[@TimSweeneyEpic][8] 可能会很喜欢 😊
+>
+> ![pic.twitter.com/7mt9fXt7TH][9]
+>
+> — Lutris Gaming (@LutrisGaming) [April 17, 2019][10]
+
+作为一名狂热的游戏玩家和 Linux 用户,我立即得到了这个消息,并安装了 Lutris 来运行 Epic 游戏。
+
+**备注:** 我使用 [Ubuntu 19.04][11] 来测试 Linux 环境下的游戏运行情况。
+
+### 通过 Lutris 在 Linux 下使用 Epic 游戏商城
+
+为了在你的 Linux 系统中安装 Epic 游戏商城,请确保你已经安装了 Wine 和 Python 3。接下来,[在 Ubuntu 中安装 Wine][12] ,或任何你正在使用的 Linux 发行版本也都可以。然后, [从官方网站下载 Lutris][13].
+
+#### 安装 Epic 游戏商城
+
+Lutris 安装成功后,直接启动它。
+
+当我尝试时,我遇到了一个问题(当我用 GUI 启动时却没有遇到)。当我尝试在命令行输入 `lutris` 来启动时,我发现了下图所示的错误:
+
+![][15]
+
+感谢 Abhishek,我了解到了这是一个常见问题 (你可以在 [GitHub][16] 上查看这个问题)。
+
+总之,为了解决这个问题,我需要在命令行中输入以下命令:
+
+```
+export LC_ALL=C
+```
+
+当你遇到同样的问题时,只要你输入这个命令,就能正常启动 Lutris 了。
+
+**注意**:每次启动 Lutris 时都必须输入这个命令。因此,最好将其添加到 `.bashrc` 文件或环境变量列表中。
+
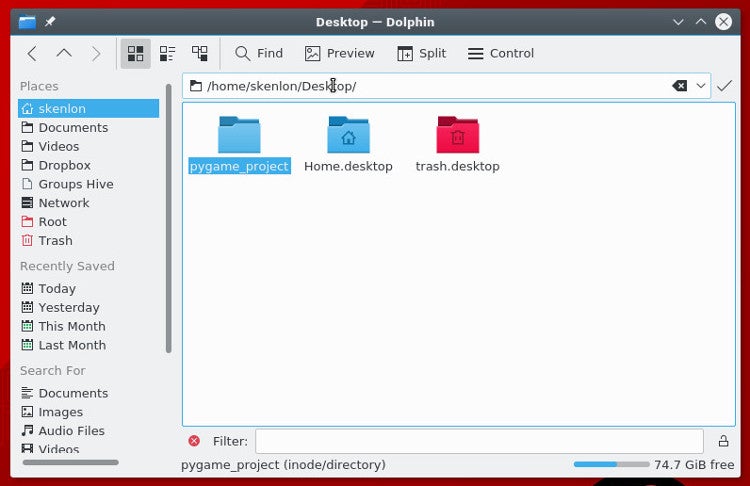
+上述操作完成后,只要启动并搜索 “Epic Games Store” 会显示以下图片中的内容:
+
+![Epic Games Store in Lutris][17]
+
+在这里,我已经安装过了,所以你将会看到“安装”选项,它会自动询问你是否需要安装需要的包。只需要继续操作就可以成功安装。就是这样,不需要任何黑科技。
+
+#### 玩一款 Epic 游戏商城中的游戏
+
+![Epic Games Store][18]
+
+现在我们已经通过 Lutris 在 Linux 上安装了 Epic 游戏商城,启动它并登录你的账号就可以开始了。
+
+但这真会奏效吗?
+
+*是的,Epic 游戏商城可以运行。* **但是所有游戏都不能玩。**(LCTT 译注:莫生气,请看文末的进一步解释!)
+
+好吧,我并没有尝试过所有内容,但是我拿了一个免费的游戏(Transistor —— 一款回合制 ARPG 游戏)来检查它是否工作。
+
+![Transistor – Epic Games Store][19]
+
+很不幸,游戏没有启动。当我运行时界面显示了 “Running” 不过什么都没有发生。
+
+到目前为止,我还不知道有什么解决方案 —— 所以如果我找到解决方案,我会尽力让你们知道最新情况。
+
+### 总结
+
+通过 Lutris 这样的工具使 Linux 的游戏场景得到了改善,这终归是个好消息 。不过,仍有许多工作要做。
+
+对于在 Linux 上运行的游戏来说,无障碍运行仍然是一个挑战。其中可能就会有我遇到的这种问题,或者其它类似的。但它正朝着正确的方向发展 —— 即使还存在着一些问题。
+
+你有什么看法吗?你是否也尝试用 Lutris 在 Linux 上启动 Epic 游戏商城?在下方评论让我们看看你的意见。
+
+### 补充
+
+Transistor 实际上有一个原生的 Linux 移植版。到目前为止,我从 Epic 获得的所有游戏都是如此。所以我会试着压下我的郁闷,而因为 Epic 只让你玩你通过他们的商店/启动器购买的游戏,所以在 Linux 机器上用 Lutris 玩这个原生的 Linux 游戏是不可能的。这简直愚蠢极了。Steam 有一个原生的 Linux 启动器,虽然不是很理想,但它可以工作。GOG 允许你从网站下载购买的内容,可以在你喜欢的任何平台上玩这些游戏。他们的启动器完全是可选的。
+
+我对此非常恼火,因为我在我的 Epic 库中的游戏都是可以在我的笔记本电脑上运行得很好的游戏,当我坐在桌面前时,玩起来很有趣。但是因为那台桌面机是我唯一拥有的 Windows 机器……
+
+我选择使用 Linux 时已经知道会存在兼容性问题,并且我有一个专门用于游戏的 Windows 机器,而我通过 Epic 获得的游戏都是免费的,所以我在这里只是表示一下不满。但是,他们两个作为最著名的竞争对手,Epic 应该有在我的 Linux 机器上玩原生 Linux 移植版的机制。
+
+--------------------------------------------------------------------------------
+
+via: https://itsfoss.com/epic-games-lutris-linux/
+
+作者:[Ankush Das][a]
+选题:[lujun9972][b]
+译者:[Modrisco](https://github.com/Modrisco)
+校对:[wxy](https://github.com/wxy)
+
+本文由 [LCTT](https://github.com/LCTT/TranslateProject) 原创编译,[Linux中国](https://linux.cn/) 荣誉推出
+
+[a]: https://itsfoss.com/author/ankush/
+[b]: https://github.com/lujun9972
+[1]: https://linux.cn/article-7316-1.html
+[2]: https://linux.cn/article-10061-1.html
+[3]: https://linux.cn/article-10054-1.html
+[4]: https://lutris.net/
+[5]: https://itsfoss.com/wp-content/uploads/2019/04/epic-games-store-lutris-linux-800x450.png
+[6]: https://www.epicgames.com/store/en-US/
+[7]: https://twitter.com/EpicGames?ref_src=twsrc%5Etfw
+[8]: https://twitter.com/TimSweeneyEpic?ref_src=twsrc%5Etfw
+[9]: https://pbs.twimg.com/media/D4XkXafX4AARDkW?format=jpg&name=medium
+[10]: https://twitter.com/LutrisGaming/status/1118552969816018948?ref_src=twsrc%5Etfw
+[11]: https://itsfoss.com/ubuntu-19-04-release-features/
+[12]: https://itsfoss.com/install-latest-wine/
+[13]: https://lutris.net/downloads/
+[14]: https://itsfoss.com/ubuntu-mate-entroware/
+[15]: https://itsfoss.com/wp-content/uploads/2019/04/lutris-error.jpg
+[16]: https://github.com/lutris/lutris/issues/660
+[17]: https://itsfoss.com/wp-content/uploads/2019/04/lutris-epic-games-store-800x520.jpg
+[18]: https://itsfoss.com/wp-content/uploads/2019/04/epic-games-store-800x450.jpg
+[19]: https://itsfoss.com/wp-content/uploads/2019/04/transistor-game-epic-games-store-800x410.jpg
+[20]: https://itsfoss.com/skpe-alpha-linux/
diff --git a/published/20190423 How to identify same-content files on Linux.md b/published/20190423 How to identify same-content files on Linux.md
new file mode 100644
index 0000000000..6353fe86b3
--- /dev/null
+++ b/published/20190423 How to identify same-content files on Linux.md
@@ -0,0 +1,256 @@
+[#]: collector: (lujun9972)
+[#]: translator: (tomjlw)
+[#]: reviewer: (wxy)
+[#]: publisher: (wxy)
+[#]: url: (https://linux.cn/article-10955-1.html)
+[#]: subject: (How to identify same-content files on Linux)
+[#]: via: (https://www.networkworld.com/article/3390204/how-to-identify-same-content-files-on-linux.html#tk.rss_all)
+[#]: author: (Sandra Henry-Stocker https://www.networkworld.com/author/Sandra-Henry_Stocker/)
+
+如何在 Linux 上识别同样内容的文件
+======
+> 有时文件副本相当于对硬盘空间的巨大浪费,并会在你想要更新文件时造成困扰。以下是用来识别这些文件的六个命令。
+
+![Vinoth Chandar \(CC BY 2.0\)][1]
+
+在最近的帖子中,我们看了[如何识别并定位硬链接的文件][2](即,指向同一硬盘内容并共享 inode)。在本文中,我们将查看能找到具有相同*内容*,却不相链接的文件的命令。
+
+硬链接很有用是因为它们能够使文件存放在文件系统内的多个地方却不会占用额外的硬盘空间。另一方面,有时文件副本相当于对硬盘空间的巨大浪费,在你想要更新文件时也会有造成困扰之虞。在本文中,我们将看一下多种识别这些文件的方式。
+
+### 用 diff 命令比较文件
+
+可能比较两个文件最简单的方法是使用 `diff` 命令。输出会显示你文件的不同之处。`<` 和 `>` 符号代表在当参数传过来的第一个(`<`)或第二个(`>`)文件中是否有额外的文字行。在这个例子中,在 `backup.html` 中有额外的文字行。
+
+```
+$ diff index.html backup.html
+2438a2439,2441
+>
+> That's all there is to report.
+>
+```
+
+如果 `diff` 没有输出那代表两个文件相同。
+
+```
+$ diff home.html index.html
+$
+```
+
+`diff` 的唯一缺点是它一次只能比较两个文件并且你必须指定用来比较的文件,这篇帖子中的一些命令可以为你找到多个重复文件。
+
+### 使用校验和
+
+`cksum`(checksum) 命令计算文件的校验和。校验和是一种将文字内容转化成一个长数字(例如2819078353 228029)的数学简化。虽然校验和并不是完全独有的,但是文件内容不同校验和却相同的概率微乎其微。
+
+```
+$ cksum *.html
+2819078353 228029 backup.html
+4073570409 227985 home.html
+4073570409 227985 index.html
+```
+
+在上述示例中,你可以看到产生同样校验和的第二个和第三个文件是如何可以被默认为相同的。
+
+### 使用 find 命令
+
+虽然 `find` 命令并没有寻找重复文件的选项,它依然可以被用来通过名字或类型寻找文件并运行 `cksum` 命令。例如:
+
+```
+$ find . -name "*.html" -exec cksum {} \;
+4073570409 227985 ./home.html
+2819078353 228029 ./backup.html
+4073570409 227985 ./index.html
+```
+
+### 使用 fslint 命令
+
+`fslint` 命令可以被特地用来寻找重复文件。注意我们给了它一个起始位置。如果它需要遍历相当多的文件,这就需要花点时间来完成。注意它是如何列出重复文件并寻找其它问题的,比如空目录和坏 ID。
+
+```
+$ fslint .
+-----------------------------------file name lint
+-------------------------------Invalid utf8 names
+-----------------------------------file case lint
+----------------------------------DUPlicate files <==
+home.html
+index.html
+-----------------------------------Dangling links
+--------------------redundant characters in links
+------------------------------------suspect links
+--------------------------------Empty Directories
+./.gnupg
+----------------------------------Temporary Files
+----------------------duplicate/conflicting Names
+------------------------------------------Bad ids
+-------------------------Non Stripped executables
+```
+
+你可能需要在你的系统上安装 `fslint`。你可能也需要将它加入你的命令搜索路径:
+
+```
+$ export PATH=$PATH:/usr/share/fslint/fslint
+```
+
+### 使用 rdfind 命令
+
+`rdfind` 命令也会寻找重复(相同内容的)文件。它的名字意即“重复数据搜寻”,并且它能够基于文件日期判断哪个文件是原件——这在你选择删除副本时很有用因为它会移除较新的文件。
+
+```
+$ rdfind ~
+Now scanning "/home/shark", found 12 files.
+Now have 12 files in total.
+Removed 1 files due to nonunique device and inode.
+Total size is 699498 bytes or 683 KiB
+Removed 9 files due to unique sizes from list.2 files left.
+Now eliminating candidates based on first bytes:removed 0 files from list.2 files left.
+Now eliminating candidates based on last bytes:removed 0 files from list.2 files left.
+Now eliminating candidates based on sha1 checksum:removed 0 files from list.2 files left.
+It seems like you have 2 files that are not unique
+Totally, 223 KiB can be reduced.
+Now making results file results.txt
+```
+
+你可以在 `dryrun` 模式中运行这个命令 (换句话说,仅仅汇报可能会另外被做出的改动)。
+
+```
+$ rdfind -dryrun true ~
+(DRYRUN MODE) Now scanning "/home/shark", found 12 files.
+(DRYRUN MODE) Now have 12 files in total.
+(DRYRUN MODE) Removed 1 files due to nonunique device and inode.
+(DRYRUN MODE) Total size is 699352 bytes or 683 KiB
+Removed 9 files due to unique sizes from list.2 files left.
+(DRYRUN MODE) Now eliminating candidates based on first bytes:removed 0 files from list.2 files left.
+(DRYRUN MODE) Now eliminating candidates based on last bytes:removed 0 files from list.2 files left.
+(DRYRUN MODE) Now eliminating candidates based on sha1 checksum:removed 0 files from list.2 files left.
+(DRYRUN MODE) It seems like you have 2 files that are not unique
+(DRYRUN MODE) Totally, 223 KiB can be reduced.
+(DRYRUN MODE) Now making results file results.txt
+```
+
+`rdfind` 命令同样提供了类似忽略空文档(`-ignoreempty`)和跟踪符号链接(`-followsymlinks`)的功能。查看 man 页面获取解释。
+
+```
+-ignoreempty ignore empty files
+-minsize ignore files smaller than speficied size
+-followsymlinks follow symbolic links
+-removeidentinode remove files referring to identical inode
+-checksum identify checksum type to be used
+-deterministic determiness how to sort files
+-makesymlinks turn duplicate files into symbolic links
+-makehardlinks replace duplicate files with hard links
+-makeresultsfile create a results file in the current directory
+-outputname provide name for results file
+-deleteduplicates delete/unlink duplicate files
+-sleep set sleep time between reading files (milliseconds)
+-n, -dryrun display what would have been done, but don't do it
+```
+
+注意 `rdfind` 命令提供了 `-deleteduplicates true` 的设置选项以删除副本。希望这个命令语法上的小问题不会惹恼你。;-)
+
+```
+$ rdfind -deleteduplicates true .
+...
+Deleted 1 files. <==
+```
+
+你将可能需要在你的系统上安装 `rdfind` 命令。试验它以熟悉如何使用它可能是一个好主意。
+
+### 使用 fdupes 命令
+
+`fdupes` 命令同样使得识别重复文件变得简单。它同时提供了大量有用的选项——例如用来迭代的 `-r`。在这个例子中,它像这样将重复文件分组到一起:
+
+```
+$ fdupes ~
+/home/shs/UPGRADE
+/home/shs/mytwin
+
+/home/shs/lp.txt
+/home/shs/lp.man
+
+/home/shs/penguin.png
+/home/shs/penguin0.png
+/home/shs/hideme.png
+```
+
+这是使用迭代的一个例子,注意许多重复文件是重要的(用户的 `.bashrc` 和 `.profile` 文件)并且不应被删除。
+
+```
+# fdupes -r /home
+/home/shark/home.html
+/home/shark/index.html
+
+/home/dory/.bashrc
+/home/eel/.bashrc
+
+/home/nemo/.profile
+/home/dory/.profile
+/home/shark/.profile
+
+/home/nemo/tryme
+/home/shs/tryme
+
+/home/shs/arrow.png
+/home/shs/PNGs/arrow.png
+
+/home/shs/11/files_11.zip
+/home/shs/ERIC/file_11.zip
+
+/home/shs/penguin0.jpg
+/home/shs/PNGs/penguin.jpg
+/home/shs/PNGs/penguin0.jpg
+
+/home/shs/Sandra_rotated.png
+/home/shs/PNGs/Sandra_rotated.png
+```
+
+`fdupe` 命令的许多选项列如下。使用 `fdupes -h` 命令或者阅读 man 页面获取详情。
+
+```
+-r --recurse recurse
+-R --recurse: recurse through specified directories
+-s --symlinks follow symlinked directories
+-H --hardlinks treat hard links as duplicates
+-n --noempty ignore empty files
+-f --omitfirst omit the first file in each set of matches
+-A --nohidden ignore hidden files
+-1 --sameline list matches on a single line
+-S --size show size of duplicate files
+-m --summarize summarize duplicate files information
+-q --quiet hide progress indicator
+-d --delete prompt user for files to preserve
+-N --noprompt when used with --delete, preserve the first file in set
+-I --immediate delete duplicates as they are encountered
+-p --permissions don't soncider files with different owner/group or
+ permission bits as duplicates
+-o --order=WORD order files according to specification
+-i --reverse reverse order while sorting
+-v --version display fdupes version
+-h --help displays help
+```
+
+`fdupes` 命令是另一个你可能需要安装并使用一段时间才能熟悉其众多选项的命令。
+
+### 总结
+
+Linux 系统提供能够定位并(潜在地)能移除重复文件的一系列的好工具,以及能让你指定搜索区域及当对你所发现的重复文件时的处理方式的选项。
+
+--------------------------------------------------------------------------------
+
+via: https://www.networkworld.com/article/3390204/how-to-identify-same-content-files-on-linux.html#tk.rss_all
+
+作者:[Sandra Henry-Stocker][a]
+选题:[lujun9972][b]
+译者:[tomjlw](https://github.com/tomjlw)
+校对:[wxy](https://github.com/wxy)
+
+本文由 [LCTT](https://github.com/LCTT/TranslateProject) 原创编译,[Linux中国](https://linux.cn/) 荣誉推出
+
+[a]: https://www.networkworld.com/author/Sandra-Henry_Stocker/
+[b]: https://github.com/lujun9972
+[1]: https://images.idgesg.net/images/article/2019/04/chairs-100794266-large.jpg
+[2]: https://www.networkworld.com/article/3387961/how-to-identify-duplicate-files-on-linux.html
+[3]: https://www.youtube.com/playlist?list=PL7D2RMSmRO9J8OTpjFECi8DJiTQdd4hua
+[4]: https://www.networkworld.com/article/3242170/linux/invaluable-tips-and-tricks-for-troubleshooting-linux.html
+[5]: https://www.facebook.com/NetworkWorld/
+[6]: https://www.linkedin.com/company/network-world
+
diff --git a/published/20190427 Monitoring CPU and GPU Temperatures on Linux.md b/published/20190427 Monitoring CPU and GPU Temperatures on Linux.md
new file mode 100644
index 0000000000..1ba2cb1a9b
--- /dev/null
+++ b/published/20190427 Monitoring CPU and GPU Temperatures on Linux.md
@@ -0,0 +1,146 @@
+[#]: collector: (lujun9972)
+[#]: translator: (cycoe)
+[#]: reviewer: (wxy)
+[#]: publisher: (wxy)
+[#]: url: (https://linux.cn/article-10929-1.html)
+[#]: subject: (Monitoring CPU and GPU Temperatures on Linux)
+[#]: via: (https://itsfoss.com/monitor-cpu-gpu-temp-linux/)
+[#]: author: (It's FOSS Community https://itsfoss.com/author/itsfoss/)
+
+在 Linux 上监控 CPU 和 GPU 温度
+======
+
+> 本篇文章讨论了在 Linux 命令行中监控 CPU 和 GPU 温度的两种简单方式。
+
+由于 [Steam][1](包括 [Steam Play][2],即 Proton)和一些其他的发展,GNU/Linux 正在成为越来越多计算机用户的日常游戏平台的选择。也有相当一部分用户在遇到像[视频编辑][3]或图形设计等(Kdenlive 和 [Blender][4] 是这类应用程序中很好的例子)资源消耗型计算任务时,也会使用 GNU/Linux。
+
+不管你是否是这些用户中的一员或其他用户,你也一定想知道你的电脑 CPU 和 GPU 能有多热(如果你想要超频的话更会如此)。如果是这样,那么继续读下去。我们会介绍两个非常简单的命令来监控 CPU 和 GPU 温度。
+
+我的装置包括一台 [Slimbook Kymera][5] 和两台显示器(一台 TV 和一台 PC 监视器),使得我可以用一台来玩游戏,另一台来留意监控温度。另外,因为我使用 [Zorin OS][6],我会将关注点放在 Ubuntu 和 Ubuntu 的衍生发行版上。
+
+为了监控 CPU 和 GPU 的行为,我们将利用实用的 `watch` 命令在每几秒钟之后动态地得到读数。
+
+![][7]
+
+### 在 Linux 中监控 CPU 温度
+
+对于 CPU 温度,我们将结合使用 `watch` 与 `sensors` 命令。一篇关于[此工具的图形用户界面版本][8]的有趣文章已经在 It's FOSS 中介绍过了。然而,我们将在此处使用命令行版本:
+
+```
+watch -n 2 sensors
+```
+
+`watch` 保证了读数会在每 2 秒钟更新一次(当然,这个周期值能够根据你的需要去更改):
+
+```
+Every 2,0s: sensors
+
+iwlwifi-virtual-0
+Adapter: Virtual device
+temp1: +39.0°C
+
+acpitz-virtual-0
+Adapter: Virtual device
+temp1: +27.8°C (crit = +119.0°C)
+temp2: +29.8°C (crit = +119.0°C)
+
+coretemp-isa-0000
+Adapter: ISA adapter
+Package id 0: +37.0°C (high = +82.0°C, crit = +100.0°C)
+Core 0: +35.0°C (high = +82.0°C, crit = +100.0°C)
+Core 1: +35.0°C (high = +82.0°C, crit = +100.0°C)
+Core 2: +33.0°C (high = +82.0°C, crit = +100.0°C)
+Core 3: +36.0°C (high = +82.0°C, crit = +100.0°C)
+Core 4: +37.0°C (high = +82.0°C, crit = +100.0°C)
+Core 5: +35.0°C (high = +82.0°C, crit = +100.0°C)
+```
+
+除此之外,我们还能得到如下信息:
+
+ * 我们有 5 个核心正在被使用(并且当前的最高温度为 37.0℃)。
+ * 温度超过 82.0℃ 会被认为是过热。
+ * 超过 100.0℃ 的温度会被认为是超过临界值。
+
+根据以上的温度值我们可以得出结论,我的电脑目前的工作负载非常小。
+
+### 在 Linux 中监控 GPU 温度
+
+现在让我们来看看显卡。我从来没使用过 AMD 的显卡,因此我会将重点放在 Nvidia 的显卡上。我们需要做的第一件事是从 [Ubuntu 的附加驱动][10] 中下载合适的最新驱动。
+
+在 Ubuntu(Zorin 或 Linux Mint 也是相同的)中,进入“软件和更新 > 附加驱动”选项,选择最新的可用驱动。另外,你可以添加或启用显示卡的官方 ppa(通过命令行或通过“软件和更新 > 其他软件”来实现)。安装驱动程序后,你将可以使用 “Nvidia X Server” 的 GUI 程序以及命令行工具 `nvidia-smi`(Nvidia 系统管理界面)。因此我们将使用 `watch` 和 `nvidia-smi`:
+
+```
+watch -n 2 nvidia-smi
+```
+
+与 CPU 的情况一样,我们会在每两秒得到一次更新的读数:
+
+```
+Every 2,0s: nvidia-smi
+
+Fri Apr 19 20:45:30 2019
++-----------------------------------------------------------------------------+
+| Nvidia-SMI 418.56 Driver Version: 418.56 CUDA Version: 10.1 |
+|-------------------------------+----------------------+----------------------+
+| GPU Name Persistence-M| Bus-Id Disp.A | Volatile Uncorr. ECC |
+| Fan Temp Perf Pwr:Usage/Cap| Memory-Usage | GPU-Util Compute M. |
+|===============================+======================+======================|
+| 0 GeForce GTX 106... Off | 00000000:01:00.0 On | N/A |
+| 0% 54C P8 10W / 120W | 433MiB / 6077MiB | 4% Default |
++-------------------------------+----------------------+----------------------+
+
++-----------------------------------------------------------------------------+
+| Processes: GPU Memory |
+| GPU PID Type Process name Usage |
+|=============================================================================|
+| 0 1557 G /usr/lib/xorg/Xorg 190MiB |
+| 0 1820 G /usr/bin/gnome-shell 174MiB |
+| 0 7820 G ...equest-channel-token=303407235874180773 65MiB |
++-----------------------------------------------------------------------------+
+```
+
+从这个表格中我们得到了关于显示卡的如下信息:
+
+ * 它正在使用版本号为 418.56 的开源驱动。
+ * 显示卡的当前温度为 54.0℃,并且风扇的使用量为 0%。
+ * 电量的消耗非常低:仅仅 10W。
+ * 总量为 6GB 的 vram(视频随机存取存储器),只使用了 433MB。
+ * vram 正在被 3 个进程使用,他们的 ID 分别为 1557、1820 和 7820。
+
+大部分这些事实或数值都清晰地表明,我们没有在玩任何消耗系统资源的游戏或处理大负载的任务。当我们开始玩游戏、处理视频或其他类似任务时,这些值就会开始上升。
+
+#### 结论
+
+即便我们有 GUI 工具,但我还是发现这两个命令对于实时监控硬件非常的顺手。
+
+你将如何去使用它们呢?你可以通过阅读他们的 man 手册来学习更多关于这些工具的使用技巧。
+
+你有其他偏爱的工具吗?在评论里分享给我们吧 ;)。
+
+玩得开心!
+
+--------------------------------------------------------------------------------
+
+via: https://itsfoss.com/monitor-cpu-gpu-temp-linux/
+
+作者:[Alejandro Egea-Abellán][a]
+选题:[lujun9972][b]
+译者:[cycoe](https://github.com/cycoe)
+校对:[wxy](https://github.com/wxy)
+
+本文由 [LCTT](https://github.com/LCTT/TranslateProject) 原创编译,[Linux中国](https://linux.cn/) 荣誉推出
+
+[a]: https://itsfoss.com/author/itsfoss/
+[b]: https://github.com/lujun9972
+[1]: https://itsfoss.com/install-steam-ubuntu-linux/
+[2]: https://itsfoss.com/steam-play-proton/
+[3]: https://itsfoss.com/best-video-editing-software-linux/
+[4]: https://www.blender.org/
+[5]: https://slimbook.es/
+[6]: https://zorinos.com/
+[7]: https://itsfoss.com/wp-content/uploads/2019/04/monitor-cpu-gpu-temperature-linux-800x450.png
+[8]: https://itsfoss.com/check-laptop-cpu-temperature-ubuntu/
+[9]: https://itsfoss.com/best-command-line-games-linux/
+[10]: https://itsfoss.com/install-additional-drivers-ubuntu/
+[11]: https://itsfoss.com/review-googler-linux/
+[12]: https://itsfoss.com/wp-content/uploads/2019/04/EGEA-ABELLAN-Alejandro.jpg
diff --git a/published/20190428 Installing Budgie Desktop on Ubuntu -Quick Guide.md b/published/20190428 Installing Budgie Desktop on Ubuntu -Quick Guide.md
new file mode 100644
index 0000000000..457caaa69a
--- /dev/null
+++ b/published/20190428 Installing Budgie Desktop on Ubuntu -Quick Guide.md
@@ -0,0 +1,112 @@
+[#]: collector: (lujun9972)
+[#]: translator: (geekpi)
+[#]: reviewer: (wxy)
+[#]: publisher: (wxy)
+[#]: url: (https://linux.cn/article-10919-1.html)
+[#]: subject: (Installing Budgie Desktop on Ubuntu [Quick Guide])
+[#]: via: (https://itsfoss.com/install-budgie-ubuntu/)
+[#]: author: (Atharva Lele https://itsfoss.com/author/atharva/)
+
+在 Ubuntu 上安装 Budgie 桌面
+======
+
+> 在这个逐步的教程中学习如何在 Ubuntu 上安装 Budgie 桌面。
+
+在所有[各种 Ubuntu 版本][1]中,[Ubuntu Budgie][2] 是最被低估的版本。它外观优雅,而且需要的资源也不多。
+
+阅读这篇 《[Ubuntu Budgie 点评][3]》或观看下面的视频,了解 Ubuntu Budgie 18.04 的外观如何。
+
+- [Ubuntu 18.04 Budgie Desktop Tour [It's Elegant]](https://youtu.be/KXgreWOK33k)
+
+如果你喜欢 [Budgie 桌面][5]但你正在使用其他版本的 Ubuntu,例如默认 Ubuntu 带有 GNOME 桌面,我有个好消息。你可以在当前的 Ubuntu 系统上安装 Budgie 并切换桌面环境。
+
+在这篇文章中,我将告诉你到底该怎么做。但首先,对那些不了解 Budgie 的人进行一点介绍。
+
+Budgie 桌面环境主要由 [Solus Linux 团队开发][6]。它的设计注重优雅和现代使用。Budgie 适用于所有主流 Linux 发行版,可以让用户在其上尝试体验这种新的桌面环境。Budgie 现在非常成熟,并提供了出色的桌面体验。
+
+> 警告
+>
+> 在同一系统上安装多个桌面可能会导致冲突,你可能会遇到一些问题,如面板中缺少图标或同一程序的多个图标。
+>
+> 你也许不会遇到任何问题。是否要尝试不同桌面由你决定。
+
+### 在 Ubuntu 上安装 Budgie
+
+此方法未在 Linux Mint 上进行测试,因此我建议你 Mint 上不要按照此指南进行操作。
+
+对于正在使用 Ubuntu 的人,Budgie 现在默认是 Ubuntu 仓库的一部分。因此,我们不需要添加任何 PPA 来下载 Budgie。
+
+要安装 Budgie,只需在终端中运行此命令即可。我们首先要确保系统已完全更新。
+
+```
+sudo apt update && sudo apt upgrade
+sudo apt install ubuntu-budgie-desktop
+```
+
+下载完成后,你将看到选择显示管理器的提示。选择 “lightdm” 以获得完整的 Budgie 体验。
+
+![Select lightdm][7]
+
+安装完成后,重启计算机。然后,你会看到 Budgie 的登录页面。输入你的密码进入主屏幕。
+
+![Budgie Desktop Home][8]
+
+### 切换到其他桌面环境
+
+![Budgie login screen][9]
+
+你可以单击登录名旁边的 Budgie 图标获取登录选项。在那里,你可以在已安装的桌面环境(DE)之间进行选择。就我而言,我看到了 Budgie 和默认的 Ubuntu(GNOME)桌面。
+
+![Select your DE][10]
+
+因此,无论何时你想登录 GNOME,都可以使用此菜单执行此操作。
+
+### 如何删除 Budgie
+
+如果你不喜欢 Budgie 或只是想回到常规的以前的 Ubuntu,你可以如上节所述切换回常规桌面。
+
+但是,如果你真的想要删除 Budgie 及其组件,你可以按照以下命令回到之前的状态。
+
+**在使用这些命令之前先切换到其他桌面环境:**
+
+```
+sudo apt remove ubuntu-budgie-desktop ubuntu-budgie* lightdm
+sudo apt autoremove
+sudo apt install --reinstall gdm3
+```
+
+成功运行所有命令后,重启计算机。
+
+现在,你将回到 GNOME 或其他你有的桌面。
+
+### 你对 Budgie 有什么看法?
+
+Budgie 是[最佳 Linux 桌面环境][12]之一。希望这个简短的指南帮助你在 Ubuntu 上安装了很棒的 Budgie 桌面。
+
+如果你安装了 Budgie,你最喜欢它的什么?请在下面的评论中告诉我们。像往常一样,欢迎任何问题或建议。
+
+--------------------------------------------------------------------------------
+
+via: https://itsfoss.com/install-budgie-ubuntu/
+
+作者:[Atharva Lele][a]
+选题:[lujun9972][b]
+译者:[geekpi](https://github.com/geekpi)
+校对:[wxy](https://github.com/wxy)
+
+本文由 [LCTT](https://github.com/LCTT/TranslateProject) 原创编译,[Linux中国](https://linux.cn/) 荣誉推出
+
+[a]: https://itsfoss.com/author/atharva/
+[b]: https://github.com/lujun9972
+[1]: https://itsfoss.com/which-ubuntu-install/
+[2]: https://ubuntubudgie.org/
+[3]: https://itsfoss.com/ubuntu-budgie-18-review/
+[4]: https://www.youtube.com/c/itsfoss?sub_confirmation=1
+[5]: https://github.com/solus-project/budgie-desktop
+[6]: https://getsol.us/home/
+[7]: https://i0.wp.com/itsfoss.com/wp-content/uploads/2019/04/budgie_install_select_dm.png?fit=800%2C559&ssl=1
+[8]: https://i1.wp.com/itsfoss.com/wp-content/uploads/2019/04/budgie_homescreen.jpg?fit=800%2C500&ssl=1
+[9]: https://i2.wp.com/itsfoss.com/wp-content/uploads/2019/04/budgie_install_lockscreen.png?fit=800%2C403&ssl=1
+[10]: https://i0.wp.com/itsfoss.com/wp-content/uploads/2019/04/budgie_install_lockscreen_select_de.png?fit=800%2C403&ssl=1
+[11]: https://itsfoss.com/snapd-error-ubuntu/
+[12]: https://itsfoss.com/best-linux-desktop-environments/
diff --git a/translated/tech/20161106 Myths about -dev-urandom.md b/published/201905/20161106 Myths about -dev-urandom.md
similarity index 73%
rename from translated/tech/20161106 Myths about -dev-urandom.md
rename to published/201905/20161106 Myths about -dev-urandom.md
index 118c6426f2..76f07ebc3c 100644
--- a/translated/tech/20161106 Myths about -dev-urandom.md
+++ b/published/201905/20161106 Myths about -dev-urandom.md
@@ -7,37 +7,37 @@
**`/dev/urandom` 不安全。加密用途必须使用 `/dev/random`**
-事实:`/dev/urandom` 才是类 Unix 操作系统下推荐的加密种子。
+*事实*:`/dev/urandom` 才是类 Unix 操作系统下推荐的加密种子。
**`/dev/urandom` 是伪随机数生成器(PRND),而 `/dev/random` 是“真”随机数生成器。**
-事实:它们两者本质上用的是同一种 CSPRNG (一种密码学伪随机数生成器)。它们之间细微的差别和“真”不“真”随机完全无关
+*事实*:它们两者本质上用的是同一种 CSPRNG (一种密码学伪随机数生成器)。它们之间细微的差别和“真”“不真”随机完全无关。(参见:“Linux 随机数生成器的构架”一节)
**`/dev/random` 在任何情况下都是密码学应用更好地选择。即便 `/dev/urandom` 也同样安全,我们还是不应该用它。**
-事实:`/dev/random` 有个很恶心人的问题:它是阻塞的。(LCTT 译注:意味着请求都得逐个执行,等待前一个请求完成)
+*事实*:`/dev/random` 有个很恶心人的问题:它是阻塞的。(参见:“阻塞有什么问题?”一节)(LCTT 译注:意味着请求都得逐个执行,等待前一个请求完成)
-**但阻塞不是好事吗!`/dev/random` 只会给出电脑收集的信息熵足以支持的随机量。`/dev/urandom` 在用完了所有熵的情况下还会不断吐不安全的随机数给你。**
+**但阻塞不是好事吗!`/dev/random` 只会给出电脑收集的信息熵足以支持的随机量。`/dev/urandom` 在用完了所有熵的情况下还会不断吐出不安全的随机数给你。**
-事实:这是误解。就算我们不去考虑应用层面后续对随机种子的用法,“用完信息熵池”这个概念本身就不存在。仅仅 256 位的熵就足以生成计算上安全的随机数很长、很长的一段时间了。
+*事实*:这是误解。就算我们不去考虑应用层面后续对随机种子的用法,“用完信息熵池”这个概念本身就不存在。仅仅 256 位的熵就足以生成计算上安全的随机数很长、很长的一段时间了。(参见:“那熵池快空了的情况呢?”一节)
问题的关键还在后头:`/dev/random` 怎么知道有系统会*多少*可用的信息熵?接着看!
**但密码学家老是讨论重新选种子(re-seeding)。这难道不和上一条冲突吗?**
-事实:你说的也没错!某种程度上吧。确实,随机数生成器一直在使用系统信息熵的状态重新选种。但这么做(一部分)是因为别的原因。
+*事实*:你说的也没错!某种程度上吧。确实,随机数生成器一直在使用系统信息熵的状态重新选种。但这么做(一部分)是因为别的原因。(参见:“重新选种”一节)
这样说吧,我没有说引入新的信息熵是坏的。更多的熵肯定更好。我只是说在熵池低的时候阻塞是没必要的。
**好,就算你说的都对,但是 `/dev/(u)random` 的 man 页面和你说的也不一样啊!到底有没有专家同意你说的这堆啊?**
-事实:其实 man 页面和我说的不冲突。它看似好像在说 `/dev/urandom` 对密码学用途来说不安全,但如果你真的理解这堆密码学术语你就知道它说的并不是这个意思。
+*事实*:其实 man 页面和我说的不冲突。它看似好像在说 `/dev/urandom` 对密码学用途来说不安全,但如果你真的理解这堆密码学术语你就知道它说的并不是这个意思。(参见:“random 和 urandom 的 man 页面”一节)
man 页面确实说在一些情况下推荐使用 `/dev/random` (我觉得也没问题,但绝对不是说必要的),但它也推荐在大多数“一般”的密码学应用下使用 `/dev/urandom` 。
虽然诉诸权威一般来说不是好事,但在密码学这么严肃的事情上,和专家统一意见是很有必要的。
-所以说呢,还确实有一些*专家*和我的一件事一致的:`/dev/urandom` 就应该是类 UNIX 操作系统下密码学应用的首选。显然的,是他们的观点说服了我而不是反过来的。
+所以说呢,还确实有一些*专家*和我的一件事一致的:`/dev/urandom` 就应该是类 UNIX 操作系统下密码学应用的首选。显然的,是他们的观点说服了我而不是反过来的。(参见:“正道”一节)
------
@@ -45,9 +45,9 @@ man 页面确实说在一些情况下推荐使用 `/dev/random` (我觉得也
我尝试不讲太高深的东西,但是有两点内容必须先提一下才能让我们接着论证观点。
-首当其冲的,*什么是随机性*,或者更准确地:我们在探讨什么样的随机性?
+首当其冲的,*什么是随机性*,或者更准确地:我们在探讨什么样的随机性?(参见:“真随机”一节)
-另外一点很重要的是,我*没有尝试以说教的态度*对你们写这段话。我写这篇文章是为了日后可以在讨论起的时候指给别人看。比 140 字长(LCTT 译注:推特长度)。这样我就不用一遍遍重复我的观点了。能把论点磨炼成一篇文章本身就很有助于将来的讨论。
+另外一点很重要的是,我*没有尝试以说教的态度*对你们写这段话。我写这篇文章是为了日后可以在讨论起的时候指给别人看。比 140 字长(LCTT 译注:推特长度)。这样我就不用一遍遍重复我的观点了。能把论点磨炼成一篇文章本身就很有助于将来的讨论。(参见:“你是在说我笨?!”一节)
并且我非常乐意听到不一样的观点。但我只是认为单单地说 `/dev/urandom` 坏是不够的。你得能指出到底有什么问题,并且剖析它们。
@@ -55,43 +55,43 @@ man 页面确实说在一些情况下推荐使用 `/dev/random` (我觉得也
绝对没有!
-事实上我自己也相信了 “`/dev/urandom` 是不安全的” 好些年。这几乎不是我们的错,因为那么德高望重的人在 Usenet、论坛、推特上跟我们重复这个观点。甚至*连 man 手册*都似是而非地说着。我们当年怎么可能鄙视诸如“信息熵太低了”这种看上去就很让人信服的观点呢?
+事实上我自己也相信了 “`/dev/urandom` 是不安全的” 好些年。这几乎不是我们的错,因为那么德高望重的人在 Usenet、论坛、推特上跟我们重复这个观点。甚至*连 man 手册*都似是而非地说着。我们当年怎么可能鄙视诸如“信息熵太低了”这种看上去就很让人信服的观点呢?(参见:“random 和 urandom 的 man 页面”一节)
整个流言之所以如此广为流传不是因为人们太蠢,而是因为但凡有点关于信息熵和密码学概念的人都会觉得这个说法很有道理。直觉似乎都在告诉我们这流言讲的很有道理。很不幸直觉在密码学里通常不管用,这次也一样。
### 真随机
-什么叫一个随机变量是“真随机的”?
+随机数是“真正随机”是什么意思?
-我不想搞的太复杂以至于变成哲学范畴的东西。这种讨论很容易走偏因为随机模型大家见仁见智,讨论很快变得毫无意义。
+我不想搞的太复杂以至于变成哲学范畴的东西。这种讨论很容易走偏因为对于随机模型大家见仁见智,讨论很快变得毫无意义。
在我看来“真随机”的“试金石”是量子效应。一个光子穿过或不穿过一个半透镜。或者观察一个放射性粒子衰变。这类东西是现实世界最接近真随机的东西。当然,有些人也不相信这类过程是真随机的,或者这个世界根本不存在任何随机性。这个就百家争鸣了,我也不好多说什么了。
-密码学家一般都会通过不去讨论什么是“真随机”来避免这种争论。它们更关心的是不可预测性。只要没有*任何*方法能猜出下一个随机数就可以了。所以当你以密码学应用为前提讨论一个随机数好不好的时候,在我看来这才是最重要的。
+密码学家一般都会通过不去讨论什么是“真随机”来避免这种哲学辩论。他们更关心的是不可预测性。只要没有*任何*方法能猜出下一个随机数就可以了。所以当你以密码学应用为前提讨论一个随机数好不好的时候,在我看来这才是最重要的。
无论如何,我不怎么关心“哲学上安全”的随机数,这也包括别人嘴里的“真”随机数。
-## 两种安全,一种有用
+### 两种安全,一种有用
但就让我们退一步说,你有了一个“真”随机变量。你下一步做什么呢?
-你把它们打印出来然后挂在墙上来展示量子宇宙的美与和谐?牛逼!我很理解你。
+你把它们打印出来然后挂在墙上来展示量子宇宙的美与和谐?牛逼!我支持你。
但是等等,你说你要*用*它们?做密码学用途?额,那这就废了,因为这事情就有点复杂了。
-事情是这样的,你的真随机,量子力学加护的随机数即将被用进不理想的现实世界程序里。
+事情是这样的,你的真随机、量子力学加护的随机数即将被用进不理想的现实世界算法里去。
-因为我们使用的大多数算法并不是理论信息学上安全的。它们“只能”提供 **计算意义上的安全**。我能想到为数不多的例外就只有 Shamir 密钥分享 和 One-time pad 算法。并且就算前者是名副其实的(如果你实际打算用的话),后者则毫无可行性可言。
+因为我们使用的几乎所有的算法都并不是信息论安全性的。它们“只能”提供**计算意义上的安全**。我能想到为数不多的例外就只有 Shamir 密钥分享和一次性密码本(OTP)算法。并且就算前者是名副其实的(如果你实际打算用的话),后者则毫无可行性可言。
-但所有那些大名鼎鼎的密码学算法,AES、RSA、Diffie-Hellman、椭圆曲线,还有所有那些加密软件包,OpenSSL、GnuTLS、Keyczar、你的操作系统的加密 API,都仅仅是计算意义上的安全的。
+但所有那些大名鼎鼎的密码学算法,AES、RSA、Diffie-Hellman、椭圆曲线,还有所有那些加密软件包,OpenSSL、GnuTLS、Keyczar、你的操作系统的加密 API,都仅仅是计算意义上安全的。
-那区别是什么呢?理论信息学上的安全肯定是安全的,绝对是,其它那些的算法都可能在理论上被拥有无限计算力的穷举破解。我们依然愉快地使用它们因为全世界的计算机加起来都不可能在宇宙年龄的时间里破解,至少现在是这样。而这就是我们文章里说的“不安全”。
+那区别是什么呢?信息论安全的算法肯定是安全的,绝对是,其它那些的算法都可能在理论上被拥有无限计算力的穷举破解。我们依然愉快地使用它们是因为全世界的计算机加起来都不可能在宇宙年龄的时间里破解,至少现在是这样。而这就是我们文章里说的“不安全”。
-除非哪个聪明的家伙破解了算法本身——在只需要极少量计算力的情况下。这也是每个密码学家梦寐以求的圣杯:破解 AES 本身、破解 RSA 本身等等。
+除非哪个聪明的家伙破解了算法本身 —— 在只需要更少量计算力、在今天可实现的计算力的情况下。这也是每个密码学家梦寐以求的圣杯:破解 AES 本身、破解 RSA 本身等等。
所以现在我们来到了更底层的东西:随机数生成器,你坚持要“真随机”而不是“伪随机”。但是没过一会儿你的真随机数就被喂进了你极为鄙视的伪随机算法里了!
-真相是,如果我们最先进的 hash 算法被破解了,或者最先进的块加密被破解了,你得到这些那些“哲学上不安全的”甚至无所谓了,因为反正你也没有安全的应用方法了。
+真相是,如果我们最先进的哈希算法被破解了,或者最先进的分组加密算法被破解了,你得到的这些“哲学上不安全”的随机数甚至无所谓了,因为反正你也没有安全的应用方法了。
所以把计算性上安全的随机数喂给你的仅仅是计算性上安全的算法就可以了,换而言之,用 `/dev/urandom`。
@@ -103,7 +103,7 @@ man 页面确实说在一些情况下推荐使用 `/dev/random` (我觉得也
![image: mythical structure of the kernel's random number generator][1]
-“真随机数”,尽管可能有点瑕疵,进入操作系统然后它的熵立刻被加入内部熵计数器。然后经过“矫偏”和“漂白”之后它进入内核的熵池,然后 `/dev/random` 和 `/dev/urandom` 从里面生成随机数。
+“真正的随机性”,尽管可能有点瑕疵,进入操作系统然后它的熵立刻被加入内部熵计数器。然后经过“矫偏”和“漂白”之后它进入内核的熵池,然后 `/dev/random` 和 `/dev/urandom` 从里面生成随机数。
“真”随机数生成器,`/dev/random`,直接从池里选出随机数,如果熵计数器表示能满足需要的数字大小,那就吐出数字并且减少熵计数。如果不够的话,它会阻塞程序直至有足够的熵进入系统。
@@ -123,25 +123,25 @@ man 页面确实说在一些情况下推荐使用 `/dev/random` (我觉得也
![image: actual structure of the kernel's random number generator before Linux 4.8][2]
-> 这是个很粗糙的简化。实际上不仅有一个,而是三个熵池。一个主池,另一个给 `/dev/random`,还有一个给 `/dev/urandom`,后两者依靠从主池里获取熵。这三个池都有各自的熵计数器,但二级池(后两个)的计数器基本都在 0 附近,而“新鲜”的熵总在需要的时候从主池流过来。同时还有好多混合和回流进系统在同时进行。整个过程对于这篇文档来说都过于复杂了我们跳过。
-
-你看到最大的区别了吗?CSPRNG 并不是和随机数生成器一起跑的,以 `/dev/urandom` 需要输出但熵不够的时候进行填充。CSPRNG 是整个随机数生成过程的内部组件之一。从来就没有什么 `/dev/random` 直接从池里输出纯纯的随机性。每个随机源的输入都在 CSPRNG 里充分混合和散列过了,这一切都发生在实际变成一个随机数,被 `/dev/urandom` 或者 `/dev/random` 吐出去之前。
+你看到最大的区别了吗?CSPRNG 并不是和随机数生成器一起跑的,它在 `/dev/urandom` 需要输出但熵不够的时候进行填充。CSPRNG 是整个随机数生成过程的内部组件之一。从来就没有什么 `/dev/random` 直接从池里输出纯纯的随机性。每个随机源的输入都在 CSPRNG 里充分混合和散列过了,这一切都发生在实际变成一个随机数,被 `/dev/urandom` 或者 `/dev/random` 吐出去之前。
另外一个重要的区别是这里没有熵计数器的任何事情,只有预估。一个源给你的熵的量并不是什么很明确能直接得到的数字。你得预估它。注意,如果你太乐观地预估了它,那 `/dev/random` 最重要的特性——只给出熵允许的随机量——就荡然无存了。很不幸的,预估熵的量是很困难的。
-Linux 内核只使用事件的到达时间来预估熵的量。它通过多项式插值,某种模型,来预估实际的到达时间有多“出乎意料”。这种多项式插值的方法到底是不是好的预估熵量的方法本身就是个问题。同时硬件情况会不会以某种特定的方式影响到达时间也是个问题。而所有硬件的取样率也是个问题,因为这基本上就直接决定了随机数到达时间的颗粒度。
+> 这是个很粗糙的简化。实际上不仅有一个,而是三个熵池。一个主池,另一个给 `/dev/random`,还有一个给 `/dev/urandom`,后两者依靠从主池里获取熵。这三个池都有各自的熵计数器,但二级池(后两个)的计数器基本都在 0 附近,而“新鲜”的熵总在需要的时候从主池流过来。同时还有好多混合和回流进系统在同时进行。整个过程对于这篇文档来说都过于复杂了,我们跳过。
+
+Linux 内核只使用事件的到达时间来预估熵的量。根据模型,它通过多项式插值来预估实际的到达时间有多“出乎意料”。这种多项式插值的方法到底是不是好的预估熵量的方法本身就是个问题。同时硬件情况会不会以某种特定的方式影响到达时间也是个问题。而所有硬件的取样率也是个问题,因为这基本上就直接决定了随机数到达时间的颗粒度。
说到最后,至少现在看来,内核的熵预估还是不错的。这也意味着它比较保守。有些人会具体地讨论它有多好,这都超出我的脑容量了。就算这样,如果你坚持不想在没有足够多的熵的情况下吐出随机数,那你看到这里可能还会有一丝紧张。我睡的就很香了,因为我不关心熵预估什么的。
-最后强调一下终点:`/dev/random` 和 `/dev/urandom` 都是被同一个 CSPRNG 喂的输入。只有它们在用完各自熵池(根据某种预估标准)的时候,它们的行为会不同:`/dev/random` 阻塞,`/dev/urandom` 不阻塞。
+最后要明确一下:`/dev/random` 和 `/dev/urandom` 都是被同一个 CSPRNG 饲喂的。只有它们在用完各自熵池(根据某种预估标准)的时候,它们的行为会不同:`/dev/random` 阻塞,`/dev/urandom` 不阻塞。
##### Linux 4.8 以后
-在 Linux 4.8 里,`/dev/random` 和 `/dev/urandom` 的等价性被放弃了。现在 `/dev/urandom` 的输出不来自于熵池,而是直接从 CSPRNG 来。
-
![image: actual structure of the kernel's random number generator from Linux 4.8 onward][3]
-*我们很快会理解*为什么这不是一个安全问题。
+在 Linux 4.8 里,`/dev/random` 和 `/dev/urandom` 的等价性被放弃了。现在 `/dev/urandom` 的输出不来自于熵池,而是直接从 CSPRNG 来。
+
+*我们很快会理解*为什么这不是一个安全问题。(参见:“CSPRNG 没问题”一节)
### 阻塞有什么问题?
@@ -149,7 +149,7 @@ Linux 内核只使用事件的到达时间来预估熵的量。它通过多项
这些都是问题。阻塞本质上会降低可用性。换而言之你的系统不干你让它干的事情。不用我说,这是不好的。要是它不干活你干嘛搭建它呢?
-> 我在工厂自动化里做过和安全相关的系统。猜猜看安全系统失效的主要原因是什么?被错误操作。就这么简单。很多安全措施的流程让工人恼火了。比如时间太长,或者太不方便。你要知道人很会找捷径来“解决”问题。
+> 我在工厂自动化里做过和安全相关的系统。猜猜看安全系统失效的主要原因是什么?操作问题。就这么简单。很多安全措施的流程让工人恼火了。比如时间太长,或者太不方便。你要知道人很会找捷径来“解决”问题。
但其实有个更深刻的问题:人们不喜欢被打断。它们会找一些绕过的方法,把一些诡异的东西接在一起仅仅因为这样能用。一般人根本不知道什么密码学什么乱七八糟的,至少正常的人是这样吧。
@@ -157,23 +157,23 @@ Linux 内核只使用事件的到达时间来预估熵的量。它通过多项
到头来如果东西太难用的话,你的用户就会被迫开始做一些降低系统安全性的事情——你甚至不知道它们会做些什么。
-我们很容易会忽视可用性之类的重要性。毕竟安全第一对吧?所以比起牺牲安全,不可用,难用,不方便都是次要的?
+我们很容易会忽视可用性之类的重要性。毕竟安全第一对吧?所以比起牺牲安全,不可用、难用、不方便都是次要的?
这种二元对立的想法是错的。阻塞不一定就安全了。正如我们看到的,`/dev/urandom` 直接从 CSPRNG 里给你一样好的随机数。用它不好吗!
### CSPRNG 没问题
-现在情况听上去很沧桑。如果连高质量的 `/dev/random` 都是从一个 CSPRNG 里来的,我们怎么敢在高安全性的需求上使用它呢?
+现在情况听上去很惨淡。如果连高质量的 `/dev/random` 都是从一个 CSPRNG 里来的,我们怎么敢在高安全性的需求上使用它呢?
-实际上,“看上去随机”是现存大多数密码学基础组件的基本要求。如果你观察一个密码学哈希的输出,它一定得和随机的字符串不可区分,密码学家才会认可这个算法。如果你生成一个块加密,它的输出(在你不知道密钥的情况下)也必须和随机数据不可区分才行。
+实际上,“看上去随机”是现存大多数密码学基础组件的基本要求。如果你观察一个密码学哈希的输出,它一定得和随机的字符串不可区分,密码学家才会认可这个算法。如果你生成一个分组加密,它的输出(在你不知道密钥的情况下)也必须和随机数据不可区分才行。
-如果任何人能比暴力穷举要更有效地破解一个加密,比如它利用了某些 CSPRNG 伪随机的弱点,那这就又是老一套了:一切都废了,也别谈后面的了。块加密、哈希,一切都是基于某个数学算法,比如 CSPRNG。所以别害怕,到头来都一样。
+如果任何人能比暴力穷举要更有效地破解一个加密,比如它利用了某些 CSPRNG 伪随机的弱点,那这就又是老一套了:一切都废了,也别谈后面的了。分组加密、哈希,一切都是基于某个数学算法,比如 CSPRNG。所以别害怕,到头来都一样。
### 那熵池快空了的情况呢?
毫无影响。
-加密算法的根基建立在攻击者不能预测输出上,只要最一开始有足够的随机性(熵)就行了。一般的下限是 256 位,不需要更多了。
+加密算法的根基建立在攻击者不能预测输出上,只要最一开始有足够的随机性(熵)就行了。“足够”的下限可以是 256 位,不需要更多了。
介于我们一直在很随意的使用“熵”这个概念,我用“位”来量化随机性希望读者不要太在意细节。像我们之前讨论的那样,内核的随机数生成器甚至没法精确地知道进入系统的熵的量。只有一个预估。而且这个预估的准确性到底怎么样也没人知道。
@@ -211,7 +211,7 @@ Linux 内核只使用事件的到达时间来预估熵的量。它通过多项
我们在回到 man 页面说:“使用 `/dev/random`”。我们已经知道了,虽然 `/dev/urandom` 不阻塞,但是它的随机数和 `/dev/random` 都是从同一个 CSPRNG 里来的。
-如果你真的需要信息论理论上安全的随机数(你不需要的,相信我),那才有可能成为唯一一个你需要等足够熵进入 CSPRNG 的理由。而且你也不能用 `/dev/random`。
+如果你真的需要信息论安全性的随机数(你不需要的,相信我),那才有可能成为唯一一个你需要等足够熵进入 CSPRNG 的理由。而且你也不能用 `/dev/random`。
man 页面有毒,就这样。但至少它还稍稍挽回了一下自己:
@@ -227,7 +227,7 @@ man 页面有毒,就这样。但至少它还稍稍挽回了一下自己:
### 正道
-本篇文章里的观点显然在互联网上是“小众”的。但如果问问一个真正的密码学家,你很难找到一个认同阻塞 `/dev/random` 的人。
+本篇文章里的观点显然在互联网上是“小众”的。但如果问一个真正的密码学家,你很难找到一个认同阻塞 `/dev/random` 的人。
比如我们看看 [Daniel Bernstein][5](即著名的 djb)的看法:
@@ -238,8 +238,6 @@ man 页面有毒,就这样。但至少它还稍稍挽回了一下自己:
>
> 对密码学家来说这甚至都不好笑了
-
-
或者 [Thomas Pornin][6] 的看法,他也是我在 stackexchange 上见过最乐于助人的一位:
> 简单来说,是的。展开说,答案还是一样。`/dev/urandom` 生成的数据可以说和真随机完全无法区分,至少在现有科技水平下。使用比 `/dev/urandom` “更好的“随机性毫无意义,除非你在使用极为罕见的“信息论安全”的加密算法。这肯定不是你的情况,不然你早就说了。
@@ -260,13 +258,13 @@ Linux 的 `/dev/urandom` 会很乐意给你吐点不怎么随机的随机数,
FreeBSD 的行为更正确点:`/dev/random` 和 `/dev/urandom` 是一样的,在系统启动的时候 `/dev/random` 会阻塞到有足够的熵为止,然后它们都再也不阻塞了。
-> 与此同时 Linux 实行了一个新的系统调用,最早由 OpenBSD 引入叫 `getentrypy(2)`,在 Linux 下这个叫 `getrandom(2)`。这个系统调用有着上述正确的行为:阻塞到有足够的熵为止,然后再也不阻塞了。当然,这是个系统调用,而不是一个字节设备(LCTT 译注:指不在 `/dev/` 下),所以它在 shell 或者别的脚本语言里没那么容易获取。这个系统调用 自 Linux 3.17 起存在。
+> 与此同时 Linux 实行了一个新的系统调用,最早由 OpenBSD 引入叫 `getentrypy(2)`,在 Linux 下这个叫 `getrandom(2)`。这个系统调用有着上述正确的行为:阻塞到有足够的熵为止,然后再也不阻塞了。当然,这是个系统调用,而不是一个字节设备(LCTT 译注:不在 `/dev/` 下),所以它在 shell 或者别的脚本语言里没那么容易获取。这个系统调用 自 Linux 3.17 起存在。
-在 Linux 上其实这个问题不太大,因为 Linux 发行版会在启动的过程中储蓄一点随机数(这发生在已经有一些熵之后,因为启动程序不会在按下电源的一瞬间就开始运行)到一个种子文件中,以便系统下次启动的时候读取。所以每次启动的时候系统都会从上一次会话里带一点随机性过来。
+在 Linux 上其实这个问题不太大,因为 Linux 发行版会在启动的过程中保存一点随机数(这发生在已经有一些熵之后,因为启动程序不会在按下电源的一瞬间就开始运行)到一个种子文件中,以便系统下次启动的时候读取。所以每次启动的时候系统都会从上一次会话里带一点随机性过来。
显然这比不上在关机脚本里写入一些随机种子,因为这样的显然就有更多熵可以操作了。但这样做显而易见的好处就是它不用关心系统是不是正确关机了,比如可能你系统崩溃了。
-而且这种做法在你真正第一次启动系统的时候也没法帮你随机,不过好在系统安装器一般会写一个种子文件,所以基本上问题不大。
+而且这种做法在你真正第一次启动系统的时候也没法帮你随机,不过好在 Linux 系统安装程序一般会保存一个种子文件,所以基本上问题不大。
虚拟机是另外一层问题。因为用户喜欢克隆它们,或者恢复到某个之前的状态。这种情况下那个种子文件就帮不到你了。
diff --git a/translated/tech/20171214 Build a game framework with Python using the module Pygame.md b/published/201905/20171214 Build a game framework with Python using the module Pygame.md
similarity index 52%
rename from translated/tech/20171214 Build a game framework with Python using the module Pygame.md
rename to published/201905/20171214 Build a game framework with Python using the module Pygame.md
index 7ce7402959..931a248a8c 100644
--- a/translated/tech/20171214 Build a game framework with Python using the module Pygame.md
+++ b/published/201905/20171214 Build a game framework with Python using the module Pygame.md
@@ -1,37 +1,39 @@
[#]: collector: (lujun9972)
[#]: translator: (robsean)
-[#]: reviewer: ( )
-[#]: publisher: ( )
-[#]: url: ( )
+[#]: reviewer: (wxy)
+[#]: publisher: (wxy)
+[#]: url: (https://linux.cn/article-10850-1.html)
[#]: subject: (Build a game framework with Python using the module Pygame)
[#]: via: (https://opensource.com/article/17/12/game-framework-python)
[#]: author: (Seth Kenlon https://opensource.com/users/seth)
使用 Python 和 Pygame 模块构建一个游戏框架
======
-这系列的第一篇通过创建一个简单的骰子游戏来探究 Python。现在是来从零制作你自己的游戏的时间。
+
+ > 这系列的第一篇通过创建一个简单的骰子游戏来探究 Python。现在是来从零制作你自己的游戏的时间。
+

-在我的 [这系列的第一篇文章][1] 中, 我已经讲解如何使用 Python 创建一个简单的,基于文本的骰子游戏。这次,我将展示如何使用 Python 和 Pygame 模块来创建一个图形化游戏。它将占用一些文章来得到一个确实完成一些东西的游戏,但是在这系列的结尾,你将有一个更好的理解,如何查找和学习新的 Python 模块和如何从其基础上构建一个应用程序。
+在我的[这系列的第一篇文章][1] 中, 我已经讲解如何使用 Python 创建一个简单的、基于文本的骰子游戏。这次,我将展示如何使用 Python 模块 Pygame 来创建一个图形化游戏。它将需要几篇文章才能来得到一个确实做成一些东西的游戏,但是到这系列的结尾,你将更好地理解如何查找和学习新的 Python 模块和如何从其基础上构建一个应用程序。
在开始前,你必须安装 [Pygame][2]。
### 安装新的 Python 模块
-这里有一些方法来安装 Python 模块,但是最通用的两个是:
+有几种方法来安装 Python 模块,但是最通用的两个是:
* 从你的发行版的软件存储库
- * 使用 Python 的软件包管理器,pip
+ * 使用 Python 的软件包管理器 `pip`
-两个方法都工作很好,并且每一个都有它自己的一套优势。如果你是在 Linux 或 BSD 上开发,促使你的发行版的软件存储库确保自动及时更新。
+两个方法都工作的很好,并且每一个都有它自己的一套优势。如果你是在 Linux 或 BSD 上开发,可以利用你的发行版的软件存储库来自动和及时地更新。
-然而,使用 Python 的内置软件包管理器给予你控制更新模块时间的能力。而且,它不是明确指定操作系统的,意味着,即使当你不是在你常用的开发机器上时,你也可以使用它。pip 的其它的优势是允许模块局部安装,如果你没有一台正在使用的计算机的权限,它是有用的。
+然而,使用 Python 的内置软件包管理器可以给予你控制更新模块时间的能力。而且,它不是特定于操作系统的,这意味着,即使当你不是在你常用的开发机器上时,你也可以使用它。`pip` 的其它的优势是允许本地安装模块,如果你没有正在使用的计算机的管理权限,这是有用的。
### 使用 pip
-如果 Python 和 Python3 都安装在你的系统上,你想使用的命令很可能是 `pip3`,它区分来自Python 2.x 的 `pip` 的命令。如果你不确定,先尝试 `pip3`。
+如果 Python 和 Python3 都安装在你的系统上,你想使用的命令很可能是 `pip3`,它用来区分 Python 2.x 的 `pip` 的命令。如果你不确定,先尝试 `pip3`。
-`pip` 命令有些像大多数 Linux 软件包管理器的工作。你可以使用 `search` 搜索 Pythin 模块,然后使用 `install` 安装它们。如果你没有你正在使用的计算机的权限来安装软件,你可以使用 `--user` 选项来仅仅安装模块到你的 home 目录。
+`pip` 命令有些像大多数 Linux 软件包管理器一样工作。你可以使用 `search` 搜索 Python 模块,然后使用 `install` 安装它们。如果你没有你正在使用的计算机的管理权限来安装软件,你可以使用 `--user` 选项来仅仅安装模块到你的家目录。
```
$ pip3 search pygame
@@ -44,11 +46,11 @@ pygame_cffi (0.2.1) - A cffi-based SDL wrapper that copies the
$ pip3 install Pygame --user
```
-Pygame 是一个 Python 模块,这意味着它仅仅是一套可以被使用在你的 Python 程序中库。换句话说,它不是一个你启动的程序,像 [IDLE][3] 或 [Ninja-IDE][4] 一样。
+Pygame 是一个 Python 模块,这意味着它仅仅是一套可以使用在你的 Python 程序中的库。换句话说,它不是一个像 [IDLE][3] 或 [Ninja-IDE][4] 一样可以让你启动的程序。
### Pygame 新手入门
-一个电子游戏需要一个故事背景;一个发生的地点。在 Python 中,有两种不同的方法来创建你的故事背景:
+一个电子游戏需要一个背景设定:故事发生的地点。在 Python 中,有两种不同的方法来创建你的故事背景:
* 设置一种背景颜色
* 设置一张背景图片
@@ -57,15 +59,15 @@ Pygame 是一个 Python 模块,这意味着它仅仅是一套可以被使用
### 设置你的 Pygame 脚本
-为了开始一个新的 Pygame 脚本,在计算机上创建一个文件夹。游戏的全部文件被放在这个目录中。在工程文件夹内部保持所需要的所有的文件来运行游戏是极其重要的。
+要开始一个新的 Pygame 工程,先在计算机上创建一个文件夹。游戏的全部文件被放在这个目录中。在你的工程文件夹内部保持所需要的所有的文件来运行游戏是极其重要的。
-一个 Python 脚本以文件类型,你的姓名,和你想使用的协议开始。使用一个开放源码协议,以便你的朋友可以改善你的游戏并与你一起分享他们的更改:
+一个 Python 脚本以文件类型、你的姓名,和你想使用的许可证开始。使用一个开放源码许可证,以便你的朋友可以改善你的游戏并与你一起分享他们的更改:
```
#!/usr/bin/env python3
-# Seth Kenlon 编写
+# by Seth Kenlon
## GPLv3
# This program is free software: you can redistribute it and/or
@@ -75,14 +77,14 @@ Pygame 是一个 Python 模块,这意味着它仅仅是一套可以被使用
#
# This program is distributed in the hope that it will be useful, but
# WITHOUT ANY WARRANTY; without even the implied warranty of
-# MERCHANTABILITY or FITNESS FOR A PARTICULAR PURPOSE. See the GNU
+# MERCHANTABILITY or FITNESS FOR A PARTICULAR PURPOSE. See the GNU
# General Public License for more details.
#
# You should have received a copy of the GNU General Public License
-# along with this program. If not, see .
+# along with this program. If not, see .
```
-然后,你告诉 Python 你想使用的模块。一些模块是常见的 Python 库,当然,你想包括一个你刚刚安装的,Pygame 。
+然后,你告诉 Python 你想使用的模块。一些模块是常见的 Python 库,当然,你想包括一个你刚刚安装的 Pygame 模块。
```
import pygame # 加载 pygame 关键字
@@ -90,7 +92,7 @@ import sys # 让 python 使用你的文件系统
import os # 帮助 python 识别你的操作系统
```
-由于你将用这个脚本文件工作很多,在文件中制作成段落是有帮助的,以便你知道在哪里放原料。使用语句块注释来做这些,这些注释仅在看你的源文件代码时是可见的。在你的代码中创建三个语句块。
+由于你将用这个脚本文件做很多工作,在文件中分成段落是有帮助的,以便你知道在哪里放代码。你可以使用块注释来做这些,这些注释仅在看你的源文件代码时是可见的。在你的代码中创建三个块。
```
'''
@@ -114,7 +116,7 @@ Main Loop
接下来,为你的游戏设置窗口大小。注意,不是每一个人都有大计算机屏幕,所以,最好使用一个适合大多数人的计算机的屏幕大小。
-这里有一个方法来切换全屏模式,很多现代电子游戏做的方法,但是,由于你刚刚开始,保存它简单和仅设置一个大小。
+这里有一个方法来切换全屏模式,很多现代电子游戏都会这样做,但是,由于你刚刚开始,简单起见仅设置一个大小即可。
```
'''
@@ -124,7 +126,7 @@ worldx = 960
worldy = 720
```
-在一个脚本中使用 Pygame 引擎前,你需要一些基本的设置。你必需设置帧频,启动它的内部时钟,然后开始 (`init`) Pygame 。
+在脚本中使用 Pygame 引擎前,你需要一些基本的设置。你必须设置帧频,启动它的内部时钟,然后开始 (`init`)Pygame 。
```
fps = 40 # 帧频
@@ -137,17 +139,15 @@ pygame.init()
### 设置背景
-在你继续前,打开一个图形应用程序,并为你的游戏世界创建一个背景。在你的工程目录中的 `images` 文件夹内部保存它为 `stage.png` 。
+在你继续前,打开一个图形应用程序,为你的游戏世界创建一个背景。在你的工程目录中的 `images` 文件夹内部保存它为 `stage.png` 。
这里有一些你可以使用的自由图形应用程序。
- * [Krita][5] 是一个专业级绘图原料模拟器,它可以被用于创建漂亮的图片。如果你对电子游戏创建艺术作品非常感兴趣,你甚至可以购买一系列的[游戏艺术作品教程][6].
- * [Pinta][7] 是一个基本的,易于学习的绘图应用程序。
- * [Inkscape][8] 是一个矢量图形应用程序。使用它来绘制形状,线,样条曲线,和 Bézier 曲线。
+* [Krita][5] 是一个专业级绘图素材模拟器,它可以被用于创建漂亮的图片。如果你对创建电子游戏艺术作品非常感兴趣,你甚至可以购买一系列的[游戏艺术作品教程][6]。
+* [Pinta][7] 是一个基本的,易于学习的绘图应用程序。
+* [Inkscape][8] 是一个矢量图形应用程序。使用它来绘制形状、线、样条曲线和贝塞尔曲线。
-
-
-你的图像不必很复杂,你可以以后回去更改它。一旦你有它,在你文件的 setup 部分添加这些代码:
+你的图像不必很复杂,你可以以后回去更改它。一旦有了它,在你文件的 Setup 部分添加这些代码:
```
world = pygame.display.set_mode([worldx,worldy])
@@ -155,13 +155,13 @@ backdrop = pygame.image.load(os.path.join('images','stage.png').convert())
backdropbox = world.get_rect()
```
-如果你仅仅用一种颜色来填充你的游戏的背景,你需要做的全部是:
+如果你仅仅用一种颜色来填充你的游戏的背景,你需要做的就是:
```
world = pygame.display.set_mode([worldx,worldy])
```
-你也必需定义一个来使用的颜色。在你的 setup 部分,使用红,绿,蓝 (RGB) 的值来创建一些颜色的定义。
+你也必须定义颜色以使用。在你的 Setup 部分,使用红、绿、蓝 (RGB) 的值来创建一些颜色的定义。
```
'''
@@ -173,13 +173,13 @@ BLACK = (23,23,23 )
WHITE = (254,254,254)
```
-在这点上,你能理论上启动你的游戏。问题是,它可能仅持续一毫秒。
+至此,你理论上可以启动你的游戏了。问题是,它可能仅持续了一毫秒。
-为证明这一点,保存你的文件为 `your-name_game.py` (用你真实的名称替换 `your-name` )。然后启动你的游戏。
+为证明这一点,保存你的文件为 `your-name_game.py`(用你真实的名称替换 `your-name`)。然后启动你的游戏。
-如果你正在使用 IDLE ,通过选择来自 Run 菜单的 `Run Module` 来运行你的游戏。
+如果你正在使用 IDLE,通过选择来自 “Run” 菜单的 “Run Module” 来运行你的游戏。
-如果你正在使用 Ninja ,在左侧按钮条中单击 `Run file` 按钮。
+如果你正在使用 Ninja,在左侧按钮条中单击 “Run file” 按钮。
@@ -189,27 +189,27 @@ WHITE = (254,254,254)
$ python3 ./your-name_game.py
```
-如果你正在使用 Windows ,使用这命令:
+如果你正在使用 Windows,使用这命令:
```
py.exe your-name_game.py
```
-你启动它,不过不要期望很多,因为你的游戏现在仅仅持续几毫秒。你可以在下一部分中修复它。
+启动它,不过不要期望很多,因为你的游戏现在仅仅持续几毫秒。你可以在下一部分中修复它。
### 循环
-除非另有说明,一个 Python 脚本运行一次并仅一次。近来计算机的运行速度是非常快的,所以你的 Python 脚本运行时间少于1秒钟。
+除非另有说明,一个 Python 脚本运行一次并仅一次。近来计算机的运行速度是非常快的,所以你的 Python 脚本运行时间会少于 1 秒钟。
为强制你的游戏来处于足够长的打开和活跃状态来让人看到它(更不要说玩它),使用一个 `while` 循环。为使你的游戏保存打开,你可以设置一个变量为一些值,然后告诉一个 `while` 循环只要变量保持未更改则一直保存循环。
-这经常被称为一个"主循环",你可以使用术语 `main` 作为你的变量。在你的 setup 部分的任意位置添加这些代码:
+这经常被称为一个“主循环”,你可以使用术语 `main` 作为你的变量。在你的 Setup 部分的任意位置添加代码:
```
main = True
```
-在主循环期间,使用 Pygame 关键字来检查是否在键盘上的按键已经被按下或释放。添加这些代码到你的主循环部分:
+在主循环期间,使用 Pygame 关键字来检查键盘上的按键是否已经被按下或释放。添加这些代码到你的主循环部分:
```
'''
@@ -228,7 +228,7 @@ while main == True:
main = False
```
-也在你的循环中,刷新你世界的背景。
+也是在你的循环中,刷新你世界的背景。
如果你使用一个图片作为背景:
@@ -242,33 +242,33 @@ world.blit(backdrop, backdropbox)
world.fill(BLUE)
```
-最后,告诉 Pygame 来刷新在屏幕上的所有内容并推进游戏的内部时钟。
+最后,告诉 Pygame 来重新刷新屏幕上的所有内容,并推进游戏的内部时钟。
```
pygame.display.flip()
clock.tick(fps)
```
-保存你的文件,再次运行它来查看曾经创建的最无趣的游戏。
+保存你的文件,再次运行它来查看你曾经创建的最无趣的游戏。
退出游戏,在你的键盘上按 `q` 键。
-在这系列的 [下一篇文章][9] 中,我将向你演示,如何加强你当前空的游戏世界,所以,继续学习并创建一些将要使用的图形!
+在这系列的 [下一篇文章][9] 中,我将向你演示,如何加强你当前空空如也的游戏世界,所以,继续学习并创建一些将要使用的图形!
--------------------------------------------------------------------------------
-通过: https://opensource.com/article/17/12/game-framework-python
+via: https://opensource.com/article/17/12/game-framework-python
作者:[Seth Kenlon][a]
选题:[lujun9972][b]
译者:[robsean](https://github.com/robsean)
-校对:[校对者ID](https://github.com/校对者ID)
+校对:[wxy](https://github.com/wxy)
本文由 [LCTT](https://github.com/LCTT/TranslateProject) 原创编译,[Linux中国](https://linux.cn/) 荣誉推出
[a]: https://opensource.com/users/seth
[b]: https://github.com/lujun9972
-[1]: https://opensource.com/article/17/10/python-101
+[1]: https://linux.cn/article-9071-1.html
[2]: http://www.pygame.org/wiki/about
[3]: https://en.wikipedia.org/wiki/IDLE
[4]: http://ninja-ide.org/
diff --git a/published/201905/20171215 How to add a player to your Python game.md b/published/201905/20171215 How to add a player to your Python game.md
new file mode 100644
index 0000000000..b313a8219e
--- /dev/null
+++ b/published/201905/20171215 How to add a player to your Python game.md
@@ -0,0 +1,163 @@
+[#]: collector: (lujun9972)
+[#]: translator: (cycoe)
+[#]: reviewer: (wxy)
+[#]: publisher: (wxy)
+[#]: url: (https://linux.cn/article-10858-1.html)
+[#]: subject: (How to add a player to your Python game)
+[#]: via: (https://opensource.com/article/17/12/game-python-add-a-player)
+[#]: author: (Seth Kenlon https://opensource.com/users/seth)
+
+如何在你的 Python 游戏中添加一个玩家
+======
+> 这是用 Python 从头开始构建游戏的系列文章的第三部分。
+
+
+
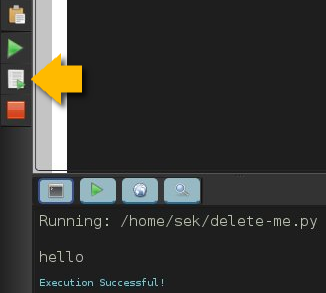
+在 [这个系列的第一篇文章][1] 中,我解释了如何使用 Python 创建一个简单的基于文本的骰子游戏。在第二部分中,我向你们展示了如何从头开始构建游戏,即从 [创建游戏的环境][2] 开始。但是每个游戏都需要一名玩家,并且每个玩家都需要一个可操控的角色,这也就是我们接下来要在这个系列的第三部分中需要做的。
+
+在 Pygame 中,玩家操控的图标或者化身被称作妖精。如果你现在还没有任何可用于玩家妖精的图像,你可以使用 [Krita][3] 或 [Inkscape][4] 来自己创建一些图像。如果你对自己的艺术细胞缺乏自信,你也可以在 [OpenClipArt.org][5] 或 [OpenGameArt.org][6] 搜索一些现成的图像。如果你还未按照上一篇文章所说的单独创建一个 `images` 文件夹,那么你需要在你的 Python 项目目录中创建它。将你想要在游戏中使用的图片都放 `images` 文件夹中。
+
+为了使你的游戏真正的刺激,你应该为你的英雄使用一张动态的妖精图片。这意味着你需要绘制更多的素材,并且它们要大不相同。最常见的动画就是走路循环,通过一系列的图像让你的妖精看起来像是在走路。走路循环最快捷粗糙的版本需要四张图像。
+
+
+
+注意:这篇文章中的代码示例同时兼容静止的和动态的玩家妖精。
+
+将你的玩家妖精命名为 `hero.png`。如果你正在创建一个动态的妖精,则需要在名字后面加上一个数字,从 `hero1.png` 开始。
+
+### 创建一个 Python 类
+
+在 Python 中,当你在创建一个你想要显示在屏幕上的对象时,你需要创建一个类。
+
+在你的 Python 脚本靠近顶端的位置,加入如下代码来创建一个玩家。在以下的代码示例中,前三行已经在你正在处理的 Python 脚本中:
+
+```
+import pygame
+import sys
+import os # 以下是新代码
+
+class Player(pygame.sprite.Sprite):
+ '''
+ 生成一个玩家
+ '''
+ def __init__(self):
+ pygame.sprite.Sprite.__init__(self)
+ self.images = []
+ img = pygame.image.load(os.path.join('images','hero.png')).convert()
+ self.images.append(img)
+ self.image = self.images[0]
+ self.rect = self.image.get_rect()
+```
+
+如果你的可操控角色拥有一个走路循环,在 `images` 文件夹中将对应图片保存为 `hero1.png` 到 `hero4.png` 的独立文件。
+
+使用一个循环来告诉 Python 遍历每个文件。
+
+```
+'''
+对象
+'''
+
+class Player(pygame.sprite.Sprite):
+ '''
+ 生成一个玩家
+ '''
+ def __init__(self):
+ pygame.sprite.Sprite.__init__(self)
+ self.images = []
+ for i in range(1,5):
+ img = pygame.image.load(os.path.join('images','hero' + str(i) + '.png')).convert()
+ self.images.append(img)
+ self.image = self.images[0]
+ self.rect = self.image.get_rect()
+```
+
+### 将玩家带入游戏世界
+
+现在已经创建好了一个 Player 类,你需要使用它在你的游戏世界中生成一个玩家妖精。如果你不调用 Player 类,那它永远不会起作用,(游戏世界中)也就不会有玩家。你可以通过立马运行你的游戏来验证一下。游戏会像上一篇文章末尾看到的那样运行,并得到明确的结果:一个空荡荡的游戏世界。
+
+为了将一个玩家妖精带到你的游戏世界,你必须通过调用 Player 类来生成一个妖精,并将它加入到 Pygame 的妖精组中。在如下的代码示例中,前三行是已经存在的代码,你需要在其后添加代码:
+
+```
+world = pygame.display.set_mode([worldx,worldy])
+backdrop = pygame.image.load(os.path.join('images','stage.png')).convert()
+backdropbox = screen.get_rect()
+
+# 以下是新代码
+
+player = Player() # 生成玩家
+player.rect.x = 0 # 移动 x 坐标
+player.rect.y = 0 # 移动 y 坐标
+player_list = pygame.sprite.Group()
+player_list.add(player)
+```
+
+尝试启动你的游戏来看看发生了什么。高能预警:它不会像你预期的那样工作,当你启动你的项目,玩家妖精没有出现。事实上它生成了,只不过只出现了一毫秒。你要如何修复一个只出现了一毫秒的东西呢?你可能回想起上一篇文章中,你需要在主循环中添加一些东西。为了使玩家的存在时间超过一毫秒,你需要告诉 Python 在每次循环中都绘制一次。
+
+将你的循环底部的语句更改如下:
+
+```
+ world.blit(backdrop, backdropbox)
+ player_list.draw(screen) # 绘制玩家
+ pygame.display.flip()
+ clock.tick(fps)
+```
+
+现在启动你的游戏,你的玩家出现了!
+
+### 设置 alpha 通道
+
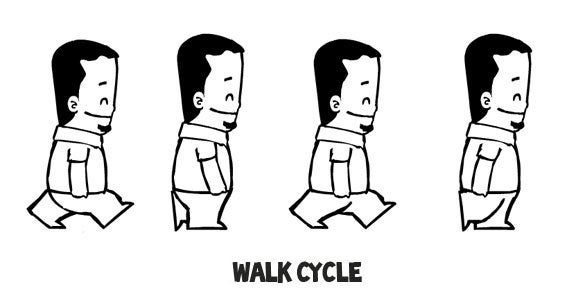
+根据你如何创建你的玩家妖精,在它周围可能会有一个色块。你所看到的是 alpha 通道应该占据的空间。它本来是不可见的“颜色”,但 Python 现在还不知道要使它不可见。那么你所看到的,是围绕在妖精周围的边界区(或现代游戏术语中的“命中区”)内的空间。
+
+
+
+你可以通过设置一个 alpha 通道和 RGB 值来告诉 Python 使哪种颜色不可见。如果你不知道你使用 alpha 通道的图像的 RGB 值,你可以使用 Krita 或 Inkscape 打开它,并使用一种独特的颜色,比如 `#00ff00`(差不多是“绿屏绿”)来填充图像周围的空白区域。记下颜色对应的十六进制值(此处为 `#00ff00`,绿屏绿)并将其作为 alpha 通道用于你的 Python 脚本。
+
+使用 alpha 通道需要在你的妖精生成相关代码中添加如下两行。类似第一行的代码已经存在于你的脚本中,你只需要添加另外两行:
+
+```
+ img = pygame.image.load(os.path.join('images','hero' + str(i) + '.png')).convert()
+ img.convert_alpha() # 优化 alpha
+ img.set_colorkey(ALPHA) # 设置 alpha
+```
+
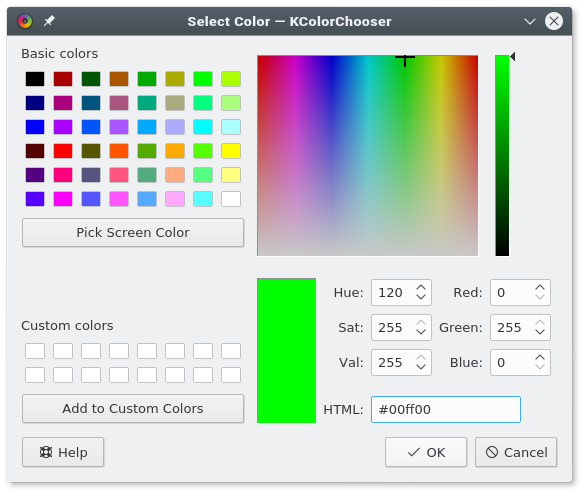
+除非你告诉它,否则 Python 不知道将哪种颜色作为 alpha 通道。在你代码的设置相关区域,添加一些颜色定义。将如下的变量定义添加于你的设置相关区域的任意位置:
+
+```
+ALPHA = (0, 255, 0)
+```
+
+在以上示例代码中,`0,255,0` 被我们使用,它在 RGB 中所代表的值与 `#00ff00` 在十六进制中所代表的值相同。你可以通过一个优秀的图像应用程序,如 [GIMP][7]、Krita 或 Inkscape,来获取所有这些颜色值。或者,你可以使用一个优秀的系统级颜色选择器,如 [KColorChooser][8],来检测颜色。
+
+
+
+如果你的图像应用程序将你的妖精背景渲染成了其他的值,你可以按需调整 `ALPHA` 变量的值。不论你将 alpha 设为多少,最后它都将“不可见”。RGB 颜色值是非常严格的,因此如果你需要将 alpha 设为 000,但你又想将 000 用于你图像中的黑线,你只需要将图像中线的颜色设为 111。这样一来,(图像中的黑线)就足够接近黑色,但除了电脑以外没有人能看出区别。
+
+运行你的游戏查看结果。
+
+
+
+在 [这个系列的第四篇文章][9] 中,我会向你们展示如何使你的妖精动起来。多么的激动人心啊!
+
+--------------------------------------------------------------------------------
+
+via: https://opensource.com/article/17/12/game-python-add-a-player
+
+作者:[Seth Kenlon][a]
+选题:[lujun9972][b]
+译者:[cycoe](https://github.com/cycoe)
+校对:[wxy](https://github.com/wxy)
+
+本文由 [LCTT](https://github.com/LCTT/TranslateProject) 原创编译,[Linux中国](https://linux.cn/) 荣誉推出
+
+[a]: https://opensource.com/users/seth
+[b]: https://github.com/lujun9972
+[1]: https://linux.cn/article-9071-1.html
+[2]: https://linux.cn/article-10850-1.html
+[3]: http://krita.org
+[4]: http://inkscape.org
+[5]: http://openclipart.org
+[6]: https://opengameart.org/
+[7]: http://gimp.org
+[8]: https://github.com/KDE/kcolorchooser
+[9]: https://opensource.com/article/17/12/program-game-python-part-4-moving-your-sprite
diff --git a/published/201905/20180130 An introduction to the DomTerm terminal emulator for Linux.md b/published/201905/20180130 An introduction to the DomTerm terminal emulator for Linux.md
new file mode 100644
index 0000000000..13652f26ef
--- /dev/null
+++ b/published/201905/20180130 An introduction to the DomTerm terminal emulator for Linux.md
@@ -0,0 +1,130 @@
+DomTerm:一款为 Linux 打造的终端模拟器
+======
+> 了解一下 DomTerm,这是一款终端模拟器和复用器,带有 HTML 图形和其它不多见的功能。
+
+
+
+[DomTerm][1] 是一款现代化的终端模拟器,它使用浏览器引擎作为 “GUI 工具包”。这就支持了一些相关的特性,例如可嵌入图像和链接、HTML 富文本以及可折叠(显示/隐藏)命令。除此以外,它看起来感觉就像一个功能完整、独立的终端模拟器,有着出色 xterm 兼容性(包括鼠标处理和 24 位色)和恰当的 “装饰” (菜单)。另外它内置支持了会话管理和副窗口(如同 `tmux` 和 `GNU Screen` 中一样)、基本输入编辑(如在 `readline` 中)以及分页(如在 `less` 中)。
+
+
+
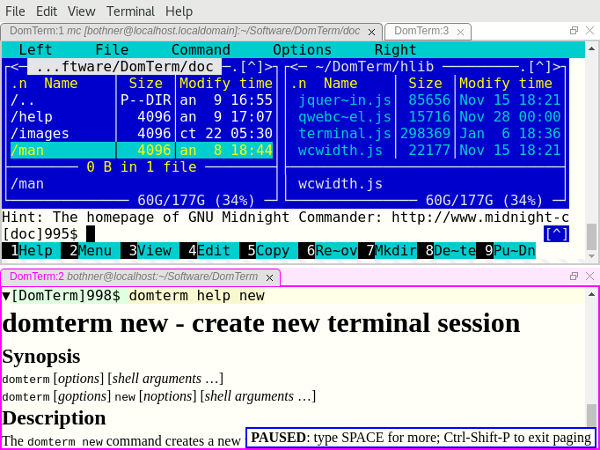
+*图 1: DomTerminal 终端模拟器。*
+
+在以下部分我们将看一看这些特性。我们将假设你已经安装好了 `domterm` (如果你需要获取并构建 Dormterm 请跳到本文最后)。开始之前先让我们概览一下这项技术。
+
+### 前端 vs. 后端
+
+DomTerm 大部分是用 JavaScript 写的,它运行在一个浏览器引擎中。它可以是像例如 Chrome 或者 Firefox 一样的桌面浏览器(见图 3),也可以是一个内嵌的浏览器。使用一个通用的网页浏览器没有问题,但是用户体验却不够好(因为菜单是为通用的网页浏览而不是为了终端模拟器所打造),并且其安全模型也会妨碍使用。因此使用内嵌的浏览器更好一些。
+
+目前以下这些是支持的:
+
+ * qdomterm,使用了 Qt 工具包 和 QtWebEngine
+ * 一个内嵌的 [Electron][2](见图 1)
+ * atom-domterm 以 [Atom 文本编辑器][3](同样基于 Electron)包的形式运行 DomTerm,并和 Atom 面板系统集成在一起(见图 2)
+ * 一个为 JavaFX 的 WebEngine 包装器,这对 Java 编程十分有用(见图 4)
+ * 之前前端使用 [Firefox-XUL][4] 作为首选,但是 Mozilla 已经终止了 XUL
+
+![在 Atom 编辑器中的 DomTerm 终端面板][6]
+
+*图 2:在 Atom 编辑器中的 DomTerm 终端面板。*
+
+目前,Electron 前端可能是最佳选择,紧随其后的是 Qt 前端。如果你使用 Atom,atom-domterm 也工作得相当不错。
+
+后端服务器是用 C 写的。它管理着伪终端(PTY)和会话。它同样也是一个为前端提供 Javascript 和其它文件的 HTTP 服务器。`domterm` 命令启动终端任务和执行其它请求。如果没有服务器在运行,domterm 就会自己来服务。后端与服务器之间的通讯通常是用 WebSockets(在服务器端是[libwebsockets][8])完成的。然而,JavaFX 的嵌入既不用 Websockets 也不用 DomTerm 服务器。相反 Java 应用直接通过 Java-Javascript 桥接进行通讯。
+
+### 一个稳健的可兼容 xterm 的终端模拟器
+
+DomTerm 看上去感觉像一个现代的终端模拟器。它处理鼠标事件、24 位色、Unicode、倍宽字符(CJK)以及输入方式。DomTerm 在 [vttest 测试套件][9] 上工作地十分出色。
+
+其不同寻常的特性包括:
+
+**展示/隐藏按钮(“折叠”):** 小三角(如上图 2)是隐藏/展示相应输出的按钮。仅需在[提示符][11]中添加特定的[转义字符][10]就可以创建按钮。
+
+**对于 readline 和类似输入编辑器的鼠标点击支持:** 如果你点击输入区域(黄色),DomTerm 会向应用发送正确的方向键按键序列。(可以通过提示符中的转义字符启用这一特性,你也可以通过 `Alt+点击` 强制使用。)
+
+**用 CSS 样式化终端:** 这通常是在 `~/.domterm/settings.ini` 里完成的,保存时会自动重载。例如在图 2 中,设置了终端专用的背景色。
+
+### 一个更好的 REPL 控制台
+
+一个经典的终端模拟器基于长方形的字符单元格工作的。这在 REPL(命令行)上没问题,但是并不理想。这里有些通常在终端模拟器中不常见的 REPL 很有用的 DomTerm 特性:
+
+**一个能“打印”图片、图形、数学公式或者一组可点击的链接的命令:** 应用可以发送包含几乎任何 HTML 的转义字符。(HTML 会被剔除部分,以移除 JavaScript 和其它危险特性。)
+
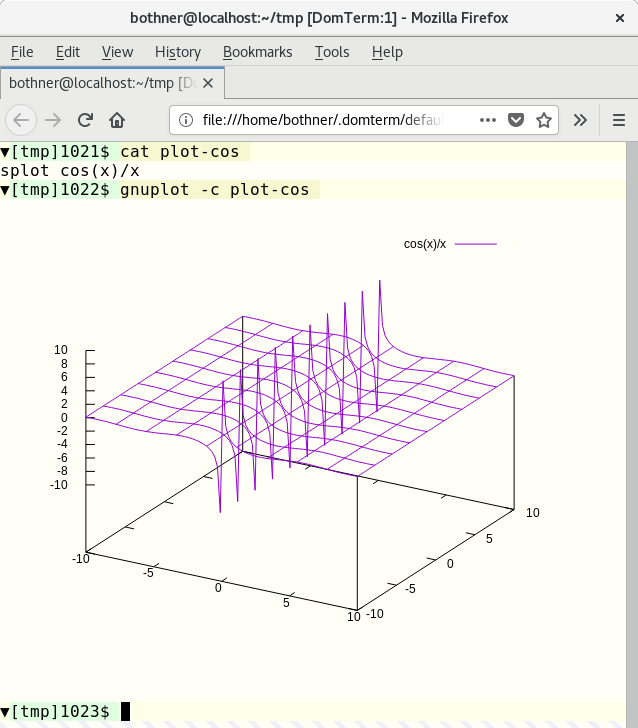
+图 3 显示了来自 [gnuplot][12] 会话的一个片段。Gnuplot(2.1 或者跟高版本)支持 DormTerm 作为终端类型。图形输出被转换成 [SVG 图片][13],然后被打印到终端。我的博客帖子[在 DormTerm 上的 Gnuplot 展示][14]在这方面提供了更多信息。
+
+
+
+*图 3:Gnuplot 截图。*
+
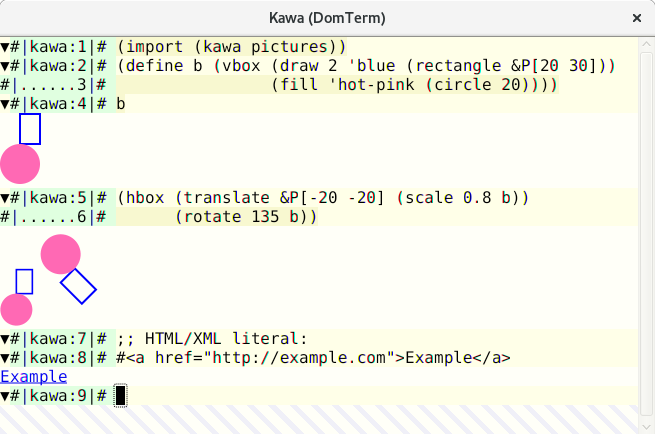
+[Kawa][15] 语言有一个创建并转换[几何图像值][16]的库。如果你将这样的图片值打印到 DomTerm 终端,图片就会被转换成 SVG 形式并嵌入进输出中。
+
+
+
+*图 4:Kawa 中可计算的几何形状。*
+
+**富文本输出:** 有着 HTML 样式的帮助信息更加便于阅读,看上去也更漂亮。图片 1 的下面面板展示 `dormterm help` 的输出。(如果没在 DomTerm 下运行的话输出的是普通文本。)注意自带的分页器中的 `PAUSED` 消息。
+
+**包括可点击链接的错误消息:** DomTerm 可以识别语法 `filename:line:column` 并将其转化成一个能在可定制文本编辑器中打开文件并定位到行的链接。(这适用于相对路径的文件名,如果你用 `PROMPT_COMMAND` 或类似的跟踪目录。)
+
+编译器可以侦测到它在 DomTerm 下运行,并直接用转义字符发出文件链接。这比依赖 DomTerm 的样式匹配要稳健得多,因为它可以处理空格和其他字符并且无需依赖目录追踪。在图 4 中,你可以看到来自 [Kawa Compiler][15] 的错误消息。悬停在文件位置上会使其出现下划线,`file:` URL 出现在 `atom-domterm` 消息栏(窗口底部)中。(当不用 atom-domterm 时,这样的消息会在一个浮层的框中显示,如图 1 中所看到的 `PAUSED` 消息所示。)
+
+点击链接时的动作是可以配置的。默认对于带有 `#position` 后缀的 `file:` 链接的动作是在文本编辑器中打开那个文件。
+
+**结构化内部表示:**以下内容均以内部节点结构表示:命令、提示符、输入行、正常和错误输出、标签,如果“另存为 HTML”,则保留结构。HTML 文件与 XML 兼容,因此你可以使用 XML 工具搜索或转换输出。命令 `domterm view-saved` 会以一种启用命令折叠(显示/隐藏按钮处于活动状态)和重新调整窗口大小的方式打开保存的 HTML 文件。
+
+**内建的 Lisp 样式优美打印:** 你可以在输出中包括优美打印指令(比如,grouping),这样断行会根据窗口大小调整而重新计算。查看我的文章 [DomTerm 中的动态优美打印][17]以更深入探讨。
+
+**基本的内建行编辑**,带着历史记录(像 GNU readline 一样): 这使用浏览器自带的编辑器,因此它有着优秀的鼠标和选择处理机制。你可以在正常字符模式(大多数输入的字符被指接送向进程);或者行模式(通常的字符是直接插入的,而控制字符导致编辑操作,回车键会向进程发送被编辑行)之间转换。默认的是自动模式,根据 PTY 是在原始模式还是终端模式中,DomTerm 在字符模式与行模式间转换。
+
+**自带的分页器**(类似简化版的 `less`):键盘快捷键控制滚动。在“页模式”中,输出在每个新的屏幕(或者单独的行,如果你想一行行地向前移)后暂停;页模式对于用户输入简单智能,因此(如果你想的话)你无需阻碍交互式程序就可以运行它。
+
+### 多路复用和会话
+
+**标签和平铺:** 你不仅可以创建多个终端标签,也可以平铺它们。你可以要么使用鼠标或键盘快捷键来创建或者切换面板和标签。它们可以用鼠标重新排列并调整大小。这是通过 [GoldenLayout][18] JavaScript 库实现的。图 1 展示了一个有着两个面板的窗口。上面的有两个标签,一个运行 [Midnight Commander][20];底下的面板以 HTML 形式展示了 `dormterm help` 输出。然而相反在 Atom 中我们使用其自带的可拖拽的面板和标签。你可以在图 2 中看到这个。
+
+**分离或重接会话:** 与 `tmux` 和 GNU `screen` 类似,DomTerm 支持会话安排。你甚至可以给同样的会话接上多个窗口或面板。这支持多用户会话分享和远程链接。(为了安全,同一个服务器的所有会话都需要能够读取 Unix 域接口和一个包含随机密钥的本地文件。当我们有了良好、安全的远程链接,这个限制将会有所放松。)
+
+**domterm 命令** 类似与 `tmux` 和 GNU `screen`,它有多个选项可以用于控制或者打开单个或多个会话的服务器。主要的差别在于,如果它没在 DomTerm 下运行,`dormterm` 命令会创建一个新的顶层窗口,而不是在现有的终端中运行。
+
+与 `tmux` 和 `git` 类似,`dormterm` 命令有许多子命令。一些子命令创建窗口或者会话。另一些(例如“打印”一张图片)仅在现有的 DormTerm 会话下起作用。
+
+命令 `domterm browse` 打开一个窗口或者面板以浏览一个指定的 URL,例如浏览文档的时候。
+
+### 获取并安装 DomTerm
+
+DomTerm 可以从其 [Github 仓库][21]获取。目前没有提前构建好的包,但是有[详细指导][22]。所有的前提条件在 Fedora 27 上都有,这使得其特别容易被搭建。
+
+--------------------------------------------------------------------------------
+
+via: https://opensource.com/article/18/1/introduction-domterm-terminal-emulator
+
+作者:[Per Bothner][a]
+译者:[tomjlw](https://github.com/tomjlw)
+校对:[wxy](https://github.com/wxy)
+
+本文由 [LCTT](https://github.com/LCTT/TranslateProject) 原创编译,[Linux中国](https://linux.cn/) 荣誉推出
+
+[a]:https://opensource.com/users/perbothner
+[1]:http://domterm.org/
+[2]:https://electronjs.org/
+[3]:https://atom.io/
+[4]:https://en.wikipedia.org/wiki/XUL
+[5]:/file/385346
+[6]:https://opensource.com/sites/default/files/images/dt-atom1.png (DomTerm terminal panes in Atom editor)
+[7]:https://opensource.com/sites/default/files/images/dt-atom1.png
+[8]:https://libwebsockets.org/
+[9]:http://invisible-island.net/vttest/
+[10]:http://domterm.org/Wire-byte-protocol.html
+[11]:http://domterm.org/Shell-prompts.html
+[12]:http://www.gnuplot.info/
+[13]:https://developer.mozilla.org/en-US/docs/Web/SVG
+[14]:http://per.bothner.com/blog/2016/gnuplot-in-domterm/
+[15]:https://www.gnu.org/software/kawa/
+[16]:https://www.gnu.org/software/kawa/Composable-pictures.html
+[17]:http://per.bothner.com/blog/2017/dynamic-prettyprinting/
+[18]:https://golden-layout.com/
+[19]:https://opensource.com/sites/default/files/u128651/domterm1.png
+[20]:https://midnight-commander.org/
+[21]:https://github.com/PerBothner/DomTerm
+[22]:http://domterm.org/Downloading-and-building.html
+
diff --git a/published/201905/20180312 ddgr - A Command Line Tool To Search DuckDuckGo From The Terminal.md b/published/201905/20180312 ddgr - A Command Line Tool To Search DuckDuckGo From The Terminal.md
new file mode 100644
index 0000000000..3d8083d440
--- /dev/null
+++ b/published/201905/20180312 ddgr - A Command Line Tool To Search DuckDuckGo From The Terminal.md
@@ -0,0 +1,229 @@
+ddgr:一个从终端搜索 DuckDuckGo 的命令行工具
+======
+
+在 Linux 中,Bash 技巧非常棒,它使 Linux 中的一切成为可能。
+
+对于开发人员或系统管理员来说,它真的很管用,因为他们大部分时间都在使用终端。你知道他们为什么喜欢这种技巧吗?
+
+因为这些技巧可以提高他们的工作效率,也能使他们工作更快。
+
+### 什么是 ddgr
+
+[ddgr][1] 是一个命令行实用程序,用于从终端搜索 DuckDuckGo。如果设置了 `BROWSER` 环境变量,ddgr 可以在几个基于文本的浏览器中开箱即用。
+
+确保你的系统安装了任何一个基于文本的浏览器。你可能知道 [googler][2],它允许用户从 Linux 命令行进行 Google 搜索。
+
+它在命令行用户中非常受欢迎,他们期望对隐私敏感的 DuckDuckGo 也有类似的实用程序,这就是 `ddgr` 出现的原因。
+
+与 Web 界面不同,你可以指定每页要查看的搜索结果数。
+
+**建议阅读:**
+
+- [Googler – 从 Linux 命令行搜索 Google][2]
+- [Buku – Linux 中一个强大的命令行书签管理器][3]
+- [SoCLI – 从终端搜索和浏览 StackOverflow 的简单方法][4]
+- [RTV(Reddit 终端查看器)- 一个简单的 Reddit 终端查看器][5]
+
+### 什么是 DuckDuckGo
+
+DDG 即 DuckDuckGo。DuckDuckGo(DDG)是一个真正保护用户搜索和隐私的互联网搜索引擎。它没有过滤用户的个性化搜索结果,对于给定的搜索词,它会向所有用户显示相同的搜索结果。
+
+大多数用户更喜欢谷歌搜索引擎,但是如果你真的担心隐私,那么你可以放心地使用 DuckDuckGo。
+
+### ddgr 特性
+
+ * 快速且干净(没有广告、多余的 URL 或杂物参数),自定义颜色
+ * 旨在以最小的空间提供最高的可读性
+ * 指定每页显示的搜索结果数
+ * 可以在 omniprompt 中导航结果,在浏览器中打开 URL
+ * 用于 Bash、Zsh 和 Fish 的搜索和选项补完脚本
+ * 支持 DuckDuckGo Bang(带有自动补完)
+ * 直接在浏览器中打开第一个结果(如同 “I’m Feeling Ducky”)
+ * 不间断搜索:无需退出即可在 omniprompt 中触发新搜索
+ * 关键字支持(例如:filetype:mime、site:somesite.com)
+ * 按时间、指定区域搜索,禁用安全搜索
+ * 支持 HTTPS 代理,支持 Do Not Track,可选择禁用用户代理字符串
+ * 支持自定义 URL 处理程序脚本或命令行实用程序
+ * 全面的文档,man 页面有方便的使用示例
+ * 最小的依赖关系
+
+### 需要条件
+
+`ddgr` 需要 Python 3.4 或更高版本。因此,确保你的系统应具有 Python 3.4 或更高版本。
+
+```
+$ python3 --version
+Python 3.6.3
+```
+
+### 如何在 Linux 中安装 ddgr
+
+我们可以根据发行版使用以下命令轻松安装 `ddgr`。
+
+对于 Fedora ,使用 [DNF 命令][6]来安装 `ddgr`。
+
+```
+# dnf install ddgr
+```
+
+或者我们可以使用 [SNAP 命令][7]来安装 `ddgr`。
+
+```
+# snap install ddgr
+```
+
+对于 LinuxMint/Ubuntu,使用 [APT-GET 命令][8] 或 [APT 命令][9]来安装 `ddgr`。
+
+```
+$ sudo add-apt-repository ppa:twodopeshaggy/jarun
+$ sudo apt-get update
+$ sudo apt-get install ddgr
+```
+
+对于基于 Arch Linux 的系统,使用 [Yaourt 命令][10]或 [Packer 命令][11]从 AUR 仓库安装 `ddgr`。
+
+```
+$ yaourt -S ddgr
+或
+$ packer -S ddgr
+```
+
+对于 Debian,使用 [DPKG 命令][12] 安装 `ddgr`。
+
+```
+# wget https://github.com/jarun/ddgr/releases/download/v1.2/ddgr_1.2-1_debian9.amd64.deb
+# dpkg -i ddgr_1.2-1_debian9.amd64.deb
+```
+
+对于 CentOS 7,使用 [YUM 命令][13]来安装 `ddgr`。
+
+```
+# yum install https://github.com/jarun/ddgr/releases/download/v1.2/ddgr-1.2-1.el7.3.centos.x86_64.rpm
+```
+
+对于 opensuse,使用 [zypper 命令][14]来安装 `ddgr`。
+
+```
+# zypper install https://github.com/jarun/ddgr/releases/download/v1.2/ddgr-1.2-1.opensuse42.3.x86_64.rpm
+```
+
+### 如何启动 ddgr
+
+在终端上输入 `ddgr` 命令,不带任何选项来进行 DuckDuckGo 搜索。你将获得类似于下面的输出。
+
+```
+$ ddgr
+```
+
+![][16]
+
+### 如何使用 ddgr 进行搜索
+
+我们可以通过两种方式启动搜索。从 omniprompt 或者直接从终端开始。你可以搜索任何你想要的短语。
+
+直接从终端:
+
+```
+$ ddgr 2daygeek
+```
+
+![][17]
+
+从 omniprompt:
+
+![][18]
+
+### Omniprompt 快捷方式
+
+输入 `?` 以获得 omniprompt,它将显示关键字列表和进一步使用 `ddgr` 的快捷方式。
+
+![][19]
+
+### 如何移动下一页、上一页和第一页
+
+它允许用户移动下一页、上一页或第一页。
+
+ * `n`: 移动到下一组搜索结果
+ * `p`: 移动到上一组搜索结果
+ * `f`: 跳转到第一页
+
+![][20]
+
+### 如何启动新搜索
+
+`d` 选项允许用户从 omniprompt 发起新的搜索。例如,我搜索了 “2daygeek website”,现在我将搜索 “Magesh Maruthamuthu” 这个新短语。
+
+从 omniprompt:
+
+```
+ddgr (? for help) d magesh maruthmuthu
+```
+
+![][21]
+
+### 在搜索结果中显示完整的 URL
+
+默认情况下,它仅显示文章标题,在搜索中添加 `x` 选项以在搜索结果中显示完整的文章网址。
+
+```
+$ ddgr -n 5 -x 2daygeek
+```
+
+![][22]
+
+### 限制搜索结果
+
+默认情况下,搜索结果每页显示 10 个结果。如果你想为方便起见限制页面结果,可以使用 `ddgr` 带有 `--num` 或 ` -n` 参数。
+
+```
+$ ddgr -n 5 2daygeek
+```
+
+![][23]
+
+### 网站特定搜索
+
+要搜索特定网站的特定页面,使用以下格式。这将从网站获取给定关键字的结果。例如,我们在 2daygeek 网站下搜索 “Package Manager”,查看结果。
+
+```
+$ ddgr -n 5 --site 2daygeek "package manager"
+```
+
+![][24]
+
+--------------------------------------------------------------------------------
+
+via: https://www.2daygeek.com/ddgr-duckduckgo-search-from-the-command-line-in-linux/
+
+作者:[Magesh Maruthamuthu][a]
+译者:[MjSeven](https://github.com/MjSeven)
+校对:[wxy](https://github.com/wxy)
+选题:[lujun9972](https://github.com/lujun9972)
+
+本文由 [LCTT](https://github.com/LCTT/TranslateProject) 原创编译,[Linux中国](https://linux.cn/) 荣誉推出
+
+[a]:https://www.2daygeek.com/author/magesh/
+[1]:https://github.com/jarun/ddgr
+[2]:https://www.2daygeek.com/googler-google-search-from-the-command-line-on-linux/
+[3]:https://www.2daygeek.com/buku-command-line-bookmark-manager-linux/
+[4]:https://www.2daygeek.com/socli-search-and-browse-stack-overflow-from-linux-terminal/
+[5]:https://www.2daygeek.com/rtv-reddit-terminal-viewer-a-simple-terminal-viewer-for-reddit/
+[6]:https://www.2daygeek.com/dnf-command-examples-manage-packages-fedora-system/
+[7]:https://www.2daygeek.com/snap-command-examples/
+[8]:https://www.2daygeek.com/apt-get-apt-cache-command-examples-manage-packages-debian-ubuntu-systems/
+[9]:https://www.2daygeek.com/apt-command-examples-manage-packages-debian-ubuntu-systems/
+[10]:https://www.2daygeek.com/install-yaourt-aur-helper-on-arch-linux/
+[11]:https://www.2daygeek.com/install-packer-aur-helper-on-arch-linux/
+[12]:https://www.2daygeek.com/dpkg-command-to-manage-packages-on-debian-ubuntu-linux-mint-systems/
+[13]:https://www.2daygeek.com/yum-command-examples-manage-packages-rhel-centos-systems/
+[14]:https://www.2daygeek.com/zypper-command-examples-manage-packages-opensuse-system/
+[15]:data:image/gif;base64,R0lGODlhAQABAIAAAAAAAP///yH5BAEAAAAALAAAAAABAAEAAAIBRAA7
+[16]:https://www.2daygeek.com/wp-content/uploads/2018/03/ddgr-duckduckgo-command-line-search-for-linux1.png
+[17]:https://www.2daygeek.com/wp-content/uploads/2018/03/ddgr-duckduckgo-command-line-search-for-linux-3.png
+[18]:https://www.2daygeek.com/wp-content/uploads/2018/03/ddgr-duckduckgo-command-line-search-for-linux-2.png
+[19]:https://www.2daygeek.com/wp-content/uploads/2018/03/ddgr-duckduckgo-command-line-search-for-linux-4.png
+[20]:https://www.2daygeek.com/wp-content/uploads/2018/03/ddgr-duckduckgo-command-line-search-for-linux-5a.png
+[21]:https://www.2daygeek.com/wp-content/uploads/2018/03/ddgr-duckduckgo-command-line-search-for-linux-6a.png
+[22]:https://www.2daygeek.com/wp-content/uploads/2018/03/ddgr-duckduckgo-command-line-search-for-linux-7a.png
+[23]:https://www.2daygeek.com/wp-content/uploads/2018/03/ddgr-duckduckgo-command-line-search-for-linux-8.png
+[24]:https://www.2daygeek.com/wp-content/uploads/2018/03/ddgr-duckduckgo-command-line-search-for-linux-9a.png
diff --git a/published/201905/20180429 The Easiest PDO Tutorial (Basics).md b/published/201905/20180429 The Easiest PDO Tutorial (Basics).md
new file mode 100644
index 0000000000..cadc526b0f
--- /dev/null
+++ b/published/201905/20180429 The Easiest PDO Tutorial (Basics).md
@@ -0,0 +1,155 @@
+PHP PDO 简单教程
+======
+
+
+
+大约 80% 的 Web 应用程序由 PHP 提供支持。类似地,SQL 也是如此。PHP 5.5 版本之前,我们有用于访问 MySQL 数据库的 mysql_ 命令,但由于安全性不足,它们最终被弃用。
+
+弃用这件事是发生在 2013 年的 PHP 5.5 上,我写这篇文章的时间是 2018 年,PHP 版本为 7.2。mysql_ 的弃用带来了访问数据库的两种主要方法:mysqli 和 PDO 库。
+
+虽然 mysqli 库是官方指定的,但由于 mysqli 只能支持 mysql 数据库,而 PDO 可以支持 12 种不同类型的数据库驱动程序,因此 PDO 获得了更多的赞誉。此外,PDO 还有其它一些特性,使其成为大多数开发人员的更好选择。你可以在下表中看到一些特性比较:
+
+| | PDO | MySQLi
+---|---|---
+| 数据库支持 | 12 种驱动 | 只有 MySQL
+| 范例 | OOP | 过程 + OOP
+| 预处理语句(客户端侧) | Yes | No
+| 1命名参数 | Yes | No
+
+现在我想对于大多数开发人员来说,PDO 是首选的原因已经很清楚了。所以让我们深入研究它,并希望在本文中尽量涵盖关于 PDO 你需要的了解的。
+
+### 连接
+
+第一步是连接到数据库,由于 PDO 是完全面向对象的,所以我们将使用 PDO 类的实例。
+
+我们要做的第一件事是定义主机、数据库名称、用户名、密码和数据库字符集。
+
+```
+$host = 'localhost';
+$db = 'theitstuff';
+$user = 'root';
+$pass = 'root';
+$charset = 'utf8mb4';
+$dsn = "mysql:host=$host;dbname=$db;charset=$charset";
+$conn = new PDO($dsn, $user, $pass);
+```
+
+之后,正如你在上面的代码中看到的,我们创建了 DSN 变量,DSN 变量只是一个保存数据库信息的变量。对于一些在外部服务器上运行 MySQL 的人,你还可以通过提供一个 `port=$port_number` 来调整端口号。
+
+最后,你可以创建一个 PDO 类的实例,我使用了 `$conn` 变量,并提供了 `$dsn`、`$user`、`$pass` 参数。如果你遵循这些步骤,你现在应该有一个名为 `$conn` 的对象,它是 PDO 连接类的一个实例。现在是时候进入数据库并运行一些查询。
+
+### 一个简单的 SQL 查询
+
+现在让我们运行一个简单的 SQL 查询。
+
+```
+$tis = $conn->query('SELECT name, age FROM students');
+while ($row = $tis->fetch())
+{
+ echo $row['name']."\t";
+ echo $row['age'];
+ echo "
";
+}
+```
+
+这是使用 PDO 运行查询的最简单形式。我们首先创建了一个名为 `tis`(TheITStuff 的缩写 )的变量,然后你可以看到我们使用了创建的 `$conn` 对象中的查询函数。
+
+然后我们运行一个 `while` 循环并创建了一个 `$row` 变量来从 `$tis` 对象中获取内容,最后通过调用列名来显示每一行。
+
+很简单,不是吗?现在让我们来看看预处理语句。
+
+### 预处理语句
+
+预处理语句是人们开始使用 PDO 的主要原因之一,因为它提供了可以阻止 SQL 注入的语句。
+
+有两种基本方法可供使用,你可以使用位置参数或命名参数。
+
+#### 位置参数
+
+让我们看一个使用位置参数的查询示例。
+
+```
+$tis = $conn->prepare("INSERT INTO STUDENTS(name, age) values(?, ?)");
+$tis->bindValue(1,'mike');
+$tis->bindValue(2,22);
+$tis->execute();
+```
+
+在上面的例子中,我们放置了两个问号,然后使用 `bindValue()` 函数将值映射到查询中。这些值绑定到语句问号中的位置。
+
+我还可以使用变量而不是直接提供值,通过使用 `bindParam()` 函数相同例子如下:
+
+```
+$name='Rishabh'; $age=20;
+$tis = $conn->prepare("INSERT INTO STUDENTS(name, age) values(?, ?)");
+$tis->bindParam(1,$name);
+$tis->bindParam(2,$age);
+$tis->execute();
+```
+
+### 命名参数
+
+命名参数也是预处理语句,它将值/变量映射到查询中的命名位置。由于没有位置绑定,因此在多次使用相同变量的查询中非常有效。
+
+```
+$name='Rishabh'; $age=20;
+$tis = $conn->prepare("INSERT INTO STUDENTS(name, age) values(:name, :age)");
+$tis->bindParam(':name', $name);
+$tis->bindParam(':age', $age);
+$tis->execute();
+```
+
+你可以注意到,唯一的变化是我使用 `:name` 和 `:age` 作为占位符,然后将变量映射到它们。冒号在参数之前使用,让 PDO 知道该位置是一个变量,这非常重要。
+
+你也可以类似地使用 `bindValue()` 来使用命名参数直接映射值。
+
+### 获取数据
+
+PDO 在获取数据时非常丰富,它实际上提供了许多格式来从数据库中获取数据。
+
+你可以使用 `PDO::FETCH_ASSOC` 来获取关联数组,`PDO::FETCH_NUM` 来获取数字数组,使用 `PDO::FETCH_OBJ` 来获取对象数组。
+
+```
+$tis = $conn->prepare("SELECT * FROM STUDENTS");
+$tis->execute();
+$result = $tis->fetchAll(PDO::FETCH_ASSOC);
+```
+
+你可以看到我使用了 `fetchAll`,因为我想要所有匹配的记录。如果只需要一行,你可以简单地使用 `fetch`。
+
+现在我们已经获取了数据,现在是时候循环它了,这非常简单。
+
+```
+foreach ($result as $lnu){
+ echo $lnu['name'];
+ echo $lnu['age']."
";
+}
+```
+
+你可以看到,因为我请求了关联数组,所以我正在按名称访问各个成员。
+
+虽然在定义希望如何传输递数据方面没有要求,但在定义 `$conn` 变量本身时,实际上可以将其设置为默认值。
+
+你需要做的就是创建一个 `$options` 数组,你可以在其中放入所有默认配置,只需在 `$conn` 变量中传递数组即可。
+
+```
+$options = [
+ PDO::ATTR_DEFAULT_FETCH_MODE => PDO::FETCH_ASSOC,
+];
+$conn = new PDO($dsn, $user, $pass, $options);
+```
+
+这是一个非常简短和快速的 PDO 介绍,我们很快就会制作一个高级教程。如果你在理解本教程的任何部分时遇到任何困难,请在评论部分告诉我,我会在那你为你解答。
+
+--------------------------------------------------------------------------------
+
+via: http://www.theitstuff.com/easiest-pdo-tutorial-basics
+
+作者:[Rishabh Kandari][a]
+选题:[lujun9972](https://github.com/lujun9972)
+译者:[MjSeven](https://github.com/MjSeven)
+校对:[wxy](https://github.com/wxy)
+
+本文由 [LCTT](https://github.com/LCTT/TranslateProject) 原创编译,[Linux中国](https://linux.cn/) 荣誉推出
+
+[a]:http://www.theitstuff.com/author/reevkandari
diff --git a/translated/tech/20180518 What-s a hero without a villain- How to add one to your Python game.md b/published/201905/20180518 What-s a hero without a villain- How to add one to your Python game.md
similarity index 83%
rename from translated/tech/20180518 What-s a hero without a villain- How to add one to your Python game.md
rename to published/201905/20180518 What-s a hero without a villain- How to add one to your Python game.md
index a4a2138136..c4bb5c84f0 100644
--- a/translated/tech/20180518 What-s a hero without a villain- How to add one to your Python game.md
+++ b/published/201905/20180518 What-s a hero without a villain- How to add one to your Python game.md
@@ -1,21 +1,22 @@
-没有恶棍,英雄又将如何?如何向你的 Python 游戏中添加一个敌人
+如何向你的 Python 游戏中添加一个敌人
======
+
+> 在本系列的第五部分,学习如何增加一个坏蛋与你的好人战斗。
+

在本系列的前几篇文章中(参见 [第一部分][1]、[第二部分][2]、[第三部分][3] 以及 [第四部分][4]),你已经学习了如何使用 Pygame 和 Python 在一个空白的视频游戏世界中生成一个可玩的角色。但没有恶棍,英雄又将如何?
如果你没有敌人,那将会是一个非常无聊的游戏。所以在此篇文章中,你将为你的游戏添加一个敌人并构建一个用于创建关卡的框架。
-在对玩家妖精实现全部功能仍有许多事情可做之前,跳向敌人似乎就很奇怪。但你已经学到了很多东西,创造恶棍与与创造玩家妖精非常相似。所以放轻松,使用你已经掌握的知识,看看能挑起怎样一些麻烦。
+在对玩家妖精实现全部功能之前,就来实现一个敌人似乎就很奇怪。但你已经学到了很多东西,创造恶棍与与创造玩家妖精非常相似。所以放轻松,使用你已经掌握的知识,看看能挑起怎样一些麻烦。
针对本次训练,你能够从 [Open Game Art][5] 下载一些预创建的素材。此处是我使用的一些素材:
-
-+ 印加花砖(译注:游戏中使用的花砖贴图)
++ 印加花砖(LCTT 译注:游戏中使用的花砖贴图)
+ 一些侵略者
+ 妖精、角色、物体以及特效
-
### 创造敌方妖精
是的,不管你意识到与否,你其实已经知道如何去实现敌人。这个过程与创造一个玩家妖精非常相似:
@@ -24,40 +25,27 @@
2. 创建 `update` 方法使得敌人能够检测碰撞
3. 创建 `move` 方法使得敌人能够四处游荡
-
-
-从类入手。从概念上看,它与你的 Player 类大体相同。你设置一张或者一组图片,然后设置妖精的初始位置。
+从类入手。从概念上看,它与你的 `Player` 类大体相同。你设置一张或者一组图片,然后设置妖精的初始位置。
在继续下一步之前,确保你有一张你的敌人的图像,即使只是一张临时图像。将图像放在你的游戏项目的 `images` 目录(你放置你的玩家图像的相同目录)。
如果所有的活物都拥有动画,那么游戏看起来会好得多。为敌方妖精设置动画与为玩家妖精设置动画具有相同的方式。但现在,为了保持简单,我们使用一个没有动画的妖精。
在你代码 `objects` 节的顶部,使用以下代码创建一个叫做 `Enemy` 的类:
+
```
class Enemy(pygame.sprite.Sprite):
-
'''
-
生成一个敌人
-
'''
-
def __init__(self,x,y,img):
-
pygame.sprite.Sprite.__init__(self)
-
self.image = pygame.image.load(os.path.join('images',img))
-
self.image.convert_alpha()
-
self.image.set_colorkey(ALPHA)
-
self.rect = self.image.get_rect()
-
self.rect.x = x
-
self.rect.y = y
-
```
如果你想让你的敌人动起来,使用让你的玩家拥有动画的 [相同方式][4]。
@@ -67,25 +55,21 @@ class Enemy(pygame.sprite.Sprite):
你能够通过告诉类,妖精应使用哪张图像,应出现在世界上的什么地方,来生成不只一个敌人。这意味着,你能够使用相同的敌人类,在游戏世界的任意地方生成任意数量的敌方妖精。你需要做的仅仅是调用这个类,并告诉它应使用哪张图像,以及你期望生成点的 X 和 Y 坐标。
再次,这从原则上与生成一个玩家精灵相似。在你脚本的 `setup` 节添加如下代码:
+
```
enemy = Enemy(20,200,'yeti.png') # 生成敌人
-
enemy_list = pygame.sprite.Group() # 创建敌人组
-
enemy_list.add(enemy) # 将敌人加入敌人组
-
```
-在示例代码中,X 坐标为 20,Y 坐标为 200。你可能需要根据你的敌方妖精的大小,来调整这些数字,但尽量生成在一个地方,使得你的玩家妖精能够到它。`Yeti.png` 是用于敌人的图像。
+在示例代码中,X 坐标为 20,Y 坐标为 200。你可能需要根据你的敌方妖精的大小,来调整这些数字,但尽量生成在一个范围内,使得你的玩家妖精能够碰到它。`Yeti.png` 是用于敌人的图像。
接下来,将敌人组的所有敌人绘制在屏幕上。现在,你只有一个敌人,如果你想要更多你可以稍后添加。一但你将一个敌人加入敌人组,它就会在主循环中被绘制在屏幕上。中间这一行是你需要添加的新行:
+
```
player_list.draw(world)
-
enemy_list.draw(world) # 刷新敌人
-
pygame.display.flip()
-
```
启动你的游戏,你的敌人会出现在游戏世界中你选择的 X 和 Y 坐标处。
@@ -96,42 +80,31 @@ enemy_list.add(enemy) # 将敌人加入敌人组
思考一下“关卡”是什么。你如何知道你是在游戏中的一个特定关卡中呢?
-你可以把关卡想成一系列项目的集合。就像你刚刚创建的这个平台中,一个关卡,包含了平台、敌人放置、赃物等的一个特定排列。你可以创建一个类,用来在你的玩家附近创建关卡。最终,当你创建了超过一个关卡,你就可以在你的玩家达到特定目标时,使用这个类生成下一个关卡。
+你可以把关卡想成一系列项目的集合。就像你刚刚创建的这个平台中,一个关卡,包含了平台、敌人放置、战利品等的一个特定排列。你可以创建一个类,用来在你的玩家附近创建关卡。最终,当你创建了一个以上的关卡,你就可以在你的玩家达到特定目标时,使用这个类生成下一个关卡。
将你写的用于生成敌人及其群组的代码,移动到一个每次生成新关卡时都会被调用的新函数中。你需要做一些修改,使得每次你创建新关卡时,你都能够创建一些敌人。
+
```
class Level():
-
def bad(lvl,eloc):
-
if lvl == 1:
-
enemy = Enemy(eloc[0],eloc[1],'yeti.png') # 生成敌人
-
enemy_list = pygame.sprite.Group() # 生成敌人组
-
enemy_list.add(enemy) # 将敌人加入敌人组
-
if lvl == 2:
-
print("Level " + str(lvl) )
-
-
return enemy_list
-
```
`return` 语句确保了当你调用 `Level.bad` 方法时,你将会得到一个 `enemy_list` 变量包含了所有你定义的敌人。
因为你现在将创造敌人作为每个关卡的一部分,你的 `setup` 部分也需要做些更改。不同于创造一个敌人,取而代之的是你必须去定义敌人在那里生成,以及敌人属于哪个关卡。
+
```
eloc = []
-
eloc = [200,20]
-
enemy_list = Level.bad( 1, eloc )
-
```
再次运行游戏来确认你的关卡生成正确。与往常一样,你应该会看到你的玩家,并且能看到你在本章节中添加的敌人。
@@ -140,31 +113,27 @@ enemy_list = Level.bad( 1, eloc )
一个敌人如果对玩家没有效果,那么它不太算得上是一个敌人。当玩家与敌人发生碰撞时,他们通常会对玩家造成伤害。
-因为你可能想要去跟踪玩家的生命值,因此碰撞检测发生在 Player 类,而不是 Enemy 类中。当然如果你想,你也可以跟踪敌人的生命值。它们之间的逻辑与代码大体相似,现在,我们只需要跟踪玩家的生命值。
+因为你可能想要去跟踪玩家的生命值,因此碰撞检测发生在 `Player` 类,而不是 `Enemy` 类中。当然如果你想,你也可以跟踪敌人的生命值。它们之间的逻辑与代码大体相似,现在,我们只需要跟踪玩家的生命值。
为了跟踪玩家的生命值,你必须为它确定一个变量。代码示例中的第一行是上下文提示,那么将第二行代码添加到你的 Player 类中:
+
```
self.frame = 0
-
self.health = 10
-
```
-在你 Player 类的 `update` 方法中,添加如下代码块:
+在你 `Player` 类的 `update` 方法中,添加如下代码块:
+
```
hit_list = pygame.sprite.spritecollide(self, enemy_list, False)
-
for enemy in hit_list:
-
self.health -= 1
-
print(self.health)
-
```
这段代码使用 Pygame 的 `sprite.spritecollide` 方法,建立了一个碰撞检测器,称作 `enemy_hit`。每当它的父类妖精(生成检测器的玩家妖精)的碰撞区触碰到 `enemy_list` 中的任一妖精的碰撞区时,碰撞检测器都会发出一个信号。当这个信号被接收,`for` 循环就会被触发,同时扣除一点玩家生命值。
-一旦这段代码出现在你 Player 类的 `update` 方法,并且 `update` 方法在你的主循环中被调用,Pygame 会在每个时钟 tick 检测一次碰撞。
+一旦这段代码出现在你 `Player` 类的 `update` 方法,并且 `update` 方法在你的主循环中被调用,Pygame 会在每个时钟滴答中检测一次碰撞。
### 移动敌人
@@ -176,60 +145,41 @@ enemy_list = Level.bad( 1, eloc )
举个例子,你告诉你的敌方妖精向右移动 10 步,向左移动 10 步。但敌方妖精不会计数,因此你需要创建一个变量来跟踪你的敌人已经移动了多少步,并根据计数变量的值来向左或向右移动你的敌人。
-首先,在你的 Enemy 类中创建计数变量。添加以下代码示例中的最后一行代码:
+首先,在你的 `Enemy` 类中创建计数变量。添加以下代码示例中的最后一行代码:
+
```
self.rect = self.image.get_rect()
-
self.rect.x = x
-
self.rect.y = y
-
self.counter = 0 # 计数变量
-
```
-然后,在你的 Enemy 类中创建一个 `move` 方法。使用 if-else 循环来创建一个所谓的死循环:
+然后,在你的 `Enemy` 类中创建一个 `move` 方法。使用 if-else 循环来创建一个所谓的死循环:
* 如果计数在 0 到 100 之间,向右移动;
* 如果计数在 100 到 200 之间,向左移动;
* 如果计数大于 200,则将计数重置为 0。
-
-
死循环没有终点,因为循环判断条件永远为真,所以它将永远循环下去。在此情况下,计数器总是介于 0 到 100 或 100 到 200 之间,因此敌人会永远地从左向右再从右向左移动。
你用于敌人在每个方向上移动距离的具体值,取决于你的屏幕尺寸,更确切地说,取决于你的敌人移动的平台大小。从较小的值开始,依据习惯逐步提高数值。首先进行如下尝试:
+
```
def move(self):
-
'''
-
敌人移动
-
'''
-
distance = 80
-
speed = 8
-
-
if self.counter >= 0 and self.counter <= distance:
-
self.rect.x += speed
-
elif self.counter >= distance and self.counter <= distance*2:
-
self.rect.x -= speed
-
else:
-
self.counter = 0
-
-
self.counter += 1
-
```
你可以根据需要调整距离和速度。
@@ -237,13 +187,11 @@ enemy_list = Level.bad( 1, eloc )
当你现在启动游戏,这段代码有效果吗?
当然不,你应该也知道原因。你必须在主循环中调用 `move` 方法。如下示例代码中的第一行是上下文提示,那么添加最后两行代码:
+
```
enemy_list.draw(world) #refresh enemy
-
for e in enemy_list:
-
e.move()
-
```
启动你的游戏看看当你打击敌人时发生了什么。你可能需要调整妖精的生成地点,使得你的玩家和敌人能够碰撞。当他们发生碰撞时,查看 [IDLE][6] 或 [Ninja-IDE][7] 的控制台,你可以看到生命值正在被扣除。
@@ -261,15 +209,15 @@ via: https://opensource.com/article/18/5/pygame-enemy
作者:[Seth Kenlon][a]
选题:[lujun9972](https://github.com/lujun9972)
译者:[cycoe](https://github.com/cycoe)
-校对:[校对者ID](https://github.com/校对者ID)
+校对:[wxy](https://github.com/wxy)
本文由 [LCTT](https://github.com/LCTT/TranslateProject) 原创编译,[Linux中国](https://linux.cn/) 荣誉推出
[a]: https://opensource.com/users/seth
-[1]:https://opensource.com/article/17/10/python-101
-[2]:https://opensource.com/article/17/12/game-framework-python
-[3]:https://opensource.com/article/17/12/game-python-add-a-player
-[4]:https://opensource.com/article/17/12/game-python-moving-player
+[1]:https://linux.cn/article-9071-1.html
+[2]:https://linux.cn/article-10850-1.html
+[3]:https://linux.cn/article-10858-1.html
+[4]:https://linux.cn/article-10874-1.html
[5]:https://opengameart.org
[6]:https://docs.python.org/3/library/idle.html
[7]:http://ninja-ide.org/
diff --git a/published/201905/20180605 How to use autofs to mount NFS shares.md b/published/201905/20180605 How to use autofs to mount NFS shares.md
new file mode 100644
index 0000000000..15321b2e3d
--- /dev/null
+++ b/published/201905/20180605 How to use autofs to mount NFS shares.md
@@ -0,0 +1,130 @@
+[#]: collector: (lujun9972)
+[#]: translator: (geekpi)
+[#]: reviewer: (wxy)
+[#]: publisher: (wxy)
+[#]: url: (https://linux.cn/article-10830-1.html)
+[#]: subject: (How to use autofs to mount NFS shares)
+[#]: via: (https://opensource.com/article/18/6/using-autofs-mount-nfs-shares)
+[#]: author: (Alan Formy-Duval https://opensource.com/users/alanfdoss)
+
+如何使用 autofs 挂载 NFS 共享
+======
+
+> 给你的网络文件系统(NFS)配置一个基本的自动挂载功能。
+
+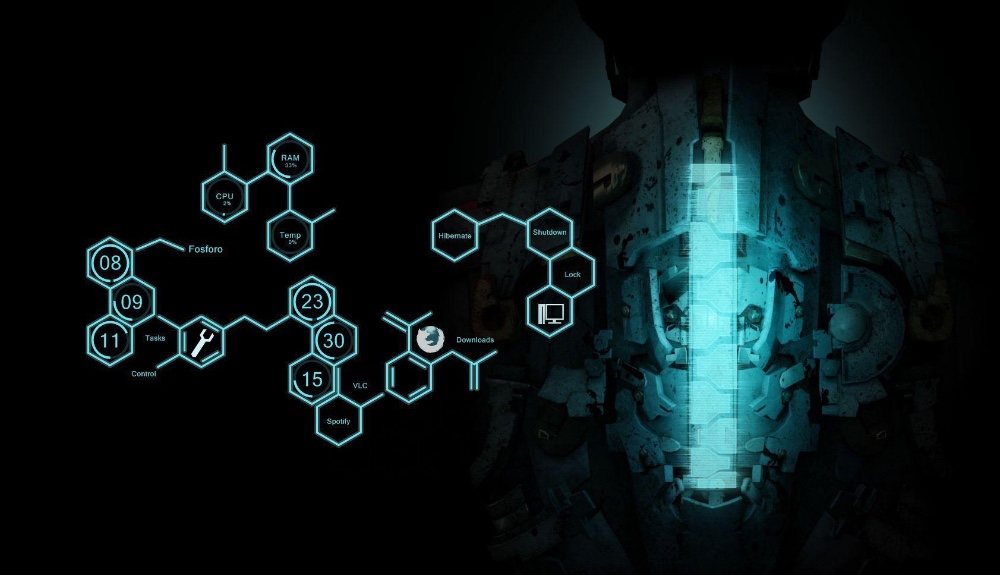
+
+大多数 Linux 文件系统在引导时挂载,并在系统运行时保持挂载状态。对于已在 `fstab` 中配置的任何远程文件系统也是如此。但是,有时你可能希望仅按需挂载远程文件系统。例如,通过减少网络带宽使用来提高性能,或出于安全原因隐藏或混淆某些目录。[autofs][1] 软件包提供此功能。在本文中,我将介绍如何配置基本的自动挂载。
+
+首先做点假设:假设有台 NFS 服务器 `tree.mydatacenter.net` 已经启动并运行。另外假设一个名为 `ourfiles` 的数据目录还有供 Carl 和 Sarah 使用的用户目录,它们都由服务器共享。
+
+一些最佳实践可以使工作更好:服务器上的用户和任何客户端工作站上的帐号有相同的用户 ID。此外,你的工作站和服务器应有相同的域名。检查相关配置文件应该确认。
+
+```
+alan@workstation1:~$ sudo getent passwd carl sarah
+[sudo] password for alan:
+carl:x:1020:1020:Carl,,,:/home/carl:/bin/bash
+sarah:x:1021:1021:Sarah,,,:/home/sarah:/bin/bash
+
+alan@workstation1:~$ sudo getent hosts
+127.0.0.1 localhost
+127.0.1.1 workstation1.mydatacenter.net workstation1
+10.10.1.5 tree.mydatacenter.net tree
+```
+
+如你所见,客户端工作站和 NFS 服务器都在 `hosts` 文件中配置。我假设这是一个基本的家庭甚至小型办公室网络,可能缺乏适合的内部域名服务(即 DNS)。
+
+### 安装软件包
+
+你只需要安装两个软件包:用于 NFS 客户端的 `nfs-common` 和提供自动挂载的 `autofs`。
+
+```
+alan@workstation1:~$ sudo apt-get install nfs-common autofs
+```
+
+你可以验证 autofs 相关的文件是否已放在 `/etc` 目录中:
+
+```
+alan@workstation1:~$ cd /etc; ll auto*
+-rw-r--r-- 1 root root 12596 Nov 19 2015 autofs.conf
+-rw-r--r-- 1 root root 857 Mar 10 2017 auto.master
+-rw-r--r-- 1 root root 708 Jul 6 2017 auto.misc
+-rwxr-xr-x 1 root root 1039 Nov 19 2015 auto.net*
+-rwxr-xr-x 1 root root 2191 Nov 19 2015 auto.smb*
+alan@workstation1:/etc$
+```
+
+### 配置 autofs
+
+现在你需要编辑其中几个文件并添加 `auto.home` 文件。首先,将以下两行添加到文件 `auto.master` 中:
+
+```
+/mnt/tree /etc/auto.misc
+/home/tree /etc/auto.home
+```
+
+每行以挂载 NFS 共享的目录开头。继续创建这些目录:
+
+```
+alan@workstation1:/etc$ sudo mkdir /mnt/tree /home/tree
+```
+
+接下来,将以下行添加到文件 `auto.misc`:
+
+```
+ourfiles -fstype=nfs tree:/share/ourfiles
+```
+
+该行表示 autofs 将挂载 `auto.master` 文件中匹配 `auto.misc` 的 `ourfiles` 共享。如上所示,这些文件将在 `/mnt/tree/ourfiles` 目录中。
+
+第三步,使用以下行创建文件 `auto.home`:
+
+```
+* -fstype=nfs tree:/home/&
+```
+
+该行表示 autofs 将挂载 `auto.master` 文件中匹配 `auto.home` 的用户共享。在这种情况下,Carl 和 Sarah 的文件将分别在目录 `/home/tree/carl` 或 `/home/tree/sarah`中。星号 `*`(称为通配符)使每个用户的共享可以在登录时自动挂载。`&` 符号也可以作为表示服务器端用户目录的通配符。它们的主目录会相应地根据 `passwd` 文件映射。如果你更喜欢本地主目录,则无需执行此操作。相反,用户可以将其用作特定文件的简单远程存储。
+
+最后,重启 `autofs` 守护进程,以便识别并加载这些配置的更改。
+
+```
+alan@workstation1:/etc$ sudo service autofs restart
+```
+
+### 测试 autofs
+
+如果更改文件 `auto.master` 中的列出目录,并运行 `ls` 命令,那么不会立即看到任何内容。例如,切换到目录 `/mnt/tree`。首先,`ls` 的输出不会显示任何内容,但在运行 `cd ourfiles` 之后,将自动挂载 `ourfiles` 共享目录。 `cd` 命令也将被执行,你将进入新挂载的目录中。
+
+```
+carl@workstation1:~$ cd /mnt/tree
+carl@workstation1:/mnt/tree$ ls
+carl@workstation1:/mnt/tree$ cd ourfiles
+carl@workstation1:/mnt/tree/ourfiles$
+```
+
+为了进一步确认正常工作,`mount` 命令会显示已挂载共享的细节。
+
+```
+carl@workstation1:~$ mount
+
+tree:/mnt/share/ourfiles on /mnt/tree/ourfiles type nfs4 (rw,relatime,vers=4.0,rsize=131072,wsize=131072,namlen=255,hard,proto=tcp,timeo=600,retrans=2,sec=sys,clientaddr=10.10.1.22,local_lock=none,addr=10.10.1.5)
+
+```
+
+对于 Carl 和 Sarah,`/home/tree` 目录工作方式相同。
+
+我发现在我的文件管理器中添加这些目录的书签很有用,可以用来快速访问。
+
+--------------------------------------------------------------------------------
+
+via: https://opensource.com/article/18/6/using-autofs-mount-nfs-shares
+
+作者:[Alan Formy-Duval][a]
+选题:[lujun9972](https://github.com/lujun9972)
+译者:[geekpi](https://github.com/geekpi)
+校对:[wxy](https://github.com/wxy)
+
+本文由 [LCTT](https://github.com/LCTT/TranslateProject) 原创编译,[Linux中国](https://linux.cn/) 荣誉推出
+
+[a]:https://opensource.com/users/alanfdoss
+[1]:https://wiki.archlinux.org/index.php/autofs
diff --git a/published/201905/20180611 3 open source alternatives to Adobe Lightroom.md b/published/201905/20180611 3 open source alternatives to Adobe Lightroom.md
new file mode 100644
index 0000000000..4cebea72fa
--- /dev/null
+++ b/published/201905/20180611 3 open source alternatives to Adobe Lightroom.md
@@ -0,0 +1,86 @@
+Adobe Lightroom 的三个开源替代品
+=======
+
+> 摄影师们:在没有 Lightroom 套件的情况下,可以看看这些 RAW 图像处理器。
+
+
+
+如今智能手机的摄像功能已经完备到多数人认为可以代替传统摄影了。虽然这在傻瓜相机的市场中是个事实,但是对于许多摄影爱好者和专业摄影师看来,一个高端单反相机所能带来的照片景深、清晰度以及真实质感是口袋中的智能手机无法与之相比的。
+
+所有的这些功能在便利性上要付出一些很小的代价;就像传统的胶片相机中的反色负片,单反照相得到的 RAW 格式文件必须预先处理才能印刷或编辑;因此对于单反相机,照片的后期处理是无可替代的,并且 首选应用就是 Adobe Lightroom。但是由于 Adobe Lightroom 的昂贵价格、基于订阅的定价模式以及专有许可证都使更多人开始关注其开源替代品。
+
+Lightroom 有两大主要功能:处理 RAW 格式的图片文件,以及数字资产管理系统(DAM) —— 通过标签、评星以及其他元数据信息来简单清晰地整理照片。
+
+在这篇文章中,我们将介绍三个开源的图片处理软件:Darktable、LightZone 以及 RawTherapee。所有的软件都有 DAM 系统,但没有任何一个具有 Lightroom 基于机器学习的图像分类和标签功能。如果你想要知道更多关于开源的 DAM 系统的软件,可以看 Terry Hacock 的文章:“[开源项目的 DAM 管理][2]”,他分享了他在自己的 [Lunatics!][3] 电影项目研究过的开源多媒体软件。
+
+### Darktable
+
+![Darktable][4]
+
+类似其他两个软件,Darktable 可以处理 RAW 格式的图像并将它们转换成可用的文件格式 —— JPEG、PNG、TIFF、PPM、PFM 和 EXR,它同时支持 Google 和 Facebook 的在线相册,上传至 Flikr,通过邮件附件发送以及创建在线相册。
+
+它有 61 个图像处理模块,可以调整图像的对比度、色调、明暗、色彩、噪点;添加水印;切割以及旋转;等等。如同另外两个软件一样,不论你做出多少次修改,这些修改都是“无损的” —— 你的初始 RAW 图像文件始终会被保存。
+
+Darktable 可以从 400 多种相机型号中直接导入照片,以及有 JPEG、CR2、DNG、OpenEXR 和 PFM 等格式的支持。图像在一个数据库中显示,因此你可以轻易地过滤并查询这些元数据,包括了文字标签、评星以及颜色标签。软件同时支持 21 种语言,支持 Linux、MacOS、BSD、Solaris 11/GNOME 以及 Windows(Windows 版本是最新发布的,Darktable 声明它比起其他版本可能还有一些不完备之处,有一些未实现的功能)。
+
+Darktable 在开源许可证 [GPLv3][7] 下发布,你可以了解更多它的 [特性][8],查阅它的 [用户手册][9],或者直接去 Github 上看[源代码][10] 。
+
+### LightZone
+
+![LightZone's tool stack][11]
+
+[LightZone][12] 和其他两个软件类似同样是无损的 RAW 格式图像处理工具:它是跨平台的,有 Windows、MacOS 和 Linux 版本,除 RAW 格式之外,它还支持 JPG 和 TIFF 格式的图像处理。接下来说说 LightZone 其他独特特性。
+
+这个软件最初在 2005 年时,是以专有许可证发布的图像处理软件,后来在 BSD 证书下开源。此外,在你下载这个软件之前,你必须注册一个免费账号,以便 LightZone的 开发团队可以跟踪软件的下载数量以及建立相关社区。(许可很快,而且是自动的,因此这不是一个很大的使用障碍。)
+
+除此之外的一个特性是这个软件的图像处理通常是通过很多可组合的工具实现的,而不是叠加滤镜(就像大多数图像处理软件),这些工具组可以被重新编排以及移除,以及被保存并且复制用到另一些图像上。如果想要编辑图片的部分区域,你还可以通过矢量工具或者根据色彩和亮度来选择像素。
+
+想要了解更多,见 LightZone 的[论坛][13] 或者查看 Github上的 [源代码][14]。
+
+### RawTherapee
+
+![RawTherapee][15]
+
+[RawTherapee][16] 是另一个值得关注的开源([GPL][17])的 RAW 图像处理器。就像 Darktable 和 LightZone,它是跨平台的(支持 Windows、MacOS 和 Linux),一切修改都在无损条件下进行,因此不论你叠加多少滤镜做出多少改变,你都可以回到你最初的 RAW 文件。
+
+RawTherapee 采用的是一个面板式的界面,包括一个历史记录面板来跟踪你做出的修改,以方便随时回到先前的图像;一个快照面板可以让你同时处理一张照片的不同版本;一个可滚动的工具面板可以方便准确地选择工具。这些工具包括了一系列的调整曝光、色彩、细节、图像变换以及去马赛克功能。
+
+这个软件可以从多数相机直接导入 RAW 文件,并且支持超过 25 种语言,得到了广泛使用。批量处理以及 [SSE][18] 优化这类功能也进一步提高了图像处理的速度以及对 CPU 性能的利用。
+
+RawTherapee 还提供了很多其他 [功能][19];可以查看它的 [官方文档][20] 以及 [源代码][21] 了解更多细节。
+
+你是否在摄影中使用另外的开源 RAW 图像处理工具?有任何建议和推荐都可以在评论中分享。
+
+------
+
+via: https://opensource.com/alternatives/adobe-lightroom
+
+作者:[Opensource.com][a]
+选题:[lujun9972](https://github.com/lujun9972)
+译者:[scoutydren](https://github.com/scoutydren)
+校对:[wxy](https://github.com/wxy)
+
+本文由 [LCTT](https://github.com/LCTT/TranslateProject) 原创编译,[Linux中国](https://linux.cn/) 荣誉推出
+
+[a]: https://opensource.com
+[1]: https://en.wikipedia.org/wiki/Raw_image_format
+[2]: https://opensource.com/article/18/3/movie-open-source-software
+[3]: http://lunatics.tv/
+[4]: https://opensource.com/sites/default/files/styles/panopoly_image_original/public/uploads/raw-image-processors_darkroom1.jpg?itok=0fjk37tC "Darktable"
+[5]: http://www.darktable.org/
+[6]: https://www.darktable.org/about/faq/#faq-windows
+[7]: https://github.com/darktable-org/darktable/blob/master/LICENSE
+[8]: https://www.darktable.org/about/features/
+[9]: https://www.darktable.org/resources/
+[10]: https://github.com/darktable-org/darktable
+[11]: https://opensource.com/sites/default/files/styles/panopoly_image_original/public/uploads/raw-image-processors_lightzone1tookstack.jpg?itok=1e3s85CZ
+[12]: http://www.lightzoneproject.org/
+[13]: http://www.lightzoneproject.org/Forum
+[14]: https://github.com/ktgw0316/LightZone
+[15]: https://opensource.com/sites/default/files/styles/panopoly_image_original/public/uploads/raw-image-processors_rawtherapee.jpg?itok=meiuLxPw "RawTherapee"
+[16]: http://rawtherapee.com/
+[17]: https://github.com/Beep6581/RawTherapee/blob/dev/LICENSE.txt
+[18]: https://en.wikipedia.org/wiki/Streaming_SIMD_Extensions
+[19]: http://rawpedia.rawtherapee.com/Features
+[20]: http://rawpedia.rawtherapee.com/Main_Page
+[21]: https://github.com/Beep6581/RawTherapee
diff --git a/published/201905/20180725 Put platforms in a Python game with Pygame.md b/published/201905/20180725 Put platforms in a Python game with Pygame.md
new file mode 100644
index 0000000000..d5f6a910d2
--- /dev/null
+++ b/published/201905/20180725 Put platforms in a Python game with Pygame.md
@@ -0,0 +1,593 @@
+[#]: collector: (lujun9972)
+[#]: translator: (robsean)
+[#]: reviewer: (wxy)
+[#]: publisher: (wxy)
+[#]: url: (https://linux.cn/article-10902-1.html)
+[#]: subject: (Put platforms in a Python game with Pygame)
+[#]: via: (https://opensource.com/article/18/7/put-platforms-python-game)
+[#]: author: (Seth Kenlon https://opensource.com/users/seth)
+
+在 Pygame 游戏中放置平台
+======
+
+> 在这个从零构建一个 Python 游戏系列的第六部分中,为你的角色创建一些平台来旅行。
+
+
+
+这是仍在进行中的关于使用 Pygame 模块来在 Python 3 中创建电脑游戏的系列文章的第六部分。先前的文章是:
+
++ [通过构建一个简单的掷骰子游戏去学习怎么用 Python 编程][24]
++ [使用 Python 和 Pygame 模块构建一个游戏框架][25]
++ [如何在你的 Python 游戏中添加一个玩家][26]
++ [用 Pygame 使你的游戏角色移动起来][27]
++ [如何向你的 Python 游戏中添加一个敌人][28]
+
+一个平台类游戏需要平台。
+
+在 [Pygame][1] 中,平台本身也是个妖精,正像你那个可玩的妖精。这一点是重要的,因为有个是对象的平台,可以使你的玩家妖精更容易与之互动。
+
+创建平台有两个主要步骤。首先,你必须给该对象编写代码,然后,你必须映射出你希望该对象出现的位置。
+
+### 编码平台对象
+
+要构建一个平台对象,你要创建一个名为 `Platform` 的类。它是一个妖精,正像你的 `Player` [妖精][2] 一样,带有很多相同的属性。
+
+你的 `Platform` 类需要知道很多平台类型的信息,它应该出现在游戏世界的哪里、它应该包含的什么图片等等。这其中很多信息可能还尚不存在,这要看你为你的游戏计划了多少,但是没有关系。正如直到[移动你的游戏角色][3]那篇文章结束时,你都没有告诉你的玩家妖精移动速度有多快,你不必事先告诉 `Platform` 每一件事。
+
+在这系列中你所写的脚本的开头附近,创建一个新的类。在这个代码示例中前三行是用于说明上下文,因此在注释的下面添加代码:
+
+```
+import pygame
+import sys
+import os
+## 新代码如下:
+
+class Platform(pygame.sprite.Sprite):
+# x location, y location, img width, img height, img file
+def __init__(self,xloc,yloc,imgw,imgh,img):
+ pygame.sprite.Sprite.__init__(self)
+ self.image = pygame.image.load(os.path.join('images',img)).convert()
+ self.image.convert_alpha()
+ self.image.set_colorkey(ALPHA)
+ self.rect = self.image.get_rect()
+ self.rect.y = yloc
+ self.rect.x = xloc
+```
+
+当被调用时,这个类在某个 X 和 Y 位置上创建一个屏上对象,具有某种宽度和高度,并使用某种图像作为纹理。这与如何在屏上绘制出玩家或敌人非常类似。
+
+### 平台的类型
+
+下一步是绘制出你的平台需要出现的地方。
+
+#### 瓷砖方式
+
+实现平台类游戏世界有几种不同的方法。在最初的横向滚轴游戏中,例如,马里奥超级兄弟和刺猬索尼克,这个技巧是使用“瓷砖”方式,也就是说有几个代表地面和各种平台的块,并且这些块被重复使用来制作一个关卡。你只能有 8 或 12 种不同的块,你可以将它们排列在屏幕上来创建地面、浮动的平台,以及你游戏中需要的一切其它的事物。有人发现这是制作游戏最容易的方法了,因为你只需要制作(或下载)一小组关卡素材就能创建很多不同的关卡。然而,这里的代码需要一点数学知识。
+
+![Supertux, a tile-based video game][5]
+
+*[SuperTux][6] ,一个基于瓷砖的电脑游戏。*
+
+#### 手工绘制方式
+
+另一种方法是将每个素材作为一个整体图像。如果你喜欢为游戏世界创建素材,那你会在用图形应用程序构建游戏世界的每个部分上花费很多时间。这种方法不需要太多的数学知识,因为所有的平台都是整体的、完整的对象,你只需要告诉 [Python][7] 将它们放在屏幕上的什么位置。
+
+每种方法都有优势和劣势,并且根据于你选择使用的方式,代码稍有不同。我将覆盖这两方面,所以你可以在你的工程中使用一种或另一种,甚至两者的混合。
+
+### 关卡绘制
+
+总的来说,绘制你的游戏世界是关卡设计和游戏编程中的一个重要的部分。这需要数学知识,但是没有什么太难的,而且 Python 擅长数学,它会有所帮助。
+
+你也许发现先在纸张上设计是有用的。拿一张表格纸,并绘制一个方框来代表你的游戏窗体。在方框中绘制平台,并标记其每一个平台的 X 和 Y 坐标,以及它的宽度和高度。在方框中的实际位置没有必要是精确的,你只要保持数字合理即可。譬如,假设你的屏幕是 720 像素宽,那么你不能在一个屏幕上放 8 块 100 像素的平台。
+
+当然,不是你游戏中的所有平台都必须容纳在一个屏幕大小的方框里,因为你的游戏将随着你的玩家行走而滚动。所以,可以继续绘制你的游戏世界到第一屏幕的右侧,直到关卡结束。
+
+如果你更喜欢精确一点,你可以使用方格纸。当设计一个瓷砖类的游戏时,这是特别有用的,因为每个方格可以代表一个瓷砖。
+
+![Example of a level map][9]
+
+*一个关卡地图示例。*
+
+#### 坐标系
+
+你可能已经在学校中学习过[笛卡尔坐标系][10]。你学习的东西也适用于 Pygame,除了在 Pygame 中你的游戏世界的坐标系的原点 `0,0` 是放置在你的屏幕的左上角而不是在中间,是你在地理课上用过的坐标是在中间的。
+
+![Example of coordinates in Pygame][12]
+
+*在 Pygame 中的坐标示例。*
+
+X 轴起始于最左边的 0,向右无限增加。Y 轴起始于屏幕顶部的 0,向下延伸。
+
+#### 图片大小
+
+如果你不知道你的玩家、敌人、平台是多大的,绘制出一个游戏世界是毫无意义的。你可以在图形程序中找到你的平台或瓷砖的尺寸。例如在 [Krita][13] 中,单击“图像”菜单,并选择“属性”。你可以在“属性”窗口的最顶部处找到它的尺寸。
+
+另外,你也可以创建一个简单的 Python 脚本来告诉你的一个图像的尺寸。打开一个新的文本文件,并输入这些代码到其中:
+
+```
+#!/usr/bin/env python3
+
+from PIL import Image
+import os.path
+import sys
+
+if len(sys.argv) > 1:
+ print(sys.argv[1])
+else:
+ sys.exit('Syntax: identify.py [filename]')
+
+pic = sys.argv[1]
+dim = Image.open(pic)
+X = dim.size[0]
+Y = dim.size[1]
+
+print(X,Y)
+```
+
+保存该文本文件为 `identify.py`。
+
+要使用这个脚本,你必须安装一些额外的 Python 模块,它们包含了这个脚本中新使用的关键字:
+
+```
+$ pip3 install Pillow --user
+```
+
+一旦安装好,在你游戏工程目录中运行这个脚本:
+
+```
+$ python3 ./identify.py images/ground.png
+(1080, 97)
+```
+
+在这个示例中,地面平台的图形的大小是 1080 像素宽和 97 像素高。
+
+### 平台块
+
+如果你选择单独地绘制每个素材,你必须创建想要插入到你的游戏世界中的几个平台和其它元素,每个素材都放在它自己的文件中。换句话说,你应该让每个素材都有一个文件,像这样:
+
+![One image file per object][15]
+
+*每个对象一个图形文件。*
+
+你可以按照你希望的次数重复使用每个平台,只要确保每个文件仅包含一个平台。你不能使用一个文件包含全部素材,像这样:
+
+![Your level cannot be one image file][17]
+
+*你的关卡不能是一个图形文件。*
+
+当你完成时,你可能希望你的游戏看起来像这样,但是如果你在一个大文件中创建你的关卡,你就没有方法从背景中区分出一个平台,因此,要么把对象绘制在它们自己的文件中,要么从一个更大的文件中裁剪出它们,并保存为单独的副本。
+
+**注意:** 如同你的其它素材,你可以使用 [GIMP][18]、Krita、[MyPaint][19],或 [Inkscape][20] 来创建你的游戏素材。
+
+平台出现在每个关卡开始的屏幕上,因此你必须在你的 `Level` 类中添加一个 `platform` 函数。在这里特例是地面平台,它重要到应该拥有它自己的一个组。通过把地面看作一组特殊类型的平台,你可以选择它是否滚动,或它上面是否可以站立,而其它平台可以漂浮在它上面。这取决于你。
+
+添加这两个函数到你的 `Level` 类:
+
+```
+def ground(lvl,x,y,w,h):
+ ground_list = pygame.sprite.Group()
+ if lvl == 1:
+ ground = Platform(x,y,w,h,'block-ground.png')
+ ground_list.add(ground)
+
+ if lvl == 2:
+ print("Level " + str(lvl) )
+
+ return ground_list
+
+def platform( lvl ):
+ plat_list = pygame.sprite.Group()
+ if lvl == 1:
+ plat = Platform(200, worldy-97-128, 285,67,'block-big.png')
+ plat_list.add(plat)
+ plat = Platform(500, worldy-97-320, 197,54,'block-small.png')
+ plat_list.add(plat)
+ if lvl == 2:
+ print("Level " + str(lvl) )
+
+ return plat_list
+```
+
+`ground` 函数需要一个 X 和 Y 位置,以便 Pygame 知道在哪里放置地面平台。它也需要知道平台的宽度和高度,这样 Pygame 知道地面延伸到每个方向有多远。该函数使用你的 `Platform` 类来生成一个屏上对象,然后将这个对象添加到 `ground_list` 组。
+
+`platform` 函数本质上是相同的,除了其有更多的平台。在这个示例中,仅有两个平台,但是你可以想有多少就有多少。在进入一个平台后,在列出另一个前你必须添加它到 `plat_list` 中。如果你不添加平台到组中,那么它将不出现在你的游戏中。
+
+> **提示:** 很难想象你的游戏世界的 0 是在顶部,因为在真实世界中发生的情况是相反的;当估计你有多高时,你不会从上往下测量你自己,而是从脚到头顶来测量。
+>
+> 如果对你来说从“地面”上来构建你的游戏世界更容易,将 Y 轴值表示为负数可能有帮助。例如,你知道你的游戏世界的底部是 `worldy` 的值。因此 `worldy` 减去地面的高度(在这个示例中是 97)是你的玩家正常站立的位置。如果你的角色是 64 像素高,那么地面减去 128 正好是你的玩家的两倍高。事实上,一个放置在 128 像素处平台大约是相对于你的玩家的两层楼高度。一个平台在 -320 处比三层楼更高。等等。
+
+正像你现在可能所知的,如果你不使用它们,你的类和函数是没有价值的。添加这些代码到你的设置部分(第一行只是上下文,所以添加最后两行):
+
+```
+enemy_list = Level.bad( 1, eloc )
+ground_list = Level.ground( 1,0,worldy-97,1080,97 )
+plat_list = Level.platform( 1 )
+```
+
+并把这些行加到你的主循环(再一次,第一行仅用于上下文):
+
+```
+enemy_list.draw(world) # 刷新敌人
+ground_list.draw(world) # 刷新地面
+plat_list.draw(world) # 刷新平台
+```
+
+### 瓷砖平台
+
+瓷砖类游戏世界更容易制作,因为你只需要在前面绘制一些块,就能在游戏中一再使用它们创建每个平台。在像 [OpenGameArt.org][21] 这样的网站上甚至有一套瓷砖供你来使用。
+
+`Platform` 类与在前面部分中的类是相同的。
+
+`ground` 和 `platform` 在 `Level` 类中,然而,必须使用循环来计算使用多少块来创建每个平台。
+
+如果你打算在你的游戏世界中有一个坚固的地面,这种地面是很简单的。你只需要从整个窗口的一边到另一边“克隆”你的地面瓷砖。例如,你可以创建一个 X 和 Y 值的列表来规定每个瓷砖应该放置的位置,然后使用一个循环来获取每个值并绘制每一个瓷砖。这仅是一个示例,所以不要添加这到你的代码:
+
+```
+# Do not add this to your code
+gloc = [0,656,64,656,128,656,192,656,256,656,320,656,384,656]
+```
+
+不过,如果你仔细看,你可以看到所有的 Y 值是相同的,X 值以 64 的增量不断地增加 —— 这就是瓷砖的大小。这种重复是精确地,是计算机擅长的,因此你可以使用一点数学逻辑来让计算机为你做所有的计算:
+
+添加这些到你的脚本的设置部分:
+
+```
+gloc = []
+tx = 64
+ty = 64
+
+i=0
+while i <= (worldx/tx)+tx:
+ gloc.append(i*tx)
+ i=i+1
+
+ground_list = Level.ground( 1,gloc,tx,ty )
+```
+
+现在,不管你的窗口的大小,Python 会通过瓷砖的宽度分割游戏世界的宽度,并创建一个数组列表列出每个 X 值。这里不计算 Y 值,因为在平的地面上这个从不会变化。
+
+为了在一个函数中使用数组,使用一个 `while` 循环,查看每个条目并在适当的位置添加一个地面瓷砖:
+
+```
+def ground(lvl,gloc,tx,ty):
+ ground_list = pygame.sprite.Group()
+ i=0
+ if lvl == 1:
+ while i < len(gloc):
+ ground = Platform(gloc[i],worldy-ty,tx,ty,'tile-ground.png')
+ ground_list.add(ground)
+ i=i+1
+
+ if lvl == 2:
+ print("Level " + str(lvl) )
+
+ return ground_list
+```
+
+除了 `while` 循环,这几乎与在上面一部分中提供的瓷砖类平台的 `ground` 函数的代码相同。
+
+对于移动的平台,原理是相似的,但是这里有一些技巧可以使它简单。
+
+你可以通过它的起始像素(它的 X 值)、距地面的高度(它的 Y 值)、绘制多少瓷砖来定义一个平台,而不是通过像素绘制每个平台。这样,你不必操心每个平台的宽度和高度。
+
+这个技巧的逻辑有一点复杂,因此请仔细复制这些代码。有一个 `while` 循环嵌套在另一个 `while` 循环的内部,因为这个函数必须考虑每个数组项的三个值来成功地建造一个完整的平台。在这个示例中,这里仅有三个平台以 `ploc.append` 语句定义,但是你的游戏可能需要更多,因此你需要多少就定义多少。当然,有一些不会出现,因为它们远在屏幕外,但是一旦当你进行滚动时,它们将呈现在眼前。
+
+```
+def platform(lvl,tx,ty):
+ plat_list = pygame.sprite.Group()
+ ploc = []
+ i=0
+ if lvl == 1:
+ ploc.append((200,worldy-ty-128,3))
+ ploc.append((300,worldy-ty-256,3))
+ ploc.append((500,worldy-ty-128,4))
+ while i < len(ploc):
+ j=0
+ while j <= ploc[i][2]:
+ plat = Platform((ploc[i][0]+(j*tx)),ploc[i][1],tx,ty,'tile.png')
+ plat_list.add(plat)
+ j=j+1
+ print('run' + str(i) + str(ploc[i]))
+ i=i+1
+
+ if lvl == 2:
+ print("Level " + str(lvl) )
+
+ return plat_list
+```
+
+要让这些平台出现在你的游戏世界,它们必须出现在你的主循环中。如果你还没有这样做,添加这些行到你的主循环(再一次,第一行仅被用于上下文)中:
+
+```
+ enemy_list.draw(world) # 刷新敌人
+ ground_list.draw(world) # 刷新地面
+ plat_list.draw(world) # 刷新平台
+```
+
+启动你的游戏,根据需要调整你的平台的放置位置。如果你看不见屏幕外产生的平台,不要担心;你不久后就可以修复它。
+
+到目前为止,这是游戏的图片和代码:
+
+![Pygame game][23]
+
+*到目前为止,我们的 Pygame 平台。*
+
+```
+#!/usr/bin/env python3
+# draw a world
+# add a player and player control
+# add player movement
+# add enemy and basic collision
+# add platform
+
+# GNU All-Permissive License
+# Copying and distribution of this file, with or without modification,
+# are permitted in any medium without royalty provided the copyright
+# notice and this notice are preserved. This file is offered as-is,
+# without any warranty.
+
+import pygame
+import sys
+import os
+
+'''
+Objects
+'''
+
+class Platform(pygame.sprite.Sprite):
+ # x location, y location, img width, img height, img file
+ def __init__(self,xloc,yloc,imgw,imgh,img):
+ pygame.sprite.Sprite.__init__(self)
+ self.image = pygame.image.load(os.path.join('images',img)).convert()
+ self.image.convert_alpha()
+ self.rect = self.image.get_rect()
+ self.rect.y = yloc
+ self.rect.x = xloc
+
+class Player(pygame.sprite.Sprite):
+ '''
+ Spawn a player
+ '''
+ def __init__(self):
+ pygame.sprite.Sprite.__init__(self)
+ self.movex = 0
+ self.movey = 0
+ self.frame = 0
+ self.health = 10
+ self.score = 1
+ self.images = []
+ for i in range(1,9):
+ img = pygame.image.load(os.path.join('images','hero' + str(i) + '.png')).convert()
+ img.convert_alpha()
+ img.set_colorkey(ALPHA)
+ self.images.append(img)
+ self.image = self.images[0]
+ self.rect = self.image.get_rect()
+
+ def control(self,x,y):
+ '''
+ control player movement
+ '''
+ self.movex += x
+ self.movey += y
+
+ def update(self):
+ '''
+ Update sprite position
+ '''
+
+ self.rect.x = self.rect.x + self.movex
+ self.rect.y = self.rect.y + self.movey
+
+ # moving left
+ if self.movex < 0:
+ self.frame += 1
+ if self.frame > ani*3:
+ self.frame = 0
+ self.image = self.images[self.frame//ani]
+
+ # moving right
+ if self.movex > 0:
+ self.frame += 1
+ if self.frame > ani*3:
+ self.frame = 0
+ self.image = self.images[(self.frame//ani)+4]
+
+ # collisions
+ enemy_hit_list = pygame.sprite.spritecollide(self, enemy_list, False)
+ for enemy in enemy_hit_list:
+ self.health -= 1
+ print(self.health)
+
+ ground_hit_list = pygame.sprite.spritecollide(self, ground_list, False)
+ for g in ground_hit_list:
+ self.health -= 1
+ print(self.health)
+
+
+class Enemy(pygame.sprite.Sprite):
+ '''
+ Spawn an enemy
+ '''
+ def __init__(self,x,y,img):
+ pygame.sprite.Sprite.__init__(self)
+ self.image = pygame.image.load(os.path.join('images',img))
+ #self.image.convert_alpha()
+ #self.image.set_colorkey(ALPHA)
+ self.rect = self.image.get_rect()
+ self.rect.x = x
+ self.rect.y = y
+ self.counter = 0
+
+ def move(self):
+ '''
+ enemy movement
+ '''
+ distance = 80
+ speed = 8
+
+ if self.counter >= 0 and self.counter <= distance:
+ self.rect.x += speed
+ elif self.counter >= distance and self.counter <= distance*2:
+ self.rect.x -= speed
+ else:
+ self.counter = 0
+
+ self.counter += 1
+
+class Level():
+ def bad(lvl,eloc):
+ if lvl == 1:
+ enemy = Enemy(eloc[0],eloc[1],'yeti.png') # spawn enemy
+ enemy_list = pygame.sprite.Group() # create enemy group
+ enemy_list.add(enemy) # add enemy to group
+
+ if lvl == 2:
+ print("Level " + str(lvl) )
+
+ return enemy_list
+
+ def loot(lvl,lloc):
+ print(lvl)
+
+ def ground(lvl,gloc,tx,ty):
+ ground_list = pygame.sprite.Group()
+ i=0
+ if lvl == 1:
+ while i < len(gloc):
+ print("blockgen:" + str(i))
+ ground = Platform(gloc[i],worldy-ty,tx,ty,'ground.png')
+ ground_list.add(ground)
+ i=i+1
+
+ if lvl == 2:
+ print("Level " + str(lvl) )
+
+ return ground_list
+
+'''
+Setup
+'''
+worldx = 960
+worldy = 720
+
+fps = 40 # frame rate
+ani = 4 # animation cycles
+clock = pygame.time.Clock()
+pygame.init()
+main = True
+
+BLUE = (25,25,200)
+BLACK = (23,23,23 )
+WHITE = (254,254,254)
+ALPHA = (0,255,0)
+
+world = pygame.display.set_mode([worldx,worldy])
+backdrop = pygame.image.load(os.path.join('images','stage.png')).convert()
+backdropbox = world.get_rect()
+player = Player() # spawn player
+player.rect.x = 0
+player.rect.y = 0
+player_list = pygame.sprite.Group()
+player_list.add(player)
+steps = 10 # how fast to move
+
+eloc = []
+eloc = [200,20]
+gloc = []
+#gloc = [0,630,64,630,128,630,192,630,256,630,320,630,384,630]
+tx = 64 #tile size
+ty = 64 #tile size
+
+i=0
+while i <= (worldx/tx)+tx:
+ gloc.append(i*tx)
+ i=i+1
+ print("block: " + str(i))
+
+enemy_list = Level.bad( 1, eloc )
+ground_list = Level.ground( 1,gloc,tx,ty )
+
+'''
+Main loop
+'''
+while main == True:
+ for event in pygame.event.get():
+ if event.type == pygame.QUIT:
+ pygame.quit(); sys.exit()
+ main = False
+
+ if event.type == pygame.KEYDOWN:
+ if event.key == pygame.K_LEFT or event.key == ord('a'):
+ player.control(-steps,0)
+ if event.key == pygame.K_RIGHT or event.key == ord('d'):
+ player.control(steps,0)
+ if event.key == pygame.K_UP or event.key == ord('w'):
+ print('jump')
+
+ if event.type == pygame.KEYUP:
+ if event.key == pygame.K_LEFT or event.key == ord('a'):
+ player.control(steps,0)
+ if event.key == pygame.K_RIGHT or event.key == ord('d'):
+ player.control(-steps,0)
+ if event.key == ord('q'):
+ pygame.quit()
+ sys.exit()
+ main = False
+
+# world.fill(BLACK)
+ world.blit(backdrop, backdropbox)
+ player.update()
+ player_list.draw(world) #refresh player position
+ enemy_list.draw(world) # refresh enemies
+ ground_list.draw(world) # refresh enemies
+ for e in enemy_list:
+ e.move()
+ pygame.display.flip()
+ clock.tick(fps)
+```
+
+(LCTT 译注:到本文翻译完为止,该系列已经近一年没有继续更新了~)
+
+--------------------------------------------------------------------------------
+
+via: https://opensource.com/article/18/7/put-platforms-python-game
+
+作者:[Seth Kenlon][a]
+选题:[lujun9972][b]
+译者:[robsean](https://github.com/robsean)
+校对:[wxy](https://github.com/wxy)
+
+本文由 [LCTT](https://github.com/LCTT/TranslateProject) 原创编译,[Linux中国](https://linux.cn/) 荣誉推出
+
+[a]: https://opensource.com/users/seth
+[b]: https://github.com/lujun9972
+[1]: https://www.pygame.org/news
+[2]: https://opensource.com/article/17/12/game-python-add-a-player
+[3]: https://opensource.com/article/17/12/game-python-moving-player
+[4]: /file/403841
+[5]: https://opensource.com/sites/default/files/uploads/supertux.png (Supertux, a tile-based video game)
+[6]: https://www.supertux.org/
+[7]: https://www.python.org/
+[8]: /file/403861
+[9]: https://opensource.com/sites/default/files/uploads/layout.png (Example of a level map)
+[10]: https://en.wikipedia.org/wiki/Cartesian_coordinate_system
+[11]: /file/403871
+[12]: https://opensource.com/sites/default/files/uploads/pygame_coordinates.png (Example of coordinates in Pygame)
+[13]: https://krita.org/en/
+[14]: /file/403876
+[15]: https://opensource.com/sites/default/files/uploads/pygame_floating.png (One image file per object)
+[16]: /file/403881
+[17]: https://opensource.com/sites/default/files/uploads/pygame_flattened.png (Your level cannot be one image file)
+[18]: https://www.gimp.org/
+[19]: http://mypaint.org/about/
+[20]: https://inkscape.org/en/
+[21]: https://opengameart.org/content/simplified-platformer-pack
+[22]: /file/403886
+[23]: https://opensource.com/sites/default/files/uploads/pygame_platforms.jpg (Pygame game)
+[24]: https://linux.cn/article-9071-1.html
+[25]: https://linux.cn/article-10850-1.html
+[26]: https://linux.cn/article-10858-1.html
+[27]: https://linux.cn/article-10874-1.html
+[28]: https://linux.cn/article-10883-1.html
+
diff --git a/published/201905/20181212 TLP - An Advanced Power Management Tool That Improve Battery Life On Linux Laptop.md b/published/201905/20181212 TLP - An Advanced Power Management Tool That Improve Battery Life On Linux Laptop.md
new file mode 100644
index 0000000000..2b38da68d0
--- /dev/null
+++ b/published/201905/20181212 TLP - An Advanced Power Management Tool That Improve Battery Life On Linux Laptop.md
@@ -0,0 +1,596 @@
+[#]: collector: (lujun9972)
+[#]: translator: (wxy)
+[#]: reviewer: (wxy)
+[#]: publisher: (wxy)
+[#]: url: (https://linux.cn/article-10848-1.html)
+[#]: subject: (TLP – An Advanced Power Management Tool That Improve Battery Life On Linux Laptop)
+[#]: via: (https://www.2daygeek.com/tlp-increase-optimize-linux-laptop-battery-life/)
+[#]: author: (Magesh Maruthamuthu https://www.2daygeek.com/author/magesh/)
+
+TLP:一个可以延长 Linux 笔记本电池寿命的高级电源管理工具
+======
+
+
+
+笔记本电池是针对 Windows 操作系统进行了高度优化的,当我在笔记本电脑中使用 Windows 操作系统时,我已经意识到这一点,但对于 Linux 来说却不一样。
+
+多年来,Linux 在电池优化方面取得了很大进步,但我们仍然需要做一些必要的事情来改善 Linux 中笔记本电脑的电池寿命。
+
+当我考虑延长电池寿命时,我没有多少选择,但我觉得 TLP 对我来说是一个更好的解决方案,所以我会继续使用它。
+
+在本教程中,我们将详细讨论 TLP 以延长电池寿命。
+
+我们之前在我们的网站上写过三篇关于 Linux [笔记本电池节电工具][1] 的文章:[PowerTOP][2] 和 [电池充电状态][3]。
+
+### TLP
+
+[TLP][4] 是一款自由开源的高级电源管理工具,可在不进行任何配置更改的情况下延长电池寿命。
+
+由于它的默认配置已针对电池寿命进行了优化,因此你可能只需要安装,然后就忘记它吧。
+
+此外,它可以高度定制化,以满足你的特定要求。TLP 是一个具有自动后台任务的纯命令行工具。它不包含GUI。
+
+TLP 适用于各种品牌的笔记本电脑。设置电池充电阈值仅适用于 IBM/Lenovo ThinkPad。
+
+所有 TLP 设置都存储在 `/etc/default/tlp` 中。其默认配置提供了开箱即用的优化的节能设置。
+
+以下 TLP 设置可用于自定义,如果需要,你可以相应地进行必要的更改。
+
+### TLP 功能
+
+* 内核笔记本电脑模式和脏缓冲区超时
+* 处理器频率调整,包括 “turbo boost”/“turbo core”
+* 限制最大/最小的 P 状态以控制 CPU 的功耗
+* HWP 能源性能提示
+* 用于多核/超线程的功率感知进程调度程序
+* 处理器性能与节能策略(`x86_energy_perf_policy`)
+* 硬盘高级电源管理级别(APM)和降速超时(按磁盘)
+* AHCI 链路电源管理(ALPM)与设备黑名单
+* PCIe 活动状态电源管理(PCIe ASPM)
+* PCI(e) 总线设备的运行时电源管理
+* Radeon 图形电源管理(KMS 和 DPM)
+* Wifi 省电模式
+* 关闭驱动器托架中的光盘驱动器
+* 音频省电模式
+* I/O 调度程序(按磁盘)
+* USB 自动暂停,支持设备黑名单/白名单(输入设备自动排除)
+* 在系统启动和关闭时启用或禁用集成的 wifi、蓝牙或 wwan 设备
+* 在系统启动时恢复无线电设备状态(从之前的关机时的状态)
+* 无线电设备向导:在网络连接/断开和停靠/取消停靠时切换无线电
+* 禁用 LAN 唤醒
+* 挂起/休眠后恢复集成的 WWAN 和蓝牙状态
+* 英特尔处理器的动态电源降低 —— 需要内核和 PHC-Patch 支持
+* 电池充电阈值 —— 仅限 ThinkPad
+* 重新校准电池 —— 仅限 ThinkPad
+
+### 如何在 Linux 上安装 TLP
+
+TLP 包在大多数发行版官方存储库中都可用,因此,使用发行版的 [包管理器][5] 来安装它。
+
+对于 Fedora 系统,使用 [DNF 命令][6] 安装 TLP。
+
+```
+$ sudo dnf install tlp tlp-rdw
+```
+
+ThinkPad 需要一些附加软件包。
+
+```
+$ sudo dnf install https://download1.rpmfusion.org/free/fedora/rpmfusion-free-release-$(rpm -E %fedora).noarch.rpm
+$ sudo dnf install http://repo.linrunner.de/fedora/tlp/repos/releases/tlp-release.fc$(rpm -E %fedora).noarch.rpm
+$ sudo dnf install akmod-tp_smapi akmod-acpi_call kernel-devel
+```
+
+安装 smartmontool 以显示 tlp-stat 中 S.M.A.R.T. 数据。
+
+```
+$ sudo dnf install smartmontools
+```
+
+对于 Debian/Ubuntu 系统,使用 [APT-GET 命令][7] 或 [APT 命令][8] 安装 TLP。
+
+```
+$ sudo apt install tlp tlp-rdw
+```
+
+ThinkPad 需要一些附加软件包。
+
+```
+$ sudo apt-get install tp-smapi-dkms acpi-call-dkms
+```
+
+安装 smartmontool 以显示 tlp-stat 中 S.M.A.R.T. 数据。
+
+```
+$ sudo apt-get install smartmontools
+```
+
+当基于 Ubuntu 的系统的官方软件包过时时,请使用以下 PPA 存储库,该存储库提供最新版本。运行以下命令以使用 PPA 安装 TLP。
+
+```
+$ sudo add-apt-repository ppa:linrunner/tlp
+$ sudo apt-get update
+$ sudo apt-get install tlp
+```
+
+对于基于 Arch Linux 的系统,使用 [Pacman 命令][9] 安装 TLP。
+
+```
+$ sudo pacman -S tlp tlp-rdw
+```
+
+ThinkPad 需要一些附加软件包。
+
+```
+$ pacman -S tp_smapi acpi_call
+```
+
+安装 smartmontool 以显示 tlp-stat 中 S.M.A.R.T. 数据。
+
+```
+$ sudo pacman -S smartmontools
+```
+
+对于基于 Arch Linux 的系统,在启动时启用 TLP 和 TLP-Sleep 服务。
+
+```
+$ sudo systemctl enable tlp.service
+$ sudo systemctl enable tlp-sleep.service
+```
+
+对于基于 Arch Linux 的系统,你还应该屏蔽以下服务以避免冲突,并确保 TLP 的无线电设备切换选项的正确操作。
+
+```
+$ sudo systemctl mask systemd-rfkill.service
+$ sudo systemctl mask systemd-rfkill.socket
+```
+
+对于 RHEL/CentOS 系统,使用 [YUM 命令][10] 安装 TLP。
+
+```
+$ sudo yum install tlp tlp-rdw
+```
+
+安装 smartmontool 以显示 tlp-stat 中 S.M.A.R.T. 数据。
+
+```
+$ sudo yum install smartmontools
+```
+
+对于 openSUSE Leap 系统,使用 [Zypper 命令][11] 安装 TLP。
+
+```
+$ sudo zypper install TLP
+```
+
+安装 smartmontool 以显示 tlp-stat 中 S.M.A.R.T. 数据。
+
+```
+$ sudo zypper install smartmontools
+```
+
+成功安装 TLP 后,使用以下命令启动服务。
+
+```
+$ systemctl start tlp.service
+```
+
+### 使用方法
+
+#### 显示电池信息
+
+```
+$ sudo tlp-stat -b
+或
+$ sudo tlp-stat --battery
+```
+
+```
+--- TLP 1.1 --------------------------------------------
+
++++ Battery Status
+/sys/class/power_supply/BAT0/manufacturer = SMP
+/sys/class/power_supply/BAT0/model_name = L14M4P23
+/sys/class/power_supply/BAT0/cycle_count = (not supported)
+/sys/class/power_supply/BAT0/energy_full_design = 60000 [mWh]
+/sys/class/power_supply/BAT0/energy_full = 48850 [mWh]
+/sys/class/power_supply/BAT0/energy_now = 48850 [mWh]
+/sys/class/power_supply/BAT0/power_now = 0 [mW]
+/sys/class/power_supply/BAT0/status = Full
+
+Charge = 100.0 [%]
+Capacity = 81.4 [%]
+```
+
+#### 显示磁盘信息
+
+```
+$ sudo tlp-stat -d
+或
+$ sudo tlp-stat --disk
+```
+
+```
+--- TLP 1.1 --------------------------------------------
+
++++ Storage Devices
+/dev/sda:
+ Model = WDC WD10SPCX-24HWST1
+ Firmware = 02.01A02
+ APM Level = 128
+ Status = active/idle
+ Scheduler = mq-deadline
+
+ Runtime PM: control = on, autosuspend_delay = (not available)
+
+ SMART info:
+ 4 Start_Stop_Count = 18787
+ 5 Reallocated_Sector_Ct = 0
+ 9 Power_On_Hours = 606 [h]
+ 12 Power_Cycle_Count = 1792
+ 193 Load_Cycle_Count = 25775
+ 194 Temperature_Celsius = 31 [°C]
+
+
++++ AHCI Link Power Management (ALPM)
+/sys/class/scsi_host/host0/link_power_management_policy = med_power_with_dipm
+/sys/class/scsi_host/host1/link_power_management_policy = med_power_with_dipm
+/sys/class/scsi_host/host2/link_power_management_policy = med_power_with_dipm
+/sys/class/scsi_host/host3/link_power_management_policy = med_power_with_dipm
+
++++ AHCI Host Controller Runtime Power Management
+/sys/bus/pci/devices/0000:00:17.0/ata1/power/control = on
+/sys/bus/pci/devices/0000:00:17.0/ata2/power/control = on
+/sys/bus/pci/devices/0000:00:17.0/ata3/power/control = on
+/sys/bus/pci/devices/0000:00:17.0/ata4/power/control = on
+```
+
+#### 显示 PCI 设备信息
+
+```
+$ sudo tlp-stat -e
+或
+$ sudo tlp-stat --pcie
+```
+
+```
+$ sudo tlp-stat -e
+or
+$ sudo tlp-stat --pcie
+
+--- TLP 1.1 --------------------------------------------
+
++++ Runtime Power Management
+Device blacklist = (not configured)
+Driver blacklist = amdgpu nouveau nvidia radeon pcieport
+
+/sys/bus/pci/devices/0000:00:00.0/power/control = auto (0x060000, Host bridge, skl_uncore)
+/sys/bus/pci/devices/0000:00:01.0/power/control = auto (0x060400, PCI bridge, pcieport)
+/sys/bus/pci/devices/0000:00:02.0/power/control = auto (0x030000, VGA compatible controller, i915)
+/sys/bus/pci/devices/0000:00:14.0/power/control = auto (0x0c0330, USB controller, xhci_hcd)
+
+......
+```
+
+#### 显示图形卡信息
+
+```
+$ sudo tlp-stat -g
+或
+$ sudo tlp-stat --graphics
+```
+
+```
+--- TLP 1.1 --------------------------------------------
+
++++ Intel Graphics
+/sys/module/i915/parameters/enable_dc = -1 (use per-chip default)
+/sys/module/i915/parameters/enable_fbc = 1 (enabled)
+/sys/module/i915/parameters/enable_psr = 0 (disabled)
+/sys/module/i915/parameters/modeset = -1 (use per-chip default)
+```
+
+#### 显示处理器信息
+
+```
+$ sudo tlp-stat -p
+或
+$ sudo tlp-stat --processor
+```
+
+```
+--- TLP 1.1 --------------------------------------------
+
++++ Processor
+CPU model = Intel(R) Core(TM) i7-6700HQ CPU @ 2.60GHz
+
+/sys/devices/system/cpu/cpu0/cpufreq/scaling_driver = intel_pstate
+/sys/devices/system/cpu/cpu0/cpufreq/scaling_governor = powersave
+/sys/devices/system/cpu/cpu0/cpufreq/scaling_available_governors = performance powersave
+/sys/devices/system/cpu/cpu0/cpufreq/scaling_min_freq = 800000 [kHz]
+/sys/devices/system/cpu/cpu0/cpufreq/scaling_max_freq = 3500000 [kHz]
+/sys/devices/system/cpu/cpu0/cpufreq/energy_performance_preference = balance_power
+/sys/devices/system/cpu/cpu0/cpufreq/energy_performance_available_preferences = default performance balance_performance balance_power power
+
+......
+
+/sys/devices/system/cpu/intel_pstate/min_perf_pct = 22 [%]
+/sys/devices/system/cpu/intel_pstate/max_perf_pct = 100 [%]
+/sys/devices/system/cpu/intel_pstate/no_turbo = 0
+/sys/devices/system/cpu/intel_pstate/turbo_pct = 33 [%]
+/sys/devices/system/cpu/intel_pstate/num_pstates = 28
+
+x86_energy_perf_policy: program not installed.
+
+/sys/module/workqueue/parameters/power_efficient = Y
+/proc/sys/kernel/nmi_watchdog = 0
+
++++ Undervolting
+PHC kernel not available.
+```
+
+#### 显示系统数据信息
+
+```
+$ sudo tlp-stat -s
+或
+$ sudo tlp-stat --system
+```
+
+```
+--- TLP 1.1 --------------------------------------------
+
++++ System Info
+System = LENOVO Lenovo ideapad Y700-15ISK 80NV
+BIOS = CDCN35WW
+Release = "Manjaro Linux"
+Kernel = 4.19.6-1-MANJARO #1 SMP PREEMPT Sat Dec 1 12:21:26 UTC 2018 x86_64
+/proc/cmdline = BOOT_IMAGE=/boot/vmlinuz-4.19-x86_64 root=UUID=69d9dd18-36be-4631-9ebb-78f05fe3217f rw quiet resume=UUID=a2092b92-af29-4760-8e68-7a201922573b
+Init system = systemd
+Boot mode = BIOS (CSM, Legacy)
+
++++ TLP Status
+State = enabled
+Last run = 11:04:00 IST, 596 sec(s) ago
+Mode = battery
+Power source = battery
+```
+
+#### 显示温度和风扇速度信息
+
+```
+$ sudo tlp-stat -t
+或
+$ sudo tlp-stat --temp
+```
+
+```
+--- TLP 1.1 --------------------------------------------
+
++++ Temperatures
+CPU temp = 36 [°C]
+Fan speed = (not available)
+```
+
+#### 显示 USB 设备数据信息
+
+```
+$ sudo tlp-stat -u
+或
+$ sudo tlp-stat --usb
+```
+
+```
+--- TLP 1.1 --------------------------------------------
+
++++ USB
+Autosuspend = disabled
+Device whitelist = (not configured)
+Device blacklist = (not configured)
+Bluetooth blacklist = disabled
+Phone blacklist = disabled
+WWAN blacklist = enabled
+
+Bus 002 Device 001 ID 1d6b:0003 control = auto, autosuspend_delay_ms = 0 -- Linux Foundation 3.0 root hub (hub)
+Bus 001 Device 003 ID 174f:14e8 control = auto, autosuspend_delay_ms = 2000 -- Syntek (uvcvideo)
+
+......
+```
+
+#### 显示警告信息
+
+```
+$ sudo tlp-stat -w
+或
+$ sudo tlp-stat --warn
+```
+
+```
+--- TLP 1.1 --------------------------------------------
+
+No warnings detected.
+```
+
+#### 状态报告及配置和所有活动的设置
+
+```
+$ sudo tlp-stat
+```
+
+```
+--- TLP 1.1 --------------------------------------------
+
++++ Configured Settings: /etc/default/tlp
+TLP_ENABLE=1
+TLP_DEFAULT_MODE=AC
+TLP_PERSISTENT_DEFAULT=0
+DISK_IDLE_SECS_ON_AC=0
+DISK_IDLE_SECS_ON_BAT=2
+MAX_LOST_WORK_SECS_ON_AC=15
+MAX_LOST_WORK_SECS_ON_BAT=60
+
+......
+
++++ System Info
+System = LENOVO Lenovo ideapad Y700-15ISK 80NV
+BIOS = CDCN35WW
+Release = "Manjaro Linux"
+Kernel = 4.19.6-1-MANJARO #1 SMP PREEMPT Sat Dec 1 12:21:26 UTC 2018 x86_64
+/proc/cmdline = BOOT_IMAGE=/boot/vmlinuz-4.19-x86_64 root=UUID=69d9dd18-36be-4631-9ebb-78f05fe3217f rw quiet resume=UUID=a2092b92-af29-4760-8e68-7a201922573b
+Init system = systemd
+Boot mode = BIOS (CSM, Legacy)
+
++++ TLP Status
+State = enabled
+Last run = 11:04:00 IST, 684 sec(s) ago
+Mode = battery
+Power source = battery
+
++++ Processor
+CPU model = Intel(R) Core(TM) i7-6700HQ CPU @ 2.60GHz
+
+/sys/devices/system/cpu/cpu0/cpufreq/scaling_driver = intel_pstate
+/sys/devices/system/cpu/cpu0/cpufreq/scaling_governor = powersave
+/sys/devices/system/cpu/cpu0/cpufreq/scaling_available_governors = performance powersave
+
+......
+
+/sys/devices/system/cpu/intel_pstate/min_perf_pct = 22 [%]
+/sys/devices/system/cpu/intel_pstate/max_perf_pct = 100 [%]
+/sys/devices/system/cpu/intel_pstate/no_turbo = 0
+/sys/devices/system/cpu/intel_pstate/turbo_pct = 33 [%]
+/sys/devices/system/cpu/intel_pstate/num_pstates = 28
+
+x86_energy_perf_policy: program not installed.
+
+/sys/module/workqueue/parameters/power_efficient = Y
+/proc/sys/kernel/nmi_watchdog = 0
+
++++ Undervolting
+PHC kernel not available.
+
++++ Temperatures
+CPU temp = 42 [°C]
+Fan speed = (not available)
+
++++ File System
+/proc/sys/vm/laptop_mode = 2
+/proc/sys/vm/dirty_writeback_centisecs = 6000
+/proc/sys/vm/dirty_expire_centisecs = 6000
+/proc/sys/vm/dirty_ratio = 20
+/proc/sys/vm/dirty_background_ratio = 10
+
++++ Storage Devices
+/dev/sda:
+ Model = WDC WD10SPCX-24HWST1
+ Firmware = 02.01A02
+ APM Level = 128
+ Status = active/idle
+ Scheduler = mq-deadline
+
+ Runtime PM: control = on, autosuspend_delay = (not available)
+
+ SMART info:
+ 4 Start_Stop_Count = 18787
+ 5 Reallocated_Sector_Ct = 0
+ 9 Power_On_Hours = 606 [h]
+ 12 Power_Cycle_Count = 1792
+ 193 Load_Cycle_Count = 25777
+ 194 Temperature_Celsius = 31 [°C]
+
+
++++ AHCI Link Power Management (ALPM)
+/sys/class/scsi_host/host0/link_power_management_policy = med_power_with_dipm
+/sys/class/scsi_host/host1/link_power_management_policy = med_power_with_dipm
+/sys/class/scsi_host/host2/link_power_management_policy = med_power_with_dipm
+/sys/class/scsi_host/host3/link_power_management_policy = med_power_with_dipm
+
++++ AHCI Host Controller Runtime Power Management
+/sys/bus/pci/devices/0000:00:17.0/ata1/power/control = on
+/sys/bus/pci/devices/0000:00:17.0/ata2/power/control = on
+/sys/bus/pci/devices/0000:00:17.0/ata3/power/control = on
+/sys/bus/pci/devices/0000:00:17.0/ata4/power/control = on
+
++++ PCIe Active State Power Management
+/sys/module/pcie_aspm/parameters/policy = powersave
+
++++ Intel Graphics
+/sys/module/i915/parameters/enable_dc = -1 (use per-chip default)
+/sys/module/i915/parameters/enable_fbc = 1 (enabled)
+/sys/module/i915/parameters/enable_psr = 0 (disabled)
+/sys/module/i915/parameters/modeset = -1 (use per-chip default)
+
++++ Wireless
+bluetooth = on
+wifi = on
+wwan = none (no device)
+
+hci0(btusb) : bluetooth, not connected
+wlp8s0(iwlwifi) : wifi, connected, power management = on
+
++++ Audio
+/sys/module/snd_hda_intel/parameters/power_save = 1
+/sys/module/snd_hda_intel/parameters/power_save_controller = Y
+
++++ Runtime Power Management
+Device blacklist = (not configured)
+Driver blacklist = amdgpu nouveau nvidia radeon pcieport
+
+/sys/bus/pci/devices/0000:00:00.0/power/control = auto (0x060000, Host bridge, skl_uncore)
+/sys/bus/pci/devices/0000:00:01.0/power/control = auto (0x060400, PCI bridge, pcieport)
+/sys/bus/pci/devices/0000:00:02.0/power/control = auto (0x030000, VGA compatible controller, i915)
+
+......
+
++++ USB
+Autosuspend = disabled
+Device whitelist = (not configured)
+Device blacklist = (not configured)
+Bluetooth blacklist = disabled
+Phone blacklist = disabled
+WWAN blacklist = enabled
+
+Bus 002 Device 001 ID 1d6b:0003 control = auto, autosuspend_delay_ms = 0 -- Linux Foundation 3.0 root hub (hub)
+Bus 001 Device 003 ID 174f:14e8 control = auto, autosuspend_delay_ms = 2000 -- Syntek (uvcvideo)
+Bus 001 Device 002 ID 17ef:6053 control = on, autosuspend_delay_ms = 2000 -- Lenovo (usbhid)
+Bus 001 Device 004 ID 8087:0a2b control = auto, autosuspend_delay_ms = 2000 -- Intel Corp. (btusb)
+Bus 001 Device 001 ID 1d6b:0002 control = auto, autosuspend_delay_ms = 0 -- Linux Foundation 2.0 root hub (hub)
+
++++ Battery Status
+/sys/class/power_supply/BAT0/manufacturer = SMP
+/sys/class/power_supply/BAT0/model_name = L14M4P23
+/sys/class/power_supply/BAT0/cycle_count = (not supported)
+/sys/class/power_supply/BAT0/energy_full_design = 60000 [mWh]
+/sys/class/power_supply/BAT0/energy_full = 51690 [mWh]
+/sys/class/power_supply/BAT0/energy_now = 50140 [mWh]
+/sys/class/power_supply/BAT0/power_now = 12185 [mW]
+/sys/class/power_supply/BAT0/status = Discharging
+
+Charge = 97.0 [%]
+Capacity = 86.2 [%]
+```
+
+--------------------------------------------------------------------------------
+
+via: https://www.2daygeek.com/tlp-increase-optimize-linux-laptop-battery-life/
+
+作者:[Magesh Maruthamuthu][a]
+选题:[lujun9972][b]
+译者:[wxy](https://github.com/wxy)
+校对:[wxy](https://github.com/wxy)
+
+本文由 [LCTT](https://github.com/LCTT/TranslateProject) 原创编译,[Linux中国](https://linux.cn/) 荣誉推出
+
+[a]: https://www.2daygeek.com/author/magesh/
+[b]: https://github.com/lujun9972
+[1]: https://www.2daygeek.com/check-laptop-battery-status-and-charging-state-in-linux-terminal/
+[2]: https://www.2daygeek.com/powertop-monitors-laptop-battery-usage-linux/
+[3]: https://www.2daygeek.com/monitor-laptop-battery-charging-state-linux/
+[4]: https://linrunner.de/en/tlp/docs/tlp-linux-advanced-power-management.html
+[5]: https://www.2daygeek.com/category/package-management/
+[6]: https://www.2daygeek.com/dnf-command-examples-manage-packages-fedora-system/
+[7]: https://www.2daygeek.com/apt-get-apt-cache-command-examples-manage-packages-debian-ubuntu-systems/
+[8]: https://www.2daygeek.com/apt-command-examples-manage-packages-debian-ubuntu-systems/
+[9]: https://www.2daygeek.com/pacman-command-examples-manage-packages-arch-linux-system/
+[10]: https://www.2daygeek.com/yum-command-examples-manage-packages-rhel-centos-systems/
+[11]: https://www.2daygeek.com/zypper-command-examples-manage-packages-opensuse-system/
diff --git a/published/201905/20181218 Using Pygame to move your game character around.md b/published/201905/20181218 Using Pygame to move your game character around.md
new file mode 100644
index 0000000000..9605601ad7
--- /dev/null
+++ b/published/201905/20181218 Using Pygame to move your game character around.md
@@ -0,0 +1,354 @@
+[#]: collector: (lujun9972)
+[#]: translator: (cycoe)
+[#]: reviewer: (wxy)
+[#]: publisher: (wxy)
+[#]: url: (https://linux.cn/article-10874-1.html)
+[#]: subject: (Using Pygame to move your game character around)
+[#]: via: (https://opensource.com/article/17/12/game-python-moving-player)
+[#]: author: (Seth Kenlon https://opensource.com/users/seth)
+
+用 Pygame 使你的游戏角色移动起来
+======
+> 在本系列的第四部分,学习如何编写移动游戏角色的控制代码。
+
+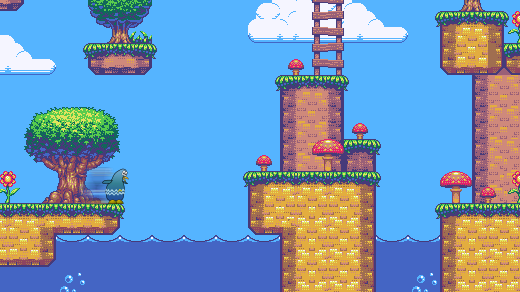
+
+在这个系列的第一篇文章中,我解释了如何使用 Python 创建一个简单的[基于文本的骰子游戏][1]。在第二部分中,我向你们展示了如何从头开始构建游戏,即从 [创建游戏的环境][2] 开始。然后在第三部分,我们[创建了一个玩家妖精][3],并且使它在你的(而不是空的)游戏世界内生成。你可能已经注意到,如果你不能移动你的角色,那么游戏不是那么有趣。在本篇文章中,我们将使用 Pygame 来添加键盘控制,如此一来你就可以控制你的角色的移动。
+
+在 Pygame 中有许多函数可以用来添加(除键盘外的)其他控制,但如果你正在敲击 Python 代码,那么你一定是有一个键盘的,这将成为我们接下来会使用的控制方式。一旦你理解了键盘控制,你可以自己去探索其他选项。
+
+在本系列的第二篇文章中,你已经为退出游戏创建了一个按键,移动角色的(按键)原则也是相同的。但是,使你的角色移动起来要稍微复杂一点。
+
+让我们从简单的部分入手:设置控制器按键。
+
+### 为控制你的玩家妖精设置按键
+
+在 IDLE、Ninja-IDE 或文本编辑器中打开你的 Python 游戏脚本。
+
+因为游戏需要时刻“监听”键盘事件,所以你写的代码需要连续运行。你知道应该把需要在游戏周期中持续运行的代码放在哪里吗?
+
+如果你回答“放在主循环中”,那么你是正确的!记住除非代码在循环中,否则(大多数情况下)它只会运行仅一次。如果它被写在一个从未被使用的类或函数中,它可能根本不会运行。
+
+要使 Python 监听传入的按键,将如下代码添加到主循环。目前的代码还不能产生任何的效果,所以使用 `print` 语句来表示成功的信号。这是一种常见的调试技术。
+
+```
+while main == True:
+ for event in pygame.event.get():
+ if event.type == pygame.QUIT:
+ pygame.quit(); sys.exit()
+ main = False
+
+ if event.type == pygame.KEYDOWN:
+ if event.key == pygame.K_LEFT or event.key == ord('a'):
+ print('left')
+ if event.key == pygame.K_RIGHT or event.key == ord('d'):
+ print('right')
+ if event.key == pygame.K_UP or event.key == ord('w'):
+ print('jump')
+
+ if event.type == pygame.KEYUP:
+ if event.key == pygame.K_LEFT or event.key == ord('a'):
+ print('left stop')
+ if event.key == pygame.K_RIGHT or event.key == ord('d'):
+ print('right stop')
+ if event.key == ord('q'):
+ pygame.quit()
+ sys.exit()
+ main = False
+```
+
+一些人偏好使用键盘字母 `W`、`A`、`S` 和 `D` 来控制玩家角色,而另一些偏好使用方向键。因此确保你包含了两种选项。
+
+注意:当你在编程时,同时考虑所有用户是非常重要的。如果你写代码只是为了自己运行,那么很可能你会成为你写的程序的唯一用户。更重要的是,如果你想找一个通过写代码赚钱的工作,你写的代码就应该让所有人都能运行。给你的用户选择权,比如提供使用方向键或 WASD 的选项,是一个优秀程序员的标志。
+
+使用 Python 启动你的游戏,并在你按下“上下左右”方向键或 `A`、`D` 和 `W` 键的时候查看控制台窗口的输出。
+
+```
+$ python ./your-name_game.py
+ left
+ left stop
+ right
+ right stop
+ jump
+```
+
+这验证了 Pygame 可以正确地检测按键。现在是时候来完成使妖精移动的艰巨任务了。
+
+### 编写玩家移动函数
+
+为了使你的妖精移动起来,你必须为你的妖精创建一个属性代表移动。当你的妖精没有在移动时,这个变量被设为 `0`。
+
+如果你正在为你的妖精设置动画,或者你决定在将来为它设置动画,你还必须跟踪帧来使走路循环保持在轨迹上。
+
+在 `Player` 类中创建如下变量。开头两行作为上下文对照(如果你一直跟着做,你的代码中就已经有这两行),因此只需要添加最后三行:
+
+```
+ def __init__(self):
+ pygame.sprite.Sprite.__init__(self)
+ self.movex = 0 # 沿 X 方向移动
+ self.movey = 0 # 沿 Y 方向移动
+ self.frame = 0 # 帧计数
+```
+
+设置好了这些变量,是时候去为妖精移动编写代码了。
+
+玩家妖精不需要时刻响应控制,有时它并没有在移动。控制妖精的代码,仅仅只是玩家妖精所有能做的事情中的一小部分。在 Python 中,当你想要使一个对象做某件事并独立于剩余其他代码时,你可以将你的新代码放入一个函数。Python 的函数以关键词 `def` 开头,(该关键词)代表了定义函数。
+
+在你的 `Player` 类中创建如下函数,来为你的妖精在屏幕上的位置增加几个像素。现在先不要担心你增加几个像素,这将在后续的代码中确定。
+
+```
+ def control(self,x,y):
+ '''
+ 控制玩家移动
+ '''
+ self.movex += x
+ self.movey += y
+```
+
+为了在 Pygame 中移动妖精,你需要告诉 Python 在新的位置重绘妖精,以及这个新位置在哪里。
+
+因为玩家妖精并不总是在移动,所以更新只需要是 Player 类中的一个函数。将此函数添加前面创建的 `control` 函数之后。
+
+要使妖精看起来像是在行走(或者飞行,或是你的妖精应该做的任何事),你需要在按下适当的键时改变它在屏幕上的位置。要让它在屏幕上移动,你需要将它的位置(由 `self.rect.x` 和 `self.rect.y` 属性指定)重新定义为当前位置加上已应用的任意 `movex` 或 `movey`。(移动的像素数量将在后续进行设置。)
+
+```
+ def update(self):
+ '''
+ 更新妖精位置
+ '''
+ self.rect.x = self.rect.x + self.movex
+```
+
+对 Y 方向做同样的处理:
+
+```
+ self.rect.y = self.rect.y + self.movey
+```
+
+对于动画,在妖精移动时推进动画帧,并使用相应的动画帧作为玩家的图像:
+
+```
+ # 向左移动
+ if self.movex < 0:
+ self.frame += 1
+ if self.frame > 3*ani:
+ self.frame = 0
+ self.image = self.images[self.frame//ani]
+
+ # 向右移动
+ if self.movex > 0:
+ self.frame += 1
+ if self.frame > 3*ani:
+ self.frame = 0
+ self.image = self.images[(self.frame//ani)+4]
+```
+
+通过设置一个变量来告诉代码为你的妖精位置增加多少像素,然后在触发你的玩家妖精的函数时使用这个变量。
+
+首先,在你的设置部分创建这个变量。在如下代码中,开头两行是上下文对照,因此只需要在你的脚本中增加第三行代码:
+
+```
+player_list = pygame.sprite.Group()
+player_list.add(player)
+steps = 10 # 移动多少个像素
+```
+
+现在你已经有了适当的函数和变量,使用你的按键来触发函数并将变量传递给你的妖精。
+
+为此,将主循环中的 `print` 语句替换为玩家妖精的名字(`player`)、函数(`.control`)以及你希望玩家妖精在每个循环中沿 X 轴和 Y 轴移动的步数。
+
+```
+ if event.type == pygame.KEYDOWN:
+ if event.key == pygame.K_LEFT or event.key == ord('a'):
+ player.control(-steps,0)
+ if event.key == pygame.K_RIGHT or event.key == ord('d'):
+ player.control(steps,0)
+ if event.key == pygame.K_UP or event.key == ord('w'):
+ print('jump')
+
+ if event.type == pygame.KEYUP:
+ if event.key == pygame.K_LEFT or event.key == ord('a'):
+ player.control(steps,0)
+ if event.key == pygame.K_RIGHT or event.key == ord('d'):
+ player.control(-steps,0)
+ if event.key == ord('q'):
+ pygame.quit()
+ sys.exit()
+ main = False
+```
+
+记住,`steps` 变量代表了当一个按键被按下时,你的妖精会移动多少个像素。如果当你按下 `D` 或右方向键时,你的妖精的位置增加了 10 个像素。那么当你停止按下这个键时,你必须(将 `step`)减 10(`-steps`)来使你的妖精的动量回到 0。
+
+现在尝试你的游戏。注意:它不会像你预想的那样运行。
+
+为什么你的妖精仍无法移动?因为主循环还没有调用 `update` 函数。
+
+将如下代码加入到你的主循环中来告诉 Python 更新你的玩家妖精的位置。增加带注释的那行:
+
+```
+ player.update() # 更新玩家位置
+ player_list.draw(world)
+ pygame.display.flip()
+ clock.tick(fps)
+```
+
+再次启动你的游戏来见证你的玩家妖精在你的命令下在屏幕上来回移动。现在还没有垂直方向的移动,因为这部分函数会被重力控制,不过这是另一篇文章中的课程了。
+
+与此同时,如果你拥有一个摇杆,你可以尝试阅读 Pygame 中 [joystick][4] 模块相关的文档,看看你是否能通过这种方式让你的妖精移动起来。或者,看看你是否能通过[鼠标][5]与你的妖精互动。
+
+最重要的是,玩的开心!
+
+### 本教程中用到的所有代码
+
+为了方便查阅,以下是目前本系列文章用到的所有代码。
+
+```
+#!/usr/bin/env python3
+# 绘制世界
+# 添加玩家和玩家控制
+# 添加玩家移动控制
+
+# GNU All-Permissive License
+# Copying and distribution of this file, with or without modification,
+# are permitted in any medium without royalty provided the copyright
+# notice and this notice are preserved. This file is offered as-is,
+# without any warranty.
+
+import pygame
+import sys
+import os
+
+'''
+Objects
+'''
+
+class Player(pygame.sprite.Sprite):
+ '''
+ 生成玩家
+ '''
+ def __init__(self):
+ pygame.sprite.Sprite.__init__(self)
+ self.movex = 0
+ self.movey = 0
+ self.frame = 0
+ self.images = []
+ for i in range(1,5):
+ img = pygame.image.load(os.path.join('images','hero' + str(i) + '.png')).convert()
+ img.convert_alpha()
+ img.set_colorkey(ALPHA)
+ self.images.append(img)
+ self.image = self.images[0]
+ self.rect = self.image.get_rect()
+
+ def control(self,x,y):
+ '''
+ 控制玩家移动
+ '''
+ self.movex += x
+ self.movey += y
+
+ def update(self):
+ '''
+ 更新妖精位置
+ '''
+
+ self.rect.x = self.rect.x + self.movex
+ self.rect.y = self.rect.y + self.movey
+
+ # 向左移动
+ if self.movex < 0:
+ self.frame += 1
+ if self.frame > 3*ani:
+ self.frame = 0
+ self.image = self.images[self.frame//ani]
+
+ # 向右移动
+ if self.movex > 0:
+ self.frame += 1
+ if self.frame > 3*ani:
+ self.frame = 0
+ self.image = self.images[(self.frame//ani)+4]
+
+
+'''
+设置
+'''
+worldx = 960
+worldy = 720
+
+fps = 40 # 帧刷新率
+ani = 4 # 动画循环
+clock = pygame.time.Clock()
+pygame.init()
+main = True
+
+BLUE = (25,25,200)
+BLACK = (23,23,23 )
+WHITE = (254,254,254)
+ALPHA = (0,255,0)
+
+world = pygame.display.set_mode([worldx,worldy])
+backdrop = pygame.image.load(os.path.join('images','stage.png')).convert()
+backdropbox = world.get_rect()
+player = Player() # 生成玩家
+player.rect.x = 0
+player.rect.y = 0
+player_list = pygame.sprite.Group()
+player_list.add(player)
+steps = 10 # 移动速度
+
+'''
+主循环
+'''
+while main == True:
+ for event in pygame.event.get():
+ if event.type == pygame.QUIT:
+ pygame.quit(); sys.exit()
+ main = False
+
+ if event.type == pygame.KEYDOWN:
+ if event.key == pygame.K_LEFT or event.key == ord('a'):
+ player.control(-steps,0)
+ if event.key == pygame.K_RIGHT or event.key == ord('d'):
+ player.control(steps,0)
+ if event.key == pygame.K_UP or event.key == ord('w'):
+ print('jump')
+
+ if event.type == pygame.KEYUP:
+ if event.key == pygame.K_LEFT or event.key == ord('a'):
+ player.control(steps,0)
+ if event.key == pygame.K_RIGHT or event.key == ord('d'):
+ player.control(-steps,0)
+ if event.key == ord('q'):
+ pygame.quit()
+ sys.exit()
+ main = False
+
+# world.fill(BLACK)
+ world.blit(backdrop, backdropbox)
+ player.update()
+ player_list.draw(world) # 更新玩家位置
+ pygame.display.flip()
+ clock.tick(fps)
+```
+
+你已经学了很多,但还仍有许多可以做。在接下来的几篇文章中,你将实现添加敌方妖精、模拟重力等等。与此同时,练习 Python 吧!
+
+--------------------------------------------------------------------------------
+
+via: https://opensource.com/article/17/12/game-python-moving-player
+
+作者:[Seth Kenlon][a]
+选题:[lujun9972][b]
+译者:[cycoe](https://github.com/cycoe)
+校对:[wxy](https://github.com/wxy)
+
+本文由 [LCTT](https://github.com/LCTT/TranslateProject) 原创编译,[Linux中国](https://linux.cn/) 荣誉推出
+
+[a]: https://opensource.com/users/seth
+[b]: https://github.com/lujun9972
+[1]: https://linux.cn/article-9071-1.html
+[2]: https://linux.cn/article-10850-1.html
+[3]: https://linux.cn/article-10858-1.html
+[4]: http://pygame.org/docs/ref/joystick.html
+[5]: http://pygame.org/docs/ref/mouse.html#module-pygame.mouse
diff --git a/published/201905/20190107 Aliases- To Protect and Serve.md b/published/201905/20190107 Aliases- To Protect and Serve.md
new file mode 100644
index 0000000000..60299f61c5
--- /dev/null
+++ b/published/201905/20190107 Aliases- To Protect and Serve.md
@@ -0,0 +1,172 @@
+[#]: collector: (lujun9972)
+[#]: translator: (wxy)
+[#]: reviewer: (wxy)
+[#]: publisher: (wxy)
+[#]: url: (https://linux.cn/article-10918-1.html)
+[#]: subject: (Aliases: To Protect and Serve)
+[#]: via: (https://www.linux.com/blog/learn/2019/1/aliases-protect-and-serve)
+[#]: author: (Paul Brown https://www.linux.com/users/bro66)
+
+命令别名:保护和服务
+======
+
+> Linux shell 允许你将命令彼此链接在一起,一次触发执行复杂的操作,并且可以对此创建别名作为快捷方式。
+
+
+
+让我们将继续我们的别名系列。到目前为止,你可能已经阅读了我们的[关于别名的第一篇文章][1],并且应该非常清楚它们是如何为你省去很多麻烦的最简单方法。例如,你已经看到它们帮助我们减少了输入,让我们看看别名派上用场的其他几个案例。
+
+### 别名即快捷方式
+
+Linux shell 最美妙的事情之一是可以使用数以万计的选项和把命令连接在一起执行真正复杂的操作。好吧,也许这种美丽是在旁观者的眼中的,但是我们觉得这个功能很实用。
+
+不利的一面是,你经常需要记得难以记忆或难以打字出来的命令组合。比如说硬盘上的空间非常宝贵,而你想要做一些清洁工作。你的第一步可能是寻找隐藏在你的家目录里的东西。你可以用来判断的一个标准是查找不再使用的内容。`ls` 可以帮助你:
+
+```
+ls -lct
+```
+
+上面的命令显示了每个文件和目录的详细信息(`-l`),并显示了每一项上次访问的时间(`-c`),然后它按从最近访问到最少访问的顺序排序这个列表(`-t`)。
+
+这难以记住吗?你可能不会每天都使用 `-c` 和 `-t` 选项,所以也许是吧。无论如何,定义一个别名,如:
+
+```
+alias lt='ls -lct'
+```
+
+会更容易一些。
+
+然后,你也可能希望列表首先显示最旧的文件:
+
+```
+alias lo='lt -F | tac'
+```
+
+![aliases][3]
+
+*图 1:使用 lt 和 lo 别名。*
+
+这里有一些有趣的事情。首先,我们使用别名(`lt`)来创建另一个别名 —— 这是完全可以的。其次,我们将一个新参数传递给 `lt`(后者又通过 `lt` 别名的定义传递给了 `ls`)。
+
+`-F` 选项会将特殊符号附加到项目的名称后,以便更好地区分常规文件(没有符号)和可执行文件(附加了 `*`)、目录文件(以 `/` 结尾),以及所有链接文件、符号链接文件(以 `@` 符号结尾)等等。`-F` 选项是当你回归到单色终端的日子里,没有其他方法可以轻松看到列表项之间的差异时用的。在这里使用它是因为当你将输出从 `lt` 传递到 `tac` 时,你会丢失 `ls` 的颜色。
+
+第三件我们需要注意的事情是我们使用了管道。管道用于你将一个命令的输出传递给另外一个命令时。第二个命令可以使用这些输出作为它的输入。在包括 Bash 在内的许多 shell 里,你可以使用管道符(`|`) 来做传递。
+
+在这里,你将来自 `lt -F` 的输出导给 `tac`。`tac` 这个命令有点玩笑的意思,你或许听说过 `cat` 命令,它名义上用于将文件彼此连接(con`cat`),而在实践中,它被用于将一个文件的内容打印到终端。`tac` 做的事情一样,但是它是以逆序将接收到的内容输出出来。明白了吗?`cat` 和 `tac`,技术人有时候也挺有趣的。
+
+`cat` 和 `tac` 都能输出通过管道传递过来的内容,在这里,也就是一个按时间顺序排序的文件列表。
+
+那么,在有些离题之后,最终我们得到的就是这个列表将当前目录中的文件和目录以新鲜度的逆序列出(即老的在前)。
+
+最后你需要注意的是,当在当前目录或任何目录运行 `lt` 时:
+
+```
+# 这可以工作:
+lt
+# 这也可以:
+lt /some/other/directory
+```
+
+……而 `lo` 只能在当前目录奏效:
+
+```
+# 这可工作:
+lo
+# 而这不行:
+lo /some/other/directory
+```
+
+这是因为 Bash 会展开别名的组分。当你键入:
+
+```
+lt /some/other/directory
+```
+
+Bash 实际上运行的是:
+
+```
+ls -lct /some/other/directory
+```
+
+这是一个有效的 Bash 命令。
+
+而当你键入:
+
+```
+lo /some/other/directory
+```
+
+Bash 试图运行:
+
+```
+ls -lct -F | tac /some/other/directory
+```
+
+这不是一个有效的命令,主要是因为 `/some/other/directory` 是个目录,而 `cat` 和 `tac` 不能用于目录。
+
+### 更多的别名快捷方式
+
+ * `alias lll='ls -R'` 会打印出目录的内容,并深入到子目录里面打印子目录的内容,以及子目录的子目录,等等。这是一个查看一个目录下所有内容的方式。
+ * `mkdir='mkdir -pv'` 可以让你一次性创建目录下的目录。按照 `mkdir` 的基本形式,要创建一个包含子目录的目录,你必须这样:
+
+```
+mkdir newdir
+mkdir newdir/subdir
+```
+
+或这样:
+
+```
+mkdir -p newdir/subdir
+```
+
+而用这个别名你将只需要这样就行:
+
+```
+mkdir newdir/subdir
+```
+
+你的新 `mkdir` 也会告诉你创建子目录时都做了什么。
+
+### 别名也是一种保护
+
+别名的另一个好处是它可以作为防止你意外地删除或覆写已有的文件的保护措施。你可能听说过这个 Linux 新用户的传言,当他们以 root 身份运行:
+
+```
+rm -rf /
+```
+
+整个系统就爆了。而决定输入如下命令的用户:
+
+```
+rm -rf /some/directory/ *
+```
+
+就很好地干掉了他们的家目录的全部内容。这里不小心键入的目录和 `*` 之间的那个空格有时候很容易就会被忽视掉。
+
+这两种情况我们都可以通过 `alias rm='rm -i'` 别名来避免。`-i` 选项会使 `rm` 询问用户是否真的要做这个操作,在你对你的文件系统做出不可弥补的损失之前给你第二次机会。
+
+对于 `cp` 也是一样,它能够覆盖一个文件而不会给你任何提示。创建一个类似 `alias cp='cp -i'` 来保持安全吧。
+
+### 下一次
+
+我们越来越深入到了脚本领域,下一次,我们将沿着这个方向,看看如何在命令行组合命令以给你真正的乐趣,并可靠地解决系统管理员每天面临的问题。
+
+
+--------------------------------------------------------------------------------
+
+via: https://www.linux.com/blog/learn/2019/1/aliases-protect-and-serve
+
+作者:[Paul Brown][a]
+选题:[lujun9972][b]
+译者:[wxy](https://github.com/wxy)
+校对:[wxy](https://github.com/wxy)
+
+本文由 [LCTT](https://github.com/LCTT/TranslateProject) 原创编译,[Linux中国](https://linux.cn/) 荣誉推出
+
+[a]: https://www.linux.com/users/bro66
+[b]: https://github.com/lujun9972
+[1]: https://linux.cn/article-10377-1.html
+[2]: https://www.linux.com/files/images/fig01png-0
+[3]: https://www.linux.com/sites/lcom/files/styles/rendered_file/public/fig01_0.png?itok=crqTm_va (aliases)
+[4]: https://www.linux.com/licenses/category/used-permission
diff --git a/published/20190307 How to Restart a Network in Ubuntu -Beginner-s Tip.md b/published/201905/20190307 How to Restart a Network in Ubuntu -Beginner-s Tip.md
similarity index 100%
rename from published/20190307 How to Restart a Network in Ubuntu -Beginner-s Tip.md
rename to published/201905/20190307 How to Restart a Network in Ubuntu -Beginner-s Tip.md
diff --git a/published/201905/20190308 Virtual filesystems in Linux- Why we need them and how they work.md b/published/201905/20190308 Virtual filesystems in Linux- Why we need them and how they work.md
new file mode 100644
index 0000000000..8ffd7c6ab0
--- /dev/null
+++ b/published/201905/20190308 Virtual filesystems in Linux- Why we need them and how they work.md
@@ -0,0 +1,210 @@
+[#]: collector: (lujun9972)
+[#]: translator: (wxy)
+[#]: reviewer: (wxy)
+[#]: publisher: (wxy)
+[#]: url: (https://linux.cn/article-10884-1.html)
+[#]: subject: (Virtual filesystems in Linux: Why we need them and how they work)
+[#]: via: (https://opensource.com/article/19/3/virtual-filesystems-linux)
+[#]: author: (Alison Chariken )
+
+详解 Linux 中的虚拟文件系统
+======
+
+> 虚拟文件系统是一种神奇的抽象,它使得 “一切皆文件” 哲学在 Linux 中成为了可能。
+
+
+
+什么是文件系统?根据早期的 Linux 贡献者和作家 [Robert Love][1] 所说,“文件系统是一个遵循特定结构的数据的分层存储。” 不过,这种描述也同样适用于 VFAT(虚拟文件分配表)、Git 和[Cassandra][2](一种 [NoSQL 数据库][3])。那么如何区别文件系统呢?
+
+### 文件系统基础概念
+
+Linux 内核要求文件系统必须是实体,它还必须在持久对象上实现 `open()`、`read()` 和 `write()` 方法,并且这些实体需要有与之关联的名字。从 [面向对象编程][4] 的角度来看,内核将通用文件系统视为一个抽象接口,这三大函数是“虚拟”的,没有默认定义。因此,内核的默认文件系统实现被称为虚拟文件系统(VFS)。
+
+![][5]
+
+*如果我们能够 `open()`、`read()` 和 `write()`,它就是一个文件,如这个主控台会话所示。*
+
+VFS 是著名的类 Unix 系统中 “一切皆文件” 概念的基础。让我们看一下它有多奇怪,上面的小小演示体现了字符设备 `/dev/console` 实际的工作。该图显示了一个在虚拟电传打字控制台(tty)上的交互式 Bash 会话。将一个字符串发送到虚拟控制台设备会使其显示在虚拟屏幕上。而 VFS 甚至还有其它更奇怪的属性。例如,它[可以在其中寻址][6]。
+
+我们熟悉的文件系统如 ext4、NFS 和 /proc 都在名为 [file_operations] [7] 的 C 语言数据结构中提供了三大函数的定义。此外,个别的文件系统会以熟悉的面向对象的方式扩展和覆盖了 VFS 功能。正如 Robert Love 指出的那样,VFS 的抽象使 Linux 用户可以轻松地将文件复制到(或复制自)外部操作系统或抽象实体(如管道),而无需担心其内部数据格式。在用户空间这一侧,通过系统调用,进程可以使用文件系统方法之一 `read()` 从文件复制到内核的数据结构中,然后使用另一种文件系统的方法 `write()` 输出数据。
+
+属于 VFS 基本类型的函数定义本身可以在内核源代码的 [fs/*.c 文件][8] 中找到,而 `fs/` 的子目录中包含了特定的文件系统。内核还包含了类似文件系统的实体,例如 cgroup、`/dev` 和 tmpfs,在引导过程的早期需要它们,因此定义在内核的 `init/` 子目录中。请注意,cgroup、`/dev` 和 tmpfs 不会调用 `file_operations` 的三大函数,而是直接读取和写入内存。
+
+下图大致说明了用户空间如何访问通常挂载在 Linux 系统上的各种类型文件系统。像管道、dmesg 和 POSIX 时钟这样的结构在此图中未显示,它们也实现了 `struct file_operations`,而且其访问也要通过 VFS 层。
+
+![How userspace accesses various types of filesystems][9]
+
+VFS 是个“垫片层”,位于系统调用和特定 `file_operations` 的实现(如 ext4 和 procfs)之间。然后,`file_operations` 函数可以与特定于设备的驱动程序或内存访问器进行通信。tmpfs、devtmpfs 和 cgroup 不使用 `file_operations` 而是直接访问内存。
+
+VFS 的存在促进了代码重用,因为与文件系统相关的基本方法不需要由每种文件系统类型重新实现。代码重用是一种被广泛接受的软件工程最佳实践!唉,但是如果重用的代码[引入了严重的错误][10],那么继承常用方法的所有实现都会受到影响。
+
+### /tmp:一个小提示
+
+找出系统中存在的 VFS 的简单方法是键入 `mount | grep -v sd | grep -v :/`,在大多数计算机上,它将列出所有未驻留在磁盘上,同时也不是 NFS 的已挂载文件系统。其中一个列出的 VFS 挂载肯定是 `/tmp`,对吧?
+
+![Man with shocked expression][11]
+
+*谁都知道把 /tmp 放在物理存储设备上简直是疯了!图片:*
+
+为什么把 `/tmp` 留在存储设备上是不可取的?因为 `/tmp` 中的文件是临时的(!),并且存储设备比内存慢,所以创建了 tmpfs 这种文件系统。此外,比起内存,物理设备频繁写入更容易磨损。最后,`/tmp` 中的文件可能包含敏感信息,因此在每次重新启动时让它们消失是一项功能。
+
+不幸的是,默认情况下,某些 Linux 发行版的安装脚本仍会在存储设备上创建 /tmp。如果你的系统出现这种情况,请不要绝望。按照一直优秀的 [Arch Wiki][12] 上的简单说明来解决问题就行,记住分配给 tmpfs 的内存就不能用于其他目的了。换句话说,包含了大文件的庞大的 tmpfs 可能会让系统耗尽内存并崩溃。
+
+另一个提示:编辑 `/etc/fstab` 文件时,请务必以换行符结束,否则系统将无法启动。(猜猜我怎么知道。)
+
+### /proc 和 /sys
+
+除了 `/tmp` 之外,大多数 Linux 用户最熟悉的 VFS 是 `/proc` 和 `/sys`。(`/dev` 依赖于共享内存,而没有 `file_operations` 结构)。为什么有两种呢?让我们来看看更多细节。
+
+procfs 为用户空间提供了内核及其控制的进程的瞬时状态的快照。在 `/proc` 中,内核发布有关其提供的设施的信息,如中断、虚拟内存和调度程序。此外,`/proc/sys` 是存放可以通过 [sysctl 命令][13]配置的设置的地方,可供用户空间访问。单个进程的状态和统计信息在 `/proc/` 目录中报告。
+
+![Console][14]
+
+*/proc/meminfo 是一个空文件,但仍包含有价值的信息。*
+
+`/proc` 文件的行为说明了 VFS 可以与磁盘上的文件系统不同。一方面,`/proc/meminfo` 包含了可由命令 `free` 展现出来的信息。另一方面,它还是空的!怎么会这样?这种情况让人联想起康奈尔大学物理学家 N. David Mermin 在 1985 年写的一篇名为《[没有人看见月亮的情况吗?][15]现实和量子理论》。事实是当进程从 `/proc` 请求数据时内核再收集有关内存的统计信息,而且当没有人查看它时,`/proc` 中的文件实际上没有任何内容。正如 [Mermin 所说][16],“这是一个基本的量子学说,一般来说,测量不会揭示被测属性的预先存在的价值。”(关于月球的问题的答案留作练习。)
+
+![Full moon][17]
+
+*当没有进程访问它们时,/proc 中的文件为空。([来源][18])*
+
+procfs 的空文件是有道理的,因为那里可用的信息是动态的。sysfs 的情况则不同。让我们比较一下 `/proc` 与 `/sys` 中不为空的文件数量。
+
+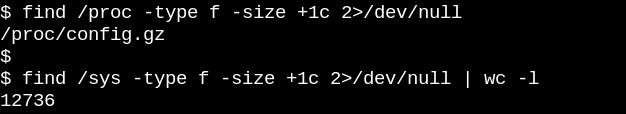
+
+procfs 只有一个不为空的文件,即导出的内核配置,这是一个例外,因为每次启动只需要生成一次。另一方面,`/sys` 有许多更大一些的文件,其中大多数由一页内存组成。通常,sysfs 文件只包含一个数字或字符串,与通过读取 `/proc/meminfo` 等文件生成的信息表格形成鲜明对比。
+
+sysfs 的目的是将内核称为 “kobject” 的可读写属性公开给用户空间。kobject 的唯一目的是引用计数:当删除对 kobject 的最后一个引用时,系统将回收与之关联的资源。然而,`/sys` 构成了内核著名的“[到用户空间的稳定 ABI][19]”,它的大部分内容[在任何情况下都没有人能“破坏”][20]。但这并不意味着 sysfs 中的文件是静态,这与易失性对象的引用计数相反。
+
+内核的稳定 ABI 限制了 `/sys` 中可能出现的内容,而不是任何给定时刻实际存在的内容。列出 sysfs 中文件的权限可以了解如何设置或读取设备、模块、文件系统等的可配置、可调参数。逻辑上强调 procfs 也是内核稳定 ABI 的一部分的结论,尽管内核的[文档][19]没有明确说明。
+
+![Console][21]
+
+*sysfs 中的文件确切地描述了实体的每个属性,并且可以是可读的、可写的,或两者兼而有之。文件中的“0”表示 SSD 不可移动的存储设备。*
+
+### 用 eBPF 和 bcc 工具一窥 VFS 内部
+
+了解内核如何管理 sysfs 文件的最简单方法是观察它的运行情况,在 ARM64 或 x86_64 上观看的最简单方法是使用 eBPF。eBPF(扩展的伯克利数据包过滤器)由[在内核中运行的虚拟机][22]组成,特权用户可以从命令行进行查询。内核源代码告诉读者内核可以做什么;而在一个启动的系统上运行 eBPF 工具会显示内核实际上做了什么。
+
+令人高兴的是,通过 [bcc][23] 工具入门使用 eBPF 非常容易,这些工具在[主要 Linux 发行版的软件包][24] 中都有,并且已经由 Brendan Gregg [给出了充分的文档说明][25]。bcc 工具是带有小段嵌入式 C 语言片段的 Python 脚本,这意味着任何对这两种语言熟悉的人都可以轻松修改它们。据当前统计,[bcc/tools 中有 80 个 Python 脚本][26],使得系统管理员或开发人员很有可能能够找到与她/他的需求相关的已有脚本。
+
+要了解 VFS 在正在运行中的系统上的工作情况,请尝试使用简单的 [vfscount][27] 或 [vfsstat][28] 脚本,这可以看到每秒都会发生数十次对 `vfs_open()` 及其相关的调用。
+
+![Console - vfsstat.py][29]
+
+*vfsstat.py 是一个带有嵌入式 C 片段的 Python 脚本,它只是计数 VFS 函数调用。*
+
+作为一个不太重要的例子,让我们看一下在运行的系统上插入 USB 记忆棒时 sysfs 中会发生什么。
+
+![Console when USB is inserted][30]
+
+*用 eBPF 观察插入 USB 记忆棒时 /sys 中会发生什么,简单的和复杂的例子。*
+
+在上面的第一个简单示例中,只要 `sysfs_create_files()` 命令运行,[trace.py][31] bcc 工具脚本就会打印出一条消息。我们看到 `sysfs_create_files()` 由一个 kworker 线程启动,以响应 USB 棒的插入事件,但是它创建了什么文件?第二个例子说明了 eBPF 的强大能力。这里,`trace.py` 正在打印内核回溯(`-K` 选项)以及 `sysfs_create_files()` 创建的文件的名称。单引号内的代码段是一些 C 源代码,包括一个易于识别的格式字符串,所提供的 Python 脚本[引入 LLVM 即时编译器(JIT)][32] 来在内核虚拟机内编译和执行它。必须在第二个命令中重现完整的 `sysfs_create_files()` 函数签名,以便格式字符串可以引用其中一个参数。在此 C 片段中出错会导致可识别的 C 编译器错误。例如,如果省略 `-I` 参数,则结果为“无法编译 BPF 文本”。熟悉 C 或 Python 的开发人员会发现 bcc 工具易于扩展和修改。
+
+插入 USB 记忆棒后,内核回溯显示 PID 7711 是一个 kworker 线程,它在 sysfs 中创建了一个名为 `events` 的文件。使用 `sysfs_remove_files()` 进行相应的调用表明,删除 USB 记忆棒会导致删除该 `events` 文件,这与引用计数的想法保持一致。在 USB 棒插入期间(未显示)在 eBPF 中观察 `sysfs_create_link()` 表明创建了不少于 48 个符号链接。
+
+无论如何,`events` 文件的目的是什么?使用 [cscope][33] 查找函数 [`__device_add_disk()`][34] 显示它调用 `disk_add_events()`,并且可以将 “media_change” 或 “eject_request” 写入到该文件。这里,内核的块层通知用户空间该 “磁盘” 的出现和消失。考虑一下这种检查 USB 棒的插入的工作原理的方法与试图仅从源头中找出该过程的速度有多快。
+
+### 只读根文件系统使得嵌入式设备成为可能
+
+确实,没有人通过拔出电源插头来关闭服务器或桌面系统。为什么?因为物理存储设备上挂载的文件系统可能有挂起的(未完成的)写入,并且记录其状态的数据结构可能与写入存储器的内容不同步。当发生这种情况时,系统所有者将不得不在下次启动时等待 [fsck 文件系统恢复工具][35] 运行完成,在最坏的情况下,实际上会丢失数据。
+
+然而,狂热爱好者会听说许多物联网和嵌入式设备,如路由器、恒温器和汽车现在都运行着 Linux。许多这些设备几乎完全没有用户界面,并且没有办法干净地让它们“解除启动”。想一想启动电池耗尽的汽车,其中[运行 Linux 的主机设备][36] 的电源会不断加电断电。当引擎最终开始运行时,系统如何在没有长时间 fsck 的情况下启动呢?答案是嵌入式设备依赖于[只读根文件系统][37](简称 ro-rootfs)。
+
+![Photograph of a console][38]
+
+*ro-rootfs 是嵌入式系统不经常需要 fsck 的原因。 来源:*
+
+ro-rootfs 提供了许多优点,虽然这些优点不如耐用性那么显然。一个是,如果 Linux 进程不可以写入,那么恶意软件也无法写入 `/usr` 或 `/lib`。另一个是,基本上不可变的文件系统对于远程设备的现场支持至关重要,因为支持人员拥有理论上与现场相同的本地系统。也许最重要(但也是最微妙)的优势是 ro-rootfs 迫使开发人员在项目的设计阶段就决定好哪些系统对象是不可变的。处理 ro-rootfs 可能经常是不方便甚至是痛苦的,[编程语言中的常量变量][39]经常就是这样,但带来的好处很容易偿还这种额外的开销。
+
+对于嵌入式开发人员,创建只读根文件系统确实需要做一些额外的工作,而这正是 VFS 的用武之地。Linux 需要 `/var` 中的文件可写,此外,嵌入式系统运行的许多流行应用程序会尝试在 `$HOME` 中创建配置的点文件。放在家目录中的配置文件的一种解决方案通常是预生成它们并将它们构建到 rootfs 中。对于 `/var`,一种方法是将其挂载在单独的可写分区上,而 `/` 本身以只读方式挂载。使用绑定或叠加挂载是另一种流行的替代方案。
+
+### 绑定和叠加挂载以及在容器中的使用
+
+运行 [man mount][40] 是了解绑定挂载和叠加挂载的最好办法,这种方法使得嵌入式开发人员和系统管理员能够在一个路径位置创建文件系统,然后以另外一个路径将其提供给应用程序。对于嵌入式系统,这代表着可以将文件存储在 `/var` 中的不可写闪存设备上,但是在启动时将 tmpfs 中的路径叠加挂载或绑定挂载到 `/var` 路径上,这样应用程序就可以在那里随意写它们的内容了。下次加电时,`/var` 中的变化将会消失。叠加挂载为 tmpfs 和底层文件系统提供了联合,允许对 ro-rootfs 中的现有文件进行直接修改,而绑定挂载可以使新的空 tmpfs 目录在 ro-rootfs 路径中显示为可写。虽然叠加文件系统是一种适当的文件系统类型,而绑定挂载由 [VFS 命名空间工具][41] 实现的。
+
+根据叠加挂载和绑定挂载的描述,没有人会对 [Linux 容器][42] 中大量使用它们感到惊讶。让我们通过运行 bcc 的 `mountsnoop` 工具监视当使用 [systemd-nspawn][43] 启动容器时会发生什么:
+
+![Console - system-nspawn invocation][44]
+
+*在 mountsnoop.py 运行的同时,system-nspawn 调用启动容器。*
+
+让我们看看发生了什么:
+
+![Console - Running mountsnoop][45]
+
+*在容器 “启动” 期间运行 `mountsnoop` 可以看到容器运行时很大程度上依赖于绑定挂载。(仅显示冗长输出的开头)*
+
+这里,`systemd-nspawn` 将主机的 procfs 和 sysfs 中的选定文件按其 rootfs 中的路径提供给容器。除了设置绑定挂载时的 `MS_BIND` 标志之外,`mount` 系统调用的一些其它标志用于确定主机命名空间和容器中的更改之间的关系。例如,绑定挂载可以将 `/proc` 和 `/sys` 中的更改传播到容器,也可以隐藏它们,具体取决于调用。
+
+### 总结
+
+理解 Linux 内部结构看似是一项不可能完成的任务,因为除了 Linux 用户空间应用程序和 glibc 这样的 C 库中的系统调用接口,内核本身也包含大量代码。取得进展的一种方法是阅读一个内核子系统的源代码,重点是理解面向用户空间的系统调用和头文件以及主要的内核内部接口,这里以 `file_operations` 表为例。`file_operations` 使得“一切都是文件”得以可以实际工作,因此掌握它们收获特别大。顶级 `fs/` 目录中的内核 C 源文件构成了虚拟文件系统的实现,虚拟文件系统是支持流行的文件系统和存储设备的广泛且相对简单的互操作性的垫片层。通过 Linux 命名空间进行绑定挂载和覆盖挂载是 VFS 魔术,它使容器和只读根文件系统成为可能。结合对源代码的研究,eBPF 内核工具及其 bcc 接口使得探测内核比以往任何时候都更简单。
+
+非常感谢 [Akkana Peck][46] 和 [Michael Eager][47] 的评论和指正。
+
+Alison Chaiken 也于 3 月 7 日至 10 日在加利福尼亚州帕萨迪纳举行的第 17 届南加州 Linux 博览会([SCaLE 17x][49])上演讲了[本主题][48]。
+
+--------------------------------------------------------------------------------
+
+via: https://opensource.com/article/19/3/virtual-filesystems-linux
+
+作者:[Alison Chariken][a]
+选题:[lujun9972][b]
+译者:[wxy](https://github.com/wxy)
+校对:[wxy](https://github.com/wxy)
+
+本文由 [LCTT](https://github.com/LCTT/TranslateProject) 原创编译,[Linux中国](https://linux.cn/) 荣誉推出
+
+[a]: https://opensource.com/users/chaiken
+[b]: https://github.com/lujun9972
+[1]: https://www.pearson.com/us/higher-education/program/Love-Linux-Kernel-Development-3rd-Edition/PGM202532.html
+[2]: http://cassandra.apache.org/
+[3]: https://en.wikipedia.org/wiki/NoSQL
+[4]: http://lwn.net/Articles/444910/
+[5]: https://opensource.com/sites/default/files/uploads/virtualfilesystems_1-console.png (Console)
+[6]: https://lwn.net/Articles/22355/
+[7]: https://git.kernel.org/pub/scm/linux/kernel/git/torvalds/linux.git/tree/include/linux/fs.h
+[8]: https://git.kernel.org/pub/scm/linux/kernel/git/torvalds/linux.git/tree/fs
+[9]: https://opensource.com/sites/default/files/uploads/virtualfilesystems_2-shim-layer.png (How userspace accesses various types of filesystems)
+[10]: https://lwn.net/Articles/774114/
+[11]: https://opensource.com/sites/default/files/uploads/virtualfilesystems_3-crazy.jpg (Man with shocked expression)
+[12]: https://wiki.archlinux.org/index.php/Tmpfs
+[13]: http://man7.org/linux/man-pages/man8/sysctl.8.html
+[14]: https://opensource.com/sites/default/files/uploads/virtualfilesystems_4-proc-meminfo.png (Console)
+[15]: http://www-f1.ijs.si/~ramsak/km1/mermin.moon.pdf
+[16]: https://en.wikiquote.org/wiki/David_Mermin
+[17]: https://opensource.com/sites/default/files/uploads/virtualfilesystems_5-moon.jpg (Full moon)
+[18]: https://commons.wikimedia.org/wiki/Moon#/media/File:Full_Moon_Luc_Viatour.jpg
+[19]: https://git.kernel.org/pub/scm/linux/kernel/git/torvalds/linux.git/tree/Documentation/ABI/stable
+[20]: https://lkml.org/lkml/2012/12/23/75
+[21]: https://opensource.com/sites/default/files/uploads/virtualfilesystems_7-sysfs.png (Console)
+[22]: https://events.linuxfoundation.org/sites/events/files/slides/bpf_collabsummit_2015feb20.pdf
+[23]: https://github.com/iovisor/bcc
+[24]: https://github.com/iovisor/bcc/blob/master/INSTALL.md
+[25]: http://brendangregg.com/ebpf.html
+[26]: https://github.com/iovisor/bcc/tree/master/tools
+[27]: https://github.com/iovisor/bcc/blob/master/tools/vfscount_example.txt
+[28]: https://github.com/iovisor/bcc/blob/master/tools/vfsstat.py
+[29]: https://opensource.com/sites/default/files/uploads/virtualfilesystems_8-vfsstat.png (Console - vfsstat.py)
+[30]: https://opensource.com/sites/default/files/uploads/virtualfilesystems_9-ebpf.png (Console when USB is inserted)
+[31]: https://github.com/iovisor/bcc/blob/master/tools/trace_example.txt
+[32]: https://events.static.linuxfound.org/sites/events/files/slides/bpf_collabsummit_2015feb20.pdf
+[33]: http://northstar-www.dartmouth.edu/doc/solaris-forte/manuals/c/user_guide/cscope.html
+[34]: https://git.kernel.org/pub/scm/linux/kernel/git/torvalds/linux.git/tree/block/genhd.c#n665
+[35]: http://www.man7.org/linux/man-pages/man8/fsck.8.html
+[36]: https://wiki.automotivelinux.org/_media/eg-rhsa/agl_referencehardwarespec_v0.1.0_20171018.pdf
+[37]: https://elinux.org/images/1/1f/Read-only_rootfs.pdf
+[38]: https://opensource.com/sites/default/files/uploads/virtualfilesystems_10-code.jpg (Photograph of a console)
+[39]: https://www.meetup.com/ACCU-Bay-Area/events/drpmvfytlbqb/
+[40]: http://man7.org/linux/man-pages/man8/mount.8.html
+[41]: https://git.kernel.org/pub/scm/linux/kernel/git/torvalds/linux.git/tree/Documentation/filesystems/sharedsubtree.txt
+[42]: https://coreos.com/os/docs/latest/kernel-modules.html
+[43]: https://www.freedesktop.org/software/systemd/man/systemd-nspawn.html
+[44]: https://opensource.com/sites/default/files/uploads/virtualfilesystems_11-system-nspawn.png (Console - system-nspawn invocation)
+[45]: https://opensource.com/sites/default/files/uploads/virtualfilesystems_12-mountsnoop.png (Console - Running mountsnoop)
+[46]: http://shallowsky.com/
+[47]: http://eagercon.com/
+[48]: https://www.socallinuxexpo.org/scale/17x/presentations/virtual-filesystems-why-we-need-them-and-how-they-work
+[49]: https://www.socallinuxexpo.org/
diff --git a/published/201905/20190319 Blockchain 2.0- Blockchain In Real Estate -Part 4.md b/published/201905/20190319 Blockchain 2.0- Blockchain In Real Estate -Part 4.md
new file mode 100644
index 0000000000..0ea20b929a
--- /dev/null
+++ b/published/201905/20190319 Blockchain 2.0- Blockchain In Real Estate -Part 4.md
@@ -0,0 +1,56 @@
+[#]: collector: (lujun9972)
+[#]: translator: (wxy)
+[#]: reviewer: (wxy)
+[#]: publisher: (wxy)
+[#]: url: (https://linux.cn/article-10914-1.html)
+[#]: subject: (Blockchain 2.0: Blockchain In Real Estate [Part 4])
+[#]: via: (https://www.ostechnix.com/blockchain-2-0-blockchain-in-real-estate/)
+[#]: author: (ostechnix https://www.ostechnix.com/author/editor/)
+
+区块链 2.0:房地产区块链(四)
+======
+
+
+
+### 区块链 2.0:“更”智能的房地产
+
+在本系列的[上一篇文章][1]中我们探讨了区块链的特征,这些区块链将使机构能够将**传统银行**和**融资系统**转换和交织在一起。这部分将探讨**房地产区块链**。房地产业正在走向革命。它是人类已知的交易最活跃、最重要的资产类别之一。然而,由于充满了监管障碍和欺诈、欺骗的无数可能性,它也是最难参与交易的之一。利用适当的共识算法的区块链的分布式分类账本功能被吹捧为这个行业的前进方向,而这个行业传统上被认为其面对变革是保守的。
+
+就其无数的业务而言,房地产一直是一个非常保守的行业。这似乎也是理所当然的。2008 年金融危机或 20 世纪上半叶的大萧条等重大经济危机成功摧毁了该行业及其参与者。然而,与大多数具有经济价值的产品一样,房地产行业具有弹性,而这种弹性则源于其保守性。
+
+全球房地产市场由价值 228 万亿 [^1] 美元的资产类别组成,出入不大。其他投资资产,如股票、债券和股票合计价值仅为 170 万亿美元。显然,在这样一个行业中实施的交易在很大程度上都是精心策划和执行的。很多时候,房地产也因许多欺诈事件而臭名昭著,并且随之而来的是毁灭性的损失。由于其运营非常保守,该行业也难以驾驭。它受到了法律的严格监管,创造了一个交织在一起的细微差别网络,这对于普通人来说太难以完全理解,使得大多数人无法进入和参与。如果你曾参与过这样的交易,那么你就会知道纸质文件的重要性和长期性。
+
+从一个微不足道的开始,虽然是一个重要的例子,以显示当前的记录管理实践在房地产行业有多糟糕,考虑一下[产权保险业务][2] [^3]。产权保险用于对冲土地所有权和所有权记录不可接受且从而无法执行的可能性。诸如此类的保险产品也称为赔偿保险。在许多情况下,法律要求财产拥有产权保险,特别是在处理多年来多次易手的财产时。抵押贷款公司在支持房地产交易时也可能坚持同样的要求。事实上,这种产品自 19 世纪 50 年代就已存在,并且仅在美国每年至少有 1.5 万亿美元的商业价值这一事实证明了一开始的说法。在这种情况下,这些记录的维护方式必须进行改革,区块链提供了一个可持续解决方案。根据[美国土地产权协会][4],平均每个案例的欺诈平均约为 10 万美元,并且涉及交易的所有产权中有 25% 的文件存在问题。区块链允许设置一个不可变的永久数据库,该数据库将跟踪资产本身,记录已经进入的每个交易或投资。这样的分类帐本系统将使包括一次性购房者在内的房地产行业的每个人的生活更加轻松,并使诸如产权保险等金融产品基本上无关紧要。将诸如房地产之类的实物资产转换为这样的数字资产是非常规的,并且目前仅在理论上存在。然而,这种变化迫在眉睫,而不是迟到 [^5]。
+
+区块链在房地产中影响最大的领域如上所述,在维护透明和安全的产权管理系统方面。基于区块链的财产记录可以包含有关财产、其所在地、所有权历史以及相关的公共记录的[信息][6]。这将允许房地产交易快速完成,并且无需第三方监控和监督。房地产评估和税收计算等任务成为有形的、客观的参数问题,而不是主观测量和猜测,因为可靠的历史数据是可公开验证的。[UBITQUITY][7] 就是这样一个平台,为企业客户提供定制的基于区块链的解决方案。该平台允许客户跟踪所有房产细节、付款记录、抵押记录,甚至允许运行智能合约,自动处理税收和租赁。
+
+这为我们带来了房地产区块链的第二大机遇和用例。由于该行业受到众多第三方的高度监管,除了参与交易的交易对手外,尽职调查和财务评估可能非常耗时。这些流程主要通过离线渠道进行,文书工作需要在最终评估报告出来之前进行数天。对于公司房地产交易尤其如此,这构成了顾问所收取的总计费时间的大部分。如果交易由抵押背书,则这些过程的重复是不可避免的。一旦与所涉及的人员和机构的数字身份相结合,就可以完全避免当前的低效率,并且可以在几秒钟内完成交易。租户、投资者、相关机构、顾问等可以单独验证数据并达成一致的共识,从而验证永久性的财产记录 [^8]。这提高了验证流程的准确性。房地产巨头 RE/MAX 最近宣布与服务提供商 XYO Network Partners 合作,[建立墨西哥房上市地产国家数据库][9]。他们希望有朝一日能够创建世界上最大的(截至目前)去中心化房地产登记中心之一。
+
+然而,区块链可以带来的另一个重要且可以说是非常民主的变化是投资房地产。与其他投资资产类别不同,即使是小型家庭投资者也可能参与其中,房地产通常需要大量的手工付款才能参与。诸如 ATLANT 和 BitOfProperty 之类的公司将房产的账面价值代币化,并将其转换为加密货币的等价物。这些代币随后在交易所出售,类似于股票和股票的交易方式。[房地产后续产生的任何现金流都会根据其在财产中的“份额”记入贷方或借记给代币所有者][4]。
+
+然而,尽管如此,区块链技术仍处于房地产领域的早期采用阶段,目前的法规还没有明确定义它。诸如分布式应用程序、分布式匿名组织(DAO)、智能合约等概念在许多国家的法律领域是闻所未闻的。一旦所有利益相关者充分接受了区块链复杂性的良好教育,就会彻底改革现有的法规和指导方针,这是最务实的前进方式。 同样,这将是一个缓慢而渐进的变化,但是它是一个急需的变化。本系列的下一篇文章将介绍 “智能合约”,例如由 UBITQUITY 和 XYO 等公司实施的那些是如何在区块链中创建和执行的。
+
+[^1]: HSBC, “Global Real Estate,” no. April, 2008
+[^3]: D. B. Burke, Law of title insurance. Aspen Law & Business, 2000.
+[^5]: M. Swan, O’Reilly – Blockchain. Blueprint for a New Economy – 2015.
+[^8]: Deloite, “Blockchain in commercial real estate The future is here ! Table of contents.”
+
+--------------------------------------------------------------------------------
+
+via: https://www.ostechnix.com/blockchain-2-0-blockchain-in-real-estate/
+
+作者:[ostechnix][a]
+选题:[lujun9972][b]
+译者:[wxy](https://github.com/wxy)
+校对:[wxy](https://github.com/wxy)
+
+本文由 [LCTT](https://github.com/LCTT/TranslateProject) 原创编译,[Linux中国](https://linux.cn/) 荣誉推出
+
+[a]: https://www.ostechnix.com/author/editor/
+[b]: https://github.com/lujun9972
+[1]: https://linux.cn/article-10689-1.html
+[2]: https://www.forbes.com/sites/jordanlulich/2018/06/21/what-is-title-insurance-and-why-its-important/#1472022b12bb
+[4]: https://www.cbinsights.com/research/blockchain-real-estate-disruption/#financing
+[6]: https://www2.deloitte.com/us/en/pages/financial-services/articles/blockchain-in-commercial-real-estate.html
+[7]: https://www.ubitquity.io/
+[9]: https://www.businesswire.com/news/home/20181012005068/en/XYO-Network-Partners-REMAX-M%C3%A9xico-Bring-Blockchain
diff --git a/translated/talk/20190327 Why DevOps is the most important tech strategy today.md b/published/201905/20190327 Why DevOps is the most important tech strategy today.md
similarity index 60%
rename from translated/talk/20190327 Why DevOps is the most important tech strategy today.md
rename to published/201905/20190327 Why DevOps is the most important tech strategy today.md
index fe014a243a..d96ae31f13 100644
--- a/translated/talk/20190327 Why DevOps is the most important tech strategy today.md
+++ b/published/201905/20190327 Why DevOps is the most important tech strategy today.md
@@ -1,48 +1,47 @@
[#]: collector: "lujun9972"
-[#]: translator: "zgj1024 "
-[#]: reviewer: " "
-[#]: publisher: " "
-[#]: url: " "
+[#]: translator: "zgj1024"
+[#]: reviewer: "wxy"
+[#]: publisher: "wxy"
+[#]: url: "https://linux.cn/article-10834-1.html"
[#]: subject: "Why DevOps is the most important tech strategy today"
[#]: via: "https://opensource.com/article/19/3/devops-most-important-tech-strategy"
-[#]: author: "Kelly AlbrechtWilly-Peter Schaub https://opensource.com/users/ksalbrecht/users/brentaaronreed/users/wpschaub/users/wpschaub/users/ksalbrecht"
+[#]: author: "Kelly Albrecht https://opensource.com/users/ksalbrecht"
为何 DevOps 是如今最重要的技术策略
======
-消除一些关于 DevOps 的疑惑
+
+> 消除一些关于 DevOps 的疑惑。
+
![CICD with gears][1]
很多人初学 [DevOps][2] 时,看到它其中一个结果就问这个是如何得来的。其实理解这部分 Devops 的怎样实现并不重要,重要的是——理解(使用) DevOps 策略的原因——这是做一个行业的领导者还是追随者的差别。
-你可能会听过些 Devops 的难以置信的成果,例如生产环境非常有弹性,“混世猴子”([Chaos Monkey][3])程序运行时,将周围的连接随机切断,每天仍可以处理数千个版本。这是令人印象深刻的,但就其本身而言,这是一个 DevOps 的无力案例,本质上会被一个[反例][4]困扰:DevOps 环境有弹性是因为没有观察到严重的故障。。。还没有。
+你可能会听过些 Devops 的难以置信的成果,例如生产环境非常有弹性,就算是有个“[癫狂的猴子][3])跳来跳去将不知道哪个插头随便拔下,每天仍可以处理数千个发布。这是令人印象深刻的,但就其本身而言,这是一个 DevOps 的证据不足的案例,其本质上会被一个[反例][4]困扰:DevOps 环境有弹性是因为严重的故障还没有被观测到。
有很多关于 DevOps 的疑惑,并且许多人还在尝试弄清楚它的意义。下面是来自我 LinkedIn Feed 中的某个人的一个案例:
-> 最近我参加一些 #DevOps 的交流会,那里一些演讲人好像在倡导 #敏捷开发是 DevOps 的子集。不知为何,我的理解洽洽相反。
+> 最近我参加一些 #DevOps 的交流会,那里一些演讲人好像在倡导 #敏捷开发是 DevOps 的子集。不知为何,我的理解恰恰相反。
>
> 能听一下你们的想法吗?你认为敏捷开发和 DevOps 之间是什么关系呢?
>
> 1. DevOps 是敏捷开发的子集
-> 2. 敏捷开发 是 DevOps 的子集
+> 2. 敏捷开发是 DevOps 的子集
> 3. DevOps 是敏捷开发的扩展,从敏捷开发结束的地方开始
> 4. DevOps 是敏捷开发的新版本
->
-科技行业的专业人士在那篇 LinkedIn 的帖子上达标各样的答案,你会怎样回复呢?
+科技行业的专业人士在那篇 LinkedIn 的帖子上表达了各种各样的答案,你会怎样回复呢?
-### DevOps源于精益和敏捷
+### DevOps 源于精益和敏捷
+
+如果我们从亨利福特的战略和丰田生产系统对福特车型的改进(的历史)开始, DevOps 就更有意义了。精益制造就诞生在那段历史中,人们对精益制作进行了良好的研究。James P. Womack 和 Daniel T. Jones 将精益思维([Lean Thinking][5])提炼为五个原则:
-如果我们从亨利福特的战略和丰田生产系统对福特车型的改进(的历史)开始, DevOps 就更有意义了。精益制造就诞生在那段历史中,人们对精益制作进行了良好的研究。James P. Womack 和 Daniel T. Jones 将精益思维( [Lean Thinking][5])提炼为五个原则:
1. 指明客户所需的价值
2. 确定提供该价值的每个产品的价值流,并对当前提供该价值所需的所有浪费步骤提起挑战
3. 使产品通过剩余的增值步骤持续流动
4. 在可以连续流动的所有步骤之间引入拉力
5. 管理要尽善尽美,以便为客户服务所需的步骤数量和时间以及信息量持续下降
-
-Lean seeks to continuously remove waste and increase the flow of value to the customer. This is easily recognizable and understood through a core tenet of lean: single piece flow. We can do a number of activities to learn why moving single pieces at a time is magnitudes faster than batches of many pieces; the [Penny Game][6] and the [Airplane Game][7] are two of them. In the Penny Game, if a batch of 20 pennies takes two minutes to get to the customer, they get the whole batch after waiting two minutes. If you move one penny at a time, the customer gets the first penny in about five seconds and continues getting pennies until the 20th penny arrives approximately 25 seconds later.
-
-精益致力于持续消除浪费并增加客户的价值流动。这很容易识别并明白精益的核心原则:单一流。我们可以做一些游戏去了解为何同一时间移动单个比批量移动要快得多。其中的两个游戏是[硬币游戏][6]和[飞机游戏][7]。在硬币游戏中,如果一批 20 个硬币到顾客手中要用 2 分钟,顾客等 2 分钟后能拿到整批硬币。如果一次只移动一个硬币,顾客会在 5 秒内得到第一枚硬币,并会持续获得硬币,直到在大约 25 秒后第 20 个硬币到达。(译者注:有相关的视频的)
+精益致力于持续消除浪费并增加客户的价值流动。这很容易识别并明白精益的核心原则:单一流。我们可以做一些游戏去了解为何同一时间移动单个比批量移动要快得多。其中的两个游戏是[硬币游戏][6]和[飞机游戏][7]。在硬币游戏中,如果一批 20 个硬币到顾客手中要用 2 分钟,顾客等 2 分钟后能拿到整批硬币。如果一次只移动一个硬币,顾客会在 5 秒内得到第一枚硬币,并会持续获得硬币,直到在大约 25 秒后第 20 个硬币到达。(LCTT 译注:有相关的视频的)
这是巨大的不同,但是不是生活中的所有事都像硬币游戏那样简单并可预测的。这就是敏捷的出现的原因。我们当然看到了高效绩敏捷团队的精益原则,但这些团队需要的不仅仅是精益去做他们要做的事。
@@ -52,13 +51,13 @@ Lean seeks to continuously remove waste and increase the flow of value to the cu
### 最佳批量大小
-要了解 DevOps 在软件开发中的请强大功能,这会帮助我们理解批处理大小的经济学。请考虑以下来自Donald Reinertsen 的[产品开发流程原则][8]的U曲线优化示例:
+要了解 DevOps 在软件开发中的强大功能,这会帮助我们理解批处理大小的经济学。请考虑以下来自Donald Reinertsen 的[产品开发流程原则][8]的U曲线优化示例:
![U-curve optimization illustration of optimal batch size][9]
-这可以类比杂货店购物来解释。假设你需要买一些鸡蛋,而你住的地方离商店只有 30 分的路程。买一个鸡蛋(图种最左边)意味着每次要花 30 分钟的路程,这就是你的_交易成本_。_持有成本_可能是鸡蛋变质和在你的冰箱中持续地占用空间。_总成本_是_交易成本_加上你的_持有成本_。这 U 型曲线解释了为什么对大部分来说,一次买一打鸡蛋是他们的_最佳批量大小_。如果你就住在商店的旁边,步行到那里不会花费你任何的时候,你可能每次只会买一小盒鸡蛋,以此来节省冰箱的空间并享受新鲜的鸡蛋。
+这可以类比杂货店购物来解释。假设你需要买一些鸡蛋,而你住的地方离商店只有 30 分钟的路程。买一个鸡蛋(图中最左边)意味着每次要花 30 分钟的路程,这就是你的*交易成本*。*持有成本*可能是鸡蛋变质和在你的冰箱中持续地占用空间。*总成本*是*交易成本*加上你的*持有成本*。这个 U 型曲线解释了为什么对大部分人来说,一次买一打鸡蛋是他们的*最佳批量大小*。如果你就住在商店的旁边,步行到那里不会花费你任何的时候,你可能每次只会买一小盒鸡蛋,以此来节省冰箱的空间并享受新鲜的鸡蛋。
-这 U 型优化曲线可以说明为什么在成功敏捷转换中生产力会显著提高。考虑敏捷转换对组织决策的影响。在传统的分级组织中,决策权是集中的。这会导致较少的人做更大的决策。敏捷方法论会有效地降低组织决策中的交易成本,方法是将决策分散到最被人熟知的认识和信息的位置:跨越高度信任,自组织的敏捷团队。
+这 U 型优化曲线可以说明为什么在成功的敏捷转换中生产力会显著提高。考虑敏捷转换对组织决策的影响。在传统的分级组织中,决策权是集中的。这会导致较少的人做更大的决策。敏捷方法论会有效地降低组织决策中的交易成本,方法是将决策分散到最被人熟知的认识和信息的位置:跨越高度信任,自组织的敏捷团队。
下面的动画演示了降低事务成本后,最佳批量大小是如何向左移动。在更频繁地做出更快的决策方面,你不能低估组织的价值。
@@ -66,22 +65,21 @@ Lean seeks to continuously remove waste and increase the flow of value to the cu
### DevOps 适合哪些地方
-自动化是 DevOps 最知名的事情之一。前面的插图非常详细地展示了自动化的价值。通过自动化,我们将交易成本降低到接近零,实质上是免费进行测试和部署。这使我们可以利用越来越小的批量工作。较小批量的工作更容易理解、提交、测试、审查和知道何时能完成。这些较小的批量大小也包含较少的差异和风险,使其更易于部署,如果出现问题,可以进行故障排除和恢复。通过自动化与扎实的敏捷实践相结合,我们可以使我们的功能开发非常接近单件流程,从而快速,持续地为客户提供价值。
+自动化是 DevOps 最知名的事情之一。前面的插图非常详细地展示了自动化的价值。通过自动化,我们将交易成本降低到接近于零,实质上是可以免费进行测试和部署。这使我们可以利用越来越小的批量工作。较小批量的工作更容易理解、提交、测试、审查和知道何时能完成。这些较小的批量大小也包含较少的差异和风险,使其更易于部署,如果出现问题,可以进行故障排除和恢复。通过自动化与扎实的敏捷实践相结合,我们可以使我们的功能开发非常接近单件流程,从而快速、持续地为客户提供价值。
更传统地说,DevOps 被理解为一种打破开发团队和运营团队之间混乱局面的方法。在这个模型中,开发团队开发新的功能,而运营团队则保持系统的稳定和平稳运行。摩擦的发生是因为开发过程中的新功能将更改引入到系统中,从而增加了停机的风险,运营团队并不认为要对此负责,但无论如何都必须处理这一问题。DevOps 不仅仅尝试让人们一起工作,更重要的是尝试在复杂的环境中安全地进行更频繁的更改。
-我们可以向 [Ron Westrum][11] 寻求有关在复杂组织中实现安全性的研究。在研究为什么有些组织比其他组织更安全时,他发现组织的文化可以预测其安全性。他确定了三种文化:病态,官僚主义的和生产式的。他发现病理的可以预测安全性较低,而生产式文化被预测为更安全(例如,在他的主要研究领域中,飞机坠毁或意外住院死亡的数量要少得多)。
+我们可以看看 [Ron Westrum][11] 在有关复杂组织中实现安全性的研究。在研究为什么有些组织比其他组织更安全时,他发现组织的文化可以预测其安全性。他确定了三种文化:病态的、官僚主义的和生产式的。他发现病态的可以预测其安全性较低,而生产式文化被预测为更安全(例如,在他的主要研究领域中,飞机坠毁或意外住院死亡的数量要少得多)。
![Three types of culture identified by Ron Westrum][12]
高效的 DevOps 团队通过精益和敏捷的实践实现了一种生成性文化,这表明速度和安全性是互补的,或者说是同一个问题的两个方面。通过将决策和功能的最佳批量大小减少到非常小,DevOps 实现了更快的信息流和价值,同时消除了浪费并降低了风险。
-与 Westrum的研究一致,在提高安全性和可靠性的同时,变化也很容易发生。。当一个敏捷的 DevOps 团队被信任做出自己的决定时,我们将获得 DevOps 目前最为人所知的工具和技术:自动化和持续交付。通过这种自动化,交易成本比以往任何时候都进一步降低,并且实现了近乎单一的精益流程,每天创造数千个决策和发布的潜力,正如我们在高效绩的 DevOps 组织中看到的那样
+与 Westrum 的研究一致,在提高安全性和可靠性的同时,变化也很容易发生。当一个敏捷的 DevOps 团队被信任做出自己的决定时,我们将获得 DevOps 目前最为人所知的工具和技术:自动化和持续交付。通过这种自动化,交易成本比以往任何时候都进一步降低,并且实现了近乎单一的精益流程,每天创造数千个决策和发布的潜力,正如我们在高效绩的 DevOps 组织中看到的那样
### 流动、反馈、学习
-DevOps 并不止于此。我们主要讨论了 DevOps 实现了革命性的流程,但通过类似的努力可以进一步放大精益和敏捷实践,从而实现更快的反馈循环和更快的学习。在[_DevOps手册_][13] 中,作者除了详细解释快速流程外, DevOps 如何在整个价值流中实现遥测,从而获得快速且持续的反馈。此外,利用[精益求精的突破][14]和scrum 的[回顾][15],高效的 DevOps 团队将不断推动学习和持续改进深入到他们的组织的基础,实现软件产品开发行业的精益制造革命。
-
+DevOps 并不止于此。我们主要讨论了 DevOps 实现了革命性的流程,但通过类似的努力可以进一步放大精益和敏捷实践,从而实现更快的反馈循环和更快的学习。在[DevOps手册][13] 中,作者除了详细解释快速流程外, DevOps 如何在整个价值流中实现遥测,从而获得快速且持续的反馈。此外,利用[精益求精的突破][14]和 scrum 的[回顾][15],高效的 DevOps 团队将不断推动学习和持续改进深入到他们的组织的基础,实现软件产品开发行业的精益制造革命。
### 从 DevOps 评估开始
@@ -91,18 +89,14 @@ DevOps 并不止于此。我们主要讨论了 DevOps 实现了革命性的流
在本文的[第二部分][16]中,我们将查看 Drupal 社区中 DevOps 调查的结果,并了解最有可能找到快速获胜的位置。
-* * *
-
-_Rob_ _Bayliss and Kelly Albrecht will present[DevOps: Why, How, and What][17] and host a follow-up [Birds of a][18]_ [_Feather_][18] _[discussion][18] at [DrupalCon 2019][19] in Seattle, April 8-12._
-
--------------------------------------------------------------------------------
via: https://opensource.com/article/19/3/devops-most-important-tech-strategy
-作者:[Kelly AlbrechtWilly-Peter Schaub][a]
+作者:[Kelly Albrecht][a]
选题:[lujun9972][b]
-译者:[译者ID](https://github.com/zgj1024)
-校对:[校对者ID](https://github.com/校对者ID)
+译者:[zgj1024](https://github.com/zgj1024)
+校对:[wxy](https://github.com/wxy)
本文由 [LCTT](https://github.com/LCTT/TranslateProject) 原创编译,[Linux中国](https://linux.cn/) 荣誉推出
diff --git a/published/201905/20190329 How to manage your Linux environment.md b/published/201905/20190329 How to manage your Linux environment.md
new file mode 100644
index 0000000000..0a226f79f7
--- /dev/null
+++ b/published/201905/20190329 How to manage your Linux environment.md
@@ -0,0 +1,173 @@
+[#]: collector: (lujun9972)
+[#]: translator: (robsean)
+[#]: reviewer: (wxy)
+[#]: publisher: (wxy)
+[#]: url: (https://linux.cn/article-10916-1.html)
+[#]: subject: (How to manage your Linux environment)
+[#]: via: (https://www.networkworld.com/article/3385516/how-to-manage-your-linux-environment.html)
+[#]: author: (Sandra Henry-Stocker https://www.networkworld.com/author/Sandra-Henry_Stocker/)
+
+如何管理你的 Linux 环境变量
+======
+
+> Linux 用户环境变量可以帮助你找到你需要的命令,无须了解系统如何配置的细节而完成大量工作。而这些设置来自哪里和如何被修改它们是另一个话题。
+
+![IIP Photo Archive \(CC BY 2.0\)][1]
+
+在 Linux 系统上的用户账户配置以多种方法简化了系统的使用。你可以运行命令,而不需要知道它们的位置。你可以重新使用先前运行的命令,而不用发愁系统是如何追踪到它们的。你可以查看你的电子邮件,查看手册页,并容易地回到你的家目录,而不用管你在文件系统中身在何方。并且,当需要的时候,你可以调整你的账户设置,以便其更符合你喜欢的方式。
+
+Linux 环境设置来自一系列的文件:一些是系统范围(意味着它们影响所有用户账户),一些是处于你的家目录中的配置文件里。系统范围的设置在你登录时生效,而本地设置在其后生效,所以,你在你账户中作出的更改将覆盖系统范围设置。对于 bash 用户,这些文件包含这些系统文件:
+
+```
+/etc/environment
+/etc/bash.bashrc
+/etc/profile
+```
+
+以及一些本地文件:
+
+```
+~/.bashrc
+~/.profile # 如果有 ~/.bash_profile 或 ~/.bash_login 就不会读此文件
+~/.bash_profile
+~/.bash_login
+```
+
+你可以修改本地存在的四个文件的任何一个,因为它们处于你的家目录,并且它们是属于你的。
+
+### 查看你的 Linux 环境设置
+
+为查看你的环境设置,使用 `env` 命令。你的输出将可能与这相似:
+
+```
+$ env
+LS_COLORS=rs=0:di=01;34:ln=01;36:mh=00:pi=40;33:so=01;35:do=01;35:bd=40;33;01:cd=40;33;
+01:or=40;31;01:mi=00:su=37;41:sg=30;43:ca=30;41:tw=30;42:ow=34;42:st=37;44:ex=01;32:
+*.tar=01;31:*.tgz=01;31:*.arc=01;31:*.arj=01;31:*.taz=01;31:*.lha=01;31:*.lz4=01;31:
+*.lzh=01;31:*.lzma=01;31:*.tlz=01;31:*.txz=01;31:*.tzo=01;31:*.t7z=01;31:*.zip=01;31:
+*.z=01;31:*.Z=01;31:*.dz=01;31:*.gz=01;31:*.lrz=01;31:*.lz=01;31:*.lzo=01;31:*.xz=01;
+31:*.zst=01;31:*.tzst=01;31:*.bz2=01;31:*.bz=01;31:*.tbz=01;31:*.tbz2=01;31:*.tz=01;31:
+*.deb=01;31:*.rpm=01;31:*.jar=01;31:*.war=01;31:*.ear=01;31:*.sar=01;31:*.rar=01;31:
+*.alz=01;31:*.ace=01;31:*.zoo=01;31:*.cpio=01;31:*.7z=01;31:*.rz=01;31:*.cab=01;31:
+*.wim=01;31:*.swm=01;31:*.dwm=01;31:*.esd=01;31:*.jpg=01;35:*.jpeg=01;35:*.mjpg=01;35:
+*.mjpeg=01;35:*.gif=01;35:*.bmp=01;35:*.pbm=01;35:*.pgm=01;35:*.ppm=01;35:*.tga=01;35:
+*.xbm=01;35:*.xpm=01;35:*.tif=01;35:*.tiff=01;35:*.png=01;35:*.svg=01;35:*.svgz=01;35:
+*.mng=01;35:*.pcx=01;35:*.mov=01;35:*.mpg=01;35:*.mpeg=01;35:*.m2v=01;35:*.mkv=01;35:
+*.webm=01;35:*.ogm=01;35:*.mp4=01;35:*.m4v=01;35:*.mp4v=01;35:*.vob=01;35:*.qt=01;35:
+*.nuv=01;35:*.wmv=01;35:*.asf=01;35:*.rm=01;35:*.rmvb=01;35:*.flc=01;35:*.avi=01;35:
+*.fli=01;35:*.flv=01;35:*.gl=01;35:*.dl=01;35:*.xcf=01;35:*.xwd=01;35:*.yuv=01;35:
+*.cgm=01;35:*.emf=01;35:*.ogv=01;35:*.ogx=01;35:*.aac=00;36:*.au=00;36:*.flac=00;36:
+*.m4a=00;36:*.mid=00;36:*.midi=00;36:*.mka=00;36:*.mp3=00;36:*.mpc=00;36:*.ogg=00;36:
+*.ra=00;36:*.wav=00;36:*.oga=00;36:*.opus=00;36:*.spx=00;36:*.spf=00;36:
+SSH_CONNECTION=192.168.0.21 34975 192.168.0.11 22
+LESSCLOSE=/usr/bin/lesspipe %s %s
+LANG=en_US.UTF-8
+OLDPWD=/home/shs
+XDG_SESSION_ID=2253
+USER=shs
+PWD=/home/shs
+HOME=/home/shs
+SSH_CLIENT=192.168.0.21 34975 22
+XDG_DATA_DIRS=/usr/local/share:/usr/share:/var/lib/snapd/desktop
+SSH_TTY=/dev/pts/0
+MAIL=/var/mail/shs
+TERM=xterm
+SHELL=/bin/bash
+SHLVL=1
+LOGNAME=shs
+DBUS_SESSION_BUS_ADDRESS=unix:path=/run/user/1000/bus
+XDG_RUNTIME_DIR=/run/user/1000
+PATH=/home/shs/bin:/usr/local/sbin:/usr/local/bin:/usr/sbin:/usr/bin:/sbin:/bin:/usr/games:/usr/local/games:/snap/bin
+LESSOPEN=| /usr/bin/lesspipe %s
+_=/usr/bin/env
+```
+
+虽然你可能会看到大量的输出,上面显示的第一大部分用于在命令行上使用颜色标识各种文件类型。当你看到类似 `*.tar=01;31:` 这样的东西,这告诉你 `tar` 文件将以红色显示在文件列表中,然而 `*.jpg=01;35:` 告诉你 jpg 文件将以紫色显现出来。这些颜色旨在使它易于从一个文件列表中分辨出某些文件。你可以在《[在 Linux 命令行中自定义你的颜色][3]》处学习更多关于这些颜色的定义,和如何自定义它们。
+
+当你更喜欢一种不加装饰的显示时,一种关闭颜色显示的简单方法是使用如下命令:
+
+```
+$ ls -l --color=never
+```
+
+这个命令可以简单地转换到一个别名:
+
+```
+$ alias ll2='ls -l --color=never'
+```
+
+你也可以使用 `echo` 命令来单独地显现某个设置。在这个命令中,我们显示在历史缓存区中将被记忆命令的数量:
+
+```
+$ echo $HISTSIZE
+1000
+```
+
+如果你已经移动到某个位置,你在文件系统中的最后位置会被记在这里:
+
+```
+PWD=/home/shs
+OLDPWD=/tmp
+```
+
+### 作出更改
+
+你可以使用一个像这样的命令更改环境设置,但是,如果你希望保持这个设置,在你的 `~/.bashrc` 文件中添加一行代码,例如 `HISTSIZE=1234`。
+
+```
+$ export HISTSIZE=1234
+```
+
+### “export” 一个变量的本意是什么
+
+导出一个环境变量可使设置用于你的 shell 和可能的子 shell。默认情况下,用户定义的变量是本地的,并不被导出到新的进程,例如,子 shell 和脚本。`export` 命令使得环境变量可用在子进程中发挥功用。
+
+### 添加和移除变量
+
+你可以很容易地在命令行和子 shell 上创建新的变量,并使它们可用。然而,当你登出并再次回来时这些变量将消失,除非你也将它们添加到 `~/.bashrc` 或一个类似的文件中。
+
+```
+$ export MSG="Hello, World!"
+```
+
+如果你需要,你可以使用 `unset` 命令来消除一个变量:
+
+```
+$ unset MSG
+```
+
+如果变量是局部定义的,你可以通过加载你的启动文件来简单地将其设置回来。例如:
+
+```
+$ echo $MSG
+Hello, World!
+$ unset $MSG
+$ echo $MSG
+
+$ . ~/.bashrc
+$ echo $MSG
+Hello, World!
+```
+
+### 小结
+
+用户账户是用一组恰当的启动文件设立的,创建了一个有用的用户环境,而个人用户和系统管理员都可以通过编辑他们的个人设置文件(对于用户)或很多来自设置起源的文件(对于系统管理员)来更改默认设置。
+
+--------------------------------------------------------------------------------
+
+via: https://www.networkworld.com/article/3385516/how-to-manage-your-linux-environment.html
+
+作者:[Sandra Henry-Stocker][a]
+选题:[lujun9972][b]
+译者:[robsean](https://github.com/robsean)
+校对:[wxy](https://github.com/wxy)
+
+本文由 [LCTT](https://github.com/LCTT/TranslateProject) 原创编译,[Linux中国](https://linux.cn/) 荣誉推出
+
+[a]: https://www.networkworld.com/author/Sandra-Henry_Stocker/
+[b]: https://github.com/lujun9972
+[1]: https://images.idgesg.net/images/article/2019/03/environment-rocks-leaves-100792229-large.jpg
+[2]: https://www.youtube.com/playlist?list=PL7D2RMSmRO9J8OTpjFECi8DJiTQdd4hua
+[3]: https://www.networkworld.com/article/3269587/customizing-your-text-colors-on-the-linux-command-line.html
+[4]: https://www.facebook.com/NetworkWorld/
+[5]: https://www.linkedin.com/company/network-world
diff --git a/published/20190401 What is 5G- How is it better than 4G.md b/published/201905/20190401 What is 5G- How is it better than 4G.md
similarity index 100%
rename from published/20190401 What is 5G- How is it better than 4G.md
rename to published/201905/20190401 What is 5G- How is it better than 4G.md
diff --git a/published/20190405 Command line quick tips- Cutting content out of files.md b/published/201905/20190405 Command line quick tips- Cutting content out of files.md
similarity index 100%
rename from published/20190405 Command line quick tips- Cutting content out of files.md
rename to published/201905/20190405 Command line quick tips- Cutting content out of files.md
diff --git a/published/201905/20190408 Getting started with Python-s cryptography library.md b/published/201905/20190408 Getting started with Python-s cryptography library.md
new file mode 100644
index 0000000000..bc6aeb05b7
--- /dev/null
+++ b/published/201905/20190408 Getting started with Python-s cryptography library.md
@@ -0,0 +1,108 @@
+[#]: collector: (lujun9972)
+[#]: translator: (geekpi)
+[#]: reviewer: (wxy)
+[#]: publisher: (wxy)
+[#]: url: (https://linux.cn/article-10833-1.html)
+[#]: subject: (Getting started with Python's cryptography library)
+[#]: via: (https://opensource.com/article/19/4/cryptography-python)
+[#]: author: (Moshe Zadka https://opensource.com/users/moshez)
+
+Python 的加密库入门
+======
+
+> 加密你的数据并使其免受攻击者的攻击。
+
+![lock on world map][1]
+
+密码学俱乐部的第一条规则是:永远不要自己*发明*密码系统。密码学俱乐部的第二条规则是:永远不要自己*实现*密码系统:在现实世界中,在*实现*以及设计密码系统阶段都找到过许多漏洞。
+
+Python 中的一个有用的基本加密库就叫做 [cryptography][2]。它既是一个“安全”方面的基础库,也是一个“危险”层。“危险”层需要更加小心和相关的知识,并且使用它很容易出现安全漏洞。在这篇介绍性文章中,我们不会涵盖“危险”层中的任何内容!
