mirror of
https://github.com/LCTT/TranslateProject.git
synced 2025-01-13 22:30:37 +08:00
[Translated] 26 The Linux Kernel--Configuring the Kernel Part 22
This commit is contained in:
parent
a657f9bf2d
commit
92134d642a
@ -1,122 +0,0 @@
|
||||
Translating----------------geekpi
|
||||
|
||||
|
||||
26 The Linux Kernel: Configuring the Kernel Part 22
|
||||
================================================================================
|
||||
|
||||
|
||||
Aloha! In this article, we will continue to configure the kernel hacks and then we will configure the whole security system.
|
||||
|
||||
The next feature to configure is needed by Alpha and s390 processor (Force weak per-cpu definitions). This feature offers a fix for an addressing issue commonly seen in such processors. Other processors do not need this feature enabled.
|
||||
|
||||
Kernel dumps can be tested with this special debugging tool (Linux Kernel Dump Test Tool Module). This software will allow a kernel developer to trigger a fake error that will cause a kernel dump. The kernel developers can then ensure that the dumps complete successfully.
|
||||
|
||||
The kernel offers some different error injection modules that allow kernel developers to test the notifiers (CPU notifier error injection module), (PM notifier error injection module), and (Memory hotplug notifier error injection module). A notifier informs the system that the hardware is present, which is important for hotplugging. These error injection modules trigger an error in this notification system so developers can test the notification system's error handling abilities.
|
||||
|
||||
The "Fault-injection framework" driver offers various tools for testing fault-handling.
|
||||
|
||||
The "Latency measuring infrastructure" driver provides the LatencyTOP tool used to find the userspace object that is blocking/interfering with a kernel execution/task.
|
||||
|
||||
Next, we have a sub-menu titled "Tracers" that contains a list of various tracers. A tracer is a piece of code that watches various kernel functions. Every time a particular function starts, a tracer will be called to watch the function.
|
||||
|
||||
This next module tests the performance of the Red-Black tree library (Red-Black tree test). The Red-Black tree library is a sorting and searching algorithm.
|
||||
|
||||
The next feature is the same except that it tests the interval tree library (Interval tree test).
|
||||
|
||||
The kernel can also debug FireWire on other systems while that particular remote system is booting (Remote debugging over FireWire early on boot) and (Remote debugging over FireWire with firewire-ohci).
|
||||
|
||||
The printk() function can be made to print various debugging messages if this feature is enabled (Enable dynamic printk() support). “printk()” is a commonly discussed system call, so remember that it prints debugging messages about the kernel.
|
||||
|
||||
Here is a Direct Memory Access (DMA) debugging driver (Enable debugging of DMA-API usage).
|
||||
|
||||
The Atomic64 self-tests checks if the system supports atomic operations (Perform an atomic64_t self-test at boot). This is where a 32-bit system performs a 64-bit operation.
|
||||
|
||||
This driver provides a self-test for all of the possible RAID6 recovery systems (Self test for hardware accelerated raid6 recovery).
|
||||
|
||||
NOTE: Self-tests are low-level tests and detection software that executes before most of the system's hardware and software turns on and executes. Self-tests search for hardware, failing devices, etc. A self-test may also be code an application uses to test itself.
