的规则:
|
||||
|
||||
*把所有从1194/UDP端口收到的包转发到服务器公网接口的1194/UDP端口。*
|
||||
|
||||
这是一个简单的防火墙规则。事不宜迟,让我们与我们难以置信的OpenVPN服务器建立第一个连接吧。
|
||||
|
||||
**Linux**: 我们只需安装openvpn包。一种连接远程OpenVPN服务器的方式是新建一个终端,切换到ovpn-client文件夹并以root身份或使用sudo来键入下列命令:
|
||||
|
||||
/usr/sbin/openvpn --config client.conf
|
||||
|
||||
任何时候,如果我们需要终止OpenVPN,按[CTRL+C]就行了。
|
||||
|
||||
**Windows**: 有一个免费的OpenVPN客户端软件叫做[OpenVPN Desktop Client][3]。 配置文件client.conf需要重命名成client.ovpn,这就是我们需要提供给OpenVPN Desktop Client的文件。程序会读取client.ovpn并给OpenVPN服务器生成一个新的连接配置。
|
||||
|
||||

|
||||
|
||||
**OS X**: [tunnelblick][4]是一款可以连接OpenVPN的免费开源OS X软件。[Viscosity][5]也可以但它是商业软件,不过我们喜欢。Viscosity会读取client.conf并给OpenVPN服务器生成一个新的连接配置。
|
||||
|
||||
**iOS/Android**: OpenVPN connect是绝佳的选择。它是免费的且可以从[App Store][6]和[Google Play store][7]获得
|
||||
|
||||
不管是什么平台,有时我们想检验我们是否真的使用OpenVPN连接了。一种检验方法是完成下面这简单的4步:
|
||||
|
||||
在连接到OpenVPN服务器前我们需要…
|
||||
|
||||
- 打开[whatip.com][8]记录我们的公网IP
|
||||
- 打开[dnsleaktest.com][10],运行标准测试(standard test),记录我们的域名解析服务器
|
||||
|
||||

|
||||
|
||||
在连接到OpenVPN服务器后重复这两部。如果我们获取到两个不同的公网IP,这意味着我们的网络出口已在远端OpenVPN服务器那。此外,如果获取了两个不同的域名解析服务器,那么就不存在DNS泄露的问题了。
|
||||
|
||||
### 感言 ###
|
||||
|
||||
我用三个不同的OpenVPN服务器,都是定制的。 一个运行在希腊Thessaloniki的家庭办公室的pfSense路由。当我不在办公室时,我用这个服务器安全的连接到局域网。剩下的两个服务器在两个不同的VPS上,一个在冰岛雷克雅未克,另一个在美国纽泽西州。当我在外且需要任意用一个WiFi热点的时候,我不必考虑安全问题:我只需简单的连接到雷克雅未克的服务器然后正常上网。有时我想看看限制用户地理位置在美国的服务。在这种不太常见的情况下,新泽西的服务器就派上用场了,当我连接时,我就获得了美国的一个公网IP,这样就可以访问有地理位置限制的服务了。值得注意的是,一些服务会把一些知名的VPN公司的IP列入黑名单。这是在你选的VPS提供商建立自己的OpenVPN*十分重要*的一个优点:这不大可能被列入黑名单.
|
||||
|
||||
无论你的物理位置在哪, OpenVPN确保客户端和服务器之间的数据流是高度加密的。没有OpenVPN的数据则是另一种情况。 取决于不同的应用层协议,它可能仍然是加密的,但它也可能是未加密的。所以除非你对OpenVPN服务器和它的本地网络有绝对的控制权,你不能完全相信另一端的管理员。这种精神是显而易见的:如果你真的在乎你自己的隐私,那么你需要注意你的行为可能在破坏它。
|
||||
|
||||
一个例子是我们有希望点对点传输。我们有一个在云上配置好的OpenVPN服务器。当需要任意用一个WiFi热点的时候,你没有丝毫的担心,因为你连在OpenVPN服务器上。然后你打开你最喜欢的电子邮件客户端从一个依然使用SMTP的老服务器收信。你猜会发生什么?你的用户名和密码以未加密的纯文本格式离开OpenVPN服务器。与此同时一个在你OpenVPN服务器附近的带宽管理员很容易就嗅探出你的证书并记录到他们越来越长的名叫"random happy people.txt"的列表。
|
||||
|
||||
所以你该做什么?很简单。你应该继续使用OpenVPN服务器,但不要使用应用了旧的或不安全的协议的应用程序。
|
||||
|
||||
享受你的OpenVPN服务器吧!
|
||||
|
||||
--------------------------------------------------------------------------------
|
||||
|
||||
via: http://parabing.com/2014/06/openvpn-on-ubuntu/
|
||||
|
||||
译者:[2q1w2007](https://github.com/2q1w2007) 校对:[校对者ID](https://github.com/校对者ID)
|
||||
|
||||
本文由 [LCTT](https://github.com/LCTT/TranslateProject) 原创翻译,[Linux中国](http://linux.cn/) 荣誉推出
|
||||
|
||||
[1]:http://zh.wikipedia.org/wiki/Openvpn
|
||||
[2]:http://www.ubuntu.com/server
|
||||
[3]:http://swupdate.openvpn.net/downloads/openvpn-client.msi
|
||||
[4]:https://code.google.com/p/tunnelblick
|
||||
[5]:https://www.sparklabs.com/viscosity
|
||||
[6]:https://itunes.apple.com/us/app/openvpn-connect/id590379981?mt=8
|
||||
[7]:https://play.google.com/store/apps/details?id=net.openvpn.openvpn
|
||||
[8]:http://www.whatip.com/
|
||||
[9]:https://dnsleaktest.com/
|
||||
@ -0,0 +1,89 @@
|
||||
如何在Linux命令行下访问SoundCloud
|
||||
================================================================================
|
||||
如果你喜欢流媒体音乐和原创音乐,你不能错过[SoundCloud][1]。这家云流媒体服务总部设在德国,这对任何音乐爱好者都非常有名且完善。自然,作为一个Linux爱好者,你可能想知道如何在Linux中加入你对音乐的热情。作为一个解决方案,我建议你使用Soundcloud2000,**SoundCloud的命令行客户端**脱胎于[Music Hack Day Stockholm '13][2]。
|
||||
|
||||
### 安装 ###
|
||||
|
||||
对于Debian或者Ubuntu用户,如下安装:
|
||||
|
||||
$ sudo apt-get install portaudio19-dev libmpg123-dev libncurses-dev ruby1.9.1-dev
|
||||
$ sudo gem install soundcloud2000
|
||||
|
||||
对于Archlinux用户,在[AUR][3]仓库中可以获取到包
|
||||
|
||||
对于Fedora用户,如下安装:
|
||||
|
||||
$ sudo yum install portaudio-devel libmpg123-devel ncurses-devel ruby-devel
|
||||
$ sudo gem install soundcloud2000
|
||||
|
||||
对于CentOS用户,安装或者升级到[最新 Ruby/RubyGems][4] (1.9或更高),启用[Repoforge repo][5],如下安装:
|
||||
|
||||
$ sudo yum install portaudio-devel mpg123-devel
|
||||
$ sudo gem install curses soundcloud2000
|
||||
|
||||
最后,到官方的github页面获取源码
|
||||
|
||||
### 使用 ###
|
||||
|
||||
Soundcloud2000非常容易使用。有些人甚至会说简单。我喜欢它的庄重以及三位作者和贡献者的努力。如下启动它:
|
||||
|
||||
$ soundcloud2000
|
||||
|
||||
这里,你将看到一个闪屏:
|
||||
|
||||