+
+cryptography 库中最有用的高级安全功能是一种 Fernet 实现。Fernet 是一种遵循最佳实践的加密缓冲区的标准。它不适用于非常大的文件,如千兆字节以上的文件,因为它要求你一次加载要加密或解密的内容到内存缓冲区中。
+
+Fernet 支持对称(即密钥)加密方式*:加密和解密使用相同的密钥,因此必须保持安全。
+
+生成密钥很简单:
+
+```
+>>> k = fernet.Fernet.generate_key()
+>>> type(k)
+
+```
+
+这些字节可以写入有适当权限的文件,最好是在安全的机器上。
+
+有了密钥后,加密也很容易:
+
+```
+>>> frn = fernet.Fernet(k)
+>>> encrypted = frn.encrypt(b"x marks the spot")
+>>> encrypted[:10]
+b'gAAAAABb1'
+```
+
+如果在你的机器上加密,你会看到略微不同的值。不仅因为(我希望)你生成了和我不同的密钥,而且因为 Fernet 将要加密的值与一些随机生成的缓冲区连接起来。这是我之前提到的“最佳实践”之一:它将阻止对手分辨哪些加密值是相同的,这有时是攻击的重要部分。
+
+解密同样简单:
+
+```
+>>> frn = fernet.Fernet(k)
+>>> frn.decrypt(encrypted)
+b'x marks the spot'
+```
+
+请注意,这仅加密和解密*字节串*。为了加密和解密*文本串*,通常需要对它们使用 [UTF-8][3] 进行编码和解码。
+
+20 世纪中期密码学最有趣的进展之一是公钥加密。它可以在发布加密密钥的同时而让*解密密钥*保持保密。例如,它可用于保存服务器使用的 API 密钥:服务器是唯一可以访问解密密钥的一方,但是任何人都可以保存公共加密密钥。
+
+虽然 cryptography 没有任何支持公钥加密的*安全*功能,但 [PyNaCl][4] 库有。PyNaCl 封装并提供了一些很好的方法来使用 Daniel J. Bernstein 发明的 [NaCl][5] 加密系统。
+
+NaCl 始终同时加密和签名或者同时解密和验证签名。这是一种防止基于可伸缩性的攻击的方法,其中攻击者会修改加密值。
+
+加密是使用公钥完成的,而签名是使用密钥完成的:
+
+```
+>>> from nacl.public import PrivateKey, PublicKey, Box
+>>> source = PrivateKey.generate()
+>>> with open("target.pubkey", "rb") as fpin:
+... target_public_key = PublicKey(fpin.read())
+>>> enc_box = Box(source, target_public_key)
+>>> result = enc_box.encrypt(b"x marks the spot")
+>>> result[:4]
+b'\xe2\x1c0\xa4'
+```
+
+解密颠倒了角色:它需要私钥进行解密,需要公钥验证签名:
+
+```
+>>> from nacl.public import PrivateKey, PublicKey, Box
+>>> with open("source.pubkey", "rb") as fpin:
+... source_public_key = PublicKey(fpin.read())
+>>> with open("target.private_key", "rb") as fpin:
+... target = PrivateKey(fpin.read())
+>>> dec_box = Box(target, source_public_key)
+>>> dec_box.decrypt(result)
+b'x marks the spot'
+```
+
+最后,[PocketProtector][6] 库构建在 PyNaCl 之上,包含完整的密钥管理方案。
+
+--------------------------------------------------------------------------------
+
+via: https://opensource.com/article/19/4/cryptography-python
+
+作者:[Moshe Zadka][a]
+选题:[lujun9972][b]
+译者:[geekpi](https://github.com/geekpi)
+校对:[wxy](https://github.com/wxy)
+
+本文由 [LCTT](https://github.com/LCTT/TranslateProject) 原创编译,[Linux中国](https://linux.cn/) 荣誉推出
+
+[a]: https://opensource.com/users/moshez
+[b]: https://github.com/lujun9972
+[1]: https://opensource.com/sites/default/files/styles/image-full-size/public/lead-images/security-lock-cloud-safe.png?itok=yj2TFPzq (lock on world map)
+[2]: https://cryptography.io/en/latest/
+[3]: https://en.wikipedia.org/wiki/UTF-8
+[4]: https://pynacl.readthedocs.io/en/stable/
+[5]: https://nacl.cr.yp.to/
+[6]: https://github.com/SimpleLegal/pocket_protector/blob/master/USER_GUIDE.md
diff --git a/published/201905/20190408 How to quickly deploy, run Linux applications as unikernels.md b/published/201905/20190408 How to quickly deploy, run Linux applications as unikernels.md
new file mode 100644
index 0000000000..87753f2a68
--- /dev/null
+++ b/published/201905/20190408 How to quickly deploy, run Linux applications as unikernels.md
@@ -0,0 +1,74 @@
+[#]: collector: (lujun9972)
+[#]: translator: (geekpi)
+[#]: reviewer: (wxy)
+[#]: publisher: (wxy)
+[#]: url: (https://linux.cn/article-10822-1.html)
+[#]: subject: (How to quickly deploy, run Linux applications as unikernels)
+[#]: via: (https://www.networkworld.com/article/3387299/how-to-quickly-deploy-run-linux-applications-as-unikernels.html#tk.rss_all)
+[#]: author: (Sandra Henry-Stocker https://www.networkworld.com/author/Sandra-Henry_Stocker/)
+
+如何快速部署并作为 unikernel 运行 Linux 应用
+======
+
+unikernel 是一种用于在云基础架构上部署应用程序的更小、更快、更安全的方式。使用 NanoVMs OPS,任何人都可以将 Linux 应用程序作为 unikernel 运行而无需额外编码。
+
+![Marcho Verch \(CC BY 2.0\)][1]
+
+随着 unikernel 的出现,构建和部署轻量级应用变得更容易、更可靠。虽然功能有限,但 unikernal 在速度和安全性方面有许多优势。
+
+### 什么是 unikernel?
+
+unikernel 是一种非常特殊的单一地址空间的机器镜像,类似于已经主导大批互联网的云应用,但它们相当小并且是单一用途的。它们很轻,只提供所需的资源。它们加载速度非常快,而且安全性更高 —— 攻击面非常有限。单个可执行文件中包含所需的所有驱动、I/O 例程和支持库。其最终生成的虚拟镜像可以无需其它部分就可以引导和运行。它们通常比容器快 10 到 20 倍。
+
+潜在的攻击者无法进入 shell 并获得控制权,因为它没有 shell。他们无法获取系统的 `/etc/passwd`或 `/etc/shadow` 文件,因为这些文件不存在。创建一个 unikernel 就像应用将自己变成操作系统。使用 unikernel,应用和操作系统将成为一个单一的实体。你忽略了不需要的东西,从而消除了漏洞并大幅提高性能。
+
+简而言之,unikernel:
+
+* 提供更高的安全性(例如,shell 破解代码无用武之地)
+* 比标准云应用占用更小空间
+* 经过高度优化
+* 启动非常快
+
+### unikernel 有什么缺点吗?
+
+unikernel 的唯一严重缺点是你必须构建它们。对于许多开发人员来说,这是一个巨大的进步。由于应用的底层特性,将应用简化为所需的内容然后生成紧凑、平稳运行的应用可能很复杂。在过去,你几乎必须是系统开发人员或底层程序员才能生成它们。
+
+### 这是怎么改变的?
+
+最近(2019 年 3 月 24 日)[NanoVMs][3] 宣布了一个将任何 Linux 应用加载为 unikernel 的工具。使用 NanoVMs OPS,任何人都可以将 Linux 应用作为 unikernel 运行而无需额外编码。该应用还可以更快、更安全地运行,并且成本和开销更低。
+
+### 什么是 NanoVMs OPS?
+
+NanoVMs 是给开发人员的 unikernel 工具。它能让你运行各种企业级软件,但仍然可以非常严格地控制它的运行。
+
+使用 OPS 的其他好处包括:
+
+* 无需经验或知识,开发人员就可以构建 unikernel。
+* 该工具可在笔记本电脑上本地构建和运行 unikernel。
+* 无需创建帐户,只需下载并一个命令即可执行 OPS。
+
+NanoVMs 的介绍可以在 [Youtube 上的 NanoVMs 视频][5] 上找到。你还可以查看该公司的 [LinkedIn 页面][6]并在[此处][7]阅读有关 NanoVMs 安全性的信息。
+
+还有有关如何[入门][8]的一些信息。
+
+--------------------------------------------------------------------------------
+
+via: https://www.networkworld.com/article/3387299/how-to-quickly-deploy-run-linux-applications-as-unikernels.html
+
+作者:[Sandra Henry-Stocker][a]
+选题:[lujun9972][b]
+译者:[geekpi](https://github.com/geekpi)
+校对:[wxy](https://github.com/wxy)
+
+本文由 [LCTT](https://github.com/LCTT/TranslateProject) 原创编译,[Linux中国](https://linux.cn/) 荣誉推出
+
+[a]: https://www.networkworld.com/author/Sandra-Henry_Stocker/
+[b]: https://github.com/lujun9972
+[1]: https://images.idgesg.net/images/article/2019/04/corn-kernels-100792925-large.jpg
+[3]: https://nanovms.com/
+[5]: https://www.youtube.com/watch?v=VHWDGhuxHPM
+[6]: https://www.linkedin.com/company/nanovms/
+[7]: https://nanovms.com/security
+[8]: https://nanovms.gitbook.io/ops/getting_started
+[9]: https://www.facebook.com/NetworkWorld/
+[10]: https://www.linkedin.com/company/network-world
diff --git a/published/201905/20190409 Anbox - Easy Way To Run Android Apps On Linux.md b/published/201905/20190409 Anbox - Easy Way To Run Android Apps On Linux.md
new file mode 100644
index 0000000000..d4829d7344
--- /dev/null
+++ b/published/201905/20190409 Anbox - Easy Way To Run Android Apps On Linux.md
@@ -0,0 +1,177 @@
+[#]: collector: (lujun9972)
+[#]: translator: (robsean)
+[#]: reviewer: (wxy)
+[#]: publisher: (wxy)
+[#]: url: (https://linux.cn/article-10843-1.html)
+[#]: subject: (Anbox – Easy Way To Run Android Apps On Linux)
+[#]: via: (https://www.2daygeek.com/anbox-best-android-emulator-for-linux/)
+[#]: author: (Magesh Maruthamuthu https://www.2daygeek.com/author/magesh/)
+
+Anbox:在 Linux 上运行 Android 应用程序的简单方式
+======
+
+Android 模拟器允许我们直接从 Linux 系统上运行我们最喜欢的 Android 应用程序或游戏。对于 Linux 来说,有很多的这样的 Android 模拟器,在过去我们介绍过几个此类应用程序。
+
+你可以通过导航到下面的网址回顾它们。
+
+ * [如何在 Linux 上安装官方 Android 模拟器 (SDK)][1]
+ * [如何在 Linux 上安装 GenyMotion (Android 模拟器)][2]
+
+今天我们将讨论 Anbox Android 模拟器。
+
+### Anbox 是什么?
+
+Anbox 是 “Android in a box” 的缩写。Anbox 是一个基于容器的方法,可以在普通的 GNU/Linux 系统上启动完整的 Android 系统。
+
+它是现代化的新模拟器之一。
+
+Anbox 可以让你在 Linux 系统上运行 Android,而没有虚拟化的迟钝,因为核心的 Android 操作系统已经使用 Linux 命名空间(LXE)放置到容器中了。
+
+Android 容器不能直接访问到任何硬件,所有硬件的访问都是通过在主机上的守护进程进行的。
+
+每个应用程序将在一个单独窗口打开,就像其它本地系统应用程序一样,并且它可以显示在启动器中。
+
+### 如何在 Linux 中安装 Anbox ?
+
+Anbox 也可作为 snap 软件包安装,请确保你已经在你的系统上启用了 snap 支持。
+
+Anbox 软件包最近被添加到 Ubuntu 18.10 (Cosmic) 和 Debian 10 (Buster) 软件仓库。如果你正在运行这些版本,那么你可以轻松地在官方发行版的软件包管理器的帮助下安装。否则可以用 snap 软件包安装。
+
+为使 Anbox 工作,确保需要的内核模块已经安装在你的系统中。对于基于 Ubuntu 的用户,使用下面的 PPA 来安装它。
+
+```
+$ sudo add-apt-repository ppa:morphis/anbox-support
+$ sudo apt update
+$ sudo apt install linux-headers-generic anbox-modules-dkms
+```
+
+在你安装 `anbox-modules-dkms` 软件包后,你必须手动重新加载内核模块,或需要系统重新启动。
+
+```
+$ sudo modprobe ashmem_linux
+$ sudo modprobe binder_linux
+```
+
+对于 Debian/Ubuntu 系统,使用 [APT-GET 命令][3] 或 [APT 命令][4] 来安装 anbox。
+
+```
+$ sudo apt install anbox
+```
+
+对于基于 Arch Linux 的系统,我们总是习惯从 AUR 储存库中获取软件包。所以,使用任一个的 [AUR 助手][5] 来安装它。我喜欢使用 [Yay 工具][6]。
+
+```
+$ yuk -S anbox-git
+```
+
+否则,你可以通过导航到下面的文章来 [在 Linux 中安装和配置 snap][7]。如果你已经在你的系统上安装 snap,其它的步骤可以忽略。
+
+```
+$ sudo snap install --devmode --beta anbox
+```
+
+### Anbox 的必要条件
+
+默认情况下,Anbox 并没有带有 Google Play Store。因此,我们需要手动下载每个应用程序(APK),并使用 Android 调试桥(ADB)安装它。
+
+ADB 工具在大多数的发行版的软件仓库是轻易可获得的,我们可以容易地安装它。
+
+对于 Debian/Ubuntu 系统,使用 [APT-GET 命令][3] 或 [APT 命令][4] 来安装 ADB。
+
+```
+$ sudo apt install android-tools-adb
+```
+
+对于 Fedora 系统,使用 [DNF 命令][8] 来安装 ADB。
+
+```
+$ sudo dnf install android-tools
+```
+
+对于基于 Arch Linux 的系统,使用 [Pacman 命令][9] 来安装 ADB。
+
+```
+$ sudo pacman -S android-tools
+```
+
+对于 openSUSE Leap 系统,使用 [Zypper 命令][10] 来安装 ADB。
+
+```
+$ sudo zypper install android-tools
+```
+
+### 在哪里下载 Android 应用程序?
+
+既然我们不能使用 Play Store ,你就得从信得过的网站来下载 APK 软件包,像 [APKMirror][11] ,然后手动安装它。
+
+### 如何启动 Anbox?
+
+Anbox 可以从 Dash 启动。这是默认的 Anbox 外貌。
+
+![][13]
+
+### 如何把应用程序推到 Anbox ?
+
+像我先前所说,我们需要手动安装它。为测试目的,我们将安装 YouTube 和 Firefox 应用程序。
+
+首先,你需要启动 ADB 服务。为做到这样,运行下面的命令。
+
+```
+$ adb devices
+```
+
+我们已经下载 YouTube 和 Firefox 应用程序,现在我们将安装。
+
+语法格式:
+
+```
+$ adb install Name-Of-Your-Application.apk
+```
+
+安装 YouTube 和 Firefox 应用程序:
+
+```
+$ adb install 'com.google.android.youtube_14.13.54-1413542800_minAPI19(x86_64)(nodpi)_apkmirror.com.apk'
+Success
+
+$ adb install 'org.mozilla.focus_9.0-330191219_minAPI21(x86)(nodpi)_apkmirror.com.apk'
+Success
+```
+
+我已经在我的 Anbox 中安装 YouTube 和 Firefox。查看下面的截图。
+
+![][14]
+
+像我们在文章的开始所说,它将以新的标签页打开任何的应用程序。在这里,我们将打开 Firefox ,并访问 [2daygeek.com][15] 网站。
+
+![][16]
+
+--------------------------------------------------------------------------------
+
+via: https://www.2daygeek.com/anbox-best-android-emulator-for-linux/
+
+作者:[Magesh Maruthamuthu][a]
+选题:[lujun9972][b]
+译者:[robsean](https://github.com/robsean)
+校对:[wxy](https://github.com/wxy)
+
+本文由 [LCTT](https://github.com/LCTT/TranslateProject) 原创编译,[Linux中国](https://linux.cn/) 荣誉推出
+
+[a]: https://www.2daygeek.com/author/magesh/
+[b]: https://github.com/lujun9972
+[1]: https://www.2daygeek.com/install-configure-sdk-android-emulator-on-linux/
+[2]: https://www.2daygeek.com/install-genymotion-android-emulator-on-ubuntu-debian-fedora-arch-linux/
+[3]: https://www.2daygeek.com/apt-get-apt-cache-command-examples-manage-packages-debian-ubuntu-systems/
+[4]: https://www.2daygeek.com/apt-command-examples-manage-packages-debian-ubuntu-systems/
+[5]: https://www.2daygeek.com/category/aur-helper/
+[6]: https://www.2daygeek.com/install-yay-yet-another-yogurt-aur-helper-on-arch-linux/
+[7]: https://www.2daygeek.com/linux-snap-package-manager-ubuntu/
+[8]: https://www.2daygeek.com/dnf-command-examples-manage-packages-fedora-system/
+[9]: https://www.2daygeek.com/pacman-command-examples-manage-packages-arch-linux-system/
+[10]: https://www.2daygeek.com/zypper-command-examples-manage-packages-opensuse-system/
+[11]: https://www.apkmirror.com/
+[12]: data:image/gif;base64,R0lGODlhAQABAIAAAAAAAP///yH5BAEAAAAALAAAAAABAAEAAAIBRAA7
+[13]: https://www.2daygeek.com/wp-content/uploads/2019/04/anbox-best-android-emulator-for-linux-1.jpg
+[14]: https://www.2daygeek.com/wp-content/uploads/2019/04/anbox-best-android-emulator-for-linux-2.jpg
+[15]: https://www.2daygeek.com/
+[16]: https://www.2daygeek.com/wp-content/uploads/2019/04/anbox-best-android-emulator-for-linux-3.jpg
diff --git a/translated/tech/20190409 How To Install And Configure Chrony As NTP Client.md b/published/201905/20190409 How To Install And Configure Chrony As NTP Client.md
similarity index 56%
rename from translated/tech/20190409 How To Install And Configure Chrony As NTP Client.md
rename to published/201905/20190409 How To Install And Configure Chrony As NTP Client.md
index bd9ddaf2ef..cf25d7af66 100644
--- a/translated/tech/20190409 How To Install And Configure Chrony As NTP Client.md
+++ b/published/201905/20190409 How To Install And Configure Chrony As NTP Client.md
@@ -1,69 +1,59 @@
[#]: collector: (lujun9972)
[#]: translator: (arrowfeng)
-[#]: reviewer: ( )
-[#]: publisher: ( )
-[#]: url: ( )
+[#]: reviewer: (wxy)
+[#]: publisher: (wxy)
+[#]: url: (https://linux.cn/article-10820-1.html)
[#]: subject: (How To Install And Configure Chrony As NTP Client?)
[#]: via: (https://www.2daygeek.com/configure-ntp-client-using-chrony-in-linux/)
[#]: author: (Magesh Maruthamuthu https://www.2daygeek.com/author/magesh/)
-如何正确安装和配置Chrony作为NTP客户端?
+如何安装和配置 Chrony 作为 NTP 客户端?
======
-NTP服务器和NTP客户端运行我们通过网络来同步时钟。
+NTP 服务器和 NTP 客户端可以让我们通过网络来同步时钟。之前,我们已经撰写了一篇关于 [NTP 服务器和 NTP 客户端的安装与配置][1] 的文章。
-在过去,我们已经撰写了一篇关于 **[NTP服务器和NTP客户端的安装与配置][1]** 的文章。
+如果你想看这些内容,点击上述的 URL 访问。
-如果你想看这些内容,点击上述的URL访问。
+### Chrony 客户端
-### 什么是Chrony客户端?
+Chrony 是 NTP 客户端的替代品。它能以更精确的时间和更快的速度同步时钟,并且它对于那些不是全天候在线的系统非常有用。
-Chrony是NTP客户端的替代品。
-
-它能以更精确的时间和更快的速度同步时钟,并且它对于那些不是全天候在线的系统非常有用。
-
-chronyd更小、更省电,它占用更少的内存且仅当需要时它才唤醒CPU。
-
-即使网络拥塞较长时间,它也能很好地运行。
-
-它支持Linux上的硬件时间戳,允许在本地网络进行极其准确的同步。
+chronyd 更小、更节能,它占用更少的内存且仅当需要时它才唤醒 CPU。即使网络拥塞较长时间,它也能很好地运行。它支持 Linux 上的硬件时间戳,允许在本地网络进行极其准确的同步。
它提供下列两个服务。
- * **`chronyc:`** Chrony的命令行接口。
- * **`chronyd:`** Chrony守护进程服务。
+ * `chronyc`:Chrony 的命令行接口。
+ * `chronyd`:Chrony 守护进程服务。
-
-
-### 如何在Linux上安装和配置Chrony?
+### 如何在 Linux 上安装和配置 Chrony?
由于安装包在大多数发行版的官方仓库中可用,因此直接使用包管理器去安装它。
-对于 **`Fedora`** 系统, 使用 **[DNF 命令][2]** 去安装chrony.
+对于 Fedora 系统,使用 [DNF 命令][2] 去安装 chrony。
```
$ sudo dnf install chrony
```
-对于 **`Debian/Ubuntu`** 系统, 使用 **[APT-GET 命令][3]** 或者 **[APT 命令][4]** 去安装chrony.
+对于 Debian/Ubuntu 系统,使用 [APT-GET 命令][3] 或者 [APT 命令][4] 去安装 chrony。
```
$ sudo apt install chrony
```
-对基于 **`Arch Linux`** 的系统, 使用 **[Pacman 命令][5]** 去安装chrony.
+对基于 Arch Linux 的系统,使用 [Pacman 命令][5] 去安装 chrony。
```
$ sudo pacman -S chrony
```
-对于 **`RHEL/CentOS`** 系统, 使用 **[YUM 命令][6]** 去安装chrony.
+对于 RHEL/CentOS 系统,使用 [YUM 命令][6] 去安装 chrony。
```
$ sudo yum install chrony
```
-对于**`openSUSE Leap`** 系统, 使用 **[Zypper 命令][7]** 去安装chrony.
+对于 openSUSE Leap 系统,使用 [Zypper 命令][7] 去安装 chrony。
```
$ sudo zypper install chrony
@@ -71,20 +61,18 @@ $ sudo zypper install chrony
在这篇文章中,我们将使用下列设置去测试。
- * **`NTP服务器:`** 主机名: CentOS7.2daygeek.com, IP:192.168.1.5, OS:CentOS 7
- * **`Chrony客户端:`** 主机名: Ubuntu18.2daygeek.com, IP:192.168.1.3, OS:Ubuntu 18.04
+ * NTP 服务器:主机名:CentOS7.2daygeek.com,IP:192.168.1.5,OS:CentOS 7
+ * Chrony 客户端:主机名:Ubuntu18.2daygeek.com,IP:192.168.1.3,OS:Ubuntu 18.04
+服务器的安装请访问 [在 Linux 上安装和配置 NTP 服务器][1] 的 URL。
-导航到 **[在Linux上安装和配置NTP服务器][1]** 的URL。
+我已经在 CentOS7.2daygeek.com 这台主机上安装和配置了 NTP 服务器,因此,将其附加到所有的客户端机器上。此外,还包括其他所需信息。
+`chrony.conf` 文件的位置根据你的发行版不同而不同。
-我已经在`CentOS7.2daygeek.com`这台主机上安装和配置了NTP服务器,因此,将其附加到所有的客户端机器上。此外,还包括其他所需信息。
+对基于 RHEL 的系统,它位于 `/etc/chrony.conf`。
-`chrony.conf`文件的位置根据你的发行版不同而不同。
-
-对基于RHEL的系统,它位于`/etc/chrony.conf`。
-
-对基于Debian的系统,它位于`/etc/chrony/chrony.conf`。
+对基于 Debian 的系统,它位于 `/etc/chrony/chrony.conf`。
```
# vi /etc/chrony/chrony.conf
@@ -98,28 +86,25 @@ makestep 1 3
cmdallow 192.168.1.0/24
```
-更新配置后需要重启Chrony服务。
+更新配置后需要重启 Chrony 服务。
-对于sysvinit系统。基于RHEL的系统需要去运行`chronyd`而不是chrony。
+对于 sysvinit 系统。基于 RHEL 的系统需要去运行 `chronyd` 而不是 `chrony`。
```
# service chronyd restart
-
# chkconfig chronyd on
```
-对于systemctl系统。 基于RHEL的系统需要去运行`chronyd`而不是chrony。
+对于 systemctl 系统。 基于 RHEL 的系统需要去运行 `chronyd` 而不是 `chrony`。
```
# systemctl restart chronyd
-
# systemctl enable chronyd
```
-使用像tacking,sources和sourcestats这样的命令去检查chrony的同步细节。
-
-去检查chrony的跟踪状态。
+使用像 `tacking`、`sources` 和 `sourcestats` 这样的子命令去检查 chrony 的同步细节。
+去检查 chrony 的追踪状态。
```
# chronyc tracking
@@ -138,7 +123,7 @@ Update interval : 2.0 seconds
Leap status : Normal
```
-运行sources命令去显示当前时间源的信息。
+运行 `sources` 命令去显示当前时间源的信息。
```
# chronyc sources
@@ -148,7 +133,7 @@ MS Name/IP address Stratum Poll Reach LastRx Last sample
^* CentOS7.2daygeek.com 2 6 17 62 +36us[+1230us] +/- 1111ms
```
-sourcestats命令显示有关chronyd当前正在检查的每个源的漂移率和偏移估计过程的信息。
+`sourcestats` 命令显示有关 chronyd 当前正在检查的每个源的漂移率和偏移估计过程的信息。
```
# chronyc sourcestats
@@ -158,7 +143,7 @@ Name/IP Address NP NR Span Frequency Freq Skew Offset Std Dev
CentOS7.2daygeek.com 5 3 71 -97.314 78.754 -469us 441us
```
-当chronyd配置为NTP客户端或对等端时,你就能通过chronyc ntpdata命令向每一个NTP源发送和接收时间戳模式和交错模式报告。
+当 chronyd 配置为 NTP 客户端或对等端时,你就能通过 `chronyc ntpdata` 命令向每一个 NTP 源发送/接收时间戳模式和交错模式的报告。
```
# chronyc ntpdata
@@ -191,15 +176,14 @@ Total RX : 46
Total valid RX : 46
```
-最后运行`date`命令。
+最后运行 `date` 命令。
```
# date
Thu Mar 28 03:08:11 CDT 2019
```
-为了立即切换系统时钟,通过转换绕过任何正在进行的调整,请以root身份发出以下命令(手动调整系统时钟)。
-To step the system clock immediately, bypassing any adjustments in progress by slewing, issue the following command as root (To adjust the system clock manually).
+为了立即跟进系统时钟,绕过任何正在进行的缓步调整,请以 root 身份运行以下命令(以手动调整系统时钟)。
```
# chronyc makestep
@@ -212,13 +196,13 @@ via: https://www.2daygeek.com/configure-ntp-client-using-chrony-in-linux/
作者:[Magesh Maruthamuthu][a]
选题:[lujun9972][b]
译者:[arrowfeng](https://github.com/arrowfeng)
-校对:[校对者ID](https://github.com/校对者ID)
+校对:[wxy](https://github.com/wxy)
本文由 [LCTT](https://github.com/LCTT/TranslateProject) 原创编译,[Linux中国](https://linux.cn/) 荣誉推出
[a]: https://www.2daygeek.com/author/magesh/
[b]: https://github.com/lujun9972
-[1]: https://www.2daygeek.com/install-configure-ntp-server-ntp-client-in-linux/
+[1]: https://linux.cn/article-10811-1.html
[2]: https://www.2daygeek.com/dnf-command-examples-manage-packages-fedora-system/
[3]: https://www.2daygeek.com/apt-get-apt-cache-command-examples-manage-packages-debian-ubuntu-systems/
[4]: https://www.2daygeek.com/apt-command-examples-manage-packages-debian-ubuntu-systems/
diff --git a/published/20190409 How To Install And Configure NTP Server And NTP Client In Linux.md b/published/201905/20190409 How To Install And Configure NTP Server And NTP Client In Linux.md
similarity index 100%
rename from published/20190409 How To Install And Configure NTP Server And NTP Client In Linux.md
rename to published/201905/20190409 How To Install And Configure NTP Server And NTP Client In Linux.md
diff --git a/translated/tech/20190411 Installing Ubuntu MATE on a Raspberry Pi.md b/published/201905/20190411 Installing Ubuntu MATE on a Raspberry Pi.md
similarity index 62%
rename from translated/tech/20190411 Installing Ubuntu MATE on a Raspberry Pi.md
rename to published/201905/20190411 Installing Ubuntu MATE on a Raspberry Pi.md
index 74d0ac4d2e..2712782f24 100644
--- a/translated/tech/20190411 Installing Ubuntu MATE on a Raspberry Pi.md
+++ b/published/201905/20190411 Installing Ubuntu MATE on a Raspberry Pi.md
@@ -1,49 +1,46 @@
[#]: collector: (lujun9972)
[#]: translator: (warmfrog)
-[#]: reviewer: ( )
-[#]: publisher: ( )
-[#]: url: ( )
+[#]: reviewer: (wxy)
+[#]: publisher: (wxy)
+[#]: url: (https://linux.cn/article-10817-1.html)
[#]: subject: (Installing Ubuntu MATE on a Raspberry Pi)
[#]: via: (https://itsfoss.com/ubuntu-mate-raspberry-pi/)
[#]: author: (Chinmay https://itsfoss.com/author/chinmay/)
-在 Raspberry Pi 上安装 Ubuntu MATE
+在树莓派上安装 Ubuntu MATE
=================================
-_**简介: 这篇快速指南告诉你如何在 Raspberry Pi 设备上安装 Ubuntu MATE。**_
+> 简介: 这篇快速指南告诉你如何在树莓派设备上安装 Ubuntu MATE。
-[Raspberry Pi][1] 是目前最流行的单板机并且是制造商的首选。[Raspbian][2] 是基于 Debian 的 Pi 的官方操作系统。它是轻量级的,内置了教育工具和能在大部分场景下完成工作的工具。
-
-[安装 Raspbian][3] 安装同样简单,但是与 [Debian][4] 一起的问题是慢的升级周期和旧的软件包。
-
-在 Raspberry Pi 上运行 Ubuntu 给你带来一个更丰富的体验和最新的软件。当在你的 Pi 上运行 Ubuntu 时我们有几个选择。
-
- 1. [Ubuntu MATE][5] :Ubuntu MATE 是仅有的原生支持 Raspberry Pi 包含一个完整的桌面环境的分发版。
- 2. [Ubuntu Server 18.04][6] \+ 手动安装一个桌面环境。
- 3. 使用 [Ubuntu Pi Flavor Maker][7] 社区构建的镜像,_这些镜像只支持 Raspberry Pi 2B 和 3B 的变种_并且**不能**更新到最新的 LTS 发布版。
+[树莓派][1] 是目前最流行的单板机并且是创客首选的板子。[Raspbian][2] 是基于 Debian 的树莓派官方操作系统。它是轻量级的,内置了教育工具和能在大部分场景下完成工作的工具。
+[安装 Raspbian][3] 安装同样简单,但是与 [Debian][4] 随同带来的问题是慢的升级周期和旧的软件包。
+在树莓派上运行 Ubuntu 可以给你带来一个更丰富的体验和最新的软件。当在你的树莓派上运行 Ubuntu 时我们有几个选择。
+ 1. [Ubuntu MATE][5] :Ubuntu MATE 是仅有的原生支持树莓派且包含一个完整的桌面环境的发行版。
+ 2. [Ubuntu Server 18.04][6] + 手动安装一个桌面环境。
+ 3. 使用 [Ubuntu Pi Flavor Maker][7] 社区构建的镜像,这些镜像只支持树莓派 2B 和 3B 的变种,并且**不能**更新到最新的 LTS 发布版。
第一个选择安装是最简单和快速的,而第二个选择给了你自由选择安装桌面环境的机会。我推荐选择前两个中的任一个。
这里是一些磁盘镜像下载链接。在这篇文章里我只会提及 Ubuntu MATE 的安装。
-### 在 Raspberry Pi 上安装 Ubuntu MATE
+### 在树莓派上安装 Ubuntu MATE
去 Ubuntu MATE 的下载页面获取推荐的镜像。
![][8]
-试验 ARM64 版只应在你需要在 Raspberry Pi 服务器上运行像 MongoDB 这样的 64-bit 应用时使用。
+试验性的 ARM64 版本只应在你需要在树莓派服务器上运行像 MongoDB 这样的 64 位应用时使用。
-[ 下载为 Raspberry Pi 准备的 Ubuntu MATE][9]
+- [下载为树莓派准备的 Ubuntu MATE][9]
#### 第 1 步:设置 SD 卡
-镜像文件一旦下载完成后需要解压。你应该简单的右击来提取它。
+镜像文件一旦下载完成后需要解压。你可以简单的右击来提取它。
-可替换地,下面命令做同样的事。
+也可以使用下面命令做同样的事。
```
xz -d ubuntu-mate***.img.xz
@@ -51,7 +48,7 @@ xz -d ubuntu-mate***.img.xz
如果你在 Windows 上你可以使用 [7-zip][10] 替代。
-安装 **[Balena Etcher][11]**,我们将使用这个工具将镜像写入 SD 卡。确保你的 SD 卡有至少 8 GB 的容量。
+安装 [Balena Etcher][11],我们将使用这个工具将镜像写入 SD 卡。确保你的 SD 卡有至少 8 GB 的容量。
启动 Etcher,选择镜像文件和 SD 卡。
@@ -59,21 +56,19 @@ xz -d ubuntu-mate***.img.xz
一旦进度完成 SD 卡就准备好了。
-#### 第 2 步:设置 Raspberry Pi
+#### 第 2 步:设置树莓派
-你可能已经知道你需要一些外设才能使用 Raspberry Pi 例如 鼠标,键盘, HDMI 线等等。你同样可以[不用键盘和鼠标安装 Raspberry Pi][13] 但是这篇指南不是那样。
+你可能已经知道你需要一些外设才能使用树莓派,例如鼠标、键盘、HDMI 线等等。你同样可以[不用键盘和鼠标安装树莓派][13],但是这篇指南不是那样。
* 插入一个鼠标和一个键盘。
* 连接 HDMI 线缆。
* 插入 SD 卡 到 SD 卡槽。
-
-
-插入电源线给它供电。确保你有一个好的电源供应(5V,3A 至少)。一个不好的电源供应可能降低性能。
+插入电源线给它供电。确保你有一个好的电源供应(5V、3A 至少)。一个不好的电源供应可能降低性能。
#### Ubuntu MATE 安装
-一旦你给 Raspberry Pi 供电,你将遇到非常熟悉的 Ubuntu 安装过程。在这里的安装过程相当直接。
+一旦你给树莓派供电,你将遇到非常熟悉的 Ubuntu 安装过程。在这里的安装过程相当直接。
![选择你的键盘布局][14]
@@ -83,7 +78,7 @@ xz -d ubuntu-mate***.img.xz
![添加用户名和密码][16]
-在设置了键盘布局,时区和用户凭证后,在几分钟后你将被带到登录界面。瞧!你快要完成了。
+在设置了键盘布局、时区和用户凭证后,在几分钟后你将被带到登录界面。瞧!你快要完成了。
![][17]
@@ -98,9 +93,9 @@ sudo apt upgrade
![][19]
-一旦更新完成安装你就可以开始了。你可以根据你的需要继续安装 Raspberry Pi 平台的为 GPIO 和其他 I/O 准备的特定软件包。
+一旦更新完成安装你就可以开始了。你可以根据你的需要继续安装树莓派平台为 GPIO 和其他 I/O 准备的特定软件包。
-是什么让你考虑在 Raspberry 上安装 Ubuntu,你对 Raspbian 的体验如何呢?在下方评论来让我知道。
+是什么让你考虑在 Raspberry 上安装 Ubuntu,你对 Raspbian 的体验如何呢?请在下方评论来让我知道。
--------------------------------------------------------------------------------
@@ -109,7 +104,7 @@ via: https://itsfoss.com/ubuntu-mate-raspberry-pi/
作者:[Chinmay][a]
选题:[lujun9972][b]
译者:[warmfrog](https://github.com/warmfrog)
-校对:[校对者ID](https://github.com/校对者ID)
+校对:[wxy](https://github.com/wxy)
本文由 [LCTT](https://github.com/LCTT/TranslateProject) 原创编译,[Linux中国](https://linux.cn/) 荣誉推出
diff --git a/translated/tech/20190415 12 Single Board Computers- Alternative to Raspberry Pi.md b/published/201905/20190415 12 Single Board Computers- Alternative to Raspberry Pi.md
similarity index 53%
rename from translated/tech/20190415 12 Single Board Computers- Alternative to Raspberry Pi.md
rename to published/201905/20190415 12 Single Board Computers- Alternative to Raspberry Pi.md
index 4e1fc6a6e9..742fca39da 100644
--- a/translated/tech/20190415 12 Single Board Computers- Alternative to Raspberry Pi.md
+++ b/published/201905/20190415 12 Single Board Computers- Alternative to Raspberry Pi.md
@@ -1,38 +1,38 @@
[#]: collector: (lujun9972)
[#]: translator: (warmfrog)
-[#]: reviewer: ( )
-[#]: publisher: ( )
-[#]: url: ( )
+[#]: reviewer: (wxy)
+[#]: publisher: (wxy)
+[#]: url: (https://linux.cn/article-10823-1.html)
[#]: subject: (12 Single Board Computers: Alternative to Raspberry Pi)
[#]: via: (https://itsfoss.com/raspberry-pi-alternatives/)
[#]: author: (Ankush Das https://itsfoss.com/author/ankush/)
-12 个可替换 Raspberry Pi 的单片机
+12 个可替代树莓派的单板机
================================
-_**简介: 正在寻找 Raspberry Pi 的替代品? 这里有一些单片机可以满足你的 DIY 渴求**_
+> 正在寻找树莓派的替代品?这里有一些单板机可以满足你的 DIY 渴求。
-Raspberry Pi 是当前最流行的单片机。你可以在你的 DIY 项目中使用它,或者用它作为一个成本效益高的系统来学习编代码,或者为了你的便利,利用一个[流媒体软件][1]运行在上面作为流媒体设备。
+树莓派是当前最流行的单板机。你可以在你的 DIY 项目中使用它,或者用它作为一个成本效益高的系统来学习编代码,或者为了你的便利,利用一个[流媒体软件][1]运行在上面作为流媒体设备。
-你可以使用 Raspberry Pi 做很多事,但它不是各种极客的最终解决方案。一些人可能在寻找更便宜的开发板,一些可能在寻找更强大的。
+你可以使用树莓派做很多事,但它不是各种极客的最终解决方案。一些人可能在寻找更便宜的开发板,一些可能在寻找更强大的。
-无论是哪种情况,我们都有很多原因需要 Raspberry Pi 的替代品。因此,在这片文章里,我们将讨论最好的十个我们认为能够替代 Raspberry Pi 的单片机。
+无论是哪种情况,我们都有很多原因需要树莓派的替代品。因此,在这片文章里,我们将讨论最好的 12 个我们认为能够替代树莓派的单板机。
![][2]
-### 满足你 DIY 渴望的 Raspberry Pi 替代品
+### 满足你 DIY 渴望的树莓派替代品
-这个列表没有特定的顺序排名。链接的一部分是附属链接。请阅读我们的[附属政策][3].
+这个列表没有特定的顺序排名。链接的一部分是赞助链接。请阅读我们的[赞助政策][3]。
-#### 1\. Onion Omega2+
+#### 1、Onion Omega2+
![][4]
-只要 **$13**,Omega2+ 是这里你可以找到的最便宜的 IoT 单片机设备。它运行 LEDE(Linux 嵌入式开发环境)Linux 系统 - 一个基于 [OpenWRT][5] 的分发版。
+只要 $13,Omega2+ 是这里你可以找到的最便宜的 IoT 单板机设备。它运行 LEDE(Linux 嵌入式开发环境)Linux 系统 —— 这是一个基于 [OpenWRT][5] 的发行版。
-由于运行一个自定义 Linux 系统,它的组成因素,花费,和灵活性使它完美适合几乎所有类型的 IoT 应用。
+由于运行一个自定义 Linux 系统,它的组成元件、花费和灵活性使它完美适合几乎所有类型的 IoT 应用。
-你可以在[亚马逊商城的 Onion Omega 装备][6]或者从他们的网站下单,可能会收取额外的邮费。
+你可以在[亚马逊商城的 Onion Omega 套件][6]或者从他们的网站下单,可能会收取额外的邮费。
**关键参数:**
@@ -44,15 +44,15 @@ Raspberry Pi 是当前最流行的单片机。你可以在你的 DIY 项目中
* USB 2.0
* 12 GPIO Pins
- [查看官网][7]
+[查看官网][7]
-#### 2\. NVIDIA Jetson Nano Developer Kit
+#### 2、NVIDIA Jetson Nano Developer Kit
-这是来自 NVIDIA 的只要 **$99** 的非常独特和有趣的 Raspberry Pi 替代品。是的,它不是每个人都能充分利用的设备 - 只为特定的一组极客或者开发者。
+这是来自 NVIDIA 的只要 **$99** 的非常独特和有趣的树莓派替代品。是的,它不是每个人都能充分利用的设备 —— 只为特定的一组极客或者开发者而生。
NVIDIA 使用下面的用例解释它:
-> NVIDIA® Jetson Nano™ Developer Kit 是一个小的,强大的让你并行运行多个神经网络的应用像图像分类,对象侦察,分段,语音处理。全部在一个易于使用的运行功率只有 5 瓦特平台。
+> NVIDIA® Jetson Nano™ Developer Kit 是一个小的、强大的计算机,可以让你并行运行多个神经网络的应用像图像分类、对象侦察、图像分段、语音处理。全部在一个易于使用的、运行功率只有 5 瓦特的平台上。
>
> nvidia
@@ -66,20 +66,17 @@ NVIDIA 使用下面的用例解释它:
* Display: HDMI 2.0
* 4 x USB 3.0 and eDP 1.4
+[查看官网][9]
-
-[查看官网
-][9]
-
-#### 3\. ASUS Tinker Board S
+#### 3、ASUS Tinker Board S
![][10]
-ASUS Tinker Board S 不是大多数可负担得起的可替代 Raspberry Pi 的替换设备 (**$82**, [亚马逊商城][11]),但是它是一个强大的替代品。它的特点是有你通常可以发现与标准 Raspberry Pi 3 Model 一样的 40 针脚的连接器,但是提供了强大的处理器和 GPU。同样的,Tinker Board S 的大小恰巧和标准的 Raspberry Pi 3 一样大。
+ASUS Tinker Board S 不是大多数人可负担得起的树莓派的替换设备 (**$82**,[亚马逊商城][11]),但是它是一个强大的替代品。它的特点是它有你通常可以发现与标准树莓派 3 一样的 40 针脚的连接器,但是提供了强大的处理器和 GPU。同样的,Tinker Board S 的大小恰巧和标准的树莓派3 一样大。
这个板子的主要亮点是 16 GB [eMMC][12] (用外行术语说,它的板上有一个类似 SSD 的存储单元使它工作时运行的更快。) 的存在。
-**关键参数**
+**关键参数:**
* Rockchip Quad-Core RK3288 processor
* 2 GB DDR3 RAM
@@ -92,20 +89,17 @@ ASUS Tinker Board S 不是大多数可负担得起的可替代 Raspberry Pi 的
* 28 GPIO pins
* HDMI Interface
+[查看网站][13]
-
-[查看网站
-][13]
-
-#### 4\. ClockworkPi
+#### 4、ClockworkPi
![][14]
-如果你在想方设法组装一个模块化的复古的游戏控制台,Clockwork Pi 通常是 [GameShell Kit][15] 的一部分。然而,你可以 使用 $49 单独购买板子。
+如果你正在想方设法组装一个模块化的复古的游戏控制台,Clockwork Pi 可能就是你需要的,它通常是 [GameShell Kit][15] 的一部分。然而,你可以 使用 $49 单独购买板子。
-它紧凑的大小,WiFi 连接性,和 micro HDMI 端口的存在使它成为很多事物的选择。
+它紧凑的大小、WiFi 连接性和 micro HDMI 端口的存在使它成为许多方面的选择。
-**关键参数**
+**关键参数:**
* Allwinner R16-J Quad-core Cortex-A7 CPU @1.2GHz
* Mali-400 MP2 GPU
@@ -114,41 +108,33 @@ ASUS Tinker Board S 不是大多数可负担得起的可替代 Raspberry Pi 的
* Micro HDMI output
* MicroSD Card Slot
+[查看官网][16]
-
-[查看官网
-][16]
-
-#### 5\. Arduino Mega 2560
+#### 5、Arduino Mega 2560
![][17]
-如果你正在研究机器人项目或者你想要一个 3D 打印机 - Arduino Mega 2560 将是 Raspberry Pi 的便利的替代品。不像 Raspberry Pi,它是基于微控制器而不是微处理器的。
+如果你正在研究机器人项目或者你想要一个 3D 打印机 —— Arduino Mega 2560 将是树莓派的便利的替代品。不像树莓派,它是基于微控制器而不是微处理器的。
-在他们的[官网][18],它会花费你 $38.50 或者在[在亚马逊商城 $33][19]。
+在他们的[官网][18],你需要花费 $38.50,或者在[在亚马逊商城是 $33][19]。
**关键参数:**
-**Key Specifications:**
-
* Microcontroller: ATmega2560
* Clock Speed: 16 MHz
* Digital I/O Pins: 54
* Analog Input Pins: 16
* Flash Memory: 256 KB of which 8 KB used by bootloader
+[查看官网][18]
-
-[查看官网
-][18]
-
-#### 6\. Rock64 Media Board
+#### 6、Rock64 Media Board
![][20]
-对于与你可能想要 Raspberry Pi 3 B+ 相同的投资,你将在 Rock64 Media Board 上获得更快的处理器和双倍的内存。除此之外,如果你想要 1 GB RAM 版的,它提供了一个 Raspberry Pi 的 更便宜的替代,花费更少,只要 $10 。
+用与你可能想要的树莓派 3 B+ 相同的价格,你将在 Rock64 Media Board 上获得更快的处理器和双倍的内存。除此之外,如果你想要 1 GB RAM 版的,它提供了一个比树莓派更便宜的替代品,花费更少,只要 $10 。
-不像 Raspberry Pi,这里没有无线连接支持,但是 USB 3.0 和 HDMI 2.0 的存在使它与众不同,如果它对你很重要的话。
+不像树莓派,它没有无线连接支持,但是 USB 3.0 和 HDMI 2.0 的存在使它与众不同,如果它对你很重要的话。
**关键参数:**
@@ -159,20 +145,18 @@ ASUS Tinker Board S 不是大多数可负担得起的可替代 Raspberry Pi 的
* USB 3.0
* HDMI 2.0
+[查看官网][21]
-
-[查看官网
-][21]
-
-#### 7\. Odroid-XU4
+#### 7、Odroid-XU4
![][22]
-Odroid-XU4 是一个完美的 Raspberry Pi 的替代,如果你有能够稍微提高预算的空间($80-$100 甚至更低,取决于存储的容量)。
+Odroid-XU4 是一个完美的树莓派的替代品,如果你有能够稍微提高预算的空间($80-$100 甚至更低,取决于存储的容量)。
-它确实是一个强大的替代并且体积更小。 支持 eMMC 和 USB 3.0 使它工作起来更快。
+它确实是一个强大的替代品并且体积更小。支持 eMMC 和 USB 3.0 使它工作起来更快。
**关键参数:**
+
* Samsung Exynos 5422 Octa ARM Cortex™-A15 Quad 2Ghz and Cortex™-A7 Quad 1.3GHz CPUs
* 2Gbyte LPDDR3 RAM
* GPU: Mali-T628 MP6
@@ -181,16 +165,13 @@ Odroid-XU4 是一个完美的 Raspberry Pi 的替代,如果你有能够稍微提
* eMMC 5.0 module socket
* MicroSD Card Slot
+[查看官网][23]
-
-[查看官网
-][23]
-
-#### 8\. **PocketBeagle**
+#### 8、PocketBeagle
![][24]
-它是一个难以置信的小的单片机 - 几乎和 Raspberry Pi Zero 相似。然而它会花费完全大小的 Raspberry Pi 3 相同的价格。主要的亮点是你可以用它作为一个 USB 便携式信息终端 并且进入 Linux 命令行工作。
+它是一个难以置信的小的单板机 —— 几乎和树莓派Zero 相似。然而它的价格相当于完整大小的树莓派 3。主要的亮点是你可以用它作为一个 USB 便携式信息终端,并且进入 Linux 命令行工作。
**关键参数:**
@@ -200,22 +181,18 @@ Odroid-XU4 是一个完美的 Raspberry Pi 的替代,如果你有能够稍微提
* microUSB
* USB 2.0
+[查看官网][25]
-
-[查看官网
-][25]
-
-#### 9\. Le Potato
+#### 9、Le Potato
![][26]
-由 [Libre Computer][27] 出品的 Le Potato,同样被它的型号 AML-S905X-CC 标识。它花费你 [$45][28]。
+由 [Libre Computer][27] 出品的 Le Potato,其型号是 AML-S905X-CC。它需要花费你 [$45][28]。
-如果你花费的比 Raspberry Pi 更多的钱,你就能得到想要双倍内存和 HDMI 2.0 接口,这可能是一个完美的选择。尽管,你还是不能发现嵌入的无线连接。
+如果你花费的比树莓派更多的钱,你就能得到双倍内存和 HDMI 2.0 接口,这可能是一个完美的选择。尽管,你还是不能找到嵌入的无线连接。
**关键参数:**
-
* Amlogic S905X SoC
* 2GB DDR3 SDRAM
* USB 2.0
@@ -224,18 +201,15 @@ Odroid-XU4 是一个完美的 Raspberry Pi 的替代,如果你有能够稍微提
* MicroSD Card Slot
* eMMC Interface
+[查看官网][29]
-
-[查看官网
-][29]
-
-#### 10\. Banana Pi M64
+#### 10、Banana Pi M64
![][30]
-它自带了 8 Gigs 的 eMMC - 是替代 Raspberry Pi 的主要亮点。由于相同的原因,它花费 $60。
+它自带了 8G 的 eMMC —— 这是替代树莓派的主要亮点。因此,它需要花费 $60。
-HDMI 接口的存在使它胜任 4K。除此之外,Banana Pi 提供了更多种类的开源单片机作为 Raspberry Pi 的替代。
+HDMI 接口的存在使它胜任 4K。除此之外,Banana Pi 提供了更多种类的开源单板机作为树莓派的替代。
**关键参数:**
@@ -246,18 +220,15 @@ HDMI 接口的存在使它胜任 4K。除此之外,Banana Pi 提供了更多
* USB 2.0
* HDMI
+[查看官网][31]
-
-[查看官网
-][31]
-
-#### 11\. Orange Pi Zero
+#### 11、Orange Pi Zero
![][32]
-Orange Pi Zero 相对于 Raspberry Pi 难以置信的便宜。你可以在 Aliexpress 或者亚马逊上以最多 $10 就能够获得。如果[稍微投资多点,你能够获得 512 MB RAM][33]。
+Orange Pi Zero 相对于树莓派来说难以置信的便宜。你可以在 Aliexpress 或者亚马逊上以最多 $10 就能够获得。如果[稍微多花点,你能够获得 512 MB RAM][33]。
-如果这还不够充分,你可以花费大概 $25 获得更好的配置像 Orange Pi 3。
+如果这还不够,你可以花费大概 $25 获得更好的配置,比如 Orange Pi 3。
**关键参数:**
@@ -268,18 +239,15 @@ Orange Pi Zero 相对于 Raspberry Pi 难以置信的便宜。你可以在 Aliex
* WiFi
* USB 2.0
+[查看官网][34]
-
-[查看官网
-][34]
-
-#### 12\. VIM 2 SBC by Khadas
+#### 12、VIM 2 SBC by Khadas
![][35]
-由 Khadas 出品的 VIM 2 是最新的单片机,因此你能够在板上获取到蓝牙 5.0。[从 $99 的基础款到上限 $140][36].
+由 Khadas 出品的 VIM 2 是最新的单板机,因此你能够在板上得到蓝牙 5.0 支持。它的价格范围[从 $99 的基础款到上限 $140][36]。
-基础款包含 2 GB RAM,16 GB eMMC 和蓝牙 4.1。然而,Pro/Max 版包含蓝牙 5.0,更多的内存,更多的 eMMC 存储。
+基础款包含 2 GB RAM、16 GB eMMC 和蓝牙 4.1。然而,Pro/Max 版包含蓝牙 5.0,更多的内存,更多的 eMMC 存储。
**关键参数:**
@@ -292,13 +260,11 @@ Orange Pi Zero 相对于 Raspberry Pi 难以置信的便宜。你可以在 Aliex
* HDMI 2.0a
* WiFi
+### 总结
+我们知道有很多不同种类的单板机电脑。一些比树莓派更好 —— 它的一些小规格的版本有更便宜的价格。同样的,像 Jetson Nano 这样的单板机已经被裁剪用于特定用途。因此,取决于你需要什么 —— 你应该检查一下单板机的配置。
-**总结**
-
-我们知道有很多不同种类的单片机电脑。一些比 Raspberry Pi 更好 - 它的一些小规格的版本有更便宜的价格。同样的,单片机像 Jetson Nano 已经被裁剪用于特定用途。因此,取决于你需要什么 - 你应该验证单片机的配置。
-
-如果你认为你知道比上述提到的更好的东西,请随意在下方评论来让我们知道。
+如果你知道比上述提到的更好的东西,请随意在下方评论来让我们知道。
--------------------------------------------------------------------------------
@@ -307,7 +273,7 @@ via: https://itsfoss.com/raspberry-pi-alternatives/
作者:[Ankush Das][a]
选题:[lujun9972][b]
译者:[warmfrog](https://github.com/warmfrog)
-校对:[校对者ID](https://github.com/校对者ID)
+校对:[wxy](https://github.com/wxy)
本文由 [LCTT](https://github.com/LCTT/TranslateProject) 原创编译,[Linux中国](https://linux.cn/) 荣誉推出
diff --git a/sources/tech/20190415 How To Enable (UP) And Disable (DOWN) A Network Interface Port (NIC) In Linux.md b/published/201905/20190415 How To Enable (UP) And Disable (DOWN) A Network Interface Port (NIC) In Linux.md
similarity index 50%
rename from sources/tech/20190415 How To Enable (UP) And Disable (DOWN) A Network Interface Port (NIC) In Linux.md
rename to published/201905/20190415 How To Enable (UP) And Disable (DOWN) A Network Interface Port (NIC) In Linux.md
index 677fce8e35..46c2ce0052 100644
--- a/sources/tech/20190415 How To Enable (UP) And Disable (DOWN) A Network Interface Port (NIC) In Linux.md
+++ b/published/201905/20190415 How To Enable (UP) And Disable (DOWN) A Network Interface Port (NIC) In Linux.md
@@ -1,38 +1,30 @@
[#]: collector: (lujun9972)
[#]: translator: (bodhix)
-[#]: reviewer: ( )
-[#]: publisher: ( )
-[#]: url: ( )
+[#]: reviewer: (wxy)
+[#]: publisher: (wxy)
+[#]: url: (https://linux.cn/article-10844-1.html)
[#]: subject: (How To Enable (UP) And Disable (DOWN) A Network Interface Port (NIC) In Linux?)
[#]: via: (https://www.2daygeek.com/enable-disable-up-down-nic-network-interface-port-linux-using-ifconfig-ifdown-ifup-ip-nmcli-nmtui/)
[#]: author: (Magesh Maruthamuthu https://www.2daygeek.com/author/magesh/)
-How To Enable (UP) And Disable (DOWN) A Network Interface Port (NIC) In Linux?
+Linux 中如何启用和禁用网卡?
======
-You may need to run these commands based on your requirements.
+你可能会根据你的需要执行以下命令。我会在这里列举一些你会用到这些命令的例子。
-I can tell you few examples, where you would be needed this.
+当你添加一个网卡或者从一个物理网卡创建出一个虚拟网卡的时候,你可能需要使用这些命令将新网卡启用起来。另外,如果你对网卡做了某些修改或者网卡本身没有启用,那么你也需要使用以下的某个命令将网卡启用起来。
-When you add a new network interface or when you create a new virtual network interface from the original physical interface.
+启用、禁用网卡有很多种方法。在这篇文章里,我们会介绍我们使用过的最好的 5 种方法。
-you may need to bounce these commands to bring up the new interface.
+启用禁用网卡可以使用以下 5 个方法来完成:
-Also, if you made any changes or if it’s down then you need to run one of the below commands to bring them up.
+* `ifconfig` 命令:用于配置网卡。它可以提供网卡的很多信息。
+* `ifdown/up` 命令:`ifdown` 命令用于禁用网卡,`ifup` 命令用于启用网卡。
+* `ip` 命令:用于管理网卡,用于替代老旧的、不推荐使用的 `ifconfig` 命令。它和 `ifconfig` 命令很相似,但是提供了很多 `ifconfig` 命令所不具有的强大的特性。
+* `nmcli` 命令:是一个控制 NetworkManager 并报告网络状态的命令行工具。
+* `nmtui` 命令:是一个与 NetworkManager 交互的、基于 curses 图形库的终端 UI 应用。
-It can be done on many ways and we would like to add best five method which we used in the article.
-
-It can be done using the below five methods.
-
- * **`ifconfig Command:`** The ifconfig command is used configure a network interface. It provides so many information about NIC.
- * **`ifdown/up Command:`** The ifdown command take a network interface down and the ifup command bring a network interface up.
- * **`ip Command:`** ip command is used to manage NIC. It’s replacement of old and deprecated ifconfig command. It’s similar to ifconfig command but has many powerful features which isn’t available in ifconfig command.
- * **`nmcli Command:`** nmcli is a command-line tool for controlling NetworkManager and reporting network status.
- * **`nmtui Command:`** nmtui is a curses‐based TUI application for interacting with NetworkManager.
-
-
-
-The below output shows the available network interface card (NIC) information in my Linux system.
+以下显示的是我的 Linux 系统中可用网卡的信息。
```
# ip a
@@ -56,25 +48,25 @@ The below output shows the available network interface card (NIC) information in
valid_lft forever preferred_lft forever
```
-### 1) How To Bring UP And Bring Down A Network Interface In Linux Using ifconfig Command?
+### 1、如何使用 ifconfig 命令启用禁用网卡?
-The ifconfig command is used configure a network interface.
+`ifconfig` 命令用于配置网卡。
-It is used at boot time to set up interfaces as necessary. It provides so many information about NIC. We can use ifconfig command when we need to make any changes on NIC.
+在系统启动过程中如果需要启用网卡,调用的命令就是 `ifconfig`。`ifconfig` 可以提供很多网卡的信息。不管我们想修改网卡的什么配置,都可以使用该命令。
-Common Syntax for ifconfig:
+`ifconfig` 的常用语法:
```
# ifconfig [NIC_NAME] Down/Up
```
-Run the following command to bring down the `enp0s3` interface in Linux. Make a note, you have to input your interface name instead of us.
+执行以下命令禁用 `enp0s3` 网卡。注意,这里你需要输入你自己的网卡名字。
```
# ifconfig enp0s3 down
```
-Yes, the given interface is down now as per the following output.
+从以下输出结果可以看到网卡已经被禁用了。
```
# ip a | grep -A 1 "enp0s3:"
@@ -82,13 +74,13 @@ Yes, the given interface is down now as per the following output.
link/ether 08:00:27:c2:e4:e8 brd ff:ff:ff:ff:ff:ff
```
-Run the following command to bring down the `enp0s3` interface in Linux.
+执行以下命令启用 `enp0s3` 网卡。
```
# ifconfig enp0s3 up
```
-Yes, the given interface is up now as per the following output.
+从以下输出结果可以看到网卡已经启用了。
```
# ip a | grep -A 5 "enp0s3:"
@@ -100,27 +92,26 @@ Yes, the given interface is up now as per the following output.
valid_lft forever preferred_lft forever
```
-### 2) How To Enable And Disable A Network Interface In Linux Using ifdown/up Command?
+### 2、如何使用 ifdown/up 命令启用禁用网卡?
-The ifdown command take a network interface down and the ifup command bring a network interface up.
+`ifdown` 命令用于禁用网卡,`ifup` 命令用于启用网卡。
-**Note:**It doesn’t work on new interface device name like `enpXXX`
+注意:这两个命令不支持以 `enpXXX` 命名的新的网络设备。
-Common Syntax for ifdown/ifup:
+`ifdown`/`ifup` 的常用语法:
```
# ifdown [NIC_NAME]
-
# ifup [NIC_NAME]
```
-Run the following command to bring down the `eth1` interface in Linux.
+执行以下命令禁用 `eth1` 网卡。
```
-# ifdown eth0
+# ifdown eth1
```
-Run the following command to bring down the `eth1` interface in Linux.
+从以下输出结果可以看到网卡已经被禁用了。
```
# ip a | grep -A 3 "eth1:"
@@ -128,13 +119,13 @@ Run the following command to bring down the `eth1` interface in Linux.
link/ether 08:00:27:d5:a0:18 brd ff:ff:ff:ff:ff:ff
```
-Run the following command to bring down the `eth1` interface in Linux.
+执行以下命令启用 `eth1` 网卡。
```
-# ifup eth0
+# ifup eth1
```
-Yes, the given interface is up now as per the following output.
+从以下输出结果可以看到网卡已经启用了。
```
# ip a | grep -A 5 "eth1:"
@@ -145,32 +136,32 @@ Yes, the given interface is up now as per the following output.
valid_lft forever preferred_lft forever
```
-ifup and ifdown doesn’t supporting the latest interface device `enpXXX` names. I got the below message when i ran the command.
+`ifup` 和 `ifdown` 不支持以 `enpXXX` 命名的网卡。当执行该命令时得到的结果如下:
```
# ifdown enp0s8
Unknown interface enp0s8
```
-### 3) How To Bring UP/Bring Down A Network Interface In Linux Using ip Command?
+### 3、如何使用 ip 命令启用禁用网卡?
-ip command is used to manage Network Interface Card (NIC). It’s replacement of old and deprecated ifconfig command on modern Linux systems.
+`ip` 命令用于管理网卡,用于替代老旧的、不推荐使用的 `ifconfig` 命令。
-It’s similar to ifconfig command but has many powerful features which isn’t available in ifconfig command.
+它和 `ifconfig` 命令很相似,但是提供了很多 `ifconfig` 命令不具有的强大的特性。
-Common Syntax for ip:
+`ip` 的常用语法:
```
# ip link set Down/Up
```
-Run the following command to bring down the `enp0s3` interface in Linux.
+执行以下命令禁用 `enp0s3` 网卡。
```
# ip link set enp0s3 down
```
-Yes, the given interface is down now as per the following output.
+从以下输出结果可以看到网卡已经被禁用了。
```
# ip a | grep -A 1 "enp0s3:"
@@ -178,13 +169,13 @@ Yes, the given interface is down now as per the following output.
link/ether 08:00:27:c2:e4:e8 brd ff:ff:ff:ff:ff:ff
```
-Run the following command to bring down the `enp0s3` interface in Linux.
+执行以下命令启用 `enp0s3` 网卡。
```
# ip link set enp0s3 up
```
-Yes, the given interface is up now as per the following output.
+从以下输出结果可以看到网卡已经启用了。
```
# ip a | grep -A 5 "enp0s3:"
@@ -196,15 +187,13 @@ Yes, the given interface is up now as per the following output.
valid_lft forever preferred_lft forever
```
-### 4) How To Enable And Disable A Network Interface In Linux Using nmcli Command?
+### 4、如何使用 nmcli 命令启用禁用网卡?
-nmcli is a command-line tool for controlling NetworkManager and reporting network status.
+`nmcli` 是一个控制 NetworkManager 并报告网络状态的命令行工具。
-It can be utilized as a replacement for nm-applet or other graphical clients. nmcli is used to create, display, edit, delete, activate, and deactivate network
+`nmcli` 可以用做 nm-applet 或者其他图形化客户端的替代品。它可以用于展示、创建、修改、删除、启用和停用网络连接。除此之后,它还可以用来管理和展示网络设备状态。
-connections, as well as control and display network device status.
-
-Run the following command to identify the interface name because nmcli command is perform most of the task using `profile name` instead of `device name`.
+`nmcli` 命令大部分情况下都是使用“配置名称”工作而不是“设备名称”。所以,执行以下命令,获取网卡对应的配置名称。(LCTT 译注:在使用 `nmtui` 或者 `nmcli` 管理网络连接的时候,可以为网络连接配置一个名称,就是这里提到的配置名称`)
```
# nmcli con show
@@ -213,20 +202,20 @@ Wired connection 1 3d5afa0a-419a-3d1a-93e6-889ce9c6a18c ethernet enp0s3
Wired connection 2 a22154b7-4cc4-3756-9d8d-da5a4318e146 ethernet enp0s8
```
-Common Syntax for ip:
+`nmcli` 的常用语法:
```
# nmcli con Down/Up
```
-Run the following command to bring down the `enp0s3` interface in Linux. You have to give `profile name` instead of `device name` to bring down it.
+执行以下命令禁用 `enp0s3` 网卡。在禁用网卡的时候,你需要使用配置名称而不是设备名称。
```
# nmcli con down 'Wired connection 1'
Connection 'Wired connection 1' successfully deactivated (D-Bus active path: /org/freedesktop/NetworkManager/ActiveConnection/6)
```
-Yes, the given interface is down now as per the following output.
+从以下输出结果可以看到网卡已经禁用了。
```
# nmcli dev status
@@ -236,14 +225,14 @@ enp0s3 ethernet disconnected --
lo loopback unmanaged --
```
-Run the following command to bring down the `enp0s3` interface in Linux. You have to give `profile name` instead of `device name` to bring down it.
+执行以下命令启用 `enp0s3` 网卡。同样的,这里你需要使用配置名称而不是设备名称。
```
# nmcli con up 'Wired connection 1'
Connection successfully activated (D-Bus active path: /org/freedesktop/NetworkManager/ActiveConnection/7)
```
-Yes, the given interface is up now as per the following output.
+从以下输出结果可以看到网卡已经启用了。
```
# nmcli dev status
@@ -253,25 +242,27 @@ enp0s3 ethernet connected Wired connection 1
lo loopback unmanaged --
```
-### 5) How To Bring UP/Bring Down A Network Interface In Linux Using nmtui Command?
+### 5、如何使用 nmtui 命令启用禁用网卡?
-nmtui is a curses based TUI application for interacting with NetworkManager.
+`nmtui` 是一个与 NetworkManager 交互的、基于 curses 图形库的终端 UI 应用。
-When starting nmtui, the user is prompted to choose the activity to perform unless it was specified as the first argument.
+在启用 `nmtui` 的时候,如果第一个参数没有特别指定,它会引导用户选择对应的操作去执行。
-Run the following command launch the nmtui interface. Select “Active a connection” and hit “OK”
+执行以下命令打开 `mntui` 界面。选择 “Active a connection” 然后点击 “OK”。
```
# nmtui
```
-[![][1]![][1]][2]
+![][2]
-Select the interface which you want to bring down then hit “Deactivate” button.
-[![][1]![][1]][3]
+选择你要禁用的网卡,然后点击 “Deactivate” 按钮,就可以将网卡禁用。
-For activation do the same above procedure.
-[![][1]![][1]][4]
+![][3]
+
+如果要启用网卡,使用上述同样的步骤即可。
+
+![][4]
--------------------------------------------------------------------------------
@@ -279,8 +270,8 @@ via: https://www.2daygeek.com/enable-disable-up-down-nic-network-interface-port-
作者:[Magesh Maruthamuthu][a]
选题:[lujun9972][b]
-译者:[译者ID](https://github.com/译者ID)
-校对:[校对者ID](https://github.com/校对者ID)
+译者:[bodhix](https://github.com/bodhix)
+校对:[wxy](https://github.com/wxy)
本文由 [LCTT](https://github.com/LCTT/TranslateProject) 原创编译,[Linux中国](https://linux.cn/) 荣誉推出
diff --git a/published/201905/20190415 Inter-process communication in Linux- Shared storage.md b/published/201905/20190415 Inter-process communication in Linux- Shared storage.md
new file mode 100644
index 0000000000..de56a36982
--- /dev/null
+++ b/published/201905/20190415 Inter-process communication in Linux- Shared storage.md
@@ -0,0 +1,439 @@
+[#]: collector: (lujun9972)
+[#]: translator: (FSSlc)
+[#]: reviewer: (wxy)
+[#]: publisher: (wxy)
+[#]: url: (https://linux.cn/article-10826-1.html)
+[#]: subject: (Inter-process communication in Linux: Shared storage)
+[#]: via: (https://opensource.com/article/19/4/interprocess-communication-linux-storage)
+[#]: author: (Marty Kalin https://opensource.com/users/mkalindepauledu)
+
+Linux 下的进程间通信:共享存储
+======
+
+> 学习在 Linux 中进程是如何与其他进程进行同步的。
+
+![Filing papers and documents][1]
+
+本篇是 Linux 下[进程间通信][2](IPC)系列的第一篇文章。这个系列将使用 C 语言代码示例来阐明以下 IPC 机制:
+
+ * 共享文件
+ * 共享内存(使用信号量)
+ * 管道(命名的或非命名的管道)
+ * 消息队列
+ * 套接字
+ * 信号
+
+在聚焦上面提到的共享文件和共享内存这两个机制之前,这篇文章将带你回顾一些核心的概念。
+
+### 核心概念
+
+*进程*是运行着的程序,每个进程都有着它自己的地址空间,这些空间由进程被允许访问的内存地址组成。进程有一个或多个执行*线程*,而线程是一系列执行指令的集合:*单线程*进程就只有一个线程,而*多线程*的进程则有多个线程。一个进程中的线程共享各种资源,特别是地址空间。另外,一个进程中的线程可以直接通过共享内存来进行通信,尽管某些现代语言(例如 Go)鼓励一种更有序的方式,例如使用线程安全的通道。当然对于不同的进程,默认情况下,它们**不**能共享内存。
+
+有多种方法启动之后要进行通信的进程,下面所举的例子中主要使用了下面的两种方法:
+
+ * 一个终端被用来启动一个进程,另外一个不同的终端被用来启动另一个。
+ * 在一个进程(父进程)中调用系统函数 `fork`,以此生发另一个进程(子进程)。
+
+第一个例子采用了上面使用终端的方法。这些[代码示例][3]的 ZIP 压缩包可以从我的网站下载到。
+
+### 共享文件
+
+程序员对文件访问应该都已经很熟识了,包括许多坑(不存在的文件、文件权限损坏等等),这些问题困扰着程序对文件的使用。尽管如此,共享文件可能是最为基础的 IPC 机制了。考虑一下下面这样一个相对简单的例子,其中一个进程(生产者 `producer`)创建和写入一个文件,然后另一个进程(消费者 `consumer `)从这个相同的文件中进行读取:
+
+```
+ writes +-----------+ reads
+producer-------->| disk file |<-------consumer
+ +-----------+
+```
+
+在使用这个 IPC 机制时最明显的挑战是*竞争条件*可能会发生:生产者和消费者可能恰好在同一时间访问该文件,从而使得输出结果不确定。为了避免竞争条件的发生,该文件在处于*读*或*写*状态时必须以某种方式处于被锁状态,从而阻止在*写*操作执行时和其他操作的冲突。在标准系统库中与锁相关的 API 可以被总结如下:
+
+ * 生产者应该在写入文件时获得一个文件的排斥锁。一个*排斥*锁最多被一个进程所拥有。这样就可以排除掉竞争条件的发生,因为在锁被释放之前没有其他的进程可以访问这个文件。
+ * 消费者应该在从文件中读取内容时得到至少一个共享锁。多个*读取者*可以同时保有一个*共享*锁,但是没有*写入者*可以获取到文件内容,甚至在当只有一个*读取者*保有一个共享锁时。
+
+共享锁可以提升效率。假如一个进程只是读入一个文件的内容,而不去改变它的内容,就没有什么原因阻止其他进程来做同样的事。但如果需要写入内容,则很显然需要文件有排斥锁。
+
+标准的 I/O 库中包含一个名为 `fcntl` 的实用函数,它可以被用来检查或者操作一个文件上的排斥锁和共享锁。该函数通过一个*文件描述符*(一个在进程中的非负整数值)来标记一个文件(在不同的进程中不同的文件描述符可能标记同一个物理文件)。对于文件的锁定, Linux 提供了名为 `flock` 的库函数,它是 `fcntl` 的一个精简包装。第一个例子中使用 `fcntl` 函数来暴露这些 API 细节。
+
+#### 示例 1. 生产者程序
+
+```c
+#include
+#include
+#include
+#include
+#include
+
+#define FileName "data.dat"
+#define DataString "Now is the winter of our discontent\nMade glorious summer by this sun of York\n"
+
+void report_and_exit(const char* msg) {
+ perror(msg);
+ exit(-1); /* EXIT_FAILURE */
+}
+
+int main() {
+ struct flock lock;
+ lock.l_type = F_WRLCK; /* read/write (exclusive versus shared) lock */
+ lock.l_whence = SEEK_SET; /* base for seek offsets */
+ lock.l_start = 0; /* 1st byte in file */
+ lock.l_len = 0; /* 0 here means 'until EOF' */
+ lock.l_pid = getpid(); /* process id */
+
+ int fd; /* file descriptor to identify a file within a process */
+ if ((fd = open(FileName, O_RDWR | O_CREAT, 0666)) < 0) /* -1 signals an error */
+ report_and_exit("open failed...");
+
+ if (fcntl(fd, F_SETLK, &lock) < 0) /** F_SETLK doesn't block, F_SETLKW does **/
+ report_and_exit("fcntl failed to get lock...");
+ else {
+ write(fd, DataString, strlen(DataString)); /* populate data file */
+ fprintf(stderr, "Process %d has written to data file...\n", lock.l_pid);
+ }
+
+ /* Now release the lock explicitly. */
+ lock.l_type = F_UNLCK;
+ if (fcntl(fd, F_SETLK, &lock) < 0)
+ report_and_exit("explicit unlocking failed...");
+
+ close(fd); /* close the file: would unlock if needed */
+ return 0; /* terminating the process would unlock as well */
+}
+```
+
+上面生产者程序的主要步骤可以总结如下:
+
+ * 这个程序首先声明了一个类型为 `struct flock` 的变量,它代表一个锁,并对它的 5 个域做了初始化。第一个初始化
+
+ ```c
+lock.l_type = F_WRLCK; /* exclusive lock */
+```
+ 使得这个锁为排斥锁(read-write)而不是一个共享锁(read-only)。假如生产者获得了这个锁,则其他的进程将不能够对文件做读或者写操作,直到生产者释放了这个锁,或者显式地调用 `fcntl`,又或者隐式地关闭这个文件。(当进程终止时,所有被它打开的文件都会被自动关闭,从而释放了锁)
+ * 上面的程序接着初始化其他的域。主要的效果是*整个*文件都将被锁上。但是,有关锁的 API 允许特别指定的字节被上锁。例如,假如文件包含多个文本记录,则单个记录(或者甚至一个记录的一部分)可以被锁,而其余部分不被锁。
+ * 第一次调用 `fcntl`
+
+ ```c
+if (fcntl(fd, F_SETLK, &lock) < 0)
+```
+ 尝试排斥性地将文件锁住,并检查调用是否成功。一般来说, `fcntl` 函数返回 `-1` (因此小于 0)意味着失败。第二个参数 `F_SETLK` 意味着 `fcntl` 的调用*不是*堵塞的;函数立即做返回,要么获得锁,要么显示失败了。假如替换地使用 `F_SETLKW`(末尾的 `W` 代指*等待*),那么对 `fcntl` 的调用将是阻塞的,直到有可能获得锁的时候。在调用 `fcntl` 函数时,它的第一个参数 `fd` 指的是文件描述符,第二个参数指定了将要采取的动作(在这个例子中,`F_SETLK` 指代设置锁),第三个参数为锁结构的地址(在本例中,指的是 `&lock`)。
+ * 假如生产者获得了锁,这个程序将向文件写入两个文本记录。
+ * 在向文件写入内容后,生产者改变锁结构中的 `l_type` 域为 `unlock` 值:
+
+ ```c
+lock.l_type = F_UNLCK;
+```
+ 并调用 `fcntl` 来执行解锁操作。最后程序关闭了文件并退出。
+
+#### 示例 2. 消费者程序
+
+```c
+#include
+#include
+#include
+#include
+
+#define FileName "data.dat"
+
+void report_and_exit(const char* msg) {
+ perror(msg);
+ exit(-1); /* EXIT_FAILURE */
+}
+
+int main() {
+ struct flock lock;
+ lock.l_type = F_WRLCK; /* read/write (exclusive) lock */
+ lock.l_whence = SEEK_SET; /* base for seek offsets */
+ lock.l_start = 0; /* 1st byte in file */
+ lock.l_len = 0; /* 0 here means 'until EOF' */
+ lock.l_pid = getpid(); /* process id */
+
+ int fd; /* file descriptor to identify a file within a process */
+ if ((fd = open(FileName, O_RDONLY)) < 0) /* -1 signals an error */
+ report_and_exit("open to read failed...");
+
+ /* If the file is write-locked, we can't continue. */
+ fcntl(fd, F_GETLK, &lock); /* sets lock.l_type to F_UNLCK if no write lock */
+ if (lock.l_type != F_UNLCK)
+ report_and_exit("file is still write locked...");
+
+ lock.l_type = F_RDLCK; /* prevents any writing during the reading */
+ if (fcntl(fd, F_SETLK, &lock) < 0)
+ report_and_exit("can't get a read-only lock...");
+
+ /* Read the bytes (they happen to be ASCII codes) one at a time. */
+ int c; /* buffer for read bytes */
+ while (read(fd, &c, 1) > 0) /* 0 signals EOF */
+ write(STDOUT_FILENO, &c, 1); /* write one byte to the standard output */
+
+ /* Release the lock explicitly. */
+ lock.l_type = F_UNLCK;
+ if (fcntl(fd, F_SETLK, &lock) < 0)
+ report_and_exit("explicit unlocking failed...");
+
+ close(fd);
+ return 0;
+}
+```
+
+相比于锁的 API,消费者程序会相对复杂一点儿。特别的,消费者程序首先检查文件是否被排斥性的被锁,然后才尝试去获得一个共享锁。相关的代码为:
+
+```
+lock.l_type = F_WRLCK;
+...
+fcntl(fd, F_GETLK, &lock); /* sets lock.l_type to F_UNLCK if no write lock */
+if (lock.l_type != F_UNLCK)
+ report_and_exit("file is still write locked...");
+```
+
+在 `fcntl` 调用中的 `F_GETLK` 操作指定检查一个锁,在本例中,上面代码的声明中给了一个 `F_WRLCK` 的排斥锁。假如特指的锁不存在,那么 `fcntl` 调用将会自动地改变锁类型域为 `F_UNLCK` 以此来显示当前的状态。假如文件是排斥性地被锁,那么消费者将会终止。(一个更健壮的程序版本或许应该让消费者*睡*会儿,然后再尝试几次。)
+
+假如当前文件没有被锁,那么消费者将尝试获取一个共享(read-only)锁(`F_RDLCK`)。为了缩短程序,`fcntl` 中的 `F_GETLK` 调用可以丢弃,因为假如其他进程已经保有一个读写锁,`F_RDLCK` 的调用就可能会失败。重新调用一个只读锁能够阻止其他进程向文件进行写的操作,但可以允许其他进程对文件进行读取。简而言之,共享锁可以被多个进程所保有。在获取了一个共享锁后,消费者程序将立即从文件中读取字节数据,然后在标准输出中打印这些字节的内容,接着释放锁,关闭文件并终止。
+
+下面的 `%` 为命令行提示符,下面展示的是从相同终端开启这两个程序的输出:
+
+```
+% ./producer
+Process 29255 has written to data file...
+
+% ./consumer
+Now is the winter of our discontent
+Made glorious summer by this sun of York
+```
+
+在本次的代码示例中,通过 IPC 传输的数据是文本:它们来自莎士比亚的戏剧《理查三世》中的两行台词。然而,共享文件的内容还可以是纷繁复杂的,任意的字节数据(例如一个电影)都可以,这使得文件共享变成了一个非常灵活的 IPC 机制。但它的缺点是文件获取速度较慢,因为文件的获取涉及到读或者写。同往常一样,编程总是伴随着折中。下面的例子将通过共享内存来做 IPC,而不是通过共享文件,在性能上相应的有极大的提升。
+
+### 共享内存
+
+对于共享内存,Linux 系统提供了两类不同的 API:传统的 System V API 和更新一点的 POSIX API。在单个应用中,这些 API 不能混用。但是,POSIX 方式的一个坏处是它的特性仍在发展中,并且依赖于安装的内核版本,这非常影响代码的可移植性。例如,默认情况下,POSIX API 用*内存映射文件*来实现共享内存:对于一个共享的内存段,系统为相应的内容维护一个*备份文件*。在 POSIX 规范下共享内存可以被配置为不需要备份文件,但这可能会影响可移植性。我的例子中使用的是带有备份文件的 POSIX API,这既结合了内存获取的速度优势,又获得了文件存储的持久性。
+
+下面的共享内存例子中包含两个程序,分别名为 `memwriter` 和 `memreader`,并使用*信号量*来调整它们对共享内存的获取。在任何时候当共享内存进入一个*写入者*场景时,无论是多进程还是多线程,都有遇到基于内存的竞争条件的风险,所以,需要引入信号量来协调(同步)对共享内存的获取。
+
+`memwriter` 程序应当在它自己所处的终端首先启动,然后 `memreader` 程序才可以在它自己所处的终端启动(在接着的十几秒内)。`memreader` 的输出如下:
+
+```
+This is the way the world ends...
+```
+
+在每个源程序的最上方注释部分都解释了在编译它们时需要添加的链接参数。
+
+首先让我们复习一下信号量是如何作为一个同步机制工作的。一般的信号量也被叫做一个*计数信号量*,因为带有一个可以增加的值(通常初始化为 0)。考虑一家租用自行车的商店,在它的库存中有 100 辆自行车,还有一个供职员用于租赁的程序。每当一辆自行车被租出去,信号量就增加 1;当一辆自行车被还回来,信号量就减 1。在信号量的值为 100 之前都还可以进行租赁业务,但如果等于 100 时,就必须停止业务,直到至少有一辆自行车被还回来,从而信号量减为 99。
+
+*二元信号量*是一个特例,它只有两个值:0 和 1。在这种情况下,信号量的表现为*互斥量*(一个互斥的构造)。下面的共享内存示例将把信号量用作互斥量。当信号量的值为 0 时,只有 `memwriter` 可以获取共享内存,在写操作完成后,这个进程将增加信号量的值,从而允许 `memreader` 来读取共享内存。
+
+#### 示例 3. memwriter 进程的源程序
+
+```c
+/** Compilation: gcc -o memwriter memwriter.c -lrt -lpthread **/
+#include
+#include
+#include
+#include
+#include
+#include
+#include
+#include
+#include "shmem.h"
+
+void report_and_exit(const char* msg) {
+ perror(msg);
+ exit(-1);
+}
+
+int main() {
+ int fd = shm_open(BackingFile, /* name from smem.h */
+ O_RDWR | O_CREAT, /* read/write, create if needed */
+ AccessPerms); /* access permissions (0644) */
+ if (fd < 0) report_and_exit("Can't open shared mem segment...");
+
+ ftruncate(fd, ByteSize); /* get the bytes */
+
+ caddr_t memptr = mmap(NULL, /* let system pick where to put segment */
+ ByteSize, /* how many bytes */
+ PROT_READ | PROT_WRITE, /* access protections */
+ MAP_SHARED, /* mapping visible to other processes */
+ fd, /* file descriptor */
+ 0); /* offset: start at 1st byte */
+ if ((caddr_t) -1 == memptr) report_and_exit("Can't get segment...");
+
+ fprintf(stderr, "shared mem address: %p [0..%d]\n", memptr, ByteSize - 1);
+ fprintf(stderr, "backing file: /dev/shm%s\n", BackingFile );
+
+ /* semaphore code to lock the shared mem */
+ sem_t* semptr = sem_open(SemaphoreName, /* name */
+ O_CREAT, /* create the semaphore */
+ AccessPerms, /* protection perms */
+ 0); /* initial value */
+ if (semptr == (void*) -1) report_and_exit("sem_open");
+
+ strcpy(memptr, MemContents); /* copy some ASCII bytes to the segment */
+
+ /* increment the semaphore so that memreader can read */
+ if (sem_post(semptr) < 0) report_and_exit("sem_post");
+
+ sleep(12); /* give reader a chance */
+
+ /* clean up */
+ munmap(memptr, ByteSize); /* unmap the storage */
+ close(fd);
+ sem_close(semptr);
+ shm_unlink(BackingFile); /* unlink from the backing file */
+ return 0;
+}
+```
+
+下面是 `memwriter` 和 `memreader` 程序如何通过共享内存来通信的一个总结:
+
+ * 上面展示的 `memwriter` 程序调用 `shm_open` 函数来得到作为系统协调共享内存的备份文件的文件描述符。此时,并没有内存被分配。接下来调用的是令人误解的名为 `ftruncate` 的函数
+
+ ```c
+ftruncate(fd, ByteSize); /* get the bytes */
+```
+ 它将分配 `ByteSize` 字节的内存,在该情况下,一般为大小适中的 512 字节。`memwriter` 和 `memreader` 程序都只从共享内存中获取数据,而不是从备份文件。系统将负责共享内存和备份文件之间数据的同步。
+ * 接着 `memwriter` 调用 `mmap` 函数:
+
+ ```c
+caddr_t memptr = mmap(NULL, /* let system pick where to put segment */
+ ByteSize, /* how many bytes */
+ PROT_READ | PROT_WRITE, /* access protections */
+ MAP_SHARED, /* mapping visible to other processes */
+ fd, /* file descriptor */
+ 0); /* offset: start at 1st byte */
+```
+ 来获得共享内存的指针。(`memreader` 也做一次类似的调用。) 指针类型 `caddr_t` 以 `c` 开头,它代表 `calloc`,而这是动态初始化分配的内存为 0 的一个系统函数。`memwriter` 通过库函数 `strcpy`(字符串复制)来获取后续*写*操作的 `memptr`。
+ * 到现在为止,`memwriter` 已经准备好进行写操作了,但首先它要创建一个信号量来确保共享内存的排斥性。假如 `memwriter` 正在执行写操作而同时 `memreader` 在执行读操作,则有可能出现竞争条件。假如调用 `sem_open` 成功了:
+
+ ```c
+sem_t* semptr = sem_open(SemaphoreName, /* name */
+ O_CREAT, /* create the semaphore */
+ AccessPerms, /* protection perms */
+ 0); /* initial value */
+```
+ 那么,接着写操作便可以执行。上面的 `SemaphoreName`(任意一个唯一的非空名称)用来在 `memwriter` 和 `memreader` 识别信号量。初始值 0 将会传递给信号量的创建者,在这个例子中指的是 `memwriter` 赋予它执行*写*操作的权利。
+ * 在写操作完成后,`memwriter* 通过调用 `sem_post` 函数将信号量的值增加到 1:
+
+ ```c
+if (sem_post(semptr) < 0) ..
+```
+ 增加信号了将释放互斥锁,使得 `memreader` 可以执行它的*读*操作。为了更好地测量,`memwriter` 也将从它自己的地址空间中取消映射,
+
+ ```c
+munmap(memptr, ByteSize); /* unmap the storage *
+```
+ 这将使得 `memwriter` 不能进一步地访问共享内存。
+
+#### 示例 4. memreader 进程的源代码
+
+```c
+/** Compilation: gcc -o memreader memreader.c -lrt -lpthread **/
+#include
+#include
+#include
+#include
+#include
+#include
+#include
+#include
+#include "shmem.h"
+
+void report_and_exit(const char* msg) {
+ perror(msg);
+ exit(-1);
+}
+
+int main() {
+ int fd = shm_open(BackingFile, O_RDWR, AccessPerms); /* empty to begin */
+ if (fd < 0) report_and_exit("Can't get file descriptor...");
+
+ /* get a pointer to memory */
+ caddr_t memptr = mmap(NULL, /* let system pick where to put segment */
+ ByteSize, /* how many bytes */
+ PROT_READ | PROT_WRITE, /* access protections */
+ MAP_SHARED, /* mapping visible to other processes */
+ fd, /* file descriptor */
+ 0); /* offset: start at 1st byte */
+ if ((caddr_t) -1 == memptr) report_and_exit("Can't access segment...");
+
+ /* create a semaphore for mutual exclusion */
+ sem_t* semptr = sem_open(SemaphoreName, /* name */
+ O_CREAT, /* create the semaphore */
+ AccessPerms, /* protection perms */
+ 0); /* initial value */
+ if (semptr == (void*) -1) report_and_exit("sem_open");
+
+ /* use semaphore as a mutex (lock) by waiting for writer to increment it */
+ if (!sem_wait(semptr)) { /* wait until semaphore != 0 */
+ int i;
+ for (i = 0; i < strlen(MemContents); i++)
+ write(STDOUT_FILENO, memptr + i, 1); /* one byte at a time */
+ sem_post(semptr);
+ }
+
+ /* cleanup */
+ munmap(memptr, ByteSize);
+ close(fd);
+ sem_close(semptr);
+ unlink(BackingFile);
+ return 0;
+}
+```
+
+`memwriter` 和 `memreader` 程序中,共享内存的主要着重点都在 `shm_open` 和 `mmap` 函数上:在成功时,第一个调用返回一个备份文件的文件描述符,而第二个调用则使用这个文件描述符从共享内存段中获取一个指针。它们对 `shm_open` 的调用都很相似,除了 `memwriter` 程序创建共享内存,而 `memreader 只获取这个已经创建的内存:
+
+```c
+int fd = shm_open(BackingFile, O_RDWR | O_CREAT, AccessPerms); /* memwriter */
+int fd = shm_open(BackingFile, O_RDWR, AccessPerms); /* memreader */
+```
+
+有了文件描述符,接着对 `mmap` 的调用就是类似的了:
+
+```c
+caddr_t memptr = mmap(NULL, size, PROT_READ | PROT_WRITE, MAP_SHARED, fd, 0);
+```
+
+`mmap` 的第一个参数为 `NULL`,这意味着让系统自己决定在虚拟内存地址的哪个地方分配内存,当然也可以指定一个地址(但很有技巧性)。`MAP_SHARED` 标志着被分配的内存在进程中是共享的,最后一个参数(在这个例子中为 0 ) 意味着共享内存的偏移量应该为第一个字节。`size` 参数特别指定了将要分配的字节数目(在这个例子中是 512);另外的保护参数(`AccessPerms`)暗示着共享内存是可读可写的。
+
+当 `memwriter` 程序执行成功后,系统将创建并维护备份文件,在我的系统中,该文件为 `/dev/shm/shMemEx`,其中的 `shMemEx` 是我为共享存储命名的(在头文件 `shmem.h` 中给定)。在当前版本的 `memwriter` 和 `memreader` 程序中,下面的语句
+
+```c
+shm_unlink(BackingFile); /* removes backing file */
+```
+
+将会移除备份文件。假如没有 `unlink` 这个语句,则备份文件在程序终止后仍然持久地保存着。
+
+`memreader` 和 `memwriter` 一样,在调用 `sem_open` 函数时,通过信号量的名字来获取信号量。但 `memreader` 随后将进入等待状态,直到 `memwriter` 将初始值为 0 的信号量的值增加。
+
+```c
+if (!sem_wait(semptr)) { /* wait until semaphore != 0 */
+```
+
+一旦等待结束,`memreader` 将从共享内存中读取 ASCII 数据,然后做些清理工作并终止。
+
+共享内存 API 包括显式地同步共享内存段和备份文件。在这次的示例中,这些操作都被省略了,以免文章显得杂乱,好让我们专注于内存共享和信号量的代码。
+
+即便在信号量代码被移除的情况下,`memwriter` 和 `memreader` 程序很大几率也能够正常执行而不会引入竞争条件:`memwriter` 创建了共享内存段,然后立即向它写入;`memreader` 不能访问共享内存,直到共享内存段被创建好。然而,当一个*写操作*处于混合状态时,最佳实践需要共享内存被同步。信号量 API 足够重要,值得在代码示例中着重强调。
+
+### 总结
+
+上面共享文件和共享内存的例子展示了进程是怎样通过*共享存储*来进行通信的,前者通过文件而后者通过内存块。这两种方法的 API 相对来说都很直接。这两种方法有什么共同的缺点吗?现代的应用经常需要处理流数据,而且是非常大规模的数据流。共享文件或者共享内存的方法都不能很好地处理大规模的流数据。按照类型使用管道会更加合适一些。所以这个系列的第二部分将会介绍管道和消息队列,同样的,我们将使用 C 语言写的代码示例来辅助讲解。
+
+--------------------------------------------------------------------------------
+
+via: https://opensource.com/article/19/4/interprocess-communication-linux-storage
+
+作者:[Marty Kalin][a]
+选题:[lujun9972][b]
+译者:[FSSlc](https://github.com/FSSlc)
+校对:[wxy](https://github.com/wxy)
+
+本文由 [LCTT](https://github.com/LCTT/TranslateProject) 原创编译,[Linux中国](https://linux.cn/) 荣誉推出
+
+[a]: https://opensource.com/users/mkalindepauledu
+[b]: https://github.com/lujun9972
+[1]: https://opensource.com/sites/default/files/styles/image-full-size/public/lead-images/documents_papers_file_storage_work.png?itok=YlXpAqAJ (Filing papers and documents)
+[2]: https://en.wikipedia.org/wiki/Inter-process_communication
+[3]: http://condor.depaul.edu/mkalin
+[4]: http://www.opengroup.org/onlinepubs/009695399/functions/perror.html
+[5]: http://www.opengroup.org/onlinepubs/009695399/functions/exit.html
+[6]: http://www.opengroup.org/onlinepubs/009695399/functions/strlen.html
+[7]: http://www.opengroup.org/onlinepubs/009695399/functions/fprintf.html
+[8]: http://www.opengroup.org/onlinepubs/009695399/functions/strcpy.html
diff --git a/published/201905/20190415 Kubernetes on Fedora IoT with k3s.md b/published/201905/20190415 Kubernetes on Fedora IoT with k3s.md
new file mode 100644
index 0000000000..a8293d4d3b
--- /dev/null
+++ b/published/201905/20190415 Kubernetes on Fedora IoT with k3s.md
@@ -0,0 +1,209 @@
+[#]: collector: (lujun9972)
+[#]: translator: (StdioA)
+[#]: reviewer: (wxy)
+[#]: publisher: (wxy)
+[#]: url: (https://linux.cn/article-10908-1.html)
+[#]: subject: (Kubernetes on Fedora IoT with k3s)
+[#]: via: (https://fedoramagazine.org/kubernetes-on-fedora-iot-with-k3s/)
+[#]: author: (Lennart Jern https://fedoramagazine.org/author/lennartj/)
+
+使用 k3s 在 Fedora IoT 上运行 K8S
+======
+
+
+
+Fedora IoT 是一个即将发布的、面向物联网的 Fedora 版本。去年 Fedora Magazine 的《[如何使用 Fedora IoT 点亮 LED 灯][2]》一文第一次介绍了它。从那以后,它与 Fedora Silverblue 一起不断改进,以提供针对面向容器的工作流的不可变基础操作系统。
+
+Kubernetes 是一个颇受欢迎的容器编排系统。它可能最常用在那些能够处理巨大负载的强劲硬件上。不过,它也能在像树莓派 3 这样轻量级的设备上运行。让我们继续阅读,来了解如何运行它。
+
+### 为什么用 Kubernetes?
+
+虽然 Kubernetes 在云计算领域风靡一时,但让它在小型单板机上运行可能并不是常见的。不过,我们有非常明确的理由来做这件事。首先,这是一个不需要昂贵硬件就可以学习并熟悉 Kubernetes 的好方法;其次,由于它的流行性,市面上有[大量应用][3]进行了预先打包,以用于在 Kubernetes 集群中运行。更不用说,当你遇到问题时,会有大规模的社区用户为你提供帮助。
+
+最后但同样重要的是,即使是在家庭实验室这样的小规模环境中,容器编排也确实能够使事情变得更加简单。虽然在学习曲线方面,这一点并不明显,但这些技能在你将来与任何集群打交道的时候都会有帮助。不管你面对的是一个单节点树莓派集群,还是一个大规模的机器学习场,它们的操作方式都是类似的。
+
+#### K3s - 轻量级的 Kubernetes
+
+一个“正常”安装的 Kubernetes(如果有这么一说的话)对于物联网来说有点沉重。K8s 的推荐内存配置,是每台机器 2GB!不过,我们也有一些替代品,其中一个新人是 [k3s][4] —— 一个轻量级的 Kubernetes 发行版。
+
+K3s 非常特殊,因为它将 etcd 替换成了 SQLite 以满足键值存储需求。还有一点,在于整个 k3s 将使用一个二进制文件分发,而不是每个组件一个。这减少了内存占用并简化了安装过程。基于上述原因,我们只需要 512MB 内存即可运行 k3s,极度适合小型单板电脑!
+
+### 你需要的东西
+
+1. Fedora IoT 运行在虚拟机或实体设备中运行的。在[这里][5]可以看到优秀的入门指南。一台机器就足够了,不过两台可以用来测试向集群添加更多节点。
+2. [配置防火墙][6],允许 6443 和 8372 端口的通信。或者,你也可以简单地运行 `systemctl stop firewalld` 来为这次实验关闭防火墙。
+
+### 安装 k3s
+
+安装 k3s 非常简单。直接运行安装脚本:
+
+```
+curl -sfL https://get.k3s.io | sh -
+```
+
+它会下载、安装并启动 k3s。安装完成后,运行以下命令来从服务器获取节点列表:
+
+```
+kubectl get nodes
+```
+
+需要注意的是,有几个选项可以通过环境变量传递给安装脚本。这些选项可以在[文档][7]中找到。当然,你也完全可以直接下载二进制文件来手动安装 k3s。
+
+对于实验和学习来说,这样已经很棒了,不过单节点的集群也不能算一个集群。幸运的是,添加另一个节点并不比设置第一个节点要难。只需要向安装脚本传递两个环境变量,它就可以找到第一个节点,而不用运行 k3s 的服务器部分。
+
+```
+curl -sfL https://get.k3s.io | K3S_URL=https://example-url:6443 \
+ K3S_TOKEN=XXX sh -
+```
+
+上面的 `example-url` 应被替换为第一个节点的 IP 地址,或一个完全限定域名。在该节点中,(用 XXX 表示的)令牌可以在 `/var/lib/rancher/k3s/server/node-token` 文件中找到。
+
+### 部署一些容器
+
+现在我们有了一个 Kubernetes 集群,我们可以真正做些什么呢?让我们从部署一个简单的 Web 服务器开始吧。
+
+```
+kubectl create deployment my-server --image nginx
+```
+
+这会从名为 `nginx` 的容器镜像中创建出一个名叫 `my-server` 的 [部署][8](默认使用 docker hub 注册中心,以及 `latest` 标签)。
+
+```
+kubectl get pods
+```
+
+为了访问到 pod 中运行的 nginx 服务器,首先通过一个 [服务][9] 来暴露该部署。以下命令将创建一个与该部署同名的服务。
+
+```
+kubectl expose deployment my-server --port 80
+```
+
+服务将作为一种负载均衡器和 Pod 的 DNS 记录来工作。比如,当运行第二个 Pod 时,我们只需指定 `my-server`(服务名称)就可以通过 `curl` 访问 nginx 服务器。有关如何操作,可以看下面的实例。
+
+```
+# 启动一个 pod,在里面以交互方式运行 bash
+kubectl run debug --generator=run-pod/v1 --image=fedora -it -- bash
+# 等待 bash 提示符出现
+curl my-server
+# 你可以看到“Welcome to nginx!”的输出页面
+```
+
+### Ingress 控制器及外部 IP
+
+默认状态下,一个服务只能获得一个 ClusterIP(只能从集群内部访问),但你也可以通过把它的类型设置为 [LoadBalancer][10] 为该服务申请一个外部 IP。不过,并非所有应用都需要自己的 IP 地址。相反,通常可以通过基于 Host 请求头部或请求路径进行路由,从而使多个服务共享一个 IP 地址。你可以在 Kubernetes 使用 [Ingress][11] 完成此操作,而这也是我们要做的。Ingress 也提供了额外的功能,比如无需配置应用即可对流量进行 TLS 加密。
+
+Kubernetes 需要 Ingress 控制器来使 Ingress 资源工作,k3s 包含 [Traefik][12] 正是出于此目的。它还包含了一个简单的服务负载均衡器,可以为集群中的服务提供外部 IP。这篇[文档][13]描述了这种服务:
+
+> k3s 包含一个使用可用主机端口的基础服务负载均衡器。比如,如果你尝试创建一个监听 80 端口的负载均衡器,它会尝试在集群中寻找一个 80 端口空闲的节点。如果没有可用端口,那么负载均衡器将保持在 Pending 状态。
+>
+> k3s README
+
+Ingress 控制器已经通过这个负载均衡器暴露在外。你可以使用以下命令找到它正在使用的 IP 地址。
+
+```
+$ kubectl get svc --all-namespaces
+NAMESPACE NAME TYPE CLUSTER-IP EXTERNAL-IP PORT(S) AGE
+ default kubernetes ClusterIP 10.43.0.1 443/TCP 33d
+ default my-server ClusterIP 10.43.174.38 80/TCP 30m
+ kube-system kube-dns ClusterIP 10.43.0.10 53/UDP,53/TCP,9153/TCP 33d
+ kube-system traefik LoadBalancer 10.43.145.104 10.0.0.8 80:31596/TCP,443:31539/TCP 33d
+```
+
+找到名为 `traefik` 的服务。在上面的例子中,我们感兴趣的 IP 是 10.0.0.8。
+
+### 路由传入的请求
+
+让我们创建一个 Ingress,使它通过基于 Host 头部的路由规则将请求路由至我们的服务器。这个例子中我们使用 [xip.io][14] 来避免必要的 DNS 记录配置工作。它的工作原理是将 IP 地址作为子域包含,以使用 `10.0.0.8.xip.io` 的任何子域来达到 IP `10.0.0.8`。换句话说,`my-server.10.0.0.8.xip.io` 被用于访问集群中的 Ingress 控制器。你现在就可以尝试(使用你自己的 IP,而不是 10.0.0.8)。如果没有 Ingress,你应该会访问到“默认后端”,只是一个写着“404 page not found”的页面。
+
+我们可以使用以下 Ingress 让 Ingress 控制器将请求路由到我们的 Web 服务器的服务。
+
+```
+apiVersion: extensions/v1beta1
+kind: Ingress
+metadata:
+ name: my-server
+spec:
+ rules:
+ - host: my-server.10.0.0.8.xip.io
+ http:
+ paths:
+ - path: /
+ backend:
+ serviceName: my-server
+ servicePort: 80
+```
+
+将以上片段保存到 `my-ingress.yaml` 文件中,然后运行以下命令将其加入集群:
+
+```
+kubectl apply -f my-ingress.yaml
+```
+
+你现在应该能够在你选择的完全限定域名中访问到 nginx 的默认欢迎页面了。在我的例子中,它是 `my-server.10.0.0.8.xip.io`。Ingress 控制器会通过 Ingress 中包含的信息来路由请求。对 `my-server.10.0.0.8.xip.io` 的请求将被路由到 Ingress 中定义为 `backend` 的服务和端口(在本例中为 `my-server` 和 `80`)。
+
+### 那么,物联网呢?
+
+想象如下场景:你的家或农场周围有很多的设备。它是一个具有各种硬件功能、传感器和执行器的物联网设备的异构集合。也许某些设备拥有摄像头、天气或光线传感器。其它设备可能会被连接起来,用来控制通风、灯光、百叶窗或闪烁的 LED。
+
+这种情况下,你想从所有传感器中收集数据,在最终使用它来制定决策和控制执行器之前,也可能会对其进行处理和分析。除此之外,你可能还想配置一个仪表盘来可视化那些正在发生的事情。那么 Kubernetes 如何帮助我们来管理这样的事情呢?我们怎么保证 Pod 在合适的设备上运行?
+
+简单的答案就是“标签”。你可以根据功能来标记节点,如下所示:
+
+```
+kubectl label nodes =
+# 举例
+kubectl label nodes node2 camera=available
+```
+
+一旦它们被打上标签,我们就可以轻松地使用 [nodeSelector][15] 为你的工作负载选择合适的节点。拼图的最后一块:如果你想在*所有*合适的节点上运行 Pod,那应该使用 [DaemonSet][16] 而不是部署。换句话说,应为每个使用唯一传感器的数据收集应用程序创建一个 DaemonSet,并使用 nodeSelector 确保它们仅在具有适当硬件的节点上运行。
+
+服务发现功能允许 Pod 通过服务名称来寻找彼此,这项功能使得这类分布式系统的管理工作变得易如反掌。你不需要为应用配置 IP 地址或自定义端口,也不需要知道它们。相反,它们可以通过集群中的命名服务轻松找到彼此。
+
+#### 充分利用空闲资源
+
+随着集群的启动并运行,收集数据并控制灯光和气候,可能使你觉得你已经把它完成了。不过,集群中还有大量的计算资源可以用于其它项目。这才是 Kubernetes 真正出彩的地方。
+
+你不必担心这些资源的确切位置,或者去计算是否有足够的内存来容纳额外的应用程序。这正是编排系统所解决的问题!你可以轻松地在集群中部署更多的应用,让 Kubernetes 来找出适合运行它们的位置(或是否适合运行它们)。
+
+为什么不运行一个你自己的 [NextCloud][17] 实例呢?或者运行 [gitea][18]?你还可以为你所有的物联网容器设置一套 CI/CD 流水线。毕竟,如果你可以在集群中进行本地构建,为什么还要在主计算机上构建并交叉编译它们呢?
+
+这里的要点是,Kubernetes 可以更容易地利用那些你可能浪费掉的“隐藏”资源。Kubernetes 根据可用资源和容错处理规则来调度 Pod,因此你也无需手动完成这些工作。但是,为了帮助 Kubernetes 做出合理的决定,你绝对应该为你的工作负载添加[资源请求][19]配置。
+
+### 总结
+
+尽管 Kuberenetes 或一般的容器编排平台通常不会与物联网相关联,但在管理分布式系统时,使用一个编排系统肯定是有意义的。你不仅可以使用统一的方式来处理多样化和异构的设备,还可以简化它们的通信方式。此外,Kubernetes 还可以更好地对闲置资源加以利用。
+
+容器技术使构建“随处运行”应用的想法成为可能。现在,Kubernetes 可以更轻松地来负责“随处”的部分。作为构建一切的不可变基础,我们使用 Fedora IoT。
+
+--------------------------------------------------------------------------------
+
+via: https://fedoramagazine.org/kubernetes-on-fedora-iot-with-k3s/
+
+作者:[Lennart Jern][a]
+选题:[lujun9972][b]
+译者:[StdioA](https://github.com/StdioA)
+校对:[wxy](https://github.com/wxy)
+
+本文由 [LCTT](https://github.com/LCTT/TranslateProject) 原创编译,[Linux中国](https://linux.cn/) 荣誉推出
+
+[a]: https://fedoramagazine.org/author/lennartj/
+[b]: https://github.com/lujun9972
+[1]: https://fedoramagazine.org/wp-content/uploads/2019/04/k3s-1-816x345.png
+[2]: https://linux.cn/article-10380-1.html
+[3]: https://hub.helm.sh/
+[4]: https://k3s.io
+[5]: https://docs.fedoraproject.org/en-US/iot/getting-started/
+[6]: https://github.com/rancher/k3s#open-ports--network-security
+[7]: https://github.com/rancher/k3s#systemd
+[8]: https://kubernetes.io/docs/concepts/workloads/controllers/deployment/
+[9]: https://kubernetes.io/docs/concepts/services-networking/service/
+[10]: https://kubernetes.io/docs/concepts/services-networking/service/#loadbalancer
+[11]: https://kubernetes.io/docs/concepts/services-networking/ingress/
+[12]: https://traefik.io/
+[13]: https://github.com/rancher/k3s/blob/master/README.md#service-load-balancer
+[14]: http://xip.io/
+[15]: https://kubernetes.io/docs/concepts/configuration/assign-pod-node/
+[16]: https://kubernetes.io/docs/concepts/workloads/controllers/daemonset/
+[17]: https://nextcloud.com/
+[18]: https://gitea.io/en-us/
+[19]: https://kubernetes.io/docs/concepts/configuration/manage-compute-resources-container/
diff --git a/published/201905/20190416 Building a DNS-as-a-service with OpenStack Designate.md b/published/201905/20190416 Building a DNS-as-a-service with OpenStack Designate.md
new file mode 100644
index 0000000000..162097e5a9
--- /dev/null
+++ b/published/201905/20190416 Building a DNS-as-a-service with OpenStack Designate.md
@@ -0,0 +1,347 @@
+[#]: collector: (lujun9972)
+[#]: translator: (wxy)
+[#]: reviewer: (wxy)
+[#]: publisher: (wxy)
+[#]: url: (https://linux.cn/article-10840-1.html)
+[#]: subject: (Building a DNS-as-a-service with OpenStack Designate)
+[#]: via: (https://opensource.com/article/19/4/getting-started-openstack-designate)
+[#]: author: (Amjad Yaseen https://opensource.com/users/ayaseen)
+
+用 OpenStack Designate 构建一个 DNS 即服务(DNSaaS)
+======
+
+> 学习如何安装和配置 Designate,这是一个 OpenStack 的多租户 DNS 即服务(DNSaaS)。
+
+
+
+[Designate][2] 是一个多租户的 DNS 即服务,它包括一个用于域名和记录管理的 REST API 和集成了 [Neutron][3] 的框架,并支持 Bind9。
+
+DNSaaS 可以提供:
+
+ * 一个管理区域和记录的干净利落的 REST API
+ * 自动生成记录(集成 OpenStack)
+ * 支持多个授权名字服务器
+ * 可以托管多个项目/组织
+
+![Designate's architecture][4]
+
+这篇文章解释了如何在 CentOS 和 RHEL 上手动安装和配置 Designate 的最新版本,但是同样的配置也可以用在其它发行版上。
+
+### 在 OpenStack 上安装 Designate
+
+在我的 [GitHub 仓库][5]里,我已经放了 Ansible 的 bind 和 Designate 角色的示范设置。
+
+这个设置假定 bing 服务是安装 OpenStack 控制器节点之外(即使你可以在本地安装 bind)。
+
+1、在 OpenStack 控制节点上安装 Designate 和 bind 软件包:
+
+```
+# yum install openstack-designate-* bind bind-utils -y
+```
+
+2、创建 Designate 数据库和用户:
+
+```
+MariaDB [(none)]> CREATE DATABASE designate CHARACTER SET utf8 COLLATE utf8_general_ci;
+
+MariaDB [(none)]> GRANT ALL PRIVILEGES ON designate.* TO \
+'designate'@'localhost' IDENTIFIED BY 'rhlab123';
+
+MariaDB [(none)]> GRANT ALL PRIVILEGES ON designate.* TO 'designate'@'%' \
+IDENTIFIED BY 'rhlab123';
+```
+
+注意:bind 包必须安装在控制节点之外才能使远程名字服务控制(RNDC)功能正常。
+
+### 配置 bind(DNS 服务器)
+
+1、生成 RNDC 文件:
+
+```
+rndc-confgen -a -k designate -c /etc/rndc.key -r /dev/urandom
+
+cat < etcrndc.conf
+include "/etc/rndc.key";
+options {
+ default-key "designate";
+ default-server {{ DNS_SERVER_IP }};
+ default-port 953;
+};
+EOF
+```
+
+2、将下列配置添加到 `named.conf`:
+
+```
+include "/etc/rndc.key";
+controls {
+ inet {{ DNS_SERVER_IP }} allow { localhost;{{ CONTROLLER_SERVER_IP }}; } keys { "designate"; };
+};
+```
+
+在 `option` 节中,添加:
+
+```
+options {
+ ...
+ allow-new-zones yes;
+ request-ixfr no;
+ listen-on port 53 { any; };
+ recursion no;
+ allow-query { 127.0.0.1; {{ CONTROLLER_SERVER_IP }}; };
+};
+```
+
+添加正确的权限:
+
+```
+chown named:named /etc/rndc.key
+chown named:named /etc/rndc.conf
+chmod 600 /etc/rndc.key
+chown -v root:named /etc/named.conf
+chmod g+w /var/named
+
+# systemctl restart named
+# setsebool named_write_master_zones 1
+```
+
+3、把 `rndc.key` 和 `rndc.conf` 推入 OpenStack 控制节点:
+
+```
+# scp -r /etc/rndc* {{ CONTROLLER_SERVER_IP }}:/etc/
+```
+
+### 创建 OpenStack Designate 服务和端点
+
+输入:
+
+```
+# openstack user create --domain default --password-prompt designate
+# openstack role add --project services --user designate admin
+# openstack service create --name designate --description "DNS" dns
+
+# openstack endpoint create --region RegionOne dns public http://{{ CONTROLLER_SERVER_IP }}:9001/
+# openstack endpoint create --region RegionOne dns internal http://{{ CONTROLLER_SERVER_IP }}:9001/
+# openstack endpoint create --region RegionOne dns admin http://{{ CONTROLLER_SERVER_IP }}:9001/
+```
+
+### 配置 Designate 服务
+
+1、编辑 `/etc/designate/designate.conf`:
+
+在 `[service:api]` 节配置 `auth_strategy`:
+
+```
+[service:api]
+listen = 0.0.0.0:9001
+auth_strategy = keystone
+api_base_uri = http://{{ CONTROLLER_SERVER_IP }}:9001/
+enable_api_v2 = True
+enabled_extensions_v2 = quotas, reports
+```
+
+在 `[keystone_authtoken]` 节配置下列选项:
+
+```
+[keystone_authtoken]
+auth_type = password
+username = designate
+password = rhlab123
+project_name = service
+project_domain_name = Default
+user_domain_name = Default
+www_authenticate_uri = http://{{ CONTROLLER_SERVER_IP }}:5000/
+auth_url = http://{{ CONTROLLER_SERVER_IP }}:5000/
+```
+
+在 `[service:worker]` 节,启用 worker 模型:
+
+```
+enabled = True
+notify = True
+```
+
+在 `[storage:sqlalchemy]` 节,配置数据库访问:
+
+```
+[storage:sqlalchemy]
+connection = mysql+pymysql://designate:rhlab123@{{ CONTROLLER_SERVER_IP }}/designate
+```
+
+填充 Designate 数据库:
+
+```
+# su -s /bin/sh -c "designate-manage database sync" designate
+```
+
+2、 创建 Designate 的 `pools.yaml` 文件(包含 target 和 bind 细节):
+
+编辑 `/etc/designate/pools.yaml`:
+
+```
+- name: default
+ # The name is immutable. There will be no option to change the name after
+ # creation and the only way will to change it will be to delete it
+ # (and all zones associated with it) and recreate it.
+ description: Default Pool
+
+ attributes: {}
+
+ # List out the NS records for zones hosted within this pool
+ # This should be a record that is created outside of designate, that
+ # points to the public IP of the controller node.
+ ns_records:
+ - hostname: {{Controller_FQDN}}. # Thisis mDNS
+ priority: 1
+
+ # List out the nameservers for this pool. These are the actual BIND servers.
+ # We use these to verify changes have propagated to all nameservers.
+ nameservers:
+ - host: {{ DNS_SERVER_IP }}
+ port: 53
+
+ # List out the targets for this pool. For BIND there will be one
+ # entry for each BIND server, as we have to run rndc command on each server
+ targets:
+ - type: bind9
+ description: BIND9 Server 1
+
+ # List out the designate-mdns servers from which BIND servers should
+ # request zone transfers (AXFRs) from.
+ # This should be the IP of the controller node.
+ # If you have multiple controllers you can add multiple masters
+ # by running designate-mdns on them, and adding them here.
+ masters:
+ - host: {{ CONTROLLER_SERVER_IP }}
+ port: 5354
+
+ # BIND Configuration options
+ options:
+ host: {{ DNS_SERVER_IP }}
+ port: 53
+ rndc_host: {{ DNS_SERVER_IP }}
+ rndc_port: 953
+ rndc_key_file: /etc/rndc.key
+ rndc_config_file: /etc/rndc.conf
+```
+
+填充 Designate 池:
+
+```
+su -s /bin/sh -c "designate-manage pool update" designate
+```
+
+3、启动 Designate 中心和 API 服务:
+
+```
+systemctl enable --now designate-central designate-api
+```
+
+4、验证 Designate 服务运行:
+
+```
+# openstack dns service list
+
++--------------+--------+-------+--------------+
+| service_name | status | stats | capabilities |
++--------------+--------+-------+--------------+
+| central | UP | - | - |
+| api | UP | - | - |
+| mdns | UP | - | - |
+| worker | UP | - | - |
+| producer | UP | - | - |
++--------------+--------+-------+--------------+
+```
+
+### 用外部 DNS 配置 OpenStack Neutron
+
+1、为 Designate 服务配置 iptables:
+
+```
+# iptables -I INPUT -p tcp -m multiport --dports 9001 -m comment --comment "designate incoming" -j ACCEPT
+
+# iptables -I INPUT -p tcp -m multiport --dports 5354 -m comment --comment "Designate mdns incoming" -j ACCEPT
+
+# iptables -I INPUT -p tcp -m multiport --dports 53 -m comment --comment "bind incoming" -j ACCEPT
+
+# iptables -I INPUT -p udp -m multiport --dports 53 -m comment --comment "bind/powerdns incoming" -j ACCEPT
+
+# iptables -I INPUT -p tcp -m multiport --dports 953 -m comment --comment "rndc incoming - bind only" -j ACCEPT
+
+# service iptables save; service iptables restart
+# setsebool named_write_master_zones 1
+```
+
+2、 编辑 `/etc/neutron/neutron.conf` 的 `[default]` 节:
+
+```
+external_dns_driver = designate
+```
+
+3、 在 `/etc/neutron/neutron.conf` 中添加 `[designate]` 节:
+
+```
+[designate]
+url = http://{{ CONTROLLER_SERVER_IP }}:9001/v2 ## This end point of designate
+auth_type = password
+auth_url = http://{{ CONTROLLER_SERVER_IP }}:5000
+username = designate
+password = rhlab123
+project_name = services
+project_domain_name = Default
+user_domain_name = Default
+allow_reverse_dns_lookup = True
+ipv4_ptr_zone_prefix_size = 24
+ipv6_ptr_zone_prefix_size = 116
+```
+
+4、编辑 `neutron.conf` 的 `dns_domain`:
+
+```
+dns_domain = rhlab.dev.
+```
+
+重启:
+
+```
+# systemctl restart neutron-*
+```
+
+5、在 `/etc/neutron/plugins/ml2/ml2_conf.ini` 中的组成层 2(ML2)中添加 `dns`:
+
+```
+extension_drivers=port_security,qos,dns
+```
+
+6、在 Designate 中添加区域:
+
+```
+# openstack zone create –email=admin@rhlab.dev rhlab.dev.
+```
+
+在 `rhlab.dev` 区域中添加记录:
+
+```
+# openstack recordset create --record '192.168.1.230' --type A rhlab.dev. Test
+```
+
+Designate 现在就安装和配置好了。
+
+--------------------------------------------------------------------------------
+
+via: https://opensource.com/article/19/4/getting-started-openstack-designate
+
+作者:[Amjad Yaseen][a]
+选题:[lujun9972][b]
+译者:[wxy](https://github.com/wxy)
+校对:[wxy](https://github.com/wxy)
+
+本文由 [LCTT](https://github.com/LCTT/TranslateProject) 原创编译,[Linux中国](https://linux.cn/) 荣誉推出
+
+[a]: https://opensource.com/users/ayaseen
+[b]: https://github.com/lujun9972
+[1]: https://opensource.com/sites/default/files/styles/image-full-size/public/lead-images/command_line_prompt.png?itok=wbGiJ_yg (Command line prompt)
+[2]: https://docs.openstack.org/designate/latest/
+[3]: /article/19/3/openstack-neutron
+[4]: https://opensource.com/sites/default/files/uploads/openstack_designate_architecture.png (Designate's architecture)
+[5]: https://github.com/ayaseen/designate
diff --git a/translated/tech/20190416 Detecting malaria with deep learning.md b/published/201905/20190416 Detecting malaria with deep learning.md
similarity index 51%
rename from translated/tech/20190416 Detecting malaria with deep learning.md
rename to published/201905/20190416 Detecting malaria with deep learning.md
index 2089636e6a..a1ce049292 100644
--- a/translated/tech/20190416 Detecting malaria with deep learning.md
+++ b/published/201905/20190416 Detecting malaria with deep learning.md
@@ -1,85 +1,86 @@
[#]: collector: (lujun9972)
[#]: translator: (warmfrog)
-[#]: reviewer: ( )
-[#]: publisher: ( )
-[#]: url: ( )
+[#]: reviewer: (wxy)
+[#]: publisher: (wxy)
+[#]: url: (https://linux.cn/article-10891-1.html)
[#]: subject: (Detecting malaria with deep learning)
[#]: via: (https://opensource.com/article/19/4/detecting-malaria-deep-learning)
-[#]: author: (Dipanjan Sarkar https://opensource.com/users/djsarkar)
+[#]: author: (Dipanjan Sarkar https://opensource.com/users/djsarkar)
使用深度学习检测疟疾
==================
-人工智能结合开源硬件工具能够提升严重传染病疟疾的诊断。
+
+> 人工智能结合开源硬件工具能够提升严重传染病疟疾的诊断。
+
![][1]
-人工智能(AI)和开源工具,技术,和框架是促进社会进步的强有力的结合。_“健康就是财富”_可能有点陈词滥调,但它却是非常准确的!在本篇文章,我们将测试 AI 是如何与低花费,有效,精确的开源深度学习方法一起被利用来检测致死的传染病疟疾。
+人工智能(AI)和开源工具、技术和框架是促进社会进步的强有力的结合。“健康就是财富”可能有点陈词滥调,但它却是非常准确的!在本篇文章,我们将测试 AI 是如何与低成本、有效、精确的开源深度学习方法结合起来一起用来检测致死的传染病疟疾。
我既不是一个医生,也不是一个医疗保健研究者,我也绝不像他们那样合格,我只是对将 AI 应用到医疗保健研究感兴趣。在这片文章中我的想法是展示 AI 和开源解决方案如何帮助疟疾检测和减少人工劳动的方法。
![Python and TensorFlow][2]
-Python and TensorFlow: 一个构建开源深度学习方法的很棒的结合
+*Python 和 TensorFlow: 一个构建开源深度学习方法的很棒的结合*
-感谢 Python 的强大 和像 TensorFlow 这样的深度学习框架,我们能够构建鲁棒的,大规模的,有效的深度学习方法。因为这些工具是自由和开源的,我们能够构建低成本的能够轻易被任何人采纳和使用的解决方案。让我们开始吧!
+感谢 Python 的强大和像 TensorFlow 这样的深度学习框架,我们能够构建健壮的、大规模的、有效的深度学习方法。因为这些工具是自由和开源的,我们能够构建非常经济且易于被任何人采纳和使用的解决方案。让我们开始吧!
### 项目动机
-疟疾是由_疟原虫_造成的致死的,有传染性的,蚊子传播的疾病,主要通过受感染的雌性按蚊叮咬传播。共有五种寄生虫能够造成疟疾,但是样例中的大多数是这两种类型- _恶性疟原虫_ 和 _间日疟原虫_ 造成的。
+疟疾是由*疟原虫*造成的致死的、有传染性的、蚊子传播的疾病,主要通过受感染的雌性按蚊叮咬传播。共有五种寄生虫能够引起疟疾,但是大多数病例是这两种类型造成的:恶性疟原虫和间日疟原虫。
![疟疾热图][3]
这个地图显示了疟疾在全球传播分布形势,尤其在热带地区,但疾病的性质和致命性是该项目的主要动机。
-如果一个雌性蚊子咬了你,蚊子携带的寄生虫进入你的血液并且开始破坏携带氧气的红细胞(RBC)。通常,疟疾的最初症状类似于流感病毒,在蚊子叮咬后,他们通常在几天或几周内发作。然而,这些致死的寄生虫可以在你的身体里生存长达一年并且不会造成任何症状,延迟治疗可能造成并发症甚至死亡。因此,早期的检查能够挽救生命。
+如果一只受感染雌性蚊子叮咬了你,蚊子携带的寄生虫进入你的血液,并且开始破坏携带氧气的红细胞(RBC)。通常,疟疾的最初症状类似于流感病毒,在蚊子叮咬后,他们通常在几天或几周内发作。然而,这些致死的寄生虫可以在你的身体里生存长达一年并且不会造成任何症状,延迟治疗可能造成并发症甚至死亡。因此,早期的检查能够挽救生命。
-世界健康组织(WHO)的[疟疾事件][4]暗示世界近乎一半的人口面临疟疾的风险,有超过 2 亿 的疟疾病例,每年由于疟疾造成的死亡近乎 40 万。这是使疟疾检测和诊断快速,简单和有效的一个动机。
+世界健康组织(WHO)的[疟疾实情][4]表明,世界近乎一半的人口面临疟疾的风险,有超过 2 亿的疟疾病例,每年由于疟疾造成的死亡将近 40 万。这是使疟疾检测和诊断快速、简单和有效的一个动机。
### 检测疟疾的方法
-有几种方法能够用来检测和诊断疟疾。该文中的项目就是基于 Rajaraman,et al. 的论文:“[预先训练的卷积神经网络作为特征提取器,用于改善薄血涂片图像中的疟疾寄生虫检测][5]”,介绍了一些方法,包含聚合酶链反应(PCR)和快速诊断测试(RDT)。这两种测试通常在高质量的显微镜下使用,但这样的设备不是轻易能够获得的。
+有几种方法能够用来检测和诊断疟疾。该文中的项目就是基于 Rajaraman, et al. 的论文:“[预先训练的卷积神经网络作为特征提取器,用于改善薄血涂片图像中的疟疾寄生虫检测][5]”介绍的一些方法,包含聚合酶链反应(PCR)和快速诊断测试(RDT)。这两种测试通常用于无法提供高质量显微镜服务的地方。
-标准的疟疾诊断通常使基于血液涂片工作流的,根据 Carlos Ariza 的文章“[Malaria Hero: 一个更快诊断疟原虫的网络应用][6]”,我从中了解到 Adrian Rosebrock 的“[使用 Keras 的深度学习和医学图像分析][7]”。我感激这些优秀的资源的作者,让我在疟原虫预防,诊断和治疗方面有了更多的想法。
+标准的疟疾诊断通常是基于血液涂片工作流程的,根据 Carlos Ariza 的文章“[Malaria Hero:一个更快诊断疟原虫的网络应用][6]”,我从中了解到 Adrian Rosebrock 的“[使用 Keras 的深度学习和医学图像分析][7]”。我感激这些优秀的资源的作者,让我在疟原虫预防、诊断和治疗方面有了更多的想法。
![疟原虫检测的血涂片工作流程][8]
-一个疟原虫检测的血涂片工作流程
+*一个疟原虫检测的血涂片工作流程*
-根据 WHO 草案,诊断通常包括对放大 100 倍的血涂片的集中检测。训练人们人工计数在 5000 个细胞中有多少红细胞中包含疟原虫。正如上述解释中引用的 Rajaraman, et al. 的论文:
+根据 WHO 方案,诊断通常包括对放大 100 倍的血涂片的集中检测。受过训练的人们手工计算在 5000 个细胞中有多少红细胞中包含疟原虫。正如上述解释中引用的 Rajaraman, et al. 的论文:
-> 薄血涂片帮助检测疟原虫的存在性并且帮助识别造成传染(疾病控制和抑制中心,2012)的物种。诊断准确性在很大程度上取决于人类的专业知识,并且可能受到观察者间差异和疾病流行/资源受限区域大规模诊断所造成的不利影响(Mitiku, Mengistu, and Gelaw, 2003)。可替代的技术是使用聚合酶链反应(PCR)和快速诊断测试(RDT);然而,PCR 分析受限于它的性能(Hommelsheim, et al., 2014),RDT 在疾病流行的地区成本效益低(Hawkes,Katsuva, and Masumbuko, 2009)。
+> 厚血涂片有助于检测寄生虫的存在,而薄血涂片有助于识别引起感染的寄生虫种类(疾病控制和预防中心, 2012)。诊断准确性在很大程度上取决于诊断人的专业知识,并且可能受到观察者间差异和疾病流行/资源受限区域大规模诊断所造成的不利影响(Mitiku, Mengistu 和 Gelaw, 2003)。可替代的技术是使用聚合酶链反应(PCR)和快速诊断测试(RDT);然而,PCR 分析受限于它的性能(Hommelsheim, et al., 2014),RDT 在疾病流行的地区成本效益低(Hawkes, Katsuva 和 Masumbuko, 2009)。
因此,疟疾检测可能受益于使用机器学习的自动化。
-### 疟原虫检测的深度学习
+### 疟疾检测的深度学习
-人工诊断血涂片是一个加强的人工过程,需要专业知识来分类和计数被寄生虫感染的和未感染的细胞。这个过程可能不能很好的规模化,尤其在那些专业人士不足的地区。在利用最先进的图像处理和分析技术提取人工选取特征和构建基于机器学习的分类模型方面取得了一些进展。然而,这些模型不能大规模推广,因为没有更多的数据用来训练,并且人工选取特征需要花费很长时间。
+人工诊断血涂片是一个繁重的手工过程,需要专业知识来分类和计数被寄生虫感染的和未感染的细胞。这个过程可能不能很好的规模化,尤其在那些专业人士不足的地区。在利用最先进的图像处理和分析技术提取人工选取特征和构建基于机器学习的分类模型方面取得了一些进展。然而,这些模型不能大规模推广,因为没有更多的数据用来训练,并且人工选取特征需要花费很长时间。
-深度学习模型,或者更具体地讲,卷积神经网络(CNNs),已经被证明在各种计算机视觉任务中非常有效。(如果你想有额外的关于 CNNs 的背景知识,我推荐你阅读[视觉识别的 CS2331n 卷积神经网络][9]。)简单地讲,CNN 模型的关键层包含卷积和池化层,正如下面图像显示。
+深度学习模型,或者更具体地讲,卷积神经网络(CNN),已经被证明在各种计算机视觉任务中非常有效。(如果你想更多的了解关于 CNN 的背景知识,我推荐你阅读[视觉识别的 CS2331n 卷积神经网络][9]。)简单地讲,CNN 模型的关键层包含卷积和池化层,正如下图所示。
![A typical CNN architecture][10]
-一个典型的 CNN 架构
+*一个典型的 CNN 架构*
-卷积层从数据中学习空间层级模式,它是平移不变的,因此它们能够学习不同方面的图像。例如,第一个卷积层将学习小的和本地图案,例如边缘和角落,第二个卷积层学习基于第一层的特征的更大的图案,等等。这允许 CNNs 自动化提取特征并且学习对于新数据点通用的有效的特征。池化层帮助下采样和降维。
+卷积层从数据中学习空间层级模式,它是平移不变的,因此它们能够学习图像的不同方面。例如,第一个卷积层将学习小的和局部图案,例如边缘和角落,第二个卷积层将基于第一层的特征学习更大的图案,等等。这允许 CNN 自动化提取特征并且学习对于新数据点通用的有效的特征。池化层有助于下采样和减少尺寸。
-因此,CNNs 帮助自动化和规模化的特征工程。同样,在模型末尾加上密集层允许我们执行像图像分类这样的任务。使用像 CNNs 者的深度学习模型自动的疟疾检测可能非常有效,便宜和具有规模性,尤其是迁移学习和预训练模型效果非常好,甚至在少量数据的约束下。
+因此,CNN 有助于自动化和规模化的特征工程。同样,在模型末尾加上密集层允许我们执行像图像分类这样的任务。使用像 CNN 这样的深度学习模型自动的疟疾检测可能非常有效、便宜和具有规模性,尤其是迁移学习和预训练模型效果非常好,甚至在少量数据的约束下。
-Rajaraman, et al. 的论文在一个数据集上利用六个预训练模型在检测疟疾 vs 无感染样本获取到令人吃惊的 95.9% 的准确率。我们的关注点是从头开始尝试一些简单的 CNN 模型和用一个预训练的训练模型使用迁移学习来查看我们能够从相同的数据集中得到什么。我们将使用开源工具和框架,包括 Python 和 TensorFlow,来构建我们的模型。
+Rajaraman, et al. 的论文在一个数据集上利用六个预训练模型在检测疟疾对比无感染样本获取到令人吃惊的 95.9% 的准确率。我们的重点是从头开始尝试一些简单的 CNN 模型和用一个预训练的训练模型使用迁移学习来查看我们能够从相同的数据集中得到什么。我们将使用开源工具和框架,包括 Python 和 TensorFlow,来构建我们的模型。
### 数据集
-我们分析的数据来自 Lister Hill 国家生物医学交流中心(LHNCBC),国家医学图书馆(NLM)的一部分,他们细心收集和标记了健康和受感染的血涂片图像的[公众可获得的数据集][11]。这些研究者已经开发了一个运行在 Android 智能手机的移动[疟疾检测应用][12],连接到一个传统的光学显微镜。它们使用 吉姆萨染液 将 150 个受恶性疟原虫感染的和 50 个健康病人的薄血涂片染色,这些薄血涂片是在孟加拉的吉大港医学院附属医院收集和照相的。使用智能手机的内置相机获取每个显微镜视窗内的图像。这些图片由在泰国曼谷的马希多-牛津热带医学研究所的一个专家使用幻灯片阅读器标记的。
+我们分析的数据来自 Lister Hill 国家生物医学交流中心(LHNCBC)的研究人员,该中心是国家医学图书馆(NLM)的一部分,他们细心收集和标记了公开可用的健康和受感染的血涂片图像的[数据集][11]。这些研究者已经开发了一个运行在 Android 智能手机的[疟疾检测手机应用][12],连接到一个传统的光学显微镜。它们使用吉姆萨染液将 150 个受恶性疟原虫感染的和 50 个健康病人的薄血涂片染色,这些薄血涂片是在孟加拉的吉大港医学院附属医院收集和照相的。使用智能手机的内置相机获取每个显微镜视窗内的图像。这些图片由在泰国曼谷的马希多-牛津热带医学研究所的一个专家使用幻灯片阅读器标记的。
-让我们简洁的查看数据集的结构。首先,我将安装一些基础的依赖(基于使用的操作系统)。
+让我们简要地查看一下数据集的结构。首先,我将安装一些基础的依赖(基于使用的操作系统)。
![Installing dependencies][13]
-我使用的是云上的带有一个 GPU 的基于 Debian 的操作系统,这样我能更快的运行我的模型。为了查看目录结构,我们必须安装 tree 依赖(如果我们没有安装的话)使用 **sudo apt install tree**。
+我使用的是云上的带有一个 GPU 的基于 Debian 的操作系统,这样我能更快的运行我的模型。为了查看目录结构,我们必须使用 `sudo apt install tree` 安装 `tree` 及其依赖(如果我们没有安装的话)。
![Installing the tree dependency][14]
-我们有两个文件夹包含血细胞的图像,包括受感染的和健康的。我们可以获取关于图像总数更多的细节通过输入:
-
+我们有两个文件夹包含血细胞的图像,包括受感染的和健康的。我们通过输入可以获取关于图像总数更多的细节:
```
import os
@@ -97,7 +98,7 @@ len(infected_files), len(healthy_files)
(13779, 13779)
```
-看起来我们有一个平衡的 13,779 张疟疾的 和 13,779 张非疟疾的(健康的)血细胞图像。让我们根据这些构建数据帧,我们将用这些数据帧来构建我们的数据集。
+看起来我们有一个平衡的数据集,包含 13,779 张疟疾的和 13,779 张非疟疾的(健康的)血细胞图像。让我们根据这些构建数据帧,我们将用这些数据帧来构建我们的数据集。
```
@@ -107,8 +108,8 @@ import pandas as pd
np.random.seed(42)
files_df = pd.DataFrame({
-'filename': infected_files + healthy_files,
-'label': ['malaria'] * len(infected_files) + ['healthy'] * len(healthy_files)
+ 'filename': infected_files + healthy_files,
+ 'label': ['malaria'] * len(infected_files) + ['healthy'] * len(healthy_files)
}).sample(frac=1, random_state=42).reset_index(drop=True)
files_df.head()
@@ -116,9 +117,9 @@ files_df.head()
![Datasets][15]
-### 构建和参所图像数据集
+### 构建和了解图像数据集
-为了构建深度学习模型,我们需要训练数据,但是我们还需要使用不可见的数据测试模型的性能。相应的,我们将使用 60:10:30 的划分用于训练,验证和测试数据集。我们将在训练期间应用训练和验证数据集并用测试数据集来检查模型的性能。
+为了构建深度学习模型,我们需要训练数据,但是我们还需要使用不可见的数据测试模型的性能。相应的,我们将使用 60:10:30 的比例来划分用于训练、验证和测试的数据集。我们将在训练期间应用训练和验证数据集,并用测试数据集来检查模型的性能。
```
@@ -126,24 +127,23 @@ from sklearn.model_selection import train_test_split
from collections import Counter
train_files, test_files, train_labels, test_labels = train_test_split(files_df['filename'].values,
-files_df['label'].values,
-test_size=0.3, random_state=42)
+ files_df['label'].values,
+ test_size=0.3, random_state=42)
train_files, val_files, train_labels, val_labels = train_test_split(train_files,
-train_labels,
-test_size=0.1, random_state=42)
+ train_labels,
+ test_size=0.1, random_state=42)
print(train_files.shape, val_files.shape, test_files.shape)
print('Train:', Counter(train_labels), '\nVal:', Counter(val_labels), '\nTest:', Counter(test_labels))
# Output
(17361,) (1929,) (8268,)
-Train: Counter({'healthy': 8734, 'malaria': 8627})
-Val: Counter({'healthy': 970, 'malaria': 959})
+Train: Counter({'healthy': 8734, 'malaria': 8627})
+Val: Counter({'healthy': 970, 'malaria': 959})
Test: Counter({'malaria': 4193, 'healthy': 4075})
```
-这些图片维度并不相同,因此血涂片和细胞图像是基于人类,测试方法,图片的朝向。让我们总结我们的训练数据集的统计信息来决定最佳的图像维度(牢记,我们根本不会碰测试数据集)。
-
+这些图片尺寸并不相同,因为血涂片和细胞图像是基于人、测试方法、图片方向不同而不同的。让我们总结我们的训练数据集的统计信息来决定最佳的图像尺寸(牢记,我们根本不会碰测试数据集)。
```
import cv2
@@ -151,24 +151,25 @@ from concurrent import futures
import threading
def get_img_shape_parallel(idx, img, total_imgs):
-if idx % 5000 == 0 or idx == (total_imgs - 1):
-print('{}: working on img num: {}'.format(threading.current_thread().name,
-idx))
-return cv2.imread(img).shape
-
+ if idx % 5000 == 0 or idx == (total_imgs - 1):
+ print('{}: working on img num: {}'.format(threading.current_thread().name,
+ idx))
+ return cv2.imread(img).shape
+
ex = futures.ThreadPoolExecutor(max_workers=None)
data_inp = [(idx, img, len(train_files)) for idx, img in enumerate(train_files)]
print('Starting Img shape computation:')
-train_img_dims_map = ex.map(get_img_shape_parallel,
-[record[0] for record in data_inp],
-[record[1] for record in data_inp],
-[record[2] for record in data_inp])
+train_img_dims_map = ex.map(get_img_shape_parallel,
+ [record[0] for record in data_inp],
+ [record[1] for record in data_inp],
+ [record[2] for record in data_inp])
train_img_dims = list(train_img_dims_map)
-print('Min Dimensions:', np.min(train_img_dims, axis=0))
+print('Min Dimensions:', np.min(train_img_dims, axis=0))
print('Avg Dimensions:', np.mean(train_img_dims, axis=0))
print('Median Dimensions:', np.median(train_img_dims, axis=0))
print('Max Dimensions:', np.max(train_img_dims, axis=0))
+
# Output
Starting Img shape computation:
ThreadPoolExecutor-0_0: working on img num: 0
@@ -176,27 +177,26 @@ ThreadPoolExecutor-0_17: working on img num: 5000
ThreadPoolExecutor-0_15: working on img num: 10000
ThreadPoolExecutor-0_1: working on img num: 15000
ThreadPoolExecutor-0_7: working on img num: 17360
-Min Dimensions: [46 46 3]
-Avg Dimensions: [132.77311215 132.45757733 3.]
-Median Dimensions: [130. 130. 3.]
-Max Dimensions: [385 394 3]
+Min Dimensions: [46 46 3]
+Avg Dimensions: [132.77311215 132.45757733 3.]
+Median Dimensions: [130. 130. 3.]
+Max Dimensions: [385 394 3]
```
-我们应用并行处理来加速图像读取,并且在总结统计时,我们将重新调整每幅图片到 125x125 像素。让我们载入我们所有的图像并重新调整它们为这些固定的大小。
-
+我们应用并行处理来加速图像读取,并且基于汇总统计结果,我们将每幅图片的尺寸重新调整到 125x125 像素。让我们载入我们所有的图像并重新调整它们为这些固定尺寸。
```
IMG_DIMS = (125, 125)
def get_img_data_parallel(idx, img, total_imgs):
-if idx % 5000 == 0 or idx == (total_imgs - 1):
-print('{}: working on img num: {}'.format(threading.current_thread().name,
-idx))
-img = cv2.imread(img)
-img = cv2.resize(img, dsize=IMG_DIMS,
-interpolation=cv2.INTER_CUBIC)
-img = np.array(img, dtype=np.float32)
-return img
+ if idx % 5000 == 0 or idx == (total_imgs - 1):
+ print('{}: working on img num: {}'.format(threading.current_thread().name,
+ idx))
+ img = cv2.imread(img)
+ img = cv2.resize(img, dsize=IMG_DIMS,
+ interpolation=cv2.INTER_CUBIC)
+ img = np.array(img, dtype=np.float32)
+ return img
ex = futures.ThreadPoolExecutor(max_workers=None)
train_data_inp = [(idx, img, len(train_files)) for idx, img in enumerate(train_files)]
@@ -204,27 +204,28 @@ val_data_inp = [(idx, img, len(val_files)) for idx, img in enumerate(val_files)]
test_data_inp = [(idx, img, len(test_files)) for idx, img in enumerate(test_files)]
print('Loading Train Images:')
-train_data_map = ex.map(get_img_data_parallel,
-[record[0] for record in train_data_inp],
-[record[1] for record in train_data_inp],
-[record[2] for record in train_data_inp])
+train_data_map = ex.map(get_img_data_parallel,
+ [record[0] for record in train_data_inp],
+ [record[1] for record in train_data_inp],
+ [record[2] for record in train_data_inp])
train_data = np.array(list(train_data_map))
print('\nLoading Validation Images:')
-val_data_map = ex.map(get_img_data_parallel,
-[record[0] for record in val_data_inp],
-[record[1] for record in val_data_inp],
-[record[2] for record in val_data_inp])
+val_data_map = ex.map(get_img_data_parallel,
+ [record[0] for record in val_data_inp],
+ [record[1] for record in val_data_inp],
+ [record[2] for record in val_data_inp])
val_data = np.array(list(val_data_map))
print('\nLoading Test Images:')
-test_data_map = ex.map(get_img_data_parallel,
-[record[0] for record in test_data_inp],
-[record[1] for record in test_data_inp],
-[record[2] for record in test_data_inp])
+test_data_map = ex.map(get_img_data_parallel,
+ [record[0] for record in test_data_inp],
+ [record[1] for record in test_data_inp],
+ [record[2] for record in test_data_inp])
test_data = np.array(list(test_data_map))
-train_data.shape, val_data.shape, test_data.shape
+train_data.shape, val_data.shape, test_data.shape
+
# Output
Loading Train Images:
@@ -245,23 +246,22 @@ ThreadPoolExecutor-1_8: working on img num: 8267
((17361, 125, 125, 3), (1929, 125, 125, 3), (8268, 125, 125, 3))
```
-我们再次应用并行处理来加速有关图像载入和重新调整大小。最终,我们获得了想要的维度的图片张量,正如之前描述的。我们现在查看一些血细胞图像样本来对我们的数据什么样有个印象。
-
+我们再次应用并行处理来加速有关图像载入和重新调整大小的计算。最终,我们获得了所需尺寸的图片张量,正如前面的输出所示。我们现在查看一些血细胞图像样本,以对我们的数据有个印象。
```
import matplotlib.pyplot as plt
%matplotlib inline
plt.figure(1 , figsize = (8 , 8))
-n = 0
+n = 0
for i in range(16):
-n += 1
-r = np.random.randint(0 , train_data.shape[0] , 1)
-plt.subplot(4 , 4 , n)
-plt.subplots_adjust(hspace = 0.5 , wspace = 0.5)
-plt.imshow(train_data[r[0]]/255.)
-plt.title('{}'.format(train_labels[r[0]]))
-plt.xticks([]) , plt.yticks([])
+ n += 1
+ r = np.random.randint(0 , train_data.shape[0] , 1)
+ plt.subplot(4 , 4 , n)
+ plt.subplots_adjust(hspace = 0.5 , wspace = 0.5)
+ plt.imshow(train_data[r[0]]/255.)
+ plt.title('{}'.format(train_labels[r[0]]))
+ plt.xticks([]) , plt.yticks([])
```
![Malaria cell samples][16]
@@ -270,7 +270,6 @@ plt.xticks([]) , plt.yticks([])
开始我们的模型训练前,我们必须建立一些基础的配置设置。
-
```
BATCH_SIZE = 64
NUM_CLASSES = 2
@@ -290,12 +289,12 @@ val_labels_enc = le.transform(val_labels)
print(train_labels[:6], train_labels_enc[:6])
+
# Output
['malaria' 'malaria' 'malaria' 'healthy' 'healthy' 'malaria'] [1 1 1 0 0 1]
```
-我们修复我们的图像维度,批大小,和历元并编码我们的分类类标签。TensorFlow 2.0 于 2019 年三月发布,这个练习是非常好的借口来试用它。
-
+我们修复我们的图像尺寸、批量大小,和纪元,并编码我们的分类的类标签。TensorFlow 2.0 于 2019 年三月发布,这个练习是尝试它的完美理由。
```
import tensorflow as tf
@@ -312,24 +311,23 @@ tf.__version__
### 深度学习训练
-在模型训练阶段,我们将构建三个深度训练模型,使用我们的训练集训练,使用验证数据比较它们的性能。我们然后保存这些模型并在之后的模型评估阶段使用它们。
+在模型训练阶段,我们将构建三个深度训练模型,使用我们的训练集训练,使用验证数据比较它们的性能。然后,我们保存这些模型并在之后的模型评估阶段使用它们。
#### 模型 1:从头开始的 CNN
我们的第一个疟疾检测模型将从头开始构建和训练一个基础的 CNN。首先,让我们定义我们的模型架构,
-
```
inp = tf.keras.layers.Input(shape=INPUT_SHAPE)
-conv1 = tf.keras.layers.Conv2D(32, kernel_size=(3, 3),
-activation='relu', padding='same')(inp)
+conv1 = tf.keras.layers.Conv2D(32, kernel_size=(3, 3),
+ activation='relu', padding='same')(inp)
pool1 = tf.keras.layers.MaxPooling2D(pool_size=(2, 2))(conv1)
-conv2 = tf.keras.layers.Conv2D(64, kernel_size=(3, 3),
-activation='relu', padding='same')(pool1)
+conv2 = tf.keras.layers.Conv2D(64, kernel_size=(3, 3),
+ activation='relu', padding='same')(pool1)
pool2 = tf.keras.layers.MaxPooling2D(pool_size=(2, 2))(conv2)
-conv3 = tf.keras.layers.Conv2D(128, kernel_size=(3, 3),
-activation='relu', padding='same')(pool2)
+conv3 = tf.keras.layers.Conv2D(128, kernel_size=(3, 3),
+ activation='relu', padding='same')(pool2)
pool3 = tf.keras.layers.MaxPooling2D(pool_size=(2, 2))(conv3)
flat = tf.keras.layers.Flatten()(pool3)
@@ -343,31 +341,32 @@ out = tf.keras.layers.Dense(1, activation='sigmoid')(drop2)
model = tf.keras.Model(inputs=inp, outputs=out)
model.compile(optimizer='adam',
-loss='binary_crossentropy',
-metrics=['accuracy'])
+ loss='binary_crossentropy',
+ metrics=['accuracy'])
model.summary()
+
# Output
Model: "model"
_________________________________________________________________
-Layer (type) Output Shape Param #
+Layer (type) Output Shape Param #
=================================================================
-input_1 (InputLayer) [(None, 125, 125, 3)] 0
+input_1 (InputLayer) [(None, 125, 125, 3)] 0
_________________________________________________________________
-conv2d (Conv2D) (None, 125, 125, 32) 896
+conv2d (Conv2D) (None, 125, 125, 32) 896
_________________________________________________________________
-max_pooling2d (MaxPooling2D) (None, 62, 62, 32) 0
+max_pooling2d (MaxPooling2D) (None, 62, 62, 32) 0
_________________________________________________________________
-conv2d_1 (Conv2D) (None, 62, 62, 64) 18496
+conv2d_1 (Conv2D) (None, 62, 62, 64) 18496
_________________________________________________________________
...
...
_________________________________________________________________
-dense_1 (Dense) (None, 512) 262656
+dense_1 (Dense) (None, 512) 262656
_________________________________________________________________
-dropout_1 (Dropout) (None, 512) 0
+dropout_1 (Dropout) (None, 512) 0
_________________________________________________________________
-dense_2 (Dense) (None, 1) 513
+dense_2 (Dense) (None, 1) 513
=================================================================
Total params: 15,102,529
Trainable params: 15,102,529
@@ -375,26 +374,26 @@ Non-trainable params: 0
_________________________________________________________________
```
-基于这些代码的架构,我们的 CNN 模型有三个卷积和一个池化层,跟随两个致密层,以及用于正则化的丢失。让我们训练我们的模型。
+基于这些代码的架构,我们的 CNN 模型有三个卷积和一个池化层,其后是两个致密层,以及用于正则化的失活。让我们训练我们的模型。
```
import datetime
-logdir = os.path.join('/home/dipanzan_sarkar/projects/tensorboard_logs',
-datetime.datetime.now().strftime("%Y%m%d-%H%M%S"))
+logdir = os.path.join('/home/dipanzan_sarkar/projects/tensorboard_logs',
+ datetime.datetime.now().strftime("%Y%m%d-%H%M%S"))
tensorboard_callback = tf.keras.callbacks.TensorBoard(logdir, histogram_freq=1)
reduce_lr = tf.keras.callbacks.ReduceLROnPlateau(monitor='val_loss', factor=0.5,
-patience=2, min_lr=0.000001)
+ patience=2, min_lr=0.000001)
callbacks = [reduce_lr, tensorboard_callback]
-history = model.fit(x=train_imgs_scaled, y=train_labels_enc,
-batch_size=BATCH_SIZE,
-epochs=EPOCHS,
-validation_data=(val_imgs_scaled, val_labels_enc),
-callbacks=callbacks,
-verbose=1)
-
+history = model.fit(x=train_imgs_scaled, y=train_labels_enc,
+ batch_size=BATCH_SIZE,
+ epochs=EPOCHS,
+ validation_data=(val_imgs_scaled, val_labels_enc),
+ callbacks=callbacks,
+ verbose=1)
+
# Output
Train on 17361 samples, validate on 1929 samples
@@ -439,57 +438,53 @@ l2 = ax2.legend(loc="best")
![Learning curves for basic CNN][17]
-基础 CNN 学习曲线
-
-我们可以看在在第五个历元,情况并没有改善很多。让我们保存这个模型用于将来的评估。
+*基础 CNN 学习曲线*
+我们可以看在在第五个纪元,情况并没有改善很多。让我们保存这个模型用于将来的评估。
```
-`model.save('basic_cnn.h5')`
+model.save('basic_cnn.h5')
```
#### 深度迁移学习
-就像人类有与生俱来的能力在不同任务间传输知识,迁移学习允许我们利用从以前任务学到的知识用到新的任务,相关的任务,甚至在机器学习或深度学习的上下文中。如果想深入探究迁移学习,你应该看我的文章“[一个易于理解与现实应用一起学习深度学习中的迁移学习的指导实践][18]”和我的书[ Python 迁移学习实践][19]。
+就像人类有与生俱来在不同任务间传输知识的能力一样,迁移学习允许我们利用从以前任务学到的知识用到新的相关的任务,即使在机器学习或深度学习的情况下也是如此。如果想深入探究迁移学习,你应该看我的文章“[一个易于理解与现实应用一起学习深度学习中的迁移学习的指导实践][18]”和我的书《[Python 迁移学习实践][19]》。
![深度迁移学习的想法][20]
在这篇实践中我们想要探索的想法是:
-> 在我们的问题上下文中,我们能够利用一个预训练深度学习模型(在大数据集上训练的,像 ImageNet)通过应用和迁移知识来解决疟疾检测的问题吗?
+> 在我们的问题背景下,我们能够利用一个预训练深度学习模型(在大数据集上训练的,像 ImageNet)通过应用和迁移知识来解决疟疾检测的问题吗?
-我们将应用两个深度迁移学习的最流行的策略。
+我们将应用两个最流行的深度迁移学习策略。
* 预训练模型作为特征提取器
* 微调的预训练模型
-
-
-我们将使用预训练的 VGG-19 深度训练模型,由剑桥大学的视觉几何组(VGG)开发,作为我们的实验。一个像 VGG-19 的预训练模型在一个大的数据集上使用了很多不同的图像分类训练([Imagenet][21])。因此,这个模型应该已经学习到了鲁棒的特征层级结构,相对于你的 CNN 模型学到的特征,是空间不变的,转动不变的,平移不变的。因此,这个模型,已经从百万幅图片中学习到了一个好的特征显示,对于像疟疾检测这样的计算机视觉问题,可以作为一个好的合适新图像的特征提取器。在我们的问题中释放迁移学习的能力之前,让我们先讨论 VGG-19 模型。
+我们将使用预训练的 VGG-19 深度训练模型(由剑桥大学的视觉几何组(VGG)开发)进行我们的实验。像 VGG-19 这样的预训练模型是在一个大的数据集([Imagenet][21])上使用了很多不同的图像分类训练的。因此,这个模型应该已经学习到了健壮的特征层级结构,相对于你的 CNN 模型学到的特征,是空间不变的、转动不变的、平移不变的。因此,这个模型,已经从百万幅图片中学习到了一个好的特征显示,对于像疟疾检测这样的计算机视觉问题,可以作为一个好的合适新图像的特征提取器。在我们的问题中发挥迁移学习的能力之前,让我们先讨论 VGG-19 模型。
##### 理解 VGG-19 模型
-VGG-19 模型是一个构建在 ImageNet 数据库之上的 19 层(卷积和全连接的)的深度学习网络,该数据库为了图像识别和分类的目的而开发。该模型由 Karen Simonyan 和 Andrew Zisserman 构建,在它们的论文”[大规模图像识别的非常深的卷积网络][22]“中描述。VGG-19 的架构模型是:
+VGG-19 模型是一个构建在 ImageNet 数据库之上的 19 层(卷积和全连接的)的深度学习网络,ImageNet 数据库为了图像识别和分类的目的而开发。该模型是由 Karen Simonyan 和 Andrew Zisserman 构建的,在他们的论文“[大规模图像识别的非常深的卷积网络][22]”中进行了描述。VGG-19 的架构模型是:
![VGG-19 模型架构][23]
-你可以看到我们总共有 16 个使用 3x3 卷积过滤器的卷积层,与最大的池化层来下采样,和由 4096 个单元组成的两个全连接的隐藏层,每个隐藏层之后跟随一个由 1000 个单元组成的致密层,每个单元代表 ImageNet 数据库中的一个分类。我们不需要最后三层,因为我们将使用我们自己的全连接致密层来预测疟疾。我们更关心前五块,因此我们可以利用 VGG 模型作为一个有效的特征提取器。
+你可以看到我们总共有 16 个使用 3x3 卷积过滤器的卷积层,与最大的池化层来下采样,和由 4096 个单元组成的两个全连接的隐藏层,每个隐藏层之后跟随一个由 1000 个单元组成的致密层,每个单元代表 ImageNet 数据库中的一个分类。我们不需要最后三层,因为我们将使用我们自己的全连接致密层来预测疟疾。我们更关心前五个块,因此我们可以利用 VGG 模型作为一个有效的特征提取器。
-我们将使用模型之一作为一个简单的特征提取器通过冻结五个卷积块的方式来确保它们的位权在每个时期后不会更新。对于最后一个模型,我们会应用微调到 VGG 模型,我们会解冻最后两个块(第 4 和第 5)因此当我们训练我们的模型时,它们的位权在每个时期(每批数据)被更新。
+我们将使用模型之一作为一个简单的特征提取器,通过冻结五个卷积块的方式来确保它们的位权在每个纪元后不会更新。对于最后一个模型,我们会对 VGG 模型进行微调,我们会解冻最后两个块(第 4 和第 5)因此当我们训练我们的模型时,它们的位权在每个时期(每批数据)被更新。
#### 模型 2:预训练的模型作为一个特征提取器
-为了构建这个模型,我们将利用 TensorFlow 载入 VGG-19 模型并且冻结卷积块因此我们用够将他们用作特征提取器。我们插入我们自己的致密层在末尾来执行分类任务。
-
+为了构建这个模型,我们将利用 TensorFlow 载入 VGG-19 模型并冻结卷积块,因此我们能够将它们用作特征提取器。我们在末尾插入我们自己的致密层来执行分类任务。
```
-vgg = tf.keras.applications.vgg19.VGG19(include_top=False, weights='imagenet',
-input_shape=INPUT_SHAPE)
+vgg = tf.keras.applications.vgg19.VGG19(include_top=False, weights='imagenet',
+ input_shape=INPUT_SHAPE)
vgg.trainable = False
# Freeze the layers
for layer in vgg.layers:
-layer.trainable = False
-
+ layer.trainable = False
+
base_vgg = vgg
base_out = base_vgg.output
pool_out = tf.keras.layers.Flatten()(base_out)
@@ -502,37 +497,38 @@ out = tf.keras.layers.Dense(1, activation='sigmoid')(drop2)
model = tf.keras.Model(inputs=base_vgg.input, outputs=out)
model.compile(optimizer=tf.keras.optimizers.RMSprop(lr=1e-4),
-loss='binary_crossentropy',
-metrics=['accuracy'])
+ loss='binary_crossentropy',
+ metrics=['accuracy'])
model.summary()
+
# Output
Model: "model_1"
_________________________________________________________________
-Layer (type) Output Shape Param #
+Layer (type) Output Shape Param #
=================================================================
-input_2 (InputLayer) [(None, 125, 125, 3)] 0
+input_2 (InputLayer) [(None, 125, 125, 3)] 0
_________________________________________________________________
-block1_conv1 (Conv2D) (None, 125, 125, 64) 1792
+block1_conv1 (Conv2D) (None, 125, 125, 64) 1792
_________________________________________________________________
-block1_conv2 (Conv2D) (None, 125, 125, 64) 36928
+block1_conv2 (Conv2D) (None, 125, 125, 64) 36928
_________________________________________________________________
...
...
_________________________________________________________________
-block5_pool (MaxPooling2D) (None, 3, 3, 512) 0
+block5_pool (MaxPooling2D) (None, 3, 3, 512) 0
_________________________________________________________________
-flatten_1 (Flatten) (None, 4608) 0
+flatten_1 (Flatten) (None, 4608) 0
_________________________________________________________________
-dense_3 (Dense) (None, 512) 2359808
+dense_3 (Dense) (None, 512) 2359808
_________________________________________________________________
-dropout_2 (Dropout) (None, 512) 0
+dropout_2 (Dropout) (None, 512) 0
_________________________________________________________________
-dense_4 (Dense) (None, 512) 262656
+dense_4 (Dense) (None, 512) 262656
_________________________________________________________________
-dropout_3 (Dropout) (None, 512) 0
+dropout_3 (Dropout) (None, 512) 0
_________________________________________________________________
-dense_5 (Dense) (None, 1) 513
+dense_5 (Dense) (None, 1) 513
=================================================================
Total params: 22,647,361
Trainable params: 2,622,977
@@ -540,45 +536,42 @@ Non-trainable params: 20,024,384
_________________________________________________________________
```
-输出是很明白的,在我们的模型中我们有了很多层,我们将只利用 VGG-19 模型的冻结层作为特征提取器。你可以使用下列代码来验证我们的模型有多少层是实际训练的,我们的网络中总共存在多少层。
-
+从整个输出可以明显看出,在我们的模型中我们有了很多层,我们将只利用 VGG-19 模型的冻结层作为特征提取器。你可以使用下列代码来验证我们的模型有多少层是实际可训练的,以及我们的网络中总共存在多少层。
```
print("Total Layers:", len(model.layers))
-print("Total trainable layers:",
-sum([1 for l in model.layers if l.trainable]))
+print("Total trainable layers:",
+ sum([1 for l in model.layers if l.trainable]))
# Output
Total Layers: 28
Total trainable layers: 6
```
-我们将使用和我们之前的模型相似的配置和回调来训练我们的模型。参考 [我的 GitHub 仓库][24] 获取训练模型的完整代码。我们观察下列显示模型精确度和损失曲线。
+我们将使用和我们之前的模型相似的配置和回调来训练我们的模型。参考[我的 GitHub 仓库][24]以获取训练模型的完整代码。我们观察下列图表,以显示模型精确度和损失曲线。
![Learning curves for frozen pre-trained CNN][25]
-冻结的预训练的 CNN 的学习曲线
-
-这显示了我们的模型没有像我们的基础 CNN 模型那样过拟合,但是性能有点不如我们的基础的 CNN 模型。让我们保存这个模型用户将来的评估。
+*冻结的预训练的 CNN 的学习曲线*
+这表明我们的模型没有像我们的基础 CNN 模型那样过拟合,但是性能有点不如我们的基础的 CNN 模型。让我们保存这个模型,以备将来的评估。
```
-`model.save('vgg_frozen.h5')`
+model.save('vgg_frozen.h5')
```
#### 模型 3:使用图像增强来微调预训练的模型
-在我们的最后一个模型中,我们微调预定义好的 VGG-19 模型的最后两个块中层的位权。我们同样引入图像增强的概念。图像增强背后的想法和名字一样。我们从训练数据集中载入已存在的图像,并且应用转换操作,例如旋转,裁剪,转换,放大缩小,等等,来产生新的,改变的版本。由于这些随机的转换,我们每次获取到的图像不一样。我们将应用一个在 **tf.keras** 的优秀的工具叫做 **ImageDataGenerator** 来帮助构建图像增强器。
-
+在我们的最后一个模型中,我们将在预定义好的 VGG-19 模型的最后两个块中微调层的位权。我们同样引入了图像增强的概念。图像增强背后的想法和其名字一样。我们从训练数据集中载入现有图像,并且应用转换操作,例如旋转、裁剪、转换、放大缩小等等,来产生新的、改变过的版本。由于这些随机转换,我们每次获取到的图像不一样。我们将应用 tf.keras 中的一个名为 ImageDataGenerator 的优秀工具来帮助构建图像增强器。
```
train_datagen = tf.keras.preprocessing.image.ImageDataGenerator(rescale=1./255,
-zoom_range=0.05,
-rotation_range=25,
-width_shift_range=0.05,
-height_shift_range=0.05,
-shear_range=0.05, horizontal_flip=True,
-fill_mode='nearest')
+ zoom_range=0.05,
+ rotation_range=25,
+ width_shift_range=0.05,
+ height_shift_range=0.05,
+ shear_range=0.05, horizontal_flip=True,
+ fill_mode='nearest')
val_datagen = tf.keras.preprocessing.image.ImageDataGenerator(rescale=1./255)
@@ -587,13 +580,12 @@ train_generator = train_datagen.flow(train_data, train_labels_enc, batch_size=BA
val_generator = val_datagen.flow(val_data, val_labels_enc, batch_size=BATCH_SIZE, shuffle=False)
```
-我们不会应用任何转换在我们的验证数据集上(除非是调整大小,它是强制性适应的)因为我们将在每个时期来评估我们的模型性能。对于在传输学习上下文中的图像增强的详细解释,请自由查看我们上述引用的[文章][18]。让我们从一批图像增强转换中查看一些样本结果。
-
+我们不会对我们的验证数据集应用任何转换(除非是调整大小,因为这是必须的),因为我们将使用它评估每个纪元的模型性能。对于在传输学习环境中的图像增强的详细解释,请随时查看我上面引用的[文章][18]。让我们从一批图像增强转换中查看一些样本结果。
```
img_id = 0
sample_generator = train_datagen.flow(train_data[img_id:img_id+1], train_labels[img_id:img_id+1],
-batch_size=1)
+ batch_size=1)
sample = [next(sample_generator) for i in range(0,5)]
fig, ax = plt.subplots(1,5, figsize=(16, 6))
print('Labels:', [item[1][0] for item in sample])
@@ -602,24 +594,23 @@ l = [ax[i].imshow(sample[i][0][0]) for i in range(0,5)]
![Sample augmented images][26]
-你可以清晰的看到与之前的输出中我们图像的轻微变化。我们现在构建我们的学习模型,确保 VGG-19 模型的最后两块是可以训练的。
-
+你可以清晰的看到与之前的输出的我们图像的轻微变化。我们现在构建我们的学习模型,确保 VGG-19 模型的最后两块是可以训练的。
```
-vgg = tf.keras.applications.vgg19.VGG19(include_top=False, weights='imagenet',
-input_shape=INPUT_SHAPE)
+vgg = tf.keras.applications.vgg19.VGG19(include_top=False, weights='imagenet',
+ input_shape=INPUT_SHAPE)
# Freeze the layers
vgg.trainable = True
set_trainable = False
for layer in vgg.layers:
-if layer.name in ['block5_conv1', 'block4_conv1']:
-set_trainable = True
-if set_trainable:
-layer.trainable = True
-else:
-layer.trainable = False
-
+ if layer.name in ['block5_conv1', 'block4_conv1']:
+ set_trainable = True
+ if set_trainable:
+ layer.trainable = True
+ else:
+ layer.trainable = False
+
base_vgg = vgg
base_out = base_vgg.output
pool_out = tf.keras.layers.Flatten()(base_out)
@@ -632,31 +623,32 @@ out = tf.keras.layers.Dense(1, activation='sigmoid')(drop2)
model = tf.keras.Model(inputs=base_vgg.input, outputs=out)
model.compile(optimizer=tf.keras.optimizers.RMSprop(lr=1e-5),
-loss='binary_crossentropy',
-metrics=['accuracy'])
+ loss='binary_crossentropy',
+ metrics=['accuracy'])
print("Total Layers:", len(model.layers))
print("Total trainable layers:", sum([1 for l in model.layers if l.trainable]))
+
# Output
Total Layers: 28
Total trainable layers: 16
```
-在我们的模型中我们降低了学习率,因为我们微调的时候不想在预训练的数据集上做大的位权更新。模型的训练过程可能有轻微的不同,因为我们使用了数据生成器,因此我们应用了 **fit_generator(...)** 函数。
-
+在我们的模型中我们降低了学习率,因为我们不想在微调的时候对预训练的层做大的位权更新。模型的训练过程可能有轻微的不同,因为我们使用了数据生成器,因此我们将应用 `fit_generator(...)` 函数。
```
tensorboard_callback = tf.keras.callbacks.TensorBoard(logdir, histogram_freq=1)
reduce_lr = tf.keras.callbacks.ReduceLROnPlateau(monitor='val_loss', factor=0.5,
-patience=2, min_lr=0.000001)
+ patience=2, min_lr=0.000001)
callbacks = [reduce_lr, tensorboard_callback]
train_steps_per_epoch = train_generator.n // train_generator.batch_size
val_steps_per_epoch = val_generator.n // val_generator.batch_size
history = model.fit_generator(train_generator, steps_per_epoch=train_steps_per_epoch, epochs=EPOCHS,
-validation_data=val_generator, validation_steps=val_steps_per_epoch,
-verbose=1)
+ validation_data=val_generator, validation_steps=val_steps_per_epoch,
+ verbose=1)
+
# Output
Epoch 1/25
@@ -675,21 +667,20 @@ Epoch 25/25
![Learning curves for fine-tuned pre-trained CNN][27]
-微调预训练的 CNN 的学习曲线
+*微调过的预训练 CNN 的学习曲线*
让我们保存这个模型,因此我们能够在测试集上使用。
```
-`model.save('vgg_finetuned.h5')`
+model.save('vgg_finetuned.h5')
```
-这完成了我们的模型训练阶段。我们准备好在测试集上测试我们模型的性能。
+这就完成了我们的模型训练阶段。现在我们准备好了在测试集上测试我们模型的性能。
### 深度学习模型性能评估
-我们将评估我们在训练阶段构建的三个模型,通过在我们的测试集上做预测,因为仅仅验证是不够的!我们同样构建了一个检测工具模块叫做 **model_evaluation_utils**,我们可以使用相关分类指标用来评估使用我们深度学习模型的性能。第一步是测量我们的数据集。
-
+我们将通过在我们的测试集上做预测来评估我们在训练阶段构建的三个模型,因为仅仅验证是不够的!我们同样构建了一个检测工具模块叫做 `model_evaluation_utils`,我们可以使用相关分类指标用来评估使用我们深度学习模型的性能。第一步是扩展我们的数据集。
```
test_imgs_scaled = test_data / 255.
@@ -701,7 +692,6 @@ test_imgs_scaled.shape, test_labels.shape
下一步包括载入我们保存的深度学习模型,在测试集上预测。
-
```
# Load Saved Deep Learning Models
basic_cnn = tf.keras.models.load_model('./basic_cnn.h5')
@@ -713,16 +703,15 @@ basic_cnn_preds = basic_cnn.predict(test_imgs_scaled, batch_size=512)
vgg_frz_preds = vgg_frz.predict(test_imgs_scaled, batch_size=512)
vgg_ft_preds = vgg_ft.predict(test_imgs_scaled, batch_size=512)
-basic_cnn_pred_labels = le.inverse_transform([1 if pred > 0.5 else 0
-for pred in basic_cnn_preds.ravel()])
-vgg_frz_pred_labels = le.inverse_transform([1 if pred > 0.5 else 0
-for pred in vgg_frz_preds.ravel()])
-vgg_ft_pred_labels = le.inverse_transform([1 if pred > 0.5 else 0
-for pred in vgg_ft_preds.ravel()])
+basic_cnn_pred_labels = le.inverse_transform([1 if pred > 0.5 else 0
+ for pred in basic_cnn_preds.ravel()])
+vgg_frz_pred_labels = le.inverse_transform([1 if pred > 0.5 else 0
+ for pred in vgg_frz_preds.ravel()])
+vgg_ft_pred_labels = le.inverse_transform([1 if pred > 0.5 else 0
+ for pred in vgg_ft_preds.ravel()])
```
-下一步是应用我们的 **model_evaluation_utils** 模块根据相应分类指标来检查每个模块的性能。
-
+下一步是应用我们的 `model_evaluation_utils` 模块根据相应分类指标来检查每个模块的性能。
```
import model_evaluation_utils as meu
@@ -732,30 +721,30 @@ basic_cnn_metrics = meu.get_metrics(true_labels=test_labels, predicted_labels=ba
vgg_frz_metrics = meu.get_metrics(true_labels=test_labels, predicted_labels=vgg_frz_pred_labels)
vgg_ft_metrics = meu.get_metrics(true_labels=test_labels, predicted_labels=vgg_ft_pred_labels)
-pd.DataFrame([basic_cnn_metrics, vgg_frz_metrics, vgg_ft_metrics],
-index=['Basic CNN', 'VGG-19 Frozen', 'VGG-19 Fine-tuned'])
+pd.DataFrame([basic_cnn_metrics, vgg_frz_metrics, vgg_ft_metrics],
+ index=['Basic CNN', 'VGG-19 Frozen', 'VGG-19 Fine-tuned'])
```
![Model accuracy][28]
-看起来我们的第三个模型在我们的测试集上执行的最好,给出了一个模型精确性为 96% 的 F1得分,比起上述我们早期引用的研究论文和文章中提及的复杂的模型是相当好的。
+看起来我们的第三个模型在我们的测试集上执行的最好,给出了一个模型精确性为 96% 的 F1 得分,这非常好,与我们之前提到的研究论文和文章中的更复杂的模型相当。
### 总结
-疟疾检测不是一个简单的程序,全球的合格的人员的可获得性在样例诊断和治疗当中是一个严重的问题。我们看到一个关于疟疾的有趣的真实世界的医学影像案例。易于构建的,开源的技术利用 AI 在检测疟疾方面可以给我们最先进的精确性,因此允许 AI 对社会是有益的。
+疟疾检测不是一个简单的过程,全球的合格人员的不足在病例诊断和治疗当中是一个严重的问题。我们研究了一个关于疟疾的有趣的真实世界的医学影像案例。利用 AI 的、易于构建的、开源的技术在检测疟疾方面可以为我们提供最先进的精确性,因此使 AI 具有社会效益。
-我鼓励你检查这片文章中提到的文章和研究论文,没有它们,我就不能形成概念并写出来。如果你对运行和采纳这些技术感兴趣,本篇文章所有的代码都可以在[我的 GitHub 仓库][24]获得。记得从[官方网站][11]下载数据。
+我鼓励你查看这篇文章中提到的文章和研究论文,没有它们,我就不能形成概念并写出来。如果你对运行和采纳这些技术感兴趣,本篇文章所有的代码都可以在[我的 GitHub 仓库][24]获得。记得从[官方网站][11]下载数据。
-让我们希望在健康医疗方面更多的采纳开源的 AI 能力,使它在世界范围内变得便宜些,易用些。
+让我们希望在健康医疗方面更多的采纳开源的 AI 能力,使它在世界范围内变得更便宜、更易用。
--------------------------------------------------------------------------------
via: https://opensource.com/article/19/4/detecting-malaria-deep-learning
-作者:[Dipanjan (DJ) Sarkar (Red Hat)][a]
+作者:[Dipanjan (DJ) Sarkar][a]
选题:[lujun9972][b]
译者:[warmfrog](https://github.com/warmfrog)
-校对:[校对者ID](https://github.com/校对者ID)
+校对:[wxy](https://github.com/wxy)
本文由 [LCTT](https://github.com/LCTT/TranslateProject) 原创编译,[Linux中国](https://linux.cn/) 荣誉推出
diff --git a/published/201905/20190416 Inter-process communication in Linux- Using pipes and message queues.md b/published/201905/20190416 Inter-process communication in Linux- Using pipes and message queues.md
new file mode 100644
index 0000000000..714f451e2e
--- /dev/null
+++ b/published/201905/20190416 Inter-process communication in Linux- Using pipes and message queues.md
@@ -0,0 +1,578 @@
+[#]: collector: (lujun9972)
+[#]: translator: (FSSlc)
+[#]: reviewer: (wxy)
+[#]: publisher: (wxy)
+[#]: url: (https://linux.cn/article-10845-1.html)
+[#]: subject: (Inter-process communication in Linux: Using pipes and message queues)
+[#]: via: (https://opensource.com/article/19/4/interprocess-communication-linux-channels)
+[#]: author: (Marty Kalin https://opensource.com/users/mkalindepauledu)
+
+Linux 下的进程间通信:使用管道和消息队列
+======
+
+> 学习在 Linux 中进程是如何与其他进程进行同步的。
+
+![Chat bubbles][1]
+
+本篇是 Linux 下[进程间通信][2](IPC)系列的第二篇文章。[第一篇文章][3] 聚焦于通过共享文件和共享内存段这样的共享存储来进行 IPC。这篇文件的重点将转向管道,它是连接需要通信的进程之间的通道。管道拥有一个*写端*用于写入字节数据,还有一个*读端*用于按照先入先出的顺序读入这些字节数据。而这些字节数据可能代表任何东西:数字、员工记录、数字电影等等。
+
+管道有两种类型,命名管道和无名管道,都可以交互式的在命令行或程序中使用它们;相关的例子在下面展示。这篇文章也将介绍内存队列,尽管它们有些过时了,但它们不应该受这样的待遇。
+
+在本系列的第一篇文章中的示例代码承认了在 IPC 中可能受到竞争条件(不管是基于文件的还是基于内存的)的威胁。自然地我们也会考虑基于管道的 IPC 的安全并发问题,这个也将在本文中提及。针对管道和内存队列的例子将会使用 POSIX 推荐使用的 API,POSIX 的一个核心目标就是线程安全。
+
+请查看一些 [mq_open 函数的 man 页][4],这个函数属于内存队列的 API。这个 man 页中有关 [特性][5] 的章节带有一个小表格:
+
+接口 | 特性 | 值
+---|---|---
+`mq_open()` | 线程安全 | MT-Safe
+
+上面的 MT-Safe(MT 指的是多线程)意味着 `mq_open` 函数是线程安全的,进而暗示是进程安全的:一个进程的执行和它的一个线程执行的过程类似,假如竞争条件不会发生在处于*相同*进程的线程中,那么这样的条件也不会发生在处于不同进程的线程中。MT-Safe 特性保证了调用 `mq_open` 时不会出现竞争条件。一般来说,基于通道的 IPC 是并发安全的,尽管在下面例子中会出现一个有关警告的注意事项。
+
+### 无名管道
+
+首先让我们通过一个特意构造的命令行例子来展示无名管道是如何工作的。在所有的现代系统中,符号 `|` 在命令行中都代表一个无名管道。假设我们的命令行提示符为 `%`,接下来考虑下面的命令:
+
+```shell
+## 写入方在 | 左边,读取方在右边
+% sleep 5 | echo "Hello, world!"
+```
+
+`sleep` 和 `echo` 程序以不同的进程执行,无名管道允许它们进行通信。但是上面的例子被特意设计为没有通信发生。问候语 “Hello, world!” 出现在屏幕中,然后过了 5 秒后,命令行返回,暗示 `sleep` 和 `echo` 进程都已经结束了。这期间发生了什么呢?
+
+在命令行中的竖线 `|` 的语法中,左边的进程(`sleep`)是写入方,右边的进程(`echo`)为读取方。默认情况下,读取方将会阻塞,直到从通道中能够读取到字节数据,而写入方在写完它的字节数据后,将发送 流已终止的标志。(即便写入方过早终止了,一个流已终止的标志还是会发给读取方。)无名管道将保持到写入方和读取方都停止的那个时刻。
+
+在上面的例子中,`sleep` 进程并没有向通道写入任何的字节数据,但在 5 秒后就终止了,这时将向通道发送一个流已终止的标志。与此同时,`echo` 进程立即向标准输出(屏幕)写入问候语,因为这个进程并不从通道中读入任何字节,所以它并没有等待。一旦 `sleep` 和 `echo` 进程都终止了,不会再用作通信的无名管道将会消失然后返回命令行提示符。
+
+下面这个更加实用的示例将使用两个无名管道。我们假定文件 `test.dat` 的内容如下:
+
+```
+this
+is
+the
+way
+the
+world
+ends
+```
+
+下面的命令:
+
+```
+% cat test.dat | sort | uniq
+```
+
+会将 `cat`(连接的缩写)进程的输出通过管道传给 `sort` 进程以生成排序后的输出,然后将排序后的输出通过管道传给 `uniq` 进程以消除重复的记录(在本例中,会将两次出现的 “the” 缩减为一个):
+
+```
+ends
+is
+the
+this
+way
+world
+```
+
+下面展示的情景展示的是一个带有两个进程的程序通过一个无名管道通信来进行通信。
+
+#### 示例 1. 两个进程通过一个无名管道来进行通信
+
+```c
+#include /* wait */
+#include
+#include /* exit functions */
+#include /* read, write, pipe, _exit */
+#include
+
+#define ReadEnd 0
+#define WriteEnd 1
+
+void report_and_exit(const char* msg) {
+ perror(msg);
+ exit(-1); /** failure **/
+}
+
+int main() {
+ int pipeFDs[2]; /* two file descriptors */
+ char buf; /* 1-byte buffer */
+ const char* msg = "Nature's first green is gold\n"; /* bytes to write */
+
+ if (pipe(pipeFDs) < 0) report_and_exit("pipeFD");
+ pid_t cpid = fork(); /* fork a child process */
+ if (cpid < 0) report_and_exit("fork"); /* check for failure */
+
+ if (0 == cpid) { /*** child ***/ /* child process */
+ close(pipeFDs[WriteEnd]); /* child reads, doesn't write */
+
+ while (read(pipeFDs[ReadEnd], &buf, 1) > 0) /* read until end of byte stream */
+ write(STDOUT_FILENO, &buf, sizeof(buf)); /* echo to the standard output */
+
+ close(pipeFDs[ReadEnd]); /* close the ReadEnd: all done */
+ _exit(0); /* exit and notify parent at once */
+ }
+ else { /*** parent ***/
+ close(pipeFDs[ReadEnd]); /* parent writes, doesn't read */
+
+ write(pipeFDs[WriteEnd], msg, strlen(msg)); /* write the bytes to the pipe */
+ close(pipeFDs[WriteEnd]); /* done writing: generate eof */
+
+ wait(NULL); /* wait for child to exit */
+ exit(0); /* exit normally */
+ }
+ return 0;
+}
+```
+
+上面名为 `pipeUN` 的程序使用系统函数 `fork` 来创建一个进程。尽管这个程序只有一个单一的源文件,在它正确执行的情况下将会发生多进程的情况。
+
+> 下面的内容是对库函数 `fork` 如何工作的一个简要回顾:
+
+> * `fork` 函数由*父*进程调用,在失败时返回 `-1` 给父进程。在 `pipeUN` 这个例子中,相应的调用是:
+
+> ```c
+pid_t cpid = fork(); /* called in parent */
+```
+
+> 函数调用后的返回值也被保存下来了。在这个例子中,保存在整数类型 `pid_t` 的变量 `cpid` 中。(每个进程有它自己的*进程 ID*,这是一个非负的整数,用来标记进程)。复刻一个新的进程可能会因为多种原因而失败,包括*进程表*满了的原因,这个结构由系统维持,以此来追踪进程状态。明确地说,僵尸进程假如没有被处理掉,将可能引起进程表被填满的错误。
+> * 假如 `fork` 调用成功,则它将创建一个新的子进程,向父进程返回一个值,向子进程返回另外的一个值。在调用 `fork` 后父进程和子进程都将执行相同的代码。(子进程继承了到此为止父进程中声明的所有变量的拷贝),特别地,一次成功的 `fork` 调用将返回如下的东西:
+> * 向子进程返回 `0`
+> * 向父进程返回子进程的进程 ID
+> * 在一次成功的 `fork` 调用后,一个 `if`/`else` 或等价的结构将会被用来隔离针对父进程和子进程的代码。在这个例子中,相应的声明为:
+
+> ```c
+if (0 == cpid) { /*** child ***/
+...
+}
+else { /*** parent ***/
+...
+}
+```
+
+假如成功地复刻出了一个子进程,`pipeUN` 程序将像下面这样去执行。在一个整数的数列里:
+
+```c
+int pipeFDs[2]; /* two file descriptors */
+```
+
+来保存两个文件描述符,一个用来向管道中写入,另一个从管道中写入。(数组元素 `pipeFDs[0]` 是读端的文件描述符,元素 `pipeFDs[1]` 是写端的文件描述符。)在调用 `fork` 之前,对系统 `pipe` 函数的成功调用,将立刻使得这个数组获得两个文件描述符:
+
+```c
+if (pipe(pipeFDs) < 0) report_and_exit("pipeFD");
+```
+
+父进程和子进程现在都有了文件描述符的副本。但*分离关注点*模式意味着每个进程恰好只需要一个描述符。在这个例子中,父进程负责写入,而子进程负责读取,尽管这样的角色分配可以反过来。在 `if` 子句中的第一个语句将用于关闭管道的读端:
+
+```c
+close(pipeFDs[WriteEnd]); /* called in child code */
+```
+
+在父进程中的 `else` 子句将会关闭管道的读端:
+
+```c
+close(pipeFDs[ReadEnd]); /* called in parent code */
+```
+
+然后父进程将向无名管道中写入某些字节数据(ASCII 代码),子进程读取这些数据,然后向标准输出中回放它们。
+
+在这个程序中还需要澄清的一点是在父进程代码中的 `wait` 函数。一旦被创建后,子进程很大程度上独立于它的父进程,正如简短的 `pipeUN` 程序所展示的那样。子进程可以执行任意的代码,而它们可能与父进程完全没有关系。但是,假如当子进程终止时,系统将会通过一个信号来通知父进程。
+
+要是父进程在子进程之前终止又该如何呢?在这种情形下,除非采取了预防措施,子进程将会变成在进程表中的一个*僵尸*进程。预防措施有两大类型:第一种是让父进程去通知系统,告诉系统它对子进程的终止没有任何兴趣:
+
+```c
+signal(SIGCHLD, SIG_IGN); /* in parent: ignore notification */
+```
+
+第二种方法是在子进程终止时,让父进程执行一个 `wait`。这样就确保了父进程可以独立于子进程而存在。在 `pipeUN` 程序中使用了第二种方法,其中父进程的代码使用的是下面的调用:
+
+```c
+wait(NULL); /* called in parent */
+```
+
+这个对 `wait` 的调用意味着*一直等待直到任意一个子进程的终止发生*,因此在 `pipeUN` 程序中,只有一个子进程。(其中的 `NULL` 参数可以被替换为一个保存有子程序退出状态的整数变量的地址。)对于更细粒度的控制,还可以使用更灵活的 `waitpid` 函数,例如特别指定多个子进程中的某一个。
+
+`pipeUN` 将会采取另一个预防措施。当父进程结束了等待,父进程将会调用常规的 `exit` 函数去退出。对应的,子进程将会调用 `_exit` 变种来退出,这类变种将快速跟踪终止相关的通知。在效果上,子进程会告诉系统立刻去通知父进程它的这个子进程已经终止了。
+
+假如两个进程向相同的无名管道中写入内容,字节数据会交错吗?例如,假如进程 P1 向管道写入内容:
+
+```
+foo bar
+```
+
+同时进程 P2 并发地写入:
+
+```
+baz baz
+```
+
+到相同的管道,最后的结果似乎是管道中的内容将会是任意错乱的,例如像这样:
+
+```
+baz foo baz bar
+```
+
+只要没有写入超过 `PIPE_BUF` 字节,POSIX 标准就能确保写入不会交错。在 Linux 系统中, `PIPE_BUF` 的大小是 4096 字节。对于管道我更喜欢只有一个写入方和一个读取方,从而绕过这个问题。
+
+### 命名管道
+
+无名管道没有备份文件:系统将维持一个内存缓存来将字节数据从写方传给读方。一旦写方和读方终止,这个缓存将会被回收,进而无名管道消失。相反的,命名管道有备份文件和一个不同的 API。
+
+下面让我们通过另一个命令行示例来了解命名管道的要点。下面是具体的步骤:
+
+* 开启两个终端。这两个终端的工作目录应该相同。
+* 在其中一个终端中,键入下面的两个命令(命令行提示符仍然是 `%`,我的注释以 `##` 打头。):
+
+ ```shell
+% mkfifo tester ## 创建一个备份文件,名为 tester
+% cat tester ## 将管道的内容输出到 stdout
+```
+
+ 在最开始,没有任何东西会出现在终端中,因为到现在为止没有在命名管道中写入任何东西。
+* 在第二个终端中输入下面的命令:
+
+ ```shell
+% cat > tester ## redirect keyboard input to the pipe
+hello, world! ## then hit Return key
+bye, bye ## ditto
+ ## terminate session with a Control-C
+```
+
+ 无论在这个终端中输入什么,它都会在另一个终端中显示出来。一旦键入 `Ctrl+C`,就会回到正常的命令行提示符,因为管道已经被关闭了。
+* 通过移除实现命名管道的文件来进行清理:
+
+ ```shell
+% unlink tester
+```
+
+正如 `mkfifo` 程序的名字所暗示的那样,命名管道也被叫做 FIFO,因为第一个进入的字节,就会第一个出,其他的类似。有一个名为 `mkfifo` 的库函数,用它可以在程序中创建一个命名管道,它将在下一个示例中被用到,该示例由两个进程组成:一个向命名管道写入,而另一个从该管道读取。
+
+#### 示例 2. fifoWriter 程序
+
+```c
+#include
+#include
+#include
+#include
+#include
+#include
+#include
+
+#define MaxLoops 12000 /* outer loop */
+#define ChunkSize 16 /* how many written at a time */
+#define IntsPerChunk 4 /* four 4-byte ints per chunk */
+#define MaxZs 250 /* max microseconds to sleep */
+
+int main() {
+ const char* pipeName = "./fifoChannel";
+ mkfifo(pipeName, 0666); /* read/write for user/group/others */
+ int fd = open(pipeName, O_CREAT | O_WRONLY); /* open as write-only */
+ if (fd < 0) return -1; /* can't go on */
+
+ int i;
+ for (i = 0; i < MaxLoops; i++) { /* write MaxWrites times */
+ int j;
+ for (j = 0; j < ChunkSize; j++) { /* each time, write ChunkSize bytes */
+ int k;
+ int chunk[IntsPerChunk];
+ for (k = 0; k < IntsPerChunk; k++)
+ chunk[k] = rand();
+ write(fd, chunk, sizeof(chunk));
+ }
+ usleep((rand() % MaxZs) + 1); /* pause a bit for realism */
+ }
+
+ close(fd); /* close pipe: generates an end-of-stream marker */
+ unlink(pipeName); /* unlink from the implementing file */
+ printf("%i ints sent to the pipe.\n", MaxLoops * ChunkSize * IntsPerChunk);
+
+ return 0;
+}
+```
+
+上面的 `fifoWriter` 程序可以被总结为如下:
+
+* 首先程序创建了一个命名管道用来写入数据:
+
+ ```c
+mkfifo(pipeName, 0666); /* read/write perms for user/group/others */
+int fd = open(pipeName, O_CREAT | O_WRONLY);
+```
+
+ 其中的 `pipeName` 是备份文件的名字,传递给 `mkfifo` 作为它的第一个参数。接着命名管道通过我们熟悉的 `open` 函数调用被打开,而这个函数将会返回一个文件描述符。
+* 在实现层面上,`fifoWriter` 不会一次性将所有的数据都写入,而是写入一个块,然后休息随机数目的微秒时间,接着再循环往复。总的来说,有 768000 个 4 字节整数值被写入到命名管道中。
+* 在关闭命名管道后,`fifoWriter` 也将使用 `unlink` 取消对该文件的连接。
+
+ ```c
+close(fd); /* close pipe: generates end-of-stream marker */
+unlink(pipeName); /* unlink from the implementing file */
+```
+
+ 一旦连接到管道的每个进程都执行了 `unlink` 操作后,系统将回收这些备份文件。在这个例子中,只有两个这样的进程 `fifoWriter` 和 `fifoReader`,它们都做了 `unlink` 操作。
+
+这个两个程序应该在不同终端的相同工作目录中执行。但是 `fifoWriter` 应该在 `fifoReader` 之前被启动,因为需要 `fifoWriter` 去创建管道。然后 `fifoReader` 才能够获取到刚被创建的命名管道。
+
+#### 示例 3. fifoReader 程序
+
+```c
+#include
+#include
+#include
+#include
+#include
+
+unsigned is_prime(unsigned n) { /* not pretty, but efficient */
+ if (n <= 3) return n > 1;
+ if (0 == (n % 2) || 0 == (n % 3)) return 0;
+
+ unsigned i;
+ for (i = 5; (i * i) <= n; i += 6)
+ if (0 == (n % i) || 0 == (n % (i + 2))) return 0;
+
+ return 1; /* found a prime! */
+}
+
+int main() {
+ const char* file = "./fifoChannel";
+ int fd = open(file, O_RDONLY);
+ if (fd < 0) return -1; /* no point in continuing */
+ unsigned count = 0, total = 0, primes_count = 0;
+
+ while (1) {
+ int next;
+ int i;
+
+ ssize_t count = read(fd, &next, sizeof(int));
+ if (0 == count) break; /* end of stream */
+ else if (count == sizeof(int)) { /* read a 4-byte int value */
+ total++;
+ if (is_prime(next)) primes_count++;
+ }
+ }
+
+ close(fd); /* close pipe from read end */
+ unlink(file); /* unlink from the underlying file */
+ printf("Received ints: %u, primes: %u\n", total, primes_count);
+
+ return 0;
+}
+```
+
+上面的 `fifoReader` 的内容可以总结为如下:
+
+* 因为 `fifoWriter` 已经创建了命名管道,所以 `fifoReader` 只需要利用标准的 `open` 调用来通过备份文件来获取到管道中的内容:
+
+ ```c
+const char* file = "./fifoChannel";
+int fd = open(file, O_RDONLY);
+```
+
+ 这个文件的是以只读打开的。
+* 然后这个程序进入一个潜在的无限循环,在每次循环时,尝试读取 4 字节的块。`read` 调用:
+
+ ```c
+ssize_t count = read(fd, &next, sizeof(int));
+```
+
+ 返回 0 来暗示该流的结束。在这种情况下,`fifoReader` 跳出循环,关闭命名管道,并在终止前 `unlink` 备份文件。
+* 在读入 4 字节整数后,`fifoReader` 检查这个数是否为质数。这个操作代表了一个生产级别的读取器可能在接收到的字节数据上执行的逻辑操作。在示例运行中,在接收到的 768000 个整数中有 37682 个质数。
+
+重复运行示例, `fifoReader` 将成功地读取 `fifoWriter` 写入的所有字节。这不是很让人惊讶的。这两个进程在相同的机器上执行,从而可以不用考虑网络相关的问题。命名管道是一个可信且高效的 IPC 机制,因而被广泛使用。
+
+下面是这两个程序的输出,它们在不同的终端中启动,但处于相同的工作目录:
+
+```shell
+% ./fifoWriter
+768000 ints sent to the pipe.
+###
+% ./fifoReader
+Received ints: 768000, primes: 37682
+```
+
+### 消息队列
+
+管道有着严格的先入先出行为:第一个被写入的字节将会第一个被读,第二个写入的字节将第二个被读,以此类推。消息队列可以做出相同的表现,但它又足够灵活,可以使得字节块可以不以先入先出的次序来接收。
+
+正如它的名字所提示的那样,消息队列是一系列的消息,每个消息包含两部分:
+
+* 荷载,一个字节序列(在 C 中是 char)
+* 类型,以一个正整数值的形式给定,类型用来分类消息,为了更灵活的回收
+
+看一下下面对一个消息队列的描述,每个消息由一个整数类型标记:
+
+```
+ +-+ +-+ +-+ +-+
+sender--->|3|--->|2|--->|2|--->|1|--->receiver
+ +-+ +-+ +-+ +-+
+```
+
+在上面展示的 4 个消息中,标记为 1 的是开头,即最接近接收端,然后另个标记为 2 的消息,最后接着一个标记为 3 的消息。假如按照严格的 FIFO 行为执行,消息将会以 1-2-2-3 这样的次序被接收。但是消息队列允许其他收取次序。例如,消息可以被接收方以 3-2-1-2 的次序接收。
+
+`mqueue` 示例包含两个程序,`sender` 将向消息队列中写入数据,而 `receiver` 将从这个队列中读取数据。这两个程序都包含的头文件 `queue.h` 如下所示:
+
+#### 示例 4. 头文件 queue.h
+
+```c
+#define ProjectId 123
+#define PathName "queue.h" /* any existing, accessible file would do */
+#define MsgLen 4
+#define MsgCount 6
+
+typedef struct {
+ long type; /* must be of type long */
+ char payload[MsgLen + 1]; /* bytes in the message */
+} queuedMessage;
+```
+
+上面的头文件定义了一个名为 `queuedMessage` 的结构类型,它带有 `payload`(字节数组)和 `type`(整数)这两个域。该文件也定义了一些符号常数(使用 `#define` 语句),前两个常数被用来生成一个 `key`,而这个 `key` 反过来被用来获取一个消息队列的 ID。`ProjectId` 可以是任何正整数值,而 `PathName` 必须是一个存在的、可访问的文件,在这个示例中,指的是文件 `queue.h`。在 `sender` 和 `receiver` 中,它们都有的设定语句为:
+
+```c
+key_t key = ftok(PathName, ProjectId); /* generate key */
+int qid = msgget(key, 0666 | IPC_CREAT); /* use key to get queue id */
+```
+
+ID `qid` 在效果上是消息队列文件描述符的对应物。
+
+#### 示例 5. sender 程序
+
+```c
+#include
+#include
+#include
+#include
+#include
+#include "queue.h"
+
+void report_and_exit(const char* msg) {
+ perror(msg);
+ exit(-1); /* EXIT_FAILURE */
+}
+
+int main() {
+ key_t key = ftok(PathName, ProjectId);
+ if (key < 0) report_and_exit("couldn't get key...");
+
+ int qid = msgget(key, 0666 | IPC_CREAT);
+ if (qid < 0) report_and_exit("couldn't get queue id...");
+
+ char* payloads[] = {"msg1", "msg2", "msg3", "msg4", "msg5", "msg6"};
+ int types[] = {1, 1, 2, 2, 3, 3}; /* each must be > 0 */
+ int i;
+ for (i = 0; i < MsgCount; i++) {
+ /* build the message */
+ queuedMessage msg;
+ msg.type = types[i];
+ strcpy(msg.payload, payloads[i]);
+
+ /* send the message */
+ msgsnd(qid, &msg, sizeof(msg), IPC_NOWAIT); /* don't block */
+ printf("%s sent as type %i\n", msg.payload, (int) msg.type);
+ }
+ return 0;
+}
+```
+
+上面的 `sender` 程序将发送出 6 个消息,每两个为一个类型:前两个是类型 1,接着的连个是类型 2,最后的两个为类型 3。发送的语句:
+
+```c
+msgsnd(qid, &msg, sizeof(msg), IPC_NOWAIT);
+```
+
+被配置为非阻塞的(`IPC_NOWAIT` 标志),是因为这里的消息体量上都很小。唯一的危险在于一个完整的序列将可能导致发送失败,而这个例子不会。下面的 `receiver` 程序也将使用 `IPC_NOWAIT` 标志来接收消息。
+
+#### 示例 6. receiver 程序
+
+```c
+#include
+#include
+#include
+#include
+#include "queue.h"
+
+void report_and_exit(const char* msg) {
+ perror(msg);
+ exit(-1); /* EXIT_FAILURE */
+}
+
+int main() {
+ key_t key= ftok(PathName, ProjectId); /* key to identify the queue */
+ if (key < 0) report_and_exit("key not gotten...");
+
+ int qid = msgget(key, 0666 | IPC_CREAT); /* access if created already */
+ if (qid < 0) report_and_exit("no access to queue...");
+
+ int types[] = {3, 1, 2, 1, 3, 2}; /* different than in sender */
+ int i;
+ for (i = 0; i < MsgCount; i++) {
+ queuedMessage msg; /* defined in queue.h */
+ if (msgrcv(qid, &msg, sizeof(msg), types[i], MSG_NOERROR | IPC_NOWAIT) < 0)
+ puts("msgrcv trouble...");
+ printf("%s received as type %i\n", msg.payload, (int) msg.type);
+ }
+
+ /** remove the queue **/
+ if (msgctl(qid, IPC_RMID, NULL) < 0) /* NULL = 'no flags' */
+ report_and_exit("trouble removing queue...");
+
+ return 0;
+}
+```
+
+这个 `receiver` 程序不会创建消息队列,尽管 API 尽管建议那样。在 `receiver` 中,对
+
+```c
+int qid = msgget(key, 0666 | IPC_CREAT);
+```
+
+的调用可能因为带有 `IPC_CREAT` 标志而具有误导性,但是这个标志的真实意义是*如果需要就创建,否则直接获取*。`sender` 程序调用 `msgsnd` 来发送消息,而 `receiver` 调用 `msgrcv` 来接收它们。在这个例子中,`sender` 以 1-1-2-2-3-3 的次序发送消息,但 `receiver` 接收它们的次序为 3-1-2-1-3-2,这显示消息队列没有被严格的 FIFO 行为所拘泥:
+
+```shell
+% ./sender
+msg1 sent as type 1
+msg2 sent as type 1
+msg3 sent as type 2
+msg4 sent as type 2
+msg5 sent as type 3
+msg6 sent as type 3
+
+% ./receiver
+msg5 received as type 3
+msg1 received as type 1
+msg3 received as type 2
+msg2 received as type 1
+msg6 received as type 3
+msg4 received as type 2
+```
+
+上面的输出显示 `sender` 和 `receiver` 可以在同一个终端中启动。输出也显示消息队列是持久的,即便 `sender` 进程在完成创建队列、向队列写数据、然后退出的整个过程后,该队列仍然存在。只有在 `receiver` 进程显式地调用 `msgctl` 来移除该队列,这个队列才会消失:
+
+```c
+if (msgctl(qid, IPC_RMID, NULL) < 0) /* remove queue */
+```
+
+### 总结
+
+管道和消息队列的 API 在根本上来说都是单向的:一个进程写,然后另一个进程读。当然还存在双向命名管道的实现,但我认为这个 IPC 机制在它最为简单的时候反而是最佳的。正如前面提到的那样,消息队列已经不大受欢迎了,尽管没有找到什么特别好的原因来解释这个现象;而队列仍然是 IPC 工具箱中的一个工具。这个快速的 IPC 工具箱之旅将以第 3 部分(通过套接字和信号来示例 IPC)来终结。
+
+--------------------------------------------------------------------------------
+
+via: https://opensource.com/article/19/4/interprocess-communication-linux-channels
+
+作者:[Marty Kalin][a]
+选题:[lujun9972][b]
+译者:[FSSlc](https://github.com/FSSlc)
+校对:[wxy](https://github.com/wxy)
+
+本文由 [LCTT](https://github.com/LCTT/TranslateProject) 原创编译,[Linux中国](https://linux.cn/) 荣誉推出
+
+[a]: https://opensource.com/users/mkalindepauledu
+[b]: https://github.com/lujun9972
+[1]: https://opensource.com/sites/default/files/styles/image-full-size/public/lead-images/talk_chat_communication_team.png?itok=CYfZ_gE7 (Chat bubbles)
+[2]: https://en.wikipedia.org/wiki/Inter-process_communication
+[3]: https://linux.cn/article-10826-1.html
+[4]: http://man7.org/linux/man-pages/man2/mq_open.2.html
+[5]: http://man7.org/linux/man-pages/man2/mq_open.2.html#ATTRIBUTES
+[6]: http://www.opengroup.org/onlinepubs/009695399/functions/perror.html
+[7]: http://www.opengroup.org/onlinepubs/009695399/functions/exit.html
+[8]: http://www.opengroup.org/onlinepubs/009695399/functions/strlen.html
+[9]: http://www.opengroup.org/onlinepubs/009695399/functions/rand.html
+[10]: http://www.opengroup.org/onlinepubs/009695399/functions/printf.html
+[11]: http://www.opengroup.org/onlinepubs/009695399/functions/strcpy.html
+[12]: http://www.opengroup.org/onlinepubs/009695399/functions/puts.html
diff --git a/translated/tech/20190419 Building scalable social media sentiment analysis services in Python.md b/published/201905/20190419 Building scalable social media sentiment analysis services in Python.md
similarity index 65%
rename from translated/tech/20190419 Building scalable social media sentiment analysis services in Python.md
rename to published/201905/20190419 Building scalable social media sentiment analysis services in Python.md
index a216ce8495..dd2dadd739 100644
--- a/translated/tech/20190419 Building scalable social media sentiment analysis services in Python.md
+++ b/published/201905/20190419 Building scalable social media sentiment analysis services in Python.md
@@ -1,16 +1,18 @@
[#]: collector: (lujun9972)
[#]: translator: (MjSeven)
-[#]: reviewer: ( )
-[#]: publisher: ( )
-[#]: url: ( )
+[#]: reviewer: (wxy)
+[#]: publisher: (wxy)
+[#]: url: (https://linux.cn/article-10867-1.html)
[#]: subject: (Building scalable social media sentiment analysis services in Python)
[#]: via: (https://opensource.com/article/19/4/social-media-sentiment-analysis-python-scalable)
[#]: author: (Michael McCune https://opensource.com/users/elmiko/users/jschlessman)
使用 Python 构建可扩展的社交媒体情感分析服务
======
-学习如何使用 spaCy、vaderSentiment、Flask 和 Python 来为你的工作添加情感分析能力。
-![Tall building with windows][1]
+
+> 学习如何使用 spaCy、vaderSentiment、Flask 和 Python 来为你的作品添加情感分析能力。
+
+
本系列的[第一部分][2]提供了情感分析工作原理的一些背景知识,现在让我们研究如何将这些功能添加到你的设计中。
@@ -20,7 +22,7 @@
* 一个终端 shell
* shell 中的 Python 语言二进制文件(3.4+ 版本)
- * 用于安装 Python 包的 **pip** 命令
+ * 用于安装 Python 包的 `pip` 命令
* (可选)一个 [Python 虚拟环境][3]使你的工作与系统隔离开来
#### 配置环境
@@ -53,33 +55,44 @@ Type "help", "copyright", "credits" or "license" for more information.
>>>
```
-_(你的 Python 解释器版本打印可能与此不同。)_
+*(你的 Python 解释器版本打印可能与此不同。)*
- 1. 导入所需模块:
- ```
- >>> import spacy
- >>> from vaderSentiment import vaderSentiment
- ```
-2. 从 spaCy 加载英语语言模型:
- ```
- >>> english = spacy.load("en_core_web_sm")
- ```
- 3. 处理一段文本。本例展示了一个非常简单的句子,我们希望它能给我们带来些许积极的情感:
- ```
- >>> result = english("I like to eat applesauce with sugar and cinnamon.")
- ```
-4. 从处理后的结果中收集句子。SpaCy 已识别并处理短语中的实体,这一步为每个句子生成情感(即时在本例中只有一个句子):
- ```
- >>> sentences = [str(s) for s in result.sents]
- ```
- 5. 使用 vaderSentiments 创建一个分析器:
- ```
- >>> analyzer = vaderSentiment.SentimentIntensityAnalyzer()
- ```
- 6. 对句子进行情感分析:
- ```
- >>> sentiment = [analyzer.polarity_scores(str(s)) for s in sentences]
- ```
+1、导入所需模块:
+
+```
+>>> import spacy
+>>> from vaderSentiment import vaderSentiment
+```
+
+2、从 spaCy 加载英语语言模型:
+
+```
+>>> english = spacy.load("en_core_web_sm")
+```
+
+3、处理一段文本。本例展示了一个非常简单的句子,我们希望它能给我们带来些许积极的情感:
+
+```
+>>> result = english("I like to eat applesauce with sugar and cinnamon.")
+```
+
+4、从处理后的结果中收集句子。SpaCy 已识别并处理短语中的实体,这一步为每个句子生成情感(即时在本例中只有一个句子):
+
+```
+>>> sentences = [str(s) for s in result.sents]
+```
+
+5、使用 vaderSentiments 创建一个分析器:
+
+```
+>>> analyzer = vaderSentiment.SentimentIntensityAnalyzer()
+```
+
+6、对句子进行情感分析:
+
+```
+>>> sentiment = [analyzer.polarity_scores(str(s)) for s in sentences]
+```
`sentiment` 变量现在包含例句的极性分数。打印出这个值,看看它是如何分析这个句子的。
@@ -90,7 +103,7 @@ _(你的 Python 解释器版本打印可能与此不同。)_
这个结构是什么意思?
-表面上,这是一个只有一个字典对象的数组。如果有多个句子,那么每个句子都会对应一个字典对象。字典中有四个键对应不同类型的情感。**neg** 键表示负面情感,因为在本例中没有报告任何负面情感,**0.0** 值证明了这一点。**neu** 键表示中性情感,它的得分相当高,为**0.737**(最高为 **1.0**)。**pos** 键代表积极情感,得分适中,为 **0.263**。最后,**cmpound** 键代表文本的总体得分,它可以从负数到正数,**0.3612** 表示积极方面的情感多一点。
+表面上,这是一个只有一个字典对象的数组。如果有多个句子,那么每个句子都会对应一个字典对象。字典中有四个键对应不同类型的情感。`neg` 键表示负面情感,因为在本例中没有报告任何负面情感,`0.0` 值证明了这一点。`neu` 键表示中性情感,它的得分相当高,为 `0.737`(最高为 `1.0`)。`pos` 键代表积极情感,得分适中,为 `0.263`。最后,`cmpound` 键代表文本的总体得分,它可以从负数到正数,`0.3612` 表示积极方面的情感多一点。
要查看这些值可能如何变化,你可以使用已输入的代码做一个小实验。以下代码块显示了如何对类似句子的情感评分的评估。
@@ -113,9 +126,9 @@ _(你的 Python 解释器版本打印可能与此不同。)_
#### 前提条件
* 一个终端 shell
- * shell 中的 Python 语言二进制文件(3.4+版本)
- * 安装 Python 包的 **pip** 命令
- * **curl** 命令
+ * shell 中的 Python 语言二进制文件(3.4+ 版本)
+ * 安装 Python 包的 `pip` 命令
+ * `curl` 命令
* 一个文本编辑器
* (可选) 一个 [Python 虚拟环境][3]使你的工作与系统隔离开来
@@ -123,19 +136,21 @@ _(你的 Python 解释器版本打印可能与此不同。)_
这个环境几乎与上一节中的环境相同,唯一的区别是在 Python 环境中添加了 Flask 包。
- 1. 安装所需依赖项:
- ```
- pip install spacy vaderSentiment flask
- ```
-2. 安装 spaCy 的英语语言模型:
- ```
- python -m spacy download en_core_web_sm
- ```
+1、安装所需依赖项:
+```
+pip install spacy vaderSentiment flask
+```
+
+2、安装 spaCy 的英语语言模型:
+
+```
+python -m spacy download en_core_web_sm
+```
#### 创建应用程序文件
-打开编辑器,创建一个名为 **app.py** 的文件。添加以下内容 _(不用担心,我们将解释每一行)_ :
+打开编辑器,创建一个名为 `app.py` 的文件。添加以下内容 *(不用担心,我们将解释每一行)*:
```
@@ -179,10 +194,9 @@ analyzer = vader.SentimentIntensityAnalyzer()
english = spacy.load("en_core_web_sm")
```
-接下来的三行代码创建了一些全局变量。第一个变量 **app**,它是 Flask 用于创建 HTTP 路由的主要入口点。第二个变量 **analyzer** 与上一个示例中使用的类型相同,它将用于生成情感分数。最后一个变量 **english** 也与上一个示例中使用的类型相同,它将用于注释和标记初始文本输入。
-
-你可能想知道为什么全局声明这些变量。对于 **app** 变量,这是许多 Flask 应用程序的标准过程。但是,对于 **analyzer** 和 **english** 变量,将它们设置为全局变量的决定是基于与所涉及的类关联的加载时间。虽然加载时间可能看起来很短,但是当它在 HTTP 服务器的上下文中运行时,这些延迟会对性能产生负面影响。
+接下来的三行代码创建了一些全局变量。第一个变量 `app`,它是 Flask 用于创建 HTTP 路由的主要入口点。第二个变量 `analyzer` 与上一个示例中使用的类型相同,它将用于生成情感分数。最后一个变量 `english` 也与上一个示例中使用的类型相同,它将用于注释和标记初始文本输入。
+你可能想知道为什么全局声明这些变量。对于 `app` 变量,这是许多 Flask 应用程序的标准过程。但是,对于 `analyzer` 和 `english` 变量,将它们设置为全局变量的决定是基于与所涉及的类关联的加载时间。虽然加载时间可能看起来很短,但是当它在 HTTP 服务器的上下文中运行时,这些延迟会对性能产生负面影响。
```
def get_sentiments(text):
@@ -192,8 +206,7 @@ def get_sentiments(text):
return sentiments
```
-这部分是服务的核心 -- 一个用于从一串文本生成情感值的函数。你可以看到此函数中的操作对应于你之前在 Python 解释器中运行的命令。这里它们被封装在一个函数定义中,**text** 源作为文本变量传入,最后 **sentiments** 变量返回给调用者。
-
+这部分是服务的核心 —— 一个用于从一串文本生成情感值的函数。你可以看到此函数中的操作对应于你之前在 Python 解释器中运行的命令。这里它们被封装在一个函数定义中,`text` 源作为文本变量传入,最后 `sentiments` 变量返回给调用者。
```
@app.route("/", methods=["POST", "GET"])
@@ -206,11 +219,11 @@ def index():
return flask.json.dumps(sentiments)
```
-源文件的最后一个函数包含了指导 Flask 如何为服务配置 HTTP 服务器的逻辑。它从一行开始,该行将 HTTP 路由 **/** 与请求方法 **POST** 和 **GET** 相关联。
+源文件的最后一个函数包含了指导 Flask 如何为服务配置 HTTP 服务器的逻辑。它从一行开始,该行将 HTTP 路由 `/` 与请求方法 `POST` 和 `GET` 相关联。
-在函数定义行之后,**if** 子句将检测请求方法是否为 **GET**。如果用户向服务发送此请求,那么下面的行将返回一条指示如何访问服务器的文本消息。这主要是为了方便最终用户。
+在函数定义行之后,`if` 子句将检测请求方法是否为 `GET`。如果用户向服务发送此请求,那么下面的行将返回一条指示如何访问服务器的文本消息。这主要是为了方便最终用户。
-下一行使用 **flask.request** 对象来获取请求的主体,该主体应包含要处理的文本字符串。**decode** 函数将字节数组转换为可用的格式化字符串。经过解码的文本消息被传递给 **get_sentiments** 函数以生成情感分数。最后,分数通过 HTTP 框架返回给用户。
+下一行使用 `flask.request` 对象来获取请求的主体,该主体应包含要处理的文本字符串。`decode` 函数将字节数组转换为可用的格式化字符串。经过解码的文本消息被传递给 `get_sentiments` 函数以生成情感分数。最后,分数通过 HTTP 框架返回给用户。
你现在应该保存文件,如果尚未保存,那么返回 shell。
@@ -222,7 +235,7 @@ def index():
FLASK_APP=app.py flask run
```
-现在,你将在 shell 中看到来自服务器的一些输出,并且服务器将处于运行状态。要测试服务器是否正在运行,你需要打开第二个 shell 并使用 **curl** 命令。
+现在,你将在 shell 中看到来自服务器的一些输出,并且服务器将处于运行状态。要测试服务器是否正在运行,你需要打开第二个 shell 并使用 `curl` 命令。
首先,输入以下命令检查是否打印了指令信息:
@@ -252,11 +265,11 @@ curl http://localhost:5000 --header "Content-Type: application/json" --data "I l
### 继续探索
-现在你已经了解了自然语言处理和情感分析背后的原理和机制,下面是进一步发现探索主题的一些方法。
+现在你已经了解了自然语言处理和情感分析背后的原理和机制,下面是进一步发现探索该主题的一些方法。
#### 在 OpenShift 上创建流式情感分析器
-虽然创建本地应用程序来研究情绪分析很方便,但是接下来需要能够部署应用程序以实现更广泛的用途。按照[ Radnaalytics.io][11] 提供的指导和代码进行操作,你将学习如何创建一个情感分析仪,可以集装箱化并部署到 Kubernetes 平台。你还将了解如何将 APache Kafka 用作事件驱动消息传递的框架,以及如何将 Apache Spark 用作情绪分析的分布式计算平台。
+虽然创建本地应用程序来研究情绪分析很方便,但是接下来需要能够部署应用程序以实现更广泛的用途。按照[Radnaalytics.io][11] 提供的指导和代码进行操作,你将学习如何创建一个情感分析仪,可以容器化并部署到 Kubernetes 平台。你还将了解如何将 Apache Kafka 用作事件驱动消息传递的框架,以及如何将 Apache Spark 用作情绪分析的分布式计算平台。
#### 使用 Twitter API 发现实时数据
@@ -266,17 +279,17 @@ curl http://localhost:5000 --header "Content-Type: application/json" --data "I l
via: https://opensource.com/article/19/4/social-media-sentiment-analysis-python-scalable
-作者:[Michael McCune ][a]
+作者:[Michael McCune][a]
选题:[lujun9972][b]
译者:[MjSeven](https://github.com/MjSeven)
-校对:[校对者ID](https://github.com/校对者ID)
+校对:[wxy](https://github.com/wxy)
本文由 [LCTT](https://github.com/LCTT/TranslateProject) 原创编译,[Linux中国](https://linux.cn/) 荣誉推出
[a]: https://opensource.com/users/elmiko/users/jschlessman
[b]: https://github.com/lujun9972
[1]: https://opensource.com/sites/default/files/styles/image-full-size/public/lead-images/windows_building_sky_scale.jpg?itok=mH6CAX29 (Tall building with windows)
-[2]: https://opensource.com/article/19/4/social-media-sentiment-analysis-python-part-1
+[2]: https://linux.cn/article-10852-1.html
[3]: https://virtualenv.pypa.io/en/stable/
[4]: https://pypi.org/project/spacy/
[5]: https://pypi.org/project/vaderSentiment/
diff --git a/published/201905/20190419 Getting started with social media sentiment analysis in Python.md b/published/201905/20190419 Getting started with social media sentiment analysis in Python.md
new file mode 100644
index 0000000000..b9abec9325
--- /dev/null
+++ b/published/201905/20190419 Getting started with social media sentiment analysis in Python.md
@@ -0,0 +1,116 @@
+[#]: collector: (lujun9972)
+[#]: translator: (MjSeven)
+[#]: reviewer: (wxy)
+[#]: publisher: (wxy)
+[#]: url: (https://linux.cn/article-10852-1.html)
+[#]: subject: (Getting started with social media sentiment analysis in Python)
+[#]: via: (https://opensource.com/article/19/4/social-media-sentiment-analysis-python)
+[#]: author: (Michael McCune https://opensource.com/users/elmiko/users/jschlessman)
+
+使用 Python 进行社交媒体情感分析入门
+======
+
+> 学习自然语言处理的基础知识并探索两个有用的 Python 包。
+
+
+
+自然语言处理(NLP)是机器学习的一种,它解决了口语或书面语言和计算机辅助分析这些语言之间的相关性。日常生活中我们经历了无数的 NLP 创新,从写作帮助和建议到实时语音翻译,还有口译。
+
+本文研究了 NLP 的一个特定领域:情感分析。重点是确定输入语言的积极、消极或中性性质。本部分将解释 NLP 和情感分析的背景,并探讨两个开源的 Python 包。[第 2 部分][2]将演示如何开始构建自己的可扩展情感分析服务。
+
+在学习情感分析时,对 NLP 有一个大体了解是有帮助的。本文不会深入研究数学本质。相反,我们的目标是阐明 NLP 中的关键概念,这些概念对于将这些方法实际结合到你的解决方案中至关重要。
+
+### 自然语言和文本数据
+
+合理的起点是从定义开始:“什么是自然语言?”它是我们人类相互交流的方式,沟通的主要方式是口语和文字。我们可以更进一步,只关注文本交流。毕竟,生活在 Siri、Alexa 等无处不在的时代,我们知道语音是一组与文本无关的计算。
+
+### 数据前景和挑战
+
+我们只考虑使用文本数据,我们可以对语言和文本做什么呢?首先是语言,特别是英语,除了规则还有很多例外,含义的多样性和语境差异,这些都可能使人类口译员感到困惑,更不用说计算机翻译了。在小学,我们学习文章和标点符号,通过讲母语,我们获得了寻找直觉上表示唯一意义的词的能力。比如,出现诸如 “a”、“the” 和 “or” 之类的文章,它们在 NLP 中被称为*停止词*,因为传统上 NLP 算法是在一个序列中找到这些词时意味着搜索停止。
+
+由于我们的目标是自动将文本分类为情感类,因此我们需要一种以计算方式处理文本数据的方法。因此,我们必须考虑如何向机器表示文本数据。众所周知,利用和解释语言的规则很复杂,输入文本的大小和结构可能会有很大差异。我们需要将文本数据转换为数字数据,这是机器和数学的首选方式。这种转变属于*特征提取*的范畴。
+
+在提取输入文本数据的数字表示形式后,一个改进可能是:给定一个文本输入体,为上面列出的文章确定一组向量统计数据,并根据这些数据对文档进行分类。例如,过多的副词可能会使撰稿人感到愤怒,或者过度使用停止词可能有助于识别带有内容填充的学期论文。诚然,这可能与我们情感分析的目标没有太大关系。
+
+### 词袋
+
+当你评估一个文本陈述是积极还是消极的时候,你使用哪些上下文来评估它的极性?(例如,文本中是否具有积极的、消极的或中性的情感)一种方式是隐含形容词:被称为 “disgusting”(恶心) 的东西被认为是消极的,但如果同样的东西被称为 “beautiful”(漂亮),你会认为它是积极的。从定义上讲,俗语给人一种熟悉感,通常是积极的,而脏话可能是敌意的表现。文本数据也可以包括表情符号,它带有固定的情感。
+
+理解单个单词的极性影响为文本的[词袋][3](BoW)模型提供了基础。它分析一组单词或词汇表,并提取关于这些单词在输入文本中是否存在的度量。词汇表是通过处理已知极性的文本形成称为*标记的训练数据*。从这组标记数据中提取特征,然后分析特征之间的关系,并将标记与数据关联起来。
+
+“词袋”这个名称说明了它的用途:即不考虑空间位置或上下文的的单个词。词汇表通常是由训练集中出现的所有单词构建的,训练后往往会被修剪。如果在训练之前没有清理停止词,那么停止词会因为其高频率和低语境而被移除。很少使用的单词也可以删除,因为缺乏为一般输入实例提供的信息。
+
+但是,重要的是要注意,你可以(并且应该)进一步考虑单词在单个训练数据实例之外的情形,这称为[词频][4](TF)。你还应该考虑输入数据在所有训练实例中的单词计数,通常,出现在所有文档中的低频词更重要,这被称为[逆文本频率指数][5](IDF)。这些指标一定会在本主题系列的其他文章和软件包中提及,因此了解它们会有所帮助。
+
+词袋在许多文档分类应用程序中很有用。然而,在情感分析中,当缺乏情境意识的问题被利用时,事情就可以解决。考虑以下句子:
+
+ * 我们不喜欢这场战争。
+ * 我讨厌下雨天,好事是今天是晴天。
+ * 这不是生死攸关的问题。
+
+这些短语的情感对于人类口译员来说是有难度的,而且通过严格关注单个词汇的实例,对于机器翻译来说也是困难的。
+
+在 NLP 中也可以使用称为 “n-grams” 的单词分组。一个二元组考虑两个相邻单词组成的组而不是(或除了)单个词袋。这应该可以缓解诸如上述“不喜欢”之类的情况,但由于缺乏语境意思,它仍然是个问题。此外,在上面的第二句中,下半句的情感语境可以被理解为否定前半部分。因此,这种方法中也会丢失上下文线索的空间局部性。从实用角度来看,使问题复杂化的是从给定输入文本中提取的特征的稀疏性。对于一个完整的大型词汇表,每个单词都有一个计数,可以将其视为一个整数向量。大多数文档的向量中都有大量的零计数向量,这给操作增加了不必要的空间和时间复杂度。虽然已经提出了许多用于降低这种复杂性的简便方法,但它仍然是一个问题。
+
+### 词嵌入
+
+词嵌入是一种分布式表示,它允许具有相似含义的单词具有相似的表示。这是基于使用实值向量来与它们周围相关联。重点在于使用单词的方式,而不仅仅是它们的存在与否。此外,词嵌入的一个巨大实用优势是它们关注于密集向量。通过摆脱具有相应数量的零值向量元素的单词计数模型,词嵌入在时间和存储方面提供了一个更有效的计算范例。
+
+以下是两个优秀的词嵌入方法。
+
+#### Word2vec
+
+第一个是 [Word2vec][6],它是由 Google 开发的。随着你对 NLP 和情绪分析研究的深入,你可能会看到这种嵌入方法。它要么使用一个连续的词袋(CBOW),要么使用一个连续 skip-gram 模型。在 CBOW 中,一个单词的上下文是在训练中根据围绕它的单词来学习的。连续 skip-gram 学习倾向于围绕给定的单词学习单词。虽然这可能超出了你需要解决的问题,但是如果你曾经面对必须生成自己的词嵌入情况,那么 Word2vec 的作者就提倡使用 CBOW 方法来提高速度并评估频繁的单词,而 skip-gram 方法更适合嵌入稀有单词更重要的嵌入。
+
+#### GloVe
+
+第二个是[用于词表示的全局向量][7](GloVe),它是斯坦福大学开发的。它是 Word2vec 方法的扩展,试图通过将经典的全局文本统计特征提取获得的信息与 Word2vec 确定的本地上下文信息相结合。实际上,在一些应用程序中,GloVe 性能优于 Word2vec,而在另一些应用程序中则不如 Word2vec。最终,用于词嵌入的目标数据集将决定哪种方法最优。因此,最好了解它们的存在性和高级机制,因为你很可能会遇到它们。
+
+#### 创建和使用词嵌入
+
+最后,知道如何获得词嵌入是有用的。在第 2 部分中,你将看到我们通过利用社区中其他人的实质性工作,站到了巨人的肩膀上。这是获取词嵌入的一种方法:即使用现有的经过训练和验证的模型。实际上,有无数的模型适用于英语和其他语言,一定会有一种模型可以满足你的应用程序,让你开箱即用!
+
+如果没有的话,就开发工作而言,另一个极端是培训你自己的独立模型,而不考虑你的应用程序。实质上,你将获得大量标记的训练数据,并可能使用上述方法之一来训练模型。即使这样,你仍然只是在理解你输入文本数据。然后,你需要为你应用程序开发一个特定的模型(例如,分析软件版本控制消息中的情感价值),这反过来又需要自己的时间和精力。
+
+你还可以对针对你的应用程序的数据训练一个词嵌入,虽然这可以减少时间和精力,但这个词嵌入将是特定于应用程序的,这将会降低它的可重用性。
+
+### 可用的工具选项
+
+考虑到所需的大量时间和计算能力,你可能想知道如何才能找到解决问题的方法。的确,开发可靠模型的复杂性可能令人望而生畏。但是,有一个好消息:已经有许多经过验证的模型、工具和软件库可以为我们提供所需的大部分内容。我们将重点关注 [Python][8],因为它为这些应用程序提供了大量方便的工具。
+
+#### SpaCy
+
+[SpaCy][9] 提供了许多用于解析输入文本数据和提取特征的语言模型。它经过了高度优化,并被誉为同类中最快的库。最棒的是,它是开源的!SpaCy 会执行标识化、词性分类和依赖项注释。它包含了用于执行此功能的词嵌入模型,还有用于为超过 46 种语言的其他特征提取操作。在本系列的第二篇文章中,你将看到它如何用于文本分析和特征提取。
+
+#### vaderSentiment
+
+[vaderSentiment][10] 包提供了积极、消极和中性情绪的衡量标准。正如 [原论文][11] 的标题(《VADER:一个基于规则的社交媒体文本情感分析模型》)所示,这些模型是专门为社交媒体文本数据开发和调整的。VADER 接受了一组完整的人类标记过的数据的训练,包括常见的表情符号、UTF-8 编码的表情符号以及口语术语和缩写(例如 meh、lol、sux)。
+
+对于给定的输入文本数据,vaderSentiment 返回一个极性分数百分比的三元组。它还提供了一个单个的评分标准,称为 *vaderSentiment 复合指标*。这是一个在 `[-1, 1]` 范围内的实值,其中对于分值大于 `0.05` 的情绪被认为是积极的,对于分值小于 `-0.05` 的被认为是消极的,否则为中性。
+
+在[第 2 部分][2]中,你将学习如何使用这些工具为你的设计添加情感分析功能。
+
+--------------------------------------------------------------------------------
+
+via: https://opensource.com/article/19/4/social-media-sentiment-analysis-python
+
+作者:[Michael McCune][a]
+选题:[lujun9972][b]
+译者:[MjSeven](https://github.com/MjSeven)
+校对:[wxy](https://github.com/wxy)
+
+本文由 [LCTT](https://github.com/LCTT/TranslateProject) 原创编译,[Linux中国](https://linux.cn/) 荣誉推出
+
+[a]: https://opensource.com/users/elmiko/users/jschlessman
+[b]: https://github.com/lujun9972
+[1]: https://opensource.com/sites/default/files/styles/image-full-size/public/lead-images/getting_started_with_python.png?itok=MFEKm3gl (Raspberry Pi and Python)
+[2]: https://opensource.com/article/19/4/social-media-sentiment-analysis-python-part-2
+[3]: https://en.wikipedia.org/wiki/Bag-of-words_model
+[4]: https://en.wikipedia.org/wiki/Tf%E2%80%93idf#Term_frequency
+[5]: https://en.wikipedia.org/wiki/Tf%E2%80%93idf#Inverse_document_frequency
+[6]: https://en.wikipedia.org/wiki/Word2vec
+[7]: https://en.wikipedia.org/wiki/GloVe_(machine_learning)
+[8]: https://www.python.org/
+[9]: https://pypi.org/project/spacy/
+[10]: https://pypi.org/project/vaderSentiment/
+[11]: http://comp.social.gatech.edu/papers/icwsm14.vader.hutto.pdf
diff --git a/published/20190419 This is how System76 does open hardware.md b/published/201905/20190419 This is how System76 does open hardware.md
similarity index 100%
rename from published/20190419 This is how System76 does open hardware.md
rename to published/201905/20190419 This is how System76 does open hardware.md
diff --git a/published/201905/20190422 2 new apps for music tweakers on Fedora Workstation.md b/published/201905/20190422 2 new apps for music tweakers on Fedora Workstation.md
new file mode 100644
index 0000000000..00ccf16a53
--- /dev/null
+++ b/published/201905/20190422 2 new apps for music tweakers on Fedora Workstation.md
@@ -0,0 +1,140 @@
+[#]: collector: (lujun9972)
+[#]: translator: (wxy)
+[#]: reviewer: (wxy)
+[#]: publisher: (wxy)
+[#]: url: (https://linux.cn/article-10841-1.html)
+[#]: subject: (2 new apps for music tweakers on Fedora Workstation)
+[#]: via: (https://fedoramagazine.org/2-new-apps-for-music-tweakers-on-fedora-workstation/)
+[#]: author: (Justin W. Flory https://fedoramagazine.org/author/jflory7/)
+
+2 个给使用 Fedora 工作站的音乐爱好者的新应用
+======
+
+![][1]
+
+Linux 操作系统非常适合进行独特的自定义和调整,以使你的计算机更好地为你工作。例如,[i3 窗口管理器][2] 就让用户认识到了构成现代 Linux 桌面的各种组件和部分。
+
+Fedora 上有两个音乐爱好者会感兴趣的新软件包:mpris-scrobbler 和 playerctl。mpris-scrobbler 可以在 Last.fm 和/或 ListenBrainz 等音乐跟踪服务上[跟踪你的音乐收听历史][3]。 playerctl 是一个命令行的[音乐播放器的控制器][4]。
+
+### mpris-scrobbler:记录你的音乐收听趋势
+
+mpris-scrobbler 是一个命令行应用程序,用于将音乐的播放历史记录提交给 [Last.fm][5]、[Libre.fm][6] 或 [ListenBrainz][7] 等服务。它监听 [MPRIS D-Bus 接口][8] 以检测正在播放的内容。它可以连接几个不同的音乐客户端,如 spotify 客户端、[vlc][9]、audacious、bmp、[cmus][10] 等。
+
+![Last.fm last week in music report. Generated from user-submitted listening history.][11]
+
+#### 安装和配置 mpris-scrobbler
+
+mpris-scrobbler 在 Fedora 28 或更高版本以及 EPEL 7 存储库中可用。在终端中运行以下命令进行安装:
+
+```
+sudo dnf install mpris-scrobbler
+```
+
+安装完成后,使用 `systemctl` 启动并启用该服务。以下命令启动 mpris-scrobbler 并始终在系统重启后启动它:
+
+```
+systemctl --user enable --now mpris-scrobbler.service
+```
+
+#### 提交播放信息给 ListenBrainz
+
+这里将介绍如何将 mpris-scrobbler 与 ListenBrainz 帐户相关联。要使用 Last.fm 或 Libre.fm,请参阅其[上游文档][12]。
+
+要将播放信息提交到 ListenBrainz 服务器,你需要有一个 ListenBrainz API 令牌。如果你有帐户,请从[个人资料设置页面][13]中获取该令牌。如果有了令牌,请运行此命令以使用 ListenBrainz API 令牌进行身份验证:
+
+```
+$ mpris-scrobbler-signon token listenbrainz
+Token for listenbrainz.org:
+```
+
+最后,通过在 Fedora 上用你的音乐客户端播放一首歌来测试它。你播放的歌曲会出现在 ListenBrainz 个人资料页中。
+
+![Basic statistics and play history from a user profile on ListenBrainz. The current track is playing on a Fedora Workstation laptop with mpris-scrobbler.][14]
+
+### playerctl 可以控制音乐回放
+
+`playerctl` 是一个命令行工具,它可以控制任何实现了 MPRIS D-Bus 接口的音乐播放器。你可以轻松地将其绑定到键盘快捷键或媒体热键上。以下是如何在命令行中安装、使用它,以及为 i3 窗口管理器创建键绑定的方法。
+
+#### 安装和使用 playerctl
+
+`playerctl` 在 Fedora 28 或更高版本中可用。在终端运行如下命令以安装:
+
+```
+sudo dnf install playerctl
+```
+
+现在已安装好,你可以立即使用它。在 Fedora 上打开你的音乐播放器。接下来,尝试用以下命令来控制终端的播放。
+
+播放或暂停当前播放的曲目:
+
+```
+playerctl play-pause
+```
+
+如果你想跳过下一首曲目:
+
+```
+playerctl next
+```
+
+列出所有正在运行的播放器:
+
+```
+playerctl -l
+```
+
+仅使用 spotify 客户端播放或暂停当前播放的内容:
+
+```
+playerctl -p spotify play-pause
+```
+
+#### 在 i3wm 中创建 playerctl 键绑定
+
+你是否使用窗口管理器,比如 [i3 窗口管理器][2]?尝试使用 `playerctl` 进行键绑定。你可以将不同的命令绑定到不同的快捷键,例如键盘上的播放/暂停按钮。参照下面的 [i3wm 配置摘录][15] 看看如何做:
+
+```
+# Media player controls
+bindsym XF86AudioPlay exec "playerctl play-pause"
+bindsym XF86AudioNext exec "playerctl next"
+bindsym XF86AudioPrev exec "playerctl previous"
+```
+
+### 体验一下音乐播放器
+
+想了解关于在 Fedora 上定制音乐聆听体验的更多信息吗?Fedora Magazine 为你提供服务。看看 Fedora 上这[五个很酷的音乐播放器][16]。
+
+也可以通过使用 MusicBrainz Picard 对音乐库进行排序和组织,[为你的混乱的音乐库带来秩序][17]。
+
+--------------------------------------------------------------------------------
+
+via: https://fedoramagazine.org/2-new-apps-for-music-tweakers-on-fedora-workstation/
+
+作者:[Justin W. Flory][a]
+选题:[lujun9972][b]
+译者:[wxy](https://github.com/wxy)
+校对:[wxy](https://github.com/wxy)
+
+本文由 [LCTT](https://github.com/LCTT/TranslateProject) 原创编译,[Linux中国](https://linux.cn/) 荣誉推出
+
+[a]: https://fedoramagazine.org/author/jflory7/
+[b]: https://github.com/lujun9972
+[1]: https://fedoramagazine.org/wp-content/uploads/2019/04/2-music-tweak-apps-816x345.jpg
+[2]: https://fedoramagazine.org/getting-started-i3-window-manager/
+[3]: https://github.com/mariusor/mpris-scrobbler
+[4]: https://github.com/acrisci/playerctl
+[5]: https://www.last.fm/
+[6]: https://libre.fm/
+[7]: https://listenbrainz.org/
+[8]: https://specifications.freedesktop.org/mpris-spec/latest/
+[9]: https://www.videolan.org/vlc/
+[10]: https://cmus.github.io/
+[11]: https://fedoramagazine.org/wp-content/uploads/2019/02/Screenshot_2019-04-13-jflory7%E2%80%99s-week-in-music2-1024x500.png
+[12]: https://github.com/mariusor/mpris-scrobbler#authenticate-to-the-service
+[13]: https://listenbrainz.org/profile/
+[14]: https://fedoramagazine.org/wp-content/uploads/2019/04/Screenshot_2019-04-13-User-jflory-ListenBrainz.png
+[15]: https://github.com/jwflory/swiss-army/blob/ba6ac0c71855e33e3caa1ee1fe51c05d2df0529d/roles/apps/i3wm/files/config#L207-L210
+[16]: https://fedoramagazine.org/5-cool-music-player-apps/
+[17]: https://fedoramagazine.org/picard-brings-order-music-library/
+[18]: https://unsplash.com/photos/Qrspubmx6kE?utm_source=unsplash&utm_medium=referral&utm_content=creditCopyText
+[19]: https://unsplash.com/search/photos/music?utm_source=unsplash&utm_medium=referral&utm_content=creditCopyText
diff --git a/published/20190422 8 environment-friendly open software projects you should know.md b/published/201905/20190422 8 environment-friendly open software projects you should know.md
similarity index 100%
rename from published/20190422 8 environment-friendly open software projects you should know.md
rename to published/201905/20190422 8 environment-friendly open software projects you should know.md
diff --git a/published/20190422 Tracking the weather with Python and Prometheus.md b/published/201905/20190422 Tracking the weather with Python and Prometheus.md
similarity index 100%
rename from published/20190422 Tracking the weather with Python and Prometheus.md
rename to published/201905/20190422 Tracking the weather with Python and Prometheus.md
diff --git a/published/20190423 Four Methods To Check The Default Gateway Or Router IP Address In Linux.md b/published/201905/20190423 Four Methods To Check The Default Gateway Or Router IP Address In Linux.md
similarity index 100%
rename from published/20190423 Four Methods To Check The Default Gateway Or Router IP Address In Linux.md
rename to published/201905/20190423 Four Methods To Check The Default Gateway Or Router IP Address In Linux.md
diff --git a/translated/tech/20190423 How To Monitor Disk I-O Activity Using iotop And iostat Commands In Linux.md b/published/201905/20190423 How To Monitor Disk I-O Activity Using iotop And iostat Commands In Linux.md
similarity index 70%
rename from translated/tech/20190423 How To Monitor Disk I-O Activity Using iotop And iostat Commands In Linux.md
rename to published/201905/20190423 How To Monitor Disk I-O Activity Using iotop And iostat Commands In Linux.md
index ffececb666..66b202a011 100644
--- a/translated/tech/20190423 How To Monitor Disk I-O Activity Using iotop And iostat Commands In Linux.md
+++ b/published/201905/20190423 How To Monitor Disk I-O Activity Using iotop And iostat Commands In Linux.md
@@ -1,74 +1,62 @@
[#]: collector: (lujun9972)
[#]: translator: (warmfrog)
-[#]: reviewer: ( )
-[#]: publisher: ( )
-[#]: url: ( )
+[#]: reviewer: (wxy)
+[#]: publisher: (wxy)
+[#]: url: (https://linux.cn/article-10815-1.html)
[#]: subject: (How To Monitor Disk I/O Activity Using iotop And iostat Commands In Linux?)
[#]: via: (https://www.2daygeek.com/check-monitor-disk-io-in-linux-using-iotop-iostat-command/)
[#]: author: (Magesh Maruthamuthu https://www.2daygeek.com/author/magesh/)
在 Linux 中如何使用 iotop 和 iostat 监控磁盘 I/O 活动?
-===================================================
+======================================
-你知道在 Linux 中我们使用什么工具检修和监控实时的磁盘活动吗?
+你知道在 Linux 中我们使用什么工具检修和监控实时的磁盘活动吗?如果 [Linux 系统性能][1]变慢,我们会用 [top 命令][2] 来查看系统性能。它被用来检查是什么进程在服务器上占有如此高的使用率,对于大多数 Linux 系统管理员来说很常见,现实世界中被 Linux 系统管理员广泛采用。
-如果 **[Linux 系统性能][1]**变慢,我们会用 **[top 命令][12]** 来查看系统性能。
-
-它被用来检查是什么进程在服务器上占有如此高的使用率。
-
-对于大多数 Linux 系统管理员来说很常见。
-
-现实世界中被 Linux 系统管理员广泛采用。
-
-如果在进程输出中你没有看到很大的不同,你仍然有选择查看其他东西。
-
-我会建议你在 top 输出中检查 `wa` 状态因为大多数时间服务器性能由于在硬盘上的高 I/O 读和写降低了性能。
-
-如果它很高或者波动,很可能就是它造成的。因此,我们需要检查硬盘上的 I/O 活动。
+如果在进程输出中你没有看到很大的不同,你仍然有选择查看其他东西。我会建议你在 `top` 输出中检查 `wa` 状态,因为大多数时间里服务器性能由于在硬盘上的高 I/O 读和写降低了性能。如果它很高或者波动,很可能就是它造成的。因此,我们需要检查硬盘上的 I/O 活动。
我们可以在 Linux 中使用 `iotop` 和 `iostat` 命令监控所有的磁盘和文件系统的磁盘 I/O 统计。
### 什么是 iotop?
-iotop 是一个类似 top 的工具来显示实时的磁盘活动。
+`iotop` 是一个类似 `top` 的工具,用来显示实时的磁盘活动。
-iotop 监控 Linux 内核输出的 I/O 使用信息并且显示一个系统中进程或线程的当前 I/O 使用情况。
+`iotop` 监控 Linux 内核输出的 I/O 使用信息,并且显示一个系统中进程或线程的当前 I/O 使用情况。
-它显示每个进程/线程读写 I/O 带宽。它同样显示当等待换入和等待 I/O 的线程/进程 时间花费的百分比。
+它显示每个进程/线程读写 I/O 带宽。它同样显示当等待换入和等待 I/O 的线程/进程花费的时间的百分比。
-Total DISK READ 和 Total DISK WRITE 的值表示了一方面进程和内核线程之间的总的读写带宽,另一方面表示内核块设备子系统的。
+`Total DISK READ` 和 `Total DISK WRITE` 的值一方面表示了进程和内核线程之间的总的读写带宽,另一方面也表示内核块设备子系统的。
-Actual DISK READ 和 Actual DISK WRITE 的值表示在内核块设备子系统和下面硬件(HDD,SSD,等等。)对应的实际磁盘 I/O 带宽。
+`Actual DISK READ` 和 `Actual DISK WRITE` 的值表示在内核块设备子系统和下面硬件(HDD、SSD 等等)对应的实际磁盘 I/O 带宽。
### 如何在 Linux 中安装 iotop ?
我们可以轻松在包管理器的帮助下安装,因为该软件包在所有的 Linux 发行版仓库中都可以获得。
-对于 **`Fedora`** 系统,使用 **[DNF 命令][3]** 来安装 iotop。
+对于 Fedora 系统,使用 [DNF 命令][3] 来安装 `iotop`。
```
$ sudo dnf install iotop
```
-对于 **`Debian/Ubuntu`** 系统,使用 **[API-GET 命令][4]** 或者 **[APT 命令][5]** 来安装 iotop。
+对于 Debian/Ubuntu 系统,使用 [API-GET 命令][4] 或者 [APT 命令][5] 来安装 `iotop`。
```
$ sudo apt install iotop
```
-对于基于 **`Arch Linux`** 的系统,使用 **[Pacman Command][6]** 来安装 iotop。
+对于基于 Arch Linux 的系统,使用 [Pacman Command][6] 来安装 `iotop`。
```
$ sudo pacman -S iotop
```
-对于 **`RHEL/CentOS`** 的系统,使用 **[YUM Command][7]** 来安装 iotop。
+对于 RHEL/CentOS 的系统,使用 [YUM Command][7] 来安装 `iotop`。
```
$ sudo yum install iotop
```
-对于使用 **`openSUSE Leap`** 的系统,使用 **[Zypper Command][8]** 来安装 iotop。
+对于使用 openSUSE Leap 的系统,使用 [Zypper Command][8] 来安装 `iotop`。
```
$ sudo zypper install iotop
@@ -76,72 +64,70 @@ $ sudo zypper install iotop
### 在 Linux 中如何使用 iotop 命令来监控磁盘 I/O 活动/统计?
-iotop 命令有很多参数来检查关于磁盘 I/O 的变化
+`iotop` 命令有很多参数来检查关于磁盘 I/O 的变化:
```
# iotop
```
-[![][9]![][9]][10]
+![10]
-如果你想检查那个进程实际在做 I/O,那么运行 iotop 命令加上 `-o` 或者 `--only` 参数。
+如果你想检查那个进程实际在做 I/O,那么运行 `iotop` 命令加上 `-o` 或者 `--only` 参数。
```
# iotop --only
```
-[![][9]![][9]][11]
-
-**细节:**
-
- * **`IO:`** 它显示每个进程的 I/O 利用率,包含磁盘和交换。
- * **`SWAPIN:`** 它只显示每个进程的交换使用率。
+![11]
+细节:
+ * `IO`:它显示每个进程的 I/O 利用率,包含磁盘和交换。
+ * `SWAPIN`: 它只显示每个进程的交换使用率。
### 什么是 iostat?
-iostat 被用来报告中央处理单元(CPU)的统计和设备与分区的输出/输出的统计。
+`iostat` 被用来报告中央处理单元(CPU)的统计和设备与分区的输出/输出的统计。
-iostat 命令通过观察与他们平均传输率相关的设备活跃时间来监控系统输入/输出设备载入。
+`iostat` 命令通过观察与它们平均传输率相关的设备活跃时间来监控系统输入/输出设备负载。
-iostat 命令生成的报告可以被用来改变系统配置来更好的平衡物理磁盘之间的输入/输出负载。
+`iostat` 命令生成的报告可以被用来改变系统配置来更好的平衡物理磁盘之间的输入/输出负载。
-所有的统计都在 iostat 命令每次运行时被报告。该报告包含一个 CPU 头部,后面是一行 CPU 统计。
+所有的统计都在 `iostat` 命令每次运行时被报告。该报告包含一个 CPU 头部,后面是一行 CPU 统计。
-在多处理器系统中,CPU 统计被计算为系统层面的所有处理器的平均值。一个设备头行显示后紧跟一行每个配置设备的统计。
+在多处理器系统中,CPU 统计被计算为系统层面的所有处理器的平均值。设备头行后紧跟显示每个配置的设备一行的统计。
-iostat 命令生成两种类型的报告,CPU 利用率报告和设备利用率报告。
+`iostat` 命令生成两种类型的报告,CPU 利用率报告和设备利用率报告。
### 在 Linux 中怎样安装 iostat?
-iostat 工具是 sysstat 包的一部分,所以我们可以轻松地在包管理器地帮助下安装因为在所有的 Linux 发行版的仓库都是可以获得的。
+`iostat` 工具是 `sysstat` 包的一部分,所以我们可以轻松地在包管理器地帮助下安装,因为在所有的 Linux 发行版的仓库都是可以获得的。
-对于 **`Fedora`** 系统,使用 **[DNF Command][3]** 来安装 sysstat。
+对于 Fedora 系统,使用 [DNF Command][3] 来安装 `sysstat`。
```
$ sudo dnf install sysstat
```
-对于 **`Debian/Ubuntu`** 系统,使用 **[APT-GET Command][4]** 或者 **[APT Command][5]** 来安装 sysstat。
+对于 Debian/Ubuntu 系统,使用 [APT-GET Command][4] 或者 [APT Command][5] 来安装 `sysstat`。
```
$ sudo apt install sysstat
```
-对于基于 **`Arch Linux`** 的系统,使用 **[Pacman Command][6]** 来安装 sysstat。
+对于基于 Arch Linux 的系统,使用 [Pacman Command][6] 来安装 `sysstat`。
```
$ sudo pacman -S sysstat
```
-对于 **`RHEL/CentOS`** 系统,使用 **[YUM Command][7]** 来安装 sysstat。
+对于 RHEL/CentOS 系统,使用 [YUM Command][7] 来安装 `sysstat`。
```
$ sudo yum install sysstat
```
-对于 **`openSUSE Leap`** 系统,使用 **[Zypper Command][8]** 来安装 sysstat。
+对于 openSUSE Leap 系统,使用 [Zypper Command][8] 来安装 `sysstat`。
```
$ sudo zypper install sysstat
@@ -149,9 +135,9 @@ $ sudo zypper install sysstat
### 在 Linux 中如何使用 sysstat 命令监控磁盘 I/O 活动/统计?
-在 iostat 命令中有很多参数来检查关于 I/O 和 CPU 的变化统计信息。
+在 `iostat` 命令中有很多参数来检查关于 I/O 和 CPU 的变化统计信息。
-不加参数运行 iostat 命令会看到完整的系统统计。
+不加参数运行 `iostat` 命令会看到完整的系统统计。
```
# iostat
@@ -169,7 +155,7 @@ loop1 0.00 0.00 0.00 0.00 1093
loop2 0.00 0.00 0.00 0.00 1077 0 0
```
-运行 iostat 命令加上 `-d` 参数查看所有设备的 I/O 统计。
+运行 `iostat` 命令加上 `-d` 参数查看所有设备的 I/O 统计。
```
# iostat -d
@@ -184,7 +170,7 @@ loop1 0.00 0.00 0.00 0.00 1093
loop2 0.00 0.00 0.00 0.00 1077 0 0
```
-运行 iostat 命令加上 `-p` 参数查看所有的设备和分区的 I/O 统计。
+运行 `iostat` 命令加上 `-p` 参数查看所有的设备和分区的 I/O 统计。
```
# iostat -p
@@ -206,7 +192,7 @@ loop1 0.00 0.00 0.00 0.00 1093
loop2 0.00 0.00 0.00 0.00 1077 0 0
```
-运行 iostat 命令加上 `-x` 参数显示所有设备的详细的 I/O 统计信息。
+运行 `iostat` 命令加上 `-x` 参数显示所有设备的详细的 I/O 统计信息。
```
# iostat -x
@@ -224,7 +210,7 @@ loop1 0.00 0.00 0.00 0.00 0.40 12.86 0.00 0.
loop2 0.00 0.00 0.00 0.00 0.38 19.58 0.00 0.00 0.00 0.00 0.00 0.00 0.00 0.00 0.00 0.00 0.00 0.00 0.00 0.00
```
-运行 iostat 命令加上 `-d [设备名]` 参数查看具体设备和它的分区的 I/O 统计信息。
+运行 `iostat` 命令加上 `-d [设备名]` 参数查看具体设备和它的分区的 I/O 统计信息。
```
# iostat -p [Device_Name]
@@ -242,7 +228,7 @@ sda2 0.18 6.76 80.21 0.00 3112916 36924
sda1 0.00 0.01 0.00 0.00 3224 0 0
```
-运行 iostat 命令加上 `-m` 参数以 `MB` 为单位而不是 `KB` 查看所有设备的统计。默认以 KB 显示输出。
+运行 `iostat` 命令加上 `-m` 参数以 MB 为单位而不是 KB 查看所有设备的统计。默认以 KB 显示输出。
```
# iostat -m
@@ -260,7 +246,7 @@ loop1 0.00 0.00 0.00 0.00 1
loop2 0.00 0.00 0.00 0.00 1 0 0
```
-运行 iostat 命令使用特定的间隔使用如下的格式。在这个例子中,我们打算以 5 秒捕获的间隔捕获两个报告。
+运行 `iostat` 命令使用特定的间隔使用如下的格式。在这个例子中,我们打算以 5 秒捕获的间隔捕获两个报告。
```
# iostat [Interval] [Number Of Reports]
@@ -290,7 +276,7 @@ loop1 0.00 0.00 0.00 0.00 0
loop2 0.00 0.00 0.00 0.00 0 0 0
```
-运行 iostat 命令 与 `-N` 参数来查看 LVM 磁盘 I/O 统计报告。
+运行 `iostat` 命令与 `-N` 参数来查看 LVM 磁盘 I/O 统计报告。
```
# iostat -N
@@ -307,7 +293,7 @@ sdc 0.01 0.12 0.00 2108 0
2g-2gvol1 0.00 0.07 0.00 1204 0
```
-运行 nfsiostat 命令来查看 Network File System(NFS)的 I/O 统计。
+运行 `nfsiostat` 命令来查看 Network File System(NFS)的 I/O 统计。
```
# nfsiostat
@@ -320,7 +306,7 @@ via: https://www.2daygeek.com/check-monitor-disk-io-in-linux-using-iotop-iostat-
作者:[Magesh Maruthamuthu][a]
选题:[lujun9972][b]
译者:[warmfrog](https://github.com/warmfrog)
-校对:[校对者ID](https://github.com/校对者ID)
+校对:[wxy](https://github.com/wxy)
本文由 [LCTT](https://github.com/LCTT/TranslateProject) 原创编译,[Linux中国](https://linux.cn/) 荣誉推出
diff --git a/published/201905/20190425 Automate backups with restic and systemd.md b/published/201905/20190425 Automate backups with restic and systemd.md
new file mode 100644
index 0000000000..677a87c3f4
--- /dev/null
+++ b/published/201905/20190425 Automate backups with restic and systemd.md
@@ -0,0 +1,132 @@
+[#]: collector: (lujun9972)
+[#]: translator: (geekpi)
+[#]: reviewer: (wxy)
+[#]: publisher: (wxy)
+[#]: url: (https://linux.cn/article-10875-1.html)
+[#]: subject: (Automate backups with restic and systemd)
+[#]: via: (https://fedoramagazine.org/automate-backups-with-restic-and-systemd/)
+[#]: author: (Link Dupont https://fedoramagazine.org/author/linkdupont/)
+
+使用 restic 和 systemd 自动备份
+======
+
+![][1]
+
+及时备份很重要。即使在 [Fedora Magazine][3] 中,[备份软件][2] 也是一个常见的讨论话题。本文演示了如何仅使用 systemd 以及 `restic` 来自动备份。
+
+有关 `restic` 的介绍,请查看我们的文章[在 Fedora 上使用 restic 进行加密备份][4]。然后继续阅读以了解更多详情。
+
+为了自动创建快照以及清理数据,需要运行两个 systemd 服务。第一个运行*备份*命令的服务需要以常规频率运行。第二个服务负责数据清理。
+
+如果你根本不熟悉 systemd,那么这是个很好的学习机会。查看 [Magazine 上关于 systemd 的系列文章] [5],从单元文件的这个入门开始:
+
+- [systemd 单元文件基础][6]
+
+如果你还没有安装 `restic`,请注意它在官方的 Fedora 仓库中。要安装它,请[带上 sudo][7] 运行此命令:
+
+```
+$ sudo dnf install restic
+```
+
+### 备份
+
+首先,创建 `~/.config/systemd/user/restic-backup.service`。将下面的文本复制并粘贴到文件中以获得最佳效果。
+
+```
+[Unit]
+Description=Restic backup service
+[Service]
+Type=oneshot
+ExecStart=restic backup --verbose --one-file-system --tag systemd.timer $BACKUP_EXCLUDES $BACKUP_PATHS
+ExecStartPost=restic forget --verbose --tag systemd.timer --group-by "paths,tags" --keep-daily $RETENTION_DAYS --keep-weekly $RETENTION_WEEKS --keep-monthly $RETENTION_MONTHS --keep-yearly $RETENTION_YEARS
+EnvironmentFile=%h/.config/restic-backup.conf
+```
+
+此服务引用环境文件来加载密钥(例如 `RESTIC_PASSWORD`)。创建 `~/.config/restic-backup.conf`。复制并粘贴以下内容以获得最佳效果。此示例使用 BackBlaze B2 存储。请相应地调整 ID、密钥、仓库和密码值。
+
+```
+BACKUP_PATHS="/home/rupert"
+BACKUP_EXCLUDES="--exclude-file /home/rupert/.restic_excludes --exclude-if-present .exclude_from_backup"
+RETENTION_DAYS=7
+RETENTION_WEEKS=4
+RETENTION_MONTHS=6
+RETENTION_YEARS=3
+B2_ACCOUNT_ID=XXXXXXXXXXXXXXXXXXXXXXXXX
+B2_ACCOUNT_KEY=XXXXXXXXXXXXXXXXXXXXXXXXXXXXXXX
+RESTIC_REPOSITORY=b2:XXXXXXXXXXXXXXXXXX:/
+RESTIC_PASSWORD=XXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXX
+```
+
+现在已安装该服务,请重新加载 systemd:`systemctl -user daemon-reload`。尝试手动运行该服务以创建备份:`systemctl -user start restic-backup`。
+
+因为该服务类型是*一次性*,它将运行一次并退出。验证服务运行并根据需要创建快照后,设置计时器以定期运行此服务。例如,要每天运行 `restic-backup.service`,请按如下所示创建 `~/.config/systemd/user/restic-backup.timer`。再次复制并粘贴此文本:
+
+```
+[Unit]
+Description=Backup with restic daily
+[Timer]
+OnCalendar=daily
+Persistent=true
+[Install]
+WantedBy=timers.target
+```
+
+运行以下命令启用:
+
+```
+$ systemctl --user enable --now restic-backup.timer
+```
+
+### 清理
+
+虽然主服务运行 `forget` 命令仅保留保留策略中的快照,但实际上并未从 `restic` 仓库中删除数据。 `prune` 命令检查仓库和当前快照,并删除与快照无关的所有数据。由于 `prune` 可能是一个耗时的过程,因此无需在每次运行备份时运行。这是第二个服务和计时器的场景。首先,通过复制和粘贴此文本来创建文件 `~/.config/systemd/user/restic-prune.service`:
+
+```
+[Unit]
+Description=Restic backup service (data pruning)
+[Service]
+Type=oneshot
+ExecStart=restic prune
+EnvironmentFile=%h/.config/restic-backup.conf
+```
+
+与主 `restic-backup.service` 服务类似,`restic-prune` 也是一次性服务,并且可以手动运行。设置完服务后,创建 `~/.config/systemd/user/restic-prune.timer` 并启用相应的计时器:
+
+```
+[Unit]
+Description=Prune data from the restic repository monthly
+[Timer]
+OnCalendar=monthly
+Persistent=true
+[Install]
+WantedBy=timers.target
+```
+
+就是这些了!`restic` 将会每日运行并按月清理数据。
+
+* * *
+
+图片来自 [Unsplash][9] 由 [Samuel Zeller][8] 拍摄。
+
+--------------------------------------------------------------------------------
+
+via: https://fedoramagazine.org/automate-backups-with-restic-and-systemd/
+
+作者:[Link Dupont][a]
+选题:[lujun9972][b]
+译者:[geekpi](https://github.com/geekpi)
+校对:[wxy](https://github.com/wxy)
+
+本文由 [LCTT](https://github.com/LCTT/TranslateProject) 原创编译,[Linux中国](https://linux.cn/) 荣誉推出
+
+[a]: https://fedoramagazine.org/author/linkdupont/
+[b]: https://github.com/lujun9972
+[1]: https://fedoramagazine.org/wp-content/uploads/2019/04/restic-systemd-816x345.jpg
+[2]: https://restic.net/
+[3]: https://fedoramagazine.org/?s=backup
+[4]: https://fedoramagazine.org/use-restic-encrypted-backups/
+[5]: https://fedoramagazine.org/series/systemd-series/
+[6]: https://fedoramagazine.org/systemd-getting-a-grip-on-units/
+[7]: https://fedoramagazine.org/howto-use-sudo/
+[8]: https://unsplash.com/photos/JuFcQxgCXwA?utm_source=unsplash&utm_medium=referral&utm_content=creditCopyText
+[9]: https://unsplash.com/search/photos/archive?utm_source=unsplash&utm_medium=referral&utm_content=creditCopyText
diff --git a/published/201905/20190430 Upgrading Fedora 29 to Fedora 30.md b/published/201905/20190430 Upgrading Fedora 29 to Fedora 30.md
new file mode 100644
index 0000000000..4d9123601f
--- /dev/null
+++ b/published/201905/20190430 Upgrading Fedora 29 to Fedora 30.md
@@ -0,0 +1,96 @@
+[#]: collector: (lujun9972)
+[#]: translator: (geekpi)
+[#]: reviewer: (wxy)
+[#]: publisher: (wxy)
+[#]: url: (https://linux.cn/article-10854-1.html)
+[#]: subject: (Upgrading Fedora 29 to Fedora 30)
+[#]: via: (https://fedoramagazine.org/upgrading-fedora-29-to-fedora-30/)
+[#]: author: (Ryan Lerch https://fedoramagazine.org/author/ryanlerch/)
+
+将 Fedora 29 升级到 Fedora 30
+======
+
+![][1]
+
+Fedora 30 [已经发布了][2]。你可能希望将系统升级到最新版本的 Fedora。Fedora 工作站版本有图形化升级的方法。另外,Fedora 也提供了一个命令行方法,用于将 Fedora 29 升级到 Fedora 30。
+
+### 将 Fedora 29 工作站版本升级到 Fedora 30
+
+在发布不久后,桌面会显示一条通知告诉你可以升级。你可以单击通知启动 “GNOME 软件” 应用。或者你可以从 GNOME Shell 中选择“软件”。
+
+在 “GNOME 软件” 中选择*更新*选项卡,你会看到一个页面通知你可以更新 Fedora 30。
+
+如果你在屏幕上看不到任何内容,请尝试点击左上角的重新加载按钮。发布后,所有系统都可能需要一段时间才能看到可用的升级。
+
+选择“下载”获取升级包。你可以继续做其他的事直到下载完成。然后使用 “GNOME 软件” 重启系统并应用升级。升级需要时间,因此你可以喝杯咖啡,稍后再回来。
+
+### 使用命令行
+
+如果你过去升级过 Fedora 版本,你可能熟悉 `dnf upgrade` 插件。这是从 Fedora 29 升级到 Fedora 30 的推荐和支持的方式。使用这个插件将使你的 Fedora 30 升级简单易行。
+
+#### 1、更新软件并备份系统
+
+在你执行任何操作之前,你需要确保在开始升级之前拥有 Fedora 29 的最新软件。要更新软件,请使用 “GNOME 软件” 或在终端中输入以下命令。
+
+```
+sudo dnf upgrade --refresh
+```
+
+此外,请确保在继续之前备份系统。关于备份的帮助,请参阅 Fedora Magazine 上的[备份系列][3]。
+
+#### 2、安装 DNF 插件
+
+接下来,打开终端并输入以下命令来安装插件:
+
+```
+sudo dnf install dnf-plugin-system-upgrade
+```
+
+#### 3、使用 DNF 开始更新
+
+现在你的系统是最新的,完成了备份,并且已安装 DNF 插件,你可以在终端中使用以下命令开始升级:
+
+```
+sudo dnf system-upgrade download --releasever=30
+```
+
+此命令将开始在本地下载所有升级文件以准备升级。如果你因为没有更新包、错误的依赖,或过时的包在升级时遇到问题,请在输入上面的命令时添加 `-- allowerasing` 标志。这将允许 DNF 删除可能阻止系统升级的软件包。
+
+#### 4、重启并升级
+
+当前面的命令完成下载所有升级文件后,你的系统就可以重启了。要将系统引导至升级过程,请在终端中输入以下命令:
+
+```
+sudo dnf system-upgrade reboot
+```
+
+此后你的系统将重启。在许多版本之前,`fedup` 工具将在内核选择/引导页面上创建一个新选项。使用 `dnf-plugin-system-upgrade` 包,你的系统将使用当前 Fedora 29 安装的内核重启。这个是正常的。在内核选择页面后不久,系统开始升级过程。
+
+现在可以休息一下了!完成后你的系统将重启,你就可以登录新升级的 Fedora 30 了。
+
+![][4]
+
+### 解决升级问题
+
+升级系统时偶尔可能会出现意外问题。如果你遇到任何问题,请访问 [DNF 系统升级的维基页面][5],以获取有关出现问题时的故障排除的更多信息。
+
+如果你在升级时遇到问题并在系统上安装了第三方仓库,那么可能需要在升级时禁用这些仓库。有关 Fedora 对未提供仓库的支持,请与仓库的提供商联系。
+
+--------------------------------------------------------------------------------
+
+via: https://fedoramagazine.org/upgrading-fedora-29-to-fedora-30/
+
+作者:[Ryan Lerch][a]
+选题:[lujun9972][b]
+译者:[geekpi](https://github.com/geekpi)
+校对:[wxy](https://github.com/wxy)
+
+本文由 [LCTT](https://github.com/LCTT/TranslateProject) 原创编译,[Linux中国](https://linux.cn/) 荣誉推出
+
+[a]: https://fedoramagazine.org/author/ryanlerch/
+[b]: https://github.com/lujun9972
+[1]: https://fedoramagazine.org/wp-content/uploads/2019/04/29-30-816x345.jpg
+[2]: https://fedoramagazine.org/announcing-fedora-30/
+[3]: https://fedoramagazine.org/taking-smart-backups-duplicity/
+[4]: https://cdn.fedoramagazine.org/wp-content/uploads/2016/06/Screenshot_f23-ws-upgrade-test_2016-06-10_110906-1024x768.png
+[5]: https://fedoraproject.org/wiki/DNF_system_upgrade#Resolving_post-upgrade_issues
diff --git a/published/201905/20190501 3 apps to manage personal finances in Fedora.md b/published/201905/20190501 3 apps to manage personal finances in Fedora.md
new file mode 100644
index 0000000000..dee4fb0985
--- /dev/null
+++ b/published/201905/20190501 3 apps to manage personal finances in Fedora.md
@@ -0,0 +1,73 @@
+[#]: collector: (lujun9972)
+[#]: translator: (geekpi)
+[#]: reviewer: (wxy)
+[#]: publisher: (wxy)
+[#]: url: (https://linux.cn/article-10903-1.html)
+[#]: subject: (3 apps to manage personal finances in Fedora)
+[#]: via: (https://fedoramagazine.org/3-apps-to-manage-personal-finances-in-fedora/)
+[#]: author: (Paul W. Frields https://fedoramagazine.org/author/pfrields/)
+
+3 款在 Fedora 中管理个人财务的应用
+======
+
+![][1]
+
+网上有很多可以用来管理你个人财务的服务。虽然它们可能很方便,但这通常也意味着将你最宝贵的个人数据放在你无法监控的公司。也有些人对这些不太在意。
+
+无论你是否在意,你可能会对你自己系统上的应用感兴趣。这意味着如果你不想,你的数据永远不会离开自己的计算机。这三款之一可能就是你想找的。
+
+### HomeBank
+
+HomeBank 是一款可以管理多个账户的全功能软件。它很容易设置并保持更新。它有多种方式画出你的分类和负债,以便你可以看到资金流向何处。它可以通过官方 Fedora 仓库下载。
+
+![A simple account set up in HomeBank with a few transactions.][2]
+
+要安装 HomeBank,请打开“软件中心”,搜索 “HomeBank”,然后选择该应用。单击“安装”将其添加到你的系统中。HomeBank 也可以通过 Flatpak 安装。
+
+### KMyMoney
+
+KMyMoney 是一个成熟的应用,它已经存在了很长一段时间。它有一系列稳定的功能,可帮助你管理多个帐户,包括资产、负债、税收等。KMyMoney 包含一整套用于管理投资和进行预测的工具。它还提供大量报告,以了解你的资金运作方式。
+
+![A subset of the many reports available in KMyMoney.][3]
+
+要安装它,请使用软件中心,或使用命令行:
+
+```
+$ sudo dnf install kmymoney
+```
+
+### GnuCash
+
+用于个人财务的最受欢迎的免费 GUI 应用之一是 GnuCash。GnuCash 不仅可以用于个人财务。它还有管理企业收入、资产和负债的功能。这并不意味着你不能用它来管理自己的账户。从查看[在线教程和指南][4]开始了解。
+
+![Checking account records shown in GnuCash.][5]
+
+打开“软件中心”,搜索 “GnuCash”,然后选择应用。单击“安装”将其添加到你的系统中。或者如上所述使用 `dnf install` 来安装 “gnucash” 包。
+
+它现在可以通过 Flathub 安装,这使得安装变得简单。如果你没有安装 Flathub,请查看 [Fedora Magazine 上的这篇文章][6]了解如何使用它。这样你也可以在终端使用 `flatpak install gnucash` 命令。
+
+* * *
+
+照片由 [Fabian Blank][7] 拍摄,发布在 [Unsplash][8] 上。
+
+--------------------------------------------------------------------------------
+
+via: https://fedoramagazine.org/3-apps-to-manage-personal-finances-in-fedora/
+
+作者:[Paul W. Frields][a]
+选题:[lujun9972][b]
+译者:[geekpi](https://github.com/geekpi)
+校对:[wxy](https://github.com/wxy)
+
+本文由 [LCTT](https://github.com/LCTT/TranslateProject) 原创编译,[Linux中国](https://linux.cn/) 荣誉推出
+
+[a]: https://fedoramagazine.org/author/pfrields/
+[b]: https://github.com/lujun9972
+[1]: https://fedoramagazine.org/wp-content/uploads/2019/04/personal-finance-3-apps-816x345.jpg
+[2]: https://fedoramagazine.org/wp-content/uploads/2019/04/Screenshot-from-2019-04-28-16-16-16-1024x637.png
+[3]: https://fedoramagazine.org/wp-content/uploads/2019/04/Screenshot-from-2019-04-28-16-27-10-1-1024x649.png
+[4]: https://www.gnucash.org/viewdoc.phtml?rev=3&lang=C&doc=guide
+[5]: https://fedoramagazine.org/wp-content/uploads/2019/04/Screenshot-from-2019-04-28-16-41-27-1024x631.png
+[6]: https://fedoramagazine.org/install-flathub-apps-fedora/
+[7]: https://unsplash.com/photos/pElSkGRA2NU?utm_source=unsplash&utm_medium=referral&utm_content=creditCopyText
+[8]: https://unsplash.com/search/photos/money?utm_source=unsplash&utm_medium=referral&utm_content=creditCopyText
diff --git a/published/201905/20190501 Cisco issues critical security warning for Nexus data-center switches.md b/published/201905/20190501 Cisco issues critical security warning for Nexus data-center switches.md
new file mode 100644
index 0000000000..e71bd21d6b
--- /dev/null
+++ b/published/201905/20190501 Cisco issues critical security warning for Nexus data-center switches.md
@@ -0,0 +1,75 @@
+[#]: collector: (lujun9972)
+[#]: translator: (hopefully2333)
+[#]: reviewer: (wxy)
+[#]: publisher: (wxy)
+[#]: url: (https://linux.cn/article-10876-1.html)
+[#]: subject: (Cisco issues critical security warning for Nexus data-center switches)
+[#]: via: (https://www.networkworld.com/article/3392858/cisco-issues-critical-security-warning-for-nexus-data-center-switches.html)
+[#]: author: (Michael Cooney https://www.networkworld.com/author/Michael-Cooney/)
+
+思科针对 Nexus 数据中心交换机发出危急安全预警
+======
+
+> 思科围绕着 Nexus 的交换机、Firepower 防火墙和其他设备,发布了 40 个安全报告。
+
+![Thinkstock][1]
+
+日前,思科发布了 40 个左右的安全报告,但只有其中的一个被评定为“[危急][2]”:思科 Nexus 9000 系列应用中心基础设施(ACI)模式数据中心交换机中的一个漏洞,可能会让攻击者隐秘地访问到系统资源。
+
+这个新发现的漏洞,被通用漏洞评分系统给到了 9.8 分(满分 10 分),思科表示,它是思科 Nexus 9000 系列的安全 shell (ssh)密钥管理方面的问题,这个漏洞允许远程攻击者以 root 用户的权限来连接到受影响的系统。
+
+思科表示,“**这个漏洞是因为所有的设备都存在一对默认的 ssh 密钥对**,攻击者可以使用提取到的密钥材料,并通过 IPv6 来创建连接到目标设备的 SSH 连接。这个漏洞仅能通过 IPv6 来进行利用,IPv4 不会被攻击”。
+
+型号为 Nexus 9000 系列且 NX-OS 软件版本在 14.1 之前的设备会受此漏洞的影响,该公司表示没有解决这个问题的变通办法。
+
+然而,思科公司已经为解决这个漏洞[发布了免费的软件更新][4]。
+
+该公司同样对 Nexus 9000 系列发布了一个“高危”级别的安全预警报告,报告中表示存在一种攻击,允许攻击者以 root 用户权限在受影响的设备上执行任意操作系统命令。思科表示,如果要用这种方式攻击成功,攻击者需要对应设备的有效的管理员用户凭证。
+
+[思科表示][5],这个漏洞是由于过于宽泛的系统文件权限造成的。攻击者可以通过向受影响的设备进行认证,构造一个精心设计的命令字符串,并将这个字符串写入到特定位置的文件里。攻击者通过这种方式来利用这个漏洞。
+
+思科发布了解决这个漏洞的软件更新。
+
+另外两个被评为“高危”级别的漏洞的影响范围同样包括 Nexus 9000 系列:
+
+- 思科 Nexus 9000 系列软件后台操作功能中的[漏洞][7],能够允许一个已认证的本地攻击者在受影响的设备上提权到 root 权限。这个漏洞是由于在受影响的设备上用户提供的文件验证不充分。思科表示,攻击者可以通过登录到受影响设备的命令行界面,并在文件系统的特定目录中构造一个精心设计过的文件,以此来利用这个漏洞。
+- 交换机软件后台操作功能中的[弱点][7]能够允许攻击者登录到受影响设备的命令行界面,并在文件系统的特定目录里创建一个精心构造过的文件。思科表示,这个漏洞是由于在受影响的设备上用户提供的文件验证不充分。
+
+思科同样为这些漏洞[发布了软件更新][4]。
+
+此外,这些安全警告中的一部分是针对思科 FirePower 防火墙系列中大量的“高危”漏洞警告。
+
+例如,思科[写道][8],思科 Firepower 威胁防御软件的 SMB 协议预处理检测引擎中的多个漏洞能够允许未认证的相邻、远程攻击者造成拒绝服务攻击(DoS)的情况。
+
+思科表示,思科 Firepower 2100 系列中思科 Firepower 软件里的内部数据包处理功能有[另一个漏洞][9],能够让未认证的远程攻击者造成受影响的设备停止处理流量,从而导致 DOS 的情况。
+
+[软件补丁][4]可用于这些漏洞。
+
+其他的产品,比如思科[自适应安全虚拟设备][10]和 [web 安全设备][11]同样也有高优先级的补丁。
+
+--------------------------------------------------------------------------------
+
+via: https://www.networkworld.com/article/3392858/cisco-issues-critical-security-warning-for-nexus-data-center-switches.html
+
+作者:[Michael Cooney][a]
+选题:[lujun9972][b]
+译者:[hopefully2333](https://github.com/hopefully2333)
+校对:[wxy](https://github.com/wxy)
+
+本文由 [LCTT](https://github.com/LCTT/TranslateProject) 原创编译,[Linux中国](https://linux.cn/) 荣誉推出
+
+[a]: https://www.networkworld.com/author/Michael-Cooney/
+[b]: https://github.com/lujun9972
+[1]: https://images.idgesg.net/images/article/2018/02/lock_broken_unlocked_binary_code_security_circuits_protection_privacy_thinkstock_873916354-100750739-large.jpg
+[2]: https://tools.cisco.com/security/center/content/CiscoSecurityAdvisory/cisco-sa-20190501-nexus9k-sshkey
+[3]: https://www.networkworld.com/article/3284352/data-center/how-to-plan-a-software-defined-data-center-network.html
+[4]: https://www.cisco.com/c/en/us/about/legal/cloud-and-software/end_user_license_agreement.html
+[5]: https://tools.cisco.com/security/center/content/CiscoSecurityAdvisory/cisco-sa-20190501-nexus9k-rpe
+[6]: https://pluralsight.pxf.io/c/321564/424552/7490?u=https%3A%2F%2Fwww.pluralsight.com%2Fpaths%2Fcertified-information-systems-security-professional-cisspr
+[7]: https://tools.cisco.com/security/center/content/CiscoSecurityAdvisory/cisco-sa-20190501-aci-hw-clock-util
+[8]: https://tools.cisco.com/security/center/content/CiscoSecurityAdvisory/cisco-sa-20190501-frpwr-smb-snort
+[9]: https://tools.cisco.com/security/center/content/CiscoSecurityAdvisory/cisco-sa-20190501-frpwr-dos
+[10]: https://tools.cisco.com/security/center/content/CiscoSecurityAdvisory/cisco-sa-20190501-asa-ipsec-dos
+[11]: https://tools.cisco.com/security/center/content/CiscoSecurityAdvisory/cisco-sa-20190501-wsa-privesc
+[12]: https://www.facebook.com/NetworkWorld/
+[13]: https://www.linkedin.com/company/network-world
diff --git a/published/201905/20190501 Write faster C extensions for Python with Cython.md b/published/201905/20190501 Write faster C extensions for Python with Cython.md
new file mode 100644
index 0000000000..b3ff2f0edd
--- /dev/null
+++ b/published/201905/20190501 Write faster C extensions for Python with Cython.md
@@ -0,0 +1,81 @@
+[#]: collector: (lujun9972)
+[#]: translator: (geekpi)
+[#]: reviewer: (wxy)
+[#]: publisher: (wxy)
+[#]: url: (https://linux.cn/article-10859-1.html)
+[#]: subject: (Write faster C extensions for Python with Cython)
+[#]: via: (https://opensource.com/article/19/5/python-cython)
+[#]: author: (Moshe Zadka https://opensource.com/users/moshez/users/moshez/users/foundjem/users/jugmac00)
+
+使用 Cython 为 Python 编写更快的 C 扩展
+======
+
+> 在我们这个包含了 7 个 PyPI 库的系列文章中学习解决常见的 Python 问题的方法。
+
+
+
+Python 是当今使用最多的[流行编程语言][2]之一,因为:它是开源的,它有广泛的用途(例如 Web 编程、业务应用、游戏、科学编程等等),它有一个充满活力和专注的社区支持它。这个社区可以让我们在 [Python Package Index][3](PyPI)中有如此庞大、多样化的软件包,用以扩展和改进 Python 并解决不可避免的问题。
+
+在本系列中,我们将介绍七个可以帮助你解决常见 Python 问题的 PyPI 库。首先是 [Cython][4],一个简化 Python 编写 C 扩展的语言。
+
+### Cython
+
+使用 Python 很有趣,但有时,用它编写的程序可能很慢。所有的运行时动态调度会带来很大的代价:有时它比用 C 或 Rust 等系统语言编写的等效代码慢 10 倍。
+
+将代码迁移到一种全新的语言可能会在成本和可靠性方面付出巨大代价:所有的手工重写工作都将不可避免地引入错误。我们可以两者兼得么?
+
+为了练习一下优化,我们需要一些慢代码。有什么比斐波那契数列的意外指数实现更慢?
+
+```
+def fib(n):
+ if n < 2:
+ return 1
+ return fib(n-1) + fib(n-2)
+```
+
+由于对 `fib` 的调用会导致两次再次调用,因此这种效率极低的算法需要很长时间才能执行。例如,在我的新笔记本电脑上,`fib(36)` 需要大约 4.5 秒。这个 4.5 秒会成为我们探索 Python 的 Cython 扩展能提供的帮助的基准。
+
+使用 Cython 的正确方法是将其集成到 `setup.py` 中。然而,使用 `pyximport` 可以快速地进行尝试。让我们将 `fib` 代码放在 `fib.pyx` 中并使用 Cython 运行它。
+
+```
+>>> import pyximport; pyximport.install()
+>>> import fib
+>>> fib.fib(36)
+```
+
+只使用 Cython 而不*修改*代码,这个算法在我笔记本上花费的时间减少到大约 2.5 秒。几乎无需任何努力,这几乎减少了 50% 的运行时间。当然,得到了一个不错的成果。
+
+加把劲,我们可以让它变得更快。
+
+```
+cpdef int fib(int n):
+ if n < 2:
+ return 1
+ return fib(n - 1) + fib(n - 2)
+```
+
+我们将 `fib` 中的代码变成用 `cpdef` 定义的函数,并添加了两个类型注释:它接受一个整数并返回一个整数。
+
+这个变得快*多*了,大约只用了 0.05 秒。它是如此之快,以至于我可能开始怀疑我的测量方法包含噪声:之前,这种噪声在信号中丢失了。
+
+当下次你的 Python 代码花费太多 CPU 时间时,也许会导致风扇狂转,为何不看看 Cython 是否可以解决问题呢?
+
+在本系列的下一篇文章中,我们将看一下 Black,一个自动纠正代码格式错误的项目。
+
+--------------------------------------------------------------------------------
+
+via: https://opensource.com/article/19/5/python-cython
+
+作者:[Moshe Zadka][a]
+选题:[lujun9972][b]
+译者:[geekpi](https://github.com/geekpi)
+校对:[wxy](https://github.com/wxy)
+
+本文由 [LCTT](https://github.com/LCTT/TranslateProject) 原创编译,[Linux中国](https://linux.cn/) 荣誉推出
+
+[a]: https://opensource.com/users/moshez/users/moshez/users/foundjem/users/jugmac00
+[b]: https://github.com/lujun9972
+[1]: https://opensource.com/sites/default/files/styles/image-full-size/public/lead-images/code_hand_draw.png?itok=dpAf--Db (Hand drawing out the word "code")
+[2]: https://opensource.com/article/18/5/numbers-python-community-trends
+[3]: https://pypi.org/
+[4]: https://pypi.org/project/Cython/
diff --git a/published/201905/20190502 Format Python however you like with Black.md b/published/201905/20190502 Format Python however you like with Black.md
new file mode 100644
index 0000000000..dd56785451
--- /dev/null
+++ b/published/201905/20190502 Format Python however you like with Black.md
@@ -0,0 +1,99 @@
+[#]: collector: (lujun9972)
+[#]: translator: (geekpi)
+[#]: reviewer: (wxy)
+[#]: publisher: (wxy)
+[#]: url: (https://linux.cn/article-10864-1.html)
+[#]: subject: (Format Python however you like with Black)
+[#]: via: (https://opensource.com/article/19/5/python-black)
+[#]: author: (Moshe Zadka https://opensource.com/users/moshez/users/moshez/users/moshez)
+
+使用 Black 自由格式化 Python
+======
+
+> 在我们覆盖 7 个 PyPI 库的系列文章中了解解决 Python 问题的更多信息。
+
+
+
+Python 是当今使用最多的[流行编程语言][2]之一,因为:它是开源的,它有广泛的用途(例如 Web 编程、业务应用、游戏、科学编程等等),它有一个充满活力和专注的社区支持它。这个社区可以让我们在 [Python Package Index][3](PyPI)中有如此庞大、多样化的软件包,用以扩展和改进 Python 并解决不可避免的问题。
+
+在本系列中,我们将介绍七个可以帮助你解决常见 Python 问题的 PyPI 库。在第一篇文章中,我们了解了 [Cython][4]。今天,我们将使用 [Black][5] 这个代码格式化工具。
+
+### Black
+
+有时创意可能是一件美妙的事情。有时它只是一种痛苦。我喜欢创造性地解决难题,但我希望我的 Python 格式尽可能一致。没有人对使用“有趣”缩进的代码印象深刻。
+
+但是比不一致的格式更糟糕的是除了检查格式之外什么都没有做的代码审查。这对审查者来说很烦人,对于被审查者来说甚至更烦人。当你的 linter 告诉你代码缩进不正确时,但没有提示*正确*的缩进量,这也会令人气愤。
+
+使用 Black,它不会告诉你*要*做什么,它是一个优良、勤奋的机器人:它将为你修复代码。
+
+要了解它如何工作的,请随意写一些非常不一致的内容,例如:
+
+```
+def add(a, b): return a+b
+
+def mult(a, b):
+ return \
+ a * b
+```
+
+Black 抱怨了么?并没有,它为你修复了!