|
||||
|
||||
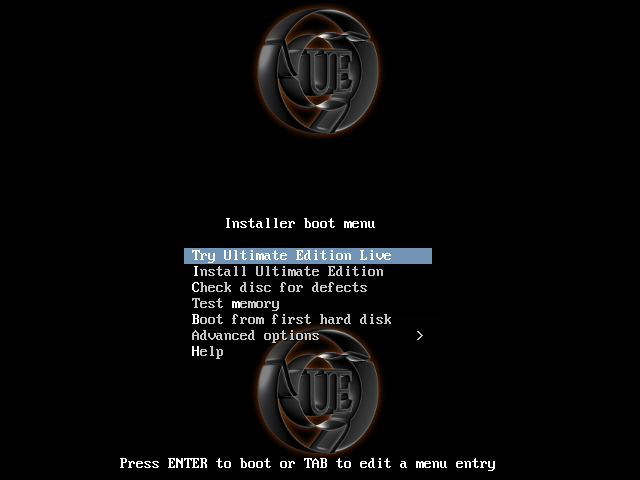
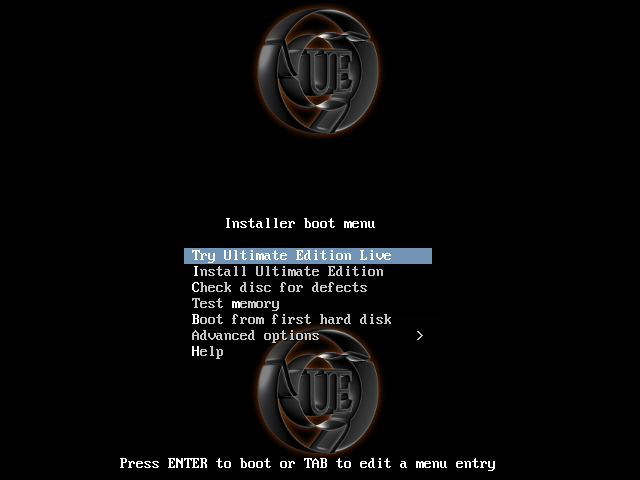
In the Kernel Hacking menu (if you are using a menu-like interface such as ncurses), there is a sub-menu titled "Sample kernel code". If you make your own personal modules, this is where you can enable them. In a later article, we will discuss how to implement custom/home-made kernel modules. Just remember this is where you enable your module.
|
||||
|
||||

|
||||
|
||||
The Kernel GNU DeBugger (KGDB) has many features that can be enabled or disabled (KGDB: kernel debugger). This debugger only works with two Linux systems plugged into each other via serial connection.
|
||||
|
||||
This feature provides extra boot-up messages for the decompression of the bzimage (Enable verbose x86 bootup info messages). You set the kernel encryption near the beginning of the configuration process.
|
||||
|
||||
Printk() prints various information to the boot-screen of dmesg, but after the serial and console drivers load. Enable this driver to make printk start printing messages sooner (Early printk).
|
||||
|
||||
This next driver is the same as above, but uses the EHCI port (Early printk via EHCI debug port).
|
||||
|
||||
The kernel can be set to watch for stack overflows so the kernel can manage the error better (Check for stack overflows). The kernel will execute more slowly, but overflows will not cause as much damage.
|
||||
|
||||
The page-table for the kernel can be seen on debugfs with this enabled (Export kernel pagetable layout to userspace via debugfs). However, this will slow down the kernel. This is needed for debugging purposes.
|
||||
|
||||
The kernel's written mistakes can be caught with this feature (Write protect kernel read-only data structures). This option turns the kernel's read-only data to write-protected mode. This debugging tool harms the kernel's speed. That debugging tool has a tool to debug itself (Testcase for the DEBUG_RODATA feature).
|
||||
|
||||
To prevent the execution of modules with modified code (due to an error), then enable this protective feature (Set loadable kernel module data as NX and text as RO). The debugging tool for that feature is provided by this driver (Testcase for the NX non-executable stack feature).
|
||||
|
||||
The kernel can be set to flush one of the TLB entries at a time or the whole table using this option (Set upper limit of TLB entries to flush one-by-one).
|
||||
|
||||
The next feature is an IOMMU debugging feature (Enable IOMMU debugging). There is another debugging test that disables some IOMMU features to test for extra stability (Enable IOMMU stress-test mode). The IOMMU stands for input/output memory management unit.
|
||||
|
||||
Enabling this option will make the kernel perform selt-tests on the change_page_attr() system call on thirty second intervals (CPA self-test code). This system call changes page attributes.
|
||||
|
||||
Any kernel code marked as "inline" can not be manipulated as much as it would by GCC than if it were not marked (Allow gcc to uninline functions marked). The GCC compiler adds code that it feels will make the code better (GCC is good at doing so). However, some code is not meant to be manipulated by GCC.
|
||||
|
||||
This next driver offers sanity checks for the "copy_from_user()" system call (Strict copy size checks). copy_from_user() copies a block of userspace data to kernelspace.
|
||||
|
||||
Here is another self-test; this one is for NMI (NMI Selftest).
|
||||
|
||||
Now, we can move on to the "Security Options" which is seen as a sub-menu in the main menu if you are using a menu-based interface, like ncurses. The first option allows access keys and authentication tokens to be stored in the kernel (Enable access key retention support). This is used for many reasons like accessing encrypted filesystems.