|
||||
|
||||
接着是歌曲列表:
|
||||
|
||||
|
||||
|
||||
您可以通过上下键滚动列表,回车播放一首歌曲,空格键是暂停/恢复,左右箭头键是快进/快退。正如你所看到的,没有什么突破性的但绝对符合人体工程学。
|
||||
|
||||
如果随机列表太长无法滚动完,你有一个选项来查看所有曲目,用户通过点击'u'键接着输入自己的名字。
|
||||
|
||||

|
||||
|
||||
这可能是Soundcloud2000的主要默认之一。而导航没有优化过,我寄予厚望的改善和支持的软件还是很年轻的。
|
||||
|
||||
### 红利 ###
|
||||
|
||||
另外一个额外的红利:如果你喜欢在终端上使用SoundCloud的想法,但不想安装任何额外的软件(也许你不能),我劝你去[cmd.fm][6]。该网站是一个伪装的SoundCloud,因为它隐藏在一个shell接口后。
|
||||
|
||||
[][7]
|
||||
|
||||
输入“help”可以得到命令列表,这比Soundcloud2000长很多。比如,我看到:
|
||||
|
||||
- _genres to list all genres
|
||||
- _play random to play a random track
|
||||
- _pause to pause the current track
|
||||
- _playlist new to make a new playlist
|
||||
- _loop to loop current track
|
||||
- _cinema to watch and ASCII version of Star Wars which completely blew my mind.
|
||||
|
||||
它甚至支持通过tab键自动完成流派
|
||||
|
||||
最后,Soundcloud2000的确是一个整洁的程序。我们可以原谅其目前的缺陷,因为它还年轻。我真的希望它会成长,并包含更多的功能(并从潜在的cmd.fm得到的灵感)。
|
||||
|
||||
如果您喜欢这个主意,我邀请你支持程序员,如果你喜欢这类举措,请支持[Music Hack Day][8],这其中混合了软件开发和音乐。
|
||||
|
||||
你认为在命令行下使用SoundCloud怎么样?让我们在评论中知道你的想法。
|
||||
|
||||
--------------------------------------------------------------------------------
|
||||
|
||||
via: http://xmodulo.com/2014/07/access-soundcloud-command-line-linux.html
|
||||
|
||||
原文作者:[Adrien Brochard][a]
|
||||
|
||||
译者:[geekpi](https://github.com/geekpi) 校对:[校对者ID](https://github.com/校对者ID)
|
||||
|
||||
本文由 [LCTT](https://github.com/LCTT/TranslateProject) 原创翻译,[Linux中国](http://linux.cn/) 荣誉推出
|
||||
|
||||
[a]:http://xmodulo.com/author/adrien
|
||||
[1]:https://soundcloud.com/
|
||||
[2]:https://www.hackerleague.org/hackathons/music-hack-day-stockholm-13/
|
||||
[3]:https://aur.archlinux.org/packages/ruby-soundcloud2000/
|
||||
[4]:http://ask.xmodulo.com/upgrade-ruby-centos.html
|
||||
[5]:http://xmodulo.com/2013/01/how-to-set-up-rpmforge-repoforge-repository-on-centos.html
|
||||
[6]:https://cmd.fm/
|
||||
[7]:https://www.flickr.com/photos/xmodulo/14494448218/
|
||||
[8]:http://new.musichackday.org/
|
||||
Loading…
Reference in New Issue
Block a user