+
+```
+$ black math
+reformatted math
+All done! ✨ 🍰 ✨
+1 file reformatted.
+$ cat math
+def add(a, b):
+ return a + b
+
+
+def mult(a, b):
+ return a * b
+```
+
+Black 确实提供了报错而不是修复的选项,甚至还有输出 diff 编辑样式的选项。这些选项在持续集成 (CI)系统中非常有用,可以在本地强制运行 Black。此外,如果 diff 输出被记录到 CI 输出中,你可以直接将其粘贴到 `patch` 中,以便在极少数情况下你需要修复输出,但无法本地安装 Black 使用。
+
+
+```
+$ black --check --diff bad
+--- math 2019-04-09 17:24:22.747815 +0000
++++ math 2019-04-09 17:26:04.269451 +0000
+@@ -1,7 +1,7 @@
+-def add(a, b): return a + b
++def add(a, b):
++ return a + b
+
+
+ def mult(a, b):
+- return \
+- a * b
++ return a * b
+
+would reformat math
+All done! 💥 💔 💥
+1 file would be reformatted.
+$ echo $?
+1
+```
+
+在本系列的下一篇文章中,我们将介绍 attrs ,这是一个可以帮助你快速编写简洁、正确的代码的库。
+
+--------------------------------------------------------------------------------
+
+via: https://opensource.com/article/19/5/python-black
+
+作者:[Moshe Zadka][a]
+选题:[lujun9972][b]
+译者:[geekpi](https://github.com/geekpi)
+校对:[wxy](https://github.com/wxy)
+
+本文由 [LCTT](https://github.com/LCTT/TranslateProject) 原创编译,[Linux中国](https://linux.cn/) 荣誉推出
+
+[a]: https://opensource.com/users/moshez/users/moshez/users/moshez
+[b]: https://github.com/lujun9972
+[1]: https://opensource.com/sites/default/files/styles/image-full-size/public/lead-images/openstack_python_vim_1.jpg?itok=lHQK5zpm (OpenStack source code (Python) in VIM)
+[2]: https://opensource.com/article/18/5/numbers-python-community-trends
+[3]: https://pypi.org/
+[4]: https://opensource.com/article/19/4/7-python-problems-solved-cython
+[5]: https://pypi.org/project/black/
diff --git a/published/201905/20190502 Get started with Libki to manage public user computer access.md b/published/201905/20190502 Get started with Libki to manage public user computer access.md
new file mode 100644
index 0000000000..347196d553
--- /dev/null
+++ b/published/201905/20190502 Get started with Libki to manage public user computer access.md
@@ -0,0 +1,61 @@
+[#]: collector: (lujun9972)
+[#]: translator: (geekpi)
+[#]: reviewer: (wxy)
+[#]: publisher: (wxy)
+[#]: url: (https://linux.cn/article-10880-1.html)
+[#]: subject: (Get started with Libki to manage public user computer access)
+[#]: via: (https://opensource.com/article/19/5/libki-computer-access)
+[#]: author: (Don Watkins https://opensource.com/users/don-watkins/users/tony-thomas)
+
+使用 Libki 来管理公共用户访问计算机
+======
+> Libki 是一个跨平台的计算机预约和用时管理系统。
+
+
+
+提供公共计算机的图书馆、学校、学院和其他组织需要一种管理用户访问权限的好方法 —— 否则,就无法阻止某些人独占机器并确保每个人都有公平的用时。这是 [Libki][2] 要解决的问题。
+
+Libki 是一个面向 Windows 和 Linux PC 的开源、跨平台的计算机预约和用时管理系统。它提供了一个基于 Web 的服务器和一个基于 Web 的管理系统,员工可以使用它来管理计算机访问,包括创建和删除用户、设置帐户用时限制、登出和禁止用户以及设置访问限制。
+
+根据其首席开发人员 [Kyle Hall][3] 所说,Libki 主要用于 PC 用时控制,作为 Envisionware 出品的专有计算机访问控制软件的开源替代品。当用户登录 Libki 管理的计算机时,他们会有一段使用计算机的时间。时间到了之后,他们就会被登出。时间默认设置为 45 分钟,但可以使用基于 Web 的管理系统轻松调整。一些组织在登出用户之前提供 24 小时访问权限,而有的组织则使用它来跟踪使用情况而不设置用时限制。
+
+Kyle 目前是 [ByWater Solutions][4] 的首席开发人员,该公司为图书馆提供开源软件解决方案(包括 Libki)。在职业生涯早期,他在宾夕法尼亚州的[米德维尔公共图书馆][5]担任 IT 技术时开发了 Libki。在其他员工的午休期间,偶尔会要求他关注孩子们的房间。图书馆使用纸质注册表来管理对儿童房间计算机的访问,这意味着不断的监督和检查,以确保来到那里的人能够公平地使用。
+
+Kyle 说,“我发现这很笨拙而不便的,我想找到一个解决方案。这个解决方案需要同时是 FOSS 和跨平台的。最后,没有现有的软件适合我们的特殊需求,那就是为什么我开发了 Libki。“
+
+或者,正如 Libki 的网站所宣称的那样,“Libki 的诞生是为了避免与青少年打交道(的麻烦),现在允许图书馆员避免与世界各地的青少年打交道(的麻烦)!”
+
+### 易于安装和使用
+
+我最近决定在我经常在那里做志愿者的当地的公共图书馆尝试 Libki。我按照[文档][6]在 Ubuntu 18.04 Server 中自动进行了安装,它很快就启动起来了。
+
+我计划在我们当地的图书馆支持 Libki,但我想知道在那些没有 IT 相关经验的人或者无法构建和部署服务器的图书馆是怎样的。Kyle 说:“ByWater Solutions 可以云端托管 Libki 服务器,这使得每个人的维护和管理变得更加简单。”
+
+Kyle 表示,ByWater 并不打算将 Libki 与其最受欢迎的产品,开源集成图书馆系统 (ILS)Koha 或其支持的任何其他[项目][7]捆绑在一起。他说: “Libki 和 Koha 是不同[类型]的软件,满足不同的需求,但它们在图书馆中确实很好地协同工作。事实上,我很早就开发了 Libki 的 SIP2 集成,因此它可以支持使用 Koha 进行单点登录。“
+
+### 如何贡献
+
+Libki 客户端是 GPLv3 许可,Libki 服务器是 AGPLv3 许可。Kyle 说他希望 Libki 拥有一个更加活跃和强大的社区,项目一直在寻找新人加入其[贡献者][8]。如果你想参加,请访问 [Libki 社区页面][9]并加入邮件列表。
+
+--------------------------------------------------------------------------------
+
+via: https://opensource.com/article/19/5/libki-computer-access
+
+作者:[Don Watkins][a]
+选题:[lujun9972][b]
+译者:[geekpi](https://github.com/geekpi)
+校对:[wxy](https://github.com/wxy)
+
+本文由 [LCTT](https://github.com/LCTT/TranslateProject) 原创编译,[Linux中国](https://linux.cn/) 荣誉推出
+
+[a]: https://opensource.com/users/don-watkins/users/tony-thomas
+[b]: https://github.com/lujun9972
+[1]: https://opensource.com/sites/default/files/styles/image-full-size/public/lead-images/desk_clock_job_work.jpg?itok=Nj4fuhl6
+[2]: https://libki.org/
+[3]: https://www.linkedin.com/in/kylemhallinfo/
+[4]: https://opensource.com/article/19/4/software-libraries
+[5]: https://meadvillelibrary.org/
+[6]: https://manual.libki.org/master/libki-manual.html#_automatic_installation
+[7]: https://bywatersolutions.com/projects
+[8]: https://github.com/Libki/libki-server/graphs/contributors
+[9]: https://libki.org/community/
diff --git a/published/201905/20190503 API evolution the right way.md b/published/201905/20190503 API evolution the right way.md
new file mode 100644
index 0000000000..069687be7a
--- /dev/null
+++ b/published/201905/20190503 API evolution the right way.md
@@ -0,0 +1,693 @@
+[#]: collector: (lujun9972)
+[#]: translator: (MjSeven)
+[#]: reviewer: (wxy)
+[#]: publisher: (wxy)
+[#]: url: (https://linux.cn/article-10900-1.html)
+[#]: subject: (API evolution the right way)
+[#]: via: (https://opensource.com/article/19/5/api-evolution-right-way)
+[#]: author: (A. Jesse https://opensource.com/users/emptysquare)
+
+API 演进的正确方式
+======
+
+> 负责任的库作者与其用户的十个约定。
+
+
+
+想象一下你是一个造物主,为一个生物设计一个身体。出于仁慈,你希望它能随着时间进化:首先,因为它必须对环境的变化作出反应;其次,因为你的智慧在增长,你对这个小东西想到了更好的设计,它不应该永远保持一个样子。
+
+![Serpents][2]
+
+然而,这个生物可能有赖于其目前解剖学的特征。你不能无所顾忌地添加翅膀或改变它的身材比例。它需要一个有序的过程来适应新的身体。作为一个负责任的设计者,你如何才能温柔地引导这种生物走向更大的进步呢?
+
+对于负责任的库维护者也是如此。我们向依赖我们代码的人保证我们的承诺:我们会发布 bug 修复和有用的新特性。如果对库的未来有利,我们有时会删除某些特性。我们会不断创新,但我们不会破坏使用我们库的人的代码。我们怎样才能一次实现所有这些目标呢?
+
+### 添加有用的特性
+
+你的库不应该永远保持不变:你应该添加一些特性,使你的库更适合用户。例如,如果你有一个爬行动物类,并且如果有个可以飞行的翅膀是有用的,那就去添加吧。
+
+```
+class Reptile:
+ @property
+ def teeth(self):
+ return 'sharp fangs'
+
+ # 如果 wings 是有用的,那就添加它!
+ @property
+ def wings(self):
+ return 'majestic wings'
+```
+
+但要注意,特性是有风险的。考虑 Python 标准库中以下功能,看看它出了什么问题。
+
+```
+bool(datetime.time(9, 30)) == True
+bool(datetime.time(0, 0)) == False
+```
+
+这很奇怪:将任何时间对象转换为布尔值都会得到 True,但午夜时间除外。(更糟糕的是,时区感知时间的规则更加奇怪。)
+
+我已经写了十多年的 Python 了,但直到上周才发现这条规则。这种奇怪的行为会在用户代码中引起什么样的 bug?
+
+比如说一个日历应用程序,它带有一个创建事件的函数。如果一个事件有一个结束时间,那么函数也应该要求它有一个开始时间。
+
+```
+def create_event(day,
+ start_time=None,
+ end_time=None):
+ if end_time and not start_time:
+ raise ValueError("Can't pass end_time without start_time")
+
+# 女巫集会从午夜一直开到凌晨 4 点
+create_event(datetime.date.today(),
+ datetime.time(0, 0),
+ datetime.time(4, 0))
+```
+
+不幸的是,对于女巫来说,从午夜开始的事件无法通过校验。当然,一个了解午夜怪癖的细心程序员可以正确地编写这个函数。
+
+```
+def create_event(day,
+ start_time=None,
+ end_time=None):
+ if end_time is not None and start_time is None:
+ raise ValueError("Can't pass end_time without start_time")
+```
+
+但这种微妙之处令人担忧。如果一个库作者想要创建一个伤害用户的 API,那么像午夜的布尔转换这样的“特性”很有效。
+
+![Man being chased by an alligator][3]
+
+但是,负责任的创建者的目标是使你的库易于正确使用。
+
+这个功能是由 Tim Peters 在 2002 年首次编写 datetime 模块时造成的。即时是像 Tim 这样的奠基 Python 的高手也会犯错误。[这个怪异之处后来被消除了][4],现在所有时间的布尔值都是 True。
+
+```
+# Python 3.5 以后
+
+bool(datetime.time(9, 30)) == True
+bool(datetime.time(0, 0)) == True
+```
+
+不知道午夜怪癖的古怪之处的程序员现在可以从这种晦涩的 bug 中解脱出来,但是一想到任何依赖于古怪的旧行为的代码现在没有注意变化,我就会感到紧张。如果从来没有实现这个糟糕的特性,情况会更好。这就引出了库维护者的第一个承诺:
+
+#### 第一个约定:避免糟糕的特性
+
+最痛苦的变化是你必须删除一个特性。一般来说,避免糟糕特性的一种方法是少添加特性!没有充分的理由,不要使用公共方法、类、功能或属性。因此:
+
+#### 第二个约定:最小化特性
+
+特性就像孩子:在充满激情的瞬间孕育,但是它们必须要支持多年(LCTT 译注:我怀疑作者在开车,可是我没有证据)。不要因为你能做傻事就去做傻事。不要画蛇添足!
+
+![Serpents with and without feathers][5]
+
+但是,当然,在很多情况下,用户需要你的库中尚未提供的东西,你如何选择合适的功能给他们?以下另一个警示故事。
+
+### 一个来自 asyncio 的警示故事
+
+你可能知道,当你调用一个协程函数,它会返回一个协程对象:
+
+```
+async def my_coroutine():
+ pass
+
+print(my_coroutine())
+```
+
+```
+
+```
+
+你的代码必须 “等待” 这个对象以此来运行协程。人们很容易忘记这一点,所以 asyncio 的开发人员想要一个“调试模式”来捕捉这个错误。当协程在没有等待的情况下被销毁时,调试模式将打印一个警告,并在其创建的行上进行回溯。
+
+当 Yury Selivanov 实现调试模式时,他添加了一个“协程装饰器”的基础特性。装饰器是一个函数,它接收一个协程并返回任何内容。Yury 使用它在每个协程上接入警告逻辑,但是其他人可以使用它将协程转换为字符串 “hi!”。
+
+```
+import sys
+
+def my_wrapper(coro):
+ return 'hi!'
+
+sys.set_coroutine_wrapper(my_wrapper)
+
+async def my_coroutine():
+ pass
+
+print(my_coroutine())
+```
+
+```
+hi!
+```
+
+这是一个地狱般的定制。它改变了 “异步" 的含义。调用一次 `set_coroutine_wrapper` 将在全局永久改变所有的协程函数。正如 [Nathaniel Smith 所说][6]:“一个有问题的 API” 很容易被误用,必须被删除。如果 asyncio 开发人员能够更好地按照其目标来设计该特性,他们就可以避免删除该特性的痛苦。负责任的创建者必须牢记这一点:
+
+#### 第三个约定:保持特性单一
+
+幸运的是,Yury 有良好的判断力,他将该特性标记为临时,所以 asyncio 用户知道不能依赖它。Nathaniel 可以用更单一的功能替换 `set_coroutine_wrapper`,该特性只定制回溯深度。
+
+```
+import sys
+
+sys.set_coroutine_origin_tracking_depth(2)
+
+async def my_coroutine():
+ pass
+
+print(my_coroutine())
+
+```
+
+```
+
+
+RuntimeWarning:'my_coroutine' was never awaited
+
+Coroutine created at (most recent call last)
+ File "script.py", line 8, in
+ print(my_coroutine())
+```
+
+这样好多了。没有可以更改协程的类型的其他全局设置,因此 asyncio 用户无需编写防御代码。造物主应该像 Yury 一样有远见。
+
+#### 第四个约定:标记实验特征“临时”
+
+如果你只是预感你的生物需要犄角和四叉舌,那就引入这些特性,但将它们标记为“临时”。
+
+![Serpent with horns][7]
+
+你可能会发现犄角是无关紧要的,但是四叉舌是有用的。在库的下一个版本中,你可以删除前者并标记后者为正式的。
+
+### 删除特性
+
+无论我们如何明智地指导我们的生物进化,总会有一天想要删除一个正式特征。例如,你可能已经创建了一只蜥蜴,现在你选择删除它的腿。也许你想把这个笨拙的家伙变成一条时尚而现代的蟒蛇。
+
+![Lizard transformed to snake][8]
+
+删除特性主要有两个原因。首先,通过用户反馈或者你自己不断增长的智慧,你可能会发现某个特性是个坏主意。午夜怪癖的古怪行为就是这种情况。或者,最初该特性可能已经很好地适应了你的库环境,但现在生态环境发生了变化,也许另一个神发明了哺乳动物,你的生物想要挤进哺乳动物的小洞穴里,吃掉里面美味的哺乳动物,所以它不得不失去双腿。
+
+![A mouse][9]
+
+同样,Python 标准库会根据语言本身的变化删除特性。考虑 asyncio 的 Lock 功能,在把 `await` 作为一个关键字添加进来之前,它一直在等待:
+
+```
+lock = asyncio.Lock()
+
+async def critical_section():
+ await lock
+ try:
+ print('holding lock')
+ finally:
+ lock.release()
+```
+
+但是现在,我们可以做“异步锁”:
+
+
+```
+lock = asyncio.Lock()
+
+async def critical_section():
+ async with lock:
+ print('holding lock')
+```
+
+新方法好多了!很短,并且在一个大函数中使用其他 try-except 块时不容易出错。因为“尽量找一种,最好是唯一一种明显的解决方案”,[旧语法在 Python 3.7 中被弃用][10],并且很快就会被禁止。
+
+不可避免的是,生态变化会对你的代码产生影响,因此要学会温柔地删除特性。在此之前,请考虑删除它的成本或好处。负责任的维护者不会愿意让用户更改大量代码或逻辑。(还记得 Python 3 在重新添加会 `u` 字符串前缀之前删除它是多么痛苦吗?)如果代码删除是机械性的动作,就像一个简单的搜索和替换,或者如果该特性是危险的,那么它可能值得删除。
+
+#### 是否删除特性
+
+![Balance scales][11]
+
+反对 | 支持
+---|---
+代码必须改变 | 改变是机械性的
+逻辑必须改变 | 特性是危险的
+
+就我们饥饿的蜥蜴而言,我们决定删除它的腿,这样它就可以滑进老鼠洞里吃掉它。我们该怎么做呢?我们可以删除 `walk` 方法,像下面一样修改代码:
+
+```
+class Reptile:
+ def walk(self):
+ print('step step step')
+```
+
+变成这样:
+
+```
+class Reptile:
+ def slither(self):
+ print('slide slide slide')
+```
+
+这不是一个好主意,这个生物习惯于走路!或者,就库而言,你的用户拥有依赖于现有方法的代码。当他们升级到最新库版本时,他们的代码将会崩溃。
+
+```
+# 用户的代码,哦,不!
+Reptile.walk()
+```
+
+因此,负责任的创建者承诺:
+
+#### 第五条预定:温柔地删除
+
+温柔地删除一个特性需要几个步骤。从用腿走路的蜥蜴开始,首先添加新方法 `slither`。接下来,弃用旧方法。
+
+```
+import warnings
+
+class Reptile:
+ def walk(self):
+ warnings.warn(
+ "walk is deprecated, use slither",
+ DeprecationWarning, stacklevel=2)
+ print('step step step')
+
+ def slither(self):
+ print('slide slide slide')
+```
+
+Python 的 warnings 模块非常强大。默认情况下,它会将警告输出到 stderr,每个代码位置只显示一次,但你可以禁用警告或将其转换为异常,以及其它选项。
+
+一旦将这个警告添加到库中,PyCharm 和其他 IDE 就会使用删除线呈现这个被弃用的方法。用户马上就知道该删除这个方法。
+
+> Reptile().~~walk()~~
+
+当他们使用升级后的库运行代码时会发生什么?
+
+```
+$ python3 script.py
+
+DeprecationWarning: walk is deprecated, use slither
+ script.py:14: Reptile().walk()
+
+step step step
+```
+
+默认情况下,他们会在 stderr 上看到警告,但脚本会成功并打印 “step step step”。警告的回溯显示必须修复用户代码的哪一行。(这就是 `stacklevel` 参数的作用:它显示了用户需要更改的调用,而不是库中生成警告的行。)请注意,错误消息有指导意义,它描述了库用户迁移到新版本必须做的事情。
+
+你的用户可能会希望测试他们的代码,并证明他们没有调用弃用的库方法。仅警告不会使单元测试失败,但异常会失败。Python 有一个命令行选项,可以将弃用警告转换为异常。
+
+```
+> python3 -Werror::DeprecationWarning script.py
+
+Traceback (most recent call last):
+ File "script.py", line 14, in
+ Reptile().walk()
+ File "script.py", line 8, in walk
+ DeprecationWarning, stacklevel=2)
+DeprecationWarning: walk is deprecated, use slither
+```
+
+现在,“step step step” 没有输出出来,因为脚本以一个错误终止。
+
+因此,一旦你发布了库的一个版本,该版本会警告已启用的 `walk` 方法,你就可以在下一个版本中安全地删除它。对吧?
+
+考虑一下你的库用户在他们项目的 `requirements` 中可能有什么。
+
+```
+# 用户的 requirements.txt 显示 reptile 包的依赖关系
+reptile
+```
+
+下次他们部署代码时,他们将安装最新版本的库。如果他们尚未处理所有的弃用,那么他们的代码将会崩溃,因为代码仍然依赖 `walk`。你需要温柔一点,你必须向用户做出三个承诺:维护更改日志,选择版本化方案和编写升级指南。
+
+#### 第六个约定:维护变更日志
+
+你的库必须有更改日志,其主要目的是宣布用户所依赖的功能何时被弃用或删除。
+
+> **版本 1.1 中的更改**
+>
+> **新特性**
+>
+> * 新功能 Reptile.slither()
+>
+> **弃用**
+>
+> * Reptile.walk() 已弃用,将在 2.0 版本中删除,请使用 slither()
+
+负责任的创建者会使用版本号来表示库发生了怎样的变化,以便用户能够对升级做出明智的决定。“版本化方案”是一种用于交流变化速度的语言。
+
+#### 第七个约定:选择一个版本化方案
+
+有两种广泛使用的方案,[语义版本控制][12]和基于时间的版本控制。我推荐任何库都进行语义版本控制。Python 的风格在 [PEP 440][13] 中定义,像 `pip` 这样的工具可以理解语义版本号。
+
+如果你为库选择语义版本控制,你可以使用版本号温柔地删除腿,例如:
+
+> 1.0: 第一个“稳定”版,带有 `walk()`
+> 1.1: 添加 `slither()`,废弃 `walk()`
+> 2.0: 删除 `walk()`
+
+你的用户依赖于你的库的版本应该有一个范围,例如:
+
+```
+# 用户的 requirements.txt
+reptile>=1,<2
+```
+
+这允许他们在主要版本中自动升级,接收错误修正并可能引发一些弃用警告,但不会升级到**下**个主要版本并冒着更改破坏其代码的风险。
+
+如果你遵循基于时间的版本控制,则你的版本可能会编号:
+
+> 2017.06.0: 2017 年 6 月的版本
+> 2018.11.0: 添加 `slither()`,废弃 `walk()`
+> 2019.04.0: 删除 `walk()`
+
+用户可以这样依赖于你的库:
+
+```
+# 用户的 requirements.txt,基于时间控制的版本
+reptile==2018.11.*
+```
+
+这非常棒,但你的用户如何知道你的版本方案,以及如何测试代码来进行弃用呢?你必须告诉他们如何升级。
+
+#### 第八个约定:写一个升级指南
+
+下面是一个负责任的库创建者如何指导用户:
+
+> **升级到 2.0**
+>
+> **从弃用的 API 迁移**
+>
+> 请参阅更改日志以了解已弃用的特性。
+>
+> **启用弃用警告**
+>
+> 升级到 1.1 并使用以下代码测试代码:
+>
+> `python -Werror::DeprecationWarning`
+>
+> 现在可以安全地升级了。
+
+你必须通过向用户显示命令行选项来教会用户如何处理弃用警告。并非所有 Python 程序员都知道这一点 —— 我自己就每次都得查找这个语法。注意,你必须*发布*一个版本,它输出来自每个弃用的 API 的警告,以便用户可以在再次升级之前使用该版本进行测试。在本例中,1.1 版本是小版本。它允许你的用户逐步重写代码,分别修复每个弃用警告,直到他们完全迁移到最新的 API。他们可以彼此独立地测试代码和库的更改,并隔离 bug 的原因。
+
+如果你选择语义版本控制,则此过渡期将持续到下一个主要版本,从 1.x 到 2.0,或从 2.x 到 3.0 以此类推。删除生物腿部的温柔方法是至少给它一个版本来调整其生活方式。不要一次性把腿删掉!
+
+![A skink][14]
+
+版本号、弃用警告、更改日志和升级指南可以协同工作,在不违背与用户约定的情况下温柔地改进你的库。[Twisted 项目的兼容性政策][15] 解释的很漂亮:
+
+> “先行者总是自由的”
+>
+> 运行的应用程序在没有任何警告的情况下都可以升级为 Twisted 的一个次要版本。
+>
+> 换句话说,任何运行其测试而不触发 Twisted 警告的应用程序应该能够将其 Twisted 版本升级至少一次,除了可能产生新警告之外没有任何不良影响。
+>
+
+现在,我们的造物主已经获得了智慧和力量,可以通过添加方法来添加特性,并温柔地删除它们。我们还可以通过添加参数来添加特性,但这带来了新的难度。你准备好了吗?
+
+### 添加参数
+
+想象一下,你只是给了你的蛇形生物一对翅膀。现在你必须允许它选择是滑行还是飞行。目前它的 `move` 功能只接受一个参数。
+
+```
+# 你的库代码
+def move(direction):
+ print(f'slither {direction}')
+
+# 用户的应用
+move('north')
+```
+
+你想要添加一个 `mode` 参数,但如果用户升级库,这会破坏他们的代码,因为他们只传递了一个参数。
+
+```
+# 你的库代码
+def move(direction, mode):
+ assert mode in ('slither', 'fly')
+ print(f'{mode} {direction}')
+
+# 一个用户的代码,出现错误!
+move('north')
+```
+
+一个真正聪明的创建者者会承诺不会以这种方式破坏用户的代码。
+
+#### 第九条约定:兼容地添加参数
+
+要保持这个约定,请使用保留原始行为的默认值添加每个新参数。
+
+```
+# 你的库代码
+def move(direction, mode='slither'):
+ assert mode in ('slither', 'fly')
+ print(f'{mode} {direction}')
+
+# 用户的应用
+move('north')
+```
+
+随着时间推移,参数是函数演化的自然历史。它们首先列出最老的参数,每个都有默认值。库用户可以传递关键字参数以选择特定的新行为,并接受所有其他行为的默认值。
+
+```
+# 你的库代码
+def move(direction,
+ mode='slither',
+ turbo=False,
+ extra_sinuous=False,
+ hail_lyft=False):
+ # ...
+
+# 用户应用
+move('north', extra_sinuous=True)
+```
+
+但是有一个危险,用户可能会编写如下代码:
+
+```
+# 用户应用,简写
+move('north', 'slither', False, True)
+```
+
+如果在你在库的下一个主要版本中去掉其中一个参数,例如 `turbo`,会发生什么?
+
+```
+# 你的库代码,下一个主要版本中 "turbo" 被删除
+def move(direction,
+ mode='slither',
+ extra_sinuous=False,
+ hail_lyft=False):
+ # ...
+
+# 用户应用,简写
+move('north', 'slither', False, True)
+```
+
+用户的代码仍然能编译,这是一件坏事。代码停止了曲折的移动并开始招呼 Lyft,这不是它的本意。我相信你可以预测我接下来要说的内容:删除参数需要几个步骤。当然,首先弃用 `trubo` 参数。我喜欢这种技术,它可以检测任何用户的代码是否依赖于这个参数。
+
+```
+# 你的库代码
+_turbo_default = object()
+
+def move(direction,
+ mode='slither',
+ turbo=_turbo_default,
+ extra_sinuous=False,
+ hail_lyft=False):
+ if turbo is not _turbo_default:
+ warnings.warn(
+ "'turbo' is deprecated",
+ DeprecationWarning,
+ stacklevel=2)
+ else:
+ # The old default.
+ turbo = False
+```
+
+但是你的用户可能不会注意到警告。警告声音不是很大:它们可以在日志文件中被抑制或丢失。用户可能会漫不经心地升级到库的下一个主要版本——那个删除 `turbo` 的版本。他们的代码运行时将没有错误、默默做错误的事情!正如 Python 之禅所说:“错误绝不应该被默默 pass”。实际上,爬行动物的听力很差,所有当它们犯错误时,你必须非常大声地纠正它们。
+
+![Woman riding an alligator][16]
+
+保护用户的最佳方法是使用 Python 3 的星型语法,它要求调用者传递关键字参数。
+
+```
+# 你的库代码
+# 所有 “*” 后的参数必须以关键字方式传输。
+def move(direction,
+ *,
+ mode='slither',
+ turbo=False,
+ extra_sinuous=False,
+ hail_lyft=False):
+ # ...
+
+# 用户代码,简写
+# 错误!不能使用位置参数,关键字参数是必须的
+move('north', 'slither', False, True)
+```
+
+有了这个星,以下是唯一允许的语法:
+
+```
+# 用户代码
+move('north', extra_sinuous=True)
+```
+
+现在,当你删除 `turbo` 时,你可以确定任何依赖于它的用户代码都会明显地提示失败。如果你的库也支持 Python2,这没有什么大不了。你可以模拟星型语法([归功于 Brett Slatkin][17]):
+
+```
+# 你的库代码,兼容 Python 2
+def move(direction, **kwargs):
+ mode = kwargs.pop('mode', 'slither')
+ turbo = kwargs.pop('turbo', False)
+ sinuous = kwargs.pop('extra_sinuous', False)
+ lyft = kwargs.pop('hail_lyft', False)
+
+ if kwargs:
+ raise TypeError('Unexpected kwargs: %r'
+ % kwargs)
+
+# ...
+```
+
+要求关键字参数是一个明智的选择,但它需要远见。如果允许按位置传递参数,则不能仅在以后的版本中将其转换为仅关键字。所以,现在加上星号。你可以在 asyncio API 中观察到,它在构造函数、方法和函数中普遍使用星号。尽管到目前为止,`Lock` 只接受一个可选参数,但 asyncio 开发人员立即添加了星号。这是幸运的。
+
+```
+# In asyncio.
+class Lock:
+ def __init__(self, *, loop=None):
+ # ...
+```
+
+现在,我们已经获得了改变方法和参数的智慧,同时保持与用户的约定。现在是时候尝试最具挑战性的进化了:在不改变方法或参数的情况下改变行为。
+
+### 改变行为
+
+假设你创造的生物是一条响尾蛇,你想教它一种新行为。
+
+![Rattlesnake][18]
+
+横向移动!这个生物的身体看起来是一样的,但它的行为会发生变化。我们如何为这一进化步骤做好准备?
+
+![][19]
+
+*Image by HCA [[CC BY-SA 4.0][20]], [via Wikimedia Commons][21], 由 Opensource.com 修改*
+
+当行为在没有新函数或新参数的情况下发生更改时,负责任的创建者可以从 Python 标准库中学习。很久以前,os 模块引入了 `stat` 函数来获取文件统计信息,比如创建时间。起初,这个时间总是整数。
+
+```
+>>> os.stat('file.txt').st_ctime
+1540817862
+```
+
+有一天,核心开发人员决定在 `os.stat` 中使用浮点数来提供亚秒级精度。但他们担心现有的用户代码还没有做好准备更改。于是他们在 Python 2.3 中创建了一个设置 `stat_float_times`,默认情况下是 `False` 。用户可以将其设置为 True 来选择浮点时间戳。
+
+```
+>>> # Python 2.3.
+>>> os.stat_float_times(True)
+>>> os.stat('file.txt').st_ctime
+1540817862.598021
+```
+
+从 Python 2.5 开始,浮点时间成为默认值,因此 2.5 及之后版本编写的任何新代码都可以忽略该设置并期望得到浮点数。当然,你可以将其设置为 `False` 以保持旧行为,或将其设置为 `True` 以确保所有 Python 版本都得到浮点数,并为删除 `stat_float_times` 的那一天准备代码。
+
+多年过去了,在 Python 3.1 中,该设置已被弃用,以便为人们为遥远的未来做好准备,最后,经过数十年的旅程,[这个设置被删除][22]。浮点时间现在是唯一的选择。这是一个漫长的过程,但负责任的神灵是有耐心的,因为我们知道这个渐进的过程很有可能于意外的行为变化拯救用户。
+
+#### 第十个约定:逐渐改变行为
+
+以下是步骤:
+
+ * 添加一个标志来选择新行为,默认为 `False`,如果为 `False` 则发出警告
+ * 将默认值更改为 `True`,表示完全弃用标记
+ * 删除该标志
+
+如果你遵循语义版本控制,版本可能如下:
+
+库版本 | 库 API | 用户代码
+---|---|---
+1.0 | 没有标志 | 预期的旧行为
+1.1 | 添加标志,默认为 `False`,如果是 `False`,则警告 | 设置标志为 `True`,处理新行为
+2.0 | 改变默认为 `True`,完全弃用标志 | 处理新行为
+3.0 | 移除标志 | 处理新行为
+
+你需要**两**个主要版本来完成该操作。如果你直接从“添加标志,默认为 `False`,如果是 `False` 则发出警告”变到“删除标志”,而没有中间版本,那么用户的代码将无法升级。为 1.1 正确编写的用户代码必须能够升级到下一个版本,除了新警告之外,没有任何不良影响,但如果在下一个版本中删除了该标志,那么该代码将崩溃。一个负责任的神明从不违反扭曲的政策:“先行者总是自由的”。
+
+### 负责任的创建者
+
+![Demeter][23]
+
+我们的 10 个约定大致可以分为三类:
+
+**谨慎发展**
+
+ 1. 避免不良功能
+ 2. 最小化特性
+ 3. 保持功能单一
+ 4. 标记实验特征“临时”
+ 5. 温柔删除功能
+
+**严格记录历史**
+
+ 1. 维护更改日志
+ 2. 选择版本方案
+ 3. 编写升级指南
+
+**缓慢而明显地改变**
+
+ 1. 兼容添加参数
+ 2. 逐渐改变行为
+
+如果你对你所创造的物种保持这些约定,你将成为一个负责任的造物主。你的生物的身体可以随着时间的推移而进化,一直在改善和适应环境的变化,而不是在生物没有准备好就突然改变。如果你维护一个库,请向用户保留这些承诺,这样你就可以在不破坏依赖该库的代码的情况下对库进行更新。
+
+* * *
+
+_这篇文章最初是在 [A. Jesse Jiryu Davis 的博客上'][24]出现的,经允许转载。_
+
+插图参考:
+
+ * [《世界进步》, Delphian Society, 1913][25]
+ * [《走进蛇的历史》, Charles Owen, 1742][26]
+ * [关于哥斯达黎加的 batrachia 和爬行动物,关于尼加拉瓜和秘鲁的爬行动物和鱼类学的记录, Edward Drinker Cope, 1875][27]
+ * [《自然史》, Richard Lydekker et. al., 1897][28]
+ * [Mes Prisons, Silvio Pellico, 1843][29]
+ * [Tierfotoagentur / m.blue-shadow][30]
+ * [洛杉矶公共图书馆, 1930][31]
+
+
+
+--------------------------------------------------------------------------------
+
+via: https://opensource.com/article/19/5/api-evolution-right-way
+
+作者:[A. Jesse][a]
+选题:[lujun9972][b]
+译者:[MjSeven](https://github.com/MjSeven)
+校对:[wxy](https://github.com/wxy)
+
+本文由 [LCTT](https://github.com/LCTT/TranslateProject) 原创编译,[Linux中国](https://linux.cn/) 荣誉推出
+
+[a]: https://opensource.com/users/emptysquare
+[b]: https://github.com/lujun9972
+[1]: https://opensource.com/sites/default/files/styles/image-full-size/public/lead-images/browser_desktop_website_checklist_metrics.png?itok=OKKbl1UR (Browser of things)
+[2]: https://opensource.com/sites/default/files/uploads/praise-the-creator.jpg (Serpents)
+[3]: https://opensource.com/sites/default/files/uploads/bite.jpg (Man being chased by an alligator)
+[4]: https://bugs.python.org/issue13936
+[5]: https://opensource.com/sites/default/files/uploads/feathers.jpg (Serpents with and without feathers)
+[6]: https://bugs.python.org/issue32591
+[7]: https://opensource.com/sites/default/files/uploads/horns.jpg (Serpent with horns)
+[8]: https://opensource.com/sites/default/files/uploads/lizard-to-snake.jpg (Lizard transformed to snake)
+[9]: https://opensource.com/sites/default/files/uploads/mammal.jpg (A mouse)
+[10]: https://bugs.python.org/issue32253
+[11]: https://opensource.com/sites/default/files/uploads/scale.jpg (Balance scales)
+[12]: https://semver.org
+[13]: https://www.python.org/dev/peps/pep-0440/
+[14]: https://opensource.com/sites/default/files/uploads/skink.jpg (A skink)
+[15]: https://twistedmatrix.com/documents/current/core/development/policy/compatibility-policy.html
+[16]: https://opensource.com/sites/default/files/uploads/loudly.jpg (Woman riding an alligator)
+[17]: http://www.informit.com/articles/article.aspx?p=2314818
+[18]: https://opensource.com/sites/default/files/uploads/rattlesnake.jpg (Rattlesnake)
+[19]: https://opensource.com/sites/default/files/articles/neonate_sidewinder_sidewinding_with_tracks_unlabeled.png
+[20]: https://creativecommons.org/licenses/by-sa/4.0
+[21]: https://commons.wikimedia.org/wiki/File:Neonate_sidewinder_sidewinding_with_tracks_unlabeled.jpg
+[22]: https://bugs.python.org/issue31827
+[23]: https://opensource.com/sites/default/files/uploads/demeter.jpg (Demeter)
+[24]: https://emptysqua.re/blog/api-evolution-the-right-way/
+[25]: https://www.gutenberg.org/files/42224/42224-h/42224-h.htm
+[26]: https://publicdomainreview.org/product-att/artist/charles-owen/
+[27]: https://archive.org/details/onbatrachiarepti00cope/page/n3
+[28]: https://www.flickr.com/photos/internetarchivebookimages/20556001490
+[29]: https://www.oldbookillustrations.com/illustrations/stationery/
+[30]: https://www.alamy.com/mediacomp/ImageDetails.aspx?ref=D7Y61W
+[31]: https://www.vintag.es/2013/06/riding-alligator-c-1930s.html
diff --git a/published/201905/20190503 Check your spelling at the command line with Ispell.md b/published/201905/20190503 Check your spelling at the command line with Ispell.md
new file mode 100644
index 0000000000..a4c84a78d8
--- /dev/null
+++ b/published/201905/20190503 Check your spelling at the command line with Ispell.md
@@ -0,0 +1,82 @@
+[#]: collector: (lujun9972)
+[#]: translator: (geekpi)
+[#]: reviewer: (wxy)
+[#]: publisher: (wxy)
+[#]: url: (https://linux.cn/article-10895-1.html)
+[#]: subject: (Check your spelling at the command line with Ispell)
+[#]: via: (https://opensource.com/article/19/5/spelling-command-line-ispell)
+[#]: author: (Scott Nesbitt https://opensource.com/users/scottnesbitt)
+
+使用 Ispell 在命令行中检查拼写
+======
+
+> Ispell 可以帮助你在纯文本中消除超过 50 种语言的拼写错误。
+
+
+
+好的拼写是一种技巧。它是一项需要时间学习和掌握的技能。也就是说,有些人从来没有完全掌握这种技能,我知道有两三个出色的作家就无法完全掌握拼写。
+
+即使你拼写得很好,偶尔也会输入错字。特别是在最后期限前如果你快速敲击键盘,那就更是如此。无论你的拼写的是什么,通过拼写检查器检查你所写的内容总是一个好主意。
+
+我用[纯文本][2]完成了我的大部分写作,并经常使用名为 [Aspell][3] 的命令行拼写检查器来完成这项工作。Aspell 不是唯一的工具。你可能还想要看下不错的 [Ispell][4]。
+
+### 入门
+
+自 1971 年以来,Ispell 就以各种形式出现过。不要被它的年龄欺骗。Ispell 仍然是一个可以在 21 世纪高效使用的应用。
+
+在开始之前,请打开终端窗口并输入 `which ispell` 来检查计算机上是否安装了 Ispell。如果未安装,请打开发行版的软件包管理器并从那里安装 Ispell。
+
+不要忘记为你使用的语言安装词典。我唯一使用的语言是英语,所以我只需下载美国和英国英语字典。你可以不局限于我的(也是唯一的)母语。Ispell 有[超过 50 种语言的词典][5]。
+
+![Installing Ispell dictionaries][6]
+
+### 使用 Ispell
+
+如果你还没有猜到,Ispell 只能用在文本文件。这包括用 HTML、LaTeX 和 [nroff 或 troff][7] 标记的文档。之后会有更多相关内容。
+
+要开始使用,请打开终端窗口并进入包含要运行拼写检查的文件的目录。输入 `ispell` 后跟文件名,然后按回车键。
+
+![Checking spelling with Ispell][8]
+
+Ispell 高亮了它无法识别的第一个词。如果单词拼写错误,Ispell 通常会提供一个或多个备选方案。按下 `R`,然后按下正确选择旁边的数字。在上面的截图中,我按了 `R` 和 `0` 来修复错误。
+
+另一方面,如果单词拼写正确,请按下 `A` 然后移动到下一个拼写错误的单词。
+
+继续这样做直到到达文件的末尾。Ispell 会保存你的更改,创建你刚检查的文件的备份(扩展名为 `.bak`),然后关闭。
+
+### 其他几个选项
+
+此示例说明了 Ispell 的基本用法。这个程序有[很多选项][9],有些你*可能*会用到,而另一些你*可能永远*不会使用。让我们快速看下我经常使用的一些。
+
+之前我提到过 Ispell 可以用于某些标记语言。你需要告诉它文件的格式。启动 Ispell 时,为 TeX 或 LaTeX 文件添加 `-t`,为 HTML 文件添加 `-H`,对于 groff 或 troff 文件添加 `-n`。例如,如果输入 `ispell -t myReport.tex`,Ispell 将忽略所有标记。
+
+如果你不想在检查文件后创建备份文件,请将 `-x` 添加到命令行。例如,`ispell -x myFile.txt`。
+
+如果 Ispell 遇到拼写正确但不在其字典中的单词,比如名字,会发生什么?你可以按 `I` 将该单词添加到个人单词列表中。这会将单词保存到 `/home` 目录下的 `.ispell_default` 的文件中。
+
+这些是我在使用 Ispell 时最有用的选项,但请查看 [Ispell 的手册页][9]以了解其所有选项。
+
+Ispell 比 Aspell 或其他命令行拼写检查器更好或者更快么?我会说它不比其他的差或者慢。Ispell 不是适合所有人。它也许也不适合你。但有更多选择也不错,不是么?
+
+--------------------------------------------------------------------------------
+
+via: https://opensource.com/article/19/5/spelling-command-line-ispell
+
+作者:[Scott Nesbitt][a]
+选题:[lujun9972][b]
+译者:[geekpi](https://github.com/geekpi)
+校对:[wxy](https://github.com/wxy)
+
+本文由 [LCTT](https://github.com/LCTT/TranslateProject) 原创编译,[Linux中国](https://linux.cn/) 荣誉推出
+
+[a]: https://opensource.com/users/scottnesbitt
+[b]: https://github.com/lujun9972
+[1]: https://opensource.com/sites/default/files/styles/image-full-size/public/lead-images/command_line_prompt.png?itok=wbGiJ_yg (Command line prompt)
+[2]: https://plaintextproject.online
+[3]: https://opensource.com/article/18/2/how-check-spelling-linux-command-line-aspell
+[4]: https://www.cs.hmc.edu/~geoff/ispell.html
+[5]: https://www.cs.hmc.edu/~geoff/ispell-dictionaries.html
+[6]: https://opensource.com/sites/default/files/uploads/ispell-install-dictionaries.png (Installing Ispell dictionaries)
+[7]: https://opensource.com/article/18/2/how-format-academic-papers-linux-groff-me
+[8]: https://opensource.com/sites/default/files/uploads/ispell-checking.png (Checking spelling with Ispell)
+[9]: https://www.cs.hmc.edu/~geoff/ispell-man.html
diff --git a/published/201905/20190503 Say goodbye to boilerplate in Python with attrs.md b/published/201905/20190503 Say goodbye to boilerplate in Python with attrs.md
new file mode 100644
index 0000000000..f6d3d5a0c0
--- /dev/null
+++ b/published/201905/20190503 Say goodbye to boilerplate in Python with attrs.md
@@ -0,0 +1,105 @@
+[#]: collector: (lujun9972)
+[#]: translator: (geekpi)
+[#]: reviewer: (wxy)
+[#]: publisher: ( )
+[#]: url: ( )
+[#]: subject: (Say goodbye to boilerplate in Python with attrs)
+[#]: via: (https://opensource.com/article/19/5/python-attrs)
+[#]: author: (Moshe Zadka https://opensource.com/users/moshez/users/moshez)
+
+使用 attrs 来告别 Python 中的样板
+======
+
+> 在我们覆盖 7 个 PyPI 库的系列文章中了解更多解决 Python 问题的信息。
+
+
+
+Python是当今使用最多[流行的编程语言][2]之一,因为:它是开源的,它具有广泛的用途(例如 Web 编程、业务应用、游戏、科学编程等等),它有一个充满活力和专注的社区支持它。这个社区是我们在 [Python Package Index][3](PyPI)中提供如此庞大、多样化的软件包的原因,用以扩展和改进 Python。并解决不可避免的问题。
+
+在本系列中,我们将介绍七个可以帮助你解决常见 Python 问题的 PyPI 库。今天,我们将研究 [attrs][4],这是一个帮助你快速编写简洁、正确的代码的 Python 包。
+
+### attrs
+
+如果你已经写过一段时间的 Python,那么你可能习惯这样写代码:
+
+```
+class Book(object):
+
+ def __init__(self, isbn, name, author):
+ self.isbn = isbn
+ self.name = name
+ self.author = author
+```
+
+接着写一个 `__repr__` 函数。否则,很难记录 `Book` 的实例:
+
+
+```
+def __repr__(self):
+ return f"Book({self.isbn}, {self.name}, {self.author})"
+```
+
+接下来你会写一个好看的 docstring 来记录期望的类型。但是你注意到你忘了添加 `edition` 和 `published_year` 属性,所以你必须在五个地方修改它们。
+
+如果你不必这么做如何?
+
+```
+@attr.s(auto_attribs=True)
+class Book(object):
+ isbn: str
+ name: str
+ author: str
+ published_year: int
+ edition: int
+```
+
+使用新的类型注释语法注释类型属性,`attrs` 会检测注释并创建一个类。
+
+ISBN 有特定格式。如果我们想强行使用该格式怎么办?
+
+```
+@attr.s(auto_attribs=True)
+class Book(object):
+ isbn: str = attr.ib()
+ @isbn.validator
+ def pattern_match(self, attribute, value):
+ m = re.match(r"^(\d{3}-)\d{1,3}-\d{2,3}-\d{1,7}-\d$", value)
+ if not m:
+ raise ValueError("incorrect format for isbn", value)
+ name: str
+ author: str
+ published_year: int
+ edition: int
+```
+
+`attrs` 库也对[不可变式编程][5]支持良好。将第一行改成 `@attr.s(auto_attribs=True, frozen=True)` 意味着 `Book` 现在是不可变的:尝试修改一个属性将会引发一个异常。相反,比如,如果希望将发布日期向后一年,我们可以修改成 `attr.evolve(old_book, published_year=old_book.published_year+1)` 来得到一个*新的*实例。
+
+本系列的下一篇文章我们将来看下 `singledispatch`,一个能让你向 Python 库添加方法的库。
+
+#### 查看本系列先前的文章
+
+* [Cython][6]
+* [Black][7]
+
+
+
+--------------------------------------------------------------------------------
+
+via: https://opensource.com/article/19/5/python-attrs
+
+作者:[Moshe Zadka][a]
+选题:[lujun9972][b]
+译者:[geekpi](https://github.com/geekpi)
+校对:[wxy](https://github.com/wxy)
+
+本文由 [LCTT](https://github.com/LCTT/TranslateProject) 原创编译,[Linux中国](https://linux.cn/) 荣誉推出
+
+[a]: https://opensource.com/users/moshez/users/moshez
+[b]: https://github.com/lujun9972
+[1]: https://opensource.com/sites/default/files/styles/image-full-size/public/lead-images/programming_code_keyboard_orange_hands.png?itok=G6tJ_64Y (Programming at a browser, orange hands)
+[2]: https://opensource.com/article/18/5/numbers-python-community-trends
+[3]: https://pypi.org/
+[4]: https://pypi.org/project/attrs/
+[5]: https://opensource.com/article/18/10/functional-programming-python-immutable-data-structures
+[6]: https://linux.cn/article-10859-1.html
+[7]: https://linux.cn/article-10864-1.html
diff --git a/published/201905/20190504 Add methods retroactively in Python with singledispatch.md b/published/201905/20190504 Add methods retroactively in Python with singledispatch.md
new file mode 100644
index 0000000000..b0704dd59f
--- /dev/null
+++ b/published/201905/20190504 Add methods retroactively in Python with singledispatch.md
@@ -0,0 +1,105 @@
+[#]: collector: (lujun9972)
+[#]: translator: (geekpi)
+[#]: reviewer: (wxy)
+[#]: publisher: (wxy)
+[#]: url: (https://linux.cn/article-10887-1.html)
+[#]: subject: (Add methods retroactively in Python with singledispatch)
+[#]: via: (https://opensource.com/article/19/5/python-singledispatch)
+[#]: author: (Moshe Zadka https://opensource.com/users/moshez)
+
+使用 singledispatch 在 Python 中追溯地添加方法
+======
+
+> 在我们覆盖 7 个 PyPI 库的系列文章中了解更多解决 Python 问题的信息。
+
+
+
+Python 是当今使用最多[流行的编程语言][2]之一,因为:它是开源的,它具有广泛的用途(例如 Web 编程、业务应用、游戏、科学编程等等),它有一个充满活力和专注的社区支持它。这个社区是我们在 [Python Package Index][3](PyPI)中提供如此庞大、多样化的软件包的原因,用以扩展和改进 Python。并解决不可避免的问题。
+
+在本系列中,我们将介绍七个可以帮助你解决常见 Python 问题的 PyPI 库。今天,我们将研究 [singledispatch][4],这是一个能让你追溯地向 Python 库添加方法的库。
+
+### singledispatch
+
+想象一下,你有一个有 Circle、Square 等类的“形状”库。
+
+Circle 类有半径、Square 有边、Rectangle 有高和宽。我们的库已经存在,我们不想改变它。
+
+然而,我们想给库添加一个面积计算。如果我们不会和其他人共享这个库,我们只需添加 `area` 方法,这样我们就能调用 `shape.area()` 而无需关心是什么形状。
+
+虽然可以进入类并添加一个方法,但这是一个坏主意:没有人希望他们的类会被添加新的方法,程序会因奇怪的方式出错。
+
+相反,functools 中的 `singledispatch` 函数可以帮助我们。
+
+
+```
+@singledispatch
+def get_area(shape):
+ raise NotImplementedError("cannot calculate area for unknown shape",
+ shape)
+```
+
+`get_area` 函数的“基类”实现会报错。这保证了如果我们出现一个新的形状时,我们会明确地报错而不是返回一个无意义的结果。
+
+
+```
+@get_area.register(Square)
+def _get_area_square(shape):
+ return shape.side ** 2
+@get_area.register(Circle)
+def _get_area_circle(shape):
+ return math.pi * (shape.radius ** 2)
+```
+
+这种方式的好处是如果某人写了一个匹配我们代码的*新*形状,它们可以自己实现 `get_area`。
+
+
+```
+from area_calculator import get_area
+
+@attr.s(auto_attribs=True, frozen=True)
+class Ellipse:
+ horizontal_axis: float
+ vertical_axis: float
+
+@get_area.register(Ellipse)
+def _get_area_ellipse(shape):
+ return math.pi * shape.horizontal_axis * shape.vertical_axis
+```
+
+*调用* `get_area` 很直接。
+
+
+```
+print(get_area(shape))
+```
+
+这意味着我们可以将大量的 `if isintance()`/`elif isinstance()` 的代码以这种方式修改,而无需修改接口。下一次你要修改 if isinstance,你试试 `singledispatch!
+
+在本系列的下一篇文章中,我们将介绍 tox,一个用于自动化 Python 代码测试的工具。
+
+#### 回顾本系列的前几篇文章:
+
+ * [Cython][5]
+ * [Black][6]
+ * [attrs][7]
+
+--------------------------------------------------------------------------------
+
+via: https://opensource.com/article/19/5/python-singledispatch
+
+作者:[Moshe Zadka][a]
+选题:[lujun9972][b]
+译者:[geekpi](https://github.com/geekpi)
+校对:[wxy](https://github.com/wxy)
+
+本文由 [LCTT](https://github.com/LCTT/TranslateProject) 原创编译,[Linux中国](https://linux.cn/) 荣誉推出
+
+[a]: https://opensource.com/users/moshez
+[b]: https://github.com/lujun9972
+[1]: https://opensource.com/sites/default/files/styles/image-full-size/public/lead-images/computer_code_programming_laptop.jpg?itok=ormv35tV
+[2]: https://opensource.com/article/18/5/numbers-python-community-trends
+[3]: https://pypi.org/
+[4]: https://pypi.org/project/singledispatch/
+[5]: https://linux.cn/article-10859-1.html
+[6]: https://linux.cn/article-10864-1.html
+[7]: https://linux.cn/article-10871-1.html
diff --git a/published/201905/20190504 Using the force at the Linux command line.md b/published/201905/20190504 Using the force at the Linux command line.md
new file mode 100644
index 0000000000..8b340047f6
--- /dev/null
+++ b/published/201905/20190504 Using the force at the Linux command line.md
@@ -0,0 +1,219 @@
+[#]: collector: (lujun9972)
+[#]: translator: (Moelf)
+[#]: reviewer: (wxy)
+[#]: publisher: (wxy)
+[#]: url: (https://linux.cn/article-10881-1.html)
+[#]: subject: (Using the force at the Linux command line)
+[#]: via: (https://opensource.com/article/19/5/may-the-force-linux)
+[#]: author: (Alan Formy-Duval https://opensource.com/users/alanfdoss)
+
+在 Linux 命令行下使用“原力”
+======
+
+> 和绝地武士的原力一样,`-f` 参数是很强大的,并伴随着潜在的毁灭性,在你能用好的时候又很便利。
+
+
+
+近些年来,科幻发烧友开始在每年的 5 月 4 日庆祝[星战节][2],其口号是绝地武士的祝福语”愿原力和你同在“。虽然大多数 Linux 用户可能不是绝地武士,但我们依然可以使用原力。自然,如果尤达大师只是叫天行者卢克输入什么 “man X-Wing 战机“、“man 原力”,或者 RTFM(去读原力手册,肯定是这个意思对不对),那这电影肯定没啥意思。(LCTT 译注:RTFM 是 “Read The Fucking Manual” 的缩写 —— 读读该死的手册吧)。
+
+很多 Linux 命令都有 `-f` 选项,意思你现在肯定也知道了,原力(LCTT 译注:force 选项原意是“强制”)!很多时候你先尝试执行命令然后失败了,或者提示你需要补充输入更多选项。通常这都是为了保护你试着改变的文件,或者告诉用户该设备正忙或文件已经存在之类的。
+
+如果你不想被这些提醒打扰或者压根就不在乎,就使用原力吧!
+
+不过要小心,通常使用原力选项是摧毁性的。所以用户一定要格外注意!并且确保你知道自己在做什么!用原力就要承担后果!
+
+以下是一些常见 Linux 命令的原力选项和它们的效果,以及常见使用场景。
+
+### cp
+
+`cp` 是 “copy” 的缩写,这是个被用来复制文件或者目录的命令。其 [man 页面][3] 说:
+
+> -f, --force
+>
+> 如果已经存在的目标文件无法被打开,删除它并重试
+
+你可能会用它来处理只读状态的文件:
+
+```
+[alan@workstation ~]$ ls -l
+total 8
+-rw-rw---- 1 alan alan 13 May 1 12:24 Hoth
+-r--r----- 1 alan alan 14 May 1 12:23 Naboo
+[alan@workstation ~]$ cat Hoth Naboo
+Icy Planet
+
+Green Planet
+```
+
+如果你想要复制一个叫做 `Hoth` 的文件到 `Naboo`,但因为 `Naboo` 目前是只读状态,`cp` 命令不会执行:
+
+```
+[alan@workstation ~]$ cp Hoth Naboo
+cp: cannot create regular file 'Naboo': Permission denied
+```
+
+但通过使用原力,`cp` 会强制执行。`Hoth` 的内容和文件权限会直接被复制到 `Naboo`:
+
+
+```
+[alan@workstation ~]$ cp -f Hoth Naboo
+[alan@workstation ~]$ cat Hoth Naboo
+Icy Planet
+
+Icy Planet
+
+[alan@workstation ~]$ ls -l
+total 8
+-rw-rw---- 1 alan alan 12 May 1 12:32 Hoth
+-rw-rw---- 1 alan alan 12 May 1 12:38 Naboo
+```
+
+### ln
+
+`ln` 命令是用来在文件之间建立链接的,其 [man 页面][4] 描述的原力选项如下:
+
+
+> -f, --force
+>
+> 移除当前存在的文件
+
+
+假设莱娅公主在维护一个 Java 应用服务器,并且她又一个存放这所有 Java 版本的目录,比如:
+
+```
+leia@workstation:/usr/lib/java$ ls -lt
+total 28
+lrwxrwxrwx 1 leia leia 12 Mar 5 2018 jdk -> jdk1.8.0_162
+drwxr-xr-x 8 leia leia 4096 Mar 5 2018 jdk1.8.0_162
+drwxr-xr-x 8 leia leia 4096 Aug 28 2017 jdk1.8.0_144
+```
+
+正如你所看到的,这里有很多个版本的 JDK,并有一个符号链接指向最新版的 JDK。她接着用一个脚本来安装最新版本的 JDK。但是如果没有原力选项的话以下命令是不会成功的:
+
+```
+tar xvzmf jdk1.8.0_181.tar.gz -C jdk1.8.0_181/
+ln -vs jdk1.8.0_181 jdk
+```
+
+`tar` 命令会解压 .gz 文件到一个特定的目标目录,但 `ln` 命令会失败,因为这个链接已经存在了。这样的结果是该符号链接不会指向最新版本的 JDK:
+
+```
+leia@workstation:/usr/lib/java$ ln -vs jdk1.8.0_181 jdk
+ln: failed to create symbolic link 'jdk/jdk1.8.0_181': File exists
+leia@workstation:/usr/lib/java$ ls -lt
+total 28
+drwxr-x--- 2 leia leia 4096 May 1 15:44 jdk1.8.0_181
+lrwxrwxrwx 1 leia leia 12 Mar 5 2018 jdk -> jdk1.8.0_162
+drwxr-xr-x 8 leia leia 4096 Mar 5 2018 jdk1.8.0_162
+drwxr-xr-x 8 leia leia 4096 Aug 28 2017 jdk1.8.0_144
+```
+
+她可以通过使用原力选项强制 `ln` 更新链接,但这里她还需要使用 `-n`,`-n` 是因为这个情况下链接其实指向一个目录而非文件。这样的话,链接就会正确指向最新版本的JDK了。
+
+```
+leia@workstation:/usr/lib/java$ ln -vsnf jdk1.8.0_181 jdk
+'jdk' -> 'jdk1.8.0_181'
+leia@workstation:/usr/lib/java$ ls -lt
+total 28
+lrwxrwxrwx 1 leia leia 12 May 1 16:13 jdk -> jdk1.8.0_181
+drwxr-x--- 2 leia leia 4096 May 1 15:44 jdk1.8.0_181
+drwxr-xr-x 8 leia leia 4096 Mar 5 2018 jdk1.8.0_162
+drwxr-xr-x 8 leia leia 4096 Aug 28 2017 jdk1.8.0_144
+```
+
+你可以配置 Java 应用使其一直使用在 `/usr/lib/java/jdk` 处的 JDK,而不用每次升级都更新。
+
+### rm
+
+`rm` 命令是 “remove” 的缩写(也叫做删除,因为某些系统 `del` 命令也干这事)。其 [man 页面][5] 对原力选项的描述如下:
+
+
+> -f, --force
+>
+> 无视不存在的文件或者参数,不向用户确认
+
+如果你尝试删除一个只读的文件,`rm` 会寻求用户的确认:
+
+```
+[alan@workstation ~]$ ls -l
+total 4
+-r--r----- 1 alan alan 16 May 1 11:38 B-wing
+[alan@workstation ~]$ rm B-wing
+rm: remove write-protected regular file 'B-wing'?
+```
+
+你一定要输入 `y` 或者 `n` 来回答确认才能让 `rm` 命令继续。如果你使用原力选项,`rm` 就不会寻求你的确认而直接删除文件:
+
+```
+[alan@workstation ~]$ rm -f B-wing
+[alan@workstation ~]$ ls -l
+total 0
+[alan@workstation ~]$
+```
+
+最常见的 `rm` 原力选项用法是用来删除目录。 `-r`(递归)选项会让 `rm` 删除目录,当和原力选项结合起来,它会删除这个文件夹及其内容而无需用户确认。
+
+`rm` 命令和一些选项结合起来是致命的,一直以来互联网上都有关于误用 `rm` 删除整个系统之类的玩笑和鬼故事。比如最出名的一不当心执行 `rm -rf .` 会直接删除目录和文件(没有用户确认)。(LCTT 译注:真的这么干过的校对飘过~~请按下回车前再三确认:我是谁,我在哪里,我在干什么)
+
+### userdel
+
+`userdel` 命令使用来删除用户的。其 [man 页面][6] 是这样描述它的原力选项的:
+
+> -f, --force
+>
+> 这个选项会强制移除用户,即便用户当前处于登入状态。它同时还会强制
+删除用户的目录和邮件存储,即便这个用户目录被别人共享或者邮件存储并不
+属于这个用户。如果 `USERGROUPS_ENAB` 在 `/etc/login.defs` 里是 `yes`
+并且有一个组和此用户同名的话,这个组也会被移除,即便这个组还是别
+的用户的主要用户组也一样。
+>
+> 注意:这个选项有风险并可能让系统处于不稳定状态。
+
+当欧比旺抵达穆斯塔法星的时候,他知道自己的使命。他需要删掉达斯·维达的用户账户——而达斯还在里面呢。
+
+```
+[root@workstation ~]# ps -fu darth
+UID PID PPID C STIME TTY TIME CMD
+darth 7663 7655 0 13:28 pts/3 00:00:00 -bash
+[root@workstation ~]# userdel darth
+userdel: user darth is currently used by process 7663
+```
+
+因为达斯还登在系统里,欧比旺需要使用原力选项操作 `userdel`。这能强制删除当前登入的用户。
+
+```
+[root@workstation ~]# userdel -f darth
+userdel: user darth is currently used by process 7663
+[root@workstation ~]# finger darth
+finger: darth: no such user.
+[root@workstation ~]# ps -fu darth
+error: user name does not exist
+```
+
+正如我们所见到的一样,`finger` 和 `ps` 命令让我们确认了达斯已经被删除了。
+
+### 在 Shell 脚本里使用原力
+
+很多命令都有原力选项,而在 shell 脚本里他们特别有用。因为我们经常使用脚本完成定期或者自动化的任务,避免用户输入至关重要,不然的话自动任务就无法完成了
+
+我希望上面的几个例子能帮你理解一些需要使用原力的情况。你在命令行使用原力或把它们写入脚本之前应当完全理解它们的作用。误用原力会有毁灭性的后果——时常是对整个系统,甚至不仅限于一台设备。
+
+--------------------------------------------------------------------------------
+
+via: https://opensource.com/article/19/5/may-the-force-linux
+
+作者:[Alan Formy-Duval][a]
+选题:[lujun9972][b]
+译者:[Jerry Ling](https://github.com/Moelf)
+校对:[wxy](https://github.com/wxy)
+
+本文由 [LCTT](https://github.com/LCTT/TranslateProject) 原创编译,[Linux中国](https://linux.cn/) 荣誉推出
+
+[a]: https://opensource.com/users/alanfdoss
+[b]: https://github.com/lujun9972
+[1]: https://opensource.com/sites/default/files/styles/image-full-size/public/lead-images/fireworks_light_art_design.jpg?itok=hfx9i4By (Fireworks)
+[2]: https://www.starwars.com/star-wars-day
+[3]: http://man7.org/linux/man-pages/man1/cp.1.html
+[4]: http://man7.org/linux/man-pages/man1/ln.1.html
+[5]: http://man7.org/linux/man-pages/man1/rm.1.html
+[6]: http://man7.org/linux/man-pages/man8/userdel.8.html
diff --git a/published/201905/20190505 Duc - A Collection Of Tools To Inspect And Visualize Disk Usage.md b/published/201905/20190505 Duc - A Collection Of Tools To Inspect And Visualize Disk Usage.md
new file mode 100644
index 0000000000..13d10c9c57
--- /dev/null
+++ b/published/201905/20190505 Duc - A Collection Of Tools To Inspect And Visualize Disk Usage.md
@@ -0,0 +1,244 @@
+[#]: collector: (lujun9972)
+[#]: translator: (tomjlw)
+[#]: reviewer: (wxy)
+[#]: publisher: (wxy)
+[#]: url: (https://linux.cn/article-10892-1.html)
+[#]: subject: (Duc – A Collection Of Tools To Inspect And Visualize Disk Usage)
+[#]: via: (https://www.ostechnix.com/duc-a-collection-of-tools-to-inspect-and-visualize-disk-usage/)
+[#]: author: (sk https://www.ostechnix.com/author/sk/)
+
+Duc:一个能够可视化洞察硬盘使用情况的工具包
+======
+
+![Duc:一个能够洞察并可视化硬盘使用情况的工具包][1]
+
+Duc 是一个在类 Unix 操作系统上可以用来索引、洞察及可视化硬盘使用情况的工具包。别把它当成一个仅能用漂亮图表展现硬盘使用情况的 CLI 工具。它对巨大的文件系统也支持的很好。Duc 已在由超过五亿个文件和几 PB 的存储组成的系统上测试过,没有任何问题。
+
+Duc 是一个快速而且灵活的工具。它将你的硬盘使用情况存在一个优化过的数据库里,这样你就可以在索引完成后迅速找到你的数据。此外,它自带不同的用户交互界面与后端以访问数据库并绘制图表。
+
+以下列出的是目前支持的用户界面(UI):
+
+ 1. 命令行界面(`duc ls`)
+ 2. Ncurses 控制台界面(`duc ui`)
+ 3. X11 GUI(`duc gui`)
+ 4. OpenGL GUI(`duc gui`)
+
+支持的后端数据库:
+
+ * Tokyocabinet
+ * Leveldb
+ * Sqlite3
+
+Duc 默认使用 Tokyocabinet 作为后端数据库。
+
+### 安装 Duc
+
+Duc 可以从 Debian 以及其衍生品例如 Ubuntu 的默认仓库中获取。因此在基于 DEB 的系统上安装 Duc 是小菜一碟。
+
+```
+$ sudo apt-get install duc
+```
+
+在其它 Linux 发行版上你需要像以下所展示的那样手动从源代码编译安装 Duc。
+
+可以从 Github 上的[发行][2]页面下载最新的 Duc 源代码的 .tgz 文件。在写这篇教程的时候,最新的版本是1.4.4。
+
+```
+$ wget https://github.com/zevv/duc/releases/download/1.4.4/duc-1.4.4.tar.gz
+```
+
+然后一个接一个地运行以下命令来安装 DUC。
+
+```
+$ tar -xzf duc-1.4.4.tar.gz
+$ cd duc-1.4.4
+$ ./configure
+$ make
+$ sudo make install
+```
+
+### 使用 Duc
+
+`duc` 的典型用法是:
+
+```
+$ duc
+```
+
+你可以通过运行以下命令来浏览总的选项列表以及子命令:
+
+```
+$ duc help
+```
+
+你也可以像下面这样了解一个特定子命令的用法。
+
+```
+$ duc help
+```
+
+要查看所有命令与其选项的列表,仅需运行:
+
+```
+$ duc help --all
+```
+
+让我们看看一些 `duc` 工具的特定用法。
+
+### 创建索引(数据库)
+
+首先,你需要创建一个你文件系统的索引文件(数据库)。使用 `duc index` 命令以创建索引文件。
+
+比如说,要创建你的 `/home` 目录的索引,仅需运行:
+
+```
+$ duc index /home
+```
+
+上述命令将会创建你的 `/home` 目录的索引,并将其保存在 `$HOME/.duc.db` 文件中。如果你以后需要往 `/home` 目录添加新的文件或目录,只要在之后重新运行一下上面的命令来重建索引。
+
+### 查询索引
+
+Duc 有不同的子命令来查询并探索索引。
+
+要查看可访问的索引列表,运行:
+
+```
+$ duc info
+```
+
+示例输出:
+
+```
+Date Time Files Dirs Size Path
+2019-04-09 15:45:55 3.5K 305 654.6M /home
+```
+
+如你在上述输出所见,我已经索引好了 `/home` 目录。
+
+要列出当前工作目录中所有的文件和目录,你可以这样做:
+
+```
+$ duc ls
+```
+
+要列出指定的目录,例如 `/home/sk/Downloads` 中的文件/目录,仅需像下面这样将路径作为参数传过去。
+
+```
+$ duc ls /home/sk/Downloads
+```
+
+类似的,运行 `duc ui` 命令来打开基于 ncurses 的控制台用户界面以探索文件系统使用情况,运行`duc gui` 以打开图形界面(X11)来探索文件系统。
+
+要了解更多子命令的用法,仅需参考帮助部分。
+
+```
+$ duc help ls
+```
+
+上述命令将会展现 `ls` 子命令的帮助部分。
+
+### 可视化硬盘使用状况
+
+在之前的部分我们以及看到如何用 duc 子命令列出文件和目录。在此之外,你甚至可以用一张漂亮的图表展示文件大小。
+
+要展示所提供目录的图表,像以下这样使用 `ls` 子命令。
+
+```
+$ duc ls -Fg /home/sk
+```
+
+示例输出:
+
+![使用 “duc ls” 命令可视化硬盘使用情况][3]
+
+如你在上述输出所见,`ls` 子命令查询 duc 数据库并列出了所提供目录包含的文件与目录的大小,在这里就是 `/home/sk/`。
+
+这里 `-F` 选项是往条目中用来添加文件类型指示符(`/`),`-g` 选项是用来绘制每个条目相对大小的图表。
+
+请注意如果未提供任何路径,就会使用当前工作目录。
+
+你可以使用 `-R` 选项来用[树状结构][4]浏览硬盘使用情况。
+
+```
+$ duc ls -R /home/sk
+```
+
+![用树状结构可视化硬盘使用情况][5]
+
+要查询 duc 数据库并打开基于 ncurses 的控制台以探索所提供的目录,像以下这样使用 `ui` 子命令。
+
+```
+$ duc ui /home/sk
+```
+
+![][6]
+
+类似的,我们使用 `gui *` 子命令来查询 duc 数据库以及打开一个图形界面(X11)来了解指定路径的硬盘使用情况。
+
+```
+$ duc gui /home/sk
+```
+
+![][7]
+
+像我之前所提到的,我们可以像下面这样了解更多关于特定子命令的用法。
+
+```
+$ duc help <子命令名字>
+```
+
+我仅仅覆盖了基本用法的部分,参考 man 页面了解关于 `duc` 工具的更多细节。
+
+```
+$ man duc
+```
+
+相关阅读:
+
+ * [Filelight – 在你的 Linux 系统上可视化硬盘使用情况][8]
+ * [一些好的 du 命令的替代品][9]
+ * [如何在 Linux 中用 Ncdu 检查硬盘使用情况][10]
+ * [Agedu——发现 Linux 中被浪费的硬盘空间][11]
+ * [如何在 Linux 中找到目录大小][12]
+ * [为初学者打造的带有示例的 df 命令教程][13]
+
+### 总结
+
+Duc 是一款简单却有用的硬盘用量查看器。如果你想要快速简便地知道哪个文件/目录占用你的硬盘空间,Duc 可能是一个好的选择。你还等什么呢?获取这个工具,扫描你的文件系统,摆脱无用的文件/目录。
+
+现在就到此为止了。希望这篇文章有用处。更多好东西马上就到。保持关注!
+
+欢呼吧!
+
+资源:
+
+ * [Duc 网站][14]
+
+--------------------------------------------------------------------------------
+
+via: https://www.ostechnix.com/duc-a-collection-of-tools-to-inspect-and-visualize-disk-usage/
+
+作者:[sk][a]
+选题:[lujun9972][b]
+译者:[tomjlw](https://github.com/tomjlw)
+校对:[wxy](https://github.com/wxy)
+
+本文由 [LCTT](https://github.com/LCTT/TranslateProject) 原创编译,[Linux中国](https://linux.cn/) 荣誉推出
+
+[a]: https://www.ostechnix.com/author/sk/
+[b]: https://github.com/lujun9972
+[1]: https://www.ostechnix.com/wp-content/uploads/2019/04/duc-720x340.png
+[2]: https://github.com/zevv/duc/releases
+[3]: http://www.ostechnix.com/wp-content/uploads/2019/04/duc-1-1.png
+[4]: https://www.ostechnix.com/view-directory-tree-structure-linux/
+[5]: http://www.ostechnix.com/wp-content/uploads/2019/04/duc-2.png
+[6]: http://www.ostechnix.com/wp-content/uploads/2019/04/duc-3.png
+[7]: http://www.ostechnix.com/wp-content/uploads/2019/04/duc-4.png
+[8]: https://www.ostechnix.com/filelight-visualize-disk-usage-on-your-linux-system/
+[9]: https://www.ostechnix.com/some-good-alternatives-to-du-command/
+[10]: https://www.ostechnix.com/check-disk-space-usage-linux-using-ncdu/
+[11]: https://www.ostechnix.com/agedu-find-out-wasted-disk-space-in-linux/
+[12]: https://www.ostechnix.com/find-size-directory-linux/
+[13]: https://www.ostechnix.com/the-df-command-tutorial-with-examples-for-beginners/
+[14]: https://duc.zevv.nl/
diff --git a/published/201905/20190505 How To Create SSH Alias In Linux.md b/published/201905/20190505 How To Create SSH Alias In Linux.md
new file mode 100644
index 0000000000..2438fb745a
--- /dev/null
+++ b/published/201905/20190505 How To Create SSH Alias In Linux.md
@@ -0,0 +1,197 @@
+[#]: collector: (lujun9972)
+[#]: translator: (MjSeven)
+[#]: reviewer: (wxy)
+[#]: publisher: (wxy)
+[#]: url: (https://linux.cn/article-10851-1.html)
+[#]: subject: (How To Create SSH Alias In Linux)
+[#]: via: (https://www.ostechnix.com/how-to-create-ssh-alias-in-linux/)
+[#]: author: (sk https://www.ostechnix.com/author/sk/)
+
+如何在 Linux 中创建 SSH 别名
+======
+
+
+
+如果你经常通过 SSH 访问许多不同的远程系统,这个技巧将为你节省一些时间。你可以通过 SSH 为频繁访问的系统创建 SSH 别名,这样你就不必记住所有不同的用户名、主机名、SSH 端口号和 IP 地址等。此外,它避免了在 SSH 到 Linux 服务器时重复输入相同的用户名、主机名、IP 地址、端口号。
+
+### 在 Linux 中创建 SSH 别名
+
+在我知道这个技巧之前,我通常使用以下任意一种方式通过 SSH 连接到远程系统。
+
+使用 IP 地址:
+
+```
+$ ssh 192.168.225.22
+```
+
+或使用端口号、用户名和 IP 地址:
+
+```
+$ ssh -p 22 sk@192.168.225.22
+```
+
+或使用端口号、用户名和主机名:
+
+```
+$ ssh -p 22 sk@server.example.com
+```
+
+这里
+
+ * `22` 是端口号,
+ * `sk` 是远程系统的用户名,
+ * `192.168.225.22` 是我远程系统的 IP,
+ * `server.example.com` 是远程系统的主机名。
+
+我相信大多数 Linux 新手和(或一些)管理员都会以这种方式通过 SSH 连接到远程系统。但是,如果你通过 SSH 连接到多个不同的系统,记住所有主机名或 IP 地址,还有用户名是困难的,除非你将它们写在纸上或者将其保存在文本文件中。别担心!这可以通过为 SSH 连接创建别名(或快捷方式)轻松解决。
+
+我们可以用两种方法为 SSH 命令创建别名。
+
+#### 方法 1 – 使用 SSH 配置文件
+
+这是我创建别名的首选方法。
+
+我们可以使用 SSH 默认配置文件来创建 SSH 别名。为此,编辑 `~/.ssh/config` 文件(如果此文件不存在,只需创建一个):
+
+```
+$ vi ~/.ssh/config
+```
+
+添加所有远程主机的详细信息,如下所示:
+
+```
+Host webserver
+ HostName 192.168.225.22
+ User sk
+
+Host dns
+ HostName server.example.com
+ User root
+
+Host dhcp
+ HostName 192.168.225.25
+ User ostechnix
+ Port 2233
+```
+
+![][2]
+
+*使用 SSH 配置文件在 Linux 中创建 SSH 别名*
+
+将 `Host`、`Hostname`、`User` 和 `Port` 配置的值替换为你自己的值。添加所有远程主机的详细信息后,保存并退出该文件。
+
+现在你可以使用以下命令通过 SSH 进入系统:
+
+```
+$ ssh webserver
+$ ssh dns
+$ ssh dhcp
+```
+
+就是这么简单!
+
+看看下面的截图。
+
+![][3]
+
+*使用 SSH 别名访问远程系统*
+
+看到了吗?我只使用别名(例如 `webserver`)来访问 IP 地址为 `192.168.225.22` 的远程系统。
+
+请注意,这只使用于当前用户。如果要为所有用户(系统范围内)提供别名,请在 `/etc/ssh/ssh_config` 文件中添加以上行。
+
+你还可以在 SSH 配置文件中添加许多其他内容。例如,如果你[已配置基于 SSH 密钥的身份验证][4],说明 SSH 密钥文件的位置,如下所示:
+
+```
+Host ubuntu
+ HostName 192.168.225.50
+ User senthil
+ IdentityFIle ~/.ssh/id_rsa_remotesystem
+```
+
+确保已使用你自己的值替换主机名、用户名和 SSH 密钥文件路径。
+
+现在使用以下命令连接到远程服务器:
+
+```
+$ ssh ubuntu
+```
+
+这样,你可以添加希望通过 SSH 访问的任意多台远程主机,并使用别名快速访问它们。
+
+#### 方法 2 – 使用 Bash 别名
+
+这是创建 SSH 别名的一种应急变通的方法,可以加快通信的速度。你可以使用 [alias 命令][5]使这项任务更容易。
+
+打开 `~/.bashrc` 或者 `~/.bash_profile` 文件:
+
+```
+alias webserver='ssh sk@server.example.com'
+alias dns='ssh sk@server.example.com'
+alias dhcp='ssh sk@server.example.com -p 2233'
+alias ubuntu='ssh sk@server.example.com -i ~/.ssh/id_rsa_remotesystem'
+```
+
+再次确保你已使用自己的值替换主机、主机名、端口号和 IP 地址。保存文件并退出。
+
+然后,使用命令应用更改:
+
+```
+$ source ~/.bashrc
+```
+
+或者
+
+```
+$ source ~/.bash_profile
+```
+
+在此方法中,你甚至不需要使用 `ssh 别名` 命令。相反,只需使用别名,如下所示。
+
+```
+$ webserver
+$ dns
+$ dhcp
+$ ubuntu
+```
+
+![][6]
+
+这两种方法非常简单,但对于经常通过 SSH 连接到多个不同系统的人来说非常有用,而且非常方便。使用适合你的上述任何一种方法,通过 SSH 快速访问远程 Linux 系统。
+
+建议阅读:
+
+ * [允许或拒绝 SSH 访问 Linux 中的特定用户或组][7]
+ * [如何在 Linux 上 SSH 到特定目录][8]
+ * [如何在 Linux 中断开 SSH 会话][9]
+ * [4 种方式在退出 SSH 会话后保持命令运行][10]
+ * [SSLH – 共享相同端口的 HTTPS 和 SSH][11]
+
+目前这就是全部了,希望它对你有帮助。更多好东西要来了,敬请关注!
+
+干杯!
+
+--------------------------------------------------------------------------------
+
+via: https://www.ostechnix.com/how-to-create-ssh-alias-in-linux/
+
+作者:[sk][a]
+选题:[lujun9972][b]
+译者:[MjSeven](https://github.com/MjSeven)
+校对:[wxy](https://github.com/wxy)
+
+本文由 [LCTT](https://github.com/LCTT/TranslateProject) 原创编译,[Linux中国](https://linux.cn/) 荣誉推出
+
+[a]: https://www.ostechnix.com/author/sk/
+[b]: https://github.com/lujun9972
+[1]: https://www.ostechnix.com/wp-content/uploads/2019/04/ssh-alias-720x340.png
+[2]: http://www.ostechnix.com/wp-content/uploads/2019/04/Create-SSH-Alias-In-Linux.png
+[3]: http://www.ostechnix.com/wp-content/uploads/2019/04/create-ssh-alias.png
+[4]: https://www.ostechnix.com/configure-ssh-key-based-authentication-linux/
+[5]: https://www.ostechnix.com/the-alias-and-unalias-commands-explained-with-examples/
+[6]: http://www.ostechnix.com/wp-content/uploads/2019/04/create-ssh-alias-1.png
+[7]: https://www.ostechnix.com/allow-deny-ssh-access-particular-user-group-linux/
+[8]: https://www.ostechnix.com/how-to-ssh-into-a-particular-directory-on-linux/
+[9]: https://www.ostechnix.com/how-to-stop-ssh-session-from-disconnecting-in-linux/
+[10]: https://www.ostechnix.com/4-ways-keep-command-running-log-ssh-session/
+[11]: https://www.ostechnix.com/sslh-share-port-https-ssh/
diff --git a/published/201905/20190505 Kindd - A Graphical Frontend To dd Command.md b/published/201905/20190505 Kindd - A Graphical Frontend To dd Command.md
new file mode 100644
index 0000000000..fbcf447bad
--- /dev/null
+++ b/published/201905/20190505 Kindd - A Graphical Frontend To dd Command.md
@@ -0,0 +1,142 @@
+[#]: collector: (lujun9972)
+[#]: translator: (robsean)
+[#]: reviewer: (wxy)
+[#]: publisher: (wxy)
+[#]: url: (https://linux.cn/article-10847-1.html)
+[#]: subject: (Kindd – A Graphical Frontend To dd Command)
+[#]: via: (https://www.ostechnix.com/kindd-a-graphical-frontend-to-dd-command/)
+[#]: author: (sk https://www.ostechnix.com/author/sk/)
+
+Kindd:一个图形化 dd 命令前端
+======
+
+![Kindd - A Graphical Frontend To dd Command][1]
+
+前不久,我们已经学习如何在类 Unix 系统中 [使用 dd 命令创建可启动的 ISO][2]。请记住,`dd` 命令是最具危险性和破坏性的命令之一。如果你不确定你实际在做什么,你可能会在几分钟内意外地擦除你的硬盘数据。`dd` 命令仅仅从 `if` 参数获取数据,并写入数据到 `of` 参数。它将不关心它正在覆盖什么,它也不关心是否在磁道上有一个分区表,或一个启动扇区,或者一个家文件夹,或者任何重要的东西。它将简单地做它被告诉去做的事。如果你是初学者,一般地尝试避免使用 `dd` 命令来做实验。幸好,这有一个支持 `dd` 命令的简单的 GUI 实用程序。向 “Kindd” 问好,一个属于 `dd` 命令的图形化前端。它是自由开源的、用 Qt Quick 所写的工具。总的来说,这个工具对那些对命令行不适应的初学者是非常有用的。
+
+它的开发者创建这个工具主要是为了提供:
+
+1. 一个用于 `dd` 命令的现代化的、简单而安全的图形化用户界面,
+2. 一种简单地创建可启动设备的图形化方法,而不必使用终端。
+
+### 安装 Kindd
+
+Kindd 在 [AUR][3] 中是可用的。所以,如果你是 Arch 用户,使用任一的 AUR 助手工具来安装它,例如 [Yay][4] 。
+
+要安装其 Git 发布版,运行:
+
+```
+$ yay -S kindd-git
+```
+
+要安装正式发布版,运行:
+
+```
+$ yay -S kindd
+```
+
+在安装后,从菜单或应用程序启动器启动 Kindd。
+
+对于其它的发行版,你需要从源文件手动编译和安装它,像下面所示。
+
+确保你已经安装下面的必要条件。
+
+ * git
+ * coreutils
+ * polkit
+ * qt5-base
+ * qt5-quickcontrols
+ * qt5-quickcontrols2
+ * qt5-graphicaleffects
+
+一旦所有必要条件安装,使用 `git` 克隆 Kindd 储存库:
+
+```
+git clone https://github.com/LinArcX/Kindd/
+```
+
+转到你刚刚克隆 Kindd 的目录,并编译和安装它:
+
+```
+cd Kindd
+qmake
+make
+```
+
+最后运行下面的命令来启动 Kindd 应用程序:
+
+```
+./kindd
+```
+
+Kindd 内部使用 pkexec。pkexec 代理被默认安装在大多数桌面环境中。但是,如果你使用 i3 (或者可能还有一些其它的桌面环境),你应该首先安装 polkit-gnome ,然后粘贴下面的行到 i3 配置文件:
+
+```
+exec /usr/lib/polkit-gnome/polkit-gnome-authentication-agent-1 &
+```
+
+### 使用 Kindd 创建可启动的 ISO
+
+为从一个 ISO 创建一个可启动的 USB,插入 USB 驱动器。然后,从菜单或终端启动 Kindd 。
+
+这是 Kindd 默认界面的外观:
+
+![][5]
+
+*Kindd 界面*
+
+正如你所能看到的,Kindd 界面是非常简单的和明白易懂的。这里仅有两部分,即设备列表,它显示你的系统上的可用的设备(hdd 和 Usb),并创建可启动的 .iso 。默认情况下,你将在“创建可启动 .iso”部分。
+
+在第一列中输入块大小,在第二列中选择 ISO 文件的路径,并在第三列中选择正确的设备(USB 驱动器路径)。单击“转换/复制”按钮来开始创建可启动的 ISO 。
+
+![][6]
+
+一旦进程被完成,你将看到成功的信息。
+
+![][7]
+
+现在,拔出 USB 驱动器,并用该 USB 启动器启动你的系统,来检查它是否真地工作。
+
+如果你不知道真实的设备名称(目标路径),只需要在列出的设备上单击,并检查 USB 驱动器名称。
+
+![][8]
+
+Kindd 还处在早期开发阶段。因此,可能有错误。如果你找到一些错误,请在这篇的指南的结尾所给的 GitHub 页面报告它们。
+
+这就是全部。希望这是有用的。更多的好东西将会来。敬请期待!
+
+谢谢!
+
+资源:
+
+ * [Kindd GitHub 储存库][11]
+
+相关阅读:
+
+ * [Etcher:一个来创建可启动 SD 卡或 USB 驱动器的漂亮的应用程序][9]
+ * [Bootiso 让你安全地创建可启动的 USB 驱动器][10]
+
+--------------------------------------------------------------------------------
+
+via: https://www.ostechnix.com/kindd-a-graphical-frontend-to-dd-command/
+
+作者:[sk][a]
+选题:[lujun9972][b]
+译者:[robsean](https://github.com/robsean)
+校对:[wxy](https://github.com/wxy)
+
+本文由 [LCTT](https://github.com/LCTT/TranslateProject) 原创编译,[Linux中国](https://linux.cn/) 荣誉推出
+
+[a]: https://www.ostechnix.com/author/sk/
+[b]: https://github.com/lujun9972
+[1]: https://www.ostechnix.com/wp-content/uploads/2019/04/kindd-720x340.png
+[2]: https://www.ostechnix.com/how-to-create-bootable-usb-drive-using-dd-command/
+[3]: https://aur.archlinux.org/packages/kindd-git/
+[4]: https://www.ostechnix.com/yay-found-yet-another-reliable-aur-helper/
+[5]: http://www.ostechnix.com/wp-content/uploads/2019/04/kindd-interface.png
+[6]: http://www.ostechnix.com/wp-content/uploads/2019/04/kindd-1.png
+[7]: http://www.ostechnix.com/wp-content/uploads/2019/04/kindd-2.png
+[8]: http://www.ostechnix.com/wp-content/uploads/2019/04/kindd-3.png
+[9]: https://www.ostechnix.com/etcher-beauitiful-app-create-bootable-sd-cards-usb-drives/
+[10]: https://www.ostechnix.com/bootiso-lets-you-safely-create-bootable-usb-drive/
+[11]: https://github.com/LinArcX/Kindd
diff --git a/published/201905/20190505 Linux Shell Script To Monitor Disk Space Usage And Send Email.md b/published/201905/20190505 Linux Shell Script To Monitor Disk Space Usage And Send Email.md
new file mode 100644
index 0000000000..c981988120
--- /dev/null
+++ b/published/201905/20190505 Linux Shell Script To Monitor Disk Space Usage And Send Email.md
@@ -0,0 +1,198 @@
+[#]: collector: (lujun9972)
+[#]: translator: (warmfrog)
+[#]: reviewer: (wxy)
+[#]: publisher: (wxy)
+[#]: url: (https://linux.cn/article-10868-1.html)
+[#]: subject: (Linux Shell Script To Monitor Disk Space Usage And Send Email)
+[#]: via: (https://www.2daygeek.com/linux-shell-script-to-monitor-disk-space-usage-and-send-email/)
+[#]: author: (Magesh Maruthamuthu https://www.2daygeek.com/author/magesh/)
+
+用 Linux Shell 脚本来监控磁盘使用情况并发送邮件
+============================================
+
+市场上有很多用来监控 Linux 系统的监控工具,当系统到达阀值后它将发送一封邮件。它监控所有的东西例如 CPU 利用率、内存利用率、交换空间利用率、磁盘空间利用率等等。然而,它更适合小环境和大环境。
+
+想一想如果你只有少量系统,那么什么是最好的方式来应对这种情况。
+
+是的,我们想要写一个 [shell 脚本][1] 来实现。
+
+在这篇指南中我们打算写一个 shell 脚本来监控系统的磁盘空间使用率。当系统到达给定的阀值,它将给对应的邮件地址发送一封邮件。在这篇文章中我们总共添加了四个 shell 脚本,每个用于不同的目的。之后,我们会想出其他 shell 脚本来监控 CPU,内存和交换空间利用率。
+
+在此之前,我想澄清一件事,根据我观察的磁盘空间使用率 shell 脚本使用情况。
+
+大多数用户在多篇博客中评论说,当他们运行磁盘空间使用率脚本时他们获得了以下错误。
+
+```
+# sh /opt/script/disk-usage-alert-old.sh
+
+/dev/mapper/vg_2g-lv_root
+test-script.sh: line 7: [: /dev/mapper/vg_2g-lv_root: integer expression expected
+/ 9.8G
+```
+
+是的,这是对的。甚至,当我第一次运行这个脚本的时候我遇到了相同的问题。之后,我发现了根本原因。
+
+当你在基于 RHEL 5 & RHEL 6 的系统上运行包含用于磁盘空间警告的 `df -h` 或 `df -H` 的 shell 脚本中时,你会发现上述错误信息,因为输出格式不对,查看下列输出。
+
+为了解决这个问题,我们需要用 `df -Ph` (POSIX 输出格式),但是默认的 `df -h` 在基于 RHEL 7 的系统上运行的很好。
+
+```
+# df -h
+
+Filesystem Size Used Avail Use% Mounted on
+/dev/mapper/vg_2g-lv_root
+ 10G 6.7G 3.4G 67% /
+tmpfs 7.8G 0 7.8G 0% /dev/shm
+/dev/sda1 976M 95M 830M 11% /boot
+/dev/mapper/vg_2g-lv_home
+ 5.0G 4.3G 784M 85% /home
+/dev/mapper/vg_2g-lv_tmp
+ 4.8G 14M 4.6G 1% /tmp
+```
+
+### 方法一:Linux Shell 脚本来监控磁盘空间使用率和发送邮件
+
+你可以使用下列 shell 脚本在 Linux 系统中来监控磁盘空间使用率。
+
+当系统到达给定的阀值限制时,它将发送一封邮件。在这个例子中,我们设置阀值为 60% 用于测试目的,你可以改变这个限制来符合你的需求。
+
+如果超过一个文件系统到达给定的阀值,它将发送多封邮件,因为这个脚本使用了循环。
+
+同样,替换你的邮件地址来获取这份警告。
+
+```
+# vi /opt/script/disk-usage-alert.sh
+
+#!/bin/sh
+df -Ph | grep -vE '^Filesystem|tmpfs|cdrom' | awk '{ print $5,$1 }' | while read output;
+do
+ echo $output
+ used=$(echo $output | awk '{print $1}' | sed s/%//g)
+ partition=$(echo $output | awk '{print $2}')
+ if [ $used -ge 60 ]; then
+ echo "The partition \"$partition\" on $(hostname) has used $used% at $(date)" | mail -s "Disk Space Alert: $used% Used On $(hostname)" [email protected]
+ fi
+done
+```
+
+输出:我获得了下列两封邮件警告。
+
+```
+The partition "/dev/mapper/vg_2g-lv_home" on 2g.CentOS7 has used 85% at Mon Apr 29 06:16:14 IST 2019
+
+The partition "/dev/mapper/vg_2g-lv_root" on 2g.CentOS7 has used 67% at Mon Apr 29 06:16:14 IST 2019
+```
+
+最终添加了一个 [cronjob][2] 来自动完成。它会每 10 分钟运行一次。
+
+```
+# crontab -e
+*/10 * * * * /bin/bash /opt/script/disk-usage-alert.sh
+```
+
+### 方法二:Linux Shell 脚本来监控磁盘空间使用率和发送邮件
+
+作为代替,你可以使用下列的 shell 脚本。对比上面的脚本我们做了少量改变。
+
+```
+# vi /opt/script/disk-usage-alert-1.sh
+
+#!/bin/sh
+df -Ph | grep -vE '^Filesystem|tmpfs|cdrom' | awk '{ print $5,$1 }' | while read output;
+do
+ max=60%
+ echo $output
+ used=$(echo $output | awk '{print $1}')
+ partition=$(echo $output | awk '{print $2}')
+ if [ ${used%?} -ge ${max%?} ]; then
+ echo "The partition \"$partition\" on $(hostname) has used $used at $(date)" | mail -s "Disk Space Alert: $used Used On $(hostname)" [email protected]
+ fi
+done
+```
+
+输出:我获得了下列两封邮件警告。
+
+
+```
+The partition "/dev/mapper/vg_2g-lv_home" on 2g.CentOS7 has used 85% at Mon Apr 29 06:16:14 IST 2019
+
+The partition "/dev/mapper/vg_2g-lv_root" on 2g.CentOS7 has used 67% at Mon Apr 29 06:16:14 IST 2019
+```
+
+最终添加了一个 [cronjob][2] 来自动完成。它会每 10 分钟运行一次。
+
+```
+# crontab -e
+*/10 * * * * /bin/bash /opt/script/disk-usage-alert-1.sh
+```
+
+### 方法三:Linux Shell 脚本来监控磁盘空间使用率和发送邮件
+
+我更喜欢这种方法。因为,它工作起来很有魔力,你只会收到一封关于所有事的邮件。
+
+这相当简单和直接。
+
+```
+*/10 * * * * df -Ph | sed s/%//g | awk '{ if($5 > 60) print $0;}' | mail -s "Disk Space Alert On $(hostname)" [email protected]
+```
+
+输出: 我获得了一封关于所有警告的邮件。
+
+```
+Filesystem Size Used Avail Use Mounted on
+/dev/mapper/vg_2g-lv_root 10G 6.7G 3.4G 67 /
+/dev/mapper/vg_2g-lv_home 5.0G 4.3G 784M 85 /home
+```
+
+### 方法四:Linux Shell 脚本来监控某个分区的磁盘空间使用情况和发送邮件
+
+```
+# vi /opt/script/disk-usage-alert-2.sh
+
+#!/bin/bash
+used=$(df -Ph | grep '/dev/mapper/vg_2g-lv_dbs' | awk {'print $5'})
+max=80%
+if [ ${used%?} -ge ${max%?} ]; then
+echo "The Mount Point "/DB" on $(hostname) has used $used at $(date)" | mail -s "Disk space alert on $(hostname): $used used" [email protected]
+fi
+```
+
+输出: 我得到了下面的邮件警告。
+
+```
+The partition /dev/mapper/vg_2g-lv_dbs on 2g.CentOS6 has used 82% at Mon Apr 29 06:16:14 IST 2019
+```
+
+最终添加了一个 [cronjob][2] 来自动完成这些工作。它将每 10 分钟运行一次。
+
+```
+# crontab -e
+*/10 * * * * /bin/bash /opt/script/disk-usage-alert-2.sh
+```
+
+注意: 你将在 10 分钟后收到一封邮件警告,因为这个脚本被计划为每 10 分钟运行一次(但也不是精确的 10 分钟,取决于时间)。
+
+例如这个例子。如果你的系统在 8:25 到达了限制,你将在 5 分钟后收到邮件警告。希望现在讲清楚了。
+
+--------------------------------------------------------------------------------
+
+via: https://www.2daygeek.com/linux-shell-script-to-monitor-disk-space-usage-and-send-email/
+
+作者:[Magesh Maruthamuthu][a]
+选题:[lujun9972][b]
+译者:[warmfrog](https://github.com/warmfrog)
+校对:[wxy](https://github.com/wxy)
+
+本文由 [LCTT](https://github.com/LCTT/TranslateProject) 原创编译,[Linux中国](https://linux.cn/) 荣誉推出
+
+[a]: https://www.2daygeek.com/author/magesh/
+[b]: https://github.com/lujun9972
+[1]: https://www.2daygeek.com/category/shell-script/
+[2]: https://www.2daygeek.com/crontab-cronjob-to-schedule-jobs-in-linux/
+
+
+
+
+
+
+
diff --git a/published/201905/20190505 Ping Multiple Servers And Show The Output In Top-like Text UI.md b/published/201905/20190505 Ping Multiple Servers And Show The Output In Top-like Text UI.md
new file mode 100644
index 0000000000..8d90b5b520
--- /dev/null
+++ b/published/201905/20190505 Ping Multiple Servers And Show The Output In Top-like Text UI.md
@@ -0,0 +1,78 @@
+[#]: collector: (lujun9972)
+[#]: translator: (geekpi)
+[#]: reviewer: (wxy)
+[#]: publisher: (wxy)
+[#]: url: (https://linux.cn/article-10824-1.html)
+[#]: subject: (Ping Multiple Servers And Show The Output In Top-like Text UI)
+[#]: via: (https://www.ostechnix.com/ping-multiple-servers-and-show-the-output-in-top-like-text-ui/)
+[#]: author: (sk https://www.ostechnix.com/author/sk/)
+
+ping 多台服务器并在类似 top 的界面中显示
+======
+
+![Ping Multiple Servers And Show The Output In Top-like Text UI][1]
+
+不久前,我们写了篇关于 [fping][2] 的文章,该程序能使我们能够同时 ping 多台主机。与传统的 `ping` 不同,`fping` 不会等待一台主机的超时。它使用循环法,这表示它将 ICMP Echo 请求发送到一台主机,然后转到另一台主机,最后一次显示哪些主机开启或关闭。今天,我们将讨论一个名为 `pingtop` 的类似程序。顾名思义,它会一次 ping 多台服务器,并在类似 `top` 的终端 UI 中显示结果。它是用 Python 写的自由开源程序。
+
+### 安装 pingtop
+
+可以使用 `pip` 安装 `pingtop`,`pip` 是一个软件包管理器,用于安装用 Python 开发的程序。确保已在 Linux 中安装了 Python 3.7.x 和 pip。
+
+要在 Linux 上安装 `pip`,请参阅以下链接。
+
+* [如何使用 pip 管理 Python 包][3]
+
+安装 `pip` 后,运行以下命令安装 `pingtop`:
+
+```
+$ pip install pingtop
+```
+
+现在让我们继续使用 `pingtop` ping 多个系统。
+
+### ping 多台服务器并在类似 top 的终端 UI 中显示
+
+要 ping 多个主机/系统,请运行:
+
+```
+$ pingtop ostechnix.com google.com facebook.com twitter.com
+```
+
+现在,你将在一个漂亮的类似 `top` 的终端 UI 中看到结果,如下所示。
+
+![][4]
+
+*使用 pingtop ping 多台服务器*
+
+
+建议阅读:
+
+ * [一些你可能想知道的替代 “top” 命令的程序][5]
+
+我个人目前没有使用 pingtop 的情况。但我喜欢在这个在文本界面中展示 ping 命令输出的想法。试试看它,也许有帮助。
+
+就是这些了。还有更多好东西。敬请期待!干杯!
+
+资源:
+
+ * [pingtop GitHub 仓库][6]
+
+--------------------------------------------------------------------------------
+
+via: https://www.ostechnix.com/ping-multiple-servers-and-show-the-output-in-top-like-text-ui/
+
+作者:[sk][a]
+选题:[lujun9972][b]
+译者:[geekpi](https://github.com/geekpi)
+校对:[wxy](https://github.com/wxy)
+
+本文由 [LCTT](https://github.com/LCTT/TranslateProject) 原创编译,[Linux中国](https://linux.cn/) 荣誉推出
+
+[a]: https://www.ostechnix.com/author/sk/
+[b]: https://github.com/lujun9972
+[1]: https://www.ostechnix.com/wp-content/uploads/2019/04/pingtop-720x340.png
+[2]: https://www.ostechnix.com/ping-multiple-hosts-linux/
+[3]: https://linux.cn/article-10110-1.html
+[4]: http://www.ostechnix.com/wp-content/uploads/2019/04/pingtop-1.gif
+[5]: https://www.ostechnix.com/some-alternatives-to-top-command-line-utility-you-might-want-to-know/
+[6]: https://github.com/laixintao/pingtop
diff --git a/published/201905/20190505 apt-clone - Backup Installed Packages And Restore Those On Fresh Ubuntu System.md b/published/201905/20190505 apt-clone - Backup Installed Packages And Restore Those On Fresh Ubuntu System.md
new file mode 100644
index 0000000000..fa7db2e2bb
--- /dev/null
+++ b/published/201905/20190505 apt-clone - Backup Installed Packages And Restore Those On Fresh Ubuntu System.md
@@ -0,0 +1,111 @@
+[#]: collector: (lujun9972)
+[#]: translator: (geekpi)
+[#]: reviewer: (wxy)
+[#]: publisher: (wxy)
+[#]: url: (https://linux.cn/article-10837-1.html)
+[#]: subject: (apt-clone : Backup Installed Packages And Restore Those On Fresh Ubuntu System)
+[#]: via: (https://www.2daygeek.com/apt-clone-backup-installed-packages-and-restore-them-on-fresh-ubuntu-system/)
+[#]: author: (Magesh Maruthamuthu https://www.2daygeek.com/author/magesh/)
+
+apt-clone:备份已安装的软件包并在新的 Ubuntu 系统上恢复它们
+======
+
+当我们在基于 Ubuntu/Debian 的系统上使用 `apt-clone`,包安装会变得更加容易。如果你需要在少量系统上安装相同的软件包时,`apt-clone` 会适合你。
+
+如果你想在每个系统上手动构建和安装必要的软件包,这是一个耗时的过程。它可以通过多种方式实现,Linux 中有许多程序可用。我们过去曾写过一篇关于 [Aptik][1] 的文章。它是能让 Ubuntu 用户备份和恢复系统设置和数据的程序之一。
+
+### 什么是 apt-clone?
+
+[apt-clone][2] 能让你为 Debian/Ubuntu 系统创建所有已安装软件包的备份,这些软件包可以在新安装的系统(或容器)或目录中恢复。
+
+该备份可以在相同操作系统版本和架构的多个系统上还原。
+
+### 如何安装 apt-clone?
+
+`apt-clone` 包可以在 Ubuntu/Debian 的官方仓库中找到,所以,使用 [apt 包管理器][3] 或 [apt-get 包管理器][4] 来安装它。
+
+使用 `apt` 包管理器安装 `apt-clone`。
+
+```
+$ sudo apt install apt-clone
+```
+
+使用 `apt-get` 包管理器安装 `apt-clone`。
+
+```
+$ sudo apt-get install apt-clone
+```
+
+### 如何使用 apt-clone 备份已安装的软件包?
+
+成功安装 `apt-clone` 之后。只需提供一个保存备份文件的位置。我们将在 `/backup` 目录下保存已安装的软件包备份。
+
+`apt-clone` 会将已安装的软件包列表保存到 `apt-clone-state-Ubuntu18.2daygeek.com.tar.gz` 中。
+
+```
+$ sudo apt-clone clone /backup
+```
+
+我们同样可以通过运行 `ls` 命令来检查。
+
+```
+$ ls -lh /backup/
+total 32K
+-rw-r--r-- 1 root root 29K Apr 20 19:06 apt-clone-state-Ubuntu18.2daygeek.com.tar.gz
+```
+
+运行以下命令,查看备份文件的详细信息。
+
+```
+$ apt-clone info /backup/apt-clone-state-Ubuntu18.2daygeek.com.tar.gz
+Hostname: Ubuntu18.2daygeek.com
+Arch: amd64
+Distro: bionic
+Meta: libunity-scopes-json-def-desktop, ubuntu-desktop
+Installed: 1792 pkgs (194 automatic)
+Date: Sat Apr 20 19:06:43 2019
+```
+
+根据上面的输出,备份文件中总共有 1792 个包。
+
+### 如何恢复使用 apt-clone 进行备份的软件包?
+
+你可以使用任何远程复制程序来复制远程服务器上的文件。
+
+```
+$ scp /backup/apt-clone-state-ubunt-18-04.tar.gz Destination-Server:/opt
+```
+
+复制完成后,使用 `apt-clone` 执行还原。
+
+使用以下命令进行还原。
+
+```
+$ sudo apt-clone restore /opt/apt-clone-state-Ubuntu18.2daygeek.com.tar.gz
+```
+
+请注意,还原将覆盖现有的 `/etc/apt/sources.list` 并安装/删除包。所以要小心。
+
+如果你要将所有软件包还原到文件夹而不是实际还原,可以使用以下命令。
+
+```
+$ sudo apt-clone restore /opt/apt-clone-state-Ubuntu18.2daygeek.com.tar.gz --destination /opt/oldubuntu
+```
+
+--------------------------------------------------------------------------------
+
+via: https://www.2daygeek.com/apt-clone-backup-installed-packages-and-restore-them-on-fresh-ubuntu-system/
+
+作者:[Magesh Maruthamuthu][a]
+选题:[lujun9972][b]
+译者:[geekpi](https://github.com/geekpi)
+校对:[wxy](https://github.com/wxy)
+
+本文由 [LCTT](https://github.com/LCTT/TranslateProject) 原创编译,[Linux中国](https://linux.cn/) 荣誉推出
+
+[a]: https://www.2daygeek.com/author/magesh/
+[b]: https://github.com/lujun9972
+[1]: https://www.2daygeek.com/aptik-backup-restore-ppas-installed-apps-users-data/
+[2]: https://github.com/mvo5/apt-clone
+[3]: https://www.2daygeek.com/apt-command-examples-manage-packages-debian-ubuntu-systems/
+[4]: https://www.2daygeek.com/apt-get-apt-cache-command-examples-manage-packages-debian-ubuntu-systems/
diff --git a/published/201905/20190506 How to Add Application Shortcuts on Ubuntu Desktop.md b/published/201905/20190506 How to Add Application Shortcuts on Ubuntu Desktop.md
new file mode 100644
index 0000000000..2e6946ac79
--- /dev/null
+++ b/published/201905/20190506 How to Add Application Shortcuts on Ubuntu Desktop.md
@@ -0,0 +1,118 @@
+[#]: collector: (lujun9972)
+[#]: translator: (warmfrog)
+[#]: reviewer: (wxy)
+[#]: publisher: (wxy)
+[#]: url: (https://linux.cn/article-10872-1.html)
+[#]: subject: (How to Add Application Shortcuts on Ubuntu Desktop)
+[#]: via: (https://itsfoss.com/ubuntu-desktop-shortcut/)
+[#]: author: (Abhishek Prakash https://itsfoss.com/author/abhishek/)
+
+如何在 Ubuntu 桌面手动添加应用快捷方式
+===============================
+
+> 在这篇快速指南中,你将学到如何在 Ubuntu 桌面和其他使用 GNOME 桌面的发行版中添加应用图标。
+
+一个经典的桌面操作系统在“桌面屏”上总是有图标的。这些桌面图标包括文件管理器、回收站和应用图标。
+
+当在 Windows 中安装应用时,一些程序会询问你是否在桌面创建一个快捷方式。但在 Linux 系统中不是这样。
+
+但是如果你热衷于这个特点,让我给你展示如何在 Ubuntu 桌面和其他使用 GNOME 桌面的发行版中创建应用的快捷方式。
+
+![Application Shortcuts on Desktop in Ubuntu with GNOME desktop][2]
+
+如果你想知道我的桌面外观,我正在使用 Ant 主题和 Tela 图标集。你可以获取一些 [GTK 主题][3] 和 [为 Ubuntu 准备的图标集][4]并换成你喜欢的。
+
+### 在 Ubuntu 中添加桌面快捷方式
+
+![][5]
+
+个人来讲,我更喜欢为应用图标准备的 Ubuntu 启动器方式。如果我经常使用一个程序,我会添加到启动器。但是我知道不是每个人都有相同的偏好,可能少数人更喜欢桌面的快捷方式。
+
+让我们看在桌面中创建应用快捷方式的最简单方式。
+
+> 免责声明
+
+> 这篇指南已经在 Ubuntu 18.04 LTS 的 GNOME 桌面上测试过了。它可能在其他发行版和桌面环境上也能发挥作用,但你必须自己尝试。一些 GNOME 特定步骤可能会变,所以请在[其他桌面环境][7]尝试时注意。
+
+#### 准备
+
+首先最重要的事是确保你有 GNOME 桌面的图标权限。
+
+如果你跟随 Ubuntu 18.04 自定义提示,你会知道如何安装 GNOME Tweaks 工具。在这个工具中,确保你设置“Show Icons”选项为启用。
+
+![Allow icons on desktop in GNOME][9]
+
+一旦你确保已经设置,是时候在桌面添加应用快捷方式了。
+
+#### 第一步:定位应用的 .desktop 文件
+
+到 “Files -> Other Location -> Computer”。
+
+![Go to Other Locations -> Computer][11]
+
+从这里,到目录 “usr -> share -> applications”。你会在这里看到几个你已经安装的 [Ubuntu 应用][12]。即使你没有看到图标,你应该看到被命名为“应用名.desktop”形式的文件。
+
+![Application Shortcuts][13]
+
+#### 第二步:拷贝 .desktop 文件到桌面
+
+现在你要做的只是查找应用图标(或者它的 desktop 文件)。当你找到后,拖文件到桌面或者拷贝文件(使用 `Ctrl+C` 快捷方式)并在桌面粘贴(使用 `Ctrl+V` 快捷方式)。
+
+![Add .desktop file to the desktop][14]
+
+#### 第三步:运行 desktop 文件
+
+当你这么做,你应该在桌面上看到一个图标的文本文件而不是应用 logo。别担心,一会就不一样了。
+
+你要做的就是双击桌面的那个文件。它将警告你它是一个“未信任的应用启动器’,点击“信任并启动”。
+
+![Launch Desktop Shortcut][15]
+
+这个应用像往常一样启动,好事是你会察觉到 .desktop 文件现在已经变成应用图标了。我相信你喜欢应用图标的方式,不是吗?
+
+![Application shortcut on the desktop][16]
+
+#### Ubuntu 19.04 或者 GNOME 3.32 用户的疑难杂症
+
+如果你使用 Ubuntu 19.04 或者 GNOME 3.32,你的 .desktop 文件可能根本不会启动。你应该右击 .desktop 文件并选择 “允许启动”。
+
+在这之后,你应该能够启动应用并且桌面上的应用快捷方式能够正常显示了。
+
+### 总结
+
+如果你不喜欢桌面的某个应用启动器,选择删除就是了。它会删除应用快捷方式,但是应用仍安全的保留在你的系统中。
+
+我希望你发现这篇快速指南有帮助并喜欢在 Ubuntu 桌面上的应用快捷方式。
+
+如果你有问题或建议,请在下方评论让我知道。
+
+--------------------------------------------------------------------------------
+
+via: https://itsfoss.com/ubuntu-desktop-shortcut/
+
+作者:[Abhishek Prakash][a]
+选题:[lujun9972][b]
+译者:[warmfrog](https://github.com/warmfrog)
+校对:[wxy](https://github.com/wxy)
+
+本文由 [LCTT](https://github.com/LCTT/TranslateProject) 原创编译,[Linux中国](https://linux.cn/) 荣誉推出
+
+[a]: https://itsfoss.com/author/abhishek/
+[b]: https://github.com/lujun9972
+[1]: https://www.ubuntu.com/
+[2]: https://i2.wp.com/itsfoss.com/wp-content/uploads/2019/05/app-shortcut-on-ubuntu-desktop.jpeg?resize=800%2C450&ssl=1
+[3]: https://itsfoss.com/best-gtk-themes/
+[4]: https://itsfoss.com/best-icon-themes-ubuntu-16-04/
+[5]: https://i1.wp.com/itsfoss.com/wp-content/uploads/2019/05/add-ubuntu-desktop-shortcut.jpeg?resize=800%2C450&ssl=1
+[6]: https://www.gnome.org/
+[7]: https://itsfoss.com/best-linux-desktop-environments/
+[8]: https://www.youtube.com/c/itsfoss?sub_confirmation=1
+[9]: https://i0.wp.com/itsfoss.com/wp-content/uploads/2019/05/allow-icons-on-desktop-gnome.jpg?ssl=1
+[10]: https://itsfoss.com/replace-linux-from-dual-boot/
+[11]: https://i0.wp.com/itsfoss.com/wp-content/uploads/2019/05/Adding-desktop-shortcut-Ubuntu-gnome-1.png?resize=800%2C436&ssl=1
+[12]: https://itsfoss.com/best-ubuntu-apps/
+[13]: https://i1.wp.com/itsfoss.com/wp-content/uploads/2019/05/application-shortcuts-in-ubuntu.png?resize=800%2C422&ssl=1
+[14]: https://i0.wp.com/itsfoss.com/wp-content/uploads/2019/05/add-desktop-file-to-desktop.jpeg?resize=800%2C458&ssl=1
+[15]: https://i2.wp.com/itsfoss.com/wp-content/uploads/2019/05/launch-desktop-shortcut-.jpeg?resize=800%2C349&ssl=1
+[16]: https://i2.wp.com/itsfoss.com/wp-content/uploads/2019/05/app-shortcut-on-desktop-ubuntu-gnome.jpeg?resize=800%2C375&ssl=1
+[17]: https://itsfoss.com/install-nemo-file-manager-ubuntu/
diff --git a/published/201905/20190508 How to use advanced rsync for large Linux backups.md b/published/201905/20190508 How to use advanced rsync for large Linux backups.md
new file mode 100644
index 0000000000..694158d9d4
--- /dev/null
+++ b/published/201905/20190508 How to use advanced rsync for large Linux backups.md
@@ -0,0 +1,139 @@
+[#]: collector: (lujun9972)
+[#]: translator: (warmfrog)
+[#]: reviewer: (wxy)
+[#]: publisher: (wxy)
+[#]: url: (https://linux.cn/article-10865-1.html)
+[#]: subject: (How to use advanced rsync for large Linux backups)
+[#]: via: (https://opensource.com/article/19/5/advanced-rsync)
+[#]: author: (Alan Formy-Duval https://opensource.com/users/alanfdoss/users/marcobravo)
+
+如何使用 rsync 的高级用法进行大型备份
+=====================================
+
+> 基础的 `rsync` 命令通常足够来管理你的 Linux 备份,但是额外的选项使大型备份集更快、更强大。
+
+![Filing papers and documents][1]
+
+很明显,备份一直是 Linux 世界的热门话题。回到 2017,David Both 为 [Opensource.com][2] 的读者在[使用 rsync 备份 Linux 系统][3]方面提了一些建议,在这年的更早时候,他发起了一项问卷调查询问大家,[在 Linux 中你的 /home 目录的主要备份策略是什么][4],在今年的另一个问卷调查中,Don Watkins 问到,[你使用哪种开源备份解决方案][5]。
+
+我的回复是 [rsync][6]。我真的非常喜欢 rsync!市场上有大量大而复杂的工具,对于管理磁带机或者存储库设备,这些可能是必要的,但是可能你需要的只是一个简单的开源命令行工具。
+
+### rsync 基础
+
+我为一个大概拥有 35,000 开发者并有着几十 TB 文件的全球性机构管理二进制仓库。我经常一次移动或者归档上百 GB 的数据。使用的是 `rsync`。这种经历使我对这个简单的工具充满信心。(所以,是的,我在家使用它来备份我的 Linux 系统)
+
+基础的 `rsync` 命令很简单。
+
+
+```
+rsync -av 源目录 目的地目录
+```
+
+实际上,在各种指南中教的 `rsync` 命令在大多数通用情况下都运行的很好。然而,假设我们需要备份大量的数据。例如包含 2,000 个子目录的目录,每个包含 50GB 到 700GB 的数据。在这个目录运行 `rsync` 可能需要大量时间,尤其是当你使用校验选项时(我倾向使用)。
+
+当我们试图同步大量数据或者通过慢的网络连接时,可能遇到性能问题。让我给你展示一些我使用的方法来确保好的性能和可靠性。
+
+### rsync 高级用法
+
+`rsync` 运行时出现的第一行是:“正在发送增量文件列表。” 如果你在网上搜索这一行,你将看到很多类似的问题:为什么它一直运行,或者为什么它似乎挂起了。
+
+这里是一个基于这个场景的例子。假设我们有一个 `/storage` 的目录,我们想要备份到一个外部 USB 磁盘,我们可以使用下面的命令:
+
+```
+rsync -cav /storage /media/WDPassport
+```
+
+`-c` 选项告诉 `rsync` 使用文件校验和而不是时间戳来决定改变的文件,这通常消耗的时间更久。为了分解 `/storage` 目录,我通过子目录同步,使用 `find` 命令。这是一个例子:
+
+
+```
+find /storage -type d -exec rsync -cav {} /media/WDPassport \;
+```
+
+这看起来可以,但是如果 `/storage` 目录有任何文件,它们将被跳过。因此,我们如何同步 `/storage` 目录中的文件呢?同样有一个细微的差别是这些选项将造成 `rsync` 会同步 `.` 目录,该目录是源目录自身;这意味着它会同步子目录两次,这并不是我们想要的。
+
+长话短说,我的解决方案是一个 “双-递增”脚本。这允许我分解一个目录,例如,当你的家目录有多个大的目录,例如音乐或者家庭照片时,分解 `/home` 目录为单个的用户家目录。
+
+这是我的脚本的一个例子:
+
+```
+HOMES="alan"
+DRIVE="/media/WDPassport"
+
+for HOME in $HOMES; do
+cd /home/$HOME
+rsync -cdlptgov --delete . /$DRIVE/$HOME
+find . -maxdepth 1 -type d -not -name "." -exec rsync -crlptgov --delete {} /$DRIVE/$HOME \;
+done
+```
+
+第一个 `rsync` 命令拷贝它在源目录中发现的文件和目录。然而,它将目录留着不处理,因此我们能够通过 `find` 命令迭代它们。这通过传递 `-d` 参数来完成,它告诉 `rsync` 不要递归目录。
+
+
+```
+-d, --dirs 传输目录而不递归
+```
+
+然后 `find` 命令传递每个目录来单独运行 `rsync`。之后 `rsync` 拷贝目录的内容。这通过传递 `-r` 参数来完成,它告诉 `rsync` 要递归目录。
+
+
+```
+-r, --recursive 递归进入目录
+```
+
+这使得 `rsync` 使用的增量文件保持在一个合理的大小。
+
+大多数 `rsync` 指南为了简便使用 `-a` (或者 `archive`) 参数。这实际是一个复合参数。
+
+```
+-a, --archive 归档模式;等价于 -rlptgoD(没有 -H,-A,-X)
+```
+
+我传递的其他参数包含在 `a` 中;这些是 `-l`、`-p`、`-t`、`-g`和 `-o`。
+
+
+```
+-l, --links 复制符号链接作为符号链接
+-p, --perms 保留权限
+-t, --times 保留修改时间
+-g, --group 保留组
+-o, --owner 保留拥有者(只适用于超级管理员)
+```
+
+`--delete` 选项告诉 `rsync` 删除目的地目录中所有在源目录不存在的任意文件。这种方式,运行的结果仅仅是复制。你同样可以排除 `.Trash` 目录或者 MacOS 创建的 `.DS_Store` 文件。
+
+
+```
+-not -name ".Trash*" -not -name ".DS_Store"
+```
+
+### 注意
+
+最后一条建议: `rsync` 可以是破坏性的命令。幸运的是,它的睿智的创造者提供了 “空运行” 的能力。如果我们加入 `n` 选项,rsync 会显示预期的输出但不写任何数据。
+
+
+```
+`rsync -cdlptgovn --delete . /$DRIVE/$HOME`
+```
+
+这个脚本适用于非常大的存储规模和高延迟或者慢链接的情况。一如既往,我确信仍有提升的空间。如果你有任何建议,请在下方评论中分享。
+
+--------------------------------------------------------------------------------
+
+via: https://opensource.com/article/19/5/advanced-rsync
+
+作者:[Alan Formy-Duval][a]
+选题:[lujun9972][b]
+译者:[warmfrog](https://github.com/warmfrog)
+校对:[wxy](https://github.com/wxy)
+
+本文由 [LCTT](https://github.com/LCTT/TranslateProject) 原创编译,[Linux中国](https://linux.cn/) 荣誉推出
+
+[a]: https://opensource.com/users/alanfdoss/users/marcobravo
+[b]: https://github.com/lujun9972
+[1]: https://opensource.com/sites/default/files/styles/image-full-size/public/lead-images/documents_papers_file_storage_work.png?itok=YlXpAqAJ (Filing papers and documents)
+[2]: http://Opensource.com
+[3]: https://linux.cn/article-8237-1.html
+[4]: https://opensource.com/poll/19/4/backup-strategy-home-directory-linux
+[5]: https://opensource.com/article/19/2/linux-backup-solutions
+[6]: https://en.wikipedia.org/wiki/Rsync
diff --git a/published/201905/20190509 21 Best Kali Linux Tools for Hacking and Penetration Testing.md b/published/201905/20190509 21 Best Kali Linux Tools for Hacking and Penetration Testing.md
new file mode 100644
index 0000000000..f3ac78e47a
--- /dev/null
+++ b/published/201905/20190509 21 Best Kali Linux Tools for Hacking and Penetration Testing.md
@@ -0,0 +1,263 @@
+[#]: collector: (lujun9972)
+[#]: translator: (wxy)
+[#]: reviewer: (wxy)
+[#]: publisher: (wxy)
+[#]: url: (https://linux.cn/article-10860-1.html)
+[#]: subject: (21 Best Kali Linux Tools for Hacking and Penetration Testing)
+[#]: via: (https://itsfoss.com/best-kali-linux-tools/)
+[#]: author: (Ankush Das https://itsfoss.com/author/ankush/)
+
+用于黑客渗透测试的 21 个最佳 Kali Linux 工具
+======
+
+> 这里是最好的 Kali Linux 工具列表,它们可以让你评估 Web 服务器的安全性,并帮助你执行黑客渗透测试。
+
+如果你读过 [Kali Linux 点评][1],你就知道为什么它被认为是[最好的黑客渗透测试的 Linux 发行版][2]之一,而且名副其实。它带有许多工具,使你可以更轻松地测试、破解以及进行与数字取证相关的任何其他工作。
+
+它是道德黑客最推荐的 Linux 发行版之一。即使你不是黑客而是网站管理员 —— 你仍然可以利用其中某些工具轻松地扫描你的网络服务器或网页。
+
+在任何一种情况下,无论你的目的是什么 —— 让我们来看看你应该使用的一些最好的 Kali Linux 工具。
+
+*注意:这里不是所提及的所有工具都是开源的。*
+
+### 用于黑客渗透测试的 Kali Linux 工具
+
+
+
+Kali Linux 预装了几种类型的工具。如果你发现有的工具没有安装,只需下载并进行设置即可。这很简单。
+
+#### 1、Nmap
+
+![Kali Linux Nmap][4]
+
+[Nmap][5] (即 “网络映射器”)是 Kali Linux 上最受欢迎的信息收集工具之一。换句话说,它可以获取有关主机的信息:其 IP 地址、操作系统检测以及网络安全的详细信息(如开放的端口数量及其含义)。
+
+它还提供防火墙规避和欺骗功能。
+
+#### 2、Lynis
+
+![Lynis Kali Linux Tool][6]
+
+[Lynis][7] 是安全审计、合规性测试和系统强化的强大工具。当然,你也可以将其用于漏洞检测和渗透测试。
+
+它将根据检测到的组件扫描系统。例如,如果它检测到 Apache —— 它将针对入口信息运行与 Apache 相关的测试。
+
+#### 3、WPScan
+
+![][8]
+
+WordPress 是[最好的开源 CMS][9]之一,而这个工具是最好的免费 WordpPress 安全审计工具。它是免费的,但不是开源的。
+
+如果你想知道一个 WordPress 博客是否在某种程度上容易受到攻击,[WPScan][10] 就是你的朋友。
+
+此外,它还为你提供了所用的插件的详细信息。当然,一个安全性很好的博客可能不会暴露给你很多细节,但它仍然是 WordPress 安全扫描找到潜在漏洞的最佳工具。
+
+#### 4、Aircrack-ng
+
+![][11]
+
+[Aircrack-ng][12] 是评估 WiFi 网络安全性的工具集合。它不仅限于监控和获取信息 —— 还包括破坏网络(WEP、WPA 1 和 WPA 2)的能力。
+
+如果你忘记了自己的 WiFi 网络的密码,可以尝试使用它来重新获得访问权限。它还包括各种无线攻击能力,你可以使用它们来定位和监控 WiFi 网络以增强其安全性。
+
+#### 5、Hydra
+
+![][13]
+
+如果你正在寻找一个有趣的工具来破解登录密码,[Hydra][14] 将是 Kali Linux 预装的最好的工具之一。
+
+它可能不再被积极维护,但它现在放在 [GitHub][15] 上,所以你也可以为它做贡献。
+
+#### 6、Wireshark
+
+![][17]
+
+[Wireshark][18] 是 Kali Linux 上最受欢迎的网络分析仪。它也可以归类为用于网络嗅探的最佳 Kali Linux 工具之一。
+
+它正在积极维护,所以我肯定会建议你试试它。
+
+#### 7、Metasploit Framework
+
+![][19]
+
+[Metsploit Framework][20](MSF)是最常用的渗透测试框架。它提供两个版本:一个开源版,另外一个是其专业版。使用此工具,你可以验证漏洞、测试已知漏洞并执行完整的安全评估。
+
+当然,免费版本不具备所有功能,所以如果你在意它们的区别,你应该在[这里][21]比较一下版本。
+
+#### 8、Skipfish
+
+![][22]
+
+与 WPScan 类似,但它不仅仅专注于 WordPress。[Skipfish][23] 是一个 Web 应用扫描程序,可以为你提供几乎所有类型的 Web 应用程序的洞察信息。它快速且易于使用。此外,它的递归爬取方法使它更好用。
+
+Skipfish 生成的报告可以用于专业的 Web 应用程序安全评估。
+
+#### 9、Maltego
+
+![][24]
+
+[Maltego][25] 是一种令人印象深刻的数据挖掘工具,用于在线分析信息并连接信息点(如果有的话)。 根据这些信息,它创建了一个有向图,以帮助分析这些数据之间的链接。
+
+请注意,这不是一个开源工具。
+
+它已预装,但你必须注册才能选择要使用的版本。如果个人使用,社区版就足够了(只需要注册一个帐户),但如果想用于商业用途,则需要订阅 classic 或 XL 版本。
+
+#### 10、Nessus
+
+![Nessus][26]
+
+如果你的计算机连接到了网络,Nessus 可以帮助你找到潜在攻击者可能利用的漏洞。当然,如果你是多台连接到网络的计算机的管理员,则可以使用它并保护这些计算机。
+
+但是,它不再是免费的工具了,你可以从[官方网站][27]免费试用 7 天。
+
+#### 11、Burp Suite Scanner
+
+![][28]
+
+[Burp Suite Scanner][29] 是一款出色的网络安全分析工具。与其它 Web 应用程序安全扫描程序不同,Burp 提供了 GUI 和一些高级工具。
+
+社区版仅将功能限制为一些基本的手动工具。对于专业人士,你必须考虑升级。与前面的工具类似,这也不是开源的。
+
+我使用过免费版本,但是如果你想了解更多细节,你应该查看他们[官方网站][29]上提供的功能。
+
+#### 12、BeEF
+
+![][30]
+
+BeEF(浏览器利用框架)是另一个令人印象深刻的工具。它专为渗透测试人员量身定制,用于评估 Web 浏览器的安全性。
+
+这是最好的 Kali Linux 工具之一,因为很多用户在谈论 Web 安全时希望了解并修复客户端的问题。
+
+#### 13、Apktool
+
+![][31]
+
+[Apktool][32] 确实是 Kali Linux 上用于逆向工程 Android 应用程序的流行工具之一。当然,你应该正确利用它 —— 出于教育目的。
+
+使用此工具,你可以自己尝试一下,并让原开发人员了解你的想法。你认为你会用它做什么?
+
+#### 14、sqlmap
+
+![][34]
+
+如果你正在寻找一个开源渗透测试工具 —— [sqlmap][35] 是最好的之一。它可以自动化利用 SQL 注入漏洞的过程,并帮助你接管数据库服务器。
+
+#### 15、John the Ripper
+
+![John The Ripper][36]
+
+[John the Ripper][37] 是 Kali Linux 上流行的密码破解工具。它也是自由开源的。但是,如果你对[社区增强版][37]不感兴趣,可以用于商业用途的[专业版][38]。
+
+#### 16、Snort
+
+想要实时流量分析和数据包记录功能吗?[Snort][39] 可以鼎力支持你。即使它是一个开源的入侵防御系统,也有很多东西可以提供。
+
+如果你还没有安装它,[官方网站][40]提及了安装过程。
+
+#### 17、Autopsy Forensic Browser
+
+![][41]
+
+[Autopsy][42] 是一个数字取证工具,用于调查计算机上发生的事情。那么,你也可以使用它从 SD 卡恢复图像。它也被执法官员使用。你可以阅读[文档][43]来探索可以用它做什么。
+
+你还应该查看他们的 [GitHub 页面][44]。
+
+#### 18、King Phisher
+
+![King Phisher][45]
+
+网络钓鱼攻击现在非常普遍。[King Phisher 工具][46]可以通过模拟真实的网络钓鱼攻击来帮助测试和提升用户意识。出于显而易见的原因,在模拟一个组织的服务器内容前,你需要获得许可。
+
+#### 19、Nikto
+
+![Nikto][47]
+
+[Nikto][48] 是一款功能强大的 Web 服务器扫描程序 —— 这使其成为最好的 Kali Linux 工具之一。 它会检查存在潜在危险的文件/程序、过时的服务器版本等等。
+
+#### 20、Yersinia
+
+![][49]
+
+[Yersinia][50] 是一个有趣的框架,用于在网络上执行第 2 层攻击(第 2 层是指 [OSI 模型][51]的数据链路层)。当然,如果你希望你的网络安全,则必须考虑所有七个层。但是,此工具侧重于第 2 层和各种网络协议,包括 STP、CDP,DTP 等。
+
+#### 21、Social Engineering Toolkit (SET)
+
+![][52]
+
+如果你正在进行相当严格的渗透测试,那么这应该是你应该检查的最佳工具之一。社交工程是一个大问题,使用 [SET][53] 工具,你可以帮助防止此类攻击。
+
+### 总结
+
+实际上 Kali Linux 捆绑了很多工具。请参考 Kali Linux 的[官方工具列表页面][54]来查找所有内容。
+
+你会发现其中一些是完全自由开源的,而有些则是专有解决方案(但是免费)。但是,出于商业目的,你应该始终选择高级版本。
+
+我们可能错过了你最喜欢的某个 Kali Linux 工具。请在下面的评论部分告诉我们。
+
+--------------------------------------------------------------------------------
+
+via: https://itsfoss.com/best-kali-linux-tools/
+
+作者:[Ankush Das][a]
+选题:[lujun9972][b]
+译者:[wxy](https://github.com/wxy)
+校对:[wxy](https://github.com/wxy)
+
+本文由 [LCTT](https://github.com/LCTT/TranslateProject) 原创编译,[Linux中国](https://linux.cn/) 荣誉推出
+
+[a]: https://itsfoss.com/author/ankush/
+[b]: https://github.com/lujun9972
+[1]: https://itsfoss.com/kali-linux-review/
+[2]: https://itsfoss.com/linux-hacking-penetration-testing/
+[3]: https://i1.wp.com/itsfoss.com/wp-content/uploads/2019/04/kali-linux-tools.jpg?resize=800%2C518&ssl=1
+[4]: https://i1.wp.com/itsfoss.com/wp-content/uploads/2019/04/kali-linux-nmap.jpg?resize=800%2C559&ssl=1
+[5]: https://nmap.org/
+[6]: https://i2.wp.com/itsfoss.com/wp-content/uploads/2019/04/lynis-kali-linux-tool.jpg?resize=800%2C525&ssl=1
+[7]: https://cisofy.com/lynis/
+[8]: https://i1.wp.com/itsfoss.com/wp-content/uploads/2019/04/wpscan-kali-linux.jpg?resize=800%2C545&ssl=1
+[9]: https://itsfoss.com/open-source-cms/
+[10]: https://wpscan.org/
+[11]: https://i2.wp.com/itsfoss.com/wp-content/uploads/2019/04/aircrack-ng-kali-linux-tool.jpg?resize=800%2C514&ssl=1
+[12]: https://www.aircrack-ng.org/
+[13]: https://i2.wp.com/itsfoss.com/wp-content/uploads/2019/04/hydra-kali-linux.jpg?resize=800%2C529&ssl=1
+[14]: https://github.com/vanhauser-thc/thc-hydra
+[15]: https://github.com/vanhauser-thc/THC-Archive
+[16]: https://itsfoss.com/new-linux-distros-2013/
+[17]: https://i0.wp.com/itsfoss.com/wp-content/uploads/2019/04/wireshark-network-analyzer.jpg?resize=800%2C556&ssl=1
+[18]: https://www.wireshark.org/
+[19]: https://i1.wp.com/itsfoss.com/wp-content/uploads/2019/04/metasploit-framework.jpg?resize=800%2C561&ssl=1
+[20]: https://github.com/rapid7/metasploit-framework
+[21]: https://www.rapid7.com/products/metasploit/download/editions/
+[22]: https://i2.wp.com/itsfoss.com/wp-content/uploads/2019/04/skipfish-kali-linux-tool.jpg?resize=800%2C515&ssl=1
+[23]: https://gitlab.com/kalilinux/packages/skipfish/
+[24]: https://i1.wp.com/itsfoss.com/wp-content/uploads/2019/04/maltego.jpg?resize=800%2C403&ssl=1
+[25]: https://www.paterva.com/web7/buy/maltego-clients.php
+[26]: https://i2.wp.com/itsfoss.com/wp-content/uploads/2019/05/nessus.jpg?resize=800%2C456&ssl=1
+[27]: https://www.tenable.com/try
+[28]: https://i0.wp.com/itsfoss.com/wp-content/uploads/2019/04/burp-suite-community-edition-800x582.jpg?resize=800%2C582&ssl=1
+[29]: https://portswigger.net/burp
+[30]: https://i1.wp.com/itsfoss.com/wp-content/uploads/2019/04/beef-framework.jpg?resize=800%2C339&ssl=1
+[31]: https://i0.wp.com/itsfoss.com/wp-content/uploads/2019/04/apktool.jpg?resize=800%2C504&ssl=1
+[32]: https://github.com/iBotPeaches/Apktool
+[33]: https://itsfoss.com/format-factory-alternative-linux/
+[34]: https://i1.wp.com/itsfoss.com/wp-content/uploads/2019/05/sqlmap.jpg?resize=800%2C528&ssl=1
+[35]: http://sqlmap.org/
+[36]: https://i2.wp.com/itsfoss.com/wp-content/uploads/2019/05/john-the-ripper.jpg?ssl=1
+[37]: https://github.com/magnumripper/JohnTheRipper
+[38]: https://www.openwall.com/john/pro/
+[39]: https://www.snort.org/
+[40]: https://www.snort.org/#get-started
+[41]: https://i1.wp.com/itsfoss.com/wp-content/uploads/2019/05/autopsy-forensic-browser.jpg?resize=800%2C319&ssl=1
+[42]: https://www.sleuthkit.org/autopsy/
+[43]: https://www.sleuthkit.org/autopsy/docs.php
+[44]: https://github.com/sleuthkit/autopsy
+[45]: https://i2.wp.com/itsfoss.com/wp-content/uploads/2019/05/king-phisher.jpg?resize=800%2C626&ssl=1
+[46]: https://github.com/securestate/king-phisher
+[47]: https://i2.wp.com/itsfoss.com/wp-content/uploads/2019/05/nikto.jpg?resize=800%2C511&ssl=1
+[48]: https://gitlab.com/kalilinux/packages/nikto/
+[49]: https://i1.wp.com/itsfoss.com/wp-content/uploads/2019/05/yersinia.jpg?resize=800%2C516&ssl=1
+[50]: https://github.com/tomac/yersinia
+[51]: https://en.wikipedia.org/wiki/OSI_model
+[52]: https://i1.wp.com/itsfoss.com/wp-content/uploads/2019/05/social-engineering-toolkit.jpg?resize=800%2C511&ssl=1
+[53]: https://www.trustedsec.com/social-engineer-toolkit-set/
+[54]: https://tools.kali.org/tools-listing
diff --git a/published/201905/20190510 How to Use 7Zip in Ubuntu and Other Linux -Quick Tip.md b/published/201905/20190510 How to Use 7Zip in Ubuntu and Other Linux -Quick Tip.md
new file mode 100644
index 0000000000..f3de1044ee
--- /dev/null
+++ b/published/201905/20190510 How to Use 7Zip in Ubuntu and Other Linux -Quick Tip.md
@@ -0,0 +1,109 @@
+[#]: collector: (lujun9972)
+[#]: translator: (warmfrog)
+[#]: reviewer: (wxy)
+[#]: publisher: (wxy)
+[#]: url: (https://linux.cn/article-10855-1.html)
+[#]: subject: (How to Use 7Zip in Ubuntu and Other Linux [Quick Tip])
+[#]: via: (https://itsfoss.com/use-7zip-ubuntu-linux/)
+[#]: author: (Abhishek Prakash https://itsfoss.com/author/abhishek/)
+
+如何在 Ubuntu 和其他 Linux 发行版上使用 7Zip
+==============================================
+
+
+
+> 不能在 Linux 中提取 .7z 文件?学习如何在 Ubuntu 和其他 Linux 发行版中安装和使用 7zip。
+
+[7Zip][1](更适当的写法是 7-Zip)是一种在 Windows 用户中广泛流行的归档格式。一个 7Zip 归档文件通常以 .7z 扩展结尾。它大部分是开源的,除了包含一些少量解压 rar 文件的代码。
+
+默认大多数 Linux 发行版不支持 7Zip。如果你试图提取它,你会看见这个错误:
+
+> 不能打开这种文件类型
+
+> 没有已安装的适用 7-zip 归档文件的命令。你想搜索一个命令来打开这个文件吗?
+
+![][2]
+
+不要担心,你可以轻松的在 Ubuntu 和其他 Linux 发行版中安装 7zip。
+
+一个问题是你会注意到如果你试图用 [apt-get install 命令][3],你会发现没有以 7zip 开头的候选安装。因为在 Linux 中 7Zip 包的名字是 [p7zip][4]。以字母 “p” 开头而不是预期的数字 “7”。
+
+让我们看一下如何在 Ubuntu 和其他 Linux 发行版中安装 7zip。
+
+### 在 Ubuntu Linux 中安装 7Zip
+
+你需要做的第一件事是安装 p7zip 包。你会在 Ubuntu 中发现 3 个包:p7zip、p7zip-full 和 pzip-rar。
+
+pzip 和 p7zip-full 的不同是 pzip 是一个轻量级的版本,仅仅对 .7z 文件提供支持,而 p7zip-full 提供了更多的 7z 压缩算法(例如音频文件)。
+
+p7zip-rar 包在 7z 中提供了对 [RAR 文件][6] 的支持
+
+在大多数情况下安装 p7zip-full 就足够了,但是你可能想安装 p7zip-rar 来支持 rar 文件的解压。
+
+p7zip 包在 [Ubuntu 的 universe 仓库][7] 因此保证你可以使用以下命令:
+
+```
+sudo add-apt-repository universe
+sudo apt update
+```
+
+在 Ubuntu 和基于 Debian 的发行版中使用以下命令。
+
+```
+sudo apt install p7zip-full p7zip-rar
+```
+
+这很好。现在在你的系统就有了 7zip 归档的支持。
+
+### 在 Linux 中提取 7Zip 归档文件
+
+安装了 7Zip 后,在 Linux 中,你可以在图形用户界面或者 命令行中提取 7zip 文件。
+
+在图形用户界面,你可以像提取其他压缩文件一样提取 .7z 文件。右击文件来提取它。
+
+在终端中,你可以使用下列命令提取 .7z 归档文件:
+
+```
+7z e file.7z
+```
+
+### 在 Linux 中压缩文件为 7zip 归档格式
+
+你可以在图形界面压缩文件为 7zip 归档格式。简单的在文件或目录上右击,选择“压缩”。你应该看到几种类型的文件格式选项。选择 .7z。
+
+![7zip Archive Ubuntu][9]
+
+作为替换,你也可以在命令行中使用。这里是你可以用来压缩的命令:
+
+```
+7z a 输出的文件名 要压缩的文件
+```
+
+默认,归档文件有 .7z 扩展。你可以通过在指定输出文件扩展名为 .zip 以压缩为 zip 格式。
+
+### 总结
+
+就是这样。看,在 Linux 中使用 7zip 多简单?我希望你喜欢这个快速指南。如果你有问题或者建议,请随意在下方评论让我知道。
+
+--------------------------------------------------------------------------------
+
+via: https://itsfoss.com/use-7zip-ubuntu-linux/
+
+作者:[Abhishek Prakash][a]
+选题:[lujun9972][b]
+译者:[warmfrog](https://github.com/warmfrog)
+校对:[wxy](https://github.com/wxy)
+
+本文由 [LCTT](https://github.com/LCTT/TranslateProject) 原创编译,[Linux中国](https://linux.cn/) 荣誉推出
+
+[a]: https://itsfoss.com/author/abhishek/
+[b]: https://github.com/lujun9972
+[1]: https://www.7-zip.org/
+[2]: https://i0.wp.com/itsfoss.com/wp-content/uploads/2015/07/Install_7zip_ubuntu_1.png?ssl=1
+[3]: https://itsfoss.com/apt-get-linux-guide/
+[4]: https://sourceforge.net/projects/p7zip/
+[5]: https://i2.wp.com/itsfoss.com/wp-content/uploads/2019/05/7zip-linux.png?resize=800%2C450&ssl=1
+[6]: https://itsfoss.com/use-rar-ubuntu-linux/
+[7]: https://itsfoss.com/ubuntu-repositories/
+[8]: https://itsfoss.com/easily-share-files-linux-windows-mac-nitroshare/
+[9]: https://i2.wp.com/itsfoss.com/wp-content/uploads/2019/05/7zip-archive-ubuntu.png?resize=800%2C239&ssl=1
diff --git a/published/201905/20190510 PHP in 2019.md b/published/201905/20190510 PHP in 2019.md
new file mode 100644
index 0000000000..5b6aa01eb2
--- /dev/null
+++ b/published/201905/20190510 PHP in 2019.md
@@ -0,0 +1,169 @@
+[#]: collector: (lujun9972)
+[#]: translator: (wxy)
+[#]: reviewer: (wxy)
+[#]: publisher: (wxy)
+[#]: url: (https://linux.cn/article-10870-1.html)
+[#]: subject: (PHP in 2019)
+[#]: via: (https://stitcher.io/blog/php-in-2019)
+[#]: author: (Brent https://stitcher.io/blog/php-in-2019)
+
+9102 年的 PHP
+======
+
+你还记得篇流行的博客文章《[PHP:设计糟糕的分形][3]》吗?我第一次读到它时,我在一个有很多遗留的 PHP 项目的糟糕地方工作。这篇文章让我觉得我是否应该放弃,并去做与编程完全不同的事情。
+
+还好,我之后很快就换了工作,更重要的是,自从 5.x 版本以来,PHP 成功地进步了很多。今天,我在向那些不再使用 PHP 编程,或者陷入遗留项目的人们致意。
+
+剧透:今天有些事情仍然很糟糕,就像几乎每种编程语言都有它的怪癖一样。许多核心功能仍然有不一致的调用方法,仍然有令人困惑的配置设置,仍然有许多开发人员在那里写蹩脚的代码 —— 因为他们必须如此,或是他们不知道更好的写法。
+
+今天我想看看好的一面:让我们关注已经发生变化的事情,以及编写干净而可维护的 PHP 代码的方法。在此之前,我想请你暂时搁置任何偏见。
+
+然后,你可以像以前一样对 PHP 自由吐槽。虽然,你可能会对 PHP 在过去的几年里的一些改进感到惊讶。(LCTT 译注:说实话,我是真的感到吃惊)
+
+### 提前看结论
+
+* PHP 在积极地开发,每年都有新版本
+* 自 PHP 5 时代以来的性能已经翻倍,如果不是三倍的话
+* 有一个非常活跃的框架、包和平台的生态系统
+* PHP 在过去几年中添加了许多新功能,并且这种语言在不断发展
+* 像静态分析这样的工具在过去几年中已经成熟,并且一直保持增长
+
+更新:人们让我展示一些实际的代码。我觉得这没问题!这是我的一个业余项目的[源代码][4],用 PHP 和 Laravel 编写的;[这里][5]列出了我们在办公室维护的几百个自由开源软件包。这两者都是现代 PHP 项目的好例子。
+
+那让我们开始吧。
+
+### 历史总结
+
+出于更好地衡量的目的,让我们快速回顾一下如今的 PHP 发布周期。我们现在的 PHP 为 7.3,预计在 2019 年底为 7.4。PHP 8.0 将是 7.4 之后的下一个版本。
+
+自从 5.x 时代以来,核心团队试图保持每年发布一个版本的周期,并且他们在过去的四年中成功地做到了这一点。
+
+一般来说,每个新版本都会在两年内得到积极支持,并再获得一年以上的“安全修复”。其目标是激励 PHP 开发人员尽可能保持最新:例如,每年进行小规模升级比在 5.4 到 7.0 之间跳转更容易。
+
+可以在 [这里][6] 找到 PHP 时间轴的活动概述。
+
+最后,PHP 5.6 是最新的 5.x 版本,而 8.0 是当前的下一个大版本。如果你想知道 PHP 6 发生了什么,你可以听听 [PHP Roundtable 播客][7]。
+
+了解了这个,让我们揭穿一些关于现代 PHP 的常见误解。
+
+### PHP 的性能
+
+早在 5.x 时代,PHP 的表现就是……嗯,平均水平。但是在 7.0 版本中,PHP 从头开始重写了核心部分,导致其性能提升了两到三倍!
+
+但光是嘴说是不够的。让我们来看看基准测试。幸运的是,人们花了很多时间对 PHP 性能进行了基准测试。 我发现 [Kinsta][8] 有一个很好的更新的测试列表。
+
+自 7.0 升级以来,性能就一直在提升而没有回退。PHP Web 应用程序的性能可与其它语言中的 Web 框架相提并论,甚至在某些情况下更好。你可以看看这个[广泛的基准测试套件][9]。
+
+当然 PHP 框架不会胜过 C 和 Rust,但它们比 Rails 或 Django 要好得多,并且与 ExpressJS 相当。
+
+### 框架和生态系统
+
+说到框架:PHP 可不仅仅是 WordPress。让我告诉你 —— 某些专业的 PHP 开发人员:WordPress 绝不代表当代的 PHP 生态系统。
+
+一般来说,有两个主要的 Web 应用程序框架,[Symfony][10] 和 [Laravel][11],以及一些较小的应用程序框架。当然还有 Zend、Yii、Cake、Code Igniter 等等,但是如果你想知道现代 PHP 开发是怎么样的,这两者之一都是很好的选择。
+
+这两个框架都有一个庞大的包和产品的生态系统。从管理面板和 CRM 到独立软件包,从 CI 到分析器,以及几个 Web 套接字服务器、队列管理器、支付集成等众多服务。老实说,要列出的内容太多了。
+
+这些框架虽然适用于实际开发。如果你只是需要个内容管理系统(CMS),WordPress 和 CraftCMS 等平台就够了。
+
+衡量 PHP 生态系统当前状态的一种方法是查看 Packagist,这是 PHP 主要的软件包存储库。它现在呈指数级增长。每天下载量达到了 2500 万次,可以说 PHP 生态系统已不再是以前的小型弱势群体了。
+
+请查看此图表,它列出一段时间内的软件包和版本数量变化。它也可以在 [Packagist 网站][12]上找到它。
+
+![][13]
+
+除了应用程序框架和 CMS 之外,我们还看到过去几年里异步框架的兴起。
+
+这些是用 PHP 或其他语言编写的框架和服务器,允许用户运行真正的异步 PHP,这些例子包括 [Swoole][14](创始人韩天峰),以及 [Amp][15] 和 [ReactPHP][16]。
+
+我们已经进入了异步的世界,像 Web 套接字和具有大量 I/O 的应用程序之类的东西在 PHP 世界中已经变得非常重要。
+
+在内部邮件列表里(PHP 核心开发人员讨论语言开发的地方)已经谈到了[将 libuv 添加到核心][17]。如果你还不知道 libuv:Node.js 全有赖它提供异步性。
+
+### 语言本身
+
+虽然尚未提供 `async` 和 `await`,但在过去几年中,PHP 语言本身已经有了很多改进。这是 PHP 中新功能的非详尽列表:
+
+
++ [短闭包](https://stitcher.io/blog/short-closures-in-php)(箭头函数)
++ [Null 合并操作符](https://stitcher.io/blog/shorthand-comparisons-in-php#null-coalescing-operator)(`??`)
++ [Trait](https://www.php.net/manual/en/language.oop5.traits.php)(一种代码重用方式)
++ [属性类型](https://stitcher.io/blog/new-in-php-74#typed-properties-rfc)
++ [展开操作符](https://wiki.php.net/rfc/argument_unpacking)(参数解包 `...`)
++ [JIT 编译器](https://wiki.php.net/rfc/jit)(即时编译器)
++ [FFI](https://wiki.php.net/rfc/ffi)(外部函数接口)
++ [匿名类](https://www.php.net/manual/en/language.oop5.anonymous.php)
++ [返回类型声明](https://www.php.net/manual/en/functions.returning-values.php#functions.returning-values.type-declaration)
++ [现代化的加密支持](https://wiki.php.net/rfc/libsodium)
++ [生成器](https://wiki.php.net/rfc/generators)
++ [等等](https://www.php.net/ChangeLog-7.php)
+
+当我们讨论语言功能时,我们还要谈谈当今该语言的发展过程。虽然社区可以提出 RFC,但是得有一个活跃的志愿者核心团队才能推着它前进。
+
+接下来,这些 RFC 将在“内部”邮件列表中进行讨论,这个邮件列表也可以[在线阅读][18]。在添加新的语言特性之前,必须进行投票。只有得到了至少 2/3 多数同意的 RFC 才能进入核心。
+
+可能有大约 100 人能够投票,但不需要每个人对每个 RFC 进行投票。核心团队的成员当然可以投票,他们是维护代码库的人。除了他们之外,还有一群人从 PHP 社区中被单独挑选出来。这些人包括 PHP 文档的维护者,对 PHP 项目整体有贡献的人,以及 PHP 社区中的杰出开发人员。
+
+虽然大多数核心开发都是在自愿的基础上完成的,但其中一位核心 PHP 开发人员 Nikita Popov 最近受雇于 [JetBrains][19] 全职从事于 PHP 语言的开发。另一个例子是 Linux 基金会最近决定[投资 Zend 框架][20]。像这样的雇佣和收购确保了 PHP 未来发展的稳定性。
+
+### 工具
+
+除了核心本身,我们看到过去几年中围绕它的工具有所增加。首先浮现于我脑海中的是静态分析器,比如由 Vimeo 创建 [Psalm][21],以及 [Phan][22] 和 [PHPStan][23]。
+
+这些工具将静态分析你的 PHP 代码并报告任何类型错误和可能的错误等。在某种程度上,它们提供的功能可以与 TypeScript 进行比较,但是现在这种语言不能转译,因此不支持使用自定义语法。
+
+尽管这意味着我们需要依赖 docblocks,但是 PHP 之父 Rasmus Lerdorf 确实提到了[添加静态分析引擎][24]到核心的想法。虽然会有很多潜力,但这是一项艰巨的任务。
+
+说到转译,以及受到 JavaScript 社区的启发;他们已经努力在用户领域中扩展 PHP 语法。一个名为 [Pre][25] 的项目正是如此:允许将新的 PHP 语法转译为普通的 PHP 代码。
+
+虽然这个思路已经在 JavaScript 世界中被证明了,但如果提供了适当的 IDE 和静态分析支持,它就能在 PHP 中工作了。这是一个非常有趣的想法,但必须发展起来才能称之为“主流”。
+
+### 结语
+
+尽管如此,你仍然可以将 PHP 视为一种糟糕的语言。虽然这种语言肯定有它的缺点和背负了 20 年的遗产;但我可以放胆地说,我喜欢用它工作。
+
+根据我的经验,我能够创建可靠、可维护和高质量的软件。我工作的客户对最终结果感到满意,“俺也一样”。
+
+尽管仍然可以用 PHP 做很多乱七八糟的事情,但我认为如果明智和正确地使用的话,它是 Web 开发的绝佳选择。
+
+你不同意吗?让我知道为什么!你可以通过 [Twitter][2] 或 [电子邮件][26] 与我联系。
+
+--------------------------------------------------------------------------------
+
+via: https://stitcher.io/blog/php-in-2019
+
+作者:[Brent][a]
+选题:[lujun9972][b]
+译者:[wxy](https://github.com/wxy)
+校对:[wxy](https://github.com/wxy)
+
+本文由 [LCTT](https://github.com/LCTT/TranslateProject) 原创编译,[Linux中国](https://linux.cn/) 荣誉推出
+
+[a]: https://stitcher.io/blog/php-in-2019
+[b]: https://github.com/lujun9972
+[1]: https://stitcher.io/
+[2]: https://twitter.com/brendt_gd
+[3]: https://eev.ee/blog/2012/04/09/php-a-fractal-of-bad-design/
+[4]: https://github.com/brendt/aggregate.stitcher.io
+[5]: https://spatie.be/open-source/packages
+[6]: https://www.php.net/supported-versions.php
+[7]: https://www.phproundtable.com/episode/what-happened-to-php-6
+[8]: https://kinsta.com/blog/php-benchmarks/
+[9]: https://github.com/the-benchmarker/web-frameworks
+[10]: https://symfony.com/
+[11]: https://laravel.com/
+[12]: https://packagist.org/statistics
+[13]: https://stitcher.io/resources/img/blog/php-in-2019/packagist.png
+[14]: https://www.swoole.co.uk/
+[15]: https://amphp.org/
+[16]: https://reactphp.org/
+[17]: https://externals.io/message/102415#102415
+[18]: https://externals.io/
+[19]: https://blog.jetbrains.com/phpstorm/2019/01/nikita-popov-joins-phpstorm-team/
+[20]: https://getlaminas.org/
+[21]: https://github.com/vimeo/psalm
+[22]: https://github.com/phan/phan
+[23]: https://github.com/phpstan/phpstan
+[24]: https://externals.io/message/101477#101592
+[25]: https://preprocess.io/
+[26]: mailto:brendt@stitcher.io
diff --git a/published/201905/20190513 How to SSH into a Raspberry Pi -Beginner-s Tip.md b/published/201905/20190513 How to SSH into a Raspberry Pi -Beginner-s Tip.md
new file mode 100644
index 0000000000..ca59e6c392
--- /dev/null
+++ b/published/201905/20190513 How to SSH into a Raspberry Pi -Beginner-s Tip.md
@@ -0,0 +1,120 @@
+[#]: collector: (lujun9972)
+[#]: translator: (tomjlw)
+[#]: reviewer: (wxy)
+[#]: publisher: (wxy)
+[#]: url: (https://linux.cn/article-10888-1.html)
+[#]: subject: (How to SSH into a Raspberry Pi [Beginner’s Tip])
+[#]: via: (https://itsfoss.com/ssh-into-raspberry/)
+[#]: author: (Chinmay https://itsfoss.com/author/chinmay/)
+
+新手教程:如何 SSH 进入树莓派
+======
+
+> 在这篇树莓派文章中,你将学到如何在树莓派中启用 SSH 以及之后如何通过 SSH 进入树莓派。
+
+在你可以用[树莓派][1]做的所有事情中,将其作为一个家庭网络的服务器是十分流行的做法。小体积与低功耗使它成为运行轻量级服务器的完美设备。
+
+在这种情况下你做得到的事情之一是能够每次在树莓派上无须接上显示器、键盘、鼠标以及走到放置你的树莓派的地方就可以运行指令。
+
+你可以从其它任意电脑、笔记本、台式机甚至你的手机通过 SSH([Secure Shell][2])登入你的树莓派来做到这一点。让我展示给你看:
+
+### 如何 SSH 进入树莓派
+
+![][3]
+
+我假设你已经[在你的树莓派上运行 Raspbian][4] 并已经成功通过有线或者无线网连进网络了。你的树莓派接入网络这点是很重要的,否则你无法通过 SSH 连接树莓派(抱歉说出这种显而易见的事实)。
+
+#### 步骤一:在树莓派上启用 SSH
+
+SSH 在树莓派上是默认关闭的,因此在你安装好全新的 Raspbian 后打开树莓派时,你需要启用它。
+
+首先通过菜单进入树莓派的配置界面。
+
+![树莓派菜单,树莓派配置][5]
+
+现在进入接口标签,启动 SSH 并重启你的树莓派。
+
+![在树莓派上启动 SSH][6]
+
+你也可以通过终端直接启动 SSH。仅需输入命令 `sudo raspi-config` 然后进入高级设置以启用 SSH。
+
+#### 步骤二: 找到树莓派的 IP 地址
+
+在大多数情况下,你的树莓派会被分配一个看起来长得像 `192.168.x.x` 或者 `10.x.x.x` 的本地 IP 地址。你可以[使用多种 Linux 命令来找到 IP 地址][7]。
+
+我在这使用古老而好用的 `ifconfig` 命令,但是你也可以使用 `ip address`。
+
+```
+ifconfig
+```
+
+![树莓派网络配置][9]
+
+这行命令展现了所有活跃中的网络适配器以及其配置的列表。第一个条目(`eth0`)展示了例如`192.168.2.105` 的有效 IP 地址。我用有线网将我的树莓派连入网络,因此这里显示的是 `eth0`。如果你用无线网的话在叫做 `wlan0` 的条目下查看。
+
+你也可以用其他方法例如查看你的路由器或者调制解调器的网络设备表以找到 IP 地址。
+
+#### 步骤三:SSH 进你的树莓派
+
+既然你已经启用了 SSH 功能并且找到了 IP 地址,你可以从任何电脑 SSH 进入你的树莓派。你同样需要树莓派的用户名和密码。
+
+默认用户名和密码是:
+
+ * 用户名:`pi`
+ * 密码:`raspberry`
+
+如果你已改变了默认的密码,那就使用新的而不是以上的密码。理想状态下你必须改变默认的密码。在过去,有一款[恶意软件感染数千使用默认用户名和密码的树莓派设备][8]。
+
+(在 Mac 或 Linux 上)从你想要 SSH 进树莓派的电脑上打开终端输入以下命令,在 Windows 上,你可以用类似 [Putty][10] 的 SSH 客户端。
+
+这里,使用你在之前步骤中找到的 IP 地址。
+
+```
+ssh [受保护的邮件]
+```
+
+> 注意: 确保你的树莓派和你用来 SSH 进入树莓派的电脑接入了同一个网络。
+
+![通过命令行 SSH][11]
+
+第一次你会看到一个警告,输入 `yes` 并按下回车。
+
+![输入密码 \(默认是 ‘raspberry‘\)][12]
+
+现在,输入密码按下回车。
+
+![成功通过 SSH 登入][13]
+
+成功登入你将会看到树莓派的终端。现在你可以通过这个终端无需物理上访问你的树莓派就可以远程(在当前网络内)在它上面运行指令。
+
+在此之上你也可以设置 SSH 密钥这样每次通过 SSH 登入时就可以无需输入密码,但那完全是另一个话题了。
+
+我希望你通过跟着这个教程已能够 SSH 进入你的树莓派。在下方评论中让我知道你打算用你的树莓派做些什么!
+
+--------------------------------------------------------------------------
+
+via: https://itsfoss.com/ssh-into-raspberry/
+
+作者:[Chinmay][a]
+选题:[lujun9972][b]
+译者:[tomjlw](https://github.com/tomjlw)
+校对:[wxy](https://github.com/wxy)
+
+本文由 [LCTT](https://github.com/LCTT/TranslateProject) 原创编译,[Linux中国](https://linux.cn/) 荣誉推出
+
+[a]: https://itsfoss.com/author/chinmay/
+[b]: https://github.com/lujun9972
+[1]: https://www.raspberrypi.org/
+[2]: https://en.wikipedia.org/wiki/Secure_Shell
+[3]: https://i2.wp.com/itsfoss.com/wp-content/uploads/2019/05/ssh-into-raspberry-pi.png?resize=800%2C450&ssl=1
+[4]: https://itsfoss.com/tutorial-how-to-install-raspberry-pi-os-raspbian-wheezy/
+[5]: https://i0.wp.com/itsfoss.com/wp-content/uploads/2019/05/Raspberry-pi-configuration.png?ssl=1
+[6]: https://i0.wp.com/itsfoss.com/wp-content/uploads/2019/05/enable-ssh-raspberry-pi.png?ssl=1
+[7]: https://linuxhandbook.com/find-ip-address/
+[8]: https://itsfoss.com/raspberry-pi-malware-threat/
+[9]: https://i0.wp.com/itsfoss.com/wp-content/uploads/2019/05/ifconfig-rapberry-pi.png?ssl=1
+[10]: https://itsfoss.com/putty-linux/
+[11]: https://i1.wp.com/itsfoss.com/wp-content/uploads/2019/05/SSH-into-pi-warning.png?fit=800%2C199&ssl=1
+[12]: https://i0.wp.com/itsfoss.com/wp-content/uploads/2019/05/SSH-into-pi-password.png?fit=800%2C202&ssl=1
+[13]: https://i0.wp.com/itsfoss.com/wp-content/uploads/2019/05/SSH-into-Pi-successful-login.png?fit=800%2C306&ssl=1
+[14]: https://itsfoss.com/speed-up-ubuntu-unity-on-low-end-system/
diff --git a/published/201905/20190516 Building Smaller Container Images.md b/published/201905/20190516 Building Smaller Container Images.md
new file mode 100644
index 0000000000..35efa5ea3a
--- /dev/null
+++ b/published/201905/20190516 Building Smaller Container Images.md
@@ -0,0 +1,117 @@
+[#]: collector: (lujun9972)
+[#]: translator: (geekpi)
+[#]: reviewer: (wxy)
+[#]: publisher: (wxy)
+[#]: url: (https://linux.cn/article-10885-1.html)
+[#]: subject: (Building Smaller Container Images)
+[#]: via: (https://fedoramagazine.org/building-smaller-container-images/)
+[#]: author: (Muayyad Alsadi https://fedoramagazine.org/author/alsadi/)
+
+构建更小的容器镜像的技巧
+======
+
+![][1]
+
+Linux 容器已经成为一个热门话题,保证容器镜像较小被认为是一个好习惯。本文提供了有关如何构建较小 Fedora 容器镜像的一些技巧。
+
+### microdnf
+
+Fedora 的 DNF 是用 Python 编写的,因为它有各种各样的插件,因此它的设计是可扩展的。但是 有一个 Fedora 基本容器镜像替代品,它使用一个较小的名为 [microdnf][2] 的包管理器,使用 C 编写。要在 Dockerfile 中使用这个最小的镜像,`FROM` 行应该如下所示:
+
+```
+FROM registry.fedoraproject.org/fedora-minimal:30
+```
+
+如果你的镜像不需要像 Python 这样的典型 DNF 依赖项,例如,如果你在制作 NodeJS 镜像时,那么这是一个重要的节省项。
+
+### 在一个层中安装和清理
+
+为了节省空间,使用 `dnf clean all` 或其 microdnf 等效的 `microdnf clean all` 删除仓库元数据非常重要。但是你不应该分两步执行此操作,因为这实际上会将这些文件保存在容器镜像中,然后在另一层中将其标记为删除。要正确地执行此操作,你应该像这样一步完成安装和清理:
+
+```
+FROM registry.fedoraproject.org/fedora-minimal:30
+RUN microdnf install nodejs && microdnf clean all
+```
+
+### 使用 microdnf 进行模块化
+
+模块化是一种给你选择不同堆栈版本的方法。例如,你可能需要在项目中用非 LTS 的 NodeJS v11,旧的 LTS NodeJS v8 用于另一个,最新的 LTS NodeJS v10 用于另一个。你可以使用冒号指定流。
+
+```
+# dnf module list
+# dnf module install nodejs:8
+```
+
+`dnf module install` 命令意味着两个命令,一个启用流,另一个是从它安装 nodejs。
+
+```
+# dnf module enable nodejs:8
+# dnf install nodejs
+```
+
+尽管 `microdnf` 不提供与模块化相关的任何命令,但是可以启用带有配置文件的模块,并且 libdnf(被 microdnf 使用)[似乎][3]支持模块化流。该文件看起来像这样:
+
+```
+/etc/dnf/modules.d/nodejs.module
+[nodejs]
+name=nodejs
+stream=8
+profiles=
+state=enabled
+```
+
+使用模块化的 `microdnf` 的完整 Dockerfile 如下所示:
+
+```
+FROM registry.fedoraproject.org/fedora-minimal:30
+RUN \
+ echo -e "[nodejs]\nname=nodejs\nstream=8\nprofiles=\nstate=enabled\n" > /etc/dnf/modules.d/nodejs.module && \
+ microdnf install nodejs zopfli findutils busybox && \
+ microdnf clean all
+```
+
+### 多阶段构建
+
+在许多情况下,你可能需要大量的无需用于运行软件的构建时依赖项,例如构建一个静态链接依赖项的 Go 二进制文件。多阶段构建是分离应用构建和应用运行时的有效方法。
+
+例如,下面的 Dockerfile 构建了一个 Go 应用 [confd][4]。
+
+```
+# building container
+FROM registry.fedoraproject.org/fedora-minimal AS build
+RUN mkdir /go && microdnf install golang && microdnf clean all
+WORKDIR /go
+RUN export GOPATH=/go; CGO_ENABLED=0 go get github.com/kelseyhightower/confd
+
+FROM registry.fedoraproject.org/fedora-minimal
+WORKDIR /
+COPY --from=build /go/bin/confd /usr/local/bin
+CMD ["confd"]
+```
+
+通过在 `FROM` 指令之后添加 `AS` 并从基本容器镜像中添加另一个 `FROM` 然后使用 `COPY --from=` 指令将内容从*构建*的容器复制到第二个容器来完成多阶段构建。
+
+可以使用 `podman` 构建并运行此 Dockerfile:
+
+```
+$ podman build -t myconfd .
+$ podman run -it myconfd
+```
+
+--------------------------------------------------------------------------------
+
+via: https://fedoramagazine.org/building-smaller-container-images/
+
+作者:[Muayyad Alsadi][a]
+选题:[lujun9972][b]
+译者:[geekpi](https://github.com/geekpi)
+校对:[wxy](https://github.com/wxy)
+
+本文由 [LCTT](https://github.com/LCTT/TranslateProject) 原创编译,[Linux中国](https://linux.cn/) 荣誉推出
+
+[a]: https://fedoramagazine.org/author/alsadi/
+[b]: https://github.com/lujun9972
+[1]: https://fedoramagazine.org/wp-content/uploads/2019/05/smaller-container-images-816x345.jpg
+[2]: https://github.com/rpm-software-management/microdnf
+[3]: https://bugzilla.redhat.com/show_bug.cgi?id=1575626
+[4]: https://github.com/kelseyhightower/confd
diff --git a/published/201905/20190516 Querying 10 years of GitHub data with GHTorrent and Libraries.io.md b/published/201905/20190516 Querying 10 years of GitHub data with GHTorrent and Libraries.io.md
new file mode 100644
index 0000000000..5c51721c84
--- /dev/null
+++ b/published/201905/20190516 Querying 10 years of GitHub data with GHTorrent and Libraries.io.md
@@ -0,0 +1,156 @@
+[#]: collector: (lujun9972)
+[#]: translator: (wxy)
+[#]: reviewer: (wxy)
+[#]: publisher: (wxy)
+[#]: url: (https://linux.cn/article-10906-1.html)
+[#]: subject: (Querying 10 years of GitHub data with GHTorrent and Libraries.io)
+[#]: via: (https://opensource.com/article/19/5/chaossearch-github-ghtorrent)
+[#]: author: (Pete Cheslock https://opensource.com/users/petecheslock/users/ghaff/users/payalsingh/users/davidmstokes)
+
+用 GHTorrent 和 Libraries.io 查询 10 年的 GitHub 数据
+======
+
+> 有一种方法可以在没有任何本地基础设施的情况下使用开源数据集探索 GitHub 数据。
+
+
+
+我一直在寻找新的数据集,以用它们来展示我们团队工作的力量。[CHAOSSEARCH][2] 可以将你的 [Amazon S3][3] 对象存储数据转换为完全可搜索的 [Elasticsearch][4] 式集群。使用 Elasticsearch API 或 [Kibana][5] 等工具,你可以查询你所要找的任何数据。
+
+当我找到 [GHTorrent][6] 项目进行探索时,我很兴奋。GHTorrent 旨在通过 GitHub API 构建所有可用数据的离线版本。如果你喜欢数据集,这是一个值得一看的项目,甚至你可以考虑[捐赠一个 GitHub API 密钥][7]。
+
+### 访问 GHTorrent 数据
+
+有许多方法可以访问和使用 [GHTorrent 的数据][8],它以 [NDJSON][9] 格式提供。这个项目可以以多种形式提供数据,包括用于恢复到 [MySQL][11] 数据库的 [CSV][10],可以转储所有对象的 [MongoDB][12],以及用于将数据直接导出到 Google 对象存储中的 Google Big Query(免费)。 有一点需要注意:这个数据集有从 2008 年到 2017 年几乎完整的数据集,但从 2017 年到现在的数据还不完整。这将影响我们确定性查询的能力,但它仍然是一个令人兴奋的信息量。
+
+我选择 Google Big Query 来避免自己运行任何数据库,那么我就可以很快下载包括用户和项目在内的完整数据库。CHAOSSEARCH 可以原生分析 NDJSON 格式,因此在将数据上传到 Amazon S3 之后,我能够在几分钟内对其进行索引。CHAOSSEARCH 平台不要求用户设置索引模式或定义其数据的映射,它可以发现所有字段本身(字符串、整数等)。
+
+随着我的数据完全索引并准备好进行搜索和聚合,我想深入了解看看我们可以发现什么,比如哪些软件语言是 GitHub 项目最受欢迎的。
+
+(关于格式化的说明:下面这是一个有效的 JSON 查询,我们不会在这里正确格式化以避免滚动疲劳。要正确格式化它,你可以在本地复制它并发送到命令行实用程序,如 [jq][13]。)
+
+```
+{"aggs":{"2":{"date_histogram":{"field":"root.created_at","interval":"1M","time_zone":"America/New_York","min_doc_count":1}}},"size":0,"_source":{"excludes":[]},"stored_fields":["*"],"script_fields":{},"docvalue_fields":["root.created_at","root.updated_at"],"query":{"bool":{"must":[],"filter":[{"match_all":{}}],"should":[],"must_not":[{"match_phrase":{"root.language":{"query":""}}}]}}}
+```
+
+对于那些近年来跟踪开源语言状态的人来说,这个结果并不令人惊讶。
+
+![Which software languages are the most popular on GitHub.][14]
+
+[JavaScript][15] 仍然是卫冕冠军,虽然有些人认为 JavaScript 正在逐渐消失,但它仍然是 800 磅重的大猩猩,很可能会保持这种状态一段时间。[Java][16] 面临类似的谣言,但这些数据表明它是开源生态系统的重要组成部分。
+
+考虑到像 [Docker][17] 和 [Kubernetes][18] 这样的项目的流行,你可能会想,“Go([Golang][19])怎么样?”这是一个提醒的好时机,这里讨论的 GitHub 数据集包含一些空缺,最明显的是在 2017 年之后我看到 Golang 项目随处可见,而这里并没有显示。我希望用完整的 GitHub 数据集重复此搜索,看看它是否会改变排名。
+
+现在让我们来探讨项目创建的速度。 (提醒:这是为了便于阅读而合并的有效 JSON。)
+
+```
+{"aggs":{"2":{"date_histogram":{"field":"root.created_at","interval":"1M","time_zone":"America/New_York","min_doc_count":1}}},"size":0,"_source":{"excludes":[]},"stored_fields":["*"],"script_fields":{},"docvalue_fields":["root.created_at","root.updated_at"],"query":{"bool":{"must":[],"filter":[{"match_all":{}}],"should":[],"must_not":[{"match_phrase":{"root.language":{"query":""}}}]}}}
+```
+
+我们可以看到创建新项目的速度,也会给人留下深刻的印象,从 2012 年左右开始大幅增长:
+
+![The rate at which new projects are created on GitHub.][20]
+
+既然我知道了创建项目的速度以及用于创建这些项目的最流行的语言,我还想知道这些项目选择的开源许可证。遗憾的是,这个 GitHub 项目数据集中并不存在这些数据,但是 [Tidelift][21] 的精彩团队在 [Libraries.io][22] [数据][23] 里发布了一个 GitHub 项目的详细列表,包括使用的许可证以及其中有关开源软件状态的其他详细信息。将此数据集导入 CHAOSSEARCH 只花了几分钟,让我看看哪些开源软件许可证在 GitHub 上最受欢迎:
+
+(提醒:这是为了便于阅读而合并的有效 JSON。)
+
+```
+{"aggs":{"2":{"terms":{"field":"Repository License","size":10,"order":{"_count":"desc"}}}},"size":0,"_source":{"excludes":[]},"stored_fields":["*"],"script_fields":{},"docvalue_fields":["Created Timestamp","Last synced Timestamp","Latest Release Publish Timestamp","Updated Timestamp"],"query":{"bool":{"must":[],"filter":[{"match_all":{}}],"should":[],"must_not":[{"match_phrase":{"Repository License":{"query":""}}}]}}}
+```
+
+结果显示了一些重要的异常值:
+
+![Which open source software licenses are the most popular on GitHub.][24]
+
+如你所见,[MIT 许可证][25] 和 [Apache 2.0 许可证][26] 的开源项目远远超过了其他大多数开源许可证,而 [各种 BSD 和 GPL 许可证][27] 则差得很远。鉴于 GitHub 的开放模式,我不能说我对这些结果感到惊讶。我猜想是用户(而不是公司)创建了大多数项目,并且他们使用 MIT 许可证可以使其他人轻松地使用、共享和贡献。而鉴于有不少公司希望确保其商标得到尊重并为其业务提供开源组件,那么 Apache 2.0 许可证数量高企的背后也是有道理的。
+
+现在我确定了最受欢迎的许可证,我很想看看最少使用的许可证。通过调整我的上一个查询,我将前 10 名逆转为最后 10 名,并且只找到了两个使用 [伊利诺伊大学 - NCSA 开源许可证][28] 的项目。我之前从未听说过这个许可证,但它与 Apache 2.0 非常接近。看到所有 GitHub 项目中使用了多少个不同的软件许可证,这很有意思。
+
+![The University of Illinois/NCSA open source license.][29]
+
+之后,我针对特定语言(JavaScript)来查看最常用的许可证。(提醒:这是为了便于阅读而合并的有效JSON。)
+
+```
+{"aggs":{"2":{"terms":{"field":"Repository License","size":10,"order":{"_count":"desc"}}}},"size":0,"_source":{"excludes":[]},"stored_fields":["*"],"script_fields":{},"docvalue_fields":["Created Timestamp","Last synced Timestamp","Latest Release Publish Timestamp","Updated Timestamp"],"query":{"bool":{"must":[{"match_phrase":{"Repository Language":{"query":"JavaScript"}}}],"filter":[{"match_all":{}}],"should":[],"must_not":[{"match_phrase":{"Repository License":{"query":""}}}]}}}
+```
+
+这个输出有一些意外。
+
+![The most popular open source licenses used for GitHub JavaScript projects.][30]
+
+尽管使用 `npm init` 创建的 [NPM][31] 模块的默认许可证是来自 [Internet Systems Consortium(ISC)][32] 的许可证,但你可以看到相当多的这些项目使用 MIT 以及 Apache 2.0 的开源许可证。
+
+由于 Libraries.io 数据集中包含丰富的开源项目内容,并且由于 GHTorrent 数据缺少最近几年的数据(因此缺少有关 Golang 项目的任何细节),因此我决定运行类似的查询来查看 Golang 项目是如何许可他们的代码的。
+
+(提醒:这是为了便于阅读而合并的有效 JSON。)
+
+```
+{"aggs":{"2":{"terms":{"field":"Repository License","size":10,"order":{"_count":"desc"}}}},"size":0,"_source":{"excludes":[]},"stored_fields":["*"],"script_fields":{},"docvalue_fields":["Created Timestamp","Last synced Timestamp","Latest Release Publish Timestamp","Updated Timestamp"],"query":{"bool":{"must":[{"match_phrase":{"Repository Language":{"query":"Go"}}}],"filter":[{"match_all":{}}],"should":[],"must_not":[{"match_phrase":{"Repository License":{"query":""}}}]}}}
+```
+
+结果与 Javascript 完全不同。
+
+![How Golang projects license their GitHub code.][33]
+
+Golang 项目与 JavaScript 项目惊人逆转 —— 使用 Apache 2.0 的 Golang 项目几乎是 MIT 许可证的三倍。虽然很难准确地解释为什么会出现这种情况,但在过去的几年中,Golang 已经出现了大规模的增长,特别是在开源和商业化的项目和软件产品公司中。
+
+正如我们上面所了解的,这些公司中的许多公司都希望强制执行其商标策略,因此转向 Apache 2.0 许可证是有道理的。
+
+#### 总结
+
+最后,我通过深入了解 GitHub 用户和项目的数据找到了一些有趣的结果。其中一些我肯定会猜到,但是一些结果对我来说也是惊喜,特别是像很少使用的 NCSA 许可证这样的异常值。
+
+总而言之,你可以看到 CHAOSSEARCH 平台能够快速轻松地找到有趣问题的复杂答案。我无需自己运行任何数据库就可以深入研究这个数据集,甚至可以在 Amazon S3 上以低成本的方式存储数据,因此无需维护。 现在,我可以随时查询有关这些数据的任何其他问题。
+
+你对数据提出了哪些其他问题,以及你使用了哪些数据集?请在评论或推特上告诉我 [@petecheslock] [34]。
+
+本文的一个版本最初发布在 [CHAOSSEARCH][35],有更多结果可供发现。
+
+--------------------------------------------------------------------------------
+
+via: https://opensource.com/article/19/5/chaossearch-github-ghtorrent
+
+作者:[Pete Cheslock][a]
+选题:[lujun9972][b]
+译者:[wxy](https://github.com/wxy)
+校对:[wxy](https://github.com/wxy)
+
+本文由 [LCTT](https://github.com/LCTT/TranslateProject) 原创编译,[Linux中国](https://linux.cn/) 荣誉推出
+
+[a]: https://opensource.com/users/petecheslock/users/ghaff/users/payalsingh/users/davidmstokes
+[b]: https://github.com/lujun9972
+[1]: https://opensource.com/sites/default/files/styles/image-full-size/public/lead-images/search_find_code_issue_bug_programming.png?itok=XPrh7fa0 (magnifying glass on computer screen)
+[2]: https://chaossearch.io/
+[3]: https://aws.amazon.com/s3/
+[4]: https://www.elastic.co/
+[5]: https://www.elastic.co/products/kibana
+[6]: http://ghtorrent.org
+[7]: http://ghtorrent.org/services.html
+[8]: http://ghtorrent.org/downloads.html
+[9]: http://ndjson.org
+[10]: https://en.wikipedia.org/wiki/Comma-separated_values
+[11]: https://en.wikipedia.org/wiki/MySQL
+[12]: https://www.mongodb.com/
+[13]: https://stedolan.github.io/jq/
+[14]: https://opensource.com/sites/default/files/uploads/github-1_500.png (Which software languages are the most popular on GitHub.)
+[15]: https://en.wikipedia.org/wiki/JavaScript
+[16]: /resources/java
+[17]: /resources/what-docker
+[18]: /resources/what-is-kubernetes
+[19]: https://golang.org/
+[20]: https://opensource.com/sites/default/files/uploads/github-2_500.png (The rate at which new projects are created on GitHub.)
+[21]: https://tidelift.com
+[22]: http://libraries.io/
+[23]: https://libraries.io/data
+[24]: https://opensource.com/sites/default/files/uploads/github-3_500.png (Which open source software licenses are the most popular on GitHub.)
+[25]: https://opensource.org/licenses/MIT
+[26]: https://opensource.org/licenses/Apache-2.0
+[27]: https://opensource.org/licenses
+[28]: https://tldrlegal.com/license/university-of-illinois---ncsa-open-source-license-(ncsa)
+[29]: https://opensource.com/sites/default/files/uploads/github-4_500_0.png (The University of Illinois/NCSA open source license.)
+[30]: https://opensource.com/sites/default/files/uploads/github-5_500_0.png (The most popular open source licenses used for GitHub JavaScript projects.)
+[31]: https://www.npmjs.com/
+[32]: https://en.wikipedia.org/wiki/ISC_license
+[33]: https://opensource.com/sites/default/files/uploads/github-6_500.png (How Golang projects license their GitHub code.)
+[34]: https://twitter.com/petecheslock
+[35]: https://chaossearch.io/blog/where-are-the-github-users-part-1/
diff --git a/published/201905/20190518 Change Power Modes in Ubuntu with Slimbook Battery Optimizer.md b/published/201905/20190518 Change Power Modes in Ubuntu with Slimbook Battery Optimizer.md
new file mode 100644
index 0000000000..15c51dc608
--- /dev/null
+++ b/published/201905/20190518 Change Power Modes in Ubuntu with Slimbook Battery Optimizer.md
@@ -0,0 +1,102 @@
+[#]: collector: (lujun9972)
+[#]: translator: (zhs852)
+[#]: reviewer: (wxy)
+[#]: publisher: (wxy)
+[#]: url: (https://linux.cn/article-10897-1.html)
+[#]: subject: (Change Power Modes in Ubuntu with Slimbook Battery Optimizer)
+[#]: via: (https://itsfoss.com/slimbook-battry-optimizer-ubuntu/)
+[#]: author: (Abhishek Prakash https://itsfoss.com/author/abhishek/)
+
+在 Ubuntu 中使用 Slimbook Battery Optimizer 切换电源模式
+======
+
+> Slimbook Battery Optimizer 是一个美观实用的指示器小程序,它可以让你在安装了 Linux 的笔记本上快速切换电源模式来延长续航时间。
+
+[Slimbook][1] 是一个销售 [预装 Linux 的笔记本电脑][2] 的西班牙电脑制造商,他们发布了一款好用的小程序,用来在基于 Ubuntu 的 Linux 发行版下调整电池性能。
+
+因为 Slimbook 销售他们自己的 Linux 系统,所以他们制作了一些在 Linux 上用于调整他们自己硬件性能的小工具。Battery Optimizer 就是这样一个工具。
+
+要使用这个实用小程序,你不必购买 Slimbook 的产品,因为 Slimbook 已经将它在 [他们的官方 PPA 源][3] 发行了。
+
+### Slimbook Battery Optimizer 简介
+
+这个程序叫 Slimbook Battery。它是一个常驻顶栏的指示器小程序,使得你可以快速切换电源模式。
+
+![Slimbook Battery Mode Ubuntu][4]
+
+你可能在 Windows 中见过类似的程序。Slimbook Battery 和它们一样,提供了类似的电源计划:
+
+ * 节能:最大程度延长电池续航时间
+ * 平衡:性能与节能间的最佳平衡
+ * 高性能:最大程度提高性能
+
+你可以在高级模式中配置这些模式:
+
+![配置多种多样的电源模式][5]
+
+如果你觉得你把设置调乱了,你可以用“恢复默认设置”的按钮还原它。
+
+你也可以修改像程序自启或默认电源模式这样的通用设置。
+
+![Slimbook Battery 通用设置][6]
+
+Slimbook 有专门为多种电源管理参数提供的页面。如果你希望自己配置,请参照 [此页][7]。
+
+不过,我认为 Slimbook 的界面需要一些改进。例如,某些页面上的“问题标记”的图标应该改为可点击的,以此提供更多信息。然而,在我写这篇文章时,那个标记仍然无法点击。
+
+总的来说,Slimbook Battery 是一个小巧精美的软件,你可以用它来快速切换电源模式。如果你决定在 Ubuntu 及其衍生发行版上(比如 Linux Mint 或 elementary OS 等),你可以使用官方 [PPA 源][8]。
+
+#### 在基于 Ubuntu 的发行版上安装 Slimbook Battery
+
+打开终端,一步一步地使用以下命令:
+
+```
+sudo add-apt-repository ppa:slimbook/slimbook
+sudo apt update
+sudo apt install slimbookbattery
+```
+
+安装好之后,在菜单中搜索 Slimbook Battery:
+
+![启动 Slimbook Battery Optimizer][10]
+
+在你点击它之后,你会发现它出现在了顶栏。你可以在这里选择你希望使用的电源模式。
+
+![Slimbook Battery 电源模式][4]
+
+#### 卸载 Slimbook Battery
+
+如果你不再使用它,你可以通过以下命令来卸载它:
+
+```
+sudo apt remove slimbookbattery
+sudo add-apt-repository -r ppa:slimbook/slimbook
+```
+
+在我看来,这样的应用程序为某些特定的目的服务,这是值得鼓励的。这个工具给了你一条调整电源模式的捷径,和调整性能的更多选项。
+
+你用过 Slimbook Battery 吗?你觉得它如何?
+
+--------------------------------------------------------------------------------
+
+via: https://itsfoss.com/slimbook-battry-optimizer-ubuntu/
+
+作者:[Abhishek Prakash][a]
+选题:[lujun9972][b]
+译者:[zhs852](https://github.com/zhs852)
+校对:[wxy](https://github.com/wxy)
+
+本文由 [LCTT](https://github.com/LCTT/TranslateProject) 原创编译,[Linux中国](https://linux.cn/) 荣誉推出
+
+[a]: https://itsfoss.com/author/abhishek/
+[b]: https://github.com/lujun9972
+[1]: https://slimbook.es/en/
+[2]: https://itsfoss.com/get-linux-laptops/
+[3]: https://launchpad.net/~slimbook/+archive/ubuntu/slimbook
+[4]: https://i1.wp.com/itsfoss.com/wp-content/uploads/2019/05/slimbook-battery-mode-ubuntu.jpg?resize=800%2C400&ssl=1
+[5]: https://i0.wp.com/itsfoss.com/wp-content/uploads/2019/05/slimbook-battery-optimizer-2.jpg?ssl=1
+[6]: https://i0.wp.com/itsfoss.com/wp-content/uploads/2019/05/slimbook-battery-optimizer-1.jpg?ssl=1
+[7]: https://slimbook.es/en/tutoriales/aplicaciones-slimbook/398-slimbook-battery-3-application-for-optimize-battery-of-your-laptop
+[8]: https://itsfoss.com/ppa-guide/
+[9]: https://itsfoss.com/ubuntu-forums-hacked-again/
+[10]: https://i1.wp.com/itsfoss.com/wp-content/uploads/2019/05/slimbook-battery-optimizer.jpg?ssl=1
diff --git a/published/201905/20190520 PiShrink - Make Raspberry Pi Images Smaller.md b/published/201905/20190520 PiShrink - Make Raspberry Pi Images Smaller.md
new file mode 100644
index 0000000000..3913d663df
--- /dev/null
+++ b/published/201905/20190520 PiShrink - Make Raspberry Pi Images Smaller.md
@@ -0,0 +1,118 @@
+[#]: collector: (lujun9972)
+[#]: translator: (geekpi)
+[#]: reviewer: (wxy)
+[#]: publisher: (wxy)
+[#]: url: (https://linux.cn/article-10894-1.html)
+[#]: subject: (PiShrink – Make Raspberry Pi Images Smaller)
+[#]: via: (https://www.ostechnix.com/pishrink-make-raspberry-pi-images-smaller/)
+[#]: author: (sk https://www.ostechnix.com/author/sk/)
+
+PiShrink:使树莓派镜像更小
+======
+
+![Make Raspberry Pi Images Smaller With PiShrink In Linux][1]
+
+树莓派不需要过多介绍。它是一款小巧、价格实惠,只有信用卡大小的电脑,它可以连接到显示器或电视。我们可以连接一个标准的键盘和鼠标,并将其用作一台成熟的台式计算机来完成日常任务,如互联网浏览、播放视频/玩游戏、文字处理和电子表格制作等。它主要是为学校的计算机科学教学而开发的。如今,树莓派被广泛用于大学、中小型组织和研究所来教授编码。
+
+如果你有一台树莓派,你可能需要了解一个名为 PiShrink 的 bash 脚本,该脚本可使树莓派镜像更小。PiShrink 将自动缩小镜像,然后在启动时将其调整为 SD 卡的最大大小。这能更快地将镜像复制到 SD 卡中,同时缩小的镜像将更好地压缩。这对于将大容量镜像放入 SD 卡非常有用。在这个简短的指南中,我们将学习如何在类 Unix 系统中将树莓派镜像缩小到更小。
+
+### 安装 PiShrink
+
+要在 Linux 机器上安装 PiShrink,请先使用以下命令下载最新版本:
+
+```
+$ wget https://raw.githubusercontent.com/Drewsif/PiShrink/master/pishrink.sh
+```
+
+接下来,将下载的 PiShrink 变成二进制可执行文件:
+
+```
+$ chmod +x pishrink.sh
+```
+
+最后,移动到目录:
+
+```
+$ sudo mv pishrink.sh /usr/local/bin/
+```
+
+### 使树莓派镜像更小
+
+你可能已经知道,Raspbian 是所有树莓派型号的官方操作系统。树莓派基金会为 PC 和 Mac 开发了树莓派桌面版本。你可以创建一个 live CD,并在虚拟机中运行它,甚至也可以将其安装在桌面上。树莓派也有少量非官方操作系统镜像。为了测试,我从[官方下载页面][2]下载了官方的 Raspbian 系统。
+
+解压下载的系统镜像:
+
+```
+$ unzip 2019-04-08-raspbian-stretch-lite.zip
+```
+
+上面的命令将提取当前目录中 `2019-04-08-raspbian-stretch-lite.zip` 文件的内容。
+
+让我们看下提取文件的实际大小:
+
+```
+$ du -h 2019-04-08-raspbian-stretch-lite.img
+1.7G 2019-04-08-raspbian-stretch-lite.img
+```
+
+如你所见,提取的树莓派系统镜像大小为 1.7G。
+
+现在,使用 PiShrink 缩小此文件的大小,如下所示:
+
+```
+$ sudo pishrink.sh 2019-04-08-raspbian-stretch-lite.img
+```
+
+示例输出:
+
+```
+Creating new /etc/rc.local
+rootfs: 39795/107072 files (0.1% non-contiguous), 239386/428032 blocks
+resize2fs 1.45.0 (6-Mar-2019)
+resize2fs 1.45.0 (6-Mar-2019)
+Resizing the filesystem on /dev/loop1 to 280763 (4k) blocks.
+Begin pass 3 (max = 14)
+Scanning inode table XXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXX
+Begin pass 4 (max = 3728)
+Updating inode references XXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXX
+The filesystem on /dev/loop1 is now 280763 (4k) blocks long.
+
+Shrunk 2019-04-08-raspbian-stretch-lite.img from 1.7G to 1.2G
+```
+
+正如你在上面的输出中看到的,树莓派镜像的大小已减少到 1.2G。
+
+你还可以使用 `-s` 标志跳过该过程的自动扩展部分。
+
+```
+$ sudo pishrink.sh -s 2019-04-08-raspbian-stretch-lite.img newpi.img
+```
+
+这将创建一个源镜像文件(即 `2019-04-08-raspbian-stretch-lite.img`)的副本到一个新镜像文件(`newpi.img`)并进行处理。有关更多详细信息,请查看最后给出的官方 GitHub 页面。
+
+就是这些了。希望本文有用。还有更多好东西,敬请期待!
+
+
+资源:
+
+ * [PiShrink 的 GitHub 仓库][4]
+ * [树莓派网站][5]
+
+--------------------------------------------------------------------------------
+
+via: https://www.ostechnix.com/pishrink-make-raspberry-pi-images-smaller/
+
+作者:[sk][a]
+选题:[lujun9972][b]
+译者:[geekpi](https://github.com/geekpi)
+校对:[wxy](https://github.com/wxy)
+
+本文由 [LCTT](https://github.com/LCTT/TranslateProject) 原创编译,[Linux中国](https://linux.cn/) 荣誉推出
+
+[a]: https://www.ostechnix.com/author/sk/
+[b]: https://github.com/lujun9972
+[1]: https://www.ostechnix.com/wp-content/uploads/2019/05/pishrink-720x340.png
+[2]: https://www.raspberrypi.org/downloads/
+[3]: http://www.ostechnix.com/wp-content/uploads/2019/05/pishrink-1.png
+[4]: https://github.com/Drewsif/PiShrink
+[5]: https://www.raspberrypi.org/
diff --git a/published/201905/20190520 xsos - A Tool To Read SOSReport In Linux.md b/published/201905/20190520 xsos - A Tool To Read SOSReport In Linux.md
new file mode 100644
index 0000000000..af4e47f976
--- /dev/null
+++ b/published/201905/20190520 xsos - A Tool To Read SOSReport In Linux.md
@@ -0,0 +1,396 @@
+[#]: collector: (lujun9972)
+[#]: translator: (wxy)
+[#]: reviewer: (wxy)
+[#]: publisher: (wxy)
+[#]: url: (https://linux.cn/article-10889-1.html)
+[#]: subject: (xsos – A Tool To Read SOSReport In Linux)
+[#]: via: (https://www.2daygeek.com/xsos-a-tool-to-read-sosreport-in-linux/)
+[#]: author: (Magesh Maruthamuthu https://www.2daygeek.com/author/magesh/)
+
+xsos:一个在 Linux 上阅读 SOSReport 的工具
+======
+
+
+
+我们都已经知道 [SOSReport][1]。它用来收集可用于诊断的系统信息。Redhat 的支持服务建议我们在提交案例时提供 SOSReport 来分析当前的系统状态。
+
+它会收集全部类型的报告,以帮助用户找出问题的根本原因。我们可以轻松地提取和阅读 SOSReport,但它很难阅读。因为它的每个部分都是一个单独的文件。
+
+那么,在 Linux 中使用语法高亮显示阅读所有这些内容的最佳方法是什么。是的,这可以通过 `xsos` 工具做到。
+
+### sosreport
+
+`sosreport` 命令是一个从运行中的系统(尤其是 RHEL 和 OEL 系统)收集大量配置细节、系统信息和诊断信息的工具。它可以帮助技术支持工程师在很多方面分析系统。
+
+此报告包含有关系统的大量信息,例如引导信息、文件系统、内存、主机名、已安装的 RPM、系统 IP、网络详细信息、操作系统版本、已安装的内核、已加载的内核模块、打开的文件列表、PCI 设备列表、挂载点及其细节、运行中的进程信息、进程树输出、系统路由、位于 `/etc` 文件夹中的所有配置文件,以及位于 `/var` 文件夹中的所有日志文件。
+
+这将需要一段时间来生成报告,这取决于你的系统安装和配置。
+
+完成后,`sosreport` 将在 `/tmp` 目录下生成一个压缩的归档文件。
+
+### xsos
+
+[xsos][3] 是一个帮助用户轻松读取 Linux 系统上的 `sosreport` 的工具。另一方面,我们可以说它是 `sosreport` 考官。
+
+它可以立即从 `sosreport` 或正在运行的系统中汇总系统信息。
+
+`xsos` 将尝试简化、解析、计算并格式化来自数十个文件(和命令)的数据,以便为你提供有关系统的详细概述。
+
+你可以通过运行以下命令立即汇总系统信息。
+
+```
+# curl -Lo ./xsos bit.ly/xsos-direct; chmod +x ./xsos; ./xsos -ya
+```
+
+![][5]
+
+### 如何在 Linux 上安装 xsos
+
+我们可以使用以下两种方法轻松安装 `xsos`。
+
+如果你正在寻找最新的前沿版本。使用以下步骤:
+
+```
+# curl -Lo /usr/local/bin/xsos bit.ly/xsos-direct
+# chmod +x /usr/local/bin/xsos
+```
+
+下面是安装 `xsos` 的推荐方法。它将从 rpm 文件安装 `xsos`。
+
+```
+# yum install http://people.redhat.com/rsawhill/rpms/latest-rsawaroha-release.rpm
+# yum install xsos
+```
+
+### 如何在 Linux 上使用 xsos
+
+一旦通过上述方法之一安装了 xsos。只需运行 `xsos` 命令,不带任何选项,它们会显示有关系统的基本信息。
+
+```
+# xsos
+
+OS
+ Hostname: CentOS7.2daygeek.com
+ Distro: [redhat-release] CentOS Linux release 7.6.1810 (Core)
+ [centos-release] CentOS Linux release 7.6.1810 (Core)
+ [os-release] CentOS Linux 7 (Core) 7 (Core)
+ RHN: (missing)
+ RHSM: (missing)
+ YUM: 2 enabled plugins: fastestmirror, langpacks
+ Runlevel: N 5 (default graphical)
+ SELinux: enforcing (default enforcing)
+ Arch: mach=x86_64 cpu=x86_64 platform=x86_64
+ Kernel:
+ Booted kernel: 3.10.0-957.el7.x86_64
+ GRUB default: 3.10.0-957.el7.x86_64
+ Build version:
+ Linux version 3.10.0-957.el7.x86_64 ([email protected]) (gcc version 4.8.5 20150623 (Red
+ Hat 4.8.5-36) (GCC) ) #1 SMP Thu Nov 8 23:39:32 UTC 2018
+ Booted kernel cmdline:
+ root=/dev/mapper/centos-root ro crashkernel=auto rd.lvm.lv=centos/root rd.lvm.lv=centos/swap rhgb quiet
+ LANG=en_US.UTF-8
+ GRUB default kernel cmdline:
+ root=/dev/mapper/centos-root ro crashkernel=auto rd.lvm.lv=centos/root rd.lvm.lv=centos/swap rhgb quiet
+ LANG=en_US.UTF-8
+ Taint-check: 0 (kernel untainted)
+ - - - - - - - - - - - - - - - - - - -
+ Sys time: Sun May 12 10:05:21 CDT 2019
+ Boot time: Sun May 12 09:50:20 CDT 2019 (epoch: 1557672620)
+ Time Zone: America/Chicago
+ Uptime: 15 min, 1 user
+ LoadAvg: [1 CPU] 0.00 (0%), 0.04 (4%), 0.09 (9%)
+ /proc/stat:
+ procs_running: 2 procs_blocked: 0 processes [Since boot]: 6423
+ cpu [Utilization since boot]:
+ us 1%, ni 0%, sys 1%, idle 99%, iowait 0%, irq 0%, sftirq 0%, steal 0%
+```
+
+### 如何使用 xsos 命令在 Linux 中查看生成的 SOSReport 输出?
+
+我们需要份 SOSReport 以使用 `xsos` 命令进一步阅读。
+
+是的,我已经生成了一个 SOSReport,文件如下。
+
+```
+# ls -lls -lh /var/tmp/sosreport-CentOS7-01-1005-2019-05-12-pomeqsa.tar.xz
+9.8M -rw-------. 1 root root 9.8M May 12 10:13 /var/tmp/sosreport-CentOS7-01-1005-2019-05-12-pomeqsa.tar.xz
+```
+
+运行如下命令解开它。
+
+```
+# tar xf sosreport-CentOS7-01-1005-2019-05-12-pomeqsa.tar.xz
+```
+
+要查看全部信息,带上 `-a` 或 `--all` 开关运行 `xsos`:
+
+```
+# xsos --all /var/tmp/sosreport-CentOS7-01-1005-2019-05-12-pomeqsa
+```
+
+要查看 BIOS 信息,带上 `-b` 或 `--bios` 开关运行 `xsos`。
+
+```
+# xsos --bios /var/tmp/sosreport-CentOS7-01-1005-2019-05-12-pomeqsa
+DMIDECODE
+ BIOS:
+ Vend: innotek GmbH
+ Vers: VirtualBox
+ Date: 12/01/2006
+ BIOS Rev:
+ FW Rev:
+ System:
+ Mfr: innotek GmbH
+ Prod: VirtualBox
+ Vers: 1.2
+ Ser: 0
+ UUID: 002f47b8-2af2-48f5-be1d-67b67e03514c
+ CPU:
+ 0 of 0 CPU sockets populated, 0 cores/0 threads per CPU
+ 0 total cores, 0 total threads
+ Mfr:
+ Fam:
+ Freq:
+ Vers:
+ Memory:
+ Total: 0 MiB (0 GiB)
+ DIMMs: 0 of 0 populated
+ MaxCapacity: 0 MiB (0 GiB / 0.00 TiB)
+```
+
+要查看系统基本信息,如主机名、发行版、SELinux、内核信息、正常运行时间等,请使用 `-o` 或 `--os` 开关运行 `xsos`。
+
+```
+# xsos --os /var/tmp/sosreport-CentOS7-01-1005-2019-05-12-pomeqsa
+OS
+ Hostname: CentOS7.2daygeek.com
+ Distro: [redhat-release] CentOS Linux release 7.6.1810 (Core)
+ [centos-release] CentOS Linux release 7.6.1810 (Core)
+ [os-release] CentOS Linux 7 (Core) 7 (Core)
+ RHN: (missing)
+ RHSM: (missing)
+ YUM: 2 enabled plugins: fastestmirror, langpacks
+ SELinux: enforcing (default enforcing)
+ Arch: mach=x86_64 cpu=x86_64 platform=x86_64
+ Kernel:
+ Booted kernel: 3.10.0-957.el7.x86_64
+ GRUB default: 3.10.0-957.el7.x86_64
+ Build version:
+ Linux version 3.10.0-957.el7.x86_64 ([email protected]) (gcc version 4.8.5 20150623 (Red
+ Hat 4.8.5-36) (GCC) ) #1 SMP Thu Nov 8 23:39:32 UTC 2018
+ Booted kernel cmdline:
+ root=/dev/mapper/centos-root ro crashkernel=auto rd.lvm.lv=centos/root rd.lvm.lv=centos/swap rhgb quiet
+ LANG=en_US.UTF-8
+ GRUB default kernel cmdline:
+ root=/dev/mapper/centos-root ro crashkernel=auto rd.lvm.lv=centos/root rd.lvm.lv=centos/swap rhgb quiet
+ LANG=en_US.UTF-8
+ Taint-check: 536870912 (see https://access.redhat.com/solutions/40594)
+ 29 TECH_PREVIEW: Technology Preview code is loaded
+ - - - - - - - - - - - - - - - - - - -
+ Sys time: Sun May 12 10:12:22 CDT 2019
+ Boot time: Sun May 12 09:50:20 CDT 2019 (epoch: 1557672620)
+ Time Zone: America/Chicago
+ Uptime: 22 min, 1 user
+ LoadAvg: [1 CPU] 1.19 (119%), 0.27 (27%), 0.14 (14%)
+ /proc/stat:
+ procs_running: 8 procs_blocked: 2 processes [Since boot]: 9005
+ cpu [Utilization since boot]:
+ us 1%, ni 0%, sys 1%, idle 99%, iowait 0%, irq 0%, sftirq 0%, steal 0%
+```
+
+要查看 kdump 配置,请使用 `-k` 或 `--kdump` 开关运行 `xsos`。
+
+```
+# xsos --kdump /var/tmp/sosreport-CentOS7-01-1005-2019-05-12-pomeqsa
+KDUMP CONFIG
+ kexec-tools rpm version:
+ kexec-tools-2.0.15-21.el7.x86_64
+ Service enablement:
+ UNIT STATE
+ kdump.service enabled
+ kdump initrd/initramfs:
+ 13585734 Feb 19 05:51 initramfs-3.10.0-957.el7.x86_64kdump.img
+ Memory reservation config:
+ /proc/cmdline { crashkernel=auto }
+ GRUB default { crashkernel=auto }
+ Actual memory reservation per /proc/iomem:
+ 2a000000-340fffff : Crash kernel
+ kdump.conf:
+ path /var/crash
+ core_collector makedumpfile -l --message-level 1 -d 31
+ kdump.conf "path" available space:
+ System MemTotal (uncompressed core size) { 1.80 GiB }
+ Available free space on target path's fs { 22.68 GiB } (fs=/)
+ Panic sysctls:
+ kernel.sysrq [bitmask] = "16" (see proc man page)
+ kernel.panic [secs] = 0 (no autoreboot on panic)
+ kernel.hung_task_panic = 0
+ kernel.panic_on_oops = 1
+ kernel.panic_on_io_nmi = 0
+ kernel.panic_on_unrecovered_nmi = 0
+ kernel.panic_on_stackoverflow = 0
+ kernel.softlockup_panic = 0
+ kernel.unknown_nmi_panic = 0
+ kernel.nmi_watchdog = 1
+ vm.panic_on_oom [0-2] = 0 (no panic)
+```
+
+要查看有关 CPU 的信息,请使用 `-c` 或 `--cpu` 开关运行 `xsos`。
+
+```
+# xsos --cpu /var/tmp/sosreport-CentOS7-01-1005-2019-05-12-pomeqsa
+CPU
+ 1 logical processors
+ 1 Intel Core i7-6700HQ CPU @ 2.60GHz (flags: aes,constant_tsc,ht,lm,nx,pae,rdrand)
+```
+
+要查看内存利用情况,请使用 `-m` 或 `--mem` 开关运行 `xsos`。
+
+```
+# xsos --mem /var/tmp/sosreport-CentOS7-01-1005-2019-05-12-pomeqsa
+MEMORY
+ Stats graphed as percent of MemTotal:
+ MemUsed ▊▊▊▊▊▊▊▊▊▊▊▊▊▊▊▊▊▊▊▊▊▊▊▊▊▊▊▊▊..................... 58.8%
+ Buffers .................................................. 0.6%
+ Cached ▊▊▊▊▊▊▊▊▊▊▊▊▊▊▊................................... 29.9%
+ HugePages .................................................. 0.0%
+ Dirty .................................................. 0.7%
+ RAM:
+ 1.8 GiB total ram
+ 1.1 GiB (59%) used
+ 0.5 GiB (28%) used excluding Buffers/Cached
+ 0.01 GiB (1%) dirty
+ HugePages:
+ No ram pre-allocated to HugePages
+ LowMem/Slab/PageTables/Shmem:
+ 0.09 GiB (5%) of total ram used for Slab
+ 0.02 GiB (1%) of total ram used for PageTables
+ 0.01 GiB (1%) of total ram used for Shmem
+ Swap:
+ 0 GiB (0%) used of 2 GiB total
+```
+
+要查看添加的磁盘信息,请使用 `-d` 和 `-disks` 开关运行 `xsos`。
+
+```
+# xsos --disks /var/tmp/sosreport-CentOS7-01-1005-2019-05-12-pomeqsa
+STORAGE
+ Whole Disks from /proc/partitions:
+ 2 disks, totaling 40 GiB (0.04 TiB)
+ - - - - - - - - - - - - - - - - - - - - -
+ Disk Size in GiB
+ ---- -----------
+ sda 30
+ sdb 10
+```
+
+要查看网络接口配置,请使用 `-e` 或 `--ethtool` 开关运行 `xsos`。
+
+```
+# xsos --ethtool /var/tmp/sosreport-CentOS7-01-1005-2019-05-12-pomeqsa
+ETHTOOL
+ Interface Status:
+ enp0s10 0000:00:0a.0 link=up 1000Mb/s full (autoneg=Y) rx ring 256/4096 drv e1000 v7.3.21-k8-NAPI / fw UNKNOWN
+ enp0s9 0000:00:09.0 link=up 1000Mb/s full (autoneg=Y) rx ring 256/4096 drv e1000 v7.3.21-k8-NAPI / fw UNKNOWN
+ virbr0 N/A link=DOWN rx ring UNKNOWN drv bridge v2.3 / fw N/A
+ virbr0-nic tap link=DOWN rx ring UNKNOWN drv tun v1.6 / fw UNKNOWN
+```
+
+要查看有关 IP 地址的信息,请使用 `-i` 或 `--ip` 开关运行 `xsos`。
+
+```
+# xsos --ip /var/tmp/sosreport-CentOS7-01-1005-2019-05-12-pomeqsa
+IP4
+ Interface Master IF MAC Address MTU State IPv4 Address
+ ========= ========= ================= ====== ===== ==================
+ lo - - 65536 up 127.0.0.1/8
+ enp0s9 - 08:00:27:0b:bc:e9 1500 up 192.168.1.8/24
+ enp0s10 - 08:00:27:b2:08:91 1500 up 192.168.1.9/24
+ virbr0 - 52:54:00:ae:01:94 1500 up 192.168.122.1/24
+ virbr0-nic virbr0 52:54:00:ae:01:94 1500 DOWN -
+
+IP6
+ Interface Master IF MAC Address MTU State IPv6 Address Scope
+ ========= ========= ================= ====== ===== =========================================== =====
+ lo - - 65536 up ::1/128 host
+ enp0s9 - 08:00:27:0b:bc:e9 1500 up fe80::945b:8333:f4bc:9723/64 link
+ enp0s10 - 08:00:27:b2:08:91 1500 up fe80::7ed4:1fab:23c3:3790/64 link
+ virbr0 - 52:54:00:ae:01:94 1500 up - -
+ virbr0-nic virbr0 52:54:00:ae:01:94 1500 DOWN - -
+```
+
+要通过 `ps` 查看正在运行的进程,请使用 `-p` 或 `--ps` 开关运行 `xsos`。
+
+```
+# xsos --ps /var/tmp/sosreport-CentOS7-01-1005-2019-05-12-pomeqsa
+PS CHECK
+ Total number of threads/processes:
+ 501 / 171
+ Top users of CPU & MEM:
+ USER %CPU %MEM RSS
+ root 20.6% 14.1% 0.30 GiB
+ gdm 0.3% 16.8% 0.33 GiB
+ postfix 0.0% 0.6% 0.01 GiB
+ polkitd 0.0% 0.6% 0.01 GiB
+ daygeek 0.0% 0.2% 0.00 GiB
+ colord 0.0% 0.4% 0.01 GiB
+ Uninteruptible sleep threads/processes (0/0):
+ [None]
+ Defunct zombie threads/processes (0/0):
+ [None]
+ Top CPU-using processes:
+ USER PID %CPU %MEM VSZ-MiB RSS-MiB TTY STAT START TIME COMMAND
+ root 6542 15.6 4.2 875 78 pts/0 Sl+ 10:11 0:07 /usr/bin/python /sbin/sosreport
+ root 7582 3.0 0.1 10 2 pts/0 S 10:12 0:00 /bin/bash /usr/sbin/dracut --print-cmdline
+ root 7969 0.7 0.1 95 4 ? Ss 10:12 0:00 /usr/sbin/certmonger -S -p
+ root 7889 0.4 0.2 24 4 ? Ss 10:12 0:00 /usr/lib/systemd/systemd-hostnamed
+ gdm 3866 0.3 7.1 2856 131 ? Sl 09:50 0:04 /usr/bin/gnome-shell
+ root 8553 0.2 0.1 47 3 ? S 10:12 0:00 /usr/lib/systemd/systemd-udevd
+ root 6971 0.2 0.4 342 9 ? Sl 10:12 0:00 /usr/sbin/abrt-dbus -t133
+ root 3200 0.2 0.9 982 18 ? Ssl 09:50 0:02 /usr/sbin/libvirtd
+ root 2855 0.1 0.1 88 3 ? Ss 09:50 0:01 /sbin/rngd -f
+ rtkit 2826 0.0 0.0 194 2 ? SNsl 09:50 0:00 /usr/libexec/rtkit-daemon
+ Top MEM-using processes:
+ USER PID %CPU %MEM VSZ-MiB RSS-MiB TTY STAT START TIME COMMAND
+ gdm 3866 0.3 7.1 2856 131 ? Sl 09:50 0:04 /usr/bin/gnome-shell
+ root 6542 15.6 4.2 875 78 pts/0 Sl+ 10:11 0:07 /usr/bin/python /sbin/sosreport
+ root 3264 0.0 1.2 271 23 tty1 Ssl+ 09:50 0:00 /usr/bin/X :0 -background
+ root 3200 0.2 0.9 982 18 ? Ssl 09:50 0:02 /usr/sbin/libvirtd
+ root 3189 0.0 0.9 560 17 ? Ssl 09:50 0:00 /usr/bin/python2 -Es /usr/sbin/tuned
+ gdm 4072 0.0 0.9 988 17 ? Sl 09:50 0:00 /usr/libexec/gsd-media-keys
+ gdm 4076 0.0 0.8 625 16 ? Sl 09:50 0:00 /usr/libexec/gsd-power
+ gdm 4056 0.0 0.8 697 16 ? Sl 09:50 0:00 /usr/libexec/gsd-color
+ root 2853 0.0 0.7 622 14 ? Ssl 09:50 0:00 /usr/sbin/NetworkManager --no-daemon
+ gdm 4110 0.0 0.7 544 14 ? Sl 09:50 0:00 /usr/libexec/gsd-wacom
+ Top thread-spawning processes:
+ # USER PID %CPU %MEM VSZ-MiB RSS-MiB TTY STAT START TIME COMMAND
+ 17 root 3200 0.2 0.9 982 18 ? - 09:50 0:02 /usr/sbin/libvirtd
+ 12 root 6542 16.1 4.5 876 83 pts/0 - 10:11 0:07 /usr/bin/python /sbin/sosreport
+ 10 gdm 3866 0.3 7.1 2856 131 ? - 09:50 0:04 /usr/bin/gnome-shell
+ 7 polkitd 2864 0.0 0.6 602 13 ? - 09:50 0:01 /usr/lib/polkit-1/polkitd --no-debug
+ 6 root 2865 0.0 0.0 203 1 ? - 09:50 0:00 /usr/sbin/gssproxy -D
+ 5 root 3189 0.0 0.9 560 17 ? - 09:50 0:00 /usr/bin/python2 -Es /usr/sbin/tuned
+ 5 root 2823 0.0 0.3 443 6 ? - 09:50 0:00 /usr/libexec/udisks2/udisksd
+ 5 gdm 4102 0.0 0.2 461 5 ? - 09:50 0:00 /usr/libexec/gsd-smartcard
+ 4 root 3215 0.0 0.2 470 4 ? - 09:50 0:00 /usr/sbin/gdm
+ 4 gdm 4106 0.0 0.2 444 5 ? - 09:50 0:00 /usr/libexec/gsd-sound
+```
+
+--------------------------------------------------------------------------------
+
+via: https://www.2daygeek.com/xsos-a-tool-to-read-sosreport-in-linux/
+
+作者:[Magesh Maruthamuthu][a]
+选题:[lujun9972][b]
+译者:[wxy](https://github.com/wxy)
+校对:[wxy](https://github.com/wxy)
+
+本文由 [LCTT](https://github.com/LCTT/TranslateProject) 原创编译,[Linux中国](https://linux.cn/) 荣誉推出
+
+[a]: https://www.2daygeek.com/author/magesh/
+[b]: https://github.com/lujun9972
+[1]: https://www.2daygeek.com/how-to-create-collect-sosreport-in-linux/
+[2]: https://www.2daygeek.com/oswbb-how-to-install-and-configure-oswatcher-black-box-for-system-diagnostics/
+[3]: https://github.com/ryran/xsos
+[4]: data:image/gif;base64,R0lGODlhAQABAIAAAAAAAP///yH5BAEAAAAALAAAAAABAAEAAAIBRAA7
+[5]: https://www.2daygeek.com/wp-content/uploads/2019/05/xsos-a-tool-to-read-sosreport-in-linux-1.jpg
diff --git a/published/20190505 How To Install-Uninstall Listed Packages From A File In Linux.md b/published/20190505 How To Install-Uninstall Listed Packages From A File In Linux.md
new file mode 100644
index 0000000000..4960672f5a
--- /dev/null
+++ b/published/20190505 How To Install-Uninstall Listed Packages From A File In Linux.md
@@ -0,0 +1,331 @@
+[#]: collector: (lujun9972)
+[#]: translator: (way-ww)
+[#]: reviewer: (wxy)
+[#]: publisher: (wxy)
+[#]: url: (https://linux.cn/article-10923-1.html)
+[#]: subject: (How To Install/Uninstall Listed Packages From A File In Linux?)
+[#]: via: (https://www.2daygeek.com/how-to-install-uninstall-listed-packages-from-a-file-in-linux/)
+[#]: author: (Magesh Maruthamuthu https://www.2daygeek.com/author/magesh/)
+
+如何在 Linux 上安装/卸载一个文件中列出的软件包?
+======
+
+在某些情况下,你可能想要将一个服务器上的软件包列表安装到另一个服务器上。例如,你已经在服务器 A 上安装了 15 个软件包并且这些软件包也需要被安装到服务器 B、服务器 C 上等等。
+
+我们可以手动去安装这些软件但是这将花费大量的时间。你可以手动安装一俩个服务器,但是试想如果你有大概十个服务器呢。在这种情况下你无法手动完成工作,那么怎样才能解决问题呢?
+
+不要担心我们可以帮你摆脱这样的情况和场景。我们在这篇文章中增加了四种方法来克服困难。
+
+我希望这可以帮你解决问题。我已经在 Centos7 和 Ubuntu 18.04 上测试了这些命令。
+
+我也希望这可以在其他发行版上工作。这仅仅需要使用该发行版的官方包管理器命令替代本文中的包管理器命令就行了。
+
+如果想要 [检查 Linux 系统上已安装的软件包列表][1],请点击链接。
+
+例如,如果你想要在基于 RHEL 系统上创建软件包列表请使用以下步骤。其他发行版也一样。
+
+```
+# rpm -qa --last | head -15 | awk '{print $1}' > /tmp/pack1.txt
+
+# cat /tmp/pack1.txt
+mariadb-server-5.5.60-1.el7_5.x86_64
+perl-DBI-1.627-4.el7.x86_64
+perl-DBD-MySQL-4.023-6.el7.x86_64
+perl-PlRPC-0.2020-14.el7.noarch
+perl-Net-Daemon-0.48-5.el7.noarch
+perl-IO-Compress-2.061-2.el7.noarch
+perl-Compress-Raw-Zlib-2.061-4.el7.x86_64
+mariadb-5.5.60-1.el7_5.x86_64
+perl-Data-Dumper-2.145-3.el7.x86_64
+perl-Compress-Raw-Bzip2-2.061-3.el7.x86_64
+httpd-2.4.6-88.el7.centos.x86_64
+mailcap-2.1.41-2.el7.noarch
+httpd-tools-2.4.6-88.el7.centos.x86_64
+apr-util-1.5.2-6.el7.x86_64
+apr-1.4.8-3.el7_4.1.x86_64
+```
+
+### 方法一:如何在 Linux 上使用 cat 命令安装文件中列出的包?
+
+为实现这个目标,我将使用简单明了的第一种方法。为此,创建一个文件并添加上你想要安装的包列表。
+
+出于测试的目的,我们将只添加以下的三个软件包名到文件中。
+
+```
+# cat /tmp/pack1.txt
+
+apache2
+mariadb-server
+nano
+```
+
+只要简单的运行 [apt 命令][2] 就能在 Ubuntu/Debian 系统上一次性安装所有的软件包。
+
+```
+# apt -y install $(cat /tmp/pack1.txt)
+
+Reading package lists... Done
+Building dependency tree
+Reading state information... Done
+The following packages were automatically installed and are no longer required:
+ libopts25 sntp
+Use 'sudo apt autoremove' to remove them.
+Suggested packages:
+ apache2-doc apache2-suexec-pristine | apache2-suexec-custom spell
+The following NEW packages will be installed:
+ apache2 mariadb-server nano
+0 upgraded, 3 newly installed, 0 to remove and 24 not upgraded.
+Need to get 339 kB of archives.
+After this operation, 1,377 kB of additional disk space will be used.
+Get:1 http://in.archive.ubuntu.com/ubuntu bionic-updates/main amd64 apache2 amd64 2.4.29-1ubuntu4.6 [95.1 kB]
+Get:2 http://in.archive.ubuntu.com/ubuntu bionic/main amd64 nano amd64 2.9.3-2 [231 kB]
+Get:3 http://in.archive.ubuntu.com/ubuntu bionic-updates/universe amd64 mariadb-server all 1:10.1.38-0ubuntu0.18.04.1 [12.9 kB]
+Fetched 339 kB in 19s (18.0 kB/s)
+Selecting previously unselected package apache2.
+(Reading database ... 290926 files and directories currently installed.)
+Preparing to unpack .../apache2_2.4.29-1ubuntu4.6_amd64.deb ...
+Unpacking apache2 (2.4.29-1ubuntu4.6) ...
+Selecting previously unselected package nano.
+Preparing to unpack .../nano_2.9.3-2_amd64.deb ...
+Unpacking nano (2.9.3-2) ...
+Selecting previously unselected package mariadb-server.
+Preparing to unpack .../mariadb-server_1%3a10.1.38-0ubuntu0.18.04.1_all.deb ...
+Unpacking mariadb-server (1:10.1.38-0ubuntu0.18.04.1) ...
+Processing triggers for ufw (0.36-0ubuntu0.18.04.1) ...
+Setting up apache2 (2.4.29-1ubuntu4.6) ...
+Processing triggers for ureadahead (0.100.0-20) ...
+Processing triggers for install-info (6.5.0.dfsg.1-2) ...
+Setting up nano (2.9.3-2) ...
+update-alternatives: using /bin/nano to provide /usr/bin/editor (editor) in auto mode
+update-alternatives: using /bin/nano to provide /usr/bin/pico (pico) in auto mode
+Processing triggers for systemd (237-3ubuntu10.20) ...
+Processing triggers for man-db (2.8.3-2ubuntu0.1) ...
+Setting up mariadb-server (1:10.1.38-0ubuntu0.18.04.1) ...
+```
+
+至于删除,需要使用相同的命令格式和适当的选项。
+
+```
+# apt -y remove $(cat /tmp/pack1.txt)
+Reading package lists... Done
+Building dependency tree
+Reading state information... Done
+The following packages were automatically installed and are no longer required:
+ apache2-bin apache2-data apache2-utils galera-3 libaio1 libapr1 libaprutil1 libaprutil1-dbd-sqlite3 libaprutil1-ldap libconfig-inifiles-perl libdbd-mysql-perl libdbi-perl libjemalloc1 liblua5.2-0
+ libmysqlclient20 libopts25 libterm-readkey-perl mariadb-client-10.1 mariadb-client-core-10.1 mariadb-common mariadb-server-10.1 mariadb-server-core-10.1 mysql-common sntp socat
+Use 'apt autoremove' to remove them.
+The following packages will be REMOVED:
+ apache2 mariadb-server nano
+0 upgraded, 0 newly installed, 3 to remove and 24 not upgraded.
+After this operation, 1,377 kB disk space will be freed.
+(Reading database ... 291046 files and directories currently installed.)
+Removing apache2 (2.4.29-1ubuntu4.6) ...
+Removing mariadb-server (1:10.1.38-0ubuntu0.18.04.1) ...
+Removing nano (2.9.3-2) ...
+update-alternatives: using /usr/bin/vim.tiny to provide /usr/bin/editor (editor) in auto mode
+Processing triggers for ufw (0.36-0ubuntu0.18.04.1) ...
+Processing triggers for install-info (6.5.0.dfsg.1-2) ...
+Processing triggers for man-db (2.8.3-2ubuntu0.1) ...
+```
+
+使用 [yum 命令][3] 在基于 RHEL (如 Centos、RHEL (Redhat) 和 OEL (Oracle Enterprise Linux)) 的系统上安装文件中列出的软件包。
+
+```
+# yum -y install $(cat /tmp/pack1.txt)
+```
+
+使用以命令在基于 RHEL (如 Centos、RHEL (Redhat) 和 OEL (Oracle Enterprise Linux)) 的系统上卸载文件中列出的软件包。
+
+```
+# yum -y remove $(cat /tmp/pack1.txt)
+```
+
+使用以下 [dnf 命令][4] 在 Fedora 系统上安装文件中列出的软件包。
+
+```
+# dnf -y install $(cat /tmp/pack1.txt)
+```
+
+使用以下命令在 Fedora 系统上卸载文件中列出的软件包。
+
+```
+# dnf -y remove $(cat /tmp/pack1.txt)
+```
+
+使用以下 [zypper 命令][5] 在 openSUSE 系统上安装文件中列出的软件包。
+
+```
+# zypper -y install $(cat /tmp/pack1.txt)
+```
+
+使用以下命令从 openSUSE 系统上卸载文件中列出的软件包。
+
+```
+# zypper -y remove $(cat /tmp/pack1.txt)
+```
+
+使用以下 [pacman 命令][6] 在基于 Arch Linux (如 Manjaro 和 Antergos) 的系统上安装文件中列出的软件包。
+
+```
+# pacman -S $(cat /tmp/pack1.txt)
+```
+
+使用以下命令从基于 Arch Linux (如 Manjaro 和 Antergos) 的系统中卸载文件中列出的软件包。
+
+
+```
+# pacman -Rs $(cat /tmp/pack1.txt)
+```
+
+### 方法二:如何使用 cat 和 xargs 命令在 Linux 中安装文件中列出的软件包。
+
+甚至,我更喜欢使用这种方法,因为这是一种非常简单直接的方法。
+
+使用以下 `apt` 命令在基于 Debian 的系统 (如 Debian、Ubuntu 和 Linux Mint) 上安装文件中列出的软件包。
+
+```
+# cat /tmp/pack1.txt | xargs apt -y install
+```
+
+使用以下 `apt` 命令 从基于 Debian 的系统 (如 Debian、Ubuntu 和 Linux Mint) 上卸载文件中列出的软件包。
+
+```
+# cat /tmp/pack1.txt | xargs apt -y remove
+```
+
+使用以下 `yum` 命令在基于 RHEL (如 Centos,RHEL (Redhat) 和 OEL (Oracle Enterprise Linux)) 的系统上安装文件中列出的软件包。
+
+```
+# cat /tmp/pack1.txt | xargs yum -y install
+```
+
+使用以命令从基于 RHEL (如 Centos、RHEL (Redhat) 和 OEL (Oracle Enterprise Linux)) 的系统上卸载文件中列出的软件包。
+
+```
+# cat /tmp/pack1.txt | xargs yum -y remove
+```
+
+使用以下 `dnf` 命令在 Fedora 系统上安装文件中列出的软件包。
+
+```
+# cat /tmp/pack1.txt | xargs dnf -y install
+```
+
+使用以下命令从 Fedora 系统上卸载文件中列出的软件包。
+
+```
+# cat /tmp/pack1.txt | xargs dnf -y remove
+```
+
+使用以下 `zypper` 命令在 openSUSE 系统上安装文件中列出的软件包。
+
+
+```
+# cat /tmp/pack1.txt | xargs zypper -y install
+```
+
+使用以下命令从 openSUSE 系统上卸载文件中列出的软件包。
+
+```
+# cat /tmp/pack1.txt | xargs zypper -y remove
+```
+
+使用以下 `pacman` 命令在基于 Arch Linux (如 Manjaro 和 Antergos) 的系统上安装文件中列出的软件包。
+
+```
+# cat /tmp/pack1.txt | xargs pacman -S
+```
+
+使用下以命令从基于 Arch Linux (如 Manjaro 和 Antergos) 的系统上卸载文件中列出的软件包。
+
+```
+# cat /tmp/pack1.txt | xargs pacman -Rs
+```
+
+### 方法三 : 如何使用 For 循环在 Linux 上安装文件中列出的软件包
+
+我们也可以使用 `for` 循环命令来实现此目的。
+
+安装批量包可以使用以下一条 `for` 循环的命令。
+
+```
+# for pack in `cat /tmp/pack1.txt` ; do apt -y install $i; done
+```
+
+要使用 shell 脚本安装批量包,请使用以下 `for` 循环。
+
+```
+# vi /opt/scripts/bulk-package-install.sh
+
+#!/bin/bash
+for pack in `cat /tmp/pack1.txt`
+do apt -y remove $pack
+done
+```
+
+为 `bulk-package-install.sh` 设置可执行权限。
+
+```
+# chmod + bulk-package-install.sh
+```
+
+最后运行这个脚本。
+
+```
+# sh bulk-package-install.sh
+```
+
+### 方法四:如何使用 While 循环在 Linux 上安装文件中列出的软件包
+
+我们也可以使用 `while` 循环命令来实现目的。
+
+安装批量包可以使用以下一条 `while` 循环的命令。
+
+```
+# file="/tmp/pack1.txt"; while read -r pack; do apt -y install $pack; done < "$file"
+```
+
+要使用 shell 脚本安装批量包,请使用以下 `while` 循环。
+
+```
+# vi /opt/scripts/bulk-package-install.sh
+
+#!/bin/bash
+file="/tmp/pack1.txt"
+while read -r pack
+do apt -y remove $pack
+done < "$file"
+```
+
+为 `bulk-package-install.sh` 设置可执行权限。
+
+```
+# chmod + bulk-package-install.sh
+```
+
+最后运行这个脚本。
+
+```
+# sh bulk-package-install.sh
+```
+
+--------------------------------------------------------------------------------
+
+via: https://www.2daygeek.com/how-to-install-uninstall-listed-packages-from-a-file-in-linux/
+
+作者:[Magesh Maruthamuthu][a]
+选题:[lujun9972][b]
+译者:[way-ww](https://github.com/way-ww)
+校对:[wxy](https://github.com/wxy)
+
+本文由 [LCTT](https://github.com/LCTT/TranslateProject) 原创编译,[Linux中国](https://linux.cn/) 荣誉推出
+
+[a]: https://www.2daygeek.com/author/magesh/
+[b]: https://github.com/lujun9972
+[1]: https://linux.cn/article-10116-1.html
+[2]: https://www.2daygeek.com/apt-command-examples-manage-packages-debian-ubuntu-systems/
+[3]: https://www.2daygeek.com/yum-command-examples-manage-packages-rhel-centos-systems/
+[4]: https://www.2daygeek.com/dnf-command-examples-manage-packages-fedora-system/
+[5]: https://www.2daygeek.com/zypper-command-examples-manage-packages-opensuse-system/
+[6]: https://www.2daygeek.com/pacman-command-examples-manage-packages-arch-linux-system/
+
diff --git a/published/20190517 Using Testinfra with Ansible to verify server state.md b/published/20190517 Using Testinfra with Ansible to verify server state.md
new file mode 100644
index 0000000000..9b2dc01e26
--- /dev/null
+++ b/published/20190517 Using Testinfra with Ansible to verify server state.md
@@ -0,0 +1,154 @@
+[#]: collector: (lujun9972)
+[#]: translator: (geekpi)
+[#]: reviewer: (wxy)
+[#]: publisher: (wxy)
+[#]: url: (https://linux.cn/article-10943-1.html)
+[#]: subject: (Using Testinfra with Ansible to verify server state)
+[#]: via: (https://opensource.com/article/19/5/using-testinfra-ansible-verify-server-state)
+[#]: author: (Clement Verna https://opensource.com/users/cverna/users/paulbischoff/users/dcritch/users/cobiacomm/users/wgarry155/users/kadinroob/users/koreyhilpert)
+
+使用 Testinfra 和 Ansible 验证服务器状态
+======
+
+> Testinfra 是一个功能强大的库,可用于编写测试来验证基础设施的状态。另外它与 Ansible 和 Nagios 相结合,提供了一个用于架构即代码 (IaC) 的简单解决方案。
+
+![Terminal command prompt on orange background][1]
+
+根据设计,[Ansible][2] 传递机器的期望状态,以确保 Ansible 剧本或角色的内容部署到目标机器上。但是,如果你需要确保所有基础架构更改都在 Ansible 中,该怎么办?或者想随时验证服务器的状态?
+
+[Testinfra][3] 是一个基础架构测试框架,它可以轻松编写单元测试来验证服务器的状态。它是一个 Python 库,使用强大的 [pytest][4] 测试引擎。
+
+### 开始使用 Testinfra
+
+可以使用 Python 包管理器(`pip`)和 Python 虚拟环境轻松安装 Testinfra。
+
+```
+$ python3 -m venv venv
+$ source venv/bin/activate
+(venv) $ pip install testinfra
+```
+
+Testinfra 也可以通过 Fedora 和 CentOS 的 EPEL 仓库中使用。例如,在 CentOS 7 上,你可以使用以下命令安装它:
+
+```
+$ yum install -y epel-release
+$ yum install -y python-testinfra
+```
+
+#### 一个简单的测试脚本
+
+在 Testinfra 中编写测试很容易。使用你选择的代码编辑器,将以下内容添加到名为 `test_simple.py` 的文件中:
+
+```
+import testinfra
+
+def test_os_release(host):
+ assert host.file("/etc/os-release").contains("Fedora")
+
+def test_sshd_inactive(host):
+ assert host.service("sshd").is_running is False
+```
+
+默认情况下,Testinfra 为测试用例提供了一个 `host` 对象,该对象能访问不同的辅助模块。例如,第一个测试使用 `file` 模块来验证主机上文件的内容,第二个测试用例使用 `service` 模块来检查 systemd 服务的状态。
+
+要在本机运行这些测试,请执行以下命令:
+
+```
+(venv)$ pytest test_simple.py
+================================ test session starts ================================
+platform linux -- Python 3.7.3, pytest-4.4.1, py-1.8.0, pluggy-0.9.0
+rootdir: /home/cverna/Documents/Python/testinfra
+plugins: testinfra-3.0.0
+collected 2 items
+test_simple.py ..
+
+================================ 2 passed in 0.05 seconds ================================
+```
+
+有关 Testinfra API 的完整列表,你可以参考[文档][5]。
+
+### Testinfra 和 Ansible
+
+Testinfra 支持的后端之一是 Ansible,这意味着 Testinfra 可以直接使用 Ansible 的清单文件和清单中定义的一组机器来对它们进行测试。
+
+我们使用以下清单文件作为示例:
+
+```
+[web]
+app-frontend01
+app-frontend02
+
+[database]
+db-backend01
+```
+
+我们希望确保我们的 Apache Web 服务器在 `app-frontend01` 和 `app-frontend02` 上运行。让我们在名为 `test_web.py` 的文件中编写测试:
+
+```
+def check_httpd_service(host):
+ """Check that the httpd service is running on the host"""
+ assert host.service("httpd").is_running
+```
+
+要使用 Testinfra 和 Ansible 运行此测试,请使用以下命令:
+
+
+```
+(venv) $ pip install ansible
+(venv) $ py.test --hosts=web --ansible-inventory=inventory --connection=ansible test_web.py
+```
+
+在调用测试时,我们使用 Ansible 清单文件的 `[web]` 组作为目标计算机,并指定我们要使用 Ansible 作为连接后端。
+
+#### 使用 Ansible 模块
+
+Testinfra 还为 Ansible 提供了一个很好的可用于测试的 API。该 Ansible 模块能够在测试中运行 Ansible 动作,并且能够轻松检查动作的状态。
+
+```
+def check_ansible_play(host):
+ """
+ Verify that a package is installed using Ansible
+ package module
+ """
+ assert not host.ansible("package", "name=httpd state=present")["changed"]
+```
+
+默认情况下,Ansible 的[检查模式][6]已启用,这意味着 Ansible 将报告在远程主机上执行动作时会发生的变化。
+
+### Testinfra 和 Nagios
+
+现在我们可以轻松地运行测试来验证机器的状态,我们可以使用这些测试来触发监控系统上的警报。这是捕获意外的更改的好方法。
+
+Testinfra 提供了与 [Nagios][7] 的集成,它是一种流行的监控解决方案。默认情况下,Nagios 使用 [NRPE][8] 插件对远程主机进行检查,但使用 Testinfra 可以直接从 Nagios 主控节点上运行测试。
+
+要使 Testinfra 输出与 Nagios 兼容,我们必须在触发测试时使用 `--nagios` 标志。我们还使用 `-qq` 这个 pytest 标志来启用 pytest 的静默模式,这样就不会显示所有测试细节。
+
+```
+(venv) $ py.test --hosts=web --ansible-inventory=inventory --connection=ansible --nagios -qq line test.py
+TESTINFRA OK - 1 passed, 0 failed, 0 skipped in 2.55 seconds
+```
+
+Testinfra 是一个功能强大的库,可用于编写测试以验证基础架构的状态。 另外与 Ansible 和 Nagios 相结合,提供了一个用于架构即代码 (IaC) 的简单解决方案。 它也是使用 [Molecule][9] 开发 Ansible 角色过程中添加测试的关键组件。
+
+--------------------------------------------------------------------------------
+
+via: https://opensource.com/article/19/5/using-testinfra-ansible-verify-server-state
+
+作者:[Clement Verna][a]
+选题:[lujun9972][b]
+译者:[geekpi](https://github.com/geekpi)
+校对:[wxy](https://github.com/wxy)
+
+本文由 [LCTT](https://github.com/LCTT/TranslateProject) 原创编译,[Linux中国](https://linux.cn/) 荣誉推出
+
+[a]: https://opensource.com/users/cverna/users/paulbischoff/users/dcritch/users/cobiacomm/users/wgarry155/users/kadinroob/users/koreyhilpert
+[b]: https://github.com/lujun9972
+[1]: https://opensource.com/sites/default/files/styles/image-full-size/public/lead-images/terminal_command_linux_desktop_code.jpg?itok=p5sQ6ODE (Terminal command prompt on orange background)
+[2]: https://www.ansible.com/
+[3]: https://testinfra.readthedocs.io/en/latest/
+[4]: https://pytest.org/
+[5]: https://testinfra.readthedocs.io/en/latest/modules.html#modules
+[6]: https://docs.ansible.com/ansible/playbooks_checkmode.html
+[7]: https://www.nagios.org/
+[8]: https://en.wikipedia.org/wiki/Nagios#NRPE
+[9]: https://github.com/ansible/molecule
diff --git a/published/20190520 Getting Started With Docker.md b/published/20190520 Getting Started With Docker.md
new file mode 100644
index 0000000000..2349664ad9
--- /dev/null
+++ b/published/20190520 Getting Started With Docker.md
@@ -0,0 +1,471 @@
+[#]: collector: "lujun9972"
+[#]: translator: "zhang5788"
+[#]: reviewer: "wxy"
+[#]: publisher: "wxy"
+[#]: url: "https://linux.cn/article-10940-1.html"
+[#]: subject: "Getting Started With Docker"
+[#]: via: "https://www.ostechnix.com/getting-started-with-docker/"
+[#]: author: "sk https://www.ostechnix.com/author/sk/"
+
+Docker 入门指南
+======
+
+![Getting Started With Docker][1]
+
+在我们的上一个教程中,我们已经了解[如何在 Ubuntu 上安装 Docker][1],和如何在 [CentOS 上安装 Docker][2]。今天,我们将会了解 Docker 的一些基础用法。该教程包含了如何创建一个新的 Docker 容器,如何运行该容器,如何从现有的 Docker 容器中创建自己的 Docker 镜像等 Docker 的一些基础知识、操作。所有步骤均在 Ubuntu 18.04 LTS server 版本下测试通过。
+
+### 入门指南
+
+在开始指南之前,不要混淆 Docker 镜像和 Docker 容器这两个概念。在之前的教程中,我就解释过,Docker 镜像是决定 Docker 容器行为的一个文件,Docker 容器则是 Docker 镜像的运行态或停止态。(LCTT 译注:在 macOS 下使用 Docker 终端时,不需要加 `sudo`)
+
+#### 1、搜索 Docker 镜像
+
+我们可以从 Docker 仓库中获取镜像,例如 [Docker hub][3],或者自己创建镜像。这里解释一下,Docker hub 是一个云服务器,用来提供给 Docker 的用户们创建、测试,和保存他们的镜像。
+
+Docker hub 拥有成千上万个 Docker 镜像文件。你可以通过 `docker search`命令在这里搜索任何你想要的镜像。
+
+例如,搜索一个基于 Ubuntu 的镜像文件,只需要运行:
+
+```shell
+$ sudo docker search ubuntu
+```
+
+示例输出:
+
+![][5]
+
+搜索基于 CentOS 的镜像,运行:
+
+```shell
+$ sudo docker search centos
+```
+
+搜索 AWS 的镜像,运行:
+
+```shell
+$ sudo docker search aws
+```
+
+搜索 WordPress 的镜像:
+
+```shell
+$ sudo docker search wordpress
+```
+
+Docker hub 拥有几乎所有种类的镜像,包含操作系统、程序和其他任意的类型,这些你都能在 Docker hub 上找到已经构建完的镜像。如果你在搜索时,无法找到你想要的镜像文件,你也可以自己构建一个,将其发布出去,或者仅供你自己使用。
+
+#### 2、下载 Docker 镜像
+
+下载 Ubuntu 的镜像,你需要在终端运行以下命令:
+
+```shell
+$ sudo docker pull ubuntu
+```
+
+这条命令将会从 Docker hub 下载最近一个版本的 Ubuntu 镜像文件。
+
+示例输出:
+
+```
+Using default tag: latest
+latest: Pulling from library/ubuntu
+6abc03819f3e: Pull complete
+05731e63f211: Pull complete
+0bd67c50d6be: Pull complete
+Digest: sha256:f08638ec7ddc90065187e7eabdfac3c96e5ff0f6b2f1762cf31a4f49b53000a5
+Status: Downloaded newer image for ubuntu:latest
+```
+
+![下载 Docker 镜像][6]
+
+你也可以下载指定版本的 Ubuntu 镜像。运行以下命令:
+
+```shell
+$ docker pull ubuntu:18.04
+```
+
+Docker 允许在任意的宿主机操作系统下,下载任意的镜像文件,并运行。
+
+例如,下载 CentOS 镜像:
+
+```shell
+$ sudo docker pull centos
+```
+
+所有下载的镜像文件,都被保存在 `/var/lib/docker` 文件夹下。(LCTT 译注:不同操作系统存放的文件夹并不是一致的,具体存放位置请在官方查询)
+
+查看已经下载的镜像列表,可以使用以下命令:
+
+```shell
+$ sudo docker images
+```
+
+示例输出:
+
+```shell
+REPOSITORY TAG IMAGE ID CREATED SIZE
+ubuntu latest 7698f282e524 14 hours ago 69.9MB
+centos latest 9f38484d220f 2 months ago 202MB
+hello-world latest fce289e99eb9 4 months ago 1.84kB
+```
+
+正如你看到的那样,我已经下载了三个镜像文件:`ubuntu`、`centos` 和 `hello-world`。
+
+现在,让我们继续,来看一下如何运行我们刚刚下载的镜像。
+
+#### 3、运行 Docker 镜像
+
+运行一个容器有两种方法。我们可以使用标签或者是镜像 ID。标签指的是特定的镜像快照。镜像 ID 是指镜像的唯一标识。
+
+正如上面结果中显示,`latest` 是所有镜像的一个标签。`7698f282e524` 是 Ubuntu Docker 镜像的镜像 ID,`9f38484d220f`是 CentOS 镜像的镜像 ID,`fce289e99eb9` 是 hello_world 镜像的 镜像 ID。
+
+下载完 Docker 镜像之后,你可以通过下面的命令来使用其标签来启动:
+
+```shell
+$ sudo docker run -t -i ubuntu:latest /bin/bash
+```
+
+在这条语句中:
+
+* `-t`:在该容器中启动一个新的终端
+* `-i`:通过容器中的标准输入流建立交互式连接
+* `ubuntu:latest`:带有标签 `latest` 的 Ubuntu 容器
+* `/bin/bash`:在新的容器中启动 BASH Shell
+
+或者,你可以通过镜像 ID 来启动新的容器:
+
+```shell
+$ sudo docker run -t -i 7698f282e524 /bin/bash
+```
+
+在这条语句里:
+
+* `7698f282e524` — 镜像 ID
+
+在启动容器之后,将会自动进入容器的 shell 中(注意看命令行的提示符)。
+
+![][7]
+
+*Docker 容器的 Shell*
+
+如果想要退回到宿主机的终端(在这个例子中,对我来说,就是退回到 18.04 LTS),并且不中断该容器的执行,你可以按下 `CTRL+P`,再按下 `CTRL+Q`。现在,你就安全的返回到了你的宿主机系统中。需要注意的是,Docker 容器仍然在后台运行,我们并没有中断它。
+
+可以通过下面的命令来查看正在运行的容器:
+
+```shell
+$ sudo docker ps
+```
+
+示例输出:
+
+```shell
+CONTAINER ID IMAGE COMMAND CREATED STATUS PORTS NAMES
+32fc32ad0d54 ubuntu:latest "/bin/bash" 7 minutes ago Up 7 minutes modest_jones
+```
+
+![][8]
+
+*列出正在运行的容器*
+
+可以看到:
+
+* `32fc32ad0d54` – 容器 ID
+* `ubuntu:latest` – Docker 镜像
+
+需要注意的是,容器 ID 和 Docker 的镜像 ID是不同的。
+
+可以通过以下命令查看所有正在运行和停止运行的容器:
+
+```shell
+$ sudo docker ps -a
+```
+
+在宿主机中断容器的执行:
+
+```shell
+$ sudo docker stop
+```
+
+例如:
+
+```shell
+$ sudo docker stop 32fc32ad0d54
+```
+
+如果想要进入正在运行的容器中,你只需要运行:
+
+```shell
+$ sudo docker attach 32fc32ad0d54
+```
+
+正如你看到的,`32fc32ad0d54` 是一个容器的 ID。当你在容器中想要退出时,只需要在容器内的终端中输入命令:
+
+```shell
+# exit
+```
+
+你可以使用这个命令查看后台正在运行的容器:
+
+```shell
+$ sudo docker ps
+```
+
+#### 4、构建自己的 Docker 镜像
+
+Docker 不仅仅可以下载运行在线的容器,你也可以创建你的自己的容器。
+
+想要创建自己的 Docker 镜像,你需要先运行一个你已经下载完的容器:
+
+```shell
+$ sudo docker run -t -i ubuntu:latest /bin/bash
+```
+
+现在,你运行了一个容器,并且进入了该容器。然后,在该容器安装任意一个软件或做任何你想做的事情。
+
+例如,我们在容器中安装一个 Apache web 服务器。
+
+当你完成所有的操作,安装完所有的软件之后,你可以执行以下的命令来构建你自己的 Docker 镜像:
+
+```shell
+# apt update
+# apt install apache2
+```
+
+同样的,在容器中安装和测试你想要安装的所有软件。
+
+当你安装完毕之后,返回的宿主机的终端。记住,不要关闭容器。想要返回到宿主机而不中断容器。请按下`CTRL+P`,再按下 `CTRL+Q`。
+
+从你的宿主机的终端中,运行以下命令如寻找容器的 ID:
+
+```shell
+$ sudo docker ps
+```
+
+最后,从一个正在运行的容器中创建 Docker 镜像:
+
+```shell
+$ sudo docker commit 3d24b3de0bfc ostechnix/ubuntu_apache
+```
+
+示例输出:
+
+```shell
+sha256:ce5aa74a48f1e01ea312165887d30691a59caa0d99a2a4aa5116ae124f02f962
+```
+
+在这里:
+
+* `3d24b3de0bfc` — 指 Ubuntu 容器的 ID。
+* `ostechnix` — 我们创建的容器的用户名称
+* `ubuntu_apache` — 我们创建的镜像
+
+让我们检查一下我们新创建的 Docker 镜像:
+
+```shell
+$ sudo docker images
+```
+
+示例输出:
+
+```shell
+REPOSITORY TAG IMAGE ID CREATED SIZE
+ostechnix/ubuntu_apache latest ce5aa74a48f1 About a minute ago 191MB
+ubuntu latest 7698f282e524 15 hours ago 69.9MB
+centos latest 9f38484d220f 2 months ago 202MB
+hello-world latest fce289e99eb9 4 months ago 1.84kB
+```
+
+![][9]
+
+*列出所有的 Docker 镜像*
+
+正如你看到的,这个新的镜像就是我们刚刚在本地系统上从运行的容器上创建的。
+
+现在,你可以从这个镜像创建一个新的容器。
+
+```shell
+$ sudo docker run -t -i ostechnix/ubuntu_apache /bin/bash
+```
+
+#### 5、删除容器
+
+如果你在 Docker 上的工作已经全部完成,你就可以删除那些你不需要的容器。
+
+想要删除一个容器,首先,你需要停止该容器。
+
+我们先来看一下正在运行的容器有哪些
+
+```shell
+$ sudo docker ps
+```
+
+示例输出:
+
+```shell
+CONTAINER ID IMAGE COMMAND CREATED STATUS PORTS NAMES
+3d24b3de0bfc ubuntu:latest "/bin/bash" 28 minutes ago Up 28 minutes goofy_easley
+```
+
+使用容器 ID 来停止该容器:
+
+```shell
+$ sudo docker stop 3d24b3de0bfc
+```
+
+现在,就可以删除该容器了。
+
+```shell
+$ sudo docker rm 3d24b3de0bfc
+```
+
+你就可以按照这样的方法来删除那些你不需要的容器了。
+
+当需要删除的容器数量很多时,一个一个删除也是很麻烦的,我们可以直接删除所有的已经停止的容器。只需要运行:
+
+```shell
+$ sudo docker container prune
+```
+
+按下 `Y`,来确认你的操作:
+
+```sehll
+WARNING! This will remove all stopped containers.
+Are you sure you want to continue? [y/N] y
+Deleted Containers:
+32fc32ad0d5445f2dfd0d46121251c7b5a2aea06bb22588fb2594ddbe46e6564
+5ec614e0302061469ece212f0dba303c8fe99889389749e6220fe891997f38d0
+
+Total reclaimed space: 5B
+```
+
+这个命令仅支持最新的 Docker。(LCTT 译注:仅支持 1.25 及以上版本的 Docker)
+
+#### 6、删除 Docker 镜像
+
+当你删除了不要的 Docker 容器后,你也可以删除你不需要的 Docker 镜像。
+
+列出已经下载的镜像:
+
+```shell
+$ sudo docker images
+```
+
+示例输出:
+
+```shell
+REPOSITORY TAG IMAGE ID CREATED SIZE
+ostechnix/ubuntu_apache latest ce5aa74a48f1 5 minutes ago 191MB
+ubuntu latest 7698f282e524 15 hours ago 69.9MB
+centos latest 9f38484d220f 2 months ago 202MB
+hello-world latest fce289e99eb9 4 months ago 1.84kB
+```
+
+由上面的命令可以知道,在本地的系统中存在三个镜像。
+
+使用镜像 ID 来删除镜像。
+
+```shell
+$ sudo docekr rmi ce5aa74a48f1
+```
+
+示例输出:
+
+```shell
+Untagged: ostechnix/ubuntu_apache:latest
+Deleted: sha256:ce5aa74a48f1e01ea312165887d30691a59caa0d99a2a4aa5116ae124f02f962
+Deleted: sha256:d21c926f11a64b811dc75391bbe0191b50b8fe142419f7616b3cee70229f14cd
+```
+
+#### 解决问题
+
+Docker 禁止我们删除一个还在被容器使用的镜像。
+
+例如,当我试图删除 Docker 镜像 `b72889fa879c` 时,我只能获得一个错误提示:
+
+```shell
+Error response from daemon: conflict: unable to delete b72889fa879c (must be forced) - image is being used by stopped container dde4dd285377
+```
+
+这是因为这个 Docker 镜像正在被一个容器使用。
+
+所以,我们来检查一个正在运行的容器:
+
+```shell
+$ sudo docker ps
+```
+
+示例输出:
+
+![][10]
+
+注意,现在并没有正在运行的容器!!!
+
+查看一下所有的容器(包含所有的正在运行和已经停止的容器):
+
+```shell
+$ sudo docker pa -a
+```
+
+示例输出:
+
+![][11]
+
+可以看到,仍然有一些已经停止的容器在使用这些镜像。
+
+让我们把这些容器删除:
+
+```shell
+$ sudo docker rm 12e892156219
+```
+
+我们仍然使用容器 ID 来删除这些容器。
+
+当我们删除了所有使用该镜像的容器之后,我们就可以删除 Docker 的镜像了。
+
+例如:
+
+```shell
+$ sudo docekr rmi b72889fa879c
+```
+
+我们再来检查一下本机存在的镜像:
+
+```shell
+$ sudo docker images
+```
+
+想要知道更多的细节,请参阅本指南末尾给出的官方资源的链接或者在评论区进行留言。
+
+这就是全部的教程了,希望你可以了解 Docker 的一些基础用法。
+
+更多的教程马上就会到来,敬请关注。
+
+---
+
+via: https://www.ostechnix.com/getting-started-with-docker/
+
+作者:[sk][a]
+选题:[lujun9972][b]
+译者:[zhang5788](https://github.com/zhang5788)
+校对:[wxy](https://github.com/wxy)
+
+本文由 [LCTT](https://github.com/LCTT/TranslateProject) 原创编译,[Linux中国](https://linux.cn/) 荣誉推出
+
+[a]: https://www.ostechnix.com/author/sk/
+[b]: https://github.com/lujun9972
+[1]: https://www.ostechnix.com/wp-content/uploads/2016/04/docker-basics-720x340.png
+[2]: http://www.ostechnix.com/install-docker-ubuntu/
+[3]: https://www.ostechnix.com/install-docker-centos/
+[4]: https://hub.docker.com/
+[5]: http://www.ostechnix.com/wp-content/uploads/2016/04/Search-Docker-images.png
+[6]: http://www.ostechnix.com/wp-content/uploads/2016/04/Download-docker-images.png
+[7]: http://www.ostechnix.com/wp-content/uploads/2016/04/Docker-containers-shell.png
+[8]: http://www.ostechnix.com/wp-content/uploads/2016/04/List-running-containers.png
+[9]: http://www.ostechnix.com/wp-content/uploads/2016/04/List-docker-images.png
+[10]: http://www.ostechnix.com/wp-content/uploads/2016/04/sk@sk-_005-1-1.jpg
+[11]: http://www.ostechnix.com/wp-content/uploads/2016/04/sk@sk-_006-1.jpg
+[12]: https://ostechnix.tradepub.com/free/w_java39/prgm.cgi?a=1
+[13]: https://ostechnix.tradepub.com/free/w_pacb32/prgm.cgi?a=1
+[14]: https://ostechnix.tradepub.com/free/w_pacb31/prgm.cgi?a=1
+[15]: https://ostechnix.tradepub.com/free/w_pacb29/prgm.cgi?a=1
+[16]: https://ostechnix.tradepub.com/free/w_pacb28/prgm.cgi?a=1
diff --git a/published/20190520 When IoT systems fail- The risk of having bad IoT data.md b/published/20190520 When IoT systems fail- The risk of having bad IoT data.md
new file mode 100644
index 0000000000..6d8ee2c96a
--- /dev/null
+++ b/published/20190520 When IoT systems fail- The risk of having bad IoT data.md
@@ -0,0 +1,75 @@
+[#]: collector: (lujun9972)
+[#]: translator: (chen-ni)
+[#]: reviewer: (wxy)
+[#]: publisher: (wxy)
+[#]: url: (https://linux.cn/article-10961-1.html)
+[#]: subject: (When IoT systems fail: The risk of having bad IoT data)
+[#]: via: (https://www.networkworld.com/article/3396230/when-iot-systems-fail-the-risk-of-having-bad-iot-data.html)
+[#]: author: (Fredric Paul https://www.networkworld.com/author/Fredric-Paul/)
+
+当物联网系统出现故障:使用低质量物联网数据的风险
+======
+
+> 伴随着物联网设备使用量的增长,这些设备产生的数据可以让消费者节约巨大的开支,也给商家带来新的机遇。但是当故障不可避免地出现的时候,会发生什么呢?
+
+![Oonal / Getty Images][1]
+
+不管你看的是什么统计数字,很明显物联网正在走进个人和私人生活的方方面面。这种增长虽然有不少好处,但是也带来了新的风险。一个很重要的问题是,出现问题的时候谁来负责呢?
+
+也许最大的问题出在基于物联网数据进行的个性化营销以及定价策略上。[保险公司长期以来致力于寻找利用物联网数据的最佳方式][2],我去年写过家庭财产保险公司是如何开始利用物联网传感器减少水灾带来的损失的。一些公司正在研究保险公司竞购消费者的可能性:这种业务基于智能家居数据所揭示的风险的高低。
+
+但是最大的进步出现在汽车保险领域。许多汽车保险公司已经可以让客户在车辆上安装追踪设备,如果数据证明他们的驾驶习惯良好就可以获取保险折扣。
+
+- 延伸阅读:[保险公司终于有了一个利用智能家居物联网的好办法][3]
+
+### UBI 车险的崛起
+
+UBI(基于使用的保险)车险是一种“按需付费”的业务,可以通过追踪速度、位置,以及其他因素来评估风险并计算车险保费。到 2020 年,预计有 [5000 万美国司机][4]会加入到 UBI 车险的项目中。
+
+不出所料,保险公司对 UBI 车险青睐有加,因为 UBI 车险可以帮助他们更加精确地计算风险。事实上,[AIG 爱尔兰已经在尝试让国家向 25 岁以下的司机强制推行 UBI 车险][5]。并且,被认定为驾驶习惯良好的司机自然也很乐意节省一笔费用。当然也有反对的声音了,大多数是来自于隐私权倡导者,以及会因此支付更多费用的群体。
+
+### 出了故障会发生什么?
+
+但是还有一个更加令人担忧的潜在问题:当物联网设备提供的数据有错误,或者在传输过程中出了问题会发生什么?因为尽管有自动化程序、错误检查等等,还是不可避免地会偶尔发生一些故障。
+
+不幸的是,这并不是一个理论上某天会给细心的司机不小心多扣几块钱保费的问题。这已经是一个会带来严重后果的现实问题。就像[保险行业仍然没有想清楚谁应该“拥有”面向客户的物联网设备产生的数据][6]一样,我们也不清楚谁将对这些数据所带来的问题负责。
+
+计算机“故障”据说曾导致赫兹的出租车辆被误报为被盗(虽然在这个例子中这并不是一个严格意义上的物联网问题),并且导致无辜的租车人被逮捕并扣留。结果呢?刑事指控,多年的诉讼官司,以及舆论的指责。非常强烈的舆论指责。
+
+我们非常容易想象一些类似的情况,比如说一个物联网传感器出了故障,然后报告说某辆车超速了,然而事实上并没有超速。想想为这件事打官司的麻烦吧,或者想想和你的保险公司如何争执不下。
+
+(当然,这个问题还有另外一面:消费者可能会想办法篡改他们的物联网设备上的数据,以获得更低的费率或者转移事故责任。我们同样也没有可行的办法来应对*这个问题*。)
+
+### 政府监管是否有必要
+
+考虑到这些问题的潜在影响,以及所涉及公司对处理这些问题的无动于衷,我们似乎有理由猜想政府干预的必要性。
+
+这可能是美国众议员 Bob Latta(俄亥俄州,共和党)[重新引入 SMART IOT(物联网现代应用、研究及趋势的现状)法案][7]背后的一个动机。这项由 Latta 和美国众议员 Peter Welch(佛蒙特州,民主党)领导的两党合作物联网工作组提出的[法案][8],于去年秋天通过美国众议院,但被美国参议院驳回了。美国商务部需要研究物联网行业的状况,并在两年后向美国众议院能源与商业部和美国参议院商务委员会报告。
+
+Latta 在一份声明中表示,“由于预计会有数万亿美元的经济影响,我们需要考虑物联网所带来的的政策,机遇和挑战。SMART IoT 法案会让人们更容易理解美国政府在物联网政策上的做法、可以改进的地方,以及美国联邦政策如何影响尖端技术的研究和发明。”
+
+这项研究受到了欢迎,但该法案甚至可能不会被通过。即便通过了,物联网在两年的等待时间里也可能会翻天覆地,让美国政府还是无法跟上。
+
+--------------------------------------------------------------------------------
+
+via: https://www.networkworld.com/article/3396230/when-iot-systems-fail-the-risk-of-having-bad-iot-data.html
+
+作者:[Fredric Paul][a]
+选题:[lujun9972][b]
+译者:[chen-ni](https://github.com/chen-ni)
+校对:[wxy](https://github.com/wxy)
+
+本文由 [LCTT](https://github.com/LCTT/TranslateProject) 原创编译,[Linux中国](https://linux.cn/) 荣誉推出
+
+[a]: https://www.networkworld.com/author/Fredric-Paul/
+[b]: https://github.com/lujun9972
+[1]: https://images.idgesg.net/images/article/2018/08/cloud_connected_smart_cars_by_oonal_gettyimages-692819426_1200x800-100767788-large.jpg
+[2]: https://www.networkworld.com/article/3264655/most-insurance-carriers-not-ready-to-use-iot-data.html
+[3]: https://www.networkworld.com/article/3296706/finally-a-smart-way-for-insurers-to-leverage-iot-in-smart-homes.html
+[4]: https://www.businessinsider.com/iot-is-changing-the-auto-insurance-industry-2015-8
+[5]: https://www.iotforall.com/iot-data-is-disrupting-the-insurance-industry/
+[6]: https://www.sas.com/en_us/insights/articles/big-data/5-challenges-for-iot-in-insurance-industry.html
+[7]: https://www.multichannel.com/news/latta-re-ups-smart-iot-act
+[8]: https://latta.house.gov/uploadedfiles/smart_iot_116th.pdf
+[9]: https://www.facebook.com/NetworkWorld/
+[10]: https://www.linkedin.com/company/network-world
diff --git a/published/20190520 Zettlr - Markdown Editor for Writers and Researchers.md b/published/20190520 Zettlr - Markdown Editor for Writers and Researchers.md
new file mode 100644
index 0000000000..487c0f0fe3
--- /dev/null
+++ b/published/20190520 Zettlr - Markdown Editor for Writers and Researchers.md
@@ -0,0 +1,109 @@
+[#]: collector: (lujun9972)
+[#]: translator: (geekpi)
+[#]: reviewer: (wxy)
+[#]: publisher: (wxy)
+[#]: url: (https://linux.cn/article-10922-1.html)
+[#]: subject: (Zettlr – Markdown Editor for Writers and Researchers)
+[#]: via: (https://itsfoss.com/zettlr-markdown-editor/)
+[#]: author: (John Paul https://itsfoss.com/author/john/)
+
+Zettlr:适合写作者和研究人员的 Markdown 编辑器
+======
+
+有很多[适用于 Linux 的 Markdown 编辑器][1],并且还在继续增加。问题是,像 [Boostnote][2] 一样,大多数是为编码人员设计的,可能不会受到非技术人员的欢迎。让我们看一个想要替代 Word 和昂贵的文字处理器,适用于非技术人员的 Markdown 编辑器。我们来看看 Zettlr 吧。
+
+### Zettlr Markdown 编辑器
+
+![Zettlr Light Mode][3]
+
+我可能在网站上提到过一两次,我更喜欢用 [Markdown][4] 写下我的所有文档。它易于学习,不会让你受困于专有文档格式。我还在我的[适合作者的开源工具列表][5]中提到了 Markdown 编辑器。
+
+我用过许多 Markdown 编辑器,但是我一直有兴趣尝试新的。最近,我遇到了 Zettlr,一个开源 Markdown 编辑器。
+
+[Zettlr][6] 是一位名叫 [Hendrik Erz][7] 的德国社会学家/政治理论家创建的。Hendrik 创建了 Zettlr,因为他对目前的文字处理器感到不满意。他想要可以让他“专注于写作和阅读”的编辑器。
+
+在发现 Markdown 之后,他在不同的操作系统上尝试了几个 Markdown 编辑器。但它们都没有他想要的东西。[根据 Hendrik 的说法][8],“但我不得不意识到没有为高效组织大量文本而写的编辑器。大多数编辑都是由编码人员编写的,因此可以满足工程师和数学家的需求。没有为我这样的社会科学、历史或政治学的学生的编辑器。“
+
+所以他决定创造自己的。2017 年 11 月,他开始编写 Zettlr。
+
+![Zettlr About][9]
+
+#### Zettlr 功能
+
+Zettlr 有许多简洁的功能,包括:
+
+ * 从 [Zotero 数据库][10]导入源并在文档中引用它们
+ * 使用可选的行屏蔽,让你无打扰地专注于写作
+ * 支持代码高亮
+ * 使用标签对信息进行排序
+ * 能够为该任务设定写作目标
+ * 查看一段时间的写作统计
+ * 番茄钟计时器
+ * 浅色/深色主题
+ * 使用 [reveal.js][11] 创建演示文稿
+ * 快速预览文档
+ * 可以在一个项目文件夹中搜索 Markdown 文档,并用热图展示文字搜索密度。
+ * 将文件导出为 HTML、PDF、ODT、DOC、reStructuredText、LaTex、TXT、Emacs ORG、[TextBundle][12] 和 Textpack
+ * 将自定义 CSS 添加到你的文档
+
+当我写这篇文章时,一个对话框弹出来告诉我最近发布了 [1.3.0 beta][14]。此测试版将包括几个新的主题,以及一大堆修复,新功能和改进。
+
+![Zettlr Night Mode][15]
+
+#### 安装 Zettlr
+
+目前,唯一可安装 Zettlr 的 Linux 存储库是 [AUR][16]。如果你的 Linux 发行版不是基于 Arch 的,你可以从网站上下载 macOS、Windows、Debian 和 Fedora 的[安装程序][17]。
+
+#### 对 Zettlr 的最后一点想法
+
+注意:为了测试 Zettlr,我用它来写这篇文章。
+
+Zettlr 有许多我希望我之前选择的编辑器 (ghostwriter) 有的简洁的功能,例如为文档设置字数目标。我也喜欢在不打开文档的情况下预览文档的功能。
+
+![Zettlr Settings][18]
+
+我也遇到了几个问题,但这些更多的是因为 Zettlr 与 ghostwriter 的工作方式略有不同。例如,当我尝试从网站复制引用或名称时,它会将内嵌样式粘贴到 Zettlr 中。幸运的是,它有一个“不带样式粘贴”的选项。有几次我在打字时有轻微的延迟。但那可能是因为它是一个 Electron 程序。
+
+总的来说,我认为 Zettlr 是第一次使用 Markdown 用户的好选择。它有许多 Markdown 编辑器已有的功能,并为那些只使用过文字处理器的用户增加了一些功能。
+
+正如 Hendrik 在 [Zettlr 网站][8]中所说的那样,“让自己摆脱文字处理器的束缚,看看你的写作过程如何通过身边的技术得到改善!”
+
+如果你觉得 Zettlr 有用,请考虑支持 [Hendrik][19]。正如他在网站上所说,“它是免费的,因为我不相信激烈竞争、早逝的创业文化。我只是想帮忙。”
+
+你有没有用过 Zettlr?你最喜欢的 Markdown 编辑器是什么?请在下面的评论中告诉我们。
+
+如果你觉得这篇文章有趣,请在社交媒体,Hacker News 或 [Reddit][21] 上分享它。
+
+--------------------------------------------------------------------------------
+
+via: https://itsfoss.com/zettlr-markdown-editor/
+
+作者:[John Paul][a]
+选题:[lujun9972][b]
+译者:[geekpi](https://github.com/geekpi)
+校对:[wxy](https://github.com/wxy)
+
+本文由 [LCTT](https://github.com/LCTT/TranslateProject) 原创编译,[Linux中国](https://linux.cn/) 荣誉推出
+
+[a]: https://itsfoss.com/author/john/
+[b]: https://github.com/lujun9972
+[1]: https://itsfoss.com/best-markdown-editors-linux/
+[2]: https://itsfoss.com/boostnote-linux-review/
+[3]: https://i1.wp.com/itsfoss.com/wp-content/uploads/2019/05/Zettlr-light-mode.png?fit=800%2C462&ssl=1
+[4]: https://daringfireball.net/projects/markdown/
+[5]: https://itsfoss.com/open-source-tools-writers/
+[6]: https://www.zettlr.com/
+[7]: https://github.com/nathanlesage
+[8]: https://www.zettlr.com/about
+[9]: https://i1.wp.com/itsfoss.com/wp-content/uploads/2019/05/zettlr-about.png?fit=800%2C528&ssl=1
+[10]: https://www.zotero.org/
+[11]: https://revealjs.com/#/
+[12]: http://textbundle.org/
+[13]: https://itsfoss.com/great-little-book-shelf-review/
+[14]: https://github.com/Zettlr/Zettlr/releases/tag/v1.3.0-beta
+[15]: https://i0.wp.com/itsfoss.com/wp-content/uploads/2019/05/Zettlr-night-mode.png?fit=800%2C469&ssl=1
+[16]: https://aur.archlinux.org/packages/zettlr-bin/
+[17]: https://www.zettlr.com/download
+[18]: https://i1.wp.com/itsfoss.com/wp-content/uploads/2019/05/zettlr-settings.png?fit=800%2C353&ssl=1
+[19]: https://www.zettlr.com/supporters
+[21]: http://reddit.com/r/linuxusersgroup
diff --git a/published/20190522 French IT giant Atos enters the edge-computing business.md b/published/20190522 French IT giant Atos enters the edge-computing business.md
new file mode 100644
index 0000000000..1be6353555
--- /dev/null
+++ b/published/20190522 French IT giant Atos enters the edge-computing business.md
@@ -0,0 +1,62 @@
+[#]: collector: (lujun9972)
+[#]: translator: (chen-ni)
+[#]: reviewer: (wxy)
+[#]: publisher: (wxy)
+[#]: url: (https://linux.cn/article-10934-1.html)
+[#]: subject: (French IT giant Atos enters the edge-computing business)
+[#]: via: (https://www.networkworld.com/article/3397139/atos-is-the-latest-to-enter-the-edge-computing-business.html)
+[#]: author: (Andy Patrizio https://www.networkworld.com/author/Andy-Patrizio/)
+
+法国 IT 巨头 Atos 进军边缘计算
+======
+
+> Atos 另辟蹊径,通过一种只有行李箱大小的设备 BullSequana Edge 进军边缘计算。
+
+![iStock][1]
+
+法国 IT 巨头 Atos 是最近才开展边缘计算业务的,他们的产品是一个叫做 BullSequana Edge 的小型设备。和竞争对手们的集装箱大小的设备不同(比如说 Vapor IO 和 Schneider Electronics 的产品),Atos 的边缘设备完全可以被放进衣柜里。
+
+Atos 表示,他们的这个设备使用人工智能应用提供快速响应,适合需要快速响应的领域比如生产 4.0、自动驾驶汽车、健康管理,以及零售业和机场的安保系统。在这些领域,数据需要在边缘进行实时处理和分析。
+
+[延伸阅读:[什么是边缘计算?][2] 以及 [边缘网络和物联网如何重新定义数据中心][3]]
+
+BullSequana Edge 可以作为独立的基础设施单独采购,也可以和 Atos 的边缘软件捆绑采购,并且这个软件还是非常出色的。Atos 表示 BullSequana Edge 主要支持三种使用场景:
+
+ * AI(人工智能):Atos 的边缘计算机视觉软件为监控摄像头提供先进的特征抽取和分析技术,包括人像、人脸、行为等特征。这些分析可以支持系统做出自动化响应。
+ * 大数据:Atos 边缘数据分析系统通过预测性和规范性的解决方案,帮助机构优化商业模型。它使用数据湖的功能,确保数据的可信度和可用性。
+ * 容器:Atos 边缘数据容器(EDC)是一种一体化容器解决方案。它可以作为一个去中心化的 IT 系统在边缘运行,并且可以在没有数据中心的环境下自动运行,而不需要现场操作。
+
+由于体积小,BullSequana Edge 并不具备很强的处理能力。它装载一个 16 核的 Intel Xeon 中央处理器,可以装备最多两枚英伟达 Tesla T4 图形处理器或者是 FPGA(现场可编程门阵列)。Atos 表示,这就足够让复杂的 AI 模型在边缘进行低延迟的运行了。
+
+考虑到数据的敏感性,BullSequana Edge 同时装备了一个入侵感应器,用来在遭遇物理入侵的时候禁用机器。
+
+虽然大多数边缘设备都被安放在信号塔附近,但是考虑到边缘系统可能被安放在任何地方,BullSequana Edge 还支持通过无线电、全球移动通信系统(GSM),或者 Wi-Fi 来进行通信。
+
+Atos 在美国也许不是一个家喻户晓的名字,但是在欧洲它可以和 IBM 相提并论,并且在过去的十年里已经收购了诸如 Bull SA、施乐 IT 外包以及西门子 IT 等 IT 巨头们。
+
+关于边缘网络的延伸阅读:
+
+ * [边缘网络和物联网如何重新定义数据中心][3]
+ * [边缘计算的最佳实践][4]
+ * [边缘计算如何提升物联网安全][5]
+
+--------------------------------------------------------------------------------
+
+via: https://www.networkworld.com/article/3397139/atos-is-the-latest-to-enter-the-edge-computing-business.html
+
+作者:[Andy Patrizio][a]
+选题:[lujun9972][b]
+译者:[chen-ni](https://github.com/chen-ni)
+校对:[wxy](https://github.com/wxy)
+
+本文由 [LCTT](https://github.com/LCTT/TranslateProject) 原创编译,[Linux中国](https://linux.cn/) 荣誉推出
+
+[a]: https://www.networkworld.com/author/Andy-Patrizio/
+[b]: https://github.com/lujun9972
+[1]: https://images.idgesg.net/images/article/2019/01/huawei-18501-edge-gartner-100786331-large.jpg
+[2]: https://www.networkworld.com/article/3224893/internet-of-things/what-is-edge-computing-and-how-it-s-changing-the-network.html
+[3]: https://www.networkworld.com/article/3291790/data-center/how-edge-networking-and-iot-will-reshape-data-centers.html
+[4]: https://www.networkworld.com/article/3331978/lan-wan/edge-computing-best-practices.html
+[5]: https://www.networkworld.com/article/3331905/internet-of-things/how-edge-computing-can-help-secure-the-iot.html
+[6]: https://www.facebook.com/NetworkWorld/
+[7]: https://www.linkedin.com/company/network-world
diff --git a/published/20190522 Securing telnet connections with stunnel.md b/published/20190522 Securing telnet connections with stunnel.md
new file mode 100644
index 0000000000..644d288c41
--- /dev/null
+++ b/published/20190522 Securing telnet connections with stunnel.md
@@ -0,0 +1,201 @@
+[#]: collector: (lujun9972)
+[#]: translator: (geekpi)
+[#]: reviewer: (wxy)
+[#]: publisher: (wxy)
+[#]: url: (https://linux.cn/article-10945-1.html)
+[#]: subject: (Securing telnet connections with stunnel)
+[#]: via: (https://fedoramagazine.org/securing-telnet-connections-with-stunnel/)
+[#]: author: (Curt Warfield https://fedoramagazine.org/author/rcurtiswarfield/)
+
+使用 stunnel 保护 telnet 连接
+======
+
+![][1]
+
+Telnet 是一种客户端-服务端协议,通过 TCP 的 23 端口连接到远程服务器。Telnet 并不加密数据,因此它被认为是不安全的,因为数据是以明文形式发送的,所以密码很容易被嗅探。但是,仍有老旧系统需要使用它。这就是用到 **stunnel** 的地方。
+
+stunnel 旨在为使用不安全连接协议的程序增加 SSL 加密。本文将以 telnet 为例介绍如何使用它。
+
+### 服务端安装
+
+[使用 sudo][2] 安装 stunnel 以及 telnet 的服务端和客户端:
+
+```
+sudo dnf -y install stunnel telnet-server telnet
+```
+
+添加防火墙规则,在提示时输入你的密码:
+
+```
+firewall-cmd --add-service=telnet --perm
+firewall-cmd --reload
+```
+
+接下来,生成 RSA 私钥和 SSL 证书:
+
+```
+openssl genrsa 2048 > stunnel.key
+openssl req -new -key stunnel.key -x509 -days 90 -out stunnel.crt
+```
+
+系统将一次提示你输入以下信息。当询问 `Common Name` 时,你必须输入正确的主机名或 IP 地址,但是你可以按回车键跳过其他所有内容。
+
+```
+You are about to be asked to enter information that will be
+incorporated into your certificate request.
+What you are about to enter is what is called a Distinguished Name or a DN.
+There are quite a few fields but you can leave some blank
+For some fields there will be a default value,
+If you enter '.', the field will be left blank.
+-----
+Country Name (2 letter code) [XX]:
+State or Province Name (full name) []:
+Locality Name (eg, city) [Default City]:
+Organization Name (eg, company) [Default Company Ltd]:
+Organizational Unit Name (eg, section) []:
+Common Name (eg, your name or your server's hostname) []:
+Email Address []
+```
+
+将 RSA 密钥和 SSL 证书合并到单个 `.pem` 文件中,并将其复制到 SSL 证书目录:
+
+```
+cat stunnel.crt stunnel.key > stunnel.pem
+sudo cp stunnel.pem /etc/pki/tls/certs/
+```
+
+现在可以定义服务和用于加密连接的端口了。选择尚未使用的端口。此例使用 450 端口进行隧道传输 telnet。编辑或创建 `/etc/stunnel/telnet.conf`:
+
+```
+cert = /etc/pki/tls/certs/stunnel.pem
+sslVersion = TLSv1
+chroot = /var/run/stunnel
+setuid = nobody
+setgid = nobody
+pid = /stunnel.pid
+socket = l:TCP_NODELAY=1
+socket = r:TCP_NODELAY=1
+[telnet]
+accept = 450
+connect = 23
+```
+
+`accept` 选项是服务器将监听传入 telnet 请求的接口。`connect` 选项是 telnet 服务器的内部监听接口。
+
+接下来,创建一个 systemd 单元文件的副本来覆盖原来的版本:
+
+```
+sudo cp /usr/lib/systemd/system/stunnel.service /etc/systemd/system
+```
+
+编辑 `/etc/systemd/system/stunnel.service` 来添加两行。这些行在启动时为服务创建 chroot 监狱。
+
+```
+[Unit]
+Description=TLS tunnel for network daemons
+After=syslog.target network.target
+
+[Service]
+ExecStart=/usr/bin/stunnel
+Type=forking
+PrivateTmp=true
+ExecStartPre=-/usr/bin/mkdir /var/run/stunnel
+ExecStartPre=/usr/bin/chown -R nobody:nobody /var/run/stunnel
+
+[Install]
+WantedBy=multi-user.target
+```
+
+接下来,配置 SELinux 以在你刚刚指定的新端口上监听 telnet:
+
+```
+sudo semanage port -a -t telnetd_port_t -p tcp 450
+```
+
+最后,添加新的防火墙规则:
+
+```
+firewall-cmd --add-port=450/tcp --perm
+firewall-cmd --reload
+```
+
+现在你可以启用并启动 telnet 和 stunnel。
+
+```
+systemctl enable telnet.socket stunnel@telnet.service --now
+```
+
+要注意 `systemctl` 命令是有顺序的。systemd 和 stunnel 包默认提供额外的[模板单元文件][3]。该模板允许你将 stunnel 的多个配置文件放到 `/etc/stunnel` 中,并使用文件名启动该服务。例如,如果你有一个 `foobar.conf` 文件,那么可以使用 `systemctl start stunnel@foobar.service` 启动该 stunnel 实例,而无需自己编写任何单元文件。
+
+如果需要,可以将此 stunnel 模板服务设置为在启动时启动:
+
+```
+systemctl enable stunnel@telnet.service
+```
+
+### 客户端安装
+
+本文的这部分假设你在客户端系统上以普通用户([拥有 sudo 权限][2])身份登录。安装 stunnel 和 telnet 客户端:
+
+```
+dnf -y install stunnel telnet
+```
+
+将 `stunnel.pem` 从远程服务器复制到客户端的 `/etc/pki/tls/certs` 目录。在此例中,远程 telnet 服务器的 IP 地址为 `192.168.1.143`。
+
+```
+sudo scp myuser@192.168.1.143:/etc/pki/tls/certs/stunnel.pem
+/etc/pki/tls/certs/
+```
+
+创建 `/etc/stunnel/telnet.conf`:
+
+```
+cert = /etc/pki/tls/certs/stunnel.pem
+client=yes
+[telnet]
+accept=450
+connect=192.168.1.143:450
+```
+
+`accept` 选项是用于 telnet 会话的端口。`connect` 选项是你远程服务器的 IP 地址以及监听的端口。
+
+接下来,启用并启动 stunnel:
+
+```
+systemctl enable stunnel@telnet.service --now
+```
+
+测试你的连接。由于有一条已建立的连接,你会 `telnet` 到 `localhost` 而不是远程 telnet 服务器的主机名或者 IP 地址。
+
+```
+[user@client ~]$ telnet localhost 450
+Trying ::1...
+telnet: connect to address ::1: Connection refused
+Trying 127.0.0.1...
+Connected to localhost.
+Escape character is '^]'.