|
||||
|
||||
The following option is for creating and sealing/unsealing keys (TRUSTED KEYS). Encrypted keys are encrypted/decrypted using this driver (ENCRYPTED KEYS).
|
||||
|
||||
Keys can be viewed in proc with this feature enabled (Enable the /proc/keys file by which keys may be viewed).
|
||||
|
||||
Extra restrictions can be applied to syslog with this security feature (Restrict unprivileged access to the kernel syslog).
|
||||
|
||||
If this option is enabled, then the user can select different security models (Enable different security models). Otherwise, the defaults will be used. Disable this if you do not fully understand security or if you are fine with your kernel using the defaults.
|
||||
|
||||
The securityfs filesystem is offered by this driver (Enable the securityfs filesystem).
|
||||
|
||||
Hooks are added to networking and socket security when this feature is enabled (Socket and Networking Security Hooks). These hooks are access controls.
|
||||
|
||||
IPSec networking hooks (also called XFRM networking hooks) are implemented when this option is enabled (XFRM (IPSec) Networking Security Hooks). Security hooks are also available for files (Security hooks for pathname based access control).
|
||||
|
||||
The next driver provides support for Intel's Trusted Execution Technology (Enable Intel(R) Trusted Execution Technology (Intel(R) TXT)).
|
||||
|
||||
The user can set the range of memory addresses that cannot be reserved for userspace (Low address space for LSM to protect from user allocation). The starting point is 0. The user types the end point for this option. For most platforms, 65536 is a recommended choice.
|
||||
|
||||
SELinux (mentioned in the Kernel Security article) is one of the popular Linux-Security-Modules (NSA SELinux Support). Many options and features exist for SELinux. The boot parameter determines whether SELinux is started {1} or not started {0} when the kernel executes (NSA SELinux boot parameter). SELinux can be configured with the ability to be temporarily disabled at times when the Root user needs to do so (NSA SELinux runtime disable). Users can develop and test new policies with this feature enabled (NSA SELinux Development Support). AVC statistics are collected and stored by this feature (NSA SELinux AVC Statistics). A default can be set for the checkreqprot flag; a "1" means SELinux will check the application's requested protection and zero will default to the kernel's protection for mmap and mprotect system calls (NSA SELinux checkreqprot default value). Many SELinux policies exist; the user can set the latest version that they wish SELinux not to excede (NSA SELinux maximum supported policy format version).
|
||||
|
||||
One of the other Linux-Security-Modules (LSM), SMACK, is supported by the kernel (Simplified Mandatory Access Control Kernel Support).
|
||||
|
||||
TOMOYO is another supported LSM (TOMOYO Linux Support). The maximum number of entries permitted to be added during learning-mode is set in the following feature (Default maximal count for learning mode). The amount of log entires can also be set (Default maximal count for audit log). Next, this option allows/disallows TOMOYO to be activated without a policy loader (Activate without calling userspace policy loader). The location of the policy loader is configured here ((/sbin/tomoyo-init) Location of userspace policy loader) and the executable that triggers the execution is set here ((/sbin/init) Trigger for calling userspace policy loader).
|
||||
|
||||
Again, the kernel supports another LSM - AppArmor (AppArmor support). Like with SELinux, the default boot parameter can be set for AppArmor (AppArmor boot parameter default value).
|
||||
|
||||
Yama is another LSM (Yama support). Yama can be used with another LSM if this feature is enabled (Yama stacked with other LSMs).
|
||||
|
||||
This driver gives the kernel the ability to use multiple keyrings for verification processes (Digital signature verification using multiple keyrings).
|
||||
|
||||
Asymmetric keys are supported with this feature (Enable asymmetric keys support).
|
||||
|
||||
The kernel can keep and maintain a list of hashes and important system files (Integrity Measurement Architecture(IMA)). Then, if malware changes an important file, the kernel will know because the hashes are checked before the file or executable are used. It is highly recommended that this feature be enabled.
|
||||
|
||||
Extra security attributes are added to files if this feature is enabled (EVM support). The version can be set using this next option (EVM HMAC version). The two choices are version 1 and 2.
|
||||
|
||||
Remember all of the different Linux Security Modules (LSMs)? Well, the default can be set here (Default security module (AppArmor)).