+
+Kernel 5.0.9-301.fc30.x86_64 on an x86_64 (0)
+server login: myuser
+Password: XXXXXXX
+Last login: Sun May 5 14:28:22 from localhost
+[myuser@server ~]$
+```
+
+--------------------------------------------------------------------------------
+
+via: https://fedoramagazine.org/securing-telnet-connections-with-stunnel/
+
+作者:[Curt Warfield][a]
+选题:[lujun9972][b]
+译者:[geekpi](https://github.com/geekpi)
+校对:[wxy](https://github.com/wxy)
+
+本文由 [LCTT](https://github.com/LCTT/TranslateProject) 原创编译,[Linux中国](https://linux.cn/) 荣誉推出
+
+[a]: https://fedoramagazine.org/author/rcurtiswarfield/
+[b]: https://github.com/lujun9972
+[1]: https://fedoramagazine.org/wp-content/uploads/2019/05/stunnel-816x345.jpg
+[2]: https://fedoramagazine.org/howto-use-sudo/
+[3]: https://fedoramagazine.org/systemd-template-unit-files/
diff --git a/published/20190525 4 Ways to Run Linux Commands in Windows.md b/published/20190525 4 Ways to Run Linux Commands in Windows.md
new file mode 100644
index 0000000000..88944d79af
--- /dev/null
+++ b/published/20190525 4 Ways to Run Linux Commands in Windows.md
@@ -0,0 +1,119 @@
+[#]: collector: (lujun9972)
+[#]: translator: (geekpi)
+[#]: reviewer: (wxy)
+[#]: publisher: (wxy)
+[#]: url: (https://linux.cn/article-10935-1.html)
+[#]: subject: (4 Ways to Run Linux Commands in Windows)
+[#]: via: (https://itsfoss.com/run-linux-commands-in-windows/)
+[#]: author: (Abhishek Prakash https://itsfoss.com/author/abhishek/)
+
+在 Windows 中运行 Linux 命令的 4 种方法
+======
+
+> 想要使用 Linux 命令,但又不想离开 Windows ?以下是在 Windows 中运行 Linux bash 命令的几种方法。
+
+如果你正在课程中正在学习 shell 脚本,那么需要使用 Linux 命令来练习命令和脚本。
+
+你的学校实验室可能安装了 Linux,但是你自己没有安装了 [Linux 的笔记本电脑][1],而是像其他人一样的 Windows 计算机。你的作业需要运行 Linux 命令,你或许想知道如何在 Windows 上运行 Bash 命令和脚本。
+
+你可以[在双启动模式下同时安装 Windows 和 Linux][2]。此方法能让你在启动计算机时选择 Linux 或 Windows。但是,为了运行 Linux 命令而使用单独分区的麻烦可能不适合所有人。
+
+你也可以[使用在线 Linux 终端][3],但你的作业无法保存。
+
+好消息是,有几种方法可以在 Windows 中运行 Linux 命令,就像其他常规应用一样。不是很酷吗?
+
+### 在 Windows 中使用 Linux 命令
+
+
+
+作为一个热心的 Linux 用户和推广者,我希望看到越来越多的人使用“真正的” Linux,但我知道有时候,这不是优先考虑的问题。如果你只是想练习 Linux 来通过考试,可以使用这些方法之一在 Windows 上运行 Bash 命令。
+
+#### 1、在 Windows 10 上使用 Linux Bash Shell
+
+你是否知道可以在 Windows 10 中运行 Linux 发行版? [Windows 的 Linux 子系统 (WSL)][5] 能让你在 Windows 中运行 Linux。即将推出的 WSL 版本将在 Windows 内部使用真正 Linux 内核。
+
+此 WSL 也称为 Bash on Windows,它作为一个常规的 Windows 应用运行,并提供了一个命令行模式的 Linux 发行版。不要害怕命令行模式,因为你的目的是运行 Linux 命令。这就是你所需要的。
+
+![Ubuntu Linux inside Windows][6]
+
+你可以在 Windows 应用商店中找到一些流行的 Linux 发行版,如 Ubuntu、Kali Linux、openSUSE 等。你只需像任何其他 Windows 应用一样下载和安装它。安装后,你可以运行所需的所有 Linux 命令。
+
+![Linux distributions in Windows 10 Store][8]
+
+请参考教程:[在 Windows 上安装 Linux bash shell][9]。
+
+#### 2、使用 Git Bash 在 Windows 上运行 Bash 命令
+
+你可能知道 [Git][10] 是什么。它是由 [Linux 创建者 Linus Torvalds][11] 开发的版本控制系统。
+
+[Git for Windows][12] 是一组工具,能让你在命令行和图形界面中使用 Git。Git for Windows 中包含的工具之一是 Git Bash。
+
+Git Bash 为 Git 命令行提供了仿真层。除了 Git 命令,Git Bash 还支持许多 Bash 程序,如 `ssh`、`scp`、`cat`、`find` 等。
+
+![Git Bash][13]
+
+换句话说,你可以使用 Git Bash 运行许多常见的 Linux/Bash 命令。
+
+你可以从其网站免费下载和安装 Git for Windows 工具来在 Windows 中安装 Git Bash。
+
+- [下载 Git for Windows][12]
+
+#### 3、使用 Cygwin 在 Windows 中使用 Linux 命令
+
+如果要在 Windows 中运行 Linux 命令,那么 Cygwin 是一个推荐的工具。Cygwin 创建于 1995 年,旨在提供一个原生运行于 Windows 中的 POSIX 兼容环境。Cygwin 是由 Red Hat 员工和许多其他志愿者维护的自由开源软件。
+
+二十年来,Windows 用户使用 Cygwin 来运行和练习 Linux/Bash 命令。十多年前,我甚至用 Cygwin 来学习 Linux 命令。
+
+![Cygwin][14]
+
+你可以从下面的官方网站下载 Cygwin。我还建议你参考这个 [Cygwin 备忘录][15]来开始使用。
+
+- [下载 Cygwin][16]
+
+#### 4、在虚拟机中使用 Linux
+
+另一种方法是使用虚拟化软件并在其中安装 Linux。这样,你可以在 Windows 中安装 Linux 发行版(带有图形界面)并像常规 Windows 应用一样运行它。
+
+这种方法要求你的系统有大的内存,至少 4GB ,但如果你有超过 8GB 的内存那么更好。这里的好处是你可以真实地使用桌面 Linux。如果你喜欢这个界面,那么你可能会在以后决定[切换到 Linux][17]。
+
+![Ubuntu Running in Virtual Machine Inside Windows][18]
+
+有两种流行的工具可在 Windows 上创建虚拟机,它们是 Oracle VirtualBox 和 VMware Workstation Player。你可以使用两者中的任何一个。就个人而言,我更喜欢 VirtualBox。
+
+你可以按照[本教程学习如何在 VirtualBox 中安装 Linux][20]。
+
+### 总结
+
+运行 Linux 命令的最佳方法是使用 Linux。当选择不安装 Linux 时,这些工具能让你在 Windows 上运行 Linux 命令。都试试看,看哪种适合你。
+
+--------------------------------------------------------------------------------
+
+via: https://itsfoss.com/run-linux-commands-in-windows/
+
+作者:[Abhishek Prakash][a]
+选题:[lujun9972][b]
+译者:[geekpi](https://github.com/geekpi)
+校对:[wxy](https://github.com/wxy)
+
+本文由 [LCTT](https://github.com/LCTT/TranslateProject) 原创编译,[Linux中国](https://linux.cn/) 荣誉推出
+
+[a]: https://itsfoss.com/author/abhishek/
+[b]: https://github.com/lujun9972
+[1]: https://itsfoss.com/get-linux-laptops/
+[2]: https://itsfoss.com/guide-install-linux-mint-16-dual-boot-windows/
+[3]: https://itsfoss.com/online-linux-terminals/
+[4]: https://i0.wp.com/itsfoss.com/wp-content/uploads/2019/05/run-linux-commands-in-windows.png?resize=800%2C450&ssl=1
+[5]: https://itsfoss.com/bash-on-windows/
+[6]: https://i2.wp.com/itsfoss.com/wp-content/uploads/2016/08/install-ubuntu-windows-10-linux-subsystem-10.jpeg?resize=800%2C268&ssl=1
+[8]: https://i1.wp.com/itsfoss.com/wp-content/uploads/2016/08/install-ubuntu-windows-10-linux-subsystem-4.jpeg?resize=800%2C632&ssl=1
+[9]: https://itsfoss.com/install-bash-on-windows/
+[10]: https://itsfoss.com/basic-git-commands-cheat-sheet/
+[11]: https://itsfoss.com/linus-torvalds-facts/
+[12]: https://gitforwindows.org/
+[13]: https://i2.wp.com/itsfoss.com/wp-content/uploads/2019/05/git-bash.png?ssl=1
+[14]: https://i1.wp.com/itsfoss.com/wp-content/uploads/2019/05/cygwin-shell.jpg?ssl=1
+[15]: http://www.voxforge.org/home/docs/cygwin-cheat-sheet
+[16]: https://www.cygwin.com/
+[17]: https://itsfoss.com/reasons-switch-linux-windows-xp/
+[18]: https://i1.wp.com/itsfoss.com/wp-content/uploads/2019/05/ubuntu-running-in-virtual-machine-inside-windows.jpeg?resize=800%2C450&ssl=1
+[20]: https://itsfoss.com/install-linux-in-virtualbox/
diff --git a/published/20190527 20- FFmpeg Commands For Beginners.md b/published/20190527 20- FFmpeg Commands For Beginners.md
new file mode 100644
index 0000000000..2a646c6d89
--- /dev/null
+++ b/published/20190527 20- FFmpeg Commands For Beginners.md
@@ -0,0 +1,471 @@
+[#]: collector: (lujun9972)
+[#]: translator: (robsean)
+[#]: reviewer: (wxy)
+[#]: publisher: (wxy)
+[#]: url: (https://linux.cn/article-10932-1.html)
+[#]: subject: (20+ FFmpeg Commands For Beginners)
+[#]: via: (https://www.ostechnix.com/20-ffmpeg-commands-beginners/)
+[#]: author: (sk https://www.ostechnix.com/author/sk/)
+
+给初学者的 20 多个 FFmpeg 命令示例
+======
+
+
+
+在这个指南中,我将用示例来阐明如何使用 FFmpeg 媒体框架来做各种各样的音频、视频转码和转换的操作。我已经为初学者汇集了最常用的 20 多个 FFmpeg 命令,我将不时地添加更多的示例来保持更新这个指南。请给这个指南加书签,以后回来检查更新。让我们开始吧,如果你还没有在你的 Linux 系统中安装 FFmpeg,参考下面的指南。
+
+* [在 Linux 中安装 FFmpeg][2]
+
+### 针对初学者的 20 多个 FFmpeg 命令
+
+FFmpeg 命令的典型语法是:
+
+```
+ffmpeg [全局选项] {[输入文件选项] -i 输入_url_地址} ...
+ {[输出文件选项] 输出_url_地址} ...
+```
+
+现在我们将查看一些重要的和有用的 FFmpeg 命令。
+
+#### 1、获取音频/视频文件信息
+
+为显示你的媒体文件细节,运行:
+
+```
+$ ffmpeg -i video.mp4
+```
+
+样本输出:
+
+```
+ffmpeg version n4.1.3 Copyright (c) 2000-2019 the FFmpeg developers
+built with gcc 8.2.1 (GCC) 20181127
+configuration: --prefix=/usr --disable-debug --disable-static --disable-stripping --enable-fontconfig --enable-gmp --enable-gnutls --enable-gpl --enable-ladspa --enable-libaom --enable-libass --enable-libbluray --enable-libdrm --enable-libfreetype --enable-libfribidi --enable-libgsm --enable-libiec61883 --enable-libjack --enable-libmodplug --enable-libmp3lame --enable-libopencore_amrnb --enable-libopencore_amrwb --enable-libopenjpeg --enable-libopus --enable-libpulse --enable-libsoxr --enable-libspeex --enable-libssh --enable-libtheora --enable-libv4l2 --enable-libvidstab --enable-libvorbis --enable-libvpx --enable-libwebp --enable-libx264 --enable-libx265 --enable-libxcb --enable-libxml2 --enable-libxvid --enable-nvdec --enable-nvenc --enable-omx --enable-shared --enable-version3
+libavutil 56. 22.100 / 56. 22.100
+libavcodec 58. 35.100 / 58. 35.100
+libavformat 58. 20.100 / 58. 20.100
+libavdevice 58. 5.100 / 58. 5.100
+libavfilter 7. 40.101 / 7. 40.101
+libswscale 5. 3.100 / 5. 3.100
+libswresample 3. 3.100 / 3. 3.100
+libpostproc 55. 3.100 / 55. 3.100
+Input #0, mov,mp4,m4a,3gp,3g2,mj2, from 'video.mp4':
+Metadata:
+major_brand : isom
+minor_version : 512
+compatible_brands: isomiso2avc1mp41
+encoder : Lavf58.20.100
+Duration: 00:00:28.79, start: 0.000000, bitrate: 454 kb/s
+Stream #0:0(und): Video: h264 (High) (avc1 / 0x31637661), yuv420p(tv, smpte170m/bt470bg/smpte170m), 1920x1080 [SAR 1:1 DAR 16:9], 318 kb/s, 30 fps, 30 tbr, 15360 tbn, 60 tbc (default)
+Metadata:
+handler_name : ISO Media file produced by Google Inc. Created on: 04/08/2019.
+Stream #0:1(eng): Audio: aac (LC) (mp4a / 0x6134706D), 44100 Hz, stereo, fltp, 128 kb/s (default)
+Metadata:
+handler_name : ISO Media file produced by Google Inc. Created on: 04/08/2019.
+At least one output file must be specified
+```
+
+如你在上面的输出中看到的,FFmpeg 显示该媒体文件信息,以及 FFmpeg 细节,例如版本、配置细节、版权标记、构建参数和库选项等等。
+
+如果你不想看 FFmpeg 标语和其它细节,而仅仅想看媒体文件信息,使用 `-hide_banner` 标志,像下面。
+
+```
+$ ffmpeg -i video.mp4 -hide_banner
+```
+
+样本输出:
+
+![][3]
+
+*使用 FFMpeg 查看音频、视频文件信息。*
+
+看见了吗?现在,它仅显示媒体文件细节。
+
+
+#### 2、转换视频文件到不同的格式
+
+FFmpeg 是强有力的音频和视频转换器,因此,它能在不同格式之间转换媒体文件。举个例子,要转换 mp4 文件到 avi 文件,运行:
+
+```
+$ ffmpeg -i video.mp4 video.avi
+```
+
+类似地,你可以转换媒体文件到你选择的任何格式。
+
+例如,为转换 YouTube flv 格式视频为 mpeg 格式,运行:
+
+```
+$ ffmpeg -i video.flv video.mpeg
+```
+
+如果你想维持你的源视频文件的质量,使用 `-qscale 0` 参数:
+
+```
+$ ffmpeg -i input.webm -qscale 0 output.mp4
+```
+
+为检查 FFmpeg 的支持格式的列表,运行:
+
+```
+$ ffmpeg -formats
+```
+
+#### 3、转换视频文件到音频文件
+
+我转换一个视频文件到音频文件,只需具体指明输出格式,像 .mp3,或 .ogg,或其它任意音频格式。
+
+上面的命令将转换 input.mp4 视频文件到 output.mp3 音频文件。
+
+```
+$ ffmpeg -i input.mp4 -vn output.mp3
+```
+
+此外,你也可以对输出文件使用各种各样的音频转换编码选项,像下面演示。
+
+```
+$ ffmpeg -i input.mp4 -vn -ar 44100 -ac 2 -ab 320 -f mp3 output.mp3
+```
+
+在这里,
+
+ * `-vn` – 表明我们已经在输出文件中禁用视频录制。
+ * `-ar` – 设置输出文件的音频频率。通常使用的值是22050 Hz、44100 Hz、48000 Hz。
+ * `-ac` – 设置音频通道的数目。
+ * `-ab` – 表明音频比特率。
+ * `-f` – 输出文件格式。在我们的实例中,它是 mp3 格式。
+
+#### 4、更改视频文件的分辨率
+
+如果你想设置一个视频文件为指定的分辨率,你可以使用下面的命令:
+
+```
+$ ffmpeg -i input.mp4 -filter:v scale=1280:720 -c:a copy output.mp4
+```
+
+或,
+
+```
+$ ffmpeg -i input.mp4 -s 1280x720 -c:a copy output.mp4
+```
+
+上面的命令将设置所给定视频文件的分辨率到 1280×720。
+
+类似地,为转换上面的文件到 640×480 大小,运行:
+
+```
+$ ffmpeg -i input.mp4 -filter:v scale=640:480 -c:a copy output.mp4
+```
+
+或者,
+
+```
+$ ffmpeg -i input.mp4 -s 640x480 -c:a copy output.mp4
+```
+
+这个技巧将帮助你缩放你的视频文件到较小的显示设备上,例如平板电脑和手机。
+
+#### 5、压缩视频文件
+
+减小媒体文件的大小到较小来节省硬件的空间总是一个好主意.
+
+下面的命令将压缩并减少输出文件的大小。
+
+```
+$ ffmpeg -i input.mp4 -vf scale=1280:-1 -c:v libx264 -preset veryslow -crf 24 output.mp4
+```
+
+请注意,如果你尝试减小视频文件的大小,你将损失视频质量。如果 24 太有侵略性,你可以降低 `-crf` 值到或更低值。
+
+你也可以通过下面的选项来转换编码音频降低比特率,使其有立体声感,从而减小大小。
+
+```
+-ac 2 -c:a aac -strict -2 -b:a 128k
+```
+
+#### 6、压缩音频文件
+
+正像压缩视频文件一样,为节省一些磁盘空间,你也可以使用 `-ab` 标志压缩音频文件。
+
+例如,你有一个 320 kbps 比特率的音频文件。你想通过更改比特率到任意较低的值来压缩它,像下面。
+
+```
+$ ffmpeg -i input.mp3 -ab 128 output.mp3
+```
+
+各种各样可用的音频比特率列表是:
+
+ 1. 96kbps
+ 2. 112kbps
+ 3. 128kbps
+ 4. 160kbps
+ 5. 192kbps
+ 6. 256kbps
+ 7. 320kbps
+
+#### 7、从一个视频文件移除音频流
+
+如果你不想要一个视频文件中的音频,使用 `-an` 标志。
+
+```
+$ ffmpeg -i input.mp4 -an output.mp4
+```
+
+在这里,`-an` 表示没有音频录制。
+
+上面的命令会撤销所有音频相关的标志,因为我们不要来自 input.mp4 的音频。
+
+#### 8、从一个媒体文件移除视频流
+
+类似地,如果你不想要视频流,你可以使用 `-vn` 标志从媒体文件中简单地移除它。`-vn` 代表没有视频录制。换句话说,这个命令转换所给定媒体文件为音频文件。
+
+下面的命令将从所给定媒体文件中移除视频。
+
+```
+$ ffmpeg -i input.mp4 -vn output.mp3
+```
+
+你也可以使用 `-ab` 标志来指出输出文件的比特率,如下面的示例所示。
+
+```
+$ ffmpeg -i input.mp4 -vn -ab 320 output.mp3
+```
+
+#### 9、从视频中提取图像
+
+FFmpeg 的另一个有用的特色是我们可以从一个视频文件中轻松地提取图像。如果你想从一个视频文件中创建一个相册,这可能是非常有用的。
+
+为从一个视频文件中提取图像,使用下面的命令:
+
+```
+$ ffmpeg -i input.mp4 -r 1 -f image2 image-%2d.png
+```
+
+在这里,
+
+ * `-r` – 设置帧速度。即,每秒提取帧到图像的数字。默认值是 25。
+ * `-f` – 表示输出格式,即,在我们的实例中是图像。
+ * `image-%2d.png` – 表明我们如何想命名提取的图像。在这个实例中,命名应该像这样image-01.png、image-02.png、image-03.png 等等开始。如果你使用 `%3d`,那么图像的命名像 image-001.png、image-002.png 等等开始。
+
+#### 10、裁剪视频
+
+FFMpeg 允许以我们选择的任何范围裁剪一个给定的媒体文件。
+
+裁剪一个视频文件的语法如下给定:
+
+```
+ffmpeg -i input.mp4 -filter:v "crop=w:h:x:y" output.mp4
+```
+
+在这里,
+
+ * `input.mp4` – 源视频文件。
+ * `-filter:v` – 表示视频过滤器。
+ * `crop` – 表示裁剪过滤器。
+ * `w` – 我们想自源视频中裁剪的矩形的宽度。
+ * `h` – 矩形的高度。
+ * `x` – 我们想自源视频中裁剪的矩形的 x 坐标 。
+ * `y` – 矩形的 y 坐标。
+
+比如说你想要一个来自视频的位置 (200,150),且具有 640 像素宽度和 480 像素高度的视频,命令应该是:
+
+```
+$ ffmpeg -i input.mp4 -filter:v "crop=640:480:200:150" output.mp4
+```
+
+请注意,剪切视频将影响质量。除非必要,请勿剪切。
+
+#### 11、转换一个视频的具体的部分
+
+有时,你可能想仅转换视频文件的一个具体的部分到不同的格式。以示例说明,下面的命令将转换所给定视频input.mp4 文件的开始 10 秒到视频 .avi 格式。
+
+```
+$ ffmpeg -i input.mp4 -t 10 output.avi
+```
+
+在这里,我们以秒具体说明时间。此外,以 `hh.mm.ss` 格式具体说明时间也是可以的。
+
+#### 12、设置视频的屏幕高宽比
+
+你可以使用 `-aspect` 标志设置一个视频文件的屏幕高宽比,像下面。
+
+```
+$ ffmpeg -i input.mp4 -aspect 16:9 output.mp4
+```
+
+通常使用的高宽比是:
+
+ * 16:9
+ * 4:3
+ * 16:10
+ * 5:4
+ * 2:21:1
+ * 2:35:1
+ * 2:39:1
+
+#### 13、添加海报图像到音频文件
+
+你可以添加海报图像到你的文件,以便图像将在播放音频文件时显示。这对托管在视频托管主机或共享网站中的音频文件是有用的。
+
+```
+$ ffmpeg -loop 1 -i inputimage.jpg -i inputaudio.mp3 -c:v libx264 -c:a aac -strict experimental -b:a 192k -shortest output.mp4
+```
+
+#### 14、使用开始和停止时间剪下一段媒体文件
+
+可以使用开始和停止时间来剪下一段视频为小段剪辑,我们可以使用下面的命令。
+
+```
+$ ffmpeg -i input.mp4 -ss 00:00:50 -codec copy -t 50 output.mp4
+```
+
+在这里,
+
+ * `–s` – 表示视频剪辑的开始时间。在我们的示例中,开始时间是第 50 秒。
+ * `-t` – 表示总的持续时间。
+
+当你想使用开始和结束时间从一个音频或视频文件剪切一部分时,它是非常有用的。
+
+类似地,我们可以像下面剪下音频。
+
+```
+$ ffmpeg -i audio.mp3 -ss 00:01:54 -to 00:06:53 -c copy output.mp3
+```
+
+#### 15、切分视频文件为多个部分
+
+一些网站将仅允许你上传具体指定大小的视频。在这样的情况下,你可以切分大的视频文件到多个较小的部分,像下面。
+
+```
+$ ffmpeg -i input.mp4 -t 00:00:30 -c copy part1.mp4 -ss 00:00:30 -codec copy part2.mp4
+```
+
+在这里,
+
+ * `-t 00:00:30` 表示从视频的开始到视频的第 30 秒创建一部分视频。
+ * `-ss 00:00:30` 为视频的下一部分显示开始时间戳。它意味着第 2 部分将从第 30 秒开始,并将持续到原始视频文件的结尾。
+
+#### 16、接合或合并多个视频部分到一个
+
+FFmpeg 也可以接合多个视频部分,并创建一个单个视频文件。
+
+创建包含你想接合文件的准确的路径的 `join.txt`。所有的文件都应该是相同的格式(相同的编码格式)。所有文件的路径应该逐个列出,像下面。
+
+```
+file /home/sk/myvideos/part1.mp4
+file /home/sk/myvideos/part2.mp4
+file /home/sk/myvideos/part3.mp4
+file /home/sk/myvideos/part4.mp4
+```
+
+现在,接合所有文件,使用命令:
+
+```
+$ ffmpeg -f concat -i join.txt -c copy output.mp4
+```
+
+如果你得到一些像下面的错误;
+
+```
+[concat @ 0x555fed174cc0] Unsafe file name '/path/to/mp4'
+join.txt: Operation not permitted
+```
+
+添加 `-safe 0` :
+
+```
+$ ffmpeg -f concat -safe 0 -i join.txt -c copy output.mp4
+```
+
+上面的命令将接合 part1.mp4、part2.mp4、part3.mp4 和 part4.mp4 文件到一个称为 output.mp4 的单个文件中。
+
+#### 17、添加字幕到一个视频文件
+
+我们可以使用 FFmpeg 来添加字幕到视频文件。为你的视频下载正确的字幕,并如下所示添加它到你的视频。
+
+```
+$ fmpeg -i input.mp4 -i subtitle.srt -map 0 -map 1 -c copy -c:v libx264 -crf 23 -preset veryfast output.mp4
+```
+
+#### 18、预览或测试视频或音频文件
+
+你可能希望通过预览来验证或测试输出的文件是否已经被恰当地转码编码。为完成预览,你可以从你的终端播放它,用命令:
+
+```
+$ ffplay video.mp4
+```
+
+![][7]
+
+类似地,你可以测试音频文件,像下面所示。
+
+```
+$ ffplay audio.mp3
+```
+
+![][8]
+
+#### 19、增加/减少视频播放速度
+
+FFmpeg 允许你调整视频播放速度。
+
+为增加视频播放速度,运行:
+
+```
+$ ffmpeg -i input.mp4 -vf "setpts=0.5*PTS" output.mp4
+```
+
+该命令将双倍视频的速度。
+
+为降低你的视频速度,你需要使用一个大于 1 的倍数。为减少播放速度,运行:
+
+```
+$ ffmpeg -i input.mp4 -vf "setpts=4.0*PTS" output.mp4
+```
+
+#### 20、创建动画的 GIF
+
+出于各种目的,我们在几乎所有的社交和专业网络上使用 GIF 图像。使用 FFmpeg,我们可以简单地和快速地创建动画的视频文件。下面的指南阐释了如何在类 Unix 系统中使用 FFmpeg 和 ImageMagick 创建一个动画的 GIF 文件。
+
+ * [在 Linux 中如何创建动画的 GIF][9]
+
+#### 21、从 PDF 文件中创建视频
+
+我长年累月的收集了很多 PDF 文件,大多数是 Linux 教程,保存在我的平板电脑中。有时我懒得从平板电脑中阅读它们。因此,我决定从 PDF 文件中创建一个视频,在一个大屏幕设备(像一台电视机或一台电脑)中观看它们。如果你想知道如何从一批 PDF 文件中制作一个电影,下面的指南将帮助你。
+
+ * [在 Linux 中如何从 PDF 文件中创建一个视频][10]
+
+#### 22、获取帮助
+
+在这个指南中,我已经覆盖大多数常常使用的 FFmpeg 命令。它有很多不同的选项来做各种各样的高级功能。要学习更多用法,请参考手册页。
+
+```
+$ man ffmpeg
+```
+
+这就是全部了。我希望这个指南将帮助你入门 FFmpeg。如果你发现这个指南有用,请在你的社交和专业网络上分享它。更多好东西将要来。敬请期待!
+
+谢谢!
+
+--------------------------------------------------------------------------------
+
+via: https://www.ostechnix.com/20-ffmpeg-commands-beginners/
+
+作者:[sk][a]
+选题:[lujun9972][b]
+译者:[robsean](https://github.com/robsean)
+校对:[wxy](https://github.com/wxy)
+
+本文由 [LCTT](https://github.com/LCTT/TranslateProject) 原创编译,[Linux中国](https://linux.cn/) 荣誉推出
+
+[a]: https://www.ostechnix.com/author/sk/
+[b]: https://github.com/lujun9972
+[1]: https://www.ostechnix.com/wp-content/uploads/2017/05/FFmpeg-Commands-720x340.png
+[2]: https://www.ostechnix.com/install-ffmpeg-linux/
+[3]: http://www.ostechnix.com/wp-content/uploads/2017/05/sk@sk_001.png
+[4]: https://ostechnix.tradepub.com/free/w_make141/prgm.cgi
+[5]: https://ostechnix.tradepub.com/free/w_make75/prgm.cgi
+[6]: https://ostechnix.tradepub.com/free/w_make235/prgm.cgi
+[7]: http://www.ostechnix.com/wp-content/uploads/2017/05/Menu_004.png
+[8]: http://www.ostechnix.com/wp-content/uploads/2017/05/Menu_005-3.png
+[9]: https://www.ostechnix.com/create-animated-gif-ubuntu-16-04/
+[10]: https://www.ostechnix.com/create-video-pdf-files-linux/
diff --git a/published/20190527 A deeper dive into Linux permissions.md b/published/20190527 A deeper dive into Linux permissions.md
new file mode 100644
index 0000000000..a4bba97507
--- /dev/null
+++ b/published/20190527 A deeper dive into Linux permissions.md
@@ -0,0 +1,171 @@
+[#]: collector: (lujun9972)
+[#]: translator: (geekpi)
+[#]: reviewer: (wxy)
+[#]: publisher: (wxy)
+[#]: url: (https://linux.cn/article-10947-1.html)
+[#]: subject: (A deeper dive into Linux permissions)
+[#]: via: (https://www.networkworld.com/article/3397790/a-deeper-dive-into-linux-permissions.html)
+[#]: author: (Sandra Henry-Stocker https://www.networkworld.com/author/Sandra-Henry_Stocker/)
+
+更深入地了解 Linux 权限
+======
+> 在 Linux 上查看文件权限时,有时你会看到的不仅仅是普通的 r、w、x 和 -。如何更清晰地了解这些字符试图告诉你什么以及这些权限如何工作?
+
+
+
+在 Linux 上查看文件权限时,有时你会看到的不仅仅是普通的 `r`、`w`、`x` 和 `-`。除了在所有者、组和其他中看到 `rwx` 之外,你可能会看到 `s` 或者 `t`,如下例所示:
+
+```
+drwxrwsrwt
+```
+
+要进一步明确的方法之一是使用 `stat` 命令查看权限。`stat` 的第四行输出以八进制和字符串格式显示文件权限:
+
+```
+$ stat /var/mail
+ File: /var/mail
+ Size: 4096 Blocks: 8 IO Block: 4096 directory
+Device: 801h/2049d Inode: 1048833 Links: 2
+Access: (3777/drwxrwsrwt) Uid: ( 0/ root) Gid: ( 8/ mail)
+Access: 2019-05-21 19:23:15.769746004 -0400
+Modify: 2019-05-21 19:03:48.226656344 -0400
+Change: 2019-05-21 19:03:48.226656344 -0400
+ Birth: -
+```
+
+这个输出提示我们,分配给文件权限的位数超过 9 位。事实上,有 12 位。这些额外的三位提供了一种分配超出通常的读、写和执行权限的方法 - 例如,`3777`(二进制 `011111111111`)表示使用了两个额外的设置。
+
+该值的第一个 `1` (第二位)表示 SGID(设置 GID),为运行文件而赋予临时权限,或以该关联组的权限来使用目录。
+
+```
+011111111111
+ ^
+```
+
+SGID 将正在使用该文件的用户作为该组成员之一而分配临时权限。
+
+第二个 `1`(第三位)是“粘连”位。它确保*只有*文件的所有者能够删除或重命名该文件或目录。
+
+```
+011111111111
+ ^
+```
+
+如果权限是 `7777` 而不是 `3777`,我们知道 SUID(设置 UID)字段也已设置。
+
+```
+111111111111
+^
+```
+
+SUID 将正在使用该文件的用户作为文件拥有者分配临时权限。
+
+至于我们上面看到的 `/var/mail` 目录,所有用户都需要访问,因此需要一些特殊值来提供它。
+
+但现在让我们更进一步。
+
+特殊权限位的一个常见用法是使用 `passwd` 之类的命令。如果查看 `/usr/bin/passwd` 文件,你会注意到 SUID 位已设置,它允许你更改密码(以及 `/etc/shadow` 文件的内容),即使你是以普通(非特权)用户身份运行,并且对此文件没有读取或写入权限。当然,`passwd` 命令很聪明,不允许你更改其他人的密码,除非你是以 root 身份运行或使用 `sudo`。
+
+```
+$ ls -l /usr/bin/passwd
+-rwsr-xr-x 1 root root 63736 Mar 22 14:32 /usr/bin/passwd
+$ ls -l /etc/shadow
+-rw-r----- 1 root shadow 2195 Apr 22 10:46 /etc/shadow
+```
+
+现在,让我们看一下使用这些特殊权限可以做些什么。
+
+### 如何分配特殊文件权限
+
+与 Linux 命令行中的许多东西一样,你可以有不同的方法设置。 `chmod` 命令允许你以数字方式或使用字符表达式更改权限。
+
+要以数字方式更改文件权限,你可以使用这样的命令来设置 SUID 和 SGID 位:
+
+```
+$ chmod 6775 tryme
+```
+
+或者你可以使用这样的命令:
+
+```
+$ chmod ug+s tryme <== 用于 SUID 和 SGID 权限
+```
+
+如果你要添加特殊权限的文件是脚本,你可能会对它不符合你的期望感到惊讶。这是一个非常简单的例子:
+
+```
+$ cat tryme
+#!/bin/bash
+
+echo I am $USER
+```
+
+即使设置了 SUID 和 SGID 位,并且 root 是文件所有者,运行脚本也不会产生你可能期望的 “I am root”。为什么?因为 Linux 会忽略脚本的 SUID 和 SGID 位。
+
+```
+$ ls -l tryme
+-rwsrwsrwt 1 root root 29 May 26 12:22 tryme
+$ ./tryme
+I am jdoe
+```
+
+另一方面,如果你对一个编译的程序之类进行类似的尝试,就像下面这个简单的 C 程序一样,你会看到不同的效果。在此示例程序中,我们提示用户输入文件名并创建它,并给文件写入权限。
+
+```
+#include
+
+int main()
+{
+ FILE *fp; /* file pointer*/
+ char fName[20];
+
+ printf("Enter the name of file to be created: ");
+ scanf("%s",fName);
+
+ /* create the file with write permission */
+ fp=fopen(fName,"w");
+ /* check if file was created */
+ if(fp==NULL)
+ {
+ printf("File not created");
+ exit(0);
+ }
+
+ printf("File created successfully\n");
+ return 0;
+}
+```
+
+编译程序并运行该命令以使 root 用户成为所有者并设置所需权限后,你将看到它以预期的 root 权限运行 - 留下新创建的 root 为所有者的文件。当然,你必须具有 `sudo` 权限才能运行一些需要的命令。
+
+```
+$ cc -o mkfile mkfile.c <== 编译程序
+$ sudo chown root:root mkfile <== 更改所有者和组为 “root”
+$ sudo chmod ug+s mkfile <== 添加 SUID and SGID 权限
+$ ./mkfile <== 运行程序
+Enter name of file to be create: empty
+File created successfully
+$ ls -l empty
+-rw-rw-r-- 1 root root 0 May 26 13:15 empty
+```
+
+请注意,文件所有者是 root - 如果程序未以 root 权限运行,则不会发生这种情况。
+
+权限字符串中不常见设置的位置(例如,rw**s**rw**s**rw**t**)可以帮助提醒我们每个位的含义。至少第一个 “s”(SUID) 位于所有者权限区域中,第二个 (SGID) 位于组权限区域中。为什么粘连位是 “t” 而不是 “s” 超出了我的理解。也许创造者想把它称为 “tacky bit”,但由于这个词的不太令人喜欢的第二个定义而改变了他们的想法。无论如何,额外的权限设置为 Linux 和其他 Unix 系统提供了许多额外的功能。
+
+--------------------------------------------------------------------------------
+
+via: https://www.networkworld.com/article/3397790/a-deeper-dive-into-linux-permissions.html
+
+作者:[Sandra Henry-Stocker][a]
+选题:[lujun9972][b]
+译者:[geekpi](https://github.com/geekpi)
+校对:[wxy](https://github.com/wxy)
+
+本文由 [LCTT](https://github.com/LCTT/TranslateProject) 原创编译,[Linux中国](https://linux.cn/) 荣誉推出
+
+[a]: https://www.networkworld.com/author/Sandra-Henry_Stocker/
+[b]: https://github.com/lujun9972
+[1]: https://images.idgesg.net/images/article/2019/05/shs_rwsr-100797564-large.jpg
+[2]: https://www.facebook.com/NetworkWorld/
+[3]: https://www.linkedin.com/company/network-world
diff --git a/published/20190527 Dockly - Manage Docker Containers From Terminal.md b/published/20190527 Dockly - Manage Docker Containers From Terminal.md
new file mode 100644
index 0000000000..44e9dc2c21
--- /dev/null
+++ b/published/20190527 Dockly - Manage Docker Containers From Terminal.md
@@ -0,0 +1,146 @@
+[#]: collector: (lujun9972)
+[#]: translator: (geekpi)
+[#]: reviewer: (wxy)
+[#]: publisher: (wxy)
+[#]: url: (https://linux.cn/article-10925-1.html)
+[#]: subject: (Dockly – Manage Docker Containers From Terminal)
+[#]: via: (https://www.ostechnix.com/dockly-manage-docker-containers-from-terminal/)
+[#]: author: (sk https://www.ostechnix.com/author/sk/)
+
+Dockly:从终端管理 Docker 容器
+======
+
+
+
+几天前,我们发布了一篇指南,其中涵盖了[开始使用 Docker][2] 时需要了解的几乎所有细节。在该指南中,我们向你展示了如何详细创建和管理 Docker 容器。还有一些可用于管理 Docker 容器的非官方工具。如果你看过我们以前的文章,你可能会看到两个基于 Web 的工具,[Portainer][3] 和 [PiCluster][4]。它们都使得 Docker 管理任务在 Web 浏览器中变得更加容易和简单。今天,我遇到了另一个名为 Dockly 的 Docker 管理工具。
+
+与上面的工具不同,Dockly 是一个 TUI(文本界面)程序,用于在类 Unix 系统中从终端管理 Docker 容器和服务。它是使用 NodeJS 编写的自由开源工具。在本简要指南中,我们将了解如何安装 Dockly 以及如何从命令行管理 Docker 容器。
+
+### 安装 Dockly
+
+确保已在 Linux 上安装了 NodeJS。如果尚未安装,请参阅以下指南。
+
+* [如何在 Linux 上安装 NodeJS][5]
+
+安装 NodeJS 后,运行以下命令安装 Dockly:
+
+```
+# npm install -g dockly
+```
+
+### 使用 Dockly 在终端管理 Docker 容器
+
+使用 Dockly 管理 Docker 容器非常简单!你所要做的就是打开终端并运行以下命令:
+
+```
+# dockly
+```
+
+Dockly 将通过 unix 套接字自动连接到你的本机 docker 守护进程,并在终端中显示正在运行的容器列表,如下所示。
+
+![][6]
+
+*使用 Dockly 管理 Docker 容器*
+
+正如你在上面的截图中看到的,Dockly 在顶部显示了运行容器的以下信息:
+
+* 容器 ID,
+* 容器名称,
+* Docker 镜像,
+* 命令,
+* 运行中容器的状态,
+* 状态。
+
+在右上角,你将看到容器的 CPU 和内存利用率。使用向上/向下箭头键在容器之间移动。
+
+在底部,有少量的键盘快捷键来执行各种 Docker 管理任务。以下是目前可用的键盘快捷键列表:
+
+* `=` - 刷新 Dockly 界面,
+* `/` - 搜索容器列表视图,
+* `i` - 显示有关当前所选容器或服务的信息,
+* `回车` - 显示当前容器或服务的日志,
+* `v` - 在容器和服务视图之间切换,
+* `l` - 在选定的容器上启动 `/bin/bash` 会话,
+* `r` - 重启选定的容器,
+* `s` - 停止选定的容器,
+* `h` - 显示帮助窗口,
+* `q` - 退出 Dockly。
+
+#### 查看容器的信息
+
+使用向上/向下箭头选择一个容器,然后按 `i` 以显示所选容器的信息。
+
+![][7]
+
+*查看容器的信息*
+
+#### 重启容器
+
+如果你想随时重启容器,只需选择它并按 `r` 即可重新启动。
+
+![][8]
+
+*重启 Docker 容器*
+
+#### 停止/删除容器和镜像
+
+如果不再需要容器,我们可以立即停止和/或删除一个或所有容器。为此,请按 `m` 打开菜单。
+
+![][9]
+
+*停止,删除 Docker 容器和镜像*
+
+在这里,你可以执行以下操作。
+
+* 停止所有 Docker 容器,
+* 删除选定的容器,
+* 删除所有容器,
+* 删除所有 Docker 镜像等。
+
+#### 显示 Dockly 帮助部分
+
+如果你有任何疑问,只需按 `h` 即可打开帮助部分。
+
+![][10]
+
+*Dockly 帮助*
+
+有关更多详细信息,请参考最后给出的官方 GitHub 页面。
+
+就是这些了。希望这篇文章有用。如果你一直在使用 Docker 容器,请试试 Dockly,看它是否有帮助。
+
+建议阅读:
+
+ * [如何自动更新正在运行的 Docker 容器][11]
+ * [ctop:一个 Linux 容器的命令行监控工具][12]
+
+资源:
+
+ * [Dockly 的 GitHub 仓库][13]
+
+--------------------------------------------------------------------------------
+
+via: https://www.ostechnix.com/dockly-manage-docker-containers-from-terminal/
+
+作者:[sk][a]
+选题:[lujun9972][b]
+译者:[geekpi](https://github.com/geekpi)
+校对:[wxy](https://github.com/wxy)
+
+本文由 [LCTT](https://github.com/LCTT/TranslateProject) 原创编译,[Linux中国](https://linux.cn/) 荣誉推出
+
+[a]: https://www.ostechnix.com/author/sk/
+[b]: https://github.com/lujun9972
+[1]: https://www.ostechnix.com/wp-content/uploads/2019/05/Dockly-720x340.png
+[2]: https://www.ostechnix.com/getting-started-with-docker/
+[3]: https://www.ostechnix.com/portainer-an-easiest-way-to-manage-docker/
+[4]: https://www.ostechnix.com/picluster-simple-web-based-docker-management-application/
+[5]: https://www.ostechnix.com/install-node-js-linux/
+[6]: http://www.ostechnix.com/wp-content/uploads/2019/05/Manage-Docker-Containers-Using-Dockly.png
+[7]: http://www.ostechnix.com/wp-content/uploads/2019/05/View-containers-information.png
+[8]: http://www.ostechnix.com/wp-content/uploads/2019/05/Restart-containers.png
+[9]: http://www.ostechnix.com/wp-content/uploads/2019/05/stop-remove-containers-and-images.png
+[10]: http://www.ostechnix.com/wp-content/uploads/2019/05/Dockly-Help.png
+[11]: https://www.ostechnix.com/automatically-update-running-docker-containers/
+[12]: https://www.ostechnix.com/ctop-commandline-monitoring-tool-linux-containers/
+[13]: https://github.com/lirantal/dockly
diff --git a/published/20190527 How To Check Available Security Updates On Red Hat (RHEL) And CentOS System.md b/published/20190527 How To Check Available Security Updates On Red Hat (RHEL) And CentOS System.md
new file mode 100644
index 0000000000..e853c92615
--- /dev/null
+++ b/published/20190527 How To Check Available Security Updates On Red Hat (RHEL) And CentOS System.md
@@ -0,0 +1,312 @@
+[#]: collector: (lujun9972)
+[#]: translator: (jdh8383)
+[#]: reviewer: (wxy)
+[#]: publisher: (wxy)
+[#]: url: (https://linux.cn/article-10938-1.html)
+[#]: subject: (How To Check Available Security Updates On Red Hat (RHEL) And CentOS System?)
+[#]: via: (https://www.2daygeek.com/check-list-view-find-available-security-updates-on-redhat-rhel-centos-system/)
+[#]: author: (Magesh Maruthamuthu https://www.2daygeek.com/author/magesh/)
+
+如何在 CentOS 或 RHEL 系统上检查可用的安全更新?
+======
+
+
+
+当你更新系统时,根据你所在公司的安全策略,有时候可能只需要打上与安全相关的补丁。大多数情况下,这应该是出于程序兼容性方面的考量。那该怎样实践呢?有没有办法让 `yum` 只安装安全补丁呢?
+
+答案是肯定的,可以用 `yum` 包管理器轻松实现。
+
+在这篇文章中,我们不但会提供所需的信息。而且,我们会介绍一些额外的命令,可以帮你获取指定安全更新的详实信息。
+
+希望这样可以启发你去了解并修复你列表上的那些漏洞。一旦有安全漏洞被公布,就必须更新受影响的软件,这样可以降低系统中的安全风险。
+
+对于 RHEL 或 CentOS 6 系统,运行下面的 [Yum 命令][1] 来安装 yum 安全插件。
+
+```
+# yum -y install yum-plugin-security
+```
+
+在 RHEL 7&8 或是 CentOS 7&8 上面,这个插件已经是 `yum` 的一部分了,不用单独安装。
+
+要列出全部可用的补丁(包括安全、Bug 修复以及产品改进),但不安装它们:
+
+```
+# yum updateinfo list available
+Loaded plugins: changelog, package_upload, product-id, search-disabled-repos,
+ : subscription-manager, verify, versionlock
+RHSA-2014:1031 Important/Sec. 389-ds-base-1.3.1.6-26.el7_0.x86_64
+RHSA-2015:0416 Important/Sec. 389-ds-base-1.3.3.1-13.el7.x86_64
+RHBA-2015:0626 bugfix 389-ds-base-1.3.3.1-15.el7_1.x86_64
+RHSA-2015:0895 Important/Sec. 389-ds-base-1.3.3.1-16.el7_1.x86_64
+RHBA-2015:1554 bugfix 389-ds-base-1.3.3.1-20.el7_1.x86_64
+RHBA-2015:1960 bugfix 389-ds-base-1.3.3.1-23.el7_1.x86_64
+RHBA-2015:2351 bugfix 389-ds-base-1.3.4.0-19.el7.x86_64
+RHBA-2015:2572 bugfix 389-ds-base-1.3.4.0-21.el7_2.x86_64
+RHSA-2016:0204 Important/Sec. 389-ds-base-1.3.4.0-26.el7_2.x86_64
+RHBA-2016:0550 bugfix 389-ds-base-1.3.4.0-29.el7_2.x86_64
+RHBA-2016:1048 bugfix 389-ds-base-1.3.4.0-30.el7_2.x86_64
+RHBA-2016:1298 bugfix 389-ds-base-1.3.4.0-32.el7_2.x86_64
+```
+
+要统计补丁的大约数量,运行下面的命令:
+
+```
+# yum updateinfo list available | wc -l
+11269
+```
+
+想列出全部可用的安全补丁但不安装,以下命令用来展示你系统里已安装和待安装的推荐补丁:
+
+```
+# yum updateinfo list security all
+Loaded plugins: changelog, package_upload, product-id, search-disabled-repos,
+ : subscription-manager, verify, versionlock
+ RHSA-2014:1031 Important/Sec. 389-ds-base-1.3.1.6-26.el7_0.x86_64
+ RHSA-2015:0416 Important/Sec. 389-ds-base-1.3.3.1-13.el7.x86_64
+ RHSA-2015:0895 Important/Sec. 389-ds-base-1.3.3.1-16.el7_1.x86_64
+ RHSA-2016:0204 Important/Sec. 389-ds-base-1.3.4.0-26.el7_2.x86_64
+ RHSA-2016:2594 Moderate/Sec. 389-ds-base-1.3.5.10-11.el7.x86_64
+ RHSA-2017:0920 Important/Sec. 389-ds-base-1.3.5.10-20.el7_3.x86_64
+ RHSA-2017:2569 Moderate/Sec. 389-ds-base-1.3.6.1-19.el7_4.x86_64
+ RHSA-2018:0163 Important/Sec. 389-ds-base-1.3.6.1-26.el7_4.x86_64
+ RHSA-2018:0414 Important/Sec. 389-ds-base-1.3.6.1-28.el7_4.x86_64
+ RHSA-2018:1380 Important/Sec. 389-ds-base-1.3.7.5-21.el7_5.x86_64
+ RHSA-2018:2757 Moderate/Sec. 389-ds-base-1.3.7.5-28.el7_5.x86_64
+ RHSA-2018:3127 Moderate/Sec. 389-ds-base-1.3.8.4-15.el7.x86_64
+ RHSA-2014:1031 Important/Sec. 389-ds-base-libs-1.3.1.6-26.el7_0.x86_64
+```
+
+要显示所有待安装的安全补丁:
+
+```
+# yum updateinfo list security all | grep -v "i"
+
+ RHSA-2014:1031 Important/Sec. 389-ds-base-1.3.1.6-26.el7_0.x86_64
+ RHSA-2015:0416 Important/Sec. 389-ds-base-1.3.3.1-13.el7.x86_64
+ RHSA-2015:0895 Important/Sec. 389-ds-base-1.3.3.1-16.el7_1.x86_64
+ RHSA-2016:0204 Important/Sec. 389-ds-base-1.3.4.0-26.el7_2.x86_64
+ RHSA-2016:2594 Moderate/Sec. 389-ds-base-1.3.5.10-11.el7.x86_64
+ RHSA-2017:0920 Important/Sec. 389-ds-base-1.3.5.10-20.el7_3.x86_64
+ RHSA-2017:2569 Moderate/Sec. 389-ds-base-1.3.6.1-19.el7_4.x86_64
+ RHSA-2018:0163 Important/Sec. 389-ds-base-1.3.6.1-26.el7_4.x86_64
+ RHSA-2018:0414 Important/Sec. 389-ds-base-1.3.6.1-28.el7_4.x86_64
+ RHSA-2018:1380 Important/Sec. 389-ds-base-1.3.7.5-21.el7_5.x86_64
+ RHSA-2018:2757 Moderate/Sec. 389-ds-base-1.3.7.5-28.el7_5.x86_64
+```
+
+要统计全部安全补丁的大致数量,运行下面的命令:
+
+```
+# yum updateinfo list security all | wc -l
+3522
+```
+
+下面根据已装软件列出可更新的安全补丁。这包括 bugzilla(bug 修复)、CVE(知名漏洞数据库)、安全更新等:
+
+```
+# yum updateinfo list security
+
+或者
+
+# yum updateinfo list sec
+
+Loaded plugins: changelog, package_upload, product-id, search-disabled-repos,
+ : subscription-manager, verify, versionlock
+
+RHSA-2018:3665 Important/Sec. NetworkManager-1:1.12.0-8.el7_6.x86_64
+RHSA-2018:3665 Important/Sec. NetworkManager-adsl-1:1.12.0-8.el7_6.x86_64
+RHSA-2018:3665 Important/Sec. NetworkManager-bluetooth-1:1.12.0-8.el7_6.x86_64
+RHSA-2018:3665 Important/Sec. NetworkManager-config-server-1:1.12.0-8.el7_6.noarch
+RHSA-2018:3665 Important/Sec. NetworkManager-glib-1:1.12.0-8.el7_6.x86_64
+RHSA-2018:3665 Important/Sec. NetworkManager-libnm-1:1.12.0-8.el7_6.x86_64
+RHSA-2018:3665 Important/Sec. NetworkManager-ppp-1:1.12.0-8.el7_6.x86_64
+RHSA-2018:3665 Important/Sec. NetworkManager-team-1:1.12.0-8.el7_6.x86_64
+RHSA-2018:3665 Important/Sec. NetworkManager-tui-1:1.12.0-8.el7_6.x86_64
+RHSA-2018:3665 Important/Sec. NetworkManager-wifi-1:1.12.0-8.el7_6.x86_64
+RHSA-2018:3665 Important/Sec. NetworkManager-wwan-1:1.12.0-8.el7_6.x86_64
+```
+
+显示所有与安全相关的更新,并且返回一个结果来告诉你是否有可用的补丁:
+
+```
+# yum --security check-update
+Loaded plugins: changelog, package_upload, product-id, search-disabled-repos, subscription-manager, verify, versionlock
+rhel-7-server-rpms | 2.0 kB 00:00:00
+--> policycoreutils-devel-2.2.5-20.el7.x86_64 from rhel-7-server-rpms excluded (updateinfo)
+--> smc-raghumalayalam-fonts-6.0-7.el7.noarch from rhel-7-server-rpms excluded (updateinfo)
+--> amanda-server-3.3.3-17.el7.x86_64 from rhel-7-server-rpms excluded (updateinfo)
+--> 389-ds-base-libs-1.3.4.0-26.el7_2.x86_64 from rhel-7-server-rpms excluded (updateinfo)
+--> 1:cups-devel-1.6.3-26.el7.i686 from rhel-7-server-rpms excluded (updateinfo)
+--> openwsman-client-2.6.3-3.git4391e5c.el7.i686 from rhel-7-server-rpms excluded (updateinfo)
+--> 1:emacs-24.3-18.el7.x86_64 from rhel-7-server-rpms excluded (updateinfo)
+--> augeas-libs-1.4.0-2.el7_4.2.i686 from rhel-7-server-rpms excluded (updateinfo)
+--> samba-winbind-modules-4.2.3-10.el7.i686 from rhel-7-server-rpms excluded (updateinfo)
+--> tftp-5.2-11.el7.x86_64 from rhel-7-server-rpms excluded (updateinfo)
+.
+.
+35 package(s) needed for security, out of 115 available
+NetworkManager.x86_64 1:1.12.0-10.el7_6 rhel-7-server-rpms
+NetworkManager-adsl.x86_64 1:1.12.0-10.el7_6 rhel-7-server-rpms
+NetworkManager-bluetooth.x86_64 1:1.12.0-10.el7_6 rhel-7-server-rpms
+NetworkManager-config-server.noarch 1:1.12.0-10.el7_6 rhel-7-server-rpms
+NetworkManager-glib.x86_64 1:1.12.0-10.el7_6 rhel-7-server-rpms
+NetworkManager-libnm.x86_64 1:1.12.0-10.el7_6 rhel-7-server-rpms
+NetworkManager-ppp.x86_64 1:1.12.0-10.el7_6 rhel-7-server-rpms
+```
+
+列出所有可用的安全补丁,并且显示其详细信息:
+
+```
+# yum info-sec
+.
+.
+===============================================================================
+ tzdata bug fix and enhancement update
+===============================================================================
+ Update ID : RHBA-2019:0689
+ Release : 0
+ Type : bugfix
+ Status : final
+ Issued : 2019-03-28 19:27:44 UTC
+Description : The tzdata packages contain data files with rules for various
+ : time zones.
+ :
+ : The tzdata packages have been updated to version
+ : 2019a, which addresses recent time zone changes.
+ : Notably:
+ :
+ : * The Asia/Hebron and Asia/Gaza zones will start
+ : DST on 2019-03-30, rather than 2019-03-23 as
+ : previously predicted.
+ : * Metlakatla rejoined Alaska time on 2019-01-20,
+ : ending its observances of Pacific standard time.
+ :
+ : (BZ#1692616, BZ#1692615, BZ#1692816)
+ :
+ : Users of tzdata are advised to upgrade to these
+ : updated packages.
+ Severity : None
+```
+
+如果你想要知道某个更新的具体内容,可以运行下面这个命令:
+
+```
+# yum updateinfo RHSA-2019:0163
+
+Loaded plugins: changelog, package_upload, product-id, search-disabled-repos, subscription-manager, verify, versionlock
+rhel-7-server-rpms | 2.0 kB 00:00:00
+===============================================================================
+ Important: kernel security, bug fix, and enhancement update
+===============================================================================
+ Update ID : RHSA-2019:0163
+ Release : 0
+ Type : security
+ Status : final
+ Issued : 2019-01-29 15:21:23 UTC
+ Updated : 2019-01-29 15:23:47 UTC Bugs : 1641548 - CVE-2018-18397 kernel: userfaultfd bypasses tmpfs file permissions
+ : 1641878 - CVE-2018-18559 kernel: Use-after-free due to race condition in AF_PACKET implementation
+ CVEs : CVE-2018-18397
+ : CVE-2018-18559
+Description : The kernel packages contain the Linux kernel, the core of any
+ : Linux operating system.
+ :
+ : Security Fix(es):
+ :
+ : * kernel: Use-after-free due to race condition in
+ : AF_PACKET implementation (CVE-2018-18559)
+ :
+ : * kernel: userfaultfd bypasses tmpfs file
+ : permissions (CVE-2018-18397)
+ :
+ : For more details about the security issue(s),
+ : including the impact, a CVSS score, and other
+ : related information, refer to the CVE page(s)
+ : listed in the References section.
+ :
+ : Bug Fix(es):
+ :
+ : These updated kernel packages include also
+ : numerous bug fixes and enhancements. Space
+ : precludes documenting all of the bug fixes in this
+ : advisory. See the descriptions in the related
+ : Knowledge Article:
+ : https://access.redhat.com/articles/3827321
+ Severity : Important
+updateinfo info done
+```
+
+跟之前类似,你可以只查询那些通过 CVE 释出的系统漏洞:
+
+```
+# yum updateinfo list cves
+
+Loaded plugins: changelog, package_upload, product-id, search-disabled-repos,
+ : subscription-manager, verify, versionlock
+CVE-2018-15688 Important/Sec. NetworkManager-1:1.12.0-8.el7_6.x86_64
+CVE-2018-15688 Important/Sec. NetworkManager-adsl-1:1.12.0-8.el7_6.x86_64
+CVE-2018-15688 Important/Sec. NetworkManager-bluetooth-1:1.12.0-8.el7_6.x86_64
+CVE-2018-15688 Important/Sec. NetworkManager-config-server-1:1.12.0-8.el7_6.noarch
+CVE-2018-15688 Important/Sec. NetworkManager-glib-1:1.12.0-8.el7_6.x86_64
+CVE-2018-15688 Important/Sec. NetworkManager-libnm-1:1.12.0-8.el7_6.x86_64
+CVE-2018-15688 Important/Sec. NetworkManager-ppp-1:1.12.0-8.el7_6.x86_64
+CVE-2018-15688 Important/Sec. NetworkManager-team-1:1.12.0-8.el7_6.x86_64
+```
+
+你也可以查看那些跟 bug 修复相关的更新,运行下面的命令:
+
+```
+# yum updateinfo list bugfix | less
+
+Loaded plugins: changelog, package_upload, product-id, search-disabled-repos,
+ : subscription-manager, verify, versionlock
+RHBA-2018:3349 bugfix NetworkManager-1:1.12.0-7.el7_6.x86_64
+RHBA-2019:0519 bugfix NetworkManager-1:1.12.0-10.el7_6.x86_64
+RHBA-2018:3349 bugfix NetworkManager-adsl-1:1.12.0-7.el7_6.x86_64
+RHBA-2019:0519 bugfix NetworkManager-adsl-1:1.12.0-10.el7_6.x86_64
+RHBA-2018:3349 bugfix NetworkManager-bluetooth-1:1.12.0-7.el7_6.x86_64
+RHBA-2019:0519 bugfix NetworkManager-bluetooth-1:1.12.0-10.el7_6.x86_64
+RHBA-2018:3349 bugfix NetworkManager-config-server-1:1.12.0-7.el7_6.noarch
+RHBA-2019:0519 bugfix NetworkManager-config-server-1:1.12.0-10.el7_6.noarch
+```
+
+要想得到待安装更新的摘要信息,运行这个:
+
+```
+# yum updateinfo summary
+Loaded plugins: changelog, package_upload, product-id, search-disabled-repos, subscription-manager, verify, versionlock
+rhel-7-server-rpms | 2.0 kB 00:00:00
+Updates Information Summary: updates
+ 13 Security notice(s)
+ 9 Important Security notice(s)
+ 3 Moderate Security notice(s)
+ 1 Low Security notice(s)
+ 35 Bugfix notice(s)
+ 1 Enhancement notice(s)
+updateinfo summary done
+```
+
+如果只想打印出低级别的安全更新,运行下面这个命令。类似的,你也可以只查询重要级别和中等级别的安全更新。
+
+```
+# yum updateinfo list sec | grep -i "Low"
+
+RHSA-2019:0201 Low/Sec. libgudev1-219-62.el7_6.3.x86_64
+RHSA-2019:0201 Low/Sec. systemd-219-62.el7_6.3.x86_64
+RHSA-2019:0201 Low/Sec. systemd-libs-219-62.el7_6.3.x86_64
+RHSA-2019:0201 Low/Sec. systemd-sysv-219-62.el7_6.3.x86_64
+```
+
+--------------------------------------------------------------------------------
+
+via: https://www.2daygeek.com/check-list-view-find-available-security-updates-on-redhat-rhel-centos-system/
+
+作者:[Magesh Maruthamuthu][a]
+选题:[lujun9972][b]
+译者:[jdh8383](https://github.com/jdh8383)
+校对:[wxy](https://github.com/wxy)
+
+本文由 [LCTT](https://github.com/LCTT/TranslateProject) 原创编译,[Linux中国](https://linux.cn/) 荣誉推出
+
+[a]: https://www.2daygeek.com/author/magesh/
+[b]: https://github.com/lujun9972
+[1]: https://www.2daygeek.com/yum-command-examples-manage-packages-rhel-centos-systems/
diff --git a/published/20190527 How to write a good C main function.md b/published/20190527 How to write a good C main function.md
new file mode 100644
index 0000000000..4f993ee777
--- /dev/null
+++ b/published/20190527 How to write a good C main function.md
@@ -0,0 +1,474 @@
+[#]: collector: (lujun9972)
+[#]: translator: (MjSeven)
+[#]: reviewer: (wxy)
+[#]: publisher: (wxy)
+[#]: url: (https://linux.cn/article-10949-1.html)
+[#]: subject: (How to write a good C main function)
+[#]: via: (https://opensource.com/article/19/5/how-write-good-c-main-function)
+[#]: author: (Erik O'Shaughnessy https://opensource.com/users/jnyjny)
+
+如何写好 C main 函数
+======
+
+> 学习如何构造一个 C 文件并编写一个 C main 函数来成功地处理命令行参数。
+
+
+
+我知道,现在孩子们用 Python 和 JavaScript 编写他们的疯狂“应用程序”。但是不要这么快就否定 C 语言 —— 它能够提供很多东西,并且简洁。如果你需要速度,用 C 语言编写可能就是你的答案。如果你正在寻找稳定的职业或者想学习如何捕获[空指针解引用][2],C 语言也可能是你的答案!在本文中,我将解释如何构造一个 C 文件并编写一个 C main 函数来成功地处理命令行参数。
+
+我:一个顽固的 Unix 系统程序员。
+
+你:一个有编辑器、C 编译器,并有时间打发的人。
+
+让我们开工吧。
+
+### 一个无聊但正确的 C 程序
+
+![Parody O'Reilly book cover, "Hating Other People's Code"][3]
+
+C 程序以 `main()` 函数开头,通常保存在名为 `main.c` 的文件中。
+
+```
+/* main.c */
+int main(int argc, char *argv[]) {
+
+}
+```
+
+这个程序可以*编译*但不*干*任何事。
+
+```
+$ gcc main.c
+$ ./a.out -o foo -vv
+$
+```
+
+正确但无聊。
+
+### main 函数是唯一的。
+
+`main()` 函数是开始执行时所执行的程序的第一个函数,但不是第一个执行的函数。*第一个*函数是 `_start()`,它通常由 C 运行库提供,在编译程序时自动链入。此细节高度依赖于操作系统和编译器工具链,所以我假装没有提到它。
+
+`main()` 函数有两个参数,通常称为 `argc` 和 `argv`,并返回一个有符号整数。大多数 Unix 环境都希望程序在成功时返回 `0`(零),失败时返回 `-1`(负一)。
+
+参数 | 名称 | 描述
+---|---|---
+`argc` | 参数个数 | 参数向量的个数
+`argv` | 参数向量 | 字符指针数组
+
+参数向量 `argv` 是调用你的程序的命令行的标记化表示形式。在上面的例子中,`argv` 将是以下字符串的列表:
+
+```
+argv = [ "/path/to/a.out", "-o", "foo", "-vv" ];
+```
+
+参数向量在其第一个索引 `argv[0]` 中确保至少会有一个字符串,这是执行程序的完整路径。
+
+### main.c 文件的剖析
+
+当我从头开始编写 `main.c` 时,它的结构通常如下:
+
+```
+/* main.c */
+/* 0 版权/许可证 */
+/* 1 包含 */
+/* 2 定义 */
+/* 3 外部声明 */
+/* 4 类型定义 */
+/* 5 全局变量声明 */
+/* 6 函数原型 */
+
+int main(int argc, char *argv[]) {
+/* 7 命令行解析 */
+}
+
+/* 8 函数声明 */
+```
+
+下面我将讨论这些编号的各个部分,除了编号为 0 的那部分。如果你必须把版权或许可文本放在源代码中,那就放在那里。
+
+另一件我不想讨论的事情是注释。
+
+```
+“评论谎言。”
+- 一个愤世嫉俗但聪明又好看的程序员。
+```
+
+与其使用注释,不如使用有意义的函数名和变量名。
+
+鉴于程序员固有的惰性,一旦添加了注释,维护负担就会增加一倍。如果更改或重构代码,则需要更新或扩充注释。随着时间的推移,代码会变得面目全非,与注释所描述的内容完全不同。
+
+如果你必须写注释,不要写关于代码正在做*什么*,相反,写下代码*为什么*要这样写。写一些你将要在五年后读到的注释,那时你已经将这段代码忘得一干二净。世界的命运取决于你。*不要有压力。*
+
+#### 1、包含
+
+我添加到 `main.c` 文件的第一个东西是包含文件,它们为程序提供大量标准 C 标准库函数和变量。C 标准库做了很多事情。浏览 `/usr/include` 中的头文件,你可以了解到它们可以做些什么。
+
+`#include` 字符串是 [C 预处理程序][4](cpp)指令,它会将引用的文件完整地包含在当前文件中。C 中的头文件通常以 `.h` 扩展名命名,且不应包含任何可执行代码。它只有宏、定义、类型定义、外部变量和函数原型。字符串 `` 告诉 cpp 在系统定义的头文件路径中查找名为 `header.h` 的文件,它通常在 `/usr/include` 目录中。
+
+```
+/* main.c */
+#include
+#include
+#include
+#include
+#include
+#include
+#include
+#include
+```
+
+这是我默认会全局包含的最小包含集合,它将引入:
+
+\#include 文件 | 提供的东西
+---|---
+stdio | 提供 `FILE`、`stdin`、`stdout`、`stderr` 和 `fprint()` 函数系列
+stdlib | 提供 `malloc()`、`calloc()` 和 `realloc()`
+unistd | 提供 `EXIT_FAILURE`、`EXIT_SUCCESS`
+libgen | 提供 `basename()` 函数
+errno | 定义外部 `errno` 变量及其可以接受的所有值
+string | 提供 `memcpy()`、`memset()` 和 `strlen()` 函数系列
+getopt | 提供外部 `optarg`、`opterr`、`optind` 和 `getopt()` 函数
+sys/types | 类型定义快捷方式,如 `uint32_t` 和 `uint64_t`
+
+#### 2、定义
+
+```
+/* main.c */
+<...>
+
+#define OPTSTR "vi:o:f:h"
+#define USAGE_FMT "%s [-v] [-f hexflag] [-i inputfile] [-o outputfile] [-h]"
+#define ERR_FOPEN_INPUT "fopen(input, r)"
+#define ERR_FOPEN_OUTPUT "fopen(output, w)"
+#define ERR_DO_THE_NEEDFUL "do_the_needful blew up"
+#define DEFAULT_PROGNAME "george"
+```
+
+这在现在没有多大意义,但 `OPTSTR` 定义我这里会说明一下,它是程序推荐的命令行开关。参考 [getopt(3)][5] man 页面,了解 `OPTSTR` 将如何影响 `getopt()` 的行为。
+
+`USAGE_FMT` 定义了一个 `printf()` 风格的格式字符串,它用在 `usage()` 函数中。
+
+我还喜欢将字符串常量放在文件的 `#define` 这一部分。如果需要,把它们收集在一起可以更容易地修正拼写、重用消息和国际化消息。
+
+最后,在命名 `#define` 时全部使用大写字母,以区别变量和函数名。如果需要,可以将单词放连在一起或使用下划线分隔,只要确保它们都是大写的就行。
+
+#### 3、外部声明
+
+```
+/* main.c */
+<...>
+
+extern int errno;
+extern char *optarg;
+extern int opterr, optind;
+```
+
+`extern` 声明将该名称带入当前编译单元的命名空间(即 “文件”),并允许程序访问该变量。这里我们引入了三个整数变量和一个字符指针的定义。`opt` 前缀的几个变量是由 `getopt()` 函数使用的,C 标准库使用 `errno` 作为带外通信通道来传达函数可能的失败原因。
+
+#### 4、类型定义
+
+```
+/* main.c */
+<...>
+
+typedef struct {
+ int verbose;
+ uint32_t flags;
+ FILE *input;
+ FILE *output;
+} options_t;
+```
+
+在外部声明之后,我喜欢为结构、联合和枚举声明 `typedef`。命名一个 `typedef` 是一种传统习惯。我非常喜欢使用 `_t` 后缀来表示该名称是一种类型。在这个例子中,我将 `options_t` 声明为一个包含 4 个成员的 `struct`。C 是一种空格无关的编程语言,因此我使用空格将字段名排列在同一列中。我只是喜欢它看起来的样子。对于指针声明,我在名称前面加上星号,以明确它是一个指针。
+
+#### 5、全局变量声明
+
+```
+/* main.c */
+<...>
+
+int dumb_global_variable = -11;
+```
+
+全局变量是一个坏主意,你永远不应该使用它们。但如果你必须使用全局变量,请在这里声明,并确保给它们一个默认值。说真的,*不要使用全局变量*。
+
+#### 6、函数原型
+
+```
+/* main.c */
+<...>
+
+void usage(char *progname, int opt);
+int do_the_needful(options_t *options);
+```
+
+在编写函数时,将它们添加到 `main()` 函数之后而不是之前,在这里放函数原型。早期的 C 编译器使用单遍策略,这意味着你在程序中使用的每个符号(变量或函数名称)必须在使用之前声明。现代编译器几乎都是多遍编译器,它们在生成代码之前构建一个完整的符号表,因此并不严格要求使用函数原型。但是,有时你无法选择代码要使用的编译器,所以请编写函数原型并继续这样做下去。
+
+当然,我总是包含一个 `usage()` 函数,当 `main()` 函数不理解你从命令行传入的内容时,它会调用这个函数。
+
+#### 7、命令行解析
+
+```
+/* main.c */
+<...>
+
+int main(int argc, char *argv[]) {
+ int opt;
+ options_t options = { 0, 0x0, stdin, stdout };
+
+ opterr = 0;
+
+ while ((opt = getopt(argc, argv, OPTSTR)) != EOF)
+ switch(opt) {
+ case 'i':
+ if (!(options.input = fopen(optarg, "r")) ){
+ perror(ERR_FOPEN_INPUT);
+ exit(EXIT_FAILURE);
+ /* NOTREACHED */
+ }
+ break;
+
+ case 'o':
+ if (!(options.output = fopen(optarg, "w")) ){
+ perror(ERR_FOPEN_OUTPUT);
+ exit(EXIT_FAILURE);
+ /* NOTREACHED */
+ }
+ break;
+
+ case 'f':
+ options.flags = (uint32_t )strtoul(optarg, NULL, 16);
+ break;
+
+ case 'v':
+ options.verbose += 1;
+ break;
+
+ case 'h':
+ default:
+ usage(basename(argv[0]), opt);
+ /* NOTREACHED */
+ break;
+ }
+
+ if (do_the_needful(&options) != EXIT_SUCCESS) {
+ perror(ERR_DO_THE_NEEDFUL);
+ exit(EXIT_FAILURE);
+ /* NOTREACHED */
+ }
+
+ return EXIT_SUCCESS;
+}
+```
+
+好吧,代码有点多。这个 `main()` 函数的目的是收集用户提供的参数,执行最基本的输入验证,然后将收集到的参数传递给使用它们的函数。这个示例声明一个使用默认值初始化的 `options` 变量,并解析命令行,根据需要更新 `options`。
+
+`main()` 函数的核心是一个 `while` 循环,它使用 `getopt()` 来遍历 `argv`,寻找命令行选项及其参数(如果有的话)。文件前面定义的 `OPTSTR` 是驱动 `getopt()` 行为的模板。`opt` 变量接受 `getopt()` 找到的任何命令行选项的字符值,程序对检测命令行选项的响应发生在 `switch` 语句中。
+
+如果你注意到了可能会问,为什么 `opt` 被声明为 32 位 `int`,但是预期是 8 位 `char`?事实上 `getopt()` 返回一个 `int`,当它到达 `argv` 末尾时取负值,我会使用 `EOF`(*文件末尾*标记)匹配。`char` 是有符号的,但我喜欢将变量匹配到它们的函数返回值。
+
+当检测到一个已知的命令行选项时,会发生特定的行为。在 `OPTSTR` 中指定一个以冒号结尾的参数,这些选项可以有一个参数。当一个选项有一个参数时,`argv` 中的下一个字符串可以通过外部定义的变量 `optarg` 提供给程序。我使用 `optarg` 来打开文件进行读写,或者将命令行参数从字符串转换为整数值。
+
+这里有几个关于代码风格的要点:
+
+ * 将 `opterr` 初始化为 `0`,禁止 `getopt` 触发 `?`。
+ * 在 `main()` 的中间使用 `exit(EXIT_FAILURE);` 或 `exit(EXIT_SUCCESS);`。
+ * `/* NOTREACHED */` 是我喜欢的一个 lint 指令。
+ * 在返回 int 类型的函数末尾使用 `return EXIT_SUCCESS;`。
+ * 显示强制转换隐式类型。
+
+这个程序的命令行格式,经过编译如下所示:
+
+```
+$ ./a.out -h
+a.out [-v] [-f hexflag] [-i inputfile] [-o outputfile] [-h]
+```
+
+事实上,在编译后 `usage()` 就会向 `stderr` 发出这样的内容。
+
+#### 8、函数声明
+
+```
+/* main.c */
+<...>
+
+void usage(char *progname, int opt) {
+ fprintf(stderr, USAGE_FMT, progname?progname:DEFAULT_PROGNAME);
+ exit(EXIT_FAILURE);
+ /* NOTREACHED */
+}
+
+int do_the_needful(options_t *options) {
+
+ if (!options) {
+ errno = EINVAL;
+ return EXIT_FAILURE;
+ }
+
+ if (!options->input || !options->output) {
+ errno = ENOENT;
+ return EXIT_FAILURE;
+ }
+
+ /* XXX do needful stuff */
+
+ return EXIT_SUCCESS;
+}
+```
+
+我最后编写的函数不是个样板函数。在本例中,函数 `do_the_needful()` 接受一个指向 `options_t` 结构的指针。我验证 `options` 指针不为 `NULL`,然后继续验证 `input` 和 `output` 结构成员。如果其中一个测试失败,返回 `EXIT_FAILURE`,并且通过将外部全局变量 `errno` 设置为常规错误代码,我可以告知调用者常规的错误原因。调用者可以使用便捷函数 `perror()` 来根据 `errno` 的值发出便于阅读的错误消息。
+
+函数几乎总是以某种方式验证它们的输入。如果完全验证代价很大,那么尝试执行一次并将验证后的数据视为不可变。`usage()` 函数使用 `fprintf()` 调用中的条件赋值验证 `progname` 参数。接下来 `usage()` 函数就退出了,所以我不会费心设置 `errno`,也不用操心是否使用正确的程序名。
+
+在这里,我要避免的最大错误是解引用 `NULL` 指针。这将导致操作系统向我的进程发送一个名为 `SYSSEGV` 的特殊信号,导致不可避免的死亡。用户最不希望看到的是由 `SYSSEGV` 而导致的崩溃。最好是捕获 `NULL` 指针以发出更合适的错误消息并优雅地关闭程序。
+
+有些人抱怨在函数体中有多个 `return` 语句,他们喋喋不休地说些“控制流的连续性”之类的东西。老实说,如果函数中间出现错误,那就应该返回这个错误条件。写一大堆嵌套的 `if` 语句只有一个 `return` 绝不是一个“好主意”™。
+
+最后,如果你编写的函数接受四个以上的参数,请考虑将它们绑定到一个结构中,并传递一个指向该结构的指针。这使得函数签名更简单,更容易记住,并且在以后调用时不会出错。它还可以使调用函数速度稍微快一些,因为需要复制到函数堆栈中的东西更少。在实践中,只有在函数被调用数百万或数十亿次时,才会考虑这个问题。如果认为这没有意义,那也无所谓。
+
+### 等等,你不是说没有注释吗!?!!
+
+在 `do_the_needful()` 函数中,我写了一种特殊类型的注释,它被是作为占位符设计的,而不是为了说明代码:
+
+```
+/* XXX do needful stuff */
+```
+
+当你写到这里时,有时你不想停下来编写一些特别复杂的代码,你会之后再写,而不是现在。那就是我留给自己再次回来的地方。我插入一个带有 `XXX` 前缀的注释和一个描述需要做什么的简短注释。之后,当我有更多时间的时候,我会在源代码中寻找 `XXX`。使用什么前缀并不重要,只要确保它不太可能在另一个上下文环境(如函数名或变量)中出现在你代码库里。
+
+### 把它们组合在一起
+
+好吧,当你编译这个程序后,它*仍然*几乎没有任何作用。但是现在你有了一个坚实的骨架来构建你自己的命令行解析 C 程序。
+
+```
+/* main.c - the complete listing */
+
+#include
+#include
+#include
+#include
+#include
+#include
+#include
+
+#define OPTSTR "vi:o:f:h"
+#define USAGE_FMT "%s [-v] [-f hexflag] [-i inputfile] [-o outputfile] [-h]"
+#define ERR_FOPEN_INPUT "fopen(input, r)"
+#define ERR_FOPEN_OUTPUT "fopen(output, w)"
+#define ERR_DO_THE_NEEDFUL "do_the_needful blew up"
+#define DEFAULT_PROGNAME "george"
+
+extern int errno;
+extern char *optarg;
+extern int opterr, optind;
+
+typedef struct {
+ int verbose;
+ uint32_t flags;
+ FILE *input;
+ FILE *output;
+} options_t;
+
+int dumb_global_variable = -11;
+
+void usage(char *progname, int opt);
+int do_the_needful(options_t *options);
+
+int main(int argc, char *argv[]) {
+ int opt;
+ options_t options = { 0, 0x0, stdin, stdout };
+
+ opterr = 0;
+
+ while ((opt = getopt(argc, argv, OPTSTR)) != EOF)
+ switch(opt) {
+ case 'i':
+ if (!(options.input = fopen(optarg, "r")) ){
+ perror(ERR_FOPEN_INPUT);
+ exit(EXIT_FAILURE);
+ /* NOTREACHED */
+ }
+ break;
+
+ case 'o':
+ if (!(options.output = fopen(optarg, "w")) ){
+ perror(ERR_FOPEN_OUTPUT);
+ exit(EXIT_FAILURE);
+ /* NOTREACHED */
+ }
+ break;
+
+ case 'f':
+ options.flags = (uint32_t )strtoul(optarg, NULL, 16);
+ break;
+
+ case 'v':
+ options.verbose += 1;
+ break;
+
+ case 'h':
+ default:
+ usage(basename(argv[0]), opt);
+ /* NOTREACHED */
+ break;
+ }
+
+ if (do_the_needful(&options) != EXIT_SUCCESS) {
+ perror(ERR_DO_THE_NEEDFUL);
+ exit(EXIT_FAILURE);
+ /* NOTREACHED */
+ }
+
+ return EXIT_SUCCESS;
+}
+
+void usage(char *progname, int opt) {
+ fprintf(stderr, USAGE_FMT, progname?progname:DEFAULT_PROGNAME);
+ exit(EXIT_FAILURE);
+ /* NOTREACHED */
+}
+
+int do_the_needful(options_t *options) {
+
+ if (!options) {
+ errno = EINVAL;
+ return EXIT_FAILURE;
+ }
+
+ if (!options->input || !options->output) {
+ errno = ENOENT;
+ return EXIT_FAILURE;
+ }
+
+ /* XXX do needful stuff */
+
+ return EXIT_SUCCESS;
+}
+```
+
+现在,你已经准备好编写更易于维护的 C 语言。如果你有任何问题或反馈,请在评论中分享。
+
+--------------------------------------------------------------------------------
+
+via: https://opensource.com/article/19/5/how-write-good-c-main-function
+
+作者:[Erik O'Shaughnessy][a]
+选题:[lujun9972][b]
+译者:[MjSeven](https://github.com/MjSeven)
+校对:[wxy](https://github.com/wxy)
+
+本文由 [LCTT](https://github.com/LCTT/TranslateProject) 原创编译,[Linux中国](https://linux.cn/) 荣誉推出
+
+[a]: https://opensource.com/users/jnyjny
+[b]: https://github.com/lujun9972
+[1]: https://opensource.com/sites/default/files/styles/image-full-size/public/lead-images/code_hand_draw.png?itok=dpAf--Db (Hand drawing out the word "code")
+[2]: https://www.owasp.org/index.php/Null_Dereference
+[3]: https://opensource.com/sites/default/files/uploads/hatingotherpeoplescode-big.png (Parody O'Reilly book cover, "Hating Other People's Code")
+[4]: https://en.wikipedia.org/wiki/C_preprocessor
+[5]: https://linux.die.net/man/3/getopt
+[6]: http://www.opengroup.org/onlinepubs/009695399/functions/fopen.html
+[7]: http://www.opengroup.org/onlinepubs/009695399/functions/perror.html
+[8]: http://www.opengroup.org/onlinepubs/009695399/functions/exit.html
+[9]: http://www.opengroup.org/onlinepubs/009695399/functions/strtoul.html
+[10]: http://www.opengroup.org/onlinepubs/009695399/functions/fprintf.html
diff --git a/published/20190529 NVMe on Linux.md b/published/20190529 NVMe on Linux.md
new file mode 100644
index 0000000000..374d3ef2f2
--- /dev/null
+++ b/published/20190529 NVMe on Linux.md
@@ -0,0 +1,68 @@
+[#]: collector: (lujun9972)
+[#]: translator: (warmfrog)
+[#]: reviewer: (wxy)
+[#]: publisher: (wxy)
+[#]: url: (https://linux.cn/article-10946-1.html)
+[#]: subject: (NVMe on Linux)
+[#]: via: (https://www.networkworld.com/article/3397006/nvme-on-linux.html)
+[#]: author: (Sandra Henry-Stocker https://www.networkworld.com/author/Sandra-Henry_Stocker/)
+
+Linux 上的 NVMe
+===============
+
+> 如果你还没注意到,一些极速的固态磁盘技术已经可以用在 Linux 和其他操作系统上了。
+
+![Sandra Henry-Stocker][1]
+
+NVMe 意即非易失性内存主机控制器接口规范,它是一个主机控制器接口和存储协议,用于加速企业和客户端系统以及固态驱动器(SSD)之间的数据传输。它通过电脑的高速 PCIe 总线工作。每当我看到这些名词时,我的感受是“羡慕”。而羡慕的原因很重要。
+
+使用 NVMe,数据传输的速度比旋转磁盘快很多。事实上,NVMe 驱动能够比 SATA SSD 快 7 倍。这比我们今天很多人用的固态硬盘快了 7 倍多。这意味着,如果你用一个 NVMe 驱动盘作为启动盘,你的系统能够启动的非常快。事实上,如今任何人买一个新的系统可能都不会考虑那些没有自带 NVMe 的,不管是服务器或者个人电脑。
+
+### NVMe 在 Linux 下能工作吗?
+
+是的!NVMe 自 Linux 内核 3.3 版本就支持了。然而,要升级系统,通常同时需要一个 NVMe 控制器和一个 NVMe 磁盘。一些外置磁盘也行,但是要连接到系统上,需要的可不仅仅是通用的 USB 接口。
+
+先使用下列命令检查内核版本:
+
+```
+$ uname -r
+5.0.0-15-generic
+```
+
+如果你的系统已经用了 NVMe,你将看到一个设备(例如,`/dev/nvme0`),但是只有在你安装了 NVMe 控制器的情况下才显示。如果你没有 NVMe 控制器,你可以用下列命令获取使用 NVMe 的相关信息。
+
+```
+$ modinfo nvme | head -6
+filename: /lib/modules/5.0.0-15-generic/kernel/drivers/nvme/host/nvme.ko
+version: 1.0
+license: GPL
+author: Matthew Wilcox
+srcversion: AA383008D5D5895C2E60523
+alias: pci:v0000106Bd00002003sv*sd*bc*sc*i*
+```
+
+### 了解更多
+
+如果你想了解极速的 NVMe 存储的更多细节,可在 [PCWorld][3] 获取。
+
+规范、白皮书和其他资源可在 [NVMexpress.org][4] 获取。
+
+--------------------------------------------------------------------------------
+
+via: https://www.networkworld.com/article/3397006/nvme-on-linux.html
+
+作者:[Sandra Henry-Stocker][a]
+选题:[lujun9972][b]
+译者:[warmfrog](https://github.com/warmfrog)
+校对:[wxy](https://github.com/wxy)
+
+本文由 [LCTT](https://github.com/LCTT/TranslateProject) 原创编译,[Linux中国](https://linux.cn/) 荣誉推出
+
+[a]: https://www.networkworld.com/author/Sandra-Henry_Stocker/
+[b]: https://github.com/lujun9972
+[1]: https://images.idgesg.net/images/article/2019/05/nvme-100797708-large.jpg
+[2]: https://www.networkworld.com/slideshow/153439/linux-best-desktop-distros-for-newbies.html#tk.nww-infsb
+[3]: https://www.pcworld.com/article/2899351/everything-you-need-to-know-about-nvme.html
+[4]: https://nvmexpress.org/
+[5]: https://www.facebook.com/NetworkWorld/
+[6]: https://www.linkedin.com/company/network-world
diff --git a/published/20190531 Unity Editor is Now Officially Available for Linux.md b/published/20190531 Unity Editor is Now Officially Available for Linux.md
new file mode 100644
index 0000000000..7b579caf06
--- /dev/null
+++ b/published/20190531 Unity Editor is Now Officially Available for Linux.md
@@ -0,0 +1,89 @@
+[#]: collector: (lujun9972)
+[#]: translator: (geekpi)
+[#]: reviewer: (wxy)
+[#]: publisher: (wxy)
+[#]: url: (https://linux.cn/article-10974-1.html)
+[#]: subject: (Unity Editor is Now Officially Available for Linux)
+[#]: via: (https://itsfoss.com/unity-editor-linux/)
+[#]: author: (Ankush Das https://itsfoss.com/author/ankush/)
+
+Unity 编辑器现已正式面向 Linux 推出
+======
+
+如果你是设计师、开发者或艺术家,你可能一直在使用 Linux 上的实验性 [Unity 编辑器][1]。然而,不能一直用实验性版本 —— 开发者需要一个完整稳定的工作经验。
+
+因此,他们最近宣布你可以在 Linux 上使用完整功能的 Unity 编辑器了。
+
+虽然这是一个令人兴奋的消息,但它正式支持哪些 Linux 发行版?我们来谈谈更多细节……
+
+> 非 FOSS 警告
+
+> Linux (或任何其他平台)上的 Unity 编辑器不是开源软件。我们在这里介绍它是因为:
+
+### 官方支持 Ubuntu 和 CentOS 7
+
+![][2]
+
+无论你拥有个人许可还是专业许可,如果你安装了 Unity 2019.1 或更高版本,都可以使用该编辑器。
+
+此外,他们优先支持 Ubuntu 16.04、Ubuntu 18.04 和 CentOS 7。
+
+在[公告][3]中,他们还提到了支持的配置:
+
+* x86-64 架构
+* 运行在 X11 窗口系统之上的 Gnome 桌面环境
+* Nvidia 官方专有显卡驱动和 AMD Mesa 显卡驱动
+* 桌面计算机,在没有仿真或兼容层的设备/硬件上运行
+
+你可以尝试其他的 —— 但最好坚持官方要求以获得最佳体验。
+
+> 关于第三方工具的说明
+
+> 如果你碰巧在某个项目中使用了任何第三方工具,那么必须单独检查它们是否支持。
+
+### 如何在 Linux 上安装 Unity 编辑器
+
+现在你已经了解了,那么该如何安装?
+
+要安装 Unity,你需要下载并安装 [Unity Hub][4]。
+
+![Unity Hub][5]
+
+你需要完成以下步骤:
+
+* 从[官方论坛页面][4]下载适用于 Linux 的 Unity Hub。
+* 它将下载一个 AppImage 文件。简单地说,让它可执行并运行它。如果你不了解,你应该查看关于[如何在 Linux 上使用 AppImage][6] 的指南。
+* 启动 Unity Hub 后,它会要求你使用 Unity ID 登录(或注册)以激活许可证。有关许可证生效的更多信息,请参阅他们的 [FAQ 页面][7]。
+* 使用 Unity ID 登录后,进入 “Installs” 选项(如上图所示)并添加所需的版本/组件。
+
+就是这些了。这就是获取并快速安装的最佳方法。
+
+### 总结
+
+即使这是一个令人兴奋的消息,但官方配置支持似乎并不广泛。如果你在 Linux 上使用它,请在[他们的 Linux 论坛帖子][9]上分享你的反馈和意见。
+
+你觉得怎么样?此外,你是使用 Unity Hub 安装它,还是有更好的方法来安装?
+
+请在下面的评论中告诉我们你的想法。
+
+--------------------------------------------------------------------------------
+
+via: https://itsfoss.com/unity-editor-linux/
+
+作者:[Ankush Das][a]
+选题:[lujun9972][b]
+译者:[geekpi](https://github.com/geekpi)
+校对:[wxy](https://github.com/wxy)
+
+本文由 [LCTT](https://github.com/LCTT/TranslateProject) 原创编译,[Linux中国](https://linux.cn/) 荣誉推出
+
+[a]: https://itsfoss.com/author/ankush/
+[b]: https://github.com/lujun9972
+[1]: https://unity3d.com/unity/editor
+[2]: https://i2.wp.com/itsfoss.com/wp-content/uploads/2019/05/Unity-Editor-on-Linux.png?resize=800%2C450&ssl=1
+[3]: https://blogs.unity3d.com/2019/05/30/announcing-the-unity-editor-for-linux/
+[4]: https://forum.unity.com/threads/unity-hub-v-1-6-0-is-now-available.640792/
+[5]: https://i2.wp.com/itsfoss.com/wp-content/uploads/2019/05/unity-hub.jpg?fit=800%2C532&ssl=1
+[6]: https://itsfoss.com/use-appimage-linux/
+[7]: https://support.unity3d.com/hc/en-us/categories/201268913-Licenses
+[9]: https://forum.unity.com/forums/linux-editor.93/
diff --git a/published/20190531 Why translation platforms matter.md b/published/20190531 Why translation platforms matter.md
new file mode 100644
index 0000000000..92cdbb20b1
--- /dev/null
+++ b/published/20190531 Why translation platforms matter.md
@@ -0,0 +1,87 @@
+[#]: collector: (lujun9972)
+[#]: translator: (wxy)
+[#]: reviewer: (wxy)
+[#]: publisher: (wxy)
+[#]: url: (https://linux.cn/article-10953-1.html)
+[#]: subject: (Why translation platforms matter)
+[#]: via: (https://opensource.com/article/19/5/translation-platforms)
+[#]: author: (Jean-Baptiste Holcroft https://opensource.com/users/jibec/users/annegentle/users/bcotton)
+
+什么是翻译平台最重要的地方?
+======
+
+> 技术上的考虑并不是判断一个好的翻译平台的最佳方式。
+
+
+
+语言翻译可以使开源软件能够被世界各地的人们使用,这是非开发人员参与他们喜欢的(开源)项目的好方法。有许多[翻译工具][2],你可以根据他们处理翻译中涉及的主要功能区域的能力来评估:技术交互能力、团队支持能力和翻译支持能力。
+
+技术交互方面包括:
+
+* 支持的文件格式
+* 与开源存储库的同步
+* 自动化支持工具
+* 接口可能性
+
+对团队合作(也可称为“社区活力”)的支持包括该平台如何:
+
+* 监控变更(按译者、项目等)
+* 跟进由项目推动的更新
+* 显示进度状态
+* 是否启用审核和验证步骤
+* 协助(来自同一团队和跨语言的)翻译人员和项目维护人员之间的讨论
+* 平台支持的全球通讯(新闻等)
+
+翻译协助包括:
+
+* 清晰、符合人体工程学的界面
+* 简单几步就可以找到项目并开始工作
+* 可以简单地了解到翻译和分发之间流程
+* 可以使用翻译记忆机
+* 词汇表丰富
+
+前两个功能区域与源代码管理平台的差别不大,只有一些小的差别。我觉得最后一个区域也主要与源代码有关。但是,它们处理的数据非常不同,翻译平台的用户通常也不如开发人员了解技术,而数量也更多。
+
+### 我的推荐
+
+在我看来,GNOME 平台提供了最好的翻译平台,原因如下:
+
+* 其网站包含了团队组织和翻译平台。很容易看出谁在负责以及他们在团队中的角色。一切都集中在几个屏幕之内。
+* 很容易找到要处理的内容,并且你会很快意识到你必须将文件下载到本地计算机并在修改后将其发回。这个流程不是很先进,但逻辑很容易理解。
+* 一旦你发回文件,平台就可以向邮件列表发送通告,以便团队知道后续步骤,并且可以全局轻松讨论翻译(而不是评论特定句子)。
+* 它支持多达 297 种语言。
+* 它显示了基本句子、高级菜单和文档的明确的进度百分比。
+
+再加上可预测的 GNOME 发布计划,社区可以使用一切可以促进社区工作的工具。
+
+如果我们看看 Debian 翻译团队,他们多年来一直在为 Debian (LCTT 译注:此处原文是“Fedora”,疑为笔误)翻译了难以想象的大量内容(尤其是新闻),我们看到他们有一个高度以来于规则的翻译流程,完全基于电子邮件,手动推送到存储库。该团队还将所有内容都放在流程中,而不是工具中,尽管这似乎需要相当大的技术能力,但它已成为领先的语言群体之一,已经运作多年。
+
+我认为,成功的翻译平台的主要问题不是基于单一的(技术、翻译)工作的能力,而是基于如何构建和支持翻译团队的流程。这就是可持续性的原因。
+
+生产过程是构建团队最重要的方式;通过正确地将它们组合在一起,新手很容易理解该过程是如何工作的,采用它们,并将它们解释给下一组新人。
+
+要建立一个可持续发展的社区,首先要考虑的是支持协同工作的工具,然后是可用性。
+
+这解释了我为什么对 [Zanata][3] 工具沮丧,从技术和界面的角度来看,这是有效的,但在帮助构建社区方面却很差。我认为翻译是一个社区驱动的过程(可能是开源软件开发中最受社区驱动的过程之一),这对我来说是一个关键问题。
+
+* * *
+
+本文改编自“[什么是一个好的翻译平台?][4]”,最初发表在 Jibec 期刊上,并经许可重复使用。
+
+--------------------------------------------------------------------------------
+
+via: https://opensource.com/article/19/5/translation-platforms
+
+作者:[Jean-Baptiste Holcroft][a]
+选题:[lujun9972][b]
+译者:[wxy](https://github.com/wxy)
+校对:[wxy](https://github.com/wxy)
+
+本文由 [LCTT](https://github.com/LCTT/TranslateProject) 原创编译,[Linux中国](https://linux.cn/) 荣誉推出
+
+[a]: https://opensource.com/users/jibec/users/annegentle/users/bcotton
+[b]: https://github.com/lujun9972
+[1]: https://opensource.com/sites/default/files/styles/image-full-size/public/lead-images/people_remote_teams_world.png?itok=_9DCHEel
+[2]: https://opensource.com/article/17/6/open-source-localization-tools
+[3]: http://zanata.org/
+[4]: https://jibecfed.fedorapeople.org/blog-hugo/en/2016/09/whats-a-good-translation-platform/
diff --git a/published/20190604 How To Verify NTP Setup (Sync) is Working or Not In Linux.md b/published/20190604 How To Verify NTP Setup (Sync) is Working or Not In Linux.md
new file mode 100644
index 0000000000..4c28227f63
--- /dev/null
+++ b/published/20190604 How To Verify NTP Setup (Sync) is Working or Not In Linux.md
@@ -0,0 +1,145 @@
+[#]: collector: (lujun9972)
+[#]: translator: (wxy)
+[#]: reviewer: (wxy)
+[#]: publisher: (wxy)
+[#]: url: (https://linux.cn/article-10951-1.html)
+[#]: subject: (How To Verify NTP Setup (Sync) is Working or Not In Linux?)
+[#]: via: (https://www.2daygeek.com/check-verify-ntp-sync-is-working-or-not-in-linux-using-ntpq-ntpstat-timedatectl/)
+[#]: author: (Magesh Maruthamuthu https://www.2daygeek.com/author/magesh/)
+
+如何在 Linux 下确认 NTP 是否同步?
+======
+
+
+
+NTP 意即网络时间协议,它通过网络同步计算机系统之间的时钟。NTP 服务器可以使组织中的所有服务器保持同步,以准确时间执行基于时间的作业。NTP 客户端会将其时钟与 NTP 服务器同步。
+
+我们已经写了一篇关于 NTP 服务器和客户端安装和配置的文章。如果你想查看这些文章,请导航至以下链接。
+
+ * [如何在 Linux 上安装、配置 NTP 服务器和客户端?][1]
+ * [如何安装和配置 Chrony 作为 NTP 客户端?][2]
+
+我假设我你经使用上述链接设置了 NTP 服务器和 NTP 客户端。现在,如何验证 NTP 设置是否正常工作?
+
+Linux 中有三个命令可用于验证 NTP 同步情况。详情如下。在本文中,我们将告诉您如何使用所有这些命令验证 NTP 同步。
+
+ * `ntpq`:ntpq 是一个标准的 NTP 查询程序。
+ * `ntpstat`:显示网络世界同步状态。
+ * `timedatectl`:它控制 systemd 系统中的系统时间和日期。
+
+### 方法 1:如何使用 ntpq 命令检查 NTP 状态?
+
+`ntpq` 实用程序用于监视 NTP 守护程序 `ntpd` 的操作并确定性能。
+
+该程序可以以交互模式运行,也可以使用命令行参数进行控制。它通过向服务器发送多个查询来打印出连接的对等项列表。如果 NTP 正常工作,你将获得类似于下面的输出。
+
+```
+# ntpq -p
+
+ remote refid st t when poll reach delay offset jitter
+==============================================================================
+*CentOS7.2daygee 133.243.238.163 2 u 14 64 37 0.686 0.151 16.432
+```
+
+细节:
+
+* `-p`:打印服务器已知的对等项列表以及其状态摘要。
+
+### 方法 2:如何使用 ntpstat 命令检查 NTP 状态?
+
+`ntpstat` 将报告在本地计算机上运行的 NTP 守护程序(`ntpd`)的同步状态。如果发现本地系统与参考时间源保持同步,则 `ntpstat` 将报告大致的时间精度。
+
+`ntpstat` 命令根据 NTP 同步状态返回三种状态码。详情如下。
+
+* `0`:如果时钟同步则返回 0。
+* `1`:如果时钟不同步则返回 1。
+* `2`:如果时钟状态不确定,则返回 2,例如 ntpd 不可联系时。
+
+```
+# ntpstat
+
+synchronised to NTP server (192.168.1.8) at stratum 3
+ time correct to within 508 ms
+ polling server every 64 s
+```
+
+### 方法 3:如何使用 timedatectl 命令检查 NTP 状态?
+
+[timedatectl 命令][3]用于查询和更改系统时钟及其在 systmed 系统中的设置。
+
+```
+# timedatectl
+或
+# timedatectl status
+
+ Local time: Thu 2019-05-30 05:01:05 CDT
+ Universal time: Thu 2019-05-30 10:01:05 UTC
+ RTC time: Thu 2019-05-30 10:01:05
+ Time zone: America/Chicago (CDT, -0500)
+ NTP enabled: yes
+NTP synchronized: yes
+ RTC in local TZ: no
+ DST active: yes
+ Last DST change: DST began at
+ Sun 2019-03-10 01:59:59 CST
+ Sun 2019-03-10 03:00:00 CDT
+ Next DST change: DST ends (the clock jumps one hour backwards) at
+ Sun 2019-11-03 01:59:59 CDT
+ Sun 2019-11-03 01:00:00 CST
+```
+
+### 更多技巧
+
+Chrony 是一个 NTP 客户端的替代品。它可以更快地同步系统时钟,时间精度更高,对于一直不在线的系统尤其有用。
+
+chronyd 较小,它使用较少的内存,只在必要时才唤醒 CPU,这样可以更好地节省电能。即使网络拥塞较长时间,它也能很好地运行。
+
+你可以使用以下任何命令来检查 Chrony 状态。
+
+检查 Chrony 跟踪状态。
+
+```
+# chronyc tracking
+
+Reference ID : C0A80105 (CentOS7.2daygeek.com)
+Stratum : 3
+Ref time (UTC) : Thu Mar 28 05:57:27 2019
+System time : 0.000002545 seconds slow of NTP time
+Last offset : +0.001194361 seconds
+RMS offset : 0.001194361 seconds
+Frequency : 1.650 ppm fast
+Residual freq : +184.101 ppm
+Skew : 2.962 ppm
+Root delay : 0.107966967 seconds
+Root dispersion : 1.060455322 seconds
+Update interval : 2.0 seconds
+Leap status : Normal
+```
+
+运行 `sources` 命令以显示有关当前时间源的信息。
+
+```
+# chronyc sources
+
+210 Number of sources = 1
+MS Name/IP address Stratum Poll Reach LastRx Last sample
+===============================================================================
+^* CentOS7.2daygeek.com 2 6 17 62 +36us[+1230us] +/- 1111ms
+```
+
+--------------------------------------------------------------------------------
+
+via: https://www.2daygeek.com/check-verify-ntp-sync-is-working-or-not-in-linux-using-ntpq-ntpstat-timedatectl/
+
+作者:[Magesh Maruthamuthu][a]
+选题:[lujun9972][b]
+译者:[wxy](https://github.com/wxy)
+校对:[wxy](https://github.com/wxy)
+
+本文由 [LCTT](https://github.com/LCTT/TranslateProject) 原创编译,[Linux中国](https://linux.cn/) 荣誉推出
+
+[a]: https://www.2daygeek.com/author/magesh/
+[b]: https://github.com/lujun9972
+[1]: https://linux.cn/article-10811-1.html
+[2]: https://linux.cn/article-10820-1.html
+[3]: https://www.2daygeek.com/change-set-time-date-and-timezone-on-linux/
diff --git a/published/20190604 Two Methods To Check Or List Installed Security Updates on Redhat (RHEL) And CentOS System.md b/published/20190604 Two Methods To Check Or List Installed Security Updates on Redhat (RHEL) And CentOS System.md
new file mode 100644
index 0000000000..97cb82380d
--- /dev/null
+++ b/published/20190604 Two Methods To Check Or List Installed Security Updates on Redhat (RHEL) And CentOS System.md
@@ -0,0 +1,164 @@
+[#]: collector: (lujun9972)
+[#]: translator: (geekpi)
+[#]: reviewer: (wxy)
+[#]: publisher: (wxy)
+[#]: url: (https://linux.cn/article-10960-1.html)
+[#]: subject: (Two Methods To Check Or List Installed Security Updates on Redhat (RHEL) And CentOS System)
+[#]: via: (https://www.2daygeek.com/check-installed-security-updates-on-redhat-rhel-and-centos-system/)
+[#]: author: (Magesh Maruthamuthu https://www.2daygeek.com/author/magesh/)
+
+在 RHEL 和 CentOS 上检查或列出已安装的安全更新的两种方法
+======
+
+
+
+我们过去曾写过两篇关于这个主题的文章,每篇文章都是根据不同的要求发表的。如果你想在开始之前浏览这些文章。请通过以下链接:
+
+* [如何检查 RHEL 和 CentOS 上的可用安全更新?][1]
+* [在 RHEL 和 CentOS 上安装安全更新的四种方法?][2]
+
+这些文章与其他文章相互关联,因此,在深入研究之前,最好先阅读这些文章。
+
+在本文中,我们将向你展示如何检查已安装的安全更新。我会介绍两种方法,你可以选择最适合你的。
+
+此外,我还添加了一个小的 shell 脚本,它为你提供已安装的安全包计数。
+
+运行以下命令获取系统上已安装的安全更新的列表。
+
+```
+# yum updateinfo list security installed
+
+Loaded plugins: changelog, package_upload, product-id, search-disabled-repos,
+ : subscription-manager, verify, versionlock
+RHSA-2015:2315 Moderate/Sec. ModemManager-glib-1.1.0-8.git20130913.el7.x86_64
+RHSA-2015:2315 Moderate/Sec. NetworkManager-1:1.0.6-27.el7.x86_64
+RHSA-2016:2581 Low/Sec. NetworkManager-1:1.4.0-12.el7.x86_64
+RHSA-2017:2299 Moderate/Sec. NetworkManager-1:1.8.0-9.el7.x86_64
+RHSA-2015:2315 Moderate/Sec. NetworkManager-adsl-1:1.0.6-27.el7.x86_64
+RHSA-2016:2581 Low/Sec. NetworkManager-adsl-1:1.4.0-12.el7.x86_64
+RHSA-2017:2299 Moderate/Sec. NetworkManager-adsl-1:1.8.0-9.el7.x86_64
+RHSA-2015:2315 Moderate/Sec. NetworkManager-bluetooth-1:1.0.6-27.el7.x86_64
+```
+
+要计算已安装的安全包的数量,请运行以下命令:
+
+```
+# yum updateinfo list security installed | wc -l
+1046
+```
+
+仅打印安装包列表:
+
+```
+# yum updateinfo list security all | grep -w "i"
+
+i RHSA-2015:2315 Moderate/Sec. ModemManager-glib-1.1.0-8.git20130913.el7.x86_64
+i RHSA-2015:2315 Moderate/Sec. NetworkManager-1:1.0.6-27.el7.x86_64
+i RHSA-2016:2581 Low/Sec. NetworkManager-1:1.4.0-12.el7.x86_64
+i RHSA-2017:2299 Moderate/Sec. NetworkManager-1:1.8.0-9.el7.x86_64
+i RHSA-2015:2315 Moderate/Sec. NetworkManager-adsl-1:1.0.6-27.el7.x86_64
+i RHSA-2016:2581 Low/Sec. NetworkManager-adsl-1:1.4.0-12.el7.x86_64
+i RHSA-2017:2299 Moderate/Sec. NetworkManager-adsl-1:1.8.0-9.el7.x86_64
+i RHSA-2015:2315 Moderate/Sec. NetworkManager-bluetooth-1:1.0.6-27.el7.x86_64
+i RHSA-2016:2581 Low/Sec. NetworkManager-bluetooth-1:1.4.0-12.el7.x86_64
+i RHSA-2017:2299 Moderate/Sec. NetworkManager-bluetooth-1:1.8.0-9.el7.x86_64
+i RHSA-2015:2315 Moderate/Sec. NetworkManager-config-server-1:1.0.6-27.el7.x86_64
+i RHSA-2016:2581 Low/Sec. NetworkManager-config-server-1:1.4.0-12.el7.x86_64
+i RHSA-2017:2299 Moderate/Sec. NetworkManager-config-server-1:1.8.0-9.el7.noarch
+```
+
+要计算已安装的安全包的数量,请运行以下命令:
+
+```
+# yum updateinfo list security all | grep -w "i" | wc -l
+1043
+```
+
+或者,你可以检查指定包修复的漏洞列表。
+
+在此例中,我们将检查 “openssh” 包中已修复的漏洞列表:
+
+```
+# rpm -q --changelog openssh | grep -i CVE
+
+- Fix for CVE-2017-15906 (#1517226)
+- CVE-2015-8325: privilege escalation via user's PAM environment and UseLogin=yes (#1329191)
+- CVE-2016-1908: possible fallback from untrusted to trusted X11 forwarding (#1298741)
+- CVE-2016-3115: missing sanitisation of input for X11 forwarding (#1317819)
+- prevents CVE-2016-0777 and CVE-2016-0778
+- Security fixes released with openssh-6.9 (CVE-2015-5352) (#1247864)
+- only query each keyboard-interactive device once (CVE-2015-5600) (#1245971)
+- add new option GSSAPIEnablek5users and disable using ~/.k5users by default CVE-2014-9278
+- prevent a server from skipping SSHFP lookup - CVE-2014-2653 (#1081338)
+- change default value of MaxStartups - CVE-2010-5107 (#908707)
+- CVE-2010-4755
+- merged cve-2007_3102 to audit patch
+- fixed audit log injection problem (CVE-2007-3102)
+- CVE-2006-5794 - properly detect failed key verify in monitor (#214641)
+- CVE-2006-4924 - prevent DoS on deattack detector (#207957)
+- CVE-2006-5051 - don't call cleanups from signal handler (#208459)
+- use fork+exec instead of system in scp - CVE-2006-0225 (#168167)
+```
+
+同样,你可以通过运行以下命令来检查相应的包中是否修复了指定的漏洞:
+
+```
+# rpm -q --changelog openssh | grep -i CVE-2016-3115
+
+- CVE-2016-3115: missing sanitisation of input for X11 forwarding (#1317819)
+```
+
+### 如何使用 Shell 脚本计算安装的安全包?
+
+我添加了一个小的 shell 脚本,它可以帮助你计算已安装的安全包列表。
+
+```
+# vi /opt/scripts/security-check.sh
+
+#!/bin/bash
+echo "+-------------------------+"
+echo "|Security Advisories Count|"
+echo "+-------------------------+"
+for i in Important Moderate Low
+do
+sec=$(yum updateinfo list security installed | grep $i | wc -l)
+echo "$i: $sec"
+done | column -t
+echo "+-------------------------+"
+```
+
+给 `security-check.sh` 文件执行权限。
+
+```
+$ chmod +x security-check.sh
+```
+
+最后执行脚本统计。
+
+```
+# sh /opt/scripts/security-check.sh
+
++-------------------------+
+|Security Advisories Count|
++-------------------------+
+Important: 480
+Moderate: 410
+Low: 111
++-------------------------+
+```
+
+--------------------------------------------------------------------------------
+
+via: https://www.2daygeek.com/check-installed-security-updates-on-redhat-rhel-and-centos-system/
+
+作者:[Magesh Maruthamuthu][a]
+选题:[lujun9972][b]
+译者:[geekpi](https://github.com/geekpi)
+校对:[wxy](https://github.com/wxy)
+
+本文由 [LCTT](https://github.com/LCTT/TranslateProject) 原创编译,[Linux中国](https://linux.cn/) 荣誉推出
+
+[a]: https://www.2daygeek.com/author/magesh/
+[b]: https://github.com/lujun9972
+[1]: https://linux.cn/article-10938-1.html
+[2]: https://www.2daygeek.com/install-security-updates-on-redhat-rhel-centos-system/
diff --git a/published/20190607 5 reasons to use Kubernetes.md b/published/20190607 5 reasons to use Kubernetes.md
new file mode 100644
index 0000000000..8de8d3ad4a
--- /dev/null
+++ b/published/20190607 5 reasons to use Kubernetes.md
@@ -0,0 +1,68 @@
+[#]: collector: (lujun9972)
+[#]: translator: (geekpi)
+[#]: reviewer: (wxy)
+[#]: publisher: (wxy)
+[#]: url: (https://linux.cn/article-10973-1.html)
+[#]: subject: (5 reasons to use Kubernetes)
+[#]: via: (https://opensource.com/article/19/6/reasons-kubernetes)
+[#]: author: (Daniel Oh https://opensource.com/users/daniel-oh)
+
+使用 Kubernetes 的 5 个理由
+======
+
+> Kubernetes 解决了一些开发和运维团队每天关注的的常见问题。
+
+
+
+[Kubernetes][2](K8S)是面向企业的开源容器编排工具的事实标准。它提供了应用部署、扩展、容器管理和其他功能,使企业能够通过容错能力快速优化硬件资源利用率并延长生产环境运行时间。该项目最初由谷歌开发,并将该项目捐赠给[云原生计算基金会][3](CNCF)。2018 年,它成为第一个从 CNCF [毕业][4]的项目。
+
+这一切都很好,但它并不能解释为什么开发者和运维人员应该在 Kubernetes 上投入宝贵的时间和精力。Kubernetes 之所以如此有用,是因为它有助于开发者和运维人员迅速解决他们每天都在努力解决的问题。
+
+以下是 Kubernetes 帮助开发者和运维人员解决他们最常见问题的五种能力。
+
+### 1、厂商无关
+
+许多公有云提供商不仅提供托管 Kubernetes 服务,还提供许多基于这些服务构建的云产品,来用于本地应用容器编排。由于与供应商无关,使运营商能够轻松、安全地设计、构建和管理多云和混合云平台,而不会有供应商锁定的风险。Kubernetes 还消除了运维团队对复杂的多云/混合云战略的担忧。
+
+### 2、服务发现
+
+为了开发微服务应用,Java 开发人员必须控制服务可用性(就应用是否可以提供服务而言),并确保服务持续存在,以响应客户端的请求,而没有任何例外。Kubernetes 的[服务发现功能][5]意味着开发人员不再需要自己管理这些东西。
+
+### 3、触发
+
+你的 DevOps 会如何在上千台虚拟机上部署多语言、云原生应用?理想情况下,开发和运维会在 bug 修复、功能增强、新功能、安全更新时触发部署。Kubernetes 的[部署功能][6]会自动化这个日常工作。更重要的时,它支持高级部署策略,例如[蓝绿部署和金丝雀部署][7]。
+
+### 4、可伸缩性
+
+自动扩展是处理云环境中大量工作负载所需的关键功能。通过构建容器平台,你可以为终端用户提高系统可靠性。[Kubernetes Horizontal Pod Autoscaler][8](HPA)允许一个集群增加或减少应用程序(或 Pod)的数量,以应对峰值流量或性能峰值,从而减少对意外系统中断的担忧。
+
+### 5、容错性
+
+在现代应用体系结构中,应考虑故障处理代码来控制意外错误并快速从中恢复。但是开发人员需要花费大量的时间和精力来模拟偶然的错误。Kubernetes 的 [ReplicaSet][9] 通过确保指定数量的 Pod 持续保持活动来帮助开发人员解决此问题。
+
+### 结论
+
+Kubernetes 使企业能够轻松、快速、安全地解决常见的开发和运维问题。它还提供其他好处,例如构建无缝的多云/混合云战略,节省基础架构成本以及加快产品上市时间。
+
+--------------------------------------------------------------------------------
+
+via: https://opensource.com/article/19/6/reasons-kubernetes
+
+作者:[Daniel Oh][a]
+选题:[lujun9972][b]
+译者:[geekpi](https://github.com/geekpi)
+校对:[wxy](https://github.com/wxy)
+
+本文由 [LCTT](https://github.com/LCTT/TranslateProject) 原创编译,[Linux中国](https://linux.cn/) 荣誉推出
+
+[a]: https://opensource.com/users/daniel-oh
+[b]: https://github.com/lujun9972
+[1]: https://opensource.com/sites/default/files/styles/image-full-size/public/lead-images/ship_wheel_gear_devops_kubernetes.png?itok=xm4a74Kv
+[2]: https://opensource.com/resources/what-is-kubernetes
+[3]: https://www.cncf.io/projects/
+[4]: https://www.cncf.io/blog/2018/03/06/kubernetes-first-cncf-project-graduate/
+[5]: https://kubernetes.io/docs/concepts/services-networking/service/
+[6]: https://kubernetes.io/docs/concepts/workloads/controllers/deployment/
+[7]: https://opensource.com/article/17/5/colorful-deployments
+[8]: https://kubernetes.io/docs/tasks/run-application/horizontal-pod-autoscale/
+[9]: https://kubernetes.io/docs/concepts/workloads/controllers/replicaset/
diff --git a/published/20190608 An open source bionic leg, Python data pipeline, data breach detection, and more news.md b/published/20190608 An open source bionic leg, Python data pipeline, data breach detection, and more news.md
new file mode 100644
index 0000000000..4df0e7accd
--- /dev/null
+++ b/published/20190608 An open source bionic leg, Python data pipeline, data breach detection, and more news.md
@@ -0,0 +1,82 @@
+[#]: collector: (lujun9972)
+[#]: translator: (wxy)
+[#]: reviewer: (wxy)
+[#]: publisher: (wxy)
+[#]: url: (https://linux.cn/article-10965-1.html)
+[#]: subject: (An open source bionic leg, Python data pipeline, data breach detection, and more news)
+[#]: via: (https://opensource.com/article/19/6/news-june-8)
+[#]: author: (Scott Nesbitt https://opensource.com/users/scottnesbitt)
+
+开源新闻:开源仿生腿、Python 数据管道、数据泄露检测
+======
+
+> 了解过去两周来最大的开源头条新闻。
+
+![][1]
+
+在本期开源新闻综述中,我们将介绍一个开源仿生腿、一个新的开源医学影像组织,麦肯锡发布的首个开源软件,以及更多!
+
+### 使用开源推进仿生学
+
+我们这一代人从电视剧《六百万美元人》和《仿生女人》中学到了仿生学一词。让科幻小说(尽管基于事实)正在成为现实的,要归功于[由密歇根大学和 Shirley Ryan AbilityLab 设计][2]的假肢。
+
+该腿采用简单、低成本的模块化设计,“旨在通过为仿生学领域的零碎研究工作提供统一的平台,提高患者的生活质量并加速科学进步”。根据首席设计师 Elliot Rouse 的说法,它将“使研究人员能够有效地解决与一系列的实验室和社区活动中控制仿生腿相关的挑战。”
+
+你可以从[开源腿][3]网站了解有该腿的更多信息并下载该设计。
+
+### 麦肯锡发布了一个用于构建产品级数据管道的 Python 库
+
+咨询巨头麦肯锡公司最近发布了其[第一个开源工具][4],名为 Kedro,它是一个用于创建机器学习和数据管道的 Python 库。
+
+Kedro 使得“管理大型工作流程更加容易,并确保整个项目的代码质量始终如一”,产品经理 Yetunde Dada 说。虽然它最初是作为一种专有的工具,但麦肯锡开源了 Kedro,因此“客户可以在我们离开项目后使用它 —— 这是我们回馈的方式,”工程师 Nikolaos Tsaousis 说。
+
+如果你有兴趣了解一下,可以从 GitHub 上获取 [Kedro 的源代码][5]。
+
+### 新联盟推进开源医学成像
+
+一组专家和患者倡导者聚集在一起组成了[开源成像联盟][6]。该联盟旨在“通过数字成像和机器学习帮助推进特发性肺纤维化和其他间质性肺病的诊断。”
+
+根据联盟执行董事 Elizabeth Estes 的说法,该项目旨在“协作加速诊断,帮助预后处置,最终让医生更有效地治疗患者”。为此,他们正在组织和分享“来自患者的 15,000 个匿名图像扫描和临床数据,这将作为机器学习程序的输入数据来开发算法。”
+
+### Mozilla 发布了一种简单易用的方法,以确定你是否遭受过数据泄露
+
+向不那么精通软件的人解释安全性始终是一项挑战,无论你的技能水平如何,都很难监控你的风险。Mozilla 发布了 [Firefox Monitor][7],其数据由 [Have I Been Pwned][8] 提供,它是一种查看你的任何电子邮件是否出现在重大数据泄露事件中的简单方式。你可以输入电子邮件逐个搜索,或注册他们的服务以便将来通知你。
+
+该网站还提供了大量有用的教程,用于了解黑客如何做的,数据泄露后如何处理以及如何创建强密码。请务必将网站加入书签,以防家人要求你在假日期间提供建议。
+
+### 其它新闻
+
+* [想要一款去谷歌化的 Android?把你的手机发送给这个人][9]
+* [CockroachDB 发行版使用了非 OSI 批准的许可证,但仍然保持开源][10]
+* [基础设施自动化公司 Chef 承诺开源][11]
+* [俄罗斯的 Windows 替代品将获得安全升级][12]
+* [使用此代码在几分钟内从 Medium 切换到你自己的博客][13]
+* [开源推进联盟宣布与台湾自由软件协会建立新合作伙伴关系][14]
+
+--------------------------------------------------------------------------------
+
+via: https://opensource.com/article/19/6/news-june-8
+
+作者:[Scott Nesbitt][a]
+选题:[lujun9972][b]
+译者:[wxy](https://github.com/wxy)
+校对:[wxy](https://github.com/wxy)
+
+本文由 [LCTT](https://github.com/LCTT/TranslateProject) 原创编译,[Linux中国](https://linux.cn/) 荣誉推出
+
+[a]: https://opensource.com/users/scottnesbitt
+[b]: https://github.com/lujun9972
+[1]: https://opensource.com/sites/default/files/styles/image-full-size/public/lead-images/weekly_news_roundup_tv.png?itok=B6PM4S1i
+[2]: https://news.umich.edu/open-source-bionic-leg-first-of-its-kind-platform-aims-to-rapidly-advance-prosthetics/
+[3]: https://opensourceleg.com/
+[4]: https://www.information-age.com/kedro-mckinseys-open-source-software-tool-123482991/
+[5]: https://github.com/quantumblacklabs/kedro
+[6]: https://pulmonaryfibrosisnews.com/2019/05/31/international-open-source-imaging-consortium-osic-launched-to-advance-ipf-diagnosis/
+[7]: https://monitor.firefox.com/
+[8]: https://haveibeenpwned.com/
+[9]: https://fossbytes.com/want-a-google-free-android-send-your-phone-to-this-guy/
+[10]: https://www.cockroachlabs.com/blog/oss-relicensing-cockroachdb/
+[11]: https://www.infoq.com/news/2019/05/chef-open-source/
+[12]: https://www.nextgov.com/cybersecurity/2019/05/russias-would-be-windows-replacement-gets-security-upgrade/157330/
+[13]: https://github.com/mathieudutour/medium-to-own-blog
+[14]: https://opensource.org/node/994
diff --git a/published/20190610 Screen Command Examples To Manage Multiple Terminal Sessions.md b/published/20190610 Screen Command Examples To Manage Multiple Terminal Sessions.md
new file mode 100644
index 0000000000..936974a5d2
--- /dev/null
+++ b/published/20190610 Screen Command Examples To Manage Multiple Terminal Sessions.md
@@ -0,0 +1,282 @@
+[#]: collector: (lujun9972)
+[#]: translator: (wxy)
+[#]: reviewer: (wxy)
+[#]: publisher: (wxy)
+[#]: url: (https://linux.cn/article-10962-1.html)
+[#]: subject: (Screen Command Examples To Manage Multiple Terminal Sessions)
+[#]: via: (https://www.ostechnix.com/screen-command-examples-to-manage-multiple-terminal-sessions/)
+[#]: author: (sk https://www.ostechnix.com/author/sk/)
+
+screen 命令示例:管理多个终端会话
+======
+
+
+
+GNU Screen 是一个终端多路复用器(窗口管理器)。顾名思义,Screen 可以在多个交互式 shell 之间复用物理终端,因此我们可以在每个终端会话中执行不同的任务。所有的 Screen 会话都完全独立地运行程序。因此,即使会话意外关闭或断开连接,在 Screen 会话内运行的程序或进程也将继续运行。例如,当通过 SSH [升级 Ubuntu][2] 服务器时,`screen` 命令将继续运行升级过程,以防万一 SSH 会话因任何原因而终止。
+
+GNU Screen 允许我们轻松创建多个 Screen 会话,在不同会话之间切换,在会话之间复制文本,随时连上或脱离会话等等。它是每个 Linux 管理员应该在必要时学习和使用的重要命令行工具之一。在本简要指南中,我们将看到 `screen` 命令的基本用法以及在 Linux 中的示例。
+
+### 安装 GNU Screen
+
+GNU Screen 在大多数 Linux 操作系统的默认存储库中都可用。
+
+要在 Arch Linux 上安装 GNU Screen,请运行:
+
+```
+$ sudo pacman -S screen
+```
+
+在 Debian、Ubuntu、Linux Mint 上:
+
+```
+$ sudo apt-get install screen
+```
+
+在 Fedora 上:
+
+```
+$ sudo dnf install screen
+```
+
+在 RHEL、CentOS 上:
+
+```
+$ sudo yum install screen
+```
+
+在 SUSE/openSUSE 上:
+
+```
+$ sudo zypper install screen
+```
+
+让我们继续看一些 `screen` 命令示例。
+
+### 管理多个终端会话的 Screen 命令示例
+
+在 Screen 中所有命令的默认前缀快捷方式是 `Ctrl + a`。使用 Screen 时,你需要经常使用此快捷方式。所以,要记住这个键盘快捷键。
+
+#### 创建新的 Screen 会话
+
+让我们创建一个新的 Screen 会话并连上它。为此,请在终端中键入以下命令:
+
+```
+screen
+```
+
+现在,在此会话中运行任何程序或进程,即使你与此会话断开连接,正在运行的进程或程序也将继续运行。
+
+#### 从 Screen 会话脱离
+
+要从屏幕会话中脱离,请按 `Ctrl + a` 和 `d`。你无需同时按下两个组合键。首先按 `Ctrl + a` 然后按 `d`。从会话中脱离后,你将看到类似下面的输出。
+
+```
+[detached from 29149.pts-0.sk]
+```
+
+这里,`29149` 是 Screen ID,`pts-0.sk` 是屏幕会话的名称。你可以使用 Screen ID 或相应的会话名称来连上、脱离和终止屏幕会话。
+
+#### 创建命名会话
+
+你还可以用你选择的任何自定义名称创建一个 Screen 会话,而不是默认用户名,如下所示。
+
+```
+screen -S ostechnix
+```
+
+上面的命令将创建一个名为 `xxxxx.ostechnix` 的新 Screen 会话,并立即连上它。要从当前会话中脱离,请按 `Ctrl + a`,然后按 `d`。
+
+当你想要查找哪些进程在哪些会话上运行时,命名会话会很有用。例如,当在会话中设置 LAMP 系统时,你可以简单地将其命名为如下所示。
+
+```
+screen -S lampstack
+```
+
+#### 创建脱离的会话
+
+有时,你可能想要创建一个会话,但不希望自动连上该会话。在这种情况下,运行以下命令来创建名为`senthil` 的已脱离会话:
+
+```
+screen -S senthil -d -m
+```
+
+也可以缩短为:
+
+```
+screen -dmS senthil
+```
+
+上面的命令将创建一个名为 `senthil` 的会话,但不会连上它。
+
+#### 列出屏幕会话
+
+要列出所有正在运行的会话(连上的或脱离的),请运行:
+
+```
+screen -ls
+```
+
+示例输出:
+
+```
+There are screens on:
+ 29700.senthil (Detached)
+ 29415.ostechnix (Detached)
+ 29149.pts-0.sk (Detached)
+3 Sockets in /run/screens/S-sk.
+```
+
+如你所见,我有三个正在运行的会话,并且所有会话都已脱离。
+
+#### 连上 Screen 会话
+
+如果你想连上会话,例如 `29415.ostechnix`,只需运行:
+
+```
+screen -r 29415.ostechnix
+```
+
+或:
+
+```
+screen -r ostechnix
+```
+
+或使用 Screen ID:
+
+```
+screen -r 29415
+```
+
+要验证我们是否连上到上述会话,只需列出打开的会话并检查。
+
+```
+screen -ls
+```
+
+示例输出:
+
+```
+There are screens on:
+ 29700.senthil (Detached)
+ 29415.ostechnix (Attached)
+ 29149.pts-0.sk (Detached)
+3 Sockets in /run/screens/S-sk.
+```
+
+如你所见,在上面的输出中,我们目前已连上到 `29415.ostechnix` 会话。要退出当前会话,请按 `ctrl + a d`。
+
+#### 创建嵌套会话
+
+当我们运行 `screen` 命令时,它将为我们创建一个会话。但是,我们可以创建嵌套会话(会话内的会话)。
+
+首先,创建一个新会话或连上已打开的会话。然后我将创建一个名为 `nested` 的新会话。
+
+```
+screen -S nested
+```
+
+现在,在会话中按 `Ctrl + a` 和 `c` 创建另一个会话。只需重复此操作即可创建任意数量的嵌套 Screen 会话。每个会话都将分配一个号码。号码将从 `0` 开始。
+
+你可以按 `Ctrl + n` 移动到下一个会话,然后按 `Ctrl + p` 移动到上一个会话。
+
+以下是管理嵌套会话的重要键盘快捷键列表。
+
+* `Ctrl + a "` - 列出所有会话
+* `Ctrl + a 0` - 切换到会话号 0
+* `Ctrl + a n` - 切换到下一个会话
+* `Ctrl + a p` - 切换到上一个会话
+* `Ctrl + a S` - 将当前区域水平分割为两个区域
+* `Ctrl + a l` - 将当前区域垂直分割为两个区域
+* `Ctrl + a Q` - 关闭除当前会话之外的所有会话
+* `Ctrl + a X` - 关闭当前会话
+* `Ctrl + a \` - 终止所有会话并终止 Screen
+* `Ctrl + a ?` - 显示键绑定。要退出,请按回车
+
+#### 锁定会话
+
+Screen 有一个锁定会话的选项。为此,请按 `Ctrl + a` 和 `x`。 输入你的 Linux 密码以锁定。
+
+```
+Screen used by sk on ubuntuserver.
+Password:
+```
+
+#### 记录会话
+
+你可能希望记录 Screen 会话中的所有内容。为此,只需按 `Ctrl + a` 和 `H` 即可。
+
+或者,你也可以使用 `-L` 参数启动新会话来启用日志记录。
+
+```
+screen -L
+```
+
+从现在开始,你在会话中做的所有活动都将记录并存储在 `$HOME` 目录中名为 `screenlog.x` 的文件中。这里,`x` 是一个数字。
+
+你可以使用 `cat` 命令或任何文本查看器查看日志文件的内容。
+
+![][3]
+
+*记录 Screen 会话*
+
+#### 终止 Screen 会话
+
+如果不再需要会话,只需杀死它。要杀死名为 `senthil` 的脱离会话:
+
+```
+screen -r senthil -X quit
+```
+
+或:
+
+```
+screen -X -S senthil quit
+```
+
+或:
+
+```
+screen -X -S 29415 quit
+```
+
+如果没有打开的会话,你将看到以下输出:
+
+```
+$ screen -ls
+No Sockets found in /run/screens/S-sk.
+```
+
+更多细节请参照 man 手册页:
+
+```
+$ man screen
+```
+
+还有一个名为 Tmux 的类似的命令行实用程序,它与 GNU Screen 执行相同的工作。要了解更多信息,请参阅以下指南。
+
+* [Tmux 命令示例:管理多个终端会话][5]
+
+### 资源
+
+ * [GNU Screen 主页][6]
+
+--------------------------------------------------------------------------------
+
+via: https://www.ostechnix.com/screen-command-examples-to-manage-multiple-terminal-sessions/
+
+作者:[sk][a]
+选题:[lujun9972][b]
+译者:[wxy](https://github.com/wxy)
+校对:[wxy](https://github.com/wxy)
+
+本文由 [LCTT](https://github.com/LCTT/TranslateProject) 原创编译,[Linux中国](https://linux.cn/) 荣誉推出
+
+[a]: https://www.ostechnix.com/author/sk/
+[b]: https://github.com/lujun9972
+[1]: https://www.ostechnix.com/wp-content/uploads/2019/06/Screen-Command-Examples-720x340.jpg
+[2]: https://www.ostechnix.com/how-to-upgrade-to-ubuntu-18-04-lts-desktop-and-server/
+[3]: https://www.ostechnix.com/wp-content/uploads/2019/06/Log-screen-sessions.png
+[4]: https://www.ostechnix.com/record-everything-terminal/
+[5]: https://www.ostechnix.com/tmux-command-examples-to-manage-multiple-terminal-sessions/
+[6]: https://www.gnu.org/software/screen/
diff --git a/published/20190610 Try a new game on Free RPG Day.md b/published/20190610 Try a new game on Free RPG Day.md
new file mode 100644
index 0000000000..64e95e2ac3
--- /dev/null
+++ b/published/20190610 Try a new game on Free RPG Day.md
@@ -0,0 +1,84 @@
+[#]: collector: (lujun9972)
+[#]: translator: (wxy)
+[#]: reviewer: (wxy)
+[#]: publisher: (wxy)
+[#]: url: (https://linux.cn/article-10976-1.html)
+[#]: subject: (Try a new game on Free RPG Day)
+[#]: via: (https://opensource.com/article/19/5/free-rpg-day)
+[#]: author: (Seth Kenlon https://opensource.com/users/seth/users/erez/users/seth)
+
+在免费 RPG 日试玩一下新游戏
+======
+
+> 6 月 15 日,你可以在当地的游戏商家庆祝桌面角色扮演游戏并获得免费的 RPG 资料。
+
+
+
+(LCTT 译注:“免费 RPG 日”是受“免费漫画书日”启发而发起的庆祝活动,从 2007 年开始已经举办多次。这里的 RPG 游戏并非我们通常所指的电脑 RPG 游戏,而是指使用纸和笔的桌面游戏,是一种西方传统游戏形式。)
+
+你有没有想过尝试一下《龙与地下城》,但不知道如何开始?你是否在年轻时玩过《开拓者》并一直在考虑重返快乐时光?你是否对角色扮演游戏(RPG)感到好奇,但不确定你是否想玩一个?你是否对桌面游戏的概念完全陌生,直到现在才听说过这种 RPG 游戏?无论是哪一个并不重要,因为[免费 RPG 日] [2]适合所有人!
+
+第一个免费 RPG 日活动发生在 2007 年,是由世界各地的桌面游戏商家举办的。这个想法是以 0 美元的价格为新手和有经验的游戏玩家带来新的、独家的 RPG 快速入门规则和冒险体验。在这样的一天里,你可以走进当地的桌面游戏商家,得到一本小册子,其中包含桌面 RPG 的简单的初学者规则,你可以在商家里与那里的人或者回家与朋友一起玩。这本小册子是给你的,应该一直留着的。
+
+这一活动如此的受欢迎,此后该传统一直延续至今。今年,免费 RPG 日定于 6 月 15 日星期六举行。
+
+### 有什么收获?
+
+显然,免费 RPG 日背后的想法是让你沉迷于桌面 RPG 游戏。但在你本能的犬儒主义开始之前,考虑到它会慢慢上瘾,爱上一个鼓励你阅读规则和知识的游戏并不太糟,这样你和你的家人、朋友就有了共度时光的借口了。桌面 RPG 是一个功能强大、富有想象力和有趣的媒介,而免费 RPG 日则是对这种游戏很好的介绍。
+
+![FreeRPG Day logo][3]
+
+### 开源游戏
+
+像许多其他行业一样,开源现象影响了桌面游戏。回到世纪之交,《Magic:The Gathering and Dungeons&Dragons》 的提供者[威世智公司][4]决定通过开发[开源游戏许可证][5](OGL)来采用开源方法。他们将此许可证用于世界上第一个 RPG(《龙与地下城》,D&D)的版本 3 和 3.5。几年后,当他们在第四版上(对开源)产生了动摇时,《龙》杂志的出版商复刻了 D&D 3.5 的“代码”,将其混制版本发布为《开拓者》 RPG,从而保持了创新和整个第三方游戏开发者产业的健康发展。最近,威世智公司在 D&D 5e 版本中才又重回了 OGL。
+
+OGL 允许开发人员至少可以在他们自己产品中使用该游戏的机制。不管你可以不可以使用自定义怪物、武器、王国或流行角色的名称,但你可以随时使用 OGL 游戏的规则和数学计算。事实上,OGL 游戏的规则通常作为[系统参考文档][6](SRD)免费发布的,因此,无论你是否购买了规则书的副本,你都可以了解游戏的玩法。
+
+如果你之前从未玩过桌面 RPG,那么使用笔和纸玩的游戏也可以拥有游戏引擎似乎很奇怪,但计算就是计算,不管是数字的还是模拟的。作为一个简单的例子:假设游戏引擎规定玩家角色有一个代表其力量的数字。当那个玩家角色与一个有其两倍力量的巨人战斗时,在玩家掷骰子以增加她的角色的力量攻击时,真的会感到紧张。如果没有掷出一个很好的点数的话,她的力量将无法与巨人相匹敌。知道了这一点,第三方或独立开发者就可以为这个游戏引擎设计一个怪物,同时了解骰子滚动可能对玩家的能力得分产生的影响。这意味着他们可以根据游戏引擎的优先级进行数学计算。他们可以设计一系列用来杀死的怪物,在游戏引擎的环境中它们具有有意义的能力和技能,并且他们可以宣称与该引擎的兼容性。
+
+此外,OGL 允许出版商为其材料定义产品标识。产品标识可以是出版物的商业外观(图形元素和布局)、徽标、术语、传说、专有名称等。未经出版商同意,任何定义为产品标识的内容都可能**无法**重复使用。例如,假设一个出版商发行了一本武器手册,其中包括一个名为 Sigint 的魔法砍刀,它对所有针对僵尸的攻击都给予 +2 魔法附加攻击值。这个特性来自一个故事,该砍刀是一个具有潜伏的僵尸基因的科学家锻造的。但是,该出版物在 OGL 第 1e 节中列出的所有武器的正确名称都被保留为产品标识。这意味着你可以在自己的出版物中使用该数字(武器的持久性、它所造成的伤害,+2 魔法奖励等等)以及与该武器相关的传说(它由一个潜伏的僵尸锻造),但是你不能使用该武器的名称(Sigint)。
+
+OGL 是一个非常灵活的许可证,因此开发人员必须仔细阅读其第 1e 节。 一些出版商只保留出版物本身的布局,而其他出版商保留除数字和最通用术语之外的所有内容。
+
+当卓越的 RPG 特许经营权拥抱开源时,至今仍能感受到的它给整个行业掀起的波澜。第三方开发人员可以为 5e 和《开拓者》系统创建内容。由威世智公司创建的整个 [DungeonMastersGuild.com][7] 网站为 D&D 5e 制作了独立内容,旨在促进独立出版。[Starfinder][8]、[OpenD6][9]、[战士,盗贼和法师][10]、[剑与巫师][11] 等及很多其它游戏都采用了 OGL。其他系统,如 Brent Newhall 的 《[Dungeon Delvers][12]》、《[Fate][13]》、《[Dungeon World][14]》 等等,都是根据[知识共享许可][15]授权的的。
+
+### 获取你的 RPG
+
+在免费 RPG 日,你可以前往当地游戏商铺,玩 RPG 以及获取与朋友将来一起玩的 RPG 游戏材料。就像[Linux 安装节][16] 或 [软件自由日][17]一样,该活动的定义很松散。每个商家举办的自由 RPG 日都有所不同,每个商家都可以玩他们选择的任何游戏。但是,游戏发行商捐赠的免费内容每年都是相同的。显然,免费的东西视情况而定,但是当你参加免费 RPG 日活动时,请注意有多少游戏采用了开源许可证(如果是 OGL 游戏,OGL 会打印在书背面)。《开拓者》、《Starfinder》 和 D&D 的任何内容肯定都会带有 OGL 的一些优势。许多其他系统的内容使用知识共享许可。有些则像 90 年代复活的 [Dead Earth][18] RPG 一样,使用 [GNU 自由文档许可证] [19]。
+
+有大量的游戏资源是通过开源许可证开发的。你可能需要也可能不需要关心游戏的许可证;毕竟,许可证与你是否可以与朋友一起玩无关。但是如果你喜欢支持[自由文化][20]而不仅仅是你运行的软件,那么试试一些 OGL 或知识共享游戏吧。如果你不熟悉游戏,请在免费 RPG 日在当地游戏商家试玩桌面 RPG 游戏!
+
+
+--------------------------------------------------------------------------------
+
+via: https://opensource.com/article/19/5/free-rpg-day
+
+作者:[Seth Kenlon][a]
+选题:[lujun9972][b]
+译者:[wxy](https://github.com/wxy)
+校对:[wxy](https://github.com/wxy)
+
+本文由 [LCTT](https://github.com/LCTT/TranslateProject) 原创编译,[Linux中国](https://linux.cn/) 荣誉推出
+
+[a]: https://opensource.com/users/seth/users/erez/users/seth
+[b]: https://github.com/lujun9972
+[1]: https://opensource.com/sites/default/files/styles/image-full-size/public/lead-images/team-game-play-inclusive-diversity-collaboration.png?itok=8sUXV7W1 (plastic game pieces on a board)
+[2]: https://www.freerpgday.com/
+[3]: https://opensource.com/sites/default/files/uploads/freerpgday-logoblank.jpg (FreeRPG Day logo)
+[4]: https://company.wizards.com/
+[5]: http://www.opengamingfoundation.org/licenses.html
+[6]: https://www.d20pfsrd.com/
+[7]: https://www.dmsguild.com/
+[8]: https://paizo.com/starfinder
+[9]: https://ogc.rpglibrary.org/index.php?title=OpenD6
+[10]: http://www.stargazergames.eu/games/warrior-rogue-mage/
+[11]: https://froggodgames.com/frogs/product/swords-wizardry-complete-rulebook/
+[12]: http://brentnewhall.com/games/doku.php?id=games:dungeon_delvers
+[13]: http://www.faterpg.com/licensing/licensing-fate-cc-by/
+[14]: http://dungeon-world.com/
+[15]: https://creativecommons.org/
+[16]: https://www.tldp.org/HOWTO/Installfest-HOWTO/introduction.html
+[17]: https://www.softwarefreedomday.org/
+[18]: https://mixedsignals.ml/games/blog/blog_dead-earth
+[19]: https://www.gnu.org/licenses/fdl-1.3.en.html
+[20]: https://opensource.com/article/18/1/creative-commons-real-world
diff --git a/scripts/check/common.inc.sh b/scripts/check/common.inc.sh
index 2bc0334930..905699a139 100644
--- a/scripts/check/common.inc.sh
+++ b/scripts/check/common.inc.sh
@@ -10,7 +10,7 @@ export TSL_DIR='translated' # 已翻译
export PUB_DIR='published' # 已发布
# 定义匹配规则
-export CATE_PATTERN='(talk|tech)' # 类别
+export CATE_PATTERN='(talk|tech|news)' # 类别
export FILE_PATTERN='[0-9]{8} [a-zA-Z0-9_.,() -]*\.md' # 文件名
# 获取用于匹配操作的正则表达式
diff --git a/sources/news/20190606 Cisco to buy IoT security, management firm Sentryo.md b/sources/news/20190606 Cisco to buy IoT security, management firm Sentryo.md
new file mode 100644
index 0000000000..f8db1bfab5
--- /dev/null
+++ b/sources/news/20190606 Cisco to buy IoT security, management firm Sentryo.md
@@ -0,0 +1,106 @@
+[#]: collector: (lujun9972)
+[#]: translator: ( )
+[#]: reviewer: ( )
+[#]: publisher: ( )
+[#]: url: ( )
+[#]: subject: (Cisco to buy IoT security, management firm Sentryo)
+[#]: via: (https://www.networkworld.com/article/3400847/cisco-to-buy-iot-security-management-firm-sentryo.html)
+[#]: author: (Michael Cooney https://www.networkworld.com/author/Michael-Cooney/)
+
+Cisco to buy IoT security, management firm Sentryo
+======
+Buying Sentryo will give Cisco support for anomaly and real-time threat detection for the industrial internet of things.
+![IDG Worldwide][1]
+
+Looking to expand its IoT security and management offerings Cisco plans to acquire [Sentryo][2], a company based in France that offers anomaly detection and real-time threat detection for Industrial Internet of Things ([IIoT][3]) networks.
+
+Founded in 2014 Sentryo products include ICS CyberVision – an asset inventory, network monitoring and threat intelligence platform – and CyberVision network edge sensors, which analyze network flows.
+
+**More on IoT:**
+
+ * [What is the IoT? How the internet of things works][4]
+ * [What is edge computing and how it’s changing the network][5]
+ * [Most powerful Internet of Things companies][6]
+ * [10 Hot IoT startups to watch][7]
+ * [The 6 ways to make money in IoT][8]
+ * [What is digital twin technology? [and why it matters]][9]
+ * [Blockchain, service-centric networking key to IoT success][10]
+ * [Getting grounded in IoT networking and security][11]
+ * [Building IoT-ready networks must become a priority][12]
+ * [What is the Industrial IoT? [And why the stakes are so high]][13]
+
+
+
+“We have incorporated Sentryo’s edge sensor and our industrial networking hardware with Cisco’s IOx application framework,” wrote Rob Salvagno, Cisco vice president of Corporate Development and Cisco Investments in a [blog][14] about the proposed buy.
+
+“We believe that connectivity is foundational to IoT projects and by unleashing the power of the network we can dramatically improve operational efficiencies and uncover new business opportunities. With the addition of Sentryo, Cisco can offer control systems engineers deeper visibility into assets to optimize, detect anomalies and secure their networks.”
+
+Gartner [wrote][15] of Sentryo’s system: “ICS CyberVision product provides visibility into its customers'' OT networks in way all OT users will understand, not just technical IT staff. With the increased focus of both hackers and regulators on industrial control systems, it is vital to have the right visibility of an organization’s OT. Many OT networks not only are geographically dispersed, but also are complex and consist of hundreds of thousands of components.”
+
+Sentryo's ICS CyberVision lets enterprises ensure continuity, resilience and safety of their industrial operations while preventing possible cyberattacks, said [Nandini Natarajan][16] , industry analyst at Frost & Sullivan. "It automatically profiles assets and communication flows using a unique 'universal OT language' in the form of tags, which describe in plain text what each asset is doing. ICS CyberVision gives anyone immediate insights into an asset's role and behaviors; it offers many different analytic views leveraging artificial intelligence algorithms to let users deep-dive into the vast amount of data a typical industrial control system can generate. Sentryo makes it easy to see important or relevant information."
+
+In addition, Sentryo's platform uses deep packet inspection (DPI) to extract information from communications among industrial assets, Natarajan said. This DPI engine is deployed through an edge-computing architecture that can run either on Sentryo sensor appliances or on network equipment that is already installed. Thus, Sentryo can embed visibility and cybersecurity features in the industrial network rather than deploying an out-of-band monitoring network, Natarajan said.
+
+**[[Prepare to become a Certified Information Security Systems Professional with this comprehensive online course from PluralSight. Now offering a 10-day free trial!][17] ]**
+
+Sentryo’s technology will broaden [Cisco’s][18] overarching IoT plan. In January it [launched][19] a family of switches, software, developer tools and blueprints to meld IoT and industrial networking with [intent-based networking][20] (IBN) and classic IT security, monitoring and application-development support.
+
+The new platforms can be managed by Cisco’s DNA Center, and Cisco IoT Field Network Director, letting customers fuse their IoT and industrial-network control with their business IT world.
+
+DNA Center is Cisco’s central management tool for enterprise networks, featuring automation capabilities, assurance setting, fabric provisioning and policy-based segmentation. It is also at the center of the company’s IBN initiative offering customers the ability to automatically implement network and policy changes on the fly and ensure data delivery. The IoT Field Network Director is software that manages multiservice networks of Cisco industrial, connected grid routers and endpoints.
+
+Liz Centoni, senior vice president and general manager of Cisco's IoT business group said the company expects the [Sentryo technology to help][21] IoT customers in a number of ways:
+
+Network-enabled, passive DPI capabilities to discover IoT and OT assets, and establish communication patterns between devices and systems. Sentryo’s sensor is natively deployable on Cisco’s IOx framework and can be built into the industrial network these devices run on instead of adding additional hardware.
+
+As device identification and communication patterns are created, Cisco will integrate this with DNA Center and Identity Services Engine(ISE) to allow customers to easily define segmentation policy. This integration will allow OT teams to leverage IT security teams’ expertise to secure their environments without risk to the operational processes.
+
+With these IoT devices lacking modern embedded software and security capabilities, segmentation will be the key technology to allow communication from operational assets to the rightful systems, and reduce risk of cyber security incidents like we saw with [WannaCry][22] and [Norsk Hydro][23].
+
+According to [Crunchbase][24], Sentryo has $3.5M in estimated revenue annually and it competes most closely with Cymmetria, Team8, and Indegy. The acquisition is expected to close before the end of Cisco’s Q1 Fiscal Year 2020 -- October 26, 2019. Financial details of the acquisition were not detailed.
+
+Sentryo is Cisco’s second acquisition this year. It bought Singularity for its network analytics technology in January. In 2018 Cisco bought six companies including Duo security software.
+
+** **
+
+Join the Network World communities on [Facebook][25] and [LinkedIn][26] to comment on topics that are top of mind.
+
+--------------------------------------------------------------------------------
+
+via: https://www.networkworld.com/article/3400847/cisco-to-buy-iot-security-management-firm-sentryo.html
+
+作者:[Michael Cooney][a]
+选题:[lujun9972][b]
+译者:[译者ID](https://github.com/译者ID)
+校对:[校对者ID](https://github.com/校对者ID)
+
+本文由 [LCTT](https://github.com/LCTT/TranslateProject) 原创编译,[Linux中国](https://linux.cn/) 荣誉推出
+
+[a]: https://www.networkworld.com/author/Michael-Cooney/
+[b]: https://github.com/lujun9972
+[1]: https://images.idgesg.net/images/article/2018/09/nwan_019_iiot-100771131-large.jpg
+[2]: https://www.sentryo.net/
+[3]: https://www.networkworld.com/article/3243928/what-is-the-industrial-iot-and-why-the-stakes-are-so-high.html
+[4]: https://www.networkworld.com/article/3207535/internet-of-things/what-is-the-iot-how-the-internet-of-things-works.html
+[5]: https://www.networkworld.com/article/3224893/internet-of-things/what-is-edge-computing-and-how-it-s-changing-the-network.html
+[6]: https://www.networkworld.com/article/2287045/internet-of-things/wireless-153629-10-most-powerful-internet-of-things-companies.html
+[7]: https://www.networkworld.com/article/3270961/internet-of-things/10-hot-iot-startups-to-watch.html
+[8]: https://www.networkworld.com/article/3279346/internet-of-things/the-6-ways-to-make-money-in-iot.html
+[9]: https://www.networkworld.com/article/3280225/internet-of-things/what-is-digital-twin-technology-and-why-it-matters.html
+[10]: https://www.networkworld.com/article/3276313/internet-of-things/blockchain-service-centric-networking-key-to-iot-success.html
+[11]: https://www.networkworld.com/article/3269736/internet-of-things/getting-grounded-in-iot-networking-and-security.html
+[12]: https://www.networkworld.com/article/3276304/internet-of-things/building-iot-ready-networks-must-become-a-priority.html
+[13]: https://www.networkworld.com/article/3243928/internet-of-things/what-is-the-industrial-iot-and-why-the-stakes-are-so-high.html
+[14]: https://blogs.cisco.com/news/cisco-industrial-iot-news
+[15]: https://www.globenewswire.com/news-release/2018/06/28/1531119/0/en/Sentryo-Named-a-Cool-Vendor-by-Gartner.html
+[16]: https://www.linkedin.com/pulse/industrial-internet-things-iiot-decoded-nandini-natarajan/
+[17]: https://pluralsight.pxf.io/c/321564/424552/7490?u=https%3A%2F%2Fwww.pluralsight.com%2Fpaths%2Fcertified-information-systems-security-professional-cisspr
+[18]: https://www.cisco.com/c/dam/en_us/solutions/iot/ihs-report.pdf
+[19]: https://www.networkworld.com/article/3336454/cisco-goes-after-industrial-iot.html
+[20]: https://www.networkworld.com/article/3202699/what-is-intent-based-networking.html
+[21]: https://blogs.cisco.com/news/securing-the-internet-of-things-cisco-announces-intent-to-acquire-sentryo
+[22]: https://blogs.cisco.com/security/talos/wannacry
+[23]: https://www.securityweek.com/norsk-hydro-may-have-lost-40m-first-week-after-cyberattack
+[24]: https://www.crunchbase.com/organization/sentryo#section-web-traffic-by-similarweb
+[25]: https://www.facebook.com/NetworkWorld/
+[26]: https://www.linkedin.com/company/network-world
diff --git a/sources/news/20190606 Zorin OS Becomes Even More Awesome With Zorin 15 Release.md b/sources/news/20190606 Zorin OS Becomes Even More Awesome With Zorin 15 Release.md
new file mode 100644
index 0000000000..c7dc93c70a
--- /dev/null
+++ b/sources/news/20190606 Zorin OS Becomes Even More Awesome With Zorin 15 Release.md
@@ -0,0 +1,116 @@
+[#]: collector: (lujun9972)
+[#]: translator: ( )
+[#]: reviewer: ( )
+[#]: publisher: ( )
+[#]: url: ( )
+[#]: subject: (Zorin OS Becomes Even More Awesome With Zorin 15 Release)
+[#]: via: (https://itsfoss.com/zorin-os-15-release/)
+[#]: author: (Ankush Das https://itsfoss.com/author/ankush/)
+
+Zorin OS Becomes Even More Awesome With Zorin 15 Release
+======
+
+Zorin OS has always been known as one of the [beginner-focused Linux distros][1] out there. Yes, it may not be the most popular – but it sure is a good distribution specially for Windows migrants.
+
+A few years back, I remember, a friend of mine always insisted me to install [Zorin OS][2]. Personally, I didn’t like the UI back then. But, now that Zorin OS 15 is here – I have more reasons to get it installed as my primary OS.
+
+Fret not, in this article, we’ll talk about everything that you need to know.
+
+### New Features in Zorin 15
+
+Let’s see the major changes in the latest release of Zorin. Zorin 15 is based on Ubuntu 18.04.2 and thus it brings the performance improvement under the hood. Other than that, there are several UI (User Interface) improvements.
+
+#### Zorin Connect
+
+![Zorin Connect][3]
+
+Zorin OS 15’s main highlight is – Zorin Connect. If you have an Android device, you are in for a treat. Similar to [PushBullet][4], [Zorin Connect][5] integrates your phone with the desktop experience.
+
+You get to sync your smartphone’s notifications on your desktop while also being able to reply to it. Heck, you can also reply to the SMS messages and view those conversations.
+
+In addition to these, you get the following abilities:
+
+ * Share files and web links between devices
+ * Use your phone as a remote control for your computer
+ * Control media playback on your computer from your phone, and pause playback automatically when a phone call arrives
+
+
+
+As mentioned in their [official announcement post][6], the data transmission will be on your local network and no data will be transmitted to the cloud. To access Zorin Connect, navigate your way through – Zorin menu > System Tools > Zorin Connect.
+
+[Get ZORIN CONNECT ON PLAY STORE][5]
+
+#### New Desktop Theme (with dark mode!)
+
+![Zorin Dark Mode][7]
+
+I’m all in when someone mentions “Dark Mode” or “Dark Theme”. For me, this is the best thing that comes baked in with Zorin OS 15.
+
+[][8]
+
+Suggested read Necuno is a New Open Source Smartphone Running KDE
+
+It’s so pleasing to my eyes when I enable the dark mode on anything, you with me?
+
+Not just a dark theme, the UI is a lot cleaner and intuitive with subtle new animations. You can find all the settings from the Zorin Appearance app built-in.
+
+#### Adaptive Background & Night Light
+
+You get an option to let the background adapt according to the brightness of the environment every hour of the day. Also, you can find the night mode if you don’t want the blue light to stress your eyes.
+
+#### To do app
+
+![Todo][9]
+
+I always wanted this to happen so that I don’t have to use a separate service that offers a Linux client to add my tasks. It’s good to see a built-in app with integration support for Google Tasks and Todoist.
+
+#### There’s More?
+
+Yes! Other major changes include the support for Flatpak, a touch layout for convertible laptops, a DND mode, and some redesigned apps (Settings, Libre Office) to give you better user experience.
+
+If you want the detailed list of changes along with the minor improvements, you can follow the [announcement post][6]. If you are already a Zorin user, you would notice that they have refreshed their website with a new look as well.
+
+### Download Zorin OS 15
+
+**Note** : _Direct upgrades from Zorin OS 12 to 15 – without needing to re-install the operating system – will be available later this year._
+
+In case you didn’t know, there are three versions of Zorin OS – Ultimate, Core, and the Lite version.
+
+If you want to support the devs and the project while unlocking the full potential of Zorin OS, you should get the ultimate edition for $39.
+
+If you just want the essentials, the core edition will do just fine (which you can download for free). In either case, if you have an old computer, the lite version is the one to go with.
+
+[DOWNLOAD ZORIN OS 15][10]
+
+**What do you think of Zorin 15?**
+
+[][11]
+
+Suggested read Ubuntu 14.04 Codenamed Trusty Tahr
+
+I’m definitely going to give it a try as my primary OS – fingers crossed. What about you? What do you think about the latest release? Feel free to let us know in the comments below.
+
+--------------------------------------------------------------------------------
+
+via: https://itsfoss.com/zorin-os-15-release/
+
+作者:[Ankush Das][a]
+选题:[lujun9972][b]
+译者:[译者ID](https://github.com/译者ID)
+校对:[校对者ID](https://github.com/校对者ID)
+
+本文由 [LCTT](https://github.com/LCTT/TranslateProject) 原创编译,[Linux中国](https://linux.cn/) 荣誉推出
+
+[a]: https://itsfoss.com/author/ankush/
+[b]: https://github.com/lujun9972
+[1]: https://itsfoss.com/best-linux-beginners/
+[2]: https://zorinos.com/
+[3]: https://i0.wp.com/itsfoss.com/wp-content/uploads/2019/06/zorin-connect.jpg?fit=800%2C473&ssl=1
+[4]: https://www.pushbullet.com/
+[5]: https://play.google.com/store/apps/details?id=com.zorinos.zorin_connect&hl=en_IN
+[6]: https://zoringroup.com/blog/2019/06/05/zorin-os-15-is-here-faster-easier-more-connected/
+[7]: https://i2.wp.com/itsfoss.com/wp-content/uploads/2019/06/zorin-dark-mode.jpg?fit=722%2C800&ssl=1
+[8]: https://itsfoss.com/necunos-linux-smartphone/
+[9]: https://i2.wp.com/itsfoss.com/wp-content/uploads/2019/06/Todo.jpg?fit=800%2C652&ssl=1
+[10]: https://zorinos.com/download/
+[11]: https://itsfoss.com/ubuntu-1404-codenamed-trusty-tahr/
diff --git a/sources/news/20190607 Free and Open Source Trello Alternative OpenProject 9 Released.md b/sources/news/20190607 Free and Open Source Trello Alternative OpenProject 9 Released.md
new file mode 100644
index 0000000000..8c5c5decf9
--- /dev/null
+++ b/sources/news/20190607 Free and Open Source Trello Alternative OpenProject 9 Released.md
@@ -0,0 +1,85 @@
+[#]: collector: (lujun9972)
+[#]: translator: ( )
+[#]: reviewer: ( )
+[#]: publisher: ( )
+[#]: url: ( )
+[#]: subject: (Free and Open Source Trello Alternative OpenProject 9 Released)
+[#]: via: (https://itsfoss.com/openproject-9-release/)
+[#]: author: (Ankush Das https://itsfoss.com/author/ankush/)
+
+Free and Open Source Trello Alternative OpenProject 9 Released
+======
+
+[OpenProject][1] is a collaborative open source project management software. It’s an alternative to proprietary solutions like [Trello][2] and [Jira][3].
+
+You can use it for free if it’s for personal use and you set it up (and host it) on your own server. This way, you control your data.
+
+Of course, you get access to premium features and priority help if you are a [Cloud or Enterprise edition user][4].
+
+The OpenProject 9 release emphasizes on new board views, package list view, and work templates.
+
+If you didn’t know about this, you can give it a try. But, if you are an existing user – you should know what’s new before migrating to OpenProject 9.
+
+### What’s New in OpenProject 9?
+
+Here are some of the major changes in the latest release of OpenProject.
+
+#### Scrum & Agile Boards
+
+![][5]
+
+For Cloud and Enterprise editions, there’s a new [scrum][6] and [agile][7] board view. You also get to showcase your work in a [kanban-style][8] fashion, making it easier to support your agile and scrum teams.
+
+The new board view makes it easy to know who’s assigned for the task and update the status in a jiffy. You also get different board view options like basic board, status board, and version boards.
+
+#### Work Package templates
+
+![Work Package Template][9]
+
+You don’t have to create everything from scratch for every unique work package. So, instead, you just keep a template – so that you can use it whenever you need to create a new work package. It will save a lot of time.
+
+#### New Work Package list view
+
+![Work Package View][10]
+
+In the work package list, there’s a subtle new addition that lets you view the avatars of the assigned people for a specific work.
+
+#### Customizable work package view for my page
+
+Your own page to display what you are working on (and the progress) shouldn’t be always boring. So, now you get the ability to customize it and even add a Gantt chart to visualize your work.
+
+[][11]
+
+Suggested read Ubuntu 12.04 Has Reached End of Life
+
+**Wrapping Up**
+
+For detailed instructions on migrating and installation, you should follow the [official announcement post][12] covering all the essential details for the users.
+
+Also, we would love to know about your experience with OpenProject 9, let us know about it in the comments section below! If you use some other project management software, feel free to suggest it to us and rest of your fellow It’s FOSS readers.
+
+--------------------------------------------------------------------------------
+
+via: https://itsfoss.com/openproject-9-release/
+
+作者:[Ankush Das][a]
+选题:[lujun9972][b]
+译者:[译者ID](https://github.com/译者ID)
+校对:[校对者ID](https://github.com/校对者ID)
+
+本文由 [LCTT](https://github.com/LCTT/TranslateProject) 原创编译,[Linux中国](https://linux.cn/) 荣誉推出
+
+[a]: https://itsfoss.com/author/ankush/
+[b]: https://github.com/lujun9972
+[1]: https://www.openproject.org/
+[2]: https://trello.com/
+[3]: https://www.atlassian.com/software/jira
+[4]: https://www.openproject.org/pricing/
+[5]: https://i1.wp.com/itsfoss.com/wp-content/uploads/2019/06/open-project-9-scrum-agile.jpeg?fit=800%2C517&ssl=1
+[6]: https://en.wikipedia.org/wiki/Scrum_(software_development)
+[7]: https://en.wikipedia.org/wiki/Agile_software_development
+[8]: https://en.wikipedia.org/wiki/Kanban
+[9]: https://i2.wp.com/itsfoss.com/wp-content/uploads/2019/06/work-package-template.jpg?ssl=1
+[10]: https://i2.wp.com/itsfoss.com/wp-content/uploads/2019/06/work-package-view.jpg?fit=800%2C454&ssl=1
+[11]: https://itsfoss.com/ubuntu-12-04-end-of-life/
+[12]: https://www.openproject.org/openproject-9-new-scrum-agile-board-view/
diff --git a/sources/talk/20170717 The Ultimate Guide to JavaScript Fatigue- Realities of our industry.md b/sources/talk/20170717 The Ultimate Guide to JavaScript Fatigue- Realities of our industry.md
new file mode 100644
index 0000000000..923d4618a9
--- /dev/null
+++ b/sources/talk/20170717 The Ultimate Guide to JavaScript Fatigue- Realities of our industry.md
@@ -0,0 +1,221 @@
+[#]: collector: (lujun9972)
+[#]: translator: ( )
+[#]: reviewer: ( )
+[#]: publisher: ( )
+[#]: url: ( )
+[#]: subject: (The Ultimate Guide to JavaScript Fatigue: Realities of our industry)
+[#]: via: (https://lucasfcosta.com/2017/07/17/The-Ultimate-Guide-to-JavaScript-Fatigue.html)
+[#]: author: (Lucas Fernandes Da Costa https://lucasfcosta.com)
+
+The Ultimate Guide to JavaScript Fatigue: Realities of our industry
+======
+
+**Complaining about JS Fatigue is just like complaining about the fact that humanity has created too many tools to solve the problems we have** , from email to airplanes and spaceships.
+
+Last week I’ve done a talk about this very same subject at the NebraskaJS 2017 Conference and I got so many positive feedbacks that I just thought this talk should also become a blog post in order to reach more people and help them deal with JS Fatigue and understand the realities of our industry. **My goal with this post is to change the way you think about software engineering in general and help you in any areas you might work on**.
+
+One of the things that has inspired me to write this blog post and that totally changed my life is [this great post by Patrick McKenzie, called “Don’t Call Yourself a Programmer and other Career Advice”][1]. **I highly recommend you read that**. Most of this blog post is advice based on what Patrick has written in that post applied to the JavaScript ecosystem and with a few more thoughts I’ve developed during these last years working in the tech industry.
+
+This first section is gonna be a bit philosophical, but I swear it will be worth reading.
+
+### Realities of Our Industry 101
+
+Just like Patrick has done in [his post][1], let’s start with the most basic and essential truth about our industry:
+
+Software solves business problems
+
+This is it. **Software does not exist to please us as programmers** and let us write beautiful code. Neither it exists to create jobs for people in the tech industry. **Actually, it exists to kill as many jobs as possible, including ours** , and this is why basic income will become much more important in the next few years, but that’s a whole other subject.
+
+I’m sorry to say that, but the reason things are that way is that there are only two things that matter in the software engineering (and any other industries):
+
+**Cost versus Revenue**
+
+**The more you decrease cost and increase revenue, the more valuable you are** , and one of the most common ways of decreasing cost and increasing revenue is replacing human beings by machines, which are more effective and usually cost less in the long run.
+
+You are not paid to write code
+
+**Technology is not a goal.** Nobody cares about which programming language you are using, nobody cares about which frameworks your team has chosen, nobody cares about how elegant your data structures are and nobody cares about how good is your code. **The only thing that somebody cares about is how much does your software cost and how much revenue it generates**.
+
+Writing beautiful code does not matter to your clients. We write beautiful code because it makes us more productive in the long run and this decreases cost and increases revenue.
+
+The whole reason why we try not to write bugs is not that we value correctness, but that **our clients** value correctness. If you have ever seen a bug becoming a feature you know what I’m talking about. That bug exists but it should not be fixed. That happens because our goal is not to fix bugs, our goal is to generate revenue. If our bugs make clients happy then they increase revenue and therefore we are accomplishing our goals.
+
+Reusable space rockets, self-driving cars, robots, artificial intelligence: these things do not exist just because someone thought it would be cool to create them. They exist because there are business interests behind them. And I’m not saying the people behind them just want money, I’m sure they think that stuff is also cool, but the truth is that if they were not economically viable or had any potential to become so, they would not exist.
+
+Probably I should not even call this section “Realities of Our Industry 101”, maybe I should just call it “Realities of Capitalism 101”.
+
+And given that our only goal is to increase revenue and decrease cost, I think we as programmers should be paying more attention to requirements and design and start thinking with our minds and participating more actively in business decisions, which is why it is extremely important to know the problem domain we are working on. How many times before have you found yourself trying to think about what should happen in certain edge cases that have not been thought before by your managers or business people?
+
+In 1975, Boehm has done a research in which he found out that about 64% of all errors in the software he was studying were caused by design, while only 36% of all errors were coding errors. Another study called [“Higher Order Software—A Methodology for Defining Software”][2] also states that **in the NASA Apollo project, about 73% of all errors were design errors**.
+
+The whole reason why Design and Requirements exist is that they define what problems we’re going to solve and solving problems is what generates revenue.
+
+> Without requirements or design, programming is the art of adding bugs to an empty text file.
+>
+> * Louis Srygley
+>
+
+
+This same principle also applies to the tools we’ve got available in the JavaScript ecosystem. Babel, webpack, react, Redux, Mocha, Chai, Typescript, all of them exist to solve a problem and we gotta understand which problem they are trying to solve, we need to think carefully about when most of them are needed, otherwise, we will end up having JS Fatigue because:
+
+JS Fatigue happens when people use tools they don't need to solve problems they don't have.
+
+As Donald Knuth once said: “Premature optimization is the root of all evil”. Remember that software only exists to solve business problems and most software out there is just boring, it does not have any high scalability or high-performance constraints. Focus on solving business problems, focus on decreasing cost and generating revenue because this is all that matters. Optimize when you need, otherwise you will probably be adding unnecessary complexity to your software, which increases cost, and not generating enough revenue to justify that.
+
+This is why I think we should apply [Test Driven Development][3] principles to everything we do in our job. And by saying this I’m not just talking about testing. **I’m talking about waiting for problems to appear before solving them. This is what TDD is all about**. As Kent Beck himself says: “TDD reduces fear” because it guides your steps and allows you take small steps towards solving your problems. One problem at a time. By doing the same thing when it comes to deciding when to adopt new technologies then we will also reduce fear.
+
+Solving one problem at a time also decreases [Analysis Paralysis][4], which is basically what happens when you open Netflix and spend three hours concerned about making the optimal choice instead of actually watching something. By solving one problem at a time we reduce the scope of our decisions and by reducing the scope of our decisions we have fewer choices to make and by having fewer choices to make we decrease Analysis Paralysis.
+
+Have you ever thought about how easier it was to decide what you were going to watch when there were only a few TV channels available? Or how easier it was to decide which game you were going to play when you had only a few cartridges at home?
+
+### But what about JavaScript?
+
+By the time I’m writing this post NPM has 489,989 packages and tomorrow approximately 515 new ones are going to be published.
+
+And the packages we use and complain about have a history behind them we must comprehend in order to understand why we need them. **They are all trying to solve problems.**
+
+Babel, Dart, CoffeeScript and other transpilers come from our necessity of writing code other than JavaScript but making it runnable in our browsers. Babel even lets us write new generation JavaScript and make sure it will work even on older browsers, which has always been a great problem given the inconsistencies and different amount of compliance to the ECMA Specification between browsers. Even though the ECMA spec is becoming more and more solid these days, we still need Babel. And if you want to read more about Babel’s history I highly recommend that you read [this excellent post by Henry Zhu][5].
+
+Module bundlers such as Webpack and Browserify also have their reason to exist. If you remember well, not so long ago we used to suffer a lot with lots of `script` tags and making them work together. They used to pollute the global namespace and it was reasonably hard to make them work together when one depended on the other. In order to solve this [`Require.js`][6] was created, but it still had its problems, it was not that straightforward and its syntax also made it prone to other problems, as you can see [in this blog post][7]. Then Node.js came with `CommonJS` imports, which were synchronous, simple and clean, but we still needed a way to make that work on our browsers and this is why we needed Webpack and Browserify.
+
+And Webpack itself actually solves more problems than that by allowing us to deal with CSS, images and many other resources as if they were JavaScript dependencies.
+
+Front-end frameworks are a bit more complicated, but the reason why they exist is to reduce the cognitive load when we write code so that we don’t need to worry about manipulating the DOM ourselves or even dealing with messy browser APIs (another problem JQuery came to solve), which is not only error prone but also not productive.
+
+This is what we have been doing this whole time in computer science. We use low-level abstractions and build even more abstractions on top of it. The more we worry about describing how our software should work instead of making it work, the more productive we are.
+
+But all those tools have something in common: **they exist because the web platform moves too fast**. Nowadays we’re using web technology everywhere: in web browsers, in desktop applications, in phone applications or even in watch applications.
+
+This evolution also creates problems we need to solve. PWAs, for example, do not exist only because they’re cool and we programmers have fun writing them. Remember the first section of this post: **PWAs exist because they create business value**.
+
+And usually standards are not fast enough to be created and therefore we need to create our own solutions to these things, which is why it is great to have such a vibrant and creative community with us. We’re solving problems all the time and **we are allowing natural selection to do its job**.
+
+The tools that suit us better thrive, get more contributors and develop themselves more quickly and sometimes other tools end up incorporating the good ideas from the ones that thrive and becoming even more popular than them. This is how we evolve.
+
+By having more tools we also have more choices. If you remember the UNIX philosophy well, it states that we should aim at creating programs that do one thing and do it well.
+
+We can clearly see this happening in the JS testing environment, for example, where we have Mocha for running tests and Chai for doing assertions, while in Java JUnit tries to do all these things. This means that if we have a problem with one of them or if we find another one that suits us better, we can simply replace that small part and still have the advantages of the other ones.
+
+The UNIX philosophy also states that we should write programs that work together. And this is exactly what we are doing! Take a look at Babel, Webpack and React, for example. They work very well together but we still do not need one to use the other. In the testing environment, for example, if we’re using Mocha and Chai all of a sudden we can just install Karma and run those same tests in multiple environments.
+
+### How to Deal With It
+
+My first advice for anyone suffering from JS Fatigue would definitely be to stay aware that **you don’t need to know everything**. Trying to learn it all at once, even when we don’t have to do so, only increases the feeling of fatigue. Go deep in areas that you love and for which you feel an inner motivation to study and adopt a lazy approach when it comes to the other ones. I’m not saying that you should be lazy, I’m just saying that you can learn those only when needed. Whenever you face a problem that requires you to use a certain technology to solve it, go learn.
+
+Another important thing to say is that **you should start from the beginning**. Make sure you have learned enough about JavaScript itself before using any JavaScript frameworks. This is the only way you will be able to understand them and bend them to your will, otherwise, whenever you face an error you have never seen before you won’t know which steps to take in order to solve it. Learning core web technologies such as CSS, HTML5, JavaScript and also computer science fundamentals or even how the HTTP protocol works will help you master any other technologies a lot more quickly.
+
+But please, don’t get too attached to that. Sometimes you gotta risk yourself and start doing things on your own. As Sacha Greif has written in [this blog post][8], spending too much time learning the fundamentals is just like trying to learn how to swim by studying fluid dynamics. Sometimes you just gotta jump into the pool and try to swim by yourself.
+
+And please, don’t get too attached to a single technology. All of the things we have available nowadays have already been invented in the past. Of course, they have different features and a brand new name, but, in their essence, they are all the same.
+
+If you look at NPM, it is nothing new, we already had Maven Central and Ruby Gems quite a long time ago.
+
+In order to transpile your code, Babel applies the very same principles and theory as some of the oldest and most well-known compilers, such as the GCC.
+
+Even JSX is not a new idea. It E4X (ECMAScript for XML) already existed more than 10 years ago.
+
+Now you might ask: “what about Gulp, Grunt and NPM Scripts?” Well, I’m sorry but we can solve all those problems with GNU Make in 1976. And actually, there are a reasonable number of JavaScript projects that still use it, such as Chai.js, for example. But we do not do that because we are hipsters that like vintage stuff. We use `make` because it solves our problems, and this is what you should aim at doing, as we’ve talked before.
+
+If you really want to understand a certain technology and be able to solve any problems you might face, please, dig deep. One of the most decisive factors to success is curiosity, so **dig deep into the technologies you like**. Try to understand them from bottom-up and whenever you think something is just “magic”, debunk that myth by exploring the codebase by yourself.
+
+In my opinion, there is no better quote than this one by Richard Feinman, when it comes to really learning something:
+
+> What I cannot create, I do not understand
+
+And just below this phrase, [in the same blackboard, Richard also wrote][9]:
+
+> Know how to solve every problem that has been solved
+
+Isn’t this just amazing?
+
+When Richard said that, he was talking about being able to take any theoretical result and re-derive it, but I think the exact same principle can be applied to software engineering. The tools that solve our problems have already been invented, they already exist, so we should be able to get to them all by ourselves.
+
+This is the very reason I love [some of the videos available in Egghead.io][10] in which Dan Abramov explains how to implement certain features that exist in Redux from scratch or [blog posts that teach you how to build your own JSX renderer][11].
+
+So why not trying to implement these things by yourself or going to GitHub and reading their codebase in order to understand how they work? I’m sure you will find a lot of useful knowledge out there. Comments and tutorials might lie and be incorrect sometimes, the code cannot.
+
+Another thing that we have been talking a lot in this post is that **you should not get ahead of yourself**. Follow a TDD approach and solve one problem at a time. You are paid to increase revenue and decrease cost and you do this by solving problems, this is the reason why software exists.
+
+And since we love comparing our role to the ones related to civil engineering, let’s do a quick comparison between software development and civil engineering, just as [Sam Newman does in his brilliant book called “Building Microservices”][12].
+
+We love calling ourselves “engineers” or “architects”, but is that term really correct? We have been developing software for what we know as computers less than a hundred years ago, while the Colosseum, for example, exists for about two thousand years.
+
+When was the last time you’ve seen a bridge falling and when was the last time your telephone or your browser crashed?
+
+In order to explain this, I’ll use an example I love.
+
+This is the beautiful and awesome city of Barcelona:
+
+![The City of Barcelona][13]
+
+When we look at it this way and from this distance, it just looks like any other city in the world, but when we look at it from above, this is how Barcelona looks:
+
+![Barcelona from above][14]
+
+As you can see, every block has the same size and all of them are very organized. If you’ve ever been to Barcelona you will also know how good it is to move through the city and how well it works.
+
+But the people that planned Barcelona could not predict what it was going to look like in the next two or three hundred years. In cities, people come in and people move through it all the time so what they had to do was make it grow organically and adapt as the time goes by. They had to be prepared for changes.
+
+This very same thing happens to our software. It evolves quickly, refactors are often needed and requirements change more frequently than we would like them to.
+
+So, instead of acting like a Software Engineer, act as a Town Planner. Let your software grow organically and adapt as needed. Solve problems as they come by but make sure everything still has its place.
+
+Doing this when it comes to software is even easier than doing this in cities due to the fact that **software is flexible, civil engineering is not**. **In the software world, our build time is compile time**. In Barcelona we cannot simply destroy buildings to give space to new ones, in Software we can do that a lot easier. We can break things all the time, we can make experiments because we can build as many times as we want and it usually takes seconds and we spend a lot more time thinking than building. Our job is purely intellectual.
+
+So **act like a town planner, let your software grow and adapt as needed**.
+
+By doing this you will also have better abstractions and know when it’s the right time to adopt them.
+
+As Sam Koblenski says:
+
+> Abstractions only work well in the right context, and the right context develops as the system develops.
+
+Nowadays something I see very often is people looking for boilerplates when they’re trying to learn a new technology, but, in my opinion, **you should avoid boilerplates when you’re starting out**. Of course boilerplates and generators are useful if you are already experienced, but they take a lot of control out of your hands and therefore you won’t learn how to set up a project and you won’t understand exactly where each piece of the software you are using fits.
+
+When you feel like you are struggling more than necessary to get something simple done, it might be the right time for you to look for an easier way to do this. In our role **you should strive to be lazy** , you should work to not work. By doing that you have more free time to do other things and this decreases cost and increases revenue, so that’s another way of accomplishing your goal. You should not only work harder, you should work smarter.
+
+Probably someone has already had the same problem as you’re having right now, but if nobody did it might be your time to shine and build your own solution and help other people.
+
+But sometimes you will not be able to realize you could be more effective in your tasks until you see someone doing them better. This is why it is so important to **talk to people**.
+
+By talking to people you share experiences that help each other’s careers and we discover new tools to improve our workflow and, even more important than that, learn how they solve their problems. This is why I like reading blog posts in which companies explain how they solve their problems.
+
+Especially in our area we like to think that Google and StackOverflow can answer all our questions, but we still need to know which questions to ask. I’m sure you have already had a problem you could not find a solution for because you didn’t know exactly what was happening and therefore didn’t know what was the right question to ask.
+
+But if I needed to sum this whole post in a single advice, it would be:
+
+Solve problems.
+
+Software is not a magic box, software is not poetry (unfortunately). It exists to solve problems and improves peoples’ lives. Software exists to push the world forward.
+
+**Now it’s your time to go out there and solve problems**.
+
+
+--------------------------------------------------------------------------------
+
+via: https://lucasfcosta.com/2017/07/17/The-Ultimate-Guide-to-JavaScript-Fatigue.html
+
+作者:[Lucas Fernandes Da Costa][a]
+选题:[lujun9972][b]
+译者:[译者ID](https://github.com/译者ID)
+校对:[校对者ID](https://github.com/校对者ID)
+
+本文由 [LCTT](https://github.com/LCTT/TranslateProject) 原创编译,[Linux中国](https://linux.cn/) 荣誉推出
+
+[a]: https://lucasfcosta.com
+[b]: https://github.com/lujun9972
+[1]: http://www.kalzumeus.com/2011/10/28/dont-call-yourself-a-programmer/
+[2]: http://ieeexplore.ieee.org/document/1702333/
+[3]: https://en.wikipedia.org/wiki/Test_Driven_Development
+[4]: https://en.wikipedia.org/wiki/Analysis_paralysis
+[5]: https://babeljs.io/blog/2016/12/07/the-state-of-babel
+[6]: http://requirejs.org
+[7]: https://benmccormick.org/2015/05/28/moving-past-requirejs/
+[8]: https://medium.freecodecamp.org/a-study-plan-to-cure-javascript-fatigue-8ad3a54f2eb1
+[9]: https://www.quora.com/What-did-Richard-Feynman-mean-when-he-said-What-I-cannot-create-I-do-not-understand
+[10]: https://egghead.io/lessons/javascript-redux-implementing-store-from-scratch
+[11]: https://jasonformat.com/wtf-is-jsx/
+[12]: https://www.barnesandnoble.com/p/building-microservices-sam-newman/1119741399/2677517060476?st=PLA&sid=BNB_DRS_Marketplace+Shopping+Books_00000000&2sid=Google_&sourceId=PLGoP4760&k_clickid=3x4760
+[13]: /assets/barcelona-city.jpeg
+[14]: /assets/barcelona-above.jpeg
+[15]: https://twitter.com/thewizardlucas
diff --git a/sources/talk/20171222 18 Cyber-Security Trends Organizations Need to Brace for in 2018.md b/sources/talk/20171222 18 Cyber-Security Trends Organizations Need to Brace for in 2018.md
deleted file mode 100644
index 09223ccb21..0000000000
--- a/sources/talk/20171222 18 Cyber-Security Trends Organizations Need to Brace for in 2018.md
+++ /dev/null
@@ -1,116 +0,0 @@
-18 Cyber-Security Trends Organizations Need to Brace for in 2018
-======
-
-### 18 Cyber-Security Trends Organizations Need to Brace for in 2018
-
-Enterprises, end users and governments faced no shortage of security challenges in 2017. Some of those same challenges will continue into 2018, and there will be new problems to solve as well. Ransomware has been a concern for several years and will likely continue to be a big issue in 2018. The new year is also going to bring the formal introduction of the European Union's General Data Protection Regulation (GDPR), which will impact how organizations manage private information. A key trend that emerged in 2017 was an increasing use of artificial intelligence (AI) to help solve cyber-security challenges, and that's a trend that will continue to accelerate in 2018. What else will the new year bring? In this slide show, eWEEK presents 18 security predictions for the year ahead from 18 security experts.
-
-
-### Africa Emerges as New Area for Threat Actors and Targets
-
-"In 2018, Africa will emerge as a new focus area for cyber-threats--both targeting organizations based there and attacks originating from the continent. With its growth in technology adoption and operations and rising economy, and its increasing number of local resident threat actors, Africa has the largest potential for net-new impactful cyber events." -Steve Stone, IBM X-Force IRIS
-
-
-### AI vs. AI
-
-"2018 will see a rise in AI-based attacks as cyber-criminals begin using machine learning to spoof human behaviors. The cyber-security industry will need to tune their own AI tools to better combat the new threats. The cat and mouse game of cybercrime and security innovation will rapidly escalate to include AI-enabled tools on both sides." --Caleb Barlow, vice president of Threat Intelligence, IBM Security
-
-
-### Cyber-Security as a Growth Driver
-
-"CEOs view cyber-security as one of their top risks, but many also see it as an opportunity to innovate and find new ways to generate revenue. In 2018 and beyond, effective cyber-security measures will support companies that are transforming their security, privacy and continuity controls in an effort to grow their businesses." -Greg Bell, KMPG's Global Cyber Security Practice co-leader
-
-
-### GDPR Means Good Enough Isn't Good Enough
-
-"Too many professionals share a 'good enough' philosophy that they've adopted from their consumer mindset that they can simply upgrade and patch to comply with the latest security and compliance best practices or regulations. In 2018, with the upcoming enforcement of the EU GDPR 'respond fast' rules, organizations will quickly come to terms, and face fines, with why 'good enough' is not 'good' anymore." -Kris Lovejoy, CEO of BluVector
-
-
-### Consumerization of Cyber-Security
-
-"2018 will mark the debut of the 'consumerization of cyber-security.' This means consumers will be offered a unified, comprehensive suite of security offerings, including, in addition to antivirus and spyware protection, credit and identify abuse monitoring and identity restoration. This is a big step forward compared to what is available in one package today. McAfee Total Protection, which safeguards consumer identities in addition to providing virus and malware protection, is an early, simplified example of this. Consumers want to feel more secure." -Don Dixon, co-founder and managing director, Trident Capital Cybersecurity
-
-
-### Ransomware Will Continue
-
-"Ransomware will continue to plague organizations with 'old' attacks 'refreshed' and reused. The threat of ransomware will continue into 2018. This year we've seen ransomware wreak havoc across the globe with both WannaCry and NotPetya hitting the headlines. Threats of this type and on this scale will be a common feature of the next 12 months." -Andrew Avanessian, chief operating officer at Avecto
-
-
-### More Encryption Will Be Needed
-
-"It will become increasingly clear in the industry that HTTPS does not offer the robust security and end-to-end encryption as is commonly believed, and there will be a push to encrypt data before it is sent over HTTPS." -Darren Guccione, CEO and co-founder, Keeper Security
-
-
-### Denial of Service Will Become Financially Lucrative
-
-"Denial of service will become as financially lucrative as identity theft. Using stolen identities for new account fraud has been the major revenue driver behind breaches. However, in recent years ransomware attacks have caused as much if not more damage, as increased reliance on distributed applications and cloud services results in massive business damage when information, applications or systems are held hostage by attackers." -John Pescatore. SANS' director of emerging security trends
-
-
-### Goodbye Social Security Number
-
-"2018 is the turning point for the retirement of the Social Security number. At this point, the vast majority of SSNs are compromised, and we can no longer rely on them--nor should we have previously." -Michael Sutton, CISO, Zscaler
-
-
-### Post-Quantum Cyber-Security Discussion Warms Up the Boardroom
-
-"The uncertainty of cyber-security in a post-quantum world is percolating some circles, but 2018 is the year the discussions gain momentum in the top levels of business. As security experts grapple with preparing for a post-quantum world, top executives will begin to ask what can be done to ensure all of our connected 'things' remain secure." -Malte Pollmann, CEO of Utimaco
-
-
-### Market Consolidation Is Coming
-
-"There will be accelerated consolidation of cyber niche markets flooded with too many 'me-too' companies offering extremely similar products and services. As an example, authentication, end-point security and threat intelligence now boast a total of more than 25 competitors. Ultimately, only three to six companies in each niche can survive." -Mike Janke, co-founder of DataTribe
-
-
-### Health Care Will Be a Lucrative Target
-
-"Health records are highly valued on the black market because they are saturated with Personally Identifiable Information (PII). Health care institutions will continue to be a target as they have tighter allocations for security in their IT budgets. Also, medical devices are hard to update and often run on older operating system versions." -Larry Cashdollar, senior engineer, Security Intelligence Response Team, Akamai
-
-
-### 2018: The Year of Simple Multifactor Authentication for SMBs
-
-"Unfortunately, effective multifactor authentication (MFA) solutions have remained largely out of reach for the average small- and medium-sized business. Though enterprise multifactor technology is quite mature, it often required complex on-premises solutions and expensive hardware tokens that most small businesses couldn't afford or manage. However, the growth of SaaS and smartphones has introduced new multifactor solutions that are inexpensive and easy for small businesses to use. Next year, many SMBs will adopt these new MFA solutions to secure their more privileged accounts and users. 2018 will be the year of MFA for SMBs." -Corey Nachreiner, CTO at WatchGuard Technologies
-
-
-### Automation Will Improve the IT Skills Gap
-
-"The security skills gap is widening every year, with no signs of slowing down. To combat the skills gap and assist in the growing adoption of advanced analytics, automation will become an even higher priority for CISOs." -Haiyan Song, senior vice president of Security Markets at Splunk
-
-
-### Industrial Security Gets Overdue Attention
-
-"The high-profile attacks of 2017 acted as a wake-up call, and many plant managers now worry that they could be next. Plant manufacturers themselves will offer enhanced security. Third-party companies going on their own will stay in a niche market. The industrial security manufacturers themselves will drive a cooperation with the security industry to provide security themselves. This is because there is an awareness thing going on and impending government scrutiny. This is different from what happened in the rest of IT/IoT where security vendors just go to market by themselves as a layer on top of IT (i.e.: an antivirus on top of Windows)." -Renaud Deraison, co-founder and CTO, Tenable
-
-
-### Cryptocurrencies Become the New Playground for Identity Thieves
-
-"The rising value of cryptocurrencies will lead to greater attention from hackers and bad actors. Next year we'll see more fraud, hacks and money laundering take place across the top cryptocurrency marketplaces. This will lead to a greater focus on identity verification and, ultimately, will result in legislation focused on trader identity." -Stephen Maloney, executive vice president of Business Development & Strategy, Acuant
-
-
-### GDPR Compliance Will Be a Challenge
-
-"In 2018, three quarters of companies or apps will be ruled out of compliance with GDPR and at least one major corporation will be fined to the highest extent in 2018 to set an example for others. Most companies are preparing internally by performing more security assessments and recruiting a mix of security professionals with privacy expertise and lawyers, but with the deadline quickly approaching, it's clear the bulk of businesses are woefully behind and may not be able to avoid these consequences." -Sanjay Beri, founder and CEO, Netskope
-
-
-### Data Security Solidifies Its Spot in the IT Security Stack
-
-"Many businesses are stuck in the mindset that security of networks, servers and applications is sufficient to protect their data. However, the barrage of breaches in 2017 highlights a clear disconnect between what organizations think is working and what actually works. In 2018, we expect more businesses to implement data security solutions that complement their existing network security deployments." -Jim Varner, CEO of SecurityFirst
-
-
-### [Eight Cyber-Security Vendors Raise New Funding in November 2017][1]
-
-Though the pace of funding slowed in November, multiple firms raised new venture capital to develop and improve their cyber-security products.
-
-Though the pace of funding slowed in November, multiple firms raised new venture capital to develop and improve their cyber-security products.
-
---------------------------------------------------------------------------------
-
-via: http://voip.eweek.com/security/18-cyber-security-trends-organizations-need-to-brace-for-in-2018
-
-作者:[Sean Michael Kerner][a]
-译者:[译者ID](https://github.com/译者ID)
-校对:[校对者ID](https://github.com/校对者ID)
-
-本文由 [LCTT](https://github.com/LCTT/TranslateProject) 原创编译,[Linux中国](https://linux.cn/) 荣誉推出
-
-[a]:http://voip.eweek.com/Authors/sean-michael-kerner
-[1]:http://voip.eweek.com/security/eight-cyber-security-vendors-raise-new-funding-in-november-2017
diff --git a/sources/talk/20180209 A review of Virtual Labs virtualization solutions for MOOCs - WebLog Pro Olivier Berger.md b/sources/talk/20180209 A review of Virtual Labs virtualization solutions for MOOCs - WebLog Pro Olivier Berger.md
deleted file mode 100644
index 0cb3755ca1..0000000000
--- a/sources/talk/20180209 A review of Virtual Labs virtualization solutions for MOOCs - WebLog Pro Olivier Berger.md
+++ /dev/null
@@ -1,255 +0,0 @@
-A review of Virtual Labs virtualization solutions for MOOCs – WebLog Pro Olivier Berger
-======
-### 1 Introduction
-
-This is a memo that tries to capture some of the experience gained in the [FLIRT project][3] on the topic of Virtual Labs for MOOCs (Massive Open Online Courses).
-
-In this memo, we try to draw an overview of some benefits and concerns with existing approaches at using virtualization techniques for running Virtual Labs, as distributions of tools made available for distant learners.
-
-We describe 3 main technical architectures: (1) running Virtual Machine images locally on a virtual machine manager, or (2) displaying the remote execution of similar virtual machines on a IaaS cloud, and (3) the potential of connecting to the remote execution of minimized containers on a remote PaaS cloud.
-
-We then elaborate on some perspectives for locally running ports of applications to the WebAssembly virtual machine of the modern Web browsers.
-
-Disclaimer: This memo doesn’t intend to point to extensive literature on the subject, so part of our analysis may be biased by our particular context.
-
-### 2 Context : MOOCs
-
-Many MOOCs (Massive Open Online Courses) include a kind of “virtual laboratory” for learners to experiment with tools, as a way to apply the knowledge, practice, and be more active in the learning process. In quite a few (technical) disciplines, this can consist in using a set of standard applications in a professional domain, which represent typical tools that would be used in real life scenarii.
-
-Our main perspective will be that of a MOOC editor and of MOOC production teams which want to make “virtual labs” available for MOOC participants.
-
-Such a “virtual lab” would typically contain installations of existing applications, pre-installed and configured, and loaded with scenario data in order to perform a lab.
-
-The main constraint here is that such labs would typically be fabricated with limited software development expertise and funds[1][4]. Thus we consider here only the assembly of existing “normal” applications and discard the option of developping novel “serious games” and simulator applications for such MOOCs.
-
-#### 2.1 The FLIRT project
-
-The [FLIRT project][5] groups a consortium of 19 partners in Industry, SMEs and Academia to work on a collection of MOOCs and SPOCs for professional development in Networks and Telecommunications. Lead by Institut Mines Telecom, it benefits from the funding support of the French “Investissements d’avenir” programme.
-
-As part of the FLIRT roadmap, we’re leading an “innovation task” focused on Virtual Labs in the context of the Cloud. This memo was produced as part of this task.
-
-#### 2.2 Some challenges in virtual labs design for distant learning
-
-Virtual Labs used in distance learning contexts require the use of software applications in autonomy, either running on a personal, or professional computer. In general, the technical skills of participants may be diverse. So much for the quality (bandwith, QoS, filtering, limitations: firewaling) of the hardware and networks they use at home or at work. It’s thus very optimistic to seek for one solution fits all strategy.
-
-Most of the time there’s a learning curve on getting familiar with the tools which students will have to use, which constitutes as many challenges to overcome for beginners. These tools may not be suited for beginners, but they will still be selected by the trainers as they’re representative of the professional context being taught.
-
-In theory, this usability challenge should be addressed by devising an adapted pedagogical approach, especially in a context of distance learning, so that learners can practice the labs on their own, without the presence of a tutor or professor. Or some particular prerequisite skills could be required (“please follow System Administration 101 before applying to this course”).
-
-Unfortunately there are many cases where instructors basically just translate to a distant learning scenario, previous lab resources that had previously been devised for in presence learning. This lets learner faced with many challenges to overcome. The only support resource is often a regular forum on the MOOC’s LMS (Learning Management System).
-
-My intuition[2][6] is that developing ad-hoc simulators for distant education would probably be more efficient and easy to use for learners. But that would require a too high investment for the designers of the courses.
-
-In the context of MOOCs which are mainly free to participate to, not much investment is possible in devising ad-hoc lab applications, and instructors have to rely on existing applications, tools and scenarii to deliver a cheap enough environment. Furthermore, technical or licensing constraints[3][7] may lead to selecting lab tools which may not be easy to learn, but have the great advantage or being freely redistributable[4][8].
-
-### 3 Virtual Machines for Virtual Labs
-
-The learners who will try unattended learning in such typical virtual labs will face difficulties in making specialized applications run. They must overcome the technical details of downloading, installing and configuring programs, before even trying to perform a particular pedagogical scenario linked to the matter studied.
-
-To diminish these difficulties, one traditional approach for implementing labs in MOOCs has been to assemble in advance a Virtual Machine image. This already made image can then be downloaded and run with a virtual machine simulator (like [VirtualBox][9][5][10]).
-
-The pre-loaded VM will already have everything ready for use, so that the learners don’t have to install anything on their machines.
-
-An alternative is to let learners download and install the needed software tools themselves, but this leads to so many compatibility issues or technical skill prerequisites, that this is often not advised, and mentioned only as a fallback option.
-
-#### 3.1 Downloading and installation issues
-
-Experience shows[2][11] that such virtual machines also bring some issues. Even if installation of every piece of software is no longer required, learners still need to be able to run the VM simulator on a wide range of diverse hardware, OSes and configurations. Even managing to download the VMs, still causes many issues (lack admin privileges, weight vs download speed, memory or CPU load, disk space, screen configurations, firewall filtering, keayboard layout, etc.).
-
-These problems aren’t generally faced by the majority of learners, but the impacted minority is not marginal either, and they generally will produce a lot of support requests for the MOOC team (usually in the forums), which needs to be anticipated by the community managers.
-
-The use of VMs is no show stopper for most, but can be a serious problem for a minority of learners, and is then no silver bullet.
-
-Some general usability issues may also emerge if users aren’t used to the look and feel of the enclosed desktop. For instance, the VM may consist of a GNU/Linux desktop, whereas users would use a Windows or Mac OS system.
-
-#### 3.2 Fabrication issues for the VM images
-
-On the MOOC team’s side, the fabrication of a lightweight, fast, tested, license-free and easy to use VM image isn’t necessarily easy.
-
-Software configurations tend to rot as time passes, and maintenance may not be easy when the later MOOC editions evolutions lead to the need to maintain the virtual lab scenarii years later.
-
-Ideally, this would require adopting an “industrial” process in building (and testing) the lab VMs, but this requires quite an expertise (system administration, packaging, etc.) that may or not have been anticipated at the time of building the MOOC (unlike video editing competence, for instance).
-
-Our experiment with the [Vagrant][12] technology [[0][13]] and Debian packaging was interesting in this respect, as it allowed us to use a well managed “script” to precisely control the build of a minimal VM image.
-
-### 4 Virtual Labs as a Service
-
-To overcome the difficulties in downloading and running Virtual Machines on one’s local computer, we have started exploring the possibility to run these applications in a kind of Software as a Service (SaaS) context, “on the cloud”.
-
-But not all applications typically used in MOOC labs are already available for remote execution on the cloud (unless the course deals precisely with managing email in GMail).
-
-We have then studied the option to use such an approach not for a single application, but for a whole virtual “desktop” which would be available on the cloud.
-
-#### 4.1 IaaS deployments
-
-A way to achieve this goal is to deploy Virtual Machine images quite similar to the ones described above, on the cloud, in an Infrastructure as a Service (IaaS) context[6][14], to offer access to remote desktops for every learners.
-
-There are different technical options to achieve this goal, but a simplified description of the architecture can be seen as just running Virtual Machines on a single IaaS platform instead of on each learner’s computer. Access to the desktop and application interfaces is made possible with the use of Web pages (or other dedicated lightweight clients) which will display a “full screen” display of the remote desktop running for the user on the cloud VM. Under the hood, the remote display of a Linux desktop session is made with technologies like [VNC][15] and [RDP][16] connecting to a [Guacamole][17] server on the remote VM.
-
-In the context of the FLIRT project, we have made early experiments with such an architecture. We used the CloVER solution by our partner [ProCAN][18] which provides a virtual desktops broker between [OpenEdX][19] and an [OpenStack][20] IaaS public platform.
-
-The expected benefit is that users don’t have to install anything locally, as the only tool needed locally is a Web browser (displaying a full-screen [HTML5 canvas][21] displaying the remote desktop run by the Guacamole server running on the cloud VM.
-
-But there are still some issues with such an approach. First, the cost of operating such an infrastructure : Virtual Machines need to be hosted on a IaaS platform, and that cost of operation isn’t null[7][22] for the MOOC editor, compared to the cost of VirtualBox and a VM running on the learner’s side (basically zero for the MOOC editor).
-
-Another issue, which could be more problematic lies in the need for a reliable connection to the Internet during the whole sequences of lab execution by the learners[8][23]. Even if Guacamole is quite efficient at compressing rendering traffic, some basic connectivity is needed during the whole Lab work sessions, preventing some mobile uses for instance.
-
-One other potential annoyance is the potential delays for making a VM available to a learner (provisioning a VM), when huge VMs images need to be copied inside the IaaS platform when a learner connects to the Virtual Lab activity for the first time (several minutes delays). This may be worse if the VM image is too big (hence the need for optimization of the content[9][24]).
-
-However, the fact that all VMs are running on a platform under the control of the MOOC editor allows new kind of features for the MOOC. For instance, learners can submit results of their labs directly to the LMS without the need to upload or copy-paste results manually. This can help monitor progress or perform evaluation or grading.
-
-The fact that their VMs run on the same platform also allows new kinds of pedagogical scenarii, as VMs of multiple learners can be interconnected, allowing cooperative activities between learners. The VM images may then need to be instrumented and deployed in particular configurations, which may require the use of a dedicated broker like CloVER to manage such scenarii.
-
-For the records, we have yet to perform a rigorous benchmarking of such a solution in order to evaluate its benefits, or constraints given particular contexts. In FLIRT, our main focus will be in the context of SPOCs for professional training (a bit different a context than public MOOCs).
-
-Still this approach doesn’t solve the VMs fabrication issues for the MOOC staff. Installing software inside a VM, be it local inside a VirtualBox simulator of over the cloud through a remote desktop display, makes not much difference. This relies mainly on manual operations and may not be well managed in terms of quality of the process (reproducibility, optimization).
-
-#### 4.2 PaaS deployments using containers
-
-Some key issues in the IaaS context described above, are the cost of operation of running full VMs, and long provisioning delays.
-
-We’re experimenting with new options to address these issues, through the use of [Linux containers][25] running on a PaaS (Platform as a Service) platform, instead of full-fleshed Virtual Machines[10][26].
-
-The main difference, with containers instead of Virtual Machines, lies in the reduced size of images, and much lower CPU load requirements, as the container remove the need for one layer of virtualization. Also, the deduplication techniques at the heart of some virtual file-systems used by container platforms lead to really fast provisioning, avoiding the need to wait for the labs to start.
-
-The traditional making of VMs, done by installing packages and taking a snapshot, was affordable for the regular teacher, but involved manual operations. In this respect, one other major benefit of containers is the potential for better industrialization of the virtual lab fabrication, as they are generally not assembled manually. Instead, one uses a “scripting” approach in describing which applications and their dependencies need to be put inside a container image. But this requires new competence from the Lab creators, like learning the [Docker][27] technology (and the [OpenShift][28] PaaS, for instance), which may be quite specialized. Whereas Docker containers tend to become quite popular in Software Development faculty (through the “[devops][29]” hype), they may be a bit new to other field instructors.
-
-The learning curve to mastering the automation of the whole container-based labs installation needs to be evaluated. There’s a trade-off to consider in adopting technology like Vagrant or Docker: acquiring container/PaaS expertise vs quality of industrialization and optimization. The production of a MOOC should then require careful planning if one has to hire or contract with a PaaS expert for setting up the Virtual Labs.
-
-We may also expect interesting pedagogical benefits. As containers are lightweight, and platforms allow to “easily” deploy multiple interlinked containers (over dedicated virtual networks), this enables the setup of more realistic scenarii, where each learner may be provided with multiple “nodes” over virtual networks (all running their individual containers). This would be particularly interesting for Computer Networks or Security teaching for instance, where each learner may have access both to client and server nodes, to study client-server protocols, for instance. This is particularly interesting for us in the context of our FLIRT project, where we produce a collection of Computer Networks courses.
-
-Still, this mode of operation relies on a good connectivity of the learners to the Cloud. In contexts of distance learning in poorly connected contexts, the PaaS architecture doesn’t solve that particular issue compared to the previous IaaS architecture.
-
-### 5 Future server-less Virtual Labs with WebAssembly
-
-As we have seen, the IaaS or PaaS based Virtual Labs running on the Cloud offer alternatives to installing local virtual machines on the learner’s computer. But they both require to be connected for the whole duration of the Lab, as the applications would be executed on the remote servers, on the Cloud (either inside VMs or containers).
-
-We have been thinking of another alternative which could allow the deployment of some Virtual Labs on the local computers of the learners without the hassles of downloading and installing a Virtual Machine manager and VM image. We envision the possibility to use the infrastructure provided by modern Web browsers to allow running the lab’s applications.
-
-At the time of writing, this architecture is still highly experimental. The main idea is to rebuild the applications needed for the Lab so that they can be run in the “generic” virtual machine present in the modern browsers, the [WebAssembly][30] and Javascript execution engine.
-
-WebAssembly is a modern language which seeks for maximum portability, and as its name hints, is a kind of assembly language for the Web platform. What is of interest for us is that WebAssembly is portable on most modern Web browsers, making it a very interesting platform for portability.
-
-Emerging toolchains allow recompiling applications written in languages like C or C++ so that they can be run on the WebAssembly virtual machine in the browser. This is interesting as it doesn’t require modifying the source code of these programs. Of course, there are limitations, in the kind of underlying APIs and libraries compatible with that platform, and on the sandboxing of the WebAssembly execution engine enforced by the Web browser.
-
-Historically, WebAssembly has been developped so as to allow running games written in C++ for a framework like Unity, in the Web browser.
-
-In some contexts, for instance for tools with an interactive GUI, and processing data retrieved from files, and which don’t need very specific interaction with the underlying operating system, it seems possible to port these programs to WebAssembly for running them inside the Web browser.
-
-We have to experiment deeper with this technology to validate its potential for running Virtual Labs in the context of a Web browser.
-
-We used a similar approach in the past in porting a Relational Database course lab to the Web browser, for standalone execution. A real database would run in the minimal SQLite RDBMS, recompiled to JavaScript[11][31]. Instead of having to download, install and run a VM with a RDBMS, the students would only connect to a Web page, which would load the DBMS in memory, and allow performing the lab SQL queries locally, disconnected from any third party server.
-
-In a similar manner, we can think for instance, of a Lab scenario where the Internet packet inspector features of the Wireshark tool would run inside the WebAssembly virtual machine, to allow dissecting provided capture files, without having to install Wireshard, directly into the Web browser.
-
-We expect to publish a report on that last experiment in the future with more details and results.
-
-### 6 Conclusion
-
-The most promising architecture for Virtual Lab deployments seems to be the use of containers on a PaaS platform for deploying virtual desktops or virtual application GUIs available in the Web browser.
-
-This would allow the controlled fabrication of Virtual Labs containing the exact bits needed for learners to practice while minimizing the delays.
-
-Still the need for always-on connectivity can be a problem.
-
-Also, the potential for inter-networked containers allowing the kind of multiple nodes and collaborative scenarii we described, would require a lot of expertise to develop, and management platforms for the MOOC operators, which aren’t yet mature.
-
-We hope to be able to report on our progress in the coming months and years on those aspects.
-
-### 7 References
-
-
-
-[0]
-Olivier Berger, J Paul Gibson, Claire Lecocq and Christian Bac “Designing a virtual laboratory for a relational database MOOC”. International Conference on Computer Supported Education, SCITEPRESS, 23-25 may 2015, Lisbonne, Portugal, 2015, vol. 7, pp. 260-268, ISBN 978-989-758-107-6 – [DOI: 10.5220/0005439702600268][1] ([preprint (HTML)][2])
-
-### 8 Copyright
-
- [][45]
-
-This work is licensed under a [Creative Commons Attribution-NonCommercial-ShareAlike 4.0 International License][46]
-
-.
-
-### Footnotes:
-
-[1][32] – The FLIRT project also works on business model aspects of MOOC or SPOC production in the context of professional development, but the present memo starts from a minimalitic hypothesis where funding for course production is quite limited.
-
-[2][33] – research-based evidence needed
-
-[3][34] – In typical MOOCs which are free to participate, the VM should include only gratis tools, which typically means a GNU/Linux distribution loaded with applications available under free and open source licenses.
-
-[4][35] – Typically, Free and Open Source software, aka Libre Software
-
-[5][36] – VirtualBox is portable on many operating systems, making it a very popular solution for such a need
-
-[6][37] – the IaaS platform could typically be an open cloud for MOOCs or a private cloud for SPOCs (for closer monitoring of student activity or security control reasons).
-
-[7][38] – Depending of the expected use of the lab by learners, this cost may vary a lot. The size and configuration required for the included software may have an impact (hence the need to minimize the footprint of the VM images). With diminishing costs in general this may not be a show stopper. Refer to marketing figures of commercial IaaS offerings for accurate figures. Attention to additional licensing costs if the OS of the VM isn’t free software, or if other licenses must be provided for every learners.
-
-[8][39] – The needs for always-on connectivity may not be a problem for professional development SPOCs where learners connect from enterprise networks for instance. It may be detrimental when MOOCs are very popular in southern countries where high bandwidth is both unreliable and expensive.
-
-[9][40] – In this respect, providing a full Linux desktop inside the VM doesn’t necessarily make sense. Instead, running applications full-screen may be better, avoiding installation of whole desktop environments like Gnome or XFCE… but which has usability consequences. Careful tuning and testing is needed in any case.
-
-[10][41] – The availability of container based architectures is quite popular in the industry, but has not yet been deployed to a large scale in the context of large public MOOC hosting platforms, to our knowledge, at the time of writing. There are interesting technical challenges which the FLIRT project tries to tackle together with its partner ProCAN.
-
-[11][42] – See the corresponding paragraph [http://www-inf.it-sudparis.eu/PROSE/csedu2015/#standalone-sql-env][43] in [0][44]
-
-
---------------------------------------------------------------------------------
-
-via: https://www-public.tem-tsp.eu/~berger_o/weblog/a-review-of-virtual-labs-virtualization-solutions-for-moocs/
-
-作者:[Author;Olivier Berger;Télécom Sudparis][a]
-译者:[译者ID](https://github.com/译者ID)
-校对:[校对者ID](https://github.com/校对者ID)
-
-本文由 [LCTT](https://github.com/LCTT/TranslateProject) 原创编译,[Linux中国](https://linux.cn/) 荣誉推出
-
-[a]:https://www-public.tem-tsp.eu
-[1]:http://dx.doi.org/10.5220/0005439702600268
-[2]:http://www-inf.it-sudparis.eu/PROSE/csedu2015/
-[3]:https://www-public.tem-tsp.eu/~berger_o/weblog/a-review-of-virtual-labs-virtualization-solutions-for-moocs/#org50fdc1a
-[4]:https://www-public.tem-tsp.eu/~berger_o/weblog/a-review-of-virtual-labs-virtualization-solutions-for-moocs/#fn.1
-[5]:http://flirtmooc.wixsite.com/flirt-mooc-telecom
-[6]:https://www-public.tem-tsp.eu/~berger_o/weblog/a-review-of-virtual-labs-virtualization-solutions-for-moocs/#fn.2
-[7]:https://www-public.tem-tsp.eu/~berger_o/weblog/a-review-of-virtual-labs-virtualization-solutions-for-moocs/#fn.3
-[8]:https://www-public.tem-tsp.eu/~berger_o/weblog/a-review-of-virtual-labs-virtualization-solutions-for-moocs/#fn.4
-[9]:http://virtualbox.org
-[10]:https://www-public.tem-tsp.eu/~berger_o/weblog/a-review-of-virtual-labs-virtualization-solutions-for-moocs/#fn.5
-[11]:https://www-public.tem-tsp.eu/~berger_o/weblog/a-review-of-virtual-labs-virtualization-solutions-for-moocs/#fn.2
-[12]:https://www.vagrantup.com/
-[13]:https://www-public.tem-tsp.eu/~berger_o/weblog/a-review-of-virtual-labs-virtualization-solutions-for-moocs/#orgde5af50
-[14]:https://www-public.tem-tsp.eu/~berger_o/weblog/a-review-of-virtual-labs-virtualization-solutions-for-moocs/#fn.6
-[15]:https://en.wikipedia.org/wiki/Virtual_Network_Computing
-[16]:https://en.wikipedia.org/wiki/Remote_Desktop_Protocol
-[17]:http://guacamole.apache.org/
-[18]:https://www.procan-group.com/
-[19]:https://open.edx.org/
-[20]:http://openstack.org/
-[21]:https://en.wikipedia.org/wiki/Canvas_element
-[22]:https://www-public.tem-tsp.eu/~berger_o/weblog/a-review-of-virtual-labs-virtualization-solutions-for-moocs/#fn.7
-[23]:https://www-public.tem-tsp.eu/~berger_o/weblog/a-review-of-virtual-labs-virtualization-solutions-for-moocs/#fn.8
-[24]:https://www-public.tem-tsp.eu/~berger_o/weblog/a-review-of-virtual-labs-virtualization-solutions-for-moocs/#fn.9
-[25]:https://www.redhat.com/en/topics/containers
-[26]:https://www-public.tem-tsp.eu/~berger_o/weblog/a-review-of-virtual-labs-virtualization-solutions-for-moocs/#fn.10
-[27]:https://en.wikipedia.org/wiki/Docker_(software)
-[28]:https://www.openshift.com/
-[29]:https://en.wikipedia.org/wiki/DevOps
-[30]:http://webassembly.org/
-[31]:https://www-public.tem-tsp.eu/~berger_o/weblog/a-review-of-virtual-labs-virtualization-solutions-for-moocs/#fn.11
-[32]:https://www-public.tem-tsp.eu/~berger_o/weblog/a-review-of-virtual-labs-virtualization-solutions-for-moocs/#fnr.1
-[33]:https://www-public.tem-tsp.eu/~berger_o/weblog/a-review-of-virtual-labs-virtualization-solutions-for-moocs/#fnr.2
-[34]:https://www-public.tem-tsp.eu/~berger_o/weblog/a-review-of-virtual-labs-virtualization-solutions-for-moocs/#fnr.3
-[35]:https://www-public.tem-tsp.eu/~berger_o/weblog/a-review-of-virtual-labs-virtualization-solutions-for-moocs/#fnr.4
-[36]:https://www-public.tem-tsp.eu/~berger_o/weblog/a-review-of-virtual-labs-virtualization-solutions-for-moocs/#fnr.5
-[37]:https://www-public.tem-tsp.eu/~berger_o/weblog/a-review-of-virtual-labs-virtualization-solutions-for-moocs/#fnr.6
-[38]:https://www-public.tem-tsp.eu/~berger_o/weblog/a-review-of-virtual-labs-virtualization-solutions-for-moocs/#fnr.7
-[39]:https://www-public.tem-tsp.eu/~berger_o/weblog/a-review-of-virtual-labs-virtualization-solutions-for-moocs/#fnr.8
-[40]:https://www-public.tem-tsp.eu/~berger_o/weblog/a-review-of-virtual-labs-virtualization-solutions-for-moocs/#fnr.9
-[41]:https://www-public.tem-tsp.eu/~berger_o/weblog/a-review-of-virtual-labs-virtualization-solutions-for-moocs/#fnr.10
-[42]:https://www-public.tem-tsp.eu/~berger_o/weblog/a-review-of-virtual-labs-virtualization-solutions-for-moocs/#fnr.11
-[43]:http://www-inf.it-sudparis.eu/PROSE/csedu2015/#standalone-sql-env
-[44]:https://www-public.tem-tsp.eu/~berger_o/weblog/a-review-of-virtual-labs-virtualization-solutions-for-moocs/#orgde5af50
-[45]:http://creativecommons.org/licenses/by-nc-sa/4.0/
-[46]:http://creativecommons.org/licenses/by-nc-sa/4.0/
diff --git a/sources/talk/20180604 10 principles of resilience for women in tech.md b/sources/talk/20180604 10 principles of resilience for women in tech.md
index 3f451089bb..e5d6b09401 100644
--- a/sources/talk/20180604 10 principles of resilience for women in tech.md
+++ b/sources/talk/20180604 10 principles of resilience for women in tech.md
@@ -1,93 +1,94 @@
-10 principles of resilience for women in tech
-======
-
-
-
-Being a woman in tech is pretty damn cool. For every headline about [what Silicon Valley thinks of women][1], there are tens of thousands of women building, innovating, and managing technology teams around the world. Women are helping build the future despite the hurdles they face, and the community of women and allies growing to support each other is stronger than ever. From [BetterAllies][2] to organizations like [Girls Who Code][3] and communities like the one I met recently at [Red Hat Summit][4], there are more efforts than ever before to create an inclusive community for women in tech.
-
-But the tech industry has not always been this welcoming, nor is the experience for women always aligned with the aspiration. And so we're feeling the pain. Women in technology roles have dropped from its peak in 1991 at 36% to 25% today, [according to a report by NCWIT][5]. [Harvard Business Review estimates][6] that more than half of the women in tech will eventually leave due to hostile work conditions. Meanwhile, Ernst & Young recently shared [a study][7] and found that merely 11% of high school girls are planning to pursue STEM careers.
-
-We have much work to do, lest we build a future that is less inclusive than the one we live in today. We need everyone at the table, in the lab, at the conference and in the boardroom.
-
-I've been interviewing both women and men for more than a year now about their experiences in tech, all as part of [The Chasing Grace Project][8], a documentary series about women in tech. The purpose of the series is to help recruit and retain female talent for the tech industry and to give women a platform to be seen, heard, and acknowledged for their experiences. We believe that compelling story can begin to transform culture.
-
-### What Chasing Grace taught me
-
-What I've learned is that no matter the dismal numbers, women want to keep building and they collectively possess a resilience unmatched by anything I've ever seen. And this is inspiring me. I've found a power, a strength, and a beauty in every story I've heard that is the result of resilience. I recently shared with the attendees at the Red Hat Summit Women’s Leadership Luncheon the top 10 principles of resilience I've heard from throughout my interviews so far. I hope that by sharing them here the ideas and concepts can support and inspire you, too.
-
-#### 1\. Practice optimism
-
-When taken too far, optimism can give you blind spots. But a healthy dose of optimism allows you to see the best in people and situations and that positive energy comes back to you 100-fold. I haven’t met a woman yet as part of this project who isn’t an optimist.
-
-#### 2\. Build mental toughness
-
-I haven’t met a woman yet as part of this project who isn’t an optimist.
-
-When I recently asked a 32-year-old tech CEO, who is also a single mom of three young girls, what being a CEO required she said _mental toughness_. It really summed up what I’d heard in other words from other women, but it connected with me on another level when she proceeded to tell me how caring for her daughter—who was born with a hole in heart—prepared her for what she would encounter as a tech CEO. Being mentally tough to her means fighting for what you love, persisting like a badass, and building your EQ as well as your IQ.
-
-#### 3\. Recognize your power
-
-When I recently asked a 32-year-old tech CEO, who is also a single mom of three young girls, what being a CEO required she said. It really summed up what I’d heard in other words from other women, but it connected with me on another level when she proceeded to tell me how caring for her daughter—who was born with a hole in heart—prepared her for what she would encounter as a tech CEO. Being mentally tough to her means fighting for what you love, persisting like a badass, and building your EQ as well as your IQ.
-
-Most of the women I’ve interviewed don’t know their own power and so they give it away unknowingly. Too many women have told me that they willingly took on the housekeeping roles on their teams—picking up coffee, donuts, office supplies, and making the team dinner reservations. Usually the only woman on their teams, this put them in a position to be seen as less valuable than their male peers who didn’t readily volunteer for such tasks. All of us, men and women, have innate powers. Identify and know what your powers are and understand how to use them for good. You have so much more power than you realize. Know it, recognize it, use it strategically, and don’t give it away. It’s yours.
-
-#### 4\. Know your strength
-
-Not sure whether you can confront your boss about why you haven’t been promoted? You can. You don’t know your strength until you exercise it. Then, you’re unstoppable. Test your strength by pushing your fear aside and see what happens.
-
-#### 5\. Celebrate vulnerability
-
-Every single successful women I've interviewed isn't afraid to be vulnerable. She finds her strength in acknowledging where she is vulnerable and she looks to connect with others in that same place. Exposing, sharing, and celebrating each other’s vulnerabilities allows us to tap into something far greater than simply asserting strength; it actually builds strength—mental and emotional muscle. One women with whom we’ve talked shared how starting her own tech company made her feel like she was letting her husband down. She shared with us the details of that conversation with her husband. Honest conversations that share our doubts and our aspirations is what makes women uniquely suited to lead in many cases. Allow yourself to be seen and heard. It’s where we grow and learn.
-
-#### 6\. Build community
-
-If it doesn't exist, build it.
-
-Building community seems like a no-brainer in the world of open source, right? But take a moment to think about how many minorities in tech, especially those outside the collaborative open source community, don’t always feel like part of the community. Many women in tech, for example, have told me they feel alone. Reach out and ask questions or answer questions in community forums, at meetups, and in IRC and Slack. When you see a woman alone at an event, consider engaging with her and inviting her into a conversation. Start a meetup group in your company or community for women in tech. I've been so pleased with the number of companies that host these groups. If it doesn't exists, build it.
-
-#### 7\. Celebrate victories
-
-Building community seems like a no-brainer in the world of open source, right? But take a moment to think about how many minorities in tech, especially those outside the collaborative open source community, don’t always feel like part of the community. Many women in tech, for example, have told me they feel alone. Reach out and ask questions or answer questions in community forums, at meetups, and in IRC and Slack. When you see a woman alone at an event, consider engaging with her and inviting her into a conversation. Start a meetup group in your company or community for women in tech. I've been so pleased with the number of companies that host these groups. If it doesn't exists, build it.
-
-One of my favorite Facebook groups is [TechLadies][9] because of its recurring hashtag #YEPIDIDTHAT. It allows women to share their victories in a supportive community. No matter how big or small, don't let a victory go unrecognized. When you recognize your wins, you own them. They become a part of you and you build on top of each one.
-
-#### 8\. Be curious
-
-Being curious in the tech community often means asking questions: How does that work? What language is that written in? How can I make this do that? When I've managed teams over the years, my best employees have always been those who ask a lot of questions, those who are genuinely curious about things. But in this context, I mean be curious when your gut tells you something doesn't seem right. _The energy in the meeting was off. Did he/she just say what I think he said?_ Ask questions. Investigate. Communicate openly and clearly. It's the only way change happens.
-
-#### 9\. Harness courage
-
-One women told me a story about a meeting in which the women in the room kept being dismissed and talked over. During the debrief roundtable portion of the meeting, she called it out and asked if others noticed it, too. Being a 20-year tech veteran, she'd witnessed and experienced this many times but she had never summoned the courage to speak up about it. She told me she was incredibly nervous and was texting other women in the room to see if they agreed it should be addressed. She didn't want to be a "troublemaker." But this kind of courage results in an increased understanding by everyone in that room and can translate into other meetings, companies, and across the industry.
-
-#### 10\. Share your story
-
-When people connect to compelling story, they begin to change behaviors.
-
-Share your experience with a friend, a group, a community, or an industry. Be empowered by the experience of sharing your experience. Stories change culture. When people connect to compelling story, they begin to change behaviors. When people act, companies and industries begin to transform.
-
-Share your experience with a friend, a group, a community, or an industry. Be empowered by the experience of sharing your experience. Stories change culture. When people connect to compelling story, they begin to change behaviors. When people act, companies and industries begin to transform.
-
-If you would like to support [The Chasing Grace Project][8], email Jennifer Cloer to learn more about how to get involved: [jennifer@wickedflicksproductions.com][10]
-
---------------------------------------------------------------------------------
-
-via: https://opensource.com/article/18/6/being-woman-tech-10-principles-resilience
-
-作者:[Jennifer Cloer][a]
-选题:[lujun9972](https://github.com/lujun9972)
-译者:[译者ID](https://github.com/译者ID)
-校对:[校对者ID](https://github.com/校对者ID)
-
-本文由 [LCTT](https://github.com/LCTT/TranslateProject) 原创编译,[Linux中国](https://linux.cn/) 荣誉推出
-
-[a]:https://opensource.com/users/jennifer-cloer
-[1]:http://www.newsweek.com/2015/02/06/what-silicon-valley-thinks-women-302821.html%E2%80%9D
-[2]:https://opensource.com/article/17/6/male-allies-tech-industry-needs-you%E2%80%9D
-[3]:https://twitter.com/GirlsWhoCode%E2%80%9D
-[4]:http://opensource.com/tags/red-hat-summit%E2%80%9D
-[5]:https://www.ncwit.org/sites/default/files/resources/womenintech_facts_fullreport_05132016.pdf%E2%80%9D
-[6]:Dhttp://www.latimes.com/business/la-fi-women-tech-20150222-story.html%E2%80%9D
-[7]:http://www.ey.com/us/en/newsroom/news-releases/ey-news-new-research-reveals-the-differences-between-boys-and-girls-career-and-college-plans-and-an-ongoing-need-to-engage-girls-in-stem%E2%80%9D
-[8]:https://www.chasinggracefilm.com/
-[9]:https://www.facebook.com/therealTechLadies/%E2%80%9D
-[10]:mailto:jennifer@wickedflicksproductions.com
+XYenChi is translating
+10 principles of resilience for women in tech
+======
+
+
+
+Being a woman in tech is pretty damn cool. For every headline about [what Silicon Valley thinks of women][1], there are tens of thousands of women building, innovating, and managing technology teams around the world. Women are helping build the future despite the hurdles they face, and the community of women and allies growing to support each other is stronger than ever. From [BetterAllies][2] to organizations like [Girls Who Code][3] and communities like the one I met recently at [Red Hat Summit][4], there are more efforts than ever before to create an inclusive community for women in tech.
+
+But the tech industry has not always been this welcoming, nor is the experience for women always aligned with the aspiration. And so we're feeling the pain. Women in technology roles have dropped from its peak in 1991 at 36% to 25% today, [according to a report by NCWIT][5]. [Harvard Business Review estimates][6] that more than half of the women in tech will eventually leave due to hostile work conditions. Meanwhile, Ernst & Young recently shared [a study][7] and found that merely 11% of high school girls are planning to pursue STEM careers.
+
+We have much work to do, lest we build a future that is less inclusive than the one we live in today. We need everyone at the table, in the lab, at the conference and in the boardroom.
+
+I've been interviewing both women and men for more than a year now about their experiences in tech, all as part of [The Chasing Grace Project][8], a documentary series about women in tech. The purpose of the series is to help recruit and retain female talent for the tech industry and to give women a platform to be seen, heard, and acknowledged for their experiences. We believe that compelling story can begin to transform culture.
+
+### What Chasing Grace taught me
+
+What I've learned is that no matter the dismal numbers, women want to keep building and they collectively possess a resilience unmatched by anything I've ever seen. And this is inspiring me. I've found a power, a strength, and a beauty in every story I've heard that is the result of resilience. I recently shared with the attendees at the Red Hat Summit Women’s Leadership Luncheon the top 10 principles of resilience I've heard from throughout my interviews so far. I hope that by sharing them here the ideas and concepts can support and inspire you, too.
+
+#### 1\. Practice optimism
+
+When taken too far, optimism can give you blind spots. But a healthy dose of optimism allows you to see the best in people and situations and that positive energy comes back to you 100-fold. I haven’t met a woman yet as part of this project who isn’t an optimist.
+
+#### 2\. Build mental toughness
+
+I haven’t met a woman yet as part of this project who isn’t an optimist.
+
+When I recently asked a 32-year-old tech CEO, who is also a single mom of three young girls, what being a CEO required she said _mental toughness_. It really summed up what I’d heard in other words from other women, but it connected with me on another level when she proceeded to tell me how caring for her daughter—who was born with a hole in heart—prepared her for what she would encounter as a tech CEO. Being mentally tough to her means fighting for what you love, persisting like a badass, and building your EQ as well as your IQ.
+
+#### 3\. Recognize your power
+
+When I recently asked a 32-year-old tech CEO, who is also a single mom of three young girls, what being a CEO required she said. It really summed up what I’d heard in other words from other women, but it connected with me on another level when she proceeded to tell me how caring for her daughter—who was born with a hole in heart—prepared her for what she would encounter as a tech CEO. Being mentally tough to her means fighting for what you love, persisting like a badass, and building your EQ as well as your IQ.
+
+Most of the women I’ve interviewed don’t know their own power and so they give it away unknowingly. Too many women have told me that they willingly took on the housekeeping roles on their teams—picking up coffee, donuts, office supplies, and making the team dinner reservations. Usually the only woman on their teams, this put them in a position to be seen as less valuable than their male peers who didn’t readily volunteer for such tasks. All of us, men and women, have innate powers. Identify and know what your powers are and understand how to use them for good. You have so much more power than you realize. Know it, recognize it, use it strategically, and don’t give it away. It’s yours.
+
+#### 4\. Know your strength
+
+Not sure whether you can confront your boss about why you haven’t been promoted? You can. You don’t know your strength until you exercise it. Then, you’re unstoppable. Test your strength by pushing your fear aside and see what happens.
+
+#### 5\. Celebrate vulnerability
+
+Every single successful women I've interviewed isn't afraid to be vulnerable. She finds her strength in acknowledging where she is vulnerable and she looks to connect with others in that same place. Exposing, sharing, and celebrating each other’s vulnerabilities allows us to tap into something far greater than simply asserting strength; it actually builds strength—mental and emotional muscle. One women with whom we’ve talked shared how starting her own tech company made her feel like she was letting her husband down. She shared with us the details of that conversation with her husband. Honest conversations that share our doubts and our aspirations is what makes women uniquely suited to lead in many cases. Allow yourself to be seen and heard. It’s where we grow and learn.
+
+#### 6\. Build community
+
+If it doesn't exist, build it.
+
+Building community seems like a no-brainer in the world of open source, right? But take a moment to think about how many minorities in tech, especially those outside the collaborative open source community, don’t always feel like part of the community. Many women in tech, for example, have told me they feel alone. Reach out and ask questions or answer questions in community forums, at meetups, and in IRC and Slack. When you see a woman alone at an event, consider engaging with her and inviting her into a conversation. Start a meetup group in your company or community for women in tech. I've been so pleased with the number of companies that host these groups. If it doesn't exists, build it.
+
+#### 7\. Celebrate victories
+
+Building community seems like a no-brainer in the world of open source, right? But take a moment to think about how many minorities in tech, especially those outside the collaborative open source community, don’t always feel like part of the community. Many women in tech, for example, have told me they feel alone. Reach out and ask questions or answer questions in community forums, at meetups, and in IRC and Slack. When you see a woman alone at an event, consider engaging with her and inviting her into a conversation. Start a meetup group in your company or community for women in tech. I've been so pleased with the number of companies that host these groups. If it doesn't exists, build it.
+
+One of my favorite Facebook groups is [TechLadies][9] because of its recurring hashtag #YEPIDIDTHAT. It allows women to share their victories in a supportive community. No matter how big or small, don't let a victory go unrecognized. When you recognize your wins, you own them. They become a part of you and you build on top of each one.
+
+#### 8\. Be curious
+
+Being curious in the tech community often means asking questions: How does that work? What language is that written in? How can I make this do that? When I've managed teams over the years, my best employees have always been those who ask a lot of questions, those who are genuinely curious about things. But in this context, I mean be curious when your gut tells you something doesn't seem right. _The energy in the meeting was off. Did he/she just say what I think he said?_ Ask questions. Investigate. Communicate openly and clearly. It's the only way change happens.
+
+#### 9\. Harness courage
+
+One women told me a story about a meeting in which the women in the room kept being dismissed and talked over. During the debrief roundtable portion of the meeting, she called it out and asked if others noticed it, too. Being a 20-year tech veteran, she'd witnessed and experienced this many times but she had never summoned the courage to speak up about it. She told me she was incredibly nervous and was texting other women in the room to see if they agreed it should be addressed. She didn't want to be a "troublemaker." But this kind of courage results in an increased understanding by everyone in that room and can translate into other meetings, companies, and across the industry.
+
+#### 10\. Share your story
+
+When people connect to compelling story, they begin to change behaviors.
+
+Share your experience with a friend, a group, a community, or an industry. Be empowered by the experience of sharing your experience. Stories change culture. When people connect to compelling story, they begin to change behaviors. When people act, companies and industries begin to transform.
+
+Share your experience with a friend, a group, a community, or an industry. Be empowered by the experience of sharing your experience. Stories change culture. When people connect to compelling story, they begin to change behaviors. When people act, companies and industries begin to transform.
+
+If you would like to support [The Chasing Grace Project][8], email Jennifer Cloer to learn more about how to get involved: [jennifer@wickedflicksproductions.com][10]
+
+--------------------------------------------------------------------------------
+
+via: https://opensource.com/article/18/6/being-woman-tech-10-principles-resilience
+
+作者:[Jennifer Cloer][a]
+选题:[lujun9972](https://github.com/lujun9972)
+译者:[译者ID](https://github.com/译者ID)
+校对:[校对者ID](https://github.com/校对者ID)
+
+本文由 [LCTT](https://github.com/LCTT/TranslateProject) 原创编译,[Linux中国](https://linux.cn/) 荣誉推出
+
+[a]:https://opensource.com/users/jennifer-cloer
+[1]:http://www.newsweek.com/2015/02/06/what-silicon-valley-thinks-women-302821.html%E2%80%9D
+[2]:https://opensource.com/article/17/6/male-allies-tech-industry-needs-you%E2%80%9D
+[3]:https://twitter.com/GirlsWhoCode%E2%80%9D
+[4]:http://opensource.com/tags/red-hat-summit%E2%80%9D
+[5]:https://www.ncwit.org/sites/default/files/resources/womenintech_facts_fullreport_05132016.pdf%E2%80%9D
+[6]:Dhttp://www.latimes.com/business/la-fi-women-tech-20150222-story.html%E2%80%9D
+[7]:http://www.ey.com/us/en/newsroom/news-releases/ey-news-new-research-reveals-the-differences-between-boys-and-girls-career-and-college-plans-and-an-ongoing-need-to-engage-girls-in-stem%E2%80%9D
+[8]:https://www.chasinggracefilm.com/
+[9]:https://www.facebook.com/therealTechLadies/%E2%80%9D
+[10]:mailto:jennifer@wickedflicksproductions.com
diff --git a/sources/talk/20180705 New Training Options Address Demand for Blockchain Skills.md b/sources/talk/20180705 New Training Options Address Demand for Blockchain Skills.md
deleted file mode 100644
index dedbf748d6..0000000000
--- a/sources/talk/20180705 New Training Options Address Demand for Blockchain Skills.md
+++ /dev/null
@@ -1,45 +0,0 @@
-New Training Options Address Demand for Blockchain Skills
-======
-
-
-
-Blockchain technology is transforming industries and bringing new levels of trust to contracts, payment processing, asset protection, and supply chain management. Blockchain-related jobs are the second-fastest growing in today’s labor market, [according to TechCrunch][1]. But, as in the rapidly expanding field of artificial intelligence, there is a pronounced blockchain skills gap and a need for expert training resources.
-
-### Blockchain for Business
-
-A new training option was recently announced from The Linux Foundation. Enrollment is now open for a free training course called[Blockchain: Understanding Its Uses and Implications][2], as well as a [Blockchain for Business][2] professional certificate program. Delivered through the edX training platform, the new course and program provide a way to learn about the impact of blockchain technologies and a means to demonstrate that knowledge. Certification, in particular, can make a difference for anyone looking to work in the blockchain arena.
-
-“In the span of only a year or two, blockchain has gone from something seen only as related to cryptocurrencies to a necessity for businesses across a wide variety of industries,” [said][3] Linux Foundation General Manager, Training & Certification Clyde Seepersad. “Providing a free introductory course designed not only for technical staff but business professionals will help improve understanding of this important technology, while offering a certificate program through edX will enable professionals from all over the world to clearly demonstrate their expertise.”
-
-TechCrunch [also reports][4] that venture capital is rapidly flowing toward blockchain-focused startups. And, this new program is designed for business professionals who need to understand the potential – or threat – of blockchain to their company and industry.
-
-“Professional Certificate programs on edX deliver career-relevant education in a flexible, affordable way, by focusing on the critical skills industry leaders and successful professionals are seeking today,” said Anant Agarwal, edX CEO and MIT Professor.
-
-### Hyperledger Fabric
-
-The Linux Foundation is steward to many valuable blockchain resources and includes some notable community members. In fact, a recent New York Times article — “[The People Leading the Blockchain Revolution][5]” — named Brian Behlendorf, Executive Director of The Linux Foundation’s [Hyperledger Project][6], one of the [top influential voices][7] in the blockchain world.
-
-Hyperledger offers proven paths for gaining credibility and skills in the blockchain space. For example, the project offers a free course titled Introduction to Hyperledger Fabric for Developers. Fabric has emerged as a key open source toolset in the blockchain world. Through the Hyperledger project, you can also take the B9-lab Certified Hyperledger Fabric Developer course. More information on both courses is available [here][8].
-
-“As you can imagine, someone needs to do the actual coding when companies move to experiment and replace their legacy systems with blockchain implementations,” states the Hyperledger website. “With training, you could gain serious first-mover advantage.”
-
---------------------------------------------------------------------------------
-
-via: https://www.linux.com/blog/2018/7/new-training-options-address-demand-blockchain-skills
-
-作者:[SAM DEAN][a]
-选题:[lujun9972](https://github.com/lujun9972)
-译者:[译者ID](https://github.com/译者ID)
-校对:[校对者ID](https://github.com/校对者ID)
-
-本文由 [LCTT](https://github.com/LCTT/TranslateProject) 原创编译,[Linux中国](https://linux.cn/) 荣誉推出
-
-[a]:https://www.linux.com/users/sam-dean
-[1]:https://techcrunch.com/2018/02/14/blockchain-engineers-are-in-demand/
-[2]:https://www.edx.org/course/understanding-blockchain-and-its-implications
-[3]:https://www.linuxfoundation.org/press-release/as-demand-skyrockets-for-blockchain-expertise-the-linux-foundation-and-edx-offer-new-introductory-blockchain-course-and-blockchain-for-business-professional-certificate-program/
-[4]:https://techcrunch.com/2018/05/20/with-at-least-1-3-billion-invested-globally-in-2018-vc-funding-for-blockchain-blows-past-2017-totals/
-[5]:https://www.nytimes.com/2018/06/27/business/dealbook/blockchain-stars.html
-[6]:https://www.hyperledger.org/
-[7]:https://www.linuxfoundation.org/blog/hyperledgers-brian-behlendorf-named-as-top-blockchain-influencer-by-new-york-times/
-[8]:https://www.hyperledger.org/resources/training
diff --git a/sources/talk/20180802 How blockchain will influence open source.md b/sources/talk/20180802 How blockchain will influence open source.md
deleted file mode 100644
index 707f4fe033..0000000000
--- a/sources/talk/20180802 How blockchain will influence open source.md
+++ /dev/null
@@ -1,185 +0,0 @@
-How blockchain will influence open source
-======
-
-
-
-What [Satoshi Nakamoto][1] started as Bitcoin a decade ago has found a lot of followers and turned into a movement for decentralization. For some, blockchain technology is a religion that will have the same impact on humanity as the Internet has had. For others, it is hype and technology suitable only for Ponzi schemes. While blockchain is still evolving and trying to find its place, one thing is for sure: It is a disruptive technology that will fundamentally transform certain industries. And I'm betting open source will be one of them.
-
-### The open source model
-
-Open source is a collaborative software development and distribution model that allows people with common interests to gather and produce something that no individual can create on their own. It allows the creation of value that is bigger than the sum of its parts. Open source is enabled by distributed collaboration tools (IRC, email, git, wiki, issue trackers, etc.), distributed and protected by an open source licensing model and often governed by software foundations such as the [Apache Software Foundation][2] (ASF), [Cloud Native Computing Foundation][3] (CNCF), etc.
-
-One interesting aspect of the open source model is the lack of financial incentives in its core. Some people believe open source work should remain detached from money and remain a free and voluntary activity driven only by intrinsic motivators (such as "common purpose" and "for the greater good”). Others believe open source work should be rewarded directly or indirectly through extrinsic motivators (such as financial incentive). While the idea of open source projects prospering only through voluntary contributions is romantic, in reality, the majority of open source contributions are done through paid development. Yes, we have a lot of voluntary contributions, but these are on a temporary basis from contributors who come and go, or for exceptionally popular projects while they are at their peak. Creating and sustaining open source projects that are useful for enterprises requires developing, documenting, testing, and bug-fixing for prolonged periods, even when the software is no longer shiny and exciting. It is a boring activity that is best motivated through financial incentives.
-
-### Commercial open source
-
-Software foundations such as ASF survive on donations and other income streams such as sponsorships, conference fees, etc. But those funds are primarily used to run the foundations, to provide legal protection for the projects, and to ensure there are enough servers to run builds, issue trackers, mailing lists, etc.
-
-Similarly, CNCF has member fees and other income streams, which are used to run the foundation and provide resources for the projects. These days, most software is not built on laptops; it is run and tested on hundreds of machines on the cloud, and that requires money. Creating marketing campaigns, brand designs, distributing stickers, etc. takes money, and some foundations can assist with that as well. At its core, foundations implement the right processes to interact with users, developers, and control mechanisms and ensure distribution of available financial resources to open source projects for the common good.
-
-If users of open source projects can donate money and the foundations can distribute it in a fair way, what is missing?
-
-What is missing is a direct, transparent, trusted, decentralized, automated bidirectional link for transfer of value between the open source producers and the open source consumer. Currently, the link is either unidirectional or indirect:
-
- * **Unidirectional** : A developer (think of a "developer" as any role that is involved in the production, maintenance, and distribution of software) can use their brain juice and devote time to do a contribution and share that value with all open source users. But there is no reverse link.
-
- * **Indirect** : If there is a bug that affects a specific user/company, the options are:
-
- * To have in-house developers to fix the bug and do a pull request. That is ideal, but it not always possible to hire in-house developers who are knowledgeable about hundreds of open source projects used daily.
-
- * To hire a freelancer specializing in that specific open source project and pay for the services. Ideally, the freelancer is also a committer for the open source project and can directly change the project code quickly. Otherwise, the fix might not ever make it to the project.
-
- * To approach a company providing services around the open source project. Such companies typically employ open source committers to influence and gain credibility in the community and offer products, expertise, and professional services.
-
-
-
-
-The third option has been a successful [model][4] for sustaining many open source projects. Whether they provide services (training, consulting, workshops), support, packaging, open core, or SaaS, there are companies that employ hundreds of staff members who work on open source full time. There is a long [list of companies][5] that have managed to build a successful open source business model over the years, and that list is growing steadily.
-
-The companies that back open source projects play an important role in the ecosystem: They are the catalyst between the open source projects and the users. The ones that add real value do more than just package software nicely; they can identify user needs and technology trends, and they create a full stack and even an ecosystem of open source projects to address these needs. They can take a boring project and support it for years. If there is a missing piece in the stack, they can start an open source project from scratch and build a community around it. They can acquire a closed source software company and open source the projects (here I got a little carried away, but yes, I'm talking about my employer, [Red Hat][6]).
-
-To summarize, with the commercial open source model, projects are officially or unofficially managed and controlled by a very few individuals or companies that monetize them and give back to the ecosystem by ensuring the project is successful. It is a win-win-win for open source developers, managing companies, and end users. The alternative is inactive projects and expensive closed source software.
-
-### Self-sustaining, decentralized open source
-
-For a project to become part of a reputable foundation, it must conform to certain criteria. For example, ASF and CNCF require incubation and graduation processes, respectively, where apart from all the technical and formal requirements, a project must have a healthy number of active committer and users. And that is the essence of forming a sustainable open source project. Having source code on GitHub is not the same thing as having an active open source project. The latter requires committers who write the code and users who use the code, with both groups enforcing each other continuously by exchanging value and forming an ecosystem where everybody benefits. Some project ecosystems might be tiny and short-lived, and some may consist of multiple projects and competing service providers, with very complex interactions lasting for many years. But as long as there is an exchange of value and everybody benefits from it, the project is developed, maintained, and sustained.
-
-If you look at ASF [Attic][7], you will find projects that have reached their end of life. When a project is no longer technologically fit for its purpose, it is usually its natural end. Similarly, in the ASF [Incubator][8], you will find tons of projects that never graduated but were instead retired. Typically, these projects were not able to build a large enough community because they are too specialized or there are better alternatives available.
-
-But there are also cases where projects with high potential and superior technology cannot sustain themselves because they cannot form or maintain a functioning ecosystem for the exchange of value. The open source model and the foundations do not provide a framework and mechanisms for developers to get paid for their work or for users to get their requests heard. There isn’t a common value commitment framework for either party. As a result, some projects can sustain themselves only in the context of commercial open source, where a company acts as an intermediary and value adder between developers and users. That adds another constraint and requires a service provider company to sustain some open source projects. Ideally, users should be able to express their interest in a project and developers should be able to show their commitment to the project in a transparent and measurable way, which forms a community with common interest and intent for the exchange of value.
-
-Imagine there is a model with mechanisms and tools that enable direct interaction between open source users and developers. This includes not only code contributions through pull requests, questions over the mailing lists, GitHub stars, and stickers on laptops, but also other ways that allow users to influence projects' destinies in a richer, more self-controlled and transparent manner.
-
-This model could include incentives for actions such as:
-
- * Funding open source projects directly rather than through software foundations
-
- * Influencing the direction of projects through voting (by token holders)
-
- * Feature requests driven by user needs
-
- * On-time pull request merges
-
- * Bounties for bug hunts
-
- * Better test coverage incentives
-
- * Up-to-date documentation rewards
-
- * Long-term support guarantees
-
- * Timely security fixes
-
- * Expert assistance, support, and services
-
- * Budget for evangelism and promotion of the projects
-
- * Budget for regular boring activities
-
- * Fast email and chat assistance
-
- * Full visibility of the overall project findings, etc.
-
-
-
-
-If you haven't guessed, I'm talking about using blockchain and [smart contracts][9] to allow such interactions between users and developers—smart contracts that will give power to the hand of token holders to influence projects.
-
-![blockchain_in_open_source_ecosystem.png][11]
-
-The usage of blockchain in the open source ecosystem
-
-Existing channels in the open source ecosystem provide ways for users to influence projects through financial commitments to service providers or other limited means through the foundations. But the addition of blockchain-based technology to the open source ecosystem could open new channels for interaction between users and developers. I'm not saying this will replace the commercial open source model; most companies working with open source do many things that cannot be replaced by smart contracts. But smart contracts can spark a new way of bootstrapping new open source projects, giving a second life to commodity projects that are a burden to maintain. They can motivate developers to apply boring pull requests, write documentation, get tests to pass, etc., providing a direct value exchange channel between users and open source developers. Blockchain can add new channels to help open source projects grow and become self-sustaining in the long term, even when company backing is not feasible. It can create a new complementary model for self-sustaining open source projects—a win-win.
-
-### Tokenizing open source
-
-There are already a number of initiatives aiming to tokenize open source. Some focus only on an open source model, and some are more generic but apply to open source development as well:
-
- * [Gitcoin][12] \- grow open source, one of the most promising ones in this area.
-
- * [Oscoin][13] \- cryptocurrency for open source
-
- * [Open collective][14] \- a platform for supporting open source projects.
-
- * [FundYourselfNow][15] \- Kickstarter and ICOs for projects.
-
- * [Kauri][16] \- support for open source project documentation.
-
- * [Liberapay][17] \- a recurrent donations platform.
-
- * [FundRequest][18] \- a decentralized marketplace for open source collaboration.
-
- * [CanYa][19] \- recently acquired [Bountysource][20], now the world’s largest open source P2P bounty platform.
-
- * [OpenGift][21] \- a new model for open source monetization.
-
- * [Hacken][22] \- a white hat token for hackers.
-
- * [Coinlancer][23] \- a decentralized job market.
-
- * [CodeFund][24] \- an open source ad platform.
-
- * [IssueHunt][25] \- a funding platform for open source maintainers and contributors.
-
- * [District0x 1Hive][26] \- a crowdfunding and curation platform.
-
- * [District0x Fixit][27] \- github bug bounties.
-
-
-
-
-This list is varied and growing rapidly. Some of these projects will disappear, others will pivot, but a few will emerge as the [SourceForge][28], the ASF, the GitHub of the future. That doesn't necessarily mean they'll replace these platforms, but they'll complement them with token models and create a richer open source ecosystem. Every project can pick its distribution model (license), governing model (foundation), and incentive model (token). In all cases, this will pump fresh blood to the open source world.
-
-### The future is open and decentralized
-
- * Software is eating the world.
-
- * Every company is a software company.
-
- * Open source is where innovation happens.
-
-
-
-
-Given that, it is clear that open source is too big to fail and too important to be controlled by a few or left to its own destiny. Open source is a shared-resource system that has value to all, and more importantly, it must be managed as such. It is only a matter of time until every company on earth will want to have a stake and a say in the open source world. Unfortunately, we don't have the tools and the habits to do it yet. Such tools would allow anybody to show their appreciation or ignorance of software projects. It would create a direct and faster feedback loop between producers and consumers, between developers and users. It will foster innovation—innovation driven by user needs and expressed through token metrics.
-
---------------------------------------------------------------------------------
-
-via: https://opensource.com/article/18/8/open-source-tokenomics
-
-作者:[Bilgin lbryam][a]
-选题:[lujun9972](https://github.com/lujun9972)
-译者:[译者ID](https://github.com/译者ID)
-校对:[校对者ID](https://github.com/校对者ID)
-
-本文由 [LCTT](https://github.com/LCTT/TranslateProject) 原创编译,[Linux中国](https://linux.cn/) 荣誉推出
-
-[a]:https://opensource.com/users/bibryam
-[1]:https://en.wikipedia.org/wiki/Satoshi_Nakamoto
-[2]:https://www.apache.org/
-[3]:https://www.cncf.io/
-[4]:https://medium.com/open-consensus/3-oss-business-model-progressions-dafd5837f2d
-[5]:https://docs.google.com/spreadsheets/d/17nKMpi_Dh5slCqzLSFBoWMxNvWiwt2R-t4e_l7LPLhU/edit#gid=0
-[6]:http://jobs.redhat.com/
-[7]:https://attic.apache.org/
-[8]:http://incubator.apache.org/
-[9]:https://en.wikipedia.org/wiki/Smart_contract
-[10]:/file/404421
-[11]:https://opensource.com/sites/default/files/uploads/blockchain_in_open_source_ecosystem.png (blockchain_in_open_source_ecosystem.png)
-[12]:https://gitcoin.co/
-[13]:http://oscoin.io/
-[14]:https://opencollective.com/opensource
-[15]:https://www.fundyourselfnow.com/page/about
-[16]:https://kauri.io/
-[17]:https://liberapay.com/
-[18]:https://fundrequest.io/
-[19]:https://canya.io/
-[20]:https://www.bountysource.com/
-[21]:https://opengift.io/pub/
-[22]:https://hacken.io/
-[23]:https://www.coinlancer.com/home
-[24]:https://codefund.io/
-[25]:https://issuehunt.io/
-[26]:https://blog.district0x.io/district-proposal-spotlight-1hive-283957f57967
-[27]:https://github.com/district0x/district-proposals/issues/177
-[28]:https://sourceforge.net/
diff --git a/sources/talk/20180816 Debian Turns 25- Here are Some Interesting Facts About Debian Linux.md b/sources/talk/20180816 Debian Turns 25- Here are Some Interesting Facts About Debian Linux.md
deleted file mode 100644
index c90262dfee..0000000000
--- a/sources/talk/20180816 Debian Turns 25- Here are Some Interesting Facts About Debian Linux.md
+++ /dev/null
@@ -1,116 +0,0 @@
-Debian Turns 25! Here are Some Interesting Facts About Debian Linux
-======
-One of the oldest Linux distribution still in development, Debian has just turned 25. Let’s have a look at some interesting facts about this awesome FOSS project.
-
-### 10 Interesting facts about Debian Linux
-
-![Interesting facts about Debian Linux][1]
-
-The facts presented here have been collected from various sources available from the internet. They are true to my knowledge, but in case of any error, please remind me to update the article.
-
-#### 1\. One of the oldest Linux distributions still under active development
-
-[Debian project][2] was announced on 16th August 1993 by Ian Murdock, Debian Founder. Like Linux creator [Linus Torvalds][3], Ian was a college student when he announced Debian project.
-
-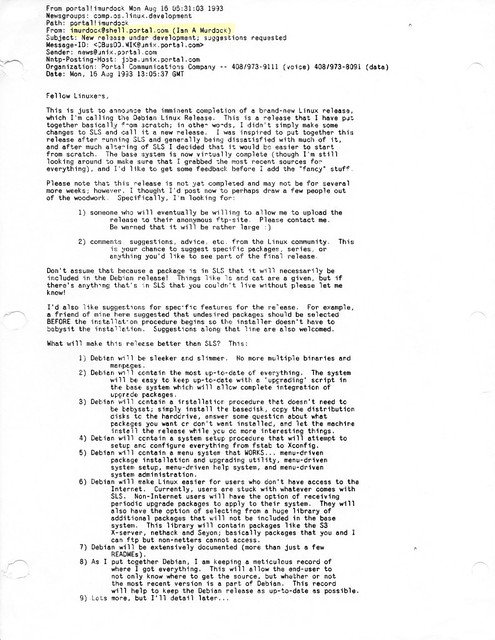
-
-#### 2\. Some people get tattoo while some name their project after their girlfriend’s name
-
-The project was named by combining the name of Ian and his then-girlfriend Debra Lynn. Ian and Debra got married and had three children. Debra and Ian got divorced in 2008.
-
-#### 3\. Ian Murdock: The Maverick behind the creation of Debian project
-
-![Debian Founder Ian Murdock][4]
-Ian Murdock
-
-[Ian Murdock][5] led the Debian project from August 1993 until March 1996. He shaped Debian into a community project based on the principals of Free Software. The [Debian Manifesto][6] and the [Debian Social Contract][7] are still governing the project.
-
-He founded a commercial Linux company called [Progeny Linux Systems][8] and worked for a number of Linux related companies such as Sun Microsystems, Linux Foundation and Docker.
-
-Sadly, [Ian committed suicide in December 2015][9]. His contribution to Debian is certainly invaluable.
-
-#### 4\. Debian is a community project in the true sense
-
-Debian is a community based project in true sense. No one ‘owns’ Debian. Debian is being developed by volunteers from all over the world. It is not a commercial project, backed by corporates like many other Linux distributions.
-
-Debian Linux distribution is composed of Free Software only. It’s one of the few Linux distributions that is true to the spirit of [Free Software][10] and takes proud in being called a GNU/Linux distribution.
-
-Debian has its non-profit organization called [Software in Public Interest][11] (SPI). Along with Debian, SPI supports many other open source projects financially.
-
-#### 5\. Debian and its 3 branches
-
-Debian has three branches or versions: Debian Stable, Debian Unstable (Sid) and Debian Testing.
-
-Debian Stable, as the name suggests, is the stable branch that has all the software and packages well tested to give you a rock solid stable system. Since it takes time before a well-tested software lands in the stable branch, Debian Stable often contains older versions of programs and hence people joke that Debian Stable means stale.
-
-[Debian Unstable][12] codenamed Sid is the version where all the development of Debian takes place. This is where the new packages first land or developed. After that, these changes are propagated to the testing version.
-
-[Debian Testing][13] is the next release after the current stable release. If the current stable release is N, Debian testing would be the N+1 release. The packages from Debian Unstable are tested in this version. After all the new changes are well tested, Debian Testing is then ‘promoted’ as the new Stable version.
-
-There is no strict release schedule for Debian.
-
-#### 7\. There was no Debian 1.0 release
-
-Debian 1.0 was never released. The CD vendor, InfoMagic, accidentally shipped a development release of Debian and entitled it 1.0 in 1996. To prevent confusion between the CD version and the actual Debian release, the Debian Project renamed its next release to “Debian 1.1”.
-
-#### 8\. Debian releases are codenamed after Toy Story characters
-
-![Toy Story Characters][14]
-
-Debian releases are codenamed after the characters from Pixar’s hit animation movie series [Toy Story][15].
-
-Debian 1.1 was the first release with a codename. It was named Buzz after the Toy Story character Buzz Lightyear.
-
-It was in 1996 and [Bruce Perens][16] had taken over leadership of the Project from Ian Murdock. Bruce was working at Pixar at the time.
-
-This trend continued and all the subsequent releases had codenamed after Toy Story characters. For example, the current stable release is Stretch while the upcoming release has been codenamed Buster.
-
-The unstable Debian version is codenamed Sid. This character in Toy Story is a kid with emotional problems and he enjoys breaking toys. This is symbolic in the sense that Debian Unstable might break your system with untested packages.
-
-#### 9\. Debian also has a BSD ditribution
-
-Debian is not limited to Linux. Debian also has a distribution based on FreeBSD kernel. It is called [Debian GNU/kFreeBSD][17].
-
-#### 10\. Google uses Debian
-
-[Google uses Debian][18] as its in-house development platform. Earlier, Google used a customized version of Ubuntu as its development platform. Recently they opted for Debian based gLinux.
-
-#### Happy 25th birthday Debian
-
-![Happy 25th birthday Debian][19]
-
-I hope you liked these little facts about Debian. Stuff like these are reasons why people love Debian.
-
-I wish a very happy 25th birthday to Debian. Please continue to be awesome. Cheers :)
-
---------------------------------------------------------------------------------
-
-via: https://itsfoss.com/debian-facts/
-
-作者:[Abhishek Prakash][a]
-选题:[lujun9972](https://github.com/lujun9972)
-译者:[译者ID](https://github.com/译者ID)
-校对:[校对者ID](https://github.com/校对者ID)
-
-本文由 [LCTT](https://github.com/LCTT/TranslateProject) 原创编译,[Linux中国](https://linux.cn/) 荣誉推出
-
-[a]: https://itsfoss.com/author/abhishek/
-[1]:https://4bds6hergc-flywheel.netdna-ssl.com/wp-content/uploads/2018/08/Interesting-facts-about-debian.jpeg
-[2]:https://www.debian.org
-[3]:https://itsfoss.com/linus-torvalds-facts/
-[4]:https://4bds6hergc-flywheel.netdna-ssl.com/wp-content/uploads/2018/08/ian-murdock.jpg
-[5]:https://en.wikipedia.org/wiki/Ian_Murdock
-[6]:https://www.debian.org/doc/manuals/project-history/ap-manifesto.en.html
-[7]:https://www.debian.org/social_contract
-[8]:https://en.wikipedia.org/wiki/Progeny_Linux_Systems
-[9]:https://itsfoss.com/ian-murdock-dies-mysteriously/
-[10]:https://www.fsf.org/
-[11]:https://www.spi-inc.org/
-[12]:https://www.debian.org/releases/sid/
-[13]:https://www.debian.org/releases/testing/
-[14]:https://4bds6hergc-flywheel.netdna-ssl.com/wp-content/uploads/2018/08/toy-story-characters.jpeg
-[15]:https://en.wikipedia.org/wiki/Toy_Story_(franchise)
-[16]:https://perens.com/about-bruce-perens/
-[17]:https://wiki.debian.org/Debian_GNU/kFreeBSD
-[18]:https://itsfoss.com/goobuntu-glinux-google/
-[19]:https://4bds6hergc-flywheel.netdna-ssl.com/wp-content/uploads/2018/08/happy-25th-birthday-Debian.jpeg
diff --git a/sources/talk/20180818 What Did Ada Lovelace-s Program Actually Do.md b/sources/talk/20180818 What Did Ada Lovelace-s Program Actually Do.md
index 8bbb651cfd..fc669a1a3c 100644
--- a/sources/talk/20180818 What Did Ada Lovelace-s Program Actually Do.md
+++ b/sources/talk/20180818 What Did Ada Lovelace-s Program Actually Do.md
@@ -1,3 +1,5 @@
+Northurland Translating
+
What Did Ada Lovelace's Program Actually Do?
======
The story of Microsoft’s founding is one of the most famous episodes in computing history. In 1975, Paul Allen flew out to Albuquerque to demonstrate the BASIC interpreter that he and Bill Gates had written for the Altair microcomputer. Because neither of them had a working Altair, Allen and Gates tested their interpreter using an emulator that they wrote and ran on Harvard’s computer system. The emulator was based on nothing more than the published specifications for the Intel 8080 processor. When Allen finally ran their interpreter on a real Altair—in front of the person he and Gates hoped would buy their software—he had no idea if it would work. But it did. The next month, Allen and Gates officially founded their new company.
diff --git a/sources/talk/20181004 Interview With Peter Ganten, CEO of Univention GmbH.md b/sources/talk/20181004 Interview With Peter Ganten, CEO of Univention GmbH.md
deleted file mode 100644
index 5a0c1aabdd..0000000000
--- a/sources/talk/20181004 Interview With Peter Ganten, CEO of Univention GmbH.md
+++ /dev/null
@@ -1,97 +0,0 @@
-Interview With Peter Ganten, CEO of Univention GmbH
-======
-I have been asking the Univention team to share the behind-the-scenes story of [**Univention**][1] for a couple of months. Finally, today we got the interview of **Mr. Peter H. Ganten** , CEO of Univention GmbH. Despite his busy schedule, in this interview, he shares what he thinks of the Univention project and its impact on open source ecosystem, what open source developers and companies will need to do to keep thriving and what are the biggest challenges for open source projects.
-
-**OSTechNix: What’s your background and why have you founded Univention?**
-
-**Peter Ganten:** I studied physics and psychology. In psychology I was a research assistant and coded evaluation software. I realized how important it is that results have to be disclosed in order to verify or falsify them. The same goes for the code that leads to the results. This brought me into contact with Open Source Software (OSS) and Linux.
-
-
-
-I was a kind of technical lab manager and I had the opportunity to try out a lot, which led to my book about Debian. That was still in the New Economy era where the first business models emerged on how to make money with Open Source. When the bubble burst, I had the plan to make OSS a solid business model without venture capital but with Hanseatic business style – seriously, steadily, no bling bling.
-
-**What were the biggest challenges at the beginning?**
-
-When I came from the university, the biggest challenge clearly was to gain entrepreneurial and business management knowledge. I quickly learned that it’s not about Open Source software as an end to itself but always about customer value, and the benefits OSS offers its customers. We all had to learn a lot.
-
-In the beginning, we expected that Linux on the desktop would become established in a similar way as Linux on the server. However, this has not yet been proven true. The replacement has happened with Android and the iPhone. Our conclusion then was to change our offerings towards ID management and enterprise servers.
-
-**Why does UCS matter? And for whom makes it sense to use it?**
-
-There is cool OSS in all areas, but many organizations are not capable to combine it all together and make it manageable. For the basic infrastructure (Windows desktops, users, user rights, roles, ID management, apps) we need a central instance to which groupware, CRM etc. is connected. Without Univention this would have to be laboriously assembled and maintained manually. This is possible for very large companies, but far too complex for many other organizations.
-
-[**UCS**][2] can be used out of the box and is scalable. That’s why it’s becoming more and more popular – more than 10,000 organizations are using UCS already today.
-
-**Who are your users and most important clients? What do they love most about UCS?**
-
-The Core Edition is free of charge and used by organizations from all sectors and industries such as associations, micro-enterprises, universities or large organizations with thousands of users. In the enterprise environment, where Long Term Servicing (LTS) and professional support are particularly important, we have organizations ranging in size from 30-50 users to several thousand users. One of the target groups is the education system in Germany. In many large cities and within their school administrations UCS is used, for example, in Cologne, Hannover, Bremen, Kassel and in several federal states. They are looking for manageable IT and apps for schools. That’s what we offer, because we can guarantee these authorities full control over their users’ identities.
-
-Also, more and more cloud service providers and MSPs want to take UCS to deliver a selection of cloud-based app solutions.
-
-**Is UCS 100% Open Source? If so, how can you run a profitable business selling it?**
-
-Yes, UCS is 100% Open Source, every line, the whole code is OSS. You can download and use UCS Core Edition for **FREE!**
-
-We know that in large, complex organizations, vendor support and liability is needed for LTS, SLAs, and we offer that with our Enterprise subscriptions and consulting services. We don’t offer these in the Core Edition.
-
-**And what are you giving back to the OS community?**
-
-A lot. We are involved in the Debian team and co-finance the LTS maintenance for Debian. For important OS components in UCS like [**OpenLDAP**][3], Samba or KVM we co-finance the development or have co-developed them ourselves. We make it all freely available.
-
-We are also involved on the political level in ensuring that OSS is used. We are engaged, for example, in the [**Free Software Foundation Europe (FSFE)**][4] and the [**German Open Source Business Alliance**][5], of which I am the chairman. We are working hard to make OSS more successful.
-
-**How can I get started with UCS?**
-
-It’s easy to get started with the Core Edition, which, like the Enterprise Edition, has an App Center and can be easily installed on your own hardware or as an appliance in a virtual machine. Just [**download Univention ISO**][6] and install it as described in the below link.
-
-Alternatively, you can try the [**UCS Online Demo**][7] to get a first impression of Univention Corporate Server without actually installing it on your system.
-
-**What do you think are the biggest challenges for Open Source?**
-
-There is a certain attitude you can see over and over again even in bigger projects: OSS alone is viewed as an almost mandatory prerequisite for a good, sustainable, secure and trustworthy IT solution – but just having decided to use OSS is no guarantee for success. You have to carry out projects professionally and cooperate with the manufacturers. A danger is that in complex projects people think: “Oh, OSS is free, I just put it all together by myself”. But normally you do not have the know-how to successfully implement complex software solutions. You would never proceed like this with Closed Source. There people think: “Oh, the software costs 3 $ millions, so it’s okay if I have to spend another 300,000 Dollars on consultants.”
-
-At OSS this is different. If such projects fail and leave burnt ground behind, we have to explain again and again that the failure of such projects is not due to the nature of OSS but to its poor implementation and organization in a specific project: You have to conclude reasonable contracts and involve partners as in the proprietary world, but you’ll gain a better solution.
-
-Another challenge: We must stay innovative, move forward, attract new people who are enthusiastic about working on projects. That’s sometimes a challenge. For example, there are a number of proprietary cloud services that are good but lead to extremely high dependency. There are approaches to alternatives in OSS, but no suitable business models yet. So it’s hard to find and fund developers. For example, I can think of Evernote and OneNote for which there is no reasonable OSS alternative.
-
-**And what will the future bring for Univention?**
-
-I don’t have a crystal ball, but we are extremely optimistic. We see a very high growth potential in the education market. More OSS is being made in the public sector, because we have repeatedly experienced the dead ends that can be reached if we solely rely on Closed Source.
-
-Overall, we will continue our organic growth at double-digit rates year after year.
-
-UCS and its core functionalities of identity management, infrastructure management and app center will increasingly be offered and used from the cloud as a managed service. We will support our technology in this direction, e.g., through containers, so that a hypervisor or bare metal is not always necessary for operation.
-
-**You have been the CEO of Univention for a long time. What keeps you motivated?**
-
-I have been the CEO of Univention for more than 16 years now. My biggest motivation is to realize that something is moving. That we offer the better way for IT. That the people who go this way with us are excited to work with us. I go home satisfied in the evening (of course not every evening). It’s totally cool to work with the team I have. It motivates and pushes you every time I need it myself.
-
-I’m a techie and nerd at heart, I enjoy dealing with technology. So I’m totally happy at this place and I’m grateful to the world that I can do whatever I want every day. Not everyone can say that.
-
-**Who gives you inspiration?**
-
-My employees, the customers and the Open Source projects. The exchange with other people.
-
-The motivation behind everything is that we want to make sure that mankind will be able to influence and change the IT that surrounds us today and in the future just the way we want it and we thinks it’s good. We want to make a contribution to this. That is why Univention is there. That is important to us every day.
-
-
-
---------------------------------------------------------------------------------
-
-via: https://www.ostechnix.com/interview-with-peter-ganten-ceo-of-univention-gmbh/
-
-作者:[SK][a]
-选题:[lujun9972](https://github.com/lujun9972)
-译者:[译者ID](https://github.com/译者ID)
-校对:[校对者ID](https://github.com/校对者ID)
-
-本文由 [LCTT](https://github.com/LCTT/TranslateProject) 原创编译,[Linux中国](https://linux.cn/) 荣誉推出
-
-[a]: https://www.ostechnix.com/author/sk/
-[1]: https://www.ostechnix.com/introduction-univention-corporate-server/
-[2]: https://www.univention.com/products/ucs/
-[3]: https://www.ostechnix.com/redhat-and-suse-announced-to-withdraw-support-for-openldap/
-[4]: https://fsfe.org/
-[5]: https://osb-alliance.de/
-[6]: https://www.univention.com/downloads/download-ucs/
-[7]: https://www.univention.com/downloads/ucs-online-demo/
diff --git a/sources/talk/20190131 OOP Before OOP with Simula.md b/sources/talk/20190131 OOP Before OOP with Simula.md
index cae9d9bd3a..aca160ad2d 100644
--- a/sources/talk/20190131 OOP Before OOP with Simula.md
+++ b/sources/talk/20190131 OOP Before OOP with Simula.md
@@ -1,5 +1,5 @@
[#]: collector: (lujun9972)
-[#]: translator: ( )
+[#]: translator: (warmfrog)
[#]: reviewer: ( )
[#]: publisher: ( )
[#]: url: ( )
diff --git a/sources/talk/20190228 Why CLAs aren-t good for open source.md b/sources/talk/20190228 Why CLAs aren-t good for open source.md
deleted file mode 100644
index ca39619762..0000000000
--- a/sources/talk/20190228 Why CLAs aren-t good for open source.md
+++ /dev/null
@@ -1,76 +0,0 @@
-[#]: collector: (lujun9972)
-[#]: translator: ( )
-[#]: reviewer: ( )
-[#]: publisher: ( )
-[#]: url: ( )
-[#]: subject: (Why CLAs aren't good for open source)
-[#]: via: (https://opensource.com/article/19/2/cla-problems)
-[#]: author: (Richard Fontana https://opensource.com/users/fontana)
-
-Why CLAs aren't good for open source
-======
-Few legal topics in open source are as controversial as contributor license agreements.
-
-
-Few legal topics in open source are as controversial as [contributor license agreements][1] (CLAs). Unless you count the special historical case of the [Fedora Project Contributor Agreement][2] (which I've always seen as an un-CLA), or, like [Karl Fogel][3], you classify the [DCO][4] as a [type of CLA][5], today Red Hat makes no use of CLAs for the projects it maintains.
-
-It wasn't always so. Red Hat's earliest projects followed the traditional practice I've called "inbound=outbound," in which contributions to a project are simply provided under the project's open source license with no execution of an external, non-FOSS contract required. But in the early 2000s, Red Hat began experimenting with the use of contributor agreements. Fedora started requiring contributors to sign a CLA based on the widely adapted [Apache ICLA][6], while a Free Software Foundation-derived copyright assignment agreement and a pair of bespoke CLAs were inherited from the Cygnus and JBoss acquisitions, respectively. We even took [a few steps][7] towards adopting an Apache-style CLA across the rapidly growing set of Red Hat-led projects.
-
-This came to an end, in large part because those of us on the Red Hat legal team heard and understood the concerns and objections raised by Red Hat engineers and the wider technical community. We went on to become de facto leaders of what some have called the anti-CLA movement, marked notably by our [opposition to Project Harmony][8] and our [efforts][9] to get OpenStack to replace its CLA with the DCO. (We [reluctantly][10] sign tolerable upstream project CLAs out of practical necessity.)
-
-### Why CLAs are problematic
-
-Our choice not to use CLAs is a reflection of our values as an authentic open source company with deep roots in the free software movement. Over the years, many in the open source community have explained why CLAs, and the very similar mechanism of copyright assignment, are a bad policy for open source.
-
-One reason is the red tape problem. Normally, open source development is characterized by frictionless contribution, which is enabled by inbound=outbound without imposition of further legal ceremony or process. This makes it relatively easy for new contributors to get involved in a project, allowing more effective growth of contributor communities and driving technical innovation upstream. Frictionless contribution is a key part of the advantage open source development holds over proprietary alternatives. But frictionless contribution is negated by CLAs. Having to sign an unusual legal agreement before a contribution can be accepted creates a bureaucratic hurdle that slows down development and discourages participation. This cost persists despite the growing use of automation by CLA-using projects.
-
-CLAs also give rise to an asymmetry of legal power among a project's participants, which also discourages the growth of strong contributor and user communities around a project. With Apache-style CLAs, the company or organization leading the project gets special rights that other contributors do not receive, while those other contributors must shoulder certain legal obligations (in addition to the red tape burden) from which the project leader is exempt. The problem of asymmetry is most severe in copyleft projects, but it is present even when the outbound license is permissive.
-
-When assessing the arguments for and against CLAs, bear in mind that today, as in the past, the vast majority of the open source code in any product originates in projects that follow the inbound=outbound practice. The use of CLAs by a relatively small number of projects causes collateral harm to all the others by signaling that, for some reason, open source licensing is insufficient to handle contributions flowing into a project.
-
-### The case for CLAs
-
-Since CLAs continue to be a minority practice and originate from outside open source community culture, I believe that CLA proponents should bear the burden of explaining why they are necessary or beneficial relative to their costs. I suspect that most companies using CLAs are merely emulating peer company behavior without critical examination. CLAs have an understandable, if superficial, appeal to risk-averse lawyers who are predisposed to favor greater formality, paper, and process regardless of the business costs. Still, some arguments in favor of CLAs are often advanced and deserve consideration.
-
-**Easy relicensing:** If administered appropriately, Apache-style CLAs give the project steward effectively unlimited power to sublicense contributions under terms of the steward's choice. This is sometimes seen as desirable because of the potential need to relicense a project under some other open source license. But the value of easy relicensing has been greatly exaggerated by pointing to a few historical cases involving major relicensing campaigns undertaken by projects with an unusually large number of past contributors (all of which were successful without the use of a CLA). There are benefits in relicensing being hard because it results in stable legal expectations around a project and encourages projects to consult their contributor communities before undertaking significant legal policy changes. In any case, most inbound=outbound open source projects never attempt to relicense during their lifetime, and for the small number that do, relicensing will be relatively painless because typically the number of past contributors to contact will not be large.
-
-**Provenance tracking:** It is sometimes claimed that CLAs enable a project to rigorously track the provenance of contributions, which purportedly has some legal benefit. It is unclear what is achieved by the use of CLAs in this regard that is not better handled through such non-CLA means as preserving Git commit history. And the DCO would seem to be much better suited to tracking contributions, given that it is normally used on a per-commit basis, while CLAs are signed once per contributor and are administratively separate from code contributions. Moreover, provenance tracking is often described as though it were a benefit for the public, yet I know of no case where a project provides transparent, ready public access to CLA acceptance records.
-
-**License revocation:** Some CLA advocates warn of the prospect that a contributor may someday attempt to revoke a past license grant. To the extent that the concern is about largely judgment-proof individual contributors with no corporate affiliation, it is not clear why an Apache-style CLA provides more meaningful protection against this outcome compared to the use of an open source license. And, as with so many of the legal risks raised in discussions of open source legal policy, this appears to be a phantom risk. I have heard of only a few purported attempts at license revocation over the years, all of which were resolved quickly when the contributor backed down in the face of community pressure.
-
-**Unauthorized employee contribution:** This is a special case of the license revocation issue and has recently become a point commonly raised by CLA advocates. When an employee contributes to an upstream project, normally the employer owns the copyrights and patents for which the project needs licenses, and only certain executives are authorized to grant such licenses. Suppose an employee contributed proprietary code to a project without approval from the employer, and the employer later discovers this and demands removal of the contribution or sues the project's users. This risk of unauthorized contributions is thought to be minimized by use of something like the [Apache CCLA][11] with its representations and signature requirement, coupled with some adequate review process to ascertain that the CCLA signer likely was authorized to sign (a step which I suspect is not meaningfully undertaken by most CLA-using companies).
-
-Based on common sense and common experience, I contend that in nearly all cases today, employee contributions are done with the actual or constructive knowledge and consent of the employer. If there were an atmosphere of high litigation risk surrounding open source software, perhaps this risk should be taken more seriously, but litigation arising out of open source projects remains remarkably uncommon.
-
-More to the point, I know of no case where an allegation of copyright or patent infringement against an inbound=outbound project, not stemming from an alleged open source license violation, would have been prevented by use of a CLA. Patent risk, in particular, is often cited by CLA proponents when pointing to the risk of unauthorized contributions, but the patent license grants in Apache-style CLAs are, by design, quite narrow in scope. Moreover, corporate contributions to an open source project will typically be few in number, small in size (and thus easily replaceable), and likely to be discarded as time goes on.
-
-### Alternatives
-
-If your company does not buy into the anti-CLA case and cannot get comfortable with the simple use of inbound=outbound, there are alternatives to resorting to an asymmetric and administratively burdensome Apache-style CLA requirement. The use of the DCO as a complement to inbound=outbound addresses at least some of the concerns of risk-averse CLA advocates. If you must use a true CLA, there is no need to use the Apache model (let alone a [monstrous derivative][10] of it). Consider the non-specification core of the [Eclipse Contributor Agreement][12]—essentially the DCO wrapped inside a CLA—or the Software Freedom Conservancy's [Selenium CLA][13], which merely ceremonializes an inbound=outbound contribution policy.
-
---------------------------------------------------------------------------------
-
-via: https://opensource.com/article/19/2/cla-problems
-
-作者:[Richard Fontana][a]
-选题:[lujun9972][b]
-译者:[译者ID](https://github.com/译者ID)
-校对:[校对者ID](https://github.com/校对者ID)
-
-本文由 [LCTT](https://github.com/LCTT/TranslateProject) 原创编译,[Linux中国](https://linux.cn/) 荣誉推出
-
-[a]: https://opensource.com/users/fontana
-[b]: https://github.com/lujun9972
-[1]: https://opensource.com/article/18/3/cla-vs-dco-whats-difference
-[2]: https://opensource.com/law/10/6/new-contributor-agreement-fedora
-[3]: https://www.red-bean.com/kfogel/
-[4]: https://developercertificate.org
-[5]: https://producingoss.com/en/contributor-agreements.html#developer-certificate-of-origin
-[6]: https://www.apache.org/licenses/icla.pdf
-[7]: https://www.freeipa.org/page/Why_CLA%3F
-[8]: https://opensource.com/law/11/7/trouble-harmony-part-1
-[9]: https://wiki.openstack.org/wiki/OpenStackAndItsCLA
-[10]: https://opensource.com/article/19/1/cla-proliferation
-[11]: https://www.apache.org/licenses/cla-corporate.txt
-[12]: https://www.eclipse.org/legal/ECA.php
-[13]: https://docs.google.com/forms/d/e/1FAIpQLSd2FsN12NzjCs450ZmJzkJNulmRC8r8l8NYwVW5KWNX7XDiUw/viewform?hl=en_US&formkey=dFFjXzBzM1VwekFlOWFWMjFFRjJMRFE6MQ#gid=0
diff --git a/sources/talk/20190311 Discuss everything Fedora.md b/sources/talk/20190311 Discuss everything Fedora.md
deleted file mode 100644
index 5795fbf3f7..0000000000
--- a/sources/talk/20190311 Discuss everything Fedora.md
+++ /dev/null
@@ -1,45 +0,0 @@
-[#]: collector: (lujun9972)
-[#]: translator: ( )
-[#]: reviewer: ( )
-[#]: publisher: ( )
-[#]: url: ( )
-[#]: subject: (Discuss everything Fedora)
-[#]: via: (https://fedoramagazine.org/discuss-everything-fedora/)
-[#]: author: (Ryan Lerch https://fedoramagazine.org/introducing-flatpak/)
-
-Discuss everything Fedora
-======
-
-
-Are you interested in how Fedora is being developed? Do you want to get involved, or see what goes into making a release? You want to check out [Fedora Discussion][1]. It is a relatively new place where members of the Fedora Community meet to discuss, ask questions, and interact. Keep reading for more information.
-
-Note that the Fedora Discussion system is mainly aimed at contributors. If you have questions on using Fedora, check out [Ask Fedora][2] (which is being migrated in the future).
-
-![][3]
-
-Fedora Discussion is a forum and discussion site that uses the [Discourse open source discussion platform][4].
-
-There are already several categories useful for Fedora users, including [Desktop][5] (covering Fedora Workstation, Fedora Silverblue, KDE, XFCE, and more) and the [Server, Cloud, and IoT][6] category . Additionally, some of the [Fedora Special Interest Groups (SIGs) have discussions as well][7]. Finally, the [Fedora Friends][8] category helps you connect with other Fedora users and Community members by providing discussions about upcoming meetups and hackfests.
-
-
---------------------------------------------------------------------------------
-
-via: https://fedoramagazine.org/discuss-everything-fedora/
-
-作者:[Ryan Lerch][a]
-选题:[lujun9972][b]
-译者:[译者ID](https://github.com/译者ID)
-校对:[校对者ID](https://github.com/校对者ID)
-
-本文由 [LCTT](https://github.com/LCTT/TranslateProject) 原创编译,[Linux中国](https://linux.cn/) 荣誉推出
-
-[a]: https://fedoramagazine.org/introducing-flatpak/
-[b]: https://github.com/lujun9972
-[1]: https://discussion.fedoraproject.org/
-[2]: https://ask.fedoraproject.org
-[3]: https://fedoramagazine.org/wp-content/uploads/2019/03/discussion-screenshot-1024x663.png
-[4]: https://www.discourse.org/about
-[5]: https://discussion.fedoraproject.org/c/desktop
-[6]: https://discussion.fedoraproject.org/c/server
-[7]: https://discussion.fedoraproject.org/c/sigs
-[8]: https://discussion.fedoraproject.org/c/friends
diff --git a/sources/talk/20190322 How to save time with TiDB.md b/sources/talk/20190322 How to save time with TiDB.md
deleted file mode 100644
index 534c04de1f..0000000000
--- a/sources/talk/20190322 How to save time with TiDB.md
+++ /dev/null
@@ -1,143 +0,0 @@
-[#]: collector: (lujun9972)
-[#]: translator: ( )
-[#]: reviewer: ( )
-[#]: publisher: ( )
-[#]: url: ( )
-[#]: subject: (How to save time with TiDB)
-[#]: via: (https://opensource.com/article/19/3/how-save-time-tidb)
-[#]: author: (Morgan Tocker https://opensource.com/users/morgo)
-
-How to save time with TiDB
-======
-
-TiDB, an open source-compatible, cloud-based database engine, simplifies many of MySQL database administrators' common tasks.
-
-![Team checklist][1]
-
-Last November, I wrote about key [differences between MySQL and TiDB][2], an open source-compatible, cloud-based database engine, from the perspective of scaling both solutions in the cloud. In this follow-up article, I'll dive deeper into the ways [TiDB][3] streamlines and simplifies administration.
-
-If you come from a MySQL background, you may be used to doing a lot of manual tasks that are either not required or much simpler with TiDB.
-
-The inspiration for TiDB came from the founders managing sharded MySQL at scale at some of China's largest internet companies. Since requirements for operating a large system at scale are a key concern, I'll look at some typical MySQL database administrator (DBA) tasks and how they translate to TiDB.
-
-[![TiDB architecture][4]][5]
-
-In [TiDB's architecture][5]:
-
- * SQL processing is separated from data storage. The SQL processing (TiDB) and storage (TiKV) components independently scale horizontally.
- * PD (Placement Driver) acts as the cluster manager and stores metadata.
- * All components natively provide high availability, with PD and TiKV using the [Raft consensus algorithm][6].
- * You can access your data via either MySQL (TiDB) or Spark (TiSpark) protocols.
-
-
-
-### Adding/fixing replication slaves
-
-**tl;dr:** It doesn't happen in the same way as in MySQL.
-
-Replication and redundancy of data are automatically managed by TiKV. You also don't need to worry about creating initial backups to seed replicas, as _both_ the provisioning and replication are handled for you.
-
-Replication is also quorum-based using the Raft consensus algorithm, so you don't have to worry about the inconsistency problems surrounding failures that you do with asynchronous replication (the default in MySQL and what many users are using).
-
-TiDB does support its own binary log, so it can be used for asynchronous replication between clusters.
-
-### Optimizing slow queries
-
-**tl;dr:** Still happens in TiDB
-
-There is no real way out of optimizing slow queries that have been introduced by development teams.
-
-As a mitigating factor though, if you need to add breathing room to your database's capacity while you work on optimization, the TiDB's architecture allows you to horizontally scale.
-
-### Upgrades and maintenance
-
-**tl;dr:** Still required, but generally easier
-
-Because the TiDB server is stateless, you can roll through an upgrade and deploy new TiDB servers. Then you can remove the older TiDB servers from the load balancer pool, shutting down them once connections have drained.
-
-Upgrading PD is also quite straightforward since only the PD leader actively answers requests at a time. You can perform a rolling upgrade and upgrade PD's non-leader peers one at a time, and then change the leader before upgrading the final PD server.
-
-For TiKV, the upgrade is marginally more complex. If you want to remove a node, I recommend first setting it to be a follower on each of the regions where it is currently a leader. After that, you can bring down the node without impacting your application. If the downtime is brief, TiKV will recover with its regional peers from the Raft log. In a longer downtime, it will need to re-copy data. This can all be managed for you, though, if you choose to deploy using Ansible or Kubernetes.
-
-### Manual sharding
-
-**tl;dr:** Not required
-
-Manual sharding is mainly a pain on the part of the application developers, but as a DBA, you might have to get involved if the sharding is naive or has problems such as hotspots (many workloads do) that require re-balancing.