|
||||
|
||||
In the next article, we can configure the "Cryptographic API". There may be two additional configuration articles left than what I estimated. After that, there are other kernel topics to discuss.
|
||||
|
||||
SNEAK PEAK: After this article, there is one more about the configuration process. Then, we can finally compile and install the kernel.
|
||||
|
||||
MESSAGE TO MY FANS: Feel free to post and/or email suggestions for kernel topics you would like me to cover in the following kernel articles. I still have a list of the suggestions some readers have sent me over the course of this series. Please feel free to send more.
|
||||
|
||||
--------------------------------------------------------------------------------
|
||||
|
||||
via: http://www.linux.org/threads/the-linux-kernel-configuring-the-kernel-part-22.5017/
|
||||
|
||||
译者:[译者ID](https://github.com/译者ID) 校对:[校对者ID](https://github.com/校对者ID)
|
||||
|
||||
本文由 [LCTT](https://github.com/LCTT/TranslateProject) 原创翻译,[Linux中国](http://linux.cn/) 荣誉推出
|
||||
@ -0,0 +1,119 @@
|
||||
戴文的Linux内核专题:26 配置内核 (22)
|
||||
================================================================================
|
||||
|
||||
|
||||
你好!本篇我们将继续配置"kernel hacks",接着我们会配置整个安全系统。
|
||||
|
||||
Alpha和s390处理器需要配置下一个特性(Force weak per-cpu definitions)。这个特性修复了一个在这类处理器中普遍存在的寻址问题。其他的处理器无需启用这个特性。
|
||||
|
||||
内核转储可以用这个特殊的调试工具测试(Linux Kernel Dump Test Tool Module)。这个软件会允许内核开发者触发一个假错误来导致内核转储。内核开发者可以保证转储成功执行。
|
||||
|
||||
内核提供了不同的错误注射模块来允许内核开发者测试通知(CPU notifier error injection module)、 (PM notifier error injection module) 和 (Memory hotplug notifier error injection module)。通知器提醒系统硬件还在,这对热插拔很重要。这些错误注射模块在这些通知系统中触发一个错误,那么开发者就可以测试通知系统的错误处理能力了。
|
||||
|
||||
"Fault-injection framework"驱动提供了不同的用于测试错误处理的工具。
|
||||
|
||||
"Latency measuring infrastructure"驱动提供了延迟检测工具LatencyTop,以找出用户空间中由于内核执行/任务而被阻碍/干扰的对象。
|
||||
|
||||
下面,我们有一个子菜单名为"Tracers",它包含了不同追踪器的列表。追踪器是一段监视不同内核函数的代码。每次某个特定的函数启动,追踪器将被调用来检测函数。
|
||||
|
||||
下面的模块用来测试红黑树库的性能(Red-Black tree test)。红黑树是一个排序和搜索算法。
|
||||
|
||||
下面的特性是相同的除了用来测试区间树库(Interval tree test)。
|
||||
|
||||
在启动远程特定系统时,内核同样可以在其他系统上调试FireWire (Remote debugging over FireWire early on boot) 和 (Remote debugging over FireWire with firewire-ohci)。
|
||||
|
||||
printk()函数可以用来打印不同的调试信息,如果这个特性启用的话(Enable dynamic printk() support)。"printk()"是一个常被讨论的系统调用,所以记住这个打印内核相关消息。
|
||||
|
||||
这是一个直接内存访问(DMA)调试驱动(Enable debugging of DMA-API usage)。
|
||||
|
||||
Atomic64自我测试检查系统是否支持原子操作(Perform an atomic64_t self-test at boot)。这是一个32位系统执行64位操作。
|
||||
|
||||
这个驱动提供了对于所有可能的RAID6恢复系统的自我测试(Self test for hardware accelerated raid6 recovery)。
|
||||
|
||||