-
-In TiDB, re-sharding or re-balancing happens automatically in the background. The PD server observes when data regions (TiKV's term for chunks of data in key-value form) get too small, too big, or too frequently accessed.
-
-You can also explicitly configure PD to store regions on certain TiKV servers. This works really well when combined with MySQL partitioning.
-
-### Capacity planning
-
-**tl;dr:** Much easier
-
-Capacity planning on a MySQL database can be a little bit hard because you need to plan your physical infrastructure requirements two to three years from now. As data grows (and the working set changes), this can be a difficult task. I wouldn't say it completely goes away in the cloud either, since changing a master server's hardware is always hard.
-
-TiDB splits data into approximately 100MiB chunks that it distributes among TiKV servers. Because this increment is much smaller than a full server, it's much easier to move around and redistribute data. It's also possible to add new servers in smaller increments, which is easier on planning.
-
-### Scaling
-
-**tl;dr:** Much easier
-
-This is related to capacity planning and sharding. When we talk about scaling, many people think about very large _systems,_ but that is not exclusively how I think of the problem:
-
- * Scaling is being able to start with something very small, without having to make huge investments upfront on the chance it could become very large.
- * Scaling is also a people problem. If a system requires too much internal knowledge to operate, it can become hard to grow as an engineering organization. The barrier to entry for new hires can become very high.
-
-
-
-Thus, by providing automatic sharding, TiDB can scale much easier.
-
-### Schema changes (DDL)
-
-**tl;dr:** Mostly better
-
-The data definition language (DDL) supported in TiDB is all online, which means it doesn't block other reads or writes to the system. It also doesn't block the replication stream.
-
-That's the good news, but there are a couple of limitations to be aware of:
-
- * TiDB does not currently support all DDL operations, such as changing the primary key or some "change data type" operations.
- * TiDB does not currently allow you to chain multiple DDL changes in the same command, e.g., _ALTER TABLE t1 ADD INDEX (x), ADD INDEX (y)_. You will need to break these queries up into individual DDL queries.
-
-
-
-This is an area that we're looking to improve in [TiDB 3.0][7].
-
-### Creating one-off data dumps for the reporting team
-
-**tl;dr:** May not be required
-
-DBAs loathe manual tasks that create one-off exports of data to be consumed by another team, perhaps in an analytics tool or data warehouse.
-
-This is often required when the types of queries that are be executed on the dataset are analytical. TiDB has hybrid transactional/analytical processing (HTAP) capabilities, so in many cases, these queries should work fine. If your analytics team is using Spark, you can also use the [TiSpark][8] connector to allow them to connect directly to TiKV.
-
-This is another area we are improving with [TiFlash][7], a column store accelerator. We are also working on a plugin system to support external authentication. This will make it easier to manage access by the reporting team.
-
-### Conclusion
-
-In this post, I looked at some common MySQL DBA tasks and how they translate to TiDB. If you would like to learn more, check out our [TiDB Academy course][9] designed for MySQL DBAs (it's free!).
-
---------------------------------------------------------------------------------
-
-via: https://opensource.com/article/19/3/how-save-time-tidb
-
-作者:[Morgan Tocker][a]
-选题:[lujun9972][b]
-译者:[译者ID](https://github.com/译者ID)
-校对:[校对者ID](https://github.com/校对者ID)
-
-本文由 [LCTT](https://github.com/LCTT/TranslateProject) 原创编译,[Linux中国](https://linux.cn/) 荣誉推出
-
-[a]: https://opensource.com/users/morgo
-[b]: https://github.com/lujun9972
-[1]: https://opensource.com/sites/default/files/styles/image-full-size/public/lead-images/checklist_todo_clock_time_team.png?itok=1z528Q0y (Team checklist)
-[2]: https://opensource.com/article/18/11/key-differences-between-mysql-and-tidb
-[3]: https://github.com/pingcap/tidb
-[4]: https://opensource.com/sites/default/files/uploads/tidb_architecture.png (TiDB architecture)
-[5]: https://pingcap.com/docs/architecture/
-[6]: https://raft.github.io/
-[7]: https://pingcap.com/blog/tidb-3.0-beta-stability-at-scale/
-[8]: https://github.com/pingcap/tispark
-[9]: https://pingcap.com/tidb-academy/
diff --git a/sources/talk/20190410 Google partners with Intel, HPE and Lenovo for hybrid cloud.md b/sources/talk/20190410 Google partners with Intel, HPE and Lenovo for hybrid cloud.md
deleted file mode 100644
index 5603086a53..0000000000
--- a/sources/talk/20190410 Google partners with Intel, HPE and Lenovo for hybrid cloud.md
+++ /dev/null
@@ -1,60 +0,0 @@
-[#]: collector: (lujun9972)
-[#]: translator: ( )
-[#]: reviewer: ( )
-[#]: publisher: ( )
-[#]: url: ( )
-[#]: subject: (Google partners with Intel, HPE and Lenovo for hybrid cloud)
-[#]: via: (https://www.networkworld.com/article/3388062/google-partners-with-intel-hpe-and-lenovo-for-hybrid-cloud.html#tk.rss_all)
-[#]: author: (Andy Patrizio https://www.networkworld.com/author/Andy-Patrizio/)
-
-Google partners with Intel, HPE and Lenovo for hybrid cloud
-======
-Google boosted its on-premises and cloud connections with Kubernetes and serverless computing.
-![Ilze Lucero \(CC0\)][1]
-
-Still struggling to get its Google Cloud business out of single-digit marketshare, Google this week introduced new partnerships with Lenovo and Intel to help bolster its hybrid cloud offerings, both built on Google’s Kubernetes container technology.
-
-At Google’s Next ’19 show this week, Intel and Google said they will collaborate on Google's Anthos, a new reference design based on the second-Generation Xeon Scalable processor introduced last week and an optimized Kubernetes software stack designed to deliver increased workload portability between public and private cloud environments.
-
-**[ Read also:[What hybrid cloud means in practice][2] | Get regularly scheduled insights: [Sign up for Network World newsletters][3] ]**
-
-As part the Anthos announcement, Hewlett Packard Enterprise (HPE) said it has validated Anthos on its ProLiant servers, while Lenovo has done the same for its ThinkAgile platform. This solution will enable customers to get a consistent Kubernetes experience between Google Cloud and their on-premises HPE or Lenovo servers. No official word from Dell yet, but they can’t be far behind.
-
-Users will be able to manage their Kubernetes clusters and enforce policy consistently across environments – either in the public cloud or on-premises. In addition, Anthos delivers a fully integrated stack of hardened components, including OS and container runtimes that are tested and validated by Google, so customers can upgrade their clusters with confidence and minimize downtime.
-
-### What is Google Anthos?
-
-Google formally introduced [Anthos][4] at this year’s show. Anthos, formerly Cloud Services Platform, is meant to allow users to run their containerized applications without spending time on building, managing, and operating Kubernetes clusters. It runs both on Google Cloud Platform (GCP) with Google Kubernetes Engine (GKE) and in your data center with GKE On-Prem. Anthos will also let you manage workloads running on third-party clouds such as Amazon Web Services (AWS) and Microsoft Azure.
-
-Google also announced the beta release of Anthos Migrate, which auto-migrates virtual machines (VM) from on-premises or other clouds directly into containers in GKE with minimal effort. This allows enterprises to migrate their infrastructure in one streamlined motion, without upfront modifications to the original VMs or applications.
-
-Intel said it will publish the production design as an Intel Select Solution, as well as a developer platform, making it available to anyone who wants it.
-
-### Serverless environments
-
-Google isn’t stopping with Kubernetes containers, it’s also pushing ahead with serverless environments. [Cloud Run][5] is Google’s implementation of serverless computing, which is something of a misnomer. You still run your apps on servers; you just aren’t using a dedicated physical server. It is stateless, so resources are not allocated until you actually run or use the application.
-
-Cloud Run is a fully serverless offering that takes care of all infrastructure management, including the provisioning, configuring, scaling, and managing of servers. It automatically scales up or down within seconds, even down to zero depending on traffic, ensuring you pay only for the resources you actually use. Cloud Run can be used on GKE, offering the option to run side by side with other workloads deployed in the same cluster.
-
-Join the Network World communities on [Facebook][6] and [LinkedIn][7] to comment on topics that are top of mind.
-
---------------------------------------------------------------------------------
-
-via: https://www.networkworld.com/article/3388062/google-partners-with-intel-hpe-and-lenovo-for-hybrid-cloud.html#tk.rss_all
-
-作者:[Andy Patrizio][a]
-选题:[lujun9972][b]
-译者:[译者ID](https://github.com/译者ID)
-校对:[校对者ID](https://github.com/校对者ID)
-
-本文由 [LCTT](https://github.com/LCTT/TranslateProject) 原创编译,[Linux中国](https://linux.cn/) 荣誉推出
-
-[a]: https://www.networkworld.com/author/Andy-Patrizio/
-[b]: https://github.com/lujun9972
-[1]: https://images.idgesg.net/images/article/2018/03/cubes_blocks_squares_containers_ilze_lucero_cc0_via_unsplash_1200x800-100752172-large.jpg
-[2]: https://www.networkworld.com/article/3249495/what-hybrid-cloud-mean-practice
-[3]: https://www.networkworld.com/newsletters/signup.html
-[4]: https://cloud.google.com/blog/topics/hybrid-cloud/new-platform-for-managing-applications-in-todays-multi-cloud-world
-[5]: https://cloud.google.com/blog/products/serverless/announcing-cloud-run-the-newest-member-of-our-serverless-compute-stack
-[6]: https://www.facebook.com/NetworkWorld/
-[7]: https://www.linkedin.com/company/network-world
diff --git a/sources/talk/20190410 HPE and Nutanix partner for hyperconverged private cloud systems.md b/sources/talk/20190410 HPE and Nutanix partner for hyperconverged private cloud systems.md
deleted file mode 100644
index 76f908c68b..0000000000
--- a/sources/talk/20190410 HPE and Nutanix partner for hyperconverged private cloud systems.md
+++ /dev/null
@@ -1,60 +0,0 @@
-[#]: collector: (lujun9972)
-[#]: translator: ( )
-[#]: reviewer: ( )
-[#]: publisher: ( )
-[#]: url: ( )
-[#]: subject: (HPE and Nutanix partner for hyperconverged private cloud systems)
-[#]: via: (https://www.networkworld.com/article/3388297/hpe-and-nutanix-partner-for-hyperconverged-private-cloud-systems.html#tk.rss_all)
-[#]: author: (Andy Patrizio https://www.networkworld.com/author/Andy-Patrizio/)
-
-HPE and Nutanix partner for hyperconverged private cloud systems
-======
-Both companies will sell HP ProLiant appliances with Nutanix software but to different markets.
-![Hewlett Packard Enterprise][1]
-
-Hewlett Packard Enterprise (HPE) has partnered with Nutanix to offer Nutanix’s hyperconverged infrastructure (HCI) software available as a managed private cloud service and on HPE-branded appliances.
-
-As part of the deal, the two companies will be competing against each other in hardware sales, sort of. If you want the consumption model you get through HPE’s GreenLake, where your usage is metered and you pay for only the time you use it (similar to the cloud), then you would get the ProLiant hardware from HPE.
-
-If you want an appliance model where you buy the hardware outright, like in the traditional sense of server sales, you would get the same ProLiant through Nutanix.
-
-**[ Read also:[What is hybrid cloud computing?][2] and [Multicloud mania: what to know][3] ]**
-
-As it is, HPE GreenLake offers multiple cloud offerings to customers, including virtualization courtesy of VMware and Microsoft. With the Nutanix partnership, HPE is adding Nutanix’s free Acropolis hypervisor to its offerings.
-
-“Customers get to choose an alternative to VMware with this,” said Pradeep Kumar, senior vice president and general manager of HPE’s Pointnext consultancy. “They like the Acropolis license model, since it’s license-free. Then they have choice points so pricing is competitive. Some like VMware, and I think it’s our job to offer them both and they can pick and choose.”
-
-Kumar added that the whole Nutanix stack is 15 to 18% less with Acropolis than a VMware-powered system, since they save on the hypervisor.
-
-The HPE-Nutanix partnership offers a fully managed hybrid cloud infrastructure delivered as a service and deployed in customers’ data centers or co-location facility. The managed private cloud service gives enterprises a hyperconverged environment in-house without having to manage the infrastructure themselves and, more importantly, without the burden of ownership. GreenLake operates more like a lease than ownership.
-
-### HPE GreenLake's private cloud services promise to significantly reduce costs
-
-HPE is pushing hard on GreenLake, which basically mimics cloud platform pricing models of paying for what you use rather than outright ownership. Kumar said HPE projects the consumption model will account for 30% of HPE’s business in the next few years.
-
-GreenLake makes some hefty promises. According to Nutanix-commissioned IDC research, customers will achieve a 60% reduction in the five-year cost of operations, while a HPE-commissioned Forrester report found customers benefit from a 30% Capex savings due to eliminated need for overprovisioning and a 90% reduction in support and professional services costs.
-
-By shifting to an IT as a Service model, HPE claims to provide a 40% increase in productivity by reducing the support load on IT operations staff and to shorten the time to deploy IT projects by 65%.
-
-The two new offerings from the partnership – HPE GreenLake’s private cloud service running Nutanix software and the HPE-branded appliances integrated with Nutanix software – are expected to be available during the 2019 third quarter, the companies said.
-
-Join the Network World communities on [Facebook][4] and [LinkedIn][5] to comment on topics that are top of mind.
-
---------------------------------------------------------------------------------
-
-via: https://www.networkworld.com/article/3388297/hpe-and-nutanix-partner-for-hyperconverged-private-cloud-systems.html#tk.rss_all
-
-作者:[Andy Patrizio][a]
-选题:[lujun9972][b]
-译者:[译者ID](https://github.com/译者ID)
-校对:[校对者ID](https://github.com/校对者ID)
-
-本文由 [LCTT](https://github.com/LCTT/TranslateProject) 原创编译,[Linux中国](https://linux.cn/) 荣誉推出
-
-[a]: https://www.networkworld.com/author/Andy-Patrizio/
-[b]: https://github.com/lujun9972
-[1]: https://images.techhive.com/images/article/2015/11/hpe_building-100625424-large.jpg
-[2]: https://www.networkworld.com/article/3233132/cloud-computing/what-is-hybrid-cloud-computing.html
-[3]: https://www.networkworld.com/article/3252775/hybrid-cloud/multicloud-mania-what-to-know.html
-[4]: https://www.facebook.com/NetworkWorld/
-[5]: https://www.linkedin.com/company/network-world
diff --git a/sources/talk/20190418 Cisco warns WLAN controller, 9000 series router and IOS-XE users to patch urgent security holes.md b/sources/talk/20190418 Cisco warns WLAN controller, 9000 series router and IOS-XE users to patch urgent security holes.md
deleted file mode 100644
index 5abcb3bcba..0000000000
--- a/sources/talk/20190418 Cisco warns WLAN controller, 9000 series router and IOS-XE users to patch urgent security holes.md
+++ /dev/null
@@ -1,76 +0,0 @@
-[#]: collector: (lujun9972)
-[#]: translator: ( )
-[#]: reviewer: ( )
-[#]: publisher: ( )
-[#]: url: ( )
-[#]: subject: (Cisco warns WLAN controller, 9000 series router and IOS/XE users to patch urgent security holes)
-[#]: via: (https://www.networkworld.com/article/3390159/cisco-warns-wlan-controller-9000-series-router-and-iosxe-users-to-patch-urgent-security-holes.html#tk.rss_all)
-[#]: author: (Michael Cooney https://www.networkworld.com/author/Michael-Cooney/)
-
-Cisco warns WLAN controller, 9000 series router and IOS/XE users to patch urgent security holes
-======
-Cisco says unpatched vulnerabilities could lead to DoS attacks, arbitrary code execution, take-over of devices.
-![Woolzian / Getty Images][1]
-
-Cisco this week issued 31 security advisories but directed customer attention to “critical” patches for its IOS and IOS XE Software Cluster Management and IOS software for Cisco ASR 9000 Series routers. A number of other vulnerabilities also need attention if customers are running Cisco Wireless LAN Controllers.
-
-The [first critical patch][2] has to do with a vulnerability in the Cisco Cluster Management Protocol (CMP) processing code in Cisco IOS and Cisco IOS XE Software that could allow an unauthenticated, remote attacker to send malformed CMP-specific Telnet options while establishing a Telnet session with an affected Cisco device configured to accept Telnet connections. An exploit could allow an attacker to execute arbitrary code and obtain full control of the device or cause a reload of the affected device, Cisco said.
-
-**[ Also see[What to consider when deploying a next generation firewall][3]. | Get regularly scheduled insights by [signing up for Network World newsletters][4]. ]**
-
-The problem has a Common Vulnerability Scoring System number of 9.8 out of 10.
-
-According to Cisco, the Cluster Management Protocol utilizes Telnet internally as a signaling and command protocol between cluster members. The vulnerability is due to the combination of two factors:
-
- * The failure to restrict the use of CMP-specific Telnet options only to internal, local communications between cluster members and instead accept and process such options over any Telnet connection to an affected device
- * The incorrect processing of malformed CMP-specific Telnet options.
-
-
-
-Cisco says the vulnerability can be exploited during Telnet session negotiation over either IPv4 or IPv6. This vulnerability can only be exploited through a Telnet session established _to_ the device; sending the malformed options on Telnet sessions _through_ the device will not trigger the vulnerability.
-
-The company says there are no workarounds for this problem, but disabling Telnet as an allowed protocol for incoming connections would eliminate the exploit vector. Cisco recommends disabling Telnet and using SSH instead. Information on how to do both can be found on the [Cisco Guide to Harden Cisco IOS Devices][5]. For patch information [go here][6].
-
-The second critical patch involves a vulnerability in the sysadmin virtual machine (VM) on Cisco’s ASR 9000 carrier class routers running Cisco IOS XR 64-bit Software could let an unauthenticated, remote attacker access internal applications running on the sysadmin VM, Cisco said in the [advisory][7]. This CVSS also has a 9.8 rating.
-
-**[[Prepare to become a Certified Information Security Systems Professional with this comprehensive online course from PluralSight. Now offering a 10-day free trial!][8] ]**
-
-Cisco said the vulnerability is due to incorrect isolation of the secondary management interface from internal sysadmin applications. An attacker could exploit this vulnerability by connecting to one of the listening internal applications. A successful exploit could result in unstable conditions, including both denial of service (DoS) and remote unauthenticated access to the device, Cisco stated.
-
-Cisco has released [free software updates][6] that address the vulnerability described in this advisory.
-
-Lastly, Cisco wrote that [multiple vulnerabilities][9] in the administrative GUI configuration feature of Cisco Wireless LAN Controller (WLC) Software could let an authenticated, remote attacker cause the device to reload unexpectedly during device configuration when the administrator is using this GUI, causing a DoS condition on an affected device. The attacker would need to have valid administrator credentials on the device for this exploit to work, Cisco stated.
-
-“These vulnerabilities are due to incomplete input validation for unexpected configuration options that the attacker could submit while accessing the GUI configuration menus. An attacker could exploit these vulnerabilities by authenticating to the device and submitting crafted user input when using the administrative GUI configuration feature,” Cisco stated.
-
-“These vulnerabilities have a Security Impact Rating (SIR) of High because they could be exploited when the software fix for the Cisco Wireless LAN Controller Cross-Site Request Forgery Vulnerability is not in place,” Cisco stated. “In that case, an unauthenticated attacker who first exploits the cross-site request forgery vulnerability could perform arbitrary commands with the privileges of the administrator user by exploiting the vulnerabilities described in this advisory.”
-
-Cisco has released [software updates][10] that address these vulnerabilities and said that there are no workarounds.
-
-Join the Network World communities on [Facebook][11] and [LinkedIn][12] to comment on topics that are top of mind.
-
---------------------------------------------------------------------------------
-
-via: https://www.networkworld.com/article/3390159/cisco-warns-wlan-controller-9000-series-router-and-iosxe-users-to-patch-urgent-security-holes.html#tk.rss_all
-
-作者:[Michael Cooney][a]
-选题:[lujun9972][b]
-译者:[译者ID](https://github.com/译者ID)
-校对:[校对者ID](https://github.com/校对者ID)
-
-本文由 [LCTT](https://github.com/LCTT/TranslateProject) 原创编译,[Linux中国](https://linux.cn/) 荣誉推出
-
-[a]: https://www.networkworld.com/author/Michael-Cooney/
-[b]: https://github.com/lujun9972
-[1]: https://images.idgesg.net/images/article/2019/02/compromised_data_security_breach_vulnerability_by_woolzian_gettyimages-475563052_2400x1600-100788413-large.jpg
-[2]: https://tools.cisco.com/security/center/content/CiscoSecurityAdvisory/cisco-sa-20170317-cmp
-[3]: https://www.networkworld.com/article/3236448/lan-wan/what-to-consider-when-deploying-a-next-generation-firewall.html
-[4]: https://www.networkworld.com/newsletters/signup.html
-[5]: http://www.cisco.com/c/en/us/support/docs/ip/access-lists/13608-21.html
-[6]: https://www.cisco.com/c/en/us/about/legal/cloud-and-software/end_user_license_agreement.html
-[7]: https://tools.cisco.com/security/center/content/CiscoSecurityAdvisory/cisco-sa-20190417-asr9k-exr
-[8]: https://pluralsight.pxf.io/c/321564/424552/7490?u=https%3A%2F%2Fwww.pluralsight.com%2Fpaths%2Fcertified-information-systems-security-professional-cisspr
-[9]: https://tools.cisco.com/security/center/content/CiscoSecurityAdvisory/cisco-sa-20190417-wlc-iapp
-[10]: https://www.cisco.com/c/en/us/support/web/tsd-cisco-worldwide-contacts.html
-[11]: https://www.facebook.com/NetworkWorld/
-[12]: https://www.linkedin.com/company/network-world
diff --git a/sources/talk/20190418 Fujitsu completes design of exascale supercomputer, promises to productize it.md b/sources/talk/20190418 Fujitsu completes design of exascale supercomputer, promises to productize it.md
deleted file mode 100644
index 59978d555c..0000000000
--- a/sources/talk/20190418 Fujitsu completes design of exascale supercomputer, promises to productize it.md
+++ /dev/null
@@ -1,58 +0,0 @@
-[#]: collector: (lujun9972)
-[#]: translator: ( )
-[#]: reviewer: ( )
-[#]: publisher: ( )
-[#]: url: ( )
-[#]: subject: (Fujitsu completes design of exascale supercomputer, promises to productize it)
-[#]: via: (https://www.networkworld.com/article/3389748/fujitsu-completes-design-of-exascale-supercomputer-promises-to-productize-it.html#tk.rss_all)
-[#]: author: (Andy Patrizio https://www.networkworld.com/author/Andy-Patrizio/)
-
-Fujitsu completes design of exascale supercomputer, promises to productize it
-======
-Fujitsu hopes to be the first to offer exascale supercomputing using Arm processors.
-![Riken Advanced Institute for Computational Science][1]
-
-Fujitsu and Japanese research institute Riken announced the design for the post-K supercomputer, to be launched in 2021, is complete and that they will productize the design for sale later this year.
-
-The K supercomputer was a massive system, built by Fujitsu and housed at the Riken Advanced Institute for Computational Science campus in Kobe, Japan, with more than 80,000 nodes and using Sparc64 VIIIfx processors, a derivative of the Sun Microsystems Sparc processor developed under a license agreement that pre-dated Oracle buying out Sun in 2010.
-
-**[ Also read:[10 of the world's fastest supercomputers][2] ]**
-
-It was ranked as the top supercomputer when it was launched in June 2011 with a computation speed of over 8 petaflops. And in November 2011, K became the first computer to top 10 petaflops. It was eventually surpassed as the world's fastest supercomputer by the IBM’s Sequoia, but even now, eight years later, it’s still in the top 20 of supercomputers in the world.
-
-### What's in the Post-K supercomputer?
-
-The new system, dubbed “Post-K,” will feature an Arm-based processor called A64FX, a high-performance CPU developed by Fujitsu, designed for exascale systems. The chip is based off the Arm8 design, which is popular in smartphones, with 48 cores plus four “assistant” cores and the ability to access up to 32GB of memory per chip.
-
-A64FX is the first CPU to adopt the Scalable Vector Extension (SVE), an instruction set specifically designed for Arm-based supercomputers. Fujitsu claims A64FX will offer a peak double precision (64-bit) floating point operations performance of over 2.7 teraflops per chip. The system will have one CPU per node and 384 nodes per rack. That comes out to one petaflop per rack.
-
-Contrast that with Summit, the top supercomputer in the world built by IBM for the Oak Ridge National Laboratory using IBM Power9 processors and Nvidia GPUs. A Summit rack has a peak computer of 864 teraflops.
-
-Let me put it another way: IBM’s Power processor and Nvidia’s Tesla are about to get pwned by a derivative chip to the one in your iPhone.
-
-**[[Get certified as an Apple Technical Coordinator with this seven-part online course from PluralSight.][3] ]**
-
-Fujitsu will productize the Post-K design and sell it as the successor to the Fujitsu Supercomputer PrimeHPC FX100. The company said it is also considering measures such as developing an entry-level model that will be easy to deploy, or supplying these technologies to other vendors.
-
-Post-K will be installed in the Riken Center for Computational Science (R-CCS), where the K computer is currently located. The system will be one of the first exascale supercomputers in the world, although the U.S. and China are certainly gunning to be first if only for bragging rights.
-
-Join the Network World communities on [Facebook][4] and [LinkedIn][5] to comment on topics that are top of mind.
-
---------------------------------------------------------------------------------
-
-via: https://www.networkworld.com/article/3389748/fujitsu-completes-design-of-exascale-supercomputer-promises-to-productize-it.html#tk.rss_all
-
-作者:[Andy Patrizio][a]
-选题:[lujun9972][b]
-译者:[译者ID](https://github.com/译者ID)
-校对:[校对者ID](https://github.com/校对者ID)
-
-本文由 [LCTT](https://github.com/LCTT/TranslateProject) 原创编译,[Linux中国](https://linux.cn/) 荣誉推出
-
-[a]: https://www.networkworld.com/author/Andy-Patrizio/
-[b]: https://github.com/lujun9972
-[1]: https://images.idgesg.net/images/article/2018/06/riken_advanced_institute_for_computational_science_k-computer_supercomputer_1200x800-100762135-large.jpg
-[2]: https://www.networkworld.com/article/3236875/embargo-10-of-the-worlds-fastest-supercomputers.html
-[3]: https://pluralsight.pxf.io/c/321564/424552/7490?u=https%3A%2F%2Fwww.pluralsight.com%2Fpaths%2Fapple-certified-technical-trainer-10-11
-[4]: https://www.facebook.com/NetworkWorld/
-[5]: https://www.linkedin.com/company/network-world
diff --git a/sources/talk/20190419 Intel follows AMD-s lead (again) into single-socket Xeon servers.md b/sources/talk/20190419 Intel follows AMD-s lead (again) into single-socket Xeon servers.md
deleted file mode 100644
index 9685591b2c..0000000000
--- a/sources/talk/20190419 Intel follows AMD-s lead (again) into single-socket Xeon servers.md
+++ /dev/null
@@ -1,61 +0,0 @@
-[#]: collector: (lujun9972)
-[#]: translator: ( )
-[#]: reviewer: ( )
-[#]: publisher: ( )
-[#]: url: ( )
-[#]: subject: (Intel follows AMD’s lead (again) into single-socket Xeon servers)
-[#]: via: (https://www.networkworld.com/article/3390201/intel-follows-amds-lead-again-into-single-socket-xeon-servers.html#tk.rss_all)
-[#]: author: (Andy Patrizio https://www.networkworld.com/author/Andy-Patrizio/)
-
-Intel follows AMD’s lead (again) into single-socket Xeon servers
-======
-Intel's new U series of processors are aimed at the low-end market where one processor is good enough.
-![Intel][1]
-
-I’m really starting to wonder who the leader in x86 really is these days because it seems Intel is borrowing another page out of AMD’s playbook.
-
-Intel launched a whole lot of new Xeon Scalable processors earlier this month, but they neglected to mention a unique line: the U series of single-socket processors. The folks over at Serve The Home sniffed it out first, and Intel has confirmed the existence of the line, just that they “didn’t broadly promote them.”
-
-**[ Read also:[Intel makes a play for high-speed fiber networking for data centers][2] ]**
-
-To backtrack a bit, AMD made a major push for [single-socket servers][3] when it launched the Epyc line of server chips. Epyc comes with up to 32 cores and multithreading, and Intel (and Dell) argued that one 32-core/64-thread processor was enough to handle many loads and a lot cheaper than a two-socket system.
-
-The new U series isn’t available in the regular Intel [ARK database][4] listing of Xeon Scalable processors, but they do show up if you search. Intel says they are looking into that .There are two processors for now, one with 24 cores and two with 20 cores.
-
-The 24-core Intel [Xeon Gold 6212U][5] will be a counterpart to the Intel Xeon Platinum 8260, with a 2.4GHz base clock speed and a 3.9GHz turbo clock and the ability to access up to 1TB of memory. The Xeon Gold 6212U will have the same 165W TDP as the 8260 line, but with a single socket that’s 165 fewer watts of power.
-
-Also, Intel is suggesting a price of about $2,000 for the Intel Xeon Gold 6212U, a big discount over the Xeon Platinum 8260’s $4,702 list price. So, that will translate into much cheaper servers.
-
-The [Intel Xeon Gold 6210U][6] with 20 cores carries a suggested price of $1,500, has a base clock rate of 2.50GHz with turbo boost to 3.9GHz and a 150 watt TDP. Finally, there is the 20-core Intel [Xeon Gold 6209U][7] with a price of around $1,000 that is identical to the 6210 except its base clock speed is 2.1GHz with a turbo boost of 3.9GHz and a TDP of 125 watts due to its lower clock speed.
-
-**[[Get certified as an Apple Technical Coordinator with this seven-part online course from PluralSight.][8] ]**
-
-All of the processors support up to 1TB of DDR4-2933 memory and Intel’s Optane persistent memory.
-
-In terms of speeds and feeds, AMD has a slight advantage over Intel in the single-socket race, and Epyc 2 is rumored to be approaching completion, which will only further advance AMD’s lead.
-
-Join the Network World communities on [Facebook][9] and [LinkedIn][10] to comment on topics that are top of mind.
-
---------------------------------------------------------------------------------
-
-via: https://www.networkworld.com/article/3390201/intel-follows-amds-lead-again-into-single-socket-xeon-servers.html#tk.rss_all
-
-作者:[Andy Patrizio][a]
-选题:[lujun9972][b]
-译者:[译者ID](https://github.com/译者ID)
-校对:[校对者ID](https://github.com/校对者ID)
-
-本文由 [LCTT](https://github.com/LCTT/TranslateProject) 原创编译,[Linux中国](https://linux.cn/) 荣誉推出
-
-[a]: https://www.networkworld.com/author/Andy-Patrizio/
-[b]: https://github.com/lujun9972
-[1]: https://images.idgesg.net/images/article/2018/06/intel_generic_cpu_background-100760187-large.jpg
-[2]: https://www.networkworld.com/article/3307852/intel-makes-a-play-for-high-speed-fiber-networking-for-data-centers.html
-[3]: https://www.networkworld.com/article/3253626/amd-lands-dell-as-its-latest-epyc-server-processor-customer.html
-[4]: https://ark.intel.com/content/www/us/en/ark/products/series/192283/2nd-generation-intel-xeon-scalable-processors.html
-[5]: https://ark.intel.com/content/www/us/en/ark/products/192453/intel-xeon-gold-6212u-processor-35-75m-cache-2-40-ghz.html
-[6]: https://ark.intel.com/content/www/us/en/ark/products/192452/intel-xeon-gold-6210u-processor-27-5m-cache-2-50-ghz.html
-[7]: https://ark.intel.com/content/www/us/en/ark/products/193971/intel-xeon-gold-6209u-processor-27-5m-cache-2-10-ghz.html
-[8]: https://pluralsight.pxf.io/c/321564/424552/7490?u=https%3A%2F%2Fwww.pluralsight.com%2Fpaths%2Fapple-certified-technical-trainer-10-11
-[9]: https://www.facebook.com/NetworkWorld/
-[10]: https://www.linkedin.com/company/network-world
diff --git a/sources/talk/20190423 Edge computing is in most industries- future.md b/sources/talk/20190423 Edge computing is in most industries- future.md
new file mode 100644
index 0000000000..3f5a6d4c00
--- /dev/null
+++ b/sources/talk/20190423 Edge computing is in most industries- future.md
@@ -0,0 +1,63 @@
+[#]: collector: (lujun9972)
+[#]: translator: (ninifly )
+[#]: reviewer: ( )
+[#]: publisher: ( )
+[#]: url: ( )
+[#]: subject: (Edge computing is in most industries’ future)
+[#]: via: (https://www.networkworld.com/article/3391016/edge-computing-is-in-most-industries-future.html#tk.rss_all)
+[#]: author: (Anne Taylor https://www.networkworld.com/author/Anne-Taylor/)
+
+Edge computing is in most industries’ future
+======
+Nearly every industry can take advantage of edge computing in the journey to speed digital transformation efforts
+![iStock][1]
+
+The growth of edge computing is about to take a huge leap. Right now, companies are generating about 10% of their data outside a traditional data center or cloud. But within the next six years, that will increase to 75%, [according to Gartner][2].
+
+That’s largely down to the need to process data emanating from devices, such as Internet of Things (IoT) sensors. Early adopters include:
+
+ * **Manufacturers:** Devices and sensors seem endemic to this industry, so it’s no surprise to see the need to find faster processing methods for the data produced. A recent [_Automation World_][3] survey found that 43% of manufacturers have deployed edge projects. Most popular use cases have included production/manufacturing data analysis and equipment data analytics.
+
+ * **Retailers** : Like most industries deeply affected by the need to digitize operations, retailers are being forced to innovate their customer experiences. To that end, these organizations are “investing aggressively in compute power located closer to the buyer,” [writes Dave Johnson][4], executive vice president of the IT division at Schneider Electric. He cites examples such as augmented-reality mirrors in fitting rooms that offer different clothing options without the consumer having to try on the items, and beacon-based heat maps that show in-store traffic.
+
+
+
+ * **Healthcare organizations** : As healthcare costs continue to escalate, this industry is ripe for innovation that improves productivity and cost efficiencies. Management consulting firm [McKinsey & Co. has identified][5] at least 11 healthcare use cases that benefit patients, the facility, or both. Two examples: tracking mobile medical devices for nursing efficiency as well as optimization of equipment, and wearable devices that track user exercise and offer wellness advice.
+
+
+
+While these are strong use cases, as the edge computing market grows, so too will the number of industries adopting it.
+
+**Getting the edge on digital transformation**
+
+Faster processing at the edge fits perfectly into the objectives and goals of digital transformation — improving efficiencies, productivity, speed to market, and the customer experience. Here are just a few of the potential applications and industries that will be changed by edge computing:
+
+**Agriculture:** Farmers and organizations already use drones to transmit field and climate conditions to watering equipment. Other applications might include monitoring and location tracking of workers, livestock, and equipment to improve productivity, efficiencies, and costs.
+
+**Energy** : There are multiple potential applications in this sector that could benefit both consumers and providers. For example, smart meters help homeowners better manage energy use while reducing grid operators’ need for manual meter reading. Similarly, sensors on water pipes would detect leaks, while providing real-time consumption data.
+
+**Financial services** : Banks are adopting interactive ATMs that quickly process data to provide better customer experiences. At the organizational level, transactional data can be more quickly analyzed for fraudulent activity.
+
+**Logistics** : As consumers demand faster delivery of goods and services, logistics companies will need to transform mapping and routing capabilities to get real-time data, especially in terms of last-mile planning and tracking. That could involve street-, package-, and car-based sensors transmitting data for processing.
+
+All industries have the potential for transformation, thanks to edge computing. But it will depend on how they address their computing infrastructure. Discover how to overcome any IT obstacles at [APC.com][6].
+
+--------------------------------------------------------------------------------
+
+via: https://www.networkworld.com/article/3391016/edge-computing-is-in-most-industries-future.html#tk.rss_all
+
+作者:[Anne Taylor][a]
+选题:[lujun9972][b]
+译者:[译者ID](https://github.com/译者ID)
+校对:[校对者ID](https://github.com/校对者ID)
+
+本文由 [LCTT](https://github.com/LCTT/TranslateProject) 原创编译,[Linux中国](https://linux.cn/) 荣誉推出
+
+[a]: https://www.networkworld.com/author/Anne-Taylor/
+[b]: https://github.com/lujun9972
+[1]: https://images.idgesg.net/images/article/2019/04/istock-1019389496-100794424-large.jpg
+[2]: https://www.gartner.com/smarterwithgartner/what-edge-computing-means-for-infrastructure-and-operations-leaders/
+[3]: https://www.automationworld.com/article/technologies/cloud-computing/its-not-edge-vs-cloud-its-both
+[4]: https://blog.schneider-electric.com/datacenter/2018/07/10/why-brick-and-mortar-retail-quickly-establishing-leadership-edge-computing/
+[5]: https://www.mckinsey.com/industries/high-tech/our-insights/new-demand-new-markets-what-edge-computing-means-for-hardware-companies
+[6]: https://www.apc.com/us/en/solutions/business-solutions/edge-computing.jsp
diff --git a/sources/talk/20190423 Open architecture and open source - The new wave for SD-WAN.md b/sources/talk/20190423 Open architecture and open source - The new wave for SD-WAN.md
new file mode 100644
index 0000000000..8be9e14ada
--- /dev/null
+++ b/sources/talk/20190423 Open architecture and open source - The new wave for SD-WAN.md
@@ -0,0 +1,186 @@
+[#]: collector: (lujun9972)
+[#]: translator: ( )
+[#]: reviewer: ( )
+[#]: publisher: ( )
+[#]: url: ( )
+[#]: subject: (Open architecture and open source – The new wave for SD-WAN?)
+[#]: via: (https://www.networkworld.com/article/3390151/open-architecture-and-open-source-the-new-wave-for-sd-wan.html#tk.rss_all)
+[#]: author: (Matt Conran https://www.networkworld.com/author/Matt-Conran/)
+
+Open architecture and open source – The new wave for SD-WAN?
+======
+As networking continues to evolve, you certainly don't want to break out a forklift every time new technologies are introduced. Open architecture would allow you to replace the components of a system, and give you more flexibility to control your own networking destiny.
+![opensource.com \(CC BY-SA 2.0\)][1]
+
+I recently shared my thoughts about the [role of open source in networking][2]. I discussed two significant technological changes that we have witnessed. I call them waves, and these waves will redefine how we think about networking and security.
+
+The first wave signifies that networking is moving to the software so that it can run on commodity off-the-shelf hardware. The second wave is the use of open source technologies, thereby removing the barriers to entry for new product innovation and rapid market access. This is especially supported in the SD-WAN market rush.
+
+Seemingly, we are beginning to see less investment in hardware unless there is a specific segment that needs to be resolved. But generally, software-based platforms are preferred as they bring many advantages. It is evident that there has been a technology shift. We have moved networking from hardware to software and this shift has positive effects for users, enterprises and service providers.
+
+**[ Don’t miss[customer reviews of top remote access tools][3] and see [the most powerful IoT companies][4] . | Get daily insights by [signing up for Network World newsletters][5]. ]**
+
+### Performance (hardware vs software)
+
+There has always been a misconception that the hardware-based platforms are faster due to the hardware acceleration that exists in the network interface controller (NIC). However, this is a mistaken belief. Nowadays, software platforms can reach similar performance levels as compared to hardware-based platforms.
+
+Initially, people viewed hardware as a performance-based vehicle but today this does not hold true anymore. Even the bigger vendors are switching to software-based platforms. We are beginning to see this almost everywhere in networking.
+
+### SD-WAN and open source
+
+SD-WAN really took off quite rapidly due to the availability of open source. It enabled the vendors to leverage all the available open source components and then create their solution on top. By and large, SD-WAN vendors used the open source as the foundation of their solution and then added additional proprietary code over the baseline.
+
+However, even when using various open source components, there is still a lot of work left for these vendors to make it to a complete SD-WAN solution, even for reaching a baseline of centrally managed routers with flexible network architecture control, not to talk about complete feature set of SD-WAN.
+
+The result of the work done by these vendors is still closed products so the fact they are using open source components in their products is merely a time-to-market advantage but not a big benefit to the end users (enterprises) or service providers launching hosted services with these products. They are still limited in flexibility and vendor diversity is only achieved through a multi-vendor strategy which in practice means launching multiple silo services each based on a different SD-WAN vendor without real selection of the technologies that make each of the SD-WAN services they launch.
+
+I recently came across a company called [Flexiwan][6], their goal is to fundamentally change this limitation of SD-WAN by offering a full open source solution that, as they say, “includes integration points in the core of the system that allow for 3rd party logic to be integrated in an efficient way.” They call this an open architecture, which, in practical terms, means a service provider or enterprise can integrate his own application logic into the core of the SD-WAN router…or select best of breed sub-technologies or applications instead of having these dictated by the vendor himself. I believe there is the possibility of another wave of SD-WAN with a fully open source and open architecture to SD-WAN.
+
+This type of architecture brings many benefits to users, enterprises and service providers, especially when compared to the typical lock-in of bigger vendors, such as Cisco and VMware.
+
+With an open source open architecture, it’s easier to control the versions and extend more flexibility by using the software offered by different providers. It offers the ability to switch providers, not to mention being easier to install and upgrade the versions.
+
+### SD-WAN, open source and open architecture
+
+An SD-WAN solution that is an open source with open architecture provides a modular and decomposed type of SD-WAN. This enables the selection of elements to provide a solution.
+
+For example, enterprises and service providers can select the best-of-breed technologies from independent vendors, such as deep packet inspection (DPI), security, wide area network (WAN) optimization, session border controller (SBC), VoIP and other traffic specific optimization logic.
+
+Some SD-WAN vendors define an open architecture in such a way that they just have a set of APIs, for example, northbound APIs, to enable one to build management or do service chaining. This is one approach to an open architecture but in fact, it’s pretty limited since it does not bring the full benefits that an open architecture should offer.
+
+### Open source and the fear of hacking
+
+However, when I think about an open source and open architecture for SD-WAN, the first thing that comes to mind is bad actors. What about the code? If it’s an open source, the bad actor can find vulnerabilities, right?
+
+The community is a powerful force and will fix any vulnerability. Also with open source, the vendor, who is the one responsible for the open source component will fix the vulnerability much faster than a closed solution, where you are unaware of the vulnerability until a fix is released.
+
+### The SD-WAN evolution
+
+Before we go any further, let’s examine the history of SD-WAN and its origins, how we used to connect from the wide area network (WAN) to other branches via private or public links.
+
+SD-WAN offers the ability to connect your organization to a WAN. This could be connecting to the Internet or other branches, to optimally deliver applications with a good user-experience. Essentially, SD-WAN allows the organizations to design the architecture of their network dynamically by means of software.
+
+### In the beginning, there was IPSec
+
+It started with IPSec. Around two decades back, in 1995, the popular design was that of mesh architecture. As a result, we had a lot of point-to-point connections. Firstly, mesh architectures with IPSec VPNs are tiresome to manage as there is a potential for 100s of virtual private network (VPN) configurations.
+
+Authentically, IPSec started with two fundamental goals. The first was the tunneling protocol that would allow organizations to connect the users or other networks to their private network. This enabled the enterprises to connect to networks that they did not have a direct route to.
+
+The second goal of IPSec was to encrypt packets at the network layer and therefore securing the data in motion. Let’s face it: at that time, IPSec was terrible for complicated multi-site interconnectivity and high availability designs. If left to its defaults, IPSec is best suited for static designs.
+
+This was the reason why we had to step in the next era where additional functionality was added to IPSec. For example, IPSec had issues in supporting routing protocols using multicast. To overcome this, IPSec over generic routing encapsulation (GRE) was introduced.
+
+### The next era of SD-WAN
+
+During the journey to 2008, one could argue that the next era of WAN connectivity was when additional features were added to IPSec. At this time IPSec became known as a “Swiss army knife.” It could do many things but not anything really well.
+
+Back then, you could create multiple links, but it failed to select the traffic over these links other than by using simple routing. You needed to add a routing protocol. For advanced agile architectures, IPSec had to be incorporated with other higher-level protocols.
+
+Features were then added based on measuring the quality. Link quality features were added to analyze any delay, drops and to select alternative links for your applications. We began to add tunnels, multi-links and to select the traffic based on the priority, not just based on the routing.
+
+The most common way to the tunnel was to have IPSec over GRE. You have the GRE tunnel that enables you to send any protocol end-to-end by using IPSec for the encryption. All this functionality was added to achieve and create dynamic tunnels over IPSec and to optimize the IPSec tunnels.
+
+This was a move in the right direction, but it was still complex. It was not centrally managed and was error-prone with complex configurations that were unable to manage large deployments. IPSec had far too many limitations, so in the mid-2000s early SD-WAN vendors started cropping up. Some of these vendors enabled the enterprises to aggregate many separate digital subscriber lines (DSL) links into one faster logical link. At the same time, others added time stamps and/or sequence numbers to packets to improve the network performance and security when running over best effort (internet) links.
+
+International WAN connectivity was a popular focus since the cost delta between the Internet and private multiprotocol label switching (MPLS) was 10x+ different. Primarily, enterprises wanted the network performance and security of MPLS without having to pay a premium for it.
+
+Most of these solutions sat in-front or behind a traditional router from companies like Cisco. Evidently, just like WAN Optimization vendors, these were additional boxes/solutions that enterprises added to their networks.
+
+### The next era of SD-WAN, circa 2012
+
+It was somewhere in 2012 that we started to see the big rush to the SD-WAN market. Vendors such as Velocloud, Viptela and a lot of the other big players in the SD-WAN market kicked off with the objective of claiming some of the early SD-WAN success and going after the edge router market with a full feature router replacement and management simplicity.
+
+Open source networking software and other open source components for managing the traffic enabled these early SD-WAN vendors to lay a foundation where a lot of the code base was open source. They would then “glue” it together and add their own additional features.
+
+Around this time, Intel was driving data plane development kit (DPDK) and advanced encryption standard (AES) instruction set, which enabled that software to run on commodity hardware. The SD-WAN solutions were delivered as closed solutions where each solution used its own set of features. The features and technologies chosen for each vendor were different and not compatible with each other.
+
+### The recent era of SD-WAN, circa 2017
+
+A tipping point in 2017 was the gold rush for SD-WAN deployments. Everyone wanted to have SD-WAN as fast as possible.
+
+The SD-WAN market has taken off, as seen by 50 vendors with competing, proprietary solutions and market growth curves with a CAGR of 100%. There is a trend of big vendors like Cisco, Vmware and Oracle acquiring startups to compete in this new market.
+
+As a result, Cisco, which is the traditional enterprise market leader in WAN routing solutions felt threatened since its IWAN solution, which had been around since 2008, was too complex (a 900-page configuration and operations manual). Besides, its simple solution based on the Meraki acquisition was not feature-rich enough for the large enterprises.
+
+With their acquisition of Viptela, Cisco currently has a 13% of the market share, and for the first time in decades, it is not the market leader. The large cloud vendors, such as Google and Facebook are utilizing their own technology for routing within their very large private networks.
+
+At some point between 2012 and 2017, we witnessed the service providers adopting SD-WAN. This introduced the onset and movement of managed SD-WAN services. As a result, the service providers wanted to have SD-WAN on the menu for their customers. But there were many limitations in the SD-WAN market, as it was offered as a closed-box solution, giving the service providers limited control.
+
+At this point surfaced an expectation of change, as service providers and enterprises looked for more control. Customers can get better functionality from a multi-vendor approach than from a single vendor.
+
+### Don’t forget DIY SD-WAN
+
+Up to 60% of service providers and enterprises within the USA are now looking at DIY SD-WAN. A DIY SD-WAN solution is not where the many pieces of open source are taken and caste into something. The utmost focus is on the solution that can be self-managed but buy from a vendor.
+
+Today, the majority of the market is looking for managed solutions and the upper section that has the expertise wants to be equipped with more control options.
+
+### SD-WAN vendors attempting everything
+
+There is a trend that some vendors try to do everything with SD-WAN. As a result, whether you are an enterprise or a service provider, you are locked into a solution that is dictated by the SD-WAN vendor.
+
+The SD-WAN vendors have made the supplier choice or developed what they think is relevant. Evidently, some vendors are using stacks and software development kits (SDKs) that they purchased, for example, for deep packet inspection (DPI).
+
+Ultimately, you are locked into a specific solution that the vendor has chosen for you. If you are a service provider, you might disapprove of this limitation and if you are an enterprise with specific expertise, you might want to zoom in for more control.
+
+### All-in-one security vendors
+
+Many SD-WAN vendors promote themselves as security companies. But would you prefer to buy a security solution from an SD-WAN vendor or from an experienced vendor, such as Checkpoint?
+
+Both: enterprise and service providers want to have a choice, but with an integrated black box security solution, you don't have a choice. The more you integrate and throw into the same box, the stronger the vendor lock-in is and the weaker the flexibility.
+
+Essentially, with this approach, you are going for the lowest common denominator instead of the highest. Ideally, the technology of the services that you deploy on your network requires expertise. One vendor cannot be an expert in everything.
+
+An open architecture lies in a place for experts in different areas to join together and add their own specialist functionality.
+
+### Encrypted traffic
+
+As a matter of fact, what is not encrypted today will be encrypted tomorrow. The vendor of the application can perform intelligent things that the SD-WAN vendor cannot because they control both sides. Hence, if you can put something inside the SD-WAN edge device, they can make smart decisions even if the traffic is encrypted.
+
+But in the case of traditional SD-WANs, there needs to be a corporation with a content provider. However, with an open architecture, you can integrate anything, and nothing prevents the integration. A lot of traffic is encrypted and it's harder to manage encrypted traffic. However, an open architecture would allow the content providers to manage the traffic more effectively.
+
+### 2019 and beyond: what is an open architecture?
+
+Cloud providers and enterprises have discovered that 90% of the user experience and security problems arise due to the network: between where the cloud provider resides and where the end-user consumes the application.
+
+Therefore, both cloud providers and large enterprise with digital strategies are focusing on building their solutions based on open source stacks. Having a viable open source SD-WAN solution is the next step in the SD-WAN evolution, where it moves to involve the community in the solution. This is similar to what happens with containers and tools.
+
+Now, since we’re in 2019, are we going to witness a new era of SD-WAN? Are we moving to the open architecture with an open source SD-WAN solution? An open architecture should be the core of the SD-WAN infrastructure, where additional technologies are integrated inside the SD-WAN solution and not only complementary VNFs. There is an interface and native APIs that allow you to integrate logic into the router. This way, the router will be able to intercept and act according to the traffic.
+
+So, if I’m a service provider and have my own application, I would want to write logic that would be able to communicate with my application. Without an open architecture, the service providers can’t really offer differentiation and change the way SD-WAN makes decisions and interacts with the traffic of their applications.
+
+There is a list of various technologies that you need to be an expert in to be able to integrate. And each one of these technologies can be a company, for example, DPI, VoIP optimization, and network monitoring to name a few. An open architecture will allow you to pick and choose these various elements as per your requirements.
+
+Networking is going through a lot of changes and it will continue to evolve with the passage of time. As a result, you wouldn’t want something that forces you to break out a forklift each time new technologies are introduced. Primarily, open architecture allows you to replace the components of the system and add code or elements that handle specific traffic and applications.
+
+### Open source
+
+Open source gives you more flexibility to control your own destiny. It offers the ability to select your own services that you want to be applied to your system. It provides security in the sense that if something happens to the vendor or there is a vulnerability in the system, you know that you are backed by the community that can fix such misadventures.
+
+From the perspective of the business model, it makes a more flexible and cost-effective system. Besides, with open source, the total cost of ownership will also be lower.
+
+**This article is published as part of the IDG Contributor Network.[Want to Join?][7]**
+
+Join the Network World communities on [Facebook][8] and [LinkedIn][9] to comment on topics that are top of mind.
+
+--------------------------------------------------------------------------------
+
+via: https://www.networkworld.com/article/3390151/open-architecture-and-open-source-the-new-wave-for-sd-wan.html#tk.rss_all
+
+作者:[Matt Conran][a]
+选题:[lujun9972][b]
+译者:[译者ID](https://github.com/译者ID)
+校对:[校对者ID](https://github.com/校对者ID)
+
+本文由 [LCTT](https://github.com/LCTT/TranslateProject) 原创编译,[Linux中国](https://linux.cn/) 荣誉推出
+
+[a]: https://www.networkworld.com/author/Matt-Conran/
+[b]: https://github.com/lujun9972
+[1]: https://images.techhive.com/images/article/2017/03/6554314981_7f95641814_o-100714680-large.jpg
+[2]: https://www.networkworld.com/article/3338143/the-role-of-open-source-in-networking.html
+[3]: https://www.networkworld.com/article/3262145/lan-wan/customer-reviews-top-remote-access-tools.html#nww-fsb
+[4]: https://www.networkworld.com/article/2287045/internet-of-things/wireless-153629-10-most-powerful-internet-of-things-companies.html#nww-fsb
+[5]: https://www.networkworld.com/newsletters/signup.html#nww-fsb
+[6]: https://flexiwan.com/sd-wan-open-source/
+[7]: /contributor-network/signup.html
+[8]: https://www.facebook.com/NetworkWorld/
+[9]: https://www.linkedin.com/company/network-world
diff --git a/sources/talk/20190424 Cisco- DNSpionage attack adds new tools, morphs tactics.md b/sources/talk/20190424 Cisco- DNSpionage attack adds new tools, morphs tactics.md
new file mode 100644
index 0000000000..e202384558
--- /dev/null
+++ b/sources/talk/20190424 Cisco- DNSpionage attack adds new tools, morphs tactics.md
@@ -0,0 +1,97 @@
+[#]: collector: (lujun9972)
+[#]: translator: ( )
+[#]: reviewer: ( )
+[#]: publisher: ( )
+[#]: url: ( )
+[#]: subject: (Cisco: DNSpionage attack adds new tools, morphs tactics)
+[#]: via: (https://www.networkworld.com/article/3390666/cisco-dnspionage-attack-adds-new-tools-morphs-tactics.html#tk.rss_all)
+[#]: author: (Michael Cooney https://www.networkworld.com/author/Michael-Cooney/)
+
+Cisco: DNSpionage attack adds new tools, morphs tactics
+======
+Cisco's Talos security group says DNSpionage tools have been upgraded to be more stealthy
+![Calvin Dexter / Getty Images][1]
+
+The group behind the Domain Name System attacks known as DNSpionage have upped their dark actions with new tools and malware to focus their attacks and better hide their activities.
+
+Cisco Talos security researchers, who discovered [DNSpionage][2] in November, this week warned of new exploits and capabilities of the nefarious campaign.
+
+**More about DNS:**
+
+ * [DNS in the cloud: Why and why not][3]
+ * [DNS over HTTPS seeks to make internet use more private][4]
+ * [How to protect your infrastructure from DNS cache poisoning][5]
+ * [ICANN housecleaning revokes old DNS security key][6]
+
+
+
+“The threat actor's ongoing development of DNSpionage malware shows that the attacker continues to find new ways to avoid detection. DNS tunneling is a popular method of exfiltration for some actors and recent examples of DNSpionage show that we must ensure DNS is monitored as closely as an organization's normal proxy or weblogs,” [Talos wrote][7]. “DNS is essentially the phonebook of the internet, and when it is tampered with, it becomes difficult for anyone to discern whether what they are seeing online is legitimate.”
+
+In Talos’ initial report, researchers said a DNSpionage campaign targeted various businesses in the Middle East as well as United Arab Emirates government domains. It also utilized two malicious websites containing job postings that were used to compromise targets via crafted Microsoft Office documents with embedded macros. The malware supported HTTP and DNS communication with the attackers.
+
+In a separate DNSpionage campaign, the attackers used the same IP address to redirect the DNS of legitimate .gov and private company domains. During each DNS compromise, the actor carefully generated “Let's Encrypt” certificates for the redirected domains. These certificates provide X.509 certificates for [Transport Layer Security (TLS)][8] free of charge to the user, Talos said.
+
+This week Cisco said DNSpionage actors have created a new remote administrative tool that supports HTTP and DNS communication with the attackers' command and control (C2).
+
+“In our previous post concerning DNSpionage, we showed that the malware author used malicious macros embedded in a Microsoft Word document. In the new sample from Lebanon identified at the end of February, the attacker used an Excel document with a similar macro.”
+
+**[[Prepare to become a Certified Information Security Systems Professional with this comprehensive online course from PluralSight. Now offering a 10-day free trial!][9] ]**
+
+Talos wrote: “The malware supports HTTP and DNS communication to the C2 server. The HTTP communication is hidden in the comments in the HTML code. This time, however, the C2 server mimics the GitHub platform instead of Wikipedia. While the DNS communication follows the same method we described in our previous article, the developer added some new features in this latest version and, this time, the actor removed the debug mode.”
+
+Talos added that the domain used for the C2 campaign is “bizarre.”
+
+“The previous version of DNSpionage attempted to use legitimate-looking domains in an attempt to remain undetected. However, this newer version uses the domain ‘coldfart[.]com,’ which would be easier to spot than other APT campaigns which generally try to blend in with traffic more suitable to enterprise environments. The domain was also hosted in the U.S., which is unusual for any espionage-style attack.”
+
+Talos researchers said they discovered that DNSpionage added a reconnaissance phase, that ensures the payload is being dropped on specific targets rather than indiscriminately downloaded on every machine.
+
+This level of attack also returns information about the workstation environment, including platform-specific information, the name of the domain and the local computer, and information concerning the operating system, Talos wrote. This information is key to helping the malware select the victims only and attempts to avoid researchers or sandboxes. Again, it shows the actor's improved abilities, as they now fingerprint the victim.
+
+This new tactic indicates an improved level of sophistication and is likely in response to the significant amount of public interest in the campaign.
+
+Talos noted that there have been several other public reports of DNSpionage attacks, and in January, the U.S. Department of Homeland Security issued an [alert][10] warning users about this threat activity.
+
+“In addition to increased reports of threat activity, we have also discovered new evidence that the threat actors behind the DNSpionage campaign continue to change their tactics, likely in an attempt to improve the efficacy of their operations,” Talos stated.
+
+In April, Cisco Talos identified an undocumented malware developed in .NET. On the analyzed samples, the malware author left two different internal names in plain text: "DropperBackdoor" and "Karkoff."
+
+“The malware is lightweight compared to other malware due to its small size and allows remote code execution from the C2 server. There is no obfuscation and the code can be easily disassembled,” Talos wrote.
+
+The Karkoff malware searches for two specific anti-virus platforms: Avira and Avast and will work around them.
+
+“The discovery of Karkoff also shows the actor is pivoting and is increasingly attempting to avoid detection while remaining very focused on the Middle Eastern region,” Talos wrote.
+
+Talos distinguished DNSpionage from another DNS attack method, “[Sea Turtle][11]”, it detailed this month. Sea Turtle involves state-sponsored attackers that are abusing DNS to target organizations and harvest credentials to gain access to sensitive networks and systems in a way that victims are unable to detect. This displays unique knowledge about how to manipulate DNS, Talos stated.
+
+By obtaining control of victims’ DNS, attackers can change or falsify any data victims receive from the Internet, illicitly modify DNS name records to point users to actor-controlled servers and users visiting those sites would never know, Talos reported.
+
+“While this incident is limited to targeting primarily national security organizations in the Middle East and North Africa, and we do not want to overstate the consequences of this specific campaign, we are concerned that the success of this operation will lead to actors more broadly attacking the global DNS system,” Talos stated about Sea Turtle.
+
+Join the Network World communities on [Facebook][12] and [LinkedIn][13] to comment on topics that are top of mind.
+
+--------------------------------------------------------------------------------
+
+via: https://www.networkworld.com/article/3390666/cisco-dnspionage-attack-adds-new-tools-morphs-tactics.html#tk.rss_all
+
+作者:[Michael Cooney][a]
+选题:[lujun9972][b]
+译者:[译者ID](https://github.com/译者ID)
+校对:[校对者ID](https://github.com/校对者ID)
+
+本文由 [LCTT](https://github.com/LCTT/TranslateProject) 原创编译,[Linux中国](https://linux.cn/) 荣誉推出
+
+[a]: https://www.networkworld.com/author/Michael-Cooney/
+[b]: https://github.com/lujun9972
+[1]: https://images.idgesg.net/images/article/2019/02/cyber_attack_threat_danger_breach_hack_security_by_calvindexter_gettyimages-860363294_2400x800-100788395-large.jpg
+[2]: https://blog.talosintelligence.com/2018/11/dnspionage-campaign-targets-middle-east.html
+[3]: https://www.networkworld.com/article/3273891/hybrid-cloud/dns-in-the-cloud-why-and-why-not.html
+[4]: https://www.networkworld.com/article/3322023/internet/dns-over-https-seeks-to-make-internet-use-more-private.html
+[5]: https://www.networkworld.com/article/3298160/internet/how-to-protect-your-infrastructure-from-dns-cache-poisoning.html
+[6]: https://www.networkworld.com/article/3331606/security/icann-housecleaning-revokes-old-dns-security-key.html
+[7]: https://blog.talosintelligence.com/2019/04/dnspionage-brings-out-karkoff.html
+[8]: https://www.networkworld.com/article/2303073/lan-wan-what-is-transport-layer-security-protocol.html
+[9]: https://pluralsight.pxf.io/c/321564/424552/7490?u=https%3A%2F%2Fwww.pluralsight.com%2Fpaths%2Fcertified-information-systems-security-professional-cisspr
+[10]: https://www.us-cert.gov/ncas/alerts/AA19-024A
+[11]: https://www.networkworld.com/article/3389747/cisco-talos-details-exceptionally-dangerous-dns-hijacking-attack.html
+[12]: https://www.facebook.com/NetworkWorld/
+[13]: https://www.linkedin.com/company/network-world
diff --git a/sources/talk/20190424 How data storage will shift to blockchain.md b/sources/talk/20190424 How data storage will shift to blockchain.md
new file mode 100644
index 0000000000..b31653e0f7
--- /dev/null
+++ b/sources/talk/20190424 How data storage will shift to blockchain.md
@@ -0,0 +1,70 @@
+[#]: collector: (lujun9972)
+[#]: translator: ( )
+[#]: reviewer: ( )
+[#]: publisher: ( )
+[#]: url: ( )
+[#]: subject: (How data storage will shift to blockchain)
+[#]: via: (https://www.networkworld.com/article/3390722/how-data-storage-will-shift-to-blockchain.html#tk.rss_all)
+[#]: author: (Patrick Nelson https://www.networkworld.com/author/Patrick-Nelson/)
+
+How data storage will shift to blockchain
+======
+Move over cloud and traditional in-house enterprise data center storage, distributed storage based on blockchain may be arriving imminently.
+![Cybrain / Getty Images][1]
+
+If you thought cloud storage was digging in its heels to become the go-to method for storing data, and at the same time grabbing share from own-server, in-house storage, you may be interested to hear that some think both are on the way out. Instead organizations will use blockchain-based storage.
+
+Decentralized blockchain-based file storage will be more secure, will make it harder to lose data, and will be cheaper than anything seen before, say organizations actively promoting the slant on encrypted, distributed technology.
+
+**[ Read also:[Why blockchain (might be) coming to an IoT implementation near you][2] ]**
+
+### Storing transactional data in a blockchain
+
+China company [FileStorm][3], which describes itself in marketing materials as the first [Interplanetary File Storage][4] (IPFS) platform on blockchain, says the key to making it all work is to only store the transactional data in blockchain. The actual data files, such as large video files, are distributed in IPFS.
+
+IPFS is a distributed, peer-to-peer file storage protocol. File parts come from multiple computers all at the same time, supposedly making the storage hardy. FileStorm adds blockchain on top of it for a form of transactional indexing.
+
+“Blockchain is designed to store transactions forever, and the data can never be altered, thus a trustworthy system is created,” says Raymond Fu, founder of FileStorm and chief product officer of MOAC, the underlying blockchain system used, in a video on the FileStorm website.
+
+“The blocks are used to store only small transactional data,” he says. You can’t store the large files on it. Those are distributed. Decentralized data storage platforms are needed for added decentralized blockchain, he says.
+
+YottaChain, another blockchain storage start-up project is coming at the whole thing from a slightly different angle. It claims its non-IPFS system is more secure partly because it performs deduplication after encryption.
+
+“Data is 10,000 times more secure than [traditional] centralized storage,” it says on its [website][5]. Deduplication eliminates duplicated or redundant data.
+
+### Disrupting data storage
+
+“Blockchain will disrupt data storage,” [says BlockApps separately][6]. The blockchain backend platform provider says advantages to this new generation of storage include that decentralizing data provides more security and privacy. That's due in part because it's harder to hack than traditional centralized storage. That the files are spread piecemeal among nodes, conceivably all over the world, makes it impossible for even the participating node to view the contents of the complete file, it says.
+
+Sharding, which is the term for the breaking apart and node-spreading of the actual data, is secured through keys. Markets can award token coins for mining, and coins can be spent to gain storage. Excess storage can even be sold. And cryptocurrencies have been started to “incentivize usage and to create a market for buying and selling decentralized storage,” BlockApps explains.
+
+The final parts of this new storage mix are that lost files are minimized because data can be duplicated simply — the data sets, for example, can be stored multiple times for error correction — and costs are reduced due to efficiencies.
+
+Square Tech (Shenzhen) Co., which makes blockchain file storage nodes, says in its marketing materials that it intends to build service centers globally to monitor its nodes in real time. Interestingly, another area the company has gotten involved in is the internet of things (IoT), and [it says][7] it wants “to unite the technical resources, capital, and human resources of the IoT industry and blockchain.” Perhaps we end up with a form of the internet of storage things?
+
+“The entire cloud computing industry will be disrupted by blockchain technology in just a few short years,” says BlockApps. Dropbox and Amazon “may even become overpriced and obsolete if they do not find ways to integrate with the advances.”
+
+Join the Network World communities on [Facebook][8] and [LinkedIn][9] to comment on topics that are top of mind.
+
+--------------------------------------------------------------------------------
+
+via: https://www.networkworld.com/article/3390722/how-data-storage-will-shift-to-blockchain.html#tk.rss_all
+
+作者:[Patrick Nelson][a]
+选题:[lujun9972][b]
+译者:[译者ID](https://github.com/译者ID)
+校对:[校对者ID](https://github.com/校对者ID)
+
+本文由 [LCTT](https://github.com/LCTT/TranslateProject) 原创编译,[Linux中国](https://linux.cn/) 荣誉推出
+
+[a]: https://www.networkworld.com/author/Patrick-Nelson/
+[b]: https://github.com/lujun9972
+[1]: https://images.idgesg.net/images/article/2019/02/chains_binary_data_blockchain_security_by_cybrain_gettyimages-926677890_2400x1600-100788435-large.jpg
+[2]: https://www.networkworld.com/article/3386881/why-blockchain-might-be-coming-to-an-iot-implementation-near-you.html
+[3]: http://filestorm.net/
+[4]: https://ipfs.io/
+[5]: https://www.yottachain.io/
+[6]: https://blockapps.net/blockchain-disrupt-data-storage/
+[7]: http://www.sikuaikeji.com/
+[8]: https://www.facebook.com/NetworkWorld/
+[9]: https://www.linkedin.com/company/network-world
diff --git a/sources/talk/20190424 No, drone delivery still isn-t ready for prime time.md b/sources/talk/20190424 No, drone delivery still isn-t ready for prime time.md
new file mode 100644
index 0000000000..c948f458ce
--- /dev/null
+++ b/sources/talk/20190424 No, drone delivery still isn-t ready for prime time.md
@@ -0,0 +1,91 @@
+[#]: collector: (lujun9972)
+[#]: translator: ( )
+[#]: reviewer: ( )
+[#]: publisher: ( )
+[#]: url: ( )
+[#]: subject: (No, drone delivery still isn’t ready for prime time)
+[#]: via: (https://www.networkworld.com/article/3390677/drone-delivery-not-ready-for-prime-time.html#tk.rss_all)
+[#]: author: (Fredric Paul https://www.networkworld.com/author/Fredric-Paul/)
+
+No, drone delivery still isn’t ready for prime time
+======
+Despite incremental progress and limited regulatory approval in the U.S. and Australia, drone delivery still isn’t a viable option in the vast majority of use cases.
+![Sorry imKirk \(CC0\)][1]
+
+April has a been a big month for drone delivery. First, [Alphabet’s Wing Aviation drones got approval from Australia’s Civil Aviation Safety Authority (CASA)][2], for public deliveries in the country, and this week [Wing earned Air Carrier Certification from the U.S. Federal Aviation Administration][3]. These two regulatory wins got lot of people got very excited. Finally, the conventional wisdom exulted, drone delivery is actually becoming a reality.
+
+Not so fast.
+
+### Drone delivery still in pilot/testing mode
+
+Despite some small-scale successes and the first signs of regulatory acceptance, drone delivery remains firmly in the carefully controlled pilot/test phase (and yes, I know drones don’t carry pilots).
+
+**[ Also read:[Coffee drone delivery: Ideas this bad could kill the internet of things][4] ]**
+
+For example, despite getting FAA approval to begin commercial deliveries, Wing is still working up beginning delivery trials to test the technology and gather information in Virginia later this year.
+
+But what about that public approval from CASA for deliveries outside Canberra? That’s [a real business][5] now, right?
+
+Well, yes and no.
+
+On the “yes” side, the Aussie approval reportedly came after 18 months of tests, 70,000 flights, and more than 3,000 actual deliveries of products from local coffee shops and pharmacies. So, at least some people somewhere in the world are actually getting stuff dropped at their doors by drones.
+
+In the “no” column, however, goes the fact that the approval covers only about 100 suburban homes, though more are planned to be added “in the coming weeks and months.” More importantly, the approval includes strict limits on when and where the drones can go. No crossing main roads, no nighttime deliveries, and prohibitions to stay away from people. And drone-eligible customers need a safety briefing!
+
+### Safety briefings required for customers
+
+That still sounds like a small-scale test, not a full-scale commercial roll-out. And while I think drone-safety classes are probably a good idea – and the testing period apparently passed without any injuries – even the perceived _need_ for them is not be a great advertisement for rapid expansion of drone deliveries.
+
+Ironically, though, a bigger issue than protecting people from the drones, perhaps, is protecting the drones from people. Instructions to stay 2 to 5 meters away from folks will help, but as I’ve previously addressed, these things are already seen as attractive nuisances and vandalism targets. Further raising the stakes, many local residents were said to be annoyed at the noise created by the drones. Now imagine those contraptions buzzing right by you all loaded down with steaming hot coffee or delicious ice cream.
+
+And even with all those caveats, no one is talking about the key factors in making drone deliveries a viable business: How much will those deliveries cost and who will pay? For a while, the desire to explore the opportunity will drive investment, but that won’t last forever. If drone deliveries aren’t cost effective for businesses, they won’t spread very far.
+
+From the customer perspective, most drone delivery tests are not yet charging for the service. If and when they start carrying fees as well as purchases, the novelty factor will likely entice many shoppers to pony up to get their items airlifted directly to their homes. But that also won’t last. Drone delivery will have to demonstrate that it’s better — faster, cheaper, or more reliable — than the existing alternatives to find its niche.
+
+### Drone deliveries are fast, commercial roll-out will be slow
+
+Long term, I have no doubt that drone delivery will eventually become an accepted part of the transportation infrastructure. I don’t necessarily buy into Wing’s prediction of an AU $40 million drone delivery market in Australia coming to pass anytime soon, but real commercial operations seem inevitable.
+
+It’s just going to be more limited than many proponents claim, and it’s likely to take a lot longer than expected to become mainstream. For example, despite ongoing testing, [Amazon has already missed Jeff Bezos’ 2018 deadline to begin commercial drone deliveries][6], and we haven’t heard much about [Walmart’s drone delivery plans][7] lately. And while tests by a number of companies continue in locations ranging from Iceland and Finland to the U.K. and the U.S. have created a lot of interest, they have not yet translated into widespread availability.
+
+Apart from the issue of how much consumers really want their stuff delivered by an armada of drones (a [2016 U.S. Post Office study][8] found that 44% of respondents liked the idea, while 34% didn’t — and 37% worried that drone deliveries might not be safe), a lot has to happen before that vision becomes reality.
+
+At a minimum, successful implementations of full-scale commercial drone delivery will require better planning, better-thought-out business cases, more rugged and efficient drone technology, and significant advances in flight control and autonomous flight. Like drone deliveries themselves, all that stuff is coming; it just hasn’t arrived yet.
+
+**More about drones and the internet of things:**
+
+ * [Drone defense -- powered by IoT -- is now a thing][9]
+ * [Ideas this bad could kill the Internet of Things][4]
+ * [10 reasons Amazon's drone delivery plan still won't fly][10]
+ * [Amazon’s successful drone delivery test doesn’t really prove anything][11]
+
+
+
+Join the Network World communities on [Facebook][12] and [LinkedIn][13] to comment on topics that are top of mind.
+
+--------------------------------------------------------------------------------
+
+via: https://www.networkworld.com/article/3390677/drone-delivery-not-ready-for-prime-time.html#tk.rss_all
+
+作者:[Fredric Paul][a]
+选题:[lujun9972][b]
+译者:[译者ID](https://github.com/译者ID)
+校对:[校对者ID](https://github.com/校对者ID)
+
+本文由 [LCTT](https://github.com/LCTT/TranslateProject) 原创编译,[Linux中国](https://linux.cn/) 荣誉推出
+
+[a]: https://www.networkworld.com/author/Fredric-Paul/
+[b]: https://github.com/lujun9972
+[1]: https://images.idgesg.net/images/article/2018/07/drone_mountains_by_sorry_imkirk_cc0_via_unsplash_1200x800-100763763-large.jpg
+[2]: https://medium.com/wing-aviation/wing-launches-commercial-air-delivery-service-in-canberra-5da134312474
+[3]: https://medium.com/wing-aviation/wing-becomes-first-certified-air-carrier-for-drones-in-the-us-43401883f20b
+[4]: https://www.networkworld.com/article/3301277/ideas-this-bad-could-kill-the-internet-of-things.html
+[5]: https://wing.com/australia/canberra
+[6]: https://www.businessinsider.com/jeff-bezos-predicted-amazon-would-be-making-drone-deliveries-by-2018-2018-12?r=US&IR=T
+[7]: https://www.networkworld.com/article/2999828/walmart-delivery-drone-plans.html
+[8]: https://www.uspsoig.gov/sites/default/files/document-library-files/2016/RARC_WP-17-001.pdf
+[9]: https://www.networkworld.com/article/3309413/drone-defense-powered-by-iot-is-now-a-thing.html
+[10]: https://www.networkworld.com/article/2900317/10-reasons-amazons-drone-delivery-plan-still-wont-fly.html
+[11]: https://www.networkworld.com/article/3185478/amazons-successful-drone-delivery-test-doesnt-really-prove-anything.html
+[12]: https://www.facebook.com/NetworkWorld/
+[13]: https://www.linkedin.com/company/network-world
diff --git a/sources/talk/20190429 Cisco goes all in on WiFi 6.md b/sources/talk/20190429 Cisco goes all in on WiFi 6.md
new file mode 100644
index 0000000000..decd25500a
--- /dev/null
+++ b/sources/talk/20190429 Cisco goes all in on WiFi 6.md
@@ -0,0 +1,87 @@
+[#]: collector: (lujun9972)
+[#]: translator: ( )
+[#]: reviewer: ( )
+[#]: publisher: ( )
+[#]: url: ( )
+[#]: subject: (Cisco goes all in on WiFi 6)
+[#]: via: (https://www.networkworld.com/article/3391919/cisco-goes-all-in-on-wifi-6.html#tk.rss_all)
+[#]: author: (Michael Cooney https://www.networkworld.com/author/Michael-Cooney/)
+
+Cisco goes all in on WiFi 6
+======
+Cisco rolls out Catalyst and Meraki WiFi 6-based access points, Catalyst 9000 switch
+![undefined / Getty Images][1]
+
+Cisco has taken the wraps off a family of WiFi 6 access points, roaming technology and developer-community support all to make wireless a solid enterprise equal with the wired world.
+
+“Best-effort’ wireless for enterprise customers doesn’t cut it any more. There’s been a change in customer expectations that there will be an uninterrupted unplugged experience,” said Scott Harrell, senior vice president and general manager of enterprise networking at Cisco. **“ **It is now a wireless-first world.** ”**
+
+**More about 802.11ax (Wi-Fi 6)**
+
+ * [Why 802.11ax is the next big thing in wireless][2]
+ * [FAQ: 802.11ax Wi-Fi][3]
+ * [Wi-Fi 6 (802.11ax) is coming to a router near you][4]
+ * [Wi-Fi 6 with OFDMA opens a world of new wireless possibilities][5]
+ * [802.11ax preview: Access points and routers that support Wi-Fi 6 are on tap][6]
+
+
+
+Bringing a wireless-first enterprise world together is one of the drivers behind a new family of WiFi 6-based access points (AP) for Cisco’s Catalyst and Meraki portfolios. WiFi 6 (802.11ax) is designed for high-density public or private environments. But it also will be beneficial in internet of things (IoT) deployments, and in offices that use bandwidth-hogging applications like videoconferencing.
+
+The Cisco Catalyst 9100 family and Meraki [MR 45/55][7] WiFi-6 access points are built on Cisco silicon and communicate via pre-802.1ax protocols. The silicon in these access points now acts a rich sensor providing IT with insights about what is going on the wireless network in real-time, and that enables faster reactions to problems and security concerns, Harrell said.
+
+Aside from WiFi 6, the boxes include support for visibility and communications with Zigbee, BLE and Thread protocols. The Catalyst APs support uplink speeds of 2.5 Gbps, in addition to 100 Mbps and 1 Gbps. All speeds are supported on Category 5e cabling for an industry first, as well as 10GBASE-T (IEEE 802.3bz) cabling, Cisco said.
+
+Wireless traffic aggregates to wired networks so and the wired network must also evolve. Technology like multi-gigabit Ethernet must be driven into the access layer, which in turn drives higher bandwidth needs at the aggregation and core layers, [Harrell said][8].
+
+Handling this influx of wireless traffic was part of the reason Cisco also upgraded its iconic Catalyst 6000 with the [Catalyst 9600 this week][9]. The 9600 brings with it support for Cat 6000 features such as support for MPLS, virtual switching and IPv6, while adding or bolstering support for wireless netowrks as well as Intent-based networking (IBN) and security segmentation. The 9600 helps fill out the company’s revamped lineup which includes the 9200 family of access switches, the 9500 aggregation switch and 9800 wireless controller.
+
+“WiFi doesn’t exist in a vacuum – how it connects to the enterprise and the data center or the Internet is key and in Cisco’s case that key is now the 9600 which has been built to handle the increased traffic,” said Lee Doyle, principal analyst with Doyle Research.
+
+The new 9600 ties in with the recently [released Catalyst 9800][10], which features 40Gbps to 100Gbps performance, depending on the model, hot-patching to simplify updates and eliminate update-related downtime, Encrypted Traffic Analytics (ETA), policy-based micro- and macro-segmentation and Trustworthy solutions to detect malware on wired or wireless connected devices, Cisco said.
+
+All Catalyst 9000 family members support other Cisco products such as [DNA Center][11] , which controls automation capabilities, assurance setting, fabric provisioning and policy-based segmentation for enterprise wired and wireless networks.
+
+The new APs are pre-standard, but other vendors including Aruba, NetGear and others are also selling pre-standard 802.11ax devices. Cisco getting into the market solidifies the validity of this strategy, said Brandon Butler, a senior research analyst with IDC.
+
+Many experts [expect the standard][12] to be ratified late this year.
+
+“We expect to see volume shipments of WiFi 6 products by early next year and it being the de facto WiFi standard by 2022.”
+
+On top of the APs and 9600 switch, Cisco extended its software development community – [DevNet][13] – to offer WiFi 6 learning labs, sandboxes and developer resources.
+
+The Cisco Catalyst and Meraki access platforms are open and programmable all the way down to the chipset level, allowing applications to take advantage of network programmability, Cisco said.
+
+Cisco also said it had added more vendors to now include Apple, Samsung, Boingo, Presidio and Intel for its ongoing [OpenRoaming][14] project. OpenRoaming, which is in beta promises to let users move seamlessly between wireless networks and LTE without interruption.
+
+Join the Network World communities on [Facebook][15] and [LinkedIn][16] to comment on topics that are top of mind.
+
+--------------------------------------------------------------------------------
+
+via: https://www.networkworld.com/article/3391919/cisco-goes-all-in-on-wifi-6.html#tk.rss_all
+
+作者:[Michael Cooney][a]
+选题:[lujun9972][b]
+译者:[译者ID](https://github.com/译者ID)
+校对:[校对者ID](https://github.com/校对者ID)
+
+本文由 [LCTT](https://github.com/LCTT/TranslateProject) 原创编译,[Linux中国](https://linux.cn/) 荣誉推出
+
+[a]: https://www.networkworld.com/author/Michael-Cooney/
+[b]: https://github.com/lujun9972
+[1]: https://images.idgesg.net/images/article/2019/04/cisco_catalyst_wifi_coffee-cup_coffee-beans_-100794990-large.jpg
+[2]: https://www.networkworld.com/article/3215907/mobile-wireless/why-80211ax-is-the-next-big-thing-in-wi-fi.html
+[3]: https://%20https//www.networkworld.com/article/3048196/mobile-wireless/faq-802-11ax-wi-fi.html
+[4]: https://www.networkworld.com/article/3311921/mobile-wireless/wi-fi-6-is-coming-to-a-router-near-you.html
+[5]: https://www.networkworld.com/article/3332018/wi-fi/wi-fi-6-with-ofdma-opens-a-world-of-new-wireless-possibilities.html
+[6]: https://www.networkworld.com/article/3309439/mobile-wireless/80211ax-preview-access-points-and-routers-that-support-the-wi-fi-6-protocol-on-tap.html
+[7]: https://meraki.cisco.com/lib/pdf/meraki_datasheet_MR55.pdf
+[8]: https://blogs.cisco.com/news/unplugged-and-uninterrupted
+[9]: https://www.networkworld.com/article/3391580/venerable-cisco-catalyst-6000-switches-ousted-by-new-catalyst-9600.html
+[10]: https://www.networkworld.com/article/3321000/cisco-links-wireless-wired-worlds-with-new-catalyst-9000-switches.html
+[11]: https://www.networkworld.com/article/3280988/cisco/cisco-opens-dna-center-network-control-and-management-software-to-the-devops-masses.html
+[12]: https://www.networkworld.com/article/3336263/is-jumping-ahead-to-wi-fi-6-the-right-move.html
+[13]: https://developer.cisco.com/wireless/?utm_campaign=colaunch-wireless19&utm_source=pressrelease&utm_medium=ciscopress-wireless-main
+[14]: https://www.cisco.com/c/en/us/solutions/enterprise-networks/802-11ax-solution/openroaming.html
+[15]: https://www.facebook.com/NetworkWorld/
+[16]: https://www.linkedin.com/company/network-world
diff --git a/sources/talk/20190430 Measuring the edge- Finding success with edge deployments.md b/sources/talk/20190430 Measuring the edge- Finding success with edge deployments.md
new file mode 100644
index 0000000000..abc1d7dd0c
--- /dev/null
+++ b/sources/talk/20190430 Measuring the edge- Finding success with edge deployments.md
@@ -0,0 +1,73 @@
+[#]: collector: (lujun9972)
+[#]: translator: ( )
+[#]: reviewer: ( )
+[#]: publisher: ( )
+[#]: url: ( )
+[#]: subject: (Measuring the edge: Finding success with edge deployments)
+[#]: via: (https://www.networkworld.com/article/3391570/measuring-the-edge-finding-success-with-edge-deployments.html#tk.rss_all)
+[#]: author: (Anne Taylor https://www.networkworld.com/author/Anne-Taylor/)
+
+Measuring the edge: Finding success with edge deployments
+======
+To make the most of edge computing investments, it’s important to first understand objectives and expectations.
+![iStock][1]
+
+Edge computing deployments are well underway as companies seek to better process the wealth of data being generated, for example, by Internet of Things (IoT) devices.
+
+So, what are the results? Plus, how can you ensure success with your own edge projects?
+
+**Measurements of success**
+
+The [use cases for edge computing deployments][2] vary widely, as do the business drivers and, ultimately, the benefits.
+
+Whether they’re seeking improved network or application performance, real-time data analytics, a better customer experience, or other efficiencies, enterprises are accomplishing their goals. Based on two surveys — one by [_Automation World_][3] and another by [Futurum Research][4] — respondents have reported:
+
+ * Decreased network downtime
+ * Increased productivity
+ * Increased profitability/reduced costs
+ * Improved business processes
+
+
+
+Basically, success metrics can be bucketed into two categories: direct value propositions and cost reductions. In the former, companies are seeking results that measure revenue generation — such as improved digital experiences with customers and users. In the latter, metrics that prove the value of digitizing processes — like speed, quality, and efficacy — will demonstrate success with edge deployments.
+
+**Goalposts for success with edge**
+
+Edge computing deployments are underway. But before diving in, understand what’s driving these projects.
+
+According to the Futurum Research, 29% of respondents are currently investing in edge infrastructure, and 62% expect to adopt within the year. For these companies, the driving force has been the business, which expects operational efficiencies from these investments. Beyond that, there’s an expectation down the road to better align with IoT strategy.
+
+That being the case, it’s worth considering your business case before diving into edge. Ask: Are you seeking innovation and revenue generation amid digital transformation efforts? Or is your company looking for a low-risk, “test the waters” type of investment in edge?
+
+Next up, what type of edge project makes sense for your environment? Edge data centers fall into three categories: local devices for a specific purpose (e.g., an appliance for security systems or a gateway for cloud-to-premises storage); small local data centers (typically one to 10 racks for storage and processing); and regional data centers (10+ racks for large office spaces).
+
+Then, think about these best practices before talking with vendors:
+
+ * Management: Especially for unmanned edge data centers, remote management is critical. You’ll need predictive alerts and a service contract that enables IT to be just as resilient as a regular data center.
+ * Security:Much of today’s conversation has been around data security. That starts with physical protection. Too many data breaches — including theft and employee error — are caused by physical access to IT assets.
+ * Standardization: There is no need to reinvent the wheel when it comes to edge data center deployments. Using standard components makes it easier for the internal IT team to deploy, manage, and maintain.
+
+
+
+Finally, consider the ecosystem. The end-to-end nature of edge requires not just technology integration, but also that all third parties work well together. A good ecosystem connects customers, partners, and vendors.
+
+Get further information to kickstart your edge computing environment at [APC.com][5].
+
+--------------------------------------------------------------------------------
+
+via: https://www.networkworld.com/article/3391570/measuring-the-edge-finding-success-with-edge-deployments.html#tk.rss_all
+
+作者:[Anne Taylor][a]
+选题:[lujun9972][b]
+译者:[译者ID](https://github.com/译者ID)
+校对:[校对者ID](https://github.com/校对者ID)
+
+本文由 [LCTT](https://github.com/LCTT/TranslateProject) 原创编译,[Linux中国](https://linux.cn/) 荣誉推出
+
+[a]: https://www.networkworld.com/author/Anne-Taylor/
+[b]: https://github.com/lujun9972
+[1]: https://images.idgesg.net/images/article/2019/04/istock-912928582-100795093-large.jpg
+[2]: https://www.networkworld.com/article/3391016/edge-computing-is-in-most-industries-future.html
+[3]: https://www.automationworld.com/article/technologies/cloud-computing/its-not-edge-vs-cloud-its-both
+[4]: https://futurumresearch.com/edge-computing-from-edge-to-enterprise/
+[5]: https://www.apc.com/us/en/solutions/business-solutions/edge-computing.jsp
diff --git a/sources/talk/20190501 Vapor IO provides direct, high-speed connections from the edge to AWS.md b/sources/talk/20190501 Vapor IO provides direct, high-speed connections from the edge to AWS.md
new file mode 100644
index 0000000000..0ddef36770
--- /dev/null
+++ b/sources/talk/20190501 Vapor IO provides direct, high-speed connections from the edge to AWS.md
@@ -0,0 +1,69 @@
+[#]: collector: (lujun9972)
+[#]: translator: ( )
+[#]: reviewer: ( )
+[#]: publisher: ( )
+[#]: url: ( )
+[#]: subject: (Vapor IO provides direct, high-speed connections from the edge to AWS)
+[#]: via: (https://www.networkworld.com/article/3391922/vapor-io-provides-direct-high-speed-connections-from-the-edge-to-aws.html#tk.rss_all)
+[#]: author: (Andy Patrizio https://www.networkworld.com/author/Andy-Patrizio/)
+
+Vapor IO provides direct, high-speed connections from the edge to AWS
+======
+With a direct fiber line, latency between the edge and the cloud can be dramatically reduced.
+![Vapor IO][1]
+
+Edge computing startup Vapor IO now offers a direct connection between its edge containers to Amazon Web Services (AWS) via a high-speed fiber network link.
+
+The company said that connection between its Kinetic Edge containers and AWS will be provided by Crown Castle's Cloud Connect fiber network, which uses Amazon Direct Connect Services. This would help reduce network latency by essentially drawing a straight fiber line from Vapor IO's edge computing data centers to Amazon's cloud computing data centers.
+
+“When combined with Crown Castle’s high-speed Cloud Connect fiber, the Kinetic Edge lets AWS developers build applications that span the entire continuum from core to edge. By enabling new classes of applications at the edge, we make it possible for any AWS developer to unlock the next generation of real-time, innovative use cases,” wrote Matt Trifiro, chief marketing officer of Vapor IO, in a [blog post][2].
+
+**[ Read also:[What is edge computing and how it’s changing the network][3] ]**
+
+Vapor IO clams that the connection will lower latency by as much as 75%. “Connecting workloads and data at the Kinetic Edge with workloads and data in centralized AWS data centers makes it possible to build edge applications that leverage the full power of AWS,” wrote Trifiro.
+
+Developers building applications at the Kinetic Edge will have access to the full suite of AWS cloud computing services, including Amazon Simple Storage Service (Amazon S3), Amazon Elastic Cloud Compute (Amazon EC2), Amazon Virtual Private Cloud (Amazon VPC), and Amazon Relational Database Service (Amazon RDS).
+
+Crown Castle is the largest provider of shared communications infrastructure in the U.S., with 40,000 cell towers and 60,000 miles of fiber, offering 1Gbps to 10Gbps private fiber connectivity between the Kinetic Edge and AWS.
+
+AWS Direct Connect is a essentially a private connection between Amazon's AWS customers and their the AWS data centers, so customers don’t have to rout their traffic over the public internet and compete with Netflix and YouTube, for example, for bandwidth.
+
+### How edge computing works
+
+The structure of [edge computing][3] is the reverse of the standard internet design. Rather than sending all the data up to central servers, as much processing as possible is done at the edge. This is to reduce the sheer volume of data coming upstream and thus reduce latency.
+
+With things like smart cars, even if 95% of data is eliminated that remaining, 5% can still be a lot, so moving it fast is essential. Vapor IO said it will shuttle workloads to Amazon’s USEAST and USWEST data centers, depending on location.
+
+This shows how the edge is up-ending the traditional internet design and moving more computing outside the traditional data center, although a connection upstream is still important because it allows for rapid movement of necessary data from the edge to the cloud, where it can be stored or processed.
+
+**More about edge networking:**
+
+ * [How edge networking and IoT will reshape data centers][4]
+ * [Edge computing best practices][5]
+ * [How edge computing can help secure the IoT][6]
+
+
+
+Join the Network World communities on [Facebook][7] and [LinkedIn][8] to comment on topics that are top of mind.
+
+--------------------------------------------------------------------------------
+
+via: https://www.networkworld.com/article/3391922/vapor-io-provides-direct-high-speed-connections-from-the-edge-to-aws.html#tk.rss_all
+
+作者:[Andy Patrizio][a]
+选题:[lujun9972][b]
+译者:[译者ID](https://github.com/译者ID)
+校对:[校对者ID](https://github.com/校对者ID)
+
+本文由 [LCTT](https://github.com/LCTT/TranslateProject) 原创编译,[Linux中国](https://linux.cn/) 荣誉推出
+
+[a]: https://www.networkworld.com/author/Andy-Patrizio/
+[b]: https://github.com/lujun9972
+[1]: https://images.idgesg.net/images/article/2018/09/vapor-io-kinetic-edge-data-center-100771510-large.jpg
+[2]: https://www.vapor.io/powering-amazon-web-services-at-the-kinetic-edge/
+[3]: https://www.networkworld.com/article/3224893/what-is-edge-computing-and-how-it-s-changing-the-network.html
+[4]: https://www.networkworld.com/article/3291790/data-center/how-edge-networking-and-iot-will-reshape-data-centers.html
+[5]: https://www.networkworld.com/article/3331978/lan-wan/edge-computing-best-practices.html
+[6]: https://www.networkworld.com/article/3331905/internet-of-things/how-edge-computing-can-help-secure-the-iot.html
+[7]: https://www.facebook.com/NetworkWorld/
+[8]: https://www.linkedin.com/company/network-world
diff --git a/sources/talk/20190501 Yet another killer cloud quarter puts pressure on data centers.md b/sources/talk/20190501 Yet another killer cloud quarter puts pressure on data centers.md
new file mode 100644
index 0000000000..d65fe448b4
--- /dev/null
+++ b/sources/talk/20190501 Yet another killer cloud quarter puts pressure on data centers.md
@@ -0,0 +1,92 @@
+[#]: collector: (lujun9972)
+[#]: translator: ( )
+[#]: reviewer: ( )
+[#]: publisher: ( )
+[#]: url: ( )
+[#]: subject: (Yet another killer cloud quarter puts pressure on data centers)
+[#]: via: (https://www.networkworld.com/article/3391465/another-strong-cloud-computing-quarter-puts-pressure-on-data-centers.html#tk.rss_all)
+[#]: author: (Fredric Paul https://www.networkworld.com/author/Fredric-Paul/)
+
+Yet another killer cloud quarter puts pressure on data centers
+======
+Continued strong growth from Amazon Web Services, Microsoft Azure, and Google Cloud Platform signals even more enterprises are moving to the cloud.
+![Getty Images][1]
+
+You’d almost think I’d get tired of [writing this story over and over and over][2]… but the ongoing growth of cloud computing is too big a trend to ignore.
+
+Critically, the impressive growth numbers of the three leading cloud infrastructure providers—Amazon Web Services (AWS), Microsoft Azure, and Google Cloud Platform—doesn’t occur in a vacuum. It’s not just about new workloads being run in the cloud; it’s also about more and more enterprises moving existing workloads to the cloud from on-premises data centers.
+
+**[ Also read:[Is the cloud already killing the enterprise data center?][3] ]**
+
+To put these trends in perspective, let’s take a look at the results for all three vendors.
+
+### AWS keeps on trucking
+
+AWS remains by far the dominant player in the cloud infrastructure market, with a massive [$7.7 billion in quarterly sales][4] (an annual run rate of a whopping $30.8 billion). Even more remarkable, somehow AWS continues to grow revenue by almost 42% year over year. Oh, and that kind of growth is not just unique _this_ quarter; the unit has topped 40% revenue growth _every_ quarter since the beginning of 2017. (To be fair, the first quarter of 2018 saw an amazing 49% revenue growth.)
+
+And unlike many fast-growing tech companies, that incredible expansion isn’t being fueled by equally impressive losses. AWS earned a healthy $2.2 billion operating profit in the quarter, up 59% from the same period last year. One reason? [The company told analysts][5] it made big data center investments in 2016 and 2017, so it hasn’t had to do so more recently (it expects to boost spending on data centers later this year). The company [reportedly][6] described AWS revenue growth as “lumpy,” but it seems to me that the numbers merely vary between huge and even bigger.
+
+### Microsoft Azure grows even faster than AWS
+
+Sure, 41% growth is good, but [Microsoft’s quarterly Azure revenue][7] almost doubled that, jumping 73% year over year (fairly consistent with the previous—also stellar—quarter), helping the company exceed estimates for both sales and revenue and sparking a brief shining moment of a $1 billion valuation for the company. Microsoft doesn’t break out Azure’s sales and revenue, but [the commercial cloud business, which includes Azure as well as other cloud businesses, grew 41% in the quarter to $9.6 billion][8].
+
+It’s impossible to tell exactly how big Azure is, but it appears to be growing faster than AWS, though off a much smaller base. While some analysts reportedly say Azure is growing faster than AWS was at a similar stage in its development, that may not bear much significance because the addressable cloud market is now far larger than it used be.
+
+According to [the New York Times][9], like AWS, Microsoft is also now reaping the benefits of heavy investments in new data centers around the world. And the Times credits Microsoft with “particular success” in [hybrid cloud installations][10], helping ease concerns among some slow-to-change enterprise about full-scale cloud adoption.
+
+**[ Also read:[Why hybrid cloud will turn out to be a transition strategy][11] ]**
+
+### Can Google Cloud Platform keep up?
+
+Even as the [overall quarterly numbers for Alphabet][12]—Google’s parent company—didn’t meet analysts’ revenue expectations (which sent the stock tumbling), Google Cloud Platform seems to have continued its strong growth. Alphabet doesn’t break out its cloud unit, but sales in Alphabet’s “Other Revenue” category—which includes cloud computing along with hardware—jumped 25% compared to the same period last year, hitting $5.4 billion.
+
+More telling, perhaps, Alphabet Chief Financial Officer Ruth Porat [reportedly][13] told analysts that "Google Cloud Platform remains one of the fastest growing businesses in Alphabet." [Porat also mentioned][14] that hiring in the cloud unit was so aggressive that it drove a 20% jump in Alphabet’s operating expenses!
+
+### Companies keep going cloud
+
+But the raw numbers tell only part of the story. All that growth means existing customers are spending more, but also that ever-increasing numbers of enterprises are abandoning their hassle and expense of running their data centers in favor of buying what they need from the cloud.
+
+**[ Also read:[Large enterprises abandon data centers for the cloud][15] ]**
+
+The New York Times quotes Amy Hood, Microsoft’s chief financial officer, explaining that, “You don’t really get revenue growth unless you have a usage growth, so this is customers deploying and using Azure.” And the Times notes that Microsoft has signed big deals with companies such as [Walgreens Boots Alliance][16] that combined Azure with other Microsoft cloud-based services.
+
+This growth is true in existing markets, and also includes new markets. For example, AWS just opened new regions in [Indonesia][17] and [Hong Kong][18].
+
+**[ Now read:[After virtualization and cloud, what's left on premises?][19] ]**
+
+Join the Network World communities on [Facebook][20] and [LinkedIn][21] to comment on topics that are top of mind.
+
+--------------------------------------------------------------------------------
+
+via: https://www.networkworld.com/article/3391465/another-strong-cloud-computing-quarter-puts-pressure-on-data-centers.html#tk.rss_all
+
+作者:[Fredric Paul][a]
+选题:[lujun9972][b]
+译者:[译者ID](https://github.com/译者ID)
+校对:[校对者ID](https://github.com/校对者ID)
+
+本文由 [LCTT](https://github.com/LCTT/TranslateProject) 原创编译,[Linux中国](https://linux.cn/) 荣誉推出
+
+[a]: https://www.networkworld.com/author/Fredric-Paul/
+[b]: https://github.com/lujun9972
+[1]: https://images.idgesg.net/images/article/2019/02/cloud_comput_connect_blue-100787048-large.jpg
+[2]: https://www.networkworld.com/article/3292935/cloud-computing-just-had-another-kick-ass-quarter.html
+[3]: https://www.networkworld.com/article/3268384/is-the-cloud-already-killing-the-enterprise-data-center.html
+[4]: https://www.latimes.com/business/la-fi-amazon-earnings-cloud-computing-aws-20190425-story.html
+[5]: https://www.businessinsider.com/amazon-q1-2019-earnings-aws-advertising-retail-prime-2019-4
+[6]: https://www.computerweekly.com/news/252462310/Amazon-cautions-against-reading-too-much-into-slowdown-in-AWS-revenue-growth-rate
+[7]: https://www.microsoft.com/en-us/Investor/earnings/FY-2019-Q3/press-release-webcast
+[8]: https://www.cnbc.com/2019/04/24/microsoft-q3-2019-earnings.html
+[9]: https://www.nytimes.com/2019/04/24/technology/microsoft-earnings.html
+[10]: https://www.networkworld.com/article/3268448/what-is-hybrid-cloud-really-and-whats-the-best-strategy.html
+[11]: https://www.networkworld.com/article/3238466/why-hybrid-cloud-will-turn-out-to-be-a-transition-strategy.html
+[12]: https://abc.xyz/investor/static/pdf/2019Q1_alphabet_earnings_release.pdf?cache=8ac2b86
+[13]: https://www.forbes.com/sites/jilliandonfro/2019/04/29/google-alphabet-q1-earnings-2019/#52f5c8c733be
+[14]: https://www.youtube.com/watch?v=31_KHdse_0Y
+[15]: https://www.networkworld.com/article/3240587/large-enterprises-abandon-data-centers-for-the-cloud.html
+[16]: https://www.walgreensbootsalliance.com
+[17]: https://www.businesswire.com/news/home/20190403005931/en/AWS-Open-New-Region-Indonesia
+[18]: https://www.apnews.com/Business%20Wire/57eaf4cb603e46e6b05b634d9751699b
+[19]: https://https//www.networkworld.com/article/3232626/virtualization/extreme-virtualization-impact-on-enterprises.html
+[20]: https://www.facebook.com/NetworkWorld/
+[21]: https://www.linkedin.com/company/network-world
diff --git a/sources/talk/20190502 Revolutionary data compression technique could slash compute costs.md b/sources/talk/20190502 Revolutionary data compression technique could slash compute costs.md
new file mode 100644
index 0000000000..00316946f6
--- /dev/null
+++ b/sources/talk/20190502 Revolutionary data compression technique could slash compute costs.md
@@ -0,0 +1,65 @@
+[#]: collector: (lujun9972)
+[#]: translator: ( )
+[#]: reviewer: ( )
+[#]: publisher: ( )
+[#]: url: ( )
+[#]: subject: (Revolutionary data compression technique could slash compute costs)
+[#]: via: (https://www.networkworld.com/article/3392716/revolutionary-data-compression-technique-could-slash-compute-costs.html#tk.rss_all)
+[#]: author: (Patrick Nelson https://www.networkworld.com/author/Patrick-Nelson/)
+
+Revolutionary data compression technique could slash compute costs
+======
+A new form of data compression, called Zippads, will create faster computer programs that could drastically lower the costs of computing.
+![Kevin Stanchfield \(CC BY 2.0\)][1]
+
+There’s a major problem with today’s money-saving memory compression used for storing more data in less space. The issue is that computers store and run memory in predetermined blocks, yet many modern programs function and play out in variable chunks.
+
+The way it’s currently done is actually, highly inefficient. That’s because the compressed programs, which use objects rather than evenly configured slabs of data, don’t match the space used to store and run them, explain scientists working on a revolutionary new compression system called Zippads.
+
+The answer, they say—and something that if it works would drastically reduce those inefficiencies, speed things up, and importantly, reduce compute costs—is to compress the varied objects and not the cache lines, as is the case now. Cache lines are fixed-size blocks of memory that are transferred to memory cache.
+
+**[ Read also:[How to deal with backup when you switch to hyperconverged infrastructure][2] ]**
+
+“Objects, not cache lines, are the natural unit of compression,” writes Po-An Tsai and Daniel Sanchez in their MIT Computer Science and Artificial Intelligence Laboratory (CSAIL) [paper][3] (pdf).
+
+They say object-based programs — of the kind used now everyday, such as Python — should be compressed based on their programmed object size, not on some fixed value created by traditional or even state-of-the art cached methods.
+
+The alternative, too, isn’t to recklessly abandon object-oriented programming just because it’s inefficient at using compression. One must adapt compression to that now common object-using code.
+
+The scientists claim their new system can increase the compression ratio 1.63 times and improve performance by 17%. It’s the “first compressed memory hierarchy designed for object-based applications,” they say.
+
+### The benefits of compression
+
+Compression is a favored technique for making computers more efficient. The main advantage over simply adding more memory is that costs are lowered significantly—you don’t need to add increasing physical main memory hardware because you’re cramming more data into existing.
+
+However, to date, hardware memory compression has been best suited to more old-school large blocks of data, not the “random, fine-grained memory accesses,” the team explains. It’s not great at accessing small pieces of data, such as words, for example.
+
+### How the Zippads compression system works
+
+In Zippads, as the new system is called, stored object hierarchical levels (called “pads”) are located on-chip and are directly accessed. The different levels (pads) have changing speed grades, with newly referenced objects being placed in the fastest pad. As a pad fills up, it begins the process of evicting older, not-so-active objects and ultimately recycles the unused code that is taking up desirable fast space and isn’t being used. Cleverly, at the fast level, the code parts aren’t even compressed, but as they prove their non-usefulness they get kicked down to compressed, slow-to-access, lower-importance pads—and are brought back up as necessary.
+
+Zippads would “see computers that can run much faster or can run many more apps at the same speeds,” an[ MIT News][4] article says. “Each application consumes less memory, it runs faster, so a device can support more applications within its allotted memory.” Bandwidth is freed up, in other words.
+
+“All computer systems would benefit from this,” Sanchez, a professor of computer science and electrical engineering, says in the article. “Programs become faster because they stop being bottlenecked by memory bandwidth.”
+
+Join the Network World communities on [Facebook][5] and [LinkedIn][6] to comment on topics that are top of mind.
+
+--------------------------------------------------------------------------------
+
+via: https://www.networkworld.com/article/3392716/revolutionary-data-compression-technique-could-slash-compute-costs.html#tk.rss_all
+
+作者:[Patrick Nelson][a]
+选题:[lujun9972][b]
+译者:[译者ID](https://github.com/译者ID)
+校对:[校对者ID](https://github.com/校对者ID)
+
+本文由 [LCTT](https://github.com/LCTT/TranslateProject) 原创编译,[Linux中国](https://linux.cn/) 荣誉推出
+
+[a]: https://www.networkworld.com/author/Patrick-Nelson/
+[b]: https://github.com/lujun9972
+[1]: https://images.idgesg.net/images/article/2019/02/memory-100787327-large.jpg
+[2]: https://www.networkworld.com/article/3389396/how-to-deal-with-backup-when-you-switch-to-hyperconverged-infrastructure.html
+[3]: http://people.csail.mit.edu/poantsai/papers/2019.zippads.asplos.pdf
+[4]: http://news.mit.edu/2019/hardware-data-compression-0416
+[5]: https://www.facebook.com/NetworkWorld/
+[6]: https://www.linkedin.com/company/network-world
diff --git a/sources/talk/20190506 Cisco boosts SD-WAN with multicloud-to-branch access system.md b/sources/talk/20190506 Cisco boosts SD-WAN with multicloud-to-branch access system.md
new file mode 100644
index 0000000000..c676e5effb
--- /dev/null
+++ b/sources/talk/20190506 Cisco boosts SD-WAN with multicloud-to-branch access system.md
@@ -0,0 +1,89 @@
+[#]: collector: (lujun9972)
+[#]: translator: ( )
+[#]: reviewer: ( )
+[#]: publisher: ( )
+[#]: url: ( )
+[#]: subject: (Cisco boosts SD-WAN with multicloud-to-branch access system)
+[#]: via: (https://www.networkworld.com/article/3393232/cisco-boosts-sd-wan-with-multicloud-to-branch-access-system.html#tk.rss_all)
+[#]: author: (Michael Cooney https://www.networkworld.com/author/Michael-Cooney/)
+
+Cisco boosts SD-WAN with multicloud-to-branch access system
+======
+Cisco's SD-WAN Cloud onRamp for CoLocation can tie branch offices to private data centers in regional corporate headquarters via colocation facilities for shorter, faster, possibly more secure connections.
+![istock][1]
+
+Cisco is looking to give traditional or legacy wide-area network users another reason to move to the [software-defined WAN world][2].
+
+The company has rolled out an integrated hardware/software package called SD-WAN Cloud onRamp for CoLocation that lets customers tie distributed multicloud applications back to a local branch office or local private data center. The idea is that a cloud-to-branch link would be shorter, faster and possibly more secure that tying cloud-based applications directly all the way to the data center.
+
+**More about SD-WAN**
+
+ * [How to buy SD-WAN technology: Key questions to consider when selecting a supplier][3]
+ * [How to pick an off-site data-backup method][4]
+ * [SD-Branch: What it is and why you’ll need it][5]
+ * [What are the options for security SD-WAN?][6]
+
+
+
+“With Cisco SD-WAN Cloud onRamp for CoLocation operating regionally, connections from colocation facilities to branches are set up and configured according to traffic loads (such as video vs web browsing vs email) SLAs (requirements for low latency/jitter), and Quality of Experience for optimizing cloud application performance,” wrote Anand Oswal, senior vice president of engineering, in Cisco’s Enterprise Networking Business in a [blog about the new service][7].
+
+According to Oswal, each branch or private data center is equipped with a network interface that provides a secure tunnel to the regional colocation facility. In turn, the Cloud onRamp for CoLocation establishes secure tunnels to SaaS application platforms, multi-cloud platform services, and enterprise data centers, he stated.
+
+Traffic is securely routed through the Cloud onRamp for CoLocation stack which includes security features such as application-aware firewalls, URL-filtering, intrusion detection/prevention, DNS-layer security, and Advanced Malware Protection (AMP) Threat Grid, as well as other network services such as load-balancing and Wide Area Application Services, Oswal wrote.
+
+A typical use case for the package is an enterprise that has dozens of distributed branch offices, clustered around major cities, spread over several countries. The goal is to tie each branch to enterprise data center databases, SaaS applications, and multi-cloud services while meeting service level agreements and application quality of experience, Oswal stated.
+
+“With virtualized Cisco SD-WAN running on regional colocation centers, the branch workforce has access to applications and data residing in AWS, Azure, and Google cloud platforms as well as SaaS providers such as Microsoft 365 and Salesforce—transparently and securely,” Oswal said. “Distributing SD-WAN features over a regional architecture also brings processing power closer to where data is being generated—at the cloud edge.”
+
+The idea is that paths to designated SaaS applications will be monitored continuously for performance, and the application traffic will be dynamically routed to the best-performing path, without requiring human intervention, Oswal stated.
+
+For a typical configuration, a region covering a target city uses a colocation IaaS provider that hosts the Cisco Cloud onRamp for CoLocation, which includes:
+
+ * Cisco vManage software that lets customers manage applications and provision, monitor and troubleshooting the WAN.
+ * [Cisco Cloud Services Platform (CSP) 5000][8] The systems are x86 Linux Kernel-based Virtual Machine (KVM) software and hardware platforms for the data center, regional hub, and colocation Network Functions Virtualization (NFV). The platforms let enterprise IT teams or service providers deploy any Cisco or third-party network virtual service with Cisco’s [Network Services Orchestrator (NSO)][9] or any other northbound management and orchestration system.
+ * The Cisco [Catalyst 9500 Series][10] aggregation switches. Based on an x86 CPU, the Catalyst 9500 Series is Cisco’s lead purpose-built fixed core and aggregation enterprise switching platform, built for security, IoT, and cloud. The switches come with a 4-core x86, 2.4-GHz CPU, 16-GB DDR4 memory, and 16-GB internal storage.
+
+
+
+If the features of the package sound familiar, that’s because the [Cloud onRamp for CoLocation][11] package is the second generation of a similar SD-WAN package offered by Viptela which Cisco [bought in 2017][12].
+
+SD-WAN's driving principle is to simplify the way big companies turn up new links to branch offices, better manage the way those links are utilized – for data, voice or video – and potentially save money in the process.
+
+It's a profoundly hot market with tons of players including [Cisco][13], VMware, Silver Peak, Riverbed, Aryaka, Fortinet, Nokia and Versa. IDC says the SD-WAN infrastructure market will hit $4.5 billion by 2022, growing at a more than 40% yearly clip between now and then.
+
+[SD-WAN][14] lets networks route traffic based on centrally managed roles and rules, no matter what the entry and exit points of the traffic are, and with full security. For example, if a user in a branch office is working in Office365, SD-WAN can route their traffic directly to the closest cloud data center for that app, improving network responsiveness for the user and lowering bandwidth costs for the business.
+
+"SD-WAN has been a promised technology for years, but in 2019 it will be a major driver in how networks are built and re-built," Oswal said a Network World [article][15] earlier this year.
+
+Join the Network World communities on [Facebook][16] and [LinkedIn][17] to comment on topics that are top of mind.
+
+--------------------------------------------------------------------------------
+
+via: https://www.networkworld.com/article/3393232/cisco-boosts-sd-wan-with-multicloud-to-branch-access-system.html#tk.rss_all
+
+作者:[Michael Cooney][a]
+选题:[lujun9972][b]
+译者:[译者ID](https://github.com/译者ID)
+校对:[校对者ID](https://github.com/校对者ID)
+
+本文由 [LCTT](https://github.com/LCTT/TranslateProject) 原创编译,[Linux中国](https://linux.cn/) 荣誉推出
+
+[a]: https://www.networkworld.com/author/Michael-Cooney/
+[b]: https://github.com/lujun9972
+[1]: https://images.idgesg.net/images/article/2018/02/istock-578801262-100750453-large.jpg
+[2]: https://www.networkworld.com/article/3209131/what-sdn-is-and-where-its-going.html
+[3]: https://www.networkworld.com/article/3323407/sd-wan/how-to-buy-sd-wan-technology-key-questions-to-consider-when-selecting-a-supplier.html
+[4]: https://www.networkworld.com/article/3328488/backup-systems-and-services/how-to-pick-an-off-site-data-backup-method.html
+[5]: https://www.networkworld.com/article/3250664/lan-wan/sd-branch-what-it-is-and-why-youll-need-it.html
+[6]: https://www.networkworld.com/article/3285728/sd-wan/what-are-the-options-for-securing-sd-wan.html?nsdr=true
+[7]: https://blogs.cisco.com/enterprise/cisco-sd-wan-cloud-onramp-for-colocation-multicloud
+[8]: https://www.cisco.com/c/en/us/products/collateral/switches/cloud-services-platform-5000/nb-06-csp-5k-data-sheet-cte-en.html#ProductOverview
+[9]: https://www.cisco.com/go/nso
+[10]: https://www.cisco.com/c/en/us/products/collateral/switches/catalyst-9500-series-switches/data_sheet-c78-738978.html
+[11]: https://www.networkworld.com/article/3207751/viptela-cloud-onramp-optimizes-cloud-access.html
+[12]: https://www.networkworld.com/article/3193784/cisco-grabs-up-sd-wan-player-viptela-for-610m.html?nsdr=true
+[13]: https://www.networkworld.com/article/3322937/what-will-be-hot-for-cisco-in-2019.html
+[14]: https://www.networkworld.com/article/3031279/sd-wan/sd-wan-what-it-is-and-why-you-ll-use-it-one-day.html
+[15]: https://www.networkworld.com/article/3332027/cisco-touts-5-technologies-that-will-change-networking-in-2019.html
+[16]: https://www.facebook.com/NetworkWorld/
+[17]: https://www.linkedin.com/company/network-world
diff --git a/sources/talk/20190507 SD-WAN is Critical for IoT.md b/sources/talk/20190507 SD-WAN is Critical for IoT.md
new file mode 100644
index 0000000000..a5867d5afd
--- /dev/null
+++ b/sources/talk/20190507 SD-WAN is Critical for IoT.md
@@ -0,0 +1,74 @@
+[#]: collector: (lujun9972)
+[#]: translator: ( )
+[#]: reviewer: ( )
+[#]: publisher: ( )
+[#]: url: ( )
+[#]: subject: (SD-WAN is Critical for IoT)
+[#]: via: (https://www.networkworld.com/article/3393445/sd-wan-is-critical-for-iot.html#tk.rss_all)
+[#]: author: (Rami Rammaha https://www.networkworld.com/author/Rami-Rammaha/)
+
+SD-WAN is Critical for IoT
+======
+
+![istock][1]
+
+The Internet of Things (IoT) is everywhere and its use is growing fast. IoT is used by local governments to build smart cities. It’s used to build smart businesses. And, consumers are benefitting as it’s built into smart homes and smart cars. Industry analyst first estimates that over 20 billion IoT devices will be connected by 2020. That’s a 2.5x increase from the more than 8 billion connected devices in 2017*.
+
+Manufacturing companies have the highest IoT spend to date of industries while the health care market is experiencing the highest IoT growth. By 2020, 50 percent of IoT spending will be driven by manufacturing, transportation and logistics, and utilities.
+
+IoT growth is being fueled by the promise of analytical data insights that will ultimately yield greater efficiencies and enhanced customer satisfaction. The top use cases driving IoT growth are self-optimizing production, predictive maintenance and automated inventory management.
+
+From a high-level view, the IoT architecture includes sensors that collect and transmit data (i.e. temperature, speed, humidity, video feed, pressure, IR, proximity, etc.) from “things” like cars, trucks, machines, etc. that are connected over the internet. Data collected is then analyzed, translating raw data into actionable information. Businesses can then act on this information. And at more advanced levels, machine learning and AI algorithms learn and adapt to this information and automatically respond at a system level.
+
+IDC estimates that by 2025, over 75 billion IoT devices* will be connected. By that time, nearly a quarter of the world’s projected 163 zettabytes* (163 trillion gigabytes) of data will have been created in real-time, and the vast majority of that data will have been created by IoT devices. This massive amount of data will drive an exponential increase in traffic on the network infrastructure requiring massive scalability. Also, this increasing amount of data will require tremendous processing power to mine it and transform it into actionable intelligence. In parallel, security risks will continue to increase as there will be many more potential entry points onto the network. Lastly, management of the overall infrastructure will require better orchestration of policies as well as the means to streamline on-going operations.
+
+### **How does SD-WAN enable IoT business initiatives?**
+
+There are three key elements that an [SD-WAN][2] platform must include:
+
+ 1. **Visibility** : Real-time visibility into the network is key. It takes the guesswork out of rapid problem resolution, enabling organizations to run more efficiently by accelerating troubleshooting and applying preventive measures. Furthermore, a CIO is able to pull metrics and see bandwidth consumed by any IoT application.
+ 2. **Security** : IoT traffic must be isolated from other application traffic. IT must prevent – or at least reduce – the possible attack surface that may be exposed to IoT device traffic. Also, the network must continue delivering other application traffic in the event of a melt down on a WAN link caused by a DDoS attack.
+ 3. **Agility** : With the increased number of connected devices, applications and users, a comprehensive, intelligent and centralized orchestration approach that continuously adapts to deliver the best experience to the business and users is critical to success.
+
+
+
+### Key Silver Peak EdgeConnect SD-WAN capabilities for IoT
+
+1\. Silver Peak has an [embedded real-time visibility engine][3] allowing IT to gain complete observability into the performance attributes of the network and applications in real-time. The [EdgeConnect][4] SD-WAN appliances deployed in branch offices send information to the centralized [Unity Orchestrator™][5]. Orchestrator collects the data and presents it in a comprehensive management dashboard via customizable widgets. These widgets provide a wealth of operational data including a health heatmap for every SD-WAN appliance deployed, flow counts, active tunnels, logical topologies, top talkers, alarms, bandwidth consumed by each application and location, latency and jitter and much more. Furthermore, the platform maintains weeks’ worth of data with context allowing IT to playback and see what has transpired at a specific time and location, similar to a DVR.
+
+![Click to read Solution Brief][6]
+
+2\. The second set of key capabilities center around security and end-to-end zone-based segmentation. An IoT traffic zone may be created on the LAN or branch side. IoT traffic is then mapped all the way across the WAN to the data center or cloud where the data will be processed. Zone-based segmentation is accomplished in a simplified and automated way within the Orchestrator GUI. In cases where further traffic inspection is required, IT can simply service chain to another security service. There are several key benefits realized by this approach. IT can easily and quickly apply segmentation policies; segmentation mitigates the attack surface; and IT can save on additional security investments.
+
+![***Click to read Solution Brief ***][7]
+
+3\. EdgeConnect employs machine learning at the global level where with internet sensors and third-party sensors feed into the cloud portal software. The software tracks the geolocation of all IP addresses and IP reputation, distributing signals down to the Unity Orchestrator running in each individual customer’s enterprise. In turn, it is speaking to the edge devices sitting in the branch offices. There, distributed learning is done by looking at the first packet, making an inference based on the first packet what the application is. So, if seeing that 100 times now, every time packets come from that particular IP address and turns out to be an IoT, we can make an inference that IP belongs to IoT application. In parallel, we’re using a mix of traditional techniques to validate the identification of the application. All this combined other multi-level intelligence enables simple and automated policy orchestration across a large number of devices and applications.
+
+![***Click to read Solution Brief ***][8]
+
+SD-WAN plays a foundational role as businesses continue to embrace IoT, but choosing the right SD-WAN platform is even more critical to ensuring businesses are ultimately able to fully optimize their operations.
+
+* Source: [IDC][9]
+
+--------------------------------------------------------------------------------
+
+via: https://www.networkworld.com/article/3393445/sd-wan-is-critical-for-iot.html#tk.rss_all
+
+作者:[Rami Rammaha][a]
+选题:[lujun9972][b]
+译者:[译者ID](https://github.com/译者ID)
+校对:[校对者ID](https://github.com/校对者ID)
+
+本文由 [LCTT](https://github.com/LCTT/TranslateProject) 原创编译,[Linux中国](https://linux.cn/) 荣誉推出
+
+[a]: https://www.networkworld.com/author/Rami-Rammaha/
+[b]: https://github.com/lujun9972
+[1]: https://images.idgesg.net/images/article/2019/05/istock-1019172426-100795551-large.jpg
+[2]: https://www.silver-peak.com/sd-wan/sd-wan-explained
+[3]: https://www.silver-peak.com/resource-center/simplify-sd-wan-operations-greater-visibility
+[4]: https://www.silver-peak.com/products/unity-edge-connect
+[5]: https://www.silver-peak.com/products/unity-orchestrator
+[6]: https://images.idgesg.net/images/article/2019/05/1_simplify-100795554-large.jpg
+[7]: https://images.idgesg.net/images/article/2019/05/2_centralize-100795555-large.jpg
+[8]: https://images.idgesg.net/images/article/2019/05/3_increase-100795558-large.jpg
+[9]: https://www.information-age.com/data-forecast-grow-10-fold-2025-123465538/
diff --git a/sources/talk/20190507 Server shipments to pick up in the second half of 2019.md b/sources/talk/20190507 Server shipments to pick up in the second half of 2019.md
new file mode 100644
index 0000000000..8169c594ef
--- /dev/null
+++ b/sources/talk/20190507 Server shipments to pick up in the second half of 2019.md
@@ -0,0 +1,56 @@
+[#]: collector: (lujun9972)
+[#]: translator: ( )
+[#]: reviewer: ( )
+[#]: publisher: ( )
+[#]: url: ( )
+[#]: subject: (Server shipments to pick up in the second half of 2019)
+[#]: via: (https://www.networkworld.com/article/3393167/server-shipments-to-pick-up-in-the-second-half-of-2019.html#tk.rss_all)
+[#]: author: (Andy Patrizio https://www.networkworld.com/author/Andy-Patrizio/)
+
+Server shipments to pick up in the second half of 2019
+======
+Server sales slowed in anticipation of the new Intel Xeon processors, but they are expected to start up again before the end of the year.
+![Thinkstock][1]
+
+Global server shipments are not expected to return to growth momentum until the third quarter or even the fourth quarter of 2019, according to Taiwan-based tech news site DigiTimes, which cited unnamed server supply chain sources. The one bright spot remains cloud providers like Amazon, Google, and Facebook, which continue their buying binge.
+
+Normally I’d be reluctant to cite such a questionable source, but given most of the OEMs and ODMs are based in Taiwan and DigiTimes (the article is behind a paywall so I cannot link) has shown it has connections to them, I’m inclined to believe them.
+
+Quanta Computer chairman Barry Lam told the publication that Quanta's shipments of cloud servers have risen steadily, compared to sharp declines in shipments of enterprise servers. Lam continued that enterprise servers command only 1-2% of the firm's total server shipments.
+
+**[ Also read:[Gartner: IT spending to drop due to falling equipment prices][2] ]**
+
+[Server shipments began to slow down in the first quarter][3] thanks in part to the impending arrival of second-generation Xeon Scalable processors from Intel. And since it takes a while to get parts and qualify them, this quarter won’t be much better.
+
+In its latest quarterly earnings, Intel's data center group (DCG) said sales declined 6% year over year, the first decline of its kind since the first quarter of 2012 and reversing an average growth of over 20% in the past.
+
+[The Osbourne Effect][4] wasn’t the sole reason. An economic slowdown in China and the trade war, which will add significant tariffs to Chinese-made products, are also hampering sales.
+
+DigiTimes says Inventec, Intel's largest server motherboard supplier, expects shipments of enterprise server motherboards to further lose steams for the rest of the year, while sales of data center servers are expected to grow 10-15% on year in 2019.
+
+**[[Get certified as an Apple Technical Coordinator with this seven-part online course from PluralSight.][5] ]**
+
+It went on to say server shipments may concentrate in the second half or even the fourth quarter of the year, while cloud-based data center servers for the cloud giants will remain positive as demand for edge computing, new artificial intelligence (AI) applications, and the proliferation of 5G applications begin in 2020.
+
+Join the Network World communities on [Facebook][6] and [LinkedIn][7] to comment on topics that are top of mind.
+
+--------------------------------------------------------------------------------
+
+via: https://www.networkworld.com/article/3393167/server-shipments-to-pick-up-in-the-second-half-of-2019.html#tk.rss_all
+
+作者:[Andy Patrizio][a]
+选题:[lujun9972][b]
+译者:[译者ID](https://github.com/译者ID)
+校对:[校对者ID](https://github.com/校对者ID)
+
+本文由 [LCTT](https://github.com/LCTT/TranslateProject) 原创编译,[Linux中国](https://linux.cn/) 荣誉推出
+
+[a]: https://www.networkworld.com/author/Andy-Patrizio/
+[b]: https://github.com/lujun9972
+[1]: https://images.techhive.com/images/article/2017/04/2_data_center_servers-100718306-large.jpg
+[2]: https://www.networkworld.com/article/3391062/it-spending-to-drop-due-to-falling-equipment-prices-gartner-predicts.html
+[3]: https://www.networkworld.com/article/3332144/server-sales-projected-to-slow-while-memory-prices-drop.html
+[4]: https://en.wikipedia.org/wiki/Osborne_effect
+[5]: https://pluralsight.pxf.io/c/321564/424552/7490?u=https%3A%2F%2Fwww.pluralsight.com%2Fpaths%2Fapple-certified-technical-trainer-10-11
+[6]: https://www.facebook.com/NetworkWorld/
+[7]: https://www.linkedin.com/company/network-world
diff --git a/sources/talk/20190507 Some IT pros say they have too much data.md b/sources/talk/20190507 Some IT pros say they have too much data.md
new file mode 100644
index 0000000000..a645ae52e9
--- /dev/null
+++ b/sources/talk/20190507 Some IT pros say they have too much data.md
@@ -0,0 +1,66 @@
+[#]: collector: (lujun9972)
+[#]: translator: ( )
+[#]: reviewer: ( )
+[#]: publisher: ( )
+[#]: url: ( )
+[#]: subject: (Some IT pros say they have too much data)
+[#]: via: (https://www.networkworld.com/article/3393205/some-it-pros-say-they-have-too-much-data.html#tk.rss_all)
+[#]: author: (Andy Patrizio https://www.networkworld.com/author/Andy-Patrizio/)
+
+Some IT pros say they have too much data
+======
+IT professionals have too many data sources to count, and they spend a huge amount of time wrestling that data into usable condition, a survey from Ivanti finds.
+![Getty Images][1]
+
+A new survey has found that a growing number of IT professionals have too many data sources to even count, and they are spending more and more time just wrestling that data into usable condition.
+
+Ivanti, an IT asset management firm, [surveyed 400 IT professionals on their data situation][2] and found IT faces numerous challenges when it comes to siloes, data, and implementation. The key takeaway is data overload is starting to overwhelm IT managers and data lakes are turning into data oceans.
+
+**[ Read also:[Understanding mass data fragmentation][3] | Get daily insights [Sign up for Network World newsletters][4] ]**
+
+Among the findings from Ivanti's survey:
+
+ * Fifteen percent of IT professionals say they have too many data sources to count, and 37% of professionals said they have about 11-25 different sources for data.
+ * More than half of IT professionals (51%) report they have to work with their data for days, weeks or more before it's actionable.
+ * Only 10% of respondents said the data they receive is actionable within minutes.
+ * One in three respondents said they have the resources to act on their data, but more than half (52%) said they only sometimes have the resources.
+
+
+
+“It’s clear from the results of this survey that IT professionals are in need of a more unified approach when working across organizational departments and resulting silos,” said Duane Newman, vice president of product management at Ivanti, in a statement.
+
+### The problem with siloed data
+
+The survey found siloed data represents a number of problems and challenges. Three key priorities suffer the most: automation (46%), user productivity and troubleshooting (42%), and customer experience (41%). The survey also found onboarding/offboarding suffers the least (20%) due to siloes, so apparently HR and IT are getting things right.
+
+In terms of what they want from real-time insight, about 70% of IT professionals said their security status was the top priority over other issues. Respondents were least interested in real-time insights around warranty data.
+
+### Data lake method a recipe for disaster
+
+I’ve been immersed in this subject for other publications for some time now. Too many companies are hoovering up data for the sake of collecting it with little clue as to what they will do with it later. One thing you have to say about data warehouses, the schema on write at least forces you to think about what you are collecting and how you might use it because you have to store it away in a usable form.
+
+The new data lake method is schema on read, meaning you filter/clean it when you read it into an application, and that’s just a recipe for disaster. If you are looking at data collected a month or a year ago, do you even know what it all is? Now you have to apply schema to data and may not even remember collecting it.
+
+Too many people think more data is good when it isn’t. You just drown in it. When you reach a point of having too many data sources to count, you’ve gone too far and are not going to get insight. You’re going to get overwhelmed. Collect data you know you can use. Otherwise you are wasting petabytes of disk space.
+
+Join the Network World communities on [Facebook][5] and [LinkedIn][6] to comment on topics that are top of mind.
+
+--------------------------------------------------------------------------------
+
+via: https://www.networkworld.com/article/3393205/some-it-pros-say-they-have-too-much-data.html#tk.rss_all
+
+作者:[Andy Patrizio][a]
+选题:[lujun9972][b]
+译者:[译者ID](https://github.com/译者ID)
+校对:[校对者ID](https://github.com/校对者ID)
+
+本文由 [LCTT](https://github.com/LCTT/TranslateProject) 原创编译,[Linux中国](https://linux.cn/) 荣誉推出
+
+[a]: https://www.networkworld.com/author/Andy-Patrizio/
+[b]: https://github.com/lujun9972
+[1]: https://images.idgesg.net/images/article/2018/03/database_data-center_futuristic-technology-100752012-large.jpg
+[2]: https://www.ivanti.com/blog/survey-it-professionals-data-sources
+[3]: https://www.networkworld.com/article/3262145/lan-wan/customer-reviews-top-remote-access-tools.html#nww-fsb
+[4]: https://www.networkworld.com/newsletters/signup.html#nww-fsb
+[5]: https://www.facebook.com/NetworkWorld/
+[6]: https://www.linkedin.com/company/network-world
diff --git a/sources/talk/20190509 Cisco adds AMP to SD-WAN for ISR-ASR routers.md b/sources/talk/20190509 Cisco adds AMP to SD-WAN for ISR-ASR routers.md
new file mode 100644
index 0000000000..a5ec6212d8
--- /dev/null
+++ b/sources/talk/20190509 Cisco adds AMP to SD-WAN for ISR-ASR routers.md
@@ -0,0 +1,74 @@
+[#]: collector: (lujun9972)
+[#]: translator: ( )
+[#]: reviewer: ( )
+[#]: publisher: ( )
+[#]: url: ( )
+[#]: subject: (Cisco adds AMP to SD-WAN for ISR/ASR routers)
+[#]: via: (https://www.networkworld.com/article/3394597/cisco-adds-amp-to-sd-wan-for-israsr-routers.html#tk.rss_all)
+[#]: author: (Michael Cooney https://www.networkworld.com/author/Michael-Cooney/)
+
+Cisco adds AMP to SD-WAN for ISR/ASR routers
+======
+Cisco SD-WAN now sports Advanced Malware Protection on its popular edge routers, adding to their routing, segmentation, security, policy and orchestration capabilities.
+![vuk8691 / Getty Images][1]
+
+Cisco has added support for Advanced Malware Protection (AMP) to its million-plus ISR/ASR edge routers, in an effort to [reinforce branch and core network malware protection][2] at across the SD-WAN.
+
+Cisco last year added its Viptela SD-WAN technology to the IOS XE version 16.9.1 software that runs its core ISR/ASR routers such as the ISR models 1000, 4000 and ASR 5000, in use by organizations worldwide. Cisco bought Viptela in 2017.
+
+**More about SD-WAN**
+
+ * [How to buy SD-WAN technology: Key questions to consider when selecting a supplier][3]
+ * [How to pick an off-site data-backup method][4]
+ * [SD-Branch: What it is and why you’ll need it][5]
+ * [What are the options for security SD-WAN?][6]
+
+
+
+The release of Cisco IOS XE offered an instant upgrade path for creating cloud-controlled SD-WAN fabrics to connect distributed offices, people, devices and applications operating on the installed base, Cisco said. At the time Cisco said that Cisco SD-WAN on edge routers builds a secure virtual IP fabric by combining routing, segmentation, security, policy and orchestration.
+
+With the recent release of [IOS-XE SD-WAN 16.11][7], Cisco has brought AMP and other enhancements to its SD-WAN.
+
+“Together with Cisco Talos [Cisco’s security-intelligence arm], AMP imbues your SD-WAN branch, core and campuses locations with threat intelligence from millions of worldwide users, honeypots, sandboxes, and extensive industry partnerships,” wrote Cisco’s Patrick Vitalone a product marketing manager in a [blog][8] about the security portion of the new software. “In total, AMP identifies more than 1.1 million unique malware samples a day." When AMP in Cisco SD-WAN spots malicious behavior it automatically blocks it, he wrote.
+
+The idea is to use integrated preventative engines, exploit prevention and intelligent signature-based antivirus to stop malicious attachments and fileless malware before they execute, Vitalone wrote.
+
+AMP support is added to a menu of security features already included in the SD-WAN software including support for URL filtering, [Cisco Umbrella][9] DNS security, Snort Intrusion Prevention, the ability to segment users across the WAN and embedded platform security, including the [Cisco Trust Anchor][10] module.
+
+**[[Prepare to become a Certified Information Security Systems Professional with this comprehensive online course from PluralSight. Now offering a 10-day free trial!][11] ]**
+
+The software also supports [SD-WAN Cloud onRamp for CoLocation][12], which lets customers tie distributed multicloud applications back to a local branch office or local private data center. That way a cloud-to-branch link would be shorter, faster and possibly more secure that tying cloud-based applications directly to the data center.
+
+“The idea that this kind of security technology is now integrated into Cisco’s SD-WAN offering is a critical for Cisco and customers looking to evaluate SD-WAN offerings,” said Lee Doyle, principal analyst at Doyle Research.
+
+IOS-XE SD-WAN 16.11 is available now.
+
+Join the Network World communities on [Facebook][13] and [LinkedIn][14] to comment on topics that are top of mind.
+
+--------------------------------------------------------------------------------
+
+via: https://www.networkworld.com/article/3394597/cisco-adds-amp-to-sd-wan-for-israsr-routers.html#tk.rss_all
+
+作者:[Michael Cooney][a]
+选题:[lujun9972][b]
+译者:[译者ID](https://github.com/译者ID)
+校对:[校对者ID](https://github.com/校对者ID)
+
+本文由 [LCTT](https://github.com/LCTT/TranslateProject) 原创编译,[Linux中国](https://linux.cn/) 荣誉推出
+
+[a]: https://www.networkworld.com/author/Michael-Cooney/
+[b]: https://github.com/lujun9972
+[1]: https://images.idgesg.net/images/article/2018/09/shimizu_island_el_nido_palawan_philippines_by_vuk8691_gettyimages-155385042_1200x800-100773533-large.jpg
+[2]: https://www.networkworld.com/article/3285728/what-are-the-options-for-securing-sd-wan.html
+[3]: https://www.networkworld.com/article/3323407/sd-wan/how-to-buy-sd-wan-technology-key-questions-to-consider-when-selecting-a-supplier.html
+[4]: https://www.networkworld.com/article/3328488/backup-systems-and-services/how-to-pick-an-off-site-data-backup-method.html
+[5]: https://www.networkworld.com/article/3250664/lan-wan/sd-branch-what-it-is-and-why-youll-need-it.html
+[6]: https://www.networkworld.com/article/3285728/sd-wan/what-are-the-options-for-securing-sd-wan.html?nsdr=true
+[7]: https://www.cisco.com/c/en/us/td/docs/routers/sdwan/release/notes/xe-16-11/sd-wan-rel-notes-19-1.html
+[8]: https://blogs.cisco.com/enterprise/enabling-amp-in-cisco-sd-wan
+[9]: https://www.networkworld.com/article/3167837/cisco-umbrella-cloud-service-shapes-security-for-cloud-mobile-resources.html
+[10]: https://www.cisco.com/c/dam/en_us/about/doing_business/trust-center/docs/trustworthy-technologies-datasheet.pdf
+[11]: https://pluralsight.pxf.io/c/321564/424552/7490?u=https%3A%2F%2Fwww.pluralsight.com%2Fpaths%2Fcertified-information-systems-security-professional-cisspr
+[12]: https://www.networkworld.com/article/3393232/cisco-boosts-sd-wan-with-multicloud-to-branch-access-system.html
+[13]: https://www.facebook.com/NetworkWorld/
+[14]: https://www.linkedin.com/company/network-world
diff --git a/sources/talk/20190509 When it comes to uptime, not all cloud providers are created equal.md b/sources/talk/20190509 When it comes to uptime, not all cloud providers are created equal.md
new file mode 100644
index 0000000000..8f9db8a94b
--- /dev/null
+++ b/sources/talk/20190509 When it comes to uptime, not all cloud providers are created equal.md
@@ -0,0 +1,83 @@
+[#]: collector: (lujun9972)
+[#]: translator: ( )
+[#]: reviewer: ( )
+[#]: publisher: ( )
+[#]: url: ( )
+[#]: subject: (When it comes to uptime, not all cloud providers are created equal)
+[#]: via: (https://www.networkworld.com/article/3394341/when-it-comes-to-uptime-not-all-cloud-providers-are-created-equal.html#tk.rss_all)
+[#]: author: (Zeus Kerravala https://www.networkworld.com/author/Zeus-Kerravala/)
+
+When it comes to uptime, not all cloud providers are created equal
+======
+Cloud uptime is critical today, but vendor-provided data can be confusing. Here's an analysis of how AWS, Google Cloud and Microsoft Azure compare.
+![Getty Images][1]
+
+The cloud is not just important; it's mission-critical for many companies. More and more IT and business leaders I talk to look at public cloud as a core component of their digital transformation strategies — using it as part of their hybrid cloud or public cloud implementation.
+
+That raises the bar on cloud reliability, as a cloud outage means important services are not available to the business. If this is a business-critical service, the company may not be able to operate while that key service is offline.
+
+Because of the growing importance of the cloud, it’s critical that buyers have visibility into the reliability number for the cloud providers. The challenge is the cloud providers don't disclose the disruptions in a consistent manner. In fact, some are confusing to the point where it’s difficult to glean any kind of meaningful conclusion.
+
+**[ RELATED:[What IT pros need to know about Azure Stack][2] and [Which cloud performs better, AWS, Azure or Google?][3] | Get regularly scheduled insights: [Sign up for Network World newsletters][4] ]**
+
+### Reported cloud outage times don't always reflect actual downtime
+
+Microsoft Azure and Google Cloud Platform (GCP) both typically provide information on date and time, but only high-level data on the services affected and sparse information on regional impact. The problem with that is it’s difficult to get a sense of overall reliability. For instance, if Azure reports a one-hour outage that impacts five services in three regions, the website might show just a single hour. In actuality, that’s 15 hours of total downtime.
+
+Between Azure, GCP and Amazon Web Services (AWS), [Azure is the most obscure][5], as it provides the least amount of detail. [GCP does a better job of providing detail][6] at the service level but tends to be obscure with regional information. Sometimes it’s very clear as to what services are unavailable, and other times it’s not.
+
+[AWS has the most granular reporting][7], as it shows every service in every region. If an incident occurs that impacts three services, all three of those services would light up red. If those were unavailable for one hour, AWS would record three hours of downtime.
+
+Another inconsistency between the cloud providers is the amount of historical downtime data that is available. At one time, all three of the cloud vendors provided a one-year view into outages. GCP and AWS still do this, but Azure moved to only a [90-day view][5] sometime over the past year.
+
+### Azure has significantly higher downtime than GCP and AWS
+
+The next obvious question is who has the most downtime? To answer that, I worked with a third-party firm that has continually collected downtime information directly from the vendor websites. I have personally reviewed the information and can validate its accuracy. Based on the vendors own reported numbers, from the beginning of 2018 through May 3, 2019, AWS leads the pack with only 338 hours of downtime, followed by GCP closely at 361. Microsoft Azure has a whopping total of 1,934 hours of self-reported downtime.
+
+![][8]
+
+A few points on these numbers. First, this is an aggregation of the self-reported data from the vendors' websites, which isn’t the “true” number, as regional information or service granularity is sometimes obscured. If a service is unavailable for an hour and it’s reported for an hour on the website but it spanned five regions, correctly five hours should have been used. But for this calculation, we used only one hour because that is what was self-reported.
+
+Because of this, the numbers are most favorable to Microsoft because they provide the least amount of regional information. The numbers are least favorable to AWS because they provide the most granularity. Also, I believe AWS has the most services in most regions, so they have more opportunities for an outage.
+
+We had considered normalizing the data, but that would require a significant amount of work to destruct the downtime on a per service per region basis. I may choose to do that in the future, but for now, the vendor-reported view is a good indicator of relative performance.
+
+Another important point is that only infrastructure as a service (IaaS) services were used to calculate downtime. If Google Street View or Bing Maps went down, most businesses would not care, so it would have been unfair to roll those number in.
+
+### SLAs do not correlate to reliability
+
+Given the importance of cloud services today, I would like to see every cloud provider post a 12-month running total of downtime somewhere on their website so customers can do an “apples to apples” comparison. This obviously isn’t the only factor used in determining which cloud provider to use, but it is one of the more critical ones.
+
+Also, buyers should be aware that there is a big difference between service-level agreements (SLAs) and downtime. A cloud operator can promise anything they want, even provide a 100% SLA, but that just means they need to reimburse the business when a service isn’t available. Most IT leaders I have talked to say the few bucks they get back when a service is out is a mere fraction of what the outage actually cost them.
+
+### Measure twice and cut once to minimize business disruption
+
+If you’re reading this and you’re researching cloud services, it’s important to not just make the easy decision of buying for convenience. Many companies look at Azure because Microsoft gives away Azure credits as part of the Enterprise Agreement (EA). I’ve interviewed several companies that took the path of least resistance, but they wound up disappointed with availability and then switched to AWS or GCP later, which can have a disruptive effect.
+
+I’m certainly not saying to not buy Microsoft Azure, but it is important to do your homework to understand the historical performance of the services you’re considering in the regions you need them. The information on the vendor websites may not tell the full picture, so it’s important to do the necessary due diligence to ensure you understand what you’re buying before you buy it.
+
+Join the Network World communities on [Facebook][9] and [LinkedIn][10] to comment on topics that are top of mind.
+
+--------------------------------------------------------------------------------
+
+via: https://www.networkworld.com/article/3394341/when-it-comes-to-uptime-not-all-cloud-providers-are-created-equal.html#tk.rss_all
+
+作者:[Zeus Kerravala][a]
+选题:[lujun9972][b]
+译者:[译者ID](https://github.com/译者ID)
+校对:[校对者ID](https://github.com/校对者ID)
+
+本文由 [LCTT](https://github.com/LCTT/TranslateProject) 原创编译,[Linux中国](https://linux.cn/) 荣誉推出
+
+[a]: https://www.networkworld.com/author/Zeus-Kerravala/
+[b]: https://github.com/lujun9972
+[1]: https://images.idgesg.net/images/article/2019/02/cloud_comput_connect_blue-100787048-large.jpg
+[2]: https://www.networkworld.com/article/3208029/azure-stack-microsoft-s-private-cloud-platform-and-what-it-pros-need-to-know-about-it
+[3]: https://www.networkworld.com/article/3319776/the-network-matters-for-public-cloud-performance.html
+[4]: https://www.networkworld.com/newsletters/signup.html
+[5]: https://azure.microsoft.com/en-us/status/history/
+[6]: https://status.cloud.google.com/incident/appengine/19008
+[7]: https://status.aws.amazon.com/
+[8]: https://images.idgesg.net/images/article/2019/05/public-cloud-downtime-100795948-large.jpg
+[9]: https://www.facebook.com/NetworkWorld/
+[10]: https://www.linkedin.com/company/network-world
diff --git a/sources/talk/20190510 Supermicro moves production from China.md b/sources/talk/20190510 Supermicro moves production from China.md
new file mode 100644
index 0000000000..21739fa416
--- /dev/null
+++ b/sources/talk/20190510 Supermicro moves production from China.md
@@ -0,0 +1,58 @@
+[#]: collector: (lujun9972)
+[#]: translator: ( )
+[#]: reviewer: ( )
+[#]: publisher: ( )
+[#]: url: ( )
+[#]: subject: (Supermicro moves production from China)
+[#]: via: (https://www.networkworld.com/article/3394404/supermicro-moves-production-from-china.html#tk.rss_all)
+[#]: author: (Andy Patrizio https://www.networkworld.com/author/Andy-Patrizio/)
+
+Supermicro moves production from China
+======
+Supermicro was cleared of any activity related to the Chinese government and secret chips in its motherboards, but it is taking no chances and is moving its facilities.
+![Frank Schwichtenberg \(CC BY 4.0\)][1]
+
+Server maker Supermicro, based in Fremont, California, is reportedly moving production out of China over customer concerns that the Chinese government had secretly inserted chips for spying into its motherboards.
+
+The claims were made by Bloomberg late last year in a story that cited more than 100 sources in government and private industry, including Apple and Amazon Web Services (AWS). However, Apple CEO Tim Cook and AWS CEO Andy Jassy denied the claims and called for Bloomberg to retract the article. And a few months later, the third-party investigations firm Nardello & Co examined the claims and [cleared Supermicro][2] of any surreptitious activity.
+
+At first it seemed like Supermicro was weathering the storm, but the story did have a negative impact. Server sales have fallen since the Bloomberg story, and the company is forecasting a near 10% decline in total revenues for the March quarter compared to the previous three months.
+
+**[ Also read:[Who's developing quantum computers][3] ]**
+
+And now, Nikkei Asian Review reports that despite the strong rebuttals, some customers remain cautious about the company's products. To address those concerns, Nikkei says Supermicro has told suppliers to [move production out of China][4], citing industry sources familiar with the matter.
+
+It also has the side benefit of mitigating against the U.S.-China trade war, which is only getting worse. Since the tariffs are on the dollar amount of the product, that can quickly add up even for a low-end system, as Serve The Home noted in [this analysis][5].
+
+Supermicro is the world's third-largest server maker by shipments, selling primarily to cloud providers like Amazon and Facebook. It does its own assembly in its Fremont facility but outsources motherboard production to numerous suppliers, mostly China and Taiwan.
+
+"We have to be more self-reliant [to build in-house manufacturing] without depending only on those outsourcing partners whose production previously has mostly been in China," an executive told Nikkei.
+
+Nikkei notes that roughly 90% of the motherboards shipped worldwide in 2017 were made in China, but that percentage dropped to less than 50% in 2018, according to Digitimes Research, a tech supply chain specialist based in Taiwan.
+
+Supermicro just held a groundbreaking ceremony in Taiwan for a 800,000 square foot manufacturing plant in Taiwan and is expanding its San Jose, California, plant as well. So, they must be anxious to be free of China if they are willing to expand in one of the most expensive real estate markets in the world.
+
+A Supermicro spokesperson said via email, “We have been expanding our manufacturing capacity for many years to meet increasing customer demand. We are currently constructing a new Green Computing Park building in Silicon Valley, where we are the only Tier 1 solutions vendor manufacturing in Silicon Valley, and we proudly broke ground this week on a new manufacturing facility in Taiwan. To support our continued global growth, we look forward to expanding in Europe as well.”
+
+Join the Network World communities on [Facebook][6] and [LinkedIn][7] to comment on topics that are top of mind.
+
+--------------------------------------------------------------------------------
+
+via: https://www.networkworld.com/article/3394404/supermicro-moves-production-from-china.html#tk.rss_all
+
+作者:[Andy Patrizio][a]
+选题:[lujun9972][b]
+译者:[译者ID](https://github.com/译者ID)
+校对:[校对者ID](https://github.com/校对者ID)
+
+本文由 [LCTT](https://github.com/LCTT/TranslateProject) 原创编译,[Linux中国](https://linux.cn/) 荣誉推出
+
+[a]: https://www.networkworld.com/author/Andy-Patrizio/
+[b]: https://github.com/lujun9972
+[1]: https://images.idgesg.net/images/article/2019/05/supermicro_-_x11sae__cebit_2016_01-100796121-large.jpg
+[2]: https://www.networkworld.com/article/3326828/investigator-finds-no-evidence-of-spy-chips-on-super-micro-motherboards.html
+[3]: https://www.networkworld.com/article/3275385/who-s-developing-quantum-computers.html
+[4]: https://asia.nikkei.com/Economy/Trade-war/Server-maker-Super-Micro-to-ditch-made-in-China-parts-on-spy-fears
+[5]: https://www.servethehome.com/how-tariffs-hurt-intel-xeon-d-atom-and-amd-epyc-3000/
+[6]: https://www.facebook.com/NetworkWorld/
+[7]: https://www.linkedin.com/company/network-world
diff --git a/sources/talk/20190513 HPE-s CEO lays out his technology vision.md b/sources/talk/20190513 HPE-s CEO lays out his technology vision.md
new file mode 100644
index 0000000000..c9a8de9c8a
--- /dev/null
+++ b/sources/talk/20190513 HPE-s CEO lays out his technology vision.md
@@ -0,0 +1,162 @@
+[#]: collector: (lujun9972)
+[#]: translator: ( )
+[#]: reviewer: ( )
+[#]: publisher: ( )
+[#]: url: ( )
+[#]: subject: (HPE’s CEO lays out his technology vision)
+[#]: via: (https://www.networkworld.com/article/3394879/hpe-s-ceo-lays-out-his-technology-vision.html)
+[#]: author: (Eric Knorr )
+
+HPE’s CEO lays out his technology vision
+======
+In an exclusive interview, HPE CEO Antonio Neri unpacks his portfolio of technology initiatives, from edge computing to tomorrow’s memory-driven architecture.
+![HPE][1]
+
+Like Microsoft's Satya Nadella, HPE CEO Antonio Neri is a technologist with a long history of leading initiatives in his company. Meg Whitman, his former boss at HPE, showed her appreciation of Neri’s acumen by promoting him to HPE Executive Vice President in 2015 – and gave him the green light to acquire [Aruba][2], [SimpliVity][3], [Nimble Storage][4], and [Plexxi][5], all of which added key items to HPE’s portfolio.
+
+Neri succeeded Whitman as CEO just 16 months ago. In a recent interview with Network World, Neri’s engineering background was on full display as he explained HPE’s technology roadmap. First and foremost, he sees a huge opportunity in [edge computing][6], into which HPE is investing $4 billion over four years to further develop edge “connectivity, security, and obviously cloud and analytics.”
+
+**More about edge networking**
+
+ * [How edge networking and IoT will reshape data centers][7]
+ * [Edge computing best practices][8]
+ * [How edge computing can help secure the IoT][9]
+
+
+
+Although his company abandoned its public cloud efforts in 2015, Neri is also bullish on the self-service “cloud experience,” which he asserts HPE is already implementing on-prem today in a software-defined, consumption-driven model. More fundamentally, he believes we are on the brink of a memory-driven computing revolution, where storage and memory become one and, depending on the use case, various compute engines are brought to bear on zettabytes of data.
+
+This interview, conducted by Network World Editor-in-Chief Eric Knorr and edited for length and clarity, digs into Neri’s technology vision. [A companion interview on CIO][10] centers on Neri’s views of innovation, management, and company culture.
+
+**Eric Knorr: ** Your biggest and highest profile investment so far has been in edge computing. My understanding of edge computing is that we’re really talking about mini-data centers, defined by IDC as less than 100 square feet in size. What’s the need for a $4 billion investment in that?
+
+**Antonio Neri:** It’s twofold. We focus first on connectivity. Think about Aruba as a platform company, a cloud-enabled company. Now we offer branch solutions and edge data center solutions that include [wireless][11], LAN, [WAN][12] connectivity and soon [5G][13]. We give you a control plane so that that connectivity experience can be seen consistently the same way. All the policy management, the provisioning and the security aspects of it.
+
+**Knorr:** Is 5G a big focus?
+
+**[[Get certified as an Apple Technical Coordinator with this seven-part online course from PluralSight.][14] ]**
+
+**Neri:** It’s a big focus for us. What customers are telling us is that it’s hard to get 5G inside the building. How you do hand off between 5G and Wi-Fi and give them the same experience? Because the problem is that we have LAN, wireless, and WAN already fully integrated into the control plane, but 5G sits over here. If you are an enterprise, you have to manage these two pipes independently.
+
+With the new spectrum, though, they are kind of comingling anyway. [Customers ask] why don’t you give me [a unified] experience on top of that, with all this policy management and cloud-enablement, so I can provision the right connectivity for the right use case? A sensor can use a lower radio access or [Bluetooth][15] or other type of connectivity because you don’t need persistent connectivity and you don’t have the power to do it.
+
+In some cases, you just put a SIM on it, and you have 5G, but in another one it’s just wireless connectivity. Wi-Fi connectivity is significantly lower cost than 5G. The use cases will dictate what type of connectivity you need, but the reality is they all want one experience. And we can do that because we have a great platform and a great partnership with MSPs, telcos, and providers.
+
+**Knorr:** So it sounds like much of your investment is going into that integration.
+
+**Neri:** The other part is how we provide the ability to provision the right cloud computing at the edge for the right use cases. Think about, for example, a manufacturing floor. We can converge the OT and IT worlds through a converged infrastructure aspect that digitizes the analog process into a digital process. We bring the cloud compute in there, which is fully virtualized and containerized, we integrate Wi-Fi connectivity or LAN connectivity, and we eliminate all these analog processes that are multi-failure touchpoints because you have multiple things that have to come together.
+
+That’s a great example of a cloud at the edge. And maybe that small cloud is connected to a big cloud which could be in the large data center, which the customer owns – or it can be one of the largest public cloud providers.
+
+**Knorr:** It’s difficult to talk about the software-defined data center and private cloud without talking about [VMware][16]. Where do your software-defined solutions leave off and where does VMware begin?
+
+**Neri:** Where we stop is everything below the hypervisor, including the software-defined storage and things like SimpliVity. That has been the advantage we’ve had with [HPE OneView][17], so we can provision and manage the infrastructure-life-cycle and software-defined aspects at the infrastructure level. And let’s not forget security, because we’ve integrated [silicon root of trust][18] into our systems, which is a good advantage for us in the government space.
+
+Then above that we continue to develop capabilities. Customers want choice. That’s why [the partnership with Nutanix][19] was important. We offer an alternative to vSphere and vCloud Foundation with Nutanix Prism and Acropolis.
+
+**Knorr:** VMware has become the default for the private cloud, though.
+
+**Neri:** Obviously, VMware owns 60 percent of the on-prem virtualized environment, but more and more, containers are becoming the way to go in a cloud-native approach. For us, we own the full container stack, because we base our solution on Kubernetes. We deploy that. That’s why the partnership with Nutanix is important. With Nutanix, we offer KVM and the Prism stack and then we’re fully integrated with HPE OneView for the rest of the infrastructure.
+
+**Knorr:** You also offer GKE [Google [Kubernetes][20] Engine] on-prem.
+
+**Neri:** Correct. We’re working with Google on the next version of that.
+
+**Knorr:** How long do you think it will be before you start seeing Kubernetes and containers on bare metal?
+
+**Neri:** It’s an interesting question. Many customers tell us it’s like going back to the future. It’s like we’re paying this tax on the virtualization layer.
+
+**Knorr:** Exactly.
+
+**Neri:** I can go bare metal and containers and be way more efficient. It is a little bit back to the future. But it’s a different future.
+
+**Knorr:** And it makes the promise of [hybrid cloud][21] a little more real. I know HPE has been very bullish on hybrid.
+
+**Neri:** We have been the one to say the world would be hybrid.
+
+**Knorr:** But today, how hybrid is hybrid really? I mean, you have workloads in the public cloud, you have workloads in a [private cloud][22]. Can you really rope it all together into hybrid?
+
+**Neri:** I think you have to have portability eventually.
+
+**Knorr:** Eventually. It’s not really true now, though.
+
+**Neri:** No, not true now. If you look at it from the software brokering perspective that makes hybrid very small. We know this eventually has to be all connected, but it’s not there yet. More and more of these workloads have to go back and forth.
+
+If you ask me what the CIO role of the future will look like, it would be a service provider. I wake up in the morning, have a screen that says – oh, you know what? Today it’s cheaper to run that app here. I just slice it there and then it just moves. Whatever attributes on the data I want to manage and so forth – oh, today I have capacity here and by the way, why are you not using it? Slide it back here. That’s the hybrid world.
+
+Many people, when they started with the cloud, thought, “I’ll just virtualize everything,” but that’s not the cloud. You’re [virtualizing][23], but you have to make it self-service. Obviously, cloud-native applications have developed that are different today. That’s why containers are definitely a much more efficient way, and that’s why I agree that the bare-metal piece of this is coming back.
+
+**Knorr:** Do you worry about public cloud incursions into the [data center][24]?
+
+**Neri:** It’s happening. Of course I’m worried. But what at least gives me comfort is twofold. One is that the customer wants choice. They don’t want to be locked in. Service is important. It’s one thing to say: Here’s the system. The other is: Who’s going to maintain it for me? Who is going to run it for me? And even though you have all the automation tools in the world, somebody has to watch this thing. Our job is to bring the public-cloud experience on prem, so that the customer has that choice.
+
+**Knorr:** Part of that is economics.
+
+**Neri:** When you look at economics it’s no longer just the cost of compute anymore. What we see more and more is the cost of the data bandwidth back and forth. That’s why the first question a customer asks is: Where should I put my data? And that dictates a lot of things, because today the data transfer bill is way higher than the cost of renting a VM.
+
+The other thing is that when you go on the public cloud you can spin up a VM, but the problem is if you don’t shut it off, the bill keeps going. We brought, in the context of [composability][25], the ability to shut it off automatically. That’s why composability is important, because we can run, first of all, multi-workloads in the same infrastructure – whether it’s bare metal, virtualized or containerized. It’s called composable because the software layers of intelligence compose the right solutions from compute, storage, fabric and memory to that workload. When it doesn’t need it, it gives it back.
+
+**Knorr:** Is there any opportunity left at the hardware level to innovate?
+
+**Neri:** That’s why we think about memory-driven computing. Today we have a very CPU-centric approach. This is a limiting factor, and the reality is, if you believe data is the core of the architecture going forward, then the CPU can’t be the core of the architecture anymore.
+
+You have a bunch of inefficiency by moving data back and forth across the system, which also creates energy waste and so forth. What we are doing is basically rearchitecting this for once in 70 years. We take memory and storage and collapse the two into one, so this becomes one central pool, which is nonvolatile and becomes the core. And then we bring the right computing capability to the data.
+
+In an AI use case, you don’t move the data. You bring accelerators or GPUs to the data. For general purpose, you may use an X86, and maybe in video transcoding, you use an ARM-based architecture. The magic is this: You can do this on zettabytes of data and the benefit is there is no waste, very little power to keep it alive, and it’s persistent.
+
+We call this the Generation Z fabric, which is based on a data fabric and silicon photonics. Now we go from copper, which is generating a lot of waste and a lot of heat and energy, to silicon photonics. So we not only scale this to zettabytes, we can do massive amounts of computation by bringing the right compute at the speed that’s needed to the data – and we solve a cost and scale problem too, because copper today costs a significant amount of money, and gold-plated connectors are hundreds of dollars.
+
+We’re going to actually implement this capability in silicon photonics in our current architectures by the end of the year. In Synergy, for example, which is a composable blade system, at the back of the rack you can swap from Ethernet to silicon photonics. It was designed that way. We already prototyped this in a simple 2U chassis with 160 TB of memory and 2000 cores. We were able to process a billion-record database with 55 million combinations of algorithms in less than a minute.
+
+**Knorr:** So you’re not just focusing on the edge, but the core, too.
+
+**Neri:** As you go down from the cloud to the edge, that architecture actually scales to the smallest things. You can do it on a massive scale or you can do it on a small scale. We will deploy these technologies in our systems architectures now. Once the whole ecosystem is developed, because we also need an ISV ecosystem that can code applications in this new world or you’re not taking advantage of it. Also, the current Linux kernel can only handle so much memory, so you have to rewrite the kernel. We are working with two universities to do that.
+
+The hardware will continue to evolve and develop, but there still is a lot of innovation that has to happen. What’s holding us back, honestly, is the software.
+
+**Knorr:** And that’s where a lot of your investment is going?
+
+**Neri:** Correct. Exactly right. Systems software, not application software. It’s the system software that makes this infrastructure solution-oriented, workload-optimized, autonomous and efficient.
+
+Join the Network World communities on [Facebook][26] and [LinkedIn][27] to comment on topics that are top of mind.
+
+--------------------------------------------------------------------------------
+
+via: https://www.networkworld.com/article/3394879/hpe-s-ceo-lays-out-his-technology-vision.html
+
+作者:[Eric Knorr][a]
+选题:[lujun9972][b]
+译者:[译者ID](https://github.com/译者ID)
+校对:[校对者ID](https://github.com/校对者ID)
+
+本文由 [LCTT](https://github.com/LCTT/TranslateProject) 原创编译,[Linux中国](https://linux.cn/) 荣誉推出
+
+[a]:
+[b]: https://github.com/lujun9972
+[1]: https://images.idgesg.net/images/article/2019/05/antonio-neri_hpe_new-100796112-large.jpg
+[2]: https://www.networkworld.com/article/2891130/aruba-networks-is-different-than-hps-failed-wireless-acquisitions.html
+[3]: https://www.networkworld.com/article/3158784/hpe-buying-simplivity-for-650-million-to-boost-hyperconvergence.html
+[4]: https://www.networkworld.com/article/3177376/hpe-to-pay-1-billion-for-nimble-storage-after-cutting-emc-ties.html
+[5]: https://www.networkworld.com/article/3273113/hpe-snaps-up-hyperconverged-network-hcn-vendor-plexxi.html
+[6]: https://www.networkworld.com/article/3224893/what-is-edge-computing-and-how-it-s-changing-the-network.html
+[7]: https://www.networkworld.com/article/3291790/data-center/how-edge-networking-and-iot-will-reshape-data-centers.html
+[8]: https://www.networkworld.com/article/3331978/lan-wan/edge-computing-best-practices.html
+[9]: https://www.networkworld.com/article/3331905/internet-of-things/how-edge-computing-can-help-secure-the-iot.html
+[10]: https://www.cio.com/article/3394598/hpe-ceo-antonio-neri-rearchitects-for-the-future.html
+[11]: https://www.networkworld.com/article/3238664/80211-wi-fi-standards-and-speeds-explained.html
+[12]: https://www.networkworld.com/article/3248989/what-is-a-wide-area-network-a-definition-examples-and-where-wans-are-headed.html
+[13]: https://www.networkworld.com/article/3203489/what-is-5g-how-is-it-better-than-4g.html
+[14]: https://pluralsight.pxf.io/c/321564/424552/7490?u=https%3A%2F%2Fwww.pluralsight.com%2Fpaths%2Fapple-certified-technical-trainer-10-11
+[15]: https://www.networkworld.com/article/3235124/internet-of-things-definitions-a-handy-guide-to-essential-iot-terms.html
+[16]: https://www.networkworld.com/article/3340259/vmware-s-transformation-takes-hold.html
+[17]: https://www.networkworld.com/article/2174203/hp-expands-oneview-into-vmware-environs.html
+[18]: https://www.networkworld.com/article/3199826/hpe-highlights-innovation-in-software-defined-it-security-at-discover.html
+[19]: https://www.networkworld.com/article/3388297/hpe-and-nutanix-partner-for-hyperconverged-private-cloud-systems.html
+[20]: https://www.infoworld.com/article/3268073/what-is-kubernetes-container-orchestration-explained.html
+[21]: https://www.networkworld.com/article/3268448/what-is-hybrid-cloud-really-and-whats-the-best-strategy.html
+[22]: https://www.networkworld.com/article/2159885/cloud-computing-gartner-5-things-a-private-cloud-is-not.html
+[23]: https://www.networkworld.com/article/3285906/whats-the-future-of-server-virtualization.html
+[24]: https://www.networkworld.com/article/3223692/what-is-a-data-centerhow-its-changed-and-what-you-need-to-know.html
+[25]: https://www.networkworld.com/article/3266106/what-is-composable-infrastructure.html
+[26]: https://www.facebook.com/NetworkWorld/
+[27]: https://www.linkedin.com/company/network-world
diff --git a/sources/talk/20190513 Top auto makers rely on cloud providers for IoT.md b/sources/talk/20190513 Top auto makers rely on cloud providers for IoT.md
new file mode 100644
index 0000000000..5adf5f65a7
--- /dev/null
+++ b/sources/talk/20190513 Top auto makers rely on cloud providers for IoT.md
@@ -0,0 +1,53 @@
+[#]: collector: (lujun9972)
+[#]: translator: ( )
+[#]: reviewer: ( )
+[#]: publisher: ( )
+[#]: url: ( )
+[#]: subject: (Top auto makers rely on cloud providers for IoT)
+[#]: via: (https://www.networkworld.com/article/3395137/top-auto-makers-rely-on-cloud-providers-for-iot.html)
+[#]: author: (Jon Gold https://www.networkworld.com/author/Jon-Gold/)
+
+Top auto makers rely on cloud providers for IoT
+======
+
+For the companies looking to implement the biggest and most complex [IoT][1] setups in the world, the idea of pairing up with [AWS][2], [Google Cloud][3] or [Azure][4] seems to be one whose time has come. Within the last two months, BMW and Volkswagen have both announced large-scale deals with Microsoft and Amazon, respectively, to help operate their extensive network of operational technology.
+
+According to Alfonso Velosa, vice president and analyst at Gartner, part of the impetus behind those two deals is that the automotive sector fits in very well with the architecture of the public cloud. Public clouds are great at collecting and processing data from a diverse array of different sources, whether they’re in-vehicle sensors, dealerships, mechanics, production lines or anything else.
+
+**[ RELATED:[What hybrid cloud means in practice][5]. | Get regularly scheduled insights by [signing up for Network World newsletters][6]. ]**
+
+“What they’re trying to do is create a broader ecosystem. They think they can leverage the capabilities from these folks,” Velosa said.
+
+### Cloud providers as IoT partners
+
+The idea is automated analytics for service and reliability data, manufacturing and a host of other operational functions. And while the full realization of that type of service is still very much a work in progress, it has clear-cut advantages for big companies – a skilled partner handling tricky implementation work, built-in capability for sophisticated analytics and security, and, of course, the ability to scale up in a big way.
+
+Hence, the structure of the biggest public clouds has upside for many large-scale IoT deployments, not just the ones taking place in the auto industry. The cloud giants have vast infrastructures, with multiple points of presence all over the world.
+
+To continue reading this article register now
+
+[Get Free Access][7]
+
+[Learn More][8] Existing Users [Sign In][7]
+
+--------------------------------------------------------------------------------
+
+via: https://www.networkworld.com/article/3395137/top-auto-makers-rely-on-cloud-providers-for-iot.html
+
+作者:[Jon Gold][a]
+选题:[lujun9972][b]
+译者:[译者ID](https://github.com/译者ID)
+校对:[校对者ID](https://github.com/校对者ID)
+
+本文由 [LCTT](https://github.com/LCTT/TranslateProject) 原创编译,[Linux中国](https://linux.cn/) 荣誉推出
+
+[a]: https://www.networkworld.com/author/Jon-Gold/
+[b]: https://github.com/lujun9972
+[1]: https://www.networkworld.com/article/3207535/what-is-iot-how-the-internet-of-things-works.html
+[2]: https://www.networkworld.com/article/3324043/aws-does-hybrid-cloud-with-on-prem-hardware-vmware-help.html
+[3]: https://www.networkworld.com/article/3388218/cisco-google-reenergize-multicloudhybrid-cloud-joint-development.html
+[4]: https://www.networkworld.com/article/3385078/microsoft-introduces-azure-stack-for-hci.html
+[5]: https://www.networkworld.com/article/3249495/what-hybrid-cloud-mean-practice
+[6]: https://www.networkworld.com/newsletters/signup.html
+[7]: javascript://
+[8]: /learn-about-insider/
diff --git a/sources/talk/20190514 Brillio and Blue Planet Partner to Bring Network Automation to the Enterprise.md b/sources/talk/20190514 Brillio and Blue Planet Partner to Bring Network Automation to the Enterprise.md
new file mode 100644
index 0000000000..e821405199
--- /dev/null
+++ b/sources/talk/20190514 Brillio and Blue Planet Partner to Bring Network Automation to the Enterprise.md
@@ -0,0 +1,56 @@
+[#]: collector: (lujun9972)
+[#]: translator: ( )
+[#]: reviewer: ( )
+[#]: publisher: ( )
+[#]: url: ( )
+[#]: subject: (Brillio and Blue Planet Partner to Bring Network Automation to the Enterprise)
+[#]: via: (https://www.networkworld.com/article/3394687/brillio-and-blue-planet-partner-to-bring-network-automation-to-the-enterprise.html)
+[#]: author: (Rick Hamilton, Senior Vice President, Blue Planet Software )
+
+Brillio and Blue Planet Partner to Bring Network Automation to the Enterprise
+======
+Rick Hamilton, senior vice president of Blue Planet, a division of Ciena, explains how partnering with Brillio brings the next generation of network capabilities to enterprises—just when they need it most.
+![Kritchanut][1]
+
+![][2]
+
+_Rick Hamilton, senior vice president of Blue Planet, a division of Ciena, explains how partnering with Brillio brings the next generation of network capabilities to enterprises—just when they need it most._
+
+In February 2019, we announced that Blue Planet was evolving into a more independent division, helping us increase our focus on innovative intelligent automation solutions that help our enterprise and service provider customers accelerate and achieve their business transformation goals.
+
+Today we’re excited to make another leap forward in delivering these benefits to enterprises of all types via our partnership with digital transformation services and solutions leader Brillio. Together, we are co-creating intelligent cloud and network management solutions that increase service visibility and improve service assurance by effectively leveraging the convergence of cloud, IoT, and AI.
+
+**Accelerating digital transformation in the enterprise**
+
+Enterprises continue to look toward cloud services to create new and incremental revenue streams based on innovative solution offerings and on-demand product/solution delivery models, and to optimize their infrastructure investments. In fact, Gartner predicts that enterprise IT spending for cloud-based offerings will continue to grow faster than non-cloud IT offerings, making up 28% of spending by 2022, up from 19% in 2018.
+
+As enterprises adopt cloud, they realize there are many challenges associated with traditional approaches to operating and managing complex and hybrid multi-cloud environments. Our partnership with Brillio enables us to help these organizations across industries such as manufacturing, logistics, retail, and financial services meet their technical and business needs with high-impact solutions that improve customer experiences, drive operational efficiencies, and improve quality of service.
+
+This is achieved by combining the Blue Planet intelligent automation platform and the Brillio CLIP™services delivery excellence platform and user-centered design (UCD) lead solution framework. Together, we offer end-to-end visibility of application and infrastructure assets in a hybrid multi-cloud environment and provide service assurance and self-healing capabilities that improve network and service availability.
+
+**Partnering on research and development**
+
+Brillio will also partner with Blue Planet on longer-term R&D efforts. As one of a preferred product engineering services providers, Brillio will work closely with our engineering team to develop and deliver network intelligence and automation solutions to help enterprises build dynamic, programmable infrastructure that leverage analytics and automation to realize the Adaptive Network vision.
+
+Of course, a partnership like this is a two-way street, and we consider Brillio’s choice to work with us to be a testament to our expertise, vision, and execution. In the words of Brillio Chairman and CEO Raj Mamodia, “Blue Planet’s experience in end-to-end service orchestration coupled with Brillio’s expertise in cloudification, user-centered enterprise solutions design, and rapid software development delivers distinct advantages to the industry. Through integration of technologies like cloud, IoT, and AI into our combined solutions, our partnership spurs greater innovation and helps us address the large and growing enterprise networking automation market.”
+
+Co-creating intelligent hybrid cloud and network management solutions with Brillio is key to advancing enterprise digital transformation initiatives. Partnering with Brillio helps us address the plethora of challenges facing enterprises today on their digital journey. Our partnership enables Blue Planet to achieve faster time-to-market and greater efficiency in developing new solutions to enable enterprises to continue to thrive and grow.
+
+[Learn more about Blue Planet here][3]
+
+--------------------------------------------------------------------------------
+
+via: https://www.networkworld.com/article/3394687/brillio-and-blue-planet-partner-to-bring-network-automation-to-the-enterprise.html
+
+作者:[Rick Hamilton, Senior Vice President, Blue Planet Software][a]
+选题:[lujun9972][b]
+译者:[译者ID](https://github.com/译者ID)
+校对:[校对者ID](https://github.com/校对者ID)
+
+本文由 [LCTT](https://github.com/LCTT/TranslateProject) 原创编译,[Linux中国](https://linux.cn/) 荣誉推出
+
+[a]:
+[b]: https://github.com/lujun9972
+[1]: https://images.idgesg.net/images/article/2019/05/istock-952625346-100796314-large.jpg
+[2]: https://images.idgesg.net/images/article/2019/05/rick-100796315-small.jpg
+[3]: https://www.blueplanet.com/?utm_campaign=X1058319&utm_source=NWW&utm_term=BPWeb_Brillio&utm_medium=sponsoredpost3Q19
diff --git a/sources/talk/20190514 Las Vegas targets transport, public safety with IoT deployments.md b/sources/talk/20190514 Las Vegas targets transport, public safety with IoT deployments.md
new file mode 100644
index 0000000000..84a563c8bc
--- /dev/null
+++ b/sources/talk/20190514 Las Vegas targets transport, public safety with IoT deployments.md
@@ -0,0 +1,65 @@
+[#]: collector: (lujun9972)
+[#]: translator: ( )
+[#]: reviewer: ( )
+[#]: publisher: ( )
+[#]: url: ( )
+[#]: subject: (Las Vegas targets transport, public safety with IoT deployments)
+[#]: via: (https://www.networkworld.com/article/3395536/las-vegas-targets-transport-public-safety-with-iot-deployments.html)
+[#]: author: (Jon Gold https://www.networkworld.com/author/Jon-Gold/)
+
+Las Vegas targets transport, public safety with IoT deployments
+======
+
+![Franck V. \(CC0\)][1]
+
+The city of Las Vegas’ pilot program with NTT and Dell, designed to crack down on wrong-way driving on municipal roads, is just part of the big plans that Sin City has for leveraging IoT tech in the future, according to the city's director of technology Michael Sherwood, who sat down with Network World at the IoT World conference in Silicon Valley this week.
+
+The system uses smart cameras and does most of its processing at the edge, according to Sherwood. The only information that gets sent back to the city’s private cloud is metadata – aggregated information about overall patterns, for decision-making and targeting purposes, not data about individual traffic incidents and wrong-way drivers.
+
+**[ Also see[What is edge computing?][2] and [How edge networking and IoT will reshape data centers][3].]**
+
+It’s an important public safety consideration, he said, but it’s a small part of the larger IoT-enabled framework that the city envisions for the future.
+
+“Our goal is to make our data open to the public, not only for transparency purposes, but to help spur development and create new applications to make Vegas a better place to live,” said Sherwood.
+
+[The city’s public data repository][4] already boasts a range of relevant data, some IoT-generated, some not. And efforts to make that data store more open have already begun to bear fruit, according to Sherwood. For example, one hackathon about a year ago resulted in an Alexa app that tells users how many traffic lights are out, by tracking energy usage data via the city’s portal, among other applications.
+
+As with IoT in general, Sherwood said that the city’s efforts have been bolstered by an influx of operational talen. Rather than additional IT staff to run the new systems, they’ve brought in experts from the traffic department to help get the most out of the framework.
+
+Another idea for leveraging the city’s traffic data involves tracking the status of the curb. Given the rise of Uber and Lyft and other on-demand transportation services, linking a piece of camera-generated information like “rideshares are parked along both sides of this street” directly into a navigation app could help truck drivers avoid gridlock.
+
+“We’re really looking to make the roads a living source of information,” Sherwood said.
+
+**Safer parks**
+
+Las Vegas is also pursuing related public safety initiatives. One pilot project aims to make public parks safer by installing infrared cameras so authorities can tell whether people are in parks after hours without incurring undue privacy concerns, given that facial recognition is very tricky in infrared.
+
+It’s the test-and-see method of IoT development, according to Sherwood.
+
+“That’s a way of starting with an IoT project: start with one park. The cost to do something like this is not astronomical, and it allows you to gauge some other information from it,” he said.
+
+The city has also worked to keep the costs of these projects low or even show a returnon investment, Sherwood added. Workforce development programs could train municipal workers to do simple maintenance on smart cameras in parks or along roadways, and the economic gains made from the successful use of the systems ought to outweigh deployment and operational outlay.
+
+“If it’s doing it’s job, those efficiencies should cover the system’s cost,” he said.
+
+Join the Network World communities on [Facebook][5] and [LinkedIn][6] to comment on topics that are top of mind.
+
+--------------------------------------------------------------------------------
+
+via: https://www.networkworld.com/article/3395536/las-vegas-targets-transport-public-safety-with-iot-deployments.html
+
+作者:[Jon Gold][a]
+选题:[lujun9972][b]
+译者:[译者ID](https://github.com/译者ID)
+校对:[校对者ID](https://github.com/校对者ID)
+
+本文由 [LCTT](https://github.com/LCTT/TranslateProject) 原创编译,[Linux中国](https://linux.cn/) 荣誉推出
+
+[a]: https://www.networkworld.com/author/Jon-Gold/
+[b]: https://github.com/lujun9972
+[1]: https://images.idgesg.net/images/article/2018/07/pedestrian-walk-sign_go_start_begin_traffic-light_by-franck-v-unsplaash-100765089-large.jpg
+[2]: https://www.networkworld.com/article/3224893/internet-of-things/what-is-edge-computing-and-how-it-s-changing-the-network.html
+[3]: https://www.networkworld.com/article/3291790/data-center/how-edge-networking-and-iot-will-reshape-data-centers.html
+[4]: https://opendata.lasvegasnevada.gov/
+[5]: https://www.facebook.com/NetworkWorld/
+[6]: https://www.linkedin.com/company/network-world
diff --git a/sources/talk/20190514 Mobility and SD-WAN, Part 1- SD-WAN with 4G LTE is a Reality.md b/sources/talk/20190514 Mobility and SD-WAN, Part 1- SD-WAN with 4G LTE is a Reality.md
new file mode 100644
index 0000000000..1ecd68fa41
--- /dev/null
+++ b/sources/talk/20190514 Mobility and SD-WAN, Part 1- SD-WAN with 4G LTE is a Reality.md
@@ -0,0 +1,64 @@
+[#]: collector: (lujun9972)
+[#]: translator: ( )
+[#]: reviewer: ( )
+[#]: publisher: ( )
+[#]: url: ( )
+[#]: subject: (Mobility and SD-WAN, Part 1: SD-WAN with 4G LTE is a Reality)
+[#]: via: (https://www.networkworld.com/article/3394866/mobility-and-sd-wan-part-1-sd-wan-with-4g-lte-is-a-reality.html)
+[#]: author: (Francisca Segovia )
+
+Mobility and SD-WAN, Part 1: SD-WAN with 4G LTE is a Reality
+======
+
+![istock][1]
+
+Without a doubt, 5G — the fifth generation of mobile wireless technology — is the hottest topic in wireless circles today. You can’t throw a stone without hitting 5G news. While telecommunications providers are in a heated competition to roll out 5G, it’s important to reflect on current 4G LTE (Long Term Evolution) business solutions as a preview of what we have learned and what’s possible.
+
+This is part one of a two-part blog series that will explore the [SD-WAN][2] journey through the evolution of these wireless technologies.
+
+### **Mobile SD-WAN is a reality**
+
+4G LTE commercialization continues to expand. According to [the GSM (Groupe Spéciale Mobile) Association][3], 710 operators have rolled out 4G LTE in 217 countries, reaching 83 percent of the world’s population. The evolution of 4G is transforming the mobile industry and is setting the stage for the advent of 5G.
+
+Mobile connectivity is increasingly integrated with SD-WAN, along with MPLS and broadband WAN services today. 4G LTE represents a very attractive transport alternative, as a backup or even an active member of the WAN transport mix to connect users to critical business applications. And in some cases, 4G LTE might be the only choice in locations where fixed lines aren’t available or reachable. Furthermore, an SD-WAN can optimize 4G LTE connectivity and bring new levels of performance and availability to mobile-based business use cases by selecting the best path available across several 4G LTE connections.
+
+### **Increasing application performance and availability with 4G LTE**
+
+Silver Peak has partnered with [BEC Technologies][4] to create a joint solution that enables customers to incorporate one or more low-cost 4G LTE services into any [Unity EdgeConnect™][5] SD-WAN edge platform deployment. All the capabilities of the EdgeConnect platform are supported across LTE links including packet-based link bonding, dynamic path control, path conditioning along with the optional [Unity Boost™ WAN Optimization][6] performance pack. This ensures always-consistent, always-available application performance even in the event of an outage or degraded service.
+
+EdgeConnect also incorporates sophisticated NAT traversal technology that eliminates the requirement for provisioning the LTE service with extra-cost static IP addresses. The Silver Peak [Unity Orchestrator™][7] management software enables the prioritization of LTE bandwidth usage based on branch and application requirements – active-active or backup-only. This solution is ideal in retail point-of-sale and other deployment use cases where always-available WAN connectivity is critical for the business.
+
+### **Automated SD-WAN enables innovative services**
+
+An example of an innovative mobile SD-WAN service is [swyMed’s DOT Telemedicine Backpack][8] powered by the EdgeConnect [Ultra Small][9] hardware platform. This integrated telemedicine solution enables first responders to connect to doctors and communicate patient vital statistics and real-time video anywhere, any time, greatly improving and expediting care for emergency patients. Using a lifesaving backpack provisioned with two LTE services from different carriers, EdgeConnect continuously monitors the underlying 4G LTE services for packet loss, latency and jitter. In the case of transport failure or brownout, EdgeConnect automatically initiates a sub-second failover so that voice, video and data connections continue without interruption over the remaining active 4G service. By bonding the two LTE links together with the EdgeConnect SD-WAN, swyMed can achieve an aggregate signal quality in excess of 90 percent, bringing mobile telemedicine to areas that would have been impossible in the past due to poor signal strength.
+
+To learn more about SD-WAN and the unique advantages that SD-WAN provides to enterprises across all industries, visit the [SD-WAN Explained][2] page on our website.
+
+### **Prepare for the 5G future**
+
+In summary, the adoption of 4G LTE is a reality. Service providers are taking advantage of the distinct benefits of SD-WAN to offer managed SD-WAN services that leverage 4G LTE.
+
+As the race for the 5G gains momentum, service providers are sure to look for ways to drive new revenue streams to capitalize on their initial investments. Stay tuned for part 2 of this 2-blog series where I will discuss how SD-WAN is one of the technologies that can help service providers to transition from 4G to 5G and enable the monetization of a new wave of managed 5G services.
+
+--------------------------------------------------------------------------------
+
+via: https://www.networkworld.com/article/3394866/mobility-and-sd-wan-part-1-sd-wan-with-4g-lte-is-a-reality.html
+
+作者:[Francisca Segovia][a]
+选题:[lujun9972][b]
+译者:[译者ID](https://github.com/译者ID)
+校对:[校对者ID](https://github.com/校对者ID)
+
+本文由 [LCTT](https://github.com/LCTT/TranslateProject) 原创编译,[Linux中国](https://linux.cn/) 荣誉推出
+
+[a]:
+[b]: https://github.com/lujun9972
+[1]: https://images.idgesg.net/images/article/2019/05/istock-952414660-100796279-large.jpg
+[2]: https://www.silver-peak.com/sd-wan/sd-wan-explained
+[3]: https://www.gsma.com/futurenetworks/resources/all-ip-statistics/
+[4]: https://www.silver-peak.com/resource-center/edgeconnect-4glte-solution-bec-technologies
+[5]: https://www.silver-peak.com/products/unity-edge-connect
+[6]: https://www.silver-peak.com/products/unity-boost
+[7]: https://www.silver-peak.com/products/unity-orchestrator
+[8]: https://www.silver-peak.com/resource-center/mobile-telemedicine-helps-save-lives-streaming-real-time-clinical-data-and-patient
+[9]: https://www.silver-peak.com/resource-center/edgeconnect-us-ec-us-specification-sheet
diff --git a/sources/talk/20190515 Extreme addresses networked-IoT security.md b/sources/talk/20190515 Extreme addresses networked-IoT security.md
new file mode 100644
index 0000000000..1ad756eded
--- /dev/null
+++ b/sources/talk/20190515 Extreme addresses networked-IoT security.md
@@ -0,0 +1,71 @@
+[#]: collector: (lujun9972)
+[#]: translator: ( )
+[#]: reviewer: ( )
+[#]: publisher: ( )
+[#]: url: ( )
+[#]: subject: (Extreme addresses networked-IoT security)
+[#]: via: (https://www.networkworld.com/article/3395539/extreme-addresses-networked-iot-security.html)
+[#]: author: (Michael Cooney https://www.networkworld.com/author/Michael-Cooney/)
+
+Extreme addresses networked-IoT security
+======
+The ExtremeAI security app features machine learning that can understand typical behavior of IoT devices and alert when it finds anomalies.
+![Getty Images][1]
+
+[Extreme Networks][2] has taken the wraps off a new security application it says will use machine learning and artificial intelligence to help customers effectively monitor, detect and automatically remediate security issues with networked IoT devices.
+
+The application – ExtremeAI security—features machine-learning technology that can understand typical behavior of IoT devices and automatically trigger alerts when endpoints act in unusual or unexpected ways, Extreme said.
+
+**More about edge networking**
+
+ * [How edge networking and IoT will reshape data centers][3]
+ * [Edge computing best practices][4]
+ * [How edge computing can help secure the IoT][5]
+
+
+
+Extreme said that the ExtremeAI Security application can tie into all leading threat intelligence feeds, and had close integration with its existing [Extreme Workflow Composer][6] to enable automatic threat mitigation and remediation.
+
+The application integrates the company’s ExtremeAnalytics application which lets customers view threats by severity, category, high-risk endpoints and geography. An automated ticketing feature integrates with variety of popular IT tools such as Slack, Jira, and ServiceNow, and the application interoperates with many popular security tools, including existing network taps, the vendor stated.
+
+There has been an explosion of new endpoints ranging from million-dollar smart MRI machines to five-dollar sensors, which creates a complex and difficult job for network and security administrators, said Abby Strong, vice president of product marketing for Extreme. “We need smarter, secure and more self-healing networks especially where IT cybersecurity resources are stretched to the limit.”
+
+Extreme is trying to address an issue that is important to enterprise-networking customers: how to get actionable, usable insights as close to real-time as possible, said Rohit Mehra, Vice President of Network Infrastructure at IDC. “Extreme is melding automation, analytics and security that can look at network traffic patterns and allow the system to take action when needed.”
+
+The ExtremeAI application, which will be available in October, is but one layer of IoT security Extreme offers. Already on the market, its [Defender for IoT][7] package, which includes a Defender application and adapter, lets customers monitor, set policies and isolate IoT devices across an enterprise.
+
+**[[Prepare to become a Certified Information Security Systems Professional with this comprehensive online course from PluralSight. Now offering a 10-day free trial!][8] ]**
+
+The Extreme AI and Defender packages are now part of what the company calls Extreme Elements, which is a menu of its new and existing Smart OmniEdge, Automated Campus and Agile Data Center software, hardware and services that customers can order to build a manageable, secure system.
+
+Aside from the applications, the Elements include Extreme Management Center, the company’s network management software; the company’s x86-based intelligent appliances, including the ExtremeCloud Appliance; and [ExtremeSwitching X465 premium][9], a stackable multi-rate gigabit Ethernet switch.
+
+The switch and applications are just the beginning of a very busy time for Extreme. In its [3Q earnings cal][10]l this month company CEO Ed Meyercord noted Extreme was in the “early stages of refreshing 70 percent of our products” and seven different products will become generally available this quarter – a record for Extreme, he said.
+
+Join the Network World communities on [Facebook][11] and [LinkedIn][12] to comment on topics that are top of mind.
+
+--------------------------------------------------------------------------------
+
+via: https://www.networkworld.com/article/3395539/extreme-addresses-networked-iot-security.html
+
+作者:[Michael Cooney][a]
+选题:[lujun9972][b]
+译者:[译者ID](https://github.com/译者ID)
+校对:[校对者ID](https://github.com/校对者ID)
+
+本文由 [LCTT](https://github.com/LCTT/TranslateProject) 原创编译,[Linux中国](https://linux.cn/) 荣誉推出
+
+[a]: https://www.networkworld.com/author/Michael-Cooney/
+[b]: https://github.com/lujun9972
+[1]: https://images.idgesg.net/images/article/2019/02/iot_security_tablet_conference_digital-100787102-large.jpg
+[2]: https://www.networkworld.com/article/3289508/extreme-facing-challenges-girds-for-future-networking-battles.html
+[3]: https://www.networkworld.com/article/3291790/data-center/how-edge-networking-and-iot-will-reshape-data-centers.html
+[4]: https://www.networkworld.com/article/3331978/lan-wan/edge-computing-best-practices.html
+[5]: https://www.networkworld.com/article/3331905/internet-of-things/how-edge-computing-can-help-secure-the-iot.html
+[6]: https://www.extremenetworks.com/product/workflow-composer/
+[7]: https://www.extremenetworks.com/product/extreme-defender-for-iot/
+[8]: https://pluralsight.pxf.io/c/321564/424552/7490?u=https%3A%2F%2Fwww.pluralsight.com%2Fpaths%2Fcertified-information-systems-security-professional-cisspr
+[9]: https://community.extremenetworks.com/extremeswitching-exos-223284/extremexos-30-2-and-smart-omniedge-premium-x465-switches-are-now-available-7823377
+[10]: https://seekingalpha.com/news/3457137-extreme-networks-minus-15-percent-quarterly-miss-light-guidance
+[11]: https://www.facebook.com/NetworkWorld/
+[12]: https://www.linkedin.com/company/network-world
diff --git a/sources/talk/20190515 IBM overhauls mainframe-software pricing, adds hybrid, private-cloud services.md b/sources/talk/20190515 IBM overhauls mainframe-software pricing, adds hybrid, private-cloud services.md
new file mode 100644
index 0000000000..b69109641d
--- /dev/null
+++ b/sources/talk/20190515 IBM overhauls mainframe-software pricing, adds hybrid, private-cloud services.md
@@ -0,0 +1,77 @@
+[#]: collector: (lujun9972)
+[#]: translator: ( )
+[#]: reviewer: ( )
+[#]: publisher: ( )
+[#]: url: ( )
+[#]: subject: (IBM overhauls mainframe-software pricing, adds hybrid, private-cloud services)
+[#]: via: (https://www.networkworld.com/article/3395776/ibm-overhauls-mainframe-software-pricing-adds-hybrid-private-cloud-services.html)
+[#]: author: (Michael Cooney https://www.networkworld.com/author/Michael-Cooney/)
+
+IBM overhauls mainframe-software pricing, adds hybrid, private-cloud services
+======
+IBM brings cloud consumption model to the mainframe, adds Docker container extensions
+![Thinkstock][1]
+
+IBM continues to adopt new tools and practices for its mainframe customers to keep the Big Iron relevant in a cloud world.
+
+First of all, the company switched-up its 20-year mainframe software pricing scheme to make it more palatable to hybrid and multicloud users who might be thinking of moving workloads off the mainframe and into the cloud.
+
+**[ Check out[What is hybrid cloud computing][2] and learn [what you need to know about multi-cloud][3]. | Get regularly scheduled insights by [signing up for Network World newsletters][4]. ]**
+
+Specifically IBM rolled out Tailored Fit Pricing for the IBM Z mainframe which offers two consumption-based pricing models that can help customers cope with ever-changing workload – and hence software – costs.
+
+Tailored Fit Pricing removes the need for complex and restrictive capping, which typically weakens responsiveness and can impact service level availability, IBM said. IBM’s standard monthly mainframe licensing model calculates costs as a “rolling four-hour average” (R4HA) which would determine cost based on a customer’s peak usage during the month. Customers would many time cap usage to keep costs down, experts said
+
+Systems can now be configured to support optimal response times and service level agreements, rather than artificially slowing down workloads to manage software licensing costs, IBM stated.
+
+Predicting demand for IT services can be a major challenge and in the era of hybrid and multicloud, everything is connected and workload patterns constantly change, wrote IBM’s Ross Mauri, General Manager, IBM Z in a [blog][5] about the new pricing and services. “In this environment, managing demand for IT services can be a major challenge. As more customers shift to an enterprise IT model that incorporates on-premises, private cloud and public we’ve developed a simple cloud pricing model to drive the transformation forward.”
+
+[Tailored Fit Pricing][6] for IBM Z comes in two flavors, the Enterprise Consumption Solution and the Enterprise Capacity Solution.
+
+IBM said the Enterprise Consumption model is a tailored usage-based pricing model, where customers pay only for what they use, removing the need for complex and restrictive capping, IBM said.
+
+The Enterprise Capacity model lets customers mix and match workloads to help maximize use of the full capacity of the platform. Charges are referenced to the overall size of the physical environment and are calculated based on the estimated mix of workloads running, while providing the flexibility to vary actual usage across workloads, IBM said.
+
+The software pricing changes should be a welcome benefit to customers, experts said.
+
+“By making access to Z mainframes more flexible and ‘cloud-like,’ IBM is making it less likely that customers will consider shifting Z workloads to other systems and environments. As cloud providers become increasingly able to support mission critical applications, that’s a big deal,” wrote Charles King, president and principal analyst for Pund-IT in a [blog][7] about the IBM changes.
+
+“A notable point about both models is that discounted growth pricing is offered on all workloads – whether they be 40-year old Assembler programs or 4-day old JavaScript apps. This is in contrast to previous models which primarily rewarded only brand-new applications with growth pricing. By thinking outside the Big Iron box, the company has substantially eased the pain for its largest clients’ biggest mainframe-related headaches,” King wrote.
+
+IBM’s Tailored Fit Pricing supports an increasing number of enterprises that want to continue to grow and build new services on top of this mission-critical platform, wrote [John McKenny][8] vice president of strategy for ZSolutions Optimization at BMC Software. “In not yet released results from the 2019 BMC State of the Mainframe Survey, 62% of the survey respondents reported that they are planning to expand MIPS/MSU consumption and are growing their mainframe workloads. For customers with no current plans for growth, the affordability and cost-competitiveness of the new pricing model will re-ignite interest in also using this platform as an integral part of their hybrid cloud strategies.”
+
+In addition to the pricing, IBM announced some new services that bring the mainframe closer to cloud workloads.
+
+First, IBM rolled out z/OS Container Extensions (zCX), which makes it possible to run Linux on Z applications that are packaged as Docker Container images on z/OS. Application developers can develop and data centers can operate popular open source packages, Linux applications, IBM software, and third-party software together with z/OS applications and data, IBM said. zCX will let customers use the latest open source tools, popular NoSQL databases, analytics frameworks, application servers, and so on within the z/OS environment.
+
+“With z/OS Container Extensions, customers will be able to access the most recent development tools and processes available in Linux on the Z ecosystem, giving developers the flexibility to build new, cloud-native containerized apps and deploy them on z/OS without requiring Linux or a Linux partition,” IBM’s Mauri stated.
+
+Big Blue also rolled out z/OS Cloud Broker which will let customers access and deploy z/OS resources and services on [IBM Cloud Private][9]. [IBM Cloud Private][10] is the company’s Kubernetes-based Platform as a Service (PaaS) environment for developing and managing containerized applications. IBM said z/OS Cloud Broker is designed to help cloud application developers more easily provision and deprovision apps in z/OS environments.
+
+Join the Network World communities on [Facebook][11] and [LinkedIn][12] to comment on topics that are top of mind.
+
+--------------------------------------------------------------------------------
+
+via: https://www.networkworld.com/article/3395776/ibm-overhauls-mainframe-software-pricing-adds-hybrid-private-cloud-services.html
+
+作者:[Michael Cooney][a]
+选题:[lujun9972][b]
+译者:[译者ID](https://github.com/译者ID)
+校对:[校对者ID](https://github.com/校对者ID)
+
+本文由 [LCTT](https://github.com/LCTT/TranslateProject) 原创编译,[Linux中国](https://linux.cn/) 荣誉推出
+
+[a]: https://www.networkworld.com/author/Michael-Cooney/
+[b]: https://github.com/lujun9972
+[1]: https://images.techhive.com/images/article/2015/08/thinkstockphotos-520137237-100610459-large.jpg
+[2]: https://www.networkworld.com/article/3233132/cloud-computing/what-is-hybrid-cloud-computing.html
+[3]: https://www.networkworld.com/article/3252775/hybrid-cloud/multicloud-mania-what-to-know.html
+[4]: https://www.networkworld.com/newsletters/signup.html
+[5]: https://www.ibm.com/blogs/systems/ibm-z-defines-the-future-of-hybrid-cloud/
+[6]: https://www-01.ibm.com/common/ssi/cgi-bin/ssialias?infotype=AN&subtype=CA&htmlfid=897/ENUS219-014&appname=USN
+[7]: https://www.pund-it.com/blog/ibm-reinvents-the-z-mainframe-again/
+[8]: https://www.bmc.com/blogs/bmc-supports-ibm-tailored-fit-pricing-ibm-z/
+[9]: https://www.ibm.com/marketplace/cloud-private-on-z-and-linuxone
+[10]: https://www.networkworld.com/article/3340043/ibm-marries-on-premises-private-and-public-cloud-data.html
+[11]: https://www.facebook.com/NetworkWorld/
+[12]: https://www.linkedin.com/company/network-world
diff --git a/sources/talk/20190516 Will 5G be the first carbon-neutral network.md b/sources/talk/20190516 Will 5G be the first carbon-neutral network.md
new file mode 100644
index 0000000000..decacfac5d
--- /dev/null
+++ b/sources/talk/20190516 Will 5G be the first carbon-neutral network.md
@@ -0,0 +1,88 @@
+[#]: collector: (lujun9972)
+[#]: translator: ( )
+[#]: reviewer: ( )
+[#]: publisher: ( )
+[#]: url: ( )
+[#]: subject: (Will 5G be the first carbon-neutral network?)
+[#]: via: (https://www.networkworld.com/article/3395465/will-5g-be-the-first-carbon-neutral-network.html)
+[#]: author: (Patrick Nelson https://www.networkworld.com/author/Patrick-Nelson/)
+
+Will 5G be the first carbon-neutral network?
+======
+Increased energy consumption in new wireless networks could become ecologically unsustainable. Engineers think they have solutions that apply to 5G, but all is not certain.
+![Dushesina/Getty Images][1]
+
+If wireless networks transfer 1,000 times more data, does that mean they will use 1,000 times more energy? It probably would with the old 4G LTE wireless technologies— LTE doesn’t have much of a sleep-standby. But with 5G, we might have a more energy-efficient option.
+
+More customers want Earth-friendly options, and engineers are now working on how to achieve it — meaning 5G might introduce the first zero-carbon networks. It’s not all certain, though.
+
+**[ Related:[What is 5G wireless? And how it will change networking as we know it][2] ]**
+
+“When the 4G technology for wireless communication was developed, not many people thought about how much energy is consumed in transmitting bits of information,” says Emil Björnson, associate professor of communication systems at Linkoping University, [in an article on the school’s website][3].
+
+Standby was never built into 4G, Björnson explains. Reasons include overbuilding — the architects wanted to ensure connections didn’t fail, so they just kept the power up. The downside to that redundancy was that almost the same amount of energy is used whether the system is transmitting data or not.
+
+“We now know that this is not necessary,” Björnson says. 5G networks don’t use much power during periods of low traffic, and that reduces power consumption.
+
+Björnson says he knows how to make future-networks — those 5G networks that one day may become the enterprise broadband replacement — super efficient even when there is heavy use. Massive-MIMO (multiple-in, multiple-out) antennas are the answer, he says. That’s hundreds of connected antennas taking advantage of multipath.
+
+I’ve written before about some of Björnson's Massive-MIMO ideas. He thinks [Massive-MIMO will remove all capacity ceilings from wireless networks][4]. However, he now adds calculations to his research that he claims prove that the Massive-MIMO antenna technology will also reduce power use. He and his group are actively promoting their academic theories in a paper ([pdf][5]).
+
+**[[Take this mobile device management course from PluralSight and learn how to secure devices in your company without degrading the user experience.][6] ]**
+
+### Nokia's plan to reduce wireless networks' CO2 emissions
+
+Björnson's isn’t the only 5G-aimed eco-concept out there. Nokia points out that it isn't just radios transmitting that use electricity. Cooling is actually the main electricity hog, says the telcommunications company, which is one of the world’s principal manufacturers of mobile network equipment.
+
+Nokia says the global energy cost of Radio Access Networks (RANs) in 2016 (the last year numbers were available), which includes base transceiver stations (BTSs) needed by mobile networks, was around $80 billion. That figure increases with more users coming on stream, something that’s probable. Of the BTS’s electricity use, about 90% “converts to waste heat,” [Harry Kuosa, a marketing executive, writes on Nokia’s blog][7]. And base station sites account for about 80% of a mobile network’s entire energy use, Nokia expands on its website.
+
+“A thousand-times more traffic that creates a thousand-times higher energy costs is unsustainable,” Nokia says in its [ebook][8] on the subject, “Turning the zero carbon vision into business opportunity,” and it’s why Nokia plans liquid-cooled 5G base stations among other things, including chip improvements. It says the liquid-cooling can reduce CO2 emissions by up to 80%.
+
+### Will those ideas work?
+
+Not all agree power consumption can be reduced when implementing 5G, though. Gabriel Brown of Heavy Reading, quotes [in a tweet][9] a China Mobile executive as saying that 5G BTSs will use three times as much power as 4G LTE ones because the higher frequencies used in 5G mean one needs more BTS units to provide the same geographic coverage: For physics reasons, higher frequencies equals shorter range.
+
+If, as is projected, 5G develops into the new enterprise broadband for the internet of things (IoT), along with associated private networks covering everything else, then these eco- and cost-important questions are going to be salient — and they need answers quickly. 5G will soon be here, and [Gartner estimates that 60% of organizations will adopt it][10].
+
+**More about 5G networks:**
+
+ * [How enterprises can prep for 5G networks][11]
+ * [5G vs 4G: How speed, latency and apps support differ][12]
+ * [Private 5G networks are coming][13]
+ * [5G and 6G wireless have security issues][14]
+ * [How millimeter-wave wireless could help support 5G and IoT][15]
+
+
+
+Join the Network World communities on [Facebook][16] and [LinkedIn][17] to comment on topics that are top of mind.
+
+--------------------------------------------------------------------------------
+
+via: https://www.networkworld.com/article/3395465/will-5g-be-the-first-carbon-neutral-network.html
+
+作者:[Patrick Nelson][a]
+选题:[lujun9972][b]
+译者:[译者ID](https://github.com/译者ID)
+校对:[校对者ID](https://github.com/校对者ID)
+
+本文由 [LCTT](https://github.com/LCTT/TranslateProject) 原创编译,[Linux中国](https://linux.cn/) 荣誉推出
+
+[a]: https://www.networkworld.com/author/Patrick-Nelson/
+[b]: https://github.com/lujun9972
+[1]: https://images.idgesg.net/images/article/2019/01/4g-versus-5g_horizon_sunrise-100784230-large.jpg
+[2]: https://www.networkworld.com/article/3203489/lan-wan/what-is-5g-wireless-networking-benefits-standards-availability-versus-lte.html
+[3]: https://liu.se/en/news-item/okningen-av-mobildata-kraver-energieffektivare-nat
+[4]: https://www.networkworld.com/article/3262991/future-wireless-networks-will-have-no-capacity-limits.html
+[5]: https://arxiv.org/pdf/1812.01688.pdf
+[6]: https://pluralsight.pxf.io/c/321564/424552/7490?u=https%3A%2F%2Fwww.pluralsight.com%2Fcourses%2Fmobile-device-management-big-picture
+[7]: https://www.nokia.com/blog/nokia-has-ambitious-plans-reduce-network-power-consumption/
+[8]: https://pages.nokia.com/2364.Zero.Emissions.ebook.html?did=d000000001af&utm_campaign=5g_in_action_&utm_source=twitter&utm_medium=organic&utm_term=0dbf430c-1c94-47d7-8961-edc4f0ba3270
+[9]: https://twitter.com/Gabeuk/status/1099709788676636672?ref_src=twsrc%5Etfw%7Ctwcamp%5Etweetembed%7Ctwterm%5E1099709788676636672&ref_url=https%3A%2F%2Fwww.lightreading.com%2Fmobile%2F5g%2Fpower-consumption-5g-basestations-are-hungry-hungry-hippos%2Fd%2Fd-id%2F749979
+[10]: https://www.gartner.com/en/newsroom/press-releases/2018-12-18-gartner-survey-reveals-two-thirds-of-organizations-in
+[11]: https://www.networkworld.com/article/3306720/mobile-wireless/how-enterprises-can-prep-for-5g.html
+[12]: https://www.networkworld.com/article/3330603/mobile-wireless/5g-versus-4g-how-speed-latency-and-application-support-differ.html
+[13]: https://www.networkworld.com/article/3319176/mobile-wireless/private-5g-networks-are-coming.html
+[14]: https://www.networkworld.com/article/3315626/network-security/5g-and-6g-wireless-technologies-have-security-issues.html
+[15]: https://www.networkworld.com/article/3291323/mobile-wireless/millimeter-wave-wireless-could-help-support-5g-and-iot.html
+[16]: https://www.facebook.com/NetworkWorld/
+[17]: https://www.linkedin.com/company/network-world
diff --git a/sources/talk/20190517 HPE to buy Cray, offer HPC as a service.md b/sources/talk/20190517 HPE to buy Cray, offer HPC as a service.md
new file mode 100644
index 0000000000..a1dafef683
--- /dev/null
+++ b/sources/talk/20190517 HPE to buy Cray, offer HPC as a service.md
@@ -0,0 +1,68 @@
+[#]: collector: (lujun9972)
+[#]: translator: ( )
+[#]: reviewer: ( )
+[#]: publisher: ( )
+[#]: url: ( )
+[#]: subject: (HPE to buy Cray, offer HPC as a service)
+[#]: via: (https://www.networkworld.com/article/3396220/hpe-to-buy-cray-offer-hpc-as-a-service.html)
+[#]: author: (Tim Greene https://www.networkworld.com/author/Tim-Greene/)
+
+HPE to buy Cray, offer HPC as a service
+======
+High-performance computing offerings from HPE plus Cray could enable things like AI, ML, high-speed financial trading, creation digital twins for entire enterprise networks.
+![Cray Inc.][1]
+
+HPE has agreed to buy supercomputer-maker Cray for $1.3 billion, a deal that the companies say will bring their corporate customers high-performance computing as a service to help with analytics needed for artificial intelligence and machine learning, but also products supporting high-performance storage, compute and software.
+
+In addition to bringing HPC capabilities that can blend with and expand HPE’s current products, Cray brings with it customers in government and academia that might be interested in HPE’s existing portfolio as well.
+
+**[ Now read:[Who's developing quantum computers][2] ]**
+
+The companies say they expect to close the cash deal by the end of next April.
+
+The HPC-as-a-service would be offered through [HPE GreenLake][3], the company’s public-, private-, hybrid-cloud service. Such a service could address periodic enterprise need for fast computing that might otherwise be too expensive, says Tim Zimmerman, an analyst with Gartner.
+
+Businesses could use the service, for example, to create [digital twins][4] of their entire networks and use them to test new code to see how it will impact the network before deploying it live, Zimmerman says.
+
+Cray has HPC technology that HPE Labs might be exploring on its own, but that can be brought to market in a much quicker timeframe.
+
+HPE says that overall, buying cray give it technologies needed for massively data-intensive workloads such as AI and ML that is used for engineering services, transaction-based trading by financial firms, pharmaceutical research and academic studies into weather and genomes, for instance, Zimmerman says.
+
+As HPE puts it, Cray supercomputing platforms “have the ability to handle massive data sets, converged modelling, simulation, AI and analytics workloads.”
+
+Cray is working on [what it says will be the world’s fastest supercomputer][5] when it’s finished in 2021, cranking out 1.5 exaflops. The current fastest supercomputer is 143.5 petaflops. [Click [here][6] to see the current top 10 fastest supercomputers.]
+
+In general, HPE says it hopes to create a comprehensive line of products to support HPC infrastructure including “compute, high-performance storage, system interconnects, software and services.”
+
+Together, the talent in the two companies and their combined technologies should be able to increase innovation, HPE says.
+
+Earlier this month, HPE’s CEO Antonio Neri said in [an interview with _Network World_][7] that the company will be investing $4 billion over four years in a range of technology to boost “connectivity, security, and obviously cloud and analytics.” In laying out the company’s roadmap he made no specific mention of HPC.
+
+HPE net revenues last fiscal year were $30.9 billion. Cray’s total revenue was $456 million, with a gross profit of $130 million.
+
+The acquisition will pay $35 per share for Cray stock.
+
+Join the Network World communities on [Facebook][8] and [LinkedIn][9] to comment on topics that are top of mind.
+
+--------------------------------------------------------------------------------
+
+via: https://www.networkworld.com/article/3396220/hpe-to-buy-cray-offer-hpc-as-a-service.html
+
+作者:[Tim Greene][a]
+选题:[lujun9972][b]
+译者:[译者ID](https://github.com/译者ID)
+校对:[校对者ID](https://github.com/校对者ID)
+
+本文由 [LCTT](https://github.com/LCTT/TranslateProject) 原创编译,[Linux中国](https://linux.cn/) 荣誉推出
+
+[a]: https://www.networkworld.com/author/Tim-Greene/
+[b]: https://github.com/lujun9972
+[1]: https://images.idgesg.net/images/article/2018/06/the_cray_xc30_piz_daint_system_at_the_swiss_national_supercomputing_centre_via_cray_inc_3x2_978x652-100762113-large.jpg
+[2]: https://www.networkworld.com/article/3275385/who-s-developing-quantum-computers.html
+[3]: https://www.networkworld.com/article/3280996/hpe-adds-greenlake-hybrid-cloud-to-enterprise-service-offerings.html
+[4]: https://www.networkworld.com/article/3280225/what-is-digital-twin-technology-and-why-it-matters.html
+[5]: https://www.networkworld.com/article/3373539/doe-plans-worlds-fastest-supercomputer.html
+[6]: https://www.networkworld.com/article/3236875/embargo-10-of-the-worlds-fastest-supercomputers.html
+[7]: https://www.networkworld.com/article/3394879/hpe-s-ceo-lays-out-his-technology-vision.html
+[8]: https://www.facebook.com/NetworkWorld/
+[9]: https://www.linkedin.com/company/network-world
diff --git a/sources/talk/20190517 The modern data center and the rise in open-source IP routing suites.md b/sources/talk/20190517 The modern data center and the rise in open-source IP routing suites.md
new file mode 100644
index 0000000000..02063687a0
--- /dev/null
+++ b/sources/talk/20190517 The modern data center and the rise in open-source IP routing suites.md
@@ -0,0 +1,140 @@
+[#]: collector: (lujun9972)
+[#]: translator: ( )
+[#]: reviewer: ( )
+[#]: publisher: ( )
+[#]: url: ( )
+[#]: subject: (The modern data center and the rise in open-source IP routing suites)
+[#]: via: (https://www.networkworld.com/article/3396136/the-modern-data-center-and-the-rise-in-open-source-ip-routing-suites.html)
+[#]: author: (Matt Conran https://www.networkworld.com/author/Matt-Conran/)
+
+The modern data center and the rise in open-source IP routing suites
+======
+Open source enables passionate people to come together and fabricate work of phenomenal quality. This is in contrast to a single vendor doing everything.
+![fdecomite \(CC BY 2.0\)][1]
+
+As the cloud service providers and search engines started with the structuring process of their business, they quickly ran into the problems of managing the networking equipment. Ultimately, after a few rounds of getting the network vendors to understand their problems, these hyperscale network operators revolted.
+
+Primarily, what the operators were looking for was a level of control in managing their network which the network vendors couldn’t offer. The revolution burned the path that introduced open networking, and network disaggregation to the work of networking. Let us first learn about disaggregation followed by open networking.
+
+### Disaggregation
+
+The concept of network disaggregation involves breaking-up of the vertical networking landscape into individual pieces, where each piece can be used in the best way possible. The hardware can be separated from the software, along with open or closed IP routing suites. This enables the network operators to use the best of breed for the hardware, software and the applications.
+
+**[ Now see[7 free network tools you must have][2]. ]**
+
+Networking has always been built as an appliance and not as a platform. The mindset is that the network vendor builds an appliance and as a specialized appliance, they will completely control what you can and cannot do on that box. In plain words, they will not enable anything that is not theirs. As a result, they act as gatekeepers and not gate-enablers.
+
+Network disaggregation empowers the network operators with the ability to lay hands on the features they need when they need them. However, this is impossible in case of non-disaggregated hardware.
+
+### Disaggregation leads to using best-of-breed
+
+In the traditional vertically integrated networking market, you’re forced to live with the software because you like the hardware, or vice-versa. But network disaggregation drives different people to develop things that matter to them. This allows multiple groups of people to connect, with each one focused on doing what he or she does the best. Switching silicon manufacturers can provide the best merchant silicon. Routing suites can be provided by those who are the best at that. And the OS vendors can provide the glue that enables all of these to work well together.
+
+With disaggregation, people are driven to do what they are good at. One company does the hardware, whereas another does the software and other company does the IP routing suites. Hence, today the networking world looks like more of the server world.
+
+### Open source
+
+Within this rise of the modern data center, there is another element that is driving network disaggregation; the notion of open source. Open source is “denoting software for which the original source code is made freely available, it may be redistributed and modified.” It enables passionate people to come together and fabricate work of phenomenal quality. This is in contrast to a single vendor doing everything.
+
+As a matter of fact, the networking world has always been very vendor driven. However, the advent of open source gives the opportunity to like-minded people rather than the vendor controlling the features. This eliminates the element of vendor lock-in, thereby enabling interesting work. Open source allows more than one company to be involved.
+
+### Open source in the data center
+
+The traditional enterprise and data center networks were primarily designed by bridging and Spanning Tree Protocol (STP). However, the modern data center is driven by IP routing and the CLOS topology. As a result, you need a strong IP routing suite.
+
+That was the point where the need for an open-source routing suite surfaced, the suite that can help drive the modern data center. The primary open-source routing suites are [FRRouting (FRR)][3], BIRD, GoBGP and ExaBGP.
+
+Open-source IP routing protocol suites are slowly but steadily gaining acceptance and are used in data centers of various sizes. Why? It is because they allow a community of developers and users to work on finding solutions to common problems. Open-source IP routing protocol suites equip them to develop the specific features that they need. It also helps the network operators to create simple designs that make sense to them, as opposed to having everything controlled by the vendor. They also enable routing suites to run on compute nodes. Kubernetes among others uses this model of running a routing protocol on a compute node.
+
+Today many startups are using FRR. Out of all of the IP routing suites, FRR is preferred in the data center as the primary open-source IP routing protocol suite. Some traditional network vendors have even demonstrated the use of FRR on their networking gear.
+
+There are lots of new features currently being developed for FRR, not just by the developers but also by the network operators.
+
+### Use cases for open-source routing suites
+
+When it comes to use-cases, where do IP routing protocol suites sit? First and foremost, if you want to do any type of routing in the disaggregated network world, you need an IP routing suite.
+
+Some operators are using FRR at the edge of the network as well, thereby receiving full BGP feeds. Many solutions which use Intel’s DPDK for packet forwarding use FRR as the control plane, receiving full BGP feeds. In addition, there are other vendors using FRR as the core IP routing suite for a full leaf and spine data center architecture. You can even get a version of FRR on pfSense which is a free and open source firewall.
+
+We need to keep in mind that reference implementations are important. Open source allows you to test at scale. But vendors don’t allow you to do that. However, with FRR, we have the ability to spin up virtual machines (VMs) or even containers by using software like Vagrant to test your network. Some vendors do offer software versions, but they are not fully feature-compatible.
+
+Also, with open source you do not need to wait. This empowers you with flexibility and speed which drives the modern data center.
+
+### Deep dive on FRRouting (FRR)
+
+FRR is a Linux foundation project. In a technical Linux sense, FRR is a group of daemons that work together, providing a complete routing suite that includes BGP, IS-IS, LDP, OSPF, BFD, PIM, and RIP.
+
+Each one of these daemons communicate with the common routing information base (RIB) daemon called Zebra in order to interface with the OS and to resolve conflicts between the multiple routing protocols providing the same information. Interfacing with the OS is used to receive the link up/down events, to add and delete routes etc.
+
+### FRRouting (FRR) components: Zebra
+
+Zebra is the RIB of the routing systems. It knows everything about the state of the system relevant to routing and is able to pass and disseminate this information to all the interested parties.
+
+The RIB in FRR acts just like a traditional RIB. When a route wins, it goes into the Linux kernel data plane where the forwarding occurs. All of the routing protocols run as separate processes and each of them have their source code in FRR.
+
+For example, when BGP starts up, it needs to know, for instance, what kind of virtual routing and forwarding (VRF) and IP interfaces are available. Zebra collects and passes this information back to the interested daemons. It passes all the relevant information about state of the machine.
+
+Furthermore, you can also register information with Zebra. For example, if a particular route changes, the daemon can be informed. This can also be used for reverse path forwarding (RPF). FRR doesn't need to do a pull when changes happen on the network.
+
+There are a myriad of ways through which you can control Linux and the state. Sometimes you have to use options like the Netlink bus and sometimes you may need to read the state in proc file system of Linux. The goal of Zebra is to gather all this data for the upper level protocols.
+
+### FRR supports remote data planes
+
+FRR also has the ability to manage the remote data planes. So, what does this mean? Typically, the data forwarding plane and the routing protocols run on the same box. Another model, adopted by Openflow and SDN for example, is one in which the data forwarding plane can be on one box while FRR runs on a different box on behalf of the first box and pushes the computed routing state on the first box. In other words, the data plane and the control plane run on different boxes.
+
+If you examine the traditional world, it’s like having one large chassis with different line cards with the ability to install routes in those different line cards. FRR operates with the same model which has one control plane and the capability to offer 3 boxes, if needed. It does this via the forwarding plane manager.
+
+### Forwarding plane manager
+
+Zebra can either install routes directly into the data plane of the box it is running on or use a forwarding plane manager to install routes on a remote box. When it installs a route, the forwarding plane manager abstracts the data which displays the route and the next hops. It then pushes the data to a remote system where the remote machine processes it and programs the ASIC appropriately.
+
+After the data is abstracted, you can use whatever protocol you want in order to push the data to the remote machine. You can even include the data in an email.
+
+### What is holding people back from open source?
+
+Since last 30 years the networking world meant that you need to go to a vendor to solve a problem. But now with open-source routing suites, such as, FRR, there is a major drift in the mindset as to how you approach troubleshooting.
+
+This causes the fear of not being able to use it properly because with open source you are the one who has to fix it. This at first can be scary and daunting. But it doesn’t necessarily have to be. Also, to switch to FRR on a traditional network gear, you need the vendor to enable it, but they may be reluctant as they are on competing platforms which can be another road blocker.
+
+### The future of FRR
+
+If we examine FRR from the use case perspective of the data center, FRR is feature-complete. Anyone building an IP based data center FRR has everything available. The latest 7.0 release of FRR adds Yang/NetConf, BGP Enhancements and OpenFabric.
+
+FRR is not just about providing features, boosting the performance or being the same as or better than the traditional network vendor’s software, it is also about simplifying the process for the end user.
+
+Since the modern data center is focused on automation and ease of use, FRR has made such progress that the vendors have not caught up with. FRR is very automation friendly. For example, FRR takes BGP and makes it automation-friendly without having to change the protocol. It supports BGP unnumbered that is unmatched by any other vendor suite. This is where the vendors are trying to catch up.
+
+Also, while troubleshooting, FRR shows peer’s and host’s names and not just the IP addresses. This allows you to understand without having spent much time. However, vendors show the peer’s IP addresses which can be daunting when you need to troubleshoot.
+
+FRR provides the features that you need to run an efficient network and data center. It makes easier to configure and manage the IP routing suite. Vendors just add keep adding features over features whether they are significant or not. Then you need to travel the certification paths that teach you how to twiddle 20 million nobs. How many of those networks are robust and stable?
+
+FRR is about supporting features that matter and not every imaginable feature. FRR is an open source project that brings like-minded people together, good work that is offered isn’t turned away. As a case in point, FRR has an open source implementation of EIGRP.
+
+The problem surfaces when you see a bunch of things, you think you need them. But in reality, you should try to keep the network as simple as possible. FRR is laser-focused on the ease of use and simplifying the use rather than implementing features that are mostly not needed to drive the modern data center.
+
+For more information and to contribute, why not join the [FRR][4] [mailing list group][4].
+
+**This article is published as part of the IDG Contributor Network.[Want to Join?][5]**
+
+Join the Network World communities on [Facebook][6] and [LinkedIn][7] to comment on topics that are top of mind.
+
+--------------------------------------------------------------------------------
+
+via: https://www.networkworld.com/article/3396136/the-modern-data-center-and-the-rise-in-open-source-ip-routing-suites.html
+
+作者:[Matt Conran][a]
+选题:[lujun9972][b]
+译者:[译者ID](https://github.com/译者ID)
+校对:[校对者ID](https://github.com/校对者ID)
+
+本文由 [LCTT](https://github.com/LCTT/TranslateProject) 原创编译,[Linux中国](https://linux.cn/) 荣誉推出
+
+[a]: https://www.networkworld.com/author/Matt-Conran/
+[b]: https://github.com/lujun9972
+[1]: https://images.idgesg.net/images/article/2018/12/modular_humanoid_polyhedra_connections_structure_building_networking_by_fdecomite_cc_by_2-0_via_flickr_1200x800-100782334-large.jpg
+[2]: https://www.networkworld.com/article/2825879/7-free-open-source-network-monitoring-tools.html
+[3]: https://frrouting.org/community/7.0-launch.html
+[4]: https://frrouting.org/#participate
+[5]: /contributor-network/signup.html
+[6]: https://www.facebook.com/NetworkWorld/
+[7]: https://www.linkedin.com/company/network-world
diff --git a/sources/talk/20190521 Enterprise IoT- Companies want solutions in these 4 areas.md b/sources/talk/20190521 Enterprise IoT- Companies want solutions in these 4 areas.md
new file mode 100644
index 0000000000..9df4495f05
--- /dev/null
+++ b/sources/talk/20190521 Enterprise IoT- Companies want solutions in these 4 areas.md
@@ -0,0 +1,119 @@
+[#]: collector: (lujun9972)
+[#]: translator: ( )
+[#]: reviewer: ( )
+[#]: publisher: ( )
+[#]: url: ( )
+[#]: subject: (Enterprise IoT: Companies want solutions in these 4 areas)
+[#]: via: (https://www.networkworld.com/article/3396128/the-state-of-enterprise-iot-companies-want-solutions-for-these-4-areas.html)
+[#]: author: (Fredric Paul https://www.networkworld.com/author/Fredric-Paul/)
+
+Enterprise IoT: Companies want solutions in these 4 areas
+======
+Based on customer pain points, PwC identified four areas companies are seeking enterprise solutions for, including energy use and sustainability.
+![Jackie Niam / Getty Images][1]
+
+Internet of things (IoT) vendors and pundits like to crow about the billions and billions of connected devices that make the IoT so ubiquitous and powerful. But how much of that installed base is really relevant to the enterprise?
+
+To find out, I traded emails with Rob Mesirow, principal at [PwC’s Connected Solutions][2], the firm’s new one-stop-shop of IoT solutions, who suggests that consumer adoption may not paint a true picture of the enterprise opportunities. If you remove the health trackers and the smart thermostats from the market, he suggested, there are very few connected devices left.
+
+So, I wondered, what is actually happening on the enterprise side of IoT? What kinds of devices are we talking about, and in what kinds of numbers?
+
+**[ Read also:[Forget 'smart homes,' the new goal is 'autonomous buildings'][3] ]**
+
+“When people talk about the IoT,” Mesirow told me, “they usually focus on [consumer devices, which far outnumber business devices][4]. Yet [connected buildings currently represent only 12% of global IoT projects][5],” he noted, “and that’s without including wearables and smart home projects.” (Mesirow is talking about buildings that “use various IoT devices, including occupancy sensors that determine when people are present in a room in order to keep lighting and temperature controls at optimal levels, lowering energy costs and aiding sustainability goals. Sensors can also detect water and gas leaks and aid in predictive maintenance for HVAC systems.”)
+
+### 4 key enterprise IoT opportunities
+
+More specifically, based on customer pain points, PwC’s Connected Solutions is focusing on a few key opportunities, which Mesirow laid out in a [blog post][6] earlier this year. (Not surprisingly, the opportunities seem tied to [the group’s products][7].)
+
+“A lot of these solutions came directly from our customers’ request,” he noted. “We pre-qualify our solutions with customers before we build them.”
+
+Let’s take a look at the top four areas, along with a quick reality check on how important they are and whether the technology is ready for prime time.
+
+#### **1\. Energy use and sustainability**
+
+The IoT makes it possible to manage buildings and spaces more efficiently, with savings of 25% or more. Occupancy sensors can tell whether anyone is actually in a room, adjusting lighting and temperature to saving money and conserve energy.
+
+Connected buildings can also help determine when meeting spaces are available, which can boost occupancy at large businesses and universities by 40% while cutting infrastructure and maintenance costs. Other sensors, meanwhile, can detect water and gas leaks and aid in predictive maintenance for HVAC systems.
+
+**Reality check:** Obviously, much of this technology is not new, but there’s a real opportunity to make it work better by integrating disparate systems and adding better analytics to the data to make planning more effective.
+
+#### **2. Asset tracking
+
+**
+
+“Businesses can also use the IoT to track their assets,“ Mesirow told me, “which can range from trucks to hotel luggage carts to medical equipment. It can even assist with monitoring trash by alerting appropriate people when dumpsters need to be emptied.”
+
+Asset trackers can instantly identify the location of all kinds of equipment (saving employee time and productivity), and they can reduce the number of lost, stolen, and misplaced devices and machines as well as provide complete visibility into the location of your assets.
+
+Such trackers can also save employees from wasting time hunting down the devices and machines they need. For example, PwC noted that during an average hospital shift, more than one-third of nurses spend at least an hour looking for equipment such as blood pressure monitors and insulin pumps. Just as important, location tracking often improves asset optimization, reduced inventory needs, and improved customer experience.
+
+**Reality check:** Asset tracking offers clear value. The real question is whether a given use case is cost effective or not, as well as how the data gathered will actually be used. Too often, companies spend a lot of money and effort tracking their assets, but don’t do much with the information.
+
+#### **3\. Security and compliance**
+
+Connected solutions can create better working environments, Mesirow said. “In a hotel, for example, these smart devices can ensure that air and water quality is up to standards, provide automated pest traps, monitor dumpsters and recycling bins, detect trespassers, determine when someone needs assistance, or discover activity in an unauthorized area. Monitoring the water quality of hotel swimming pools can lower chemical and filtering costs,” he said.
+
+Mesirow cited an innovative use case where, in response to workers’ complaints about harassment, hotel operators—in conjunction with the [American Hotel and Lodging Association][8]—are giving their employees portable devices that alert security staff when workers request assistance.
+
+**Reality check:** This seems useful, but the ROI might be difficult to calculate.
+
+#### **4\. Customer experience**
+
+According to PwC, “Sensors, facial recognition, analytics, dashboards, and notifications can elevate and even transform the customer experience. … Using connected solutions, you can identify and reward your best customers by offering perks, reduced wait times, and/or shorter lines.”
+
+Those kinds of personalized customer experiences can potentially boost customer loyalty and increase revenue, Mesirow said, adding that the technology can also make staff deployments more efficient and “enhance safety by identifying trespassers and criminals who are tampering with company property.”
+
+**Reality check:** Creating a great customer experience is critical for businesses today, and this kind of personalized targeting promises to make it more efficient and effective. However, it has to be done in a way that makes customers comfortable and not creeped out. Privacy concerns are very real, especially when it comes to working with facial recognition and other kinds of surveillance technology. For example, [San Francisco recently banned city agencies from using facial recognition][9], and others may follow.
+
+**More on IoT:**
+
+ * [What is the IoT? How the internet of things works][10]
+ * [What is edge computing and how it’s changing the network][11]
+ * [Most powerful Internet of Things companies][12]
+ * [10 Hot IoT startups to watch][13]
+ * [The 6 ways to make money in IoT][14]
+ * [What is digital twin technology? [and why it matters]][15]
+ * [Blockchain, service-centric networking key to IoT success][16]
+ * [Getting grounded in IoT networking and security][17]
+ * [Building IoT-ready networks must become a priority][18]
+ * [What is the Industrial IoT? [And why the stakes are so high]][19]
+
+
+
+Join the Network World communities on [Facebook][20] and [LinkedIn][21] to comment on topics that are top of mind.
+
+--------------------------------------------------------------------------------
+
+via: https://www.networkworld.com/article/3396128/the-state-of-enterprise-iot-companies-want-solutions-for-these-4-areas.html
+
+作者:[Fredric Paul][a]
+选题:[lujun9972][b]
+译者:[译者ID](https://github.com/译者ID)
+校对:[校对者ID](https://github.com/校对者ID)
+
+本文由 [LCTT](https://github.com/LCTT/TranslateProject) 原创编译,[Linux中国](https://linux.cn/) 荣誉推出
+
+[a]: https://www.networkworld.com/author/Fredric-Paul/
+[b]: https://github.com/lujun9972
+[1]: https://images.idgesg.net/images/article/2019/02/iot_internet_of_things_by_jackie_niam_gettyimages-996958260_2400x1600-100788446-large.jpg
+[2]: https://digital.pwc.com/content/pwc-digital/en/products/connected-solutions.html#get-connected
+[3]: https://www.networkworld.com/article/3309420/forget-smart-homes-the-new-goal-is-autonomous-buildings.html
+[4]: https://www.statista.com/statistics/370350/internet-of-things-installed-base-by-category/)
+[5]: https://iot-analytics.com/top-10-iot-segments-2018-real-iot-projects/
+[6]: https://www.digitalpulse.pwc.com.au/five-unexpected-ways-internet-of-things/
+[7]: https://digital.pwc.com/content/pwc-digital/en/products/connected-solutions.html
+[8]: https://www.ahla.com/
+[9]: https://www.nytimes.com/2019/05/14/us/facial-recognition-ban-san-francisco.html
+[10]: https://www.networkworld.com/article/3207535/internet-of-things/what-is-the-iot-how-the-internet-of-things-works.html
+[11]: https://www.networkworld.com/article/3224893/internet-of-things/what-is-edge-computing-and-how-it-s-changing-the-network.html
+[12]: https://www.networkworld.com/article/2287045/internet-of-things/wireless-153629-10-most-powerful-internet-of-things-companies.html
+[13]: https://www.networkworld.com/article/3270961/internet-of-things/10-hot-iot-startups-to-watch.html
+[14]: https://www.networkworld.com/article/3279346/internet-of-things/the-6-ways-to-make-money-in-iot.html
+[15]: https://www.networkworld.com/article/3280225/internet-of-things/what-is-digital-twin-technology-and-why-it-matters.html
+[16]: https://www.networkworld.com/article/3276313/internet-of-things/blockchain-service-centric-networking-key-to-iot-success.html
+[17]: https://www.networkworld.com/article/3269736/internet-of-things/getting-grounded-in-iot-networking-and-security.html
+[18]: https://www.networkworld.com/article/3276304/internet-of-things/building-iot-ready-networks-must-become-a-priority.html
+[19]: https://www.networkworld.com/article/3243928/internet-of-things/what-is-the-industrial-iot-and-why-the-stakes-are-so-high.html
+[20]: https://www.facebook.com/NetworkWorld/
+[21]: https://www.linkedin.com/company/network-world
diff --git a/sources/talk/20190522 Experts- Enterprise IoT enters the mass-adoption phase.md b/sources/talk/20190522 Experts- Enterprise IoT enters the mass-adoption phase.md
new file mode 100644
index 0000000000..86d7bf0efe
--- /dev/null
+++ b/sources/talk/20190522 Experts- Enterprise IoT enters the mass-adoption phase.md
@@ -0,0 +1,78 @@
+[#]: collector: (lujun9972)
+[#]: translator: ( )
+[#]: reviewer: ( )
+[#]: publisher: ( )
+[#]: url: ( )
+[#]: subject: (Experts: Enterprise IoT enters the mass-adoption phase)
+[#]: via: (https://www.networkworld.com/article/3397317/experts-enterprise-iot-enters-the-mass-adoption-phase.html)
+[#]: author: (Jon Gold https://www.networkworld.com/author/Jon-Gold/)
+
+Experts: Enterprise IoT enters the mass-adoption phase
+======
+Dropping hardware prices, 5G boost business internet-of-things deployments; technical complexity encourages partnerships.
+![Avgust01 / Getty Images][1]
+
+[IoT][2] in general has taken off quickly over the past few years, but experts at the recent IoT World highlighted that the enterprise part of the market has been particularly robust of late – it’s not just an explosion of connected home gadgets anymore.
+
+Donna Moore, chairwoman of the LoRa Alliance, an industry group that works to develop and scale low-power WAN technology for mass usage, said on a panel that she’s never seen growth this fast in the sector. “I’d say we’re now in the early mass adopters [stage],” she said.
+
+**More on IoT:**
+
+ * [Most powerful Internet of Things companies][3]
+ * [10 Hot IoT startups to watch][4]
+ * [The 6 ways to make money in IoT][5]
+ * [What is digital twin technology? [and why it matters]][6]
+ * [Blockchain, service-centric networking key to IoT success][7]
+ * [Getting grounded in IoT networking and security][8]
+ * [Building IoT-ready networks must become a priority][9]
+ * [What is the Industrial IoT? [And why the stakes are so high]][10]
+
+
+
+The technology itself has pushed adoption to these heights, said Graham Trickey, head of IoT for the GSMA, a trade organization for mobile network operators. Along with price drops for wireless connectivity modules, the array of upcoming technologies nestling under the umbrella label of [5G][11] could simplify the process of connecting devices to [edge-computing][12] hardware – and the edge to the cloud or [data center][13].
+
+“Mobile operators are not just providers of connectivity now, they’re farther up the stack,” he said. Technologies like narrow-band IoT and support for highly demanding applications like telehealth are all set to be part of the final 5G spec.
+
+### Partnerships needed to deal with IoT complexity**
+
+**
+
+That’s not to imply that there aren’t still huge tasks facing both companies trying to implement their own IoT frameworks and the creators of the technology underpinning them. For one thing, IoT tech requires a huge array of different sets of specialized knowledge.
+
+“That means partnerships, because you need an expert in your [vertical] area to know what you’re looking for, you need an expert in communications, and you might need a systems integrator,” said Trickey.
+
+Phil Beecher, the president and CEO of the Wi-SUN Alliance (the acronym stands for Smart Ubiquitous Networks, and the group is heavily focused on IoT for the utility sector), concurred with that, arguing that broad ecosystems of different technologies and different partners would be needed. “There’s no one technology that’s going to solve all these problems, no matter how much some parties might push it,” he said.
+
+One of the central problems – [IoT security][14] – is particularly dear to Beecher’s heart, given the consequences of successful hacks of the electrical grid or other utilities. More than one panelist praised the passage of the EU’s General Data Protection Regulation, saying that it offered concrete guidelines for entities developing IoT tech – a crucial consideration for some companies that may not have a lot of in-house expertise in that area.
+
+Join the Network World communities on [Facebook][15] and [LinkedIn][16] to comment on topics that are top of mind.
+
+--------------------------------------------------------------------------------
+
+via: https://www.networkworld.com/article/3397317/experts-enterprise-iot-enters-the-mass-adoption-phase.html
+
+作者:[Jon Gold][a]
+选题:[lujun9972][b]
+译者:[译者ID](https://github.com/译者ID)
+校对:[校对者ID](https://github.com/校对者ID)
+
+本文由 [LCTT](https://github.com/LCTT/TranslateProject) 原创编译,[Linux中国](https://linux.cn/) 荣誉推出
+
+[a]: https://www.networkworld.com/author/Jon-Gold/
+[b]: https://github.com/lujun9972
+[1]: https://images.idgesg.net/images/article/2019/02/iot_internet_of_things_mobile_connections_by_avgust01_gettyimages-1055659210_2400x1600-100788447-large.jpg
+[2]: https://www.networkworld.com/article/3207535/what-is-iot-how-the-internet-of-things-works.html
+[3]: https://www.networkworld.com/article/2287045/internet-of-things/wireless-153629-10-most-powerful-internet-of-things-companies.html
+[4]: https://www.networkworld.com/article/3270961/internet-of-things/10-hot-iot-startups-to-watch.html
+[5]: https://www.networkworld.com/article/3279346/internet-of-things/the-6-ways-to-make-money-in-iot.html
+[6]: https://www.networkworld.com/article/3280225/internet-of-things/what-is-digital-twin-technology-and-why-it-matters.html
+[7]: https://www.networkworld.com/article/3276313/internet-of-things/blockchain-service-centric-networking-key-to-iot-success.html
+[8]: https://www.networkworld.com/article/3269736/internet-of-things/getting-grounded-in-iot-networking-and-security.html
+[9]: https://www.networkworld.com/article/3276304/internet-of-things/building-iot-ready-networks-must-become-a-priority.html
+[10]: https://www.networkworld.com/article/3243928/internet-of-things/what-is-the-industrial-iot-and-why-the-stakes-are-so-high.html
+[11]: https://www.networkworld.com/article/3203489/what-is-5g-how-is-it-better-than-4g.html
+[12]: https://www.networkworld.com/article/3224893/what-is-edge-computing-and-how-it-s-changing-the-network.html?nsdr=true
+[13]: https://www.networkworld.com/article/3223692/what-is-a-data-centerhow-its-changed-and-what-you-need-to-know.html
+[14]: https://www.networkworld.com/article/3269736/getting-grounded-in-iot-networking-and-security.html
+[15]: https://www.facebook.com/NetworkWorld/
+[16]: https://www.linkedin.com/company/network-world
diff --git a/sources/talk/20190522 The Traffic Jam Whopper project may be the coolest-dumbest IoT idea ever.md b/sources/talk/20190522 The Traffic Jam Whopper project may be the coolest-dumbest IoT idea ever.md
new file mode 100644
index 0000000000..be8a4833cc
--- /dev/null
+++ b/sources/talk/20190522 The Traffic Jam Whopper project may be the coolest-dumbest IoT idea ever.md
@@ -0,0 +1,97 @@
+[#]: collector: (lujun9972)
+[#]: translator: ( )
+[#]: reviewer: ( )
+[#]: publisher: ( )
+[#]: url: ( )
+[#]: subject: (The Traffic Jam Whopper project may be the coolest/dumbest IoT idea ever)
+[#]: via: (https://www.networkworld.com/article/3396188/the-traffic-jam-whopper-project-may-be-the-coolestdumbest-iot-idea-ever.html)
+[#]: author: (Fredric Paul https://www.networkworld.com/author/Fredric-Paul/)
+
+The Traffic Jam Whopper project may be the coolest/dumbest IoT idea ever
+======
+Burger King uses real-time IoT data to deliver burgers to drivers stuck in traffic — and it seems to be working.
+![Mike Mozart \(CC BY 2.0\)][1]
+
+People love to eat in their cars. That’s why we invented the drive-in and the drive-thru.
+
+But despite a fast-food outlet on the corner of every major intersection, it turns out we were only scratching the surface of this idea. Burger King is taking this concept to the next logical step with its new IoT-powered Traffic Jam Whopper project.
+
+I have to admit, when I first heard about this, I thought it was a joke, but apparently the [Traffic Jam Whopper project is totally real][2] and has already passed a month-long test in Mexico City. While the company hasn’t specified a timeline, it plans to roll out the Traffic Jam Whopper project in Los Angeles (where else?) and other traffic-plagued megacities such as São Paulo and Shanghai.
+
+**[ Also read:[Is IoT in the enterprise about making money or saving money?][3] | Get regularly scheduled insights: [Sign up for Network World newsletters][4] ]**
+
+### How Burger King's Traffic Jam Whopper project works
+
+According to [Nations Restaurant News][5], this is how Burger King's Traffic Jam Whopper project works:
+
+The project uses real-time data to target hungry drivers along congested roads and highways for food delivery by couriers on motorcycles.
+
+The system leverages push notifications to the Burger King app and personalized messaging on digital billboards positioned along busy roads close to a Burger King restaurant.
+
+[According to the We Believers agency][6] that put it all together, “By leveraging traffic and drivers’ real-time data [location and speed], we adjusted our billboards’ location and content, displaying information about the remaining time in traffic to order, and personalized updates about deliveries in progress.” The menu is limited to Whopper Combos to speed preparation (though the company plans to offer a wider menu as it works out the kinks).
+
+**[[Become a Microsoft Office 365 administrator in record time with this quick start course from PluralSight.][7] ]**
+
+The company said orders in Mexico City were delivered in an average of 15 minutes. Fortunately (or unfortunately, depending on how you look at it) many traffic jams hold drivers captive for far longer than that.
+
+Once the order is ready, the motorcyclist uses Google maps and GPS technology embedded into the app to locate the car that made the order. The delivery person then weaves through traffic to hand over the Whopper. (Lane-splitting is legal in California, but I have no idea if there are other potential safety or law-enforcement issues involved here. For drivers ordering burgers, at least, the Burger King app supports voice ordering. I also don’t know what happens if traffic somehow clears up before the burger arrives.)
+
+Here’s a video of the pilot program in Mexico City:
+
+#### **New technology = > new opportunities**
+
+Even more amazing, this is not _just_ a publicity stunt. NRN quotes Bruno Cardinali, head of marketing for Burger King Latin America and Caribbean, claiming the project boosted sales during rush hour, when app orders are normally slow:
+
+“Thanks to The Traffic Jam Whopper campaign, we’ve increased deliveries by 63% in selected locations across the month of April, adding a significant amount of orders per restaurant per day, just during rush hours."
+
+If nothing else, this project shows that creative thinking really can leverage IoT technology into new businesses. In this case, it’s turning notoriously bad traffic—pretty much required for this process to work—from a problem into an opportunity to generate additional sales during slow periods.
+
+**More on IoT:**
+
+ * [What is the IoT? How the internet of things works][8]
+ * [What is edge computing and how it’s changing the network][9]
+ * [Most powerful Internet of Things companies][10]
+ * [10 Hot IoT startups to watch][11]
+ * [The 6 ways to make money in IoT][12]
+ * [What is digital twin technology? [and why it matters]][13]
+ * [Blockchain, service-centric networking key to IoT success][14]
+ * [Getting grounded in IoT networking and security][15]
+ * [Building IoT-ready networks must become a priority][16]
+ * [What is the Industrial IoT? [And why the stakes are so high]][17]
+
+
+
+Join the Network World communities on [Facebook][18] and [LinkedIn][19] to comment on topics that are top of mind.
+
+--------------------------------------------------------------------------------
+
+via: https://www.networkworld.com/article/3396188/the-traffic-jam-whopper-project-may-be-the-coolestdumbest-iot-idea-ever.html
+
+作者:[Fredric Paul][a]
+选题:[lujun9972][b]
+译者:[译者ID](https://github.com/译者ID)
+校对:[校对者ID](https://github.com/校对者ID)
+
+本文由 [LCTT](https://github.com/LCTT/TranslateProject) 原创编译,[Linux中国](https://linux.cn/) 荣誉推出
+
+[a]: https://www.networkworld.com/author/Fredric-Paul/
+[b]: https://github.com/lujun9972
+[1]: https://images.idgesg.net/images/article/2019/05/burger-king-gift-card-100797164-large.jpg
+[2]: https://abc7news.com/food/burger-king-to-deliver-to-drivers-stuck-in-traffic/5299073/
+[3]: https://www.networkworld.com/article/3343917/the-big-picture-is-iot-in-the-enterprise-about-making-money-or-saving-money.html
+[4]: https://www.networkworld.com/newsletters/signup.html
+[5]: https://www.nrn.com/technology/tech-tracker-burger-king-deliver-la-motorists-stuck-traffic?cid=
+[6]: https://www.youtube.com/watch?v=LXNgEZV7lNg
+[7]: https://pluralsight.pxf.io/c/321564/424552/7490?u=https%3A%2F%2Fwww.pluralsight.com%2Fcourses%2Fadministering-office-365-quick-start
+[8]: https://www.networkworld.com/article/3207535/internet-of-things/what-is-the-iot-how-the-internet-of-things-works.html
+[9]: https://www.networkworld.com/article/3224893/internet-of-things/what-is-edge-computing-and-how-it-s-changing-the-network.html
+[10]: https://www.networkworld.com/article/2287045/internet-of-things/wireless-153629-10-most-powerful-internet-of-things-companies.html
+[11]: https://www.networkworld.com/article/3270961/internet-of-things/10-hot-iot-startups-to-watch.html
+[12]: https://www.networkworld.com/article/3279346/internet-of-things/the-6-ways-to-make-money-in-iot.html
+[13]: https://www.networkworld.com/article/3280225/internet-of-things/what-is-digital-twin-technology-and-why-it-matters.html
+[14]: https://www.networkworld.com/article/3276313/internet-of-things/blockchain-service-centric-networking-key-to-iot-success.html
+[15]: https://www.networkworld.com/article/3269736/internet-of-things/getting-grounded-in-iot-networking-and-security.html
+[16]: https://www.networkworld.com/article/3276304/internet-of-things/building-iot-ready-networks-must-become-a-priority.html
+[17]: https://www.networkworld.com/article/3243928/internet-of-things/what-is-the-industrial-iot-and-why-the-stakes-are-so-high.html
+[18]: https://www.facebook.com/NetworkWorld/
+[19]: https://www.linkedin.com/company/network-world
diff --git a/sources/talk/20190523 Benchmarks of forthcoming Epyc 2 processor leaked.md b/sources/talk/20190523 Benchmarks of forthcoming Epyc 2 processor leaked.md
new file mode 100644
index 0000000000..61ae9e656b
--- /dev/null
+++ b/sources/talk/20190523 Benchmarks of forthcoming Epyc 2 processor leaked.md
@@ -0,0 +1,55 @@
+[#]: collector: (lujun9972)
+[#]: translator: ( )
+[#]: reviewer: ( )
+[#]: publisher: ( )
+[#]: url: ( )
+[#]: subject: (Benchmarks of forthcoming Epyc 2 processor leaked)
+[#]: via: (https://www.networkworld.com/article/3397081/benchmarks-of-forthcoming-epyc-2-processor-leaked.html)
+[#]: author: (Andy Patrizio https://www.networkworld.com/author/Andy-Patrizio/)
+
+Benchmarks of forthcoming Epyc 2 processor leaked
+======
+Benchmarks of AMD's second-generation Epyc server briefly found their way online and show the chip is larger but a little slower than the Epyc 7601 on the market now.
+![Gordon Mah Ung][1]
+
+Benchmarks of engineering samples of AMD's second-generation Epyc server, code-named “Rome,” briefly found their way online and show a very beefy chip running a little slower than its predecessor.
+
+Rome is based on the Zen 2 architecture, believed to be more of an incremental improvement over the prior generation than a major leap. It’s already known that Rome would feature a 64-core, 128-thread design, but that was about all of the details.
+
+**[ Also read:[Who's developing quantum computers][2] ]**
+
+The details came courtesy of SiSoftware's Sandra PC analysis and benchmarking tool. It’s very popular and has been used by hobbyists and benchmarkers alike for more than 20 years. New benchmarks are uploaded to the Sandra database all the time, and what I suspect happened is someone running a Rome sample ran the benchmark, not realizing the results would be uploaded to the Sandra database.
+
+The benchmarks were from two different servers, a Dell PowerEdge R7515 and a Super Micro Super Server. The Dell product number is not on the market, so this would indicate a future server with Rome processors. The entry has since been deleted, but several sites, including the hobbyist site Tom’s Hardware Guide, managed to [take a screenshot][3].
+
+According to the entry, the chip is a mid-range processor with a base clock speed of 1.4GHz, jumping up to 2.2GHz in turbo mode, with 16MB of Level 2 cache and 256MB of Level 3 cache, the latter of which is crazy. The first-generation Epyc had just 32MB of L3 cache.
+
+That’s a little slower than the Epyc 7601 on the market now, but when you double the number of cores in the same space, something’s gotta give, and in this case, it’s electricity. The thermal envelope was not revealed by the benchmark. Previous Epyc processors ranged from 120 watts to 180 watts.
+
+Sandra ranked the processor at #3 for arithmetic and #5 for multimedia processing, which makes me wonder what on Earth beat the Rome chip. Interestingly, the servers were running Windows 10, not Windows Server 2019.
+
+**[[Get certified as an Apple Technical Coordinator with this seven-part online course from PluralSight.][4] ]**
+
+Rome is expected to be officially launched at the massive Computex trade show in Taiwan on May 27 and will begin shipping in the third quarter of the year.
+
+Join the Network World communities on [Facebook][5] and [LinkedIn][6] to comment on topics that are top of mind.
+
+--------------------------------------------------------------------------------
+
+via: https://www.networkworld.com/article/3397081/benchmarks-of-forthcoming-epyc-2-processor-leaked.html
+
+作者:[Andy Patrizio][a]
+选题:[lujun9972][b]
+译者:[译者ID](https://github.com/译者ID)
+校对:[校对者ID](https://github.com/校对者ID)
+
+本文由 [LCTT](https://github.com/LCTT/TranslateProject) 原创编译,[Linux中国](https://linux.cn/) 荣誉推出
+
+[a]: https://www.networkworld.com/author/Andy-Patrizio/
+[b]: https://github.com/lujun9972
+[1]: https://images.idgesg.net/images/article/2018/11/rome_2-100779395-large.jpg
+[2]: https://www.networkworld.com/article/3275385/who-s-developing-quantum-computers.html
+[3]: https://www.tomshardware.co.uk/amd-epyc-rome-processor-data-center,news-60265.html
+[4]: https://pluralsight.pxf.io/c/321564/424552/7490?u=https%3A%2F%2Fwww.pluralsight.com%2Fpaths%2Fapple-certified-technical-trainer-10-11
+[5]: https://www.facebook.com/NetworkWorld/
+[6]: https://www.linkedin.com/company/network-world
diff --git a/sources/talk/20190523 Cisco ties its security-SD-WAN gear with Teridion-s cloud WAN service.md b/sources/talk/20190523 Cisco ties its security-SD-WAN gear with Teridion-s cloud WAN service.md
new file mode 100644
index 0000000000..2638987b16
--- /dev/null
+++ b/sources/talk/20190523 Cisco ties its security-SD-WAN gear with Teridion-s cloud WAN service.md
@@ -0,0 +1,74 @@
+[#]: collector: (lujun9972)
+[#]: translator: ( )
+[#]: reviewer: ( )
+[#]: publisher: ( )
+[#]: url: ( )
+[#]: subject: (Cisco ties its security/SD-WAN gear with Teridion’s cloud WAN service)
+[#]: via: (https://www.networkworld.com/article/3396628/cisco-ties-its-securitysd-wan-gear-with-teridions-cloud-wan-service.html)
+[#]: author: (Michael Cooney https://www.networkworld.com/author/Michael-Cooney/)
+
+Cisco ties its security/SD-WAN gear with Teridion’s cloud WAN service
+======
+An agreement links Cisco Meraki MX Security/SD-WAN appliances and its Auto VPN technology to Teridion’s cloud-based WAN service that claims to accelerate TCP-based applications by up to 5X.
+![istock][1]
+
+Cisco and Teridion have tied the knot to deliver faster enterprise [software-defined WAN][2] services.
+
+The agreement links [Cisco Meraki][3] MX Security/SD-WAN appliances and its Auto [VPN][4] technology which lets users quickly bring up and configure secure sessions between branches and data centers with [Teridion’s cloud-based WAN service][5]. Teridion’s service promises customers better performance and control over traffic running from remote offices over the public internet to the [data center][6]. The service features what Teridion calls “Curated Routing” which fuses WAN acceleration techniques with route optimization to speed traffic.
+
+**More about SD-WAN**
+
+ * [How to buy SD-WAN technology: Key questions to consider when selecting a supplier][7]
+ * [How to pick an off-site data-backup method][8]
+ * [SD-Branch: What it is and why you’ll need it][9]
+ * [What are the options for security SD-WAN?][10]
+
+
+
+For example, Teridion says its WAN service can accelerate TCP-based applications like file transfers, backups and page loads, by as much as three to five times.
+
+“[The service] improves network performance for UDP based applications like voice, video, RDP, and VDI. Enterprises can get carrier grade performance over broadband and dedicated internet access. Depending on the locations of the sites, [customers] can expect to see a 15 to 30 percent reduction in latency. That’s the difference between a great quality video conference and an unworkable, choppy mess” Teridion [stated][11].
+
+Teridion says the Meraki integration creates an IPSec connection from the Cisco Meraki MX to the Teridion edge. “Customers create locations in the Teridion portal and apply the preconfigured Meraki template to them, or just upload a csv file if you have a lot of locations. Then, from each Meraki MX, create a 3rd party IPSec tunnel to the Teridion edge IP addresses that are generated as part of the Teridion configuration.”
+
+The combined Cisco Meraki and Teridion offering brings SD-WAN and security capabilities at the WAN edge that are tightly integrated with a WAN service delivered over cost-effective broadband or dedicated Internet access, said Raviv Levi, director of product management at Cisco Meraki in a statement. “This brings better reliability and consistency to the enterprise WAN across multiple sites, as well as high performance access to all SaaS applications and cloud workloads.”
+
+Meraki’s MX family supports everything from SD-WAN and [Wi-Fi][12] features to next-generation [firewall][13] and intrusion prevention in a single package.
+
+Some studies show that by 2021 over 75 percent of enterprise traffic will be SaaS-oriented, so giving branch offices SD-WAN's reliable, secure transportation options will be a necessity, Cisco said when it [upgraded the Meraki][3] boxes last year.
+
+Cisco Meraki isn’t the only SD-WAN service Teridion supports. The company also has agreements Citrix, Silver Peak, VMware (VeloCloud). Teridion also has partnerships with over 25 cloud partners, including Google, Amazon Web Services and Microsoft Azure.
+
+[Teridion for Cisco Meraki][14] is available now from authorized Teridion resellers. Pricing starts at $50 per site per month.
+
+Join the Network World communities on [Facebook][15] and [LinkedIn][16] to comment on topics that are top of mind.
+
+--------------------------------------------------------------------------------
+
+via: https://www.networkworld.com/article/3396628/cisco-ties-its-securitysd-wan-gear-with-teridions-cloud-wan-service.html
+
+作者:[Michael Cooney][a]
+选题:[lujun9972][b]
+译者:[译者ID](https://github.com/译者ID)
+校对:[校对者ID](https://github.com/校对者ID)
+
+本文由 [LCTT](https://github.com/LCTT/TranslateProject) 原创编译,[Linux中国](https://linux.cn/) 荣誉推出
+
+[a]: https://www.networkworld.com/author/Michael-Cooney/
+[b]: https://github.com/lujun9972
+[1]: https://images.idgesg.net/images/article/2018/02/istock-820219662-100749695-large.jpg
+[2]: https://www.networkworld.com/article/3031279/sd-wan-what-it-is-and-why-you-ll-use-it-one-day.html
+[3]: https://www.networkworld.com/article/3301169/cisco-meraki-amps-up-throughput-wi-fi-to-sd-wan-family.html
+[4]: https://www.networkworld.com/article/3138952/5-things-you-need-to-know-about-virtual-private-networks.html
+[5]: https://www.networkworld.com/article/3284285/teridion-enables-higher-performing-and-more-responsive-saas-applications.html
+[6]: https://www.networkworld.com/article/3223692/what-is-a-data-centerhow-its-changed-and-what-you-need-to-know.html
+[7]: https://www.networkworld.com/article/3323407/sd-wan/how-to-buy-sd-wan-technology-key-questions-to-consider-when-selecting-a-supplier.html
+[8]: https://www.networkworld.com/article/3328488/backup-systems-and-services/how-to-pick-an-off-site-data-backup-method.html
+[9]: https://www.networkworld.com/article/3250664/lan-wan/sd-branch-what-it-is-and-why-youll-need-it.html
+[10]: https://www.networkworld.com/article/3285728/sd-wan/what-are-the-options-for-securing-sd-wan.html?nsdr=true
+[11]: https://www.teridion.com/blog/teridion-announces-deep-integration-with-cisco-meraki-mx/
+[12]: https://www.networkworld.com/article/3318119/what-to-expect-from-wi-fi-6-in-2019.html
+[13]: https://www.networkworld.com/article/3230457/what-is-a-firewall-perimeter-stateful-inspection-next-generation.html
+[14]: https://www.teridion.com/meraki
+[15]: https://www.facebook.com/NetworkWorld/
+[16]: https://www.linkedin.com/company/network-world
diff --git a/sources/talk/20190523 Edge-based caching and blockchain-nodes speed up data transmission.md b/sources/talk/20190523 Edge-based caching and blockchain-nodes speed up data transmission.md
new file mode 100644
index 0000000000..54ddf76db3
--- /dev/null
+++ b/sources/talk/20190523 Edge-based caching and blockchain-nodes speed up data transmission.md
@@ -0,0 +1,74 @@
+[#]: collector: (lujun9972)
+[#]: translator: ( )
+[#]: reviewer: ( )
+[#]: publisher: ( )
+[#]: url: ( )
+[#]: subject: (Edge-based caching and blockchain-nodes speed up data transmission)
+[#]: via: (https://www.networkworld.com/article/3397105/edge-based-caching-and-blockchain-nodes-speed-up-data-transmission.html)
+[#]: author: (Patrick Nelson https://www.networkworld.com/author/Patrick-Nelson/)
+
+Edge-based caching and blockchain-nodes speed up data transmission
+======
+Using a combination of edge-based data caches and blockchain-like distributed networks, Bluzelle claims it can significantly speed up the delivery of data across the globe.
+![OlgaSalt / /getty][1]
+
+The combination of a blockchain-like distributed network, along with the ability to locate data at the edge will massively speed up future networks, such as those used by the internet of things (IoT), claims Bluzelle in announcing what is says is the first decentralized data delivery network (DDN).
+
+Distributed DDNs will be like content delivery networks (CDNs) that now cache content around the world to speed up the web, but in this case, it will be for data, the Singapore-based company explains. Distributed key-value (blockchain) networks and edge computing built into Bluzelle's system will provide significantly faster delivery than existing caching, the company claims in a press release announcing its product.
+
+“The future of data delivery can only ever be de-centrally distributed,” says Pavel Bains, CEO and co-founder of Bluzelle. It’s because the world requires instant access to data that’s being created at the edge, he argues.
+
+“But delivery is hampered by existing technology,” he says.
+
+**[ Also read:[What is edge computing?][2] and [How edge networking and IoT will reshape data centers][3]. ]**
+
+Bluzelle says decentralized caching is the logical next step to generalized data caching, used for reducing latency. “Decentralized caching expands the theory of caching,” the company writes in a [report][4] (Dropbox pdf) on its [website][5]. It says the cache must be expanded from simply being located at one unique location.
+
+“Using a combination of distributed networks, the edge and the cloud, [it’s] thereby increasing the transactional throughput of data,” the company says.
+
+This kind of thing is particularly important in consumer gaming now, where split-second responses from players around the world make or break a game experience, but it will likely be crucial for the IoT, higher-definition media, artificial intelligence, and virtual reality as they gain more of a role in digitization—including at critical enterprise applications.
+
+“Currently applications are limited to data caching technologies that require complex configuration and management of 10-plus-year-old technology constrained to a few data centers,” Bains says. “These were not designed to handle the ever-increasing volumes of data.”
+
+Bains says one of the key selling points of Bluzelle's network is that developers should be able to implement and run networks without having to also physically expand the networks manually.
+
+“Software developers don’t want to react to where their customers come from. Our architecture is designed to always have the data right where the customer is. This provides a superior consumer experience,” he says.
+
+Data caches are around now, but Bluzelle claims its system, written in C++ and available on Linux and Docker containers, among other platforms, is faster than others. It further says that if its system and a more traditional cache would connect to the same MySQL database in Virginia, say, their users will get the data three to 16 times faster than a traditional “non-edge-caching” network. Write updates to all Bluzelle nodes around the world takes 875 milliseconds (ms), it says.
+
+The company has been concentrating its efforts on gaming, and with a test setup in Virginia, it says it was able to deliver data 33 times faster—at 22ms to Singapore—than a normal, cloud-based data cache. That traditional cache (located near the database) took 727ms in the Bluzelle-published test. In a test to Ireland, it claims 16ms over 223ms using a traditional cache.
+
+An algorithm is partly the reason for the gains, the company explains. It “allows the nodes to make decisions and take actions without the need for masternodes,” the company says. Masternodes are the server-like parts of blockchain systems.
+
+**More about edge networking**
+
+ * [How edge networking and IoT will reshape data centers][3]
+ * [Edge computing best practices][6]
+ * [How edge computing can help secure the IoT][7]
+
+
+
+Join the Network World communities on [Facebook][8] and [LinkedIn][9] to comment on topics that are top of mind.
+
+--------------------------------------------------------------------------------
+
+via: https://www.networkworld.com/article/3397105/edge-based-caching-and-blockchain-nodes-speed-up-data-transmission.html
+
+作者:[Patrick Nelson][a]
+选题:[lujun9972][b]
+译者:[译者ID](https://github.com/译者ID)
+校对:[校对者ID](https://github.com/校对者ID)
+
+本文由 [LCTT](https://github.com/LCTT/TranslateProject) 原创编译,[Linux中国](https://linux.cn/) 荣誉推出
+
+[a]: https://www.networkworld.com/author/Patrick-Nelson/
+[b]: https://github.com/lujun9972
+[1]: https://images.idgesg.net/images/article/2019/02/blockchain_crypotocurrency_bitcoin-by-olgasalt-getty-100787949-large.jpg
+[2]: https://www.networkworld.com/article/3224893/internet-of-things/what-is-edge-computing-and-how-it-s-changing-the-network.html
+[3]: https://www.networkworld.com/article/3291790/data-center/how-edge-networking-and-iot-will-reshape-data-centers.html
+[4]: https://www.dropbox.com/sh/go5bnhdproy1sk5/AAC5MDoafopFS7lXUnmiLAEFa?dl=0&preview=Bluzelle+Report+-+The+Decentralized+Internet+Is+Here.pdf
+[5]: https://bluzelle.com/
+[6]: https://www.networkworld.com/article/3331978/lan-wan/edge-computing-best-practices.html
+[7]: https://www.networkworld.com/article/3331905/internet-of-things/how-edge-computing-can-help-secure-the-iot.html
+[8]: https://www.facebook.com/NetworkWorld/
+[9]: https://www.linkedin.com/company/network-world
diff --git a/sources/talk/20190523 Online performance benchmarks all companies should try to achieve.md b/sources/talk/20190523 Online performance benchmarks all companies should try to achieve.md
new file mode 100644
index 0000000000..829fb127f8
--- /dev/null
+++ b/sources/talk/20190523 Online performance benchmarks all companies should try to achieve.md
@@ -0,0 +1,80 @@
+[#]: collector: (lujun9972)
+[#]: translator: ( )
+[#]: reviewer: ( )
+[#]: publisher: ( )
+[#]: url: ( )
+[#]: subject: (Online performance benchmarks all companies should try to achieve)
+[#]: via: (https://www.networkworld.com/article/3397322/online-performance-benchmarks-all-companies-should-try-to-achieve.html)
+[#]: author: (Zeus Kerravala https://www.networkworld.com/author/Zeus-Kerravala/)
+
+Online performance benchmarks all companies should try to achieve
+======
+With digital performance more important than ever, companies must ensure their online performance meets customers’ needs. A new ThousandEyes report can help them determine that.
+![Thinkstock][1]
+
+There's no doubt about it: We have entered the experience economy, and digital performance is more important than ever.
+
+Customer experience is the top brand differentiator, topping price and every other factor. And businesses that provide a poor digital experience will find customers will actively seek a competitor. In fact, recent ZK Research found that in 2018, about two-thirds of millennials changed loyalties to a brand because of a bad experience. (Note: I am an employee of ZK Research.)
+
+To help companies determine if their online performance is leading, lacking, or on par with some of the top companies, ThousandEyes this week released its [2019 Digital Experience Performance Benchmark Report][2]. This document provides a comparative analysis of web, infrastructure, and network performance from the top 20 U.S. digital retail, travel, and media websites. Although this is a small sampling of companies, those three industries are the most competitive when it comes to using their digital platforms for competitive advantage. The aggregated data from this report can be used as an industry-agnostic performance benchmark that all companies should strive to meet.
+
+**[ Read also:[IoT providers need to take responsibility for performance][3] ]**
+
+The methodology of the study was for ThousandEyes to use its own platform to provide an independent view of performance. It uses active monitoring and a global network of monitoring agents to measure application and network layer performance for websites, applications, and services. The company collected data from 36 major cities scattered across the U.S. Six of the locations (Ashburn, Chicago, Dallas, Los Angeles, San Jose, and Seattle) also included vantage points connected to six major broadband ISPs (AT&T, CenturyLink, Charter, Comcast, Cox, and Verizon). This acts as a good proxy for what a user would experience.
+
+The test involved page load tests against the websites of the major companies in retail, media, and travel and looked at several factors, including DNS response time, round-trip latency, network time (one-way latency), HTTP response time, and page load. The averages and median times can be seen in the table below. Those can be considered the average benchmarks that all companies should try to attain.
+
+![][4]
+
+### Choice of content delivery network matters by location
+
+ThousandEyes' report also looked at how the various services that companies use impacts web performance. For example, the study measured the performance of the content delivery network (CDN) providers in the 36 markets. It found that in Albuquerque, Akamai and Fastly had the most latency, whereas Edgecast had the least. It also found that in Boston, all of the CDN providers were close. Companies can use this type of data to help them select a CDN. Without it, decision makers are essentially guessing and hoping.
+
+### CDN performance is impacted by ISP
+
+Another useful set of data was cross-referencing CDN performance by ISP, which lead to some fascinating information. With Comcast, Akamai, Cloudfront, Google and Incapula all had high amounts of latency. Only Edgecast and Fastly offered average latency. On the other hand, all of the CDNs worked great with CenturyLink. This tells a buyer, "If my customer base is largely in Comcast’s footprint, I should look at Edgecast or Fastly or my customers will be impacted."
+
+### DNS and latency directly impact page load times
+
+The ThousandEyes study also confirmed some points that many people believe as true but until now had no quantifiable evidence to support it. For example, it's widely accepted that DNS response time and network latency to the CDN edge correlate to web performance; the data in the report now supports that belief. ThousandEyes did some regression analysis and fancy math and found that in general, companies that were in the top quartile of HTTP performance had above-average DNS response time and network performance. There were a few exceptions, but in most cases, this is true.
+
+Based on all the data, the below are the benchmarks for the three infrastructure metrics gathered and is what businesses, even ones outside the three verticals studied, should hope to achieve to support a high-quality digital experience.
+
+ * DNS response time 25 ms
+ * Round trip network latency 15 ms
+ * HTTP response time 250 ms
+
+
+
+### Operations teams need to focus on digital performance
+
+Benchmarking certainly provides value, but the report also offers some recommendations on how operations teams can use the data to improve digital performance. Those include:
+
+ * **Measure site from distributed user vantage points**. There is no single point that will provide a view of digital performance everywhere. Instead, measure from a range of ISPs in different regions and take a multi-layered approach to visibility (application, network and routing).
+ * **Use internet performance information as a baseline**. Compare your organization's data to the baselines, and if you’re not meeting it in some markets, focus on improvement there.
+ * **Compare performance to industry peers**. In highly competitive industries, it’s important to understand how you rank versus the competition. Don’t be satisfied with hitting the benchmarks if your key competitors exceed them.
+ * **Build a strong performance stack.** The data shows that solid DNS and HTTP response times and low latency are correlated to solid page load times. Focus on optimizing those factors and consider them foundational to digital performance.
+
+
+
+Join the Network World communities on [Facebook][5] and [LinkedIn][6] to comment on topics that are top of mind.
+
+--------------------------------------------------------------------------------
+
+via: https://www.networkworld.com/article/3397322/online-performance-benchmarks-all-companies-should-try-to-achieve.html
+
+作者:[Zeus Kerravala][a]
+选题:[lujun9972][b]
+译者:[译者ID](https://github.com/译者ID)
+校对:[校对者ID](https://github.com/校对者ID)
+
+本文由 [LCTT](https://github.com/LCTT/TranslateProject) 原创编译,[Linux中国](https://linux.cn/) 荣誉推出
+
+[a]: https://www.networkworld.com/author/Zeus-Kerravala/
+[b]: https://github.com/lujun9972
+[1]: https://images.idgesg.net/images/article/2017/07/racing_speed_runners_internet-speed-100728363-large.jpg
+[2]: https://www.thousandeyes.com/research/digital-experience
+[3]: https://www.networkworld.com/article/3340318/iot-providers-need-to-take-responsibility-for-performance.html
+[4]: https://images.idgesg.net/images/article/2019/05/thousandeyes-100797290-large.jpg
+[5]: https://www.facebook.com/NetworkWorld/
+[6]: https://www.linkedin.com/company/network-world
diff --git a/sources/talk/20190523 Study- Most enterprise IoT transactions are unencrypted.md b/sources/talk/20190523 Study- Most enterprise IoT transactions are unencrypted.md
new file mode 100644
index 0000000000..51098dad33
--- /dev/null
+++ b/sources/talk/20190523 Study- Most enterprise IoT transactions are unencrypted.md
@@ -0,0 +1,93 @@
+[#]: collector: (lujun9972)
+[#]: translator: ( )
+[#]: reviewer: ( )
+[#]: publisher: ( )
+[#]: url: ( )
+[#]: subject: (Study: Most enterprise IoT transactions are unencrypted)
+[#]: via: (https://www.networkworld.com/article/3396647/study-most-enterprise-iot-transactions-are-unencrypted.html)
+[#]: author: (Tim Greene https://www.networkworld.com/author/Tim-Greene/)
+
+Study: Most enterprise IoT transactions are unencrypted
+======
+A Zscaler report finds 91.5% of IoT communications within enterprises are in plaintext and so susceptible to interference.
+![HYWARDS / Getty Images][1]
+
+Of the millions of enterprise-[IoT][2] transactions examined in a recent study, the vast majority were sent without benefit of encryption, leaving the data vulnerable to theft and tampering.
+
+The research by cloud-based security provider Zscaler found that about 91.5 percent of transactions by internet of things devices took place over plaintext, while 8.5 percent were encrypted with [SSL][3]. That means if attackers could intercept the unencrypted traffic, they’d be able to read it and possibly alter it, then deliver it as if it had not been changed.
+
+**[ For more on IoT security, see[our corporate guide to addressing IoT security concerns][4]. | Get regularly scheduled insights by [signing up for Network World newsletters][5]. ]**
+
+Researchers looked through one month’s worth of enterprise traffic traversing Zscaler’s cloud seeking the digital footprints of IoT devices. It found and analyzed 56 million IoT-device transactions over that time, and identified the type of devices, protocols they used, the servers they communicated with, how often communication went in and out and general IoT traffic patterns.
+
+The team tried to find out which devices generate the most traffic and the threats they face. It discovered that 1,015 organizations had at least one IoT device. The most common devices were set-top boxes (52 percent), then smart TVs (17 percent), wearables (8 percent), data-collection terminals (8 percent), printers (7 percent), IP cameras and phones (5 percent) and medical devices (1 percent).
+
+While they represented only 8 percent of the devices, data-collection terminals generated 80 percent of the traffic.
+
+The breakdown is that 18 percent of the IoT devices use SSL to communicate all the time, and of the remaining 82 percent, half used it part of the time and half never used it.
+The study also found cases of plaintext HTTP being used to authenticate devices and to update software and firmware, as well as use of outdated crypto libraries and weak default credentials.
+
+While IoT devices are common in enterprises, “many of the devices are employee owned, and this is just one of the reasons they are a security concern,” the report says. Without strict policies and enforcement, these devices represent potential vulnerabilities.
+
+**[[Prepare to become a Certified Information Security Systems Professional with this comprehensive online course from PluralSight. Now offering a 10-day free trial!][6] ]**
+
+Another reason employee-owned IoT devices are a concern is that many businesses don’t consider them a threat because no data is stored on them. But if the data they gather is transmitted insecurely, it is at risk.
+
+### 5 tips to protect enterprise IoT
+
+Zscaler recommends these security precautions:
+
+ * Change default credentials to something more secure. As employees bring in devices, encourage them to use strong passwords and to keep their firmware current.
+ * Isolate IoT devices on networks and restrict inbound and outbound network traffic.
+ * Restrict access to IoT devices from external networks and block unnecessary ports from external access.
+ * Apply regular security and firmware updates to IoT devices, and secure network traffic.
+ * Deploy tools to gain visibility of shadow-IoT devices already inside the network so they can be protected.
+
+
+
+**More on IoT:**
+
+ * [What is edge computing and how it’s changing the network][7]
+ * [Most powerful Internet of Things companies][8]
+ * [10 Hot IoT startups to watch][9]
+ * [The 6 ways to make money in IoT][10]
+ * [What is digital twin technology? [and why it matters]][11]
+ * [Blockchain, service-centric networking key to IoT success][12]
+ * [Getting grounded in IoT networking and security][13]
+ * [Building IoT-ready networks must become a priority][14]
+ * [What is the Industrial IoT? [And why the stakes are so high]][15]
+
+
+
+Join the Network World communities on [Facebook][16] and [LinkedIn][17] to comment on topics that are top of mind.
+
+--------------------------------------------------------------------------------
+
+via: https://www.networkworld.com/article/3396647/study-most-enterprise-iot-transactions-are-unencrypted.html
+
+作者:[Tim Greene][a]
+选题:[lujun9972][b]
+译者:[译者ID](https://github.com/译者ID)
+校对:[校对者ID](https://github.com/校对者ID)
+
+本文由 [LCTT](https://github.com/LCTT/TranslateProject) 原创编译,[Linux中国](https://linux.cn/) 荣誉推出
+
+[a]: https://www.networkworld.com/author/Tim-Greene/
+[b]: https://github.com/lujun9972
+[1]: https://images.idgesg.net/images/article/2019/05/network_security_network_traffic_scanning_by_hywards_gettyimages-673891964_2400x1600-100796830-large.jpg
+[2]: https://www.networkworld.com/article/3207535/what-is-iot-how-the-internet-of-things-works.html
+[3]: https://www.networkworld.com/article/3045953/5-things-you-need-to-know-about-ssl.html
+[4]: https://www.networkworld.com/article/3269165/internet-of-things/a-corporate-guide-to-addressing-iot-security-concerns.html
+[5]: https://www.networkworld.com/newsletters/signup.html
+[6]: https://pluralsight.pxf.io/c/321564/424552/7490?u=https%3A%2F%2Fwww.pluralsight.com%2Fpaths%2Fcertified-information-systems-security-professional-cisspr
+[7]: https://www.networkworld.com/article/3224893/internet-of-things/what-is-edge-computing-and-how-it-s-changing-the-network.html
+[8]: https://www.networkworld.com/article/2287045/internet-of-things/wireless-153629-10-most-powerful-internet-of-things-companies.html
+[9]: https://www.networkworld.com/article/3270961/internet-of-things/10-hot-iot-startups-to-watch.html
+[10]: https://www.networkworld.com/article/3279346/internet-of-things/the-6-ways-to-make-money-in-iot.html
+[11]: https://www.networkworld.com/article/3280225/internet-of-things/what-is-digital-twin-technology-and-why-it-matters.html
+[12]: https://www.networkworld.com/article/3276313/internet-of-things/blockchain-service-centric-networking-key-to-iot-success.html
+[13]: https://www.networkworld.com/article/3269736/internet-of-things/getting-grounded-in-iot-networking-and-security.html
+[14]: https://www.networkworld.com/article/3276304/internet-of-things/building-iot-ready-networks-must-become-a-priority.html
+[15]: https://www.networkworld.com/article/3243928/internet-of-things/what-is-the-industrial-iot-and-why-the-stakes-are-so-high.html
+[16]: https://www.facebook.com/NetworkWorld/
+[17]: https://www.linkedin.com/company/network-world
diff --git a/sources/talk/20190528 Managed WAN and the cloud-native SD-WAN.md b/sources/talk/20190528 Managed WAN and the cloud-native SD-WAN.md
new file mode 100644
index 0000000000..026b5d8e81
--- /dev/null
+++ b/sources/talk/20190528 Managed WAN and the cloud-native SD-WAN.md
@@ -0,0 +1,121 @@
+[#]: collector: (lujun9972)
+[#]: translator: ( )
+[#]: reviewer: ( )
+[#]: publisher: ( )
+[#]: url: ( )
+[#]: subject: (Managed WAN and the cloud-native SD-WAN)
+[#]: via: (https://www.networkworld.com/article/3398476/managed-wan-and-the-cloud-native-sd-wan.html)
+[#]: author: (Matt Conran https://www.networkworld.com/author/Matt-Conran/)
+
+Managed WAN and the cloud-native SD-WAN
+======
+The motivation for WAN transformation is clear, today organizations require: improved internet access and last mile connectivity, additional bandwidth and a reduction in the WAN costs.
+![Gerd Altmann \(CC0\)][1]
+
+In recent years, a significant number of organizations have transformed their wide area network (WAN). Many of these organizations have some kind of cloud-presence across on-premise data centers and remote site locations.
+
+The vast majority of organizations that I have consulted with have over 10 locations. And it is common to have headquarters in both the US and Europe, along with remote site locations spanning North America, Europe, and Asia.
+
+A WAN transformation project requires this diversity to be taken into consideration when choosing the best SD-WAN vendor to satisfy both; networking and security requirements. Fundamentally, SD-WAN is not just about physical connectivity, there are many more related aspects.
+
+**[ Related:[MPLS explained – What you need to know about multi-protocol label switching][2]**
+
+### Motivations for transforming the WAN
+
+The motivation for WAN transformation is clear: Today organizations prefer improved internet access and last mile connectivity, additional bandwidth along with a reduction in the WAN costs. Replacing Multiprotocol Label Switching (MPLS) with SD-WAN has of course been the main driver for the SD-WAN evolution, but it is only a single piece of the jigsaw puzzle.
+
+Many SD-WAN vendors are quickly brought to their knees when they try to address security and gain direct internet access from remote site locations. The problem is how to ensure optimized cloud access that is secure, has improved visibility and predictable performance without the high costs associated with MPLS? SD-WAN is not just about connecting locations. Primarily, it needs to combine many other important network and security elements into one seamless worldwide experience.
+
+According to a recent report from [Cato Networks][3] into enterprise IT managers, a staggering 85% will confront use cases in 2019 that are poorly addressed or outright ignored by SD-WAN. Examples includes providing secure, Internet access from any location (50%) and improving visibility into and control over mobile access to cloud applications, such as Office 365 (46%).
+
+### Issues with traditional SD-WAN vendors
+
+First and foremost, SD-WAN unable to address the security challenges that arise during the WAN transformation. Such security challenges include protection against malware, ransomware and implementing the necessary security policies. Besides, there is a lack of visibility that is required to police the mobile users and remote site locations accessing resources in the public cloud.
+
+To combat this, organizations have to purchase additional equipment. There has always been and will always be a high cost associated with buying such security appliances. Furthermore, the additional tools that are needed to protect the remote site locations increase the network complexity and reduce visibility. Let’s us not forget that the variety of physical appliances require talented engineers for design, deployment and maintenance.
+
+There will often be a single network-cowboy. This means the network and security configuration along with the design essentials are stored in the mind of the engineer, not in a central database from where the knowledge can be accessed if the engineer leaves his or her employment.
+
+The physical appliance approach to SD-WAN makes it hard, if not impossible, to accommodate for the future. If the current SD-WAN vendors continue to focus just on connecting the devices with the physical appliances, they will have limited ability to accommodate for example, with the future of network IoT devices. With these factors in mind what are the available options to overcome the SD-WAN shortcomings?
+
+One can opt for a do it yourself (DIY) solution, or a managed service, which can fall into the category of telcos, with the improvements of either co-managed or self-managed service categories.
+
+### Option 1: The DIY solution
+
+Firstly DIY, from the experience of trying to stitch together a global network, this is not only costly but also complex and is a very constrained approach to the network transformation. We started with physical appliances decades ago and it was sufficient to an extent. The reason it worked was that it suited the requirements of the time, but our environment has changed since then. Hence, we need to accommodate these changes with the current requirements.
+
+Even back in those days, we always had a breachable perimeter. The perimeter-approach to networking and security never really worked and it was just a matter of time before the bad actor would penetrate the guarded walls.
+
+Securing a global network involves more than just firewalling the devices. A solid security perimeter requires URL filtering, anti-malware and IPS to secure the internet traffic. If you try to deploy all these functions in a single device, such as, unified threat management (UTM), you will hit scaling problems. As a result, you will be left with appliance sprawl.
+
+Back in my early days as an engineer, I recall stitching together a global network with a mixture of security and network appliances from a variety of vendors. It was me and just two others who used to get the job done on time and for a production network, our uptime levels were superior to most.
+
+However, it involved too many late nights, daily flights to our PoPs and of course the major changes required a forklift. A lot of work had to be done at that time, which made me want to push some or most of the work to a 3rd party.
+
+### Option 2: The managed service solution
+
+Today, there is a growing need for the managed service approach to SD-WAN. Notably, it simplifies the network design, deployment and maintenance activities while offloading the complexity, in line with what most CIOs are talking about today.
+
+Managed service provides a number of benefits, such as the elimination of backhauling to centralized cloud connectors or VPN concentrators. Evidently, backhauling is never favored for a network architect. More than often it will result in increased latency, congested links, internet chokepoints, and last-mile outages.