注意:自我测试是底层测试并且在绝大多数系统硬件和软件开启和执行前侦查软件。自我测试搜索硬件,失败的设备等等。自我测试也可能被编成应用测试它本身。
|
||||
|
||||
在"Kernel Hacking"菜单中(如果你是用的是像ncurses那样的菜单接口),有一个名为"Sample kernel code"的子菜单。在以后的文章中,我们会讨论如何实现自定义/自制内核模块。只要记住这里是启用你自己的模块。
|
||||
|
||||

|
||||
|
||||
Kernel GNU DeBugger (KGDB)(内核调试器)有许多特性可以启用或者禁用(KGDB: kernel debugger)。这个调试器只工作在通过串行连接的两个Linux系统之间。
|
||||
|
||||
这个特性提供在启动时显示额外bzimage解压消息(Enable verbose x86 bootup info messages)。在内核配置的开始部分你设置了内核加密。
|
||||
|
||||
printk()打印不同的消息到dmsg的启动界面,但是在串行和控制台驱动加载后。启用这个驱动会使printk()更早打印信息(Early printk)。
|
||||
|
||||
下一个驱动和上面的一样,但是使用EHCI端口(Early printk via EHCI debug port)。
|
||||
|
||||
内核可以被设置来观察堆栈溢出,这样内核可以更好地管理错误(Check for stack overflows)。内核会执行的更慢,但是溢出不会造成如此大的损害。
|
||||
|
||||
通过启用这个,内核页面可用debugfs见到(Export kernel pagetable layout to userspace via debugfs)。然而,这个会使内核变慢。这个用于调试目的。
|
||||
|
||||
内核的写入错误可以被这个特性捕捉到(Write protect kernel read-only data structures)。这个选项会使内核的只读数据编程进入写保护模式。此调试工具会损害内核的速度。该调试工具还有一个用来调试其自身的工具(Testcase for the DEBUG_RODATA feature)。
|
||||
|
||||
为了防止被修改过代码的模块执行(由于一个错误),接着启用这个保护性特性 (Set loadable kernel module data as NX and text as RO)。这个调试工具由这个驱动提供(Testcase for the NX non-executable stack feature)。
|
||||
|
||||
使用这个选项,内核可以一次刷新一个TLB条目或者整张表 (Set upper limit of TLB entries to flush one-by-one)。
|
||||
|
||||
下一个特性是IOMMU调试特性(Enable IOMMU debugging)。这是另外一个调试测试,禁用一些IOMMU特性来用于测试稳定性(Enable IOMMU stress-test mode)。IOMMU代表"input/output memory management unit"(输入/输出内存管理单元)。
|
||||
|
||||
启用这个选项回事内核以30s的间隔在change_page_attr()系统调用上执行单端测试。这个系统调用会改变页的属性。
|
||||
|
||||
任何被标以"inline"的内核代码,如果没有被表明的也同样会被GCC操作(Allow gcc to uninline functions marked)。GCC编译器会增加使得代码更好的代码(GCC擅长这么做)。然而,一些代码不想被GCC操作。
|
||||
|
||||
下面的驱动提供了对"copy_from_user()"系统调用的基本测试(Strict copy size checks)。copy_fcrom_user()从用户空间拷贝数据块到内核空间中。
|
||||
|
||||
这里还有一个自我测试;它用于NNI(NMI Selftest)。
|
||||
|
||||
现在,我们会进入"Security Options",如果你使用像ncurses的基于菜单的接口时。第一个选项允许访问内核中存储的键和验证令牌(Enable access key retention support)。这有很多原因用到,像访问加密文件系统。
|
||||
|
||||
下面的选项用于创建并密封/开启键((TRUSTED KEYS))。加密的键使用这个驱动加密/解密(ENCRYPTED KEYS)。
|
||||
|
||||
启用这个特性键可以在/proc中看到(Enable the /proc/keys file by which keys may be viewed)。
|
||||
|
||||
使用这个安全特性,额外的限制可以应用到syslog中(Restrict unprivileged access to the kernel syslog)。
|
||||
|
||||
如果启用这个选项,那么用户可以选择不同的安全模块(Enable different security models)。不然,将会使用默认。如果你不完全理解安全或者如果你对使用默认感到没问题,那么就禁用它。
|
||||
|
||||
这个驱动提供了securityfs文件系统(Enable the securityfs filesystem)。
|
||||
|
||||
当启用这个特性后,钩子将会被增加到网络和套接字安全中(Socket and Networking Security Hooks)。这些钩子是访问控制。
|
||||
|
||||
IPSec网络钩子(also called XFRM networking hooks)在这个选项启用后实现(XFRM (IPSec) Networking Security Hooks)。安全钩子同样可被文件使用(Security hooks for pathname based access control)。