+
+Managed service can also authenticate mobile users at the local communication hub and not at a centralized point which would increase the latency. So what options are available when considering a managed service?
+
+### Telcos: An average service level
+
+Let’s be honest, telcos have a mixed track record and enterprises rely on them with caution. Essentially, you are building a network with 3rd party appliances and services that put the technical expertise outside of the organization.
+
+Secondly, the telco must orchestrate, monitor and manage numerous technical domains which are likely to introduce further complexity. As a result, troubleshooting requires close coordination with the suppliers which will have an impact on the customer experience.
+
+### Time equals money
+
+To resolve a query could easily take two or three attempts. It’s rare that you will get to the right person straight away. This eventually increases the time to resolve problems. Even for a minor feature change, you have to open tickets. Hence, with telcos, it increases the time required to solve a problem.
+
+In addition, it takes time to make major network changes such as opening new locations, which could take up to 45 days. In the same report mentioned above, 71% of the respondents are frustrated with the telco customer-service-time to resolve the problems, 73% indicated that deploying new locations requires at least 15 days and 47% claimed that “high bandwidth costs” is the biggest frustration while working with telcos.
+
+When it comes to lead times for projects, an engineer does not care. Does a project manager care if you have an optimum network design? No, many don’t, most just care about the timeframes. During my career, now spanning 18 years, I have never seen comments from any of my contacts saying “you must adhere to your project manager’s timelines”.
+
+However, out of the experience, the project managers have their ways and lead times do become a big part of your daily job. So as an engineer, 45-day lead time will certainly hit your brand hard, especially if you are an external consultant.
+
+There is also a problem with bandwidth costs. Telcos need to charge due to their complexity. There is always going to be a series of problems when working with them. Let’s face it, they offer an average service level.
+
+### Co-management and self-service management
+
+What is needed is a service that equips with the visibility and control of DIY to managed services. This, ultimately, opens the door to co-management and self-service management.
+
+Co-management allows both the telco and enterprise to make changes to the WAN. Then we have the self-service management of WAN that allows the enterprises to have sole access over the aspect of their network.
+
+However, these are just sticking plasters covering up the flaws. We need a managed service that not only connects locations but also synthesizes the site connectivity, along with security, mobile access, and cloud access.
+
+### Introducing the cloud-native approach to SD-WAN
+
+There should be a new style of managed services that combines the best of both worlds. It should offer the uptime, predictability and reach of the best telcos along with the cost structure and versatility of cloud providers. All such requirements can be met by what is known as the cloud-native carrier.
+
+Therefore, we should be looking for a platform that can connect and secure all the users and resources at scale, no matter where they are positioned. Eventually, such a platform will limit the costs and increase the velocity and agility.
+
+This is what a cloud-native carrier can offer you. You could say it’s a new kind of managed service, which is what enterprises are now looking for. A cloud-native carrier service brings the best of cloud services to the world of networking. This new style of managed service brings to SD-WAN the global reach, self-service, and agility of the cloud with the ability to easily migrate from MPLS.
+
+In summary, a cloud-native carrier service will improve global connectivity to on-premises and cloud applications, enable secure branch to internet access, and both securely and optimally integrate cloud datacenters.
+
+**This article is published as part of the IDG Contributor Network.[Want to Join?][4]**
+
+Join the Network World communities on [Facebook][5] and [LinkedIn][6] to comment on topics that are top of mind.
+
+--------------------------------------------------------------------------------
+
+via: https://www.networkworld.com/article/3398476/managed-wan-and-the-cloud-native-sd-wan.html
+
+作者:[Matt Conran][a]
+选题:[lujun9972][b]
+译者:[译者ID](https://github.com/译者ID)
+校对:[校对者ID](https://github.com/校对者ID)
+
+本文由 [LCTT](https://github.com/LCTT/TranslateProject) 原创编译,[Linux中国](https://linux.cn/) 荣誉推出
+
+[a]: https://www.networkworld.com/author/Matt-Conran/
+[b]: https://github.com/lujun9972
+[1]: https://images.techhive.com/images/article/2017/03/network-wan-100713693-large.jpg
+[2]: https://www.networkworld.com/article/2297171/sd-wan/network-security-mpls-explained.html
+[3]: https://www.catonetworks.com/news/digital-transformation-survey
+[4]: /contributor-network/signup.html
+[5]: https://www.facebook.com/NetworkWorld/
+[6]: https://www.linkedin.com/company/network-world
diff --git a/sources/talk/20190528 Moving to the Cloud- SD-WAN Matters.md b/sources/talk/20190528 Moving to the Cloud- SD-WAN Matters.md
new file mode 100644
index 0000000000..8f6f46b6f2
--- /dev/null
+++ b/sources/talk/20190528 Moving to the Cloud- SD-WAN Matters.md
@@ -0,0 +1,69 @@
+[#]: collector: (lujun9972)
+[#]: translator: ( )
+[#]: reviewer: ( )
+[#]: publisher: ( )
+[#]: url: ( )
+[#]: subject: (Moving to the Cloud? SD-WAN Matters!)
+[#]: via: (https://www.networkworld.com/article/3397921/moving-to-the-cloud-sd-wan-matters.html)
+[#]: author: (Rami Rammaha https://www.networkworld.com/author/Rami-Rammaha/)
+
+Moving to the Cloud? SD-WAN Matters!
+======
+
+![istock][1]
+
+This is the first in a two-part blog series that will explore how enterprises can realize the full transformation promise of the cloud by shifting to a business first networking model powered by a business-driven [SD-WAN][2]. The focus for this installment will be on automating secure IPsec connectivity and intelligently steering traffic to cloud providers.
+
+Over the past several years we’ve seen a major shift in data center strategies where enterprise IT organizations are shifting applications and workloads to cloud, whether private or public. More and more, enterprises are leveraging software as-a-service (SaaS) applications and infrastructure as-a-service (IaaS) cloud services from leading providers like [Amazon AWS][3], [Google Cloud][4], [Microsoft Azure][5] and [Oracle Cloud Infrastructure][6]. This represents a dramatic shift in enterprise data traffic patterns as fewer and fewer applications are hosted within the walls of the traditional corporate data center.
+
+There are several drivers for the shift to IaaS cloud services and SaaS apps, but business agility tops the list for most enterprises. The traditional IT model for provisioning and deprovisioning applications is rigid and inflexible and is no longer able to keep pace with changing business needs.
+
+According to [LogicMonitor’s Cloud Vision 2020][7] study, more than 80 percent of enterprise workloads will run in the cloud by 2020 with more than 40 percent running on public cloud platforms. This major shift in the application consumption model is having a huge [impact on organizations and infrastructure][8]. A recent article entitled “[How Amazon Web Services is luring banks to the cloud][9],” published by CNBC, reported that some companies already have completely migrated all of their applications and IT workloads to public cloud infrastructures. An interesting fact is that while many enterprises must comply with stringent regulatory compliance mandates such as PCI-DSS or HIPAA, they still have made the move to the cloud. This tells us two things – the maturity of using public cloud services and the trust these organizations have in using them is at an all-time high. Again, it is all about speed and agility – without compromising performance, security and reliability.
+
+### **Is there a direct correlation between moving to the cloud and adopting SD-WAN?**
+
+As the cloud enables businesses to move faster, an SD-WAN architecture where top-down business intent is the driver is critical to ensuring success, especially when branch offices are geographically distributed across the globe. Traditional router-centric WAN architectures were never designed to support today’s cloud consumption model for applications in the most efficient way. With a conventional router-centric WAN approach, access to applications residing in the cloud means traversing unnecessary hops, resulting in wasted bandwidth, additional cost, added latency and potentially higher packet loss. In addition, under the existing, traditional WAN model where management tends to be rigid, complex network changes can be lengthy, whether setting up new branches or troubleshooting performance issues. This leads to inefficiencies and a costly operational model. Therefore, enterprises greatly benefit from taking a business-first WAN approach toward achieving greater agility in addition to realizing substantial CAPEX and OPEX savings.
+
+A business-driven SD-WAN platform is purpose-built to tackle the challenges inherent to the traditional router-centric model and more aptly support today’s cloud consumption model. This means application policies are defined based on business intent, connecting users securely and directly to applications where ever they reside without unnecessary extra hops or security compromises. For example, if the application is hosted in the cloud and is trusted, a business-driven SD-WAN can automatically connect users to it without backhauling traffic to a POP or HQ data center. Now, in general this traffic is usually going across an internet link which, on its own, may not be secure. However, the right SD-WAN platform will have a unified stateful firewall built-in for local internet breakout allowing only branch-initiated sessions to enter the branch and providing the ability to service chain traffic to a cloud-based security service if necessary, before forwarding it to its final destination. If the application is moved and becomes hosted by another provider or perhaps back to a company’s own data center, traffic must be intelligently redirected, wherever the application is being hosted. Without automation and embedded machine learning, dynamic and intelligent traffic steering is impossible.
+
+### **A closer look at how the Silver Peak EdgeConnect™ SD-WAN edge platform addresses these challenges: **
+
+**Automate traffic steering and connectivity to cloud providers**
+
+An [EdgeConnect][10] virtual instance is easily spun up in any of the [leading cloud providers][11] through their respective marketplaces. For an SD-WAN to intelligently steer traffic to its destination, it requires insights into both HTTP and HTTPS traffic; it must be able to identify apps on the first packet received in order to steer traffic to the right destination in accordance with business intent. This is critical capability because once a TCP connection is NAT’d with a public IP address, it cannot be switched thus it can’t be re-routed once a connection is established. So, the ability of EdgeConnect to identify, classify and automatically steer traffic based on the first packet – and not the second or tenth packet – to the correct destination will assure application SLAs, minimize wasting expensive bandwidth and deliver the highest quality of experience.
+
+Another critical capability is automatic performance optimization. Irrespective of which link the traffic ends up traversing based on business intent and the unique requirements of the application, EdgeConnect automatically optimizes application performance without human intervention by correcting for out of order packets using Packet Order Correction (POC) or even under high latency conditions that can be related to distance or other issues. This is done using adaptive Forward Error Correction (FEC) and tunnel bonding where a virtual tunnel is created, resulting in a single logical overlay that traffic can be dynamically moved between the different paths as conditions change with each underlay WAN service. In this [lightboard video][12], Dinesh Fernando, a technical marketing engineer at Silver Peak, explains how EdgeConnect automates tunnel creation between sites and cloud providers, how it simplifies data transfers between multi-clouds, and how it improves application performance.
+
+If your business is global and increasingly dependent on the cloud, the business-driven EdgeConnect SD-WAN edge platform enables seamless multi-cloud connectivity, turning the network into a business accelerant. EdgeConnect delivers:
+
+ 1. A consistent deployment from the branch to the cloud, extending the reach of the SD-WAN into virtual private cloud environments
+ 2. Multi-cloud flexibility, making it easier to initiate and distribute resources across multiple cloud providers
+ 3. Investment protection by confidently migrating on premise IT resources to any combination of the leading public cloud platforms, knowing their cloud-hosted instances will be fully supported by EdgeConnect
+
+
+
+--------------------------------------------------------------------------------
+
+via: https://www.networkworld.com/article/3397921/moving-to-the-cloud-sd-wan-matters.html
+
+作者:[Rami Rammaha][a]
+选题:[lujun9972][b]
+译者:[译者ID](https://github.com/译者ID)
+校对:[校对者ID](https://github.com/校对者ID)
+
+本文由 [LCTT](https://github.com/LCTT/TranslateProject) 原创编译,[Linux中国](https://linux.cn/) 荣誉推出
+
+[a]: https://www.networkworld.com/author/Rami-Rammaha/
+[b]: https://github.com/lujun9972
+[1]: https://images.idgesg.net/images/article/2019/05/istock-899678028-100797709-large.jpg
+[2]: https://www.silver-peak.com/sd-wan/sd-wan-explained
+[3]: https://www.silver-peak.com/company/tech-partners/cloud/aws
+[4]: https://www.silver-peak.com/company/tech-partners/cloud/google-cloud
+[5]: https://www.silver-peak.com/company/tech-partners/cloud/microsoft-azure
+[6]: https://www.silver-peak.com/company/tech-partners/cloud/oracle-cloud
+[7]: https://www.logicmonitor.com/resource/the-future-of-the-cloud-a-cloud-influencers-survey/?utm_medium=pr&utm_source=businesswire&utm_campaign=cloudsurvey
+[8]: http://www.networkworld.com/article/3152024/lan-wan/in-the-age-of-digital-transformation-why-sd-wan-plays-a-key-role-in-the-transition.html
+[9]: http://www.cnbc.com/2016/11/30/how-amazon-web-services-is-luring-banks-to-the-cloud.html?__source=yahoo%257cfinance%257cheadline%257cheadline%257cstory&par=yahoo&doc=104135637
+[10]: https://www.silver-peak.com/products/unity-edge-connect
+[11]: https://www.silver-peak.com/company/tech-partners?strategic_partner_type=69
+[12]: https://www.silver-peak.com/resource-center/automate-connectivity-to-cloud-networking-with-sd-wan
diff --git a/sources/talk/20190528 With Cray buy, HPE rules but does not own the supercomputing market.md b/sources/talk/20190528 With Cray buy, HPE rules but does not own the supercomputing market.md
new file mode 100644
index 0000000000..07f9eea10c
--- /dev/null
+++ b/sources/talk/20190528 With Cray buy, HPE rules but does not own the supercomputing market.md
@@ -0,0 +1,59 @@
+[#]: collector: (lujun9972)
+[#]: translator: ( )
+[#]: reviewer: ( )
+[#]: publisher: ( )
+[#]: url: ( )
+[#]: subject: (With Cray buy, HPE rules but does not own the supercomputing market)
+[#]: via: (https://www.networkworld.com/article/3397087/with-cray-buy-hpe-rules-but-does-not-own-the-supercomputing-market.html)
+[#]: author: (Andy Patrizio https://www.networkworld.com/author/Andy-Patrizio/)
+
+With Cray buy, HPE rules but does not own the supercomputing market
+======
+In buying supercomputer vendor Cray, HPE has strengthened its high-performance-computing technology, but serious competitors remain.
+![Cray Inc.][1]
+
+Hewlett Packard Enterprise was already the leader in the high-performance computing (HPC) sector before its announced acquisition of supercomputer maker Cray earlier this month. Now it has a commanding lead, but there are still competitors to the giant.
+
+The news that HPE would shell out $1.3 billion to buy the company came just as Cray had announced plans to build three of the biggest systems yet — all exascale, and all with the same deployment time of 2021.
+
+Sales had been slowing for HPC systems, but our government, with its endless supply of money, came to the rescue, throwing hundreds of millions at Cray for systems to be built at Lawrence Berkeley National Laboratory, Argonne National Laboratory and Oak Ridge National Laboratory.
+
+**[ Read also:[How to plan a software-defined data-center network][2] ]**
+
+And HPE sees a big revenue opportunity in HPC, a market that was $2 billion in 1990 and now nearly $30 billion, according to Steve Conway, senior vice president with Hyperion Research, which follows the HPC market. HPE thinks the HPC market will grow to $35 billion by 2021, and it hopes to earn a big chunk of that pie.
+
+“They were solidly in the lead without Cray. They were already in a significant lead over the No. 2 company, Dell. This adds to their lead and gives them access to very high end of market, especially government supercomputers that sell for $300 million to $600 million each,” said Conway.
+
+He’s not exaggerating. Earlier this month the U.S. Department of Energy announced a contract with Cray to build Frontier, an exascale supercomputer at Oak Ridge National Laboratory, sometime in 2021, with a $600 million price tag. Frontier will be powered by AMD Epyc processors and Radeon GPUs, which must have them doing backflips at AMD.
+
+With Cray, HPE is sitting on a lot of technology for the supercomputing and even the high-end, non-HPC market. It had the ProLiant business, the bulk of server sales (and proof the Compaq acquisition wasn’t such a bad idea), Integrity NonStop mission-critical servers, the SGI business it acquired in in 2016, plus a variety running everything from Arm to Xeon Scalable processors.
+
+Conway thinks all of those technologies fit in different spaces, so he doubts HPE will try to consolidate any of it. All HPE has said so far is it will keep the supercomputer products it has now under the Cray business unit.
+
+But the company is still getting something it didn’t have. “It takes a certain kind of technical experience [to do HPC right] and only a few companies able to play at that level. Before this deal, HPE was not one of them,” said Conway.
+
+And in the process, HPE takes Cray away from its many competitors: IBM, Lenovo, Dell/EMC, Huawei (well, not so much now), Super Micro, NEC, Hitachi, Fujitsu, and Atos.
+
+“[The acquisition] doesn’t fundamentally change things because there’s still enough competitors that buyers can have competitive bids. But it’s gotten to be a much bigger market,” said Conway.
+
+Cray sells a lot to government, but Conway thinks there is a new opportunity in the ever-expanding AI race. “Because HPC is indispensable at the forefront of AI, there is a new area for expanding the market,” he said.
+
+Join the Network World communities on [Facebook][3] and [LinkedIn][4] to comment on topics that are top of mind.
+
+--------------------------------------------------------------------------------
+
+via: https://www.networkworld.com/article/3397087/with-cray-buy-hpe-rules-but-does-not-own-the-supercomputing-market.html
+
+作者:[Andy Patrizio][a]
+选题:[lujun9972][b]
+译者:[译者ID](https://github.com/译者ID)
+校对:[校对者ID](https://github.com/校对者ID)
+
+本文由 [LCTT](https://github.com/LCTT/TranslateProject) 原创编译,[Linux中国](https://linux.cn/) 荣誉推出
+
+[a]: https://www.networkworld.com/author/Andy-Patrizio/
+[b]: https://github.com/lujun9972
+[1]: https://images.idgesg.net/images/article/2018/06/the_cray_xc30_piz_daint_system_at_the_swiss_national_supercomputing_centre_via_cray_inc_3x2_978x652-100762113-large.jpg
+[2]: https://www.networkworld.com/article/3284352/data-center/how-to-plan-a-software-defined-data-center-network.html
+[3]: https://www.facebook.com/NetworkWorld/
+[4]: https://www.linkedin.com/company/network-world
diff --git a/sources/talk/20190529 Cisco security spotlights Microsoft Office 365 e-mail phishing increase.md b/sources/talk/20190529 Cisco security spotlights Microsoft Office 365 e-mail phishing increase.md
new file mode 100644
index 0000000000..c1e0493e63
--- /dev/null
+++ b/sources/talk/20190529 Cisco security spotlights Microsoft Office 365 e-mail phishing increase.md
@@ -0,0 +1,92 @@
+[#]: collector: (lujun9972)
+[#]: translator: ( )
+[#]: reviewer: ( )
+[#]: publisher: ( )
+[#]: url: ( )
+[#]: subject: (Cisco security spotlights Microsoft Office 365 e-mail phishing increase)
+[#]: via: (https://www.networkworld.com/article/3398925/cisco-security-spotlights-microsoft-office-365-e-mail-phishing-increase.html)
+[#]: author: (Michael Cooney https://www.networkworld.com/author/Michael-Cooney/)
+
+Cisco security spotlights Microsoft Office 365 e-mail phishing increase
+======
+Cisco blog follows DHS Cybersecurity and Infrastructure Security Agency (CISA) report detailing risks around Office 365 and other cloud services
+![weerapatkiatdumrong / Getty Images][1]
+
+It’s no secret that if you have a cloud-based e-mail service, fighting off the barrage of security issues has become a maddening daily routine.
+
+The leading e-mail service – in [Microsoft’s Office 365][2] package – seems to be getting the most attention from those attackers hellbent on stealing enterprise data or your private information via phishing attacks. Amazon and Google see their share of phishing attempts in their cloud-based services as well.
+
+**[ Also see[What to consider when deploying a next generation firewall][3]. | Get regularly scheduled insights by [signing up for Network World newsletters][4]. ]**
+
+But attackers are crafting and launching phishing campaigns targeting Office 365 users, [wrote][5] Ben Nahorney, a Threat Intelligence Analyst focused on covering the threat landscape for Cisco Security in a blog focusing on the Office 365 phishing issue.
+
+Nahorney wrote of research from security vendor [Agari Data][6], that found over the last few quarters, there has been a steady increase in the number of phishing emails impersonating Microsoft. While Microsoft has long been the most commonly impersonated brand, it now accounts for more than half of all brand impersonations seen in the last quarter.
+
+Recently cloud security firm Avanan wrote in its [annual phishing report][7], one in every 99 emails is a phishing attack, using malicious links and attachments as the main vector. “Of the phishing attacks we analyzed, 25 percent bypassed Office 365 security, a number that is likely to increase as attackers design new obfuscation methods that take advantage of zero-day vulnerabilities on the platform,” Avanan wrote.
+
+The attackers attempt to steal a user’s login credentials with the goal of taking over accounts. If successful, attackers can often log into the compromised accounts, and perform a wide variety of malicious activity: Spread malware, spam and phishing emails from within the internal network; carry out tailored attacks such as spear phishing and [business email compromise][8] [a long-standing business scam that uses spear-phishing, social engineering, identity theft, e-mail spoofing], and target partners and customers, Nahorney wrote.
+
+Nahorney wrote that at first glance, this may not seem very different than external email-based attacks. However, there is one critical distinction: The malicious emails sent are now coming from legitimate accounts.
+
+**[[Prepare to become a Certified Information Security Systems Professional with this comprehensive online course from PluralSight. Now offering a 10-day free trial!][9] ]**
+
+“For the recipient, it’s often even someone that they know, eliciting trust in a way that would not necessarily be afforded to an unknown source. To make things more complicated, attackers often leverage ‘conversation hijacking,’ where they deliver their payload by replying to an email that’s already located in the compromised inbox,” Nahorney stated.
+
+The methods used by attackers to gain access to an Office 365 account are fairly straightforward, Nahorney wrote.
+
+“The phishing campaigns usually take the form of an email from Microsoft. The email contains a request to log in, claiming the user needs to reset their password, hasn’t logged in recently or that there’s a problem with the account that needs their attention. A URL is included, enticing the reader to click to remedy the issue,” Nahorney wrote.
+
+Once logged in, nefarious activities can go on unnoticed as the attacker has what look like authorized credentials.
+
+“This gives the attacker time for reconnaissance: a chance to observe and plan additional attacks. Nor will this type of attack set off a security alert in the same way something like a brute-force attack against a webmail client will, where the attacker guesses password after password until they get in or are detected,” Nahorney stated.
+
+Nahorney suggested the following steps customers can take to protect email:
+
+ * Use multi-factor authentication. If a login attempt requires a secondary authorization before someone is allowed access to an inbox, this will stop many attackers, even with phished credentials.
+ * Deploy advanced anti-phishing technologies. Some machine-learning technologies can use local identity and relationship modeling alongside behavioral analytics to spot deception-based threats.
+ * Run regular phishing exercises. Regular, mandated phishing exercises across the entire organization will help to train employees to recognize phishing emails, so that they don’t click on malicious URLs, or enter their credentials into malicious website.
+
+
+
+### Homeland Security flags Office 365, other cloud email services
+
+The U.S. government, too, has been warning customers of Office 365 and other cloud-based email services that they should be on alert for security risks. The US Department of Homeland Security's Cybersecurity and Infrastructure Security Agency (CISA) this month [issued a report targeting][10] Office 365 and other cloud services saying:
+
+“Organizations that used a third party have had a mix of configurations that lowered their overall security posture (e.g., mailbox auditing disabled, unified audit log disabled, multi-factor authentication disabled on admin accounts). In addition, the majority of these organizations did not have a dedicated IT security team to focus on their security in the cloud. These security oversights have led to user and mailbox compromises and vulnerabilities.”
+
+The agency also posted remediation suggestions including:
+
+ * Enable unified audit logging in the Security and Compliance Center.
+ * Enable mailbox auditing for each user.
+ * Ensure Azure AD password sync is planned for and configured correctly, prior to migrating users.
+ * Disable legacy email protocols, if not required, or limit their use to specific users.
+
+
+
+Join the Network World communities on [Facebook][11] and [LinkedIn][12] to comment on topics that are top of mind.
+
+--------------------------------------------------------------------------------
+
+via: https://www.networkworld.com/article/3398925/cisco-security-spotlights-microsoft-office-365-e-mail-phishing-increase.html
+
+作者:[Michael Cooney][a]
+选题:[lujun9972][b]
+译者:[译者ID](https://github.com/译者ID)
+校对:[校对者ID](https://github.com/校对者ID)
+
+本文由 [LCTT](https://github.com/LCTT/TranslateProject) 原创编译,[Linux中国](https://linux.cn/) 荣誉推出
+
+[a]: https://www.networkworld.com/author/Michael-Cooney/
+[b]: https://github.com/lujun9972
+[1]: https://images.idgesg.net/images/article/2019/05/cso_phishing_social_engineering_security_threat_by_weerapatkiatdumrong_gettyimages-489433130_3x2_2400x1600-100796450-large.jpg
+[2]: https://docs.microsoft.com/en-us/office365/securitycompliance/security-roadmap
+[3]: https://www.networkworld.com/article/3236448/lan-wan/what-to-consider-when-deploying-a-next-generation-firewall.html
+[4]: https://www.networkworld.com/newsletters/signup.html
+[5]: https://blogs.cisco.com/security/office-365-phishing-threat-of-the-month
+[6]: https://www.agari.com/
+[7]: https://www.avanan.com/hubfs/2019-Global-Phish-Report.pdf
+[8]: https://www.networkworld.com/article/3195072/fbi-ic3-vile-5b-business-e-mail-scam-continues-to-breed.html
+[9]: https://pluralsight.pxf.io/c/321564/424552/7490?u=https%3A%2F%2Fwww.pluralsight.com%2Fpaths%2Fcertified-information-systems-security-professional-cisspr
+[10]: https://www.us-cert.gov/ncas/analysis-reports/AR19-133A
+[11]: https://www.facebook.com/NetworkWorld/
+[12]: https://www.linkedin.com/company/network-world
diff --git a/sources/talk/20190529 Nvidia launches edge computing platform for AI processing.md b/sources/talk/20190529 Nvidia launches edge computing platform for AI processing.md
new file mode 100644
index 0000000000..f608db970c
--- /dev/null
+++ b/sources/talk/20190529 Nvidia launches edge computing platform for AI processing.md
@@ -0,0 +1,53 @@
+[#]: collector: (lujun9972)
+[#]: translator: ( )
+[#]: reviewer: ( )
+[#]: publisher: ( )
+[#]: url: ( )
+[#]: subject: (Nvidia launches edge computing platform for AI processing)
+[#]: via: (https://www.networkworld.com/article/3397841/nvidia-launches-edge-computing-platform-for-ai-processing.html)
+[#]: author: (Andy Patrizio https://www.networkworld.com/author/Andy-Patrizio/)
+
+Nvidia launches edge computing platform for AI processing
+======
+EGX platform goes to the edge to do as much processing there as possible before sending data upstream to major data centers.
+![Leo Wolfert / Getty Images][1]
+
+Nvidia is launching a new platform called EGX Platform designed to bring real-time artificial intelligence (AI) to edge networks. The idea is to put AI computing closer to where sensors collect data before it is sent to larger data centers.
+
+The edge serves as a buffer to data sent to data centers. It whittles down the data collected and only sends what is relevant up to major data centers for processing. This can mean discarding more than 90% of data collected, but the trick is knowing which data to keep and which to discard.
+
+“AI is required in this data-driven world,” said Justin Boitano, senior director for enterprise and edge computing at Nvidia, on a press call last Friday. “We analyze data near the source, capture anomalies and report anomalies back to the mothership for analysis.”
+
+**[ Now read[20 hot jobs ambitious IT pros should shoot for][2]. ]**
+
+Boitano said we are hitting crossover where there is more compute at edge than cloud because more work needs to be done there.
+
+EGX comes from 14 server vendors in a range of form factors, combining AI with network, security and storage from Mellanox. Boitano said that the racks will fit in any industry-standard rack, so they will fit into edge containers from the likes of Vapor IO and Schneider Electric.
+
+EGX uses Nvidia’s low-power Jetson Nano processor, but also all the way up to Nvidia T4 processors that can deliver more than 10,000 trillion operations per second (TOPS) for real-time speech recognition and other real-time AI tasks.
+
+Nvdia is working on software stack called Nvidia Edge Stack that can be updated constantly, and the software runs in containers, so no reboots are required, just a restart of the container. EGX runs enterprise-grade Kubernetes container platforms like Red Hat Openshift.
+
+Edge Stack is optimized software that includes Nvidia drivers, a CUDA Kubernetes plugin, a CUDA container runtime, CUDA-X libraries and containerized AI frameworks and applications, including TensorRT, TensorRT Inference Server and DeepStream.
+
+The company is boasting more than 40 early adopters, including BMW Group Logistics, which uses EGX and its own Isaac robotic platforms to handle increasingly complex logistics with real-time efficiency.
+
+Join the Network World communities on [Facebook][3] and [LinkedIn][4] to comment on topics that are top of mind.
+
+--------------------------------------------------------------------------------
+
+via: https://www.networkworld.com/article/3397841/nvidia-launches-edge-computing-platform-for-ai-processing.html
+
+作者:[Andy Patrizio][a]
+选题:[lujun9972][b]
+译者:[译者ID](https://github.com/译者ID)
+校对:[校对者ID](https://github.com/校对者ID)
+
+本文由 [LCTT](https://github.com/LCTT/TranslateProject) 原创编译,[Linux中国](https://linux.cn/) 荣誉推出
+
+[a]: https://www.networkworld.com/author/Andy-Patrizio/
+[b]: https://github.com/lujun9972
+[1]: https://images.idgesg.net/images/article/2019/02/industry_4-0_industrial_iot_smart_factory_by_leowolfert_gettyimages-689799380_2400x1600-100788464-large.jpg
+[2]: https://www.networkworld.com/article/3276025/careers/20-hot-jobs-ambitious-it-pros-should-shoot-for.html
+[3]: https://www.facebook.com/NetworkWorld/
+[4]: https://www.linkedin.com/company/network-world
diff --git a/sources/talk/20190529 Satellite-based internet possible by year-end, says SpaceX.md b/sources/talk/20190529 Satellite-based internet possible by year-end, says SpaceX.md
new file mode 100644
index 0000000000..383fac66ca
--- /dev/null
+++ b/sources/talk/20190529 Satellite-based internet possible by year-end, says SpaceX.md
@@ -0,0 +1,63 @@
+[#]: collector: (lujun9972)
+[#]: translator: ( )
+[#]: reviewer: ( )
+[#]: publisher: ( )
+[#]: url: ( )
+[#]: subject: (Satellite-based internet possible by year-end, says SpaceX)
+[#]: via: (https://www.networkworld.com/article/3398940/space-internet-maybe-end-of-year-says-spacex.html)
+[#]: author: (Patrick Nelson https://www.networkworld.com/author/Patrick-Nelson/)
+
+Satellite-based internet possible by year-end, says SpaceX
+======
+Amazon, Tesla-associated SpaceX and OneWeb are emerging as just some of the potential suppliers of a new kind of data-friendly satellite internet service that could bring broadband IoT connectivity to most places on Earth.
+![Getty Images][1]
+
+With SpaceX’s successful launch of an initial array of broadband-internet-carrying satellites last week, and Amazon’s surprising posting of numerous satellite engineering-related job openings on its [job board][2] this month, one might well be asking if the next-generation internet space race is finally getting going. (I first wrote about [OneWeb’s satellite internet plans][3] it was concocting with Airbus four years ago.)
+
+This new batch of satellite-driven internet systems, if they work and are eventually switched on, could provide broadband to most places, including previously internet-barren locations, such as rural areas. That would be good for high-bandwidth, low-latency remote-internet of things (IoT) and increasingly important edge-server connections for verticals like oil and gas and maritime. [Data could even end up getting stored in compliance-friendly outer space, too][4]. Leaky ground-based connections, also, perhaps a thing of the past.
+
+Of the principal new internet suppliers, SpaceX has gotten farthest along. That’s in part because it has commercial impetus. It needed to create payload for its numerous rocket projects. The Tesla electric-car-associated company (the two firms share materials science) has not only launched its first tranche of 60 satellites for its own internet constellation, called Starlink, but also successfully launched numerous batches (making up the full constellation of 75 satellites) for Iridium’s replacement, an upgraded constellation called Iridium NEXT.
+
+[The time of 5G is almost here][5]
+
+Potential competitor OneWeb launched its first six Airbus-built satellites in February. [It has plans for 900 more][6]. SpaceX has been approved for 4,365 more by the FCC, and Project Kuiper, as Amazon’s space internet project is known, wants to place 3,236 satellites in orbit, according to International Telecommunication Union filings [discovered by _GeekWire_][7] earlier this year. [Startup LeoSat, which I wrote about last year, aims to build an internet backbone constellation][8]. Facebook, too, is exploring [space-delivered internet][9].
+
+### Why the move to space?
+
+Laser technical progress, where data is sent in open, free space, rather than via a restrictive, land-based cable or via traditional radio paths, is partly behind this space-internet rush. “Bits travel faster in free space than in glass-fiber cable,” LeoSat explained last year. Additionally, improving microprocessor tech is also part of the mix.
+
+One important difference from existing older-generation satellite constellations is that this new generation of internet satellites will be located in low Earth orbit (LEO). Initial Starlink satellites will be placed at about 350 miles above Earth, with later launches deployed at 710 miles.
+
+There’s an advantage to that. Traditional satellites in geostationary orbit, or GSO, have been deployed about 22,000 miles up. That extra distance versus LEO introduces latency and is one reason earlier generations of Internet satellites are plagued by slow round-trip times. Latency didn’t matter when GSO was introduced in 1964, and commercial satellites, traditionally, have been pitched as one-way video links, such as are used by sporting events for broadcast, and not for data.
+
+And when will we get to experience these new ISPs? “Starlink is targeted to offer service in the Northern U.S. and Canadian latitudes after six launches,” [SpaceX says on its website][10]. Each launch would deliver about 60 satellites. “SpaceX is targeting two to six launches by the end of this year.”
+
+Global penetration of the “populated world” could be obtained after 24 launches, it thinks.
+
+Join the Network World communities on [Facebook][11] and [LinkedIn][12] to comment on topics that are top of mind.
+
+--------------------------------------------------------------------------------
+
+via: https://www.networkworld.com/article/3398940/space-internet-maybe-end-of-year-says-spacex.html
+
+作者:[Patrick Nelson][a]
+选题:[lujun9972][b]
+译者:[译者ID](https://github.com/译者ID)
+校对:[校对者ID](https://github.com/校对者ID)
+
+本文由 [LCTT](https://github.com/LCTT/TranslateProject) 原创编译,[Linux中国](https://linux.cn/) 荣誉推出
+
+[a]: https://www.networkworld.com/author/Patrick-Nelson/
+[b]: https://github.com/lujun9972
+[1]: https://images.idgesg.net/images/article/2018/10/network_iot_world-map_us_globe_nodes_global-100777483-large.jpg
+[2]: https://www.amazon.jobs/en/teams/projectkuiper
+[3]: https://www.itworld.com/article/2938652/space-based-internet-starts-to-get-serious.html
+[4]: https://www.networkworld.com/article/3200242/data-should-be-stored-data-in-space-firm-says.html
+[5]: https://www.networkworld.com/article/3354477/mobile-world-congress-the-time-of-5g-is-almost-here.html
+[6]: https://www.airbus.com/space/telecommunications-satellites/oneweb-satellites-connection-for-people-all-over-the-globe.html
+[7]: https://www.geekwire.com/2019/amazon-lists-scores-jobs-bellevue-project-kuiper-broadband-satellite-operation/
+[8]: https://www.networkworld.com/article/3328645/space-data-backbone-gets-us-approval.html
+[9]: https://www.networkworld.com/article/3338081/light-based-computers-to-be-5000-times-faster.html
+[10]: https://www.starlink.com/
+[11]: https://www.facebook.com/NetworkWorld/
+[12]: https://www.linkedin.com/company/network-world
diff --git a/sources/talk/20190529 Survey finds SD-WANs are hot, but satisfaction with telcos is not.md b/sources/talk/20190529 Survey finds SD-WANs are hot, but satisfaction with telcos is not.md
new file mode 100644
index 0000000000..9b65a6c8dd
--- /dev/null
+++ b/sources/talk/20190529 Survey finds SD-WANs are hot, but satisfaction with telcos is not.md
@@ -0,0 +1,69 @@
+[#]: collector: (lujun9972)
+[#]: translator: ( )
+[#]: reviewer: ( )
+[#]: publisher: ( )
+[#]: url: ( )
+[#]: subject: (Survey finds SD-WANs are hot, but satisfaction with telcos is not)
+[#]: via: (https://www.networkworld.com/article/3398478/survey-finds-sd-wans-are-hot-but-satisfaction-with-telcos-is-not.html)
+[#]: author: (Zeus Kerravala https://www.networkworld.com/author/Zeus-Kerravala/)
+
+Survey finds SD-WANs are hot, but satisfaction with telcos is not
+======
+A recent survey of over 400 IT executives by Cato Networks found that legacy telcos might be on the outside looking in for SD-WANs.
+![istock][1]
+
+This week SD-WAN vendor Cato Networks announced the results of its [Telcos and the Future of the WAN in 2019 survey][2]. The study was a mix of companies of all sizes, with 42% being enterprise-class (over 2,500 employees). More than 70% had a network with more than 10 locations, and almost a quarter (24%) had over 100 sites. All of the respondents have a cloud presence, and almost 80% have at least two data centers. The survey had good geographic diversity, with 57% of respondents coming from the U.S. and 24% from Europe.
+
+Highlights of the survey include the following key findings:
+
+## **SD-WANs are hot but not a panacea to all networking challenges**
+
+The survey found that 44% of respondents have already deployed or will deploy an SD-WAN within the next 12 months. This number is up sharply from 25% when Cato ran the survey a year ago. Another 33% are considering SD-WAN but have no immediate plans to deploy. The primary drivers for the evolution of the WAN are improved internet access (46%), increased bandwidth (39%), improved last-mile availability (38%) and reduced WAN costs (37%). It’s good to see cost savings drop to fourth in motivation, since there is so much more to SD-WAN.
+
+[The time of 5G is almost here][3]
+
+It’s interesting that the majority of respondents believe SD-WAN alone can’t address all challenges facing the WAN. A whopping 85% stated they would be confronting issues not addressed by SD-WAN alone. This includes secure, local internet breakout, improved visibility, and control over mobile access to cloud apps. This indicates that customers are looking for SD-WAN to be the foundation of the WAN but understand that other technologies need to be deployed as well.
+
+## **Telco dissatisfaction is high**
+
+The traditional telco has been a point of frustration for network professionals for years, and the survey spelled that out loud and clear. Prior to being an analyst, I held a number of corporate IT positions and found telcos to be the single most frustrating group of companies to deal with. The problem was, there was no choice. If you need MPLS services, you need a telco. The same can’t be said for SD-WANs, though; businesses have more choices.
+
+Respondents to the survey ranked telco service as “average.” It’s been well documented that we are now in the customer-experience era and “good enough” service is no longer good enough. Regarding pricing, 54% gave telcos a failing grade. Although price isn’t everything, this will certainly open the door to competitive SD-WAN vendors. Respondents gave the highest marks for overall experience to SaaS providers, followed by cloud computing suppliers. Global telcos scored the lowest of all vendor types.
+
+A look deeper explains the frustration level. The network is now mission-critical for companies, but 48% stated they are able to reach the support personnel with the right expertise to solve a problem only on a second attempt. No retailer, airline, hotel or other type of company could survive this, but telco customers had no other options for years.
+
+**[[Prepare to become a Certified Information Security Systems Professional with this comprehensive online course from PluralSight. Now offering a 10-day free trial!][4] ]**
+
+Another interesting set of data points is the speed at which telcos address customer needs. Digital businesses compete on speed, but telco process is the antithesis of fast. Moves, adds and changes take at least one business day for half of the respondents. Also, 70% indicated that opening a new location takes 15 days, and 38% stated it requires 45 days or more.
+
+## **Security is now part of SD-WAN**
+
+The use of broadband, cloud access and other trends raise the bar on security for SD-WAN, and the survey confirmed that respondents are skeptical that SD-WANs could address these issues. Seventy percent believe SD-WANs can’t address malware/ransomware, and 49% don’t think SD-WAN helps with enforcing company policies on mobile users. Because of this, network professionals are forced to buy additional security tools from other vendors, but that can drive up complexity. SD-WAN vendors that have intrinsic security capabilities can use that as a point of differentiation.
+
+## **Managed services are critical to the growth of SD-WANs**
+
+The survey found that 75% of respondents are using some kind of managed service provider, versus only 25% using an appliance vendor. This latter number was 32% last year. I’m not surprised by this shift and expect it to continue. Legacy WANs were inefficient but straightforward to deploy. D-WANs are highly agile and more cost-effective, but complexity has gone through the roof. Network engineers need to factor in cloud connectivity, distributed security, application performance, broadband connectivity and other issues. Managed services can help businesses enjoy the benefits of SD-WAN while masking the complexity.
+
+Despite the desire to use an MSP, respondents don’t want to give up total control. Eighty percent stated they preferred self-service or co-managed models. This further explains the shift away from telcos, since they typically work with fully managed models.
+
+Join the Network World communities on [Facebook][5] and [LinkedIn][6] to comment on topics that are top of mind.
+
+--------------------------------------------------------------------------------
+
+via: https://www.networkworld.com/article/3398478/survey-finds-sd-wans-are-hot-but-satisfaction-with-telcos-is-not.html
+
+作者:[Zeus Kerravala][a]
+选题:[lujun9972][b]
+译者:[译者ID](https://github.com/译者ID)
+校对:[校对者ID](https://github.com/校对者ID)
+
+本文由 [LCTT](https://github.com/LCTT/TranslateProject) 原创编译,[Linux中国](https://linux.cn/) 荣誉推出
+
+[a]: https://www.networkworld.com/author/Zeus-Kerravala/
+[b]: https://github.com/lujun9972
+[1]: https://images.idgesg.net/images/article/2018/02/istock-465661573-100750447-large.jpg
+[2]: https://www.catonetworks.com/news/digital-transformation-survey/
+[3]: https://www.networkworld.com/article/3354477/mobile-world-congress-the-time-of-5g-is-almost-here.html
+[4]: https://pluralsight.pxf.io/c/321564/424552/7490?u=https%3A%2F%2Fwww.pluralsight.com%2Fpaths%2Fcertified-information-systems-security-professional-cisspr
+[5]: https://www.facebook.com/NetworkWorld/
+[6]: https://www.linkedin.com/company/network-world
diff --git a/sources/talk/20190601 HPE Synergy For Dummies.md b/sources/talk/20190601 HPE Synergy For Dummies.md
new file mode 100644
index 0000000000..1b7ddbe2e7
--- /dev/null
+++ b/sources/talk/20190601 HPE Synergy For Dummies.md
@@ -0,0 +1,77 @@
+[#]: collector: (lujun9972)
+[#]: translator: ( )
+[#]: reviewer: ( )
+[#]: publisher: ( )
+[#]: url: ( )
+[#]: subject: (HPE Synergy For Dummies)
+[#]: via: (https://www.networkworld.com/article/3399618/hpe-synergy-for-dummies.html)
+[#]: author: (HPE https://www.networkworld.com/author/Michael-Cooney/)
+
+HPE Synergy For Dummies
+======
+
+![istock/venimo][1]
+
+Business must move fast today to keep up with competitive forces. That means IT must provide an agile — anytime, anywhere, any workload — infrastructure that ensures growth, boosts productivity, enhances innovation, improves the customer experience, and reduces risk.
+
+A composable infrastructure helps organizations achieve these important objectives that are difficult — if not impossible — to achieve via traditional means, such as the ability to do the following:
+
+ * Deploy quickly with simple flexing, scaling, and updating
+ * Run workloads anywhere — on physical servers, on virtual servers, or in containers
+ * Operate any workload upon which the business depends, without worrying about infrastructure resources or compatibility
+ * Ensure the infrastructure is able to provide the right service levels so the business can stay in business
+
+
+
+In other words, IT must inherently become part of the fabric of products and services that are rapidly innovated at every company, with an anytime, anywhere, any workload infrastructure.
+
+**The anytime paradigm**
+
+For organizations that seek to embrace DevOps, collaboration is the cultural norm. Development and operations staff work side‐by‐side to support software across its entire life cycle, from initial idea to production support.
+
+To provide DevOps groups — as well as other stakeholders — the IT infrastructure required at the rate at which it is demanded, enterprise IT must increase its speed, agility, and flexibility to enable people anytime composition and re‐composition of resources. Composable infrastructure enables this anytime paradigm.
+
+**The anywhere ability**
+
+Bare metal and virtualized workloads are just two application foundations that need to be supported in the modern data center. Today, containers are emerging as a compelling construct, providing significant benefits for certain kinds of workloads. Unfortunately, with traditional infrastructure approaches, IT needs to build out custom, unique infrastructure to support them, at least until an infrastructure is deployed that can seamlessly handle physical, virtual, and container‐based workloads.
+
+Each environment would need its own hardware and software and might even need its own staff members supporting it.
+
+Composable infrastructure provides an environment that supports the ability to run physical, virtual, or containerized workloads.
+
+**Support any workload**
+
+Do you have a legacy on‐premises application that you have to keep running? Do you have enterprise resource planning (ERP) software that currently powers your business but that will take ten years to phase out? At the same time, do you have an emerging DevOps philosophy under which you’d like to empower developers to dynamically create computing environments as a part of their development efforts?
+
+All these things can be accomplished simultaneously on the right kind of infrastructure. Composable infrastructure enables any workload to operate as a part of the architecture.
+
+**HPE Synergy**
+
+HPE Synergy brings to life the architectural principles of composable infrastructure. It is a single, purpose-built platform that reduces operational complexity for workloads and increases operational velocity for applications and services.
+
+Download a copy of the [HPE Synergy for Dummies eBook][2] to learn how to:
+
+ * Infuse the IT architecture with the ability to enable agility, flexibility, and speed
+ * Apply composable infrastructure concepts to support both traditional and cloud-native applications
+ * Deploy HPE Synergy infrastructure to revolutionize workload support in the data center
+
+
+
+Also, you will find more information about HPE Synergy [here][3].
+
+--------------------------------------------------------------------------------
+
+via: https://www.networkworld.com/article/3399618/hpe-synergy-for-dummies.html
+
+作者:[HPE][a]
+选题:[lujun9972][b]
+译者:[译者ID](https://github.com/译者ID)
+校对:[校对者ID](https://github.com/校对者ID)
+
+本文由 [LCTT](https://github.com/LCTT/TranslateProject) 原创编译,[Linux中国](https://linux.cn/) 荣誉推出
+
+[a]: https://www.networkworld.com/author/Michael-Cooney/
+[b]: https://github.com/lujun9972
+[1]: https://images.idgesg.net/images/article/2019/06/istock-1026657600-100798064-large.jpg
+[2]: https://www.hpe.com/us/en/resources/integrated-systems/synergy-for-dummies.html
+[3]: http://hpe.com/synergy
diff --git a/sources/talk/20190601 True Hyperconvergence at Scale- HPE Simplivity With Composable Fabric.md b/sources/talk/20190601 True Hyperconvergence at Scale- HPE Simplivity With Composable Fabric.md
new file mode 100644
index 0000000000..97eb611ef8
--- /dev/null
+++ b/sources/talk/20190601 True Hyperconvergence at Scale- HPE Simplivity With Composable Fabric.md
@@ -0,0 +1,28 @@
+[#]: collector: (lujun9972)
+[#]: translator: ( )
+[#]: reviewer: ( )
+[#]: publisher: ( )
+[#]: url: ( )
+[#]: subject: (True Hyperconvergence at Scale: HPE Simplivity With Composable Fabric)
+[#]: via: (https://www.networkworld.com/article/3399619/true-hyperconvergence-at-scale-hpe-simplivity-with-composable-fabric.html)
+[#]: author: (HPE https://www.networkworld.com/author/Michael-Cooney/)
+
+True Hyperconvergence at Scale: HPE Simplivity With Composable Fabric
+======
+
+Many hyperconverged solutions only focus on software-defined storage. However, many networking functions and technologies can be consolidated for simplicity and scale in the data center. This video describes how HPE SimpliVity with Composable Fabric gives organizations the power to run any virtual machine anywhere, anytime. Read more about HPE SimpliVity [here][1].
+
+--------------------------------------------------------------------------------
+
+via: https://www.networkworld.com/article/3399619/true-hyperconvergence-at-scale-hpe-simplivity-with-composable-fabric.html
+
+作者:[HPE][a]
+选题:[lujun9972][b]
+译者:[译者ID](https://github.com/译者ID)
+校对:[校对者ID](https://github.com/校对者ID)
+
+本文由 [LCTT](https://github.com/LCTT/TranslateProject) 原创编译,[Linux中国](https://linux.cn/) 荣誉推出
+
+[a]: https://www.networkworld.com/author/Michael-Cooney/
+[b]: https://github.com/lujun9972
+[1]: https://hpe.com/info/simplivity
diff --git a/sources/talk/20190602 IoT Roundup- New research on IoT security, Microsoft leans into IoT.md b/sources/talk/20190602 IoT Roundup- New research on IoT security, Microsoft leans into IoT.md
new file mode 100644
index 0000000000..6d955c6485
--- /dev/null
+++ b/sources/talk/20190602 IoT Roundup- New research on IoT security, Microsoft leans into IoT.md
@@ -0,0 +1,71 @@
+[#]: collector: (lujun9972)
+[#]: translator: ( )
+[#]: reviewer: ( )
+[#]: publisher: ( )
+[#]: url: ( )
+[#]: subject: (IoT Roundup: New research on IoT security, Microsoft leans into IoT)
+[#]: via: (https://www.networkworld.com/article/3398607/iot-roundup-new-research-on-iot-security-microsoft-leans-into-iot.html)
+[#]: author: (Jon Gold https://www.networkworld.com/author/Jon-Gold/)
+
+IoT Roundup: New research on IoT security, Microsoft leans into IoT
+======
+Verizon sets up widely available narrow-band IoT service, while most Americans think IoT manufacturers should ensure their products protect personal information.
+As with any technology whose use is expanding at such speed, it can be tough to track exactly what’s going on in the [IoT][1] world – everything from basic usage numbers to customer attitudes to more in-depth slices of the market is constantly changing. Fortunately, the month of May brought several new pieces of research to light, which should help provide at least a partial outline of what’s really happening in IoT.
+
+### Internet of things polls
+
+Not all of the news is good. An IPSOS Mori poll performed on behalf of the Internet Society and Consumers International (respectively, an umbrella organization for open development and Internet use and a broad-based consumer advocacy group) found that, despite the skyrocketing numbers of smart devices in circulation around the world, more than half of users in large parts of the western world don’t trust those devices to safeguard their privacy.
+
+**More on IoT:**
+
+ * [What is the IoT? How the internet of things works][2]
+ * [What is edge computing and how it’s changing the network][3]
+ * [Most powerful Internet of Things companies][4]
+ * [10 Hot IoT startups to watch][5]
+ * [The 6 ways to make money in IoT][6]
+ * [What is digital twin technology? [and why it matters]][7]
+ * [Blockchain, service-centric networking key to IoT success][8]
+ * [Getting grounded in IoT networking and security][9]
+ * [Building IoT-ready networks must become a priority][10]
+ * [What is the Industrial IoT? [And why the stakes are so high]][11]
+
+
+
+While almost 70 percent of respondents owned connected devices, 55 percent said they didn’t feel their personal information was adequately protected by manufacturers. A further 28 percent said they had avoided using connected devices – smart home, fitness tracking and similar consumer gadgetry – primarily because they were concerned over privacy issues, and a whopping 85 percent of Americans agreed with the argument that manufacturers had a responsibility to produce devices that protected personal information.
+
+Those concerns are understandable, according to data from the Ponemon Institute, a tech-research organization. Its survey of corporate risk and security personnel, released in early May, found that there have been few concerted efforts to limit exposure to IoT-based security threats, and that those threats are sharply on the rise when compared to past years, with the percentage of organizations that had experienced a data breach related to unsecured IoT devices rising from 15 percent in fiscal 2017 to 26 percent in fiscal 2019.
+
+Beyond a lack of organizational wherewithal to address those threats, part of the problem in some verticals is technical. Security vendor Forescout said earlier this month that its research showed 40 percent of all healthcare IT environments had more than 20 different operating systems, and more than 30 percent had more than 100 – hardly an ideal situation for smooth patching and updating.
+
+To continue reading this article register now
+
+[Get Free Access][12]
+
+[Learn More][13] Existing Users [Sign In][12]
+
+--------------------------------------------------------------------------------
+
+via: https://www.networkworld.com/article/3398607/iot-roundup-new-research-on-iot-security-microsoft-leans-into-iot.html
+
+作者:[Jon Gold][a]
+选题:[lujun9972][b]
+译者:[译者ID](https://github.com/译者ID)
+校对:[校对者ID](https://github.com/校对者ID)
+
+本文由 [LCTT](https://github.com/LCTT/TranslateProject) 原创编译,[Linux中国](https://linux.cn/) 荣誉推出
+
+[a]: https://www.networkworld.com/author/Jon-Gold/
+[b]: https://github.com/lujun9972
+[1]: https://www.networkworld.com/article/3207535/what-is-iot-how-the-internet-of-things-works.html
+[2]: https://www.networkworld.com/article/3207535/internet-of-things/what-is-the-iot-how-the-internet-of-things-works.html
+[3]: https://www.networkworld.com/article/3224893/internet-of-things/what-is-edge-computing-and-how-it-s-changing-the-network.html
+[4]: https://www.networkworld.com/article/2287045/internet-of-things/wireless-153629-10-most-powerful-internet-of-things-companies.html
+[5]: https://www.networkworld.com/article/3270961/internet-of-things/10-hot-iot-startups-to-watch.html
+[6]: https://www.networkworld.com/article/3279346/internet-of-things/the-6-ways-to-make-money-in-iot.html
+[7]: https://www.networkworld.com/article/3280225/internet-of-things/what-is-digital-twin-technology-and-why-it-matters.html
+[8]: https://www.networkworld.com/article/3276313/internet-of-things/blockchain-service-centric-networking-key-to-iot-success.html
+[9]: https://www.networkworld.com/article/3269736/internet-of-things/getting-grounded-in-iot-networking-and-security.html
+[10]: https://www.networkworld.com/article/3276304/internet-of-things/building-iot-ready-networks-must-become-a-priority.html
+[11]: https://www.networkworld.com/article/3243928/internet-of-things/what-is-the-industrial-iot-and-why-the-stakes-are-so-high.html
+[12]: javascript://
+[13]: /learn-about-insider/
diff --git a/sources/talk/20190603 It-s time for the IoT to -optimize for trust.md b/sources/talk/20190603 It-s time for the IoT to -optimize for trust.md
new file mode 100644
index 0000000000..cc5aa9db7c
--- /dev/null
+++ b/sources/talk/20190603 It-s time for the IoT to -optimize for trust.md
@@ -0,0 +1,102 @@
+[#]: collector: (lujun9972)
+[#]: translator: ( )
+[#]: reviewer: ( )
+[#]: publisher: ( )
+[#]: url: ( )
+[#]: subject: (It’s time for the IoT to 'optimize for trust')
+[#]: via: (https://www.networkworld.com/article/3399817/its-time-for-the-iot-to-optimize-for-trust.html)
+[#]: author: (Fredric Paul https://www.networkworld.com/author/Fredric-Paul/)
+
+It’s time for the IoT to 'optimize for trust'
+======
+If we can't trust the internet of things (IoT) to gather accurate data and use it appropriately, IoT adoption and innovation are likely to suffer.
+![Bose][1]
+
+One of the strengths of internet of things (IoT) technology is that it can do so many things well. From smart toothbrushes to predictive maintenance on jetliners, the IoT has more use cases than you can count. The result is that various IoT uses cases require optimization for particular characteristics, from cost to speed to long life, as well as myriad others.
+
+But in a recent post, "[How the internet of things will change advertising][2]" (which you should definitely read), the always-insightful Stacy Higginbotham tossed in a line that I can’t stop thinking about: “It's crucial that the IoT optimizes for trust."
+
+**[ Read also: Network World's[corporate guide to addressing IoT security][3] ]**
+
+### Trust is the IoT's most important attribute
+
+Higginbotham was talking about optimizing for trust as opposed to clicks, but really, trust is more important than just about any other value in the IoT. It’s more important than bandwidth usage, more important than power usage, more important than cost, more important than reliability, and even more important than security and privacy (though they are obviously related). In fact, trust is the critical factor in almost every aspect of the IoT.
+
+Don’t believe me? Let’s take a quick look at some recent developments in the field:
+
+For one thing, IoT devices often don’t take good care of the data they collect from you. Over 90% of data transactions on IoT devices are not fully encrypted, according to a new [study from security company Zscaler][4]. The [problem][5], apparently, is that many companies have large numbers of consumer-grade IoT devices on their networks. In addition, many IoT devices are attached to the companies’ general networks, and if that network is breached, the IoT devices and data may also be compromised.
+
+In some cases, ownership of IoT data can raise surprisingly serious trust concerns. According to [Kaiser Health News][6], smartphone sleep apps, as well as smart beds and smart mattress pads, gather amazingly personal information: “It knows when you go to sleep. It knows when you toss and turn. It may even be able to tell when you’re having sex.” And while companies such as Sleep Number say they don’t share the data they gather, their written privacy policies clearly state that they _can_.
+
+### **Lack of trust may lead to new laws**
+
+In California, meanwhile, "lawmakers are pushing for new privacy rules affecting smart speakers” such as the Amazon Echo. According to the _[LA Times][7]_ , the idea is “to ensure that the devices don’t record private conversations without permission,” requiring a specific opt-in process. Why is this an issue? Because consumers—and their elected representatives—don’t trust that Amazon, or any IoT vendor, will do the right thing with the data it collects from the IoT devices it sells—perhaps because it turns out that thousands of [Amazon employees have been listening in on what Alexa users are][8] saying to their Echo devices.
+
+The trust issues get even trickier when you consider that Amazon reportedly considered letting Alexa listen to users even without a wake word like “Alexa” or “computer,” and is reportedly working on [wearable devices designed to read human emotions][9] from listening to your voice.
+
+“The trust has been breached,” said California Assemblyman Jordan Cunningham (R-Templeton) to the _LA Times_.
+
+As critics of the bill ([AB 1395][10]) point out, the restrictions matter because voice assistants require this data to improve their ability to correctly understand and respond to requests.
+
+### **Some first steps toward increasing trust**
+
+Perhaps recognizing that the IoT needs to be optimized for trust so that we are comfortable letting it do its job, Amazon recently introduced a new Alexa voice command: “[Delete what I said today][11].”
+
+Moves like that, while welcome, will likely not be enough.
+
+For example, a [new United Nations report][12] suggests that “voice assistants reinforce harmful gender stereotypes” when using female-sounding voices and names like Alexa and Siri. Put simply, “Siri’s ‘female’ obsequiousness—and the servility expressed by so many other digital assistants projected as young women—provides a powerful illustration of gender biases coded into technology products, pervasive in the technology sector and apparent in digital skills education.” I'm not sure IoT vendors are eager—or equipped—to tackle issues like that.
+
+**More on IoT:**
+
+ * [What is the IoT? How the internet of things works][13]
+ * [What is edge computing and how it’s changing the network][14]
+ * [Most powerful Internet of Things companies][15]
+ * [10 Hot IoT startups to watch][16]
+ * [The 6 ways to make money in IoT][17]
+ * [What is digital twin technology? [and why it matters]][18]
+ * [Blockchain, service-centric networking key to IoT success][19]
+ * [Getting grounded in IoT networking and security][20]
+ * [Building IoT-ready networks must become a priority][21]
+ * [What is the Industrial IoT? [And why the stakes are so high]][22]
+
+
+
+Join the Network World communities on [Facebook][23] and [LinkedIn][24] to comment on topics that are top of mind.
+
+--------------------------------------------------------------------------------
+
+via: https://www.networkworld.com/article/3399817/its-time-for-the-iot-to-optimize-for-trust.html
+
+作者:[Fredric Paul][a]
+选题:[lujun9972][b]
+译者:[译者ID](https://github.com/译者ID)
+校对:[校对者ID](https://github.com/校对者ID)
+
+本文由 [LCTT](https://github.com/LCTT/TranslateProject) 原创编译,[Linux中国](https://linux.cn/) 荣誉推出
+
+[a]: https://www.networkworld.com/author/Fredric-Paul/
+[b]: https://github.com/lujun9972
+[1]: https://images.idgesg.net/images/article/2018/09/bose-sleepbuds-2-100771579-large.jpg
+[2]: https://mailchi.mp/iotpodcast/stacey-on-iot-how-iot-changes-advertising?e=6bf9beb394
+[3]: https://www.networkworld.com/article/3269165/internet-of-things/a-corporate-guide-to-addressing-iot-security-concerns.html
+[4]: https://www.zscaler.com/blogs/research/iot-traffic-enterprise-rising-so-are-threats
+[5]: https://www.csoonline.com/article/3397044/over-90-of-data-transactions-on-iot-devices-are-unencrypted.html
+[6]: https://khn.org/news/a-wake-up-call-on-data-collecting-smart-beds-and-sleep-apps/
+[7]: https://www.latimes.com/politics/la-pol-ca-alexa-google-home-privacy-rules-california-20190528-story.html
+[8]: https://www.usatoday.com/story/tech/2019/04/11/amazon-employees-listening-alexa-customers/3434732002/
+[9]: https://www.bloomberg.com/news/articles/2019-05-23/amazon-is-working-on-a-wearable-device-that-reads-human-emotions
+[10]: https://leginfo.legislature.ca.gov/faces/billTextClient.xhtml?bill_id=201920200AB1395
+[11]: https://venturebeat.com/2019/05/29/amazon-launches-alexa-delete-what-i-said-today-voice-command/
+[12]: https://unesdoc.unesco.org/ark:/48223/pf0000367416.page=1
+[13]: https://www.networkworld.com/article/3207535/internet-of-things/what-is-the-iot-how-the-internet-of-things-works.html
+[14]: https://www.networkworld.com/article/3224893/internet-of-things/what-is-edge-computing-and-how-it-s-changing-the-network.html
+[15]: https://www.networkworld.com/article/2287045/internet-of-things/wireless-153629-10-most-powerful-internet-of-things-companies.html
+[16]: https://www.networkworld.com/article/3270961/internet-of-things/10-hot-iot-startups-to-watch.html
+[17]: https://www.networkworld.com/article/3279346/internet-of-things/the-6-ways-to-make-money-in-iot.html
+[18]: https://www.networkworld.com/article/3280225/internet-of-things/what-is-digital-twin-technology-and-why-it-matters.html
+[19]: https://www.networkworld.com/article/3276313/internet-of-things/blockchain-service-centric-networking-key-to-iot-success.html
+[20]: https://www.networkworld.com/article/3269736/internet-of-things/getting-grounded-in-iot-networking-and-security.html
+[21]: https://www.networkworld.com/article/3276304/internet-of-things/building-iot-ready-networks-must-become-a-priority.html
+[22]: https://www.networkworld.com/article/3243928/internet-of-things/what-is-the-industrial-iot-and-why-the-stakes-are-so-high.html
+[23]: https://www.facebook.com/NetworkWorld/
+[24]: https://www.linkedin.com/company/network-world
diff --git a/sources/talk/20190604 5G will augment Wi-Fi, not replace it.md b/sources/talk/20190604 5G will augment Wi-Fi, not replace it.md
new file mode 100644
index 0000000000..76346907f3
--- /dev/null
+++ b/sources/talk/20190604 5G will augment Wi-Fi, not replace it.md
@@ -0,0 +1,102 @@
+[#]: collector: (lujun9972)
+[#]: translator: (GraveAccent)
+[#]: reviewer: ( )
+[#]: publisher: ( )
+[#]: url: ( )
+[#]: subject: (5G will augment Wi-Fi, not replace it)
+[#]: via: (https://www.networkworld.com/article/3399978/5g-will-augment-wi-fi-not-replace-it.html)
+[#]: author: (Zeus Kerravala https://www.networkworld.com/author/Zeus-Kerravala/)
+
+5G will augment Wi-Fi, not replace it
+======
+Jeff Lipton, vice president of strategy and corporate development at Aruba, adds a dose of reality to the 5G hype, discussing how it and Wi-Fi will work together and how to maximize the value of both.
+![Thinkstock][1]
+
+There’s arguably no technology topic that’s currently hotter than [5G][2]. It was a major theme of the most recent [Mobile World Congress][3] show and has reared its head in other events such as Enterprise Connect and almost every vendor event I attend.
+
+Some vendors have positioned 5G as a panacea to all network problems and predict it will eradicate all other forms of networking. Views like that are obviously extreme, but I do believe that 5G will have an impact on the networking industry and is something that network engineers should be aware of.
+
+To help bring some realism to the 5G hype, I recently interviewed Jeff Lipton, vice president of strategy and corporate development at Aruba, a Hewlett Packard company, as I know HPE has been deeply involved in the evolution of both 5G and Wi-Fi.
+
+**[ Also read:[The time of 5G is almost here][3] ]**
+
+### Zeus Kerravala: 5G is being touted as the "next big thing." Do you see it that way?
+
+**Jeff Lipton:** The next big thing is connecting "things" and generating actionable insights and context from those things. 5G is one of the technologies that serve this trend. Wi-Fi 6 is another — so are edge compute, Bluetooth Low Energy (BLE), artificial intelligence (AI) and machine learning (ML). These all are important, and they each have a place.
+
+### Do you see 5G eclipsing Wi-Fi in the enterprise?
+
+![Jeff Lipton, VP of strategy and corporate development, Aruba][4]
+
+**Lipton:** No. 5G, like all cellular access, is appropriate if you need macro area coverage and high-speed handoffs. But it’s not ideal for most enterprise applications, where you generally don’t need these capabilities. From a performance standpoint, [Wi-Fi 6][5] and 5G are roughly equal on most metrics, including throughput, latency, reliability, and connection density. Where they aren’t close is economics, where Wi-Fi is far better. I don’t think many customers would be willing to trade Wi-Fi for 5G unless they need macro coverage or high-speed handoffs.
+
+### Can Wi-Fi and 5G coexist? How would an enterprise use 5G and Wi-Fi together?
+
+**Lipton:** Wi-Fi and 5G can and should be complementary. The 5G architecture decouples the cellular core and Radio Access Network (RAN). Consequently, Wi-Fi can be the enterprise radio front end and connect tightly with a 5G core. Since the economics of Wi-Fi — especially Wi-Fi 6 — are favorable and performance is extremely good, we envision many service providers using Wi-Fi as the radio front end for their 5G systems where it makes sense, as an alternative to Distributed Antenna (DAS) and small-cell systems.
+
+Wi-Fi and 5G can and should be complementary." — Jeff Lipton
+
+### If a business were considering moving to 5G only, how would this be done and how practical is it?
+
+**Lipton:** To use 5G for primary in-building access, a customer would need to upgrade their network and virtually all of their devices. 5G provides good coverage outdoors, but cellular signals can’t reliably penetrate buildings. And this problem will become worse with 5G, which partially relies on higher frequency radios. So service providers will need a way to provide indoor coverage. To provide this coverage, they propose deploying DAS or small-cell systems — paid for by the end customer. The customers would then connect their devices directly to these cellular systems and pay a service component for each device.
+
+**[[Take this mobile device management course from PluralSight and learn how to secure devices in your company without degrading the user experience.][6] ]**
+
+There are several problems with this approach. First, DAS and small-cell systems are significantly more expensive than Wi-Fi networks. And the cost doesn’t stop with the network. Every device would need to have a 5G cellular modem, which costs tens of dollars wholesale and usually over a hundred dollars to an end user. Since few, if any MacBooks, PCs, printers or AppleTVs today have 5G modems, these devices would need to be upgraded. I don’t believe many enterprises would be willing to pay this additional cost and upgrade most of their equipment for an unclear benefit.
+
+### Are economics a factor in the 5G versus Wi-Fi debate?
+
+**Lipton:** Economics is always a factor. Let’s focus the conversation on in-building enterprise applications, since this is the use case some carriers intend to target with 5G. We’ve already mentioned that upgrading to 5G would require enterprises to deploy expensive DAS or small-cell systems for in-building coverage, upgrade virtually all of their equipment to contain 5G modems, and pay service contracts for each of these devices. It’s also important to understand 5G cellular networks and DAS systems operate over licensed spectrum, which is analogous to a private highway. Service providers paid billions of dollars for this spectrum, and this expense needs to be monetized and embedded in service costs. So, from both deployment and lifecycle perspectives, Wi-Fi economics are favorable to 5G.
+
+### Are there any security implications of 5G versus Wi-Fi?
+
+**Lipton:** Cellular technologies are perceived by some to be more secure than Wi-Fi, but that’s not true. LTE is relatively secure, but it also has weak points. For example, LTE is vulnerable to a range of attacks, including data interception and device tracking, according to researchers at Purdue and the University of Iowa. 5G improves upon LTE security with multiple authentication methods and better key management.
+
+Wi-Fi security isn’t standing still either and continues to advance. Of course, Wi-Fi implementations that do not follow best practices, such as those without even basic password protection, are not optimal. But those configured with proper access controls and passwords are highly secure. With new standards — specifically, WPA3 and Enhanced Open — Wi-Fi network security has improved even further.
+
+It’s also important to keep in mind that enterprises have made enormous investments in security and compliance solutions tailored to their specific needs. With cellular networks, including 5G, enterprises lose the ability to deploy their chosen security and compliance solutions, as well as most visibility into traffic flows. While future versions of 5G will offer high-levels of customization with a feature called network slicing, enterprises would still lose the level of security and compliance customization they currently need and have.
+
+### Any parting thoughts to add to the discussion around 5G versus Wi-Fi?
+
+**Lipton:** The debate around Wi-Fi versus 5G misses the point. They each have their place, and they are in many ways complementary. The Wi-Fi and 5G markets both will grow, driven by the need to connect and analyze a growing number of things. If a customer needs macro coverage or high-speed handoffs and can pay the additional cost for these capabilities, 5G makes sense.
+
+5G also could be a fit for certain industrial use cases where customers require physical network segmentation. But for the vast majority of enterprise customers, Wi-Fi will continue to prove its value as a reliable, secure, and cost-effective wireless access technology, as it does today.
+
+**More about 802.11ax (Wi-Fi 6):**
+
+ * [Why 802.11ax is the next big thing in wireless][7]
+ * [FAQ: 802.11ax Wi-Fi][8]
+ * [Wi-Fi 6 (802.11ax) is coming to a router near you][9]
+ * [Wi-Fi 6 with OFDMA opens a world of new wireless possibilities][10]
+ * [802.11ax preview: Access points and routers that support Wi-Fi 6 are on tap][11]
+
+
+
+Join the Network World communities on [Facebook][12] and [LinkedIn][13] to comment on topics that are top of mind.
+
+--------------------------------------------------------------------------------
+
+via: https://www.networkworld.com/article/3399978/5g-will-augment-wi-fi-not-replace-it.html
+
+作者:[Zeus Kerravala][a]
+选题:[lujun9972][b]
+译者:[译者ID](https://github.com/译者ID)
+校对:[校对者ID](https://github.com/校对者ID)
+
+本文由 [LCTT](https://github.com/LCTT/TranslateProject) 原创编译,[Linux中国](https://linux.cn/) 荣誉推出
+
+[a]: https://www.networkworld.com/author/Zeus-Kerravala/
+[b]: https://github.com/lujun9972
+[1]: https://images.idgesg.net/images/article/2019/05/wireless_connection_speed_connectivity_bars_cell_tower_5g_by_thinkstock-100796921-large.jpg
+[2]: https://www.networkworld.com/article/3203489/what-is-5g-how-is-it-better-than-4g.html
+[3]: https://www.networkworld.com/article/3354477/mobile-world-congress-the-time-of-5g-is-almost-here.html
+[4]: https://images.idgesg.net/images/article/2019/06/headshot_jlipton_aruba-100798360-small.jpg
+[5]: https://www.networkworld.com/article/3215907/why-80211ax-is-the-next-big-thing-in-wi-fi.html
+[6]: https://pluralsight.pxf.io/c/321564/424552/7490?u=https%3A%2F%2Fwww.pluralsight.com%2Fcourses%2Fmobile-device-management-big-picture
+[7]: https://www.networkworld.com/article/3215907/mobile-wireless/why-80211ax-is-the-next-big-thing-in-wi-fi.html
+[8]: https://%20https//www.networkworld.com/article/3048196/mobile-wireless/faq-802-11ax-wi-fi.html
+[9]: https://www.networkworld.com/article/3311921/mobile-wireless/wi-fi-6-is-coming-to-a-router-near-you.html
+[10]: https://www.networkworld.com/article/3332018/wi-fi/wi-fi-6-with-ofdma-opens-a-world-of-new-wireless-possibilities.html
+[11]: https://www.networkworld.com/article/3309439/mobile-wireless/80211ax-preview-access-points-and-routers-that-support-the-wi-fi-6-protocol-on-tap.html
+[12]: https://www.facebook.com/NetworkWorld/
+[13]: https://www.linkedin.com/company/network-world
diff --git a/sources/talk/20190604 Data center workloads become more complex despite promises to the contrary.md b/sources/talk/20190604 Data center workloads become more complex despite promises to the contrary.md
new file mode 100644
index 0000000000..31d127e77d
--- /dev/null
+++ b/sources/talk/20190604 Data center workloads become more complex despite promises to the contrary.md
@@ -0,0 +1,64 @@
+[#]: collector: (lujun9972)
+[#]: translator: ( )
+[#]: reviewer: ( )
+[#]: publisher: ( )
+[#]: url: ( )
+[#]: subject: (Data center workloads become more complex despite promises to the contrary)
+[#]: via: (https://www.networkworld.com/article/3400086/data-center-workloads-become-more-complex-despite-promises-to-the-contrary.html)
+[#]: author: (Andy Patrizio https://www.networkworld.com/author/Andy-Patrizio/)
+
+Data center workloads become more complex despite promises to the contrary
+======
+The data center is shouldering a greater burden than ever, despite promises of ease and the cloud.
+![gorodenkoff / Getty Images][1]
+
+Data centers are becoming more complex and still run the majority of workloads despite the promises of simplicity of deployment through automation and hyperconverged infrastructure (HCI), not to mention how the cloud was supposed to take over workloads.
+
+That’s the finding of the Uptime Institute's latest [annual global data center survey][2] (registration required). The majority of IT loads still run on enterprise data centers even in the face of cloud adoption, putting pressure on administrators to have to manage workloads across the hybrid infrastructure.
+
+**[ Learn[how server disaggregation can boost data center efficiency][3] | Get regularly scheduled insights: [Sign up for Network World newsletters][4] ]**
+
+With workloads like artificial intelligence (AI) and machine language coming to the forefront, that means facilities face greater power and cooling challenges, since AI is extremely processor-intensive. That puts strain on data center administrators and power and cooling vendors alike to keep up with the growth in demand.
+
+On top of it all, everyone is struggling to get enough staff with the right skills.
+
+### Outages, staffing problems, lack of public cloud visibility among top concerns
+
+Among the key findings of Uptime's report:
+
+ * The large, privately owned enterprise data center facility still forms the bedrock of corporate IT and is expected to be running half of all workloads in 2021.
+ * The staffing problem affecting most of the data center sector has only worsened. Sixty-one percent of respondents said they had difficulty retaining or recruiting staff, up from 55% a year earlier.
+ * Outages continue to cause significant problems for operators. Just over a third (34%) of all respondents had an outage or severe IT service degradation in the past year, while half (50%) had an outage or severe IT service degradation in the past three years.
+ * Ten percent of all respondents said their most recent significant outage cost more than $1 million.
+ * A lack of visibility, transparency, and accountability of public cloud services is a major concern for enterprises that have mission-critical applications. A fifth of operators surveyed said they would be more likely to put workloads in a public cloud if there were more visibility. Half of those using public cloud for mission-critical applications also said they do not have adequate visibility.
+ * Improvements in data center facility energy efficiency have flattened out and even deteriorated slightly in the past two years. The average PUE for 2019 is 1.67.
+ * Rack power density is rising after a long period of flat or minor increases, causing many to rethink cooling strategies.
+ * Power loss was the single biggest cause of outages, accounting for one-third of outages. Sixty percent of respondents said their data center’s outage could have been prevented with better management/processes or configuration.
+
+
+
+Traditionally data centers are improving their reliability through "rigorous attention to power, infrastructure, connectivity and on-site IT replication," the Uptime report says. The solution, though, is pricy. Data center operators are getting distributed resiliency through active-active data centers where at least two active data centers replicate data to each other. Uptime found up to 40% of those surveyed were using this method.
+
+The Uptime survey was conducted in March and April of this year, surveying 1,100 end users in more than 50 countries and dividing them into two groups: the IT managers, owners, and operators of data centers and the suppliers, designers, and consultants that service the industry.
+
+Join the Network World communities on [Facebook][5] and [LinkedIn][6] to comment on topics that are top of mind.
+
+--------------------------------------------------------------------------------
+
+via: https://www.networkworld.com/article/3400086/data-center-workloads-become-more-complex-despite-promises-to-the-contrary.html
+
+作者:[Andy Patrizio][a]
+选题:[lujun9972][b]
+译者:[译者ID](https://github.com/译者ID)
+校对:[校对者ID](https://github.com/校对者ID)
+
+本文由 [LCTT](https://github.com/LCTT/TranslateProject) 原创编译,[Linux中国](https://linux.cn/) 荣誉推出
+
+[a]: https://www.networkworld.com/author/Andy-Patrizio/
+[b]: https://github.com/lujun9972
+[1]: https://images.idgesg.net/images/article/2019/05/cso_cloud_computing_backups_it_engineer_data_center_server_racks_connections_by_gorodenkoff_gettyimages-943065400_3x2_2400x1600-100796535-large.jpg
+[2]: https://uptimeinstitute.com/2019-data-center-industry-survey-results
+[3]: https://www.networkworld.com/article/3266624/how-server-disaggregation-could-make-cloud-datacenters-more-efficient.html
+[4]: https://www.networkworld.com/newsletters/signup.html
+[5]: https://www.facebook.com/NetworkWorld/
+[6]: https://www.linkedin.com/company/network-world
diff --git a/sources/talk/20190604 Moving to the Cloud- SD-WAN Matters- Part 2.md b/sources/talk/20190604 Moving to the Cloud- SD-WAN Matters- Part 2.md
new file mode 100644
index 0000000000..2f68bd6f59
--- /dev/null
+++ b/sources/talk/20190604 Moving to the Cloud- SD-WAN Matters- Part 2.md
@@ -0,0 +1,66 @@
+[#]: collector: (lujun9972)
+[#]: translator: ( )
+[#]: reviewer: ( )
+[#]: publisher: ( )
+[#]: url: ( )
+[#]: subject: (Moving to the Cloud? SD-WAN Matters! Part 2)
+[#]: via: (https://www.networkworld.com/article/3398488/moving-to-the-cloud-sd-wan-matters-part-2.html)
+[#]: author: (Rami Rammaha https://www.networkworld.com/author/Rami-Rammaha/)
+
+Moving to the Cloud? SD-WAN Matters! Part 2
+======
+
+![istock][1]
+
+This is the second installment of the blog series exploring how enterprises can realize the full transformation promise of the cloud by shifting to a business first networking model powered by a business-driven [SD-WAN][2]. The first installment explored automating secure IPsec connectivity and intelligently steering traffic to cloud providers. We also framed the direct correlation between moving to the cloud and adopting an SD-WAN. In this blog, we will expand upon several additional challenges that can be addressed with a business-driven SD-WAN when embracing the cloud:
+
+### Simplifying and automating security zone-based segmentation
+
+Securing cloud-first branches requires a robust multi-level approach that addresses following considerations:
+
+ * Restricting outside traffic coming into the branch to sessions exclusively initiated by internal users with a built-in stateful firewall, avoiding appliance sprawl and lowering operational costs; this is referred to as the app whitelist model
+ * Encrypting communications between end points within the SD-WAN fabric and between branch locations and public cloud instances
+ * Service chaining traffic to a cloud-hosted security service like [Zscaler][3] for Layer 7 inspection and analytics for internet-bound traffic
+ * Segmenting traffic spanning the branch, WAN and data center/cloud
+ * Centralizing policy orchestration and automation of zone-based firewall, VLAN and WAN overlays
+
+
+
+A traditional device-centric WAN approach for security segmentation requires the time-consuming manual configuration of routers and/or firewalls on a device-by-device and site-by-site basis. This is not only complex and cumbersome, but it simply can’t scale to 100s or 1000s of sites. Anusha Vaidyanathan, director of product management at Silver Peak, explains how to automate end-to-end zone-based segmentation, emphasizing the advantages of a business-driven approach in this [lightboard video][4].
+
+### Delivering the Highest Quality of Experience to IT teams
+
+The goal for enterprise IT is enabling business agility and increasing operational efficiency. The traditional router-centric WAN approach doesn’t provide the best quality of experience for IT as management and on-going network operations are manual and time consuming, device-centric, cumbersome, error-prone and inefficient.
+
+A business-driven SD-WAN such as the Silver Peak [Unity EdgeConnect™][5] unified SD-WAN edge platform centralizes the orchestration of business-driven policies. EdgeConnect automation, machine learning and open APIs easily integrate with third-party management tools and real-time visibility tools to deliver the highest quality of experience for IT, enabling them to reclaim nights and weekends. Manav Mishra, vice president of product management at Silver Peak, explains the latest Silver Peak innovations in this [lightboard video][6].
+
+As enterprises become increasingly dependent on the cloud and embrace a multi-cloud strategy, they must address a number of new challenges:
+
+ * A centralized approach to securely embracing the cloud and the internet
+ * How to extend the on-premise data center to a public cloud and migrating workloads between private and public cloud, taking application portability into account
+ * Deliver consistent high application performance and availability to hosted applications whether they reside in the data center, private or public clouds or are delivered as SaaS services
+ * A proactive way to quickly resolve complex issues that span the data center and cloud as well as multiple WAN transport services by harnessing the power of advanced visibility and analytics tools
+
+
+
+The business-driven EdgeConnect SD-WAN edge platform enables enterprise IT organizations to easily and consistently embrace the public cloud. Unified security and performance capabilities with automation deliver the highest quality of experience for both users and IT while lowering overall WAN expenditures.
+
+--------------------------------------------------------------------------------
+
+via: https://www.networkworld.com/article/3398488/moving-to-the-cloud-sd-wan-matters-part-2.html
+
+作者:[Rami Rammaha][a]
+选题:[lujun9972][b]
+译者:[译者ID](https://github.com/译者ID)
+校对:[校对者ID](https://github.com/校对者ID)
+
+本文由 [LCTT](https://github.com/LCTT/TranslateProject) 原创编译,[Linux中国](https://linux.cn/) 荣誉推出
+
+[a]: https://www.networkworld.com/author/Rami-Rammaha/
+[b]: https://github.com/lujun9972
+[1]: https://images.idgesg.net/images/article/2019/05/istock-909772962-100797711-large.jpg
+[2]: https://www.silver-peak.com/sd-wan/sd-wan-explained
+[3]: https://www.silver-peak.com/company/tech-partners/zscaler
+[4]: https://www.silver-peak.com/resource-center/how-to-create-sd-wan-security-zones-in-edgeconnect
+[5]: https://www.silver-peak.com/products/unity-edge-connect
+[6]: https://www.silver-peak.com/resource-center/how-to-optimize-quality-of-experience-for-it-using-sd-wan
diff --git a/sources/talk/20190605 Cisco will use AI-ML to boost intent-based networking.md b/sources/talk/20190605 Cisco will use AI-ML to boost intent-based networking.md
new file mode 100644
index 0000000000..29d2acd519
--- /dev/null
+++ b/sources/talk/20190605 Cisco will use AI-ML to boost intent-based networking.md
@@ -0,0 +1,87 @@
+[#]: collector: (lujun9972)
+[#]: translator: ( )
+[#]: reviewer: ( )
+[#]: publisher: ( )
+[#]: url: ( )
+[#]: subject: (Cisco will use AI/ML to boost intent-based networking)
+[#]: via: (https://www.networkworld.com/article/3400382/cisco-will-use-aiml-to-boost-intent-based-networking.html)
+[#]: author: (Michael Cooney https://www.networkworld.com/author/Michael-Cooney/)
+
+Cisco will use AI/ML to boost intent-based networking
+======
+Cisco explains how artificial intelligence and machine learning fit into a feedback loop that implements and maintain desired network conditions to optimize network performance for workloads using real-time data.
+![xijian / Getty Images][1]
+
+Artificial Intelligence and machine learning are expected to be some of the big topics at next week’s Cisco Live event and the company is already talking about how those technologies will help drive the next generation of [Intent-Based Networking][2].
+
+“Artificial intelligence will change how we manage networks, and it’s a change we need,” wrote John Apostolopoulos Cisco CTO and vice president of Enterprise Networking in a [blog][3] about how Cisco says these technologies impact the network.
+
+**[ Now see[7 free network tools you must have][4]. ]**
+
+AI is the next major step for networking capabilities, and while researchers have talked in the past about how great AI would be, now the compute power and algorithms exist to make it possible, Apostolopoulos told Network World.
+
+To understand how AI and ML can boost IBN, Cisco says it's necessary to understand four key factors an IBN environment needs: infrastructure, translation, activation and assurance.
+
+Infrastructure can be virtual or physical and include wireless access points, switches, routers, compute and storage. “To make the infrastructure do what we want, we use the translation function to convert the intent, or what we are trying to make the network accomplish, from a person or computer into the correct network and security policies. These policies then must be activated on the network,” Apostolopoulos said.
+
+The activation step takes the network and security polices and couples them with a deep understanding of the network infrastructure that includes both real-time and historic data about its behavior. It then activates or automates the policies across all of the network infrastructure elements, ideally optimizing for performance, reliability and security, Apostolopoulos wrote.
+
+Finally assurance maintains a continuous validation-and-verification loop. IBN improves on translation and assurance to form a valuable feedback loop about what’s going on in the network that wasn’t available before. ** **
+
+Apostolopoulos used the example of an international company that wanted to set up a world-wide video all-hands meeting. Everyone on the call had to have high-quality, low-latency video, and also needed the capability to send high-quality video into the call when it was time for Q&A.
+
+“By applying machine learning and related machine reasoning, assurance can also sift through the massive amount of data related to such a global event to correctly identify if there are any problems arising. We can then get solutions to these issues – and even automatically apply solutions – more quickly and more reliably than before,” Apostolopoulos said.
+
+In this case, assurance could identify that the use of WAN bandwidth to certain sites is increasing at a rate that will saturate the network paths and could proactively reroute some of the WAN flows through alternative paths to prevent congestion from occurring, Apostolopoulos wrote.
+
+“In prior systems, this problem would typically only be recognized after the bandwidth bottleneck occurred and users experienced a drop in call quality or even lost their connection to the meeting. It would be challenging or impossible to identify the issue in real time, much less to fix it before it distracted from the experience of the meeting. Accurate and fast identification through ML and MR coupled with intelligent automation through the feedback loop is key to successful outcome.”
+
+Apostolopoulos said AI can accelerate the path from intent into translation and activation and then examine network and behavior data in the assurance step to make sure everything is working correctly. Activation uses the insights to drive more intelligent actions for improved performance, reliability and security, creating a cycle of network optimization.
+
+So what might an implementation of this look like? Applications that run on Cisco’s DNA Center may be the central component in an IBN environment. Introduced on 2017 as the heart of its IBN initiative, [Cisco DNA Center][5] features automation capabilities, assurance setting, fabric provisioning and policy-based segmentation for enterprise networks.
+
+“DNA Center can bring together AI and ML in a unified manner,” Apostolopoulos said. “It can store data from across the network and then customers can do AI and ML on that data.”
+
+Central to Cisco's push is being able to gather metadata about traffic as it passes without slowing the traffic, which is accomplished through the use of ASICs in its campus and data-center switches.
+
+“We have designed our networking gear from the ASIC, OS and software levels to gather key data via our IBN architecture, which provides unified data collection and performs algorithmic analysis across the entire network (wired, wireless, LAN, WAN, datacenter), Apostolopoulos said. “We have a massive collection of network data, including a database of problems and associated root causes, from being the world’s top enterprise network vendor over the past 20-plus years. And we have been investing for many years to create innovative network-data analysis and ML, MR, and other AI techniques to identify and solve key problems.”
+
+Machine learning and AI can then be applied to all that data to help network operators handle everything from policy setting and network control to security.
+
+“I also want to stress that the feedback the IT user gets from the IBN system with AI is not overwhelming telemetry data,” Apostolopoulos said. Instead it is valuable and actionable insights at scale, derived from immense data and behavioral analytics using AI.
+
+Managing and developing new AI/ML-based applications from enormous data sets beyond what Cisco already has is a key driver behind it’s the company’s Unified Compute System (UCS) server that wasa rolled out last September. While the new server, the UCS C480 ML, is powerful – it includes eight Nvidia Tesla V100-32G GPUs with 128GB of DDR4 RAM, 24 SATA hard drives and more – it is the ecosystem of vendors – Cloudera, HortonWorks and others that will end up being more important.
+
+[Earlier this year Cisco forecast][6] that [AI and ML][7] will significantly boost network management this year.
+
+“In 2019, companies will start to adopt Artificial Intelligence, in particular Machine Learning, to analyze the telemetry coming off networks to see these patterns, in an attempt to get ahead of issues from performance optimization, to financial efficiency, to security,” said [Anand Oswal][8], senior vice president of engineering in Cisco’s Enterprise Networking Business. The pattern-matching capabilities of ML will be used to spot anomalies in network behavior that might otherwise be missed, while also de-prioritizing alerts that otherwise nag network operators but that aren’t critical, Oswal said.
+
+“We will also start to use these tools to categorize and cluster device and user types, which can help us create profiles for use cases as well as spot outlier activities that could indicate security incursions,” he said.
+
+The first application of AI in network management will be smarter alerts that simply report on activities that break normal patterns, but as the technology advances it will react to more situations autonomously. The idea is to give customers more information so they and the systems can make better network decisions. Workable tools should appear later in 2019, Oswal said.
+
+Join the Network World communities on [Facebook][9] and [LinkedIn][10] to comment on topics that are top of mind.
+
+--------------------------------------------------------------------------------
+
+via: https://www.networkworld.com/article/3400382/cisco-will-use-aiml-to-boost-intent-based-networking.html
+
+作者:[Michael Cooney][a]
+选题:[lujun9972][b]
+译者:[译者ID](https://github.com/译者ID)
+校对:[校对者ID](https://github.com/校对者ID)
+
+本文由 [LCTT](https://github.com/LCTT/TranslateProject) 原创编译,[Linux中国](https://linux.cn/) 荣誉推出
+
+[a]: https://www.networkworld.com/author/Michael-Cooney/
+[b]: https://github.com/lujun9972
+[1]: https://images.idgesg.net/images/article/2019/05/ai-vendor-relationship-management_bar-code_purple_artificial-intelligence_hand-on-virtual-screen-100795252-large.jpg
+[2]: http://www.networkworld.com/cms/article/3202699
+[3]: https://blogs.cisco.com/enterprise/improving-networks-with-ai
+[4]: https://www.networkworld.com/article/2825879/7-free-open-source-network-monitoring-tools.html
+[5]: https://www.networkworld.com/article/3280988/cisco-opens-dna-center-network-control-and-management-software-to-the-devops-masses.html
+[6]: https://www.networkworld.com/article/3332027/cisco-touts-5-technologies-that-will-change-networking-in-2019.html
+[7]: https://www.networkworld.com/article/3320978/data-center/network-operations-a-new-role-for-ai-and-ml.html
+[8]: https://blogs.cisco.com/author/anandoswal
+[9]: https://www.facebook.com/NetworkWorld/
+[10]: https://www.linkedin.com/company/network-world
diff --git a/sources/talk/20190606 Cloud adoption drives the evolution of application delivery controllers.md b/sources/talk/20190606 Cloud adoption drives the evolution of application delivery controllers.md
new file mode 100644
index 0000000000..d7b22353c4
--- /dev/null
+++ b/sources/talk/20190606 Cloud adoption drives the evolution of application delivery controllers.md
@@ -0,0 +1,67 @@
+[#]: collector: (lujun9972)
+[#]: translator: ( )
+[#]: reviewer: ( )
+[#]: publisher: ( )
+[#]: url: ( )
+[#]: subject: (Cloud adoption drives the evolution of application delivery controllers)
+[#]: via: (https://www.networkworld.com/article/3400897/cloud-adoption-drives-the-evolution-of-application-delivery-controllers.html)
+[#]: author: (Zeus Kerravala https://www.networkworld.com/author/Zeus-Kerravala/)
+
+Cloud adoption drives the evolution of application delivery controllers
+======
+Application delivery controllers (ADCs) are on the precipice of shifting from traditional hardware appliances to software form factors.
+![Aramyan / Getty Images / Microsoft][1]
+
+Migrating to a cloud computing model will obviously have an impact on the infrastructure that’s deployed. This shift has already been seen in the areas of servers, storage, and networking, as those technologies have evolved to a “software-defined” model. And it appears that application delivery controllers (ADCs) are on the precipice of a similar shift.
+
+In fact, a new ZK Research [study about cloud computing adoption and the impact on ADCs][2] found that, when looking at the deployment model, hardware appliances are the most widely deployed — with 55% having fully deployed or are currently testing and only 15% currently researching hardware. (Note: I am an employee of ZK Research.)
+
+Juxtapose this with containerized ADCs where only 34% have deployed or are testing but 24% are currently researching and it shows that software in containers will outpace hardware for growth. Not surprisingly, software on bare metal and in virtual machines showed similar although lower, “researching” numbers that support the thesis that the market is undergoing a shift from hardware to software.
+
+**[ Read also:[How to make hybrid cloud work][3] ]**
+
+The study, conducted in collaboration with Kemp Technologies, surveyed 203 respondents from the U.K. and U.S. The demographic split was done to understand regional differences. An equal number of mid and large size enterprises were looked at, with 44% being from over 5,000 employees and the other 56% from companies that have 300 to 5,000 people.
+
+### Incumbency helps but isn’t a fait accompli for future ADC purchases
+
+The primary tenet of my research has always been that incumbents are threatened when markets transition, and this is something I wanted to investigate in the study. The survey asked whether buyers would consider an alternative as they evolve their applications from legacy (mode 1) to cloud-native (mode 2). The results offer a bit of good news and bad news for the incumbent providers. Only 8% said they would definitely select a new vendor, but 35% said they would not change. That means the other 57% will look at alternatives. This is sensible, as the requirements for cloud ADCs are different than ones that support traditional applications.
+
+### IT pros want better automation capabilities
+
+This begs the question as to what features ADC buyers want for a cloud environment versus traditional ones. The survey asked specifically what features would be most appealing in future purchases, and the top response was automation, followed by central management, application analytics, on-demand scaling (which is a form of automation), and visibility.
+
+The desire to automate was a positive sign for the evolution of buyer mindset. Just a few years ago, the mere mention of automation would have sent IT pros into a panic. The reality is that IT can’t operate effectively without automation, and technology professionals are starting to understand that.
+
+The reason automation is needed is that manual changes are holding businesses back. The survey asked how the speed of ADC changes impacts the speed at which applications are rolled out, and a whopping 60% said it creates significant or minor delays. In an era of DevOps and continuous innovation, multiple minor delays create a drag on the business and can cause it to fall behind is more agile competitors.
+
+![][4]
+
+### ADC upgrades and service provisioning benefit most from automation
+
+The survey also drilled down on specific ADC tasks to see where automation would have the most impact. Respondents were asked how long certain tasks took, answering in minutes, days, weeks, or months. Shockingly, there wasn’t a single task where the majority said it could be done in minutes. The closest was adding DNS entries for new virtual IP addresses (VIPs) where 46% said they could do that in minutes.
+
+Upgrading, provisioning new load balancers, and provisioning new VIPs took the longest. Looking ahead, this foreshadows big problems. As the data center gets more disaggregated and distributed, IT will deploy more software-based ADCs in more places. Taking days or weeks or month to perform these functions will cause the organization to fall behind.
+
+The study clearly shows changes are in the air for the ADC market. For IT pros, I strongly recommend that as the environment shifts to the cloud, it’s prudent to evaluate new vendors. By all means, see what your incumbent vendor has, but look at least at two others that offer software-based solutions. Also, there should be a focus on automating as much as possible, so the primary evaluation criteria for ADCs should be how easy it is to implement automation.
+
+Join the Network World communities on [Facebook][5] and [LinkedIn][6] to comment on topics that are top of mind.
+
+--------------------------------------------------------------------------------
+
+via: https://www.networkworld.com/article/3400897/cloud-adoption-drives-the-evolution-of-application-delivery-controllers.html
+
+作者:[Zeus Kerravala][a]
+选题:[lujun9972][b]
+译者:[译者ID](https://github.com/译者ID)
+校对:[校对者ID](https://github.com/校对者ID)
+
+本文由 [LCTT](https://github.com/LCTT/TranslateProject) 原创编译,[Linux中国](https://linux.cn/) 荣誉推出
+
+[a]: https://www.networkworld.com/author/Zeus-Kerravala/
+[b]: https://github.com/lujun9972
+[1]: https://images.idgesg.net/images/article/2019/05/cw_microsoft_sharepoint_vs_onedrive_clouds_and_hands_by_aramyan_gettyimages-909772962_2400x1600-100796932-large.jpg
+[2]: https://kemptechnologies.com/research-papers/adc-market-research-study-zeus-kerravala/?utm_source=zkresearch&utm_medium=referral&utm_campaign=zkresearch&utm_term=zkresearch&utm_content=zkresearch
+[3]: https://www.networkworld.com/article/3119362/hybrid-cloud/how-to-make-hybrid-cloud-work.html#tk.nww-fsb
+[4]: https://images.idgesg.net/images/article/2019/06/adc-survey-zk-research-100798593-large.jpg
+[5]: https://www.facebook.com/NetworkWorld/
+[6]: https://www.linkedin.com/company/network-world
diff --git a/sources/talk/20190606 For enterprise storage, persistent memory is here to stay.md b/sources/talk/20190606 For enterprise storage, persistent memory is here to stay.md
new file mode 100644
index 0000000000..3da91bb311
--- /dev/null
+++ b/sources/talk/20190606 For enterprise storage, persistent memory is here to stay.md
@@ -0,0 +1,118 @@
+[#]: collector: (lujun9972)
+[#]: translator: ( )
+[#]: reviewer: ( )
+[#]: publisher: ( )
+[#]: url: ( )
+[#]: subject: (For enterprise storage, persistent memory is here to stay)
+[#]: via: (https://www.networkworld.com/article/3398988/for-enterprise-storage-persistent-memory-is-here-to-stay.html)
+[#]: author: (John Edwards )
+
+For enterprise storage, persistent memory is here to stay
+======
+Persistent memory – also known as storage class memory – has tantalized data center operators for many years. A new technology promises the key to success.
+![Thinkstock][1]
+
+It's hard to remember a time when semiconductor vendors haven't promised a fast, cost-effective and reliable persistent memory technology to anxious [data center][2] operators. Now, after many years of waiting and disappointment, technology may have finally caught up with the hype to make persistent memory a practical proposition.
+
+High-capacity persistent memory, also known as storage class memory ([SCM][3]), is fast and directly addressable like dynamic random-access memory (DRAM), yet is able to retain stored data even after its power has been switched off—intentionally or unintentionally. The technology can be used in data centers to replace cheaper, yet far slower traditional persistent storage components, such as [hard disk drives][4] (HDD) and [solid-state drives][5] (SSD).
+
+**Learn more about enterprise storage**
+
+ * [Why NVMe over Fabric matters][6]
+ * [What is hyperconvergence?][7]
+ * [How NVMe is changing enterprise storage][8]
+ * [Making the right hyperconvergence choice: HCI hardware or software?][9]
+
+
+
+Persistent memory can also be used to replace DRAM itself in some situations without imposing a significant speed penalty. In this role, persistent memory can deliver crucial operational benefits, such as lightning-fast database-server restarts during maintenance, power emergencies and other expected and unanticipated reboot situations.
+
+Many different types of strategic operational applications and databases, particularly those that require low-latency, high durability and strong data consistency, can benefit from persistent memory. The technology also has the potential to accelerate virtual machine (VM) storage and deliver higher performance to multi-node, distributed-cloud applications.
+
+In a sense, persistent memory marks a rebirth of core memory. "Computers in the ‘50s to ‘70s used magnetic core memory, which was direct access, non-volatile memory," says Doug Wong, a senior member of [Toshiba Memory America's][10] technical staff. "Magnetic core memory was displaced by SRAM and DRAM, which are both volatile semiconductor memories."
+
+One of the first persistent memory devices to come to market is [Intel’s Optane DC][11]. Other vendors that have released persistent memory products or are planning to do so include [Samsung][12], Toshiba America Memory and [SK Hynix][13].
+
+### Persistent memory: performance + reliability
+
+With persistent memory, data centers have a unique opportunity to gain faster performance and lower latency without enduring massive technology disruption. "It's faster than regular solid-state NAND flash-type storage, but you're also getting the benefit that it’s persistent," says Greg Schulz, a senior advisory analyst at vendor-independent storage advisory firm [StorageIO.][14] "It's the best of both worlds."
+
+Yet persistent memory offers adopters much more than speedy, reliable storage. In an ideal IT world, all of the data associated with an application would reside within DRAM to achieve maximum performance. "This is currently not practical due to limited DRAM and the fact that DRAM is volatile—data is lost when power fails," observes Scott Nelson, senior vice president and general manager of Toshiba Memory America's memory business unit.
+
+Persistent memory transports compatible applications to an "always on" status, providing continuous access to large datasets through increased system memory capacity, says Kristie Mann, [Intel's][15] director of marketing for data center memory and storage. She notes that Optane DC can supply data centers with up to three-times more system memory capacity (as much as 36TBs), system restarts in seconds versus minutes, 36% more virtual machines per node, and up to 8-times better performance on [Apache Spark][16], a widely used open-source distributed general-purpose cluster-computing framework.
+
+System memory currently represents 60% of total platform costs, Mann says. She observes that Optane DC persistent memory provides significant customer value by delivering 1.2x performance/dollar on key customer workloads. "This value will dramatically change memory/storage economics and accelerate the data-centric era," she predicts.
+
+### Where will persistent memory infiltrate enterprise storage?
+
+Persistent memory is likely to first enter the IT mainstream with minimal fanfare, serving as a high-performance caching layer for high performance SSDs. "This could be adopted relatively-quickly," Nelson observes. Yet this intermediary role promises to be merely a stepping-stone to increasingly crucial applications.
+
+Over the next few years, persistent technology will impact data centers serving enterprises across an array of sectors. "Anywhere time is money," Schulz says. "It could be financial services, but it could also be consumer-facing or sales-facing operations."
+
+Persistent memory supercharges anything data-related that requires extreme speed at extreme scale, observes Andrew Gooding, vice president of engineering at [Aerospike][17], which delivered the first commercially available open database optimized for use with Intel Optane DC.
+
+Machine learning is just one of many applications that stand to benefit from persistent memory. Gooding notes that ad tech firms, which rely on machine learning to understand consumers' reactions to online advertising campaigns, should find their work made much easier and more effective by persistent memory. "They’re collecting information as users within an ad campaign browse the web," he says. "If they can read and write all that data quickly, they can then apply machine-learning algorithms and tailor specific ads for users in real time."
+
+Meanwhile, as automakers become increasingly reliant on data insights, persistent memory promises to help them crunch numbers and refine sophisticated new technologies at breakneck speeds. "In the auto industry, manufacturers face massive data challenges in autonomous vehicles, where 20 exabytes of data needs to be processed in real time, and they're using self-training machine-learning algorithms to help with that," Gooding explains. "There are so many fields where huge amounts of data need to be processed quickly with machine-learning techniques—fraud detection, astronomy... the list goes on."
+
+Intel, like other persistent memory vendors, expects cloud service providers to be eager adopters, targeting various types of in-memory database services. Google, for example, is applying persistent memory to big data workloads on non-relational databases from vendors such as Aerospike and [Redis Labs][18], Mann says.
+
+High-performance computing (HPC) is yet another area where persistent memory promises to make a tremendous impact. [CERN][19], the European Organization for Nuclear Research, is using Intel's Optane DC to significantly reduce wait times for scientific computing. "The efficiency of their algorithms depends on ... persistent memory, and CERN considers it a major breakthrough that is necessary to the work they are doing," Mann observes.
+
+### How to prepare storage infrastructure for persistent memory
+
+Before jumping onto the persistent memory bandwagon, organizations need to carefully scrutinize their IT infrastructure to determine the precise locations of any existing data bottlenecks. This task will be primary application-dependent, Wong notes. "If there is significant performance degradation due to delays associated with access to data stored in non-volatile storage—SSD or HDD—then an SCM tier will improve performance," he explains. Yet some applications will probably not benefit from persistent memory, such as compute-bound applications where CPU performance is the bottleneck.
+
+Developers may need to reevaluate fundamental parts of their storage and application architectures, Gooding says. "They will need to know how to program with persistent memory," he notes. "How, for example, to make sure writes are flushed to the actual persistent memory device when necessary, as opposed to just sitting in the CPU cache."
+
+To leverage all of persistent memory's potential benefits, significant changes may also be required in how code is designed. When moving applications from DRAM and flash to persistent memory, developers will need to consider, for instance, what happens when a program crashes and restarts. "Right now, if they write code that leaks memory, that leaked memory is recovered on restart," Gooding explains. With persistent memory, that isn't necessarily the case. "Developers need to make sure the code is designed to reconstruct a consistent state when a program restarts," he notes. "You may not realize how much your designs rely on the traditional combination of fast volatile DRAM and block storage, so it can be tricky to change your code designs for something completely new like persistent memory."
+
+Older versions of operating systems may also need to be updated to accommodate the new technology, although newer OSes are gradually becoming persistent memory aware, Schulz says. "In other words, if they detect that persistent memory is available, then they know how to utilize that either as a cache, or some other memory."
+
+Hypervisors, such as [Hyper-V][20] and [VMware][21], now know how to leverage persistent memory to support productivity, performance and rapid restarts. By utilizing persistent memory along with the latest versions of VMware, a whole system can see an uplift in speed and also maximize the number of VMs to fit on a single host, says Ian McClarty, CEO and president of data center operator [PhoenixNAP Global IT Services][22]. "This is a great use case for companies who want to own less hardware or service providers who want to maximize hardware to virtual machine deployments."
+
+Many key enterprise applications, particularly databases, are also becoming persistent memory aware. SQL Server and [SAP’s][23] flagship [HANA][24] database management platform have both embraced persistent memory. "The SAP HANA platform is commonly used across multiple industries to process data and transactions, and then run advanced analytics ... to deliver real-time insights," Mann observes.
+
+In terms of timing, enterprises and IT organizations should begin persistent memory planning immediately, Schulz recommends. "You should be talking with your vendors and understanding their roadmap, their plans, for not only supporting this technology, but also in what mode: as storage, as memory."
+
+Join the Network World communities on [Facebook][25] and [LinkedIn][26] to comment on topics that are top of mind.
+
+--------------------------------------------------------------------------------
+
+via: https://www.networkworld.com/article/3398988/for-enterprise-storage-persistent-memory-is-here-to-stay.html
+
+作者:[John Edwards][a]
+选题:[lujun9972][b]
+译者:[译者ID](https://github.com/译者ID)
+校对:[校对者ID](https://github.com/校对者ID)
+
+本文由 [LCTT](https://github.com/LCTT/TranslateProject) 原创编译,[Linux中国](https://linux.cn/) 荣誉推出
+
+[a]:
+[b]: https://github.com/lujun9972
+[1]: https://images.idgesg.net/images/article/2017/08/file_folder_storage_sharing_thinkstock_477492571_3x2-100732889-large.jpg
+[2]: https://www.networkworld.com/article/3353637/the-data-center-is-being-reimagined-not-disappearing.html
+[3]: https://www.networkworld.com/article/3026720/the-next-generation-of-storage-disruption-storage-class-memory.html
+[4]: https://www.networkworld.com/article/2159948/hard-disk-drives-vs--solid-state-drives--are-ssds-finally-worth-the-money-.html
+[5]: https://www.networkworld.com/article/3326058/what-is-an-ssd.html
+[6]: https://www.networkworld.com/article/3273583/why-nvme-over-fabric-matters.html
+[7]: https://www.networkworld.com/article/3207567/what-is-hyperconvergence
+[8]: https://www.networkworld.com/article/3280991/what-is-nvme-and-how-is-it-changing-enterprise-storage.html
+[9]: https://www.networkworld.com/article/3318683/making-the-right-hyperconvergence-choice-hci-hardware-or-software
+[10]: https://business.toshiba-memory.com/en-us/top.html
+[11]: https://www.intel.com/content/www/us/en/architecture-and-technology/optane-dc-persistent-memory.html
+[12]: https://www.samsung.com/semiconductor/
+[13]: https://www.skhynix.com/eng/index.jsp
+[14]: https://storageio.com/
+[15]: https://www.intel.com/content/www/us/en/homepage.html
+[16]: https://spark.apache.org/
+[17]: https://www.aerospike.com/
+[18]: https://redislabs.com/
+[19]: https://home.cern/
+[20]: https://docs.microsoft.com/en-us/virtualization/hyper-v-on-windows/about/
+[21]: https://www.vmware.com/
+[22]: https://phoenixnap.com/
+[23]: https://www.sap.com/index.html
+[24]: https://www.sap.com/products/hana.html
+[25]: https://www.facebook.com/NetworkWorld/
+[26]: https://www.linkedin.com/company/network-world
diff --git a/sources/talk/20190606 Juniper- Security could help drive interest in SDN.md b/sources/talk/20190606 Juniper- Security could help drive interest in SDN.md
new file mode 100644
index 0000000000..b140969eb5
--- /dev/null
+++ b/sources/talk/20190606 Juniper- Security could help drive interest in SDN.md
@@ -0,0 +1,89 @@
+[#]: collector: (lujun9972)
+[#]: translator: ( )
+[#]: reviewer: ( )
+[#]: publisher: ( )
+[#]: url: ( )
+[#]: subject: (Juniper: Security could help drive interest in SDN)
+[#]: via: (https://www.networkworld.com/article/3400739/juniper-sdn-snapshot-finds-security-legacy-network-tech-impacts-core-network-changes.html)
+[#]: author: (Michael Cooney https://www.networkworld.com/author/Michael-Cooney/)
+
+Juniper: Security could help drive interest in SDN
+======
+Juniper finds that enterprise interest in software-defined networking (SDN) is influenced by other factors, including artificial intelligence (AI) and machine learning (ML).
+![monsitj / Getty Images][1]
+
+Security challenges and developing artificial intelligence/maching learning (AI/ML) technologies are among the key issues driving [software-defined networking][2] (SDN) implementations, according to a new Juniper survey of 500 IT decision makers.
+
+And SDN interest abounds – 98% of the 500 said they were already using or considering an SDN implementation. Juniper said it had [Wakefield Research][3] poll IT decision makers of companies with 500 or more employees about their SDN strategies between May 7 and May 14, 2019.
+
+**More about SD-WAN**
+
+ * [How to buy SD-WAN technology: Key questions to consider when selecting a supplier][4]
+ * [How to pick an off-site data-backup method][5]
+ * [SD-Branch: What it is and why you’ll need it][6]
+ * [What are the options for security SD-WAN?][7]
+
+
+
+SDN includes technologies that separate the network control plane from the forwarding plane to enable more automated provisioning and policy-based management of network resources.
+
+IDC estimates that the worldwide data-center SDN market will be worth more than $12 billion in 2022, recording a CAGR of 18.5% during the 2017-2022 period. The market-generated revenue of nearly $5.15 billion in 2017 was up more than 32.2% from 2016.
+
+There are many ideas driving the development of SDN. For example, it promises to reduce the complexity of statically defined networks; make automating network functions much easier; and allow for simpler provisioning and management of networked resources from the data center to the campus or wide area network.
+
+While the evolution of SDN is ongoing, Juniper’s study pointed out an issue that was perhaps not unexpected – many users are still managing operations via the command line interface (CLI). CLI is the primary text-based user interface used for configuring, monitoring and maintaining most networked devices.
+
+“If SDN is as attractive as it is then why manage the network with the same legacy technology of the past?” said Michael Bushong, vice president of enterprise and cloud marketing at Juniper Networks. “If you deploy SDN and don’t adjust the operational model then it is difficult to reap all the benefits SDN can bring. It’s the difference between managing devices individually which you may have done in the past to managing fleets of devices via SDN – it simplifies and reduces operational expenses.”
+
+Juniper pointed to a [Gartner prediction][8] that stated “by 2020, only 30% of network operations teams will use the command line interface (CLI) as their primary interface, down from 85% at years end 2016.” Garter stated that poll results from a recent Gartner conference found some 71% still using CLI as the primary way to make network changes.
+
+Gartner [wrote][9] in the past that CLI has remained the primary operational tool for mainstream network operations teams for easily the past 15-20 years but that “moving away from the CLI is a good thing for the networking industry, and while it won’t disappear completely (advanced/nuanced troubleshooting for example), it will be supplanted as the main interface into networking infrastructure.”
+
+Juniper’s study found that 87% of businesses are still doing most or some of their network management at the device level.
+
+What all of this shows is that customers are obviously interested in SDN but are still grappling with the best ways to get there, Bushong said.
+
+The Juniper study also found users interested in SDN because of the potential for a security boost.
+
+SDN can empowers a variety of security benefits. A customer can split up a network connection between an end user and the data center and have different security settings for the various types of network traffic. A network could have one public-facing, low-security network that does not touch any sensitive information. Another segment could have much more fine-grained remote-access control with software-based [firewall][10] and encryption policies on it, which allow sensitive data to traverse over it. SDN users can roll out security policies across the network from the data center to the edge much more rapidly than traditional network environments.
+
+“Many enterprises see security—not speed—as the biggest consequence of not making this transition in the next five years, with nearly 40 percent identifying the inability to quickly address new threats as one of their main concerns,” wrote Manoj Leelanivas, chief product officer at Juniper Networks, in a blog about the survey.
+
+“SDN is not often associated with greater security but this makes sense when we remember this is an operational transformation. In security, the challenge lies not in identifying threats or creating solutions, but in applying these solutions to a fragmented network. Streamlining complex security operations, touching many different departments and managing multiple security solutions, is where a software-defined approach can provide the answer,” Leelanivas stated.
+
+Some of the other key findings from Juniper included:
+
+ * **The future of AI** : The deployment of artificial intelligence is about changing the operational model, Bushong said. “The ability to more easily manage workflows over groups of devices and derive usable insights to help customers be more proactive rather than reactive is the direction we are moving. Everything will ultimately be AI-driven, he said.
+ * **Automation** : While automation is often considered a threat, Juniper said its respondents see it positively within the context of SDN, with 38% reporting it will improve security and 25% that it will enhance their jobs by streamlining manual operations.
+ * **Flexibility** : Agility is the #1 benefit respondents considering SDN want to gain (48%), followed by improved reliability (43%) and greater simplicity (38%).
+ * **SD-WAN** : The majority, 54%, have rolled out or are in the process of rolling out SD-WAN, while an additional 34% have it under current consideration.
+
+
+
+Join the Network World communities on [Facebook][11] and [LinkedIn][12] to comment on topics that are top of mind.
+
+--------------------------------------------------------------------------------
+
+via: https://www.networkworld.com/article/3400739/juniper-sdn-snapshot-finds-security-legacy-network-tech-impacts-core-network-changes.html
+
+作者:[Michael Cooney][a]
+选题:[lujun9972][b]
+译者:[译者ID](https://github.com/译者ID)
+校对:[校对者ID](https://github.com/校对者ID)
+
+本文由 [LCTT](https://github.com/LCTT/TranslateProject) 原创编译,[Linux中国](https://linux.cn/) 荣誉推出
+
+[a]: https://www.networkworld.com/author/Michael-Cooney/
+[b]: https://github.com/lujun9972
+[1]: https://images.idgesg.net/images/article/2019/03/sdn_software-defined-network_architecture-100791938-large.jpg
+[2]: https://www.networkworld.com/article/3209131/what-sdn-is-and-where-its-going.html
+[3]: https://www.wakefieldresearch.com/
+[4]: https://www.networkworld.com/article/3323407/sd-wan/how-to-buy-sd-wan-technology-key-questions-to-consider-when-selecting-a-supplier.html
+[5]: https://www.networkworld.com/article/3328488/backup-systems-and-services/how-to-pick-an-off-site-data-backup-method.html
+[6]: https://www.networkworld.com/article/3250664/lan-wan/sd-branch-what-it-is-and-why-youll-need-it.html
+[7]: https://www.networkworld.com/article/3285728/sd-wan/what-are-the-options-for-securing-sd-wan.html?nsdr=true
+[8]: https://blogs.gartner.com/andrew-lerner/2018/01/04/checking-in-on-the-death-of-the-cli/
+[9]: https://blogs.gartner.com/andrew-lerner/2016/11/22/predicting-the-death-of-the-cli/
+[10]: https://www.networkworld.com/article/3230457/what-is-a-firewall-perimeter-stateful-inspection-next-generation.html
+[11]: https://www.facebook.com/NetworkWorld/
+[12]: https://www.linkedin.com/company/network-world
diff --git a/sources/talk/20190606 Self-learning sensor chips won-t need networks.md b/sources/talk/20190606 Self-learning sensor chips won-t need networks.md
new file mode 100644
index 0000000000..c5abec5426
--- /dev/null
+++ b/sources/talk/20190606 Self-learning sensor chips won-t need networks.md
@@ -0,0 +1,82 @@
+[#]: collector: (lujun9972)
+[#]: translator: ( )
+[#]: reviewer: ( )
+[#]: publisher: ( )
+[#]: url: ( )
+[#]: subject: (Self-learning sensor chips won’t need networks)
+[#]: via: (https://www.networkworld.com/article/3400659/self-learning-sensor-chips-wont-need-networks.html)
+[#]: author: (Patrick Nelson https://www.networkworld.com/author/Patrick-Nelson/)
+
+Self-learning sensor chips won’t need networks
+======
+Scientists working on new, machine-learning networks aim to embed everything needed for artificial intelligence (AI) onto a processor, eliminating the need to transfer data to the cloud or computers.
+![Jiraroj Praditcharoenkul / Getty Images][1]
+
+Tiny, intelligent microelectronics should be used to perform as much sensor processing as possible on-chip rather than wasting resources by sending often un-needed, duplicated raw data to the cloud or computers. So say scientists behind new, machine-learning networks that aim to embed everything needed for artificial intelligence (AI) onto a processor.
+
+“This opens the door for many new applications, starting from real-time evaluation of sensor data,” says [Fraunhofer Institute for Microelectronic Circuits and Systems][2] on its website. No delays sending unnecessary data onwards, along with speedy processing, means theoretically there is zero latency.
+
+Plus, on-microprocessor, self-learning means the embedded, or sensor, devices can self-calibrate. They can even be “completely reconfigured to perform a totally different task afterwards,” the institute says. “An embedded system with different tasks is possible.”
+
+**[ Also read:[What is edge computing?][3] and [How edge networking and IoT will reshape data centers][4] ]**
+
+Much internet of things (IoT) data sent through networks is redundant and wastes resources: a temperature reading taken every 10 minutes, say, when the ambient temperature hasn’t changed, is one example. In fact, one only needs to know when the temperature has changed, and maybe then only when thresholds have been met.
+
+### Neural network-on-sensor chip
+
+The commercial German research organization says it’s developing a specific RISC-V microprocessor with a special hardware accelerator designed for a [brain-copying, artificial neural network (ANN) it has developed][5]. The architecture could ultimately be suitable for the condition-monitoring or predictive sensors of the kind we will likely see more of in the industrial internet of things (IIoT).
+
+Key to Fraunhofer IMS’s [Artificial Intelligence for Embedded Systems (AIfES)][6] is that the self-learning takes place at chip level rather than in the cloud or on a computer, and that it is independent of “connectivity towards a cloud or a powerful and resource-hungry processing entity.” But it still offers a “full AI mechanism, like independent learning,”
+
+It’s “decentralized AI,” says Fraunhofer IMS. "It’s not focused towards big-data processing.”
+
+Indeed, with these kinds of systems, no connection is actually required for the raw data, just for the post-analytical results, if indeed needed. Swarming can even replace that. Swarming lets sensors talk to one another, sharing relevant information without even getting a host network involved.
+
+“It is possible to build a network from small and adaptive systems that share tasks among themselves,” Fraunhofer IMS says.
+
+Other benefits in decentralized neural networks include that they can be more secure than the cloud. Because all processing takes place on the microprocessor, “no sensitive data needs to be transferred,” Fraunhofer IMS explains.
+
+### Other edge computing research
+
+The Fraunhofer researchers aren’t the only academics who believe entire networks become redundant with neuristor, brain-like AI chips. Binghamton University and Georgia Tech are working together on similar edge-oriented tech.
+
+“The idea is we want to have these chips that can do all the functioning in the chip, rather than messages back and forth with some sort of large server,” Binghamton said on its website when [I wrote about the university's work last year][7].
+
+One of the advantages of no major communications linking: Not only don't you have to worry about internet resilience, but also that energy is saved creating the link. Energy efficiency is an ambition in the sensor world — replacing batteries is time consuming, expensive, and sometimes, in the case of remote locations, extremely difficult.
+
+Memory or storage for swaths of raw data awaiting transfer to be processed at a data center, or similar, doesn’t have to be provided either — it’s been processed at the source, so it can be discarded.
+
+**More about edge networking:**
+
+ * [How edge networking and IoT will reshape data centers][4]
+ * [Edge computing best practices][8]
+ * [How edge computing can help secure the IoT][9]
+
+
+
+Join the Network World communities on [Facebook][10] and [LinkedIn][11] to comment on topics that are top of mind.
+
+--------------------------------------------------------------------------------
+
+via: https://www.networkworld.com/article/3400659/self-learning-sensor-chips-wont-need-networks.html
+
+作者:[Patrick Nelson][a]
+选题:[lujun9972][b]
+译者:[译者ID](https://github.com/译者ID)
+校对:[校对者ID](https://github.com/校对者ID)
+
+本文由 [LCTT](https://github.com/LCTT/TranslateProject) 原创编译,[Linux中国](https://linux.cn/) 荣誉推出
+
+[a]: https://www.networkworld.com/author/Patrick-Nelson/
+[b]: https://github.com/lujun9972
+[1]: https://images.idgesg.net/images/article/2019/02/industry_4-0_industrial_iot_smart_factory_automation_by_jiraroj_praditcharoenkul_gettyimages-902668940_2400x1600-100788458-large.jpg
+[2]: https://www.ims.fraunhofer.de/en.html
+[3]: https://www.networkworld.com/article/3224893/internet-of-things/what-is-edge-computing-and-how-it-s-changing-the-network.html
+[4]: https://www.networkworld.com/article/3291790/data-center/how-edge-networking-and-iot-will-reshape-data-centers.html
+[5]: https://www.ims.fraunhofer.de/en/Business_Units_and_Core_Competencies/Electronic_Assistance_Systems/News/AIfES-Artificial_Intelligence_for_Embedded_Systems.html
+[6]: https://www.ims.fraunhofer.de/en/Business_Units_and_Core_Competencies/Electronic_Assistance_Systems/technologies/Artificial-Intelligence-for-Embedded-Systems-AIfES.html
+[7]: https://www.networkworld.com/article/3326557/edge-chips-could-render-some-networks-useless.html
+[8]: https://www.networkworld.com/article/3331978/lan-wan/edge-computing-best-practices.html
+[9]: https://www.networkworld.com/article/3331905/internet-of-things/how-edge-computing-can-help-secure-the-iot.html
+[10]: https://www.facebook.com/NetworkWorld/
+[11]: https://www.linkedin.com/company/network-world
diff --git a/sources/talk/20190606 What to do when yesterday-s technology won-t meet today-s support needs.md b/sources/talk/20190606 What to do when yesterday-s technology won-t meet today-s support needs.md
new file mode 100644
index 0000000000..622537f2f9
--- /dev/null
+++ b/sources/talk/20190606 What to do when yesterday-s technology won-t meet today-s support needs.md
@@ -0,0 +1,53 @@
+[#]: collector: (lujun9972)
+[#]: translator: ( )
+[#]: reviewer: ( )
+[#]: publisher: ( )
+[#]: url: ( )
+[#]: subject: (What to do when yesterday’s technology won’t meet today’s support needs)
+[#]: via: (https://www.networkworld.com/article/3399875/what-to-do-when-yesterday-s-technology-won-t-meet-today-s-support-needs.html)
+[#]: author: (Anand Rajaram )
+
+What to do when yesterday’s technology won’t meet today’s support needs
+======
+
+![iStock][1]
+
+You probably already know that end user technology is exploding and are feeling the effects of it in your support organization every day. Remember when IT sanctioned and standardized every hardware and software instance in the workplace? Those days are long gone. Today, it’s the driving force of productivity that dictates what will or won’t be used – and that can be hard on a support organization.
+
+Whatever users need to do their jobs better, faster, more efficiently is what you are seeing come into the workplace. So naturally, that’s what comes into your service desk too. Support organizations see all kinds of [devices, applications, systems, and equipment][2], and it’s adding a great deal of complexity and demand to keep up with. In fact, four of the top five factors causing support ticket volumes to rise are attributed to new and current technology.
+
+To keep up with the steady [rise of tickets][3] and stay out in front of this surge, support organizations need to take a good, hard look at the processes and technologies they use. Yesterday’s methods won’t cut it. The landscape is simply changing too fast. Supporting today’s users and getting them back to work fast requires an expanding set of skills and tools.
+
+So where do you start with a new technology project? Just because a technology is new or hyped doesn’t mean it’s right for your organization. It’s important to understand your project goals and the experience you really want to create and match your technology choices to those goals. But don’t go it alone. Talk to your teams. Get intimately familiar with how your support organization works today. Understand your customers’ needs at a deep level. And bring the right people to the table to cover:
+
+ * Business problem analysis: What existing business issue are stakeholders unhappy with?
+ * The impact of that problem: How does that issue justify making a change?
+ * Process automation analysis: What area(s) can technology help automate?
+ * Other solutions: Have you considered any other options besides technology?
+
+
+
+With these questions answered, you’re ready to entertain your technology options. Put together your “must-haves” in a requirements document and reach out to potential suppliers. During the initial information-gathering stage, assess if the supplier understands your goals and how their technology helps you meet them. To narrow the field, compare solutions side by side against your goals. Select the top two or three for more in-depth product demos before moving into product evaluations. By the time you’re ready for implementation, you have empirical, practical knowledge of how the solution will perform against your business goals.
+
+The key takeaway is this: Technology for technology’s sake is just technology. But technology that drives business value is a solution. If you want a solution that drives results for your organization and your customers, it’s worth following a strategic selection process to match your goals with the best technology for the job.
+
+For more insight, check out the [LogMeIn Rescue][4] and HDI webinar “[Technology and the Service Desk: Expanding Mission, Expanding Skills”][5].
+
+--------------------------------------------------------------------------------
+
+via: https://www.networkworld.com/article/3399875/what-to-do-when-yesterday-s-technology-won-t-meet-today-s-support-needs.html
+
+作者:[Anand Rajaram][a]
+选题:[lujun9972][b]
+译者:[译者ID](https://github.com/译者ID)
+校对:[校对者ID](https://github.com/校对者ID)
+
+本文由 [LCTT](https://github.com/LCTT/TranslateProject) 原创编译,[Linux中国](https://linux.cn/) 荣誉推出
+
+[a]:
+[b]: https://github.com/lujun9972
+[1]: https://images.idgesg.net/images/article/2019/06/istock-1019006240-100798168-large.jpg
+[2]: https://www.logmeinrescue.com/resources/datasheets/infographic-mobile-support-are-your-employees-getting-what-they-need?utm_source=idg%20media&utm_medium=display&utm_campaign=native&sfdc=
+[3]: https://www.logmeinrescue.com/resources/analyst-reports/the-importance-of-remote-support-in-a-shift-left-world?utm_source=idg%20media&utm_medium=display&utm_campaign=native&sfdc=
+[4]: https://www.logmeinrescue.com/?utm_source=idg%20media&utm_medium=display&utm_campaign=native&sfdc=
+[5]: https://www.brighttalk.com/webcast/8855/312289?utm_source=LogMeIn7&utm_medium=brighttalk&utm_campaign=312289
diff --git a/sources/tech/20131228 Introduction to Clojure - Modern dialect of Lisp (Part 1).md b/sources/tech/20131228 Introduction to Clojure - Modern dialect of Lisp (Part 1).md
index 5e5f4df763..0fb3c6469d 100644
--- a/sources/tech/20131228 Introduction to Clojure - Modern dialect of Lisp (Part 1).md
+++ b/sources/tech/20131228 Introduction to Clojure - Modern dialect of Lisp (Part 1).md
@@ -1,5 +1,5 @@
[#]: collector: (lujun9972)
-[#]: translator: ( )
+[#]: translator: (ninifly)
[#]: reviewer: ( )
[#]: publisher: ( )
[#]: url: ( )
diff --git a/sources/tech/20170410 Writing a Time Series Database from Scratch.md b/sources/tech/20170410 Writing a Time Series Database from Scratch.md
deleted file mode 100644
index 7fb7fe9a6a..0000000000
--- a/sources/tech/20170410 Writing a Time Series Database from Scratch.md
+++ /dev/null
@@ -1,439 +0,0 @@
-LuMing Translating
-Writing a Time Series Database from Scratch
-============================================================
-
-
-I work on monitoring. In particular on [Prometheus][2], a monitoring system that includes a custom time series database, and its integration with [Kubernetes][3].
-
-In many ways Kubernetes represents all the things Prometheus was designed for. It makes continuous deployments, auto scaling, and other features of highly dynamic environments easily accessible. The query language and operational model, among many other conceptual decisions make Prometheus particularly well-suited for such environments. Yet, if monitored workloads become significantly more dynamic, this also puts new strains on monitoring system itself. With this in mind, rather than doubling back on problems Prometheus already solves well, we specifically aim to increase its performance in environments with highly dynamic, or transient services.
-
-Prometheus's storage layer has historically shown outstanding performance, where a single server is able to ingest up to one million samples per second as several million time series, all while occupying a surprisingly small amount of disk space. While the current storage has served us well, I propose a newly designed storage subsystem that corrects for shortcomings of the existing solution and is equipped to handle the next order of scale.
-
-> Note: I've no background in databases. What I say might be wrong and mislead. You can channel your criticism towards me (fabxc) in #prometheus on Freenode.
-
-### Problems, Problems, Problem Space
-
-First, a quick outline of what we are trying to accomplish and what key problems it raises. For each, we take a look at Prometheus' current approach, what it does well, and which problems we aim to address with the new design.
-
-### Time series data
-
-We have a system that collects data points over time.
-
-```
-identifier -> (t0, v0), (t1, v1), (t2, v2), (t3, v3), ....
-```
-
-Each data point is a tuple of a timestamp and a value. For the purpose of monitoring, the timestamp is an integer and the value any number. A 64 bit float turns out to be a good representation for counter as well as gauge values, so we go with that. A sequence of data points with strictly monotonically increasing timestamps is a series, which is addressed by an identifier. Our identifier is a metric name with a dictionary of _label dimensions_ . Label dimensions partition the measurement space of a single metric. Each metric name plus a unique set of labels is its own _time series_ that has a value stream associated with it.
-
-This is a typical set of series identifiers that are part of metric counting requests:
-
-```
-requests_total{path="/status", method="GET", instance=”10.0.0.1:80”}
-requests_total{path="/status", method="POST", instance=”10.0.0.3:80”}
-requests_total{path="/", method="GET", instance=”10.0.0.2:80”}
-```
-
-Let's simplify this representation right away: A metric name can be treated as just another label dimension — `__name__` in our case. At the query level, it might be be treated specially but that doesn't concern our way of storing it, as we will see later.
-
-```
-{__name__="requests_total", path="/status", method="GET", instance=”10.0.0.1:80”}
-{__name__="requests_total", path="/status", method="POST", instance=”10.0.0.3:80”}
-{__name__="requests_total", path="/", method="GET", instance=”10.0.0.2:80”}
-```
-
-When querying time series data, we want to do so by selecting series by their labels. In the simplest case `{__name__="requests_total"}` selects all series belonging to the `requests_total` metric. For all selected series, we retrieve data points within a specified time window.
-In more complex queries, we may wish to select series satisfying several label selectors at once and also represent more complex conditions than equality. For example, negative (`method!="GET"`) or regular expression matching (`method=~"PUT|POST"`).
-
-This largely defines the stored data and how it is recalled.
-
-### Vertical and Horizontal
-
-In a simplified view, all data points can be laid out on a two-dimensional plane. The _horizontal_ dimension represents the time and the series identifier space spreads across the _vertical_ dimension.
-
-```
-series
- ^
- │ . . . . . . . . . . . . . . . . . . . . . . {__name__="request_total", method="GET"}
- │ . . . . . . . . . . . . . . . . . . . . . . {__name__="request_total", method="POST"}
- │ . . . . . . .
- │ . . . . . . . . . . . . . . . . . . . ...
- │ . . . . . . . . . . . . . . . . . . . . .
- │ . . . . . . . . . . . . . . . . . . . . . {__name__="errors_total", method="POST"}
- │ . . . . . . . . . . . . . . . . . {__name__="errors_total", method="GET"}
- │ . . . . . . . . . . . . . .
- │ . . . . . . . . . . . . . . . . . . . ...
- │ . . . . . . . . . . . . . . . . . . . .
- v
- <-------------------- time --------------------->
-```
-
-Prometheus retrieves data points by periodically scraping the current values for a set of time series. The entity from which we retrieve such a batch is called a _target_ . Thereby, the write pattern is completely vertical and highly concurrent as samples from each target are ingested independently.
-To provide some measurement of scale: A single Prometheus instance collects data points from tens of thousands of _targets_ , which expose hundreds to thousands of different time series each.
-
-At the scale of collecting millions of data points per second, batching writes is a non-negotiable performance requirement. Writing single data points scattered across our disk would be painfully slow. Thus, we want to write larger chunks of data in sequence.
-This is an unsurprising fact for spinning disks, as their head would have to physically move to different sections all the time. While SSDs are known for fast random writes, they actually can't modify individual bytes but only write in _pages_ of 4KiB or more. This means writing a 16 byte sample is equivalent to writing a full 4KiB page. This behavior is part of what is known as [ _write amplification_ ][4], which as a bonus causes your SSD to wear out – so it wouldn't just be slow, but literally destroy your hardware within a few days or weeks.
-For more in-depth information on the problem, the blog series ["Coding for SSDs" series][5] is a an excellent resource. Let's just consider the main take away: sequential and batched writes are the ideal write pattern for spinning disks and SSDs alike. A simple rule to stick to.
-
-The querying pattern is significantly more differentiated than the write the pattern. We can query a single datapoint for a single series, a single datapoint for 10000 series, weeks of data points for a single series, weeks of data points for 10000 series, etc. So on our two-dimensional plane, queries are neither fully vertical or horizontal, but a rectangular combination of the two.
-[Recording rules][6] mitigate the problem for known queries but are not a general solution for ad-hoc queries, which still have to perform reasonably well.
-
-We know that we want to write in batches, but the only batches we get are vertical sets of data points across series. When querying data points for a series over a time window, not only would it be hard to figure out where the individual points can be found, we'd also have to read from a lot of random places on disk. With possibly millions of touched samples per query, this is slow even on the fastest SSDs. Reads will also retrieve more data from our disk than the requested 16 byte sample. SSDs will load a full page, HDDs will at least read an entire sector. Either way, we are wasting precious read throughput.
-So ideally, samples for the same series would be stored sequentially so we can just scan through them with as few reads as possible. On top, we only need to know where this sequence starts to access all data points.
-
-There's obviously a strong tension between the ideal pattern for writing collected data to disk and the layout that would be significantly more efficient for serving queries. It is _the_ fundamental problem our TSDB has to solve.
-
-#### Current solution
-
-Time to take a look at how Prometheus's current storage, let's call it "V2", addresses this problem.
-We create one file per time series that contains all of its samples in sequential order. As appending single samples to all those files every few seconds is expensive, we batch up 1KiB chunks of samples for a series in memory and append those chunks to the individual files, once they are full. This approach solves a large part of the problem. Writes are now batched, samples are stored sequentially. It also enables incredibly efficient compression formats, based on the property that a given sample changes only very little with respect to the previous sample in the same series. Facebook's paper on their Gorilla TSDB describes a similar chunk-based approach and [introduces a compression format][7] that reduces 16 byte samples to an average of 1.37 bytes. The V2 storage uses various compression formats including a variation of Gorilla’s.
-
-```
- ┌──────────┬─────────┬─────────┬─────────┬─────────┐ series A
- └──────────┴─────────┴─────────┴─────────┴─────────┘
- ┌──────────┬─────────┬─────────┬─────────┬─────────┐ series B
- └──────────┴─────────┴─────────┴─────────┴─────────┘
- . . .
- ┌──────────┬─────────┬─────────┬─────────┬─────────┬─────────┐ series XYZ
- └──────────┴─────────┴─────────┴─────────┴─────────┴─────────┘
- chunk 1 chunk 2 chunk 3 ...
-```
-
-While the chunk-based approach is great, keeping a separate file for each series is troubling the V2 storage for various reasons:
-
-* We actually need a lot more files than the number of time series we are currently collecting data for. More on that in the section on "Series Churn". With several million files, sooner or later way may run out of [inodes][1] on our filesystem. This is a condition we can only recover from by reformatting our disks, which is as invasive and disruptive as it could be. We generally want to avoid formatting disks specifically to fit a single application.
-* Even when chunked, several thousands of chunks per second are completed and ready to be persisted. This still requires thousands of individual disk writes every second. While it is alleviated by also batching up several completed chunks for a series, this in return increases the total memory footprint of data which is waiting to be persisted.
-* It's infeasible to keep all files open for reads and writes. In particular because ~99% of data is never queried again after 24 hours. If it is queried though though, we have to open up to thousands of files, find and read relevant data points into memory, and close them again. As this would result in high query latencies, data chunks are cached rather aggressively leading to problems outlined further in the section on "Resource Consumption".
-* Eventually, old data has to be deleted and data needs to be removed from the front of millions of files. This means that deletions are actually write intensive operations. Additionally, cycling through millions of files and analyzing them makes this a process that often takes hours. By the time it completes, it might have to start over again. Oh yea, and deleting the old files will cause further write amplification for your SSD!
-* Chunks that are currently accumulating are only held in memory. If the application crashes, data will be lost. To avoid this, the memory state is periodically checkpointed to disk, which may take significantly longer than the window of data loss we are willing to accept. Restoring the checkpoint may also take several minutes, causing painfully long restart cycles.
-
-The key take away from the existing design is the concept of chunks, which we most certainly want to keep. The most recent chunks always being held in memory is also generally good. After all, the most recent data is queried the most by a large margin.
-Having one file per time series is a concept we would like to find an alternative to.
-
-### Series Churn
-
-In the Prometheus context, we use the term _series churn_ to describe that a set of time series becomes inactive, i.e. receives no more data points, and a new set of active series appears instead.
-For example, all series exposed by a given microservice instance have a respective “instance” label attached that identifies its origin. If we perform a rolling update of our microservice and swap out every instance with a newer version, series churn occurs. In more dynamic environments those events may happen on an hourly basis. Cluster orchestration systems like Kubernetes allow continuous auto-scaling and frequent rolling updates of applications, potentially creating tens of thousands of new application instances, and with them completely new sets of time series, every day.
-
-```
-series
- ^
- │ . . . . . .
- │ . . . . . .
- │ . . . . . .
- │ . . . . . . .
- │ . . . . . . .
- │ . . . . . . .
- │ . . . . . .
- │ . . . . . .
- │ . . . . .
- │ . . . . .
- │ . . . . .
- v
- <-------------------- time --------------------->
-```
-
-So even if the entire infrastructure roughly remains constant in size, over time there's a linear growth of time series in our database. While a Prometheus server will happily collect data for 10 million time series, query performance is significantly impacted if data has to be found among a billion series.
-
-#### Current solution
-
-The current V2 storage of Prometheus has an index based on LevelDB for all series that are currently stored. It allows querying series containing a given label pair, but lacks a scalable way to combine results from different label selections.
-For example, selecting all series with label `__name__="requests_total"` works efficiently, but selecting all series with `instance="A" AND __name__="requests_total"` has scalability problems. We will later revisit what causes this and which tweaks are necessary to improve lookup latencies.
-
-This problem is in fact what spawned the initial hunt for a better storage system. Prometheus needed an improved indexing approach for quickly searching hundreds of millions of time series.
-
-### Resource consumption
-
-Resource consumption is one of the consistent topics when trying to scale Prometheus (or anything, really). But it's not actually the absolute resource hunger that is troubling users. In fact, Prometheus manages an incredible throughput given its requirements. The problem is rather its relative unpredictability and instability in face of changes. By its architecture the V2 storage slowly builds up chunks of sample data, which causes the memory consumption to ramp up over time. As chunks get completed, they are written to disk and can be evicted from memory. Eventually, Prometheus's memory usage reaches a steady state. That is until the monitored environment changes — _series churn_ increases the usage of memory, CPU, and disk IO every time we scale an application or do a rolling update.
-If the change is ongoing, it will yet again reach a steady state eventually but it will be significantly higher than in a more static environment. Transition periods are often multiple hours long and it is hard to determine what the maximum resource usage will be.
-
-The approach of having a single file per time series also makes it way too easy for a single query to knock out the Prometheus process. When querying data that is not cached in memory, the files for queried series are opened and the chunks containing relevant data points are read into memory. If the amount of data exceeds the memory available, Prometheus quits rather ungracefully by getting OOM-killed.
-After the query is completed the loaded data can be released again but it is generally cached much longer to serve subsequent queries on the same data faster. The latter is a good thing obviously.
-
-Lastly, we looked at write amplification in the context of SSDs and how Prometheus addresses it by batching up writes to mitigate it. Nonetheless, in several places it still causes write amplification by having too small batches and not aligning data precisely on page boundaries. For larger Prometheus servers, a reduced hardware lifetime was observed in the real world. Chances are that this is still rather normal for database applications with high write throughput, but we should keep an eye on whether we can mitigate it.
-
-### Starting Over
-
-By now we have a good idea of our problem domain, how the V2 storage solves it, and where its design has issues. We also saw some great concepts that we want to adapt more or less seamlessly. A fair amount of V2's problems can be addressed with improvements and partial redesigns, but to keep things fun (and after carefully evaluating my options, of course), I decided to take a stab at writing an entire time series database — from scratch, i.e. writing bytes to the file system.
-
-The critical concerns of performance and resource usage are a direct consequence of the chosen storage format. We have to find the right set of algorithms and disk layout for our data to implement a well-performing storage layer.
-
-This is where I take the shortcut and drive straight to the solution — skip the headache, failed ideas, endless sketching, tears, and despair.
-
-### V3 — Macro Design
-
-What's the macro layout of our storage? In short, everything that is revealed when running `tree` on our data directory. Just looking at that gives us a surprisingly good picture of what is going on.
-
-```
-$ tree ./data
-./data
-├── b-000001
-│ ├── chunks
-│ │ ├── 000001
-│ │ ├── 000002
-│ │ └── 000003
-│ ├── index
-│ └── meta.json
-├── b-000004
-│ ├── chunks
-│ │ └── 000001
-│ ├── index
-│ └── meta.json
-├── b-000005
-│ ├── chunks
-│ │ └── 000001
-│ ├── index
-│ └── meta.json
-└── b-000006
- ├── meta.json
- └── wal
- ├── 000001
- ├── 000002
- └── 000003
-```
-
-At the top level, we have a sequence of numbered blocks, prefixed with `b-`. Each block obviously holds a file containing an index and a "chunk" directory holding more numbered files. The “chunks” directory contains nothing but raw chunks of data points for various series. Just as for V2, this makes reading series data over a time windows very cheap and allows us to apply the same efficient compression algorithms. The concept has proven to work well and we stick with it. Obviously, there is no longer a single file per series but instead a handful of files holds chunks for many of them.
-The existence of an “index” file should not be surprising. Let's just assume it contains a lot of black magic allowing us to find labels, their possible values, entire time series and the chunks holding their data points.
-
-But why are there several directories containing the layout of index and chunk files? And why does the last one contain a "wal" directory instead? Understanding those two questions, solves about 90% of our problems.
-
-#### Many Little Databases
-
-We partition our _horizontal_ dimension, i.e. the time space, into non-overlapping blocks. Each block acts as a fully independent database containing all time series data for its time window. Hence, it has its own index and set of chunk files.
-
-```
-
-t0 t1 t2 t3 now
- ┌───────────┐ ┌───────────┐ ┌───────────┐ ┌───────────┐
- │ │ │ │ │ │ │ │ ┌────────────┐
- │ │ │ │ │ │ │ mutable │ <─── write ──── ┤ Prometheus │
- │ │ │ │ │ │ │ │ └────────────┘
- └───────────┘ └───────────┘ └───────────┘ └───────────┘ ^
- └──────────────┴───────┬──────┴──────────────┘ │
- │ query
- │ │
- merge ─────────────────────────────────────────────────┘
-```
-
-Every block of data is immutable. Of course, we must be able to add new series and samples to the most recent block as we collect new data. For this block, all new data is written to an in-memory database that provides the same lookup properties as our persistent blocks. The in-memory data structures can be updated efficiently. To prevent data loss, all incoming data is also written to a temporary _write ahead log_ , which is the set of files in our “wal” directory, from which we can re-populate the in-memory database on restart.
-All these files come with their own serialization format, which comes with all the things one would expect: lots of flags, offsets, varints, and CRC32 checksums. Good fun to come up with, rather boring to read about.
-
-This layout allows us to fan out queries to all blocks relevant to the queried time range. The partial results from each block are merged back together to form the overall result.
-
-This horizontal partitioning adds a few great capabilities:
-
-* When querying a time range, we can easily ignore all data blocks outside of this range. It trivially addresses the problem of _series churn_ by reducing the set of inspected data to begin with.
-* When completing a block, we can persist the data from our in-memory database by sequentially writing just a handful of larger files. We avoid any write-amplification and serve SSDs and HDDs equally well.
-* We keep the good property of V2 that recent chunks, which are queried most, are always hot in memory.
-* Nicely enough, we are also no longer bound to the fixed 1KiB chunk size to better align data on disk. We can pick any size that makes the most sense for the individual data points and chosen compression format.
-* Deleting old data becomes extremely cheap and instantaneous. We merely have to delete a single directory. Remember, in the old storage we had to analyze and re-write up to hundreds of millions of files, which could take hours to converge.
-
-Each block also contains a `meta.json` file. It simply holds human-readable information about the block to easily understand the state of our storage and the data it contains.
-
-##### mmap
-
-Moving from millions of small files to a handful of larger allows us to keep all files open with little overhead. This unblocks the usage of [`mmap(2)`][8], a system call that allows us to transparently back a virtual memory region by file contents. For simplicity, you might want to think of it like swap space, just that all our data is on disk already and no writes occur when swapping data out of memory.
-
-This means we can treat all contents of our database as if they were in memory without occupying any physical RAM. Only if we access certain byte ranges in our database files, the operating system lazily loads pages from disk. This puts the operating system in charge of all memory management related to our persisted data. Generally, it is more qualified to make such decisions, as it has the full view on the entire machine and all its processes. Queried data can be rather aggressively cached in memory, yet under memory pressure the pages will be evicted. If the machine has unused memory, Prometheus will now happily cache the entire database, yet will immediately return it once another application needs it.
-Therefore, queries can longer easily OOM our process by querying more persisted data than fits into RAM. The memory cache size becomes fully adaptive and data is only loaded once the query actually needs it.
-
-From my understanding, this is how a lot of databases work today and an ideal way to do it if the disk format allows — unless one is confident to outsmart the OS from within the process. We certainly get a lot of capabilities with little work from our side.
-
-#### Compaction
-
-The storage has to periodically "cut" a new block and write the previous one, which is now completed, onto disk. Only after the block was successfully persisted, the write ahead log files, which are used to restore in-memory blocks, are deleted.
-We are interested in keeping each block reasonably short (about two hours for a typical setup) to avoid accumulating too much data in memory. When querying multiple blocks, we have to merge their results into an overall result. This merge procedure obviously comes with a cost and a week-long query should not have to merge 80+ partial results.
-
-To achieve both, we introduce _compaction_ . Compaction describes the process of taking one or more blocks of data and writing them into a, potentially larger, block. It can also modify existing data along the way, e.g. dropping deleted data, or restructuring our sample chunks for improved query performance.
-
-```
-
-t0 t1 t2 t3 t4 now
- ┌────────────┐ ┌──────────┐ ┌───────────┐ ┌───────────┐ ┌───────────┐
- │ 1 │ │ 2 │ │ 3 │ │ 4 │ │ 5 mutable │ before
- └────────────┘ └──────────┘ └───────────┘ └───────────┘ └───────────┘
- ┌─────────────────────────────────────────┐ ┌───────────┐ ┌───────────┐
- │ 1 compacted │ │ 4 │ │ 5 mutable │ after (option A)
- └─────────────────────────────────────────┘ └───────────┘ └───────────┘
- ┌──────────────────────────┐ ┌──────────────────────────┐ ┌───────────┐
- │ 1 compacted │ │ 3 compacted │ │ 5 mutable │ after (option B)
- └──────────────────────────┘ └──────────────────────────┘ └───────────┘
-```
-
-In this example we have the sequential blocks `[1, 2, 3, 4]`. Blocks 1, 2, and 3 can be compacted together and the new layout is `[1, 4]`. Alternatively, compact them in pairs of two into `[1, 3]`. All time series data still exist but now in fewer blocks overall. This significantly reduces the merging cost at query time as fewer partial query results have to be merged.
-
-#### Retention
-
-We saw that deleting old data was a slow process in the V2 storage and put a toll on CPU, memory, and disk alike. How can we drop old data in our block based design? Quite simply, by just deleting the directory of a block that has no data within our configured retention window. In the example below, block 1 can safely be deleted, whereas 2 has to stick around until it falls fully behind the boundary.
-
-```
- |
- ┌────────────┐ ┌────┼─────┐ ┌───────────┐ ┌───────────┐ ┌───────────┐
- │ 1 │ │ 2 | │ │ 3 │ │ 4 │ │ 5 │ . . .
- └────────────┘ └────┼─────┘ └───────────┘ └───────────┘ └───────────┘
- |
- |
- retention boundary
-```
-
-The older data gets, the larger the blocks may become as we keep compacting previously compacted blocks. An upper limit has to be applied so blocks don’t grow to span the entire database and thus diminish the original benefits of our design.
-Conveniently, this also limits the total disk overhead of blocks that are partially inside and partially outside of the retention window, i.e. block 2 in the example above. When setting the maximum block size at 10% of the total retention window, our total overhead of keeping block 2 around is also bound by 10%.
-
-Summed up, retention deletion goes from very expensive, to practically free.
-
-> _If you've come this far and have some background in databases, you might be asking one thing by now: Is any of this new? — Not really; and probably for the better._
->
-> _The pattern of batching data up in memory, tracked in a write ahead log, and periodically flushed to disk is ubiquitous today._
-> _The benefits we have seen apply almost universally regardless of the data's domain specifics. Prominent open source examples following this approach are LevelDB, Cassandra, InfluxDB, or HBase. The key takeaway is to avoid reinventing an inferior wheel, researching proven methods, and applying them with the right twist._
-> _Running out of places to add your own magic dust later is an unlikely scenario._
-
-### The Index
-
-The initial motivation to investigate storage improvements were the problems brought by _series churn_ . The block-based layout reduces the total number of series that have to be considered for serving a query. So assuming our index lookup was of complexity _O(n^2)_ , we managed to reduce the _n_ a fair amount and now have an improved complexity of _O(n^2)_ — uhm, wait... damnit.
-A quick flashback to "Algorithms 101" reminds us that this, in theory, did not buy us anything. If things were bad before, they are just as bad now. Theory can be depressing.
-
-In practice, most of our queries will already be answered significantly faster. Yet, queries spanning the full time range remain slow even if they just need to find a handful of series. My original idea, dating back way before all this work was started, was a solution to exactly this problem: we need a more capable [ _inverted index_ ][9].
-An inverted index provides a fast lookup of data items based on a subset of their contents. Simply put, I can look up all series that have a label `app=”nginx"` without having to walk through every single series and check whether it contains that label.
-
-For that, each series is assigned a unique ID by which it can be retrieved in constant time, i.e. O(1). In this case the ID is our _forward index_ .
-
-> Example: If the series with IDs 10, 29, and 9 contain the label `app="nginx"`, the inverted index for the label "nginx" is the simple list `[10, 29, 9]`, which can be used to quickly retrieve all series containing the label. Even if there were 20 billion further series, it would not affect the speed of this lookup.
-
-In short, if _n_ is our total number of series, and _m_ is the result size for a given query, the complexity of our query using the index is now _O(m)_ . Queries scaling along the amount of data they retrieve ( _m_ ) instead of the data body being searched ( _n_ ) is a great property as _m_ is generally significantly smaller.
-For brevity, let’s assume we can retrieve the inverted index list itself in constant time.
-
-Actually, this is almost exactly the kind of inverted index V2 has and a minimum requirement to serve performant queries across millions of series. The keen observer will have noticed, that in the worst case, a label exists in all series and thus _m_ is, again, in _O(n)_ . This is expected and perfectly fine. If you query all data, it naturally takes longer. Things become problematic once we get involved with more complex queries.
-
-#### Combining Labels
-
-Labels associated with millions of series are common. Suppose a horizontally scaling “foo” microservice with hundreds of instances with thousands of series each. Every single series will have the label `app="foo"`. Of course, one generally won't query all series but restrict the query by further labels, e.g. I want to know how many requests my service instances received and query `__name__="requests_total" AND app="foo"`.
-
-To find all series satisfying both label selectors, we take the inverted index list for each and intersect them. The resulting set will typically be orders of magnitude smaller than each input list individually. As each input list has the worst case size O(n), the brute force solution of nested iteration over both lists, has a runtime of O(n^2). The same cost applies for other set operations, such as the union (`app="foo" OR app="bar"`). When adding further label selectors to the query, the exponent increases for each to O(n^3), O(n^4), O(n^5), ... O(n^k). A lot of tricks can be played to minimize the effective runtime by changing the execution order. The more sophisticated, the more knowledge about the shape of the data and the relationships between labels is needed. This introduces a lot of complexity, yet does not decrease our algorithmic worst case runtime.
-
-This is essentially the approach in the V2 storage and luckily a seemingly slight modification is enough gain significant improvements. What happens if we assume that the IDs in our inverted indices are sorted?
-
-Suppose this example of lists for our initial query:
-
-```
-__name__="requests_total" -> [ 9999, 1000, 1001, 2000000, 2000001, 2000002, 2000003 ]
- app="foo" -> [ 1, 3, 10, 11, 12, 100, 311, 320, 1000, 1001, 10002 ]
-
- intersection => [ 1000, 1001 ]
-```
-
-The intersection is fairly small. We can find it by setting a cursor at the beginning of each list and always advancing the one at the smaller number. When both numbers are equal, we add the number to our result and advance both cursors. Overall, we scan both lists in this zig-zag pattern and thus have a total cost of _O(2n) = O(n)_ as we only ever move forward in either list.
-
-The procedure for more than two lists of different set operations works similarly. So the number of _k_ set operations merely modifies the factor ( _O(k*n)_ ) instead of the exponent ( _O(n^k)_ ) of our worst-case lookup runtime. A great improvement.
-What I described here is a simplified version of the canonical search index used by practically any [full text search engine][10] out there. Every series descriptor is treated as a short "document", and every label (name + fixed value) as a "word" inside of it. We can ignore a lot of additional data typically encountered in search engine indices, such as word position and frequency data.
-Seemingly endless research exists on approaches improving the practical runtime, often making some assumptions about the input data. Unsurprisingly, there are also plenty of techniques to compress inverted indices that come with their own benefits and drawbacks. As our "documents" are tiny and the “words” are hugely repetitive across all series, compression becomes almost irrelevant. For example, a real-world dataset of ~4.4 million series with about 12 labels each has less than 5,000 unique labels. For our initial storage version, we stick to the basic approach without compression, and just a few simple tweaks added to skip over large ranges of non-intersecting IDs.
-
-While keeping the IDs sorted may sound simple, it is not always a trivial invariant to keep up. For instance, the V2 storage assigns hashes as IDs to new series and we cannot efficiently build up sorted inverted indices.
-Another daunting task is modifying the indices on disk as data gets deleted or updated. Typically, the easiest approach is to simply recompute and rewrite them but doing so while keeping the database queryable and consistent. The V3 storage does exactly this by having a separate immutable index per block that is only modified via rewrite on compaction. Only the indices for the mutable blocks, which are held entirely in memory, need to be updated.
-
-### Benchmarking
-
-I started initial development of the storage with a benchmark based on ~4.4 million series descriptors extracted from a real world data set and generated synthetic data points to feed into those series. This iteration just tested the stand-alone storage and was crucial to quickly identify performance bottlenecks and trigger deadlocks only experienced under highly concurrent load.
-
-After the conceptual implementation was done, the benchmark could sustain a write throughput of 20 million data points per second on my Macbook Pro — all while a dozen Chrome tabs and Slack were running. So while this sounded all great it also indicated that there's no further point in pushing this benchmark (or running it in a less random environment for that matter). After all, it is synthetic and thus not worth much beyond a good first impression. Starting out about 20x above the initial design target, it was time to embed this into an actual Prometheus server, adding all the practical overhead and flakes only experienced in more realistic environments.
-
-We actually had no reproducible benchmarking setup for Prometheus, in particular none that allowed A/B testing of different versions. Concerning in hindsight, but [now we have one][11]!
-
-Our tool allows us to declaratively define a benchmarking scenario, which is then deployed to a Kubernetes cluster on AWS. While this is not the best environment for all-out benchmarking, it certainly reflects our user base better than dedicated bare metal servers with 64 cores and 128GB of memory.
-We deploy two Prometheus 1.5.2 servers (V2 storage) and two Prometheus servers from the 2.0 development branch (V3 storage). Each Prometheus server runs on a dedicated machine with an SSD. A horizontally scaled application exposing typical microservice metrics is deployed to worker nodes. Additionally, the Kubernetes cluster itself and the nodes are being monitored. The whole setup is supervised by yet another Meta-Prometheus, monitoring each Prometheus server for health and performance.
-To simulate series churn, the microservice is periodically scaled up and down to remove old pods and spawn new pods, exposing new series. Query load is simulated by a selection of "typical" queries, run against one server of each Prometheus version.
-
-Overall the scaling and querying load as well as the sampling frequency significantly exceed today's production deployments of Prometheus. For instance, we swap out 60% of our microservice instances every 15 minutes to produce series churn. This would likely only happen 1-5 times a day in a modern infrastructure. This ensures that our V3 design is capable of handling the workloads of the years ahead. As a result, the performance differences between Prometheus 1.5.2 and 2.0 are larger than in a more moderate environment.
-In total, we are collecting about 110,000 samples per second from 850 targets exposing half a million series at a time.
-
-After leaving this setup running for a while, we can take a look at the numbers. We evaluate several metrics over the first 12 hours within both versiones reached a steady state.
-
-> Be aware of the slightly truncated Y axis in screen shots from the Prometheus graph UI.
-
- 
-> _Heap memory usage in GB_
-
-Memory usage is the most troubling resource for users today as it is relatively unpredictable and it may cause the process to crash.
-Obviously, the queried servers are consuming more memory, which can largely be attributed to overhead of the query engine, which will be subject to future optimizations. Overall, Prometheus 2.0's memory consumption is reduced by 3-4x. After about six hours, there is a clear spike in Prometheus 1.5, which aligns with the our retention boundary at six hours. As deletions are quite costly, resource consumption ramps up. This will become visible throughout various other graphs below.
-
- 
-> _CPU usage in cores/second_
-
-A similar pattern shows for CPU usage, but the delta between queried and non-queried servers is more significant. Averaging at about 0.5 cores/sec while ingesting about 110,000 samples/second, our new storage becomes almost negligible compared to the cycles spent on query evaluation. In total the new storage needs 3-10 times fewer CPU resources.
-
- 
->_Disk writes in MB/second_
-
-The by far most dramatic and unexpected improvement shows in write utilization of our disk. It clearly shows why Prometheus 1.5 is prone to wear out SSDs. We see an initial ramp-up as soon as the first chunks are persisted into the series files and a second ramp-up once deletion starts rewriting them. Surprisingly, the queried and non-queried server show a very different utilization.
-Prometheus 2.0 on the other hand, merely writes about a single Megabyte per second to its write ahead log. Writes periodically spike when blocks are compacted to disk. Overall savings: staggering 97-99%.
-
- 
-> _Disk size in GB_
-
-Closely related to disk writes is the total amount of occupied disk space. As we are using almost the same compression algorithm for samples, which is the bulk of our data, they should be about the same. In a more stable setup that would largely be true, but as we are dealing with high _series churn_ , there's also the per-series overhead to consider.
-As we can see, Prometheus 1.5 ramps up storage space a lot faster before both versions reach a steady state as the retention kicks in. Prometheus 2.0 seems to have a significantly lower overhead per individual series. We can nicely see how space is linearly filled up by the write ahead log and instantaneously drops as its gets compacted. The fact that the lines for both Prometheus 2.0 servers do not exactly match is a fact that needs further investigation.
-
-This all looks quite promising. The important piece left is query latency. The new index should have improved our lookup complexity. What has not substantially changed is processing of this data, e.g. in `rate()` functions or aggregations. Those aspects are part of the query engine.
-
- 
->_99th percentile query latency in seconds_
-
-Expectations are completely met by the data. In Prometheus 1.5 the query latency increases over time as more series are stored. It only levels off once retention starts and old series are deleted. In contrast, Prometheus 2.0 stays in place right from the beginning.
-Some caution must be taken on how this data was collected. The queries fired against the servers were chosen by estimating a good mix of range and instant queries, doing heavier and more lightweight computations, and touching few or many series. It does not necessarily represent a real-world distribution of queries. It is also not representative for queries hitting cold data and we can assume that all sample data is practically always hot in memory in either storage.
-Nonetheless, we can say with good confidence, that the overall query performance became very resilient to series churn and improved by up to 4x in our straining benchmarking scenario. In a more static environment, we can assume query time to be mostly spent in the query engine itself and the improvement to be notably lower.
-
- 
->_Ingested samples/second_
-
-Lastly, a quick look into our ingestion rates of the different Prometheus servers. We can see that both servers with the V3 storage have the same ingestion rate. After a few hours it becomes unstable, which is caused by various nodes of the benchmarking cluster becoming unresponsive due to high load rather than the Prometheus instances. (The fact that both 2.0 lines exactly match is hopefully convincing enough.)
-Both Prometheus 1.5.2 servers start suffering from significant drops in ingestion rate even though more CPU and memory resources are available. The high stress of series churn causes a larger amount of data to not be collected.
-
-But what's the _absolute maximum_ number of samples per second you could ingest now?
-
-I don't know — and deliberately don't care.
-
-There are a lot of factors that shape the data flowing into Prometheus and there is no single number capable of capturing quality. Maximum ingestion rate has historically been a metric leading to skewed benchmarks and neglect of more important aspects such as query performance and resilience to series churn. The rough assumption that resource usage increases linearly was confirmed by some basic testing. It is easy to extrapolate what could be possible.
-
-Our benchmarking setup simulates a highly dynamic environment stressing Prometheus more than most real-world setups today. The results show we went way above our initial design goal, while running on non-optimal cloud servers. Ultimately, success will be determined by user feedback rather than benchmarking numbers.
-
-> Note: _At time of writing this, Prometheus 1.6 is in development, which will allow configuring the maximum memory usage more reliably and may notably reduce overall consumption in favor of slightly increased CPU utilization. I did not repeat the tests against this as the overall results still hold, especially when facing high series churn._
-
-### Conclusion
-
-Prometheus sets out to handle high cardinality of series and throughput of individual samples. It remains a challenging task, but the new storage seems to position us well for the hyper-scale, hyper-convergent, GIFEE infrastructure of the futu... well, it seems to work pretty well.
-
-A [first alpha release of Prometheus 2.0][12] with the new V3 storage is available for testing. Expect crashes, deadlocks, and other bugs at this early stage.
-
-The code for the storage itself can be found [in a separate project][13]. It's surprisingly agnostic to Prometheus itself and could be widely useful for a wider range of applications looking for an efficient local storage time series database.
-
-> _There's a long list of people to thank for their contributions to this work. Here they go in no particular order:_
->
-> _The groundlaying work by Bjoern Rabenstein and Julius Volz on the V2 storage engine and their feedback on V3 was fundamental to everything seen in this new generation._
->
-> _Wilhelm Bierbaum's ongoing advice and insight contributed significantly to the new design. Brian Brazil's continous feedback ensured that we ended up with a semantically sound approach. Insightful discussions with Peter Bourgon validated the design and shaped this write-up._
->
-> _Not to forget my entire team at CoreOS and the company itself for supporting and sponsoring this work. Thanks to everyone who listened to my ramblings about SSDs, floats, and serialization formats again and again._
-
-
---------------------------------------------------------------------------------
-
-via: https://fabxc.org/blog/2017-04-10-writing-a-tsdb/
-
-作者:[Fabian Reinartz ][a]
-译者:[译者ID](https://github.com/译者ID)
-校对:[校对者ID](https://github.com/校对者ID)
-
-本文由 [LCTT](https://github.com/LCTT/TranslateProject) 原创编译,[Linux中国](https://linux.cn/) 荣誉推出
-
-[a]:https://twitter.com/fabxc
-[1]:https://en.wikipedia.org/wiki/Inode
-[2]:https://prometheus.io/
-[3]:https://kubernetes.io/
-[4]:https://en.wikipedia.org/wiki/Write_amplification
-[5]:http://codecapsule.com/2014/02/12/coding-for-ssds-part-1-introduction-and-table-of-contents/
-[6]:https://prometheus.io/docs/practices/rules/
-[7]:http://www.vldb.org/pvldb/vol8/p1816-teller.pdf
-[8]:https://en.wikipedia.org/wiki/Mmap
-[9]:https://en.wikipedia.org/wiki/Inverted_index
-[10]:https://en.wikipedia.org/wiki/Search_engine_indexing#Inverted_indices
-[11]:https://github.com/prometheus/prombench
-[12]:https://prometheus.io/blog/2017/04/10/promehteus-20-sneak-peak/
-[13]:https://github.com/prometheus/tsdb
diff --git a/sources/tech/20170414 5 projects for Raspberry Pi at home.md b/sources/tech/20170414 5 projects for Raspberry Pi at home.md
deleted file mode 100644
index 69aeaf32ac..0000000000
--- a/sources/tech/20170414 5 projects for Raspberry Pi at home.md
+++ /dev/null
@@ -1,146 +0,0 @@
-[#]: collector: (lujun9972)
-[#]: translator: ( )
-[#]: reviewer: ( )
-[#]: publisher: ( )
-[#]: url: ( )
-[#]: subject: (5 projects for Raspberry Pi at home)
-[#]: via: (https://opensource.com/article/17/4/5-projects-raspberry-pi-home)
-[#]: author: (Ben Nuttall https://opensource.com/users/bennuttall)
-
-5 projects for Raspberry Pi at home
-======
-
-![5 projects for Raspberry Pi at home][1]
-
-The [Raspberry Pi][2] computer can be used in all kinds of settings and for a variety of purposes. It obviously has a place in education for helping students with learning programming and maker skills in the classroom and the hackspace, and it has plenty of industrial applications in the workplace and in factories. I'm going to introduce five projects you might want to build in your own home.
-
-### Media center
-
-One of the most common uses for Raspberry Pi in people's homes is behind the TV running media center software serving multimedia files. It's easy to set this up, and the Raspberry Pi provides plenty of GPU (Graphics Processing Unit) power to render HD TV shows and movies to your big screen TV. [Kodi][3] (formerly XBMC) on a Raspberry Pi is a great way to playback any media you have on a hard drive or network-attached storage. You can also install a plugin to play YouTube videos.
-
-There are a few different options available, most prominently [OSMC][4] (Open Source Media Center) and [LibreELEC][5], both based on Kodi. They both perform well at playing media content, but OSMC has a more visually appearing user interface, while LibreElec is much more lightweight. All you have to do is choose a distribution, download the image and install on an SD card (or just use [NOOBS][6]), boot it up, and you're ready to go.
-
-![LibreElec ][7]
-
-LibreElec; Raspberry Pi Foundation, CC BY-SA
-
-![OSMC][8]
-
-OSMC.tv, Copyright, Used with permission
-
-Before proceeding you'll need to decide [w][9][hich Raspberry Pi model to use][9]. These distributions will work on any Pi (1, 2, 3, or Zero), and video playback will essentially be matched on each of these. Apart from the Pi 3 (and Zero W) having built-in Wi-Fi, the only noticeable difference is the reaction speed of the user interface, which will be much faster on a Pi 3. A Pi 2 will not be much slower, so that's fine if you don't need Wi-Fi, but the Pi 3 will noticeably outperform the Pi 1 and Zero when it comes to flicking through the menus.
-
-### SSH gateway
-
-If you want to be able to access computers and devices on your home network from outside over the internet, you have to open up ports on those devices to allow outside traffic. Opening ports to the internet is a security risk, meaning you're always at risk of attack, misuse, or any kind of unauthorized access. However, if you install a Raspberry Pi on your network and set up port forwarding to allow only SSH access to that Pi, you can use that as a secure gateway to hop onto other Pis and PCs on the network.
-
-Most routers allow you to configure port-forwarding rules. You'll need to give your Pi a fixed internal IP address and set up port 22 on your router to map to port 22 on your Raspberry Pi. If your ISP provides you with a static IP address, you'll be able to SSH into it with this as the host address (for example, **ssh pi@123.45.56.78** ). If you have a domain name, you can configure a subdomain to point to this IP address, so you don't have to remember it (for example, **ssh[pi@home.mydomain.com][10]** ).
-
-![][11]
-
-However, if you're going to expose a Raspberry Pi to the internet, you should be very careful not to put your network at risk. There are a few simple procedures you can follow to make it sufficiently secure:
-
-1\. Most people suggest you change your login password (which makes sense, seeing as the default password “raspberry” is well known), but this does not protect against brute-force attacks. You could change your password and add a two-factor authentication (so you need your password _and_ a time-dependent passcode generated by your phone), which is more secure. However, I believe the best way to secure your Raspberry Pi from intruders is to [disable][12] [“password authentication”][12] in your SSH configuration, so you allow only SSH key access. This means that anyone trying to SSH in by guessing your password will never succeed. Only with your private SSH key can anyone gain access. Similarly, most people suggest changing the SSH port from the default 22 to something unexpected, but a simple [Nmap][13] of your IP address will reveal your true SSH port.
-
-2\. Ideally, you would not run much in the way of other software on this Pi, so you don't end up accidentally exposing anything else. If you want to run other software, you might be better running it on another Pi on the network that is not exposed to the internet. Ensure that you keep your packages up to date by upgrading regularly, particularly the **openssh-server** package, so that any security vulnerabilities are patched.
-
-3\. Install [sshblack][14] or [fail2ban][15] to blacklist any users who seem to be acting maliciously, such as attempting to brute force your SSH password.
-
-Once you've secured your Raspberry Pi and put it online, you'll be able to log in to your network from anywhere in the world. Once you're on your Raspberry Pi, you can SSH into other devices on the network using their local IP address (for example, 192.168.1.31). If you have passwords on these devices, just use the password. If they're also SSH-key-only, you'll need to ensure your key is forwarded over SSH by using the **-A** flag: **ssh -A pi@123.45.67.89**.
-
-### CCTV / pet camera
-
-Another great home project is to set up a camera module to take photos or stream video, capture and save files, or streamed internally or to the internet. There are many reasons you might want to do this, but two common use cases are for a homemade security camera or to monitor a pet.
-
-The [Raspberry Pi camera module][16] is a brilliant accessory. It provides full HD photo and video, lots of advanced configuration, and is [easy to][17] [program][17]. The [infrared camera][18] is ideal for this kind of use, and with an infrared LED (which the Pi can control) you can see in the dark!
-
-If you want to take still images on a regular basis to keep an eye on things, you can just write a short [Python][19] script or use the command line tool [raspistill][20], and schedule it to recur in [Cron][21]. You might want to have it save them to [Dropbox][22] or another web service, upload them to a web server, or you can even create a [web app][23] to display them.
-
-If you want to stream video, internally or externally, that's really easy, too. A simple MJPEG (Motion JPEG) example is provided in the [picamera documentation][24] (under “web streaming”). Just download or copy that code into a file, run it and visit the Pi's IP address at port 8000, and you'll see your camera's output live.
-
-A more advanced streaming project, [pistreaming][25], is available, which uses [JSMpeg][26] (a JavaScript video player) with the web server and a websocket for the camera stream running separately. This method is more performant and is just as easy to get running as the previous example, but there is more code involved and if set up to stream on the internet, requires you to open two ports.
-
-Once you have web streaming set up, you can position the camera where you want it. I have one set up to keep an eye on my pet tortoise:
-
-![Tortoise ][27]
-
-Ben Nuttall, CC BY-SA
-
-If you want to be able to control where the camera actually points, you can do so using servos. A neat solution is to use Pimoroni's [Pan-Tilt HAT][28], which allows you to move the camera easily in two dimensions. To integrate this with pistreaming, see the project's [pantilthat branch][29].
-
-![Pan-tilt][30]
-
-Pimoroni.com, Copyright, Used with permission
-
-If you want to position your Pi outside, you'll need a waterproof enclosure and some way of getting power to the Pi. PoE (Power-over-Ethernet) cables can be a good way of achieving this.
-
-### Home automation and IoT
-
-It's 2017 and there are internet-connected devices everywhere, especially in the home. Our lightbulbs have Wi-Fi, our toasters are smarter than they used to be, and our tea kettles are at risk of attack from Russia. As long as you keep your devices secure, or don't connect them to the internet if they don't need to be, then you can make great use of IoT devices to automate tasks around the home.
-
-There are plenty of services you can buy or subscribe to, like Nest Thermostat or Philips Hue lightbulbs, which allow you to control your heating or your lighting from your phone, respectively—whether you're inside or away from home. You can use a Raspberry Pi to boost the power of these kinds of devices by automating interactions with them according to a set of rules involving timing or even sensors. One thing you can't do with Philips Hue is have the lights come on when you enter the room, but with a Raspberry Pi and a motion sensor, you can use a Python API to turn on the lights. Similarly, you can configure your Nest to turn on the heating when you're at home, but what if you only want it to turn on if there's at least two people home? Write some Python code to check which phones are on the network and if there are at least two, tell the Nest to turn on the heat.
-
-You can do a great deal more without integrating with existing IoT devices and with only using simple components. A homemade burglar alarm, an automated chicken coop door opener, a night light, a music box, a timed heat lamp, an automated backup server, a print server, or whatever you can imagine.
-
-### Tor proxy and blocking ads
-
-Adafruit's [Onion Pi][31] is a [Tor][32] proxy that makes your web traffic anonymous, allowing you to use the internet free of snoopers and any kind of surveillance. Follow Adafruit's tutorial on setting up Onion Pi and you're on your way to a peaceful anonymous browsing experience.
-
-![Onion-Pi][33]
-
-Onion-pi from Adafruit, Copyright, Used with permission
-
-![Pi-hole][34]You can install a Raspberry Pi on your network that intercepts all web traffic and filters out any advertising. Simply download the [Pi-hole][35] software onto the Pi, and all devices on your network will be ad-free (it even blocks in-app ads on your mobile devices).
-
-There are plenty more uses for the Raspberry Pi at home. What do you use Raspberry Pi for at home? What do you want to use it for?
-
-Let us know in the comments.
-
---------------------------------------------------------------------------------
-
-via: https://opensource.com/article/17/4/5-projects-raspberry-pi-home
-
-作者:[Ben Nuttall][a]
-选题:[lujun9972][b]
-译者:[译者ID](https://github.com/译者ID)
-校对:[校对者ID](https://github.com/校对者ID)
-
-本文由 [LCTT](https://github.com/LCTT/TranslateProject) 原创编译,[Linux中国](https://linux.cn/) 荣誉推出
-
-[a]: https://opensource.com/users/bennuttall
-[b]: https://github.com/lujun9972
-[1]: https://opensource.com/sites/default/files/styles/image-full-size/public/lead-images/raspberry_pi_home_automation.png?itok=2TnmJpD8 (5 projects for Raspberry Pi at home)
-[2]: https://www.raspberrypi.org/
-[3]: https://kodi.tv/
-[4]: https://osmc.tv/
-[5]: https://libreelec.tv/
-[6]: https://www.raspberrypi.org/downloads/noobs/
-[7]: https://opensource.com/sites/default/files/libreelec_0.png (LibreElec )
-[8]: https://opensource.com/sites/default/files/osmc.png (OSMC)
-[9]: https://opensource.com/life/16/10/which-raspberry-pi-should-you-choose-your-project
-[10]: mailto:pi@home.mydomain.com
-[11]: https://opensource.com/sites/default/files/resize/screenshot_from_2017-04-07_15-13-01-700x380.png
-[12]: http://stackoverflow.com/questions/20898384/ssh-disable-password-authentication
-[13]: https://nmap.org/
-[14]: http://www.pettingers.org/code/sshblack.html
-[15]: https://www.fail2ban.org/wiki/index.php/Main_Page
-[16]: https://www.raspberrypi.org/products/camera-module-v2/
-[17]: https://opensource.com/life/15/6/raspberry-pi-camera-projects
-[18]: https://www.raspberrypi.org/products/pi-noir-camera-v2/
-[19]: http://picamera.readthedocs.io/
-[20]: https://www.raspberrypi.org/documentation/usage/camera/raspicam/raspistill.md
-[21]: https://www.raspberrypi.org/documentation/linux/usage/cron.md
-[22]: https://github.com/RZRZR/plant-cam
-[23]: https://github.com/bennuttall/bett-bot
-[24]: http://picamera.readthedocs.io/en/release-1.13/recipes2.html#web-streaming
-[25]: https://github.com/waveform80/pistreaming
-[26]: http://jsmpeg.com/
-[27]: https://opensource.com/sites/default/files/tortoise.jpg (Tortoise)
-[28]: https://shop.pimoroni.com/products/pan-tilt-hat
-[29]: https://github.com/waveform80/pistreaming/tree/pantilthat
-[30]: https://opensource.com/sites/default/files/pan-tilt.gif (Pan-tilt)
-[31]: https://learn.adafruit.com/onion-pi/overview
-[32]: https://www.torproject.org/
-[33]: https://opensource.com/sites/default/files/onion-pi.jpg (Onion-Pi)
-[34]: https://opensource.com/sites/default/files/resize/pi-hole-250x250.png (Pi-hole)
-[35]: https://pi-hole.net/
diff --git a/sources/tech/20171215 How to add a player to your Python game.md b/sources/tech/20171215 How to add a player to your Python game.md
deleted file mode 100644
index caa1e4754e..0000000000
--- a/sources/tech/20171215 How to add a player to your Python game.md
+++ /dev/null
@@ -1,162 +0,0 @@
-[#]: collector: (lujun9972)
-[#]: translator: ( )
-[#]: reviewer: ( )
-[#]: publisher: ( )
-[#]: url: ( )
-[#]: subject: (How to add a player to your Python game)
-[#]: via: (https://opensource.com/article/17/12/game-python-add-a-player)
-[#]: author: (Seth Kenlon https://opensource.com/users/seth)
-
-How to add a player to your Python game
-======
-Part three of a series on building a game from scratch with Python.
-
-
-In the [first article of this series][1], I explained how to use Python to create a simple, text-based dice game. In the second part, I showed you how to build a game from scratch, starting with [creating the game's environment][2]. But every game needs a player, and every player needs a playable character, so that's what we'll do next in the third part of the series.
-
-In Pygame, the icon or avatar that a player controls is called a sprite. If you don't have any graphics to use for a player sprite yet, create something for yourself using [Krita][3] or [Inkscape][4]. If you lack confidence in your artistic skills, you can also search [OpenClipArt.org][5] or [OpenGameArt.org][6] for something pre-generated. Then, if you didn't already do so in the previous article, create a directory called `images` alongside your Python project directory. Put the images you want to use in your game into the `images` folder.
-
-To make your game truly exciting, you ought to use an animated sprite for your hero. It means you have to draw more assets, but it makes a big difference. The most common animation is a walk cycle, a series of drawings that make it look like your sprite is walking. The quick and dirty version of a walk cycle requires four drawings.
-
-
-
-Note: The code samples in this article allow for both a static player sprite and an animated one.
-
-Name your player sprite `hero.png`. If you're creating an animated sprite, append a digit after the name, starting with `hero1.png`.
-
-### Create a Python class
-
-In Python, when you create an object that you want to appear on screen, you create a class.
-
-Near the top of your Python script, add the code to create a player. In the code sample below, the first three lines are already in the Python script that you're working on:
-
-```
-import pygame
-import sys
-import os # new code below
-
-class Player(pygame.sprite.Sprite):
- '''
- Spawn a player
- '''
- def __init__(self):
- pygame.sprite.Sprite.__init__(self)
- self.images = []
- img = pygame.image.load(os.path.join('images','hero.png')).convert()
- self.images.append(img)
- self.image = self.images[0]
- self.rect = self.image.get_rect()
-```
-
-If you have a walk cycle for your playable character, save each drawing as an individual file called `hero1.png` to `hero4.png` in the `images` folder.
-
-Use a loop to tell Python to cycle through each file.
-
-```
-'''
-Objects
-'''
-
-class Player(pygame.sprite.Sprite):
- '''
- Spawn a player
- '''
- def __init__(self):
- pygame.sprite.Sprite.__init__(self)
- self.images = []
- for i in range(1,5):
- img = pygame.image.load(os.path.join('images','hero' + str(i) + '.png')).convert()
- self.images.append(img)
- self.image = self.images[0]
- self.rect = self.image.get_rect()
-```
-
-### Bring the player into the game world
-
-Now that a Player class exists, you must use it to spawn a player sprite in your game world. If you never call on the Player class, it never runs, and there will be no player. You can test this out by running your game now. The game will run just as well as it did at the end of the previous article, with the exact same results: an empty game world.
-
-To bring a player sprite into your world, you must call the Player class to generate a sprite and then add it to a Pygame sprite group. In this code sample, the first three lines are existing code, so add the lines afterwards:
-
-```
-world = pygame.display.set_mode([worldx,worldy])
-backdrop = pygame.image.load(os.path.join('images','stage.png')).convert()
-backdropbox = screen.get_rect()
-
-# new code below
-
-player = Player() # spawn player
-player.rect.x = 0 # go to x
-player.rect.y = 0 # go to y
-player_list = pygame.sprite.Group()
-player_list.add(player)
-```
-
-Try launching your game to see what happens. Warning: it won't do what you expect. When you launch your project, the player sprite doesn't spawn. Actually, it spawns, but only for a millisecond. How do you fix something that only happens for a millisecond? You might recall from the previous article that you need to add something to the main loop. To make the player spawn for longer than a millisecond, tell Python to draw it once per loop.
-
-Change the bottom clause of your loop to look like this:
-
-```
- world.blit(backdrop, backdropbox)
- player_list.draw(screen) # draw player
- pygame.display.flip()
- clock.tick(fps)
-```
-
-Launch your game now. Your player spawns!
-
-### Setting the alpha channel
-
-Depending on how you created your player sprite, it may have a colored block around it. What you are seeing is the space that ought to be occupied by an alpha channel. It's meant to be the "color" of invisibility, but Python doesn't know to make it invisible yet. What you are seeing, then, is the space within the bounding box (or "hit box," in modern gaming terms) around the sprite.
-
-
-
-You can tell Python what color to make invisible by setting an alpha channel and using RGB values. If you don't know the RGB values your drawing uses as alpha, open your drawing in Krita or Inkscape and fill the empty space around your drawing with a unique color, like #00ff00 (more or less a "greenscreen green"). Take note of the color's hex value (#00ff00, for greenscreen green) and use that in your Python script as the alpha channel.
-
-Using alpha requires the addition of two lines in your Sprite creation code. Some version of the first line is already in your code. Add the other two lines:
-
-```
- img = pygame.image.load(os.path.join('images','hero' + str(i) + '.png')).convert()
- img.convert_alpha() # optimise alpha
- img.set_colorkey(ALPHA) # set alpha
-```
-
-Python doesn't know what to use as alpha unless you tell it. In the setup area of your code, add some more color definitions. Add this variable definition anywhere in your setup section:
-
-```
-ALPHA = (0, 255, 0)
-```
-
-In this example code, **0,255,0** is used, which is the same value in RGB as #00ff00 is in hex. You can get all of these color values from a good graphics application like [GIMP][7], Krita, or Inkscape. Alternately, you can also detect color values with a good system-wide color chooser, like [KColorChooser][8].
-
-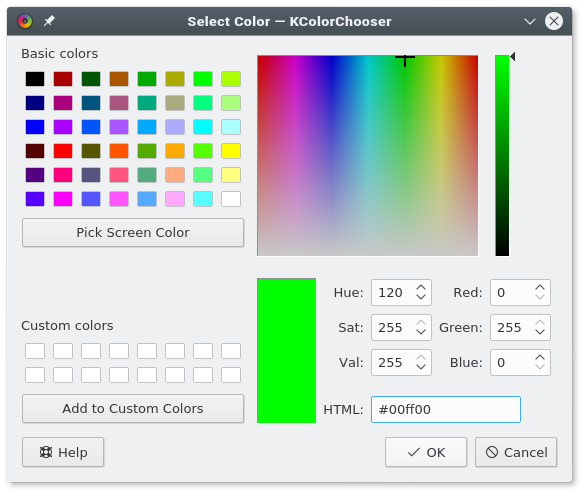
-
-If your graphics application is rendering your sprite's background as some other value, adjust the values of your alpha variable as needed. No matter what you set your alpha value, it will be made "invisible." RGB values are very strict, so if you need to use 000 for alpha, but you need 000 for the black lines of your drawing, just change the lines of your drawing to 111, which is close enough to black that nobody but a computer can tell the difference.
-
-Launch your game to see the results.
-
-
-
-In the [fourth part of this series][9], I'll show you how to make your sprite move. How exciting!
-
---------------------------------------------------------------------------------
-
-via: https://opensource.com/article/17/12/game-python-add-a-player
-
-作者:[Seth Kenlon][a]
-选题:[lujun9972][b]
-译者:[译者ID](https://github.com/译者ID)
-校对:[校对者ID](https://github.com/校对者ID)
-
-本文由 [LCTT](https://github.com/LCTT/TranslateProject) 原创编译,[Linux中国](https://linux.cn/) 荣誉推出
-
-[a]: https://opensource.com/users/seth
-[b]: https://github.com/lujun9972
-[1]: https://opensource.com/article/17/10/python-101
-[2]: https://opensource.com/article/17/12/program-game-python-part-2-creating-game-world
-[3]: http://krita.org
-[4]: http://inkscape.org
-[5]: http://openclipart.org
-[6]: https://opengameart.org/
-[7]: http://gimp.org
-[8]: https://github.com/KDE/kcolorchooser
-[9]: https://opensource.com/article/17/12/program-game-python-part-4-moving-your-sprite
diff --git a/sources/tech/20180130 An introduction to the DomTerm terminal emulator for Linux.md b/sources/tech/20180130 An introduction to the DomTerm terminal emulator for Linux.md
deleted file mode 100644
index 4553570166..0000000000
--- a/sources/tech/20180130 An introduction to the DomTerm terminal emulator for Linux.md
+++ /dev/null
@@ -1,126 +0,0 @@
-An introduction to the DomTerm terminal emulator for Linux
-======
-
-
-[DomTerm][1] is a modern terminal emulator that uses a browser engine as a "GUI toolkit." This enables some neat features, such as embeddable graphics and links, HTML rich text, and foldable (show/hide) commands. Otherwise it looks and feels like a feature-full, standalone terminal emulator, with excellent xterm compatibility (including mouse handling and 24-bit color), and appropriate "chrome" (menus). In addition, there is built-in support for session management and sub-windows (as in `tmux` and `GNU screen`), basic input editing (as in `readline`), and paging (as in `less`).
-
-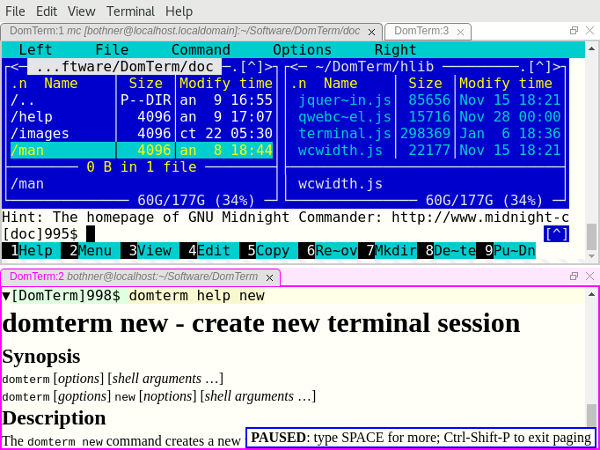
-Image 1: The DomTerminal terminal emulator. View larger image.
-
-Below we'll look more at these features. We'll assume you have `domterm` installed (skip to the end of this article if you need to get and build DomTerm). First, though, here's a quick overview of the technology.
-
-### Frontend vs. backend
-
-Most of DomTerm is written in JavaScript and runs in a browser engine. This can be a desktop web browser, such as Chrome or Firefox (see image 3), or it can be an embedded browser. Using a general web browser works fine, but the user experience isn't as nice (as the menus are designed for general browsing, not for a terminal emulator), and the security model gets in the way, so using an embedded browser is nicer.
-
-The following are currently supported:
-
- * `qtdomterm`, which uses the Qt toolkit and `QtWebEngine`
- * An `[Electron][2]` embedding (see image 1)
- * `atom-domterm` runs DomTerm as a package in the [Atom text editor][3] (which is also based on Electron) and integrates with the Atom pane system (see image 2)
- * A wrapper for JavaFX's `WebEngine`, which is useful for code written in Java (see image 4)
- * Previously, the preferred frontend used [Firefox-XUL][4], but Mozilla has since dropped XUL
-
-
-
-![DomTerm terminal panes in Atom editor][6]
-
-Image 2: DomTerm terminal panes in Atom editor. [View larger image.][7]
-
-Currently, the Electron frontend is probably the nicest option, closely followed by the Qt frontend. If you use Atom, `atom-domterm` works pretty well.
-
-The backend server is written in C. It manages pseudo terminals (PTYs) and sessions. It is also an HTTP server that provides the JavaScript and other files to the frontend. The `domterm` command starts terminal jobs and performs other requests. If there is no server running, `domterm` daemonizes itself. Communication between the backend and the server is normally done using WebSockets (with [libwebsockets][8] on the server). However, the JavaFX embedding uses neither WebSockets nor the DomTerm server; instead Java applications communicate directly using the Java-JavaScript bridge.
-
-### A solid xterm-compatible terminal emulator
-
-DomTerm looks and feels like a modern terminal emulator. It handles mouse events, 24-bit color, Unicode, double-width (CJK) characters, and input methods. DomTerm does a very good job on the [vttest testsuite][9].
-
-Unusual features include:
-
-**Show/hide buttons ("folding"):** The little triangles (seen in image 2 above) are buttons that hide/show the corresponding output. To create the buttons, just add certain [escape sequences][10] in the [prompt text][11].
-
-**Mouse-click support for`readline` and similar input editors:** If you click in the (yellow) input area, DomTerm will send the right sequence of arrow-key keystrokes to the application. (This is enabled by escape sequences in the prompt; you can also force it using Alt+Click.)
-
-**Style the terminal using CSS:** This is usually done in `~/.domterm/settings.ini`, which is automatically reloaded when saved. For example, in image 2, terminal-specific background colors were set.
-
-### A better REPL console
-
-A classic terminal emulator works on rectangular grids of character cells. This works for a REPL (command shell), but it is not ideal. Here are some DomTerm features useful for REPLs that are not typically found in terminal emulators:
-
-**A command can "print" an image, a graph, a mathematical formula, or a set of clickable links:** An application can send an escape sequence containing almost any HTML. (The HTML is scrubbed to remove JavaScript and other dangerous features.)
-
-The image 3 shows a fragment from a [`gnuplot`][12] session. Gnuplot (2.1 or later) supports `domterm` as a terminal type. Graphical output is converted to an [SVG image][13], which is then printed to the terminal. My blog post [Gnuplot display on DomTerm][14] provides more information on this.
-
-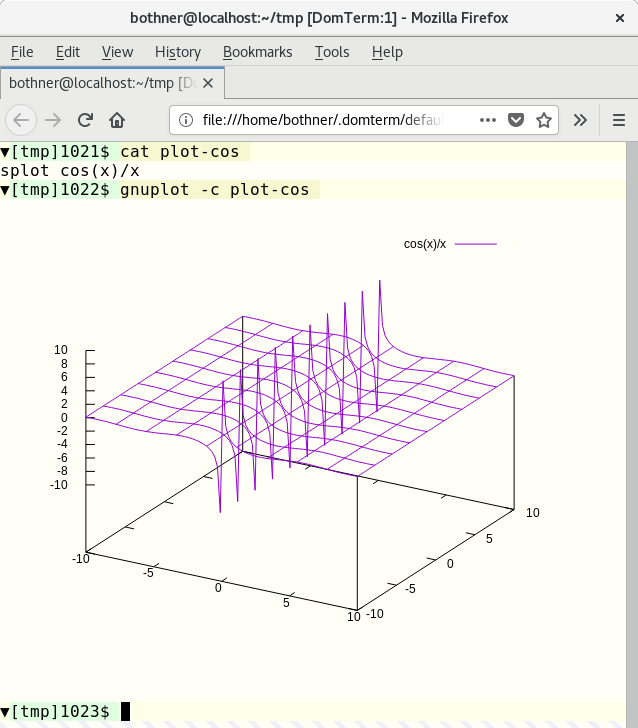
-Image 3: Gnuplot screenshot. View larger image.
-
-The [Kawa][15] language has a library for creating and transforming [geometric picture values][16]. If you print such a picture value to a DomTerm terminal, the picture is converted to SVG and embedded in the output.
-
-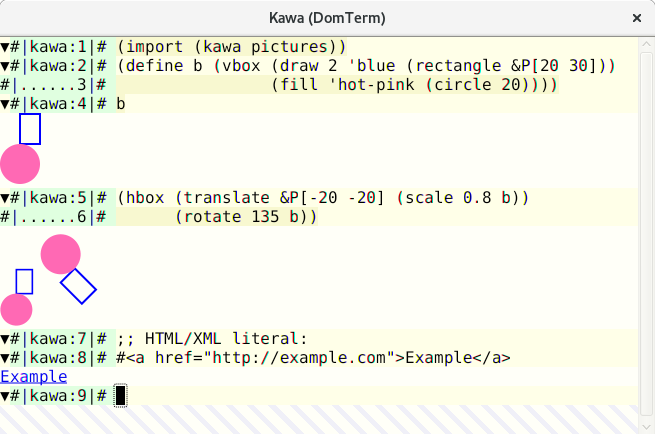
-Image 4: Computable geometry in Kawa. View larger image.
-
-**Rich text in output:** Help messages are more readable and look nicer with HTML styling. The lower pane of image 1 shows the ouput from `domterm help`. (The output is plaintext if not running under DomTerm.) Note the `PAUSED` message from the built-in pager.
-
-**Error messages can include clickable links:** DomTerm recognizes the syntax `filename:line:column:` and turns it into a link that opens the file and line in a configurable text editor. (This works for relative filenames if you use `PROMPT_COMMAND` or similar to track directories.)
-
-A compiler can detect that it is running under DomTerm and directly emit file links in an escape sequence. This is more robust than depending on DomTerm's pattern matching, as it handles spaces and other special characters, and it does not depend on directory tracking. In image 4, you can see error messages from the [Kawa compiler][15]. Hovering over the file position causes it to be underlined, and the `file:` URL shows in the `atom-domterm` message area (bottom of the window). (When not using `atom-domterm`, such messages are shown in an overlay box, as seen for the `PAUSED` message in image 1.)
-
-The action when clicking on a link is configurable. The default action for a `file:` link with a `#position` suffix is to open the file in a text editor.
-
-**Structured internal representation:** The following are all represented in the internal node structure: Commands, prompts, input lines, normal and error output, tabs, and preserving the structure if you "Save as HTML." The HTML file is compatible with XML, so you can use XML tools to search or transform the output. The command `domterm view-saved` opens a saved HTML file in a way that enables command folding (show/hide buttons are active) and reflow on window resize.
-
-**Built-in Lisp-style pretty-printing:** You can include pretty-printing directives (e.g., grouping) in the output such that line breaks are recalculated on window resize. See my article [Dynamic pretty-printing in DomTerm][17] for a deeper discussion.
-
-**Basic built-in line editing** with history (like `GNU readline`): This uses the browser's built-in editor, so it has great mouse and selection handling. You can switch between normal character-mode (most characters typed are sent directly to the process); or line-mode (regular characters are inserted while control characters cause editing actions, with Enter sending the edited line to the process). The default is automatic mode, where DomTerm switches between character-mode and line-mode depending on whether the PTY is in raw or canonical mode.
-
-**A built-in pager** (like a simplified `less`): Keyboard shortcuts will control scrolling. In "paging mode," the output pauses after each new screen (or single line, if you move forward line-by-line). The paging mode is unobtrusive and smart about user input, so you can (if you wish) run it without it interfering with interactive programs.
-
-### Multiplexing and sessions
-
-**Tabs and tiling:** Not only can you create multiple terminal tabs, you can also tile them. You can use either the mouse or a keyboard shortcut to move between panes and tabs as well as create new ones. They can be rearranged and resized with the mouse. This is implemented using the [GoldenLayout][18] JavaScript library. [Image 1][19] shows a window with two panes. The top one has two tabs, with one running [Midnight Commander][20]; the bottom pane shows `domterm help` output as HTML. However, on Atom we instead use its built-in draggable tiles and tabs; you can see this in image 2.
-
-**Detaching and reattaching to sessions:** DomTerm supports sessions arrangement, similar to `tmux` and GNU `screen`. You can even attach multiple windows or panes to the same session. This supports multi-user session sharing and remote connections. (For security, all sessions of the same server need to be able to read a Unix domain socket and a local file containing a random key. This restriction will be lifted when we have a good, safe remote-access story.)
-
-**The** **`domterm`** **command** is also like `tmux` or GNU `screen` in that has multiple options for controlling or starting a server that manages one or more sessions. The major difference is that, if it's not already running under DomTerm, the `domterm` command creates a new top-level window, rather than running in the existing terminal.
-
-The `domterm` command has a number of sub-commands, similar to `tmux` or `git`. Some sub-commands create windows or sessions. Others (such as "printing" an image) only work within an existing DomTerm session.
-
-The command `domterm browse` opens a window or pane for browsing a specified URL, such as when browsing documentation.
-
-### Getting and installing DomTerm
-
-DomTerm is available from its [GitHub repository][21]. Currently, there are no prebuilt packages, but there are [detailed instructions][22]. All prerequisites are available on Fedora 27, which makes it especially easy to build.
-
---------------------------------------------------------------------------------
-
-via: https://opensource.com/article/18/1/introduction-domterm-terminal-emulator
-
-作者:[Per Bothner][a]
-译者:[译者ID](https://github.com/译者ID)
-校对:[校对者ID](https://github.com/校对者ID)
-
-本文由 [LCTT](https://github.com/LCTT/TranslateProject) 原创编译,[Linux中国](https://linux.cn/) 荣誉推出
-
-[a]:https://opensource.com/users/perbothner
-[1]:http://domterm.org/
-[2]:https://electronjs.org/
-[3]:https://atom.io/
-[4]:https://en.wikipedia.org/wiki/XUL
-[5]:/file/385346
-[6]:https://opensource.com/sites/default/files/images/dt-atom1.png (DomTerm terminal panes in Atom editor)
-[7]:https://opensource.com/sites/default/files/images/dt-atom1.png
-[8]:https://libwebsockets.org/
-[9]:http://invisible-island.net/vttest/
-[10]:http://domterm.org/Wire-byte-protocol.html
-[11]:http://domterm.org/Shell-prompts.html
-[12]:http://www.gnuplot.info/
-[13]:https://developer.mozilla.org/en-US/docs/Web/SVG
-[14]:http://per.bothner.com/blog/2016/gnuplot-in-domterm/
-[15]:https://www.gnu.org/software/kawa/
-[16]:https://www.gnu.org/software/kawa/Composable-pictures.html
-[17]:http://per.bothner.com/blog/2017/dynamic-prettyprinting/
-[18]:https://golden-layout.com/
-[19]:https://opensource.com/sites/default/files/u128651/domterm1.png
-[20]:https://midnight-commander.org/
-[21]:https://github.com/PerBothner/DomTerm
-[22]:http://domterm.org/Downloading-and-building.html
diff --git a/sources/tech/20180312 ddgr - A Command Line Tool To Search DuckDuckGo From The Terminal.md b/sources/tech/20180312 ddgr - A Command Line Tool To Search DuckDuckGo From The Terminal.md
deleted file mode 100644
index 555a475651..0000000000
--- a/sources/tech/20180312 ddgr - A Command Line Tool To Search DuckDuckGo From The Terminal.md
+++ /dev/null
@@ -1,231 +0,0 @@
-ddgr – A Command Line Tool To Search DuckDuckGo From The Terminal
-======
-Bash tricks are really awesome in Linux that makes everything is possible in Linux.
-
-It really works well for developers or system admins because they are spending most of the time with terminal. Did you know why they are preferring this tricks?
-
-These trick will improve their productivity and also make them to work fast.
-
-### What Is ddgr
-
-[ddgr][1] is a command-line utility to search DuckDuckGo from the terminal. ddgr works out of the box with several text-based browsers if the BROWSER environment variable is set.
-
-Make sure your system should have installed any text-based browsers. You may know about [googler][2] that allow users to perform Google searches from the Linux command line.
-
-It’s highly popular among cmdline users and they are expect the similar utility for privacy-aware DuckDuckGo, that’s why ddgr came to picture.
-
-Unlike the web interface, you can specify the number of search results you would like to see per page.
-
-**Suggested Read :**
-**(#)** [Googler – Google Search From The Linux Command Line][2]
-**(#)** [Buku – A Powerful Command-line Bookmark Manager for Linux][3]
-**(#)** [SoCLI – Easy Way To Search And Browse Stack Overflow From The Terminal][4]
-**(#)** [RTV (Reddit Terminal Viewer) – A Simple Terminal Viewer For Reddit][5]
-
-### What Is DuckDuckGo
-
-DDG stands for DuckDuckGo. DuckDuckGo (DDG) is an Internet search engine that really protecting users search and privacy.
-
-They didn’t filter users personalized search results and It’s showing the same search results to all users for a given search term.
-
-Most of the users prefer google search engine, if you really worrying about privacy then you can blindly go with DuckDuckGo.
-
-### ddgr Features
-
- * Fast and clean (no ads, stray URLs or clutter), custom color
- * Designed to deliver maximum readability at minimum space
- * Specify the number of search results to show per page
- * Navigate result pages from omniprompt, open URLs in browser
- * Search and option completion scripts for Bash, Zsh and Fish
- * DuckDuckGo Bang support (along with completion)
- * Open the first result directly in browser (as in I’m Feeling Ducky)
- * Non-stop searches: fire new searches at omniprompt without exiting
- * Keywords (e.g. filetype:mime, site:somesite.com) support
- * Limit search by time, specify region, disable safe search
- * HTTPS proxy support, Do Not Track set, optionally disable User Agent
- * Support custom url handler script or cmdline utility
- * Comprehensive documentation, man page with handy usage examples
- * Minimal dependencies
-
-
-
-### Prerequisites
-
-ddgr requires Python 3.4 or later. So, make sure you system should have Python 3.4 or later version.
-```
-$ python3 --version
-Python 3.6.3
-
-```
-
-### How To Install ddgr In Linux
-
-We can easily install ddgr using the following command based on the distributions.
-
-For **`Fedora`** , use [DNF Command][6] to install ddgr.
-```
-# dnf install ddgr
-
-```
-
-Alternatively we can use [SNAP Command][7] to install ddgr.
-```
-# snap install ddgr
-
-```
-
-For **`LinuxMint/Ubuntu`** , use [APT-GET Command][8] or [APT Command][9] to install ddgr.
-```
-$ sudo add-apt-repository ppa:twodopeshaggy/jarun
-$ sudo apt-get update
-$ sudo apt-get install ddgr
-
-```
-
-For **`Arch Linux`** based systems, use [Yaourt Command][10] or [Packer Command][11] to install ddgr from AUR repository.
-```
-$ yaourt -S ddgr
-or
-$ packer -S ddgr
-
-```
-
-For **`Debian`** , use [DPKG Command][12] to install ddgr.
-```
-# wget https://github.com/jarun/ddgr/releases/download/v1.2/ddgr_1.2-1_debian9.amd64.deb
-# dpkg -i ddgr_1.2-1_debian9.amd64.deb
-
-```
-
-For **`CentOS 7`** , use [YUM Command][13] to install ddgr.
-```
-# yum install https://github.com/jarun/ddgr/releases/download/v1.2/ddgr-1.2-1.el7.3.centos.x86_64.rpm
-
-```
-
-For **`opensuse`** , use [zypper Command][14] to install ddgr.
-```
-# zypper install https://github.com/jarun/ddgr/releases/download/v1.2/ddgr-1.2-1.opensuse42.3.x86_64.rpm
-
-```
-
-### How To Launch ddgr
-
-Enter the `ddgr` command without any option on terminal to bring DuckDuckGo search. You will get the same output similar to below.
-```
-$ ddgr
-
-```
-
-![][16]
-
-### How To Search Using ddgr
-
-We can initiate the search through two ways. Either from omniprompt or directly from terminal. You can search any phrases which you want.
-
-Directly from terminal.
-```
-$ ddgr 2daygeek
-
-```
-
-![][17]
-
-From `omniprompt`.
-![][18]
-
-### Omniprompt Shortcut
-
-Enter `?` to obtain the `omniprompt`, which will show you list of keywords and shortcut to work further with ddgr.
-![][19]
-
-### How To Move Next,Previous, and Fist Page
-
-It allows user to move next page or previous page or first page.
-
- * `n:` Move to next set of search results
- * `p:` Move to previous set of search results
- * `f:` Jump to the first page
-
-
-
-![][20]
-
-### How To Initiate A New Search
-
-“ **d** ” option allow users to initiate a new search from omniprompt. For example, i searched about `2daygeek website` and now i’m going to initiate a new search with phrase “ **Magesh Maruthamuthu** “.
-
-From `omniprompt`.
-```
-ddgr (? for help) d magesh maruthmuthu
-
-```
-
-![][21]
-
-### Show Complete URLs In Search Result
-
-By default it shows only an article heading, add the “ **x** ” option in search to show complete article urls in search result.
-```
-$ ddgr -n 5 -x 2daygeek
-
-```
-
-![][22]
-
-### Limit Search Results
-
-By default search results shows 10 results per page. If you want to limit the page results for your convenience, you can do by passing `--num or -n` argument with ddgr.
-```
-$ ddgr -n 5 2daygeek
-
-```
-
-![][23]
-
-### Website Specific Search
-
-To search specific pages from the particular website, use the below format. This will fetch the results for given keywords from the website. For example, We are going search about “ **Package Manager** ” from 2daygeek website. See the results.
-```
-$ ddgr -n 5 --site 2daygeek "package manager"
-
-```
-
-![][24]
-
---------------------------------------------------------------------------------
-
-via: https://www.2daygeek.com/ddgr-duckduckgo-search-from-the-command-line-in-linux/
-
-作者:[Magesh Maruthamuthu][a]
-译者:[译者ID](https://github.com/译者ID)
-校对:[校对者ID](https://github.com/校对者ID)
-选题:[lujun9972](https://github.com/lujun9972)
-
-本文由 [LCTT](https://github.com/LCTT/TranslateProject) 原创编译,[Linux中国](https://linux.cn/) 荣誉推出
-
-[a]:https://www.2daygeek.com/author/magesh/
-[1]:https://github.com/jarun/ddgr
-[2]:https://www.2daygeek.com/googler-google-search-from-the-command-line-on-linux/
-[3]:https://www.2daygeek.com/buku-command-line-bookmark-manager-linux/
-[4]:https://www.2daygeek.com/socli-search-and-browse-stack-overflow-from-linux-terminal/
-[5]:https://www.2daygeek.com/rtv-reddit-terminal-viewer-a-simple-terminal-viewer-for-reddit/
-[6]:https://www.2daygeek.com/dnf-command-examples-manage-packages-fedora-system/
-[7]:https://www.2daygeek.com/snap-command-examples/
-[8]:https://www.2daygeek.com/apt-get-apt-cache-command-examples-manage-packages-debian-ubuntu-systems/
-[9]:https://www.2daygeek.com/apt-command-examples-manage-packages-debian-ubuntu-systems/
-[10]:https://www.2daygeek.com/install-yaourt-aur-helper-on-arch-linux/
-[11]:https://www.2daygeek.com/install-packer-aur-helper-on-arch-linux/
-[12]:https://www.2daygeek.com/dpkg-command-to-manage-packages-on-debian-ubuntu-linux-mint-systems/
-[13]:https://www.2daygeek.com/yum-command-examples-manage-packages-rhel-centos-systems/
-[14]:https://www.2daygeek.com/zypper-command-examples-manage-packages-opensuse-system/
-[15]:data:image/gif;base64,R0lGODlhAQABAIAAAAAAAP///yH5BAEAAAAALAAAAAABAAEAAAIBRAA7
-[16]:https://www.2daygeek.com/wp-content/uploads/2018/03/ddgr-duckduckgo-command-line-search-for-linux1.png
-[17]:https://www.2daygeek.com/wp-content/uploads/2018/03/ddgr-duckduckgo-command-line-search-for-linux-3.png
-[18]:https://www.2daygeek.com/wp-content/uploads/2018/03/ddgr-duckduckgo-command-line-search-for-linux-2.png
-[19]:https://www.2daygeek.com/wp-content/uploads/2018/03/ddgr-duckduckgo-command-line-search-for-linux-4.png
-[20]:https://www.2daygeek.com/wp-content/uploads/2018/03/ddgr-duckduckgo-command-line-search-for-linux-5a.png
-[21]:https://www.2daygeek.com/wp-content/uploads/2018/03/ddgr-duckduckgo-command-line-search-for-linux-6a.png
-[22]:https://www.2daygeek.com/wp-content/uploads/2018/03/ddgr-duckduckgo-command-line-search-for-linux-7a.png
-[23]:https://www.2daygeek.com/wp-content/uploads/2018/03/ddgr-duckduckgo-command-line-search-for-linux-8.png
-[24]:https://www.2daygeek.com/wp-content/uploads/2018/03/ddgr-duckduckgo-command-line-search-for-linux-9a.png
diff --git a/sources/tech/20180324 Memories of writing a parser for man pages.md b/sources/tech/20180324 Memories of writing a parser for man pages.md
deleted file mode 100644
index fb53aed395..0000000000
--- a/sources/tech/20180324 Memories of writing a parser for man pages.md
+++ /dev/null
@@ -1,109 +0,0 @@
-Memories of writing a parser for man pages
-======
-
-I generally enjoy being bored, but sometimes enough is enough—that was the case a Sunday afternoon of 2015 when I decided to start an open source project to overcome my boredom.
-
-In my quest for ideas, I stumbled upon a request to build a [“Man page viewer built with web standards”][1] by [Mathias Bynens][2] and without thinking too much, I started coding a man page parser in JavaScript, which after a lot of back and forths, ended up being [Jroff][3].
-
-Back then, I was familiar with manual pages as a concept and used them a fair amount of times, but that was all I knew, I had no idea how they were generated or if there was a standard in place. Two years later, here are some thoughts on the matter.
-
-### How man pages are written
-
-The first thing that surprised me at the time, was the notion that manpages at their core are just plain text files stored somewhere in the system (you can check this directory using the `manpath` command).
-
-This files not only contain the documentation, but also formatting information using a typesetting system from the 1970s called `troff`.
-
-> troff, and its GNU implementation groff, are programs that process a textual description of a document to produce typeset versions suitable for printing. **It’s more ‘What you describe is what you get’ rather than WYSIWYG.**
->
-> — extracted from [troff.org][4]
-
-If you are totally unfamiliar with typesetting formats, you can think of them as Markdown on steroids, but in exchange for the flexibility you have a more complex syntax:
-
-![groff-compressor][5]
-
-The `groff` file can be written manually, or generated from other formats such as Markdown, Latex, HTML, and so on with many different tools.
-
-Why `groff` and man pages are tied together has to do with history, the format has [mutated along time][6], and his lineage is composed of a chain of similarly-named programs: RUNOFF > roff > nroff > troff > groff.
-
-But this doesn’t necessarily mean that `groff` is strictly related to man pages, it’s a general-purpose format that has been used to [write books][7] and even for [phototypesetting][8].
-
-Moreover, It’s worth noting that `groff` can also call a postprocessor to convert its intermediate output to a final format, which is not necessarily ascii for terminal display! some of the supported formats are: TeX DVI, HTML, Canon, HP LaserJet4 compatible, PostScript, utf8 and many more.
-
-### Macros
-
-Other of the cool features of the format is its extensibility, you can write macros that enhance the basic functionalities.
-
-With the vast history of *nix systems, there are several macro packages that group useful macros together for specific functionalities according to the output that you want to generate, examples of macro packages are `man`, `mdoc`, `mom`, `ms`, `mm`, and the list goes on.
-
-Manual pages are conventionally written using `man` and `mdoc`.
-
-You can easily distinguish native `groff` commands from macros by the way standard `groff` packages capitalize their macro names. For `man`, each macro’s name is uppercased, like .PP, .TH, .SH, etc. For `mdoc`, only the first letter is uppercased: .Pp, .Dt, .Sh.
-
-![groff-example][9]
-
-### Challenges
-
-Whether you are considering to write your own `groff` parser, or just curious, these are some of the problems that I have found more challenging.
-
-#### Context-sensitive grammar
-
-Formally, `groff` has a context-free grammar, unfortunately, since macros describe opaque bodies of tokens, the set of macros in a package may not itself implement a context-free grammar.
-
-This kept me away (for good or bad) from the parser generators that were available at the time.
-
-#### Nested macros
-
-Most of the macros in `mdoc` are callable, this roughly means that macros can be used as arguments of other macros, for example, consider this:
-
- * The macro `Fl` (Flag) adds a dash to its argument, so `Fl s` produces `-s`
- * The macro `Ar` (Argument) provides facilities to define arguments
- * The `Op` (Optional) macro wraps its argument in brackets, as this is the standard idiom to define something as optional.
- * The following combination `.Op Fl s Ar file` produces `[-s file]` because `Op` macros can be nested.
-
-
-
-#### Lack of beginner-friendly resources
-
-Something that really confused me was the lack of a canonical, well defined and clear source to look at, there’s a lot of information in the web which assumes a lot about the reader that it takes time to grasp.
-
-### Interesting macros
-
-To wrap up, I will offer to you a very short list of macros that I found interesting while developing jroff:
-
-**man**
-
- * TH: when writing manual pages with `man` macros, your first line that is not a comment must be this macro, it accepts five parameters: title section date source manual
- * BI: bold alternating with italics (especially useful for function specifications)
- * BR: bold alternating with Roman (especially useful for referring to other manual pages)
-
-
-
-**mdoc**
-
- * .Dd, .Dt, .Os: similar to how `man` macros require the `.TH` the `mdoc` macros require these three macros, in that particular order. Their initials stand for: Document date, Document title and Operating system.
- * .Bl, .It, .El: these three macros are used to create list, their names are self-explanatory: Begin list, Item and End list.
-
-
-
-
---------------------------------------------------------------------------------
-
-via: https://monades.roperzh.com/memories-writing-parser-man-pages/
-
-作者:[Roberto Dip][a]
-译者:[译者ID](https://github.com/译者ID)
-校对:[校对者ID](https://github.com/校对者ID)
-选题:[lujun9972](https://github.com/lujun9972)
-
-本文由 [LCTT](https://github.com/LCTT/TranslateProject) 原创编译,[Linux中国](https://linux.cn/) 荣誉推出
-
-[a]:https://monades.roperzh.com
-[1]:https://github.com/h5bp/lazyweb-requests/issues/114
-[2]:https://mathiasbynens.be/
-[3]:jroff
-[4]:https://www.troff.org/
-[5]:https://user-images.githubusercontent.com/4419992/37868021-2e74027c-2f7f-11e8-894b-80829ce39435.gif
-[6]:https://manpages.bsd.lv/history.html
-[7]:https://rkrishnan.org/posts/2016-03-07-how-is-gopl-typeset.html
-[8]:https://en.wikipedia.org/wiki/Phototypesetting
-[9]:https://user-images.githubusercontent.com/4419992/37866838-e602ad78-2f6e-11e8-97a9-2a4494c766ae.jpg
diff --git a/sources/tech/20180416 How To Resize Active-Primary root Partition Using GParted Utility.md b/sources/tech/20180416 How To Resize Active-Primary root Partition Using GParted Utility.md
deleted file mode 100644
index f75baf6166..0000000000
--- a/sources/tech/20180416 How To Resize Active-Primary root Partition Using GParted Utility.md
+++ /dev/null
@@ -1,181 +0,0 @@
-How To Resize Active/Primary root Partition Using GParted Utility
-======
-Today we are going to discuss about disk partition. It’s one of the best topics in Linux. This allow users to resize the active root partition in Linux.
-
-In this article we will teach you how to resize the active root partition on Linux using Gparted utility.
-
-Just imagine, our system has 30GB disk and we didn’t configure properly while installation the Ubuntu operating system.
-
-We need to install another OS in that so we want to make secondary partition on that.
-
-Its not advisable to resize active partition. However, we are going to perform this as there is no way to free up the system.
-
-Make sure you should take backup of important data before performing this action because if something goes wrong (For example, if power got failure or your system got rebooted), you can retain your data.
-
-### What Is Gparted
-
-[GParted][1] is a free partition manager that enables you to resize, copy, and move partitions without data loss. We can use all of the features of the GParted application is by using the GParted Live bootable image. GParted Live enables you to use GParted on GNU/Linux as well as other operating systems, such as Windows or Mac OS X.
-
-### 1) Check Disk Space Usage Using df Command
-
-I just want to show you about my partition using df command. The df command output clearly showing that i only have one partition.
-```
-$ df -h
-Filesystem Size Used Avail Use% Mounted on
-/dev/sda1 30G 3.4G 26.2G 16% /
-none 4.0K 0 4.0K 0% /sys/fs/cgroup
-udev 487M 4.0K 487M 1% /dev
-tmpfs 100M 844K 99M 1% /run
-none 5.0M 0 5.0M 0% /run/lock
-none 498M 152K 497M 1% /run/shm
-none 100M 52K 100M 1% /run/user
-
-```
-
-### 2) Check Disk Partition Using fdisk Command
-
-I’m going to verify this using fdisk command.
-```
-$ sudo fdisk -l
-[sudo] password for daygeek:
-
-Disk /dev/sda: 33.1 GB, 33129218048 bytes
-255 heads, 63 sectors/track, 4027 cylinders, total 64705504 sectors
-Units = sectors of 1 * 512 = 512 bytes
-Sector size (logical/physical): 512 bytes / 512 bytes
-I/O size (minimum/optimal): 512 bytes / 512 bytes
-Disk identifier: 0x000473a3
-
- Device Boot Start End Blocks Id System
-/dev/sda1 * 2048 62609407 31303680 83 Linux
-/dev/sda2 62611454 64704511 1046529 5 Extended
-/dev/sda5 62611456 64704511 1046528 82 Linux swap / Solaris
-
-```
-
-### 3) Download GParted live ISO Image
-
-Use the below command to download GParted live ISO to perform this action.
-```
-$ wget https://downloads.sourceforge.net/gparted/gparted-live-0.31.0-1-amd64.iso
-
-```
-
-### 4) Boot Your System With GParted Live Installation Media
-
-Boot your system with GParted live installation media (like Burned CD/DVD or USB or ISO image). You will get the output similar to below screen. Here choose **GParted Live (Default settings)** and hit **Enter**.
-![][3]
-
-### 5) Keyboard Selection
-
-By default it chooses the second option, just hit **Enter**.
-![][4]
-
-### 6) Language Selection
-
-By default it chooses **33** for US English, just hit **Enter**.
-![][5]
-
-### 7) Mode Selection (GUI or Command-Line)
-
-By default it chooses **0** for GUI mode, just hit **Enter**.
-![][6]
-
-### 8) Loaded GParted Live Screen
-
-Now, GParted live screen is loaded. It is showing the list of partition which was created by me earlier.
-![][7]
-
-### 9) How To Resize The root Partition
-
-Choose the root partition you want to resize, only one partition is available here so i’m going to edit that partition to install another OS.
-![][8]
-
-To do so, press **Resize/Move** button to resize the partition.
-![][9]
-
-Here, enter the size which you want take out from this partition in first box. I’m going to claim **10GB** so, i added **10240MB** and leave rest of boxes as default, then hit **Resize/Move** button
-![][10]
-
-It will ask you once again to confirm to resize the partition because you are editing the live system partition, then hit **Ok**.
-![][11]
-
-It has been successfully shrink the partition from 30GB to 20GB. Also shows Unallocated disk space of 10GB.
-![][12]
-
-Finally click `Apply` button to perform remaining below operations.
-![][13]
-
- * **`e2fsck`** e2fsck is a file system check utility that automatically repair the file system for bad sectors, I/O errors related to HDD.
- * **`resize2fs`** The resize2fs program will resize ext2, ext3, or ext4 file systems. It can be used to enlarge or shrink an unmounted file system located on device.
- * **`e2image`** The e2image program will save critical ext2, ext3, or ext4 filesystem metadata located on device to a file specified by image-file.
-
-
-
-**`e2fsck`** e2fsck is a file system check utility that automatically repair the file system for bad sectors, I/O errors related to HDD.
-![][14]
-
-**`resize2fs`** The resize2fs program will resize ext2, ext3, or ext4 file systems. It can be used to enlarge or shrink an unmounted file system located on device.
-![][15]
-
-**`e2image`** The e2image program will save critical ext2, ext3, or ext4 filesystem metadata located on device to a file specified by image-file.
-![][16]
-
-All the operation got completed and close the dialog box.
-![][17]
-
-Now, i could able to see **10GB** of Unallocated disk partition.
-![][18]
-
-Reboot the system to check this.
-![][19]
-
-### 10) Check Free Space
-
-Login to the system back and use fdisk command to see the available space in the partition. Yes i could see **10GB** of Unallocated disk space on this partition.
-```
-$ sudo parted /dev/sda print free
-[sudo] password for daygeek:
-Model: ATA VBOX HARDDISK (scsi)
-Disk /dev/sda: 32.2GB
-Sector size (logical/physical): 512B/512B
-Partition Table: msdos
-Disk Flags:
-
-Number Start End Size Type File system Flags
- 32.3kB 10.7GB 10.7GB Free Space
- 1 10.7GB 32.2GB 21.5GB primary ext4 boot
-
-```
-
---------------------------------------------------------------------------------
-
-via: https://www.2daygeek.com/how-to-resize-active-primary-root-partition-in-linux-using-gparted-utility/
-
-作者:[Magesh Maruthamuthu][a]
-译者:[译者ID](https://github.com/译者ID)
-校对:[校对者ID](https://github.com/校对者ID)
-选题:[lujun9972](https://github.com/lujun9972)
-
-本文由 [LCTT](https://github.com/LCTT/TranslateProject) 原创编译,[Linux中国](https://linux.cn/) 荣誉推出
-
-[a]:https://www.2daygeek.com/author/magesh/
-[1]:https://gparted.org/
-[2]:data:image/gif;base64,R0lGODlhAQABAIAAAAAAAP///yH5BAEAAAAALAAAAAABAAEAAAIBRAA7
-[3]:https://www.2daygeek.com/wp-content/uploads/2014/08/how-to-resize-active-primary-root-partition-in-linux-using-gparted-utility-1.png
-[4]:https://www.2daygeek.com/wp-content/uploads/2014/08/how-to-resize-active-primary-root-partition-in-linux-using-gparted-utility-2.png
-[5]:https://www.2daygeek.com/wp-content/uploads/2014/08/how-to-resize-active-primary-root-partition-in-linux-using-gparted-utility-3.png
-[6]:https://www.2daygeek.com/wp-content/uploads/2014/08/how-to-resize-active-primary-root-partition-in-linux-using-gparted-utility-4.png
-[7]:https://www.2daygeek.com/wp-content/uploads/2014/08/how-to-resize-active-primary-root-partition-in-linux-using-gparted-utility-5.png
-[8]:https://www.2daygeek.com/wp-content/uploads/2014/08/how-to-resize-active-primary-root-partition-in-linux-using-gparted-utility-6.png
-[9]:https://www.2daygeek.com/wp-content/uploads/2014/08/how-to-resize-active-primary-root-partition-in-linux-using-gparted-utility-7.png
-[10]:https://www.2daygeek.com/wp-content/uploads/2014/08/how-to-resize-active-primary-root-partition-in-linux-using-gparted-utility-8.png
-[11]:https://www.2daygeek.com/wp-content/uploads/2014/08/how-to-resize-active-primary-root-partition-in-linux-using-gparted-utility-9.png
-[12]:https://www.2daygeek.com/wp-content/uploads/2014/08/how-to-resize-active-primary-root-partition-in-linux-using-gparted-utility-10.png
-[13]:https://www.2daygeek.com/wp-content/uploads/2014/08/how-to-resize-active-primary-root-partition-in-linux-using-gparted-utility-11.png
-[14]:https://www.2daygeek.com/wp-content/uploads/2014/08/how-to-resize-active-primary-root-partition-in-linux-using-gparted-utility-12.png
-[15]:https://www.2daygeek.com/wp-content/uploads/2014/08/how-to-resize-active-primary-root-partition-in-linux-using-gparted-utility-13.png
-[16]:https://www.2daygeek.com/wp-content/uploads/2014/08/how-to-resize-active-primary-root-partition-in-linux-using-gparted-utility-14.png
-[17]:https://www.2daygeek.com/wp-content/uploads/2014/08/how-to-resize-active-primary-root-partition-in-linux-using-gparted-utility-15.png
-[18]:https://www.2daygeek.com/wp-content/uploads/2014/08/how-to-resize-active-primary-root-partition-in-linux-using-gparted-utility-16.png
-[19]:https://www.2daygeek.com/wp-content/uploads/2014/08/how-to-resize-active-primary-root-partition-in-linux-using-gparted-utility-17.png
diff --git a/sources/tech/20180429 The Easiest PDO Tutorial (Basics).md b/sources/tech/20180429 The Easiest PDO Tutorial (Basics).md
deleted file mode 100644
index 9bda5fa335..0000000000
--- a/sources/tech/20180429 The Easiest PDO Tutorial (Basics).md
+++ /dev/null
@@ -1,170 +0,0 @@
-The Easiest PDO Tutorial (Basics)
-======
-
-
-
-Approximately 80% of the web is powered by PHP. And similarly, high number goes for SQL as well. Up until PHP version 5.5, we had the **mysql_** commands for accessing mysql databases but they were eventually deprecated due to insufficient security.
-
-This happened with PHP 5.5 in 2013 and as I write this article, the year is 2018 and we are on PHP 7.2. The deprecation of mysql**_** brought 2 major ways of accessing the database, the **mysqli** and the **PDO** libraries.
-
-Now though the mysqli library was the official successor, PDO gained more fame due to a simple reason that mysqli could only support mysql databases whereas PDO could support 12 different types of database drivers. Also, PDO had several more features that made it the better choice for most developers. You can see some of the feature comparisons in the table below;
-
-| | PDO | MySQLi |
-| Database support** | 12 drivers | Only MySQL |
-| Paradigm | OOP | Procedural + OOP |
-| Prepared Statements Client Side) | Yes | No |
-| Named Parameters | Yes | No |
-
-Now I guess it is pretty clear why PDO is the choice for most developers, so let’s dig into it and hopefully we will try to cover most of the PDO you need in this article itself.
-
-### Connection
-
-The first step is connecting to the database and since PDO is completely Object Oriented, we will be using the instance of a PDO class.
-
-The first thing we do is we define the host, database name, user, password and the database charset.
-
-`$host = 'localhost';`
-
-`$db = 'theitstuff';`
-
-`$user = 'root';`
-
-`$pass = 'root';`
-
-`$charset = 'utf8mb4';`
-
-`$dsn = "mysql:host=$host;dbname=$db;charset=$charset";`
-
-`$conn = new PDO($dsn, $user, $pass);`
-
-After that, as you can see in the code above we have created the **DSN** variable, the DSN variable is simply a variable that holds the information about the database. For some people running mysql on external servers, you could also adjust your port number by simply supplying a **port=$port_number**.
-
-Finally, you can create an instance of the PDO class, I have used the **$conn** variable and I have supplied the **$dsn, $user, $pass** parameters. If you have followed this, you should now have an object named $conn that is an instance of the PDO connection class. Now it’s time to get into the database and run some queries.
-
-### A simple SQL Query
-
-Let us now run a simple SQL query.
-
-`$tis = $conn->query('SELECT name, age FROM students');`
-
-`while ($row = $tis->fetch())`
-
-`{`
-
-`echo $row['name']."\t";`
-
-`echo $row['age'];`
-
-`echo "
";`
-
-`}`
-
-This is the simplest form of running a query with PDO. We first created a variable called **tis( **short for TheITStuff** )** and then you can see the syntax as we used the query function from the $conn object that we had created.
-
-We then ran a while loop and created a **$row** variable to fetch the contents from the **$tis** object and finally echoed out each row by calling out the column name.
-
-Easy wasn’t it ?. Now let’s get to the prepared statement.
-
-### Prepared Statements
-
-Prepared statements were one of the major reasons people started using PDO as it had prepared statements that could prevent SQL injections.
-
-There are 2 basic methods available, you could either use positional or named parameters.
-
-#### Position parameters
-
-Let us see an example of a query using positional parameters.
-
-`$tis = $conn->prepare("INSERT INTO STUDENTS(name, age) values(?, ?)");`
-
-`$tis->bindValue(1,'mike');`
-
-`$tis->bindValue(2,22);`
-
-`$tis->execute();`
-
-In the above example, we have placed 2 question marks and later used the **bindValue()** function to map the values into the query. The values are bound to the position of the question mark in the statement.
-
-I could also use variables instead of directly supplying values by using the **bindParam()** function and example for the same would be this.
-
-`$name='Rishabh'; $age=20;`
-
-`$tis = $conn->prepare("INSERT INTO STUDENTS(name, age) values(?, ?)");`
-
-`$tis->bindParam(1,$name);`
-
-`$tis->bindParam(2,$age);`
-
-`$tis->execute();`
-
-### Named Parameters
-
-Named parameters are also prepared statements that map values/variables to a named position in the query. Since there is no positional binding, it is very efficient in queries that use the same variable multiple time.
-
-`$name='Rishabh'; $age=20;`
-
-`$tis = $conn->prepare("INSERT INTO STUDENTS(name, age) values(:name, :age)");`
-
-`$tis->bindParam(':name', $name);`
-
-`$tis->bindParam(':age', $age);`
-
-`$tis->execute();`
-
-The only change you can notice is that I used **:name** and **:age** as placeholders and then mapped variables to them. The colon is used before the parameter and it is of extreme importance to let PDO know that the position is for a variable.
-
-You can similarly use **bindValue()** to directly map values using Named parameters as well.
-
-### Fetching the Data
-
-PDO is very rich when it comes to fetching data and it actually offers a number of formats in which you can get the data from your database.
-
-You can use the **PDO::FETCH_ASSOC** to fetch associative arrays, **PDO::FETCH_NUM** to fetch numeric arrays and **PDO::FETCH_OBJ** to fetch object arrays.
-
-`$tis = $conn->prepare("SELECT * FROM STUDENTS");`
-
-`$tis->execute();`
-
-`$result = $tis->fetchAll(PDO::FETCH_ASSOC);`
-
-You can see that I have used **fetchAll** since I wanted all matching records. If only one row is expected or desired, you can simply use **fetch.**
-
-Now that we have fetched the data it is time to loop through it and that is extremely easy.
-
-`foreach($result as $lnu){`
-
-`echo $lnu['name'];`
-
-`echo $lnu['age']."
";`
-
-`}`
-
-You can see that since I had requested associative arrays, I am accessing individual members by their names.
-
-Though there is absolutely no problem in defining how you want your data delivered, you could actually set one as default when defining the connection variable itself.
-
-All you need to do is create an options array where you put in all your default configs and simply pass the array in the connection variable.
-
-`$options = [`
-
-` PDO::ATTR_DEFAULT_FETCH_MODE => PDO::FETCH_ASSOC,`
-
-`];`
-
-`$conn = new PDO($dsn, $user, $pass, $options);`
-
-This was a very brief and quick intro to PDO we will be making an advanced tutorial soon. If you had any difficulties understanding any part of the tutorial, do let me know in the comment section and I’ll be there for you.
-
-
---------------------------------------------------------------------------------
-
-via: http://www.theitstuff.com/easiest-pdo-tutorial-basics
-
-作者:[Rishabh Kandari][a]
-选题:[lujun9972](https://github.com/lujun9972)
-译者:[译者ID](https://github.com/译者ID)
-校对:[校对者ID](https://github.com/校对者ID)
-
-本文由 [LCTT](https://github.com/LCTT/TranslateProject) 原创编译,[Linux中国](https://linux.cn/) 荣誉推出
-
-[a]:http://www.theitstuff.com/author/reevkandari
diff --git a/sources/tech/20180529 Manage your workstation with Ansible- Configure desktop settings.md b/sources/tech/20180529 Manage your workstation with Ansible- Configure desktop settings.md
index d04ee6d742..ed85b172af 100644
--- a/sources/tech/20180529 Manage your workstation with Ansible- Configure desktop settings.md
+++ b/sources/tech/20180529 Manage your workstation with Ansible- Configure desktop settings.md
@@ -1,3 +1,5 @@
+Translating by MjSeven
+
Manage your workstation with Ansible: Configure desktop settings
======
diff --git a/sources/tech/20180605 How to use autofs to mount NFS shares.md b/sources/tech/20180605 How to use autofs to mount NFS shares.md
deleted file mode 100644
index 69325a0670..0000000000
--- a/sources/tech/20180605 How to use autofs to mount NFS shares.md
+++ /dev/null
@@ -1,147 +0,0 @@
-[#]: collector: (lujun9972)
-[#]: translator: (geekpi)
-[#]: reviewer: ( )
-[#]: publisher: ( )
-[#]: url: ( )
-[#]: subject: (How to use autofs to mount NFS shares)
-[#]: via: (https://opensource.com/article/18/6/using-autofs-mount-nfs-shares)
-[#]: author: (Alan Formy-Duval https://opensource.com/users/alanfdoss)
-
-How to use autofs to mount NFS shares
-======
-
-
-
-Most Linux file systems are mounted at boot and remain mounted while the system is running. This is also true of any remote file systems that have been configured in the `fstab` file. However, there may be times when you prefer to have a remote file system mount only on demand—for example, to boost performance by reducing network bandwidth usage, or to hide or obfuscate certain directories for security reasons. The package [autofs][1] provides this feature. In this article, I'll describe how to get a basic automount configuration up and running.
-
-`tree.mydatacenter.net` is up and running. Also assume a data directory named `ourfiles` and two user directories, for Carl and Sarah, are being shared by this server.
-
-First, a few assumptions: Assume the NFS server namedis up and running. Also assume a data directory namedand two user directories, for Carl and Sarah, are being shared by this server.
-
-A few best practices will make things work a bit better: It is a good idea to use the same user ID for your users on the server and any client workstations where they have an account. Also, your workstations and server should have the same domain name. Checking the relevant configuration files should confirm.
-```
-alan@workstation1:~$ sudo getent passwd carl sarah
-
-[sudo] password for alan:
-
-carl:x:1020:1020:Carl,,,:/home/carl:/bin/bash
-
-sarah:x:1021:1021:Sarah,,,:/home/sarah:/bin/bash
-
-
-
-alan@workstation1:~$ sudo getent hosts
-
-127.0.0.1 localhost
-
-127.0.1.1 workstation1.mydatacenter.net workstation1
-
-10.10.1.5 tree.mydatacenter.net tree
-
-```
-
-As you can see, both the client workstation and the NFS server are configured in the `hosts` file. I’m assuming a basic home or even small office network that might lack proper internal domain name service (i.e., DNS).
-
-### Install the packages
-
-You need to install only two packages: `nfs-common` for NFS client functions, and `autofs` to provide the automount function.
-```
-alan@workstation1:~$ sudo apt-get install nfs-common autofs
-
-```
-
-You can verify that the autofs files have been placed in the `etc` directory:
-```
-alan@workstation1:~$ cd /etc; ll auto*
-
--rw-r--r-- 1 root root 12596 Nov 19 2015 autofs.conf
-
--rw-r--r-- 1 root root 857 Mar 10 2017 auto.master
-
--rw-r--r-- 1 root root 708 Jul 6 2017 auto.misc
-
--rwxr-xr-x 1 root root 1039 Nov 19 2015 auto.net*
-
--rwxr-xr-x 1 root root 2191 Nov 19 2015 auto.smb*
-
-alan@workstation1:/etc$
-
-```
-
-### Configure autofs
-
-Now you need to edit several of these files and add the file `auto.home`. First, add the following two lines to the file `auto.master`:
-```
-/mnt/tree /etc/auto.misc
-
-/home/tree /etc/auto.home
-
-```
-
-Each line begins with the directory where the NFS shares will be mounted. Go ahead and create those directories:
-```
-alan@workstation1:/etc$ sudo mkdir /mnt/tree /home/tree
-
-```
-
-Second, add the following line to the file `auto.misc`:
-```
-ourfiles -fstype=nfs tree:/share/ourfiles
-
-```
-
-This line instructs autofs to mount the `ourfiles` share at the location matched in the `auto.master` file for `auto.misc`. As shown above, these files will be available in the directory `/mnt/tree/ourfiles`.
-
-Third, create the file `auto.home` with the following line:
-```
-* -fstype=nfs tree:/home/&
-
-```
-
-This line instructs autofs to mount the users share at the location matched in the `auto.master` file for `auto.home`. In this case, Carl and Sarah's files will be available in the directories `/home/tree/carl` or `/home/tree/sarah`, respectively. The asterisk (referred to as a wildcard) makes it possible for each user's share to be automatically mounted when they log in. The ampersand also works as a wildcard representing the user's directory on the server side. Their home directory should be mapped accordingly in the `passwd` file. This doesn’t have to be done if you prefer a local home directory; instead, the user could use this as simple remote storage for specific files.
-
-Finally, restart the `autofs` daemon so it will recognize and load these configuration file changes.
-```
-alan@workstation1:/etc$ sudo service autofs restart
-
-```
-
-### Testing autofs
-
-If you change to one of the directories listed in the file `auto.master` and run the `ls` command, you won’t see anything immediately. For example, change directory `(cd)` to `/mnt/tree`. At first, the output of `ls` won’t show anything, but after running `cd ourfiles`, the `ourfiles` share directory will be automatically mounted. The `cd` command will also be executed and you will be placed into the newly mounted directory.
-```
-carl@workstation1:~$ cd /mnt/tree
-
-carl@workstation1:/mnt/tree$ ls
-
-carl@workstation1:/mnt/tree$ cd ourfiles
-
-carl@workstation1:/mnt/tree/ourfiles$
-
-```
-
-To further confirm that things are working, the `mount` command will display the details of the mounted share.
-```
-carl@workstation1:~$ mount
-
-tree:/mnt/share/ourfiles on /mnt/tree/ourfiles type nfs4 (rw,relatime,vers=4.0,rsize=131072,wsize=131072,namlen=255,hard,proto=tcp,timeo=600,retrans=2,sec=sys,clientaddr=10.10.1.22,local_lock=none,addr=10.10.1.5)
-
-```
-
-The `/home/tree` directory will work the same way for Carl and Sarah.
-
-I find it useful to bookmark these directories in my file manager for quicker access.
-
---------------------------------------------------------------------------------
-
-via: https://opensource.com/article/18/6/using-autofs-mount-nfs-shares
-
-作者:[Alan Formy-Duval][a]
-选题:[lujun9972](https://github.com/lujun9972)
-译者:[译者ID](https://github.com/译者ID)
-校对:[校对者ID](https://github.com/校对者ID)
-
-本文由 [LCTT](https://github.com/LCTT/TranslateProject) 原创编译,[Linux中国](https://linux.cn/) 荣誉推出
-
-[a]:https://opensource.com/users/alanfdoss
-[1]:https://wiki.archlinux.org/index.php/autofs
diff --git a/sources/tech/20180611 3 open source alternatives to Adobe Lightroom.md b/sources/tech/20180611 3 open source alternatives to Adobe Lightroom.md
deleted file mode 100644
index 664c054913..0000000000
--- a/sources/tech/20180611 3 open source alternatives to Adobe Lightroom.md
+++ /dev/null
@@ -1,84 +0,0 @@
-3 open source alternatives to Adobe Lightroom
-======
-
-
-
-You wouldn't be wrong to wonder whether the smartphone, that modern jack-of-all-trades, is taking over photography. While that might be valid in the point-and-shoot camera market, there are a sizeable number of photography professionals and hobbyists who recognize that a camera that fits in your pocket can never replace a high-end DSLR camera and the depth, clarity, and realism of its photos.
-
-All of that power comes with a small price in terms of convenience; like negatives from traditional film cameras, the [raw image][1] files produced by DSLRs must be processed before they can be edited or printed. For this, a digital image processing application is indispensable, and the go-to application has been Adobe Lightroom. But for many reasons—including its expensive, subscription-based pricing model and its proprietary license—there's a lot of interest in open source and other alternatives.
-
-Lightroom has two main functions: processing raw image files and digital asset management (DAM)—organizing images with tags, ratings, and other metadata to make it easier to keep track of them.
-
-In this article, we'll look at three open source image processing applications: Darktable, LightZone, and RawTherapee. All of them have DAM capabilities, but none has Lightroom's machine learning-based image categorization and tagging features. If you're looking for more information about open source DAM software, check out Terry Hancock's article "[Digital asset management for an open movie project][2]," where he shares his research on software to organize multimedia files for his [_Lunatics!_][3] open movie project.
-
-### Darktable
-
-![Darktable][4]
-
-Like the other applications on our list, [darktable][5] processes raw images into usable file formats—it exports into JPEG, PNG, TIFF, PPM, PFM, and EXR, and it also supports Google and Facebook web albums, Flickr uploads, email attachments, and web gallery creation.
-
-Its 61 image operation modules allow you to adjust contrast, tone, exposure, color, noise, etc.; add watermarks; crop and rotate; and much more. As with the other applications described in this article, those edits are "non-destructive"—that is, your original raw image is preserved no matter how many tweaks and modifications you make.
-
-Darktable imports raw images from more than 400 cameras plus JPEG, CR2, DNG, OpenEXR, and PFM; images are managed in a database so you can filter and search using metadata including tags, ratings, and color. It's also available in 21 languages and is supported on Linux, MacOS, BSD, Solaris 11/GNOME, and Windows. (The [Windows port][6] is new, and darktable warns it may have "rough edges or missing functionality" compared to other versions.)
-
-Darktable is licensed under [GPLv3][7]; you can learn more by perusing its [features][8], viewing the [user manual][9], or accessing its [source code][10] on GitHub.
-
-### LightZone
-
-![LightZone's tool stack][11]
-
-As a non-destructive raw image processing tool, [LightZone][12] is similar to the other two applications on this list: it's cross-platform, operating on Windows, MacOS, and Linux, and it supports JPG and TIFF images in addition to raw. But it's also unique in several ways.
-
-For one thing, it started out in 2005 as a proprietary image processing tool and later became an open source project under a BSD license. Also, before you can download the application, you must register for a free account; this is so the LightZone development community can track downloads and build the community. (Approval is quick and automated, so it's not a large barrier.)
-
-Another difference is that image modifications are done using stackable tools, rather than filters (like most image-editing applications); tool stacks can be rearranged or removed, as well as saved and copied to a batch of images. You can also edit certain parts of an image using a vector-based tool or by selecting pixels based on color or brightness.
-
-You can get more information on LightZone by searching its [forums][13] or accessing its [source code][14] on GitHub.
-
-### RawTherapee
-
-![RawTherapee][15]
-
-[RawTherapee][16] is another popular open source ([GPL][17]) raw image processor worth your attention. Like darktable and LightZone, it is cross-platform (Windows, MacOS, and Linux) and implements edits in a non-destructive fashion, so you maintain access to your original raw image file no matter what filters or changes you make.
-
-RawTherapee uses a panel-based interface, including a history panel to keep track of your changes and revert to a previous point; a snapshot panel that allows you to work with multiple versions of a photo; and scrollable tool panels to easily select a tool without worrying about accidentally using the wrong one. Its tools offer a wide variety of exposure, color, detail, transformation, and demosaicing features.
-
-The application imports raw files from most cameras and is localized to more than 25 languages, making it widely usable. Features like batch processing and [SSE][18] optimizations improve speed and CPU performance.
-
-RawTherapee offers many other [features][19]; check out its [documentation][20] and [source code][21] for details.
-
-Do you use another open source raw image processing tool in your photography? Do you have any related tips or suggestions for other photographers? If so, please share your recommendations in the comments.
-
---------------------------------------------------------------------------------
-
-via: https://opensource.com/alternatives/adobe-lightroom
-
-作者:[Opensource.com][a]
-选题:[lujun9972](https://github.com/lujun9972)
-译者:[译者ID](https://github.com/译者ID)
-校对:[校对者ID](https://github.com/校对者ID)
-
-本文由 [LCTT](https://github.com/LCTT/TranslateProject) 原创编译,[Linux中国](https://linux.cn/) 荣誉推出
-
-[a]:https://opensource.com
-[1]:https://en.wikipedia.org/wiki/Raw_image_format
-[2]:https://opensource.com/article/18/3/movie-open-source-software
-[3]:http://lunatics.tv/
-[4]:https://opensource.com/sites/default/files/styles/panopoly_image_original/public/uploads/raw-image-processors_darkroom1.jpg?itok=0fjk37tC (Darktable)
-[5]:http://www.darktable.org/
-[6]:https://www.darktable.org/about/faq/#faq-windows
-[7]:https://github.com/darktable-org/darktable/blob/master/LICENSE
-[8]:https://www.darktable.org/about/features/
-[9]:https://www.darktable.org/resources/
-[10]:https://github.com/darktable-org/darktable
-[11]:https://opensource.com/sites/default/files/styles/panopoly_image_original/public/uploads/raw-image-processors_lightzone1tookstack.jpg?itok=1e3s85CZ (LightZone's tool stack)
-[12]:http://www.lightzoneproject.org/
-[13]:http://www.lightzoneproject.org/Forum
-[14]:https://github.com/ktgw0316/LightZone
-[15]:https://opensource.com/sites/default/files/styles/panopoly_image_original/public/uploads/raw-image-processors_rawtherapee.jpg?itok=meiuLxPw (RawTherapee)
-[16]:http://rawtherapee.com/
-[17]:https://github.com/Beep6581/RawTherapee/blob/dev/LICENSE.txt
-[18]:https://en.wikipedia.org/wiki/Streaming_SIMD_Extensions
-[19]:http://rawpedia.rawtherapee.com/Features
-[20]:http://rawpedia.rawtherapee.com/Main_Page
-[21]:https://github.com/Beep6581/RawTherapee
diff --git a/sources/tech/20180629 100 Best Ubuntu Apps.md b/sources/tech/20180629 100 Best Ubuntu Apps.md
deleted file mode 100644
index 581d22b527..0000000000
--- a/sources/tech/20180629 100 Best Ubuntu Apps.md
+++ /dev/null
@@ -1,1184 +0,0 @@
-100 Best Ubuntu Apps
-======
-
-Earlier this year we have published the list of [20 Best Ubuntu Applications for 2018][1] which can be very useful to many users. Now we are almost in the second half of 2018, so today we are going to have a look at 100 best applications for Ubuntu which you will find very useful.
-
-![100 Best Ubuntu Apps][2]
-
-Many users who have recently switched to Ubuntu from Microsoft Windows or any other operating system face the dilemma of finding best alternative to application software they have been using for years on their previous OS. Ubuntu has thousands of free to use and open-source application software’s that perform way better than many paid software’s on Windows and other OS.
-
-Following list features many application software in various categories, so that you can find best application which best matched to your requirements.
-
-### **1\. Google Chrome Browser**
-
-Almost all the Linux distributions feature Mozilla Firefox web browser by default and it is a tough competitor to Google Chrome. But Chrome has its own advantages over Firefox like Chrome gives you direct access to your Google account from where you can sync bookmarks, browser history, extensions, etc. from Chrome browser on other operating systems and mobile phones.
-
-![Chrome][3]
-
-Google Chrome features up-to-date Flash player for Linux which is not the case with other web browsers on Linux including Mozilla Firefox and Opera web browser. If you continuously use Chrome on Windows then it is best choice to use it on Linux too.
-
-### 2\. **Steam**
-
-Gaming on Linux is a real deal now, which was a distant dream few years ago. In 2013, Valve announced Steam gaming client for Linux and everything has changed since then. Earlier users were hesitant to switch to Linux from Windows just because they would not be able to play their favourite games on Ubuntu but that is not the case now.
-
-![Steam][4]
-
-Some users might find installing Steam on Linux tricky but it worth all your efforts as thousands of Steam games are available for Linux. Some popular high-end games like Counter Strike: Global Offensive, Hitman, Dota 2 are available for Linux, you just need to make sure you have minimum hardware required to play these games.
-
-```
-$ sudo add-apt-repository multiverse
-
-$ sudo apt-get update
-
-$ sudo apt-get install steam
-```
-
-### **3\. WordPress Desktop Client**
-
-Yes you read it correct, WordPress has its dedicated desktop client for Ubuntu from where you can manage your WordPress sites. You can also write and design separately on desktop client without need for switching browser tabs.
-
-![][5]
-
-If you have websites backed by WordPress then this desktop client is must have application for you as you can also keep track of all the WordPress notifications in one single window. You can also check stats for performance of posts on website. Desktop client is available in Ubuntu Software Centre from where you can download and install it.
-
-### **4\. VLC Media Player**
-
-VLC is a very popular cross-platform and open-source media player which is also available for Ubuntu. What makes VLC a best media player is that it can play videos in all the Audio and Video formats available on planet without any issue.
-
-![][6]
-
-VLC has a slick user interface which is very easy to use and apart from that it offers lot of features such as online video streaming, audio and video customization, etc.
-
-```
-$ sudo add-apt-repository ppa:videolan/master-daily
-$ sudo apt update
-$ sudo apt-get install vlc qtwayland5
-```
-
-### **5\. Atom Text Editor**
-
-Having developed by Github, Atom is a free and open-source text editor which can also be used as Integrated Development Environment (IDE) for coding and editing in major programming languages. Atom developers claim it to be a completely hackable text editor for 21st Century.
-
-![][7]
-
-Atom Text Editor has one of the best user interfaces and it is a feature rich text editor with offerings like auto-completion, syntax highlighting and support of extensions and plug-ins.
-
-```
-$ sudo add-apt-repository ppa:webupd8team/atom
-$ sudo apt-get update
-$ sudo apt-get install atom
-```
-
-### **6\. GIMP Photo Editor**
-
-GIMP (GNU Image Manipulation Programme) is free and open-source photo editor for Ubuntu. It is arguably a best alternative to Adobe Photoshop on Windows. If you have been continuously using Adobe Photoshop and finding it difficult to get used to GIMP, then you can customize GIMP to look very similar to Photoshop.
-
-![][8]
-
-GIMP is a feature rich Photo editor and you can always use additional features by installing extensions and plug-ins anytime.
-
-```
-$ sudo apt-get install gimp
-```
-
-### **7\. Google Play Music Desktop Player**
-
-Google Play Music Desktop Player is an open-source music player which is replica of Google Play Music or you can say it’s better than that. Google always lacked a desktop music client but this third-party app fills the void perfectly.
-
-![][9]
-
-Like you can see in above screenshot, its interface is second to none in terms of look and feel. You just need to sign in into Google account and then it will import all your music and favorites into this desktop client. You can download installation files from its official [website][10] and install it using Software Center.
-
-### **8\. Franz**
-
-Franz is an instant messaging client that combines chat and messaging services into one application. It is one of the modern instant messaging platforms and it supports Facebook Messenger, WhatsApp, Telegram, HipChat, WeChat, Google Hangouts, Skype integration under one single application.
-
-![][11]
-
-Franz is complete messaging platform which you can use for business as well to manage mass customer service. To install Franz you need to download installation package from its [website][12] and open it using Software Center.
-
-### **9\. Synaptic Package Manager**
-
-Synaptic Package Manager is one of the must have tools on Ubuntu because it works for graphical interface for ‘apt-get’ command which we usually use to install apps on Ubuntu using Terminal. It gives tough competition to default app stores on various Linux distros.
-
-![][13]
-
-Synaptic comes with very simple user interface which is very fast and easy to use as compared to other app stores. On left-hand side you can browse various apps in different categories from where you can easily install and uninstall apps.
-
-```
-$ sudo apt-get install synaptic
-```
-
-### **10\. Skype**
-
-Skype is a very popular cross-platform video calling application which is now also available for Linux as a Snap app. Skype is an instant messaging application which offers features like voice and video calls, desktop screen sharing, etc.
-
-![][14]
-
-Skype has an excellent user interface which very similar to desktop client on Windows and it is very easy to use. It could be very useful app for many switchers from Windows.
-
-```
-$ sudo snap install skype
-```
-
-### **13\. VirtualBox**
-
-VirtualBox is a cross-platform virtualization software application developed by Oracle Corporation. If you love trying out new operating systems then VirtualBox is the must have Ubuntu application for you. You can tryout Linux, Mac inside Windows Operating System or Windows and Mac inside Linux.
-
-![][15]
-
-What VB actually does is it lets you run guest operating system on host operating system virtually. It creates virtual hard drive and installs guest OS on it. You can download and install VB directly from Ubuntu Software Center.
-
-### **12\. Unity Tweak Tool**
-
-Unity Tweak Tool (Gnome Tweak Tool) is must have tool for every Linux user because it gives user ability to customize desktop according to your need. You can try new GTK themes, set up desktop hot corners, customize icon set, tweak unity launcher, etc.
-
-![][16]
-
-Unity Tweak Tool can be very useful to user as it has everything covered right from the basic to advanced configurations.
-
-```
-$ sudo apt-get install unity-tweak-tool
-```
-
-### **13\. Ubuntu Cleaner**
-
-Ubuntu Cleaner is a system maintenance tool especially designed to remove packages that are no longer useful, remove unnecessary apps and clean-up browser caches. Ubuntu Cleaner has very simple user interface which is very easy to use.
-
-![][17]
-
-Ubuntu Cleaner is one of the best alternatives to BleachBit which is also a decent cleaning tool available for Linux distros.
-
-```
-$ sudo add-apt-repository ppa:gerardpuig/ppa
-$ sudo apt-get update
-$ sudo apt-get install ubuntu-cleaner
-```
-
-### 14\. Visual Studio Code
-
-Visual Studio Code is code editor which you will find very similar to Atom Text Editor and Sublime Text if you have already used them. Visual Studio Code proves to be very good educational tool as it explains everything from HTML tags to syntax in programming.
-
-![][18]
-
-Visual Studio comes with Git integration out of the box and it has excellent user interface which you will find very similar to likes of Atom Text Editor and Sublime Text. You can download and install it from Ubuntu Software Center.
-
-### **15\. Corebird**
-
-If you are looking for desktop client where you can use your Twitter then Corebird Twitter Client is the app you are looking for. It is arguably best Twitter client available for Linux distros and it offers features very similar to Twitter app on your mobile phone.
-
-![][19]
-
-Corebird Twitter Client also gives notifications whenever someone likes and retweets your tweet or messages you. You can also add multiple Twitter accounts on this client.
-
-```
-$ sudo snap install corebird
-```
-
-### **16\. Pixbuf**
-
-Pixbuf is a desktop client from Pixbuf photo community hub which lets you upload, share and sale your photos. It supports photo sharing to social media networks like Facebook, Pinterest, Instagram, Twitter, etc. and photography services including Flickr, 500px and Youpic.
-
-![][20]
-
-Pixbuf offers features like analytics which gives you stats about clicks, retweets, repins on your photo, scheduled posts, dedicated iOS extension. It also has mobile app, so that you can always be connected with your Pixbuf account from anywhere. Pixbuf is available for download in Ubuntu Software Center as a snap package.
-
-### **17\. Clementine Music Player**
-
-Clementine is a cross-platform music player and a good competitor to Rhythmbox which is default music player on Ubuntu. It is fast and easy to use music player thanks to its user friendly interface. It supports audio playback in all the major audio file formats.
-
-![][21]
-
-Apart from playing music from local library you can also listen to online radio from Spotify, SKY.fm, Soundcloud, etc. It also offers other features like smart and dynamic playlists, syncing music from cloud storages like Dropbox, Google Drive, etc.
-
-```
-$ sudo add-apt-repository ppa:me-davidsansome/clementine
-$ sudo apt-get update
-$ sudo apt-get install clementine
-```
-
-### **18\. Blender**
-
-Blender is free and open-source 3D creation application software which you can use to create 3D printed models, animated films, video games, etc. It comes with integrated game engine out of the box which you can use to develop and test video games.
-
-![blender][22]
-
-Blender has catchy user interface which is easy to use and it includes features like built-in render engine, digital sculpturing, simulation tool, animation tools and many more. It is one of the best applications you will ever find for Ubuntu considering it’s free and features it offers.
-
-### **19\. Audacity**
-
-Audacity is an open-source audio editing application which you can use to record, edit audio files. You can record audio from various inputs like microphone, electric guitar, etc. It also gives ability to edit and trim audio clips according to your need.
-
-![][23]
-
-Recently Audacity released with new features for Ubuntu which includes theme improvements, zoom toggle command, etc. Apart from these it offers features like various audio effects including noise reduction and many more.
-
-```
-$ sudo add-apt-repository ppa:ubuntuhandbook1/audacity
-$ sudo apt-get update
-$ sudo apt-get install audacity
-```
-
-### **20\. Vim**
-
-Vim is an Integrated Development Environment which you can use as standalone application or command line interface for programming in various major programming languages like Python.
-
-![][24]
-
-Most of the programmers prefer coding in Vim because it is fast and highly customizable IDE. Initially you might find it difficult to use but you will quickly get used to it.
-
-```
-$ sudo apt-get install vim
-```
-
-### **21\. Inkscape**
-
-Inkscape is an open-source and cross-platform vector graphics editor which you will find very much similar to Corel Draw and Adobe Illustrator. Using it you can create and edit vector graphics such as charts, logos, diagrams, illustrations, etc.
-
-![][25]
-
-Inkscape uses Scalable Vector Graphics (SVG) and an open XML-based W3C standard as a primary format. It supports various formats including JPEG, PNG, GIF, PDF, AI (Adobe Illustrator Format), VSD, etc.
-
-```
-$ sudo add-apt-repository ppa:inkscape.dev/stable
-$ sudo apt-get update
-$ sudo apt-get install inkscape
-```
-
-### **22\. Shotcut**
-
-Shotcut is a free, open-source and cross-platform video editing application developed by Meltytech, LLC on the MLT Multimedia Framework. It is one of the most powerful video editors you will ever find for Linux distros as it supports all the major audio, video and image formats.
-
-![][26]
-
-It gives ability to edit multiple tracks with various file formats using non-linear video editing. It also comes with support for 4K video resolutions and features like various audio and video filters, tone generator, audio mixing and many others.
-
-```
-snap install shotcut -- classic
-```
-
-### **23\. SimpleScreenRecorder**
-
-SimpleScreenRecorder is a free and lightweight screen video recorder for Ubuntu. This screen recorder can be very useful tool for you if you are a YouTube creator or application developer.
-
-![][27]
-
-It can capture a video/audio record of desktop screen or record video games directly. You can set video resolution, frame rate, etc. before starting the screen recording. It has simple user interface which you will find very easy to use.
-
-```
-$ sudo add-apt-repository ppa:marten-baert/simplescreenrecorder
-$ sudo apt-get update
-$ sudo apt-get install simplescreenrecorder
-```
-
-### **24\. Telegram**
-
-Telegram is a cloud-based instant messaging and VoIP platform which has got lot of popularity in recent years. It is an open-source and cross-platform messenger where user can send messages, share videos, photos, audio and other files.
-
-![][28]
-
-Some of the notable features in Telegram are secrete chats, voice messages, bots, telescope for video messages, live locations and social login. Privacy and security is at highest priority in Telegram, so all messages you send and receive are end-to-end encrypted.
-
-```
-```
-$ sudo snap install telegram-desktop
-
-### **25\. ClamTk**
-
-As we know viruses meant to harm Windows PC cannot do any harm to Ubuntu but it is always prone to get infected by some mails from Windows PC containing harmful files. So it is safe to have some antivirus applications on Linux too.
-
-![][29]
-
-ClamTk is a lightweight malware scanner which scans files and folders on your system and cleans if any harmful files are found. ClamTk is available as a Snap package and can be downloaded from Ubuntu Software Center.
-
-### **26\. MailSpring**
-
-MailSpring earlier known as Nylas Mail or Nylas N1 is an open-source email client. It saves all the mails locally on computer so that you can access them anytime you need. It features advanced search which uses AND and OR operations so that you can search for mails based on different parameters.
-
-![][30]
-
-MailSpring comes with excellent user interface which you will find only on handful of other mail clients. Privacy and security, scheduler, contact manager, calendar are some of the features MailSpring offers.
-
-### **27\. PyCharm**
-
-PyCharm is one of my favorite Python IDEs after Vim because it has slick user interface with lot of extensions and plug-in support. Basically it comes in two editions, one is community edition which is free and open-source and other is professional edition which is paid one.
-
-![][31]
-
-PyCharm is highly customizable IDE and sports features such as error highlighting, code analysis, integrated unit testing and Python debugger, etc. PyCharm is the preferred IDE by most of the Python programmers and developers.
-
-### **28\. Caffeine**
-
-Imagine you are watching something on YouTube or reading a news article and suddenly Ubuntu locks your screen, I know that is very annoying. It happens with many of us, so Caffeine is the tool that will help you block the Ubuntu lock screen or screensaver.
-
-![][32]
-
-Caffeine Inhibitor is lightweight tool, it adds icon on notification bar from where you can activate or deactivate it easily. No additional setting needs to be done in order to use this tool.
-
-```
-$ sudo add-apt-repository ppa:eugenesan/ppa
-$ sudo apt-get update
-$ sudo apt-get install caffeine -y
-```
-
-### **29\. Etcher USB Image Writer**
-
-Etcher is an open-source USB Image Writer developed by resin.io. It is a cross-platform application which helps you burn image files like ZIP, ISO, IMG to USB storage. If you always try out new OS then Etcher is the must have tool for you as it is easy to use and reliable.
-
-![][33]
-
-Etcher has clean user interface that guides you through process of burning image file to USB drive or SD card in three easy steps. Steps involve selecting Image file, selecting USB drive and finally flash (writes files to USB drive). You can download and install Etcher from its [website][34].
-
-### **30\. Neofetch**
-
-Neofetch is a cool system information tool that gives you all the information about your system by running “neofetch” command in Terminal. It is cool tool to have because it gives you information about desktop environment, kernel version, bash version and GTK theme you are running.
-
-![][35]
-
-As compared to other system information tools Nefetch is highly customizable tool. You can perform various customizations using command line.
-
-```
-$ sudo add-apt-repository ppa:dawidd0811/neofetch
-$ sudo apt-get update
-$ sudo apt-get update install neofetch
-```
-
-### 31\. Liferea
-
-Liferea (Linux Feed Reader) is a free and open-source news aggregator for online news feeds. It is a fast and easy to use new aggregator that supports various formats such as RSS/RDF, Atom, etc.
-
-![][36]
-Liferea comes with sync support with TinyTinyRSS out of the box and it gives you an ability to read feeds in offline mode. It is one of the best feed readers you will find for Linux in terms of reliability and flexibility.
-
-```
-$ sudo add-apt-repository ppa:ubuntuhandbook1/apps
-$ sudo apt-get update
-$ sudo apt-get install liferea
-```
-
-### 32\. Shutter
-
-It is easy to take screenshots in Ubuntu but when it comes to edit screenshots Shutter is the must have application for you. It helps you capture, edit and share screenshots easily. Using Shutter’s selector tool you can select particular part of your screen to take screenshot.
-
-![][37]
-
-Shutter is a feature-rich screenshot tool which offers features like adding effects to screenshot, draw lines, etc. It also gives you option to upload your screenshot to various image hosting sites. You can directly download and install Shutter from Software Center.
-
-### 33\. Weather
-
-Weather is a small application which gives you real-time weather information for your city or any other location in the world. It is simple and lightweight tool which gives you detailed forecast of up to 7 days and hourly details for current and next day.
-
-![][38]
-
-It integrates with GNOME shell to give you information about current weather conditions at recently searched locations. It has minimalist user interface which works smoothly on minimum hardware requirement.
-
-### 34\. Ramme
-
-Ramme is cool unofficial Instagram desktop client which gives you feel of Instagram mobile phone app. It is an Electron-based client so it replicates Instagram app and offers features like theme customization, etc.
-
-![][39]
-
-But due to Instagram’s API restrictions you can’t upload image using Ramme client but you can always go through Instagram feed, like and comment on posts, message friends. You can download Ramme installation files from[Github.][40]
-
-### **35\. Thunderbird**
-
-Thunderbird is an open-source email client which is also a default email client in most of the Linux distributions. Despite parting ways with Mozilla in 2017, Thunderbird is still very popular and best email client on Linux platform. It comes with features like spam filtering, IMAP and POP email syncing, calendar support, address book integration and many other features out of the box.
-
-![][41]
-
-It is a cross-platform email client with full community support across all supported platforms. You can always change its look and feel thanks to its highly customizable nature.
-
-### **36\. Pidgin**
-
-Pidgin is an instant messaging client where you can login into different instant messaging networks under single window. You can login to instant messaging networks like Google Talk, XMPP, AIM, Bonjour, etc.
-
-![][42]
-
-Pidgin has all the features you can expect in an instant messenger and you can always enhance its performance by installing additional plug-ins.
-
-```
-```
-$ sudo apt-get install pidgin
-
-### **37\. Krita**
-
-Krita is a free and open-source digital painting, editing and animation application developed by KDE. It has excellent user interface with everything placed perfectly so that you can easily find the tool you need.
-
-![][43]
-
-It uses OpenGL canvas which boosts Krita’s performance and it offers many features like different painting tools, animation tools, vector tools, layers and masks and many more. Krita is available in Ubuntu Software Center, you can easily download it from there.
-
-### **38\. Dropbox**
-
-Dropbox is stand-out player in cloud storage and its Linux clients works really well on Ubuntu once installed properly. While Google Drive comes out of the box on Ubuntu 16.04 LTS and later, Dropbox is still a preferred cloud storage tool on Linux in terms of features it offers.
-
-![][44]
-It always works in background and back up new files from your system to cloud storage, syncs files continuously between your computer and its cloud storage.
-
-```
-$ sudo apt-get install nautilus-dropbox
-```
-
-### 39\. Kodi
-
-Kodi formerly known as Xbox Media Center (XBMC) is an open-source media player. You can play music, videos, podcasts and video games both in online and offline mode. This software was first developed for first generation of Xbox gaming console and then slowly ported to personal computers.
-
-![][45]
-
-Kodi has very impressive video interface which is fast and powerful. It is highly customizable media player and by installing additional plug-ins you can access online streaming services like Pandora, Spotify, Amazon Prime Video, Netflix and YouTube.
-
-### **40\. Spotify**
-
-Spotify is one of the best online media streaming sites. It provides music, podcast and video streaming services both on free and paid subscription basis. Earlier Spotify was not supported on Linux but now it has its own fully functional desktop client for Ubuntu.
-
-![][46]
-
-Alongside Google Play Music Desktop Player, Spotify is must have media player for you. You just need to login to your Spotify account to access your favorite online content from anywhere.
-
-### 41\. Brackets
-
-Brackets is an open-source text editor developed by Adobe. It can be used for web development and design in web technologies such as HTML, CSS and JavaScript. It sports live preview mode which is great feature to have as it can get real-time view of whatever the changes you make in script.
-
-![][47]
-
-It is one of the modern text editors on Ubuntu and has slick user interface which takes web development task to new level. It also offers features like inline editor and supports for popular extensions like Emmet, Beautify, Git, File Icons, etc.
-
-### 42\. Bitwarden
-
-Account safety is serious concern now as we can see rise in security breaches in which users passwords are stolen and important data being compromised. So Bitwarden is recommended tool for you which stores all your account logins and passwords safe and secure at one place.
-
-![][48]
-
-Bitwarden uses AES-256 bit encryption technique to store all the login details and only user has access to his data. It also helps you to create strong passwords which are less likely to be hacked.
-
-### 43\. Terminator
-
-Terminator is an open-source terminal emulator programmed and developed in Java. It is a cross-platform emulator which lets you have privilege of multiple terminals in one single window which is not the case in Linux default terminal emulator.
-
-![][49]
-
-Other stand-out feature in Terminator includes automatic logging, drag and drop, intelligent vertical and horizontal scrolling, etc.
-
-```
-$ sudo apt-get install terminator
-```
-
-### 44\. Yak Yak
-
-Yak Yak is an open-source unofficial desktop client for Google Hangouts messenger. It could be good alternative to Microsoft’s Skype as it comes with bunch of some amazing features out of the box. You can enable desktop notifications, language preferences, and works on minimal memory and power requirements.
-
-![][50]
-
-Yak Yak comes with all the features you would expect in any instant messaging app such as typing indicator, drag and drop media files, and audio/video calling.
-
-### 45\. **Thonny**
-
-Thonny is a simple and lightweight IDE especially designed for beginners in programming. If you are new to programming then this is the must have IDE for you because it lets you learn while programming in Python.
-
-![][51]
-
-Thonny is also great tool for debugging as it supports live variables during debugging, apart from this it offers features like separate windows for executing function call, simple user interface, etc.
-
-```
-$ sudo apt-get install thonny
-```
-
-### **46\. Font Manager**
-
-Font Manager is a lightweight tool for managing, adding or removing fonts on your Ubuntu system. It is specially built for Gnome desktop environment, users don’t having idea about managing fonts using command line will find this tool very useful.
-
-![][52]
-
-Gtk+ Font Manager is not meant to be for professional users, it has simple user interface which you will find very easy to navigate. You just need to download font files from internet and add them using Font Manager.
-
-$ sudo add-apt-repository ppa:font-manager/staging
-$ sudo apt-get update
-$ sudo apt-get install font-manager
-
-### **47\. Atril Document Viewer**
-
-Atril is a simple document viewer which supports file formats like Portable Document Format (PDF), PostScript (PS), Encapsulated PostScript (EPS), DJVU and DVI. Atril comes bundled with MATE desktop environment and it is identical to Evince which is default document on the most of the Linux distros.
-
-![][53]
-
-Atril has simple and lightweight user interface which is highly customizable and offers features like search, bookmarks and UI includes thumbnails on the left-hand side.
-
-```
-$ sudo apt-get install atril
-```
-
-### **48\. Notepadqq**
-
-If you have ever used Notepad++ on Windows and looking for similar program on Linux then don’t worry developers have ported it to Linux as Notepadqq. It is a simple yet powerful text editor which you can use for daily tasks or programming in various languages.
-
-![][54]
-
-Despite being a simple text editor it has some amazing features like you can set theme between dark and light color scheme, multiple selection, regular expression search and real-time highlighting.
-
-```
-$ sudo add-apt-repository ppa:notpadqq-team/notepadqq
-$ sudo apt-get update
-$ sudo apt-get install notepadqq
-```
-
-### **49\. Amarok**
-
-Amarok is an open-source music player developed under KDE projetct. It has an intuitive interface which makes you feel home so you can discover your favorite music easily. Besides Clementine, Amarok is very good choice to have when you are looking for perfect music player for Ubuntu.
-
-![][55]
-
-Some of the top features in Amarok include intelligent playlist support, integration support for online services like MP3tunes, Last.fm, Magnatune, etc.
-
-### **50\. Cheese**
-
-Cheese is a Linux default webcam application which can be useful to you in some video chat or instant messaging applications. Apart from that you can also use this app to take photos and videos with fancy effects.
-
-![][56]
-
-It also sports burst mode which lets you take multiple snaps in quick succession and option to share your photos with friends and family. Cheese come pre-installed with most of the Linux distros but you can also download and install it from Software Center.
-
-### **51\. MyPaint**
-
-MyPaint is a free and open-source raster graphics editor which focuses on digital painting rather than image manipulation and post processing. It is cross-platform application and more or less similar to Corel Painter.
-
-![][57]
-
-MyPaint could be good alternative to those who use Microsoft Paint application on Windows. It has simple user interface which is fast and powerful. MyPaint is available is Software Center for download.
-
-### **52\. PlayOnLinux**
-
-PlayOnLinux is a front-end for WINE emulator which allows you to run Windows applications on Linux. You just need to install Windows applications and game on WINE then you can easily launch applications and games using PlayOnLinux.
-
-![][58]
-
-### **53\. Akregator**
-
-Akregator is a default RSS reader for KDE Plasma Environment developed under KDE project. It has simple user interface and comes with KDE’s Konqueror browser so that you don’t need to switch between apps while reading news feeds.
-
-![][59]
-
-Akregator also offers features like desktop notifications, automatic feeds, etc. It is one of the best feed readers you will find for across most of the Linux distros.
-
-### **54\. Brave**
-
-Brave is an open-source web browser which blocks ads and trackers so that you can browse your content fast and safely. What it actually does is that it pays to websites and YouTubers on behalf of you. If you prefer contributing to websites and YouTubers rather than seeing advertisements then this browser is for you.
-
-![][60]
-
-This is a new concept and could be good browser for those who prefer safe browsing without compromising important data on internet.
-
-### **55\. Bitcoin Core**
-
-Bitcoin Core is an official Bitcoin client which is highly secure and reliable. It keeps track of all your transactions and makes sure all transactions are valid. It restricts Bitcoin miners and banks from taking full control of your Bitcoin wallet.
-
-![][61]
-
-Bitcoin Core also offers other important features like, private keys backup, cold storage, security notifications.
-
-```
-$ sudo add-apt-repository ppa:bitcoin/bitcoin
-$ sudo apt-get update
-$ sudo apt-get install bitcoin-qt
-```
-
-### **56\. Speedy Duplicate Finder**
-
-Speedy Duplicate Finder is a cross-platform file finder which helps you find duplicate files on your system and free-up disk space. It is a smart tool which searches for duplicate files on entire hard disk and also features smart filter which helps you find file by file type, extension or size.
-
-![][62]
-
-It has a simple and clean user interface which is very easy to handle. As soon as you download it from Software Center you are good to go with disk space clean-up.
-
-### **57\. Zulip**
-
-Zulip is a free and open-source group chat application which was acquired by Dropbox. It is written in Python and uses PostgreSQL database. It was designed and developed to be a good alternative to other chat applications like Slack and HipChat.
-
-![][63]
-
-Zulip is a feature-rich application with features such as drag and drop files, group chats, private messaging, image previews and many more. It also supports integration with likes of Github, JIRA, Sentry, and hundreds of other services.
-
-### **58\. Okular**
-
-Okular is a cross-platform document viewer developed by KDE for KDE desktop environment. It is a simple document viewer and supports file formats like Portable Document Format (PDF), PostScript, DjVu, Microsoft Compiled HTML help, and many other major file formats.
-
-![][64]
-
-Okular is one of the best document viewers you should try on Ubuntu as it offers features like commenting on PDF documents, drawing lines, highlighting and much more. You can also extract text from PDF document to text file.
-
-### **59\. FocusWriter**
-
-FocusWriter is a distraction-free word processor which hides your desktop screen so that you can only focus on writing. Like you can see in the screenshot below whole Ubuntu screen is hidden, it’s just you and your word processor. But you can always access Ubuntu screen whenever you need it by just moving your mouse cursor to the edges of the screen.
-
-![][65]
-
-It is a lightweight word processor with support for file formats like TXT, RTF and ODT files. It also offers fully customizable user interface and features like timers and alarms, daily goals, sound effects and support for translation into 20 languages.
-
-### **60\. Guake**
-
-Guake is a cool drop-down terminal for GNOME Desktop Environment. Guake comes in a flash whenever you need it and disappears as soon as your task is completed. You just need to click F12 button to launch or exit it so launching Guake is way faster than launching new Terminal window.
-
-![][66]
-
-Guake is a feature-rich terminal with features like support for multiple tabs, ability to save your terminal content to file in few clicks, and fully customizable user interface.
-
-```
-$ sudo apt-get install guake
-```
-
-### **61\. KDE Connect**
-
-KDE Connect is an awesome application on Ubuntu and I would have loved to list this application much higher in this marathon article but competition is intense. Anyways KDE Connect helps you get your Android smartphone notifications directly on Ubuntu desktop.
-
-![][67]
-
-With KDE Connect you can do whole lot of other things like check your phones battery level, exchange files between computer and Android phone, clipboard sync, send SMS, and you can also use your phone as wireless mouse or keyboard.
-
-```
-$ sudo add-apt-repository ppa:webupd8team/indicator-kedeconnect
-$ sudo apt-get update
-$ sudo apt-get install kdeconnect indicator-kdeconnect
-```
-
-### **62\. CopyQ**
-
-CopyQ is a simple but very useful clipboard manager which stores content of the system clipboard whenever any changes you make so that you can search and restore it back whenever you need. It is a great tool to have as it supports text, images, HTML and other formats.
-
-![][68]
-
-CopyQ comes pre-loaded with features like drag and drop, copy/paste, edit, remove, sort, create, etc. It also supports integration with text editors like Vim, so it could be very useful tool if you are a programmer.
-
-```
-$ sudo add-apt-repository ppa:hluk/copyq
-$ sudo apt-get update
-$ sudo apt-get install copyq
-```
-
-### **63\. Tilix**
-
-Tilix is feature-rich advanced GTK3 tiling terminal emulator. If you uses GNOME desktop environment then you’re going to love Tilix as it follows GNOME Human Interface Guidelines. What Tilix emulator offers different than default terminal emulators on most of the Linux distros is it gives you ability to split terminal window into multiple terminal panes.
-
-![][69]
-
-Tilix offers features like custom links, image support, multiple panes, drag and drop, persistent layout and many more. It also has support for keyboard shortcuts and you can customize shortcuts from the Preferences settings according to your need.
-
-```
-$ sudo add-apt-repository ppa:webupd8team/terminix
-$ sudo apt-get update
-$ sudo apt-get install tilix
-```
-
-### **64\. Anbox**
-
-Anbox is an Android emulator which lets you install and run Android apps on your Linux system. It is free and open-source Android emulator that executes Android runtime environment by using Linux Containers. It uses latest Linux technologies and Android releases so that you can run any Android app like any other native application.
-
-![][70]
-
-Anbox is one of the modern and feature-rich emulators and offers features like no limit for application use, powerful user interface, and seamless integration with host operating system.
-
-First you need to install kernel modules.
-
-```
-$ sudo add-apt-repository ppa:morphis/anbox-support
-$ sudo apt-get update
-$ sudo apt install anbox-modules-dkms Now install Anbox using snap
-$ snap install --devmode -- beta anbox
-```
-
-### **65\. OpenShot**
-
-OpenShot is the best open-source video editor you will find for Linux distros. It is a cross-platform video editor which is very easy to use without any compromise with its performance. It supports all the major audio, video and image formats.
-
-![][71]
-
-OpenShot has clean user interface and offers features like drag and drop, clip resizing, scaling, trimming, snapping, real-time previews, audio mixing and editing and many other features.
-
-```
-$ sudo add-apt-repository ppa:openshot.developers/ppa
-$ sudo apt-get update
-$ sudo apt-get install openshot -qt
-```
-
-### **66\. Plank**
-
-If you are looking for cool and simple dock for your Ubuntu desktop then Plank should be #1 choice for you. It is perfect dock and you don’t need to make any tweaks after installation but if you want to, then it has built-in preferences panel where you can customize themes, dock size and position.
-
-![][72]
-
-Despite being a simple dock, Plank offers features like item rearrangement by simple drag and drop, pinned and running apps icon, transparent theme support.
-
-```
-$ sudo add-apt-repository ppa:ricotz/docky
-$ sudo apt-get update
-$ sudo apt-get install plank
-```
-
-### **67\. Filezilla**
-
-Filezilla is a free and cross-platform FTP application which sports FileZilla client and server. It lets you transfer files using FTP and encrypted FTP like FTPS and SFTP and supports IPv6 internet protocol.
-
-![][73]
-
-It is simple file transfer application with features like drag and drop, support for various languages used worldwide, powerful user interface for multitasking, control and configures transfer speed and many other features.
-
-### **68\. Stacer**
-
-Stacer is an open-source system diagnostic tool and optimizer developed using Electron development framework. It has an excellent user interface and you can clean cache memory, start-up applications, uninstall apps that are no longer needed, monitor background system processes.
-
-![][74]
-
-It also lets you check disk, memory and CPU usage and also gives real-time stats of downloads and uploads. It looks like a tough competitor to Ubuntu cleaner but both have unique features that separate them apart.
-
-```
-$ sudo add-apt-repository ppa:oguzhaninan/stacer
-$ sudo apt-get update
-$ sudo apt-get install stacer
-```
-
-### **69\. 4K Video Downloader**
-
-4K Video Downloader is simple video downloading tool which you can use to download videos, playlists, channels from Vimeo, Facebook, YouTube and other online video streaming sites. It supports downloading YouTube playlists and channels in MP4, MKV, M4A, 3GP and many other video/audio file formats.
-
-![][75]
-
-4K Video Downloader is not as simple as you would think, apart from normal video downloads it supports 3D and 360 degree video downloading. It also offers features like in-app proxy setup and direct transfer to iTunes. You can download it from [here][76].
-
-### 70\. **Qalculate**
-
-Qalculate is multi-purpose, cross-platform desktop calculator which is simple but very powerful calculator. It can be used for solving complicated maths problems and equations, currency conversions, and many other daily calculations.
-
-![][77]
-
-It has an excellent user interface and offers features such as customizable functions, unit calculations, symbolic calculations, arithmetic, plotting and many other functions you will find in any scientific calculator.
-
-### **71\. Hiri**
-
-Hiri is a cross-platform email client developed in Python programming language. It has slick user interface and it can be a good alternative to Microsoft Outlook in terms of features and services offered. This is great email client that can be used for sending and receiving emails, managing contacts, calendars and tasks.
-
-![][78]
-
-It is a feature-rich email client that offers features like integrated task manager, email synchronization, email rating, email filtering and many more.
-
-```
-$ sudo snap install hiri
-```
-
-### **72\. Sublime Text**
-
-Sublime Text is a cross-platform source code editor programmed in C++ and Python. It has Python Application Programming Interface (API) and supports all the major programming and markup languages. It is simple and lightweight text editor which can be used as IDE with features like auto-completion, syntax highlighting, split editing, etc.
-
-![][79]
-
-Some additional features in this text editor include Goto anything, Goto definition, multiple selections, command palette and fully customizable user interface.
-
-```
-$ sudo apt-get install sublime-text
-```
-
-### **73\. TeXstudio**
-
-TeXstudio is an integrated writing environment for creating and editing LaTex documents. It is an open-source editor which offers features like syntax highlighting, integrated viewer, interactive spelling checker, code folding, drag and drop, etc.
-
-![][80]
-
-It is a cross-platform editor and has very simple, lightweight user interface which is easy to use. It ships in with integration for BibTex and BibLatex bibliographies managers and also integrated PDF viewer. You can download TeXstudio installation package from its [website][81] or Ubuntu Software Center.
-
-### **74\. QtQR**
-
-QtQR is a Qt based application that lets you create and read QR codes in Ubuntu. It is developed in Python and Qt and has simple and lightweight user interface. You can encode website URL, email, text, SMS, etc. and you can also decode barcode using webcam camera.
-
-![][82]
-
-QtQR could prove to be useful tool to have if you generally deal with product sales and services because I don’t think we have any other similar tool to QtQR which requires minimal hardware to function smoothly.
-
-```
-$ sudo add-apt-repository ppa: qr-tools-developers/qr-tools-stable
-$ sudo apt-get update
-$ sudo apt-get install qtqr
-```
-
-### **75\. Kontact**
-
-Kontact is an integrated personal information manager (PIM) developed by KDE for KDE desktop environment. It is all-in-one software suite that integrates KMail, KOrganizer and KAddressBook into a single user interface from where you can manage all your mails, contacts, schedules, etc.
-
-![][83]
-
-It could be very good alternative to Microsoft Outlook as it is fast and highly configurable information manager. It has very good user interface which you will find very easy to use.
-
-```
-$ sudo apt-get install kontact
-```
-
-### **76\. NitroShare**
-
-NitroShare is a cross-platform, open-source network file sharing application. It lets you easily share files between multiple operating systems local network. It is a simple yet powerful application and it automatically detects other devices running NitroShare on local network.
-
-![][84]
-
-File transfer speed is what makes NitroShare a stand-out file sharing application as it achieves gigabit speed on capable hardware. There is no need for additional configuration required, you can start file transfer as soon as you install it.
-
-```
-$ sudo apt-add-repository ppa:george-edison55/nitroshare
-$ sudo apt-get update
-$ sudo apt-get install nitroshare
-```
-
-### **77\. Konversation**
-
-Konversation is an open-source Internet Relay Chat (IRC) client developed for KDE desktop environment. It gives speedy access to Freenode network’s channels where you can find support for most distributions.
-
-![][85]
-
-It is simple chat client with features like support for IPv6 connection, SSL server support, bookmarks, on-screen notifications, UTF-8 detection, and additional themes. It has easy to use GUI which is highly configurable.
-
-```
-$ sudo apt-get install konversation
-```
-
-### **78\. Discord**
-
-If you’re hardcore gamer and play online games frequently then I have a great application for you. Discord which is free Voice over Internet Protocol (VoIP) application especially designed for online gamers around the world. It is a cross-platform application and can be used for text and audio chats.
-
-![][86]
-
-Discord is very popular VoIP application gaming community and as it is completely free application, it is very good competitor to likes of Skype, Ventrilo and Teamspeak. It also offers features like crystal clear voice quality, modern text chat where you can share images, videos and links.
-
-### **79\. QuiteRSS**
-
-QuiteRSS is an open-source news aggregator for RSS and Atom news feeds. It is cross-platform feed reader written in Qt and C++. It has simple user interface which you can tweak in either classic or newspaper mode. It comes integrated with webkit browser out of the box so that you can perform all the tasks under single window.
-
-![][87]
-
-QuiteRSS comes with features such as content blocking, automatic scheduled feeds, import/export OPML, system tray integration and many other features you could expect in any feed reader.
-
-```
-$ sudo apt-get install quiterss
-```
-
-### **80\. MPV Media Player**
-
-MPV is a free and open-source media player based on MPlayer and MPlayer 2. It has simple user interface where user just needs to drag and drop audio/video files to play them as there is no option to add media files on GUI.
-
-![][88]
-
-One of the things about MPV is that it can play 4K videos effortlessly which is not the case with other media players on Linux distros. It also gives user ability to play videos from online video streaming sites including YouTube and Dailymotion.
-
-```
-$ sudo add-apt-repository ppa:mc3man/mpv-tests
-$ sudo apt-get update
-$ sudo apt-get install -y mpv
-```
-
-### **81\. Plume Creator**
-
-If you’re a writer then Plume Creator is must have application for you because you will not find other app for Ubuntu with privileges like Plume Creator. Writing and editing stories, chapters is tedious task and Plume Creator will ease this task for you with the help of some amazing tools it has to offer.
-
-![][89]
-
-It is an open-source application with minimal user interface which you could find confusing in the beginning but you will get used to it in some time. It offers features like edit notes, synopses, export in HTML and ODT formats support, and rich text editing.
-
-```
-$ sudo apt-get install plume-creator
-```
-
-### **82\. Chromium Web Browser**
-
-Chromium is an open-source web browser developed and distributed by Google. Chromium is very identical to Google Chrome web browser in terms of appearance and features. It is a lightweight and fast web browser with minimalist user interface.
-
-![][90]
-
-If you use Google Chrome regularly on Windows and looking for similar browser for Linux then Chromium is the best browser for you as you can login into your Google account to access all your Google services including Gmail.
-
-### **83\. Simple Weather Indicator**
-
-Simple Weather Indicator is an open-source weather indicator app developed in Python. It automatically detects your location and shows you weather information like temperature, possibility of rain, humidity, wind speed and visibility.
-
-![][91]
-
-Weather indicator comes with configurable options such as location detection, temperature SI unit, location visibility on/off, etc. It is cool app to have which adjusts with your desktop comfortably.
-
-### **84\. SpeedCrunch**
-
-SpeedCrunch is a fast and high-precision scientific calculator. It comes preloaded with math functions, user-defined functions, complex numbers and unit conversions support. It has simple user interface which is easy to use.
-
-![][92]
-
-This scientific calculator has some amazing features like result preview, syntax highlighting and auto-completion. It is a cross-platform calculator with multi-language support.
-
-### **85\. Scribus**
-
-Scribus is a free and open-source desktop publishing application that lets you create posters, magazines and books. It is a cross-platform application based on Qt toolkit and released under GNU general public license. It is a professional application with features like CMYK and ICC color management, Python based scripting engine, and PDF creation.
-
-![][93]
-
-Scribus comes with decent user interface which is easy to use and works effortlessly on systems with low hardware. It could be downloaded and installed from Software Center on all the latest Linux distros.
-
-### **86.** **Cura**
-
-Cura is an open-source 3D printing application developed by David Braam. Ultimaker Cura is the most popular software in 3D printing world and used by millions of users worldwide. It follows 3 step 3D printing model: Design, Prepare and Print.
-
-![][94]
-
-It is a feature-rich 3D printing application with seamless integration support for CAD plug-ins and add-ons. It is very simple and easy to use tool, novice artists can start right away. It supports major file formats like STL, 3MF and OBJ file formats.
-
-### **87\. Nomacs**
-
-Nomacs is an open-source, cross-platform image viewer which is supports all the major image formats including RAW and psd images. It has ability to browse images in zip or Microsoft Office files and extract them to a directory.
-
-![][95]
-
-Nomacs has very simple user interface with image thumbnails at the top and it offers some basic image manipulation features like crop, resize, rotate, color correction, etc.
-
-```
-$ sudo add-apt-repository ppa:nomacs/stable
-$ sudo apt-get update
-$ sudo apt-get install nomacs
-```
-
-### **88\. BitTicker**
-
-BitTicker is a live bitcoin-USDT Ticker for Ubuntu. It is a simple tool that connects to bittrex.com market and retrieves the latest price for BTC-USDT and display Ubuntu clock on system tray.
-
-![][96]
-
-It is simple but very useful too if you invest in Bitcoin regularly and have to study price fluctuations regulary.
-
-### **89\. Organize My Files**
-
-Organize My Files is cross-platform one click file organizer and it is available in Ubuntu as a snap package. It is a simple but powerful tool that will help you find unorganized files in a simple click and take them under control.
-
-![][97]
-
-It has intuitive user interface which is powerful and fast. It offers features such as auto organizing, recursive organizing, smart filters and multi folders organizing.
-
-### **90\. GnuCash**
-
-GnuCash is financial accounting software licensed under GNU general public license for free usage. It is an ideal software for personal and small business accounting. It has simple user interface which allows you to keep track of bank accounts, stocks, income and expenses.
-
-![][98]
-
-GnuCash implements double-entry bookkeeping system and based on professional accounting principle to ensure balanced books and accurate reports.
-
-### **91\. Calibre**
-
-Calibre is a cross-platform, open-source solution to all your e-book needs. It is a simple e-book organizer that offers features like displaying, creating, editing e-books, organizing existing e-books into virtual libraries, syncing and many more.
-
-![][99]
-
-Calibre also helps you convert e-books into whichever format you need and send them to your e-book reading device. Calibre is a very good tool to have if you regularly read and manage e-books.
-
-### **92\. MATE Dictionary**
-
-MATE Dictionary is a simple dictionary basically developed for MATE desktop environment. You just need to type the word and then this dictionary will display the meaning and references for it.
-
-![][100]
-
-It is simple and lightweight online dictionary with minimalist user interface.
-
-### **93\. Converseen**
-
-Converseen is a free cross-platform batch image processing application that lets you convert, edit, resize, rotate and flip large number of images with a single mouse click. It offers features like renaming bunch of images using prefix/suffix, extract image from a Windows icon file, etc.
-
-![][101]
-
-It has very good user interface which is easy to use even if you are a novice user. It can also convert entire PDF file into collection of images.
-
-### **94\. Tiled Map Editor**
-
-Tiled is a free software level map editor which you can use to edit the maps in various projections such as orthogonal, isometric and hexagonal. This tool can be very useful for game developers during game engine development cycle.
-
-![][102]
-
-Tiled is a versatile map editor which lets you create power boost positions, map layouts, collision areas, and enemy positions. It saves all the data in tmx format.
-
-### **95.** **Qmmp**
-
-Qmmp is a free and open-source audio player developed in Qt and C++. It is a cross-platform audio player with user interface very similar to Winamp. It has simple and intuitive user interface, Winamp skins can be used instead of default UI.
-
-![][103]
-
-It offers features such as automatic album cover fetching, multiple artists support, additional plug-ins and add-ons support and other features similar to Winamp.
-
-```
-$ sudo add-apt-repository ppa:forkotov02/ppa
-$ sudo apt-get update
-$ sudo apt-get install qmmp qmmp-q4 qmmp-plugin-pack-qt4
-```
-
-### **96\. Arora**
-
-Arora is free and open-source web browser which offers features like dedicated download manager, bookmarks, privacy mode and tabbed browsing.
-
-![][104]
-
-Arora web browser is developed by Benjamin C. Meyer and it is popular among Linux users for its lightweight nature and flexibility.
-
-### **97\. XnSketch**
-
-XnSketch is a cool application for Ubuntu that will help you transform your photos into cartoon or sketch images in few clicks. It sports 18 different effects such as black strokes, white strokes, pencil sketch and others.
-
-![][105]
-
-It has an excellent user interface which you will find easy to use. Some additional features in XnSketch include opacity and edge strength adjustment, contrast, brightness and saturation adjustment.
-
-### **98\. Geany**
-
-Geany is a simple and lightweight text editor which works like an Integrated Development Environment (IDE). It is a cross-platform text editor and supports all the major programming languages including Python, C++, LaTex, Pascal, C#, etc.
-
-![][106]
-
-Geany has simple user interface which resembles to programming editors like Notepad++. It offers IDE like features such as code navigation, auto-completion, syntax highlighting, and extensions support.
-
-```
-$ sudo apt-get install geany
-```
-
-### **99\. Mumble**
-
-Mumble is another Voice over Internet Protocol application very similar to Discord. Mumble is also basically designed for online gamers and uses client-server architecture for end-to-end chat. Voice quality is very good on Mumble and it offers end-to-end encryption to ensure privacy.
-
-![][107]
-
-Mumble is an open-source application and features very simple user interface which is easy to use. Mumble is available for download in Ubuntu Software Center.
-
-```
-$ sudo apt-get install mumble-server
-```
-
-### **100\. Deluge**
-
-Deluge is a cross-platform and lightweight BitTorrent client that can be used for downloading files on Ubuntu. BitTorrent client come bundled with many Linux distros but Deluge is the best BitTorrent client which has simple user interface which is easy to use.
-
-![][108]
-
-Deluge comes with all the features you will find in BitTorrent clients but one feature that stands out is it gives user ability to access the client from other devices as well so that you can download files to your computer even if you are not at home.
-
-```
-$ sudo add-apt-repository ppa:deluge-team/ppa
-$ sudo apt-get update
-$ sudo apt-get install deluge
-```
-
-So these are my picks for best 100 applications for Ubuntu in 2018 which you should try. All the applications listed here are tested on Ubuntu 18.04 and will definitely work on older versions too. Feel free to share your view about the article at [@LinuxHint][109] and [@SwapTirthakar][110].
-
---------------------------------------------------------------------------------
-
-via: https://linuxhint.com/100_best_ubuntu_apps/
-
-作者:[Swapnil Tirthakar][a]
-选题:[lujun9972](https://github.com/lujun9972)
-译者:[译者ID](https://github.com/译者ID)
-校对:[校对者ID](https://github.com/校对者ID)
-
-本文由 [LCTT](https://github.com/LCTT/TranslateProject) 原创编译,[Linux中国](https://linux.cn/) 荣誉推出
-
-[a]:https://linuxhint.com/author/swapnil/
-[1]:https://linuxhint.com/applications-2018-ubuntu/
-[2]:https://linuxhint.com/wp-content/uploads/2018/06/100-Best-Ubuntu-Apps.png
-[3]:https://linuxhint.com/wp-content/uploads/2018/06/Chrome.png
-[4]:https://linuxhint.com/wp-content/uploads/2018/06/Steam.png
-[5]:https://linuxhint.com/wp-content/uploads/2018/06/Wordpress.png
-[6]:https://linuxhint.com/wp-content/uploads/2018/06/VLC.png
-[7]:https://linuxhint.com/wp-content/uploads/2018/06/Atom-Text-Editor.png
-[8]:https://linuxhint.com/wp-content/uploads/2018/06/GIMP.png
-[9]:https://linuxhint.com/wp-content/uploads/2018/06/Google-Play.png
-[10]:https://www.googleplaymusicdesktopplayer.com/
-[11]:https://linuxhint.com/wp-content/uploads/2018/06/Franz.png
-[12]:https://meetfranz.com/#download
-[13]:https://linuxhint.com/wp-content/uploads/2018/06/Synaptic.png
-[14]:https://linuxhint.com/wp-content/uploads/2018/06/Skype.png
-[15]:https://linuxhint.com/wp-content/uploads/2018/06/VirtualBox.png
-[16]:https://linuxhint.com/wp-content/uploads/2018/06/Unity-Tweak-Tool.png
-[17]:https://linuxhint.com/wp-content/uploads/2018/06/Ubuntu-Cleaner.png
-[18]:https://linuxhint.com/wp-content/uploads/2018/06/Visual-Studio-Code.png
-[19]:https://linuxhint.com/wp-content/uploads/2018/06/Corebird.png
-[20]:https://linuxhint.com/wp-content/uploads/2018/06/Pixbuf.png
-[21]:https://linuxhint.com/wp-content/uploads/2018/06/Clementine.png
-[22]:https://linuxhint.com/wp-content/uploads/2016/06/blender.jpg
-[23]:https://linuxhint.com/wp-content/uploads/2018/06/Audacity.png
-[24]:https://linuxhint.com/wp-content/uploads/2018/06/Vim.png
-[25]:https://linuxhint.com/wp-content/uploads/2018/06/Inkscape-1.png
-[26]:https://linuxhint.com/wp-content/uploads/2018/06/ShotCut.png
-[27]:https://linuxhint.com/wp-content/uploads/2018/06/Simple-Screen-Recorder.png
-[28]:https://linuxhint.com/wp-content/uploads/2018/06/Telegram.png
-[29]:https://linuxhint.com/wp-content/uploads/2018/06/ClamTk.png
-[30]:https://linuxhint.com/wp-content/uploads/2018/06/Mailspring.png
-[31]:https://linuxhint.com/wp-content/uploads/2018/06/PyCharm.png
-[32]:https://linuxhint.com/wp-content/uploads/2018/06/Caffeine.png
-[33]:https://linuxhint.com/wp-content/uploads/2018/06/Etcher.png
-[34]:https://etcher.io/
-[35]:https://linuxhint.com/wp-content/uploads/2018/06/Neofetch.png
-[36]:https://linuxhint.com/wp-content/uploads/2018/06/Liferea.png
-[37]:https://linuxhint.com/wp-content/uploads/2018/06/Shutter.png
-[38]:https://linuxhint.com/wp-content/uploads/2018/06/Weather.png
-[39]:https://linuxhint.com/wp-content/uploads/2018/06/Ramme.png
-[40]:https://github.com/terkelg/ramme/releases
-[41]:https://linuxhint.com/wp-content/uploads/2018/06/Thunderbird.png
-[42]:https://linuxhint.com/wp-content/uploads/2018/06/Pidgin.png
-[43]:https://linuxhint.com/wp-content/uploads/2018/06/Krita.png
-[44]:https://linuxhint.com/wp-content/uploads/2018/06/Dropbox.png
-[45]:https://linuxhint.com/wp-content/uploads/2018/06/kodi.png
-[46]:https://linuxhint.com/wp-content/uploads/2018/06/Spotify.png
-[47]:https://linuxhint.com/wp-content/uploads/2018/06/Brackets.png
-[48]:https://linuxhint.com/wp-content/uploads/2018/06/Bitwarden.png
-[49]:https://linuxhint.com/wp-content/uploads/2018/06/Terminator.png
-[50]:https://linuxhint.com/wp-content/uploads/2018/06/Yak-Yak.png
-[51]:https://linuxhint.com/wp-content/uploads/2018/06/Thonny.png
-[52]:https://linuxhint.com/wp-content/uploads/2018/06/Font-Manager.png
-[53]:https://linuxhint.com/wp-content/uploads/2018/06/Atril.png
-[54]:https://linuxhint.com/wp-content/uploads/2018/06/Notepadqq.png
-[55]:https://linuxhint.com/wp-content/uploads/2018/06/Amarok.png
-[56]:https://linuxhint.com/wp-content/uploads/2018/06/Cheese.png
-[57]:https://linuxhint.com/wp-content/uploads/2018/06/MyPaint.png
-[58]:https://linuxhint.com/wp-content/uploads/2018/06/PlayOnLinux.png
-[59]:https://linuxhint.com/wp-content/uploads/2018/06/Akregator.png
-[60]:https://linuxhint.com/wp-content/uploads/2018/06/Brave.png
-[61]:https://linuxhint.com/wp-content/uploads/2018/06/Bitcoin-Core.png
-[62]:https://linuxhint.com/wp-content/uploads/2018/06/Speedy-Duplicate-Finder.png
-[63]:https://linuxhint.com/wp-content/uploads/2018/06/Zulip.png
-[64]:https://linuxhint.com/wp-content/uploads/2018/06/Okular.png
-[65]:https://linuxhint.com/wp-content/uploads/2018/06/Focus-Writer.png
-[66]:https://linuxhint.com/wp-content/uploads/2018/06/Guake.png
-[67]:https://linuxhint.com/wp-content/uploads/2018/06/KDE-Connect.png
-[68]:https://linuxhint.com/wp-content/uploads/2018/06/CopyQ.png
-[69]:https://linuxhint.com/wp-content/uploads/2018/06/Tilix.png
-[70]:https://linuxhint.com/wp-content/uploads/2018/06/Anbox.png
-[71]:https://linuxhint.com/wp-content/uploads/2018/06/OpenShot.png
-[72]:https://linuxhint.com/wp-content/uploads/2018/06/Plank.png
-[73]:https://linuxhint.com/wp-content/uploads/2018/06/FileZilla.png
-[74]:https://linuxhint.com/wp-content/uploads/2018/06/Stacer.png
-[75]:https://linuxhint.com/wp-content/uploads/2018/06/4K-Video-Downloader.png
-[76]:https://www.4kdownload.com/download
-[77]:https://linuxhint.com/wp-content/uploads/2018/06/Qalculate.png
-[78]:https://linuxhint.com/wp-content/uploads/2018/06/Hiri.png
-[79]:https://linuxhint.com/wp-content/uploads/2018/06/Sublime-text.png
-[80]:https://linuxhint.com/wp-content/uploads/2018/06/TeXstudio.png
-[81]:https://www.texstudio.org/
-[82]:https://linuxhint.com/wp-content/uploads/2018/06/QtQR.png
-[83]:https://linuxhint.com/wp-content/uploads/2018/06/Kontact.png
-[84]:https://linuxhint.com/wp-content/uploads/2018/06/Nitro-Share.png
-[85]:https://linuxhint.com/wp-content/uploads/2018/06/Konversation.png
-[86]:https://linuxhint.com/wp-content/uploads/2018/06/Discord.png
-[87]:https://linuxhint.com/wp-content/uploads/2018/06/QuiteRSS.png
-[88]:https://linuxhint.com/wp-content/uploads/2018/06/MPU-Media-Player.png
-[89]:https://linuxhint.com/wp-content/uploads/2018/06/Plume-Creator.png
-[90]:https://linuxhint.com/wp-content/uploads/2018/06/Chromium.png
-[91]:https://linuxhint.com/wp-content/uploads/2018/06/Simple-Weather-Indicator.png
-[92]:https://linuxhint.com/wp-content/uploads/2018/06/SpeedCrunch.png
-[93]:https://linuxhint.com/wp-content/uploads/2018/06/Scribus.png
-[94]:https://linuxhint.com/wp-content/uploads/2018/06/Cura.png
-[95]:https://linuxhint.com/wp-content/uploads/2018/06/Nomacs.png
-[96]:https://linuxhint.com/wp-content/uploads/2018/06/Bit-Ticker-1.png
-[97]:https://linuxhint.com/wp-content/uploads/2018/06/Organize-My-Files.png
-[98]:https://linuxhint.com/wp-content/uploads/2018/06/GNU-Cash.png
-[99]:https://linuxhint.com/wp-content/uploads/2018/06/Calibre.png
-[100]:https://linuxhint.com/wp-content/uploads/2018/06/MATE-Dictionary.png
-[101]:https://linuxhint.com/wp-content/uploads/2018/06/Converseen.png
-[102]:https://linuxhint.com/wp-content/uploads/2018/06/Tiled-Map-Editor.png
-[103]:https://linuxhint.com/wp-content/uploads/2018/06/Qmmp.png
-[104]:https://linuxhint.com/wp-content/uploads/2018/06/Arora.png
-[105]:https://linuxhint.com/wp-content/uploads/2018/06/XnSketch.png
-[106]:https://linuxhint.com/wp-content/uploads/2018/06/Geany.png
-[107]:https://linuxhint.com/wp-content/uploads/2018/06/Mumble.png
-[108]:https://linuxhint.com/wp-content/uploads/2018/06/Deluge.png
-[109]:https://twitter.com/linuxhint
-[110]:https://twitter.com/SwapTirthakar
diff --git a/sources/tech/20180725 Put platforms in a Python game with Pygame.md b/sources/tech/20180725 Put platforms in a Python game with Pygame.md
deleted file mode 100644
index 759bfc01df..0000000000
--- a/sources/tech/20180725 Put platforms in a Python game with Pygame.md
+++ /dev/null
@@ -1,590 +0,0 @@
-[#]: collector: (lujun9972)
-[#]: translator: ( )
-[#]: reviewer: ( )
-[#]: publisher: ( )
-[#]: url: ( )
-[#]: subject: (Put platforms in a Python game with Pygame)
-[#]: via: (https://opensource.com/article/18/7/put-platforms-python-game)
-[#]: author: (Seth Kenlon https://opensource.com/users/seth)
-
-Put platforms in a Python game with Pygame
-======
-In part six of this series on building a Python game from scratch, create some platforms for your characters to travel.
-
-
-This is part 6 in an ongoing series about creating video games in Python 3 using the Pygame module. Previous articles are:
-
-+ [Learn how to program in Python by building a simple dice game][24]
-+ [Build a game framework with Python using the Pygame module][25]
-+ [How to add a player to your Python game][26]
-+ [Using Pygame to move your game character around][27]
-+ [What's a hero without a villain? How to add one to your Python game][28]
-
-
-A platformer game needs platforms.
-
-In [Pygame][1], the platforms themselves are sprites, just like your playable sprite. That's important because having platforms that are objects makes it a lot easier for your player sprite to interact with them.
-
-There are two major steps in creating platforms. First, you must code the objects, and then you must map out where you want the objects to appear.
-
-### Coding platform objects
-
-To build a platform object, you create a class called `Platform`. It's a sprite, just like your [`Player`][2] [sprite][2], with many of the same properties.
-
-Your `Platform` class needs to know a lot of information about what kind of platform you want, where it should appear in the game world, and what image it should contain. A lot of that information might not even exist yet, depending on how much you have planned out your game, but that's all right. Just as you didn't tell your Player sprite how fast to move until the end of the [Movement article][3], you don't have to tell `Platform` everything upfront.
-
-Near the top of the script you've been writing in this series, create a new class. The first three lines in this code sample are for context, so add the code below the comment:
-
-```
-import pygame
-import sys
-import os
-## new code below:
-
-class Platform(pygame.sprite.Sprite):
-# x location, y location, img width, img height, img file
-def __init__(self,xloc,yloc,imgw,imgh,img):
- pygame.sprite.Sprite.__init__(self)
- self.image = pygame.image.load(os.path.join('images',img)).convert()
- self.image.convert_alpha()
- self.image.set_colorkey(ALPHA)
- self.rect = self.image.get_rect()
- self.rect.y = yloc
- self.rect.x = xloc
-```
-
-When called, this class creates an object onscreen in some X and Y location, with some width and height, using some image file for texture. It's very similar to how players or enemies are drawn onscreen.
-
-### Types of platforms
-
-The next step is to map out where all your platforms need to appear.
-
-#### The tile method
-
-There are a few different ways to implement a platform game world. In the original side-scroller games, such as Mario Super Bros. and Sonic the Hedgehog, the technique was to use "tiles," meaning that there were a few blocks to represent the ground and various platforms, and these blocks were used and reused to make a level. You have only eight or 12 different kinds of blocks, and you line them up onscreen to create the ground, floating platforms, and whatever else your game needs. Some people find this the easier way to make a game since you just have to make (or download) a small set of level assets to create many different levels. The code, however, requires a little more math.
-
-![Supertux, a tile-based video game][5]
-
-[SuperTux][6], a tile-based video game.
-
-#### The hand-painted method
-
-Another method is to make each and every asset as one whole image. If you enjoy creating assets for your game world, this is a great excuse to spend time in a graphics application, building each and every part of your game world. This method requires less math, because all the platforms are whole, complete objects, and you tell [Python][7] where to place them onscreen.
-
-Each method has advantages and disadvantages, and the code you must use is slightly different depending on the method you choose. I'll cover both so you can use one or the other, or even a mix of both, in your project.
-
-### Level mapping
-
-Mapping out your game world is a vital part of level design and game programming in general. It does involve math, but nothing too difficult, and Python is good at math so it can help some.
-
-You might find it helpful to design on paper first. Get a sheet of paper and draw a box to represent your game window. Draw platforms in the box, labeling each with its X and Y coordinates, as well as its intended width and height. The actual positions in the box don't have to be exact, as long as you keep the numbers realistic. For instance, if your screen is 720 pixels wide, then you can't fit eight platforms at 100 pixels each all on one screen.
-
-Of course, not all platforms in your game have to fit in one screen-sized box, because your game will scroll as your player walks through it. So keep drawing your game world to the right of the first screen until the end of the level.
-
-If you prefer a little more precision, you can use graph paper. This is especially helpful when designing a game with tiles because each grid square can represent one tile.
-
-![Example of a level map][9]
-
-Example of a level map.
-
-#### Coordinates
-
-You may have learned in school about the [Cartesian coordinate system][10]. What you learned applies to Pygame, except that in Pygame, your game world's coordinates place `0,0` in the top-left corner of your screen instead of in the middle, which is probably what you're used to from Geometry class.
-
-![Example of coordinates in Pygame][12]
-
-Example of coordinates in Pygame.
-
-The X axis starts at 0 on the far left and increases infinitely to the right. The Y axis starts at 0 at the top of the screen and extends down.
-
-#### Image sizes
-
-Mapping out a game world is meaningless if you don't know how big your players, enemies, and platforms are. You can find the dimensions of your platforms or tiles in a graphics program. In [Krita][13], for example, click on the **Image** menu and select **Properties**. You can find the dimensions at the very top of the **Properties** window.
-
-Alternately, you can create a simple Python script to tell you the dimensions of an image. Open a new text file and type this code into it:
-
-```
-#!/usr/bin/env python3
-
-from PIL import Image
-import os.path
-import sys
-
-if len(sys.argv) > 1:
- print(sys.argv[1])
-else:
- sys.exit('Syntax: identify.py [filename]')
-
-pic = sys.argv[1]
-dim = Image.open(pic)
-X = dim.size[0]
-Y = dim.size[1]
-
-print(X,Y)
-```
-
-Save the text file as `identify.py`.
-
-To set up this script, you must install an extra set of Python modules that contain the new keywords used in the script:
-
-```
-$ pip3 install Pillow --user
-```
-
-Once that is installed, run your script from within your game project directory:
-
-```
-$ python3 ./identify.py images/ground.png
-(1080, 97)
-```
-
-The image size of the ground platform in this example is 1080 pixels wide and 97 high.
-
-### Platform blocks
-
-If you choose to draw each asset individually, you must create several platforms and any other elements you want to insert into your game world, each within its own file. In other words, you should have one file per asset, like this:
-
-![One image file per object][15]
-
-One image file per object.
-
-You can reuse each platform as many times as you want, just make sure that each file only contains one platform. You cannot use a file that contains everything, like this:
-
-![Your level cannot be one image file][17]
-
-Your level cannot be one image file.
-
-You might want your game to look like that when you've finished, but if you create your level in one big file, there is no way to distinguish a platform from the background, so either paint your objects in their own file or crop them from a large file and save individual copies.
-
-**Note:** As with your other assets, you can use [GIMP][18], Krita, [MyPaint][19], or [Inkscape][20] to create your game assets.
-
-Platforms appear on the screen at the start of each level, so you must add a `platform` function in your `Level` class. The special case here is the ground platform, which is important enough to be treated as its own platform group. By treating the ground as its own special kind of platform, you can choose whether it scrolls or whether it stands still while other platforms float over the top of it. It's up to you.
-
-Add these two functions to your `Level` class:
-
-```
-def ground(lvl,x,y,w,h):
- ground_list = pygame.sprite.Group()
- if lvl == 1:
- ground = Platform(x,y,w,h,'block-ground.png')
- ground_list.add(ground)
-
- if lvl == 2:
- print("Level " + str(lvl) )
-
- return ground_list
-
-def platform( lvl ):
- plat_list = pygame.sprite.Group()
- if lvl == 1:
- plat = Platform(200, worldy-97-128, 285,67,'block-big.png')
- plat_list.add(plat)
- plat = Platform(500, worldy-97-320, 197,54,'block-small.png')
- plat_list.add(plat)
- if lvl == 2:
- print("Level " + str(lvl) )
-
- return plat_list
-```
-
-The `ground` function requires an X and Y location so Pygame knows where to place the ground platform. It also requires the width and height of the platform so Pygame knows how far the ground extends in each direction. The function uses your `Platform` class to generate an object onscreen, and then adds that object to the `ground_list` group.
-
-The `platform` function is essentially the same, except that there are more platforms to list. In this example, there are only two, but you can have as many as you like. After entering one platform, you must add it to the `plat_list` before listing another. If you don't add a platform to the group, then it won't appear in your game.
-
-> **Tip:** It can be difficult to think of your game world with 0 at the top, since the opposite is what happens in the real world; when figuring out how tall you are, you don't measure yourself from the sky down, you measure yourself from your feet to the top of your head.
->
-> If it's easier for you to build your game world from the "ground" up, it might help to express Y-axis values as negatives. For instance, you know that the bottom of your game world is the value of `worldy`. So `worldy` minus the height of the ground (97, in this example) is where your player is normally standing. If your character is 64 pixels tall, then the ground minus 128 is exactly twice as tall as your player. Effectively, a platform placed at 128 pixels is about two stories tall, relative to your player. A platform at -320 is three more stories. And so on.
-
-As you probably know by now, none of your classes and functions are worth much if you don't use them. Add this code to your setup section (the first line is just for context, so add the last two lines):
-
-```
-enemy_list = Level.bad( 1, eloc )
-ground_list = Level.ground( 1,0,worldy-97,1080,97 )
-plat_list = Level.platform( 1 )
-```
-
-And add these lines to your main loop (again, the first line is just for context):
-
-```
-enemy_list.draw(world) # refresh enemies
-ground_list.draw(world) # refresh ground
-plat_list.draw(world) # refresh platforms
-```
-
-### Tiled platforms
-
-Tiled game worlds are considered easier to make because you just have to draw a few blocks upfront and can use them over and over to create every platform in the game. There are even sets of tiles for you to use on sites like [OpenGameArt.org][21].
-
-The `Platform` class is the same as the one provided in the previous sections.
-
-The `ground` and `platform` in the `Level` class, however, must use loops to calculate how many blocks to use to create each platform.
-
-If you intend to have one solid ground in your game world, the ground is simple. You just "clone" your ground tile across the whole window. For instance, you could create a list of X and Y values to dictate where each tile should be placed, and then use a loop to take each value and draw one tile. This is just an example, so don't add this to your code:
-
-```
-# Do not add this to your code
-gloc = [0,656,64,656,128,656,192,656,256,656,320,656,384,656]
-```
-
-If you look carefully, though, you can see all the Y values are always the same, and the X values increase steadily in increments of 64, which is the size of the tiles. That kind of repetition is exactly what computers are good at, so you can use a little bit of math logic to have the computer do all the calculations for you:
-
-Add this to the setup part of your script:
-
-```
-gloc = []
-tx = 64
-ty = 64
-
-i=0
-while i <= (worldx/tx)+tx:
- gloc.append(i*tx)
- i=i+1
-
-ground_list = Level.ground( 1,gloc,tx,ty )
-```
-
-Now, regardless of the size of your window, Python divides the width of the game world by the width of the tile and creates an array listing each X value. This doesn't calculate the Y value, but that never changes on flat ground anyway.
-
-To use the array in a function, use a `while` loop that looks at each entry and adds a ground tile at the appropriate location:
-
-```
-def ground(lvl,gloc,tx,ty):
- ground_list = pygame.sprite.Group()
- i=0
- if lvl == 1:
- while i < len(gloc):
- ground = Platform(gloc[i],worldy-ty,tx,ty,'tile-ground.png')
- ground_list.add(ground)
- i=i+1
-
- if lvl == 2:
- print("Level " + str(lvl) )
-
- return ground_list
-```
-
-This is nearly the same code as the `ground` function for the block-style platformer, provided in a previous section above, aside from the `while` loop.
-
-For moving platforms, the principle is similar, but there are some tricks you can use to make your life easier.
-
-Rather than mapping every platform by pixels, you can define a platform by its starting pixel (its X value), the height from the ground (its Y value), and how many tiles to draw. That way, you don't have to worry about the width and height of every platform.
-
-The logic for this trick is a little more complex, so copy this code carefully. There is a `while` loop inside of another `while` loop because this function must look at all three values within each array entry to successfully construct a full platform. In this example, there are only three platforms defined as `ploc.append` statements, but your game probably needs more, so define as many as you need. Of course, some won't appear yet because they're far offscreen, but they'll come into view once you implement scrolling.
-
-```
-def platform(lvl,tx,ty):
- plat_list = pygame.sprite.Group()
- ploc = []
- i=0
- if lvl == 1:
- ploc.append((200,worldy-ty-128,3))
- ploc.append((300,worldy-ty-256,3))
- ploc.append((500,worldy-ty-128,4))
- while i < len(ploc):
- j=0
- while j <= ploc[i][2]:
- plat = Platform((ploc[i][0]+(j*tx)),ploc[i][1],tx,ty,'tile.png')
- plat_list.add(plat)
- j=j+1
- print('run' + str(i) + str(ploc[i]))
- i=i+1
-
- if lvl == 2:
- print("Level " + str(lvl) )
-
- return plat_list
-```
-
-To get the platforms to appear in your game world, they must be in your main loop. If you haven't already done so, add these lines to your main loop (again, the first line is just for context):
-
-```
- enemy_list.draw(world) # refresh enemies
- ground_list.draw(world) # refresh ground
- plat_list.draw(world) # refresh platforms
-```
-
-Launch your game, and adjust the placement of your platforms as needed. Don't worry that you can't see the platforms that are spawned offscreen; you'll fix that soon.
-
-Here is the game so far in a picture and in code:
-
-![Pygame game][23]
-
-Our Pygame platformer so far.
-
-```
- #!/usr/bin/env python3
-# draw a world
-# add a player and player control
-# add player movement
-# add enemy and basic collision
-# add platform
-
-# GNU All-Permissive License
-# Copying and distribution of this file, with or without modification,
-# are permitted in any medium without royalty provided the copyright
-# notice and this notice are preserved. This file is offered as-is,
-# without any warranty.
-
-import pygame
-import sys
-import os
-
-'''
-Objects
-'''
-
-class Platform(pygame.sprite.Sprite):
- # x location, y location, img width, img height, img file
- def __init__(self,xloc,yloc,imgw,imgh,img):
- pygame.sprite.Sprite.__init__(self)
- self.image = pygame.image.load(os.path.join('images',img)).convert()
- self.image.convert_alpha()
- self.rect = self.image.get_rect()
- self.rect.y = yloc
- self.rect.x = xloc
-
-class Player(pygame.sprite.Sprite):
- '''
- Spawn a player
- '''
- def __init__(self):
- pygame.sprite.Sprite.__init__(self)
- self.movex = 0
- self.movey = 0
- self.frame = 0
- self.health = 10
- self.score = 1
- self.images = []
- for i in range(1,9):
- img = pygame.image.load(os.path.join('images','hero' + str(i) + '.png')).convert()
- img.convert_alpha()
- img.set_colorkey(ALPHA)
- self.images.append(img)
- self.image = self.images[0]
- self.rect = self.image.get_rect()
-
- def control(self,x,y):
- '''
- control player movement
- '''
- self.movex += x
- self.movey += y
-
- def update(self):
- '''
- Update sprite position
- '''
-
- self.rect.x = self.rect.x + self.movex
- self.rect.y = self.rect.y + self.movey
-
- # moving left
- if self.movex < 0:
- self.frame += 1
- if self.frame > ani*3:
- self.frame = 0
- self.image = self.images[self.frame//ani]
-
- # moving right
- if self.movex > 0:
- self.frame += 1
- if self.frame > ani*3:
- self.frame = 0
- self.image = self.images[(self.frame//ani)+4]
-
- # collisions
- enemy_hit_list = pygame.sprite.spritecollide(self, enemy_list, False)
- for enemy in enemy_hit_list:
- self.health -= 1
- print(self.health)
-
- ground_hit_list = pygame.sprite.spritecollide(self, ground_list, False)
- for g in ground_hit_list:
- self.health -= 1
- print(self.health)
-
-
-class Enemy(pygame.sprite.Sprite):
- '''
- Spawn an enemy
- '''
- def __init__(self,x,y,img):
- pygame.sprite.Sprite.__init__(self)
- self.image = pygame.image.load(os.path.join('images',img))
- #self.image.convert_alpha()
- #self.image.set_colorkey(ALPHA)
- self.rect = self.image.get_rect()
- self.rect.x = x
- self.rect.y = y
- self.counter = 0
-
- def move(self):
- '''
- enemy movement
- '''
- distance = 80
- speed = 8
-
- if self.counter >= 0 and self.counter <= distance:
- self.rect.x += speed
- elif self.counter >= distance and self.counter <= distance*2:
- self.rect.x -= speed
- else:
- self.counter = 0
-
- self.counter += 1
-
-class Level():
- def bad(lvl,eloc):
- if lvl == 1:
- enemy = Enemy(eloc[0],eloc[1],'yeti.png') # spawn enemy
- enemy_list = pygame.sprite.Group() # create enemy group
- enemy_list.add(enemy) # add enemy to group
-
- if lvl == 2:
- print("Level " + str(lvl) )
-
- return enemy_list
-
- def loot(lvl,lloc):
- print(lvl)
-
- def ground(lvl,gloc,tx,ty):
- ground_list = pygame.sprite.Group()
- i=0
- if lvl == 1:
- while i < len(gloc):
- print("blockgen:" + str(i))
- ground = Platform(gloc[i],worldy-ty,tx,ty,'ground.png')
- ground_list.add(ground)
- i=i+1
-
- if lvl == 2:
- print("Level " + str(lvl) )
-
- return ground_list
-
-'''
-Setup
-'''
-worldx = 960
-worldy = 720
-
-fps = 40 # frame rate
-ani = 4 # animation cycles
-clock = pygame.time.Clock()
-pygame.init()
-main = True
-
-BLUE = (25,25,200)
-BLACK = (23,23,23 )
-WHITE = (254,254,254)
-ALPHA = (0,255,0)
-
-world = pygame.display.set_mode([worldx,worldy])
-backdrop = pygame.image.load(os.path.join('images','stage.png')).convert()
-backdropbox = world.get_rect()
-player = Player() # spawn player
-player.rect.x = 0
-player.rect.y = 0
-player_list = pygame.sprite.Group()
-player_list.add(player)
-steps = 10 # how fast to move
-
-eloc = []
-eloc = [200,20]
-gloc = []
-#gloc = [0,630,64,630,128,630,192,630,256,630,320,630,384,630]
-tx = 64 #tile size
-ty = 64 #tile size
-
-i=0
-while i <= (worldx/tx)+tx:
- gloc.append(i*tx)
- i=i+1
- print("block: " + str(i))
-
-enemy_list = Level.bad( 1, eloc )
-ground_list = Level.ground( 1,gloc,tx,ty )
-
-'''
-Main loop
-'''
-while main == True:
- for event in pygame.event.get():
- if event.type == pygame.QUIT:
- pygame.quit(); sys.exit()
- main = False
-
- if event.type == pygame.KEYDOWN:
- if event.key == pygame.K_LEFT or event.key == ord('a'):
- player.control(-steps,0)
- if event.key == pygame.K_RIGHT or event.key == ord('d'):
- player.control(steps,0)
- if event.key == pygame.K_UP or event.key == ord('w'):
- print('jump')
-
- if event.type == pygame.KEYUP:
- if event.key == pygame.K_LEFT or event.key == ord('a'):
- player.control(steps,0)
- if event.key == pygame.K_RIGHT or event.key == ord('d'):
- player.control(-steps,0)
- if event.key == ord('q'):
- pygame.quit()
- sys.exit()
- main = False
-
-# world.fill(BLACK)
- world.blit(backdrop, backdropbox)
- player.update()
- player_list.draw(world) #refresh player position
- enemy_list.draw(world) # refresh enemies
- ground_list.draw(world) # refresh enemies
- for e in enemy_list:
- e.move()
- pygame.display.flip()
- clock.tick(fps)
-```
-
---------------------------------------------------------------------------------
-
-via: https://opensource.com/article/18/7/put-platforms-python-game
-
-作者:[Seth Kenlon][a]
-选题:[lujun9972][b]
-译者:[译者ID](https://github.com/译者ID)
-校对:[校对者ID](https://github.com/校对者ID)
-
-本文由 [LCTT](https://github.com/LCTT/TranslateProject) 原创编译,[Linux中国](https://linux.cn/) 荣誉推出
-
-[a]: https://opensource.com/users/seth
-[b]: https://github.com/lujun9972
-[1]: https://www.pygame.org/news
-[2]: https://opensource.com/article/17/12/game-python-add-a-player
-[3]: https://opensource.com/article/17/12/game-python-moving-player
-[4]: /file/403841
-[5]: https://opensource.com/sites/default/files/uploads/supertux.png (Supertux, a tile-based video game)
-[6]: https://www.supertux.org/
-[7]: https://www.python.org/
-[8]: /file/403861
-[9]: https://opensource.com/sites/default/files/uploads/layout.png (Example of a level map)
-[10]: https://en.wikipedia.org/wiki/Cartesian_coordinate_system
-[11]: /file/403871
-[12]: https://opensource.com/sites/default/files/uploads/pygame_coordinates.png (Example of coordinates in Pygame)
-[13]: https://krita.org/en/
-[14]: /file/403876
-[15]: https://opensource.com/sites/default/files/uploads/pygame_floating.png (One image file per object)
-[16]: /file/403881
-[17]: https://opensource.com/sites/default/files/uploads/pygame_flattened.png (Your level cannot be one image file)
-[18]: https://www.gimp.org/
-[19]: http://mypaint.org/about/
-[20]: https://inkscape.org/en/
-[21]: https://opengameart.org/content/simplified-platformer-pack
-[22]: /file/403886
-[23]: https://opensource.com/sites/default/files/uploads/pygame_platforms.jpg (Pygame game)
-[24]: Learn how to program in Python by building a simple dice game
-[25]: https://opensource.com/article/17/12/game-framework-python
-[26]: https://opensource.com/article/17/12/game-python-add-a-player
-[27]: https://opensource.com/article/17/12/game-python-moving-player
-[28]: https://opensource.com/article/18/5/pygame-enemy
-
diff --git a/sources/tech/20180902 Learning BASIC Like It-s 1983.md b/sources/tech/20180902 Learning BASIC Like It-s 1983.md
deleted file mode 100644
index 5790ef6e88..0000000000
--- a/sources/tech/20180902 Learning BASIC Like It-s 1983.md
+++ /dev/null
@@ -1,184 +0,0 @@
-Learning BASIC Like It's 1983
-======
-I was not yet alive in 1983. This is something that I occasionally regret. I am especially sorry that I did not experience the 8-bit computer era as it was happening, because I think the people that first encountered computers when they were relatively simple and constrained have a huge advantage over the rest of us.
-
-Today, (almost) everyone knows how to use a computer, but very few people, even in the computing industry, grasp all of what is going on inside of any single machine. There are now [so many layers of software][1] doing so many different things that one struggles to identify the parts that are essential. In 1983, though, home computers were unsophisticated enough that a diligent person could learn how a particular computer worked through and through. That person is today probably less mystified than I am by all the abstractions that modern operating systems pile on top of the hardware. I expect that these layers of abstractions were easy to understand one by one as they were introduced; today, new programmers have to try to understand them all by working top to bottom and backward in time.
-
-Many famous programmers, particularly in the video game industry, started programming games in childhood on 8-bit computers like the Apple II and the Commodore 64. John Romero, Richard Garriott, and Chris Roberts are all examples. It’s easy to see how this happened. In the 8-bit computer era, many games were available only as printed BASIC listings in computer magazines and [books][2]. If you wanted to play one of those games, you had to type in the whole program by hand. Inevitably, you would get something wrong, so you would have to debug your program. By the time you got it working, you knew enough about how the program functioned to start modifying it yourself. If you were an avid gamer, you became a good programmer almost by necessity.
-
-I also played computer games throughout my childhood. But the games I played came on CD-ROMs. I sometimes found myself having to google how to fix a crashing installer, which would involve editing the Windows Registry or something like that. This kind of minor troubleshooting may have made me comfortable enough with computers to consider studying computer science in college. But it never taught me anything crucial about how computers worked or how to control them.
-
-Now, of course, I tell computers what to do for a living. All the same, I can’t help feeling that I missed out on some fundamental insight afforded only to those that grew up programming simpler computers. What would it have been like to encounter computers for the first time in the early 1980s? How would that have been different from the experience of using a computer today?
-
-This post is going to be a little different from the usual Two-Bit History post because I’m going to try to imagine an answer to these questions.
-
-### 1983
-
-It was just last week that you saw [the Commodore 64 ad][3] on TV. Now that M*A*S*H was over, you were in the market for something new to do on Monday nights. This Commodore 64 thing looked even better than the Apple II that Rudy’s family had in their basement. Plus, the ad promised that the new computer would soon bring friends “knocking down” your door. You knew several people at school that would rather be hanging out at your house than Rudy’s anyway, if only they could play Zork there.
-
-So you persuaded your parents to buy one. Your mother said that they would consider it only if having a home computer meant that you stayed away from the arcade. You reluctantly agreed. Your father thought he would start tracking the family’s finances in MultiPlan, the spreadsheet program he had heard about, which is why the computer got put in the living room. A year later, though, you would be the only one still using it. You were finally allowed to put it on the desk in your bedroom, right under your Police poster.
-
-(Your sister protested this decision, but it was 1983 and computers [weren’t for her][4].)
-
-Dad picked it up from [ComputerLand][5] on the way home from work. The two of you laid the box down next to the TV and opened it. “WELCOME TO THE WORLD OF FRIENDLY COMPUTING,” said the packaging. Twenty minutes later, you weren’t convinced—the two of you were still trying to connect the Commodore to the TV set and wondering whether the TV’s antenna cable was the 75-ohm or 300-ohm coax type. But eventually you were able to turn your TV to channel 3 and see a grainy, purple image.
-
-![Commodore 64 startup screen][6]
-
-`READY`, the computer reported. Your father pushed the computer toward you, indicating that you should be the first to give it a try. `HELLO`, you typed, carefully hunting for each letter. The computer’s response was baffling.
-
-![Commodore 64 syntax error][7]
-
-You tried typing in a few different words, but the response was always the same. Your father said that you had better read through the rest of the manual. That would be no mean feat—[the manual that came with the Commodore 64][8] was a small book. But that didn’t bother you, because the introduction to the manual foreshadowed wonders.
-
-The Commodore 64, it claimed, had “the most advanced picture maker in the microcomputer industry,” which would allow you “to design your own pictures in four different colors, just like the ones you see on arcade type video games.” The Commodore 64 also had “built-in music and sound effects that rival many well known music synthesizers.” All of these tools would be put in your hands, because the manual would walk you through it all:
-
-> Just as important as all the available hardware is the fact that this USER’S GUIDE will help you develop your understanding of computers. It won’t tell you everything there is to know about computers, but it will refer you to a wide variety of publications for more detailed information about the topics presented. Commodore wants you to really enjoy your new COMMODORE 64. And to have fun, remember: programming is not the kind of thing you can learn in a day. Be patient with yourself as you go through the USER’S GUIDE.
-
-That night, in bed, you read through the entire first three chapters—”Setup,” “Getting Started,” and “Beginning BASIC Programming”—before finally succumbing to sleep with the manual splayed across your chest.
-
-### Commodore BASIC
-
-Now, it’s Saturday morning and you’re eager to try out what you’ve learned. One of the first things the manual teaches you how to do is change the colors on the display. You follow the instructions, pressing `CTRL-9` to enter reverse type mode and then holding down the space bar to create long lines. You swap between colors using `CTRL-1` through `CTRL-8`, reveling in your sudden new power over the TV screen.
-
-![Commodore 64 color bands][9]
-
-As cool as this is, you realize it doesn’t count as programming. In order to program the computer, you learned last night, you have to speak to it in a language called BASIC. To you, BASIC seems like something out of Star Wars, but BASIC is, by 1983, almost two decades old. It was invented by two Dartmouth professors, John Kemeny and Tom Kurtz, who wanted to make computing accessible to undergraduates in the social sciences and humanities. It was widely available on minicomputers and popular in college math classes. It then became standard on microcomputers after Bill Gates and Paul Allen wrote the MicroSoft BASIC interpreter for the Altair. But the manual doesn’t explain any of this and you won’t learn it for many years.
-
-One of the first BASIC commands the manual suggests you try is the `PRINT` command. You type in `PRINT "COMMODORE 64"`, slowly, since it takes you a while to find the quotation mark symbol above the `2` key. You hit `RETURN` and this time, instead of complaining, the computer does exactly what you told it to do and displays “COMMODORE 64” on the next line.
-
-Now you try using the `PRINT` command on all sorts of different things: two numbers added together, two numbers multiplied together, even several decimal numbers. You stop typing out `PRINT` and instead use `?`, since the manual has advised you that `?` is an abbreviation for `PRINT` often used by expert programmers. You feel like an expert already, but then you remember that you haven’t even made it to chapter three, “Beginning BASIC Programming.”
-
-You get there soon enough. The chapter begins by prompting you to write your first real BASIC program. You type in `NEW` and hit `RETURN`, which gives you a clean slate. You then type your program in:
-
-```
-10 ?"COMMODORE 64"
-20 GOTO 10
-```
-
-The 10 and the 20, the manual explains, are line numbers. They order the statements for the computer. They also allow the programmer to refer to other lines of the program in certain commands, just like you’ve done here with the `GOTO` command, which directs the program back to line 10. “It is good programming practice,” the manual opines, “to number lines in increments of 10—in case you need to insert some statements later on.”
-
-You type `RUN` and stare as the screen clogs with “COMMODORE 64,” repeated over and over.
-
-![Commodore 64 showing result of printing "Commodore 64" repeatedly][10]
-
-You’re not certain that this isn’t going to blow up your computer. It takes you a second to remember that you are supposed to hit the `RUN/STOP` key to break the loop.
-
-The next few sections of the manual teach you about variables, which the manual tells you are like “a number of boxes within the computer that can each hold a number or a string of text characters.” Variables that end in a `%` symbol are whole numbers, while variables ending in a `$` symbol are strings of characters. All other variables are something called “floating point” variables. The manual warns you to be careful with variable names because only the first two letters of the name are actually recognized by the computer, even though nothing stops you from making a name as long as you want it to be. (This doesn’t particularly bother you, but you could see how 30 years from now this might strike someone as completely insane.)
-
-You then learn about the `IF... THEN...` and `FOR... NEXT...` constructs. With all these new tools, you feel equipped to tackle the next big challenge the manual throws at you. “If you’re the ambitious type,” it goads, “type in the following program and see what happens.” The program is longer and more complicated than any you have seen so far, but you’re dying to know what it does:
-
-```
-10 REM BOUNCING BALL
-20 PRINT "{CLR/HOME}"
-25 FOR X = 1 TO 10 : PRINT "{CRSR/DOWN}" : NEXT
-30 FOR BL = 1 TO 40
-40 PRINT " ●{CRSR LEFT}";:REM (● is a Shift-Q)
-50 FOR TM = 1 TO 5
-60 NEXT TM
-70 NEXT BL
-75 REM MOVE BALL RIGHT TO LEFT
-80 FOR BL = 40 TO 1 STEP -1
-90 PRINT " {CRSR LEFT}{CRSR LEFT}●{CRSR LEFT}";
-100 FOR TM = 1 TO 5
-110 NEXT TM
-120 NEXT BL
-130 GOTO 20
-```
-
-The program above takes advantage of one of the Commodore 64’s coolest features. Non-printable command characters, when passed to the `PRINT` command as part of a string, just do the action they usually perform instead of printing to the screen. This allows you to replay arbitrary chains of commands by printing strings from within your programs.
-
-It takes you a long time to type in the above program. You make several mistakes and have to re-enter some of the lines. But eventually you are able to type `RUN` and behold a masterpiece:
-
-![Commodore 64 bouncing ball][11]
-
-You think that this is a major contender for the coolest thing you have ever seen. You forget about it almost immediately though, because once you’ve learned about BASIC’s built-in functions like `RND` (which returns a random number) and `CHR$` (which returns the character matching a given number code), the manual shows you a program that many years from now will still be famous enough to be made the title of an [essay anthology][12]:
-
-```
-10 PRINT "{CLR/HOME}"
-20 PRINT CHR$(205.5 + RND(1));
-40 GOTO 20
-```
-
-When run, the above program produces a random maze:
-
-![Commodore 64 maze program][13]
-
-This is definitely the coolest thing you have ever seen.
-
-### PEEK and POKE
-
-You’ve now made it through the first four chapters of the Commodore 64 manual, including the chapter titled “Advanced BASIC,” so you’re feeling pretty proud of yourself. You’ve learned a lot this Saturday morning. But this afternoon (after a quick lunch break), you’re going to learn something that will make this magical machine in your living room much less mysterious.
-
-The next chapter in the manual is titled “Advanced Color and Graphic Commands.” It starts off by revisiting the colored bars that you were able to type out first thing this morning and shows you how you can do the same thing from a program. It then teaches you how to change the background colors of the screen.
-
-In order to do this, you need to use the BASIC `PEEK` and `POKE` commands. Those commands allow you to, respectively, examine and write to a memory address. The Commodore 64 has a main background color and a border color. Each is controlled by a specially designated memory address. You can write any color value you would like to those addresses to make the background or border that color.
-
-The manual explains:
-
-> Just as variables can be thought of as a representation of “boxes” within the machine where you placed your information, you can also think of some specially defined “boxes” within the computer that represent specific memory locations.
->
-> The Commodore 64 looks at these memory locations to see what the screen’s background and border color should be, what characters are to be displayed on the screen—and where—and a host of other tasks.
-
-You write a program to cycle through all the available combinations of background and border color:
-
-```
-10 FOR BA = 0 TO 15
-20 FOR BO = 0 TO 15
-30 POKE 53280, BA
-40 POKE 53281, BO
-50 FOR X = 1 TO 500 : NEXT X
-60 NEXT BO : NEXT BA
-```
-
-While the `POKE` commands, with their big operands, looked intimidating at first, now you see that the actual value of the number doesn’t matter that much. Obviously, you have to get the number right, but all the number represents is a “box” that Commodore just happened to store at address 53280. This box has a special purpose: Commodore uses it to determine what color the screen’s background should be.
-
-![Commodore 64 changing background colors][14]
-
-You think this is pretty neat. Just by writing to a special-purpose box in memory, you can control a fundamental property of the computer. You aren’t sure how the Commodore 64’s circuitry takes the value you write in memory and changes the color of the screen, but you’re okay not knowing that. At least you understand everything up to that point.
-
-### Special Boxes
-
-You don’t get through the entire manual that Saturday, since you are now starting to run out of steam. But you do eventually read all of it. In the process, you learn about many more of the Commodore 64’s special-purpose boxes. There are boxes you can write to control what is on screen—one box, in fact, for every place a character might appear. In chapter six, “Sprite Graphics,” you learn about the special-purpose boxes that allow you to define images that can be moved around and even scaled up and down. In chapter seven, “Creating Sound,” you learn about the boxes you can write to in order to make your Commodore 64 sing “Michael Row the Boat Ashore.” The Commodore 64, it turns out, has very little in the way of what you would later learn is called an API. Controlling the Commodore 64 mostly involves writing to memory addresses that have been given special meaning by the circuitry.
-
-The many years you ultimately spend writing to those special boxes stick with you. Even many decades later, when you find yourself programming a machine with an extensive graphics or sound API, you know that, behind the curtain, the API is ultimately writing to those boxes or something like them. You will sometimes wonder about younger programmers that have only ever used APIs, and wonder what they must think the API is doing for them. Maybe they think that the API is calling some other, hidden API. But then what do think that hidden API is calling? You will pity those younger programmers, because they must be very confused indeed.
-
-If you enjoyed this post, more like it come out every two weeks! Follow [@TwoBitHistory][15] on Twitter or subscribe to the [RSS feed][16] to make sure you know when a new post is out.
-
-Previously on TwoBitHistory…
-
-> Have you ever wondered what a 19th-century computer program would look like translated into C?
->
-> This week's post: A detailed look at how Ada Lovelace's famous program worked and what it was trying to do.
->
-> — TwoBitHistory (@TwoBitHistory) [August 19, 2018][17]
-
---------------------------------------------------------------------------------
-
-via: https://twobithistory.org/2018/09/02/learning-basic.html
-
-作者:[Two-Bit History][a]
-选题:[lujun9972][b]
-译者:[译者ID](https://github.com/译者ID)
-校对:[校对者ID](https://github.com/校对者ID)
-
-本文由 [LCTT](https://github.com/LCTT/TranslateProject) 原创编译,[Linux中国](https://linux.cn/) 荣誉推出
-
-[a]: https://twobithistory.org
-[b]: https://github.com/lujun9972
-[1]: https://www.youtube.com/watch?v=kZRE7HIO3vk
-[2]: https://en.wikipedia.org/wiki/BASIC_Computer_Games
-[3]: https://www.youtube.com/watch?v=ZekAbt2o6Ms
-[4]: https://www.npr.org/sections/money/2014/10/21/357629765/when-women-stopped-coding
-[5]: https://www.youtube.com/watch?v=MA_XtT3VAVM
-[6]: https://twobithistory.org/images/c64_startup.png
-[7]: https://twobithistory.org/images/c64_error.png
-[8]: ftp://www.zimmers.net/pub/cbm/c64/manuals/C64_Users_Guide.pdf
-[9]: https://twobithistory.org/images/c64_colors.png
-[10]: https://twobithistory.org/images/c64_print_loop.png
-[11]: https://twobithistory.org/images/c64_ball.gif
-[12]: http://10print.org/
-[13]: https://twobithistory.org/images/c64_maze.gif
-[14]: https://twobithistory.org/images/c64_background.gif
-[15]: https://twitter.com/TwoBitHistory
-[16]: https://twobithistory.org/feed.xml
-[17]: https://twitter.com/TwoBitHistory/status/1030974776821665793?ref_src=twsrc%5Etfw
diff --git a/sources/tech/20180914 A day in the life of a log message.md b/sources/tech/20180914 A day in the life of a log message.md
deleted file mode 100644
index 8d60ec9fe6..0000000000
--- a/sources/tech/20180914 A day in the life of a log message.md
+++ /dev/null
@@ -1,57 +0,0 @@
-A day in the life of a log message
-======
-
-Navigating a modern distributed system from the perspective of a log message.
-
-
-
-Chaotic systems tend to be unpredictable. This is especially evident when architecting something as complex as a distributed system. Left unchecked, this unpredictability can waste boundless amounts of time. This is why every single component of a distributed system, no matter how small, must be designed to fit together in a streamlined way.
-
-[Kubernetes][1] provides a promising model for abstracting compute resources—but even it must be reconciled with other distributed platforms such as [Apache Kafka][2] to ensure reliable data delivery. If someone were to integrate these two platforms, how would it work? Furthermore, if you were to trace something as simple as a log message through such a system, what would it look like? This article will focus on how a log message from an application running inside [OKD][3], the Origin Community Distribution of Kubernetes that powers Red Hat OpenShift, gets to a data warehouse through Kafka.
-
-### OKD-defined environment
-
-Such a journey begins in OKD, since the container platform completely overlays the hardware it abstracts. This means that the log message waits to be written to **stdout** or **stderr** streams by an application residing in a container. From there, the log message is redirected onto the node's filesystem by a container engine such as [CRI-O][4].
-
-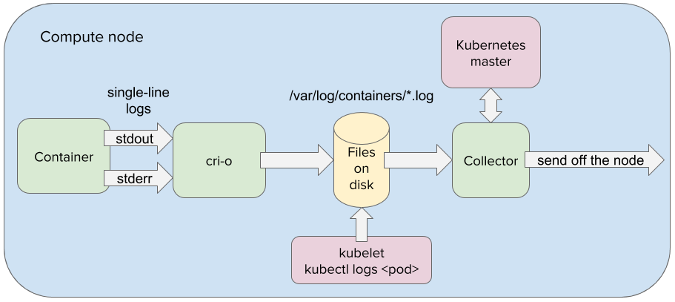
-
-ithin OpenShift, one or more containers are encapsulated within virtual compute nodes known as pods. In fact, all applications running within OKD are abstracted as pods. This allows the applications to be manipulated in a uniform way. This also greatly simplifies communication between distributed components, since pods are systematically addressable through IP addresses and [load-balanced services][5] . So when the log message is taken from the node's filesystem by a log-collector application, it can easily be delivered to another pod running within OpenShift.
-
-### Two peas in a pod
-
-To ensure ubiquitous dispersal of the log message throughout the distributed system, the log collector needs to deliver the log message into a Kafka cluster data hub running within OpenShift. Through Kafka, the log message can be delivered to the consuming applications in a reliable and fault-tolerant way with low latency. However, in order to reap the benefits of Kafka within an OKD-defined environment, Kafka needs to be fully integrated into OKD.
-
-Running a [Strimzi operator][6] will instantiate all Kafka components as pods and integrate them to run within an OKD environment. This includes Kafka brokers for queuing log messages, Kafka connectors for reading and writing from Kafka brokers, and Zookeeper nodes for managing the Kafka cluster state. Strimzi can also instantiate the log collector to double as a Kafka connector, allowing the log collector to feed the log messages directly into a Kafka broker pod running within OKD.
-
-### Kafka inside OKD
-
-When the log-collector pod delivers the log message to a Kafka broker, the collector writes to a single broker partition, appending the message to the end of the partition. One of the advantages of using Kafka is that it decouples the log collector from the log's final destination. Thanks to the decoupling, the log collector doesn't care whether the logs end up in [Elasticsearch][7], Hadoop, Amazon S3, or all of them at the same time. Kafka is well-connected to all infrastructure, so the Kafka connectors can take the log message wherever it needs to go.
-
-Once written to a Kafka broker's partition, the log message is replicated across the broker partitions within the Kafka cluster. This is a very powerful concept on its own; combined with the self-healing features of the platform, it creates a very resilient distributed system. For example, when a node becomes unavailable, the applications running on the node are almost instantaneously spawned on healthy node(s). So even if a node with the Kafka broker is lost or damaged, the log message is guaranteed to survive as many deaths as it was replicated and a new Kafka broker will quickly take the original's place.
-
-### Off to storage
-
-After it is committed to a Kafka topic, the log message waits to be consumed by a Kafka connector sink, which relays the log message to either an analytics engine or logging warehouse. Upon delivery to its final destination, the log message could be studied for anomaly detection, queried for immediate root-cause analysis, or used for other purposes. Either way, the log message is delivered by Kafka to its destination in a safe and reliable manner.
-
-OKD and Kafka are powerful distributed platforms that are evolving rapidly. It is vital to create systems that can abstract the complicated nature of distributed computing without compromising performance. After all, how can we boast of systemwide efficiency if we cannot simplify the journey of a single log message?
-
-
---------------------------------------------------------------------------------
-
-via: https://opensource.com/article/18/9/life-log-message
-
-作者:[Josef Karásek][a]
-选题:[lujun9972](https://github.com/lujun9972)
-译者:[译者ID](https://github.com/译者ID)
-校对:[校对者ID](https://github.com/校对者ID)
-
-本文由 [LCTT](https://github.com/LCTT/TranslateProject) 原创编译,[Linux中国](https://linux.cn/) 荣誉推出
-
-[a]: https://opensource.com/users/jkarasek
-[1]: https://kubernetes.io/
-[2]: https://kafka.apache.org/
-[3]: https://www.okd.io/
-[4]: http://cri-o.io/
-[5]: https://kubernetes.io/docs/concepts/services-networking/service/
-[6]: http://strimzi.io/
-[7]: https://www.elastic.co/
diff --git a/sources/tech/20181031 Working with data streams on the Linux command line.md b/sources/tech/20181031 Working with data streams on the Linux command line.md
index b391b2af0b..87403558d7 100644
--- a/sources/tech/20181031 Working with data streams on the Linux command line.md
+++ b/sources/tech/20181031 Working with data streams on the Linux command line.md
@@ -1,4 +1,3 @@
-liujing97 is translating
Working with data streams on the Linux command line
======
Learn to connect data streams from one utility to another using STDIO.
diff --git a/sources/tech/20181212 TLP - An Advanced Power Management Tool That Improve Battery Life On Linux Laptop.md b/sources/tech/20181212 TLP - An Advanced Power Management Tool That Improve Battery Life On Linux Laptop.md
deleted file mode 100644
index e1e6a7f25e..0000000000
--- a/sources/tech/20181212 TLP - An Advanced Power Management Tool That Improve Battery Life On Linux Laptop.md
+++ /dev/null
@@ -1,745 +0,0 @@
-[#]: collector: (lujun9972)
-[#]: translator: ( )
-[#]: reviewer: ( )
-[#]: publisher: ( )
-[#]: url: ( )
-[#]: subject: (TLP – An Advanced Power Management Tool That Improve Battery Life On Linux Laptop)
-[#]: via: (https://www.2daygeek.com/tlp-increase-optimize-linux-laptop-battery-life/)
-[#]: author: (Magesh Maruthamuthu https://www.2daygeek.com/author/magesh/)
-
-TLP – An Advanced Power Management Tool That Improve Battery Life On Linux Laptop
-======
-
-Laptop battery is highly optimized for Windows OS, that i had realized when i was using Windows OS in my laptop but it’s not same for Linux.
-
-Over the years Linux has improved a lot for battery optimization but still we need make some necessary things to improve laptop battery life in Linux.
-
-When i think about battery life, i got few options for that but i felt TLP is a better solutions for me so, i’m going with it.
-
-In this tutorial we are going to discuss about TLP in details to improve battery life.
-
-We had written three articles previously in our site about **[laptop battery saving utilities][1]** for Linux **[PowerTOP][2]** and **[Battery Charging State][3]**.
-
-### What is TLP?
-
-[TLP][4] is a free opensource advanced power management tool that improve your battery life without making any configuration change.
-
-Since it comes with a default configuration already optimized for battery life, so you may just install and forget it.
-
-Also, it is highly customizable to fulfill your specific requirements. TLP is a pure command line tool with automated background tasks. It does not contain a GUI.
-
-TLP runs on every laptop brand. Setting the battery charge thresholds is available for IBM/Lenovo ThinkPads only.
-
-All TLP settings are stored in `/etc/default/tlp`. The default configuration provides optimized power saving out of the box.
-
-The following TLP settings is available for customization and you need to make the necessary changes accordingly if you want it.
-
-### TLP Features
-
- * Kernel laptop mode and dirty buffer timeouts
- * Processor frequency scaling including “turbo boost” / “turbo core”
- * Limit max/min P-state to control power dissipation of the CPU
- * HWP energy performance hints
- * Power aware process scheduler for multi-core/hyper-threading
- * Processor performance versus energy savings policy (x86_energy_perf_policy)
- * Hard disk advanced power magement level (APM) and spin down timeout (per disk)
- * AHCI link power management (ALPM) with device blacklist
- * PCIe active state power management (PCIe ASPM)
- * Runtime power management for PCI(e) bus devices
- * Radeon graphics power management (KMS and DPM)
- * Wifi power saving mode
- * Power off optical drive in drive bay
- * Audio power saving mode
- * I/O scheduler (per disk)
- * USB autosuspend with device blacklist/whitelist (input devices excluded automatically)
- * Enable or disable integrated wifi, bluetooth or wwan devices upon system startup and shutdown
- * Restore radio device state on system startup (from previous shutdown).
- * Radio device wizard: switch radios upon network connect/disconnect and dock/undock
- * Disable Wake On LAN
- * Integrated WWAN and bluetooth state is restored after suspend/hibernate
- * Untervolting of Intel processors – requires kernel with PHC-Patch
- * Battery charge thresholds – ThinkPads only
- * Recalibrate battery – ThinkPads only
-
-
-
-### How to Install TLP in Linux
-
-TLP package is available in most of the distributions official repository so, use the distributions **[Package Manager][5]** to install it.
-
-For **`Fedora`** system, use **[DNF Command][6]** to install TLP.
-
-```
-$ sudo dnf install tlp tlp-rdw
-```
-
-ThinkPads require an additional packages.
-
-```
-$ sudo dnf install https://download1.rpmfusion.org/free/fedora/rpmfusion-free-release-$(rpm -E %fedora).noarch.rpm
-$ sudo dnf install http://repo.linrunner.de/fedora/tlp/repos/releases/tlp-release.fc$(rpm -E %fedora).noarch.rpm
-$ sudo dnf install akmod-tp_smapi akmod-acpi_call kernel-devel
-```
-
-Install smartmontool to display S.M.A.R.T. data in tlp-stat.
-
-```
-$ sudo dnf install smartmontools
-```
-
-For **`Debian/Ubuntu`** systems, use **[APT-GET Command][7]** or **[APT Command][8]** to install TLP.
-
-```
-$ sudo apt install tlp tlp-rdw
-```
-
-ThinkPads require an additional packages.
-
-```
-$ sudo apt-get install tp-smapi-dkms acpi-call-dkms
-```
-
-Install smartmontool to display S.M.A.R.T. data in tlp-stat.
-
-```
-$ sudo apt-get install smartmontools
-```
-
-When the official package becomes outdated for Ubuntu based systems then use the following PPA repository which provides an up-to-date version. Run the following commands to install TLP using the PPA.
-
-```
-$ sudo apt-get install tlp tlp-rdw
-```
-
-For **`Arch Linux`** based systems, use **[Pacman Command][9]** to install TLP.
-
-```
-$ sudo pacman -S tlp tlp-rdw
-```
-
-ThinkPads require an additional packages.
-
-```
-$ pacman -S tp_smapi acpi_call
-```
-
-Install smartmontool to display S.M.A.R.T. data in tlp-stat.
-
-```
-$ sudo pacman -S smartmontools
-```
-
-Enable TLP & TLP-Sleep service on boot for Arch Linux based systems.
-
-```
-$ sudo systemctl enable tlp.service
-$ sudo systemctl enable tlp-sleep.service
-```
-
-You should also mask the following services to avoid conflicts and assure proper operation of TLP’s radio device switching options for Arch Linux based systems.
-
-```
-$ sudo systemctl mask systemd-rfkill.service
-$ sudo systemctl mask systemd-rfkill.socket
-```
-
-For **`RHEL/CentOS`** systems, use **[YUM Command][10]** to install TLP.
-
-```
-$ sudo yum install tlp tlp-rdw
-```
-
-Install smartmontool to display S.M.A.R.T. data in tlp-stat.
-
-```
-$ sudo yum install smartmontools
-```
-
-For **`openSUSE Leap`** system, use **[Zypper Command][11]** to install TLP.
-
-```
-$ sudo zypper install TLP
-```
-
-Install smartmontool to display S.M.A.R.T. data in tlp-stat.
-
-```
-$ sudo zypper install smartmontools
-```
-
-After successfully TLP installed, use the following command to start the service.
-
-```
-$ systemctl start tlp.service
-```
-
-To show battery information.
-
-```
-$ sudo tlp-stat -b
-or
-$ sudo tlp-stat --battery
-
---- TLP 1.1 --------------------------------------------
-
-+++ Battery Status
-/sys/class/power_supply/BAT0/manufacturer = SMP
-/sys/class/power_supply/BAT0/model_name = L14M4P23
-/sys/class/power_supply/BAT0/cycle_count = (not supported)
-/sys/class/power_supply/BAT0/energy_full_design = 60000 [mWh]
-/sys/class/power_supply/BAT0/energy_full = 48850 [mWh]
-/sys/class/power_supply/BAT0/energy_now = 48850 [mWh]
-/sys/class/power_supply/BAT0/power_now = 0 [mW]
-/sys/class/power_supply/BAT0/status = Full
-
-Charge = 100.0 [%]
-Capacity = 81.4 [%]
-```
-
-To show disk information.
-
-```
-$ sudo tlp-stat -d
-or
-$ sudo tlp-stat --disk
-
---- TLP 1.1 --------------------------------------------
-
-+++ Storage Devices
-/dev/sda:
- Model = WDC WD10SPCX-24HWST1
- Firmware = 02.01A02
- APM Level = 128
- Status = active/idle
- Scheduler = mq-deadline
-
- Runtime PM: control = on, autosuspend_delay = (not available)
-
- SMART info:
- 4 Start_Stop_Count = 18787
- 5 Reallocated_Sector_Ct = 0
- 9 Power_On_Hours = 606 [h]
- 12 Power_Cycle_Count = 1792
- 193 Load_Cycle_Count = 25775
- 194 Temperature_Celsius = 31 [°C]
-
-
-+++ AHCI Link Power Management (ALPM)
-/sys/class/scsi_host/host0/link_power_management_policy = med_power_with_dipm
-/sys/class/scsi_host/host1/link_power_management_policy = med_power_with_dipm
-/sys/class/scsi_host/host2/link_power_management_policy = med_power_with_dipm
-/sys/class/scsi_host/host3/link_power_management_policy = med_power_with_dipm
-
-+++ AHCI Host Controller Runtime Power Management
-/sys/bus/pci/devices/0000:00:17.0/ata1/power/control = on
-/sys/bus/pci/devices/0000:00:17.0/ata2/power/control = on
-/sys/bus/pci/devices/0000:00:17.0/ata3/power/control = on
-/sys/bus/pci/devices/0000:00:17.0/ata4/power/control = on
-```
-
-To show PCI device information.
-
-```
-$ sudo tlp-stat -e
-or
-$ sudo tlp-stat --pcie
-
---- TLP 1.1 --------------------------------------------
-
-+++ Runtime Power Management
-Device blacklist = (not configured)
-Driver blacklist = amdgpu nouveau nvidia radeon pcieport
-
-/sys/bus/pci/devices/0000:00:00.0/power/control = auto (0x060000, Host bridge, skl_uncore)
-/sys/bus/pci/devices/0000:00:01.0/power/control = auto (0x060400, PCI bridge, pcieport)
-/sys/bus/pci/devices/0000:00:02.0/power/control = auto (0x030000, VGA compatible controller, i915)
-/sys/bus/pci/devices/0000:00:14.0/power/control = auto (0x0c0330, USB controller, xhci_hcd)
-/sys/bus/pci/devices/0000:00:16.0/power/control = auto (0x078000, Communication controller, mei_me)
-/sys/bus/pci/devices/0000:00:17.0/power/control = auto (0x010601, SATA controller, ahci)
-/sys/bus/pci/devices/0000:00:1c.0/power/control = auto (0x060400, PCI bridge, pcieport)
-/sys/bus/pci/devices/0000:00:1c.2/power/control = auto (0x060400, PCI bridge, pcieport)
-/sys/bus/pci/devices/0000:00:1c.3/power/control = auto (0x060400, PCI bridge, pcieport)
-/sys/bus/pci/devices/0000:00:1d.0/power/control = auto (0x060400, PCI bridge, pcieport)
-/sys/bus/pci/devices/0000:00:1f.0/power/control = auto (0x060100, ISA bridge, no driver)
-/sys/bus/pci/devices/0000:00:1f.2/power/control = auto (0x058000, Memory controller, no driver)
-/sys/bus/pci/devices/0000:00:1f.3/power/control = auto (0x040300, Audio device, snd_hda_intel)
-/sys/bus/pci/devices/0000:00:1f.4/power/control = auto (0x0c0500, SMBus, i801_smbus)
-/sys/bus/pci/devices/0000:01:00.0/power/control = auto (0x030200, 3D controller, nouveau)
-/sys/bus/pci/devices/0000:07:00.0/power/control = auto (0x080501, SD Host controller, sdhci-pci)
-/sys/bus/pci/devices/0000:08:00.0/power/control = auto (0x028000, Network controller, iwlwifi)
-/sys/bus/pci/devices/0000:09:00.0/power/control = auto (0x020000, Ethernet controller, r8168)
-/sys/bus/pci/devices/0000:0a:00.0/power/control = auto (0x010802, Non-Volatile memory controller, nvme)
-```
-
-To show graphics card information.
-
-```
-$ sudo tlp-stat -g
-or
-$ sudo tlp-stat --graphics
-
---- TLP 1.1 --------------------------------------------
-
-+++ Intel Graphics
-/sys/module/i915/parameters/enable_dc = -1 (use per-chip default)
-/sys/module/i915/parameters/enable_fbc = 1 (enabled)
-/sys/module/i915/parameters/enable_psr = 0 (disabled)
-/sys/module/i915/parameters/modeset = -1 (use per-chip default)
-```
-
-To show Processor information.
-
-```
-$ sudo tlp-stat -p
-or
-$ sudo tlp-stat --processor
-
---- TLP 1.1 --------------------------------------------
-
-+++ Processor
-CPU model = Intel(R) Core(TM) i7-6700HQ CPU @ 2.60GHz
-
-/sys/devices/system/cpu/cpu0/cpufreq/scaling_driver = intel_pstate
-/sys/devices/system/cpu/cpu0/cpufreq/scaling_governor = powersave
-/sys/devices/system/cpu/cpu0/cpufreq/scaling_available_governors = performance powersave
-/sys/devices/system/cpu/cpu0/cpufreq/scaling_min_freq = 800000 [kHz]
-/sys/devices/system/cpu/cpu0/cpufreq/scaling_max_freq = 3500000 [kHz]
-/sys/devices/system/cpu/cpu0/cpufreq/energy_performance_preference = balance_power
-/sys/devices/system/cpu/cpu0/cpufreq/energy_performance_available_preferences = default performance balance_performance balance_power power
-
-/sys/devices/system/cpu/cpu1/cpufreq/scaling_driver = intel_pstate
-/sys/devices/system/cpu/cpu1/cpufreq/scaling_governor = powersave
-/sys/devices/system/cpu/cpu1/cpufreq/scaling_available_governors = performance powersave
-/sys/devices/system/cpu/cpu1/cpufreq/scaling_min_freq = 800000 [kHz]
-/sys/devices/system/cpu/cpu1/cpufreq/scaling_max_freq = 3500000 [kHz]
-/sys/devices/system/cpu/cpu1/cpufreq/energy_performance_preference = balance_power
-/sys/devices/system/cpu/cpu1/cpufreq/energy_performance_available_preferences = default performance balance_performance balance_power power
-
-/sys/devices/system/cpu/cpu2/cpufreq/scaling_driver = intel_pstate
-/sys/devices/system/cpu/cpu2/cpufreq/scaling_governor = powersave
-/sys/devices/system/cpu/cpu2/cpufreq/scaling_available_governors = performance powersave
-/sys/devices/system/cpu/cpu2/cpufreq/scaling_min_freq = 800000 [kHz]
-/sys/devices/system/cpu/cpu2/cpufreq/scaling_max_freq = 3500000 [kHz]
-/sys/devices/system/cpu/cpu2/cpufreq/energy_performance_preference = balance_power
-/sys/devices/system/cpu/cpu2/cpufreq/energy_performance_available_preferences = default performance balance_performance balance_power power
-
-/sys/devices/system/cpu/cpu3/cpufreq/scaling_driver = intel_pstate
-/sys/devices/system/cpu/cpu3/cpufreq/scaling_governor = powersave
-/sys/devices/system/cpu/cpu3/cpufreq/scaling_available_governors = performance powersave
-/sys/devices/system/cpu/cpu3/cpufreq/scaling_min_freq = 800000 [kHz]
-/sys/devices/system/cpu/cpu3/cpufreq/scaling_max_freq = 3500000 [kHz]
-/sys/devices/system/cpu/cpu3/cpufreq/energy_performance_preference = balance_power
-/sys/devices/system/cpu/cpu3/cpufreq/energy_performance_available_preferences = default performance balance_performance balance_power power
-
-/sys/devices/system/cpu/cpu4/cpufreq/scaling_driver = intel_pstate
-/sys/devices/system/cpu/cpu4/cpufreq/scaling_governor = powersave
-/sys/devices/system/cpu/cpu4/cpufreq/scaling_available_governors = performance powersave
-/sys/devices/system/cpu/cpu4/cpufreq/scaling_min_freq = 800000 [kHz]
-/sys/devices/system/cpu/cpu4/cpufreq/scaling_max_freq = 3500000 [kHz]
-/sys/devices/system/cpu/cpu4/cpufreq/energy_performance_preference = balance_power
-/sys/devices/system/cpu/cpu4/cpufreq/energy_performance_available_preferences = default performance balance_performance balance_power power
-
-/sys/devices/system/cpu/cpu5/cpufreq/scaling_driver = intel_pstate
-/sys/devices/system/cpu/cpu5/cpufreq/scaling_governor = powersave
-/sys/devices/system/cpu/cpu5/cpufreq/scaling_available_governors = performance powersave
-/sys/devices/system/cpu/cpu5/cpufreq/scaling_min_freq = 800000 [kHz]
-/sys/devices/system/cpu/cpu5/cpufreq/scaling_max_freq = 3500000 [kHz]
-/sys/devices/system/cpu/cpu5/cpufreq/energy_performance_preference = balance_power
-/sys/devices/system/cpu/cpu5/cpufreq/energy_performance_available_preferences = default performance balance_performance balance_power power
-
-/sys/devices/system/cpu/cpu6/cpufreq/scaling_driver = intel_pstate
-/sys/devices/system/cpu/cpu6/cpufreq/scaling_governor = powersave
-/sys/devices/system/cpu/cpu6/cpufreq/scaling_available_governors = performance powersave
-/sys/devices/system/cpu/cpu6/cpufreq/scaling_min_freq = 800000 [kHz]
-/sys/devices/system/cpu/cpu6/cpufreq/scaling_max_freq = 3500000 [kHz]
-/sys/devices/system/cpu/cpu6/cpufreq/energy_performance_preference = balance_power
-/sys/devices/system/cpu/cpu6/cpufreq/energy_performance_available_preferences = default performance balance_performance balance_power power
-
-/sys/devices/system/cpu/cpu7/cpufreq/scaling_driver = intel_pstate
-/sys/devices/system/cpu/cpu7/cpufreq/scaling_governor = powersave
-/sys/devices/system/cpu/cpu7/cpufreq/scaling_available_governors = performance powersave
-/sys/devices/system/cpu/cpu7/cpufreq/scaling_min_freq = 800000 [kHz]
-/sys/devices/system/cpu/cpu7/cpufreq/scaling_max_freq = 3500000 [kHz]
-/sys/devices/system/cpu/cpu7/cpufreq/energy_performance_preference = balance_power
-/sys/devices/system/cpu/cpu7/cpufreq/energy_performance_available_preferences = default performance balance_performance balance_power power
-
-/sys/devices/system/cpu/intel_pstate/min_perf_pct = 22 [%]
-/sys/devices/system/cpu/intel_pstate/max_perf_pct = 100 [%]
-/sys/devices/system/cpu/intel_pstate/no_turbo = 0
-/sys/devices/system/cpu/intel_pstate/turbo_pct = 33 [%]
-/sys/devices/system/cpu/intel_pstate/num_pstates = 28
-
-x86_energy_perf_policy: program not installed.
-
-/sys/module/workqueue/parameters/power_efficient = Y
-/proc/sys/kernel/nmi_watchdog = 0
-
-+++ Undervolting
-PHC kernel not available.
-```
-
-To show system data information.
-
-```
-$ sudo tlp-stat -s
-or
-$ sudo tlp-stat --system
-
---- TLP 1.1 --------------------------------------------
-
-+++ System Info
-System = LENOVO Lenovo ideapad Y700-15ISK 80NV
-BIOS = CDCN35WW
-Release = "Manjaro Linux"
-Kernel = 4.19.6-1-MANJARO #1 SMP PREEMPT Sat Dec 1 12:21:26 UTC 2018 x86_64
-/proc/cmdline = BOOT_IMAGE=/boot/vmlinuz-4.19-x86_64 root=UUID=69d9dd18-36be-4631-9ebb-78f05fe3217f rw quiet resume=UUID=a2092b92-af29-4760-8e68-7a201922573b
-Init system = systemd
-Boot mode = BIOS (CSM, Legacy)
-
-+++ TLP Status
-State = enabled
-Last run = 11:04:00 IST, 596 sec(s) ago
-Mode = battery
-Power source = battery
-```
-
-To show temperatures and fan speed information.
-
-```
-$ sudo tlp-stat -t
-or
-$ sudo tlp-stat --temp
-
---- TLP 1.1 --------------------------------------------
-
-+++ Temperatures
-CPU temp = 36 [°C]
-Fan speed = (not available)
-```
-
-To show USB device data information.
-
-```
-$ sudo tlp-stat -u
-or
-$ sudo tlp-stat --usb
-
---- TLP 1.1 --------------------------------------------
-
-+++ USB
-Autosuspend = disabled
-Device whitelist = (not configured)
-Device blacklist = (not configured)
-Bluetooth blacklist = disabled
-Phone blacklist = disabled
-WWAN blacklist = enabled
-
-Bus 002 Device 001 ID 1d6b:0003 control = auto, autosuspend_delay_ms = 0 -- Linux Foundation 3.0 root hub (hub)
-Bus 001 Device 003 ID 174f:14e8 control = auto, autosuspend_delay_ms = 2000 -- Syntek (uvcvideo)
-Bus 001 Device 002 ID 17ef:6053 control = on, autosuspend_delay_ms = 2000 -- Lenovo (usbhid)
-Bus 001 Device 004 ID 8087:0a2b control = auto, autosuspend_delay_ms = 2000 -- Intel Corp. (btusb)
-Bus 001 Device 001 ID 1d6b:0002 control = auto, autosuspend_delay_ms = 0 -- Linux Foundation 2.0 root hub (hub)
-```
-
-To show warnings.
-
-```
-$ sudo tlp-stat -w
-or
-$ sudo tlp-stat --warn
-
---- TLP 1.1 --------------------------------------------
-
-No warnings detected.
-```
-
-Status report with configuration and all active settings.
-
-```
-$ sudo tlp-stat
-
---- TLP 1.1 --------------------------------------------
-
-+++ Configured Settings: /etc/default/tlp
-TLP_ENABLE=1
-TLP_DEFAULT_MODE=AC
-TLP_PERSISTENT_DEFAULT=0
-DISK_IDLE_SECS_ON_AC=0
-DISK_IDLE_SECS_ON_BAT=2
-MAX_LOST_WORK_SECS_ON_AC=15
-MAX_LOST_WORK_SECS_ON_BAT=60
-CPU_HWP_ON_AC=balance_performance
-CPU_HWP_ON_BAT=balance_power
-SCHED_POWERSAVE_ON_AC=0
-SCHED_POWERSAVE_ON_BAT=1
-NMI_WATCHDOG=0
-ENERGY_PERF_POLICY_ON_AC=performance
-ENERGY_PERF_POLICY_ON_BAT=power
-DISK_DEVICES="sda sdb"
-DISK_APM_LEVEL_ON_AC="254 254"
-DISK_APM_LEVEL_ON_BAT="128 128"
-SATA_LINKPWR_ON_AC="med_power_with_dipm max_performance"
-SATA_LINKPWR_ON_BAT="med_power_with_dipm max_performance"
-AHCI_RUNTIME_PM_TIMEOUT=15
-PCIE_ASPM_ON_AC=performance
-PCIE_ASPM_ON_BAT=powersave
-RADEON_POWER_PROFILE_ON_AC=default
-RADEON_POWER_PROFILE_ON_BAT=low
-RADEON_DPM_STATE_ON_AC=performance
-RADEON_DPM_STATE_ON_BAT=battery
-RADEON_DPM_PERF_LEVEL_ON_AC=auto
-RADEON_DPM_PERF_LEVEL_ON_BAT=auto
-WIFI_PWR_ON_AC=off
-WIFI_PWR_ON_BAT=on
-WOL_DISABLE=Y
-SOUND_POWER_SAVE_ON_AC=0
-SOUND_POWER_SAVE_ON_BAT=1
-SOUND_POWER_SAVE_CONTROLLER=Y
-BAY_POWEROFF_ON_AC=0
-BAY_POWEROFF_ON_BAT=0
-BAY_DEVICE="sr0"
-RUNTIME_PM_ON_AC=on
-RUNTIME_PM_ON_BAT=auto
-RUNTIME_PM_DRIVER_BLACKLIST="amdgpu nouveau nvidia radeon pcieport"
-USB_AUTOSUSPEND=0
-USB_BLACKLIST_BTUSB=0
-USB_BLACKLIST_PHONE=0
-USB_BLACKLIST_PRINTER=1
-USB_BLACKLIST_WWAN=1
-RESTORE_DEVICE_STATE_ON_STARTUP=0
-
-+++ System Info
-System = LENOVO Lenovo ideapad Y700-15ISK 80NV
-BIOS = CDCN35WW
-Release = "Manjaro Linux"
-Kernel = 4.19.6-1-MANJARO #1 SMP PREEMPT Sat Dec 1 12:21:26 UTC 2018 x86_64
-/proc/cmdline = BOOT_IMAGE=/boot/vmlinuz-4.19-x86_64 root=UUID=69d9dd18-36be-4631-9ebb-78f05fe3217f rw quiet resume=UUID=a2092b92-af29-4760-8e68-7a201922573b
-Init system = systemd
-Boot mode = BIOS (CSM, Legacy)
-
-+++ TLP Status
-State = enabled
-Last run = 11:04:00 IST, 684 sec(s) ago
-Mode = battery
-Power source = battery
-
-+++ Processor
-CPU model = Intel(R) Core(TM) i7-6700HQ CPU @ 2.60GHz
-
-/sys/devices/system/cpu/cpu0/cpufreq/scaling_driver = intel_pstate
-/sys/devices/system/cpu/cpu0/cpufreq/scaling_governor = powersave
-/sys/devices/system/cpu/cpu0/cpufreq/scaling_available_governors = performance powersave
-/sys/devices/system/cpu/cpu0/cpufreq/scaling_min_freq = 800000 [kHz]
-/sys/devices/system/cpu/cpu0/cpufreq/scaling_max_freq = 3500000 [kHz]
-/sys/devices/system/cpu/cpu0/cpufreq/energy_performance_preference = balance_power
-/sys/devices/system/cpu/cpu0/cpufreq/energy_performance_available_preferences = default performance balance_performance balance_power power
-
-/sys/devices/system/cpu/cpu1/cpufreq/scaling_driver = intel_pstate
-/sys/devices/system/cpu/cpu1/cpufreq/scaling_governor = powersave
-/sys/devices/system/cpu/cpu1/cpufreq/scaling_available_governors = performance powersave
-/sys/devices/system/cpu/cpu1/cpufreq/scaling_min_freq = 800000 [kHz]
-/sys/devices/system/cpu/cpu1/cpufreq/scaling_max_freq = 3500000 [kHz]
-/sys/devices/system/cpu/cpu1/cpufreq/energy_performance_preference = balance_power
-/sys/devices/system/cpu/cpu1/cpufreq/energy_performance_available_preferences = default performance balance_performance balance_power power
-
-/sys/devices/system/cpu/cpu2/cpufreq/scaling_driver = intel_pstate
-/sys/devices/system/cpu/cpu2/cpufreq/scaling_governor = powersave
-/sys/devices/system/cpu/cpu2/cpufreq/scaling_available_governors = performance powersave
-/sys/devices/system/cpu/cpu2/cpufreq/scaling_min_freq = 800000 [kHz]
-/sys/devices/system/cpu/cpu2/cpufreq/scaling_max_freq = 3500000 [kHz]
-/sys/devices/system/cpu/cpu2/cpufreq/energy_performance_preference = balance_power
-/sys/devices/system/cpu/cpu2/cpufreq/energy_performance_available_preferences = default performance balance_performance balance_power power
-
-/sys/devices/system/cpu/cpu3/cpufreq/scaling_driver = intel_pstate
-/sys/devices/system/cpu/cpu3/cpufreq/scaling_governor = powersave
-/sys/devices/system/cpu/cpu3/cpufreq/scaling_available_governors = performance powersave
-/sys/devices/system/cpu/cpu3/cpufreq/scaling_min_freq = 800000 [kHz]
-/sys/devices/system/cpu/cpu3/cpufreq/scaling_max_freq = 3500000 [kHz]
-/sys/devices/system/cpu/cpu3/cpufreq/energy_performance_preference = balance_power
-/sys/devices/system/cpu/cpu3/cpufreq/energy_performance_available_preferences = default performance balance_performance balance_power power
-
-/sys/devices/system/cpu/cpu4/cpufreq/scaling_driver = intel_pstate
-/sys/devices/system/cpu/cpu4/cpufreq/scaling_governor = powersave
-/sys/devices/system/cpu/cpu4/cpufreq/scaling_available_governors = performance powersave
-/sys/devices/system/cpu/cpu4/cpufreq/scaling_min_freq = 800000 [kHz]
-/sys/devices/system/cpu/cpu4/cpufreq/scaling_max_freq = 3500000 [kHz]
-/sys/devices/system/cpu/cpu4/cpufreq/energy_performance_preference = balance_power
-/sys/devices/system/cpu/cpu4/cpufreq/energy_performance_available_preferences = default performance balance_performance balance_power power
-
-/sys/devices/system/cpu/cpu5/cpufreq/scaling_driver = intel_pstate
-/sys/devices/system/cpu/cpu5/cpufreq/scaling_governor = powersave
-/sys/devices/system/cpu/cpu5/cpufreq/scaling_available_governors = performance powersave
-/sys/devices/system/cpu/cpu5/cpufreq/scaling_min_freq = 800000 [kHz]
-/sys/devices/system/cpu/cpu5/cpufreq/scaling_max_freq = 3500000 [kHz]
-/sys/devices/system/cpu/cpu5/cpufreq/energy_performance_preference = balance_power
-/sys/devices/system/cpu/cpu5/cpufreq/energy_performance_available_preferences = default performance balance_performance balance_power power
-
-/sys/devices/system/cpu/cpu6/cpufreq/scaling_driver = intel_pstate
-/sys/devices/system/cpu/cpu6/cpufreq/scaling_governor = powersave
-/sys/devices/system/cpu/cpu6/cpufreq/scaling_available_governors = performance powersave
-/sys/devices/system/cpu/cpu6/cpufreq/scaling_min_freq = 800000 [kHz]
-/sys/devices/system/cpu/cpu6/cpufreq/scaling_max_freq = 3500000 [kHz]
-/sys/devices/system/cpu/cpu6/cpufreq/energy_performance_preference = balance_power
-/sys/devices/system/cpu/cpu6/cpufreq/energy_performance_available_preferences = default performance balance_performance balance_power power
-
-/sys/devices/system/cpu/cpu7/cpufreq/scaling_driver = intel_pstate
-/sys/devices/system/cpu/cpu7/cpufreq/scaling_governor = powersave
-/sys/devices/system/cpu/cpu7/cpufreq/scaling_available_governors = performance powersave
-/sys/devices/system/cpu/cpu7/cpufreq/scaling_min_freq = 800000 [kHz]
-/sys/devices/system/cpu/cpu7/cpufreq/scaling_max_freq = 3500000 [kHz]
-/sys/devices/system/cpu/cpu7/cpufreq/energy_performance_preference = balance_power
-/sys/devices/system/cpu/cpu7/cpufreq/energy_performance_available_preferences = default performance balance_performance balance_power power
-
-/sys/devices/system/cpu/intel_pstate/min_perf_pct = 22 [%]
-/sys/devices/system/cpu/intel_pstate/max_perf_pct = 100 [%]
-/sys/devices/system/cpu/intel_pstate/no_turbo = 0
-/sys/devices/system/cpu/intel_pstate/turbo_pct = 33 [%]
-/sys/devices/system/cpu/intel_pstate/num_pstates = 28
-
-x86_energy_perf_policy: program not installed.
-
-/sys/module/workqueue/parameters/power_efficient = Y
-/proc/sys/kernel/nmi_watchdog = 0
-
-+++ Undervolting
-PHC kernel not available.
-
-+++ Temperatures
-CPU temp = 42 [°C]
-Fan speed = (not available)
-
-+++ File System
-/proc/sys/vm/laptop_mode = 2
-/proc/sys/vm/dirty_writeback_centisecs = 6000
-/proc/sys/vm/dirty_expire_centisecs = 6000
-/proc/sys/vm/dirty_ratio = 20
-/proc/sys/vm/dirty_background_ratio = 10
-
-+++ Storage Devices
-/dev/sda:
- Model = WDC WD10SPCX-24HWST1
- Firmware = 02.01A02
- APM Level = 128
- Status = active/idle
- Scheduler = mq-deadline
-
- Runtime PM: control = on, autosuspend_delay = (not available)
-
- SMART info:
- 4 Start_Stop_Count = 18787
- 5 Reallocated_Sector_Ct = 0
- 9 Power_On_Hours = 606 [h]
- 12 Power_Cycle_Count = 1792
- 193 Load_Cycle_Count = 25777
- 194 Temperature_Celsius = 31 [°C]
-
-
-+++ AHCI Link Power Management (ALPM)
-/sys/class/scsi_host/host0/link_power_management_policy = med_power_with_dipm
-/sys/class/scsi_host/host1/link_power_management_policy = med_power_with_dipm
-/sys/class/scsi_host/host2/link_power_management_policy = med_power_with_dipm
-/sys/class/scsi_host/host3/link_power_management_policy = med_power_with_dipm
-
-+++ AHCI Host Controller Runtime Power Management
-/sys/bus/pci/devices/0000:00:17.0/ata1/power/control = on
-/sys/bus/pci/devices/0000:00:17.0/ata2/power/control = on
-/sys/bus/pci/devices/0000:00:17.0/ata3/power/control = on
-/sys/bus/pci/devices/0000:00:17.0/ata4/power/control = on
-
-+++ PCIe Active State Power Management
-/sys/module/pcie_aspm/parameters/policy = powersave
-
-+++ Intel Graphics
-/sys/module/i915/parameters/enable_dc = -1 (use per-chip default)
-/sys/module/i915/parameters/enable_fbc = 1 (enabled)
-/sys/module/i915/parameters/enable_psr = 0 (disabled)
-/sys/module/i915/parameters/modeset = -1 (use per-chip default)
-
-+++ Wireless
-bluetooth = on
-wifi = on
-wwan = none (no device)
-
-hci0(btusb) : bluetooth, not connected
-wlp8s0(iwlwifi) : wifi, connected, power management = on
-
-+++ Audio
-/sys/module/snd_hda_intel/parameters/power_save = 1
-/sys/module/snd_hda_intel/parameters/power_save_controller = Y
-
-+++ Runtime Power Management
-Device blacklist = (not configured)
-Driver blacklist = amdgpu nouveau nvidia radeon pcieport
-
-/sys/bus/pci/devices/0000:00:00.0/power/control = auto (0x060000, Host bridge, skl_uncore)
-/sys/bus/pci/devices/0000:00:01.0/power/control = auto (0x060400, PCI bridge, pcieport)
-/sys/bus/pci/devices/0000:00:02.0/power/control = auto (0x030000, VGA compatible controller, i915)
-/sys/bus/pci/devices/0000:00:14.0/power/control = auto (0x0c0330, USB controller, xhci_hcd)
-/sys/bus/pci/devices/0000:00:16.0/power/control = auto (0x078000, Communication controller, mei_me)
-/sys/bus/pci/devices/0000:00:17.0/power/control = auto (0x010601, SATA controller, ahci)
-/sys/bus/pci/devices/0000:00:1c.0/power/control = auto (0x060400, PCI bridge, pcieport)
-/sys/bus/pci/devices/0000:00:1c.2/power/control = auto (0x060400, PCI bridge, pcieport)
-/sys/bus/pci/devices/0000:00:1c.3/power/control = auto (0x060400, PCI bridge, pcieport)
-/sys/bus/pci/devices/0000:00:1d.0/power/control = auto (0x060400, PCI bridge, pcieport)
-/sys/bus/pci/devices/0000:00:1f.0/power/control = auto (0x060100, ISA bridge, no driver)
-/sys/bus/pci/devices/0000:00:1f.2/power/control = auto (0x058000, Memory controller, no driver)
-/sys/bus/pci/devices/0000:00:1f.3/power/control = auto (0x040300, Audio device, snd_hda_intel)
-/sys/bus/pci/devices/0000:00:1f.4/power/control = auto (0x0c0500, SMBus, i801_smbus)
-/sys/bus/pci/devices/0000:01:00.0/power/control = auto (0x030200, 3D controller, nouveau)
-/sys/bus/pci/devices/0000:07:00.0/power/control = auto (0x080501, SD Host controller, sdhci-pci)
-/sys/bus/pci/devices/0000:08:00.0/power/control = auto (0x028000, Network controller, iwlwifi)
-/sys/bus/pci/devices/0000:09:00.0/power/control = auto (0x020000, Ethernet controller, r8168)
-/sys/bus/pci/devices/0000:0a:00.0/power/control = auto (0x010802, Non-Volatile memory controller, nvme)
-
-+++ USB
-Autosuspend = disabled
-Device whitelist = (not configured)
-Device blacklist = (not configured)
-Bluetooth blacklist = disabled
-Phone blacklist = disabled
-WWAN blacklist = enabled
-
-Bus 002 Device 001 ID 1d6b:0003 control = auto, autosuspend_delay_ms = 0 -- Linux Foundation 3.0 root hub (hub)
-Bus 001 Device 003 ID 174f:14e8 control = auto, autosuspend_delay_ms = 2000 -- Syntek (uvcvideo)
-Bus 001 Device 002 ID 17ef:6053 control = on, autosuspend_delay_ms = 2000 -- Lenovo (usbhid)
-Bus 001 Device 004 ID 8087:0a2b control = auto, autosuspend_delay_ms = 2000 -- Intel Corp. (btusb)
-Bus 001 Device 001 ID 1d6b:0002 control = auto, autosuspend_delay_ms = 0 -- Linux Foundation 2.0 root hub (hub)
-
-+++ Battery Status
-/sys/class/power_supply/BAT0/manufacturer = SMP
-/sys/class/power_supply/BAT0/model_name = L14M4P23
-/sys/class/power_supply/BAT0/cycle_count = (not supported)
-/sys/class/power_supply/BAT0/energy_full_design = 60000 [mWh]
-/sys/class/power_supply/BAT0/energy_full = 51690 [mWh]
-/sys/class/power_supply/BAT0/energy_now = 50140 [mWh]
-/sys/class/power_supply/BAT0/power_now = 12185 [mW]
-/sys/class/power_supply/BAT0/status = Discharging
-
-Charge = 97.0 [%]
-Capacity = 86.2 [%]
-```
-
---------------------------------------------------------------------------------
-
-via: https://www.2daygeek.com/tlp-increase-optimize-linux-laptop-battery-life/
-
-作者:[Magesh Maruthamuthu][a]
-选题:[lujun9972][b]
-译者:[译者ID](https://github.com/译者ID)
-校对:[校对者ID](https://github.com/校对者ID)
-
-本文由 [LCTT](https://github.com/LCTT/TranslateProject) 原创编译,[Linux中国](https://linux.cn/) 荣誉推出
-
-[a]: https://www.2daygeek.com/author/magesh/
-[b]: https://github.com/lujun9972
-[1]: https://www.2daygeek.com/check-laptop-battery-status-and-charging-state-in-linux-terminal/
-[2]: https://www.2daygeek.com/powertop-monitors-laptop-battery-usage-linux/
-[3]: https://www.2daygeek.com/monitor-laptop-battery-charging-state-linux/
-[4]: https://linrunner.de/en/tlp/docs/tlp-linux-advanced-power-management.html
-[5]: https://www.2daygeek.com/category/package-management/
-[6]: https://www.2daygeek.com/dnf-command-examples-manage-packages-fedora-system/
-[7]: https://www.2daygeek.com/apt-get-apt-cache-command-examples-manage-packages-debian-ubuntu-systems/
-[8]: https://www.2daygeek.com/apt-command-examples-manage-packages-debian-ubuntu-systems/
-[9]: https://www.2daygeek.com/pacman-command-examples-manage-packages-arch-linux-system/
-[10]: https://www.2daygeek.com/yum-command-examples-manage-packages-rhel-centos-systems/
-[11]: https://www.2daygeek.com/zypper-command-examples-manage-packages-opensuse-system/
diff --git a/sources/tech/20181218 Using Pygame to move your game character around.md b/sources/tech/20181218 Using Pygame to move your game character around.md
deleted file mode 100644
index 96daf8da7d..0000000000
--- a/sources/tech/20181218 Using Pygame to move your game character around.md
+++ /dev/null
@@ -1,353 +0,0 @@
-[#]: collector: (lujun9972)
-[#]: translator: ( )
-[#]: reviewer: ( )
-[#]: publisher: ( )
-[#]: url: ( )
-[#]: subject: (Using Pygame to move your game character around)
-[#]: via: (https://opensource.com/article/17/12/game-python-moving-player)
-[#]: author: (Seth Kenlon https://opensource.com/users/seth)
-
-Using Pygame to move your game character around
-======
-In the fourth part of this series, learn how to code the controls needed to move a game character.
-
-
-In the first article in this series, I explained how to use Python to create a simple, [text-based dice game][1]. In the second part, we began building a game from scratch, starting with [creating the game's environment][2]. And, in the third installment, we [created a player sprite][3] and made it spawn in your (rather empty) game world. As you've probably noticed, a game isn't much fun if you can't move your character around. In this article, we'll use Pygame to add keyboard controls so you can direct your character's movement.
-
-There are functions in Pygame to add other kinds of controls, but since you certainly have a keyboard if you're typing out Python code, that's what we'll use. Once you understand keyboard controls, you can explore other options on your own.
-
-You created a key to quit your game in the second article in this series, and the principle is the same for movement. However, getting your character to move is a little more complex.
-
-Let's start with the easy part: setting up the controller keys.
-
-### Setting up keys for controlling your player sprite
-
-Open your Python game script in IDLE, Ninja-IDE, or a text editor.
-
-Since the game must constantly "listen" for keyboard events, you'll be writing code that needs to run continuously. Can you figure out where to put code that needs to run constantly for the duration of the game?
-
-If you answered "in the main loop," you're correct! Remember that unless code is in a loop, it will run (at most) only once—and it may not run at all if it's hidden away in a class or function that never gets used.
-
-To make Python monitor for incoming key presses, add this code to the main loop. There's no code to make anything happen yet, so use `print` statements to signal success. This is a common debugging technique.
-
-```
-while main == True:
- for event in pygame.event.get():
- if event.type == pygame.QUIT:
- pygame.quit(); sys.exit()
- main = False
-
- if event.type == pygame.KEYDOWN:
- if event.key == pygame.K_LEFT or event.key == ord('a'):
- print('left')
- if event.key == pygame.K_RIGHT or event.key == ord('d'):
- print('right')
- if event.key == pygame.K_UP or event.key == ord('w'):
- print('jump')
-
- if event.type == pygame.KEYUP:
- if event.key == pygame.K_LEFT or event.key == ord('a'):
- print('left stop')
- if event.key == pygame.K_RIGHT or event.key == ord('d'):
- print('right stop')
- if event.key == ord('q'):
- pygame.quit()
- sys.exit()
- main = False
-```
-
-Some people prefer to control player characters with the keyboard characters W, A, S, and D, and others prefer to use arrow keys. Be sure to include both options.
-
-**Note: **It's vital that you consider all of your users when programming. If you write code that works only for you, it's very likely that you'll be the only one who uses your application. More importantly, if you seek out a job writing code for money, you are expected to write code that works for everyone. Giving your users choices, such as the option to use either arrow keys or WASD, is a sign of a good programmer.
-
-Launch your game using Python, and watch the console window for output as you press the right, left, and up arrows, or the A, D, and W keys.
-
-```
-$ python ./your-name_game.py
- left
- left stop
- right
- right stop
- jump
-```
-
-This confirms that Pygame detects key presses correctly. Now it's time to do the hard work of making the sprite move.
-
-### Coding the player movement function
-
-To make your sprite move, you must create a property for your sprite that represents movement. When your sprite is not moving, this variable is set to `0`.
-
-If you are animating your sprite, or should you decide to animate it in the future, you also must track frames to enable the walk cycle to stay on track.
-
-Create the variables in the Player class. The first two lines are for context (you already have them in your code, if you've been following along), so add only the last three:
-
-```
- def __init__(self):
- pygame.sprite.Sprite.__init__(self)
- self.movex = 0 # move along X
- self.movey = 0 # move along Y
- self.frame = 0 # count frames
-```
-
-With those variables set, it's time to code the sprite's movement.
-
-The player sprite doesn't need to respond to control all the time; sometimes it will not be moving. The code that controls the sprite, therefore, is only one small part of all the things the player sprite will do. When you want to make an object in Python do something independent of the rest of its code, you place your new code in a function. Python functions start with the keyword `def`, which stands for define.
-
-Make a function in your Player class to add some number of pixels to your sprite's position on screen. Don't worry about how many pixels you add yet; that will be decided in later code.
-
-```
- def control(self,x,y):
- '''
- control player movement
- '''
- self.movex += x
- self.movey += y
-```
-
-To move a sprite in Pygame, you have to tell Python to redraw the sprite in its new location—and where that new location is.
-
-Since the Player sprite isn't always moving, the updates need to be only one function within the Player class. Add this function after the `control` function you created earlier.
-
-To make it appear that the sprite is walking (or flying, or whatever it is your sprite is supposed to do), you need to change its position on screen when the appropriate key is pressed. To get it to move across the screen, you redefine its position, designated by the `self.rect.x` and `self.rect.y` properties, to its current position plus whatever amount of `movex` or `movey` is applied. (The number of pixels the move requires is set later.)
-
-```
- def update(self):
- '''
- Update sprite position
- '''
- self.rect.x = self.rect.x + self.movex
-```
-
-Do the same thing for the Y position:
-
-```
- self.rect.y = self.rect.y + self.movey
-```
-
-For animation, advance the animation frames whenever your sprite is moving, and use the corresponding animation frame as the player image:
-
-```
- # moving left
- if self.movex < 0:
- self.frame += 1
- if self.frame > 3*ani:
- self.frame = 0
- self.image = self.images[self.frame//ani]
-
- # moving right
- if self.movex > 0:
- self.frame += 1
- if self.frame > 3*ani:
- self.frame = 0
- self.image = self.images[(self.frame//ani)+4]
-```
-
-Tell the code how many pixels to add to your sprite's position by setting a variable, then use that variable when triggering the functions of your Player sprite.
-
-First, create the variable in your setup section. In this code, the first two lines are for context, so just add the third line to your script:
-
-```
-player_list = pygame.sprite.Group()
-player_list.add(player)
-steps = 10 # how many pixels to move
-```
-
-Now that you have the appropriate function and variable, use your key presses to trigger the function and send the variable to your sprite.
-
-Do this by replacing the `print` statements in your main loop with the Player sprite's name (player), the function (.control), and how many steps along the X axis and Y axis you want the player sprite to move with each loop.
-
-```
- if event.type == pygame.KEYDOWN:
- if event.key == pygame.K_LEFT or event.key == ord('a'):
- player.control(-steps,0)
- if event.key == pygame.K_RIGHT or event.key == ord('d'):
- player.control(steps,0)
- if event.key == pygame.K_UP or event.key == ord('w'):
- print('jump')
-
- if event.type == pygame.KEYUP:
- if event.key == pygame.K_LEFT or event.key == ord('a'):
- player.control(steps,0)
- if event.key == pygame.K_RIGHT or event.key == ord('d'):
- player.control(-steps,0)
- if event.key == ord('q'):
- pygame.quit()
- sys.exit()
- main = False
-```
-
-Remember, `steps` is a variable representing how many pixels your sprite moves when a key is pressed. If you add 10 pixels to the location of your player sprite when you press D or the right arrow, then when you stop pressing that key you must subtract 10 (`-steps`) to return your sprite's momentum back to 0.
-
-Try your game now. Warning: it won't do what you expect.
-
-Why doesn't your sprite move yet? Because the main loop doesn't call the `update` function.
-
-Add code to your main loop to tell Python to update the position of your player sprite. Add the line with the comment:
-
-```
- player.update() # update player position
- player_list.draw(world)
- pygame.display.flip()
- clock.tick(fps)
-```
-
-Launch your game again to witness your player sprite move across the screen at your bidding. There's no vertical movement yet because those functions will be controlled by gravity, but that's another lesson for another article.
-
-In the meantime, if you have access to a joystick, try reading Pygame's documentation for its [joystick][4] module and see if you can make your sprite move that way. Alternately, see if you can get the [mouse][5] to interact with your sprite.
-
-Most importantly, have fun!
-
-### All the code used in this tutorial
-
-For your reference, here is all the code used in this series of articles so far.
-
-```
-#!/usr/bin/env python3
-# draw a world
-# add a player and player control
-# add player movement
-
-# GNU All-Permissive License
-# Copying and distribution of this file, with or without modification,
-# are permitted in any medium without royalty provided the copyright
-# notice and this notice are preserved. This file is offered as-is,
-# without any warranty.
-
-import pygame
-import sys
-import os
-
-'''
-Objects
-'''
-
-class Player(pygame.sprite.Sprite):
- '''
- Spawn a player
- '''
- def __init__(self):
- pygame.sprite.Sprite.__init__(self)
- self.movex = 0
- self.movey = 0
- self.frame = 0
- self.images = []
- for i in range(1,5):
- img = pygame.image.load(os.path.join('images','hero' + str(i) + '.png')).convert()
- img.convert_alpha()
- img.set_colorkey(ALPHA)
- self.images.append(img)
- self.image = self.images[0]
- self.rect = self.image.get_rect()
-
- def control(self,x,y):
- '''
- control player movement
- '''
- self.movex += x
- self.movey += y
-
- def update(self):
- '''
- Update sprite position
- '''
-
- self.rect.x = self.rect.x + self.movex
- self.rect.y = self.rect.y + self.movey
-
- # moving left
- if self.movex < 0:
- self.frame += 1
- if self.frame > 3*ani:
- self.frame = 0
- self.image = self.images[self.frame//ani]
-
- # moving right
- if self.movex > 0:
- self.frame += 1
- if self.frame > 3*ani:
- self.frame = 0
- self.image = self.images[(self.frame//ani)+4]
-
-
-'''
-Setup
-'''
-worldx = 960
-worldy = 720
-
-fps = 40 # frame rate
-ani = 4 # animation cycles
-clock = pygame.time.Clock()
-pygame.init()
-main = True
-
-BLUE = (25,25,200)
-BLACK = (23,23,23 )
-WHITE = (254,254,254)
-ALPHA = (0,255,0)
-
-world = pygame.display.set_mode([worldx,worldy])
-backdrop = pygame.image.load(os.path.join('images','stage.png')).convert()
-backdropbox = world.get_rect()
-player = Player() # spawn player
-player.rect.x = 0
-player.rect.y = 0
-player_list = pygame.sprite.Group()
-player_list.add(player)
-steps = 10 # how fast to move
-
-'''
-Main loop
-'''
-while main == True:
- for event in pygame.event.get():
- if event.type == pygame.QUIT:
- pygame.quit(); sys.exit()
- main = False
-
- if event.type == pygame.KEYDOWN:
- if event.key == pygame.K_LEFT or event.key == ord('a'):
- player.control(-steps,0)
- if event.key == pygame.K_RIGHT or event.key == ord('d'):
- player.control(steps,0)
- if event.key == pygame.K_UP or event.key == ord('w'):
- print('jump')
-
- if event.type == pygame.KEYUP:
- if event.key == pygame.K_LEFT or event.key == ord('a'):
- player.control(steps,0)
- if event.key == pygame.K_RIGHT or event.key == ord('d'):
- player.control(-steps,0)
- if event.key == ord('q'):
- pygame.quit()
- sys.exit()
- main = False
-
-# world.fill(BLACK)
- world.blit(backdrop, backdropbox)
- player.update()
- player_list.draw(world) #refresh player position
- pygame.display.flip()
- clock.tick(fps)
-```
-
-You've come far and learned much, but there's a lot more to do. In the next few articles, you'll add enemy sprites, emulated gravity, and lots more. In the mean time, practice with Python!
-
---------------------------------------------------------------------------------
-
-via: https://opensource.com/article/17/12/game-python-moving-player
-
-作者:[Seth Kenlon][a]
-选题:[lujun9972][b]
-译者:[译者ID](https://github.com/译者ID)
-校对:[校对者ID](https://github.com/校对者ID)
-
-本文由 [LCTT](https://github.com/LCTT/TranslateProject) 原创编译,[Linux中国](https://linux.cn/) 荣誉推出
-
-[a]: https://opensource.com/users/seth
-[b]: https://github.com/lujun9972
-[1]: https://opensource.com/article/17/10/python-101
-[2]: https://opensource.com/article/17/12/program-game-python-part-2-creating-game-world
-[3]: https://opensource.com/article/17/12/program-game-python-part-3-spawning-player
-[4]: http://pygame.org/docs/ref/joystick.html
-[5]: http://pygame.org/docs/ref/mouse.html#module-pygame.mouse
diff --git a/sources/tech/20190107 Aliases- To Protect and Serve.md b/sources/tech/20190107 Aliases- To Protect and Serve.md
deleted file mode 100644
index 783c59dc41..0000000000
--- a/sources/tech/20190107 Aliases- To Protect and Serve.md
+++ /dev/null
@@ -1,176 +0,0 @@
-[#]: collector: (lujun9972)
-[#]: translator: ( )
-[#]: reviewer: ( )
-[#]: publisher: ( )
-[#]: url: ( )
-[#]: subject: (Aliases: To Protect and Serve)
-[#]: via: (https://www.linux.com/blog/learn/2019/1/aliases-protect-and-serve)
-[#]: author: (Paul Brown https://www.linux.com/users/bro66)
-
-Aliases: To Protect and Serve
-======
-
-
-
-Happy 2019! Here in the new year, we’re continuing our series on aliases. By now, you’ve probably read our [first article on aliases][1], and it should be quite clear how they are the easiest way to save yourself a lot of trouble. You already saw, for example, that they helped with muscle-memory, but let's see several other cases in which aliases come in handy.
-
-### Aliases as Shortcuts
-
-One of the most beautiful things about Linux's shells is how you can use zillions of options and chain commands together to carry out really sophisticated operations in one fell swoop. All right, maybe beauty is in the eye of the beholder, but let's agree that this feature published practical.
-
-The downside is that you often come up with recipes that are often hard to remember or cumbersome to type. Say space on your hard disk is at a premium and you want to do some New Year's cleaning. Your first step may be to look for stuff to get rid off in you home directory. One criteria you could apply is to look for stuff you don't use anymore. `ls` can help with that:
-
-```
-ls -lct
-```
-
-The instruction above shows the details of each file and directory (`-l`) and also shows when each item was last accessed (`-c`). It then orders the list from most recently accessed to least recently accessed (`-t`).
-
-Is this hard to remember? You probably don’t use the `-c` and `-t` options every day, so perhaps. In any case, defining an alias like
-
-```
-alias lt='ls -lct'
-```
-
-will make it easier.
-
-Then again, you may want to have the list show the oldest files first:
-
-```
-alias lo='lt -F | tac'
-```
-
-![aliases][3]
-
-Figure 1: The lt and lo aliases in action.
-
-[Used with permission][4]
-
-There are a few interesting things going here. First, we are using an alias (`lt`) to create another alias -- which is perfectly okay. Second, we are passing a new parameter to `lt` (which, in turn gets passed to `ls` through the definition of the `lt` alias).
-
-The `-F` option appends special symbols to the names of items to better differentiate regular files (that get no symbol) from executable files (that get an `*`), files from directories (end in `/`), and all of the above from links, symbolic and otherwise (that end in an `@` symbol). The `-F` option is throwback to the days when terminals where monochrome and there was no other way to easily see the difference between items. You use it here because, when you pipe the output from `lt` through to `tac` you lose the colors from `ls`.
-
-The third thing to pay attention to is the use of piping. Piping happens when you pass the output from an instruction to another instruction. The second instruction can then use that output as its own input. In many shells (including Bash), you pipe something using the pipe symbol (`|`).
-
-In this case, you are piping the output from `lt -F` into `tac`. `tac`'s name is a bit of a joke. You may have heard of `cat`, the instruction that was nominally created to con _cat_ enate files together, but that in practice is used to print out the contents of a file to the terminal. `tac` does the same, but prints out the contents it receives in reverse order. Get it? `cat` and `tac`. Developers, you so funny!
-
-The thing is both `cat` and `tac` can also print out stuff piped over from another instruction, in this case, a list of files ordered chronologically.
-
-So... after that digression, what comes out of the other end is the list of files and directories of the current directory in inverse order of freshness.
-
-The final thing you have to bear in mind is that, while `lt` will work the current directory and any other directory...
-
-```
-# This will work:
-lt
-# And so will this:
-lt /some/other/directory
-```
-
-... `lo` will only work with the current directory:
-
-```
-# This will work:
-lo
-# But this won't:
-lo /some/other/directory
-```
-
-This is because Bash expands aliases into their components. When you type this:
-
-```
-lt /some/other/directory
-```
-
-Bash REALLY runs this:
-
-```
-ls -lct /some/other/directory
-```
-
-which is a valid Bash command.
-
-However, if you type this:
-
-```
-lo /some/other/directory
-```
-
-Bash tries to run this:
-
-```
-ls -lct -F | tac /some/other/directory
-```
-
-which is not a valid instruction, because `tac` mainly because _/some/other/directory_ is a directory, and `cat` and `tac` don't do directories.
-
-### More Alias Shortcuts
-
- * `alias lll='ls -R'` prints out the contents of a directory and then drills down and prints out the contents of its subdirectories and the subdirectories of the subdirectories, and so on and so forth. It is a way of seeing everything you have under a directory.
-
- * `mkdir='mkdir -pv'` let's you make directories within directories all in one go. With the base form of `mkdir`, to make a new directory containing a subdirectory you have to do this:
-
-```
- mkdir newdir
-mkdir newdir/subdir
-```
-
-Or this:
-
-```
-mkdir -p newdir/subdir
-```
-
-while with the alias you would only have to do this:
-
-```
-mkdir newdir/subdir
-```
-
-Your new `mkdir` will also tell you what it is doing while is creating new directories.
-
-
-
-
-### Aliases as Safeguards
-
-The other thing aliases are good for is as safeguards against erasing or overwriting your files accidentally. At this stage you have probably heard the legendary story about the new Linux user who ran:
-
-```
-rm -rf /
-```
-
-as root, and nuked the whole system. Then there's the user who decided that:
-
-```
-rm -rf /some/directory/ *
-```
-
-was a good idea and erased the complete contents of their home directory. Notice how easy it is to overlook that space separating the directory path and the `*`.
-
-Both things can be avoided with the `alias rm='rm -i'` alias. The `-i` option makes `rm` ask the user whether that is what they really want to do and gives you a second chance before wreaking havoc in your file system.
-
-The same goes for `cp`, which can overwrite a file without telling you anything. Create an alias like `alias cp='cp -i'` and stay safe!
-
-### Next Time
-
-We are moving more and more into scripting territory. Next time, we'll take the next logical step and see how combining instructions on the command line gives you really interesting and sophisticated solutions to everyday admin problems.
-
-
---------------------------------------------------------------------------------
-
-via: https://www.linux.com/blog/learn/2019/1/aliases-protect-and-serve
-
-作者:[Paul Brown][a]
-选题:[lujun9972][b]
-译者:[译者ID](https://github.com/译者ID)
-校对:[校对者ID](https://github.com/校对者ID)
-
-本文由 [LCTT](https://github.com/LCTT/TranslateProject) 原创编译,[Linux中国](https://linux.cn/) 荣誉推出
-
-[a]: https://www.linux.com/users/bro66
-[b]: https://github.com/lujun9972
-[1]: https://www.linux.com/blog/learn/2019/1/aliases-protect-and-serve
-[2]: https://www.linux.com/files/images/fig01png-0
-[3]: https://www.linux.com/sites/lcom/files/styles/rendered_file/public/fig01_0.png?itok=crqTm_va (aliases)
-[4]: https://www.linux.com/licenses/category/used-permission
diff --git a/sources/tech/20190109 GoAccess - A Real-Time Web Server Log Analyzer And Interactive Viewer.md b/sources/tech/20190109 GoAccess - A Real-Time Web Server Log Analyzer And Interactive Viewer.md
deleted file mode 100644
index 3bad5ba969..0000000000
--- a/sources/tech/20190109 GoAccess - A Real-Time Web Server Log Analyzer And Interactive Viewer.md
+++ /dev/null
@@ -1,187 +0,0 @@
-[#]: collector: (lujun9972)
-[#]: translator: ( )
-[#]: reviewer: ( )
-[#]: publisher: ( )
-[#]: url: ( )
-[#]: subject: (GoAccess – A Real-Time Web Server Log Analyzer And Interactive Viewer)
-[#]: via: (https://www.2daygeek.com/goaccess-a-real-time-web-server-log-analyzer-and-interactive-viewer/)
-[#]: author: (Vinoth Kumar https://www.2daygeek.com/author/vinoth/)
-
-GoAccess – A Real-Time Web Server Log Analyzer And Interactive Viewer
-======
-
-Analyzing a log file is a big headache for Linux administrators as it’s capturing a lot of things.
-
-Most of the newbies and L1 administrators doesn’t know how to analyze this.
-
-If you have good knowledge to analyze a logs then you will be a legend for NIX system.
-
-There are many tools available in Linux to analyze the logs easily.
-
-GoAccess is one of the tool which allow users to analyze web server logs easily.
-
-We will be going to discuss in details about GoAccess tool in this article.
-
-### What is GoAccess?
-
-GoAccess is a real-time web log analyzer and interactive viewer that runs in a terminal in *nix systems or through your browser.
-
-GoAccess has minimal requirements, it’s written in C and requires only ncurses.
-
-It will support Apache, Nginx and Lighttpd logs. It provides fast and valuable HTTP statistics for system administrators that require a visual server report on the fly.
-
-GoAccess parses the specified web log file and outputs the data to the X terminal and browser.
-
-GoAccess was designed to be a fast, terminal-based log analyzer. Its core idea is to quickly analyze and view web server statistics in real time without needing to use your browser.
-
-Terminal output is the default output, it has the capability to generate a complete, self-contained, real-time HTML report, as well as a JSON, and CSV report.
-
-GoAccess allows any custom log format and the following (Combined Log Format (XLF/ELF) Apache | Nginx & Common Log Format (CLF) Apache) predefined log format options are included, but not limited to.
-
-### GoAccess Features
-
- * **`Completely Real Time:`** All the metrics are updated every 200 ms on the terminal and every second on the HTML output.
- * **`Track Application Response Time:`** Track the time taken to serve the request. Extremely useful if you want to track pages that are slowing down your site.
- * **`Visitors:`** Determine the amount of hits, visitors, bandwidth, and metrics for slowest running requests by the hour, or date.
- * **`Metrics per Virtual Host:`** Have multiple Virtual Hosts (Server Blocks)? It features a panel that displays which virtual host is consuming most of the web server resources.
-
-
-
-### How to Install GoAccess?
-
-I would advise users to install GoAccess from distribution official repository with help of Package Manager. It is available in most of the distributions official repository.
-
-As we know, we will be getting bit outdated package for standard release distribution and rolling release distributions always include latest package.
-
-If you are running the OS with standard release distributions, i would suggest you to check the alternative options such as PPA or Official GoAccess maintainer repository, etc, to get a latest package.
-
-For **`Debian/Ubuntu`** systems, use **[APT-GET Command][1]** or **[APT Command][2]** to install GoAccess on your systems.
-
-```
-# apt install goaccess
-```
-
-To get a latest GoAccess package, use the below GoAccess official repository.
-
-```
-$ echo "deb https://deb.goaccess.io/ $(lsb_release -cs) main" | sudo tee -a /etc/apt/sources.list.d/goaccess.list
-$ wget -O - https://deb.goaccess.io/gnugpg.key | sudo apt-key add -
-$ sudo apt-get update
-$ sudo apt-get install goaccess
-```
-
-For **`RHEL/CentOS`** systems, use **[YUM Package Manager][3]** to install GoAccess on your systems.
-
-```
-# yum install goaccess
-```
-
-For **`Fedora`** system, use **[DNF Package Manager][4]** to install GoAccess on your system.
-
-```
-# dnf install goaccess
-```
-
-For **`ArchLinux/Manjaro`** based systems, use **[Pacman Package Manager][5]** to install GoAccess on your systems.
-
-```
-# pacman -S goaccess
-```
-
-For **`openSUSE Leap`** system, use **[Zypper Package Manager][6]** to install GoAccess on your system.
-
-```
-# zypper install goaccess
-
-# zypper ar -f obs://server:http
-
-# zypper ref && zypper in goaccess
-```
-
-### How to Use GoAccess?
-
-After successful installation of GoAccess. Just enter the goaccess command and followed by the web server log location to view it.
-
-```
-# goaccess [options] /path/to/Web Server/access.log
-
-# goaccess /var/log/apache/2daygeek_access.log
-```
-
-When you execute the above command, it will ask you to select the **Log Format Configuration**.
-![][8]
-
-I had tested this with Apache access log. The Apache log is splitted in fifteen section. The details are below. The main section shows the summary about the fifteen section.
-
-The below screenshots included four sessions such as Unique Visitors, Requested files, Static Requests, Not found URLs.
-![][9]
-
-The below screenshots included four sessions such as Visitor Hostnames and IPs, Operating Systems, Browsers, Time Distribution.
-![][10]
-
-The below screenshots included four sessions such as Referrers URLs, Referring Sites, Google’s search engine results, HTTP status codes.
-![][11]
-
-If you would like to generate a html report, use the following format.
-
-Initially i got an error when i was trying to generate the html report.
-
-```
-# goaccess 2daygeek_access.log -a > report.html
-
-GoAccess - version 1.3 - Nov 23 2018 11:28:19
-Config file: No config file used
-
-Fatal error has occurred
-Error occurred at: src/parser.c - parse_log - 2764
-No time format was found on your conf file.Parsing... [0] [0/s]
-```
-
-It says “No time format was found on your conf file”. To overcome this issue, add the “COMBINED” log format option on it.
-
-```
-# goaccess -f 2daygeek_access.log --log-format=COMBINED -o 2daygeek.html
-Parsing...[0,165] [50,165/s]
-```
-
-![][12]
-
-GoAccess allows you to access and analyze the real-time log filtering and parsing.
-
-```
-# tail -f /var/log/apache/2daygeek_access.log | goaccess -
-```
-
-For more details navigate to man or help page.
-
-```
-# man goaccess
-or
-# goaccess --help
-```
-
---------------------------------------------------------------------------------
-
-via: https://www.2daygeek.com/goaccess-a-real-time-web-server-log-analyzer-and-interactive-viewer/
-
-作者:[Vinoth Kumar][a]
-选题:[lujun9972][b]
-译者:[译者ID](https://github.com/译者ID)
-校对:[校对者ID](https://github.com/校对者ID)
-
-本文由 [LCTT](https://github.com/LCTT/TranslateProject) 原创编译,[Linux中国](https://linux.cn/) 荣誉推出
-
-[a]: https://www.2daygeek.com/author/vinoth/
-[b]: https://github.com/lujun9972
-[1]: https://www.2daygeek.com/apt-get-apt-cache-command-examples-manage-packages-debian-ubuntu-systems/
-[2]: https://www.2daygeek.com/apt-command-examples-manage-packages-debian-ubuntu-systems/
-[3]: https://www.2daygeek.com/yum-command-examples-manage-packages-rhel-centos-systems/
-[4]: https://www.2daygeek.com/dnf-command-examples-manage-packages-fedora-system/
-[5]: https://www.2daygeek.com/pacman-command-examples-manage-packages-arch-linux-system/
-[6]: https://www.2daygeek.com/zypper-command-examples-manage-packages-opensuse-system/
-[7]: data:image/gif;base64,R0lGODlhAQABAIAAAAAAAP///yH5BAEAAAAALAAAAAABAAEAAAIBRAA7
-[8]: https://www.2daygeek.com/wp-content/uploads/2019/01/goaccess-a-real-time-web-server-log-analyzer-and-interactive-viewer-1.png
-[9]: https://www.2daygeek.com/wp-content/uploads/2019/01/goaccess-a-real-time-web-server-log-analyzer-and-interactive-viewer-2.png
-[10]: https://www.2daygeek.com/wp-content/uploads/2019/01/goaccess-a-real-time-web-server-log-analyzer-and-interactive-viewer-3.png
-[11]: https://www.2daygeek.com/wp-content/uploads/2019/01/goaccess-a-real-time-web-server-log-analyzer-and-interactive-viewer-4.png
-[12]: https://www.2daygeek.com/wp-content/uploads/2019/01/goaccess-a-real-time-web-server-log-analyzer-and-interactive-viewer-5.png
diff --git a/sources/tech/20190111 Top 5 Linux Distributions for Productivity.md b/sources/tech/20190111 Top 5 Linux Distributions for Productivity.md
index fbd8b9d120..725f3bcccb 100644
--- a/sources/tech/20190111 Top 5 Linux Distributions for Productivity.md
+++ b/sources/tech/20190111 Top 5 Linux Distributions for Productivity.md
@@ -1,5 +1,5 @@
[#]: collector: (lujun9972)
-[#]: translator: ( )
+[#]: translator: (qfzy1233)
[#]: reviewer: ( )
[#]: publisher: ( )
[#]: url: ( )
diff --git a/sources/tech/20190219 5 Good Open Source Speech Recognition-Speech-to-Text Systems.md b/sources/tech/20190219 5 Good Open Source Speech Recognition-Speech-to-Text Systems.md
deleted file mode 100644
index c7609f5022..0000000000
--- a/sources/tech/20190219 5 Good Open Source Speech Recognition-Speech-to-Text Systems.md
+++ /dev/null
@@ -1,131 +0,0 @@
-[#]: collector: (lujun9972)
-[#]: translator: ( )
-[#]: reviewer: ( )
-[#]: publisher: ( )
-[#]: url: ( )
-[#]: subject: (5 Good Open Source Speech Recognition/Speech-to-Text Systems)
-[#]: via: (https://fosspost.org/lists/open-source-speech-recognition-speech-to-text)
-[#]: author: (Simon James https://fosspost.org/author/simonjames)
-
-5 Good Open Source Speech Recognition/Speech-to-Text Systems
-======
-
-
-
-A speech-to-text (STT) system is as its name implies; A way of transforming the spoken words via sound into textual files that can be used later for any purpose.
-
-Speech-to-text technology is extremely useful. It can be used for a lot of applications such as a automation of transcription, writing books/texts using your own sound only, enabling complicated analyses on information using the generated textual files and a lot of other things.
-
-In the past, the speech-to-text technology was dominated by proprietary software and libraries; Open source alternatives didn’t exist or existed with extreme limitations and no community around. This is changing, today there are a lot of open source speech-to-text tools and libraries that you can use right now.
-
-Here we list 5 of them.
-
-### Open Source Speech Recognition Libraries
-
-#### Project DeepSpeech
-
-![5 Good Open Source Speech Recognition/Speech-to-Text Systems 15 open source speech recognition][1]
-
-This project is made by Mozilla; The organization behind the Firefox browser. It’s a 100% free and open source speech-to-text library that also implies the machine learning technology using TensorFlow framework to fulfill its mission.
-
-In other words, you can use it to build training models yourself to enhance the underlying speech-to-text technology and get better results, or even to bring it to other languages if you want. You can also easily integrate it to your other machine learning projects that you are having on TensorFlow. Sadly it sounds like the project is currently only supporting English by default.
-
-It’s also available in many languages such as Python (3.6); Which allows you to have it working in seconds:
-
-```
-pip3 install deepspeech
-deepspeech --model models/output_graph.pbmm --alphabet models/alphabet.txt --lm models/lm.binary --trie models/trie --audio my_audio_file.wav
-```
-
-You can also install it using npm:
-
-```
-npm install deepspeech
-```
-
-For more information, refer to the [project’s homepage][2].
-
-#### Kaldi
-
-![5 Good Open Source Speech Recognition/Speech-to-Text Systems 17 open source speech recognition][3]
-
-Kaldi is an open source speech recognition software written in C++, and is released under the Apache public license. It works on Windows, macOS and Linux. Its development started back in 2009.
-
-Kaldi’s main features over some other speech recognition software is that it’s extendable and modular; The community is providing tons of 3rd-party modules that you can use for your tasks. Kaldi also supports deep neural networks, and offers an [excellent documentation on its website][4].
-
-While the code is mainly written in C++, it’s “wrapped” by Bash and Python scripts. So if you are looking just for the basic usage of converting speech to text, then you’ll find it easy to accomplish that via either Python or Bash.
-
-[Project’s homepage][5].
-
-#### Julius
-
-![5 Good Open Source Speech Recognition/Speech-to-Text Systems 19 open source speech recognition][6]
-
-Probably one of the oldest speech recognition software ever; It’s development started in 1991 at the University of Kyoto, and then its ownership was transferred to an independent project team in 2005.
-
-Julius main features include its ability to perform real-time STT processes, low memory usage (Less than 64MB for 20000 words), ability to produce N-best/Word-graph output, ability to work as a server unit and a lot more. This software was mainly built for academic and research purposes. It is written in C, and works on Linux, Windows, macOS and even Android (on smartphones).
-
-Currently it supports both English and Japanese languages only. The software is probably availbale to install easily in your Linux distribution’s repository; Just search for julius package in your package manager. The latest version was [released][7] around one and half months ago.
-
-[Project’s homepage][8].
-
-#### Wav2Letter++
-
-![5 Good Open Source Speech Recognition/Speech-to-Text Systems 21 open source speech recognition][9]
-
-If you are looking for something modern, then this one is for you. Wav2Letter++ is an open source speech recognition software that was released by Facebook’s AI Research Team just 2 months ago. The code is released under the BSD license.
-
-Facebook is [describing][10] its library as “the fastest state-of-the-art speech recognition system available”. The concepts on which this tool is built makes it optimized for performance by default; Facebook’s also-new machine learning library [FlashLight][11] is used as the underlying core of Wav2Letter++.
-
-Wav2Letter++ needs you first to build a training model for the language you desire by yourself in order to train the algorithms on it. No pre-built support of any language (including English) is available; It’s just a machine-learning-driven tool to convert speech to text. It was written in C++, hence the name (Wav2Letter++).
-
-[Project’s homepage][12].
-
-#### DeepSpeech2
-
-![5 Good Open Source Speech Recognition/Speech-to-Text Systems 23 open source speech recognition][13]
-
-Researchers at the Chinese giant Baidu are also working on their own speech-to-text engine, called DeepSpeech2. It’s an end-to-end open source engine that uses the “PaddlePaddle” deep learning framework for converting both English & Mandarin Chinese languages speeches into text. The code is released under BSD license.
-
-The engine can be trained on any model and for any language you desire. The models are not released with the code; You’ll have to build them yourself, just like the other software. DeepSpeech2’s source code is written in Python; So it should be easy for you to get familiar with it if that’s the language you use.
-
-[Project’s homepage][14].
-
-### Conclusion
-
-The speech recognition category is still mainly dominated by proprietary software giants like Google and IBM (which do provide their own closed-source commercial services for this), but the open source alternatives are promising. Those 5 open source speech recognition engines should get you going in building your application, all of them are still under heavy development by time. In few years, we expect open source to become the norm for those technologies just like in the other industries.
-
-If you have any other recommendations for this list, or comments in general, we’d love to hear them below!
-
-**
-
-Shares
-
-
---------------------------------------------------------------------------------
-
-via: https://fosspost.org/lists/open-source-speech-recognition-speech-to-text
-
-作者:[Simon James][a]
-选题:[lujun9972][b]
-译者:[译者ID](https://github.com/译者ID)
-校对:[校对者ID](https://github.com/校对者ID)
-
-本文由 [LCTT](https://github.com/LCTT/TranslateProject) 原创编译,[Linux中国](https://linux.cn/) 荣誉推出
-
-[a]: https://fosspost.org/author/simonjames
-[b]: https://github.com/lujun9972
-[1]: https://i0.wp.com/fosspost.org/wp-content/uploads/2019/02/hero_speech-machine-learning2.png?resize=820%2C280&ssl=1 (5 Good Open Source Speech Recognition/Speech-to-Text Systems 16 open source speech recognition)
-[2]: https://github.com/mozilla/DeepSpeech
-[3]: https://i0.wp.com/fosspost.org/wp-content/uploads/2019/02/Screenshot-at-2019-02-19-1134.png?resize=591%2C138&ssl=1 (5 Good Open Source Speech Recognition/Speech-to-Text Systems 18 open source speech recognition)
-[4]: http://kaldi-asr.org/doc/index.html
-[5]: http://kaldi-asr.org
-[6]: https://i2.wp.com/fosspost.org/wp-content/uploads/2019/02/mic_web.png?resize=385%2C100&ssl=1 (5 Good Open Source Speech Recognition/Speech-to-Text Systems 20 open source speech recognition)
-[7]: https://github.com/julius-speech/julius/releases
-[8]: https://github.com/julius-speech/julius
-[9]: https://i2.wp.com/fosspost.org/wp-content/uploads/2019/02/fully_convolutional_ASR.png?resize=850%2C177&ssl=1 (5 Good Open Source Speech Recognition/Speech-to-Text Systems 22 open source speech recognition)
-[10]: https://code.fb.com/ai-research/wav2letter/
-[11]: https://github.com/facebookresearch/flashlight
-[12]: https://github.com/facebookresearch/wav2letter
-[13]: https://i2.wp.com/fosspost.org/wp-content/uploads/2019/02/ds2.png?resize=850%2C313&ssl=1 (5 Good Open Source Speech Recognition/Speech-to-Text Systems 24 open source speech recognition)
-[14]: https://github.com/PaddlePaddle/DeepSpeech
diff --git a/sources/tech/20190308 Virtual filesystems in Linux- Why we need them and how they work.md b/sources/tech/20190308 Virtual filesystems in Linux- Why we need them and how they work.md
deleted file mode 100644
index 1114863bf7..0000000000
--- a/sources/tech/20190308 Virtual filesystems in Linux- Why we need them and how they work.md
+++ /dev/null
@@ -1,196 +0,0 @@
-[#]: collector: (lujun9972)
-[#]: translator: ( )
-[#]: reviewer: ( )
-[#]: publisher: ( )
-[#]: url: ( )
-[#]: subject: (Virtual filesystems in Linux: Why we need them and how they work)
-[#]: via: (https://opensource.com/article/19/3/virtual-filesystems-linux)
-[#]: author: (Alison Chariken )
-
-Virtual filesystems in Linux: Why we need them and how they work
-======
-Virtual filesystems are the magic abstraction that makes the "everything is a file" philosophy of Linux possible.
-
-
-What is a filesystem? According to early Linux contributor and author [Robert Love][1], "A filesystem is a hierarchical storage of data adhering to a specific structure." However, this description applies equally well to VFAT (Virtual File Allocation Table), Git, and [Cassandra][2] (a [NoSQL database][3]). So what distinguishes a filesystem?
-
-### Filesystem basics
-
-The Linux kernel requires that for an entity to be a filesystem, it must also implement the **open()** , **read()** , and **write()** methods on persistent objects that have names associated with them. From the point of view of [object-oriented programming][4], the kernel treats the generic filesystem as an abstract interface, and these big-three functions are "virtual," with no default definition. Accordingly, the kernel's default filesystem implementation is called a virtual filesystem (VFS).
-
-
-![][5]
-If we can open(), read(), and write(), it is a file as this console session shows.
-
-VFS underlies the famous observation that in Unix-like systems "everything is a file." Consider how weird it is that the tiny demo above featuring the character device /dev/console actually works. The image shows an interactive Bash session on a virtual teletype (tty). Sending a string into the virtual console device makes it appear on the virtual screen. VFS has other, even odder properties. For example, it's [possible to seek in them][6].
-
-The familiar filesystems like ext4, NFS, and /proc all provide definitions of the big-three functions in a C-language data structure called [file_operations][7] . In addition, particular filesystems extend and override the VFS functions in the familiar object-oriented way. As Robert Love points out, the abstraction of VFS enables Linux users to blithely copy files to and from foreign operating systems or abstract entities like pipes without worrying about their internal data format. On behalf of userspace, via a system call, a process can copy from a file into the kernel's data structures with the read() method of one filesystem, then use the write() method of another kind of filesystem to output the data.
-
-The function definitions that belong to the VFS base type itself are found in the [fs/*.c files][8] in kernel source, while the subdirectories of fs/ contain the specific filesystems. The kernel also contains filesystem-like entities such as cgroups, /dev, and tmpfs, which are needed early in the boot process and are therefore defined in the kernel's init/ subdirectory. Note that cgroups, /dev, and tmpfs do not call the file_operations big-three functions, but directly read from and write to memory instead.
-
-The diagram below roughly illustrates how userspace accesses various types of filesystems commonly mounted on Linux systems. Not shown are constructs like pipes, dmesg, and POSIX clocks that also implement struct file_operations and whose accesses therefore pass through the VFS layer.
-
-![How userspace accesses various types of filesystems][9]
-VFS are a "shim layer" between system calls and implementors of specific file_operations like ext4 and procfs. The file_operations functions can then communicate either with device-specific drivers or with memory accessors. tmpfs, devtmpfs and cgroups don't make use of file_operations but access memory directly.
-
-VFS's existence promotes code reuse, as the basic methods associated with filesystems need not be re-implemented by every filesystem type. Code reuse is a widely accepted software engineering best practice! Alas, if the reused code [introduces serious bugs][10], then all the implementations that inherit the common methods suffer from them.
-
-### /tmp: A simple tip
-
-An easy way to find out what VFSes are present on a system is to type **mount | grep -v sd | grep -v :/** , which will list all mounted filesystems that are not resident on a disk and not NFS on most computers. One of the listed VFS mounts will assuredly be /tmp, right?
-
-![Man with shocked expression][11]
-Everyone knows that keeping /tmp on a physical storage device is crazy! credit:
-
-Why is keeping /tmp on storage inadvisable? Because the files in /tmp are temporary(!), and storage devices are slower than memory, where tmpfs are created. Further, physical devices are more subject to wear from frequent writing than memory is. Last, files in /tmp may contain sensitive information, so having them disappear at every reboot is a feature.
-
-Unfortunately, installation scripts for some Linux distros still create /tmp on a storage device by default. Do not despair should this be the case with your system. Follow simple instructions on the always excellent [Arch Wiki][12] to fix the problem, keeping in mind that memory allocated to tmpfs is not available for other purposes. In other words, a system with a gigantic tmpfs with large files in it can run out of memory and crash. Another tip: when editing the /etc/fstab file, be sure to end it with a newline, as your system will not boot otherwise. (Guess how I know.)
-
-### /proc and /sys
-
-Besides /tmp, the VFSes with which most Linux users are most familiar are /proc and /sys. (/dev relies on shared memory and has no file_operations). Why two flavors? Let's have a look in more detail.
-
-The procfs offers a snapshot into the instantaneous state of the kernel and the processes that it controls for userspace. In /proc, the kernel publishes information about the facilities it provides, like interrupts, virtual memory, and the scheduler. In addition, /proc/sys is where the settings that are configurable via the [sysctl command][13] are accessible to userspace. Status and statistics on individual processes are reported in /proc/ directories.
-
-![Console][14]
-/proc/meminfo is an empty file that nonetheless contains valuable information.
-
-The behavior of /proc files illustrates how unlike on-disk filesystems VFS can be. On the one hand, /proc/meminfo contains the information presented by the command **free**. On the other hand, it's also empty! How can this be? The situation is reminiscent of a famous article written by Cornell University physicist N. David Mermin in 1985 called "[Is the moon there when nobody looks?][15] Reality and the quantum theory." The truth is that the kernel gathers statistics about memory when a process requests them from /proc, and there actually is nothing in the files in /proc when no one is looking. As [Mermin said][16], "It is a fundamental quantum doctrine that a measurement does not, in general, reveal a preexisting value of the measured property." (The answer to the question about the moon is left as an exercise.)
-
-![Full moon][17]
-The files in /proc are empty when no process accesses them. ([Source][18])
-
-The apparent emptiness of procfs makes sense, as the information available there is dynamic. The situation with sysfs is different. Let's compare how many files of at least one byte in size there are in /proc versus /sys.
-
-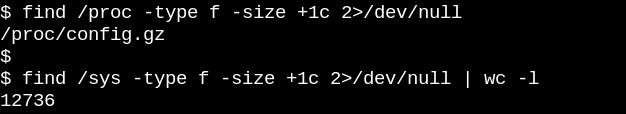
-
-Procfs has precisely one, namely the exported kernel configuration, which is an exception since it needs to be generated only once per boot. On the other hand, /sys has lots of larger files, most of which comprise one page of memory. Typically, sysfs files contain exactly one number or string, in contrast to the tables of information produced by reading files like /proc/meminfo.
-
-The purpose of sysfs is to expose the readable and writable properties of what the kernel calls "kobjects" to userspace. The only purpose of kobjects is reference-counting: when the last reference to a kobject is deleted, the system will reclaim the resources associated with it. Yet, /sys constitutes most of the kernel's famous "[stable ABI to userspace][19]" which [no one may ever, under any circumstances, "break."][20] That doesn't mean the files in sysfs are static, which would be contrary to reference-counting of volatile objects.
-
-The kernel's stable ABI instead constrains what can appear in /sys, not what is actually present at any given instant. Listing the permissions on files in sysfs gives an idea of how the configurable, tunable parameters of devices, modules, filesystems, etc. can be set or read. Logic compels the conclusion that procfs is also part of the kernel's stable ABI, although the kernel's [documentation][19] doesn't state so explicitly.
-
-![Console][21]
-Files in sysfs describe exactly one property each for an entity and may be readable, writable or both. The "0" in the file reveals that the SSD is not removable.
-
-### Snooping on VFS with eBPF and bcc tools
-
-The easiest way to learn how the kernel manages sysfs files is to watch it in action, and the simplest way to watch on ARM64 or x86_64 is to use eBPF. eBPF (extended Berkeley Packet Filter) consists of a [virtual machine running inside the kernel][22] that privileged users can query from the command line. Kernel source tells the reader what the kernel can do; running eBPF tools on a booted system shows instead what the kernel actually does.
-
-Happily, getting started with eBPF is pretty easy via the [bcc][23] tools, which are available as [packages from major Linux distros][24] and have been [amply documented][25] by Brendan Gregg. The bcc tools are Python scripts with small embedded snippets of C, meaning anyone who is comfortable with either language can readily modify them. At this count, [there are 80 Python scripts in bcc/tools][26], making it highly likely that a system administrator or developer will find an existing one relevant to her/his needs.
-
-To get a very crude idea about what work VFSes are performing on a running system, try the simple [vfscount][27] or [vfsstat][28], which show that dozens of calls to vfs_open() and its friends occur every second.
-
-![Console - vfsstat.py][29]
-vfsstat.py is a Python script with an embedded C snippet that simply counts VFS function calls.
-
-For a less trivial example, let's watch what happens in sysfs when a USB stick is inserted on a running system.
-
-![Console when USB is inserted][30]
-Watch with eBPF what happens in /sys when a USB stick is inserted, with simple and complex examples.
-
-In the first simple example above, the [trace.py][31] bcc tools script prints out a message whenever the sysfs_create_files() command runs. We see that sysfs_create_files() was started by a kworker thread in response to the USB stick insertion, but what file was created? The second example illustrates the full power of eBPF. Here, trace.py is printing the kernel backtrace (-K option) plus the name of the file created by sysfs_create_files(). The snippet inside the single quotes is some C source code, including an easily recognizable format string, that the provided Python script [induces a LLVM just-in-time compiler][32] to compile and execute inside an in-kernel virtual machine. The full sysfs_create_files() function signature must be reproduced in the second command so that the format string can refer to one of the parameters. Making mistakes in this C snippet results in recognizable C-compiler errors. For example, if the **-I** parameter is omitted, the result is "Failed to compile BPF text." Developers who are conversant with either C or Python will find the bcc tools easy to extend and modify.
-
-When the USB stick is inserted, the kernel backtrace appears showing that PID 7711 is a kworker thread that created a file called "events" in sysfs. A corresponding invocation with sysfs_remove_files() shows that removal of the USB stick results in removal of the events file, in keeping with the idea of reference counting. Watching sysfs_create_link() with eBPF during USB stick insertion (not shown) reveals that no fewer than 48 symbolic links are created.
-
-What is the purpose of the events file anyway? Using [cscope][33] to find the function [__device_add_disk()][34] reveals that it calls disk_add_events(), and either "media_change" or "eject_request" may be written to the events file. Here, the kernel's block layer is informing userspace about the appearance and disappearance of the "disk." Consider how quickly informative this method of investigating how USB stick insertion works is compared to trying to figure out the process solely from the source.
-
-### Read-only root filesystems make embedded devices possible
-
-Assuredly, no one shuts down a server or desktop system by pulling out the power plug. Why? Because mounted filesystems on the physical storage devices may have pending writes, and the data structures that record their state may become out of sync with what is written on the storage. When that happens, system owners will have to wait at next boot for the [fsck filesystem-recovery tool][35] to run and, in the worst case, will actually lose data.
-
-Yet, aficionados will have heard that many IoT and embedded devices like routers, thermostats, and automobiles now run Linux. Many of these devices almost entirely lack a user interface, and there's no way to "unboot" them cleanly. Consider jump-starting a car with a dead battery where the power to the [Linux-running head unit][36] goes up and down repeatedly. How is it that the system boots without a long fsck when the engine finally starts running? The answer is that embedded devices rely on [a read-only root fileystem][37] (ro-rootfs for short).
-
-![Photograph of a console][38]
-ro-rootfs are why embedded systems don't frequently need to fsck. Credit (with permission):
-
-A ro-rootfs offers many advantages that are less obvious than incorruptibility. One is that malware cannot write to /usr or /lib if no Linux process can write there. Another is that a largely immutable filesystem is critical for field support of remote devices, as support personnel possess local systems that are nominally identical to those in the field. Perhaps the most important (but also most subtle) advantage is that ro-rootfs forces developers to decide during a project's design phase which system objects will be immutable. Dealing with ro-rootfs may often be inconvenient or even painful, as [const variables in programming languages][39] often are, but the benefits easily repay the extra overhead.
-
-Creating a read-only rootfs does require some additional amount of effort for embedded developers, and that's where VFS comes in. Linux needs files in /var to be writable, and in addition, many popular applications that embedded systems run will try to create configuration dot-files in $HOME. One solution for configuration files in the home directory is typically to pregenerate them and build them into the rootfs. For /var, one approach is to mount it on a separate writable partition while / itself is mounted as read-only. Using bind or overlay mounts is another popular alternative.
-
-### Bind and overlay mounts and their use by containers
-
-Running **[man mount][40]** is the best place to learn about bind and overlay mounts, which give embedded developers and system administrators the power to create a filesystem in one path location and then provide it to applications at a second one. For embedded systems, the implication is that it's possible to store the files in /var on an unwritable flash device but overlay- or bind-mount a path in a tmpfs onto the /var path at boot so that applications can scrawl there to their heart's delight. At next power-on, the changes in /var will be gone. Overlay mounts provide a union between the tmpfs and the underlying filesystem and allow apparent modification to an existing file in a ro-rootfs, while bind mounts can make new empty tmpfs directories show up as writable at ro-rootfs paths. While overlayfs is a proper filesystem type, bind mounts are implemented by the [VFS namespace facility][41].
-
-Based on the description of overlay and bind mounts, no one will be surprised that [Linux containers][42] make heavy use of them. Let's spy on what happens when we employ [systemd-nspawn][43] to start up a container by running bcc's mountsnoop tool:
-
-![Console - system-nspawn invocation][44]
-The system-nspawn invocation fires up the container while mountsnoop.py runs.
-
-And let's see what happened:
-
-![Console - Running mountsnoop][45]
-Running mountsnoop during the container "boot" reveals that the container runtime relies heavily on bind mounts. (Only the beginning of the lengthy output is displayed)
-
-Here, systemd-nspawn is providing selected files in the host's procfs and sysfs to the container at paths in its rootfs. Besides the MS_BIND flag that sets bind-mounting, some of the other flags that the "mount" system call invokes determine the relationship between changes in the host namespace and in the container. For example, the bind-mount can either propagate changes in /proc and /sys to the container, or hide them, depending on the invocation.
-
-### Summary
-
-Understanding Linux internals can seem an impossible task, as the kernel itself contains a gigantic amount of code, leaving aside Linux userspace applications and the system-call interface in C libraries like glibc. One way to make progress is to read the source code of one kernel subsystem with an emphasis on understanding the userspace-facing system calls and headers plus major kernel internal interfaces, exemplified here by the file_operations table. The file operations are what makes "everything is a file" actually work, so getting a handle on them is particularly satisfying. The kernel C source files in the top-level fs/ directory constitute its implementation of virtual filesystems, which are the shim layer that enables broad and relatively straightforward interoperability of popular filesystems and storage devices. Bind and overlay mounts via Linux namespaces are the VFS magic that makes containers and read-only root filesystems possible. In combination with a study of source code, the eBPF kernel facility and its bcc interface makes probing the kernel simpler than ever before.
-
-Much thanks to [Akkana Peck][46] and [Michael Eager][47] for comments and corrections.
-
-Alison Chaiken will present [Virtual filesystems: why we need them and how they work][48] at the 17th annual Southern California Linux Expo ([SCaLE 17x][49]) March 7-10 in Pasadena, Calif.
-
---------------------------------------------------------------------------------
-
-via: https://opensource.com/article/19/3/virtual-filesystems-linux
-
-作者:[Alison Chariken][a]
-选题:[lujun9972][b]
-译者:[译者ID](https://github.com/译者ID)
-校对:[校对者ID](https://github.com/校对者ID)
-
-本文由 [LCTT](https://github.com/LCTT/TranslateProject) 原创编译,[Linux中国](https://linux.cn/) 荣誉推出
-
-[a]:
-[b]: https://github.com/lujun9972
-[1]: https://www.pearson.com/us/higher-education/program/Love-Linux-Kernel-Development-3rd-Edition/PGM202532.html
-[2]: http://cassandra.apache.org/
-[3]: https://en.wikipedia.org/wiki/NoSQL
-[4]: http://lwn.net/Articles/444910/
-[5]: https://opensource.com/sites/default/files/uploads/virtualfilesystems_1-console.png (Console)
-[6]: https://lwn.net/Articles/22355/
-[7]: https://git.kernel.org/pub/scm/linux/kernel/git/torvalds/linux.git/tree/include/linux/fs.h
-[8]: https://git.kernel.org/pub/scm/linux/kernel/git/torvalds/linux.git/tree/fs
-[9]: https://opensource.com/sites/default/files/uploads/virtualfilesystems_2-shim-layer.png (How userspace accesses various types of filesystems)
-[10]: https://lwn.net/Articles/774114/
-[11]: https://opensource.com/sites/default/files/uploads/virtualfilesystems_3-crazy.jpg (Man with shocked expression)
-[12]: https://wiki.archlinux.org/index.php/Tmpfs
-[13]: http://man7.org/linux/man-pages/man8/sysctl.8.html
-[14]: https://opensource.com/sites/default/files/uploads/virtualfilesystems_4-proc-meminfo.png (Console)
-[15]: http://www-f1.ijs.si/~ramsak/km1/mermin.moon.pdf
-[16]: https://en.wikiquote.org/wiki/David_Mermin
-[17]: https://opensource.com/sites/default/files/uploads/virtualfilesystems_5-moon.jpg (Full moon)
-[18]: https://commons.wikimedia.org/wiki/Moon#/media/File:Full_Moon_Luc_Viatour.jpg
-[19]: https://git.kernel.org/pub/scm/linux/kernel/git/torvalds/linux.git/tree/Documentation/ABI/stable
-[20]: https://lkml.org/lkml/2012/12/23/75
-[21]: https://opensource.com/sites/default/files/uploads/virtualfilesystems_7-sysfs.png (Console)
-[22]: https://events.linuxfoundation.org/sites/events/files/slides/bpf_collabsummit_2015feb20.pdf
-[23]: https://github.com/iovisor/bcc
-[24]: https://github.com/iovisor/bcc/blob/master/INSTALL.md
-[25]: http://brendangregg.com/ebpf.html
-[26]: https://github.com/iovisor/bcc/tree/master/tools
-[27]: https://github.com/iovisor/bcc/blob/master/tools/vfscount_example.txt
-[28]: https://github.com/iovisor/bcc/blob/master/tools/vfsstat.py
-[29]: https://opensource.com/sites/default/files/uploads/virtualfilesystems_8-vfsstat.png (Console - vfsstat.py)
-[30]: https://opensource.com/sites/default/files/uploads/virtualfilesystems_9-ebpf.png (Console when USB is inserted)
-[31]: https://github.com/iovisor/bcc/blob/master/tools/trace_example.txt
-[32]: https://events.static.linuxfound.org/sites/events/files/slides/bpf_collabsummit_2015feb20.pdf
-[33]: http://northstar-www.dartmouth.edu/doc/solaris-forte/manuals/c/user_guide/cscope.html
-[34]: https://git.kernel.org/pub/scm/linux/kernel/git/torvalds/linux.git/tree/block/genhd.c#n665
-[35]: http://www.man7.org/linux/man-pages/man8/fsck.8.html
-[36]: https://wiki.automotivelinux.org/_media/eg-rhsa/agl_referencehardwarespec_v0.1.0_20171018.pdf
-[37]: https://elinux.org/images/1/1f/Read-only_rootfs.pdf
-[38]: https://opensource.com/sites/default/files/uploads/virtualfilesystems_10-code.jpg (Photograph of a console)
-[39]: https://www.meetup.com/ACCU-Bay-Area/events/drpmvfytlbqb/
-[40]: http://man7.org/linux/man-pages/man8/mount.8.html
-[41]: https://git.kernel.org/pub/scm/linux/kernel/git/torvalds/linux.git/tree/Documentation/filesystems/sharedsubtree.txt
-[42]: https://coreos.com/os/docs/latest/kernel-modules.html
-[43]: https://www.freedesktop.org/software/systemd/man/systemd-nspawn.html
-[44]: https://opensource.com/sites/default/files/uploads/virtualfilesystems_11-system-nspawn.png (Console - system-nspawn invocation)
-[45]: https://opensource.com/sites/default/files/uploads/virtualfilesystems_12-mountsnoop.png (Console - Running mountsnoop)
-[46]: http://shallowsky.com/
-[47]: http://eagercon.com/
-[48]: https://www.socallinuxexpo.org/scale/17x/presentations/virtual-filesystems-why-we-need-them-and-how-they-work
-[49]: https://www.socallinuxexpo.org/
diff --git a/sources/tech/20190319 Blockchain 2.0- Blockchain In Real Estate -Part 4.md b/sources/tech/20190319 Blockchain 2.0- Blockchain In Real Estate -Part 4.md
deleted file mode 100644
index 56f8b8d8c1..0000000000
--- a/sources/tech/20190319 Blockchain 2.0- Blockchain In Real Estate -Part 4.md
+++ /dev/null
@@ -1,50 +0,0 @@
-[#]: collector: (lujun9972)
-[#]: translator: (sanfusu)
-[#]: reviewer: ( )
-[#]: publisher: ( )
-[#]: url: ( )
-[#]: subject: (Blockchain 2.0: Blockchain In Real Estate [Part 4])
-[#]: via: (https://www.ostechnix.com/blockchain-2-0-blockchain-in-real-estate/)
-[#]: author: (EDITOR https://www.ostechnix.com/author/editor/)
-
-Blockchain 2.0: Blockchain In Real Estate [Part 4]
-======
-
-
-
-### Blockchain 2.0: Smart‘er’ Real Estate
-
-The [**previous article**][1] of this series explored the features of blockchain which will enable institutions to transform and interlace **traditional banking** and **financing systems** with it. This part will explore – **Blockchain in real estate**. The real estate industry is ripe for a revolution. It’s among the most actively traded most significant asset classes known to man. However, filled with regulatory hurdles and numerous possibilities of fraud and deceit, it’s also one of the toughest to participate in. The distributed ledger capabilities of the blockchain utilizing an appropriate consensus algorithm are touted as the way forward for the industry which is traditionally regarded as conservative in its attitude to change.
-
-Real estate has always been a very conservative industry in terms of its myriad operations. Somewhat rightfully so as well. A major economic crisis such as the 2008 financial crisis or the great depression from the early half of the 20th century managed to destroy the industry and its participants. However, like most products of economic value, the real estate industry is resilient and this resilience is rooted in its conservative nature.
-
-The global real estate market comprises an asset class worth **$228 trillion dollars** [1]. Give or take. Other investment assets such as stocks, bonds, and shares combined are only worth **$170 trillion**. Obviously, any and all transactions implemented in such an industry is naturally carefully planned and meticulously executed, for the most part. For the most part, because real estate is also notorious for numerous instances of fraud and devastating loses which ensue them. The industry because of the very conservative nature of its operations is also tough to navigate. It’s heavily regulated with complex laws creating an intertwined web of nuances that are just too difficult for an average person to understand fully. This makes entry and participation near impossible for most people. If you’ve ever been involved in one such deal, you’ll know how heavy and long the paper trail was.
-
-This hard reality is now set to change, albeit a slow and gradual transformation. The very reasons the industry has stuck to its hardy tested roots all this while can finally give way to its modern-day counterpart. The backbone of the real estate industry has always been its paper records. Land deeds, titles, agreements, rental insurance, proofs, and declarations etc., are just the tip of the iceberg here. If you’ve noticed the pattern here, this should be obvious, the distributed ledger technology that is blockchain, fits in perfectly with the needs here. Forget paper records, conventional database systems are also points of major failure. They can be modified by multiple participants, is not tamper proof or un-hackable, has a complicated set of ever-changing regulatory parameters making auditing and verifying data a nightmare. The blockchain perfectly solves all of these issues and more.
-
-Starting with a trivial albeit an important example to show just how bad the current record management practices are in the real estate sector, consider the **Title Insurance business** [2], [3]. Title Insurance is used to hedge against the possibility of the land’s titles and ownership records being inadmissible and hence unenforceable. An insurance product such as this is also referred to as an indemnity cover. It is by law required in many cases that properties have title insurance, especially when dealing with property that has changed hands multiple times over the years. Mortgage firms might insist on the same as well when they back real estate deals. The fact that a product of this kind has existed since the 1850s and that it does business worth at least **$1.5 trillion a year in the US alone** is a testament to the statement at the start. A revolution in terms of how these records are maintained is imperative to have in this situation and the blockchain provides a sustainable solution. Title fraud averages around $100k per case on average as per the **American Land Title Association** and 25% of all titles involved in transactions have an issue regarding their documents[4]. The blockchain allows for setting up an immutable permanent database that will track the property itself, recording each and every transaction or investment that has gone into it. Such a ledger system will make life easier for everyone involved in the real estate industry including one-time home buyers and make financial products such as Title Insurance basically irrelevant. Converting a physical asset such as real estate to a digital asset like this is unconventional and is extant only in theory at the moment. However, such a change is imminent sooner rather than later[5].
-
-Among the areas in which blockchain will have the most impact within real estate is as highlighted above in maintaining a transparent and secure title management system for properties. A blockchain based record of the property can contain information about the property, its location, history of ownership, and any related public record of the same[6]. This will permit closing real estate deals fast and obliviates the need for 3rd party monitoring and oversight. Tasks such as real estate appraisal and tax calculations become matters of tangible objective parameters rather than subjective measures and guesses because of reliable historical data which is publicly verifiable. **UBITQUITY** is one such platform that offers customized blockchain-based solutions to enterprise customers. The platform allows customers to keep track of all property details, payment records, mortgage records and even allows running smart contracts that’ll take care of taxation and leasing automatically[7].
-
-This brings us to the second biggest opportunity and use case of blockchains in real estate. Since the sector is highly regulated by numerous 3rd parties apart from the counterparties involved in the trade, due-diligence and financial evaluations can be significantly time-consuming. These processes are predominantly carried out using offline channels and paperwork needs to travel for days before a final evaluation report comes out. This is especially true for corporate real estate deals and forms a bulk of the total billable hours charged by consultants. In case the transaction is backed by a mortgage, duplication of these processes is unavoidable. Once combined with digital identities for the people and institutions involved along with the property, the current inefficiencies can be avoided altogether and transactions can take place in a matter of seconds. The tenants, investors, institutions involved, consultants etc., could individually validate the data and arrive at a critical consensus thereby validating the property records for perpetuity[8]. This increases the accuracy of verification manifold. Real estate giant **RE/MAX** has recently announced a partnership with service provider **XYO Network Partners** for building a national database of real estate listings in Mexico. They hope to one day create one of the largest (as of yet) decentralized real estate title registry in the world[9].
-
-However, another significant and arguably a very democratic change that the blockchain can bring about is with respect to investing in real estate. Unlike other investment asset classes where even small household investors can potentially participate, real estate often requires large hands-down payments to participate. Companies such as **ATLANT** and **BitOfProperty** tokenize the book value of a property and convert them into equivalents of a cryptocurrency. These tokens are then put for sale on their exchanges similar to how stocks and shares are traded. Any cash flow that the real estate property generates afterward is credited or debited to the token owners depending on their “share” in the property[4].
-
-However, even with all of that said, Blockchain technology is still in very early stages of adoption in the real estate sector and current regulations are not exactly defined for it to be either[8]. Concepts such as distributed applications, distributed anonymous organizations, smart contracts etc., are unheard of in the legal domain in many countries. A complete overhaul of existing regulations and guidelines once all the stakeholders are well educated on the intricacies of the blockchain is the most pragmatic way forward. Again, it’ll be a slow and gradual change to go through, however a much-needed one nonetheless. The next article of the series will look at how **“Smart Contracts”** , such as those implemented by companies such as UBITQUITY and XYO are created and executed in the blockchain.
-
-
-
---------------------------------------------------------------------------------
-
-via: https://www.ostechnix.com/blockchain-2-0-blockchain-in-real-estate/
-
-作者:[EDITOR][a]
-选题:[lujun9972][b]
-译者:[译者ID](https://github.com/译者ID)
-校对:[校对者ID](https://github.com/校对者ID)
-
-本文由 [LCTT](https://github.com/LCTT/TranslateProject) 原创编译,[Linux中国](https://linux.cn/) 荣誉推出
-
-[a]: https://www.ostechnix.com/author/editor/
-[b]: https://github.com/lujun9972
-[1]: https://www.ostechnix.com/blockchain-2-0-redefining-financial-services/
diff --git a/sources/tech/20190327 HPE introduces hybrid cloud consulting business.md b/sources/tech/20190327 HPE introduces hybrid cloud consulting business.md
deleted file mode 100644
index f1d9d3564f..0000000000
--- a/sources/tech/20190327 HPE introduces hybrid cloud consulting business.md
+++ /dev/null
@@ -1,59 +0,0 @@
-[#]: collector: (lujun9972)
-[#]: translator: ( )
-[#]: reviewer: ( )
-[#]: publisher: ( )
-[#]: url: ( )
-[#]: subject: (HPE introduces hybrid cloud consulting business)
-[#]: via: (https://www.networkworld.com/article/3384919/hpe-introduces-hybrid-cloud-consulting-business.html#tk.rss_all)
-[#]: author: (Andy Patrizio https://www.networkworld.com/author/Andy-Patrizio/)
-
-HPE introduces hybrid cloud consulting business
-======
-
-### HPE's Right Mix Advisor is designed to find a balance between on-premises and cloud systems.
-
-![Hewlett Packard Enterprise][1]
-
-Hybrid cloud is pretty much the de facto way to go, with only a few firms adopting a pure cloud play to replace their data center and only suicidal firms refusing to go to the cloud. But picking the right balance between on-premises and the cloud is tricky, and a mistake can be costly.
-
-Enter Right Mix Advisor from Hewlett Packard Enterprise, a combination of consulting from HPE's Pointnext division and software tools. It draws on quite a bit of recent acquisitions. Another part of Right Mix Advisor is a British cloud consultancy RedPixie, Amazon Web Services (AWS) specialists Cloud Technology Partners, and automated discovery capabilities from an Irish startup iQuate.
-
-Right Mix Advisor gathers data points from the company’s entire enterprise, ranging from configuration management database systems (CMDBs), such as ServiceNow, to external sources, such as cloud providers. HPE says that in a recent customer engagement it scanned 9 million IP addresses across six data centers.
-
-**[ Read also:[What is hybrid cloud computing][2]. | Learn [what you need to know about multi-cloud][3]. | Get regularly scheduled insights by [signing up for Network World newsletters][4]. ]**
-
-HPE Pointnext consultants then work with the client’s IT teams to analyze the data to determine the optimal configuration for workload placement. Pointnext has become HPE’s main consulting outfit following its divestiture of EDS, which it acquired in 2008 but spun off in a merger with CSC to form DXC Consulting. Pointnext now has 25,000 consultants in 88 countries.
-
-In a typical engagement, HPE claims it can deliver a concrete action plan within weeks, whereas previously businesses may have needed months to come to a conclusion using a manual processes. HPE has found migrating the right workloads to the right mix of hybrid cloud can typically result in 40 percent total cost of ownership savings*. *
-
-Although HPE has thrown its weight behind AWS, that doesn’t mean it doesn’t support competitors. Erik Vogel, vice president of hybrid IT for HPE Pointnext, notes in the blog post announcing Right Mix Advisor that target environments could be Microsoft Azure or Azure Stack, AWS, Google or Ali Cloud.
-
-“New service providers are popping up every day, and we see the big public cloud providers constantly producing new services and pricing models. As a result, the calculus for determining your right mix is constantly changing. If Azure, for example, offers a new service capability or a 10 percent pricing discount and it makes sense to leverage it, you want to be able to move an application seamlessly into that new environment,” he wrote.
-
-Key to Right Mix Advisor is app migration, and Pointnext follows the 50/30/20 rule: About 50 percent of apps are suitable for migration to the cloud, and for about 30 percent, migration is not a good choice for migration to be worth the effort. The remaining 20 percent should be retired.
-
-“With HPE Right Mix Advisor, you can identify that 50 percent,” he wrote. “Rather than hand you a laundry list of 10,000 apps to start migrating, HPE Right Mix Advisor hones in on what’s most impactful right now to meet your business goals – the 10 things you can do on Monday morning that you can be confident will really help your business.”
-
-HPE has already done some pilot projects with the Right Mix service and expects to expand it to include channel partners.
-
-Join the Network World communities on [Facebook][5] and [LinkedIn][6] to comment on topics that are top of mind.
-
---------------------------------------------------------------------------------
-
-via: https://www.networkworld.com/article/3384919/hpe-introduces-hybrid-cloud-consulting-business.html#tk.rss_all
-
-作者:[Andy Patrizio][a]
-选题:[lujun9972][b]
-译者:[译者ID](https://github.com/译者ID)
-校对:[校对者ID](https://github.com/校对者ID)
-
-本文由 [LCTT](https://github.com/LCTT/TranslateProject) 原创编译,[Linux中国](https://linux.cn/) 荣誉推出
-
-[a]: https://www.networkworld.com/author/Andy-Patrizio/
-[b]: https://github.com/lujun9972
-[1]: https://images.techhive.com/images/article/2015/11/hpe_building-100625424-large.jpg
-[2]: https://www.networkworld.com/article/3233132/cloud-computing/what-is-hybrid-cloud-computing.html
-[3]: https://www.networkworld.com/article/3252775/hybrid-cloud/multicloud-mania-what-to-know.html
-[4]: https://www.networkworld.com/newsletters/signup.html
-[5]: https://www.facebook.com/NetworkWorld/
-[6]: https://www.linkedin.com/company/network-world
diff --git a/sources/tech/20190328 Cisco warns of two security patches that don-t work, issues 17 new ones for IOS flaws.md b/sources/tech/20190328 Cisco warns of two security patches that don-t work, issues 17 new ones for IOS flaws.md
deleted file mode 100644
index 27370bf294..0000000000
--- a/sources/tech/20190328 Cisco warns of two security patches that don-t work, issues 17 new ones for IOS flaws.md
+++ /dev/null
@@ -1,72 +0,0 @@
-[#]: collector: (lujun9972)
-[#]: translator: ( )
-[#]: reviewer: ( )
-[#]: publisher: ( )
-[#]: url: ( )
-[#]: subject: (Cisco warns of two security patches that don’t work, issues 17 new ones for IOS flaws)
-[#]: via: (https://www.networkworld.com/article/3384742/cisco-warns-of-two-security-patches-that-dont-work-issues-17-new-ones-for-ios-flaws.html#tk.rss_all)
-[#]: author: (Michael Cooney https://www.networkworld.com/author/Michael-Cooney/)
-
-Cisco warns of two security patches that don’t work, issues 17 new ones for IOS flaws
-======
-
-### Cisco is issuing 17 new fixes for security problems with IOS and IOS/XE software that runs most of its routers and switches, while it has no patch yet to replace flawed patches to RV320 and RV 325 routers.
-
-![Marisa9 / Getty][1]
-
-Cisco has dropped [17 Security advisories describing 19 vulnerabilities][2] in the software that runs most of its routers and switches, IOS and IOS/XE.
-
-The company also announced that two previously issued patches for its RV320 and RV325 Dual Gigabit WAN VPN Routers were “incomplete” and would need to be redone and reissued.
-
-**[ Also see[What to consider when deploying a next generation firewall][3]. | Get regularly scheduled insights by [signing up for Network World newsletters][4]. ]**
-
-Cisco rates both those router vulnerabilities as “High” and describes the problems like this:
-
- * [One vulnerability][5] is due to improper validation of user-supplied input. An attacker could exploit this vulnerability by sending malicious HTTP POST requests to the web-based management interface of an affected device. A successful exploit could allow the attacker to execute arbitrary commands on the underlying Linux shell as _root_.
- * The [second exposure][6] is due to improper access controls for URLs. An attacker could exploit this vulnerability by connecting to an affected device via HTTP or HTTPS and requesting specific URLs. A successful exploit could allow the attacker to download the router configuration or detailed diagnostic information.
-
-
-
-Cisco said firmware updates that address these vulnerabilities are not available and no workarounds exist, but is working on a complete fix for both.
-
-On the IOS front, the company said six of the vulnerabilities affect both Cisco IOS Software and Cisco IOS XE Software, one of the vulnerabilities affects just Cisco IOS software and ten of the vulnerabilities affect just Cisco IOS XE software. Some of the security bugs, which are all rated as “High”, include:
-
- * [A vulnerability][7] in the web UI of Cisco IOS XE Software could let an unauthenticated, remote attacker access sensitive configuration information.
- * [A vulnerability][8] in Cisco IOS XE Software could let an authenticated, local attacker inject arbitrary commands that are executed with elevated privileges. The vulnerability is due to insufficient input validation of commands supplied by the user. An attacker could exploit this vulnerability by authenticating to a device and submitting crafted input to the affected commands.
- * [A weakness][9] in the ingress traffic validation of Cisco IOS XE Software for Cisco Aggregation Services Router (ASR) 900 Route Switch Processor 3 could let an unauthenticated, adjacent attacker trigger a reload of an affected device, resulting in a denial of service (DoS) condition, Cisco said. The vulnerability exists because the software insufficiently validates ingress traffic on the ASIC used on the RSP3 platform. An attacker could exploit this vulnerability by sending a malformed OSPF version 2 message to an affected device.
- * A problem in the [authorization subsystem][10] of Cisco IOS XE Software could allow an authenticated but unprivileged (level 1), remote attacker to run privileged Cisco IOS commands by using the web UI. The vulnerability is due to improper validation of user privileges of web UI users. An attacker could exploit this vulnerability by submitting a malicious payload to a specific endpoint in the web UI, Cisco said.
- * A vulnerability in the [Cluster Management Protocol][11] (CMP) processing code in Cisco IOS Software and Cisco IOS XE Software could allow an unauthenticated, adjacent attacker to trigger a DoS condition on an affected device. The vulnerability is due to insufficient input validation when processing CMP management packets, Cisco said.
-
-
-
-Cisco has released free software updates that address the vulnerabilities described in these advisories and [directs users to their software agreements][12] to find out how they can download the fixes.
-
-Join the Network World communities on [Facebook][13] and [LinkedIn][14] to comment on topics that are top of mind.
-
---------------------------------------------------------------------------------
-
-via: https://www.networkworld.com/article/3384742/cisco-warns-of-two-security-patches-that-dont-work-issues-17-new-ones-for-ios-flaws.html#tk.rss_all
-
-作者:[Michael Cooney][a]
-选题:[lujun9972][b]
-译者:[译者ID](https://github.com/译者ID)
-校对:[校对者ID](https://github.com/校对者ID)
-
-本文由 [LCTT](https://github.com/LCTT/TranslateProject) 原创编译,[Linux中国](https://linux.cn/) 荣誉推出
-
-[a]: https://www.networkworld.com/author/Michael-Cooney/
-[b]: https://github.com/lujun9972
-[1]: https://images.idgesg.net/images/article/2019/02/woman-with-hands-over-face_mistake_oops_embarrassed_shy-by-marisa9-getty-100787990-large.jpg
-[2]: https://tools.cisco.com/security/center/viewErp.x?alertId=ERP-71135
-[3]: https://www.networkworld.com/article/3236448/lan-wan/what-to-consider-when-deploying-a-next-generation-firewall.html
-[4]: https://www.networkworld.com/newsletters/signup.html
-[5]: https://tools.cisco.com/security/center/content/CiscoSecurityAdvisory/cisco-sa-20190123-rv-inject
-[6]: https://tools.cisco.com/security/center/content/CiscoSecurityAdvisory/cisco-sa-20190123-rv-info
-[7]: https://tools.cisco.com/security/center/content/CiscoSecurityAdvisory/cisco-sa-20190327-xeid
-[8]: https://tools.cisco.com/security/center/content/CiscoSecurityAdvisory/cisco-sa-20190327-xecmd
-[9]: https://tools.cisco.com/security/center/content/CiscoSecurityAdvisory/cisco-sa-20190327-rsp3-ospf
-[10]: https://tools.cisco.com/security/center/content/CiscoSecurityAdvisory/cisco-sa-20190327-iosxe-privesc
-[11]: https://tools.cisco.com/security/center/content/CiscoSecurityAdvisory/cisco-sa-20190327-cmp-dos
-[12]: https://www.cisco.com/c/en/us/about/legal/cloud-and-software/end_user_license_agreement.html
-[13]: https://www.facebook.com/NetworkWorld/
-[14]: https://www.linkedin.com/company/network-world
diff --git a/sources/tech/20190329 How to manage your Linux environment.md b/sources/tech/20190329 How to manage your Linux environment.md
deleted file mode 100644
index 2c4ca113e3..0000000000
--- a/sources/tech/20190329 How to manage your Linux environment.md
+++ /dev/null
@@ -1,177 +0,0 @@
-[#]: collector: (lujun9972)
-[#]: translator: ( )
-[#]: reviewer: ( )
-[#]: publisher: ( )
-[#]: url: ( )
-[#]: subject: (How to manage your Linux environment)
-[#]: via: (https://www.networkworld.com/article/3385516/how-to-manage-your-linux-environment.html#tk.rss_all)
-[#]: author: (Sandra Henry-Stocker https://www.networkworld.com/author/Sandra-Henry_Stocker/)
-
-How to manage your Linux environment
-======
-
-### Linux user environments help you find the command you need and get a lot done without needing details about how the system is configured. Where the settings come from and how they can be modified is another matter.
-
-![IIP Photo Archive \(CC BY 2.0\)][1]
-
-The configuration of your user account on a Linux system simplifies your use of the system in a multitude of ways. You can run commands without knowing where they're located. You can reuse previously run commands without worrying how the system is keeping track of them. You can look at your email, view man pages, and get back to your home directory easily no matter where you might have wandered off to in the file system. And, when needed, you can tweak your account settings so that it works even more to your liking.
-
-Linux environment settings come from a series of files — some are system-wide (meaning they affect all user accounts) and some are configured in files that are sitting in your home directory. The system-wide settings take effect when you log in and local ones take effect right afterwards, so the changes that you make in your account will override system-wide settings. For bash users, these files include these system files:
-
-```
-/etc/environment
-/etc/bash.bashrc
-/etc/profile
-```
-
-And some of these local files:
-
-```
-~/.bashrc
-~/.profile -- not read if ~/.bash_profile or ~/.bash_login
-~/.bash_profile
-~/.bash_login
-```
-
-You can modify any of the local four that exist, since they sit in your home directory and belong to you.
-
-**[ Two-Minute Linux Tips:[Learn how to master a host of Linux commands in these 2-minute video tutorials][2] ]**
-
-### Viewing your Linux environment settings
-
-To view your environment settings, use the **env** command. Your output will likely look similar to this:
-
-```
-$ env
-LS_COLORS=rs=0:di=01;34:ln=01;36:mh=00:pi=40;33:so=01;35:do=01;35:bd=40;33;01:cd=40;33;
-01:or=40;31;01:mi=00:su=37;41:sg=30;43:ca=30;41:tw=30;42:ow=34;42:st=37;44:ex=01;32:
-*.tar=01;31:*.tgz=01;31:*.arc=01;31:*.arj=01;31:*.taz=01;31:*.lha=01;31:*.lz4=01;31:
-*.lzh=01;31:*.lzma=01;31:*.tlz=01;31:*.txz=01;31:*.tzo=01;31:*.t7z=01;31:*.zip=01;31:
-*.z=01;31:*.Z=01;31:*.dz=01;31:*.gz=01;31:*.lrz=01;31:*.lz=01;31:*.lzo=01;31:*.xz=01;
-31:*.zst=01;31:*.tzst=01;31:*.bz2=01;31:*.bz=01;31:*.tbz=01;31:*.tbz2=01;31:*.tz=01;31:
-*.deb=01;31:*.rpm=01;31:*.jar=01;31:*.war=01;31:*.ear=01;31:*.sar=01;31:*.rar=01;31:
-*.alz=01;31:*.ace=01;31:*.zoo=01;31:*.cpio=01;31:*.7z=01;31:*.rz=01;31:*.cab=01;31:
-*.wim=01;31:*.swm=01;31:*.dwm=01;31:*.esd=01;31:*.jpg=01;35:*.jpeg=01;35:*.mjpg=01;35:
-*.mjpeg=01;35:*.gif=01;35:*.bmp=01;35:*.pbm=01;35:*.pgm=01;35:*.ppm=01;35:*.tga=01;35:
-*.xbm=01;35:*.xpm=01;35:*.tif=01;35:*.tiff=01;35:*.png=01;35:*.svg=01;35:*.svgz=01;35:
-*.mng=01;35:*.pcx=01;35:*.mov=01;35:*.mpg=01;35:*.mpeg=01;35:*.m2v=01;35:*.mkv=01;35:
-*.webm=01;35:*.ogm=01;35:*.mp4=01;35:*.m4v=01;35:*.mp4v=01;35:*.vob=01;35:*.qt=01;35:
-*.nuv=01;35:*.wmv=01;35:*.asf=01;35:*.rm=01;35:*.rmvb=01;35:*.flc=01;35:*.avi=01;35:
-*.fli=01;35:*.flv=01;35:*.gl=01;35:*.dl=01;35:*.xcf=01;35:*.xwd=01;35:*.yuv=01;35:
-*.cgm=01;35:*.emf=01;35:*.ogv=01;35:*.ogx=01;35:*.aac=00;36:*.au=00;36:*.flac=00;36:
-*.m4a=00;36:*.mid=00;36:*.midi=00;36:*.mka=00;36:*.mp3=00;36:*.mpc=00;36:*.ogg=00;36:
-*.ra=00;36:*.wav=00;36:*.oga=00;36:*.opus=00;36:*.spx=00;36:*.spf=00;36:
-SSH_CONNECTION=192.168.0.21 34975 192.168.0.11 22
-LESSCLOSE=/usr/bin/lesspipe %s %s
-LANG=en_US.UTF-8
-OLDPWD=/home/shs
-XDG_SESSION_ID=2253
-USER=shs
-PWD=/home/shs
-HOME=/home/shs
-SSH_CLIENT=192.168.0.21 34975 22
-XDG_DATA_DIRS=/usr/local/share:/usr/share:/var/lib/snapd/desktop
-SSH_TTY=/dev/pts/0
-MAIL=/var/mail/shs
-TERM=xterm
-SHELL=/bin/bash
-SHLVL=1
-LOGNAME=shs
-DBUS_SESSION_BUS_ADDRESS=unix:path=/run/user/1000/bus
-XDG_RUNTIME_DIR=/run/user/1000
-PATH=/home/shs/bin:/usr/local/sbin:/usr/local/bin:/usr/sbin:/usr/bin:/sbin:/bin:/usr/games:/usr/local/games:/snap/bin
-LESSOPEN=| /usr/bin/lesspipe %s
-_=/usr/bin/env
-```
-
-While you're likely to get a _lot_ of output, the first big section shown above deals with the colors that are used on the command line to identify various file types. When you see something like ***.tar=01;31:** , this tells you that tar files will be displayed in a file listing in red, while ***.jpg=01;35:** tells you that jpg files will show up in purple. These colors are meant to make it easy to pick out certain files from a file listing. You can learn more about these colors are defined and how to customize them at [Customizing your colors on the Linux command line][3].
-
-One easy way to turn colors off when you prefer a simpler display is to use a command such as this one:
-
-```
-$ ls -l --color=never
-```
-
-That command could easily be turned into an alias:
-
-```
-$ alias ll2='ls -l --color=never'
-```
-
-You can also display individual settings using the **echo** command. In this command, we display the number of commands that will be remembered in our history buffer:
-
-```
-$ echo $HISTSIZE
-1000
-```
-
-Your last location in the file system will be remembered if you've moved.
-
-```
-PWD=/home/shs
-OLDPWD=/tmp
-```
-
-### Making changes
-
-You can make changes to environment settings with a command like this, but add a line lsuch as "HISTSIZE=1234" in your ~/.bashrc file if you want to retain this setting.
-
-```
-$ export HISTSIZE=1234
-```
-
-### What it means to "export" a variable
-
-Exporting a variable makes the setting available to your shell and possible subshells. By default, user-defined variables are local and are not exported to new processes such as subshells and scripts. The export command makes variables available to functions to child processes.
-
-### Adding and removing variables
-
-You can create new variables and make them available to you on the command line and subshells quite easily. However, these variables will not survive your logging out and then back in again unless you also add them to ~/.bashrc or a similar file.
-
-```
-$ export MSG="Hello, World!"
-```
-
-You can unset a variable if you need by using the **unset** command:
-
-```
-$ unset MSG
-```
-
-If the variable is defined locally, you can easily set it back up by sourcing your startup file(s). For example:
-
-```
-$ echo $MSG
-Hello, World!
-$ unset $MSG
-$ echo $MSG
-
-$ . ~/.bashrc
-$ echo $MSG
-Hello, World!
-```
-
-### Wrap-up
-
-User accounts are set up with an appropriate set of startup files for creating a userful user environment, but both individual users and sysadmins can change the default settings by editing their personal setup files (users) or the files from which many of the settings originate (sysadmins).
-
-Join the Network World communities on [Facebook][4] and [LinkedIn][5] to comment on topics that are top of mind.
-
---------------------------------------------------------------------------------
-
-via: https://www.networkworld.com/article/3385516/how-to-manage-your-linux-environment.html#tk.rss_all
-
-作者:[Sandra Henry-Stocker][a]
-选题:[lujun9972][b]
-译者:[译者ID](https://github.com/译者ID)
-校对:[校对者ID](https://github.com/校对者ID)
-
-本文由 [LCTT](https://github.com/LCTT/TranslateProject) 原创编译,[Linux中国](https://linux.cn/) 荣誉推出
-
-[a]: https://www.networkworld.com/author/Sandra-Henry_Stocker/
-[b]: https://github.com/lujun9972
-[1]: https://images.idgesg.net/images/article/2019/03/environment-rocks-leaves-100792229-large.jpg
-[2]: https://www.youtube.com/playlist?list=PL7D2RMSmRO9J8OTpjFECi8DJiTQdd4hua
-[3]: https://www.networkworld.com/article/3269587/customizing-your-text-colors-on-the-linux-command-line.html
-[4]: https://www.facebook.com/NetworkWorld/
-[5]: https://www.linkedin.com/company/network-world
diff --git a/sources/tech/20190331 How to build a mobile particulate matter sensor with a Raspberry Pi.md b/sources/tech/20190331 How to build a mobile particulate matter sensor with a Raspberry Pi.md
deleted file mode 100644
index 7eea0bd556..0000000000
--- a/sources/tech/20190331 How to build a mobile particulate matter sensor with a Raspberry Pi.md
+++ /dev/null
@@ -1,126 +0,0 @@
-[#]: collector: (lujun9972)
-[#]: translator: ( )
-[#]: reviewer: ( )
-[#]: publisher: ( )
-[#]: url: ( )
-[#]: subject: (How to build a mobile particulate matter sensor with a Raspberry Pi)
-[#]: via: (https://opensource.com/article/19/3/mobile-particulate-matter-sensor)
-[#]: author: (Stephan Tetzel https://opensource.com/users/stephan)
-
-How to build a mobile particulate matter sensor with a Raspberry Pi
-======
-
-Monitor your air quality with a Raspberry Pi, a cheap sensor, and an inexpensive display.
-
-![Team communication, chat][1]
-
-About a year ago, I wrote about [measuring air quality][2] using a Raspberry Pi and a cheap sensor. We've been using this project in our school and privately for a few years now. However, it has one disadvantage: It is not portable because it depends on a WLAN network or a wired network connection to work. You can't even access the sensor's measurements if the Raspberry Pi and the smartphone or computer are not on the same network.
-
-To overcome this limitation, we added a small screen to the Raspberry Pi so we can read the values directly from the device. Here's how we set up and configured a screen for our mobile fine particulate matter sensor.
-
-### Setting up the screen for the Raspberry Pi
-
-There is a wide range of Raspberry Pi displays available from [Amazon][3], AliExpress, and other sources. They range from ePaper screens to LCDs with touch function. We chose an inexpensive [3.5″ LCD][4] with touch and a resolution of 320×480 pixels that can be plugged directly into the Raspberry Pi's GPIO pins. It's also nice that a 3.5″ display is about the same size as a Raspberry Pi.
-
-The first time you turn on the screen and start the Raspberry Pi, the screen will remain white because the driver is missing. You have to install [the appropriate drivers][5] for the display first. Log in with SSH and execute the following commands:
-
-```
-$ rm -rf LCD-show
-$ git clone
-$ chmod -R 755 LCD-show
-$ cd LCD-show/
-```
-
-Execute the appropriate command for your screen to install the drivers. For example, this is the command for our model MPI3501 screen:
-
-```
-$ sudo ./LCD35-show
-```
-
-This command installs the appropriate drivers and restarts the Raspberry Pi.
-
-### Installing PIXEL desktop and setting up autostart
-
-Here is what we want our project to do: If the Raspberry Pi boots up, we want to display a small website with our air quality measurements.
-
-First, install the Raspberry Pi's [PIXEL desktop environment][6]:
-
-```
-$ sudo apt install raspberrypi-ui-mods
-```
-
-Then install the Chromium browser to display the website:
-
-```
-$ sudo apt install chromium-browser
-```
-
-Autologin is required for the measured values to be displayed directly after startup; otherwise, you will just see the login screen. However, autologin is not configured for the "pi" user by default. You can configure autologin with the **raspi-config** tool:
-
-```
-$ sudo raspi-config
-```
-
-In the menu, select: **3 Boot Options → B1 Desktop / CLI → B4 Desktop Autologin**.
-
-There is a step missing to start Chromium with our website right after boot. Create the folder **/home/pi/.config/lxsession/LXDE-pi/** :
-
-```
-$ mkdir -p /home/pi/config/lxsession/LXDE-pi/
-```
-
-Then create the **autostart** file in this folder:
-
-```
-$ nano /home/pi/.config/lxsession/LXDE-pi/autostart
-```
-
-and paste the following code:
-
-```
-#@unclutter
-@xset s off
-@xset -dpms
-@xset s noblank
-
-# Open Chromium in Full Screen Mode
-@chromium-browser --incognito --kiosk
-```
-
-If you want to hide the mouse pointer, you have to install the package **unclutter** and remove the comment character at the beginning of the **autostart** file:
-
-```
-$ sudo apt install unclutter
-```
-
-![Mobile particulate matter sensor][7]
-
-I've made a few small changes to the code in the last year. So, if you set up the air quality project before, make sure to re-download the script and files for the AQI website using the instructions in the [original article][2].
-
-By adding the touch screen, you now have a mobile particulate matter sensor! We use it at our school to check the quality of the air in the classrooms or to do comparative measurements. With this setup, you are no longer dependent on a network connection or WLAN. You can use the small measuring station everywhere—you can even use it with a power bank to be independent of the power grid.
-
-* * *
-
-_This article originally appeared on[Open School Solutions][8] and is republished with permission._
-
---------------------------------------------------------------------------------
-
-via: https://opensource.com/article/19/3/mobile-particulate-matter-sensor
-
-作者:[Stephan Tetzel][a]
-选题:[lujun9972][b]
-译者:[译者ID](https://github.com/译者ID)
-校对:[校对者ID](https://github.com/校对者ID)
-
-本文由 [LCTT](https://github.com/LCTT/TranslateProject) 原创编译,[Linux中国](https://linux.cn/) 荣誉推出
-
-[a]: https://opensource.com/users/stephan
-[b]: https://github.com/lujun9972
-[1]: https://opensource.com/sites/default/files/styles/image-full-size/public/lead-images/talk_chat_team_mobile_desktop.png?itok=d7sRtKfQ (Team communication, chat)
-[2]: https://opensource.com/article/18/3/how-measure-particulate-matter-raspberry-pi
-[3]: https://www.amazon.com/gp/search/ref=as_li_qf_sp_sr_tl?ie=UTF8&tag=openschoolsol-20&keywords=lcd%20raspberry&index=aps&camp=1789&creative=9325&linkCode=ur2&linkId=51d6d7676e10d6c7db203c4a8b3b529a
-[4]: https://amzn.to/2CcvgpC
-[5]: https://github.com/goodtft/LCD-show
-[6]: https://opensource.com/article/17/1/try-raspberry-pis-pixel-os-your-pc
-[7]: https://opensource.com/sites/default/files/uploads/mobile-aqi-sensor.jpg (Mobile particulate matter sensor)
-[8]: https://openschoolsolutions.org/mobile-particulate-matter-sensor/
diff --git a/sources/tech/20190402 5G- A deep dive into fast, new wireless.md b/sources/tech/20190402 5G- A deep dive into fast, new wireless.md
deleted file mode 100644
index f3941b3dde..0000000000
--- a/sources/tech/20190402 5G- A deep dive into fast, new wireless.md
+++ /dev/null
@@ -1,70 +0,0 @@
-[#]: collector: (lujun9972)
-[#]: translator: ( )
-[#]: reviewer: ( )
-[#]: publisher: ( )
-[#]: url: ( )
-[#]: subject: (5G: A deep dive into fast, new wireless)
-[#]: via: (https://www.networkworld.com/article/3385030/5g-a-deep-dive-into-fast-new-wireless.html#tk.rss_all)
-[#]: author: (Craig Mathias https://www.networkworld.com/author/Craig-Mathias/)
-
-5G: A deep dive into fast, new wireless
-======
-
-### 5G wireless networks are just about ready for prime time, overcoming backhaul and backward-compatibility issues, and promising the possibility of all-mobile networking through enhanced throughput.
-
-The next step in the evolution of wireless WAN communications - [5G networks][1] \- is about to hit the front pages, and for good reason: it will complete the evolution of cellular from wireline augmentation to wireline replacement, and strategically from mobile-first to mobile-only.
-
-So it’s not too early to start least basic planning to understanding how 5G will fit into and benefit IT plans across organizations of all sizes, industries and missions.
-
-**[ From Mobile World Congress:[The time of 5G is almost here][2] ]**
-
-5G will of course provide end-users with the additional throughput, capacity, and other elements to address the continuing and dramatic growth in geographic availability, user base, range of subscriber devices, demand for capacity, and application requirements, but will also enable service providers to benefit from new opportunities in overall strategy, service offerings and broadened marketplace presence.
-
-A look at the key features you can expect in 5G wireless. (Click for larger image.)
-
-![A look at the key features you can expect in 5G wireless.][3]
-
-This article explores the technologies and market drivers behind 5G, with an emphasis on what 5G means to enterprise and organizational IT.
-
-While 5G remains an imprecise term today, key objectives for the development of the advances required have become clear. These are as follows:
-
-## 5G speeds
-
-As is the case with Wi-Fi, major advances in cellular are first and foremost defined by new upper-bound _throughput_ numbers. The magic number here for 5G is in fact a _floor_ of 1 Gbps, with numbers as high as 10 Gbps mentioned by some. However, and again as is the case with Wi-Fi, it’s important to think more in terms of overall individual-cell and system-wide _capacity_. We believe, then, that per-user throughput of 50 Mbps is a more reasonable – but clearly still remarkable – working assumption, with up to 300 Mbps peak throughput realized in some deployments over the next five years. The possibility of reaching higher throughput than that exceeds our planning horizon, but such is, well, possible.
-
-## Reduced latency
-
-Perhaps even more important than throughput, though, is a reduction in the round-trip time for each packet. Reducing latency is important for voice, which will most certainly be all-IP in 5G implementations, video, and, again, in improving overall capacity. The over-the-air latency goal for 5G is less than 10ms, with 1ms possible in some defined classes of service.
-
-## 5G network management and OSS
-
-Operators are always seeking to reduce overhead and operating expense, so enhancements to both system management and operational support systems (OSS) yielding improvements in reliability, availability, serviceability, resilience, consistency, analytics capabilities, and operational efficiency, are all expected. The benefits of these will, in most cases, however, be transparent to end-users.
-
-## Mobility and 5G technology
-
-Very-high-speed user mobility, to as much as hundreds of kilometers per hour, will be supported, thus serving users on all modes of transportation. Regulatory and situation-dependent restrictions – most notably, on aircraft – however, will still apply.
-
-To continue reading this article register now
-
-[Get Free Access][4]
-
-[Learn More][5] Existing Users [Sign In][4]
-
---------------------------------------------------------------------------------
-
-via: https://www.networkworld.com/article/3385030/5g-a-deep-dive-into-fast-new-wireless.html#tk.rss_all
-
-作者:[Craig Mathias][a]
-选题:[lujun9972][b]
-译者:[译者ID](https://github.com/译者ID)
-校对:[校对者ID](https://github.com/校对者ID)
-
-本文由 [LCTT](https://github.com/LCTT/TranslateProject) 原创编译,[Linux中国](https://linux.cn/) 荣誉推出
-
-[a]: https://www.networkworld.com/author/Craig-Mathias/
-[b]: https://github.com/lujun9972
-[1]: https://www.networkworld.com/article/3203489/what-is-5g-how-is-it-better-than-4g.html
-[2]: https://www.networkworld.com/article/3354477/mobile-world-congress-the-time-of-5g-is-almost-here.html
-[3]: https://images.idgesg.net/images/article/2017/06/2017_nw_5g_wireless_key_features-100727485-large.jpg
-[4]: javascript://
-[5]: /learn-about-insider/
diff --git a/sources/tech/20190402 Announcing the release of Fedora 30 Beta.md b/sources/tech/20190402 Announcing the release of Fedora 30 Beta.md
deleted file mode 100644
index 19b5926e27..0000000000
--- a/sources/tech/20190402 Announcing the release of Fedora 30 Beta.md
+++ /dev/null
@@ -1,90 +0,0 @@
-[#]: collector: (lujun9972)
-[#]: translator: ( )
-[#]: reviewer: ( )
-[#]: publisher: ( )
-[#]: url: ( )
-[#]: subject: (Announcing the release of Fedora 30 Beta)
-[#]: via: (https://fedoramagazine.org/announcing-the-release-of-fedora-30-beta/)
-[#]: author: (Ben Cotton https://fedoramagazine.org/author/bcotton/)
-
-Announcing the release of Fedora 30 Beta
-======
-
-![][1]
-
-The Fedora Project is pleased to announce the immediate availability of Fedora 30 Beta, the next big step on our journey to the exciting Fedora 30 release.
-
-Download the prerelease from our Get Fedora site:
-
- * [Get Fedora 30 Beta Workstation][2]
- * [Get Fedora 30 Beta Server][3]
- * [Get Fedora 30 Beta Silverblue][4]
-
-
-
-Or, check out one of our popular variants, including KDE Plasma, Xfce, and other desktop environments, as well as images for ARM devices like the Raspberry Pi 2 and 3:
-
- * [Get Fedora 30 Beta Spins][5]
- * [Get Fedora 30 Beta Labs][6]
- * [Get Fedora 30 Beta ARM][7]
-
-
-
-### Beta Release Highlights
-
-#### New desktop environment options
-
-Fedora 30 Beta includes two new options for desktop environment. [DeepinDE][8] and [Pantheon Desktop][9] join GNOME, KDE Plasma, Xfce, and others as options for users to customize their Fedora experience.
-
-#### DNF performance improvements
-
-All dnf repository metadata for Fedora 30 Beta is compressed with the zchunk format in addition to xz or gzip. zchunk is a new compression format designed to allow for highly efficient deltas. When Fedora’s metadata is compressed using zchunk, dnf will download only the differences between any earlier copies of the metadata and the current version.
-
-#### GNOME 3.32
-
-Fedora 30 Workstation Beta includes GNOME 3.32, the latest version of the popular desktop environment. GNOME 3.32 features updated visual style, including the user interface, the icons, and the desktop itself. For a full list of GNOME 3.32 highlights, see the [release notes][10].
-
-#### Other updates
-
-Fedora 30 Beta also includes updated versions of many popular packages like Golang, the Bash shell, the GNU C Library, Python, and Perl. For a full list, see the [Change set][11] on the Fedora Wiki. In addition, many Python 2 packages are removed in preparation for Python 2 end-of-life on 2020-01-01.
-
-#### Testing needed
-
-Since this is a Beta release, we expect that you may encounter bugs or missing features. To report issues encountered during testing, contact the Fedora QA team via the mailing list or in #fedora-qa on Freenode. As testing progresses, common issues are tracked on the [Common F30 Bugs page][12].
-
-For tips on reporting a bug effectively, read [how to file a bug][13].
-
-#### What is the Beta Release?
-
-A Beta release is code-complete and bears a very strong resemblance to the final release. If you take the time to download and try out the Beta, you can check and make sure the things that are important to you are working. Every bug you find and report doesn’t just help you, it improves the experience of millions of Fedora users worldwide! Together, we can make Fedora rock-solid. We have a culture of coordinating new features and pushing fixes upstream as much as we can. Your feedback improves not only Fedora, but Linux and free software as a whole.
-
-#### More information
-
-For more detailed information about what’s new on Fedora 30 Beta release, you can consult the [Fedora 30 Change set][11]. It contains more technical information about the new packages and improvements shipped with this release.
-
---------------------------------------------------------------------------------
-
-via: https://fedoramagazine.org/announcing-the-release-of-fedora-30-beta/
-
-作者:[Ben Cotton][a]
-选题:[lujun9972][b]
-译者:[译者ID](https://github.com/译者ID)
-校对:[校对者ID](https://github.com/校对者ID)
-
-本文由 [LCTT](https://github.com/LCTT/TranslateProject) 原创编译,[Linux中国](https://linux.cn/) 荣誉推出
-
-[a]: https://fedoramagazine.org/author/bcotton/
-[b]: https://github.com/lujun9972
-[1]: https://fedoramagazine.org/wp-content/uploads/2019/03/f30-beta-816x345.jpg
-[2]: https://getfedora.org/workstation/prerelease/
-[3]: https://getfedora.org/server/prerelease/
-[4]: https://silverblue.fedoraproject.org/download
-[5]: https://spins.fedoraproject.org/prerelease
-[6]: https://labs.fedoraproject.org/prerelease
-[7]: https://arm.fedoraproject.org/prerelease
-[8]: https://www.deepin.org/en/dde/
-[9]: https://www.fosslinux.com/4652/pantheon-everything-you-need-to-know-about-the-elementary-os-desktop.htm
-[10]: https://help.gnome.org/misc/release-notes/3.32/
-[11]: https://fedoraproject.org/wiki/Releases/30/ChangeSet
-[12]: https://fedoraproject.org/wiki/Common_F30_bugs
-[13]: https://docs.fedoraproject.org/en-US/quick-docs/howto-file-a-bug/
diff --git a/sources/tech/20190403 How to rebase to Fedora 30 Beta on Silverblue.md b/sources/tech/20190403 How to rebase to Fedora 30 Beta on Silverblue.md
deleted file mode 100644
index 892afff5d6..0000000000
--- a/sources/tech/20190403 How to rebase to Fedora 30 Beta on Silverblue.md
+++ /dev/null
@@ -1,70 +0,0 @@
-[#]: collector: (lujun9972)
-[#]: translator: ( )
-[#]: reviewer: ( )
-[#]: publisher: ( )
-[#]: url: ( )
-[#]: subject: (How to rebase to Fedora 30 Beta on Silverblue)
-[#]: via: (https://fedoramagazine.org/how-to-rebase-to-fedora-30-beta-on-silverblue/)
-[#]: author: (Michal Konečný https://fedoramagazine.org/author/zlopez/)
-
-How to rebase to Fedora 30 Beta on Silverblue
-======
-
-![][1]
-
-Silverblue is [an operating system for your desktop built on Fedora][2]. It’s excellent for daily use, development, and container-based workflows. It offers [numerous advantages][3] such as being able to roll back in case of any problems. If you want to test Fedora 30 on your Silverblue system, this article tells you how. It not only shows you what to do, but also how to revert back if anything unforeseen happens.
-
-### Switching to Fedora 30 branch
-
-Switching to Fedora 30 on Silverblue is easy. First, check if the _30_ branch is available, which should be true now:
-
-```
-ostree remote refs fedora-workstation
-```
-
-You should see the following in the output:
-
-```
-fedora-workstation:fedora/30/x86_64/silverblue
-```
-
-Next, import the GPG key for the Fedora 30 branch. Without this step, you won’t be able to rebase.
-
-```
-sudo ostree remote gpg-import fedora-workstation -k /etc/pki/rpm-gpg/RPM-GPG-KEY-fedora-30-primary
-```
-
-Next, rebase your system to the Fedora 30 branch.
-
-```
-rpm-ostree rebase fedora-workstation:fedora/30/x86_64/silverblue
-```
-
-Finally, the last thing to do is restart your computer and boot to Fedora 30.
-
-### How to revert things back
-
-Remember that Fedora 30’s still in beta testing phase, so there could still be some issues. If anything bad happens — for instance, if you can’t boot to Fedora 30 at all — it’s easy to go back. Just pick the previous entry in GRUB, and your system will start in its previous state before switching to Fedora 30. To make this change permanent, use the following command:
-
-```
-rpm-ostree rollback
-```
-
-That’s it. Now you know how to rebase to Fedora 30 and back. So why not test it today? 🙂
-
---------------------------------------------------------------------------------
-
-via: https://fedoramagazine.org/how-to-rebase-to-fedora-30-beta-on-silverblue/
-
-作者:[Michal Konečný][a]
-选题:[lujun9972][b]
-译者:[译者ID](https://github.com/译者ID)
-校对:[校对者ID](https://github.com/校对者ID)
-
-本文由 [LCTT](https://github.com/LCTT/TranslateProject) 原创编译,[Linux中国](https://linux.cn/) 荣誉推出
-
-[a]: https://fedoramagazine.org/author/zlopez/
-[b]: https://github.com/lujun9972
-[1]: https://fedoramagazine.org/wp-content/uploads/2019/03/silverblue-f30beta-816x345.jpg
-[2]: https://docs.fedoraproject.org/en-US/fedora-silverblue/
-[3]: https://fedoramagazine.org/give-fedora-silverblue-a-test-drive/
diff --git a/sources/tech/20190408 Getting started with Python-s cryptography library.md b/sources/tech/20190408 Getting started with Python-s cryptography library.md
deleted file mode 100644
index 9ed9211adf..0000000000
--- a/sources/tech/20190408 Getting started with Python-s cryptography library.md
+++ /dev/null
@@ -1,111 +0,0 @@
-[#]: collector: (lujun9972)
-[#]: translator: ( )
-[#]: reviewer: ( )
-[#]: publisher: ( )
-[#]: url: ( )
-[#]: subject: (Getting started with Python's cryptography library)
-[#]: via: (https://opensource.com/article/19/4/cryptography-python)
-[#]: author: (Moshe Zadka https://opensource.com/users/moshez)
-
-Getting started with Python's cryptography library
-======
-Encrypt your data and keep it safe from attackers.
-![lock on world map][1]
-
-The first rule of cryptography club is: never _invent_ a cryptography system yourself. The second rule of cryptography club is: never _implement_ a cryptography system yourself: many real-world holes are found in the _implementation_ phase of a cryptosystem as well as in the design.
-
-One useful library for cryptographic primitives in Python is called simply [**cryptography**][2]. It has both "secure" primitives as well as a "hazmat" layer. The "hazmat" layer requires care and knowledge of cryptography and it is easy to implement security holes using it. We will not cover anything in the "hazmat" layer in this introductory article!
-
-The most useful high-level secure primitive in **cryptography** is the Fernet implementation. Fernet is a standard for encrypting buffers in a way that follows best-practices cryptography. It is not suitable for very big files—anything in the gigabyte range and above—since it requires you to load the whole buffer that you want to encrypt or decrypt into memory at once.
-
-Fernet supports _symmetric_ , or _secret key_ , cryptography: the same key is used for encryption and decryption, and therefore must be kept safe.
-
-Generating a key is easy:
-
-
-```
->>> k = fernet.Fernet.generate_key()
->>> type(k)
-
-```
-
-Those bytes can be written to a file with appropriate permissions, ideally on a secure machine.
-
-Once you have key material, encrypting is easy as well:
-
-
-```
->>> frn = fernet.Fernet(k)
->>> encrypted = frn.encrypt(b"x marks the spot")
->>> encrypted[:10]
-b'gAAAAABb1'
-```
-
-You will get slightly different values if you encrypt on your machine. Not only because (I hope) you generated a different key from me, but because Fernet concatenates the value to be encrypted with some randomly generated buffer. This is one of the "best practices" I alluded to earlier: it will prevent an adversary from being able to tell which encrypted values are identical, which is sometimes an important part of an attack.
-
-Decryption is equally simple:
-
-
-```
->>> frn = fernet.Fernet(k)
->>> frn.decrypt(encrypted)
-b'x marks the spot'
-```
-
-Note that this only encrypts and decrypts _byte strings_. In order to encrypt and decrypt _text strings_ , they will need to be encoded and decoded, usually with [UTF-8][3].
-
-One of the most interesting advances in cryptography in the mid-20th century was _public key_ cryptography. It allows the encryption key to be published while the _decryption key_ is kept secret. It can, for example, be used to store API keys to be used by a server: the server is the only thing with access to the decryption key, but anyone can add to the store by using the public encryption key.
-
-While **cryptography** does not have any public key cryptographic _secure_ primitives, the [**PyNaCl**][4] library does. PyNaCl wraps and offers some nice ways to use the [**NaCl**][5] encryption system invented by Daniel J. Bernstein.
-
-NaCl always _encrypts_ and _signs_ or _decrypts_ and _verifies signatures_ simultaneously. This is a way to prevent malleability-based attacks, where an adversary modifies the encrypted value.
-
-Encryption is done with a public key, while signing is done with a secret key:
-
-
-```
->>> from nacl.public import PrivateKey, PublicKey, Box
->>> source = PrivateKey.generate()
->>> with open("target.pubkey", "rb") as fpin:
-... target_public_key = PublicKey(fpin.read())
->>> enc_box = Box(source, target_public_key)
->>> result = enc_box.encrypt(b"x marks the spot")
->>> result[:4]
-b'\xe2\x1c0\xa4'
-```
-
-Decryption reverses the roles: it needs the private key for decryption and the public key to verify the signature:
-
-
-```
->>> from nacl.public import PrivateKey, PublicKey, Box
->>> with open("source.pubkey", "rb") as fpin:
-... source_public_key = PublicKey(fpin.read())
->>> with open("target.private_key", "rb") as fpin:
-... target = PrivateKey(fpin.read())
->>> dec_box = Box(target, source_public_key)
->>> dec_box.decrypt(result)
-b'x marks the spot'
-```
-
-The [**PocketProtector**][6] library builds on top of PyNaCl and contains a complete secrets management solution.
-
---------------------------------------------------------------------------------
-
-via: https://opensource.com/article/19/4/cryptography-python
-
-作者:[Moshe Zadka (Community Moderator)][a]
-选题:[lujun9972][b]
-译者:[译者ID](https://github.com/译者ID)
-校对:[校对者ID](https://github.com/校对者ID)
-
-本文由 [LCTT](https://github.com/LCTT/TranslateProject) 原创编译,[Linux中国](https://linux.cn/) 荣誉推出
-
-[a]: https://opensource.com/users/moshez
-[b]: https://github.com/lujun9972
-[1]: https://opensource.com/sites/default/files/styles/image-full-size/public/lead-images/security-lock-cloud-safe.png?itok=yj2TFPzq (lock on world map)
-[2]: https://cryptography.io/en/latest/
-[3]: https://en.wikipedia.org/wiki/UTF-8
-[4]: https://pynacl.readthedocs.io/en/stable/
-[5]: https://nacl.cr.yp.to/
-[6]: https://github.com/SimpleLegal/pocket_protector/blob/master/USER_GUIDE.md
diff --git a/sources/tech/20190408 How to quickly deploy, run Linux applications as unikernels.md b/sources/tech/20190408 How to quickly deploy, run Linux applications as unikernels.md
deleted file mode 100644
index 6d65eaf369..0000000000
--- a/sources/tech/20190408 How to quickly deploy, run Linux applications as unikernels.md
+++ /dev/null
@@ -1,84 +0,0 @@
-[#]: collector: (lujun9972)
-[#]: translator: ( )
-[#]: reviewer: ( )
-[#]: publisher: ( )
-[#]: url: ( )
-[#]: subject: (How to quickly deploy, run Linux applications as unikernels)
-[#]: via: (https://www.networkworld.com/article/3387299/how-to-quickly-deploy-run-linux-applications-as-unikernels.html#tk.rss_all)
-[#]: author: (Sandra Henry-Stocker https://www.networkworld.com/author/Sandra-Henry_Stocker/)
-
-How to quickly deploy, run Linux applications as unikernels
-======
-Unikernels are a smaller, faster, and more secure option for deploying applications on cloud infrastructure. With NanoVMs OPS, anyone can run a Linux application as a unikernel with no additional coding.
-![Marcho Verch \(CC BY 2.0\)][1]
-
-Building and deploying lightweight apps is becoming an easier and more reliable process with the emergence of unikernels. While limited in functionality, unikernals offer many advantages in terms of speed and security.
-
-### What are unikernels?
-
-A unikernel is a very specialized single-address-space machine image that is similar to the kind of cloud applications that have come to dominate so much of the internet, but they are considerably smaller and are single-purpose. They are lightweight, providing only the resources needed. They load very quickly and are considerably more secure -- having a very limited attack surface. Any drivers, I/O routines and support libraries that are required are included in the single executable. The resultant virtual image can then be booted and run without anything else being present. And they will often run 10 to 20 times faster than a container.
-
-**[ Two-Minute Linux Tips:[Learn how to master a host of Linux commands in these 2-minute video tutorials][2] ]**
-
-Would-be attackers cannot drop into a shell and try to gain control because there is no shell. They can't try to grab the system's /etc/passwd or /etc/shadow files because these files don't exist. Creating a unikernel is much like turning your application into its own OS. With a unikernel, the application and the OS become a single entity. You omit what you don't need, thereby removing vulnerabilities and improving performance many times over.
-
-In short, unikernels:
-
- * Provide improved security (e.g., making shell code exploits impossible)
- * Have much smaller footprints then standard cloud apps
- * Are highly optimized
- * Boot extremely quickly
-
-
-
-### Are there any downsides to unikernels?
-
-The only serious downside to unikernels is that you have to build them. For many developers, this has been a giant step. Trimming down applications to just what is needed and then producing a tight, smoothly running application can be complex because of the application's low-level nature. In the past, you pretty much had to have been a systems developer or a low level programmer to generate them.
-
-### How is this changing?
-
-Just recently (March 24, 2019) [NanoVMs][3] announced a tool that loads any Linux application as a unikernel. Using NanoVMs OPS, anyone can run a Linux application as a unikernel with no additional coding. The application will also run faster, more safely and with less cost and overhead.
-
-### What is NanoVMs OPS?
-
-NanoVMs is a unikernel tool for developers. It allows you to run all sorts of enterprise class software yet still have extremely tight control over how it works.
-
-**[[Prepare to become a Certified Information Security Systems Professional with this comprehensive online course from PluralSight. Now offering a 10-day free trial!][4] ]**
-
-Other benefits associated with OPS include:
-
- * Developers need no prior experience or knowledge to build unikernels.
- * The tool can be used to build and run unikernels locally on a laptop.
- * No accounts need to be created and only a single download and one command is required to execute OPS.
-
-
-
-An intro to NanoVMs is available on [NanoVMs on youtube][5]. You can also check out the company's [LinkedIn page][6] and can read about NanoVMs security [here][7].
-
-Here is some information on how to [get started][8].
-
-Join the Network World communities on [Facebook][9] and [LinkedIn][10] to comment on topics that are top of mind.
-
---------------------------------------------------------------------------------
-
-via: https://www.networkworld.com/article/3387299/how-to-quickly-deploy-run-linux-applications-as-unikernels.html#tk.rss_all
-
-作者:[Sandra Henry-Stocker][a]
-选题:[lujun9972][b]
-译者:[译者ID](https://github.com/译者ID)
-校对:[校对者ID](https://github.com/校对者ID)
-
-本文由 [LCTT](https://github.com/LCTT/TranslateProject) 原创编译,[Linux中国](https://linux.cn/) 荣誉推出
-
-[a]: https://www.networkworld.com/author/Sandra-Henry_Stocker/
-[b]: https://github.com/lujun9972
-[1]: https://images.idgesg.net/images/article/2019/04/corn-kernels-100792925-large.jpg
-[2]: https://www.youtube.com/playlist?list=PL7D2RMSmRO9J8OTpjFECi8DJiTQdd4hua
-[3]: https://nanovms.com/
-[4]: https://pluralsight.pxf.io/c/321564/424552/7490?u=https%3A%2F%2Fwww.pluralsight.com%2Fpaths%2Fcertified-information-systems-security-professional-cisspr
-[5]: https://www.youtube.com/watch?v=VHWDGhuxHPM
-[6]: https://www.linkedin.com/company/nanovms/
-[7]: https://nanovms.com/security
-[8]: https://nanovms.gitbook.io/ops/getting_started
-[9]: https://www.facebook.com/NetworkWorld/
-[10]: https://www.linkedin.com/company/network-world
diff --git a/sources/tech/20190409 5 Linux rookie mistakes.md b/sources/tech/20190409 5 Linux rookie mistakes.md
deleted file mode 100644
index 2e2c25a9cf..0000000000
--- a/sources/tech/20190409 5 Linux rookie mistakes.md
+++ /dev/null
@@ -1,54 +0,0 @@
-[#]: collector: (lujun9972)
-[#]: translator: ( )
-[#]: reviewer: ( )
-[#]: publisher: ( )
-[#]: url: ( )
-[#]: subject: (5 Linux rookie mistakes)
-[#]: via: (https://opensource.com/article/19/4/linux-rookie-mistakes)
-[#]: author: (Jen Wike Huger https://opensource.com/users/jen-wike/users/bcotton/users/petercheer/users/greg-p/users/greg-p)
-
-5 Linux rookie mistakes
-======
-Linux enthusiasts share some of the biggest mistakes they made.
-![magnifying glass on computer screen, finding a bug in the code][1]
-
-It's smart to learn new skills throughout your life—it keeps your mind nimble and makes you more competitive in the job market. But some skills are harder to learn than others, especially those where small rookie mistakes can cost you a lot of time and trouble when you're trying to fix them.
-
-Take learning [Linux][2], for example. If you're used to working in a Windows or MacOS graphical interface, moving to Linux, with its unfamiliar commands typed into a terminal, can have a big learning curve. But the rewards are worth it, as the millions and millions of people who have gone before you have proven.
-
-That said, the journey won't be without pitfalls. We asked some of Linux enthusiasts to think back to when they first started using Linux and tell us about the biggest mistakes they made.
-
-"Don't go into [any sort of command line interface (CLI) work] with an expectation that commands work in rational or consistent ways, as that is likely to lead to frustration. This is not due to poor design choices—though it can feel like it when you're banging your head against the proverbial desk—but instead reflects the fact that these systems have evolved and been added onto through generations of software and OS evolution. Go with the flow, write down or memorize the commands you need, and (try not to) get frustrated when [things aren't what you'd expect][3]." _—[Gina Likins][4]_
-
-"As easy as it might be to just copy and paste commands to make the thing go, read the command first and at least have a general understanding of the actions that are about to be performed. Especially if there is a pipe command. Double especially if there is more than one. There are a lot of destructive commands that look innocuous until you realize what they can do (e.g., **rm** , **dd** ), and you don't want to accidentally destroy things. (Ask me how I know.)" _—[Katie McLaughlin][5]_
-
-"Early on in my Linux journey, I wasn't as aware of the importance of knowing where you are in the filesystem. I was deleting some file in what I thought was my home directory, and I entered **sudo rm -rf *** and deleted all of the boot files on my system. Now, I frequently use **pwd** to ensure that I am where I think I am before issuing such commands. Fortunately for me, I was able to boot my wounded laptop with a USB drive and recover my files." _—[Don Watkins][6]_
-
-"Do not reset permissions on the entire file system to [777][7] because you think 'permissions are hard to understand' and you want an application to have access to something." _—[Matthew Helmke][8]_
-
-"I was removing a package from my system, and I did not check what other packages it was dependent upon. I just let it remove whatever it wanted and ended up causing some of my important programs to crash and become unavailable." _—[Kedar Vijay Kulkarni][9]_
-
-What mistakes have you made while learning to use Linux? Share them in the comments.
-
---------------------------------------------------------------------------------
-
-via: https://opensource.com/article/19/4/linux-rookie-mistakes
-
-作者:[Jen Wike Huger (Red Hat)][a]
-选题:[lujun9972][b]
-译者:[译者ID](https://github.com/译者ID)
-校对:[校对者ID](https://github.com/校对者ID)
-
-本文由 [LCTT](https://github.com/LCTT/TranslateProject) 原创编译,[Linux中国](https://linux.cn/) 荣誉推出
-
-[a]: https://opensource.com/users/jen-wike/users/bcotton/users/petercheer/users/greg-p/users/greg-p
-[b]: https://github.com/lujun9972
-[1]: https://opensource.com/sites/default/files/styles/image-full-size/public/lead-images/mistake_bug_fix_find_error.png?itok=PZaz3dga (magnifying glass on computer screen, finding a bug in the code)
-[2]: https://opensource.com/resources/linux
-[3]: https://lintqueen.com/2017/07/02/learning-while-frustrated/
-[4]: https://opensource.com/users/lintqueen
-[5]: https://opensource.com/users/glasnt
-[6]: https://opensource.com/users/don-watkins
-[7]: https://www.maketecheasier.com/file-permissions-what-does-chmod-777-means/
-[8]: https://twitter.com/matthewhelmke
-[9]: https://opensource.com/users/kkulkarn
diff --git a/sources/tech/20190409 5 open source mobile apps.md b/sources/tech/20190409 5 open source mobile apps.md
deleted file mode 100644
index 679c1a92fc..0000000000
--- a/sources/tech/20190409 5 open source mobile apps.md
+++ /dev/null
@@ -1,131 +0,0 @@
-[#]: collector: (lujun9972)
-[#]: translator: (fuzheng1998 )
-[#]: reviewer: ( )
-[#]: publisher: ( )
-[#]: url: ( )
-[#]: subject: (5 open source mobile apps)
-[#]: via: (https://opensource.com/article/19/4/mobile-apps)
-[#]: author: (Chris Hermansen https://opensource.com/users/clhermansen/users/bcotton/users/clhermansen/users/bcotton/users/clhermansen)
-
-5 open source mobile apps
-======
-You can count on these apps to meet your needs for productivity,
-communication, and entertainment.
-![][1]
-
-Like most people in the world, I'm rarely further than an arm's reach from my smartphone. My Android device provides a seemingly limitless number of communication, productivity, and entertainment services thanks to the open source mobile apps I've installed from Google Play and F-Droid.
-
-Of the many open source apps on my phone, the following five are the ones I consistently turn to whether I want to listen to music; connect with friends, family, and colleagues; or get work done on the go.
-
-### MPDroid
-
-_An Android controller for the Music Player Daemon (MPD)_
-
-![MPDroid][2]
-
-MPD is a great way to get music from little music server computers out to the big black stereo boxes. It talks straight to ALSA and therefore to the Digital-to-Analog Converter ([DAC][3]) via the ALSA hardware interface, and it can be controlled over my network—but by what? Well, it turns out that MPDroid is a great MPD controller. It manages my music database, displays album art, handles playlists, and supports internet radio. And it's open source, so if something doesn't work…
-
-MPDroid is available on [Google Play][4] and [F-Droid][5].
-
-### RadioDroid
-
-_An Android internet radio tuner that I use standalone and with Chromecast_
-
-**
-
-**
-
-**
-
-_![RadioDroid][6]_
-
-RadioDroid is to internet radio as MPDroid is to managing my music database; essentially, RadioDroid is a frontend to [Internet-Radio.com][7]. Moreover, RadioDroid can be enjoyed by plugging headphones into the Android device, by connecting the Android device directly to the stereo via the headphone jack or USB, or by using its Chromecast capability with a compatible device. It's a fine way to check the weather in Finland, listen to the Spanish top 40, or hear the latest news from down under.
-
-RadioDroid is available on [Google Play][8] and [F-Droid][9].
-
-### Signal
-
-_A secure messaging client for Android, iOS, and desktop_
-
-**
-
-**
-
-**
-
-_![Signal][10]_
-
-If you like WhatsApp but are bothered by its [getting-closer-every-day][11] relationship to Facebook, Signal should be your next thing. The only problem with Signal is convincing your contacts they're better off replacing WhatsApp with Signal. But other than that, it has a similar interface; great voice and video calling; great encryption; decent anonymity; and it's supported by a foundation that doesn't plan to monetize your use of the software. What's not to like?
-
-Signal is available for [Android][12], [iOS][13], and [desktop][14].
-
-### ConnectBot
-
-_Android SSH client_
-
-**
-
-**
-
-**
-
-_![ConnectBot][15]_
-
-Sometimes I'm far away from my computer, but I need to log into the server to do something. [ConnectBot][16] is a great solution for moving SSH sessions onto my phone.
-
-ConnectBot is available on [Google Play][17].
-
-### Termux
-
-_Android terminal emulator with many familiar utilities_
-
-**
-
-**
-
-**
-
-_![Termux][18]_
-
-Have you ever needed to run an **awk** script on your phone? [Termux][19] is your solution. If you need to do terminal-type stuff, and you don't want to maintain an SSH connection to a remote computer the whole time, bring the files over to your phone with ConnectBot, quit the session, do your stuff in Termux, and send the results back with ConnectBot.
-
-Termux is available on [Google Play][20] and [F-Droid][21].
-
-* * *
-
-What are your favorite open source mobile apps for work or fun? Please share them in the comments.
-
---------------------------------------------------------------------------------
-
-via: https://opensource.com/article/19/4/mobile-apps
-
-作者:[Chris Hermansen (Community Moderator)][a]
-选题:[lujun9972][b]
-译者:[译者ID](https://github.com/译者ID)
-校对:[校对者ID](https://github.com/校对者ID)
-
-本文由 [LCTT](https://github.com/LCTT/TranslateProject) 原创编译,[Linux中国](https://linux.cn/) 荣誉推出
-
-[a]: https://opensource.com/users/clhermansen/users/bcotton/users/clhermansen/users/bcotton/users/clhermansen
-[b]: https://github.com/lujun9972
-[1]: https://opensource.com/sites/default/files/styles/image-full-size/public/lead-images/rh_003588_01_rd3os.combacktoschoolserieshe_rh_041x_0.png?itok=tfg6_I78
-[2]: https://opensource.com/sites/default/files/uploads/mpdroid.jpg (MPDroid)
-[3]: https://opensource.com/article/17/4/fun-new-gadget
-[4]: https://play.google.com/store/apps/details?id=com.namelessdev.mpdroid&hl=en_US
-[5]: https://f-droid.org/en/packages/com.namelessdev.mpdroid/
-[6]: https://opensource.com/sites/default/files/uploads/radiodroid.png (RadioDroid)
-[7]: https://www.internet-radio.com/
-[8]: https://play.google.com/store/apps/details?id=net.programmierecke.radiodroid2
-[9]: https://f-droid.org/en/packages/net.programmierecke.radiodroid2/
-[10]: https://opensource.com/sites/default/files/uploads/signal.png (Signal)
-[11]: https://opensource.com/article/19/3/open-messenger-client
-[12]: https://play.google.com/store/apps/details?id=org.thoughtcrime.securesms
-[13]: https://itunes.apple.com/us/app/signal-private-messenger/id874139669?mt=8
-[14]: https://signal.org/download/
-[15]: https://opensource.com/sites/default/files/uploads/connectbot.png (ConnectBot)
-[16]: https://connectbot.org/
-[17]: https://play.google.com/store/apps/details?id=org.connectbot
-[18]: https://opensource.com/sites/default/files/uploads/termux.jpg (Termux)
-[19]: https://termux.com/
-[20]: https://play.google.com/store/apps/details?id=com.termux
-[21]: https://f-droid.org/packages/com.termux/
diff --git a/sources/tech/20190409 Anbox - Easy Way To Run Android Apps On Linux.md b/sources/tech/20190409 Anbox - Easy Way To Run Android Apps On Linux.md
deleted file mode 100644
index c7b0ba82c8..0000000000
--- a/sources/tech/20190409 Anbox - Easy Way To Run Android Apps On Linux.md
+++ /dev/null
@@ -1,182 +0,0 @@
-[#]: collector: (lujun9972)
-[#]: translator: ( )
-[#]: reviewer: ( )
-[#]: publisher: ( )
-[#]: url: ( )
-[#]: subject: (Anbox – Easy Way To Run Android Apps On Linux)
-[#]: via: (https://www.2daygeek.com/anbox-best-android-emulator-for-linux/)
-[#]: author: (Magesh Maruthamuthu https://www.2daygeek.com/author/magesh/)
-
-Anbox – Easy Way To Run Android Apps On Linux
-======
-
-Android emulator applications are allow us to run our favorite Android apps or games directly from Linux system.
-
-There are many android emulators were available for Linux and we had covered few applications in the past.
-
-You can review those by navigating to the following URLs.
-
- * [How To Install Official Android Emulator (SDK) On Linux][1]
- * [How To Install GenyMotion (Android Emulator) On Linux][2]
-
-
-
-Today we are going to discuss about the Anbox Android emulator.
-
-### What Is Anbox?
-
-Anbox stands for Android in a box. Anbox is a container-based approach to boot a full Android system on a regular GNU/Linux system.
-
-It’s new and modern emulator among others.
-
-Since Anbox places the core Android OS into a container using Linux namespaces (LXE) so, there is no slowness while accessing the installed applications.
-
-Anbox will let you run Android on your Linux system without the slowness of virtualization because the core Android OS has placed into a container using Linux namespaces (LXE).
-
-There is no direct access to any hardware from the Android container. All hardware access are going through the anbox daemon on the host.
-
-Each applications will be open in a separate window, just like other native system applications, and it can be showing up in the launcher.
-
-### How To Install Anbox In Linux?
-
-Anbox application is available as snap package so, make sure you have enabled snap support on your system.
-
-Anbox package is recently added to the Ubuntu (Cosmic) and Debian (Buster) repositories. If you are running these version then you can easily install with help of official distribution package manager. Other wise go with snap package installation.
-
-Make sure the necessary kernel modules should be installed in your system in order to work Anbox. For Ubuntu based users, use the following PPA to install it.
-
-```
-$ sudo add-apt-repository ppa:morphis/anbox-support
-$ sudo apt update
-$ sudo apt install linux-headers-generic anbox-modules-dkms
-```
-
-After you installed the `anbox-modules-dkms` package you have to manually reload the kernel modules or system reboot is required.
-
-```
-$ sudo modprobe ashmem_linux
-$ sudo modprobe binder_linux
-```
-
-For **`Debian/Ubuntu`** systems, use **[APT-GET Command][3]** or **[APT Command][4]** to install anbox.
-
-```
-$ sudo apt install anbox
-```
-
-We always used to get package for Arch Linux based systems from AUR repository. So, use any of the **[AUR helper][5]** to install it. I prefer to go with **[Yay utility][6]**.
-
-```
-$ yuk -S anbox-git
-```
-
-If no, you can **[install and configure snaps in Linux][7]** by navigating to the following article. Others can ignore if you have already installed snaps on your system.
-
-```
-$ sudo snap install --devmode --beta anbox
-```
-
-### Prerequisites For Anbox
-
-By default, Anbox doesn’t ship with the Google Play Store.
-
-Hence, we need to manually download each application (APK) and install it using Android Debug Bridge (ADB).
-
-The ADB tool is readily available in most of the distributions repository so, we can easily install it.
-
-For **`Debian/Ubuntu`** systems, use **[APT-GET Command][3]** or **[APT Command][4]** to install ADB.
-
-```
-$ sudo apt install android-tools-adb
-```
-
-For **`Fedora`** system, use **[DNF Command][8]** to install ADB.
-
-```
-$ sudo dnf install android-tools
-```
-
-For **`Arch Linux`** based systems, use **[Pacman Command][9]** to install ADB.
-
-```
-$ sudo pacman -S android-tools
-```
-
-For **`openSUSE Leap`** system, use **[Zypper Command][10]** to install ADB.
-
-```
-$ sudo zypper install android-tools
-```
-
-### Where To Download The Android Apps?
-
-Since you can’t use the Play Store so, you have to download the APK packages from trusted sites like [APKMirror][11] then manually install it.
-
-### How To Launch Anbox?
-
-Anbox can be launched from the Dash. This is how the default Anbox looks.
-![][13]
-
-### How To Push The Apps Into Anbox?
-
-As i told previously, we need to manually install it. For testing purpose, we are going to install `YouTube` and `Firefox` apps.
-
-First, you need to start ADB server. To do so, run the following command.
-
-```
-$ adb devices
-```
-
-We have already downloaded the `YouTube` and `Firefox` apps and the same we will install now.
-
-**Common Syntax:**
-
-```
-$ adb install Name-Of-Your-Application.apk
-```
-
-Installing YouTube and Firefox app.
-
-```
-$ adb install 'com.google.android.youtube_14.13.54-1413542800_minAPI19(x86_64)(nodpi)_apkmirror.com.apk'
-Success
-
-$ adb install 'org.mozilla.focus_9.0-330191219_minAPI21(x86)(nodpi)_apkmirror.com.apk'
-Success
-```
-
-I have installed `YouTube` and `Firefox` in my Anbox. See the screenshot below.
-![][14]
-
-As we told in the beginning of the article, it will open any app as a new tab. Here, I’m going to open Firefox and accessing the **[2daygeek.com][15]** website.
-![][16]
-
---------------------------------------------------------------------------------
-
-via: https://www.2daygeek.com/anbox-best-android-emulator-for-linux/
-
-作者:[Magesh Maruthamuthu][a]
-选题:[lujun9972][b]
-译者:[译者ID](https://github.com/译者ID)
-校对:[校对者ID](https://github.com/校对者ID)
-
-本文由 [LCTT](https://github.com/LCTT/TranslateProject) 原创编译,[Linux中国](https://linux.cn/) 荣誉推出
-
-[a]: https://www.2daygeek.com/author/magesh/
-[b]: https://github.com/lujun9972
-[1]: https://www.2daygeek.com/install-configure-sdk-android-emulator-on-linux/
-[2]: https://www.2daygeek.com/install-genymotion-android-emulator-on-ubuntu-debian-fedora-arch-linux/
-[3]: https://www.2daygeek.com/apt-get-apt-cache-command-examples-manage-packages-debian-ubuntu-systems/
-[4]: https://www.2daygeek.com/apt-command-examples-manage-packages-debian-ubuntu-systems/
-[5]: https://www.2daygeek.com/category/aur-helper/
-[6]: https://www.2daygeek.com/install-yay-yet-another-yogurt-aur-helper-on-arch-linux/
-[7]: https://www.2daygeek.com/linux-snap-package-manager-ubuntu/
-[8]: https://www.2daygeek.com/dnf-command-examples-manage-packages-fedora-system/
-[9]: https://www.2daygeek.com/pacman-command-examples-manage-packages-arch-linux-system/
-[10]: https://www.2daygeek.com/zypper-command-examples-manage-packages-opensuse-system/
-[11]: https://www.apkmirror.com/
-[12]: data:image/gif;base64,R0lGODlhAQABAIAAAAAAAP///yH5BAEAAAAALAAAAAABAAEAAAIBRAA7
-[13]: https://www.2daygeek.com/wp-content/uploads/2019/04/anbox-best-android-emulator-for-linux-1.jpg
-[14]: https://www.2daygeek.com/wp-content/uploads/2019/04/anbox-best-android-emulator-for-linux-2.jpg
-[15]: https://www.2daygeek.com/
-[16]: https://www.2daygeek.com/wp-content/uploads/2019/04/anbox-best-android-emulator-for-linux-3.jpg
diff --git a/sources/tech/20190409 The Microsoft-BMW IoT Open Manufacturing Platform might not be so open.md b/sources/tech/20190409 The Microsoft-BMW IoT Open Manufacturing Platform might not be so open.md
deleted file mode 100644
index c74f61efe4..0000000000
--- a/sources/tech/20190409 The Microsoft-BMW IoT Open Manufacturing Platform might not be so open.md
+++ /dev/null
@@ -1,69 +0,0 @@
-[#]: collector: (lujun9972)
-[#]: translator: ( )
-[#]: reviewer: ( )
-[#]: publisher: ( )
-[#]: url: ( )
-[#]: subject: (The Microsoft/BMW IoT Open Manufacturing Platform might not be so open)
-[#]: via: (https://www.networkworld.com/article/3387642/the-microsoftbmw-iot-open-manufacturing-platform-might-not-be-so-open.html#tk.rss_all)
-[#]: author: (Fredric Paul https://www.networkworld.com/author/Fredric-Paul/)
-
-The Microsoft/BMW IoT Open Manufacturing Platform might not be so open
-======
-The new industrial IoT Open Manufacturing Platform from Microsoft and BMW runs only on Microsoft Azure. That could be an issue.
-![Martyn Williams][1]
-
-Last week at [Hannover Messe][2], Microsoft and German carmaker BMW announced a partnership to build a hardware and software technology framework and reference architecture for the industrial internet of things (IoT), and foster a community to spread these smart-factory solutions across the automotive and manufacturing industries.
-
-The stated goal of the [Open Manufacturing Platform (OMP)][3]? According to the press release, it's “to drive open industrial IoT development and help grow a community to build future [Industry 4.0][4] solutions.” To make that a reality, the companies said that by the end of 2019, they plan to attract four to six partners — including manufacturers and suppliers from both inside and outside the automotive industry — and to have rolled out at least 15 use cases operating in actual production environments.
-
-**[ Read also:[An inside look at an IIoT-powered smart factory][5] | Get regularly scheduled insights: [Sign up for Network World newsletters][6] ]**
-
-### Complex and proprietary is bad for IoT
-
-It sounds like a great idea, right? As the companies rightly point out, many of today’s industrial IoT solutions rely on “complex, proprietary systems that create data silos and slow productivity.” Who wouldn’t want to “standardize data models that enable analytics and machine learning scenarios” and “accelerate future industrial IoT developments, shorten time to value, and drive production efficiencies while addressing common industrial challenges”?
-
-But before you get too excited, let’s talk about a key word in the effort: open. As Scott Guthrie, executive vice president of Microsoft Cloud + AI Group, said in a statement, "Our commitment to building an open community will create new opportunities for collaboration across the entire manufacturing value chain."
-
-### The Open Manufacturing Platform is open only to Microsoft Azure
-
-However, that will happen as long as all that collaboration occurs in Microsoft Azure. I’m not saying Azure isn’t up to the task, but it’s hardly the only (or even the leading) cloud platform interested in the industrial IoT. Putting everything in Azure might be an issue to those potential OMP partners. It’s an “open” question as to how many companies already invested in Amazon Web Services (AWS) or the Google Cloud Platform (GCP) will be willing to make the switch or go multi-cloud just to take advantage of the OMP.
-
-My guess is that Microsoft and BMW won’t have too much trouble meeting their initial goals for the OMP. It shouldn’t be that hard to get a handful of existing Azure customers to come up with 15 use cases leveraging advances in analytics, artificial intelligence (AI), and digital feedback loops. (As an example, the companies cited the autonomous transport systems in BMW’s factory in Regensburg, Germany, part of the more than 3,000 machines, robots and transport systems connected with the BMW Group’s IoT platform, which — naturally — is built on Microsoft Azure's cloud.)
-
-### Will non-Azure users jump on board the OMP?
-
-The question is whether tying all this to a single cloud provider will affect the effort to attract enough new companies — including companies not currently using Azure — to establish a truly viable open platform?
-
-Perhaps [Stacey Higginbotham at Stacy on IoT put it best][7]:
-
-> “What they really launched is a reference design for manufacturers to work from.”
-
-That’s not nothing, of course, but it’s a lot less ambitious than building a new industrial IoT platform. And it may not easily fulfill the vision of a community working together to create shared solutions that benefit everyone.
-
-**[ Now read this:[Why are IoT platforms so darn confusing?][8] ]**
-
-Join the Network World communities on [Facebook][9] and [LinkedIn][10] to comment on topics that are top of mind.
-
---------------------------------------------------------------------------------
-
-via: https://www.networkworld.com/article/3387642/the-microsoftbmw-iot-open-manufacturing-platform-might-not-be-so-open.html#tk.rss_all
-
-作者:[Fredric Paul][a]
-选题:[lujun9972][b]
-译者:[译者ID](https://github.com/译者ID)
-校对:[校对者ID](https://github.com/校对者ID)
-
-本文由 [LCTT](https://github.com/LCTT/TranslateProject) 原创编译,[Linux中国](https://linux.cn/) 荣誉推出
-
-[a]: https://www.networkworld.com/author/Fredric-Paul/
-[b]: https://github.com/lujun9972
-[1]: https://images.techhive.com/images/article/2017/01/20170107_105344-100702818-large.jpg
-[2]: https://www.hannovermesse.de/home
-[3]: https://www.prnewswire.co.uk/news-releases/microsoft-and-the-bmw-group-launch-the-open-manufacturing-platform-859672858.html
-[4]: https://en.wikipedia.org/wiki/Industry_4.0
-[5]: https://www.networkworld.com/article/3384378/an-inside-look-at-tempo-automations-iiot-powered-smart-factory.html
-[6]: https://www.networkworld.com/newsletters/signup.html
-[7]: https://mailchi.mp/iotpodcast/stacey-on-iot-industrial-iot-reminds-me-of-apples-ecosystem?e=6bf9beb394
-[8]: https://www.networkworld.com/article/3336166/why-are-iot-platforms-so-darn-confusing.html
-[9]: https://www.facebook.com/NetworkWorld/
-[10]: https://www.linkedin.com/company/network-world
diff --git a/sources/tech/20190410 How we built a Linux desktop app with Electron.md b/sources/tech/20190410 How we built a Linux desktop app with Electron.md
deleted file mode 100644
index eb11c65614..0000000000
--- a/sources/tech/20190410 How we built a Linux desktop app with Electron.md
+++ /dev/null
@@ -1,101 +0,0 @@
-[#]: collector: (lujun9972)
-[#]: translator: ( )
-[#]: reviewer: ( )
-[#]: publisher: ( )
-[#]: url: ( )
-[#]: subject: (How we built a Linux desktop app with Electron)
-[#]: via: (https://opensource.com/article/19/4/linux-desktop-electron)
-[#]: author: (Nils Ganther https://opensource.com/users/nils-ganther)
-
-How we built a Linux desktop app with Electron
-======
-A story of building an open source email service that runs natively on
-Linux desktops, thanks to the Electron framework.
-![document sending][1]
-
-[Tutanota][2] is a secure, open source email service that's been available as an app for the browser, iOS, and Android. The client code is published under GPLv3 and the Android app is available on [F-Droid][3] to enable everyone to use a completely Google-free version.
-
-Because Tutanota focuses on open source and develops on Linux clients, we wanted to release a desktop app for Linux and other platforms. Being a small team, we quickly ruled out building native apps for Linux, Windows, and MacOS and decided to adapt our app using [Electron][4].
-
-Electron is the go-to choice for anyone who wants to ship visually consistent, cross-platform applications, fast—especially if there's already a web app that needs to be freed from the shackles of the browser API. Tutanota is exactly such a case.
-
-Tutanota is based on [SystemJS][5] and [Mithril][6] and aims to offer simple, secure email communications for everybody. As such, it has to provide a lot of the standard features users expect from any email client.
-
-Some of these features, like basic push notifications, search for text and contacts, and support for two-factor authentication are easy to offer in the browser thanks to modern APIs and standards. Other features (such as automatic backups or IMAP support without involving our servers) need less-restricted access to system resources, which is exactly what the Electron framework provides.
-
-While some criticize Electron as "just a basic wrapper," it has obvious benefits:
-
- * Electron enables you to adapt a web app quickly for Linux, Windows, and MacOS desktops. In fact, most Linux desktop apps are built with Electron.
- * Electron enables you to easily bring the desktop client to feature parity with the web app.
- * Once you've published the desktop app, you can use free development capacity to add desktop-specific features that enhance usability and security.
- * And last but certainly not least, it's a great way to make the app feel native and integrated into the user's system while maintaining its identity.
-
-
-
-### Meeting users' needs
-
-At Tutanota, we do not rely on big investor money, rather we are a community-driven project. We grow our team organically based on the increasing number of users upgrading to our freemium service's paid plans. Listening to what users want is not only important to us, it is essential to our success.
-
-Offering a desktop client was users' [most-wanted feature][7] in Tutanota, and we are proud that we can now offer free beta desktop clients to all of our users. (We also implemented another highly requested feature—[search on encrypted data][8]—but that's a topic for another time.)
-
-We liked the idea of providing users with signed versions of Tutanota and enabling functions that are impossible in the browser, such as push notifications via a background process. Now we plan to add more desktop-specific features, such as IMAP support without depending on our servers to act as a proxy, automatic backups, and offline availability.
-
-We chose Electron because its combination of Chromium and Node.js promised to be the best fit for our small development team, as it required only minimal changes to our web app. It was particularly helpful to use the browser APIs for everything as we got started, slowly replacing those components with more native versions as we progressed. This approach was especially handy with attachment downloads and notifications.
-
-### Tuning security
-
-We were aware that some people cite security problems with Electron, but we found Electron's options for fine-tuning access in the web app quite satisfactory. You can use resources like the Electron's [security documentation][9] and Luca Carettoni's [Electron Security Checklist][10] to help prevent catastrophic mishaps with untrusted content in your web app.
-
-### Achieving feature parity
-
-The Tutanota web client was built from the start with a solid protocol for interprocess communication. We utilize web workers to keep user interface (UI) rendering responsive while encrypting and requesting data. This came in handy when we started implementing our mobile apps, which use the same protocol to communicate between the native part and the web view.
-
-That's why when we started building the desktop clients, a lot of bindings for things like native push notifications, opening mailboxes, and working with the filesystem were already there, so only the native (node) side had to be implemented.
-
-Another convenience was our build process using the [Babel transpiler][11], which allows us to write the entire codebase in modern ES6 JavaScript and mix-and-match utility modules between the different environments. This enabled us to speedily adapt the code for the Electron-based desktop apps. However, we encountered some challenges.
-
-### Overcoming challenges
-
-While Electron allows us to integrate with the different platforms' desktop environments pretty easily, you can't underestimate the time investment to get things just right! In the end, it was these little things that took up much more time than we expected but were also crucial to finish the desktop client project.
-
-The places where platform-specific code was necessary caused most of the friction:
-
- * Window management and the tray, for example, are still handled in subtly different ways on the three platforms.
- * Registering Tutanota as the default mail program and setting up autostart required diving into the Windows Registry while making sure to prompt the user for admin access in a [UAC][12]-compatible way.
- * We needed to use Electron's API for shortcuts and menus to offer even standard features like copy, paste, undo, and redo.
-
-
-
-This process was complicated a bit by users' expectations of certain, sometimes not directly compatible behavior of the apps on different platforms. Making the three versions feel native required some iteration and even some modest additions to the web app to offer a text search similar to the one in the browser.
-
-### Wrapping up
-
-Our experience with Electron was largely positive, and we completed the project in less than four months. Despite some rather time-consuming features, we were surprised about the ease with which we could ship a beta version of the [Tutanota desktop client for Linux][13]. If you're interested, you can dive into the source code on [GitHub][14].
-
---------------------------------------------------------------------------------
-
-via: https://opensource.com/article/19/4/linux-desktop-electron
-
-作者:[Nils Ganther][a]
-选题:[lujun9972][b]
-译者:[译者ID](https://github.com/译者ID)
-校对:[校对者ID](https://github.com/校对者ID)
-
-本文由 [LCTT](https://github.com/LCTT/TranslateProject) 原创编译,[Linux中国](https://linux.cn/) 荣誉推出
-
-[a]: https://opensource.com/users/nils-ganther
-[b]: https://github.com/lujun9972
-[1]: https://opensource.com/sites/default/files/styles/image-full-size/public/lead-images/email_paper_envelope_document.png?itok=uPj_kouJ (document sending)
-[2]: https://tutanota.com/
-[3]: https://f-droid.org/en/packages/de.tutao.tutanota/
-[4]: https://electronjs.org/
-[5]: https://github.com/systemjs/systemjs
-[6]: https://mithril.js.org/
-[7]: https://tutanota.uservoice.com/forums/237921-general/filters/top?status_id=1177482
-[8]: https://tutanota.com/blog/posts/first-search-encrypted-data/
-[9]: https://electronjs.org/docs/tutorial/security
-[10]: https://www.blackhat.com/docs/us-17/thursday/us-17-Carettoni-Electronegativity-A-Study-Of-Electron-Security-wp.pdf
-[11]: https://babeljs.io/
-[12]: https://en.wikipedia.org/wiki/User_Account_Control
-[13]: https://tutanota.com/blog/posts/desktop-clients/
-[14]: https://www.github.com/tutao/tutanota
diff --git a/sources/tech/20190411 Be your own certificate authority.md b/sources/tech/20190411 Be your own certificate authority.md
deleted file mode 100644
index f6ea26aba4..0000000000
--- a/sources/tech/20190411 Be your own certificate authority.md
+++ /dev/null
@@ -1,135 +0,0 @@
-[#]: collector: (lujun9972)
-[#]: translator: ( )
-[#]: reviewer: ( )
-[#]: publisher: ( )
-[#]: url: ( )
-[#]: subject: (Be your own certificate authority)
-[#]: via: (https://opensource.com/article/19/4/certificate-authority)
-[#]: author: (Moshe Zadka https://opensource.com/users/moshez/users/elenajon123)
-
-Be your own certificate authority
-======
-Create a simple, internal CA for your microservice architecture or
-integration testing.
-![][1]
-
-The Transport Layer Security ([TLS][2]) model, which is sometimes referred to by the older name SSL, is based on the concept of [certificate authorities][3] (CAs). These authorities are trusted by browsers and operating systems and, in turn, _sign_ servers' certificates to validate their ownership.
-
-However, for an intranet, a microservice architecture, or integration testing, it is sometimes useful to have a _local CA_ : one that is trusted only internally and, in turn, signs local servers' certificates.
-
-This especially makes sense for integration tests. Getting certificates can be a burden because the servers will be up for minutes. But having an "ignore certificate" option in the code could allow it to be activated in production, leading to a security catastrophe.
-
-A CA certificate is not much different from a regular server certificate; what matters is that it is trusted by local code. For example, in the **requests** library, this can be done by setting the **REQUESTS_CA_BUNDLE** variable to a directory containing this certificate.
-
-In the example of creating a certificate for integration tests, there is no need for a _long-lived_ certificate: if your integration tests take more than a day, you have already failed.
-
-So, calculate **yesterday** and **tomorrow** as the validity interval:
-
-
-```
->>> import datetime
->>> one_day = datetime.timedelta(days=1)
->>> today = datetime.date.today()
->>> yesterday = today - one_day
->>> tomorrow = today - one_day
-```
-
-Now you are ready to create a simple CA certificate. You need to generate a private key, create a public key, set up the "parameters" of the CA, and then self-sign the certificate: a CA certificate is _always_ self-signed. Finally, write out both the certificate file as well as the private key file.
-
-
-```
-from cryptography.hazmat.primitives.asymmetric import rsa
-from cryptography.hazmat.primitives import hashes, serialization
-from cryptography import x509
-from cryptography.x509.oid import NameOID
-
-private_key = rsa.generate_private_key(
-public_exponent=65537,
-key_size=2048,
-backend=default_backend()
-)
-public_key = private_key.public_key()
-builder = x509.CertificateBuilder()
-builder = builder.subject_name(x509.Name([
-x509.NameAttribute(NameOID.COMMON_NAME, 'Simple Test CA'),
-]))
-builder = builder.issuer_name(x509.Name([
-x509.NameAttribute(NameOID.COMMON_NAME, 'Simple Test CA'),
-]))
-builder = builder.not_valid_before(yesterday)
-builder = builder.not_valid_after(tomorrow)
-builder = builder.serial_number(x509.random_serial_number())
-builder = builder.public_key(public_key)
-builder = builder.add_extension(
-x509.BasicConstraints(ca=True, path_length=None),
-critical=True)
-certificate = builder.sign(
-private_key=private_key, algorithm=hashes.SHA256(),
-backend=default_backend()
-)
-private_bytes = private_key.private_bytes(
-encoding=serialization.Encoding.PEM,
-format=serialization.PrivateFormat.TraditionalOpenSSL,
-encryption_algorithm=serialization.NoEncrption())
-public_bytes = certificate.public_bytes(
-encoding=serialization.Encoding.PEM)
-with open("ca.pem", "wb") as fout:
-fout.write(private_bytes + public_bytes)
-with open("ca.crt", "wb") as fout:
-fout.write(public_bytes)
-```
-
-In general, a real CA will expect a [certificate signing request][4] (CSR) to sign a certificate. However, when you are your own CA, you can make your own rules! Just go ahead and sign what you want.
-
-Continuing with the integration test example, you can create the private keys and sign the corresponding public keys right then. Notice **COMMON_NAME** needs to be the "server name" in the **https** URL. If you've configured name lookup, the needed server will respond on **service.test.local**.
-
-
-```
-service_private_key = rsa.generate_private_key(
-public_exponent=65537,
-key_size=2048,
-backend=default_backend()
-)
-service_public_key = service_private_key.public_key()
-builder = x509.CertificateBuilder()
-builder = builder.subject_name(x509.Name([
-x509.NameAttribute(NameOID.COMMON_NAME, 'service.test.local')
-]))
-builder = builder.not_valid_before(yesterday)
-builder = builder.not_valid_after(tomorrow)
-builder = builder.public_key(public_key)
-certificate = builder.sign(
-private_key=private_key, algorithm=hashes.SHA256(),
-backend=default_backend()
-)
-private_bytes = service_private_key.private_bytes(
-encoding=serialization.Encoding.PEM,
-format=serialization.PrivateFormat.TraditionalOpenSSL,
-encryption_algorithm=serialization.NoEncrption())
-public_bytes = certificate.public_bytes(
-encoding=serialization.Encoding.PEM)
-with open("service.pem", "wb") as fout:
-fout.write(private_bytes + public_bytes)
-```
-
-Now the **service.pem** file has a private key and a certificate that is "valid": it has been signed by your local CA. The file is in a format that can be given to, say, Nginx, HAProxy, or most other HTTPS servers.
-
-By applying this logic to testing scripts, it's easy to create servers that look like authentic HTTPS servers, as long as the client is configured to trust the right CA.
-
---------------------------------------------------------------------------------
-
-via: https://opensource.com/article/19/4/certificate-authority
-
-作者:[Moshe Zadka (Community Moderator)][a]
-选题:[lujun9972][b]
-译者:[译者ID](https://github.com/译者ID)
-校对:[校对者ID](https://github.com/校对者ID)
-
-本文由 [LCTT](https://github.com/LCTT/TranslateProject) 原创编译,[Linux中国](https://linux.cn/) 荣誉推出
-
-[a]: https://opensource.com/users/moshez/users/elenajon123
-[b]: https://github.com/lujun9972
-[1]: https://opensource.com/sites/default/files/styles/image-full-size/public/lead-images/rh_commun_4604_02_mech_connections_rhcz0.5x.png?itok=YPPU4dMj
-[2]: https://en.wikipedia.org/wiki/Transport_Layer_Security
-[3]: https://en.wikipedia.org/wiki/Certificate_authority
-[4]: https://en.wikipedia.org/wiki/Certificate_signing_request
diff --git a/sources/tech/20190411 How do you contribute to open source without code.md b/sources/tech/20190411 How do you contribute to open source without code.md
index 659fd9064e..40c2a89842 100644
--- a/sources/tech/20190411 How do you contribute to open source without code.md
+++ b/sources/tech/20190411 How do you contribute to open source without code.md
@@ -1,5 +1,5 @@
[#]: collector: (lujun9972)
-[#]: translator: ( )
+[#]: translator: (warmfrog)
[#]: reviewer: ( )
[#]: publisher: ( )
[#]: url: ( )
diff --git a/sources/tech/20190415 Kubernetes on Fedora IoT with k3s.md b/sources/tech/20190415 Kubernetes on Fedora IoT with k3s.md
deleted file mode 100644
index 5650e80aee..0000000000
--- a/sources/tech/20190415 Kubernetes on Fedora IoT with k3s.md
+++ /dev/null
@@ -1,211 +0,0 @@
-[#]: collector: (lujun9972)
-[#]: translator: ( )
-[#]: reviewer: ( )
-[#]: publisher: ( )
-[#]: url: ( )
-[#]: subject: (Kubernetes on Fedora IoT with k3s)
-[#]: via: (https://fedoramagazine.org/kubernetes-on-fedora-iot-with-k3s/)
-[#]: author: (Lennart Jern https://fedoramagazine.org/author/lennartj/)
-
-Kubernetes on Fedora IoT with k3s
-======
-
-![][1]
-
-Fedora IoT is an upcoming Fedora edition targeted at the Internet of Things. It was introduced last year on Fedora Magazine in the article [How to turn on an LED with Fedora IoT][2]. Since then, it has continued to improve together with Fedora Silverblue to provide an immutable base operating system aimed at container-focused workflows.
-
-Kubernetes is an immensely popular container orchestration system. It is perhaps most commonly used on powerful hardware handling huge workloads. However, it can also be used on lightweight devices such as the Raspberry Pi 3. Read on to find out how.
-
-### Why Kubernetes?
-
-While Kubernetes is all the rage in the cloud, it may not be immediately obvious to run it on a small single board computer. But there are certainly reasons for doing it. First of all it is a great way to learn and get familiar with Kubernetes without the need for expensive hardware. Second, because of its popularity, there are [tons of applications][3] that comes pre-packaged for running in Kubernetes clusters. Not to mention the large community to provide help if you ever get stuck.
-
-Last but not least, container orchestration may actually make things easier, even at the small scale in a home lab. This may not be apparent when tackling the the learning curve, but these skills will help when dealing with any cluster in the future. It doesn’t matter if it’s a single node Raspberry Pi cluster or a large scale machine learning farm.
-
-#### K3s – a lightweight Kubernetes
-
-A “normal” installation of Kubernetes (if such a thing can be said to exist) is a bit on the heavy side for IoT. The recommendation is a minimum of 2 GB RAM per machine! However, there are plenty of alternatives, and one of the newcomers is [k3s][4] – a lightweight Kubernetes distribution.
-
-K3s is quite special in that it has replaced etcd with SQLite for its key-value storage needs. Another thing to note is that k3s ships as a single binary instead of one per component. This diminishes the memory footprint and simplifies the installation. Thanks to the above, k3s should be able to run k3s with just 512 MB of RAM, perfect for a small single board computer!
-
-### What you will need
-
- 1. Fedora IoT in a virtual machine or on a physical device. See the excellent getting started guide [here][5]. One machine is enough but two will allow you to test adding more nodes to the cluster.
- 2. [Configure the firewall][6] to allow traffic on ports 6443 and 8472. Or simply disable it for this experiment by running “systemctl stop firewalld”.
-
-
-
-### Install k3s
-
-Installing k3s is very easy. Simply run the installation script:
-
-```
-curl -sfL https://get.k3s.io | sh -
-```
-
-This will download, install and start up k3s. After installation, get a list of nodes from the server by running the following command:
-
-```
-kubectl get nodes
-```
-
-Note that there are several options that can be passed to the installation script through environment variables. These can be found in the [documentation][7]. And of course, there is nothing stopping you from installing k3s manually by downloading the binary directly.
-
-While great for experimenting and learning, a single node cluster is not much of a cluster. Luckily, adding another node is no harder than setting up the first one. Just pass two environment variables to the installation script to make it find the first node and avoid running the server part of k3s
-
-```
-curl -sfL https://get.k3s.io | K3S_URL=https://example-url:6443 \
- K3S_TOKEN=XXX sh -
-```
-
-The example-url above should be replaced by the IP address or fully qualified domain name of the first node. On that node the token (represented by XXX) is found in the file /var/lib/rancher/k3s/server/node-token.
-
-### Deploy some containers
-
-Now that we have a Kubernetes cluster, what can we actually do with it? Let’s start by deploying a simple web server.
-
-```
-kubectl create deployment my-server --image nginx
-```
-
-This will create a [Deployment][8] named “my-server” from the container image “nginx” (defaulting to docker hub as registry and the latest tag). You can see the Pod created by running the following command.
-
-```
-kubectl get pods
-```
-
-In order to access the nginx server running in the pod, first expose the Deployment through a [Service][9]. The following command will create a Service with the same name as the deployment.
-
-```
-kubectl expose deployment my-server --port 80
-```
-
-The Service works as a kind of load balancer and DNS record for the Pods. For instance, when running a second Pod, we will be able to _curl_ the nginx server just by specifying _my-server_ (the name of the Service). See the example below for how to do this.
-
-```
-# Start a pod and run bash interactively in it
-kubectl run debug --generator=run-pod/v1 --image=fedora -it -- bash
-# Wait for the bash prompt to appear
-curl my-server
-# You should get the "Welcome to nginx!" page as output
-```
-
-### Ingress controller and external IP
-
-By default, a Service only get a ClusterIP (only accessible inside the cluster), but you can also request an external IP for the service by setting its type to [LoadBalancer][10]. However, not all applications require their own IP address. Instead, it is often possible to share one IP address among many services by routing requests based on the host header or path. You can accomplish this in Kubernetes with an [Ingress][11], and this is what we will do. Ingresses also provide additional features such as TLS encryption of the traffic without having to modify your application.
-
-Kubernetes needs an ingress controller to make the Ingress resources work and k3s includes [Traefik][12] for this purpose. It also includes a simple service load balancer that makes it possible to get an external IP for a Service in the cluster. The [documentation][13] describes the service like this:
-
-> k3s includes a basic service load balancer that uses available host ports. If you try to create a load balancer that listens on port 80, for example, it will try to find a free host in the cluster for port 80. If no port is available the load balancer will stay in Pending.
->
-> k3s README
-
-The ingress controller is already exposed with this load balancer service. You can find the IP address that it is using with the following command.
-
-```
-$ kubectl get svc --all-namespaces
-NAMESPACE NAME TYPE CLUSTER-IP EXTERNAL-IP PORT(S) AGE
- default kubernetes ClusterIP 10.43.0.1 443/TCP 33d
- default my-server ClusterIP 10.43.174.38 80/TCP 30m
- kube-system kube-dns ClusterIP 10.43.0.10 53/UDP,53/TCP,9153/TCP 33d
- kube-system traefik LoadBalancer 10.43.145.104 10.0.0.8 80:31596/TCP,443:31539/TCP 33d
-```
-
-Look for the Service named traefik. In the above example the IP we are interested in is 10.0.0.8.
-
-### Route incoming requests
-
-Let’s create an Ingress that routes requests to our web server based on the host header. This example uses [xip.io][14] to avoid having to set up DNS records. It works by including the IP adress as a subdomain, to use any subdomain of 10.0.0.8.xip.io to reach the IP 10.0.0.8. In other words, my-server.10.0.0.8.xip.io is used to reach the ingress controller in the cluster. You can try this right now (with your own IP instead of 10.0.0.8). Without an ingress in place you should reach the “default backend” which is just a page showing “404 page not found”.
-
-We can tell the ingress controller to route requests to our web server Service with the following Ingress.
-
-```
-apiVersion: extensions/v1beta1
-kind: Ingress
-metadata:
- name: my-server
-spec:
- rules:
- - host: my-server.10.0.0.8.xip.io
- http:
- paths:
- - path: /
- backend:
- serviceName: my-server
- servicePort: 80
-```
-
-Save the above snippet in a file named _my-ingress.yaml_ and add it to the cluster by running this command:
-
-```
-kubectl apply -f my-ingress.yaml
-```
-
-You should now be able to reach the default nginx welcoming page on the fully qualified domain name you chose. In my example this would be my-server.10.0.0.8.xip.io. The ingress controller is routing the requests based on the information in the Ingress. A request to my-server.10.0.0.8.xip.io will be routed to the Service and port defined as backend in the Ingress (my-server and 80 in this case).
-
-### What about IoT then?
-
-Imagine the following scenario. You have dozens of devices spread out around your home or farm. It is a heterogeneous collection of IoT devices with various hardware capabilities, sensors and actuators. Maybe some of them have cameras, weather or light sensors. Others may be hooked up to control the ventilation, lights, blinds or blink LEDs.
-
-In this scenario, you want to gather data from all the sensors, maybe process and analyze it before you finally use it to make decisions and control the actuators. In addition to this, you may want to visualize what’s going on by setting up a dashboard. So how can Kubernetes help us manage something like this? How can we make sure that Pods run on suitable devices?
-
-The simple answer is labels. You can label the nodes according to capabilities, like this:
-
-```
-kubectl label nodes =
-# Example
-kubectl label nodes node2 camera=available
-```
-
-Once they are labeled, it is easy to select suitable nodes for your workload with [nodeSelectors][15]. The final piece to the puzzle, if you want to run your Pods on _all_ suitable nodes is to use [DaemonSets][16] instead of Deployments. In other words, create one DaemonSet for each data collecting application that uses some unique sensor and use nodeSelectors to make sure they only run on nodes with the proper hardware.
-
-The service discovery feature that allows Pods to find each other simply by Service name makes it quite easy to handle these kinds of distributed systems. You don’t need to know or configure IP addresses or custom ports for the applications. Instead, they can easily find each other through named Services in the cluster.
-
-#### Utilize spare resources
-
-With the cluster up and running, collecting data and controlling your lights and climate control you may feel that you are finished. However, there are still plenty of compute resources in the cluster that could be used for other projects. This is where Kubernetes really shines.
-
-You shouldn’t have to worry about where exactly those resources are or calculate if there is enough memory to fit an extra application here or there. This is exactly what orchestration solves! You can easily deploy more applications in the cluster and let Kubernetes figure out where (or if) they will fit.
-
-Why not run your own [NextCloud][17] instance? Or maybe [gitea][18]? You could also set up a CI/CD pipeline for all those IoT containers. After all, why would you build and cross compile them on your main computer if you can do it natively in the cluster?
-
-The point here is that Kubernetes makes it easier to make use of the “hidden” resources that you often end up with otherwise. Kubernetes handles scheduling of Pods in the cluster based on available resources and fault tolerance so that you don’t have to. However, in order to help Kubernetes make reasonable decisions you should definitely add [resource requests][19] to your workloads.
-
-### Summary
-
-While Kubernetes, or container orchestration in general, may not usually be associated with IoT, it certainly makes a lot of sense to have an orchestrator when you are dealing with distributed systems. Not only does is allow you to handle a diverse and heterogeneous fleet of devices in a unified way, but it also simplifies communication between them. In addition, Kubernetes makes it easier to utilize spare resources.
-
-Container technology made it possible to build applications that could “run anywhere”. Now Kubernetes makes it easier to manage the “anywhere” part. And as an immutable base to build it all on, we have Fedora IoT.
-
---------------------------------------------------------------------------------
-
-via: https://fedoramagazine.org/kubernetes-on-fedora-iot-with-k3s/
-
-作者:[Lennart Jern][a]
-选题:[lujun9972][b]
-译者:[译者ID](https://github.com/译者ID)
-校对:[校对者ID](https://github.com/校对者ID)
-
-本文由 [LCTT](https://github.com/LCTT/TranslateProject) 原创编译,[Linux中国](https://linux.cn/) 荣誉推出
-
-[a]: https://fedoramagazine.org/author/lennartj/
-[b]: https://github.com/lujun9972
-[1]: https://fedoramagazine.org/wp-content/uploads/2019/04/k3s-1-816x345.png
-[2]: https://fedoramagazine.org/turnon-led-fedora-iot/
-[3]: https://hub.helm.sh/
-[4]: https://k3s.io
-[5]: https://docs.fedoraproject.org/en-US/iot/getting-started/
-[6]: https://github.com/rancher/k3s#open-ports--network-security
-[7]: https://github.com/rancher/k3s#systemd
-[8]: https://kubernetes.io/docs/concepts/workloads/controllers/deployment/
-[9]: https://kubernetes.io/docs/concepts/services-networking/service/
-[10]: https://kubernetes.io/docs/concepts/services-networking/service/#loadbalancer
-[11]: https://kubernetes.io/docs/concepts/services-networking/ingress/
-[12]: https://traefik.io/
-[13]: https://github.com/rancher/k3s/blob/master/README.md#service-load-balancer
-[14]: http://xip.io/
-[15]: https://kubernetes.io/docs/concepts/configuration/assign-pod-node/
-[16]: https://kubernetes.io/docs/concepts/workloads/controllers/daemonset/
-[17]: https://nextcloud.com/
-[18]: https://gitea.io/en-us/
-[19]: https://kubernetes.io/docs/concepts/configuration/manage-compute-resources-container/
diff --git a/sources/tech/20190416 Building a DNS-as-a-service with OpenStack Designate.md b/sources/tech/20190416 Building a DNS-as-a-service with OpenStack Designate.md
deleted file mode 100644
index 2dc628a49c..0000000000
--- a/sources/tech/20190416 Building a DNS-as-a-service with OpenStack Designate.md
+++ /dev/null
@@ -1,263 +0,0 @@
-[#]: collector: (lujun9972)
-[#]: translator: ( )
-[#]: reviewer: ( )
-[#]: publisher: ( )
-[#]: url: ( )
-[#]: subject: (Building a DNS-as-a-service with OpenStack Designate)
-[#]: via: (https://opensource.com/article/19/4/getting-started-openstack-designate)
-[#]: author: (Amjad Yaseen https://opensource.com/users/ayaseen)
-
-Building a DNS-as-a-service with OpenStack Designate
-======
-Learn how to install and configure Designate, a multi-tenant
-DNS-as-a-service (DNSaaS) for OpenStack.
-![Command line prompt][1]
-
-[Designate][2] is a multi-tenant DNS-as-a-service that includes a REST API for domain and record management, a framework for integration with [Neutron][3], and integration support for Bind9.
-
-You would want to consider a DNSaaS for the following:
-
- * A clean REST API for managing zones and records
- * Automatic records generated (with OpenStack integration)
- * Support for multiple authoritative name servers
- * Hosting multiple projects/organizations
-
-
-
-![Designate's architecture][4]
-
-This article explains how to manually install and configure the latest release of Designate service on CentOS or Red Hat Enterprise Linux 7 (RHEL 7), but you can use the same configuration on other distributions.
-
-### Install Designate on OpenStack
-
-I have Ansible roles for bind and Designate that demonstrate the setup in my [GitHub repository][5].
-
-This setup presumes bind service is external (even though you can install bind locally) on the OpenStack controller node.
-
- 1. Install Designate's packages and bind (on OpenStack controller): [code]`# yum install openstack-designate-* bind bind-utils -y`
-```
- 2. Create the Designate database and user: [code] MariaDB [(none)]> CREATE DATABASE designate CHARACTER SET utf8 COLLATE utf8_general_ci;
-
-MariaDB [(none)]> GRANT ALL PRIVILEGES ON designate.* TO \
-'designate'@'localhost' IDENTIFIED BY 'rhlab123';
-
-MariaDB [(none)]> GRANT ALL PRIVILEGES ON designate.* TO 'designate'@'%' \
-IDENTIFIED BY 'rhlab123';
-```
-
-
-
-
-Note: Bind packages must be installed on the controller side for Remote Name Daemon Control (RNDC) to function properly.
-
-### Configure bind (DNS server)
-
- 1. Generate RNDC files: [code] rndc-confgen -a -k designate -c /etc/rndc.key -r /dev/urandom
-
-cat < etcrndc.conf
-include "/etc/rndc.key";
-options {
-default-key "designate";
-default-server {{ DNS_SERVER_IP }};
-default-port 953;
-};
-EOF
-```
- 2. Add the following into **named.conf** : [code]`include "/etc/rndc.key"; controls { inet {{ DNS_SERVER_IP }} allow { localhost;{{ CONTROLLER_SERVER_IP }}; } keys { "designate"; }; };`[/code] In the **option** section, add: [code] options {
-...
-allow-new-zones yes;
-request-ixfr no;
-listen-on port 53 { any; };
-recursion no;
-allow-query { 127.0.0.1; {{ CONTROLLER_SERVER_IP }}; };
-}; [/code] Add the right permissions: [code] chown named:named /etc/rndc.key
-chown named:named /etc/rndc.conf
-chmod 600 /etc/rndc.key
-chown -v root:named /etc/named.conf
-chmod g+w /var/named
-
-# systemctl restart named
-# setsebool named_write_master_zones 1
-```
-
- 3. Push **rndc.key** and **rndc.conf** into the OpenStack controller: [code]`# scp -r /etc/rndc* {{ CONTROLLER_SERVER_IP }}:/etc/`
-```
-## Create OpenStack Designate service and endpoints
-
-Enter:
-```
-
-
-# openstack user create --domain default --password-prompt designate
-# openstack role add --project services --user designate admin
-# openstack service create --name designate --description "DNS" dns
-
-# openstack endpoint create --region RegionOne dns public http://{{ CONTROLLER_SERVER_IP }}:9001/
-# openstack endpoint create --region RegionOne dns internal http://{{ CONTROLLER_SERVER_IP }}:9001/
-# openstack endpoint create --region RegionOne dns admin http://{{ CONTROLLER_SERVER_IP }}:9001/
-
-```
-## Configure Designate service
-
- 1. Edit **/etc/designate/designate.conf** :
- * In the **[service:api]** section, configure **auth_strategy** : [code] [service:api]
-listen = 0.0.0.0:9001
-auth_strategy = keystone
-api_base_uri = http://{{ CONTROLLER_SERVER_IP }}:9001/
-enable_api_v2 = True
-enabled_extensions_v2 = quotas, reports
-```
- * In the **[keystone_authtoken]** section, configure the following options: [code] [keystone_authtoken]
-auth_type = password
-username = designate
-password = rhlab123
-project_name = service
-project_domain_name = Default
-user_domain_name = Default
-www_authenticate_uri = http://{{ CONTROLLER_SERVER_IP }}:5000/
-auth_url = http://{{ CONTROLLER_SERVER_IP }}:5000/
-```
- * In the **[service:worker]** section, enable the worker model: [code] enabled = True
-notify = True
-```
- * In the **[storage:sqlalchemy]** section, configure database access: [code] [storage:sqlalchemy]
-connection = mysql+pymysql://designate:rhlab123@{{ CONTROLLER_SERVER_IP }}/designate
-```
-* Populate the Designate database: [code]`# su -s /bin/sh -c "designate-manage database sync" designate`
-```
-
-
- 2. Create Designate's **pools.yaml** file (has target and bind details):
- * Edit **/etc/designate/pools.yaml** : [code] - name: default
-# The name is immutable. There will be no option to change the name after
-# creation and the only way will to change it will be to delete it
-# (and all zones associated with it) and recreate it.