|
||||
|
||||
下一个驱动提供了对Intel可信赖执行技术的支持(Enable Intel(R) Trusted Execution Technology (Intel(R) TXT))。
|
||||
|
||||
用户可以设置无法为用户空间保留的内存寻址范围(Low address space for LSM to protect from user allocation)。开始点是0。用户在此选项中输入结束点。对于大多数平台而言,65536是一个建议值。
|
||||
|
||||
SELinux(在内核安全的文章中提到)是一种流行的Linux安全模块(NSA SELinux Support)。SELinux存在很多选项和特性。启动参数决定了当内核执行(NSA SELinux boot parameter)时SELinux是否启动{1}或者不启动{0}。SELinux可以被配置成在root用户需要时临时禁止(NSA SELinux runtime disable)。用户可以启用这个特性开发并测试新的策略(NSA SELinux Development Support)。AVC统计被这个特性收集并被存储 (NSA SELinux AVC Statistics)。对于checkreqprot标志有一个默认设置;"1"意味着SElinux会检查应用请求的保护,"0"会默认使用内核对mmap和mprotect系统调用的保护(NSA SELinux checkreqprot default value)。存在很多的SElinux策略;用户可以设置他们不希望SELinux excede的最新版本(NSA SELinux maximum supported policy format version)。
|
||||
|
||||
另外一个Linux安全模块(LSM),SMACK,也被内核支持(Simplified Mandatory Access Control Kernel Support)。
|
||||
|
||||
TOMOYO是另外一个被支持的LSM(TOMOYO Linux Support)。在学习模式中允许被添加的最大条目数目在下面的特性中设置(Default maximal count for audit log)。接下来,这个选项允许/禁用TOMOYO在没有策略加载器下被激活(Activate without calling userspace policy loader)。策略加载器的位置在这里被配置((/sbin/tomoyo-init) Location of userspace policy loader),触发执行的可执行文件在这里设置((/sbin/init) Trigger for calling userspace policy loader)。
|
||||
|
||||
再说一次,内核支持另外一个LSM - APPArmor(AppArmor support)。像SELinux一样,可以为AppArmor设置默认的启动参数(AppArmor boot parameter default value)。
|
||||
|
||||
Yama是另外一个LSM(Yama support)。如果启用这个特性Yama可以与另外一个LSM一起使用(Yama stacked with other LSMs)。
|
||||
|
||||
这个驱动让内核可以使用多个密钥链来验证进程(Digital signature verification using multiple keyrings)。
|
||||
|
||||
非对称键在这个特性中支持(Enable asymmetric keys support)。
|
||||
|
||||
内核可以保存并维护一个哈希和重要系统文件的列表(Integrity Measurement Architecture(IMA))。那么,如果恶意软件改变了一个重要的文件,内核会知道因为文件或者可执行文件被使用时内核会检测哈希值。强烈建议启用这个特性。
|
||||
|
||||
如果启用这个特性会加入额外的安全属性(EVM support)。可以用下面的选项设置版本(EVM HMAC version)。有两个选项分别是version 1和2。
|
||||
|
||||
记住所有的Linux安全模块的不同了么(LSMs)?好的,下面可以设置默认模块(Default security module (AppArmor))。
|
||||
|
||||
下一篇中,我们会配置"Cryptographic API"。我估计还会剩下两篇文章。在这之后,我们会讨论其他的内核主题。
|
||||
|
||||
先睹为快:本篇之后,关于配置还有一篇。接着,我们会完成编译并安装内核。
|
||||
|
||||
致我的粉丝:你随意给我致信或者给我电子邮件来建议你希望在以后的内核文章中想要看到的主题。我已经收到了一些来自这个系列读者的一些建议。请随意给我更多建议。
|
||||
|
||||
--------------------------------------------------------------------------------
|
||||
|
||||
via: http://www.linux.org/threads/the-linux-kernel-configuring-the-kernel-part-22.5017/
|
||||
|
||||
译者:[geekpi](https://github.com/geekpi) 校对:[校对者ID](https://github.com/校对者ID)
|
||||
|
||||
本文由 [LCTT](https://github.com/LCTT/TranslateProject) 原创翻译,[Linux中国](http://linux.cn/) 荣誉推出
|
||||
Loading…
Reference in New Issue
Block a user