-description: Default Pool
-
-attributes: {}
-
-# List out the NS records for zones hosted within this pool
-# This should be a record that is created outside of designate, that
-# points to the public IP of the controller node.
-ns_records:
-\- hostname: {{Controller_FQDN}}. # Thisis mDNS
-priority: 1
-
-# List out the nameservers for this pool. These are the actual BIND servers.
-# We use these to verify changes have propagated to all nameservers.
-nameservers:
-\- host: {{ DNS_SERVER_IP }}
-port: 53
-
-# List out the targets for this pool. For BIND there will be one
-# entry for each BIND server, as we have to run rndc command on each server
-targets:
-\- type: bind9
-description: BIND9 Server 1
-
-# List out the designate-mdns servers from which BIND servers should
-# request zone transfers (AXFRs) from.
-# This should be the IP of the controller node.
-# If you have multiple controllers you can add multiple masters
-# by running designate-mdns on them, and adding them here.
-masters:
-\- host: {{ CONTROLLER_SERVER_IP }}
-port: 5354
-
-# BIND Configuration options
-options:
-host: {{ DNS_SERVER_IP }}
-port: 53
-rndc_host: {{ DNS_SERVER_IP }}
-rndc_port: 953
-rndc_key_file: /etc/rndc.key
-rndc_config_file: /etc/rndc.conf
-```
-* Populate Designate's pools: [code]`su -s /bin/sh -c "designate-manage pool update" designate`
-```
-
-
-
- 3. Start Designate central and API services: [code]`systemctl enable --now designate-central designate-api`
-```
- 4. Verify Designate's services are up: [code] # openstack dns service list
-
-+--------------+--------+-------+--------------+
-| service_name | status | stats | capabilities |
-+--------------+--------+-------+--------------+
-| central | UP | - | - |
-| api | UP | - | - |
-| mdns | UP | - | - |
-| worker | UP | - | - |
-| producer | UP | - | - |
-+--------------+--------+-------+--------------+
-```
-
-
-
-
-### Configure OpenStack Neutron with external DNS
-
- 1. Configure iptables for Designate services: [code] # iptables -I INPUT -p tcp -m multiport --dports 9001 -m comment --comment "designate incoming" -j ACCEPT
-
-# iptables -I INPUT -p tcp -m multiport --dports 5354 -m comment --comment "Designate mdns incoming" -j ACCEPT
-
-# iptables -I INPUT -p tcp -m multiport --dports 53 -m comment --comment "bind incoming" -j ACCEPT
-
-
-# iptables -I INPUT -p udp -m multiport --dports 53 -m comment --comment "bind/powerdns incoming" -j ACCEPT
-
-# iptables -I INPUT -p tcp -m multiport --dports 953 -m comment --comment "rndc incoming - bind only" -j ACCEPT
-
-# service iptables save; service iptables restart
-# setsebool named_write_master_zones 1
-```
-2. Edit the **[default]** section of **/etc/neutron/neutron.conf** : [code]`external_dns_driver = designate`
-```
-
- 3. Add the **[designate]** section in **/_etc/_neutron/neutron.conf** : [code] [designate]
-url = http://{{ CONTROLLER_SERVER_IP }}:9001/v2 ## This end point of designate
-auth_type = password
-auth_url = http://{{ CONTROLLER_SERVER_IP }}:5000
-username = designate
-password = rhlab123
-project_name = services
-project_domain_name = Default
-user_domain_name = Default
-allow_reverse_dns_lookup = True
-ipv4_ptr_zone_prefix_size = 24
-ipv6_ptr_zone_prefix_size = 116
-```
- 4. Edit **dns_domain** in **neutron.conf** : [code] dns_domain = rhlab.dev.
-
-# systemctl restart neutron-*
-```
-
- 5. Add **dns** to the list of Modular Layer 2 (ML2) drivers in **/etc/neutron/plugins/ml2/ml2_conf.ini** : [code]`extension_drivers=port_security,qos,dns`
-```
-6. Add **zone** in Designate: [code]`# openstack zone create –email=admin@rhlab.dev rhlab.dev.`[/code] Add a new record in **zone rhlab.dev** : [code]`# openstack recordset create --record '192.168.1.230' --type A rhlab.dev. Test`
-```
-
-
-
-
-Designate should now be installed and configured.
-
---------------------------------------------------------------------------------
-
-via: https://opensource.com/article/19/4/getting-started-openstack-designate
-
-作者:[Amjad Yaseen][a]
-选题:[lujun9972][b]
-译者:[译者ID](https://github.com/译者ID)
-校对:[校对者ID](https://github.com/校对者ID)
-
-本文由 [LCTT](https://github.com/LCTT/TranslateProject) 原创编译,[Linux中国](https://linux.cn/) 荣誉推出
-
-[a]: https://opensource.com/users/ayaseen
-[b]: https://github.com/lujun9972
-[1]: https://opensource.com/sites/default/files/styles/image-full-size/public/lead-images/command_line_prompt.png?itok=wbGiJ_yg (Command line prompt)
-[2]: https://docs.openstack.org/designate/latest/
-[3]: /article/19/3/openstack-neutron
-[4]: https://opensource.com/sites/default/files/uploads/openstack_designate_architecture.png (Designate's architecture)
-[5]: https://github.com/ayaseen/designate
diff --git a/sources/tech/20190417 Inter-process communication in Linux- Sockets and signals.md b/sources/tech/20190417 Inter-process communication in Linux- Sockets and signals.md
deleted file mode 100644
index 40f64a2f5a..0000000000
--- a/sources/tech/20190417 Inter-process communication in Linux- Sockets and signals.md
+++ /dev/null
@@ -1,388 +0,0 @@
-[#]: collector: (lujun9972)
-[#]: translator: ( )
-[#]: reviewer: ( )
-[#]: publisher: ( )
-[#]: url: ( )
-[#]: subject: (Inter-process communication in Linux: Sockets and signals)
-[#]: via: (https://opensource.com/article/19/4/interprocess-communication-linux-networking)
-[#]: author: (Marty Kalin https://opensource.com/users/mkalindepauledu)
-
-Inter-process communication in Linux: Sockets and signals
-======
-
-Learn how processes synchronize with each other in Linux.
-
-
-
-This is the third and final article in a series about [interprocess communication][1] (IPC) in Linux. The [first article][2] focused on IPC through shared storage (files and memory segments), and the [second article][3] does the same for basic channels: pipes (named and unnamed) and message queues. This article moves from IPC at the high end (sockets) to IPC at the low end (signals). Code examples flesh out the details.
-
-### Sockets
-
-Just as pipes come in two flavors (named and unnamed), so do sockets. IPC sockets (aka Unix domain sockets) enable channel-based communication for processes on the same physical device (host), whereas network sockets enable this kind of IPC for processes that can run on different hosts, thereby bringing networking into play. Network sockets need support from an underlying protocol such as TCP (Transmission Control Protocol) or the lower-level UDP (User Datagram Protocol).
-
-By contrast, IPC sockets rely upon the local system kernel to support communication; in particular, IPC sockets communicate using a local file as a socket address. Despite these implementation differences, the IPC socket and network socket APIs are the same in the essentials. The forthcoming example covers network sockets, but the sample server and client programs can run on the same machine because the server uses network address localhost (127.0.0.1), the address for the local machine on the local machine.
-
-Sockets configured as streams (discussed below) are bidirectional, and control follows a client/server pattern: the client initiates the conversation by trying to connect to a server, which tries to accept the connection. If everything works, requests from the client and responses from the server then can flow through the channel until this is closed on either end, thereby breaking the connection.
-
-An iterative server, which is suited for development only, handles connected clients one at a time to completion: the first client is handled from start to finish, then the second, and so on. The downside is that the handling of a particular client may hang, which then starves all the clients waiting behind. A production-grade server would be concurrent, typically using some mix of multi-processing and multi-threading. For example, the Nginx web server on my desktop machine has a pool of four worker processes that can handle client requests concurrently. The following code example keeps the clutter to a minimum by using an iterative server; the focus thus remains on the basic API, not on concurrency.
-
-Finally, the socket API has evolved significantly over time as various POSIX refinements have emerged. The current sample code for server and client is deliberately simple but underscores the bidirectional aspect of a stream-based socket connection. Here's a summary of the flow of control, with the server started in a terminal then the client started in a separate terminal:
-
- * The server awaits client connections and, given a successful connection, reads the bytes from the client.
-
- * To underscore the two-way conversation, the server echoes back to the client the bytes received from the client. These bytes are ASCII character codes, which make up book titles.
-
- * The client writes book titles to the server process and then reads the same titles echoed from the server. Both the server and the client print the titles to the screen. Here is the server's output, essentially the same as the client's:
-
-```
-Listening on port 9876 for clients...
-War and Peace
-Pride and Prejudice
-The Sound and the Fury
-```
-
-
-
-
-#### Example 1. The socket server
-
-```
-#include
-#include
-#include
-#include
-#include
-#include
-#include
-#include
-#include "sock.h"
-
-void report(const char* msg, int terminate) {
- perror(msg);
- if (terminate) exit(-1); /* failure */
-}
-
-int main() {
- int fd = socket(AF_INET, /* network versus AF_LOCAL */
- SOCK_STREAM, /* reliable, bidirectional, arbitrary payload size */
- 0); /* system picks underlying protocol (TCP) */
- if (fd < 0) report("socket", 1); /* terminate */
-
- /* bind the server's local address in memory */
- struct sockaddr_in saddr;
- memset(&saddr, 0, sizeof(saddr)); /* clear the bytes */
- saddr.sin_family = AF_INET; /* versus AF_LOCAL */
- saddr.sin_addr.s_addr = htonl(INADDR_ANY); /* host-to-network endian */
- saddr.sin_port = htons(PortNumber); /* for listening */
-
- if (bind(fd, (struct sockaddr *) &saddr, sizeof(saddr)) < 0)
- report("bind", 1); /* terminate */
-
- /* listen to the socket */
- if (listen(fd, MaxConnects) < 0) /* listen for clients, up to MaxConnects */
- report("listen", 1); /* terminate */
-
- fprintf(stderr, "Listening on port %i for clients...\n", PortNumber);
- /* a server traditionally listens indefinitely */
- while (1) {
- struct sockaddr_in caddr; /* client address */
- int len = sizeof(caddr); /* address length could change */
-
- int client_fd = accept(fd, (struct sockaddr*) &caddr, &len); /* accept blocks */
- if (client_fd < 0) {
- report("accept", 0); /* don't terminate, though there's a problem */
- continue;
- }
-
- /* read from client */
- int i;
- for (i = 0; i < ConversationLen; i++) {
- char buffer[BuffSize + 1];
- memset(buffer, '\0', sizeof(buffer));
- int count = read(client_fd, buffer, sizeof(buffer));
- if (count > 0) {
- puts(buffer);
- write(client_fd, buffer, sizeof(buffer)); /* echo as confirmation */
- }
- }
- close(client_fd); /* break connection */
- } /* while(1) */
- return 0;
-}
-```
-
-The server program above performs the classic four-step to ready itself for client requests and then to accept individual requests. Each step is named after a system function that the server calls:
-
- 1. **socket(…)** : get a file descriptor for the socket connection
- 2. **bind(…)** : bind the socket to an address on the server's host
- 3. **listen(…)** : listen for client requests
- 4. **accept(…)** : accept a particular client request
-
-
-
-The **socket** call in full is:
-
-```
-int sockfd = socket(AF_INET, /* versus AF_LOCAL */
- SOCK_STREAM, /* reliable, bidirectional */
- 0); /* system picks protocol (TCP) */
-```
-
-The first argument specifies a network socket as opposed to an IPC socket. There are several options for the second argument, but **SOCK_STREAM** and **SOCK_DGRAM** (datagram) are likely the most used. A stream-based socket supports a reliable channel in which lost or altered messages are reported; the channel is bidirectional, and the payloads from one side to the other can be arbitrary in size. By contrast, a datagram-based socket is unreliable (best try), unidirectional, and requires fixed-sized payloads. The third argument to **socket** specifies the protocol. For the stream-based socket in play here, there is a single choice, which the zero represents: TCP. Because a successful call to **socket** returns the familiar file descriptor, a socket is written and read with the same syntax as, for example, a local file.
-
-The **bind** call is the most complicated, as it reflects various refinements in the socket API. The point of interest is that this call binds the socket to a memory address on the server machine. However, the **listen** call is straightforward:
-
-```
-if (listen(fd, MaxConnects) < 0)
-```
-
-The first argument is the socket's file descriptor and the second specifies how many client connections can be accommodated before the server issues a connection refused error on an attempted connection. ( **MaxConnects** is set to 8 in the header file sock.h.)
-
-The **accept** call defaults to a blocking wait: the server does nothing until a client attempts to connect and then proceeds. The **accept** function returns **-1** to indicate an error. If the call succeeds, it returns another file descriptor—for a read/write socket in contrast to the accepting socket referenced by the first argument in the **accept** call. The server uses the read/write socket to read requests from the client and to write responses back. The accepting socket is used only to accept client connections.
-
-By design, a server runs indefinitely. Accordingly, the server can be terminated with a **Ctrl+C** from the command line.
-
-#### Example 2. The socket client
-
-```
-#include
-#include
-#include
-#include
-#include
-#include
-#include
-#include
-#include
-#include
-#include "sock.h"
-
-const char* books[] = {"War and Peace",
- "Pride and Prejudice",
- "The Sound and the Fury"};
-
-void report(const char* msg, int terminate) {
- perror(msg);
- if (terminate) exit(-1); /* failure */
-}
-
-int main() {
- /* fd for the socket */
- int sockfd = socket(AF_INET, /* versus AF_LOCAL */
- SOCK_STREAM, /* reliable, bidirectional */
- 0); /* system picks protocol (TCP) */
- if (sockfd < 0) report("socket", 1); /* terminate */
-
- /* get the address of the host */
- struct hostent* hptr = gethostbyname(Host); /* localhost: 127.0.0.1 */
- if (!hptr) report("gethostbyname", 1); /* is hptr NULL? */
- if (hptr->h_addrtype != AF_INET) /* versus AF_LOCAL */
- report("bad address family", 1);
-
- /* connect to the server: configure server's address 1st */
- struct sockaddr_in saddr;
- memset(&saddr, 0, sizeof(saddr));
- saddr.sin_family = AF_INET;
- saddr.sin_addr.s_addr =
- ((struct in_addr*) hptr->h_addr_list[0])->s_addr;
- saddr.sin_port = htons(PortNumber); /* port number in big-endian */
-
- if (connect(sockfd, (struct sockaddr*) &saddr, sizeof(saddr)) < 0)
- report("connect", 1);
-
- /* Write some stuff and read the echoes. */
- puts("Connect to server, about to write some stuff...");
- int i;
- for (i = 0; i < ConversationLen; i++) {
- if (write(sockfd, books[i], strlen(books[i])) > 0) {
- /* get confirmation echoed from server and print */
- char buffer[BuffSize + 1];
- memset(buffer, '\0', sizeof(buffer));
- if (read(sockfd, buffer, sizeof(buffer)) > 0)
- puts(buffer);
- }
- }
- puts("Client done, about to exit...");
- close(sockfd); /* close the connection */
- return 0;
-}
-```
-
-The client program's setup code is similar to the server's. The principal difference between the two is that the client neither listens nor accepts, but instead connects:
-
-```
-if (connect(sockfd, (struct sockaddr*) &saddr, sizeof(saddr)) < 0)
-```
-
-The **connect** call might fail for several reasons; for example, the client has the wrong server address or too many clients are already connected to the server. If the **connect** operation succeeds, the client writes requests and then reads the echoed responses in a **for** loop. After the conversation, both the server and the client **close** the read/write socket, although a close operation on either side is sufficient to close the connection. The client exits thereafter but, as noted earlier, the server remains open for business.
-
-The socket example, with request messages echoed back to the client, hints at the possibilities of arbitrarily rich conversations between the server and the client. Perhaps this is the chief appeal of sockets. It is common on modern systems for client applications (e.g., a database client) to communicate with a server through a socket. As noted earlier, local IPC sockets and network sockets differ only in a few implementation details; in general, IPC sockets have lower overhead and better performance. The communication API is essentially the same for both.
-
-### Signals
-
-A signal interrupts an executing program and, in this sense, communicates with it. Most signals can be either ignored (blocked) or handled (through designated code), with **SIGSTOP** (pause) and **SIGKILL** (terminate immediately) as the two notable exceptions. Symbolic constants such as **SIGKILL** have integer values, in this case, 9.
-
-Signals can arise in user interaction. For example, a user hits **Ctrl+C** from the command line to terminate a program started from the command-line; **Ctrl+C** generates a **SIGTERM** signal. **SIGTERM** for terminate, unlike **SIGKILL** , can be either blocked or handled. One process also can signal another, thereby making signals an IPC mechanism.
-
-Consider how a multi-processing application such as the Nginx web server might be shut down gracefully from another process. The **kill** function:
-
-```
-int kill(pid_t pid, int signum); /* declaration */
-```
-
-can be used by one process to terminate another process or group of processes. If the first argument to function **kill** is greater than zero, this argument is treated as the pid (process ID) of the targeted process; if the argument is zero, the argument identifies the group of processes to which the signal sender belongs.
-
-The second argument to **kill** is either a standard signal number (e.g., **SIGTERM** or **SIGKILL** ) or 0, which makes the call to **signal** a query about whether the pid in the first argument is indeed valid. The graceful shutdown of a multi-processing application thus could be accomplished by sending a terminate signal—a call to the **kill** function with **SIGTERM** as the second argument—to the group of processes that make up the application. (The Nginx master process could terminate the worker processes with a call to **kill** and then exit itself.) The **kill** function, like so many library functions, houses power and flexibility in a simple invocation syntax.
-
-#### Example 3. The graceful shutdown of a multi-processing system
-
-```
-#include
-#include
-#include
-#include
-#include
-
-void graceful(int signum) {
- printf("\tChild confirming received signal: %i\n", signum);
- puts("\tChild about to terminate gracefully...");
- sleep(1);
- puts("\tChild terminating now...");
- _exit(0); /* fast-track notification of parent */
-}
-
-void set_handler() {
- struct sigaction current;
- sigemptyset(¤t.sa_mask); /* clear the signal set */
- current.sa_flags = 0; /* enables setting sa_handler, not sa_action */
- current.sa_handler = graceful; /* specify a handler */
- sigaction(SIGTERM, ¤t, NULL); /* register the handler */
-}
-
-void child_code() {
- set_handler();
-
- while (1) { /** loop until interrupted **/
- sleep(1);
- puts("\tChild just woke up, but going back to sleep.");
- }
-}
-
-void parent_code(pid_t cpid) {
- puts("Parent sleeping for a time...");
- sleep(5);
-
- /* Try to terminate child. */
- if (-1 == kill(cpid, SIGTERM)) {
- perror("kill");
- exit(-1);
- }
- wait(NULL); /** wait for child to terminate **/
- puts("My child terminated, about to exit myself...");
-}
-
-int main() {
- pid_t pid = fork();
- if (pid < 0) {
- perror("fork");
- return -1; /* error */
- }
- if (0 == pid)
- child_code();
- else
- parent_code(pid);
- return 0; /* normal */
-}
-```
-
-The shutdown program above simulates the graceful shutdown of a multi-processing system, in this case, a simple one consisting of a parent process and a single child process. The simulation works as follows:
-
- * The parent process tries to fork a child. If the fork succeeds, each process executes its own code: the child executes the function **child_code** , and the parent executes the function **parent_code**.
- * The child process goes into a potentially infinite loop in which the child sleeps for a second, prints a message, goes back to sleep, and so on. It is precisely a **SIGTERM** signal from the parent that causes the child to execute the signal-handling callback function **graceful**. The signal thus breaks the child process out of its loop and sets up the graceful termination of both the child and the parent. The child prints a message before terminating.
- * The parent process, after forking the child, sleeps for five seconds so that the child can execute for a while; of course, the child mostly sleeps in this simulation. The parent then calls the **kill** function with **SIGTERM** as the second argument, waits for the child to terminate, and then exits.
-
-
-
-Here is the output from a sample run:
-
-```
-% ./shutdown
-Parent sleeping for a time...
- Child just woke up, but going back to sleep.
- Child just woke up, but going back to sleep.
- Child just woke up, but going back to sleep.
- Child just woke up, but going back to sleep.
- Child confirming received signal: 15 ## SIGTERM is 15
- Child about to terminate gracefully...
- Child terminating now...
-My child terminated, about to exit myself...
-```
-
-For the signal handling, the example uses the **sigaction** library function (POSIX recommended) rather than the legacy **signal** function, which has portability issues. Here are the code segments of chief interest:
-
- * If the call to **fork** succeeds, the parent executes the **parent_code** function and the child executes the **child_code** function. The parent waits for five seconds before signaling the child:
-
-```
- puts("Parent sleeping for a time...");
-sleep(5);
-if (-1 == kill(cpid, SIGTERM)) {
-...sleepkillcpidSIGTERM...
-```
-
-If the **kill** call succeeds, the parent does a **wait** on the child's termination to prevent the child from becoming a permanent zombie; after the wait, the parent exits.
-
- * The **child_code** function first calls **set_handler** and then goes into its potentially infinite sleeping loop. Here is the **set_handler** function for review:
-
-```
- void set_handler() {
- struct sigaction current; /* current setup */
- sigemptyset(¤t.sa_mask); /* clear the signal set */
- current.sa_flags = 0; /* for setting sa_handler, not sa_action */
- current.sa_handler = graceful; /* specify a handler */
- sigaction(SIGTERM, ¤t, NULL); /* register the handler */
-}
-```
-
-The first three lines are preparation. The fourth statement sets the handler to the function **graceful** , which prints some messages before calling **_exit** to terminate. The fifth and last statement then registers the handler with the system through the call to **sigaction**. The first argument to **sigaction** is **SIGTERM** for terminate, the second is the current **sigaction** setup, and the last argument ( **NULL** in this case) can be used to save a previous **sigaction** setup, perhaps for later use.
-
-
-
-
-Using signals for IPC is indeed a minimalist approach, but a tried-and-true one at that. IPC through signals clearly belongs in the IPC toolbox.
-
-### Wrapping up this series
-
-These three articles on IPC have covered the following mechanisms through code examples:
-
- * Shared files
- * Shared memory (with semaphores)
- * Pipes (named and unnamed)
- * Message queues
- * Sockets
- * Signals
-
-
-
-Even today, when thread-centric languages such as Java, C#, and Go have become so popular, IPC remains appealing because concurrency through multi-processing has an obvious advantage over multi-threading: every process, by default, has its own address space, which rules out memory-based race conditions in multi-processing unless the IPC mechanism of shared memory is brought into play. (Shared memory must be locked in both multi-processing and multi-threading for safe concurrency.) Anyone who has written even an elementary multi-threading program with communication via shared variables knows how challenging it can be to write thread-safe yet clear, efficient code. Multi-processing with single-threaded processes remains a viable—indeed, quite appealing—way to take advantage of today's multi-processor machines without the inherent risk of memory-based race conditions.
-
-There is no simple answer, of course, to the question of which among the IPC mechanisms is the best. Each involves a trade-off typical in programming: simplicity versus functionality. Signals, for example, are a relatively simple IPC mechanism but do not support rich conversations among processes. If such a conversion is needed, then one of the other choices is more appropriate. Shared files with locking is reasonably straightforward, but shared files may not perform well enough if processes need to share massive data streams; pipes or even sockets, with more complicated APIs, might be a better choice. Let the problem at hand guide the choice.
-
-Although the sample code ([available on my website][4]) is all in C, other programming languages often provide thin wrappers around these IPC mechanisms. The code examples are short and simple enough, I hope, to encourage you to experiment.
-
---------------------------------------------------------------------------------
-
-via: https://opensource.com/article/19/4/interprocess-communication-linux-networking
-
-作者:[Marty Kalin][a]
-选题:[lujun9972][b]
-译者:[译者ID](https://github.com/译者ID)
-校对:[校对者ID](https://github.com/校对者ID)
-
-本文由 [LCTT](https://github.com/LCTT/TranslateProject) 原创编译,[Linux中国](https://linux.cn/) 荣誉推出
-
-[a]: https://opensource.com/users/mkalindepauledu
-[b]: https://github.com/lujun9972
-[1]: https://en.wikipedia.org/wiki/Inter-process_communication
-[2]: https://opensource.com/article/19/4/interprocess-communication-ipc-linux-part-1
-[3]: https://opensource.com/article/19/4/interprocess-communication-ipc-linux-part-2
-[4]: http://condor.depaul.edu/mkalin
diff --git a/sources/tech/20190419 Getting started with social media sentiment analysis in Python.md b/sources/tech/20190419 Getting started with social media sentiment analysis in Python.md
deleted file mode 100644
index 8d426a5af3..0000000000
--- a/sources/tech/20190419 Getting started with social media sentiment analysis in Python.md
+++ /dev/null
@@ -1,117 +0,0 @@
-[#]: collector: (lujun9972)
-[#]: translator: (MjSeven)
-[#]: reviewer: ( )
-[#]: publisher: ( )
-[#]: url: ( )
-[#]: subject: (Getting started with social media sentiment analysis in Python)
-[#]: via: (https://opensource.com/article/19/4/social-media-sentiment-analysis-python)
-[#]: author: (Michael McCune https://opensource.com/users/elmiko/users/jschlessman)
-
-Getting started with social media sentiment analysis in Python
-======
-Learn the basics of natural language processing and explore two useful
-Python packages.
-![Raspberry Pi and Python][1]
-
-Natural language processing (NLP) is a type of machine learning that addresses the correlation between spoken/written languages and computer-aided analysis of those languages. We experience numerous innovations from NLP in our daily lives, from writing assistance and suggestions to real-time speech translation and interpretation.
-
-This article examines one specific area of NLP: sentiment analysis, with an emphasis on determining the positive, negative, or neutral nature of the input language. This part will explain the background behind NLP and sentiment analysis and explore two open source Python packages. [Part 2][2] will demonstrate how to begin building your own scalable sentiment analysis services.
-
-When learning sentiment analysis, it is helpful to have an understanding of NLP in general. This article won't dig into the mathematical guts, rather our goal is to clarify key concepts in NLP that are crucial to incorporating these methods into your solutions in practical ways.
-
-### Natural language and text data
-
-A reasonable place to begin is defining: "What is natural language?" It is the means by which we, as humans, communicate with one another. The primary modalities for communication are verbal and text. We can take this a step further and focus solely on text communication; after all, living in an age of pervasive Siri, Alexa, etc., we know speech is a group of computations away from text.
-
-### Data landscape and challenges
-
-Limiting ourselves to textual data, what can we say about language and text? First, language, particularly English, is fraught with exceptions to rules, plurality of meanings, and contextual differences that can confuse even a human interpreter, let alone a computational one. In elementary school, we learn articles of speech and punctuation, and from speaking our native language, we acquire intuition about which words have less significance when searching for meaning. Examples of the latter would be articles of speech such as "a," "the," and "or," which in NLP are referred to as _stop words_ , since traditionally an NLP algorithm's search for meaning stops when reaching one of these words in a sequence.
-
-Since our goal is to automate the classification of text as belonging to a sentiment class, we need a way to work with text data in a computational fashion. Therefore, we must consider how to represent text data to a machine. As we know, the rules for utilizing and interpreting language are complicated, and the size and structure of input text can vary greatly. We'll need to transform the text data into numeric data, the form of choice for machines and math. This transformation falls under the area of _feature extraction_.
-
-Upon extracting numeric representations of input text data, one refinement might be, given an input body of text, to determine a set of quantitative statistics for the articles of speech listed above and perhaps classify documents based on them. For example, a glut of adverbs might make a copywriter bristle, or excessive use of stop words might be helpful in identifying term papers with content padding. Admittedly, this may not have much bearing on our goal of sentiment analysis.
-
-### Bag of words
-
-When you assess a text statement as positive or negative, what are some contextual clues you use to assess its polarity (i.e., whether the text has positive, negative, or neutral sentiment)? One way is connotative adjectives: something called "disgusting" is viewed as negative, but if the same thing were called "beautiful," you would judge it as positive. Colloquialisms, by definition, give a sense of familiarity and often positivity, whereas curse words could be a sign of hostility. Text data can also include emojis, which carry inherent sentiments.
-
-Understanding the polarity influence of individual words provides a basis for the [_bag-of-words_][3] (BoW) model of text. It considers a set of words or vocabulary and extracts measures about the presence of those words in the input text. The vocabulary is formed by considering text where the polarity is known, referred to as _labeled training data_. Features are extracted from this set of labeled data, then the relationships between the features are analyzed and labels are associated with the data.
-
-The name "bag of words" illustrates what it utilizes: namely, individual words without consideration of spatial locality or context. A vocabulary typically is built from all words appearing in the training set, which tends to be pruned afterward. Stop words, if not cleaned prior to training, are removed due to their high frequency and low contextual utility. Rarely used words can also be removed, given the lack of information they provide for general input cases.
-
-It is important to note, however, that you can (and should) go further and consider the appearance of words beyond their use in an individual instance of training data, or what is called [_term frequency_][4] (TF). You should also consider the counts of a word through all instances of input data; typically the infrequency of words among all documents is notable, which is called the [_inverse document frequency_][5] (IDF). These metrics are bound to be mentioned in other articles and software packages on this subject, so having an awareness of them can only help.
-
-BoW is useful in a number of document classification applications; however, in the case of sentiment analysis, things can be gamed when the lack of contextual awareness is leveraged. Consider the following sentences:
-
- * We are not enjoying this war.
- * I loathe rainy days, good thing today is sunny.
- * This is not a matter of life and death.
-
-
-
-The sentiment of these phrases is questionable for human interpreters, and by strictly focusing on instances of individual vocabulary words, it's difficult for a machine interpreter as well.
-
-Groupings of words, called _n-grams_ , can also be considered in NLP. A bigram considers groups of two adjacent words instead of (or in addition to) the single BoW. This should alleviate situations such as "not enjoying" above, but it will remain open to gaming due to its loss of contextual awareness. Furthermore, in the second sentence above, the sentiment context of the second half of the sentence could be perceived as negating the first half. Thus, spatial locality of contextual clues also can be lost in this approach. Complicating matters from a pragmatic perspective is the sparsity of features extracted from a given input text. For a thorough and large vocabulary, a count is maintained for each word, which can be considered an integer vector. Most documents will have a large number of zero counts in their vectors, which adds unnecessary space and time complexity to operations. While a number of clever approaches have been proposed for reducing this complexity, it remains an issue.
-
-### Word embeddings
-
-Word embeddings are a distributed representation that allows words with a similar meaning to have a similar representation. This is based on using a real-valued vector to represent words in connection with the company they keep, as it were. The focus is on the manner that words are used, as opposed to simply their existence. In addition, a huge pragmatic benefit of word embeddings is their focus on dense vectors; by moving away from a word-counting model with commensurate amounts of zero-valued vector elements, word embeddings provide a more efficient computational paradigm with respect to both time and storage.
-
-Following are two prominent word embedding approaches.
-
-#### Word2vec
-
-The first of these word embeddings, [Word2vec][6], was developed at Google. You'll probably see this embedding method mentioned as you go deeper in your study of NLP and sentiment analysis. It utilizes either a _continuous bag of words_ (CBOW) or a _continuous skip-gram_ model. In CBOW, a word's context is learned during training based on the words surrounding it. Continuous skip-gram learns the words that tend to surround a given word. Although this is more than what you'll probably need to tackle, if you're ever faced with having to generate your own word embeddings, the author of Word2vec advocates the CBOW method for speed and assessment of frequent words, while the skip-gram approach is better suited for embeddings where rare words are more important.
-
-#### GloVe
-
-The second word embedding, [_Global Vectors for Word Representation_][7] (GloVe), was developed at Stanford. It's an extension to the Word2vec method that attempts to combine the information gained through classical global text statistical feature extraction with the local contextual information determined by Word2vec. In practice, GloVe has outperformed Word2vec for some applications, while falling short of Word2vec's performance in others. Ultimately, the targeted dataset for your word embedding will dictate which method is optimal; as such, it's good to know the existence and high-level mechanics of each, as you'll likely come across them.
-
-#### Creating and using word embeddings
-
-Finally, it's useful to know how to obtain word embeddings; in part 2, you'll see that we are standing on the shoulders of giants, as it were, by leveraging the substantial work of others in the community. This is one method of acquiring a word embedding: namely, using an existing trained and proven model. Indeed, myriad models exist for English and other languages, and it's possible that one does what your application needs out of the box!
-
-If not, the opposite end of the spectrum in terms of development effort is training your own standalone model without consideration of your application. In essence, you would acquire substantial amounts of labeled training data and likely use one of the approaches above to train a model. Even then, you are still only at the point of acquiring understanding of your input-text data; you then need to develop a model specific for your application (e.g., analyzing sentiment valence in software version-control messages) which, in turn, requires its own time and effort.
-
-You also could train a word embedding on data specific to your application; while this could reduce time and effort, the word embedding would be application-specific, which would reduce reusability.
-
-### Available tooling options
-
-You may wonder how you'll ever get to a point of having a solution for your problem, given the intensive time and computing power needed. Indeed, the complexities of developing solid models can be daunting; however, there is good news: there are already many proven models, tools, and software libraries available that may provide much of what you need. We will focus on [Python][8], which conveniently has a plethora of tooling in place for these applications.
-
-#### SpaCy
-
-[SpaCy][9] provides a number of language models for parsing input text data and extracting features. It is highly optimized and touted as the fastest library of its kind. Best of all, it's open source! SpaCy performs tokenization, parts-of-speech classification, and dependency annotation. It contains word embedding models for performing this and other feature extraction operations for over 46 languages. You will see how it can be used for text analysis and feature extraction in the second article in this series.
-
-#### vaderSentiment
-
-The [vaderSentiment][10] package provides a measure of positive, negative, and neutral sentiment. As the [original paper][11]'s title ("VADER: A Parsimonious Rule-based Model for Sentiment Analysis of Social Media Text") indicates, the models were developed and tuned specifically for social media text data. VADER was trained on a thorough set of human-labeled data, which included common emoticons, UTF-8 encoded emojis, and colloquial terms and abbreviations (e.g., meh, lol, sux).
-
-For given input text data, vaderSentiment returns a 3-tuple of polarity score percentages. It also provides a single scoring measure, referred to as _vaderSentiment's compound metric_. This is a real-valued measurement within the range **[-1, 1]** wherein sentiment is considered positive for values greater than **0.05** , negative for values less than **-0.05** , and neutral otherwise.
-
-In [part 2][2], you will learn how to use these tools to add sentiment analysis capabilities to your designs.
-
---------------------------------------------------------------------------------
-
-via: https://opensource.com/article/19/4/social-media-sentiment-analysis-python
-
-作者:[Michael McCune ][a]
-选题:[lujun9972][b]
-译者:[译者ID](https://github.com/译者ID)
-校对:[校对者ID](https://github.com/校对者ID)
-
-本文由 [LCTT](https://github.com/LCTT/TranslateProject) 原创编译,[Linux中国](https://linux.cn/) 荣誉推出
-
-[a]: https://opensource.com/users/elmiko/users/jschlessman
-[b]: https://github.com/lujun9972
-[1]: https://opensource.com/sites/default/files/styles/image-full-size/public/lead-images/getting_started_with_python.png?itok=MFEKm3gl (Raspberry Pi and Python)
-[2]: https://opensource.com/article/19/4/social-media-sentiment-analysis-python-part-2
-[3]: https://en.wikipedia.org/wiki/Bag-of-words_model
-[4]: https://en.wikipedia.org/wiki/Tf%E2%80%93idf#Term_frequency
-[5]: https://en.wikipedia.org/wiki/Tf%E2%80%93idf#Inverse_document_frequency
-[6]: https://en.wikipedia.org/wiki/Word2vec
-[7]: https://en.wikipedia.org/wiki/GloVe_(machine_learning)
-[8]: https://www.python.org/
-[9]: https://pypi.org/project/spacy/
-[10]: https://pypi.org/project/vaderSentiment/
-[11]: http://comp.social.gatech.edu/papers/icwsm14.vader.hutto.pdf
diff --git a/sources/tech/20190422 2 new apps for music tweakers on Fedora Workstation.md b/sources/tech/20190422 2 new apps for music tweakers on Fedora Workstation.md
deleted file mode 100644
index 8da9ca4795..0000000000
--- a/sources/tech/20190422 2 new apps for music tweakers on Fedora Workstation.md
+++ /dev/null
@@ -1,148 +0,0 @@
-[#]: collector: (lujun9972)
-[#]: translator: ( )
-[#]: reviewer: ( )
-[#]: publisher: ( )
-[#]: url: ( )
-[#]: subject: (2 new apps for music tweakers on Fedora Workstation)
-[#]: via: (https://fedoramagazine.org/2-new-apps-for-music-tweakers-on-fedora-workstation/)
-[#]: author: (Justin W. Flory https://fedoramagazine.org/author/jflory7/)
-
-2 new apps for music tweakers on Fedora Workstation
-======
-
-![][1]
-
-Linux operating systems are great for making unique customizations and tweaks to make your computer work better for you. For example, the [i3 window manager][2] encourages users to think about the different components and pieces that make up the modern Linux desktop.
-
-Fedora has two new packages of interest for music tweakers: **mpris-scrobbler** and **playerctl**. _mpris-scrobbler_ [tracks your music listening history][3] on a music-tracking service like Last.fm and/or ListenBrainz. _playerctl_ is a command-line [music player controller][4].
-
-## _mpris-scrobbler_ records your music listening trends
-
-_mpris-scrobbler_ is a CLI application to submit play history of your music to a service like [Last.fm][5], [Libre.fm][6], or [ListenBrainz][7]. It listens on the [MPRIS D-Bus interface][8] to detect what’s playing. It connects with several different music clients like spotify-client, [vlc][9], audacious, bmp, [cmus][10], and others.
-
-![Last.fm last week in music report. Generated from user-submitted listening history.][11]
-
-### Install and configure _mpris-scrobbler_
-
-_mpris-scrobbler_ is available for Fedora 28 or later, as well as the EPEL 7 repositories. Run the following command in a terminal to install it:
-
-```
-sudo dnf install mpris-scrobbler
-```
-
-Once it is installed, use _systemctl_ to start and enable the service. The following command starts _mpris-scrobbler_ and always starts it after a system reboot:
-
-```
-systemctl --user enable --now mpris-scrobbler.service
-```
-
-### Submit plays to ListenBrainz
-
-This article explains how to link _mpris-scrobbler_ with a ListenBrainz account. To use Last.fm or Libre.fm, see the [upstream documentation][12].
-
-To submit plays to a ListenBrainz server, you need a ListenBrainz API token. If you have an account, get the token from your [profile settings page][13]. When you have a token, run this command to authenticate with your ListenBrainz API token:
-
-```
-$ mpris-scrobbler-signon token listenbrainz
-Token for listenbrainz.org:
-```
-
-Finally, test it by playing a song in your preferred music client on Fedora. The songs you play appear on your ListenBrainz profile.
-
-![Basic statistics and play history from a user profile on ListenBrainz. The current track is playing on a Fedora Workstation laptop with mpris-scrobbler.][14]
-
-## _playerctl_ controls your music playback
-
-_playerctl_ is a CLI tool to control any music player implementing the MPRIS D-Bus interface. You can easily bind it to keyboard shortcuts or media hotkeys. Here’s how to install it, use it in the command line, and create key bindings for the i3 window manager.
-
-### Install and use _playerctl_
-
-_playerctl_ is available for Fedora 28 or later. Run the following command in a terminal to install it:
-
-```
-sudo dnf install playerctl
-```
-
-Now that it’s installed, you can use it right away. Open your preferred music player on Fedora. Next, try the following commands to control playback from a terminal.
-
-To play or pause the currently playing track:
-
-```
-playerctl play-pause
-```
-
-If you want to skip to the next track:
-
-```
-playerctl next
-```
-
-For a list of all running players:
-
-```
-playerctl -l
-```
-
-To play or pause what’s currently playing, only on the spotify-client app:
-
-```
-playerctl -p spotify play-pause
-```
-
-### Create _playerctl_ key bindings in i3wm
-
-Do you use a window manager like the [i3 window manager?][2] Try using _playerctl_ for key bindings. You can bind different commands to different key shortcuts, like the play/pause buttons on your keyboard. Look at the following [i3wm config excerpt][15] to see how:
-
-```
-# Media player controls
-bindsym XF86AudioPlay exec "playerctl play-pause"
-bindsym XF86AudioNext exec "playerctl next"
-bindsym XF86AudioPrev exec "playerctl previous"
-```
-
-## Try it out with your favorite music players
-
-Need to know more about customizing the music listening experience on Fedora? The Fedora Magazine has you covered. Check out these five cool music players on Fedora:
-
-> [5 cool music player apps][16]
-
-Bring order to your music library chaos by sorting and organizing it with MusicBrainz Picard:
-
-> [Picard brings order to your music library][17]
-
-* * *
-
-_Photo by _[ _Frank Septillion_][18]_ on _[_Unsplash_][19]_._
-
---------------------------------------------------------------------------------
-
-via: https://fedoramagazine.org/2-new-apps-for-music-tweakers-on-fedora-workstation/
-
-作者:[Justin W. Flory][a]
-选题:[lujun9972][b]
-译者:[译者ID](https://github.com/译者ID)
-校对:[校对者ID](https://github.com/校对者ID)
-
-本文由 [LCTT](https://github.com/LCTT/TranslateProject) 原创编译,[Linux中国](https://linux.cn/) 荣誉推出
-
-[a]: https://fedoramagazine.org/author/jflory7/
-[b]: https://github.com/lujun9972
-[1]: https://fedoramagazine.org/wp-content/uploads/2019/04/2-music-tweak-apps-816x345.jpg
-[2]: https://fedoramagazine.org/getting-started-i3-window-manager/
-[3]: https://github.com/mariusor/mpris-scrobbler
-[4]: https://github.com/acrisci/playerctl
-[5]: https://www.last.fm/
-[6]: https://libre.fm/
-[7]: https://listenbrainz.org/
-[8]: https://specifications.freedesktop.org/mpris-spec/latest/
-[9]: https://www.videolan.org/vlc/
-[10]: https://cmus.github.io/
-[11]: https://fedoramagazine.org/wp-content/uploads/2019/02/Screenshot_2019-04-13-jflory7%E2%80%99s-week-in-music2-1024x500.png
-[12]: https://github.com/mariusor/mpris-scrobbler#authenticate-to-the-service
-[13]: https://listenbrainz.org/profile/
-[14]: https://fedoramagazine.org/wp-content/uploads/2019/04/Screenshot_2019-04-13-User-jflory-ListenBrainz.png
-[15]: https://github.com/jwflory/swiss-army/blob/ba6ac0c71855e33e3caa1ee1fe51c05d2df0529d/roles/apps/i3wm/files/config#L207-L210
-[16]: https://fedoramagazine.org/5-cool-music-player-apps/
-[17]: https://fedoramagazine.org/picard-brings-order-music-library/
-[18]: https://unsplash.com/photos/Qrspubmx6kE?utm_source=unsplash&utm_medium=referral&utm_content=creditCopyText
-[19]: https://unsplash.com/search/photos/music?utm_source=unsplash&utm_medium=referral&utm_content=creditCopyText
diff --git a/sources/tech/20190422 4 open source apps for plant-based diets.md b/sources/tech/20190422 4 open source apps for plant-based diets.md
deleted file mode 100644
index 6d77b66eea..0000000000
--- a/sources/tech/20190422 4 open source apps for plant-based diets.md
+++ /dev/null
@@ -1,68 +0,0 @@
-[#]: collector: (lujun9972)
-[#]: translator: ( )
-[#]: reviewer: ( )
-[#]: publisher: ( )
-[#]: url: ( )
-[#]: subject: (4 open source apps for plant-based diets)
-[#]: via: (https://opensource.com/article/19/4/apps-plant-based-diets)
-[#]: author: (Joshua Allen Holm https://opensource.com/users/holmja)
-
-4 open source apps for plant-based diets
-======
-These apps make it easier for vegetarians and vegans—and omnivores who
-want to eat healthier—to find food they can eat.
-![][1]
-
-Reducing your consumption of meat, dairy, and processed foods is better for the planet and better for your health. Changing your diet can be difficult, but several open source Android applications can help you switch to a more plant-based diet. Whether you are taking part in [Meatless Monday][2], following Mark Bittman's [Vegan Before 6:00][3] guidelines, or switching entirely to a [whole-food, plant-based diet][4], these apps can aid you on your journey by helping you figure out what to eat, discover vegan- and vegetarian-friendly restaurants, and easily communicate your dietary preferences to others. All of these apps are open source and available from the [F-Droid repository][5].
-
-### Daily Dozen
-
-![Daily Dozen app][6]
-
-The [Daily Dozen][7] app provides a checklist of items that Michael Greger, MD, FACLM, recommends as part of a healthy diet and lifestyle. Dr. Greger recommends consuming a whole-food, plant-based diet consisting of diverse foods and supported by daily exercise. This app lets you keep track of how many servings of each type of food you have eaten, how many servings of water (or other approved beverage, such as tea) you drank, and if you exercised each day. Each category of food provides serving sizes and lists of foods that fall under that category; for example, the Cruciferous Vegetable category includes bok choy, broccoli, brussels sprouts, and many other suggestions.
-
-### Food Restrictions
-
-![Food Restrictions app][8]
-
-[Food Restrictions][9] is a simple app that can help you communicate your dietary restrictions to others, even if those people do not speak your language. Users can enter their food restrictions for seven different categories: chicken, beef, pork, fish, cheese, milk, and peppers. There is an "I don't eat" and an "I'm allergic" option for each of those categories. The "don't eat" option shows the icon with a red X over it. The "allergic" option displays the X and a small skull icon. The same information can be displayed using text instead of icons, but the text is only available in English and Portuguese. There is also an option for displaying a text message that says the user is vegetarian or vegan, which summarizes those dietary restrictions more succinctly and more accurately than the pick-and-choose options. The vegan text clearly mentions not eating eggs and honey, which are not options in the pick-and-choose method. However, just like the text version of the pick-and-choose option, these sentences are only available in English and Portuguese.
-
-### OpenFoodFacts
-
-![Open Food Facts app][10]
-
-Avoiding unwanted ingredients when buying groceries can be frustrating, but [OpenFoodFacts][11] can help make the process easier. This app lets you scan the barcodes on products to get a report about the ingredients in a product and how healthy the product is. A product can still be very unhealthy even if it meets the criteria to be a vegan product. Having both the ingredients list and the nutrition facts lets you make informed choices when shopping. The only drawback for this app is that the data is user contributed, so not every product is available, but you can contribute new items, if you want to give back to the project.
-
-### OpenVegeMap
-
-![OpenVegeMap app][12]
-
-Find vegan and vegetarian restaurants in your neighborhood with the [OpenVegeMap][13] app. This app lets you search by either using your phone's current location or by entering an address. Restaurants are classified as Vegan only, Vegan friendly, Vegetarian only, Vegetarian friendly, Non-vegetarian, and Unknown. The app uses data from [OpenStreetMap][14] and user-contributed information about the restaurants, so be sure to double-check to make sure the information provided is up-to-date and accurate.
-
---------------------------------------------------------------------------------
-
-via: https://opensource.com/article/19/4/apps-plant-based-diets
-
-作者:[Joshua Allen Holm ][a]
-选题:[lujun9972][b]
-译者:[译者ID](https://github.com/译者ID)
-校对:[校对者ID](https://github.com/校对者ID)
-
-本文由 [LCTT](https://github.com/LCTT/TranslateProject) 原创编译,[Linux中国](https://linux.cn/) 荣誉推出
-
-[a]: https://opensource.com/users/holmja
-[b]: https://github.com/lujun9972
-[1]: https://opensource.com/sites/default/files/styles/image-full-size/public/lead-images/rh_003588_01_rd3os.combacktoschoolserieshe_rh_041x_0.png?itok=tfg6_I78
-[2]: https://www.meatlessmonday.com/
-[3]: https://www.amazon.com/dp/0385344740/
-[4]: https://nutritionstudies.org/whole-food-plant-based-diet-guide/
-[5]: https://f-droid.org/
-[6]: https://opensource.com/sites/default/files/uploads/daily_dozen.png (Daily Dozen app)
-[7]: https://f-droid.org/en/packages/org.nutritionfacts.dailydozen/
-[8]: https://opensource.com/sites/default/files/uploads/food_restrictions.png (Food Restrictions app)
-[9]: https://f-droid.org/en/packages/br.com.frs.foodrestrictions/
-[10]: https://opensource.com/sites/default/files/uploads/openfoodfacts.png (Open Food Facts app)
-[11]: https://f-droid.org/en/packages/openfoodfacts.github.scrachx.openfood/
-[12]: https://opensource.com/sites/default/files/uploads/openvegmap.png (OpenVegeMap app)
-[13]: https://f-droid.org/en/packages/pro.rudloff.openvegemap/
-[14]: https://www.openstreetmap.org/
diff --git a/sources/tech/20190425 Debian has a New Project Leader.md b/sources/tech/20190425 Debian has a New Project Leader.md
new file mode 100644
index 0000000000..00f114b907
--- /dev/null
+++ b/sources/tech/20190425 Debian has a New Project Leader.md
@@ -0,0 +1,106 @@
+[#]: collector: (lujun9972)
+[#]: translator: ( )
+[#]: reviewer: ( )
+[#]: publisher: ( )
+[#]: url: ( )
+[#]: subject: (Debian has a New Project Leader)
+[#]: via: (https://itsfoss.com/debian-project-leader-election/)
+[#]: author: (Shirish https://itsfoss.com/author/shirish/)
+
+Debian has a New Project Leader
+======
+
+Like each year, the Debian Secretary announced a call for nominations for the post of Debian Project Leader (commonly known as DPL) in early March. Soon 5 candidates shared their nomination. One of the DPL candidates backed out due to personal reasons and we had [four candidates][1] as can be seen in the Nomination section of the Vote page.
+
+### Sam Hartman, the new Debian Project Leader
+
+![][2]
+
+While I will not go much into details as Sam already outlined his position on his [platform][3], it is good to see that most Debian developers recognize that it’s no longer just the technical excellence which need to be looked at. I do hope he is able to create more teams which would leave some more time in DPL’s hands and less stress going forward.
+
+As he has shared, he would be looking into also helping the other DPL candidates, all of which presented initiatives to make Debian better.
+
+Apart from this, there had been some excellent suggestions, for example modernizing debian-installer, making lists.debian.org have a [Mailman 3][4] instance, modernizing Debian packaging and many more.
+
+While probably a year is too short a time for any of the deliverables that Debian people are thinking, some sort of push or start should enable Debian to reach greater heights than today.
+
+### A brief history of DPL elections
+
+In the beginning, Debian was similar to many distributions which have a [BDFL][5], although from the very start Debian had a sort of rolling leadership. While I wouldn’t go through the whole history, from October 1998 there was an idea [germinated][6] to have a Debian Constitution.
+
+After quite a bit of discussion between Debian users, contributors, developers etc. [Debian 1.0 Constitution][7] was released on December 2nd, 1998. One of the big changes was that it formalised the selection of Debian Project Leader via elections.
+
+From 1998 till 2019 13 Debian project leaders have been elected till date with Sam Hartman being the latest (2019).
+
+Before Sam, [Chris Lamb][8] was DPL in 2017 and again stood up for re-election in 2018. One of the biggest changes in Chris’s tenure was having more impetus to outreach than ever before. This made it possible to have many more mini-debconfs all around the world and thus increasing more number of Debian users and potential Debian Developers.
+
+[][9]
+
+Suggested read SemiCode OS: A Linux Distribution For Programmers And Web Developers
+
+### Duties and Responsibilities of the Debian Project Leader
+
+![][10]
+
+Debian Project Leader (DPL) is a non-monetary position which means that the DPL doesn’t get a salary or any monetary benefits in the traditional sense but it’s a prestigious position.
+
+Curious what what a DPL does? Here are some of the duties, responsibilities, prestige and perks associated with this position.
+
+#### Travelling
+
+As the DPL is the public face of the project, she/he is supposed to travel to many places in the world to share about Debian. While the travel may be a perk, it is and could be discounted by being not paid for the time spent articulating Debian’s position in various free software and other communities. Also travel, language, politics of free software are also some of the stress points that any DPL would have to go through.
+
+#### Communication
+
+A DPL is expected to have excellent verbal and non-verbal communication skills as she/he is the expected to share Debian’s vision of computing to technical and non-technical people. As she/he is also expected to weigh in many a sensitive matter, the Project Leader has to make choices about which communications should be made public and which should be private.
+
+#### Budgeting
+
+Quite a bit of the time the Debian Project Leader has to look into the finances along with the Secretary and take a call at various initiatives mooted by the larger community. The Project Leader has to ask and then make informed decisions on the same.
+
+#### Delegation
+
+One of the important tasks of the DPL is to delegate different tasks to suitable people. Some sensitive delegations include ftp-master, ftp-assistant, list-managers, debian-mirror, debian-infrastructure and so on.
+
+#### Influence
+
+Last but not the least, just like any other election, the people who contest for DPL have a platform where they share their ideas about where they would like to see the Debian project heading and how they would go about doing it.
+
+This is by no means an exhaustive list. I would suggest to read Lucas Nussbaum’s [mail][11] in which he outlines some more responsibilities as a Debian Project Leader.
+
+[][12]
+
+Suggested read Lightweight Linux Distribution Bodhi Linux 5.0 Released
+
+**In the end…**
+
+I wish Sam Hartman all the luck. I look forward to see how Debian grows under his leadership.
+
+I also hope that you learned a few non-technical thing around Debian. If you are an [ardent Debian user][13], stuff like this make you feel more involved with Debian project. What do you say?
+
+--------------------------------------------------------------------------------
+
+via: https://itsfoss.com/debian-project-leader-election/
+
+作者:[Shirish][a]
+选题:[lujun9972][b]
+译者:[译者ID](https://github.com/译者ID)
+校对:[校对者ID](https://github.com/校对者ID)
+
+本文由 [LCTT](https://github.com/LCTT/TranslateProject) 原创编译,[Linux中国](https://linux.cn/) 荣誉推出
+
+[a]: https://itsfoss.com/author/shirish/
+[b]: https://github.com/lujun9972
+[1]: https://www.debian.org/vote/2019/vote_001
+[2]: https://itsfoss.com/wp-content/uploads/2019/04/Debian-Project-Leader-election-800x450.png
+[3]: https://www.debian.org/vote/2019/platforms/hartmans
+[4]: http://docs.mailman3.org/en/latest/
+[5]: https://en.wikipedia.org/wiki/Benevolent_dictator_for_life
+[6]: https://lists.debian.org/debian-devel/1998/09/msg00506.html
+[7]: https://www.debian.org/devel/constitution.1.0
+[8]: https://www.debian.org/vote/2017/platforms/lamby
+[9]: https://itsfoss.com/semicode-os-linux/
+[10]: https://itsfoss.com/wp-content/uploads/2019/04/leadership-800x450.jpg
+[11]: https://lists.debian.org/debian-vote/2019/03/msg00023.html
+[12]: https://itsfoss.com/bodhi-linux-5/
+[13]: https://itsfoss.com/reasons-why-i-love-debian/
diff --git a/sources/tech/20190426 NomadBSD, a BSD for the Road.md b/sources/tech/20190426 NomadBSD, a BSD for the Road.md
new file mode 100644
index 0000000000..d31f9b4a90
--- /dev/null
+++ b/sources/tech/20190426 NomadBSD, a BSD for the Road.md
@@ -0,0 +1,125 @@
+[#]: collector: (lujun9972)
+[#]: translator: ( )
+[#]: reviewer: ( )
+[#]: publisher: ( )
+[#]: url: ( )
+[#]: subject: (NomadBSD, a BSD for the Road)
+[#]: via: (https://itsfoss.com/nomadbsd/)
+[#]: author: (John Paul https://itsfoss.com/author/john/)
+
+NomadBSD, a BSD for the Road
+======
+
+As regular It’s FOSS readers should know, I like diving into the world of BSDs. Recently, I came across an interesting BSD that is designed to live on a thumb drive. Let’s take a look at NomadBSD.
+
+### What is NomadBSD?
+
+![Nomadbsd Desktop][1]
+
+[NomadBSD][2] is different than most available BSDs. NomadBSD is a live system based on FreeBSD. It comes with automatic hardware detection and an initial config tool. NomadBSD is designed to “be used as a desktop system that works out of the box, but can also be used for data recovery, for educational purposes, or to test FreeBSD’s hardware compatibility.”
+
+This German BSD comes with an [OpenBox][3]-based desktop with the Plank application dock. NomadBSD makes use of the [DSB project][4]. DSB stands for “Desktop Suite (for) (Free)BSD” and consists of a collection of programs designed to create a simple and working environment without needing a ton of dependencies to use one tool. DSB is created by [Marcel Kaiser][5] one of the lead devs of NomadBSD.
+
+Just like the original BSD projects, you can contact the NomadBSD developers via a [mailing list][6].
+
+[][7]
+
+Suggested read Enjoy Netflix? You Should Thank FreeBSD
+
+#### Included Applications
+
+NomadBSD comes with the following software installed:
+
+ * Thunar file manager
+ * Asunder CD ripper
+ * Bash 5.0
+ * Filezilla FTP client
+ * Firefox web browser
+ * Fish Command line
+ * Gimp
+ * Qpdfview
+ * Git
+
+
+ * Hexchat IRC client
+ * Leafpad text editor
+ * Midnight Commander file manager
+ * PaleMoon web browser
+ * PCManFM file manager
+ * Pidgin messaging client
+ * Transmission BitTorrent client
+
+
+ * Redshift
+ * Sakura terminal emulator
+ * Slim login manager
+ * Thunderbird email client
+ * VLC media player
+ * Plank application dock
+ * Z Shell
+
+
+
+You can see a complete of the pre-installed applications in the [MANIFEST file][8].
+
+![Nomadbsd Openbox Menu][9]
+
+#### Version 1.2 Released
+
+NomadBSD recently released version 1.2 on April 21, 2019. This means that NomadBSD is now based on FreeBSD 12.0-p3. TRIM is now enabled by default. One of the biggest changes is that the initial command-line setup was replaced with a Qt graphical interface. They also added a Qt5 tool to install NomadBSD to your hard drive. A number of fixes were included to improve graphics support. They also added support for creating 32-bit images.
+
+[][10]
+
+Suggested read 6 Reasons Why Linux Users Switch to BSD
+
+### Installing NomadBSD
+
+Since NomadBSD is designed to be a live system, we will need to add the BSD to a USB drive. First, you will need to [download it][11]. There are several options to choose from: 64-bit, 32-bit, or 64-bit Mac.
+
+You will be a USB drive that has at least 4GB. The system that you are installing to should have a 1.2 GHz processor and 1GB of RAM to run NomadBSD comfortably. Both BIOS and UEFI are supported.
+
+All of the images available for download are compressed as a `.lzma` file. So, once you have downloaded the file, you will need to extract the `.img` file. On Linux, you can use either of these commands: `lzma -d nomadbsd-x.y.z.img.lzma` or `xzcat nomadbsd-x.y.z.img.lzma`. (Be sure to replace x.y.z with the correct file name you just downloaded.)
+
+Before we proceed, we need to find out the id of your USB drive. (Hopefully, you have inserted it by now.) I use the `lsblk` command to find my USB drive, which in my case is `sdb`. To write the image file, use this command `sudo dd if=nomadbsd-x.y.z.img of=/dev/sdb bs=1M conv=sync`. (Again, don’t forget to correct the file name.) If you are uncomfortable using `dd`, you can use [Etcher][12]. If you have Windows, you will need to use [7-zip][13] to extract the image file and Etcher or [Rufus][14] to write the image to the USB drive.
+
+When you boot from the USB drive, you will encounter a simple config tool. Once you answer the required questions, you will be greeted with a simple Openbox desktop.
+
+### Thoughts on NomadBSD
+
+I first discovered NomadBSD back in January when they released 1.2-RC1. At the time, I had been unable to install [Project Trident][15] on my laptop and was very frustrated with BSDs. I downloaded NomadBSD and tried it out. I initially ran into issues reaching the desktop, but RC2 fixed that issue. However, I was unable to get on the internet, even though I had an Ethernet cable plugged in. Luckily, I found the wifi manager in the menu and was able to connect to my wifi.
+
+Overall, my experience with NomadBSD was pleasant. Once I figured out a few things, I was good to go. I hope that NomadBSD is the first of a new generation of BSDs that focus on mobility and ease of use. BSD has conquered the server world, it’s about time they figured out how to be more user-friendly.
+
+Have you ever used NomadBSD? What is your BSD? Please let us know in the comments below.
+
+If you found this article interesting, please take a minute to share it on social media, Hacker News or [Reddit][16].
+
+--------------------------------------------------------------------------------
+
+via: https://itsfoss.com/nomadbsd/
+
+作者:[John Paul][a]
+选题:[lujun9972][b]
+译者:[译者ID](https://github.com/译者ID)
+校对:[校对者ID](https://github.com/校对者ID)
+
+本文由 [LCTT](https://github.com/LCTT/TranslateProject) 原创编译,[Linux中国](https://linux.cn/) 荣誉推出
+
+[a]: https://itsfoss.com/author/john/
+[b]: https://github.com/lujun9972
+[1]: https://itsfoss.com/wp-content/uploads/2019/04/NomadBSD-desktop-800x500.jpg
+[2]: http://nomadbsd.org/
+[3]: http://openbox.org/wiki/Main_Page
+[4]: https://freeshell.de/%7Emk/projects/dsb.html
+[5]: https://github.com/mrclksr
+[6]: http://nomadbsd.org/contact.html
+[7]: https://itsfoss.com/netflix-freebsd-cdn/
+[8]: http://nomadbsd.org/download/nomadbsd-1.2.manifest
+[9]: https://itsfoss.com/wp-content/uploads/2019/04/NomadBSD-Openbox-menu-800x500.jpg
+[10]: https://itsfoss.com/why-use-bsd/
+[11]: http://nomadbsd.org/download.html
+[12]: https://www.balena.io/etcher/
+[13]: https://www.7-zip.org/
+[14]: https://rufus.ie/
+[15]: https://itsfoss.com/project-trident-interview/
+[16]: http://reddit.com/r/linuxusersgroup
diff --git a/sources/tech/20190429 Awk utility in Fedora.md b/sources/tech/20190429 Awk utility in Fedora.md
new file mode 100644
index 0000000000..21e40641f7
--- /dev/null
+++ b/sources/tech/20190429 Awk utility in Fedora.md
@@ -0,0 +1,177 @@
+[#]: collector: (lujun9972)
+[#]: translator: ( )
+[#]: reviewer: ( )
+[#]: publisher: ( )
+[#]: url: ( )
+[#]: subject: (Awk utility in Fedora)
+[#]: via: (https://fedoramagazine.org/awk-utility-in-fedora/)
+[#]: author: (Stephen Snow https://fedoramagazine.org/author/jakfrost/)
+
+Awk utility in Fedora
+======
+
+![][1]
+
+Fedora provides _awk_ as part of its default installation, including all its editions, including the immutable ones like Silverblue. But you may be asking, what is _awk_ and why would you need it?
+
+_Awk_ is a data driven programming language that acts when it matches a pattern. On Fedora, and most other distributions, GNU _awk_ or _gawk_ is used. Read on for more about this language and how to use it.
+
+### A brief history of awk
+
+_Awk_ began at Bell Labs in 1977. Its name is an acronym from the initials of the designers: Alfred V. Aho, Peter J. Weinberger, and Brian W. Kernighan.
+
+> The specification for _awk_ in the POSIX Command Language and Utilities standard further clarified the language. Both the _gawk_ designers and the original _awk_ designers at Bell Laboratories provided feedback for the POSIX specification.
+>
+> From [The GNU Awk User’s Guide][2]
+
+For a more in-depth look at how _awk/gawk_ ended up being as powerful and useful as it is, follow the link above. Numerous individuals have contributed to the current state of _gawk_. Among those are:
+
+ * Arnold Robbins and David Trueman, the creators of _gawk_
+ * Michael Brennan, the creator of _mawk_ , which later was merged with _gawk_
+ * Jurgen Kahrs, who added networking capabilities to _gawk_ in 1997
+ * John Hague, who rewrote the _gawk_ internals and added an _awk_ -level debugger in 2011
+
+
+
+### Using awk
+
+The following sections show various ways of using _awk_ in Fedora.
+
+#### At the command line
+
+The simples way to invoke _awk_ is at the command line. You can search a text file for a particular pattern, and if found, print out the line(s) of the file that match the pattern anywhere. As an example, use _cat_ to take a look at the command history file in your home director:
+
+```
+$ cat ~/.bash_history
+```
+
+There are probably many lines scrolling by right now.
+
+_Awk_ helps with this type of file quite easily. Instead of printing the entire file out to the terminal like _cat_ , you can use _awk_ to find something of specific interest. For this example, type the following at the command line if you’re running a standard Fedora edition:
+
+```
+$ awk '/dnf/' ~/.bash_history
+```
+
+If you’re running Silverblue, try this instead:
+
+```
+$ awk '/rpm-ostree/' ~/.bash_history
+```
+
+In both cases, more data likely appears than what you really want. That’s no problem for _awk_ since it can accept regular expressions. Using the previous example, you can change the pattern to more closely match search requirements of wanting to know about installs only. Try changing the search pattern to one of these:
+
+```
+$ awk '/rpm-ostree install/' ~/.bash_history
+$ awk '/dnf install/' ~/.bash_history
+```
+
+All the entries of your bash command line history appear that have the pattern specified at any position along the line. Awk works on one line of a data file at a time. It matches pattern, then performs an action, then moves to next line until the end of file (EOF) is reached.
+
+#### From an _awk_ program
+
+Using awk at the command line as above is not much different than piping output to _grep_ , like this:
+
+```
+$ cat .bash_history | grep 'dnf install'
+```
+
+The end result of printing to standard output ( _stdout_ ) is the same with both methods.
+
+Awk is a programming language, and the command _awk_ is an interpreter of that language. The real power and flexibility of _awk_ is you can make programs with it, and combine them with shell scripts to create even more powerful programs. For more feature rich development with _awk_ , you can also incorporate C or C++ code using [Dynamic-Extensions][3].
+
+Next, to show the power of _awk_ , let’s make a couple of program files to print the header and draw five numbers for the first row of a bingo card. To do this we’ll create two awk program files.
+
+The first file prints out the header of the bingo card. For this example it is called _bingo-title.awk_. Use your favorite editor to save this text as that file name:
+```
+
+```
+
+BEGIN {
+print "B\tI\tN\tG\tO"
+}
+```
+
+```
+
+Now the title program is ready. You could try it out with this command:
+
+```
+$ awk -f bingo-title.awk
+```
+
+The program prints the word BINGO, with a tab space ( _\t_ ) between the characters. For the number selection, let’s use one of awk’s builtin numeric functions called _rand()_ and use two of the control statements, _for_ and _switch._ (Except the editor changed my program, so no switch statement used this time).
+
+The title of the second awk program is _bingo-num.awk_. Enter the following into your favorite editor and save with that file name:
+```
+
+```
+
+@include "bingo-title.awk"
+BEGIN {
+for (i = 1; i < = 5; i++) {
+b = int(rand() * 15) + (15*(i-1))
+printf "%s\t", b
+}
+print
+}
+```
+
+```
+
+The _@include_ statement in the file tells the interpreter to process the included file first. In this case the interpreter processs the _bingo-title.awk_ file so the title prints out first.
+
+#### Running the test program
+
+Now enter the command to pick a row of bingo numbers:
+
+```
+$ awk -f bingo-num.awk
+```
+
+Output appears similar to the following. Note that the _rand()_ function in _awk_ is not ideal for truly random numbers. It’s used here only as for example purposes.
+```
+
+```
+
+$ awk -f bingo-num.awk
+B I N G O
+13 23 34 53 71
+```
+
+```
+
+In the example, we created two programs with only beginning sections that used actions to manipulate data generated from within the awk program. In order to satisfy the rules of Bingo, more work is needed to achieve the desirable results. The reader is encouraged to fix the programs so they can reliably pick bingo numbers, maybe look at the awk function _srand()_ for answers on how that could be done.
+
+### Final examples
+
+_Awk_ can be useful even for mundane daily search tasks that you encounter, like listing all _flatpak’s_ on the _Flathub_ repository from _org.gnome_ (providing you have the Flathub repository setup). The command to do that would be:
+
+```
+$ flatpak remote-ls flathub --system | awk /org.gnome/
+```
+
+A listing appears that shows all output from _remote-ls_ that matches the _org.gnome_ pattern. To see flatpaks already installed from org.gnome, enter this command:
+
+```
+$ flatpak list --system | awk /org.gnome/
+```
+
+Awk is a powerful and flexible programming language that fills a niche with text file manipulation exceedingly well.
+
+--------------------------------------------------------------------------------
+
+via: https://fedoramagazine.org/awk-utility-in-fedora/
+
+作者:[Stephen Snow][a]
+选题:[lujun9972][b]
+译者:[译者ID](https://github.com/译者ID)
+校对:[校对者ID](https://github.com/校对者ID)
+
+本文由 [LCTT](https://github.com/LCTT/TranslateProject) 原创编译,[Linux中国](https://linux.cn/) 荣誉推出
+
+[a]: https://fedoramagazine.org/author/jakfrost/
+[b]: https://github.com/lujun9972
+[1]: https://fedoramagazine.org/wp-content/uploads/2019/04/awk-816x345.jpg
+[2]: https://www.gnu.org/software/gawk/manual/gawk.html#Foreword3
+[3]: https://www.gnu.org/software/gawk/manual/gawk.html#Dynamic-Extensions
diff --git a/sources/tech/20190429 How To Turn On And Shutdown The Raspberry Pi -Absolute Beginner Tip.md b/sources/tech/20190429 How To Turn On And Shutdown The Raspberry Pi -Absolute Beginner Tip.md
new file mode 100644
index 0000000000..ce667a1dff
--- /dev/null
+++ b/sources/tech/20190429 How To Turn On And Shutdown The Raspberry Pi -Absolute Beginner Tip.md
@@ -0,0 +1,111 @@
+[#]: collector: (lujun9972)
+[#]: translator: ( )
+[#]: reviewer: ( )
+[#]: publisher: ( )
+[#]: url: ( )
+[#]: subject: (How To Turn On And Shutdown The Raspberry Pi [Absolute Beginner Tip])
+[#]: via: (https://itsfoss.com/turn-on-raspberry-pi/)
+[#]: author: (Chinmay https://itsfoss.com/author/chinmay/)
+
+How To Turn On And Shutdown The Raspberry Pi [Absolute Beginner Tip]
+======
+
+_**Brief: This quick tip teaches you how to turn on Raspberry Pi and how to shut it down properly afterwards.**_
+
+The [Raspberry Pi][1] is one of the [most popular SBC (Single-Board-Computer)][2]. If you are interested in this topic, I believe that you’ve finally got a Pi device. I also advise to get all the [additional Raspberry Pi accessories][3] to get started with your device.
+
+You’re ready to turn it on and start to tinker around with it. It has it’s own similarities and differences compared to traditional computers like desktops and laptops.
+
+Today, let’s go ahead and learn how to turn on and shutdown a Raspberry Pi as it doesn’t really feature a ‘power button’ of sorts.
+
+For this article I’m using a Raspberry Pi 3B+, but it’s the same for all the Raspberry Pi variants.
+
+Bestseller No. 1
+
+[][4]
+
+[CanaKit Raspberry Pi 3 B+ (B Plus) Starter Kit (32 GB EVO+ Edition, Premium Black Case)][4]
+
+CanaKit - Personal Computers
+
+$79.99 [][5]
+
+Bestseller No. 2
+
+[][6]
+
+[CanaKit Raspberry Pi 3 B+ (B Plus) with Premium Clear Case and 2.5A Power Supply][6]
+
+CanaKit - Personal Computers
+
+$54.99 [][5]
+
+### Turn on Raspberry Pi
+
+![Micro USB port for Power][7]
+
+The micro USB port powers the Raspberry Pi, the way you turn it on is by plugging in the power cable into the micro USB port. But, before you do that you should make sure that you have done the following things.
+
+ * Preparing the micro SD card with Raspbian according to the official [guide][8] and inserting into the micro SD card slot.
+ * Plugging in the HDMI cable, USB keyboard and a Mouse.
+ * Plugging in the Ethernet Cable(Optional).
+
+
+
+Once you have done the above, plug in the power cable. This turns on the Raspberry Pi and the display will light up and load the Operating System.
+
+Bestseller No. 1
+
+[][4]
+
+[CanaKit Raspberry Pi 3 B+ (B Plus) Starter Kit (32 GB EVO+ Edition, Premium Black Case)][4]
+
+CanaKit - Personal Computers
+
+$79.99 [][5]
+
+### Shutting Down the Pi
+
+Shutting down the Pi is pretty straight forward, click the menu button and choose shutdown.
+
+![Turn off Raspberry Pi graphically][9]
+
+Alternatively, you can use the [shutdown command][10] in the terminal:
+
+```
+sudo shutdown now
+```
+
+Once the shutdown process has started **wait** till it completely finishes and then you can cut the power to it. Once the Pi shuts down, there is no real way to turn the Pi back on without turning off and turning on the power. You could the GPIO’s to turn on the Pi from the shutdown state but it’ll require additional modding.
+
+[][2]
+
+Suggested read 12 Single Board Computers: Alternative to Raspberry Pi
+
+_Note: Micro USB ports tend to be fragile, hence turn-off/on the power at source instead of frequently unplugging and plugging into the micro USB port._
+
+Well, that’s about all you should know about turning on and shutting down the Pi, what do you plan to use it for? Let me know in the comments.
+
+--------------------------------------------------------------------------------
+
+via: https://itsfoss.com/turn-on-raspberry-pi/
+
+作者:[Chinmay][a]
+选题:[lujun9972][b]
+译者:[译者ID](https://github.com/译者ID)
+校对:[校对者ID](https://github.com/校对者ID)
+
+本文由 [LCTT](https://github.com/LCTT/TranslateProject) 原创编译,[Linux中国](https://linux.cn/) 荣誉推出
+
+[a]: https://itsfoss.com/author/chinmay/
+[b]: https://github.com/lujun9972
+[1]: https://www.raspberrypi.org/
+[2]: https://itsfoss.com/raspberry-pi-alternatives/
+[3]: https://itsfoss.com/things-you-need-to-get-your-raspberry-pi-working/
+[4]: https://www.amazon.com/CanaKit-Raspberry-Starter-Premium-Black/dp/B07BCC8PK7?SubscriptionId=AKIAJ3N3QBK3ZHDGU54Q&tag=chmod7mediate-20&linkCode=xm2&camp=2025&creative=165953&creativeASIN=B07BCC8PK7&keywords=raspberry%20pi%20kit (CanaKit Raspberry Pi 3 B+ (B Plus) Starter Kit (32 GB EVO+ Edition, Premium Black Case))
+[5]: https://www.amazon.com/gp/prime/?tag=chmod7mediate-20 (Amazon Prime)
+[6]: https://www.amazon.com/CanaKit-Raspberry-Premium-Clear-Supply/dp/B07BC7BMHY?SubscriptionId=AKIAJ3N3QBK3ZHDGU54Q&tag=chmod7mediate-20&linkCode=xm2&camp=2025&creative=165953&creativeASIN=B07BC7BMHY&keywords=raspberry%20pi%20kit (CanaKit Raspberry Pi 3 B+ (B Plus) with Premium Clear Case and 2.5A Power Supply)
+[7]: https://i0.wp.com/itsfoss.com/wp-content/uploads/2019/04/raspberry-pi-3-microusb.png?fit=800%2C532&ssl=1
+[8]: https://www.raspberrypi.org/documentation/installation/installing-images/README.md
+[9]: https://i1.wp.com/itsfoss.com/wp-content/uploads/2019/04/Raspbian-ui-menu.jpg?fit=800%2C492&ssl=1
+[10]: https://linuxhandbook.com/linux-shutdown-command/
diff --git a/sources/tech/20190501 Looking into Linux modules.md b/sources/tech/20190501 Looking into Linux modules.md
new file mode 100644
index 0000000000..eb3125c19b
--- /dev/null
+++ b/sources/tech/20190501 Looking into Linux modules.md
@@ -0,0 +1,219 @@
+[#]: collector: (lujun9972)
+[#]: translator: ( )
+[#]: reviewer: ( )
+[#]: publisher: ( )
+[#]: url: ( )
+[#]: subject: (Looking into Linux modules)
+[#]: via: (https://www.networkworld.com/article/3391362/looking-into-linux-modules.html#tk.rss_all)
+[#]: author: (Sandra Henry-Stocker https://www.networkworld.com/author/Sandra-Henry_Stocker/)
+
+Looking into Linux modules
+======
+The lsmod command can tell you which kernel modules are currently loaded on your system, along with some interesting details about their use.
+![Rob Oo \(CC BY 2.0\)][1]
+
+### What are Linux modules?
+
+Kernel modules are chunks of code that are loaded and unloaded into the kernel as needed, thus extending the functionality of the kernel without requiring a reboot. In fact, unless users inquire about modules using commands like **lsmod** , they won't likely know that anything has changed.
+
+One important thing to understand is that there are _lots_ of modules that will be in use on your Linux system at all times and that a lot of details are available if you're tempted to dive into the details.
+
+One of the prime ways that lsmod is used is to examine modules when a system isn't working properly. However, most of the time, modules load as needed and users don't need to be aware of how they are working.
+
+**[ Also see:[Must-know Linux Commands][2] ]**
+
+### Listing modules
+
+The easiest way to list modules is with the **lsmod** command. While this command provides a lot of detail, this is the most user-friendly output.
+
+```
+$ lsmod
+Module Size Used by
+snd_hda_codec_realtek 114688 1
+snd_hda_codec_generic 77824 1 snd_hda_codec_realtek
+ledtrig_audio 16384 2 snd_hda_codec_generic,snd_hda_codec_realtek
+snd_hda_codec_hdmi 53248 1
+snd_hda_intel 40960 2
+snd_hda_codec 131072 4 snd_hda_codec_generic,snd_hda_codec_hdmi,snd_hda_intel
+ ,snd_hda_codec_realtek
+snd_hda_core 86016 5 snd_hda_codec_generic,snd_hda_codec_hdmi,snd_hda_intel
+ ,snd_hda_codec,snd_hda_codec_realtek
+snd_hwdep 20480 1 snd_hda_codec
+snd_pcm 102400 4 snd_hda_codec_hdmi,snd_hda_intel,snd_hda_codec,snd_hda
+ _core
+snd_seq_midi 20480 0
+snd_seq_midi_event 16384 1 snd_seq_midi
+dcdbas 20480 0
+snd_rawmidi 36864 1 snd_seq_midi
+snd_seq 69632 2 snd_seq_midi,snd_seq_midi_event
+coretemp 20480 0
+snd_seq_device 16384 3 snd_seq,snd_seq_midi,snd_rawmidi
+snd_timer 36864 2 snd_seq,snd_pcm
+kvm_intel 241664 0
+kvm 626688 1 kvm_intel
+radeon 1454080 10
+irqbypass 16384 1 kvm
+joydev 24576 0
+input_leds 16384 0
+ttm 102400 1 radeon
+drm_kms_helper 180224 1 radeon
+drm 475136 13 drm_kms_helper,radeon,ttm
+snd 81920 15 snd_hda_codec_generic,snd_seq,snd_seq_device,snd_hda
+ _codec_hdmi,snd_hwdep,snd_hda_intel,snd_hda_codec,snd
+ _hda_codec_realtek,snd_timer,snd_pcm,snd_rawmidi
+i2c_algo_bit 16384 1 radeon
+fb_sys_fops 16384 1 drm_kms_helper
+syscopyarea 16384 1 drm_kms_helper
+serio_raw 20480 0
+sysfillrect 16384 1 drm_kms_helper
+sysimgblt 16384 1 drm_kms_helper
+soundcore 16384 1 snd
+mac_hid 16384 0
+sch_fq_codel 20480 2
+parport_pc 40960 0
+ppdev 24576 0
+lp 20480 0
+parport 53248 3 parport_pc,lp,ppdev
+ip_tables 28672 0
+x_tables 40960 1 ip_tables
+autofs4 45056 2
+raid10 57344 0
+raid456 155648 0
+async_raid6_recov 24576 1 raid456
+async_memcpy 20480 2 raid456,async_raid6_recov
+async_pq 24576 2 raid456,async_raid6_recov
+async_xor 20480 3 async_pq,raid456,async_raid6_recov
+async_tx 20480 5 async_pq,async_memcpy,async_xor,raid456,async_raid6_re
+ cov
+xor 24576 1 async_xor
+raid6_pq 114688 3 async_pq,raid456,async_raid6_recov
+libcrc32c 16384 1 raid456
+raid1 45056 0
+raid0 24576 0
+multipath 20480 0
+linear 20480 0
+hid_generic 16384 0
+psmouse 151552 0
+i2c_i801 32768 0
+pata_acpi 16384 0
+lpc_ich 24576 0
+usbhid 53248 0
+hid 126976 2 usbhid,hid_generic
+e1000e 245760 0
+floppy 81920 0
+```
+
+In the output above:
+
+ * "Module" shows the name of each module
+ * "Size" shows the module size (not how much memory it is using)
+ * "Used by" shows each module's usage count and the referring modules
+
+
+
+Clearly, that's a _lot_ of modules. The number of modules loaded will depend on your system and distribution and what's running. We can count them like this:
+
+```
+$ lsmod | wc -l
+67
+```
+
+To see the number of modules available on the system (not just running), try this command:
+
+```
+$ modprobe -c | wc -l
+41272
+```
+
+### Other commands for examining modules
+
+Linux provides several commands for listing, loading and unloading, examining, and checking the status of modules.
+
+ * depmod -- generates modules.dep and map files
+ * insmod -- a simple program to insert a module into the Linux Kernel
+ * lsmod -- show the status of modules in the Linux Kernel
+ * modinfo -- show information about a Linux Kernel module
+ * modprobe -- add and remove modules from the Linux Kernel
+ * rmmod -- a simple program to remove a module from the Linux Kernel
+
+
+
+### Listing modules that are built in
+
+As mentioned above, the **lsmod** command is the most convenient command for listing modules. There are, however, other ways to examine them. The modules.builtin file lists all modules that are built into the kernel and is used by modprobe when trying to load one of these modules. Note that **$(uname -r)** in the commands below provides the name of the kernel release.
+
+```
+$ more /lib/modules/$(uname -r)/modules.builtin | head -10
+kernel/arch/x86/crypto/crc32c-intel.ko
+kernel/arch/x86/events/intel/intel-uncore.ko
+kernel/arch/x86/platform/intel/iosf_mbi.ko
+kernel/mm/zpool.ko
+kernel/mm/zbud.ko
+kernel/mm/zsmalloc.ko
+kernel/fs/binfmt_script.ko
+kernel/fs/mbcache.ko
+kernel/fs/configfs/configfs.ko
+kernel/fs/crypto/fscrypto.ko
+```
+
+You can get some additional detail on a module by using the **modinfo** command, though nothing that qualifies as an easy explanation of what service the module provides. The omitted details from the output below include a lengthy signature.
+
+```
+$ modinfo floppy | head -16
+filename: /lib/modules/5.0.0-13-generic/kernel/drivers/block/floppy.ko
+alias: block-major-2-*
+license: GPL
+author: Alain L. Knaff
+srcversion: EBEAA26742DF61790588FD9
+alias: acpi*:PNP0700:*
+alias: pnp:dPNP0700*
+depends:
+retpoline: Y
+intree: Y
+name: floppy
+vermagic: 5.0.0-13-generic SMP mod_unload
+sig_id: PKCS#7
+signer:
+sig_key:
+sig_hashalgo: md4
+```
+
+You can load or unload a module using the **modprobe** command. Using a command like the one below, you can locate the kernel object associated with a particular module:
+
+```
+$ find /lib/modules/$(uname -r) -name floppy*
+/lib/modules/5.0.0-13-generic/kernel/drivers/block/floppy.ko
+```
+
+If you needed to load the module, you could use a command like this one:
+
+```
+$ sudo modprobe floppy
+```
+
+### Wrap-up
+
+Clearly the loading and unloading of modules is a big deal. It makes Linux systems considerably more flexible and efficient than if they ran with a one-size-fits-all kernel. It also means you can make significant changes — including adding hardware — without rebooting.
+
+**[ Two-Minute Linux Tips:[Learn how to master a host of Linux commands in these 2-minute video tutorials][3] ]**
+
+Join the Network World communities on [Facebook][4] and [LinkedIn][5] to comment on topics that are top of mind.
+
+--------------------------------------------------------------------------------
+
+via: https://www.networkworld.com/article/3391362/looking-into-linux-modules.html#tk.rss_all
+
+作者:[Sandra Henry-Stocker][a]
+选题:[lujun9972][b]
+译者:[译者ID](https://github.com/译者ID)
+校对:[校对者ID](https://github.com/校对者ID)
+
+本文由 [LCTT](https://github.com/LCTT/TranslateProject) 原创编译,[Linux中国](https://linux.cn/) 荣誉推出
+
+[a]: https://www.networkworld.com/author/Sandra-Henry_Stocker/
+[b]: https://github.com/lujun9972
+[1]: https://images.idgesg.net/images/article/2019/04/modules-100794941-large.jpg
+[2]: https://www.networkworld.com/article/3391029/must-know-linux-commands.html
+[3]: https://www.youtube.com/playlist?list=PL7D2RMSmRO9J8OTpjFECi8DJiTQdd4hua
+[4]: https://www.facebook.com/NetworkWorld/
+[5]: https://www.linkedin.com/company/network-world
diff --git a/sources/tech/20190502 Crowdsourcing license compliance with ClearlyDefined.md b/sources/tech/20190502 Crowdsourcing license compliance with ClearlyDefined.md
new file mode 100644
index 0000000000..fe36e37b9c
--- /dev/null
+++ b/sources/tech/20190502 Crowdsourcing license compliance with ClearlyDefined.md
@@ -0,0 +1,99 @@
+[#]: collector: (lujun9972)
+[#]: translator: ( )
+[#]: reviewer: ( )
+[#]: publisher: ( )
+[#]: url: ( )
+[#]: subject: (Crowdsourcing license compliance with ClearlyDefined)
+[#]: via: (https://opensource.com/article/19/5/license-compliance-clearlydefined)
+[#]: author: (Jeff McAffer https://opensource.com/users/jeffmcaffer)
+
+Crowdsourcing license compliance with ClearlyDefined
+======
+Licensing is what holds open source together, and ClearlyDefined takes
+the mystery out of projects' licenses, copyright, and source location.
+![][1]
+
+Open source use continues to skyrocket, not just in use cases and scenarios but also in volume. It is trivial for a developer to depend on a 1,000 JavaScript packages from a single run of `npm install` or have thousands of packages in a [Docker][2] image. At the same time, there is increased interest in ensuring license compliance.
+
+Without the right license you may not be able to legally use a software component in the way you intend or may have obligations that run counter to your business model. For instance, a JavaScript package could be marked as [MIT license][3], which allows commercial reuse, while one of its dependencies is licensed has a [copyleft license][4] that requires you give your software away under the same license. Complying means finding the applicable license(s), and assessing and adhering to the terms, which is not too bad for individual components adn can be daunting for large initiatives.
+
+Fortunately, this open source challenge has an open source solution: [ClearlyDefined][5]. ClearlyDefined is a crowdsourced, open source, [Open Source Initiative][6] (OSI) effort to gather, curate, and upstream/normalize data about open source components, such as license, copyright, and source location. This data is the cornerstone of reducing the friction in open source license compliance.
+
+The premise behind ClearlyDefined is simple: we are all struggling to find and understand key information related to the open source we use—whether it is finding the license, knowing who to attribute, or identifying the source that goes with a particular package. Rather than struggling independently, ClearlyDefined allows us to collaborate and share the compliance effort. Moreover, the ClearlyDefined community seeks to upstream any corrections so future releases are more clearly defined and make conventions more explicit to improve community understanding of project intent.
+
+### How it works
+
+![ClearlyDefined's harvest, curate, upstream process][7]
+
+ClearlyDefined monitors the open source ecosystem and automatically harvests relevant data from open source components using a host of open source tools such as [ScanCode][8], [FOSSology][9], and [Licensee][10]. The results are summarized and aggregated to create a _definition_ , which is then surfaced to users via an API and a UI. Each definition includes:
+
+ * Declared license of the component
+ * Licenses and copyrights discovered across all files
+ * Exact source code location to the commit level
+ * Release date
+ * List of embedded components
+
+
+
+Coincidentally (well, not really), this is exactly the data you need to do license compliance.
+
+### Curating
+
+Any given definition may have gaps or imperfections due to tool issues or the data being missing or incorrect at the origin. ClearlyDefined enables users to curate the results by refining the values and filling in the gaps. These contributions are reviewed and merged, as with any open source project. The result is an improved dataset for all to use.
+
+### Getting ahead
+
+To a certain degree, this process is still chasing the problem—analyzing and curating after the packages have already been published. To get ahead of the game, the ClearlyDefined community also feeds merged curations back to the originating projects as pull requests (e.g., adding a license file, clarifying a copyright). This increases the clarity of future release and sets up a virtuous cycle.
+
+### Adapting, not mandating
+
+In doing the analysis, we've found quite a number of approaches to expressing license-related data. Different communities put LICENSE files in different places or have different practices around attribution. The ClearlyDefined philosophy is to discover these conventions and adapt to them rather than asking the communities to do something different. A side benefit of this is that implicit conventions can be made more explicit, improving clarity for all.
+
+Related to this, ClearlyDefined is careful to not look too hard for this interesting data. If we have to be too smart and infer too much to find the data, then there's a good chance the origin is not all that clear. Instead, we prefer to work with the community to better understand and clarify the conventions being used. From there, we can update the tools accordingly and make it easier to be "clearly defined."
+
+#### NOTICE files
+
+As an added bonus for users, we set up an API and UI for generating NOTICE files, making it trivial for you to comply with the attribution requirements found in most open source licenses. You can give ClearlyDefined a list of components (e.g., _drag and drop an npm package-lock.json file on the UI_ ) and get back a fully formed NOTICE file rendered by one of several renderers (e.g., text, HTML, Handlebars.js template). This is a snap, given that we already have all the compliance data. Big shout out to the [OSS Attribution Builder project][11] for making a simple and pluggable NOTICE renderer we could just pop into the ClearlyDefined service.
+
+### Getting involved
+
+You can get involved with ClearlyDefined in several ways:
+
+ * Become an active user, contributing to your compliance workflow
+ * Review other people's curations using the interface
+ * Get involved in [the code][12] (Node and React)
+ * Ask and answer questions on [our mailing list][13] or [Discord channel][14]
+ * Contribute money to the OSI targeted to ClearlyDefined. We'll use that to fund development and curation.
+
+
+
+We are excited to continue to grow our community of contributors so that licensing can continue to become an understable part of any team's open source adoption. For more information, check out [https://clearlydefined.io][15].
+
+--------------------------------------------------------------------------------
+
+via: https://opensource.com/article/19/5/license-compliance-clearlydefined
+
+作者:[Jeff McAffer][a]
+选题:[lujun9972][b]
+译者:[译者ID](https://github.com/译者ID)
+校对:[校对者ID](https://github.com/校对者ID)
+
+本文由 [LCTT](https://github.com/LCTT/TranslateProject) 原创编译,[Linux中国](https://linux.cn/) 荣誉推出
+
+[a]: https://opensource.com/users/jeffmcaffer
+[b]: https://github.com/lujun9972
+[1]: https://opensource.com/sites/default/files/styles/image-full-size/public/lead-images/OSDC_Crowdfunding_520x292_9597717_0612CM.png?itok=lxSKyFXU
+[2]: https://opensource.com/resources/what-docker
+[3]: /article/19/4/history-mit-license
+[4]: /resources/what-is-copyleft
+[5]: https://clearlydefined.io
+[6]: https://opensource.org
+[7]: https://opensource.com/sites/default/files/uploads/clearlydefined.png (ClearlyDefined's harvest, curate, upstream process)
+[8]: https://github.com/nexB/scancode-toolkit
+[9]: https://www.fossology.org/
+[10]: https://github.com/licensee/licensee
+[11]: https://github.com/amzn/oss-attribution-builder
+[12]: https://github.com/clearlydefined
+[13]: mailto:clearlydefined@googlegroups.com
+[14]: %C2%A0https://clearlydefined.io/discord)
+[15]: https://clearlydefined.io/
diff --git a/sources/tech/20190502 The making of the Breaking the Code electronic book.md b/sources/tech/20190502 The making of the Breaking the Code electronic book.md
new file mode 100644
index 0000000000..6786df8549
--- /dev/null
+++ b/sources/tech/20190502 The making of the Breaking the Code electronic book.md
@@ -0,0 +1,62 @@
+[#]: collector: (lujun9972)
+[#]: translator: ( )
+[#]: reviewer: ( )
+[#]: publisher: ( )
+[#]: url: ( )
+[#]: subject: (The making of the Breaking the Code electronic book)
+[#]: via: (https://opensource.com/article/19/5/code-book)
+[#]: author: (Alicia Gibb https://opensource.com/users/aliciagibb/users/don-watkins)
+
+The making of the Breaking the Code electronic book
+======
+Offering a safe space for middle school girls to learn technology speaks
+volumes about who should be sitting around the tech table.
+![Open hardware electronic book][1]
+
+I like a good challenge. The [Open Source Stories team][2] came to me with a great one: Create a hardware project where students could create their own thing that would be put together as a larger thing. The students would be middle school girls. My job was to figure out the hardware and make this thing make sense.
+
+After days of sketching out concepts, I was wandering through my local public library, and it dawned on me that the perfect piece of hardware where everyone could design their own part to create something whole is a book! The idea of a book using paper electronics was exciting, simple enough to be taught in a day, and fit the criteria of needing no special equipment, like soldering irons.
+
+!["Breaking the Code" book cover][3]
+
+I designed two parts to the electronics within the book. Half the circuits were developed with copper tape, LEDs, and DIY buttons, and half were developed with LilyPad Arduino microcontrollers, sensors, LEDs, and DIY buttons. Using the electronics in the book, the girls could make pages light up, buzz, or play music using various inputs such as button presses, page turns, or tilting the book.
+
+!['Breaking the Code' interior pages][4]
+
+We worked with young adult author [Lauren Sabel][5] to come up with the story, which features two girls who get locked in the basement of their school and have to solve puzzles to get out. Setting the scene in the basement gave us lots of opportunities to use lights! Along with the story, we received illustrations that the girls enhanced with electronics. The girls got creative, for example, using lights as the skeleton's eyes, not just for the obvious light bulb in the room.
+
+Creating a curriculum that was flexible enough to empower each girl to build her own successfully functioning circuit was a vital piece of the user experience. We chose components so the circuit wouldn't need to be over-engineered. We also used breakout boards and LEDs with built-in resistors so that the circuits allowed flexibility and functioned with only basic knowledge of circuit design—without getting too muddled in the deep end.
+
+!['Breaking the Code' interior pages][6]
+
+The project curriculum gave girls the confidence and skills to understand electronics by building two circuits, in the process learning circuit layout, directional aspects, cause-and-effect through inputs and outputs, and how to identify various components. Controlling electrons by pushing them through a circuit feels a bit like you're controlling a tiny part of the universe. And seeing the girls' faces light up is like seeing a universe of opportunities open in front of them.
+
+!['Breaking the Code' interior pages][7]
+
+The girls were ecstatic to see their work as a completed book, taking pride in their pages and showing others what they had built.
+
+![About 'Breaking the Code'][8]
+
+Teaching them my little corner of the world for the day was a truly empowering experience for me. As a woman in tech, I think this is the right approach for companies trying to change the gender inequalities we see in tech. Offering a safe space to learn—with lots of people in the room who look like you as mentors—speaks volumes about who should be sitting around the tech table.
+
+--------------------------------------------------------------------------------
+
+via: https://opensource.com/article/19/5/code-book
+
+作者:[Alicia Gibb][a]
+选题:[lujun9972][b]
+译者:[译者ID](https://github.com/译者ID)
+校对:[校对者ID](https://github.com/校对者ID)
+
+本文由 [LCTT](https://github.com/LCTT/TranslateProject) 原创编译,[Linux中国](https://linux.cn/) 荣誉推出
+
+[a]: https://opensource.com/users/aliciagibb/users/don-watkins
+[b]: https://github.com/lujun9972
+[1]: https://opensource.com/sites/default/files/styles/image-full-size/public/lead-images/code_book_electronics_hardware.jpg?itok=zb-zaiwz (Open hardware electronic book)
+[2]: https://www.redhat.com/en/open-source-stories
+[3]: https://opensource.com/sites/default/files/uploads/codebook_cover.jpg ("Breaking the Code" book cover)
+[4]: https://opensource.com/sites/default/files/uploads/codebook_38-39.jpg ('Breaking the Code' interior pages)
+[5]: https://www.amazon.com/Lauren-Sabel/e/B01M0FW223
+[6]: https://opensource.com/sites/default/files/uploads/codebook_lightbulb.jpg ('Breaking the Code' interior pages)
+[7]: https://opensource.com/sites/default/files/uploads/codebook_10-11.jpg ('Breaking the Code' interior pages)
+[8]: https://opensource.com/sites/default/files/uploads/codebook_pg1.jpg (About 'Breaking the Code')
diff --git a/sources/tech/20190503 Mirror your System Drive using Software RAID.md b/sources/tech/20190503 Mirror your System Drive using Software RAID.md
new file mode 100644
index 0000000000..1b5936dfa0
--- /dev/null
+++ b/sources/tech/20190503 Mirror your System Drive using Software RAID.md
@@ -0,0 +1,306 @@
+[#]: collector: (lujun9972)
+[#]: translator: ( )
+[#]: reviewer: ( )
+[#]: publisher: ( )
+[#]: url: ( )
+[#]: subject: (Mirror your System Drive using Software RAID)
+[#]: via: (https://fedoramagazine.org/mirror-your-system-drive-using-software-raid/)
+[#]: author: (Gregory Bartholomew https://fedoramagazine.org/author/glb/)
+
+Mirror your System Drive using Software RAID
+======
+
+![][1]
+
+Nothing lasts forever. When it comes to the hardware in your PC, most of it can easily be replaced. There is, however, one special-case hardware component in your PC that is not as easy to replace as the rest — your hard disk drive.
+
+### Drive Mirroring
+
+Your hard drive stores your personal data. Some of your data can be backed up automatically by scheduled backup jobs. But those jobs scan the files to be backed up for changes and trying to scan an entire drive would be very resource intensive. Also, anything that you’ve changed since your last backup will be lost if your drive fails. [Drive mirroring][2] is a better way to maintain a secondary copy of your entire hard drive. With drive mirroring, a secondary copy of _all the data_ on your hard drive is maintained _in real time_.
+
+An added benefit of live mirroring your hard drive to a secondary hard drive is that it can [increase your computer’s performance][3]. Because disk I/O is one of your computer’s main performance [bottlenecks][4], the performance improvement can be quite significant.
+
+Note that a mirror is not a backup. It only protects your data from being lost if one of your physical drives fail. Types of failures that drive mirroring, by itself, does not protect against include:
+
+ * [File System Corruption][5]
+ * [Bit Rot][6]
+ * Accidental File Deletion
+ * Simultaneous Failure of all Mirrored Drives (highly unlikely)
+
+
+
+Some of the above can be addressed by other file system features that can be used in conjunction with drive mirroring. File system features that address the above types of failures include:
+
+ * Using a [Journaling][7] or [Log-Structured][8] file system
+ * Using [Checksums][9] ([ZFS][10] , for example, does this automatically and transparently)
+ * Using [Snapshots][11]
+ * Using [BCVs][12]
+
+
+
+This guide will demonstrate one method of mirroring your system drive using the Multiple Disk and Device Administration (mdadm) toolset. Just for fun, this guide will show how to do the conversion without using any extra boot media (CDs, USB drives, etc). For more about the concepts and terminology related to the multiple device driver, you can skim the _md_ man page:
+
+```
+$ man md
+```
+
+### The Procedure
+
+ 1. **Use** [**sgdisk**][13] **to (re)partition the _extra_ drive that you have added to your computer** :
+
+```
+ $ sudo -i
+# MY_DISK_1=/dev/sdb
+# sgdisk --zap-all $MY_DISK_1
+# test -d /sys/firmware/efi/efivars || sgdisk -n 0:0:+1MiB -t 0:ef02 -c 0:grub_1 $MY_DISK_1
+# sgdisk -n 0:0:+1GiB -t 0:ea00 -c 0:boot_1 $MY_DISK_1
+# sgdisk -n 0:0:+4GiB -t 0:fd00 -c 0:swap_1 $MY_DISK_1
+# sgdisk -n 0:0:0 -t 0:fd00 -c 0:root_1 $MY_DISK_1
+```
+
+– If the drive that you will be using for the second half of the mirror in step 12 is smaller than this drive, then you will need to adjust down the size of the last partition so that the total size of all the partitions is not greater than the size of your second drive.
+– A few of the commands in this guide are prefixed with a test for the existence of an _efivars_ directory. This is necessary because those commands are slightly different depending on whether your computer is BIOS-based or UEFI-based.
+
+ 2. **Use** [**mdadm**][14] **to create RAID devices that use the new partitions to store their data** :
+
+```
+ # mdadm --create /dev/md/boot --homehost=any --metadata=1.0 --level=1 --raid-devices=2 /dev/disk/by-partlabel/boot_1 missing
+# mdadm --create /dev/md/swap --homehost=any --metadata=1.0 --level=1 --raid-devices=2 /dev/disk/by-partlabel/swap_1 missing
+# mdadm --create /dev/md/root --homehost=any --metadata=1.0 --level=1 --raid-devices=2 /dev/disk/by-partlabel/root_1 missing
+
+# cat << END > /etc/mdadm.conf
+MAILADDR root
+AUTO +all
+DEVICE partitions
+END
+
+# mdadm --detail --scan >> /etc/mdadm.conf
+```
+
+– The _missing_ parameter tells mdadm to create an array with a missing member. You will add the other half of the mirror in step 14.
+– You should configure [sendmail][15] so you will be notified if a drive fails.
+– You can configure [Evolution][16] to [monitor a local mail spool][17].
+
+ 3. **Use** [**dracut**][18] **to update the initramfs** :
+
+```
+# dracut -f --add mdraid --add-drivers xfs
+```
+
+– Dracut will include the /etc/mdadm.conf file you created in the previous section in your initramfs _unless_ you build your initramfs with the _hostonly_ option set to _no_. If you build your initramfs with the hostonly option set to no, then you should either manually include the /etc/mdadm.conf file, manually specify the UUID’s of the RAID arrays to assemble at boot time with the _rd.md.uuid_ kernel parameter, or specify the _rd.auto_ kernel parameter to have all RAID arrays automatically assembled and started at boot time. This guide will demonstrate the _rd.auto_ option since it is the most generic.
+
+ 4. **Format the RAID devices** :
+
+```
+ # mkfs -t vfat /dev/md/boot
+# mkswap /dev/md/swap
+# mkfs -t xfs /dev/md/root
+```
+
+– The new [Boot Loader Specification][19] states “if the OS is installed on a disk with GPT disk label, and no ESP partition exists yet, a new suitably sized (let’s say 500MB) ESP should be created and should be used as $BOOT” and “$BOOT must be a VFAT (16 or 32) file system”.
+
+ 5. **Reboot and set the _rd.auto_ , _rd.break_ and _single_ kernel parameters** :
+
+```
+# reboot
+```
+
+– You may need to [set your root password][20] before rebooting so that you can get into _single-user mode_ in step 7.
+– See “[Making Temporary Changes to a GRUB 2 Menu][21]” for directions on how to set kernel parameters on compters that use the GRUB 2 boot loader.
+
+ 6. **Use** [**the dracut shell**][18] **to copy the root file system** :
+
+```
+ # mkdir /newroot
+# mount /dev/md/root /newroot
+# shopt -s dotglob
+# cp -ax /sysroot/* /newroot
+# rm -rf /newroot/boot/*
+# umount /newroot
+# exit
+```
+
+– The _dotglob_ flag is set for this bash session so that the [wildcard character][22] will match hidden files.
+– Files are removed from the _boot_ directory because they will be copied to a separate partition in the next step.
+– This copy operation is being done from the dracut shell to insure that no processes are accessing the files while they are being copied.
+
+ 7. **Use _single-user mode_ to copy the non-root file systems** :
+
+```
+ # mkdir /newroot
+# mount /dev/md/root /newroot
+# mount /dev/md/boot /newroot/boot
+# shopt -s dotglob
+# cp -Lr /boot/* /newroot/boot
+# test -d /newroot/boot/efi/EFI && mv /newroot/boot/efi/EFI/* /newroot/boot/efi && rmdir /newroot/boot/efi/EFI
+# test -d /sys/firmware/efi/efivars && ln -sfr /newroot/boot/efi/fedora/grub.cfg /newroot/etc/grub2-efi.cfg
+# cp -ax /home/* /newroot/home
+# exit
+```
+
+– It is OK to run these commands in the dracut shell shown in the previous section instead of doing it from single-user mode. I’ve demonstrated using single-user mode to avoid having to explain how to mount the non-root partitions from the dracut shell.
+– The parameters being past to the _cp_ command for the _boot_ directory are a little different because the VFAT file system doesn’t support symbolic links or Unix-style file permissions.
+– In rare cases, the _rd.auto_ parameter is known to cause LVM to fail to assemble due to a [race condition][23]. If you see errors about your _swap_ or _home_ partition failing to mount when entering single-user mode, simply try again by repeating step 5 but omiting the _rd.break_ paramenter so that you will go directly to single-user mode.
+
+ 8. **Update _fstab_ on the new drive** :
+
+```
+ # cat << END > /newroot/etc/fstab
+/dev/md/root / xfs defaults 0 0
+/dev/md/boot /boot vfat defaults 0 0
+/dev/md/swap swap swap defaults 0 0
+END
+```
+
+ 9. **Configure the boot loader on the new drive** :
+
+```
+ # NEW_GRUB_CMDLINE_LINUX=$(cat /etc/default/grub | sed -n 's/^GRUB_CMDLINE_LINUX="\(.*\)"/\1/ p')
+# NEW_GRUB_CMDLINE_LINUX=${NEW_GRUB_CMDLINE_LINUX//rd.lvm.*([^ ])}
+# NEW_GRUB_CMDLINE_LINUX=${NEW_GRUB_CMDLINE_LINUX//resume=*([^ ])}
+# NEW_GRUB_CMDLINE_LINUX+=" selinux=0 rd.auto"
+# sed -i "/^GRUB_CMDLINE_LINUX=/s/=.*/=\"$NEW_GRUB_CMDLINE_LINUX\"/" /newroot/etc/default/grub
+```
+
+– You can re-enable selinux after this procedure is complete. But you will have to [relabel your file system][24] first.
+
+ 10. **Install the boot loader on the new drive** :
+
+```
+ # sed -i '/^GRUB_DISABLE_OS_PROBER=.*/d' /newroot/etc/default/grub
+# echo "GRUB_DISABLE_OS_PROBER=true" >> /newroot/etc/default/grub
+# MY_DISK_1=$(mdadm --detail /dev/md/boot | grep active | grep -m 1 -o "/dev/sd.")
+# for i in dev dev/pts proc sys run; do mount -o bind /$i /newroot/$i; done
+# chroot /newroot env MY_DISK_1=$MY_DISK_1 bash --login
+# test -d /sys/firmware/efi/efivars || MY_GRUB_DIR=/boot/grub2
+# test -d /sys/firmware/efi/efivars && MY_GRUB_DIR=$(find /boot/efi -type d -name 'fedora' -print -quit)
+# test -e /usr/sbin/grub2-switch-to-blscfg && grub2-switch-to-blscfg --grub-directory=$MY_GRUB_DIR
+# grub2-mkconfig -o $MY_GRUB_DIR/grub.cfg \;
+# test -d /sys/firmware/efi/efivars && test /boot/grub2/grubenv -nt $MY_GRUB_DIR/grubenv && cp /boot/grub2/grubenv $MY_GRUB_DIR/grubenv
+# test -d /sys/firmware/efi/efivars || grub2-install "$MY_DISK_1"
+# logout
+# for i in run sys proc dev/pts dev; do umount /newroot/$i; done
+# test -d /sys/firmware/efi/efivars && efibootmgr -c -d "$MY_DISK_1" -p 1 -l "$(find /newroot/boot -name shimx64.efi -printf '/%P\n' -quit | sed 's!/!\\!g')" -L "Fedora RAID Disk 1"
+```
+
+– The _grub2-switch-to-blscfg_ command is optional. It is only supported on Fedora 29+.
+– The _cp_ command above should not be necessary, but there appears to be a bug in the current version of grub which causes it to write to $BOOT/grub2/grubenv instead of $BOOT/efi/fedora/grubenv on UEFI systems.
+– You can use the following command to verify the contents of the _grub.cfg_ file right after running the _grub2-mkconfig_ command above:
+
+```
+# sed -n '/BEGIN .*10_linux/,/END .*10_linux/ p' $MY_GRUB_DIR/grub.cfg
+```
+
+– You should see references to _mdraid_ and _mduuid_ in the output from the above command if the RAID array was detected properly.
+
+ 11. **Boot off of the new drive** :
+
+```
+# reboot
+```
+
+– How to select the new drive is system-dependent. It usually requires pressing one of the **F12** , **F10** , **Esc** or **Del** keys when you hear the [System OK BIOS beep code][25].
+– On UEFI systems the boot loader on the new drive should be labeled “Fedora RAID Disk 1”.
+
+ 12. **Remove all the volume groups and partitions from your old drive** :
+
+```
+ # MY_DISK_2=/dev/sda
+# MY_VOLUMES=$(pvs | grep $MY_DISK_2 | awk '{print $2}' | tr "\n" " ")
+# test -n "$MY_VOLUMES" && vgremove $MY_VOLUMES
+# sgdisk --zap-all $MY_DISK_2
+```
+
+– **WARNING** : You want to make certain that everything is working properly on your new drive before you do this. A good way to verify that your old drive is no longer being used is to try booting your computer once without the old drive connected.
+– You can add another new drive to your computer instead of erasing your old one if you prefer.
+
+ 13. **Create new partitions on your old drive to match the ones on your new drive** :
+
+```
+ # test -d /sys/firmware/efi/efivars || sgdisk -n 0:0:+1MiB -t 0:ef02 -c 0:grub_2 $MY_DISK_2
+# sgdisk -n 0:0:+1GiB -t 0:ea00 -c 0:boot_2 $MY_DISK_2
+# sgdisk -n 0:0:+4GiB -t 0:fd00 -c 0:swap_2 $MY_DISK_2
+# sgdisk -n 0:0:0 -t 0:fd00 -c 0:root_2 $MY_DISK_2
+```
+
+– It is important that the partitions match in size and type. I prefer to use the _parted_ command to display the partition table because it supports setting the display unit:
+
+```
+ # parted /dev/sda unit MiB print
+# parted /dev/sdb unit MiB print
+```
+
+ 14. **Use mdadm to add the new partitions to the RAID devices** :
+
+```
+ # mdadm --manage /dev/md/boot --add /dev/disk/by-partlabel/boot_2
+# mdadm --manage /dev/md/swap --add /dev/disk/by-partlabel/swap_2
+# mdadm --manage /dev/md/root --add /dev/disk/by-partlabel/root_2
+```
+
+ 15. **Install the boot loader on your old drive** :
+
+```
+ # test -d /sys/firmware/efi/efivars || grub2-install "$MY_DISK_2"
+# test -d /sys/firmware/efi/efivars && efibootmgr -c -d "$MY_DISK_2" -p 1 -l "$(find /boot -name shimx64.efi -printf "/%P\n" -quit | sed 's!/!\\!g')" -L "Fedora RAID Disk 2"
+```
+
+ 16. **Use mdadm to test that email notifications are working** :
+
+```
+# mdadm --monitor --scan --oneshot --test
+```
+
+
+
+
+As soon as your drives have finished synchronizing, you should be able to select either drive when restarting your computer and you will receive the same live-mirrored operating system. If either drive fails, mdmonitor will send an email notification. Recovering from a drive failure is now simply a matter of swapping out the bad drive with a new one and running a few _sgdisk_ and _mdadm_ commands to re-create the mirrors (steps 13 through 15). You will no longer have to worry about losing any data if a drive fails!
+
+### Video Demonstrations
+
+Converting a UEFI PC to RAID1
+
+Converting a BIOS PC to RAID1
+
+ * TIP: Set the the quality to 720p on the above videos for best viewing.
+
+
+
+--------------------------------------------------------------------------------
+
+via: https://fedoramagazine.org/mirror-your-system-drive-using-software-raid/
+
+作者:[Gregory Bartholomew][a]
+选题:[lujun9972][b]
+译者:[译者ID](https://github.com/译者ID)
+校对:[校对者ID](https://github.com/校对者ID)
+
+本文由 [LCTT](https://github.com/LCTT/TranslateProject) 原创编译,[Linux中国](https://linux.cn/) 荣誉推出
+
+[a]: https://fedoramagazine.org/author/glb/
+[b]: https://github.com/lujun9972
+[1]: https://fedoramagazine.org/wp-content/uploads/2019/05/raid_mirroring-816x345.jpg
+[2]: https://en.wikipedia.org/wiki/Disk_mirroring
+[3]: https://en.wikipedia.org/wiki/Disk_mirroring#Additional_benefits
+[4]: https://en.wikipedia.org/wiki/Bottleneck_(software)
+[5]: https://en.wikipedia.org/wiki/Data_corruption
+[6]: https://en.wikipedia.org/wiki/Data_degradation
+[7]: https://en.wikipedia.org/wiki/Journaling_file_system
+[8]: https://www.quora.com/What-is-the-difference-between-a-journaling-vs-a-log-structured-file-system
+[9]: https://en.wikipedia.org/wiki/File_verification
+[10]: https://en.wikipedia.org/wiki/ZFS#Summary_of_key_differentiating_features
+[11]: https://en.wikipedia.org/wiki/Snapshot_(computer_storage)#File_systems
+[12]: https://en.wikipedia.org/wiki/Business_continuance_volume
+[13]: https://fedoramagazine.org/managing-partitions-with-sgdisk/
+[14]: https://fedoramagazine.org/managing-raid-arrays-with-mdadm/
+[15]: https://fedoraproject.org/wiki/QA:Testcase_Sendmail
+[16]: https://en.wikipedia.org/wiki/Evolution_(software)
+[17]: https://dotancohen.com/howto/root_email.html
+[18]: https://fedoramagazine.org/initramfs-dracut-and-the-dracut-emergency-shell/
+[19]: https://systemd.io/BOOT_LOADER_SPECIFICATION#technical-details
+[20]: https://docs.fedoraproject.org/en-US/Fedora/26/html/System_Administrators_Guide/sec-Changing_and_Resetting_the_Root_Password.html
+[21]: https://docs.fedoraproject.org/en-US/fedora/rawhide/system-administrators-guide/kernel-module-driver-configuration/Working_with_the_GRUB_2_Boot_Loader/#sec-Making_Temporary_Changes_to_a_GRUB_2_Menu
+[22]: https://en.wikipedia.org/wiki/Wildcard_character#File_and_directory_patterns
+[23]: https://en.wikipedia.org/wiki/Race_condition
+[24]: https://wiki.centos.org/HowTos/SELinux#head-867ca18a09f3103705cdb04b7d2581b69cd74c55
+[25]: https://en.wikipedia.org/wiki/Power-on_self-test#Original_IBM_POST_beep_codes
diff --git a/sources/tech/20190503 SuiteCRM- An Open Source CRM Takes Aim At Salesforce.md b/sources/tech/20190503 SuiteCRM- An Open Source CRM Takes Aim At Salesforce.md
new file mode 100644
index 0000000000..63802d4976
--- /dev/null
+++ b/sources/tech/20190503 SuiteCRM- An Open Source CRM Takes Aim At Salesforce.md
@@ -0,0 +1,105 @@
+[#]: collector: (lujun9972)
+[#]: translator: ( )
+[#]: reviewer: ( )
+[#]: publisher: ( )
+[#]: url: ( )
+[#]: subject: (SuiteCRM: An Open Source CRM Takes Aim At Salesforce)
+[#]: via: (https://itsfoss.com/suitecrm-ondemand/)
+[#]: author: (Ankush Das https://itsfoss.com/author/ankush/)
+
+SuiteCRM: An Open Source CRM Takes Aim At Salesforce
+======
+
+SuiteCRM is one of the most popular open source CRM (Customer Relationship Management) software available. With its unique-priced managed CRM hosting service, SuiteCRM is aiming to challenge enterprise CRMs like Salesforce.
+
+### SuiteCRM: An Open Source CRM Software
+
+CRM stands for Customer Relationship Management. It is used by businesses to manage the interaction with customers, keep track of services, supplies and other things that help the business manage their customers.
+
+![][1]
+
+[SuiteCRM][2] came into existence after the hugely popular [SugarCRM][3] decided to stop developing its open source version. The open source version of SugarCRM was then forked into SuiteCRM by UK-based [SalesAgility][4] team.
+
+In just a couple of years, SuiteCRM became immensely popular and started to be considered the best open source CRM software out there. You can gauge its popularity from the fact that it’s nearing a million download and it has over 100,000 community members. There are around 4 million SuiteCRM users worldwide (a CRM software usually has more than one user) and it is available in several languages. It’s even used by National Health Service ([NHS][5]) in UK.
+
+Since SuiteCRM is a free and open source software, you are free to download it and deploy it on your cloud server such as [UpCloud][6] (we at It’s FOSS use it), [DigitalOcean][7], [AWS][8] or any Linux server of our own.
+
+But configuring the software, deploying it and managing it a tiresome job and requires certain skill level or a the services of a sysadmin. This is why business oriented open source software provide a hosted version of their software.
+
+This enables you to enjoy the open source software without the additional headache and the team behind the software has a way to generate revenue and continue the development of their software.
+
+### Suite:OnDemand – Cost effective managed hosting of SuiteCRM
+
+So, recently, [SalesAgility][4] – the creators/maintainers of SuiteCRM, decided to challenge [Salesforce][9] and other enterprise CRMs by introducing [Suite:OnDemand][10] , a hosted version of SuiteCRM.
+
+[][11]
+
+Suggested read Papyrus: An Open Source Note Manager
+
+Normally, you will observe pricing plans on the basis of number of users. But, with SuiteCRM’s OnDemand cloud hosting plans, they are trying to give businesses an affordable solution on a “per-server” basis instead of paying for every user you add.
+
+In other words, they want you to pay extra only for advanced features, not for more users.
+
+Here’s what SalesAgility mentioned in their [press release][12]:
+
+> Unlike Salesforce and other enterprise CRM vendors, the practice of pricing per user has been abandoned in favour of per-server hosting packages all of which will support unlimited users. In addition, there’s no increase in cost for access to advanced features. With Suite:OnDemand every feature and benefit is available with each hosting package.
+
+Of course, unlimited users does not mean that you will have to abuse the term. So, there’s a recommended number of users for every hosting plan you opt for.
+
+![Suitecrm Hosting][13]
+
+The CEO of SalesAgility also had to describe their goals for this step:
+
+“ _We want SuiteCRM to be available to all businesses and to all users within a business,_ ”said **Dale Murray CEO** of **SalesAgility**.
+
+In addition to that, they also mentioned that they want to revolutionize the way enterprise-class CRM is being currently offered in order to make it more accessible to businesses and organizations:
+
+> “Many organisations do not have the experience to run and support our product on-premise or it is not part of their technology strategy to do so. With Suite:OnDemand we are providing our customers with a quick and easy solution to access all the features of SuiteCRM without a per user cost. We’re also saying to Salesforce that enterprise-class CRM can be delivered, enhanced, maintained and supported without charging mouth-wateringly expensive monthly fees. Our aim is to transform the CRM market to enable users to make CRM pervasive within their organisations.”
+>
+> Dale Murray, CEO of SalesAgility
+
+### Why is this a big deal?
+
+This is a huge relief for small business owners and startups because other CRMs like Saleforce and SugarCRM charge $30-$40 per month per user. If you have 10 members in your team, this will increase the cost to $300-$400 per month.
+
+[][14]
+
+Suggested read Winds Beautifully Combines Feed Reader and Podcast Player in One Single App
+
+This is also a good news for the open source community that we will have an affordable alternative to Salesforce.
+
+In addition to this, SuiteCRM is fully open source meaning there are no license fees or vendor lock-in – as they mention. You are always free to use it on your own.
+
+It is interesting to see different strategies and solutions being applied for an open source CRM software to take an aim at Salesforce directly.
+
+What do you think? Let us know your thoughts in the comments below.
+
+_With inputs from Abhishek Prakash._
+
+--------------------------------------------------------------------------------
+
+via: https://itsfoss.com/suitecrm-ondemand/
+
+作者:[Ankush Das][a]
+选题:[lujun9972][b]
+译者:[译者ID](https://github.com/译者ID)
+校对:[校对者ID](https://github.com/校对者ID)
+
+本文由 [LCTT](https://github.com/LCTT/TranslateProject) 原创编译,[Linux中国](https://linux.cn/) 荣誉推出
+
+[a]: https://itsfoss.com/author/ankush/
+[b]: https://github.com/lujun9972
+[1]: https://itsfoss.com/wp-content/uploads/2019/05/suite-crm-800x450.png
+[2]: https://suitecrm.com/
+[3]: https://www.sugarcrm.com/
+[4]: https://salesagility.com/
+[5]: https://www.nhs.uk/
+[6]: https://www.upcloud.com/register/?promo=itsfoss
+[7]: https://m.do.co/c/d58840562553
+[8]: https://aws.amazon.com/
+[9]: https://www.salesforce.com
+[10]: https://suitecrm.com/suiteondemand/
+[11]: https://itsfoss.com/papyrus-open-source-note-manager/
+[12]: https://suitecrm.com/sod-pr/
+[13]: https://itsfoss.com/wp-content/uploads/2019/05/suitecrm-hosting-800x457.jpg
+[14]: https://itsfoss.com/winds-podcast-feedreader/
diff --git a/sources/tech/20190503 Tutanota Launches New Encrypted Tool to Support Press Freedom.md b/sources/tech/20190503 Tutanota Launches New Encrypted Tool to Support Press Freedom.md
new file mode 100644
index 0000000000..692b4ecba8
--- /dev/null
+++ b/sources/tech/20190503 Tutanota Launches New Encrypted Tool to Support Press Freedom.md
@@ -0,0 +1,85 @@
+[#]: collector: (lujun9972)
+[#]: translator: ( )
+[#]: reviewer: ( )
+[#]: publisher: ( )
+[#]: url: ( )
+[#]: subject: (Tutanota Launches New Encrypted Tool to Support Press Freedom)
+[#]: via: (https://itsfoss.com/tutanota-secure-connect/)
+[#]: author: (John Paul https://itsfoss.com/author/john/)
+
+Tutanota Launches New Encrypted Tool to Support Press Freedom
+======
+
+A secure email provider has announced the release of a new product designed to help whistleblowers get their information to the media. The tool is free for journalists.
+
+### Tutanota helps you protect your privacy
+
+![][1]
+
+[Tutanota][2] is a German-based company that provides “world’s most secure email service, easy to use and private by design.” They offer end-to-end encryption for their [secure email service][3]. Recently Tutanota announced a [desktop app for their email service][4].
+
+They also make use of two-factor authentication and [open source the code][5] that they use.
+
+While you can get an account for free, you don’t have to worry about your information being sold or seeing ads. Tutanota makes money by charging for extra features and storage. They also offer solutions for non-profit organizations.
+
+Tutanota has launched a new service to further help journalists, social activists and whistleblowers in communicating securely.
+
+[][6]
+
+Suggested read Purism's New Offering is a Dream Come True for Privacy Concerned People
+
+### Secure Connect: An encrypted form for websites
+
+![][7]
+
+Tutanota has released a new piece of software named Secure Connect. Secure Connect is “an open source encrypted contact form for news sites”. The goal of the project is to create a way so that “whistleblowers can get in touch with journalists securely”. Tutanota picked the right day because May 3rd is the [Day of Press Freedom][8].
+
+According to Tutanota, Secure Connect is designed to be easily added to websites, but can also work on any blog to ensure access by smaller news agencies. A whistleblower would access Secure Connect app on a news site, preferably using Tor, and type in any information that they want to bring to light. The whistleblower would also be able to upload files. Once they submit the information, Secure Connect will assign a random address and password, “which lets the whistleblower re-access his sent message at a later stage and check for replies from the news site.”
+
+![Secure Connect Encrypted Contact Form][9]
+
+While Tutanota will be offering Secure Connect to journalists for free, they know that someone will have to foot the bill. They plan to pay for further development of the project by selling it to businesses, such as “lawyers, financial institutions, medical institutions, educational institutions, and the authorities”. Non-journalists would have to pay €24 per month.
+
+You can see a demo of Secure Connect, by clicking [here][10]. If you are a journalist interested in adding Secure Connect to your website or blog, you can contact them at [[email protected]][11] Be sure to include a link to your website.
+
+[][12]
+
+Suggested read 8 Privacy Oriented Alternative Search Engines To Google in 2019
+
+### Final Thoughts on Secure Connect
+
+I have read repeatedly about whistleblowers whose identities were accidentally exposed, either by themselves or others. Tutanota’s project looks like it would remove that possibility by making it impossible for others to discover their identity. It also gives both parties an easy way to exchange information without having to worry about encryption or PGP keys.
+
+I understand that it’s not the same as [Firefox Send][13], another encrypted file sharing program from Mozilla. The only question I have is whose servers will the whistleblowers’ information be sitting on?
+
+Do you think that Tutanota’s Secure Connect will be a boon for whistleblowers and activists? Please let us know in the comments below.
+
+If you found this article interesting, please take a minute to share it on social media, Hacker News or [Reddit][14].
+
+--------------------------------------------------------------------------------
+
+via: https://itsfoss.com/tutanota-secure-connect/
+
+作者:[John Paul][a]
+选题:[lujun9972][b]
+译者:[译者ID](https://github.com/译者ID)
+校对:[校对者ID](https://github.com/校对者ID)
+
+本文由 [LCTT](https://github.com/LCTT/TranslateProject) 原创编译,[Linux中国](https://linux.cn/) 荣誉推出
+
+[a]: https://itsfoss.com/author/john/
+[b]: https://github.com/lujun9972
+[1]: https://itsfoss.com/wp-content/uploads/2018/02/tutanota-featured-800x450.png
+[2]: https://tutanota.com/
+[3]: https://itsfoss.com/tutanota-review/
+[4]: https://itsfoss.com/tutanota-desktop/
+[5]: https://tutanota.com/blog/posts/open-source-email
+[6]: https://itsfoss.com/librem-one/
+[7]: https://itsfoss.com/wp-content/uploads/2019/05/secure-communication.jpg
+[8]: https://en.wikipedia.org/wiki/World_Press_Freedom_Day
+[9]: https://itsfoss.com/wp-content/uploads/2019/05/secure-connect-encrypted-contact-form.png
+[10]: https://secureconnect.tutao.de/contactform/demo
+[11]: /cdn-cgi/l/email-protection
+[12]: https://itsfoss.com/privacy-search-engines/
+[13]: https://itsfoss.com/firefox-send/
+[14]: http://reddit.com/r/linuxusersgroup
diff --git a/sources/tech/20190504 May the fourth be with you- How Star Wars (and Star Trek) inspired real life tech.md b/sources/tech/20190504 May the fourth be with you- How Star Wars (and Star Trek) inspired real life tech.md
new file mode 100644
index 0000000000..a05f9a6b4f
--- /dev/null
+++ b/sources/tech/20190504 May the fourth be with you- How Star Wars (and Star Trek) inspired real life tech.md
@@ -0,0 +1,93 @@
+[#]: collector: (lujun9972)
+[#]: translator: ( )
+[#]: reviewer: ( )
+[#]: publisher: ( )
+[#]: url: ( )
+[#]: subject: (May the fourth be with you: How Star Wars (and Star Trek) inspired real life tech)
+[#]: via: (https://opensource.com/article/19/5/may-the-fourth-star-wars-trek)
+[#]: author: (Jeff Macharyas https://opensource.com/users/jeffmacharyas)
+
+May the fourth be with you: How Star Wars (and Star Trek) inspired real life tech
+======
+The technologies may have been fictional, but these two acclaimed sci-fi
+series have inspired open source tech.
+![Triangulum galaxy, NASA][1]
+
+Conventional wisdom says you can either be a fan of _Star Trek_ or of _Star Wars_ , but mixing the two is like mixing matter and anti-matter. I'm not sure that's true, but even if the laws of physics cannot be changed, these two acclaimed sci-fi series have influenced the open source universe and created their own open source multi-verses.
+
+For example, fans have used the original _Star Trek_ as "source code" to create fan-made films, cartoons, and games. One of the more notable fan creations was the web series _Star Trek Continues_ , which faithfully adapted Gene Roddenberry's universe and redistributed it to the world.
+
+"Eventually we realized that there is no more profound way in which people could express what _Star Trek_ has meant to them than by creating their own very personal _Star Trek_ things," [Roddenberry said][2]. However, due to copyright restrictions, this "open source" channel [has since been curtailed][3].
+
+_Star Wars_ has a different approach to open sourcing its universe. [Jess Paguaga writes][4] on FanSided: "With a variety [of] fan film awards dating back to 2002, the _Star Wars_ brand has always supported and encouraged the creation of short films that help expand the universe of a galaxy far, far away."
+
+But, _Star Wars_ is not without its own copyright prime directives. In one case, a Darth Vader film by a YouTuber called Star Wars Theory has drawn a copyright claim from Disney. The claim does not stop production of the film, but diverts monetary gains from it, [reports James Richards][5] on FanSided.
+
+This could be one of the [Ferengi Rules of Acquisition][6], perhaps.
+
+But if you can't watch your favorite fan film, you can still get your [_Star Wars_ fix right in the Linux terminal][7] by entering:
+
+
+```
+`telnet towel.blinkenlights.nl`
+```
+
+And _Star Trek_ fans can also interact with the Federation with the original text-based video game from 1971. While a high-school senior, Mike Mayfield ported the game from punch cards to HP BASIC. If you'd like to go old school and battle Klingons, the source code is available at the [Code Project][8].
+
+### Real-life star tech
+
+Both _Star Wars_ and _Star Trek_ have inspired real-life technologies. Although those technologies were fictional, many have become the practical, open technology we use today. Some of them inspired technologies that are still in development now.
+
+In the early 1970s, Motorola engineer Martin Cooper was trying to beat AT&T at the car-phone game. He says he was watching Captain Kirk use a "communicator" on an episode of _Star Trek_ and had a eureka moment. His team went on to create the first portable cellular 800MHz phone prototype in 90 days.
+
+In _Star Wars_ , scout stormtroopers of the Galactic Empire rode the Aratech 74-Z Speeder Bike, and a real-life counterpart is the [Aero-X][9] being developed by California's Aerofex.
+
+Perhaps the most visible _Star Wars_ tech to enter our lives is droids. We first encountered R2-D2 back in the 1970s, but now we have droids vacuuming our carpets and mowing our lawns, from Roombas to the [Worx Landroid][10] lawnmower.
+
+And, in _Star Wars_ , Princess Leia appeared to Obi-Wan Kenobi as a hologram, and in Star Trek: Voyager, the ship's chief medical officer was an interactive hologram that could diagnose and treat patients. The technology to bring characters like these to "life" is still a ways off, but there are some interesting open source developments that hint of things to come. [OpenHolo][11], "an open source library containing algorithms and software implementations for holograms in various fields," is one such project.
+
+### Where's the beef?
+
+> "She handled… real meat… touched it, and cut it?" —Keiko O'Brien, Star Trek: The Next Generation
+
+In the _Star Trek_ universe, crew members get their meals by simply ordering a replicator to produce whatever food they desire. That could one day become a reality thanks to a concept created by two German students for an open source "meat-printer" they call the [Cultivator][12]. It would use bio-printing to produce something that appears to be meat; the user could even select its mineral and fat content. Perhaps with more collaboration and development, the Cultivator could become the replicator in tomorrow's kitchen!
+
+### The 501st
+
+Cosplayers, people from all walks of life who dress as their favorite characters, are the "open source embodiment" of their favorite universes. The [501st][13] [Legion][13] is an all-volunteer _Star Wars_ fan organization "formed for the express purpose of bringing together costume enthusiasts under a collective identity within which to operate," according to its charter.
+
+Jon Stallard, a member of Garrison Tyranus, the Central Virginia chapter of the 501st Legion says, "Everybody wanted to be something else when they were a kid, right? Whether it was Neil Armstrong, Batman, or the Six Million Dollar Man. Every backyard playdate was some kind of make-believe. The 501st lets us participate in our fan communities while contributing to the community at large."
+
+Are cosplayers really "open source characters"? Well, that depends. The copyright laws around cosplay and using unique props, costumes, and more are very complex, [writes Meredith Filak Rose][14] for _Public Knowledge_. "We're lucky to be living in a time where fandom generally enjoys a positive relationship with the creators whose work it admires," Rose concludes.
+
+So, it is safe to say that stormtroopers, Ferengi, Vulcans, and Yoda are all here to stay for a long, long time, near, and far, far away.
+
+Live long and prosper, you shall.
+
+--------------------------------------------------------------------------------
+
+via: https://opensource.com/article/19/5/may-the-fourth-star-wars-trek
+
+作者:[Jeff Macharyas ][a]
+选题:[lujun9972][b]
+译者:[译者ID](https://github.com/译者ID)
+校对:[校对者ID](https://github.com/校对者ID)
+
+本文由 [LCTT](https://github.com/LCTT/TranslateProject) 原创编译,[Linux中国](https://linux.cn/) 荣誉推出
+
+[a]: https://opensource.com/users/jeffmacharyas
+[b]: https://github.com/lujun9972
+[1]: https://opensource.com/sites/default/files/styles/image-full-size/public/lead-images/triangulum_galaxy_nasa_stars.jpg?itok=NdS19A7m
+[2]: https://fanlore.org/wiki/Gene_Roddenberry#His_Views_Regarding_Fanworks
+[3]: https://trekmovie.com/2016/06/23/cbs-and-paramount-release-fan-film-guidelines/
+[4]: https://dorksideoftheforce.com/2019/01/17/star-wars-fan-films/
+[5]: https://dorksideoftheforce.com/2019/01/16/disney-claims-copyright-star-wars-theory/
+[6]: https://en.wikipedia.org/wiki/Rules_of_Acquisition
+[7]: https://itsfoss.com/star-wars-linux/
+[8]: https://www.codeproject.com/Articles/28228/Star-Trek-1971-Text-Game
+[9]: https://www.livescience.com/58943-real-life-star-wars-technology.html
+[10]: https://www.digitaltrends.com/cool-tech/best-robot-lawnmowers/
+[11]: http://openholo.org/
+[12]: https://www.pastemagazine.com/articles/2016/05/the-future-is-vegan-according-to-star-trek.html
+[13]: https://www.501st.com/
+[14]: https://www.publicknowledge.org/news-blog/blogs/copyright-and-cosplay-working-with-an-awkward-fit
diff --git a/sources/tech/20190505 -Review- Void Linux, a Linux BSD Hybrid.md b/sources/tech/20190505 -Review- Void Linux, a Linux BSD Hybrid.md
new file mode 100644
index 0000000000..cc8a660252
--- /dev/null
+++ b/sources/tech/20190505 -Review- Void Linux, a Linux BSD Hybrid.md
@@ -0,0 +1,136 @@
+[#]: collector: (lujun9972)
+[#]: translator: ( )
+[#]: reviewer: ( )
+[#]: publisher: ( )
+[#]: url: ( )
+[#]: subject: ([Review] Void Linux, a Linux BSD Hybrid)
+[#]: via: (https://itsfoss.com/void-linux/)
+[#]: author: (John Paul https://itsfoss.com/author/john/)
+
+[Review] Void Linux, a Linux BSD Hybrid
+======
+
+There are distros that follow the crowd and there are others that try to make their own path through the tall weed. Today, we’ll be looking at a small distro that looks to challenge how a distro should work. We’ll be looking at Void Linux.
+
+### What is Void Linux?
+
+[Void Linux][1] is a “general purpose operating system, based on the monolithic Linux kernel. Its package system allows you to quickly install, update and remove software; software is provided in binary packages or can be built directly from sources with the help of the XBPS source packages collection.”
+
+![Void Linux Neofetch][2]
+
+Like Solus, Void Linux is written from scratch and does not depend on any other operating system. It is a rolling release. Unlike the majority of Linux distros, Void does not use [systemd][3]. Instead, it uses [runit][4]. Another thing that separates Void from the rest of Linux distros is the fact that they use LibreSSL instead of OpenSSL. Void also offers support for the [musl C library][5]. In fact, when you download a .iso file, you can choose between `glibc` and `musl`.
+
+The homegrown package manager that Void uses is named X Binary Package System (or xbps). According to the [Void wiki][6], xbps has the following features:
+
+ * Supports multiple local and remote repositories (HTTP/HTTPS/FTP).
+ * RSA signed remote repositories
+ * SHA256 hashes for package metadata, files, and binary packages
+ * Supports package states (ala dpkg) to mitigate broken package * installs/updates
+ * Ability to resume partial package install/updates
+ * Ability to unpack only files that have been modified in * package updates
+ * Ability to use virtual packages
+ * Ability to check for incompatible shared libraries in reverse dependencies
+ * Ability to replace packages
+ * Ability to put packages on hold (to never update them)
+ * Ability to preserve/update configuration files
+ * Ability to force reinstallation of any installed package
+ * Ability to downgrade any installed package
+ * Ability to execute pre/post install/remove/update scriptlets
+ * Ability to check package integrity: missing files, hashes, missing or unresolved (reverse)dependencies, dangling or modified symlinks, etc.
+
+
+
+#### System Requirements
+
+According to the [Void Linux download page][7], the system requirements differ based on the architecture you choose. 64-bit images require “EM64T CPU, 96MB RAM, 350MB disk, Ethernet/WiFi for network installation”. 32-bit images require “Pentium 4 CPU (SSE2), 96MB RAM, 350MB disk, Ethernet / WiFi for network installation”. The [Void Linux handbook][8] recommends 700 MB for storage and also notes that “Flavor installations require more resources. How much more depends on the flavor.”
+
+Void also supports ARM devices. You can download [ready to boot images][9] for Raspberry Pi and several other [Raspberry Pi alternatives][10].
+
+[][11]
+
+Suggested read NomadBSD, a BSD for the Road
+
+### Void Linux Installation
+
+NOTE: you can either install [Void Linux download page][7] via a live image or use a net installer. I used a live image.
+
+I was able to successfully install Void Linux on my Dell Latitude D630. This laptop has an Intel Centrino Duo Core processor running at 2.00 GHz, NVIDIA Quadro NVS 135M graphics chip, and 4 GB of RAM.
+
+![Void Linux Mate][12]
+
+After I `dd`ed the 800 MB Void Linux MATE image to my thumb drive and inserted it, I booted my computer. I was very quickly presented with a vanilla MATE desktop. To start installing Void, I opened up a terminal and typed `sudo void-installer`. After using the default password `voidlinux`, the installer started. The installer reminded me a little bit of the terminal Debian installer, but it was laid out more like FreeBSD. It was divided into keyboard, network, source, hostname, locale, timezone, root password, user account, bootloader, partition, and filesystems sections.
+
+Most of the sections where self-explanatory. In the source section, you could choose whether to install the packages from the local image or grab them from the web. I chose local because I did not want to eat up bandwidth or take longer than I had to. The partition and filesystems sections are usually handled automatically by most installers, but not on Void. In this case, the first section allows you to use `cfdisk` to create partitions and the second allows to specify what filesystems will be used in those partitions. I followed the partition layout on [this page][13].
+
+If you install Void Linux from the local image, you definitely need to update your system. The [Void wiki][14] recommends running `xbps-install -Suv` until there are no more updates to install. It would probably be a good idea to reboot between batches of updates.
+
+### Experience with Void Linux
+
+So far in my Linux journey, Void Linux has been by far the most difficult. It feels more like I’m [using a BSD than a Linux distro][15]. (I guess that should not be surprising since Void was created by a former [NetBSD][16] developer who wanted to experiment with his own package manager.) The steps in the command line installer are closer to that of [FreeBSD][17] than Debian.
+
+Once Void was installed and updated, I went to work installing apps. Unfortunately, I ran into an issue with missing applications. Most of these applications come preinstalled on other distros. I had to install wget, unzip, git, nano, LibreOffice to name just a few.
+
+Void does not come with a graphical package manager. There are three unofficial frontends for the xbps package manager and [one is based on qt][18]. I ran into issues getting one of the Bash-based tools to work. It hadn’t been updated in 4-5 years.
+
+![Octoxbps][19]
+
+The xbps package manager is kinda interesting. It downloads the package and its signature to verify it. You can see the [terminal print out][20] from when I installed Mcomix. Xbps does not use the normal naming convention used in most package managers (ie `apt install` or `pacman -R`), instead, it uses `xbps-install`, `xbps-query`, `xbps-remove`. Luckily, the Void wiki had a [page][21] to show what xbps command relates to apt or dnf commands.
+
+[][22]
+
+Suggested read How To Solve: error: no such partition grub rescue in Ubuntu Linux
+
+The main repo for Void is located in Germany, so I decided to switch to a more local server to ease the burden on that server and to download packages quicker. Switching to a local mirror took a couple of tries because the documentation was not very clear. Documentation for Void is located in two different places: the [wiki][23] and the [handbook][24]. For me, the wiki’s [explanation][25] was confusing and I ran into issues. So, I searched for an answer on DuckDuckGo. From there I stumbled upon the [handbook’s instructions][26], which were much clearer. (The handbook is not linked on the Void Linux website and I had to stumble across it via search.)
+
+One of the nice things about Void is the speed of the system once everything was installed. It had the quickest boot time I have ever encountered. Overall, the system was very responsive. I did not run into any system crashes.
+
+### Final Thoughts
+
+Void Linux took more work to get to a useable state than any other distro I have tried. Even the BSDs I tried felt more polished than Void. I think the tagline “General purpose Linux” is misleading. It should be “Linux with hackers and tinkerers in mind”. Personally, I prefer using distros that are ready for me to use after installing. While it is an interesting combination of Linux and BSD ideas, I don’t think I’ll add Void to my short list of go-to distros.
+
+If you like tinkering with your Linux system or like building it from scratch, give [Void Linux][7] a try.
+
+Have you ever used Void Linux? What is your favorite Debian-based distro? Please let us know in the comments below.
+
+If you found this article interesting, please take a minute to share it on social media, Hacker News or [Reddit][27].
+
+--------------------------------------------------------------------------------
+
+via: https://itsfoss.com/void-linux/
+
+作者:[John Paul][a]
+选题:[lujun9972][b]
+译者:[译者ID](https://github.com/译者ID)
+校对:[校对者ID](https://github.com/校对者ID)
+
+本文由 [LCTT](https://github.com/LCTT/TranslateProject) 原创编译,[Linux中国](https://linux.cn/) 荣誉推出
+
+[a]: https://itsfoss.com/author/john/
+[b]: https://github.com/lujun9972
+[1]: https://voidlinux.org/
+[2]: https://i2.wp.com/itsfoss.com/wp-content/uploads/2019/04/Void-Linux-Neofetch.png?resize=800%2C562&ssl=1
+[3]: https://en.wikipedia.org/wiki/Systemd
+[4]: http://smarden.org/runit/
+[5]: https://www.musl-libc.org/
+[6]: https://wiki.voidlinux.org/XBPS
+[7]: https://voidlinux.org/download/
+[8]: https://docs.voidlinux.org/installation/base-requirements.html
+[9]: https://voidlinux.org/download/#download-ready-to-boot-images-for-arm
+[10]: https://itsfoss.com/raspberry-pi-alternatives/
+[11]: https://itsfoss.com/nomadbsd/
+[12]: https://i0.wp.com/itsfoss.com/wp-content/uploads/2019/04/Void-Linux-Mate.png?resize=800%2C640&ssl=1
+[13]: https://wiki.voidlinux.org/Disks#Filesystems
+[14]: https://wiki.voidlinux.org/Post_Installation#Updates
+[15]: https://itsfoss.com/why-use-bsd/
+[16]: https://itsfoss.com/netbsd-8-release/
+[17]: https://www.freebsd.org/
+[18]: https://github.com/aarnt/octoxbps
+[19]: https://i1.wp.com/itsfoss.com/wp-content/uploads/2019/04/OctoXBPS.jpg?resize=800%2C534&ssl=1
+[20]: https://pastebin.com/g31n1bFT
+[21]: https://wiki.voidlinux.org/Rosetta_stone
+[22]: https://itsfoss.com/solve-error-partition-grub-rescue-ubuntu-linux/
+[23]: https://wiki.voidlinux.org/
+[24]: https://docs.voidlinux.org/
+[25]: https://wiki.voidlinux.org/XBPS#Official_Repositories
+[26]: https://docs.voidlinux.org/xbps/repositories/mirrors/changing.html
+[27]: http://reddit.com/r/linuxusersgroup
diff --git a/sources/tech/20190505 Blockchain 2.0 - An Introduction To Hyperledger Project (HLP) -Part 8.md b/sources/tech/20190505 Blockchain 2.0 - An Introduction To Hyperledger Project (HLP) -Part 8.md
new file mode 100644
index 0000000000..bb1d187ea4
--- /dev/null
+++ b/sources/tech/20190505 Blockchain 2.0 - An Introduction To Hyperledger Project (HLP) -Part 8.md
@@ -0,0 +1,88 @@
+[#]: collector: (lujun9972)
+[#]: translator: ( )
+[#]: reviewer: ( )
+[#]: publisher: ( )
+[#]: url: ( )
+[#]: subject: (Blockchain 2.0 – An Introduction To Hyperledger Project (HLP) [Part 8])
+[#]: via: (https://www.ostechnix.com/blockchain-2-0-an-introduction-to-hyperledger-project-hlp/)
+[#]: author: (editor https://www.ostechnix.com/author/editor/)
+
+Blockchain 2.0 – An Introduction To Hyperledger Project (HLP) [Part 8]
+======
+
+![Introduction To Hyperledger Project][1]
+
+Once a new technology platform reaches a threshold level of popularity in terms of active development and commercial interests, major global companies and smaller start-ups alike rush to catch a slice of the pie. **Linux** was one such platform back in the day. Once the ubiquity of its applications was realized individuals, firms, and institutions started displaying their interest in it and by 2000 the **Linux foundation** was formed.
+
+The Linux foundation aims to standardize and develop Linux as a platform by sponsoring their development team. The Linux Foundation is a non-profit organization that is supported by software and IT behemoths such as Microsoft, Oracle, Samsung, Cisco, IBM, Intel among others[1]. This is excluding the hundreds of individual developers who offer their services for the betterment of the platform. Over the years the Linux foundation has taken many projects under its roof. The **Hyperledger Project** is their fastest growing one till date.
+
+Such consortium led development have a lot of advantages when it comes to furthering tech into usable useful forms. Developing the standards, libraries and all the back-end protocols for large scale projects are expensive and resource intensive without a shred of income generating from it. Hence, it makes sense for companies to pool in their resources to develop the common “boring” parts by supporting such organizations and later upon completing work on these standard parts to simply plug & play and customize their products afterwards. Apart from the economics of the model, such collaborative efforts also yield standards allowing for easier use and integration into aspiring products and services.
+
+Other major innovations that were once or are currently being developed following the said consortium model include standards for WiFi (The Wi-Fi alliance), Mobile Telephony etc.
+
+### Introduction to Hyperledger Project (HLP)
+
+The Hyperledger project was launched in December 2015 by the Linux foundation as is currently among the fastest growing project they’ve incubated. It’s an umbrella organization for collaborative efforts into developing and advancing tools & standards for [**blockchain**][2] based distributed ledger technologies(DLT). Major industry players supporting the project include **IBM** , **Intel** and **SAP Ariba** among [**others**][3]. The HLP aims to create frameworks for individuals and companies to create shared as well as closed blockchains as required to further their own requirements. The design principles include a strong tilt toward developing a globally deployable, scalable, robust platform with a focus on privacy, and future auditability[2]. It is also important to note that most of the blockchains proposed and the frame.
+
+### Development goals and structure: Making it plug & play
+
+Although enterprise facing platforms exist from the likes of the Ethereum alliance, HLP is by definition business facing and supported by industry behemoths who contribute and further development in the many modules that come under the HLP banner. The HLP incubates projects in development after their induction into the cause and after finishing work on it and correcting the knick-knacks rolls it out for the public. Members of the Hyperledger project contribute their own work such as how IBM contributed their Fabric platform for collaborative development. The codebase is absorbed and developed in house by the group in the project and rolled out for all members equally for their use.
+
+Such processes make the modules in HLP highly flexible plug-in frameworks which will support rapid development and roll-outs in enterprise settings. Furthermore, other comparable platforms are open **permission-less blockchains** or rather **public chains** by default and even though it is possible to adapt them to specific applications, HLP modules support the feature natively.
+
+The differences and use cases of public & private blockchains are covered more [**here**][4] in this comparative primer on the same.
+
+The Hyperledger project’s mission is four-fold according to **Brian Behlendorf** , the executive director of the project.
+
+They are:
+
+ 1. To create an enterprise grade DLT framework and standards which anyone can port to suit their specific industrial or personal needs.
+ 2. To give rise to a robust open source community to aid the ecosystem.
+ 3. To promote and further participation of industry members of the said ecosystem such as member firms.
+ 4. To host a neutral unbiased infrastructure for the HLP community to gather and share updates and developments regarding the same.
+
+
+
+The original document can be accessed [**here**][5]****.
+
+### Structure of the HLP
+
+The **HLP consists of 12 projects** that are classified as independent modules, each usually structured and working independently to develop their module. These are first studied for their capabilities and viability before being incubated. Proposals for additions can be made by any member of the organization. After the project is incubated active development ensues after which it is rolled out. The interoperability between these modules are given a high priority, hence regular communication between these groups are maintained by the community. Currently 4 of these projects are categorized as active. The active tag implies these are ready for use but not ready for a major release yet. These 4 are arguably the most significant or rather fundamental modules to furthering the blockchain revolution. We’ll look at the individual modules and their functionalities at a later time in detail. However, a brief description of a the Hyperledger Fabric platform, arguably the most popular among them follows.
+
+### Hyperledger Fabric
+
+The **Hyperledger Fabric** [2] is a fully open-source, permissioned (non-public) blockchain-based DLT platform that is designed keeping enterprise uses in mind. The platform provides features and is structured to fit the enterprise environment. It is highly modular allowing its developers to choose from different consensus protocols, **chain code protocols ([smart contracts][6])** , or identity management systems etc., as they go along. **It is a permissioned blockchain based platform** that’s makes use of an identity management system, meaning participants will be aware of each other’s identities which is required in an enterprise setting. Fabric allows for smart contract ( _ **“chaincode”, is the term that the Hyperledger team uses**_ ) development in a variety of mainstream programming languages including **Java** , **Javascript** , **Go** etc. This allows institutions and enterprises to make use of their existing talent in the area without hiring or re-training developers to develop their own smart contracts. Fabric also uses an execute-order-validate system to handle smart contracts for better reliability compared to the standard order-validate system that is used by other platforms providing smart contract functionality. Pluggable performance, identity management systems, DBMS, Consensus platforms etc. are other features of Fabric that keeps it miles ahead of its competition.
+
+### Conclusion
+
+Projects such as the Hyperledger Fabric platforms enable a faster rate of adoption of blockchain technology in mainstream use-cases. The Hyperledger community structure itself supports open governance principles and since all the projects are led as open source platforms, this improves the security and accountability that the teams exhibit in pushing out commitments.
+
+Since major applications of such projects involve working with enterprises to further development of platforms and standards, the Hyperledger project is currently at a great position with respect to comparable projects by others.
+
+**References:**
+
+ * **[1][Samsung takes a seat with Intel and IBM at the Linux Foundation | TheINQUIRER][7]**
+ * **[2] E. Androulaki et al., “Hyperledger Fabric: A Distributed Operating System for Permissioned Blockchains,” 2018.**
+
+
+
+--------------------------------------------------------------------------------
+
+via: https://www.ostechnix.com/blockchain-2-0-an-introduction-to-hyperledger-project-hlp/
+
+作者:[editor][a]
+选题:[lujun9972][b]
+译者:[译者ID](https://github.com/译者ID)
+校对:[校对者ID](https://github.com/校对者ID)
+
+本文由 [LCTT](https://github.com/LCTT/TranslateProject) 原创编译,[Linux中国](https://linux.cn/) 荣誉推出
+
+[a]: https://www.ostechnix.com/author/editor/
+[b]: https://github.com/lujun9972
+[1]: https://www.ostechnix.com/wp-content/uploads/2019/04/Introduction-To-Hyperledger-Project-720x340.png
+[2]: https://www.ostechnix.com/blockchain-2-0-an-introduction/
+[3]: https://www.hyperledger.org/members
+[4]: https://www.ostechnix.com/blockchain-2-0-public-vs-private-blockchain-comparison/
+[5]: http://www.hitachi.com/rev/archive/2017/r2017_01/expert/index.html
+[6]: https://www.ostechnix.com/blockchain-2-0-explaining-smart-contracts-and-its-types/
+[7]: https://www.theinquirer.net/inquirer/news/2182438/samsung-takes-seat-intel-ibm-linux-foundation
diff --git a/sources/tech/20190505 Blockchain 2.0 - Public Vs Private Blockchain Comparison -Part 7.md b/sources/tech/20190505 Blockchain 2.0 - Public Vs Private Blockchain Comparison -Part 7.md
new file mode 100644
index 0000000000..a954e8514e
--- /dev/null
+++ b/sources/tech/20190505 Blockchain 2.0 - Public Vs Private Blockchain Comparison -Part 7.md
@@ -0,0 +1,106 @@
+[#]: collector: (lujun9972)
+[#]: translator: ( )
+[#]: reviewer: ( )
+[#]: publisher: ( )
+[#]: url: ( )
+[#]: subject: (Blockchain 2.0 – Public Vs Private Blockchain Comparison [Part 7])
+[#]: via: (https://www.ostechnix.com/blockchain-2-0-public-vs-private-blockchain-comparison/)
+[#]: author: (editor https://www.ostechnix.com/author/editor/)
+
+Blockchain 2.0 – Public Vs Private Blockchain Comparison [Part 7]
+======
+
+![Public vs Private blockchain][1]
+
+The previous part of the [**Blockchain 2.0**][2] series explored the [**the state of Smart contracts**][3] now. This post intends to throw some light on the different types of blockchains that can be created. Each of these are used for vastly different applications and depending on the use cases, the protocol followed by each of these differ. Now let us go ahead and learn about **Public vs Private blockchain comparison** with Open source and proprietary technology.
+
+The fundamental three-layer structure of a blockchain based distributed ledger as we know is as follows:
+
+![][4]
+
+Figure 1 – Fundamental structure of Blockchain-based ledgers
+
+The differences between the types mentioned here is attributable primarily to the protocol that rests on the underlying blockchain. The protocol dictates rules for the participants and the behavior of the blockchain in response to the said participation.
+
+Remember to keep the following things in mind while reading through this article:
+
+ * Platforms such as these are always created to solve a use-case requirement. There is no one direction that the technology should take that is best. Blockchains for instance have tremendous applications and some of these might require dropping features that seem significant in other settings. **Decentralized storage** is a major example in this regard.
+ * Blockchains are basically database systems keeping track of information by timestamping and organizing data in the form of blocks. Creators of such blockchains can choose who has the right to make these blocks and perform alterations.
+ * Blockchains can be “centralized” as well, and participation in varying extents can be limited to those who this “central authority” deems eligible.
+
+
+
+Most blockchains are either **public** or **private**. Broadly speaking, public blockchains can be considered as being the equivalent of open source software and most private blockchains can be seen as proprietary platforms deriving from the public ones. The figure below should make the basic difference obvious to most of you.
+
+![][5]
+
+Figure 2 – Public vs Private blockchain comparison with Open source and Proprietary Technology
+
+This is not to say that all private blockchains are derived from open public ones. The most popular ones however usually are though.
+
+### Public Blockchains
+
+A public blockchain can be considered as a **permission-less platform** or **network**. Anyone with the knowhow and computing resources can participate in it. This will have the following implications:
+
+ * Anyone can join and participate in a public blockchain network. All the “participant” needs is a stable internet connection along with computing resources.
+ * Participation will include reading, writing, verifying, and providing consensus during transactions. An example for participating individuals would be **Bitcoin miners**. In exchange for participating in the network the miners are paid back in Bitcoins in this case.
+ * The platform is decentralized completely and fully redundant.
+ * Because of the decentralized nature, no one entity has complete control over the data recorded in the ledger. To validate a block all (or most) participants need to vet the data.
+ * This means that once information is verified and recorded, it cannot be altered easily. Even if it is, its impossible to not leave marks.
+ * The identity of participants remains anonymous by design in platforms such as **BITCOIN** and **LITECOIN**. These platforms by design aim for protecting and securing user identities. This is primarily a feature provided by the overlying protocol stack.
+ * Examples for public blockchain networks are **BITCOIN** , **LITECOIN** , **ETHEREUM** etc.
+ * Extensive decentralizations mean that gaining consensus on transactions might take a while compared to what is typically possible over blockchain ledger networks and throughput can be a challenge for large enterprises aiming for pushing a very high number of transactions every instant.
+ * The open participation and often the high number of such participants in open chains such as bitcoin add up to considerable initial investments in computing equipment and energy costs.
+
+
+
+### Private Blockchain
+
+In contrast, a private blockchain is a **permissioned blockchain**. Meaning:
+
+ * Permission to participate in the network is restricted and is presided over by the owner or institution overseeing the network. Meaning even though an individual will be able to store data and transact (send and receive payments for example), the validation and storage of these transactions will be done only by select participants.
+ * Participation even once permission is given by the central authority will be limited by terms. For instance, in case of a private blockchain network run by a financial institution, not every customer will have access to the entire blockchain ledger, and even among those with the permission, not everyone will be able to access everything. Permissions to access select services will be given by the central figure in this case. This is often referred to as **“channeling”**.
+ * Such systems have significantly larger throughput capabilities and also showcase much faster transaction speeds compared to their public counterparts because a block of information only needs to be validated by a select few.
+ * Security by design is something the public blockchains are renowned for. They achieve this
+by:
+ * Anonymizing participants,
+ * Distributed & redundant but encrypted storage on multiple nodes,
+ * Mass consensus required for creating and altering data.
+
+
+
+Private blockchains usually don’t feature any of these in their protocol. This makes the system only as secure as most cloud-based database systems currently in use.
+
+### A note for the wise
+
+An important point to note is this, the fact that they’re named public or private (or open or closed) has nothing to do with the underlying code base. The code or the literal foundations on which the platforms are based on may or may not be publicly available and or developed in either of these cases. **R3** is a **DLT** ( **D** istributed **L** edger **T** echnology) company that leads a public consortium of over 200 multinational institutions. Their aim is to further development of blockchain and related distributed ledger technology in the domain of finance and commerce. **Corda** is the product of this joint effort. R3 defines corda as a blockchain platform that is built specially for businesses. The codebase for the same is open source and developers all over the world are encouraged to contribute to the project. However, given its business facing nature and the needs it is meant to address, corda would be categorized as a permissioned closed blockchain platform. Meaning businesses can choose the participants of the network once it is deployed and choose the kind of information these participants can access through the use of natively available smart contract tools.
+
+While it is a reality that public platforms like Bitcoin and Ethereum are responsible for the widespread awareness and development going on in the space, it can still be argued that private blockchains designed for specific use cases in enterprise or business settings is what will lead monetary investments in the short run. These are the platforms most of us will see implemented the near future in practical ways.
+
+Read the next guide about Hyperledger project in this series.
+
+ * [**Blockchain 2.0 – An Introduction To Hyperledger Project (HLP)**][6]
+
+
+
+We are working on many interesting topics on Blockchain technology. Stay tuned!
+
+--------------------------------------------------------------------------------
+
+via: https://www.ostechnix.com/blockchain-2-0-public-vs-private-blockchain-comparison/
+
+作者:[editor][a]
+选题:[lujun9972][b]
+译者:[译者ID](https://github.com/译者ID)
+校对:[校对者ID](https://github.com/校对者ID)
+
+本文由 [LCTT](https://github.com/LCTT/TranslateProject) 原创编译,[Linux中国](https://linux.cn/) 荣誉推出
+
+[a]: https://www.ostechnix.com/author/editor/
+[b]: https://github.com/lujun9972
+[1]: https://www.ostechnix.com/wp-content/uploads/2019/04/Public-Vs-Private-Blockchain-720x340.png
+[2]: https://www.ostechnix.com/blockchain-2-0-an-introduction/
+[3]: https://www.ostechnix.com/blockchain-2-0-ongoing-projects-the-state-of-smart-contracts-now/
+[4]: http://www.ostechnix.com/wp-content/uploads/2019/04/blockchain-architecture.png
+[5]: http://www.ostechnix.com/wp-content/uploads/2019/04/Public-vs-Private-blockchain-comparison.png
+[6]: https://www.ostechnix.com/blockchain-2-0-an-introduction-to-hyperledger-project-hlp/
diff --git a/sources/tech/20190505 Blockchain 2.0 - What Is Ethereum -Part 9.md b/sources/tech/20190505 Blockchain 2.0 - What Is Ethereum -Part 9.md
new file mode 100644
index 0000000000..a4669a2eb0
--- /dev/null
+++ b/sources/tech/20190505 Blockchain 2.0 - What Is Ethereum -Part 9.md
@@ -0,0 +1,83 @@
+[#]: collector: (lujun9972)
+[#]: translator: ( )
+[#]: reviewer: ( )
+[#]: publisher: ( )
+[#]: url: ( )
+[#]: subject: (Blockchain 2.0 – What Is Ethereum [Part 9])
+[#]: via: (https://www.ostechnix.com/blockchain-2-0-what-is-ethereum/)
+[#]: author: (editor https://www.ostechnix.com/author/editor/)
+
+Blockchain 2.0 – What Is Ethereum [Part 9]
+======
+
+![Ethereum][1]
+
+In the previous guide of this series, we discussed about [**Hyperledger Project (HLP)**][2], a fastest growing product developed by **Linux Foundation**. In this guide, we are going to discuss about what is **Ethereum** and its features in detail. Many researchers opine that the future of the internet will be based on principles of decentralized computing. Decentralized computing was in fact among one of the broader objectives of having the internet in the first place. However, the internet took another turn owing to differences in computing capabilities available. While modern server capabilities make the case for server-side processing and execution, lack of decent mobile networks in large parts of the world make the case for the same on the client side. Modern smartphones now have **SoCs** (system on a chip or system on chip) capable of handling many such operations on the client side itself, however, limitations owing to retrieving and storing data securely still pushes developers to have server-side computing and data management. Hence, a bottleneck in regards to data transfer capabilities is currently observed.
+
+All of that might soon change because of advancements in distributed data storage and program execution platforms. [**The blockchain**][3], for the first time in the history of the internet, basically allows for secure data management and program execution on a distributed network of users as opposed to central servers.
+
+**Ethereum** is one such blockchain platform that gives developers access to frameworks and tools used to build and run applications on such a decentralized network. Though more popularly known in general for its cryptocurrency, Ethereum is more than just **ethers** (the cryptocurrency). It’s a full **Turing complete programming language** that is designed to develop and deploy **DApps** or **Distributed APPlications** [1]. We’ll look at DApps in more detail in one of the upcoming posts.
+
+Ethereum is an open-source, supports by default a public (non-permissioned) blockchain, and features an extensive smart contract platform **(Solidity)** underneath. Ethereum provides a virtual computing environment called the **Ethereum virtual machine** to run applications and [**smart contracts**][4] as well[2]. The Ethereum virtual machine runs on thousands of participating nodes all over the world, meaning the application data while being secure, is almost impossible to be tampered with or lost.
+
+### Getting behind Ethereum: What sets it apart
+
+In 2017, a 30 plus group of the who’s who of the tech and financial world got together to leverage the Ethereum blockchain’s capabilities. Thus, the **Ethereum Enterprise Alliance (EEA)** was formed by a long list of supporting members including _Microsoft_ , _JP Morgan_ , _Cisco Systems_ , _Deloitte_ , and _Accenture_. JP Morgan already has **Quorum** , a decentralized computing platform for financial services based on Ethereum currently in operation, while Microsoft has Ethereum based cloud services it markets through its Azure cloud business[3].
+
+### What is ether and how is it related to Ethereum
+
+Ethereum creator **Vitalik Buterin** understood the true value of a decentralized processing platform and the underlying blockchain tech that powered bitcoin. He failed to gain majority agreement for his idea of proposing that Bitcoin should be developed to support running distributed applications (DApps) and programs (now referred to as smart contracts).
+
+Hence in 2013, he proposed the idea of Ethereum in a white paper he published. The original white paper is still maintained and available for readers **[here][5]**. The idea was to develop a blockchain based platform to run smart contracts and applications designed to run on nodes and user devices instead of servers.
+
+The Ethereum system is often mistaken to just mean the cryptocurrency ether, however, it has to be reiterated that Ethereum is a full stack platform for developing applications and executing them as well and has been so since inception whereas bitcoin isn’t. **Ether is currently the second biggest cryptocurrency** by market capitalization and trades at an average of $170 per ether at the time of writing this article[4].
+
+### Features and technicalities of the platform[5]
+
+ * As we’ve already mentioned, the cryptocurrency called ether is simply one of the things the platform features. The purpose of the system is more than taking care of financial transactions. In fact, the key difference between the Ethereum platform and Bitcoin is in their scripting capabilities. Ethereum is developed in a Turing complete programming language which means it has scripting and application capabilities similar to other major programming languages. Developers require this feature to create DApps and complex smart contracts on the platform, a feature that bitcoin misses on.
+ * The “mining” process of ether is more stringent and complex. While specialized ASICs may be used to mine bitcoin, the basic hashing algorithm used by Ethereum **(EThash)** reduces the advantage that ASICs have in this regard.
+ * The transaction fees itself to be paid as an incentive to miners and node operators for running the network is calculated using a computational token called **Gas**. Gas improves the system’s resilience and resistance to external hacks and attacks by requiring the initiator of the transaction to pay ethers proportionate to the number of computational resources that are required to carry out that transaction. This is in contrast to other platforms such as Bitcoin where the transaction fee is measured in tandem with the transaction size. As such, the average transaction costs in Ethereum is radically less than Bitcoin. This also implies that running applications running on the Ethereum virtual machine will require a fee depending straight up on the computational problems that the application is meant to solve. Basically, the more complex an execution, the more the fee.
+ * The block time for Ethereum is estimated to be around _**10-15 seconds**_. The block time is the average time that is required to timestamp and create a block on the blockchain network. Compared to the 10+ minutes the same transaction will take on the bitcoin network, it becomes apparent that _**Ethereum is much faster**_ with respect to transactions and verification of blocks.
+ * _It is also interesting to note that there is no hard cap on the amount of ether that can be mined or the rate at which ether can be mined leading to less radical system design than bitcoin._
+
+
+
+### Conclusion
+
+While Ethereum is comparable and far outpaces similar platforms, the platform itself lacked a definite path for development until the Ethereum enterprise alliance started pushing it. While the definite push for enterprise developments are made by the Ethereum platform, it has to be noted that Ethereum also caters to small-time developers and individuals as well. As such developing the platform for end users and enterprises leave a lot of specific functionality out of the loop for Ethereum. Also, the blockchain model proposed and developed by the Ethereum foundation is a public model whereas the one proposed by projects such as the Hyperledger project is private and permissioned.
+
+While only time can tell which platform among the ones put forward by Ethereum, Hyperledger, and R3 Corda among others will find the most fans in real-world use cases, such systems do prove the validity behind the claim of a blockchain powered future.
+
+**References:**
+
+ * [1] [**Gabriel Nicholas, “Ethereum Is Coding’s New Wild West | WIRED,” Wired , 2017**][6].
+ * [2] [**What is Ethereum? — Ethereum Homestead 0.1 documentation**][7].
+ * [3] [**Ethereum, a Virtual Currency, Enables Transactions That Rival Bitcoin’s – The New York Times**][8].
+ * [4] [**Cryptocurrency Market Capitalizations | CoinMarketCap**][9].
+ * [5] [**Introduction — Ethereum Homestead 0.1 documentation**][10].
+
+
+
+--------------------------------------------------------------------------------
+
+via: https://www.ostechnix.com/blockchain-2-0-what-is-ethereum/
+
+作者:[editor][a]
+选题:[lujun9972][b]
+译者:[译者ID](https://github.com/译者ID)
+校对:[校对者ID](https://github.com/校对者ID)
+
+本文由 [LCTT](https://github.com/LCTT/TranslateProject) 原创编译,[Linux中国](https://linux.cn/) 荣誉推出
+
+[a]: https://www.ostechnix.com/author/editor/
+[b]: https://github.com/lujun9972
+[1]: https://www.ostechnix.com/wp-content/uploads/2019/04/Ethereum-720x340.png
+[2]: https://www.ostechnix.com/blockchain-2-0-an-introduction-to-hyperledger-project-hlp/
+[3]: https://www.ostechnix.com/blockchain-2-0-an-introduction/
+[4]: https://www.ostechnix.com/blockchain-2-0-explaining-smart-contracts-and-its-types/
+[5]: https://github.com/ethereum/wiki/wiki/White-Paper
+[6]: https://www.wired.com/story/ethereum-is-codings-new-wild-west/
+[7]: http://www.ethdocs.org/en/latest/introduction/what-is-ethereum.html#ethereum-virtual-machine
+[8]: https://www.nytimes.com/2016/03/28/business/dealbook/ethereum-a-virtual-currency-enables-transactions-that-rival-bitcoins.html
+[9]: https://coinmarketcap.com/
+[10]: http://www.ethdocs.org/en/latest/introduction/index.html
diff --git a/sources/tech/20190505 Five Methods To Check Your Current Runlevel In Linux.md b/sources/tech/20190505 Five Methods To Check Your Current Runlevel In Linux.md
new file mode 100644
index 0000000000..2169f04e51
--- /dev/null
+++ b/sources/tech/20190505 Five Methods To Check Your Current Runlevel In Linux.md
@@ -0,0 +1,183 @@
+[#]: collector: (lujun9972)
+[#]: translator: ( )
+[#]: reviewer: ( )
+[#]: publisher: ( )
+[#]: url: ( )
+[#]: subject: (Five Methods To Check Your Current Runlevel In Linux?)
+[#]: via: (https://www.2daygeek.com/check-current-runlevel-in-linux/)
+[#]: author: (Magesh Maruthamuthu https://www.2daygeek.com/author/magesh/)
+
+Five Methods To Check Your Current Runlevel In Linux?
+======
+
+A run level is an operating system state on Linux system.
+
+There are seven runlevels exist, numbered from zero to six.
+
+A system can be booted into any of the given runlevel. Run levels are identified by numbers.
+
+Each runlevel designates a different system configuration and allows access to a different combination of processes.
+
+By default Linux boots either to runlevel 3 or to runlevel 5.
+
+Only one runlevel is executed at a time on startup. It doesn’t execute one after another.
+
+The default runlevel for a system is specified in the /etc/inittab file for SysVinit system.
+
+But systemd systems doesn’t read this file and it uses the following file `/etc/systemd/system/default.target` to get default runlevel information.
+
+We can check the Linux system current runlevel using the below five methods.
+
+ * **`runlevel Command:`** runlevel prints the previous and current runlevel of the system.
+ * **`who Command:`** Print information about users who are currently logged in. It will print the runlevel information with “-r” option.
+ * **`systemctl Command:`** It controls the systemd system and service manager.
+ * **`Using /etc/inittab File:`** The default runlevel for a system is specified in the /etc/inittab file for SysVinit System.
+ * **`Using /etc/systemd/system/default.target File:`** The default runlevel for a system is specified in the /etc/systemd/system/default.target file for systemd System.
+
+
+
+Detailed runlevels information is described in the below table.
+
+**Runlevel** | **SysVinit System** | **systemd System**
+---|---|---
+0 | Shutdown or Halt the system | shutdown.target
+1 | Single user mode | rescue.target
+2 | Multiuser, without NFS | multi-user.target
+3 | Full multiuser mode | multi-user.target
+4 | unused | multi-user.target
+5 | X11 (Graphical User Interface) | graphical.target
+6 | reboot the system | reboot.target
+
+The system will execute the programs/service based on the runlevel.
+
+For SysVinit system, it will be execute from the following location.
+
+ * Run level 0 – /etc/rc.d/rc0.d/
+ * Run level 1 – /etc/rc.d/rc1.d/
+ * Run level 2 – /etc/rc.d/rc2.d/
+ * Run level 3 – /etc/rc.d/rc3.d/
+ * Run level 4 – /etc/rc.d/rc4.d/
+ * Run level 5 – /etc/rc.d/rc5.d/
+ * Run level 6 – /etc/rc.d/rc6.d/
+
+
+
+For systemd system, it will be execute from the following location.
+
+ * runlevel1.target – /etc/systemd/system/rescue.target
+ * runlevel2.target – /etc/systemd/system/multi-user.target.wants
+ * runlevel3.target – /etc/systemd/system/multi-user.target.wants
+ * runlevel4.target – /etc/systemd/system/multi-user.target.wants
+ * runlevel5.target – /etc/systemd/system/graphical.target.wants
+
+
+
+### 1) How To Check Your Current Runlevel In Linux Using runlevel Command?
+
+runlevel prints the previous and current runlevel of the system.
+
+```
+$ runlevel
+N 5
+```
+
+ * **`N:`** “N” indicates that the runlevel has not been changed since the system was booted.
+ * **`5:`** “5” indicates the current runlevel of the system.
+
+
+
+### 2) How To Check Your Current Runlevel In Linux Using who Command?
+
+Print information about users who are currently logged in. It will print the runlevel information with `-r` option.
+
+```
+$ who -r
+ run-level 5 2019-04-22 09:32
+```
+
+### 3) How To Check Your Current Runlevel In Linux Using systemctl Command?
+
+systemctl is used to controls the systemd system and service manager. systemd is system and service manager for Unix like operating systems.
+
+It can work as a drop-in replacement for sysvinit system. systemd is the first process get started by kernel and holding PID 1.
+
+systemd uses `.service` files Instead of bash scripts (SysVinit uses). systemd sorts all daemons into their own Linux cgroups and you can see the system hierarchy by exploring `/cgroup/systemd` file.
+
+```
+$ systemctl get-default
+graphical.target
+```
+
+### 4) How To Check Your Current Runlevel In Linux Using /etc/inittab File?
+
+The default runlevel for a system is specified in the /etc/inittab file for SysVinit System but systemd systemd doesn’t read the files.
+
+So, it will work only on SysVinit system and not in systemd system.
+
+```
+$ cat /etc/inittab
+# inittab is only used by upstart for the default runlevel.
+#
+# ADDING OTHER CONFIGURATION HERE WILL HAVE NO EFFECT ON YOUR SYSTEM.
+#
+# System initialization is started by /etc/init/rcS.conf
+#
+# Individual runlevels are started by /etc/init/rc.conf
+#
+# Ctrl-Alt-Delete is handled by /etc/init/control-alt-delete.conf
+#
+# Terminal gettys are handled by /etc/init/tty.conf and /etc/init/serial.conf,
+# with configuration in /etc/sysconfig/init.
+#
+# For information on how to write upstart event handlers, or how
+# upstart works, see init(5), init(8), and initctl(8).
+#
+# Default runlevel. The runlevels used are:
+# 0 - halt (Do NOT set initdefault to this)
+# 1 - Single user mode
+# 2 - Multiuser, without NFS (The same as 3, if you do not have networking)
+# 3 - Full multiuser mode
+# 4 - unused
+# 5 - X11
+# 6 - reboot (Do NOT set initdefault to this)
+#
+id:5:initdefault:
+```
+
+### 5) How To Check Your Current Runlevel In Linux Using /etc/systemd/system/default.target File?
+
+The default runlevel for a system is specified in the /etc/systemd/system/default.target file for systemd System.
+
+It doesn’t work on SysVinit system.
+
+```
+$ cat /etc/systemd/system/default.target
+# This file is part of systemd.
+#
+# systemd is free software; you can redistribute it and/or modify it
+# under the terms of the GNU Lesser General Public License as published by
+# the Free Software Foundation; either version 2.1 of the License, or
+# (at your option) any later version.
+
+[Unit]
+Description=Graphical Interface
+Documentation=man:systemd.special(7)
+Requires=multi-user.target
+Wants=display-manager.service
+Conflicts=rescue.service rescue.target
+After=multi-user.target rescue.service rescue.target display-manager.service
+AllowIsolate=yes
+```
+--------------------------------------------------------------------------------
+
+via: https://www.2daygeek.com/check-current-runlevel-in-linux/
+
+作者:[Magesh Maruthamuthu][a]
+选题:[lujun9972][b]
+译者:[译者ID](https://github.com/译者ID)
+校对:[校对者ID](https://github.com/校对者ID)
+
+本文由 [LCTT](https://github.com/LCTT/TranslateProject) 原创编译,[Linux中国](https://linux.cn/) 荣誉推出
+
+[a]: https://www.2daygeek.com/author/magesh/
+[b]: https://github.com/lujun9972
diff --git a/sources/tech/20190505 How To Navigate Directories Faster In Linux.md b/sources/tech/20190505 How To Navigate Directories Faster In Linux.md
new file mode 100644
index 0000000000..e0979b3915
--- /dev/null
+++ b/sources/tech/20190505 How To Navigate Directories Faster In Linux.md
@@ -0,0 +1,350 @@
+[#]: collector: (lujun9972)
+[#]: translator: ( )
+[#]: reviewer: ( )
+[#]: publisher: ( )
+[#]: url: ( )
+[#]: subject: (How To Navigate Directories Faster In Linux)
+[#]: via: (https://www.ostechnix.com/navigate-directories-faster-linux/)
+[#]: author: (sk https://www.ostechnix.com/author/sk/)
+
+How To Navigate Directories Faster In Linux
+======
+
+![Navigate Directories Faster In Linux][1]
+
+Today we are going to learn some command line productivity hacks. As you already know, we use “cd” command to move between a stack of directories in Unix-like operating systems. In this guide I am going to teach you how to navigate directories faster without having to use “cd” command often. There could be many ways, but I only know the following five methods right now! I will keep updating this guide when I came across any methods or utilities to achieve this task in the days to come.
+
+### Five Different Methods To Navigate Directories Faster In Linux
+
+##### Method 1: Using “Pushd”, “Popd” And “Dirs” Commands
+
+This is the most frequent method that I use everyday to navigate between a stack of directories. The “Pushd”, “Popd”, and “Dirs” commands comes pre-installed in most Linux distributions, so don’t bother with installation. These trio commands are quite useful when you’re working in a deep directory structure and scripts. For more details, check our guide in the link given below.
+
+ * **[How To Use Pushd, Popd And Dirs Commands For Faster CLI Navigation][2]**
+
+
+
+##### Method 2: Using “bd” utility
+
+The “bd” utility also helps you to quickly go back to a specific parent directory without having to repeatedly typing “cd ../../.” on your Bash.
+
+Bd is also available in the [**Debian extra**][3] and [**Ubuntu universe**][4] repositories. So, you can install it using “apt-get” package manager in Debian, Ubuntu and other DEB based systems as shown below:
+
+```
+$ sudo apt-get update
+
+$ sudo apt-get install bd
+```
+
+For other distributions, you can install as shown below.
+
+```
+$ sudo wget --no-check-certificate -O /usr/local/bin/bd https://raw.github.com/vigneshwaranr/bd/master/bd
+
+$ sudo chmod +rx /usr/local/bin/bd
+
+$ echo 'alias bd=". bd -si"' >> ~/.bashrc
+
+$ source ~/.bashrc
+```
+
+To enable auto completion, run:
+
+```
+$ sudo wget -O /etc/bash_completion.d/bd https://raw.github.com/vigneshwaranr/bd/master/bash_completion.d/bd
+
+$ source /etc/bash_completion.d/bd
+```
+
+The Bd utility has now been installed. Let us see few examples to understand how to quickly move through stack of directories using this tool.
+
+Create some directories.
+
+```
+$ mkdir -p dir1/dir2/dir3/dir4/dir5/dir6/dir7/dir8/dir9/dir10
+```
+
+The above command will create a hierarchy of directories. Let us check [**directory structure**][5] using command:
+
+```
+$ tree dir1/
+dir1/
+└── dir2
+ └── dir3
+ └── dir4
+ └── dir5
+ └── dir6
+ └── dir7
+ └── dir8
+ └── dir9
+ └── dir10
+
+9 directories, 0 files
+```
+
+Alright, we have now 10 directories. Let us say you’re currently in 7th directory i.e dir7.
+
+```
+$ pwd
+/home/sk/dir1/dir2/dir3/dir4/dir5/dir6/dir7
+```
+
+You want to move to dir3. Normally you would type:
+
+```
+$ cd /home/sk/dir1/dir2/dir3
+```
+
+Right? yes! But it not necessary though! To go back to dir3, just type:
+
+```
+$ bd dir3
+```
+
+Now you will be in dir3.
+
+![][6]
+
+Navigate Directories Faster In Linux Using “bd” Utility
+
+Easy, isn’t it? It supports auto complete, so you can just type the partial name of a directory and hit the tab key to auto complete the full path.
+
+To check the contents of a specific parent directory, you don’t need to inside that particular directory. Instead, just type:
+
+```
+$ ls `bd dir1`
+```
+
+The above command will display the contents of dir1 from your current working directory.
+
+For more details, check out the following GitHub page.
+
+ * [**bd GitHub repository**][7]
+
+
+
+##### Method 3: Using “Up” Shell script
+
+The “Up” is a shell script allows you to move quickly to your parent directory. It works well on many popular shells such as Bash, Fish, and Zsh etc. Installation is absolutely easy too!
+
+To install “Up” on **Bash** , run the following commands one bye:
+
+```
+$ curl --create-dirs -o ~/.config/up/up.sh https://raw.githubusercontent.com/shannonmoeller/up/master/up.sh
+
+$ echo 'source ~/.config/up/up.sh' >> ~/.bashrc
+```
+
+The up script registers the “up” function and some completion functions via your “.bashrc” file.
+
+Update the changes using command:
+
+```
+$ source ~/.bashrc
+```
+
+On **zsh** :
+
+```
+$ curl --create-dirs -o ~/.config/up/up.sh https://raw.githubusercontent.com/shannonmoeller/up/master/up.sh
+
+$ echo 'source ~/.config/up/up.sh' >> ~/.zshrc
+```
+
+The up script registers the “up” function and some completion functions via your “.zshrc” file.
+
+Update the changes using command:
+
+```
+$ source ~/.zshrc
+```
+
+On **fish** :
+
+```
+$ curl --create-dirs -o ~/.config/up/up.fish https://raw.githubusercontent.com/shannonmoeller/up/master/up.fish
+
+$ source ~/.config/up/up.fish
+```
+
+The up script registers the “up” function and some completion functions via “funcsave”.
+
+Now it is time to see some examples.
+
+Let us create some directories.
+
+```
+$ mkdir -p dir1/dir2/dir3/dir4/dir5/dir6/dir7/dir8/dir9/dir10
+```
+
+Let us say you’re in 7th directory i.e dir7.
+
+```
+$ pwd
+/home/sk/dir1/dir2/dir3/dir4/dir5/dir6/dir7
+```
+
+You want to move to dir3. Using “cd” command, we can do this by typing the following command:
+
+```
+$ cd /home/sk/dir1/dir2/dir3
+```
+
+But it is really easy to go back to dir3 using “up” script:
+
+```
+$ up dir3
+```
+
+That’s it. Now you will be in dir3. To go one directory up, just type:
+
+```
+$ up 1
+```
+
+To go back two directory type:
+
+```
+$ up 2
+```
+
+It’s that simple. Did I type the full path? Nope. Also it supports tab completion. So just type the partial directory name and hit the tab to complete the full path.
+
+For more details, check out the GitHub page.
+
+ * [**Up GitHub Repository**][8]
+
+
+
+Please be mindful that “bd” and “up” tools can only help you to go backward i.e to the parent directory of the current working directory. You can’t move forward. If you want to switch to dir10 from dir5, you can’t! Instead, you need to use “cd” command to switch to dir10. These two utilities are meant for quickly moving you to the parent directory!
+
+##### Method 4: Using “Shortcut” tool
+
+This is yet another handy method to switch between different directories quickly and easily. This is somewhat similar to [**alias**][9] command. In this method, we create shortcuts to frequently used directories and use the shortcut name to go to that respective directory without having to type the path. If you’re working in deep directory structure and stack of directories, this method will greatly save some time. You can learn how it works in the guide given below.
+
+ * [**Create Shortcuts To The Frequently Used Directories In Your Shell**][10]
+
+
+
+##### Method 5: Using “CDPATH” Environment variable
+
+This method doesn’t require any installation. **CDPATH** is an environment variable. It is somewhat similar to **PATH** variable which contains many different paths concatenated using **‘:’** (colon). The main difference between PATH and CDPATH variables is the PATH variable is usable with all commands whereas CDPATH works only for **cd** command.
+
+I have the following directory structure.
+
+![][11]
+
+Directory structure
+
+As you see, there are four child directories under a parent directory named “ostechnix”.
+
+Now add this parent directory to CDPATH using command:
+
+```
+$ export CDPATH=~/ostechnix
+```
+
+You now can instantly cd to the sub-directories of the parent directory (i.e **~/ostechnix** in our case) from anywhere in the filesystem.
+
+For instance, currently I am in **/var/mail/** location.
+
+![][12]
+
+To cd into **~/ostechnix/Linux/** directory, we don’t have to use the full path of the directory as shown below:
+
+```
+$ cd ~/ostechnix/Linux
+```
+
+Instead, just mention the name of the sub-directory you want to switch to:
+
+```
+$ cd Linux
+```
+
+It will automatically cd to **~/ostechnix/Linux** directory instantly.
+
+![][13]
+
+As you can see in the above output, I didn’t use “cd ”. Instead, I just used “cd ” command.
+
+Please note that CDPATH will allow you to quickly navigate to only one child directory of the parent directory set in CDPATH variable. It doesn’t much help for navigating a stack of directories (directories inside sub-directories, of course).
+
+To find the values of CDPATH variable, run:
+
+```
+$ echo $CDPATH
+```
+
+Sample output would be:
+
+```
+/home/sk/ostechnix
+```
+
+**Set multiple values to CDPATH**
+
+Similar to PATH variable, we can also set multiple values (more than one directory) to CDPATH separated by colon (:).
+
+```
+$ export CDPATH=.:~/ostechnix:/etc:/var:/opt
+```
+
+**Make the changes persistent**
+
+As you already know, the above command (export) will only keep the values of CDPATH until next reboot. To permanently set the values of CDPATH, just add them to your **~/.bashrc** or **~/.bash_profile** files.
+
+```
+$ vi ~/.bash_profile
+```
+
+Add the values:
+
+```
+export CDPATH=.:~/ostechnix:/etc:/var:/opt
+```
+
+Hit **ESC** key and type **:wq** to save and exit.
+
+Apply the changes using command:
+
+```
+$ source ~/.bash_profile
+```
+
+**Clear CDPATH**
+
+To clear the values of CDPATH, use **export CDPATH=””**. Or, simply delete the entire line from **~/.bashrc** or **~/.bash_profile** files.
+
+In this article, you have learned the different ways to navigate directory stack faster and easier in Linux. As you can see, it’s not that difficult to browse a pile of directories faster. Now stop typing “cd ../../..” endlessly by using these tools. If you know any other worth trying tool or method to navigate directories faster, feel free to let us know in the comment section below. I will review and add them in this guide.
+
+And, that’s all for now. Hope this helps. More good stuffs to come. Stay tuned!
+
+Cheers!
+
+--------------------------------------------------------------------------------
+
+via: https://www.ostechnix.com/navigate-directories-faster-linux/
+
+作者:[sk][a]
+选题:[lujun9972][b]
+译者:[译者ID](https://github.com/译者ID)
+校对:[校对者ID](https://github.com/校对者ID)
+
+本文由 [LCTT](https://github.com/LCTT/TranslateProject) 原创编译,[Linux中国](https://linux.cn/) 荣誉推出
+
+[a]: https://www.ostechnix.com/author/sk/
+[b]: https://github.com/lujun9972
+[1]: https://www.ostechnix.com/wp-content/uploads/2017/12/Navigate-Directories-Faster-In-Linux-720x340.png
+[2]: https://www.ostechnix.com/use-pushd-popd-dirs-commands-faster-cli-navigation/
+[3]: https://tracker.debian.org/pkg/bd
+[4]: https://launchpad.net/ubuntu/+source/bd
+[5]: https://www.ostechnix.com/view-directory-tree-structure-linux/
+[6]: http://www.ostechnix.com/wp-content/uploads/2017/12/Navigate-Directories-Faster-1.png
+[7]: https://github.com/vigneshwaranr/bd
+[8]: https://github.com/shannonmoeller/up
+[9]: https://www.ostechnix.com/the-alias-and-unalias-commands-explained-with-examples/
+[10]: https://www.ostechnix.com/create-shortcuts-frequently-used-directories-shell/
+[11]: http://www.ostechnix.com/wp-content/uploads/2018/12/tree-command-output.png
+[12]: http://www.ostechnix.com/wp-content/uploads/2018/12/pwd-command.png
+[13]: http://www.ostechnix.com/wp-content/uploads/2018/12/cdpath.png
diff --git a/sources/tech/20190506 Use udica to build SELinux policy for containers.md b/sources/tech/20190506 Use udica to build SELinux policy for containers.md
new file mode 100644
index 0000000000..4e31288a43
--- /dev/null
+++ b/sources/tech/20190506 Use udica to build SELinux policy for containers.md
@@ -0,0 +1,199 @@
+[#]: collector: (lujun9972)
+[#]: translator: ( )
+[#]: reviewer: ( )
+[#]: publisher: ( )
+[#]: url: ( )
+[#]: subject: (Use udica to build SELinux policy for containers)
+[#]: via: (https://fedoramagazine.org/use-udica-to-build-selinux-policy-for-containers/)
+[#]: author: (Lukas Vrabec https://fedoramagazine.org/author/lvrabec/)
+
+Use udica to build SELinux policy for containers
+======
+
+![][1]
+
+While modern IT environments move towards Linux containers, the need to secure these environments is as relevant as ever. Containers are a process isolation technology. While containers can be a defense mechanism, they only excel when combined with SELinux.
+
+Fedora SELinux engineering built a new standalone tool, **udica** , to generate SELinux policy profiles for containers by automatically inspecting them. This article focuses on why _udica_ is needed in the container world, and how it makes SELinux and containers work better together. You’ll find examples of SELinux separation for containers that let you avoid turning protection off because the generic SELinux type _container_t_ is too tight. With _udica_ you can easily customize the policy with limited SELinux policy writing skills.
+
+### SELinux technology
+
+SELinux is a security technology that brings proactive security to Linux systems. It’s a labeling system that assigns a label to all _subjects_ (processes and users) and _objects_ (files, directories, sockets, etc.). These labels are then used in a security policy that controls access throughout the system. It’s important to mention that what’s not allowed in an SELinux security policy is denied by default. The policy rules are enforced by the kernel. This security technology has been in use on Fedora for several years. A real example of such a rule is:
+
+```
+allow httpd_t httpd_log_t: file { append create getattr ioctl lock open read setattr };
+```
+
+The rule allows any process labeled as _httpd_t_ ****to create, append, read and lock files labeled as _httpd_log_t_. Using the _ps_ command, you can list all processes with their labels:
+
+```
+$ ps -efZ | grep httpd
+system_u:system_r:httpd_t:s0 root 13911 1 0 Apr14 ? 00:05:14 /usr/sbin/httpd -DFOREGROUND
+...
+```
+
+To see which objects are labeled as httpd_log_t, use _semanage_ :
+
+```
+# semanage fcontext -l | grep httpd_log_t
+/var/log/httpd(/.)? all files system_u:object_r:httpd_log_t:s0
+/var/log/nginx(/.)? all files system_u:object_r:httpd_log_t:s0
+...
+```
+
+The SELinux security policy for Fedora is shipped in the _selinux-policy_ RPM package.
+
+### SELinux vs. containers
+
+In Fedora, the _container-selinux_ RPM package provides a generic SELinux policy for all containers started by engines like _podman_ or _docker_. Its main purposes are to protect the host system against a container process, and to separate containers from each other. For instance, containers confined by SELinux with the process type _container_t_ can only read/execute files in _/usr_ and write to _container_file_t_ ****files type on host file system. To prevent attacks by containers on each other, Multi-Category Security (MCS) is used.
+
+Using only one generic policy for containers is problematic, because of the huge variety of container usage. On one hand, the default container type ( _container_t_ ) is often too strict. For example:
+
+ * [Fedora SilverBlue][2] needs containers to read/write a user’s home directory
+ * [Fluentd][3] project needs containers to be able to read logs in the _/var/log_ directory
+
+
+
+On the other hand, the default container type could be too loose for certain use cases:
+
+ * It has no SELinux network controls — all container processes can bind to any network port
+ * It has no SELinux control on [Linux capabilities][4] — all container processes can use all capabilities
+
+
+
+There is one solution to handle both use cases: write a custom SELinux security policy for the container. This can be tricky, because SELinux expertise is required. For this purpose, the _udica_ tool was created.
+
+### Introducing udica
+
+Udica generates SELinux security profiles for containers. Its concept is based on the “block inheritance” feature inside the [common intermediate language][5] (CIL) supported by SELinux userspace. The tool creates a policy that combines:
+
+ * Rules inherited from specified CIL blocks (templates), and
+ * Rules discovered by inspection of container JSON file, which contains mountpoints and ports definitions
+
+
+
+You can load the final policy immediately, or move it to another system to load into the kernel. Here’s an example, using a container that:
+
+ * Mounts _/home_ as read only
+ * Mounts _/var/spool_ as read/write
+ * Exposes port _tcp/21_
+
+
+
+The container starts with this command:
+
+```
+# podman run -v /home:/home:ro -v /var/spool:/var/spool:rw -p 21:21 -it fedora bash
+```
+
+The default container type ( _container_t_ ) doesn’t allow any of these three actions. To prove it, you could use the _sesearch_ tool to query that the _allow_ rules are present on system:
+
+```
+# sesearch -A -s container_t -t home_root_t -c dir -p read
+```
+
+There’s no _allow_ rule present that lets a process labeled as _container_t_ access a directory labeled _home_root_t_ (like the _/home_ directory). The same situation occurs with _/var/spool_ , which is labeled _var_spool_t:_
+
+```
+# sesearch -A -s container_t -t var_spool_t -c dir -p read
+```
+
+On the other hand, the default policy completely allows network access.
+
+```
+# sesearch -A -s container_t -t port_type -c tcp_socket
+allow container_net_domain port_type:tcp_socket { name_bind name_connect recv_msg send_msg };
+allow sandbox_net_domain port_type:tcp_socket { name_bind name_connect recv_msg send_msg };
+```
+
+### Securing the container
+
+It would be great to restrict this access and allow the container to bind just on TCP port _21_ or with the same label. Imagine you find an example container using _podman ps_ whose ID is _37a3635afb8f_ :
+
+```
+# podman ps -q
+37a3635afb8f
+```
+
+You can now inspect the container and pass the inspection file to the _udica_ tool. The name for the new policy is _my_container_.
+
+```
+# podman inspect 37a3635afb8f > container.json
+# udica -j container.json my_container
+Policy my_container with container id 37a3635afb8f created!
+
+Please load these modules using:
+ # semodule -i my_container.cil /usr/share/udica/templates/{base_container.cil,net_container.cil,home_container.cil}
+
+Restart the container with: "--security-opt label=type:my_container.process" parameter
+```
+
+That’s it! You just created a custom SELinux security policy for the example container. Now you can load this policy into the kernel and make it active. The _udica_ output above even tells you the command to use:
+
+```
+# semodule -i my_container.cil /usr/share/udica/templates/{base_container.cil,net_container.cil,home_container.cil}
+```
+
+Now you must restart the container to allow the container engine to use the new custom policy:
+
+```
+# podman run --security-opt label=type:my_container.process -v /home:/home:ro -v /var/spool:/var/spool:rw -p 21:21 -it fedora bash
+```
+
+The example container is now running in the newly created _my_container.process_ SELinux process type:
+
+```
+# ps -efZ | grep my_container.process
+unconfined_u:system_r:container_runtime_t:s0-s0:c0.c1023 root 2275 434 1 13:49 pts/1 00:00:00 podman run --security-opt label=type:my_container.process -v /home:/home:ro -v /var/spool:/var/spool:rw -p 21:21 -it fedora bash
+system_u:system_r:my_container.process:s0:c270,c963 root 2317 2305 0 13:49 pts/0 00:00:00 bash
+```
+
+### Seeing the results
+
+The command _sesearch_ now shows _allow_ rules for accessing _/home_ and _/var/spool:_
+
+```
+# sesearch -A -s my_container.process -t home_root_t -c dir -p read
+allow my_container.process home_root_t:dir { getattr ioctl lock open read search };
+# sesearch -A -s my_container.process -t var_spool_t -c dir -p read
+allow my_container.process var_spool_t:dir { add_name getattr ioctl lock open read remove_name search write }
+```
+
+The new custom SELinux policy also allows _my_container.process_ to bind only to TCP/UDP ports labeled the same as TCP port 21:
+
+```
+# semanage port -l | grep 21 | grep ftp
+ ftp_port_t tcp 21, 989, 990
+# sesearch -A -s my_container.process -c tcp_socket -p name_bind
+ allow my_container.process ftp_port_t:tcp_socket name_bind;
+```
+
+### Conclusion
+
+The _udica_ tool helps you create SELinux policies for containers based on an inspection file without any SELinux expertise required. Now you can increase the security of containerized environments. Sources are available on [GitHub][6], and an RPM package is available in Fedora repositories for Fedora 28 and later.
+
+* * *
+
+*Photo by _[_Samuel Zeller_][7]_ on *[ _Unsplash_.][8]
+
+--------------------------------------------------------------------------------
+
+via: https://fedoramagazine.org/use-udica-to-build-selinux-policy-for-containers/
+
+作者:[Lukas Vrabec][a]
+选题:[lujun9972][b]
+译者:[译者ID](https://github.com/译者ID)
+校对:[校对者ID](https://github.com/校对者ID)
+
+本文由 [LCTT](https://github.com/LCTT/TranslateProject) 原创编译,[Linux中国](https://linux.cn/) 荣誉推出
+
+[a]: https://fedoramagazine.org/author/lvrabec/
+[b]: https://github.com/lujun9972
+[1]: https://fedoramagazine.org/wp-content/uploads/2019/05/udica-816x345.jpg
+[2]: https://silverblue.fedoraproject.org
+[3]: https://www.fluentd.org
+[4]: http://man7.org/linux/man-pages/man7/capabilities.7.html
+[5]: https://en.wikipedia.org/wiki/Common_Intermediate_Language
+[6]: https://github.com/containers/udica
+[7]: https://unsplash.com/photos/KVG-XMOs6tw?utm_source=unsplash&utm_medium=referral&utm_content=creditCopyText
+[8]: https://unsplash.com/search/photos/lockers?utm_source=unsplash&utm_medium=referral&utm_content=creditCopyText
diff --git a/sources/tech/20190508 Innovations on the Linux desktop- A look at Fedora 30-s new features.md b/sources/tech/20190508 Innovations on the Linux desktop- A look at Fedora 30-s new features.md
new file mode 100644
index 0000000000..083a8c9768
--- /dev/null
+++ b/sources/tech/20190508 Innovations on the Linux desktop- A look at Fedora 30-s new features.md
@@ -0,0 +1,140 @@
+[#]: collector: (lujun9972)
+[#]: translator: ( )
+[#]: reviewer: ( )
+[#]: publisher: ( )
+[#]: url: ( )
+[#]: subject: (Innovations on the Linux desktop: A look at Fedora 30's new features)
+[#]: via: (https://opensource.com/article/19/5/fedora-30-features)
+[#]: author: (Anderson Silva https://opensource.com/users/ansilva/users/marcobravo/users/alanfdoss/users/ansilva)
+
+Innovations on the Linux desktop: A look at Fedora 30's new features
+======
+Learn about some of the highlights in the latest version of Fedora
+Linux.
+![Fedora Linux distro on laptop][1]
+
+The latest version of Fedora Linux was released at the end of April. As a full-time Fedora user since its original release back in 2003 and an active contributor since 2007, I always find it satisfying to see new features and advancements in the community.
+
+If you want a TL;DR version of what's has changed in [Fedora 30][2], feel free to ignore this article and jump straight to Fedora's [ChangeSet][3] wiki page. Otherwise, keep on reading to learn about some of the highlights in the new version.
+
+### Upgrade vs. fresh install
+
+I upgraded my Lenovo ThinkPad T series from Fedora 29 to 30 using the [DNF system upgrade instructions][4], and so far it is working great!
+
+I also had the chance to do a fresh install on another ThinkPad, and it was a nice surprise to see a new boot screen on Fedora 30—it even picked up the Lenovo logo. I did not see this new and improved boot screen on the upgrade above; it was only on the fresh install.
+
+![Fedora 30 boot screen][5]
+
+### Desktop changes
+
+If you are a GNOME user, you'll be happy to know that Fedora 30 comes with the latest version, [GNOME 3.32][6]. It has an improved on-screen keyboard (handy for touch-screen laptops), brand new icons for core applications, and a new "Applications" panel under Settings that allows users to gain a bit more control on GNOME default handlers, access permissions, and notifications. Version 3.32 also improves Google Drive performance so that Google files and calendar appointments will be integrated with GNOME.
+
+![Applications panel in GNOME Settings][7]
+
+The new Applications panel in GNOME Settings
+
+Fedora 30 also introduces two new Desktop environments: Pantheon and Deepin. Pantheon is [ElementaryOS][8]'s default desktop environment and can be installed with a simple:
+
+
+```
+`$ sudo dnf groupinstall "Pantheon Desktop"`
+```
+
+I haven't used Pantheon yet, but I do use [Deepin][9]. Installation is simple; just run:
+
+
+```
+`$ sudo dnf install deepin-desktop`
+```
+
+then log out of GNOME and log back in, choosing "Deepin" by clicking on the gear icon on the login screen.
+
+![Deepin desktop on Fedora 30][10]
+
+Deepin desktop on Fedora 30
+
+Deepin appears as a very polished, user-friendly desktop environment that allows you to control many aspects of your environment with a click of a button. So far, the only issue I've had is that it can take a few extra seconds to complete login and return control to your mouse pointer. Other than that, it is brilliant! It is the first desktop environment I've used that seems to do high dots per inch (HiDPI) properly—or at least close to correctly.
+
+### Command line
+
+Fedora 30 upgrades the Bourne Again Shell (aka Bash) to version 5.0.x. If you want to find out about every change since its last stable version (4.4), read this [description][11]. I do want to mention that three new environments have been introduced in Bash 5:
+
+
+```
+$ echo $EPOCHSECONDS
+1556636959
+$ echo $EPOCHREALTIME
+1556636968.012369
+$ echo $BASH_ARGV0
+bash
+```
+
+Fedora 30 also updates the [Fish shell][12], a colorful shell with auto-suggestion, which can be very helpful for beginners. Fedora 30 comes with [Fish version 3][13], and you can even [try it out in a browser][14] without having to install it on your machine.
+
+(Note that Fish shell is not the same as guestfish for mounting virtual machine images, which comes with the libguestfs-tools package.)
+
+### Development
+
+Fedora 30 brings updates to the following languages: [C][15], [Boost (C++)][16], [Erlang][17], [Go][18], [Haskell][19], [Python][20], [Ruby][21], and [PHP][22].
+
+Regarding these updates, the most important thing to know is that Python 2 is deprecated in Fedora 30. The community and Fedora leadership are requesting that all package maintainers that still depend on Python 2 port their packages to Python 3 as soon as possible, as the plan is to remove virtually all Python 2 packages in Fedora 31.
+
+### Containers
+
+If you would like to run Fedora as an immutable OS for a container, kiosk, or appliance-like environment, check out [Fedora Silverblue][23]. It brings you all of Fedora's technology managed by [rpm-ostree][24], which is a hybrid image/package system that allows automatic updates and easy rollbacks for developers. It is a great option for anyone who wants to learn more and play around with [Flatpak deployments][25].
+
+Fedora Atomic is no longer available under Fedora 30, but you can still [download it][26]. If your jam is containers, don't despair: even though Fedora Atomic is gone, a brand new [Fedora CoreOS][27] is under development and should be going live soon!
+
+### What else is new?
+
+As of Fedora 30, **/usr/bin/gpg** points to [GnuPG][28] v2 by default, and [NFS][29] server configuration is now located at **/etc/nfs.conf** instead of **/etc/sysconfig/nfs**.
+
+There have also been a [few changes][30] for installation and boot time.
+
+Last but not least, check out [Fedora Spins][31] for a spin of Fedora that defaults to your favorite Window manager and [Fedora Labs][32] for functionally curated software bundles built on Fedora 30 (i.e. astronomy, security, and gaming).
+
+--------------------------------------------------------------------------------
+
+via: https://opensource.com/article/19/5/fedora-30-features
+
+作者:[Anderson Silva ][a]
+选题:[lujun9972][b]
+译者:[译者ID](https://github.com/译者ID)
+校对:[校对者ID](https://github.com/校对者ID)
+
+本文由 [LCTT](https://github.com/LCTT/TranslateProject) 原创编译,[Linux中国](https://linux.cn/) 荣誉推出
+
+[a]: https://opensource.com/users/ansilva/users/marcobravo/users/alanfdoss/users/ansilva
+[b]: https://github.com/lujun9972
+[1]: https://opensource.com/sites/default/files/styles/image-full-size/public/lead-images/fedora_on_laptop_lead.jpg?itok=XMc5wo_e (Fedora Linux distro on laptop)
+[2]: https://getfedora.org/
+[3]: https://fedoraproject.org/wiki/Releases/30/ChangeSet
+[4]: https://fedoraproject.org/wiki/DNF_system_upgrade#How_do_I_use_it.3F
+[5]: https://opensource.com/sites/default/files/uploads/fedora30_fresh-boot.jpg (Fedora 30 boot screen)
+[6]: https://help.gnome.org/misc/release-notes/3.32/
+[7]: https://opensource.com/sites/default/files/uploads/fedora10_gnome.png (Applications panel in GNOME Settings)
+[8]: https://elementary.io/
+[9]: https://www.deepin.org/en/dde/
+[10]: https://opensource.com/sites/default/files/uploads/fedora10_deepin.png (Deepin desktop on Fedora 30)
+[11]: https://git.savannah.gnu.org/cgit/bash.git/tree/NEWS
+[12]: https://fishshell.com/
+[13]: https://fishshell.com/release_notes.html
+[14]: https://rootnroll.com/d/fish-shell/
+[15]: https://docs.fedoraproject.org/en-US/fedora/f30/release-notes/developers/Development_C/
+[16]: https://docs.fedoraproject.org/en-US/fedora/f30/release-notes/developers/Development_Boost/
+[17]: https://docs.fedoraproject.org/en-US/fedora/f30/release-notes/developers/Development_Erlang/
+[18]: https://docs.fedoraproject.org/en-US/fedora/f30/release-notes/developers/Development_Go/
+[19]: https://docs.fedoraproject.org/en-US/fedora/f30/release-notes/developers/Development_Haskell/
+[20]: https://docs.fedoraproject.org/en-US/fedora/f30/release-notes/developers/Development_Python/
+[21]: https://docs.fedoraproject.org/en-US/fedora/f30/release-notes/developers/Development_Ruby/
+[22]: https://docs.fedoraproject.org/en-US/fedora/f30/release-notes/developers/Development_Web/
+[23]: https://silverblue.fedoraproject.org/
+[24]: https://rpm-ostree.readthedocs.io/en/latest/
+[25]: https://flatpak.org/setup/Fedora/
+[26]: https://getfedora.org/en/atomic/
+[27]: https://coreos.fedoraproject.org/
+[28]: https://gnupg.org/index.html
+[29]: https://en.wikipedia.org/wiki/Network_File_System
+[30]: https://docs.fedoraproject.org/en-US/fedora/f30/release-notes/sysadmin/Installation/
+[31]: https://spins.fedoraproject.org
+[32]: https://labs.fedoraproject.org/
diff --git a/sources/tech/20190508 Why startups should release their code as open source.md b/sources/tech/20190508 Why startups should release their code as open source.md
new file mode 100644
index 0000000000..f877964b5f
--- /dev/null
+++ b/sources/tech/20190508 Why startups should release their code as open source.md
@@ -0,0 +1,79 @@
+[#]: collector: (lujun9972)
+[#]: translator: ( )
+[#]: reviewer: ( )
+[#]: publisher: ( )
+[#]: url: ( )
+[#]: subject: (Why startups should release their code as open source)
+[#]: via: (https://opensource.com/article/19/5/startups-release-code)
+[#]: author: (Clément Flipo https://opensource.com/users/cl%C3%A9ment-flipo)
+
+Why startups should release their code as open source
+======
+Dokit wondered whether giving away its knowledge as open source was a
+bad business decision, but that choice has been the foundation of its
+success.
+![open source button on keyboard][1]
+
+It's always hard to recall exactly how a project started, but sometimes that can help you understand that project more clearly. When I think about it, our platform for creating user guides and documentation, [Dokit][2], came straight out of my childhood. Growing up in a house where my toys were Meccano and model airplane kits, the idea of making things, taking individual pieces and putting them together to create a new whole, was always a fundamental part of what it meant to play. My father worked for a DIY company, so there were always signs of building, repair, and instruction manuals around the house. When I was young, my parents sent me to join the Boy Scouts, where we made tables, tents and mud ovens, which helped foster my enjoyment of shared learning that I later found in the open source movement.
+
+The art of repairing things and recycling products that I learned in childhood became part of what I did for a job. Then it became my ambition to take the reassuring feel of learning how to make and do and repair at home or in a group—but put it online. That inspired Dokit's creation.
+
+### The first months
+
+It hasn't always been easy, but since founding our company in 2017, I've realized that the biggest and most worthwhile goals are generally always difficult. If we were to achieve our plan to revolutionize the way [old-fashioned manuals and user guides are created and published][3], and maximize our impact in what we knew all along would be a niche market, we knew that a guiding mission was crucial to how we organized everything else. It was from there that we reached our first big decision: to [quickly launch a proof of concept using an existing open source framework][4], MediaWiki, and from there to release all of our code as open source.
+
+In retrospect, this decision was made easier by the fact that [MediaWiki][5] was already up and running. With 15,000 developers already active around the world and on a platform that included 90% of the features we needed to meet our minimum viable product (MVP), things would have no doubt been harder without support from the engine that made its name by powering Wikipedia. Confluence, a documentation platform in use by many enterprises, offers some good features, but in the end, it was an easy choice between the two.
+
+Placing our faith in the community, we put the first version of our platform straight onto GitHub. The excitement of watching the world's makers start using our platform, even before we'd done any real advertising, felt like an early indication that we were on the right track. Although the [maker and Fablab movements][6] encourage users to share instructions, and even sets out this expectation in the [Fablab charter][7] (as stated by MIT), in reality, there is a lack of real documentation.
+
+The first and most significant reason people like using our platform is that it responds to the very real problem of poor documentation inside an otherwise great movement—one that we knew could be even better. To us, it felt a bit like we were repairing a gap in the community of makers and DIY. Within a year of our launch, Fablabs, [Wikifab][8], [Open Source Ecology][9], [Les Petits Debrouillards][10], [Ademe][11], and [Low-Tech Lab][12] had installed our tool on their servers for creating step-by-step tutorials.
+
+Before even putting out a press release, one of our users, Wikifab, began to get praise in national media as "[the Wikipedia of DIY][13]." In just two years, we've seen hundreds of communities launched on their own Dokits, ranging from the fun to the funny to the more formal product guides. Again, the power of the community is the force we want to harness, and it's constantly amazing to see projects—ranging from wind turbines to pet feeders—develop engaging product manuals using the platform we started.
+
+### Opening up open source
+
+Looking back at such a successful first two years, it's clear to us that our choice to use open source was fundamental to how we got where we are as fast as we did. The ability to gather feedback in open source is second-to-none. If a piece of code didn't work, [someone could tell us right away][14]. Why wait on appointments with consultants if you can learn along with those who are already using the service you created?
+
+The level of engagement from the community also revealed the potential (including the potential interest) in our market. [Paris has a good and growing community of developers][15], but open source took us from a pool of a few thousand locally, and brought us to millions of developers all around the world who could become a part of what we were trying to make happen. The open availability of our code also proved reassuring to our users and customers who felt safe that, even if our company went away, the code wouldn't.
+
+If that was most of what we thought might happen as a result of using open source, there were also surprises along the way. By adopting an open method, we found ourselves gaining customers, reputation, and perfectly targeted advertising that we didn't have to pay for out of our limited startup budget. We found that the availability of our code helped improve our recruitment process because we were able to test candidates using our code before we made hires, and this also helped simplify the onboarding journey for those we did hire.
+
+In what we see as a mixture of embarrassment and solidarity, the totally public nature of developers creating code in an open setting also helped drive up quality. People can share feedback with one another, but the public nature of the work also seems to encourage people to do their best. In the spirit of constant improvement and of continually building and rebuilding how Dokit works, supporting the community is something that we know we'd like to do more of and get better at in future.
+
+### Where to next?
+
+Even with the faith we've always had in what we were doing, and seeing the great product manuals that have been developed using our software, it never stops being exciting to see our project grow, and we're certain that the future has good things in store.
+
+In the early days, we found ourselves living a lot under the fear of distributing our knowledge for free. In reality, it was the opposite—open source gave us the ability to very rapidly build a startup that was sustainable from the beginning. Dokit is a platform designed to give its users the confidence to build, assemble, repair, and create entirely new inventions with the support of a community. In hindsight, we found we were doing the same thing by using open source to build a platform.
+
+Just like when doing a repair or assembling a physical product, it's only when you have confidence in your methods that things truly begin to feel right. Now, at the beginning of our third year, we're starting to see growing global interest as the industry responds to [new generations of customers who want to use, reuse, and assemble products][16] that respond to changing homes and lifestyles. By providing the support of an online community, we think we're helping to create circumstances in which people feel more confident in doing things for themselves.
+
+--------------------------------------------------------------------------------
+
+via: https://opensource.com/article/19/5/startups-release-code
+
+作者:[Clément Flipo][a]
+选题:[lujun9972][b]
+译者:[译者ID](https://github.com/译者ID)
+校对:[校对者ID](https://github.com/校对者ID)
+
+本文由 [LCTT](https://github.com/LCTT/TranslateProject) 原创编译,[Linux中国](https://linux.cn/) 荣誉推出
+
+[a]: https://opensource.com/users/cl%C3%A9ment-flipo
+[b]: https://github.com/lujun9972
+[1]: https://opensource.com/sites/default/files/styles/image-full-size/public/lead-images/button_push_open_keyboard_file_organize.png?itok=KlAsk1gx (open source button on keyboard)
+[2]: https://dokit.io/
+[3]: https://dokit.io/9-reasons-to-stop-writing-your-user-manuals-or-work-instructions-with-word-processors/
+[4]: https://medium.com/@gofloaters/5-cheap-ways-to-build-your-mvp-71d6170d5250
+[5]: https://en.wikipedia.org/wiki/MediaWiki
+[6]: https://en.wikipedia.org/wiki/Maker_culture
+[7]: http://fab.cba.mit.edu/about/charter/
+[8]: https://wikifab.org/
+[9]: https://www.opensourceecology.org/
+[10]: http://www.lespetitsdebrouillards.org/
+[11]: https://www.ademe.fr/en
+[12]: http://lowtechlab.org/
+[13]: https://www.20minutes.fr/magazine/economie-collaborative-mag/2428995-20160919-pour-construire-leurs-meubles-eux-memes-ils-creent-le-wikipedia-du-bricolage
+[14]: https://opensource.guide/how-to-contribute/
+[15]: https://www.rudebaguette.com/2013/03/here-are-the-details-on-the-new-developer-school-that-xavier-niel-is-launching-tomorrow/?lang=en
+[16]: https://www.inc.com/ari-zoldan/why-now-is-the-best-time-to-start-a-diy-home-based.html
diff --git a/sources/tech/20190509 5 essential values for the DevOps mindset.md b/sources/tech/20190509 5 essential values for the DevOps mindset.md
new file mode 100644
index 0000000000..e9dafbd673
--- /dev/null
+++ b/sources/tech/20190509 5 essential values for the DevOps mindset.md
@@ -0,0 +1,85 @@
+[#]: collector: (lujun9972)
+[#]: translator: (arrowfeng)
+[#]: reviewer: ( )
+[#]: publisher: ( )
+[#]: url: ( )
+[#]: subject: (5 essential values for the DevOps mindset)
+[#]: via: (https://opensource.com/article/19/5/values-devops-mindset)
+[#]: author: (Brent Aaron Reed https://opensource.com/users/brentaaronreed/users/wpschaub/users/wpschaub/users/wpschaub/users/cobiacomm/users/marcobravo/users/brentaaronreed)
+
+5 essential values for the DevOps mindset
+======
+People and process take more time but are more important than any
+technology "silver bullet" in solving business problems.
+![human head, brain outlined with computer hardware background][1]
+
+Many IT professionals today struggle with adapting to change and disruption. Are you struggling with just trying to keep the lights on, so to speak? Do you feel overwhelmed? This is not uncommon. Today, the status quo is not enough, so IT constantly tries to re-invent itself.
+
+With over 30 years of combined IT experience, we have witnessed how important people and relationships are to IT's ability to be effective and help the business thrive. However, most of the time, our conversations about IT solutions start with technology rather than people and process. The propensity to look for a "silver bullet" to address business and IT challenges is far too common. But you can't just buy innovation, DevOps, or effective teams and ways of working; they need to be nurtured, supported, and guided.
+
+With disruption so prevalent and there being such a critical demand for speed of change, we need both discipline and guardrails. The five essential values for the DevOps mindset, described below, will support the practices that will get us there. These values are not new ideas; they are refactored as we've learned from our experience. Some of the values may be interchangeable, they are flexible, and they guide overall principles that support (like a pillar) these five values.
+
+![5 essential values for the DevOps mindset][2]
+
+### 1\. Feedback from stakeholders is essential
+
+How do we know if we are creating more value for us than for our stakeholders? We need persistent quality data to analyze, inform, and drive better decisions. Relevant information from trusted sources is vital for any business to thrive. We need to listen to and understand what our stakeholders are saying—and not saying—and we need to implement changes in a way that enables us to adjust our thinking—and our processes and technologies—and adapt them as needed to delight our stakeholders. Too often, we see little change, or lots of change for the wrong reasons, because of incorrect information (data). Therefore, aligning change to our stakeholders' feedback is an essential value and helps us focus on what is most important to making our company successful.
+
+> Focus on our stakeholders and their feedback rather than simply changing for the sake of change.
+
+### 2\. Improve beyond the limits of today's processes
+
+We want our products and services to continuously delight our customers—our most important stakeholders—therefore, we need to improve continually. This is not only about quality; it could also mean costs, availability, relevance, and many other goals and factors. Creating repeatable processes or utilizing a common framework is great—they can improve governance and a host of other issues—however, that should not be our end goal. As we look for ways to improve, we must adjust our processes, complemented by the right tech and tools. There may be reasons to throw out a "so-called" framework because not doing so could add waste—or worse, simply "cargo culting" (doing something with of no value or purpose).
+
+> Strive to always innovate and improve beyond repeatable processes and frameworks.
+
+### 3\. No new silos to break down silos
+
+Silos and DevOps are incompatible. We see this all the time: an IT director brings in so-called "experts" to implement agile and DevOps, and what do they do? These "experts" create a new problem on top of the existing problem, which is another silo added to an IT department and a business riddled with silos. Creating "DevOps" titles goes against the very principles of agile and DevOps, which are based on the concept of breaking down silos. In both agile and DevOps, teamwork is essential, and if you don't work in a self-organizing team, you're doing neither of them.
+
+> Inspire and share collaboratively instead of becoming a hero or creating a silo.
+
+### 4\. Knowing your customer means cross-organization collaboration
+
+No part of the business is an independent entity because they all have stakeholders, and the primary stakeholder is always the customer. "The customer is always right" (or the king, as I like to say). The point is, without the customer, there really is no business, and to stay in business today, we need to "differentiate" from our competitors. We also need to know how our customers feel about us and what they want from us. Knowing what the customer wants is imperative and requires timely feedback to ensure the business addresses these primary stakeholders' needs and concerns quickly and responsibly.
+
+![Minimize time spent with build-measure-learn process][3]
+
+Whether it comes from an idea, a concept, an assumption, or direct stakeholder feedback, we need to identify and measure the feature or service our product delivers by using the explore, build, test, deliver lifecycle. Fundamentally, this means that we need to be "plugged into" our organization across the organization. There are no borders in continuous innovation, learning, and DevOps. Thus when we measure across the enterprise, we can understand the whole and take actionable, meaningful steps to improve.
+
+> Measure performance across the organization, not just in a line of business.
+
+### 5\. Inspire adoption through enthusiasm
+
+Not everyone is driven to learn, adapt, and change; however, just like smiles can be infectious, so can learning and wanting to be part of a culture of change. Adapting and evolving within a culture of learning provides a natural mechanism for a group of people to learn and pass on information (i.e., cultural transmission). Learning styles, attitudes, methods, and processes continually evolve so we can improve upon them. The next step is to apply what was learned and improved and share the information with colleagues. Learning does not happen automatically; it takes effort, evaluation, discipline, awareness, and especially communication; unfortunately these are things that tools and automation alone will not provide. Review your processes, automation, tool strategies, and implementation work, make it transparent, and collaborate with your colleagues on reuse and improvement.
+
+> Promote a culture of learning through lean quality deliverables, not just tools and automation.
+
+### Summary
+
+![Continuous goals of DevOps mindset][4]
+
+As our companies adopt DevOps, we continue to champion these five values over any book, website, or automation software. It takes time to adopt this mindset, and this is very different than what we used to do as sysadmins. It's a wholly new way of working that will take many years to mature. Do these principles align with your own? Share them in the comments or on our website, [Agents of chaos][5].
+
+* * *
+
+Can you really do DevOps without sharing scripts or code? DevOps manifesto proponents value cross-...
+
+--------------------------------------------------------------------------------
+
+via: https://opensource.com/article/19/5/values-devops-mindset
+
+作者:[Brent Aaron Reed][a]
+选题:[lujun9972][b]
+译者:[译者ID](https://github.com/译者ID)
+校对:[校对者ID](https://github.com/校对者ID)
+
+本文由 [LCTT](https://github.com/LCTT/TranslateProject) 原创编译,[Linux中国](https://linux.cn/) 荣誉推出
+
+[a]: https://opensource.com/users/brentaaronreed/users/wpschaub/users/wpschaub/users/wpschaub/users/cobiacomm/users/marcobravo/users/brentaaronreed
+[b]: https://github.com/lujun9972
+[1]: https://opensource.com/sites/default/files/styles/image-full-size/public/lead-images/brain_data.png?itok=RH6NA32X (human head, brain outlined with computer hardware background)
+[2]: https://opensource.com/sites/default/files/uploads/devops_mindset_values.png (5 essential values for the DevOps mindset)
+[3]: https://opensource.com/sites/default/files/uploads/devops_mindset_minimze-time.jpg (Minimize time spent with build-measure-learn process)
+[4]: https://opensource.com/sites/default/files/uploads/devops_mindset_continuous.png (Continuous goals of DevOps mindset)
+[5]: http://agents-of-chaos.org
diff --git a/sources/tech/20190509 A day in the life of an open source performance engineering team.md b/sources/tech/20190509 A day in the life of an open source performance engineering team.md
new file mode 100644
index 0000000000..373983e8bc
--- /dev/null
+++ b/sources/tech/20190509 A day in the life of an open source performance engineering team.md
@@ -0,0 +1,138 @@
+[#]: collector: (lujun9972)
+[#]: translator: ( )
+[#]: reviewer: ( )
+[#]: publisher: ( )
+[#]: url: ( )
+[#]: subject: (A day in the life of an open source performance engineering team)
+[#]: via: (https://opensource.com/article/19/5/life-performance-engineer)
+[#]: author: (Aakarsh Gopi https://opensource.com/users/aakarsh/users/portante/users/anaga/users/gameloid)
+
+A day in the life of an open source performance engineering team
+======
+Collaborating with the community enables performance engineering to
+address the confusion and complexity that come with working on a broad
+spectrum of products.
+![Team checklist and to dos][1]
+
+In today's world, open source software solutions are a collaborative effort of the community. Can a performance engineering team operate the same way, by collaborating with the community to address the confusion and complexity that come with working on a broad spectrum of products?
+
+To answer that question, we need to explore some basic questions:
+
+ * What does a performance engineering team do?
+ * How does a performance engineering team fulfill its responsibilities?
+ * How are open source tools developed or leveraged for performance analysis?
+
+
+
+The term "performance engineering" has different meanings, which causes difficulty in figuring out a performance engineering team's responsibilities. Adding to the confusion, a team may be charged with working on a broad spectrum of products, ranging from an operating system like RHEL, whose performance can be significantly impacted by hardware components (CPU caches, network interface controllers, disk technologies, etc.), to something much higher up in the stack like Kubernetes, which comes with the added challenges of operating at scale without compromising on performance.
+
+Performance engineering has progressed a lot since the days of running manual A/B testing and single-system benchmarks. Now, these teams test cloud infrastructures and add machine learning classifiers as a component in the CI/CD pipeline for identifying performance regression in releases of products.
+
+### What does a performance engineering team do?
+
+A performance engineering team is generally responsible for the following (among other things):
+
+ * Identifying potential performance issues
+ * Identifying any scale issues that could occur
+ * Developing tuning guides and/or tools that would enable the user to achieve the most out of a product
+ * Developing guides and/or working with customers to help with capacity planning
+ * Providing customers with performance expectations for different use cases of the product
+
+
+
+The mission of our specific team is to:
+
+ * Establish performance and scale leadership of the Red Hat portfolio; the scope includes component level, system, and solution analysis
+ * Collaborate with engineering, product management, product marketing, and Customer Experience and Engagement (CEE), as well as hardware and software partners
+ * Deliver public-facing guidance, internal enablement, and continuous integration tests
+
+
+
+Our team fulfills our mission in the following ways:
+
+ * We work with product teams to set performance goals and develop performance tests to run against those products deployed to see how they measure up to those goals.
+ * We also work to re-run performance tests to ensure there are no regressions in behaviors.
+ * We develop open source tooling to achieve our product performance goals, making them available to the communities where the products are derived to re-create what we do.
+ * We work to be transparent and open about how we do performance engineering; sharing these methods and approaches benefits communities, allowing them to reuse our work, and benefits us by leveraging the work they contribute with these tools.
+
+
+
+### How does a performance engineering team fulfill its responsibilities?
+
+Meeting these responsibilities requires collaboration with other teams, such as product management, development, QA/QE, documentation, and consulting, and with the communities.
+
+_Collaboration_ allows a team to be successful by pulling together team members' diverse knowledge and experience. A performance engineering team builds tools to share their knowledge both within the team and with the community, furthering the value of collaboration.
+
+Our performance engineering team achieves success through:
+
+ * **Collaboration:** _Intra_ -team collaboration is as important as _inter_ -team collaboration for our performance engineering team
+ * Most performance engineers tend to create a niche for themselves in one or more sub-disciplines of performance engineering via tooling, performance analysis, systems knowledge, systems configuration, and such. Our team is composed of engineers with knowledge of setting up/configuring systems across the product stack, those who know how a configuration option would affect the system's performance, and so on. Our team's success is heavily reliant on effective collaboration between performance engineers on the team.
+ * Our team works closely with other organizations at various levels within Red Hat and the communities where our products are derived.
+ * **Knowledge:** To understand the performance implications of configuration and/or system changes, deep knowledge of the product alone is not sufficient.
+ * Our team has the knowledge to cover performance across all levels of the stack:
+ * Hardware setup and configuration
+ * Networking and scale considerations
+ * Operating system setup and configuration (Linux kernel, userspace stack)
+ * Storage sub-systems (Ceph)
+ * Cloud infrastructure (OpenStack, RHV)
+ * Cloud deployments (OpenShift/Kubernetes)
+ * Product architectures
+ * Software technologies (databases like Postgres; software-defined networking and storage)
+ * Product interactions with the underlying hardware
+ * Tooling to monitor and accomplish repeatable benchmarking
+ * **Tooling:** The differentiator for our performance engineering team is the data collected through its tools to help tackle performance analysis complexity in the environments where our products are deployed.
+
+
+
+### How are open source tools developed or leveraged for performance analysis?
+
+Tooling is no longer a luxury but a need for today's performance engineering teams. With today's product solutions being so complex (and increasing in complexity as more solutions are composed to solve ever-larger problems), we need tools to help us run performance test suites in a repeatable manner, collect data about those runs, and help us distill that data so it becomes understandable and usable.
+
+Yet, no performance engineering team is judged on how performance analysis is done, but rather on the results achieved from this analysis.
+
+This tension can be resolved by collaboratively developing tools. A performance engineering team can't spend all its time developing tools, since that would prevent it from effectively collecting data. By developing its tools in a collaborative manner, a team can leverage work from the community to make further progress while still generating the result by which they will be measured.
+
+Tooling is the backbone of our performance engineering team, and we strive to use the tools already available upstream. When no tools are available in the community that fit our needs, we've built tools that help us achieve our goals and made them available to the community. Open sourcing our tools has helped us immensely because we receive contributions from our competitors and partners, allowing us to solve problems collectively through collaboration.
+
+![Performance Engineering Tools][2]
+
+Following are some of the tools our team has contributed to and rely upon for our work:
+
+ * **[Perf-c2c][3]:** Is your performance impacted by false sharing in CPU caches? The perf-c2c tool can help you tackle this problem by helping you inspect the cache lines where false sharing is detected and understand the readers/writers accessing those cache lines along with the offsets where those accesses occurred. You can read more about this tool on [Joe Mario's blog][4].
+ * **[Pbench][5]:** Do you repeat the same steps when collecting data about performance, but fail to do it consistently? Or do you find it difficult to compare results with others because you're collecting different configuration data? Pbench is a tool that attempts to standardize the way data is collected for performance so comparisons and historical reviews are much easier. Pbench is at the heart of our tooling efforts, as most of the other tools consume it in some form. Pbench is a Swiss Army Knife, as it allows the user to run benchmarks such as fio, uperf, or custom, user-defined tests while gathering metrics through tools such as sar, iostat, and pidstat, standardizing the methods of collecting configuration data about the environment. Pbench provides a dashboard UI to help review and analyze the data collected.
+ * **[Browbeat][6]:** Do you want to monitor a complex environment such as an OpenStack cluster while running tests? Browbeat is the solution, and its power lies in its ability to collect comprehensive data, ranging from logs to system metrics, about an OpenStack cluster while it orchestrates workloads. Browbeat can also monitor the OpenStack cluster while users run test/workloads of their choice either manually or through their own automation.
+ * **[Ripsaw][7]:** Do you want to compare the performance of different Kubernetes distros against the same platform? Do you want to compare the performance of the same Kubernetes distros deployed on different platforms? Ripsaw is a relatively new tool created to run workloads through Kubernetes native calls using the Ansible operator framework to provide solutions to the above questions. Ripsaw's unique selling point is that it can run against any kind of Kubernetes distribution, thus it would run the same against a Kubernetes cluster, on Minikube, or on an OpenShift cluster deployed on OpenStack or bare metal.
+ * **[ClusterLoader][8]:** Ever wondered how an OpenShift component would perform under different cluster states? If you are looking for an answer that can stress the cluster, ClusterLoader will help. The team has generalized the tool so it can be used with any Kubernetes distro. It is currently hosted in the [perf-tests repository][9].
+
+
+
+### Bottom line
+
+Given the scale at which products are evolving rapidly, performance engineering teams need to build tooling to help them keep up with products' evolution and diversification.
+
+Open source-based software solutions are a collaborative effort of the community. Our performance engineering team operates in the same way, collaborating with the community to address the confusion and complexity that comes with working on a broad spectrum of products. By developing our tools in a collaborative manner and using tools from the community, we are leveraging the community's work to make progress, while still generating the results we are measured on.
+
+_Collaboration_ is our key to accomplish our goals and ensure the success of our team.
+
+--------------------------------------------------------------------------------
+
+via: https://opensource.com/article/19/5/life-performance-engineer
+
+作者:[Aakarsh Gopi ][a]
+选题:[lujun9972][b]
+译者:[译者ID](https://github.com/译者ID)
+校对:[校对者ID](https://github.com/校对者ID)
+
+本文由 [LCTT](https://github.com/LCTT/TranslateProject) 原创编译,[Linux中国](https://linux.cn/) 荣誉推出
+
+[a]: https://opensource.com/users/aakarsh/users/portante/users/anaga/users/gameloid
+[b]: https://github.com/lujun9972
+[1]: https://opensource.com/sites/default/files/styles/image-full-size/public/lead-images/todo_checklist_team_metrics_report.png?itok=oB5uQbzf (Team checklist and to dos)
+[2]: https://opensource.com/sites/default/files/uploads/performanceengineeringtools.png (Performance Engineering Tools)
+[3]: http://man7.org/linux/man-pages/man1/perf-c2c.1.html
+[4]: https://joemario.github.io/blog/2016/09/01/c2c-blog/
+[5]: https://github.com/distributed-system-analysis/pbench
+[6]: https://github.com/openstack/browbeat
+[7]: https://github.com/cloud-bulldozer/ripsaw
+[8]: https://github.com/openshift/origin/tree/master/test/extended/cluster
+[9]: https://github.com/kubernetes/perf-tests/tree/master/clusterloader
diff --git a/sources/tech/20190509 Query freely available exchange rate data with ExchangeRate-API.md b/sources/tech/20190509 Query freely available exchange rate data with ExchangeRate-API.md
new file mode 100644
index 0000000000..3db9708c81
--- /dev/null
+++ b/sources/tech/20190509 Query freely available exchange rate data with ExchangeRate-API.md
@@ -0,0 +1,162 @@
+[#]: collector: (lujun9972)
+[#]: translator: ( )
+[#]: reviewer: ( )
+[#]: publisher: ( )
+[#]: url: ( )
+[#]: subject: (Query freely available exchange rate data with ExchangeRate-API)
+[#]: via: (https://opensource.com/article/19/5/exchange-rate-data)
+[#]: author: (Chris Hermansen https://opensource.com/users/clhermansen)
+
+Query freely available exchange rate data with ExchangeRate-API
+======
+In this interview, ExchangeRate-API's founder explains why exchange rate
+data should be freely accessible to developers who want to build useful
+stuff.
+![scientific calculator][1]
+
+Last year, [I wrote about][2] using the Groovy programming language to access foreign exchange rate data from an API to simplify my expense records. I showed how two exchange rate sites, [fixer.io][3] and apilayer.net (now [apilayer.com][4]), could provide the data I needed, allowing me to convert between Indian rupees (INR) and Canadian dollars (CAD) using the former, and Chilean pesos (CLP) and Canadian dollars using the latter.
+
+Recently, David over at [ExchangeRate-API.com][5] reached out to me to say, "the free API you mentioned (Fixer) has been bought by CurrencyLayer and had its no-signup/unlimited access deprecated." He also told me, "I run a free API called ExchangeRate-API.com that has the same JSON format as the original Fixer, doesn't require any signup, and allows unlimited requests."
+
+After exchanging a few emails, we decided to turn our conversation into an interview. Below the interview, you can find scripts and usage instructions. (The interview has been edited slightly for clarity.)
+
+### About ExchangeRate-API
+
+_**Chris:** How is ExchangeRate-API different from other online exchange-rate services? What motivates you to provide this service?_
+
+**David:** When I started ExchangeRate-API with a friend in 2010, we built and released it for free because we really needed this service for another project and couldn't find one despite extensive googling. There are now around 20 such APIs offering quite a few different approaches. Over the years, I've tried a number of different approaches, but offering quality data for free has always proven the most popular. I'm also motivated by the thought that this data should be freely accessible to developers who want to build useful stuff even if they don't have a budget.
+
+Thus, the main difference with our currency conversion API is that it's unlimited and requires no signup. This also makes starting to use it really fast—you literally just copy the endpoint URL and you're good to go.
+
+There are one or two other free and unlimited APIs, but these typically just serve the daily reference rates provided by the European Central Bank. ExchangeRate-API collects the public reference rates from a number of central banks and then blends them to reduce the risk of outlying values. It also does acceptance checking to ensure the rates aren't wildly wrong (for instance an inverted data capture recording US dollars to CLP instead of CLP to USD) and weights different sources based on their historical accuracy. This makes the service quite reliable. I'm currently working on a transparency project to compare and show the accuracy of this public reference rate blend against a proprietary data source so potential users can make more informed decisions on what type of currency data service is right for them.
+
+_**Chris:** I'm delighted that you've included Canadian dollars and Indian rupees, as that is one problem I need to solve. I'm sad to see that you don't have Chilean pesos (another problem I need to solve). Can you tell us how you select the list of currencies? Do you anticipate adding other currencies to your list?_
+
+**David:** Since my main aim for this service is to offer stable and reliable exchange rate data, I only include currencies when there is more than one data source for that currency code. For instance, after you mentioned that you're looking for CLP data, I added the daily reference rates published by the Central Bank of Chile to our system. If I can find another source that includes CLP, it would be included in our list of supported currencies, but until then, unfortunately not. The goal is to support as many currencies as possible.
+
+One thing to note is that, for some currencies, the service has the minimum two sources, but a few currency pairs (for instance USD/EUR) are included in almost every set of public reference rates. The transparent accuracy project I mentioned will hopefully make this difference clear so that users can understand why our USD/EUR rate might be more accurate than less common pairs like CLP/INR and also the degree of variance in accuracy between the pairs. It will take some work to make showing this information quick and easy to understand.
+
+### The API's architecture
+
+_**Chris:** Can you tell us a bit about your API's architecture? Do you use open source components to deliver your service?_
+
+**David:** I exclusively use open source software to run ExchangeRate-API. I'm definitely an open source enthusiast and am always getting friends to switch to open source, explaining licenses, and donating when I can to the projects I use most. I also try to email maintainers of projects I use to say thanks, but I don't do this enough.
+
+The stack is currently Ubuntu LTS, MariaDB, Nginx, PHP 7, and Memcached. I also use Bootstrap and Picnic open source CSS frameworks. I use Let's Encrypt for HTTPS certificates via the Electronic Frontier Foundation's open source ACME client, [Certbot][6]. The service makes extensive use of classic tools like UFW/iptables, cURL, OpenSSH, and Git.
+
+My approach is typically to keep everything as simple as possible while using the tried-and-tested open source building blocks. For a project that aims to _always_ be available for users to convert currencies, this feels like the best route to reliability. I love reading about innovative new projects that could be useful for a project like this (for example, CockroachDB), but I wouldn't use them until they are considered really bulletproof. Obviously, things like [Heartbleed][7] show that there are risks with "boring" projects too—but I think these are easier to manage than the potential for unknown risks with newer, cutting-edge projects.
+
+In terms of the infrastructure setup, I've steadily built and improved the system over the last nine years, and it now comprises roughly three tiers. The main cluster runs on Amazon Web Services (AWS) and consists of Ubuntu EC2 servers and a high-availability MariaDB relational database service (RDS) instance. The EC2 instances are spread across multiple AWS Availability Zones and fronted by the managed AWS Elastic Load Balancing (ELB) service. Between the RDS database instance with automated cross-zone failover and the ELB-fronted EC2 instances spread across availability zones, this setup is exceptionally available. It is, however, only in one locale. So I've set up a second tier of virtual private server (VPS) instances in different geographic locations to reduce latency and distribute the load away from the more expensive AWS infrastructure. These are currently with Linode, but I have also used DigitalOcean and Vultr recently.
+
+Finally, this is all protected behind Cloudflare. With a free service, it's inevitable that some users will choose to abuse the system, and Cloudflare is an amazing product that's vital to ExchangeRate-API. Our servers can be protected and our users get low-latency, in-region caches. Cloudflare is set up with both the load balancing and traffic steering products to reduce latency and instantly shift traffic from unhealthy parts of the infrastructure to available origins.
+
+With this very redundant approach, there hasn't been downtime as a result of infrastructure problems or user load for around three years. The few periods of degraded service experienced in this time are all due to issues with code, deployment strategy, or config mistakes. The setup currently handles hundreds of millions of requests per month with low load levels and manageable costs, so there's plenty of room for growth.
+
+The actual application code is PHP with heavy use of Memcached. Memcached is an amazing open source project started by Brad Fitzpatrick in 2003. It's not particularly glamorous, but it is an incredibly reliable and performant distributed in-memory key value store.
+
+### Engaging with the open source community
+
+_**Chris:** There is an impressive amount of open source in your configuration. How do you engage with the broader community of users in these projects?_
+
+**David:** I really struggle with the best way to be a good open source citizen while running a side project SaaS. I've considered building an open source library of some sort and releasing it, but I haven't thought of something that hasn't already been done and that I would be able to make the time commitment to reliably maintain. I'd only start a project like this if I could be confident I'd have the time to ensure users who choose the project wouldn't suddenly find themselves depending on abandonware. I've also looked into contributing to the projects that ExchangeRate-API depends on, but since I only use the biggest, most established options, I lack the expertise to make a meaningful contribution to such serious projects.
+
+I'm currently working on a new "Pro" plan for the service and I'm going to set a percentage of this income to donate to my open source dependencies. This still feels like a bandage though—answering this question makes me realize I need to put more time into starting an open source project that calls ExchangeRate-API home!
+
+### Looking ahead
+
+_**Chris:** We can only query the latest exchange rate, but it appears that you may be offering historical rates sometime later this year. Can you tell us more about the technical challenges with serving up historical data?_
+
+**David:** There is a dataset of historical rates blended using our same algorithm from multiple central bank reference sets. However, I stopped new signups for it due to some issues with the data quality. The dataset reaches back to 1990, and there were a few earlier periods that need better data validation. As such, I'm building a better system for checking and comparing the data as it's ingested as well as adding an additional data source. The plan is to have a clean and more comprehensively verified-as-accurate dataset available later this year.
+
+In terms of the technical side of things, historical data is slightly more complex than live data. Compared to the live dataset (which is just a few bytes) the historical data is millions of database rows. This data was originally served from the database infrastructure with a long time-to-live (TTL) intermediary-caching layer. This was largely performant but struggled in situations where users wanted to dump the entire dataset as fast as the network could handle it. If the cache was sufficiently warm, this was fine, but if reboots, new server deployments, etc. had taken place recently, these big request sets would "miss" enough on the cache that the database would have problematic load spikes.
+
+Obviously, the goal is an infrastructure that can handle even aggressive use cases with normal performance, so the new historical rates dataset will be accompanied by a preemptive in-memory cache rather than a request-driven one. Thankfully, RAM is cheap these days, and putting a couple hundred megabytes of data entirely into RAM is a plausible approach even for a small project like ExchangeRate-API.com.
+
+_**Chris:** It sounds like you've been through quite a few iterations of this service to get to where it is today! Where do you see it going in the next few years?_
+
+**David:** I'd aim for it to have reached coverage of every world currency so that anyone looking for this sort of software can easily and programmatically get the exchange rates they need for free.
+
+I'd also definitely like to have an affordable Pro plan that really resonates with users. Getting this right would mean better infrastructure and lower latency for free users as well.
+
+Finally, I'd like to have some sort of useful open source library under the ExchangeRate-API banner. Starting a small project that finds an enthusiastic community would be really rewarding. It's great to run something that's free-as-in-beer, but it would be even better if part of it was free-as-in-speech, as well.
+
+### How to use the service
+
+It's easy enough to test out the service using **wget** , as follows:
+
+
+```
+clh@marseille:~$ wget -O -
+\--2019-04-26 13:48:23--
+Resolving api.exchangerate-api.com (api.exchangerate-api.com)... 2606:4700:20::681a:c80, 2606:4700:20::681a:d80, 104.26.13.128, ...
+Connecting to api.exchangerate-api.com (api.exchangerate-api.com)|2606:4700:20::681a:c80|:443... connected.
+HTTP request sent, awaiting response... 200 OK
+Length: unspecified [application/json]
+Saving to: ‘STDOUT’
+
+\- [<=>
+] 0 --.-KB/s {"base":"INR","date":"2019-04-26","time_last_updated":1556236800,"rates":{"INR":1,"AUD":0.020343,"BRL":0.056786,"CAD":0.019248,"CHF":0.014554,"CNY":0.096099,"CZK":0.329222,"DKK":0.095497,"EUR":0.012789,"GBP":0.011052,"HKD":0.111898,"HUF":4.118615,"IDR":199.61769,"ILS":0.051749,"ISK":1.741659,"JPY":1.595527,"KRW":16.553091,"MXN":0.272383,"MYR":0.058964,"NOK":0.123365,"NZD":0.02161,"PEN":0.047497,"PHP":0.744974,"PLN":0.054927,"RON":0.060923,"RUB":0.921808,"SAR":0.053562,"SEK":0.135226,"SGD":0.019442,"THB":0.457501,"TRY":0- [ <=> ] 579 --.-KB/s in 0s
+
+2019-04-26 13:48:23 (15.5 MB/s) - written to stdout [579]
+
+clh@marseille:~$
+```
+
+The result is returned as a JSON payload, giving conversion rates from Indian rupees (the currency I requested in the URL) to all the currencies handled by ExchangeRate-API.
+
+The Groovy shell can access the API:
+
+
+```
+clh@marseille:~$ groovysh
+Groovy Shell (2.5.3, JVM: 1.8.0_212)
+Type ':help' or ':h' for help.
+\----------------------------------------------------------------------------------------------------------------------------------
+groovy:000> import groovy.json.JsonSlurper
+===> groovy.json.JsonSlurper
+groovy:000> result = (new JsonSlurper()).parse(
+groovy:001> new InputStreamReader((new URL('))
+groovy:002> )
+===> [base:INR, date:2019-04-26, time_last_updated:1556236800, rates:[INR:1, AUD:0.020343, BRL:0.056786, CAD:0.019248, CHF:0.014554, CNY:0.096099, CZK:0.329222, DKK:0.095497, EUR:0.012789, GBP:0.011052, HKD:0.111898, HUF:4.118615, IDR:199.61769, ILS:0.051749, ISK:1.741659, JPY:1.595527, KRW:16.553091, MXN:0.272383, MYR:0.058964, NOK:0.123365, NZD:0.02161, PEN:0.047497, PHP:0.744974, PLN:0.054927, RON:0.060923, RUB:0.921808, SAR:0.053562, SEK:0.135226, SGD:0.019442, THB:0.457501, TRY:0.084362, TWD:0.441385, USD:0.014255, ZAR:0.206271]]
+groovy:000>
+```
+
+The same JSON payload is returned as a result of the Groovy JSON slurper operating on the URL. Of course, since this is Groovy, the JSON is converted into a Map, so you can do stuff like this:
+
+
+```
+groovy:000> println result.base
+INR
+===> null
+groovy:000> println result.date
+2019-04-26
+===> null
+groovy:000> println result.rates.CAD
+0.019248
+===> null
+```
+
+And that's it!
+
+Do you use ExchangeRate-API or a similar service? Share how you use exchange rate data in the comments.
+
+--------------------------------------------------------------------------------
+
+via: https://opensource.com/article/19/5/exchange-rate-data
+
+作者:[Chris Hermansen ][a]
+选题:[lujun9972][b]
+译者:[译者ID](https://github.com/译者ID)
+校对:[校对者ID](https://github.com/校对者ID)
+
+本文由 [LCTT](https://github.com/LCTT/TranslateProject) 原创编译,[Linux中国](https://linux.cn/) 荣誉推出
+
+[a]: https://opensource.com/users/clhermansen
+[b]: https://github.com/lujun9972
+[1]: https://opensource.com/sites/default/files/styles/image-full-size/public/lead-images/calculator_money_currency_financial_tool.jpg?itok=2QMa1y8c (scientific calculator)
+[2]: https://opensource.com/article/18/3/groovy-calculate-foreign-exchange
+[3]: https://fixer.io/
+[4]: https://apilayer.com/
+[5]: https://www.exchangerate-api.com/
+[6]: https://certbot.eff.org/
+[7]: https://en.wikipedia.org/wiki/Heartbleed
diff --git a/sources/tech/20190510 5 open source hardware products for the great outdoors.md b/sources/tech/20190510 5 open source hardware products for the great outdoors.md
new file mode 100644
index 0000000000..357fbfdcb8
--- /dev/null
+++ b/sources/tech/20190510 5 open source hardware products for the great outdoors.md
@@ -0,0 +1,96 @@
+[#]: collector: (lujun9972)
+[#]: translator: ( )
+[#]: reviewer: ( )
+[#]: publisher: ( )
+[#]: url: ( )
+[#]: subject: (5 open source hardware products for the great outdoors)
+[#]: via: (https://opensource.com/article/19/5/hardware-outdoors)
+[#]: author: (Michael Weinberg https://opensource.com/users/mweinberg/users/aliciagibb)
+
+5 open source hardware products for the great outdoors
+======
+Here's some equipment you can buy or make yourself for hitting the great
+outdoors, no generators or batteries required.
+![Tree clouds][1]
+
+When people think about open source hardware, they often think about the general category of electronics that can be soldered and needs batteries. While there are [many][2] fantastic open source pieces of electronics, the overall category of open source hardware is much broader. This month we take a look at open source hardware that you can take out into the world, no power outlet or batteries required.
+
+### Hummingbird Hammocks
+
+[Hummingbird Hammocks][3] offers an entire line of open source camping gear. You can set up an open source [rain tarp][4]...
+
+![An open source rain tarp from Hummingbird Hammocks][5]
+
+...with open source [friction adjusters][6]
+
+![Open source friction adjusters from Hummingbird Hammocks.][7]
+
+Open source friction adjusters from Hummingbird Hammocks.
+
+...over your open source [hammock][8]
+
+![An open source hammock from Hummingbird Hammocks.][9]
+
+An open source hammock from Hummingbird Hammocks.
+
+...hung with open source [tree straps][10].
+
+![Open source tree straps from Hummingbird Hammocks.][11]
+
+Open source tree straps from Hummingbird Hammocks.
+
+The design for each of these items is fully documented, so you can even use them as a starting point for making your own outdoor gear (if you are willing to trust friction adjusters you design yourself).
+
+### Openfoil
+
+[Openfoil][12] is an open source hydrofoil for kitesurfing. Hydrofoils are attached to the bottom of kiteboards and allow the rider to rise out of the water. This aspect of the design makes riding in low wind situations and with smaller kites easier. It can also reduce the amount of noise the board makes on the water, making for a quieter experience. Because this hydrofoil is open source you can customize it to your needs and adventure tolerance.
+
+![Openfoil, an open source hydrofoil for kitesurfing.][13]
+
+Openfoil, an open source hydrofoil for kitesurfing.
+
+### Solar water heater
+
+If you prefer your outdoors-ing a bit closer to home, you could build this open source [solar water heater][14] created by the [Anisa Foundation][15]. This appliance focuses energy from the sun to heat water that can then be used in your home, letting you reduce your carbon footprint without having to give up long, hot showers. Of course, you can also [monitor its temperature ][16]over the internet if you need to feel connected.
+
+![An open source solar water heater from the Anisa Foundation.][17]
+
+An open source solar water heater from the Anisa Foundation.
+
+## Wrapping up
+
+As these projects make clear, open source hardware is more than just electronics. You can take it with you to the woods, to the beach, or just to your roof. Next month we’ll talk about open source instruments and musical gear. Until then, [certify][18] your open source hardware!
+
+Learn how and why you may want to start using the Open Source Hardware Certification logo on an...
+
+--------------------------------------------------------------------------------
+
+via: https://opensource.com/article/19/5/hardware-outdoors
+
+作者:[Michael Weinberg][a]
+选题:[lujun9972][b]
+译者:[译者ID](https://github.com/译者ID)
+校对:[校对者ID](https://github.com/校对者ID)
+
+本文由 [LCTT](https://github.com/LCTT/TranslateProject) 原创编译,[Linux中国](https://linux.cn/) 荣誉推出
+
+[a]: https://opensource.com/users/mweinberg/users/aliciagibb
+[b]: https://github.com/lujun9972
+[1]: https://opensource.com/sites/default/files/styles/image-full-size/public/lead-images/life_tree_clouds.png?itok=b_ftihhP (Tree clouds)
+[2]: https://certification.oshwa.org/list.html
+[3]: https://hummingbirdhammocks.com/
+[4]: https://certification.oshwa.org/us000102.html
+[5]: https://opensource.com/sites/default/files/uploads/01-hummingbird_hammocks_rain_tarp.png (An open source rain tarp from Hummingbird Hammocks)
+[6]: https://certification.oshwa.org/us000105.html
+[7]: https://opensource.com/sites/default/files/uploads/02-hummingbird_hammocks_friction_adjusters_400_px.png (Open source friction adjusters from Hummingbird Hammocks.)
+[8]: https://certification.oshwa.org/us000095.html
+[9]: https://opensource.com/sites/default/files/uploads/03-hummingbird_hammocks_hammock_400_px.png (An open source hammock from Hummingbird Hammocks.)
+[10]: https://certification.oshwa.org/us000098.html
+[11]: https://opensource.com/sites/default/files/uploads/04-hummingbird_hammocks_tree_straps_400_px_0.png (Open source tree straps from Hummingbird Hammocks.)
+[12]: https://certification.oshwa.org/fr000004.html
+[13]: https://opensource.com/sites/default/files/uploads/05-openfoil-original_size.png (Openfoil, an open source hydrofoil for kitesurfing.)
+[14]: https://certification.oshwa.org/mx000002.html
+[15]: http://www.fundacionanisa.org/index.php?lang=en
+[16]: https://thingspeak.com/channels/72565
+[17]: https://opensource.com/sites/default/files/uploads/06-solar_water_heater_500_px.png (An open source solar water heater from the Anisa Foundation.)
+[18]: https://certification.oshwa.org/
diff --git a/sources/tech/20190510 Check storage performance with dd.md b/sources/tech/20190510 Check storage performance with dd.md
new file mode 100644
index 0000000000..8cdea81f69
--- /dev/null
+++ b/sources/tech/20190510 Check storage performance with dd.md
@@ -0,0 +1,432 @@
+[#]: collector: (lujun9972)
+[#]: translator: ( )
+[#]: reviewer: ( )
+[#]: publisher: ( )
+[#]: url: ( )
+[#]: subject: (Check storage performance with dd)
+[#]: via: (https://fedoramagazine.org/check-storage-performance-with-dd/)
+[#]: author: (Gregory Bartholomew https://fedoramagazine.org/author/glb/)
+
+Check storage performance with dd
+======
+
+![][1]
+
+This article includes some example commands to show you how to get a _rough_ estimate of hard drive and RAID array performance using the _dd_ command. Accurate measurements would have to take into account things like [write amplification][2] and [system call overhead][3], which this guide does not. For a tool that might give more accurate results, you might want to consider using [hdparm][4].
+
+To factor out performance issues related to the file system, these examples show how to test the performance of your drives and arrays at the block level by reading and writing directly to/from their block devices. **WARNING** : The _write_ tests will destroy any data on the block devices against which they are run. **Do not run them against any device that contains data you want to keep!**
+
+### Four tests
+
+Below are four example dd commands that can be used to test the performance of a block device:
+
+ 1. One process reading from $MY_DISK:
+
+```
+# dd if=$MY_DISK of=/dev/null bs=1MiB count=200 iflag=nocache
+```
+
+ 2. One process writing to $MY_DISK:
+
+```
+# dd if=/dev/zero of=$MY_DISK bs=1MiB count=200 oflag=direct
+```
+
+ 3. Two processes reading concurrently from $MY_DISK:
+
+```
+# (dd if=$MY_DISK of=/dev/null bs=1MiB count=200 iflag=nocache &); (dd if=$MY_DISK of=/dev/null bs=1MiB count=200 iflag=nocache skip=200 &)
+```
+
+ 4. Two processes writing concurrently to $MY_DISK:
+
+```
+# (dd if=/dev/zero of=$MY_DISK bs=1MiB count=200 oflag=direct &); (dd if=/dev/zero of=$MY_DISK bs=1MiB count=200 oflag=direct skip=200 &)
+```
+
+
+
+
+– The _iflag=nocache_ and _oflag=direct_ parameters are important when performing the read and write tests (respectively) because without them the dd command will sometimes show the resulting speed of transferring the data to/from [RAM][5] rather than the hard drive.
+
+– The values for the _bs_ and _count_ parameters are somewhat arbitrary and what I have chosen should be large enough to provide a decent average in most cases for current hardware.
+
+– The _null_ and _zero_ devices are used for the destination and source (respectively) in the read and write tests because they are fast enough that they will not be the limiting factor in the performance tests.
+
+– The _skip=200_ parameter on the second dd command in the concurrent read and write tests is to ensure that the two copies of dd are operating on different areas of the hard drive.
+
+### 16 examples
+
+Below are demonstrations showing the results of running each of the above four tests against each of the following four block devices:
+
+ 1. MY_DISK=/dev/sda2 (used in examples 1-X)
+ 2. MY_DISK=/dev/sdb2 (used in examples 2-X)
+ 3. MY_DISK=/dev/md/stripped (used in examples 3-X)
+ 4. MY_DISK=/dev/md/mirrored (used in examples 4-X)
+
+
+
+A video demonstration of the these tests being run on a PC is provided at the end of this guide.
+
+Begin by putting your computer into _rescue_ mode to reduce the chances that disk I/O from background services might randomly affect your test results. **WARNING** : This will shutdown all non-essential programs and services. Be sure to save your work before running these commands. You will need to know your _root_ password to get into rescue mode. The _passwd_ command, when run as the root user, will prompt you to (re)set your root account password.
+
+```
+$ sudo -i
+# passwd
+# setenforce 0
+# systemctl rescue
+```
+
+You might also want to temporarily disable logging to disk:
+
+```
+# sed -r -i.bak 's/^#?Storage=.*/Storage=none/' /etc/systemd/journald.conf
+# systemctl restart systemd-journald.service
+```
+
+If you have a swap device, it can be temporarily disabled and used to perform the following tests:
+
+```
+# swapoff -a
+# MY_DEVS=$(mdadm --detail /dev/md/swap | grep active | grep -o "/dev/sd.*")
+# mdadm --stop /dev/md/swap
+# mdadm --zero-superblock $MY_DEVS
+```
+
+#### Example 1-1 (reading from sda)
+
+```
+# MY_DISK=$(echo $MY_DEVS | cut -d ' ' -f 1)
+# dd if=$MY_DISK of=/dev/null bs=1MiB count=200 iflag=nocache
+```
+
+```
+200+0 records in
+200+0 records out
+209715200 bytes (210 MB, 200 MiB) copied, 1.7003 s, 123 MB/s
+```
+
+#### Example 1-2 (writing to sda)
+
+```
+# MY_DISK=$(echo $MY_DEVS | cut -d ' ' -f 1)
+# dd if=/dev/zero of=$MY_DISK bs=1MiB count=200 oflag=direct
+```
+
+```
+200+0 records in
+200+0 records out
+209715200 bytes (210 MB, 200 MiB) copied, 1.67117 s, 125 MB/s
+```
+
+#### Example 1-3 (reading concurrently from sda)
+
+```
+# MY_DISK=$(echo $MY_DEVS | cut -d ' ' -f 1)
+# (dd if=$MY_DISK of=/dev/null bs=1MiB count=200 iflag=nocache &); (dd if=$MY_DISK of=/dev/null bs=1MiB count=200 iflag=nocache skip=200 &)
+```
+
+```
+200+0 records in
+200+0 records out
+209715200 bytes (210 MB, 200 MiB) copied, 3.42875 s, 61.2 MB/s
+200+0 records in
+200+0 records out
+209715200 bytes (210 MB, 200 MiB) copied, 3.52614 s, 59.5 MB/s
+```
+
+#### Example 1-4 (writing concurrently to sda)
+
+```
+# MY_DISK=$(echo $MY_DEVS | cut -d ' ' -f 1)
+# (dd if=/dev/zero of=$MY_DISK bs=1MiB count=200 oflag=direct &); (dd if=/dev/zero of=$MY_DISK bs=1MiB count=200 oflag=direct skip=200 &)
+```
+
+```
+200+0 records out
+209715200 bytes (210 MB, 200 MiB) copied, 3.2435 s, 64.7 MB/s
+200+0 records in
+200+0 records out
+209715200 bytes (210 MB, 200 MiB) copied, 3.60872 s, 58.1 MB/s
+```
+
+#### Example 2-1 (reading from sdb)
+
+```
+# MY_DISK=$(echo $MY_DEVS | cut -d ' ' -f 2)
+# dd if=$MY_DISK of=/dev/null bs=1MiB count=200 iflag=nocache
+```
+
+```
+200+0 records in
+200+0 records out
+209715200 bytes (210 MB, 200 MiB) copied, 1.67285 s, 125 MB/s
+```
+
+#### Example 2-2 (writing to sdb)
+
+```
+# MY_DISK=$(echo $MY_DEVS | cut -d ' ' -f 2)
+# dd if=/dev/zero of=$MY_DISK bs=1MiB count=200 oflag=direct
+```
+
+```
+200+0 records in
+200+0 records out
+209715200 bytes (210 MB, 200 MiB) copied, 1.67198 s, 125 MB/s
+```
+
+#### Example 2-3 (reading concurrently from sdb)
+
+```
+# MY_DISK=$(echo $MY_DEVS | cut -d ' ' -f 2)
+# (dd if=$MY_DISK of=/dev/null bs=1MiB count=200 iflag=nocache &); (dd if=$MY_DISK of=/dev/null bs=1MiB count=200 iflag=nocache skip=200 &)
+```
+
+```
+200+0 records in
+200+0 records out
+209715200 bytes (210 MB, 200 MiB) copied, 3.52808 s, 59.4 MB/s
+200+0 records in
+200+0 records out
+209715200 bytes (210 MB, 200 MiB) copied, 3.57736 s, 58.6 MB/s
+```
+
+#### Example 2-4 (writing concurrently to sdb)
+
+```
+# MY_DISK=$(echo $MY_DEVS | cut -d ' ' -f 2)
+# (dd if=/dev/zero of=$MY_DISK bs=1MiB count=200 oflag=direct &); (dd if=/dev/zero of=$MY_DISK bs=1MiB count=200 oflag=direct skip=200 &)
+```
+
+```
+200+0 records in
+200+0 records out
+209715200 bytes (210 MB, 200 MiB) copied, 3.7841 s, 55.4 MB/s
+200+0 records in
+200+0 records out
+209715200 bytes (210 MB, 200 MiB) copied, 3.81475 s, 55.0 MB/s
+```
+
+#### Example 3-1 (reading from RAID0)
+
+```
+# mdadm --create /dev/md/stripped --homehost=any --metadata=1.0 --level=0 --raid-devices=2 $MY_DEVS
+# MY_DISK=/dev/md/stripped
+# dd if=$MY_DISK of=/dev/null bs=1MiB count=200 iflag=nocache
+```
+
+```
+200+0 records in
+200+0 records out
+209715200 bytes (210 MB, 200 MiB) copied, 0.837419 s, 250 MB/s
+```
+
+#### Example 3-2 (writing to RAID0)
+
+```
+# MY_DISK=/dev/md/stripped
+# dd if=/dev/zero of=$MY_DISK bs=1MiB count=200 oflag=direct
+```
+
+```
+200+0 records in
+200+0 records out
+209715200 bytes (210 MB, 200 MiB) copied, 0.823648 s, 255 MB/s
+```
+
+#### Example 3-3 (reading concurrently from RAID0)
+
+```
+# MY_DISK=/dev/md/stripped
+# (dd if=$MY_DISK of=/dev/null bs=1MiB count=200 iflag=nocache &); (dd if=$MY_DISK of=/dev/null bs=1MiB count=200 iflag=nocache skip=200 &)
+```
+
+```
+200+0 records in
+200+0 records out
+209715200 bytes (210 MB, 200 MiB) copied, 1.31025 s, 160 MB/s
+200+0 records in
+200+0 records out
+209715200 bytes (210 MB, 200 MiB) copied, 1.80016 s, 116 MB/s
+```
+
+#### Example 3-4 (writing concurrently to RAID0)
+
+```
+# MY_DISK=/dev/md/stripped
+# (dd if=/dev/zero of=$MY_DISK bs=1MiB count=200 oflag=direct &); (dd if=/dev/zero of=$MY_DISK bs=1MiB count=200 oflag=direct skip=200 &)
+```
+
+```
+200+0 records in
+200+0 records out
+209715200 bytes (210 MB, 200 MiB) copied, 1.65026 s, 127 MB/s
+200+0 records in
+200+0 records out
+209715200 bytes (210 MB, 200 MiB) copied, 1.81323 s, 116 MB/s
+```
+
+#### Example 4-1 (reading from RAID1)
+
+```
+# mdadm --stop /dev/md/stripped
+# mdadm --create /dev/md/mirrored --homehost=any --metadata=1.0 --level=1 --raid-devices=2 --assume-clean $MY_DEVS
+# MY_DISK=/dev/md/mirrored
+# dd if=$MY_DISK of=/dev/null bs=1MiB count=200 iflag=nocache
+```
+
+```
+200+0 records in
+200+0 records out
+209715200 bytes (210 MB, 200 MiB) copied, 1.74963 s, 120 MB/s
+```
+
+#### Example 4-2 (writing to RAID1)
+
+```
+# MY_DISK=/dev/md/mirrored
+# dd if=/dev/zero of=$MY_DISK bs=1MiB count=200 oflag=direct
+```
+
+```
+200+0 records in
+200+0 records out
+209715200 bytes (210 MB, 200 MiB) copied, 1.74625 s, 120 MB/s
+```
+
+#### Example 4-3 (reading concurrently from RAID1)
+
+```
+# MY_DISK=/dev/md/mirrored
+# (dd if=$MY_DISK of=/dev/null bs=1MiB count=200 iflag=nocache &); (dd if=$MY_DISK of=/dev/null bs=1MiB count=200 iflag=nocache skip=200 &)
+```
+
+```
+200+0 records in
+200+0 records out
+209715200 bytes (210 MB, 200 MiB) copied, 1.67171 s, 125 MB/s
+200+0 records in
+200+0 records out
+209715200 bytes (210 MB, 200 MiB) copied, 1.67685 s, 125 MB/s
+```
+
+#### Example 4-4 (writing concurrently to RAID1)
+
+```
+# MY_DISK=/dev/md/mirrored
+# (dd if=/dev/zero of=$MY_DISK bs=1MiB count=200 oflag=direct &); (dd if=/dev/zero of=$MY_DISK bs=1MiB count=200 oflag=direct skip=200 &)
+```
+
+```
+200+0 records in
+200+0 records out
+209715200 bytes (210 MB, 200 MiB) copied, 4.09666 s, 51.2 MB/s
+200+0 records in
+200+0 records out
+209715200 bytes (210 MB, 200 MiB) copied, 4.1067 s, 51.1 MB/s
+```
+
+#### Restore your swap device and journald configuration
+
+```
+# mdadm --stop /dev/md/stripped /dev/md/mirrored
+# mdadm --create /dev/md/swap --homehost=any --metadata=1.0 --level=1 --raid-devices=2 $MY_DEVS
+# mkswap /dev/md/swap
+# swapon -a
+# mv /etc/systemd/journald.conf.bak /etc/systemd/journald.conf
+# systemctl restart systemd-journald.service
+# reboot
+```
+
+### Interpreting the results
+
+Examples 1-1, 1-2, 2-1, and 2-2 show that each of my drives read and write at about 125 MB/s.
+
+Examples 1-3, 1-4, 2-3, and 2-4 show that when two reads or two writes are done in parallel on the same drive, each process gets at about half the drive’s bandwidth (60 MB/s).
+
+The 3-x examples show the performance benefit of putting the two drives together in a RAID0 (data stripping) array. The numbers, in all cases, show that the RAID0 array performs about twice as fast as either drive is able to perform on its own. The trade-off is that you are twice as likely to lose everything because each drive only contains half the data. A three-drive array would perform three times as fast as a single drive (all drives being equal) but it would be thrice as likely to suffer a [catastrophic failure][6].
+
+The 4-x examples show that the performance of the RAID1 (data mirroring) array is similar to that of a single disk except for the case where multiple processes are concurrently reading (example 4-3). In the case of multiple processes reading, the performance of the RAID1 array is similar to that of the RAID0 array. This means that you will see a performance benefit with RAID1, but only when processes are reading concurrently. For example, if a process tries to access a large number of files in the background while you are trying to use a web browser or email client in the foreground. The main benefit of RAID1 is that your data is unlikely to be lost [if a drive fails][7].
+
+### Video demo
+
+Testing storage throughput using dd
+
+### Troubleshooting
+
+If the above tests aren’t performing as you expect, you might have a bad or failing drive. Most modern hard drives have built-in Self-Monitoring, Analysis and Reporting Technology ([SMART][8]). If your drive supports it, the _smartctl_ command can be used to query your hard drive for its internal statistics:
+
+```
+# smartctl --health /dev/sda
+# smartctl --log=error /dev/sda
+# smartctl -x /dev/sda
+```
+
+Another way that you might be able to tune your PC for better performance is by changing your [I/O scheduler][9]. Linux systems support several I/O schedulers and the current default for Fedora systems is the [multiqueue][10] variant of the [deadline][11] scheduler. The default performs very well overall and scales extremely well for large servers with many processors and large disk arrays. There are, however, a few more specialized schedulers that might perform better under certain conditions.
+
+To view which I/O scheduler your drives are using, issue the following command:
+
+```
+$ for i in /sys/block/sd?/queue/scheduler; do echo "$i: $(<$i)"; done
+```
+
+You can change the scheduler for a drive by writing the name of the desired scheduler to the /sys/block//queue/scheduler file:
+
+```
+# echo bfq > /sys/block/sda/queue/scheduler
+```
+
+You can make your changes permanent by creating a [udev rule][12] for your drive. The following example shows how to create a udev rule that will set all [rotational drives][13] to use the [BFQ][14] I/O scheduler:
+
+```
+# cat << END > /etc/udev/rules.d/60-ioscheduler-rotational.rules
+ACTION=="add|change", KERNEL=="sd[a-z]", ATTR{queue/rotational}=="1", ATTR{queue/scheduler}="bfq"
+END
+```
+
+Here is another example that sets all [solid-state drives][15] to use the [NOOP][16] I/O scheduler:
+
+```
+# cat << END > /etc/udev/rules.d/60-ioscheduler-solid-state.rules
+ACTION=="add|change", KERNEL=="sd[a-z]", ATTR{queue/rotational}=="0", ATTR{queue/scheduler}="none"
+END
+```
+
+Changing your I/O scheduler won’t affect the raw throughput of your devices, but it might make your PC seem more responsive by prioritizing the bandwidth for the foreground tasks over the background tasks or by eliminating unnecessary block reordering.
+
+* * *
+
+_Photo by _[ _James Donovan_][17]_ on _[_Unsplash_][18]_._
+
+--------------------------------------------------------------------------------
+
+via: https://fedoramagazine.org/check-storage-performance-with-dd/
+
+作者:[Gregory Bartholomew][a]
+选题:[lujun9972][b]
+译者:[译者ID](https://github.com/译者ID)
+校对:[校对者ID](https://github.com/校对者ID)
+
+本文由 [LCTT](https://github.com/LCTT/TranslateProject) 原创编译,[Linux中国](https://linux.cn/) 荣誉推出
+
+[a]: https://fedoramagazine.org/author/glb/
+[b]: https://github.com/lujun9972
+[1]: https://fedoramagazine.org/wp-content/uploads/2019/04/dd-performance-816x345.jpg
+[2]: https://www.ibm.com/developerworks/community/blogs/ibmnas/entry/misalignment_can_be_twice_the_cost1?lang=en
+[3]: https://eklitzke.org/efficient-file-copying-on-linux
+[4]: https://en.wikipedia.org/wiki/Hdparm
+[5]: https://en.wikipedia.org/wiki/Random-access_memory
+[6]: https://blog.elcomsoft.com/2019/01/why-ssds-die-a-sudden-death-and-how-to-deal-with-it/
+[7]: https://www.computerworld.com/article/2484998/ssds-do-die--as-linus-torvalds-just-discovered.html
+[8]: https://en.wikipedia.org/wiki/S.M.A.R.T.
+[9]: https://en.wikipedia.org/wiki/I/O_scheduling
+[10]: https://lwn.net/Articles/552904/
+[11]: https://en.wikipedia.org/wiki/Deadline_scheduler
+[12]: http://www.reactivated.net/writing_udev_rules.html
+[13]: https://en.wikipedia.org/wiki/Hard_disk_drive_performance_characteristics
+[14]: http://algo.ing.unimo.it/people/paolo/disk_sched/
+[15]: https://en.wikipedia.org/wiki/Solid-state_drive
+[16]: https://en.wikipedia.org/wiki/Noop_scheduler
+[17]: https://unsplash.com/photos/0ZBRKEG_5no?utm_source=unsplash&utm_medium=referral&utm_content=creditCopyText
+[18]: https://unsplash.com/search/photos/speed?utm_source=unsplash&utm_medium=referral&utm_content=creditCopyText
diff --git a/sources/tech/20190510 Keeping an open source project alive when people leave.md b/sources/tech/20190510 Keeping an open source project alive when people leave.md
new file mode 100644
index 0000000000..31a0ab7412
--- /dev/null
+++ b/sources/tech/20190510 Keeping an open source project alive when people leave.md
@@ -0,0 +1,180 @@
+[#]: collector: (lujun9972)
+[#]: translator: ( )
+[#]: reviewer: ( )
+[#]: publisher: ( )
+[#]: url: ( )
+[#]: subject: (Keeping an open source project alive when people leave)
+[#]: via: (https://opensource.com/article/19/5/code-missing-community-management)
+[#]: author: (Rodrigo Duarte Sousa https://opensource.com/users/rodrigods/users/tellesnobrega)
+
+Keeping an open source project alive when people leave
+======
+How to find out what's done, what's not, and what's missing.
+![][1]
+
+Suppose you wake up one day and decide to finally use that recipe video you keep watching all over social media. You get the ingredients, organize the necessary utensils, and start to follow the recipe steps. You cut this, cut that, then start heating the oven at the same time you put butter and onions in a pan. Then, your phone reminds you: you have a dinner appointment with your boss, and you're already late! You turn off everything and leave immediately, stopping the cooking process somewhere near the end.
+
+Some minutes later, your roommate arrives at home ready to have dinner and finds only the _ongoing work_ in the kitchen. They have the following options:
+
+ 1. Clean up the mess and start cooking something from scratch.
+ 2. Order dinner and don’t bother to cook and/or fix the mess you left.
+ 3. Start cooking “around” the mess you left, which will probably take more time since most of the utensils are dirty and there isn’t much space left in the kitchen.
+
+
+
+If you left the printed version of the recipe somewhere, your roommate also has a fourth option. They could finish what you started! The problem is that they have no idea what's missing. It is not like you crossed out each completed step. Their best bet is either to call you or to examine all of your _changes_ to infer what is missing.
+
+In this example, the kitchen is like a software project, the utensils are the code, and the recipe is a new feature being implemented. Leaving something behind is not usually doable in a company's private project since you're accountable for your work and—in a scenario where you need to leave—it's almost certain that there is someone tracking/following the project, so they avoid having a "single point of failure." With open source projects, though, this continuity rarely happens. So how can we in the open source community deal with legacy, unfinished code, or code that is completed but no one dares touch it?
+
+### Knowledge legacy in open source projects
+
+We have always felt that open source is one of the best ways for an inexperienced software engineer to improve her skills. For many, open source projects offer their first hands-on experience with particular tools. [Version control systems][2], [unit][3] and [integration][4] tests, [continuous delivery][5], [code reviews][6], [features planning][7], [bug reporting/fixing][8], and more.
+
+In addition to learning opportunities, we can also view open source projects as a career opportunity—many senior engineers in the community get paid to be there, and you can add your contributions to your resume. That’s pretty cool. There's nothing like learning while improving your resume and getting potential employers' attention so you can pay your rent.
+
+Is this whole situation an infinite loop where everyone wins? The answer is obviously no. This post focuses on one of the main issues that arise in any project: the [bus/truck factor][9]. In the open source context, specifically, when people experience major changes such as a new job or other more personal factors, they tend to leave the community. We will first describe the problems that can arise from people leaving their _recipes_ unfinished by using [OpenStack][10] as an example. Then, we'll try to discuss some ideas to try to mitigate the issues.
+
+### Common problems
+
+In the past few years, we've seen a lot of changes in the [OpenStack][11] community, where some projects lost some portion of their active contributors team. These losses led to incomplete work and even finished modules without clear maintainers. Below are other examples of what happens when people suddenly leave. While this article uses OpenStack terms, such as “specs,” these issues easily apply to software development in general:
+
+ * **Broken documentation:** A new API or setting either wasn't documented, or it was documented but not implemented.
+ * **Hard to resolve knowledge deficits:** For example, a new requirement and/or feature requires part of the code to be refactored but no one has the necessary expertise.
+ * **Incomplete features:** What are the missing tasks required for each feature? Which tasks were completed?
+ * **Debugging drama:** If the person who wrote the code isn't there, meaning that it takes a lot of engineering hours just to decrypt—so to speak—the code path that needs to be fixed.
+
+
+
+To illustrate, we will use the [Project Tree Deletion][12] feature. Project Tree Deletion is a tiny feature that one of us proposed more than three years ago and couldn’t complete. Basically, the main goal was to enable an OpenStack user/operator to erase a whole branch of projects without having to manually disable/delete every single of them starting from the leaves. Very straightforward, right? The PTD spec has been merged and has the following _work items_ :
+
+ * Update API spec documentation.
+ * Add new rules to the file **policy.json**.
+ * Add new endpoints to mirror the new features.
+ * Implement the new deletion/disabling behavior for the project’s hierarchy.
+
+
+
+What about the sequence of steps (roadmap) to get these work items done? How do we know where to start and when what to tackle next? Are there any logical dependencies between the work items? How do we know where to start, and with what?
+
+Also, how do we know which work has been completed (if any)? One of the things that we do is look in the [blueprint][13] and/or the new [bug tracker][14], for example:
+
+ * Recursive deletion and project disabling: (merged)
+ * API changes for Reseller: (merged)
+ * Add parent_id to GET /projects: (merged)
+ * Manager support for project cascade update: (merged)
+ * API support for cascade update: (abandoned)
+ * Manager support for project delete cascade: (merged)
+ * API support for project cascade delete: (abandoned)
+ * Add backend support for deleting a projects list: (merged)
+ * Test list project hierarchy is correct for a large tree: (merged)
+ * Fix cascade operations documentation: (merged)
+ * Revert “Fix cascade operations documentation”: (merged)
+ * Remove the APIs from the doc that aren't supported yet: (merged)
+
+
+
+Here we can see a lot of merged patches, but also that some were abandoned, and that some include the words Revert and Remove in their titles. Now we have strong evidence that this work is not completed, but at least some work was started to clean it up and avoid exposing something incomplete in the service API. Let’s dig a little bit deeper and look at the [_current_ delete project code][15].
+
+There, we can see an added **cascade** argument (“cascade” resembles deleting related things together, so this argument must be somehow related to the proposed feature), and that it has a special block to treat the cases for the possible values of **cascade** :
+
+
+```
+`def _delete_project(self, project, initiator=None, cascade=False):`[/code] [code]
+
+if cascade:
+# Getting reversed project's subtrees list, i.e. from the leaves
+# to the root, so we do not break parent_id FK.
+subtree_list = self.list_projects_in_subtree(project_id)
+subtree_list.reverse()
+if not self._check_whole_subtree_is_disabled(
+project_id, subtree_list=subtree_list):
+raise exception.ForbiddenNotSecurity(
+_('Cannot delete project %(project_id)s since its subtree '
+'contains enabled projects.')
+% {'project_id': project_id})
+
+project_list = subtree_list + [project]
+projects_ids = [x['id'] for x in project_list]
+
+ret = self.driver.delete_projects_from_ids(projects_ids)
+for prj in project_list:
+self._post_delete_cleanup_project(prj['id'], prj, initiator)
+else:
+ret = self.driver.delete_project(project_id)
+self._post_delete_cleanup_project(project_id, project, initiator)
+```
+
+What about the callers of this function? Do they use **cascade** at all? If we search for it, we only find occurrences in the backend tests:
+
+
+```
+$ git grep "delete_project" | grep "cascade" | grep -v "def"
+keystone/tests/unit/resource/test_backends.py: PROVIDERS.resource_api.delete_project(root_project['id'], cascade=True)
+keystone/tests/unit/resource/test_backends.py: PROVIDERS.resource_api.delete_project(p1['id'], cascade=True)
+```
+
+We can also confirm this finding by looking at the [delete projects API implementation][16].
+
+So it seems that we have a problem here, something simple that I started was left behind a very long time ago. How could the community or I have prevented this from happening?
+
+From the example above, one of the most apparent problems is the lack of a clear roadmap and list of completed tasks somewhere. To follow the actual implementation status, we had to dig into the blueprint/bug comments and the code.
+
+Based on this issue, we can sketch an idea: for each new feature, we need a roadmap stored somewhere to reflect the implementation status. Once the roadmap is defined within a spec, we can track each step as a [Launchpad][17] entry, for example, and have a better view of the progress status of that spec.
+
+Of course, these steps won’t prevent unfinished projects and they add a little bit of process, but following them can give a better view of what's missing so someone else from the community could finish or even revert what's there.
+
+### That’s not all
+
+What about other aspects of the project besides feature completion? We shouldn’t expect that every person on the core team is an expert in every single project module. This issue highlights another very important aspect of any open source community: mentoring.
+
+New people come to the community all the time and many have an incentive to continuing coming back as we discussed earlier. However, are our current community members willing to mentor them? How many times have you participated as a mentor in a program such as [Outreachy ][18]or [Google Summer of Code][19], or taken time to answer questions in the project’s chat?
+
+We also know that people eventually move on to other open source communities, so we have the chance of not leaving what we learned behind. We can always transmit that knowledge directly to those who are currently interested and actively asking questions, or indirectly, by writing documentation, blog posts, giving talks, and so forth.
+
+In order to have a healthy open source community, knowledge can’t be dominated by few people. We need to make an effort to have as many people capable of moving the project forward as possible. Also, a key aspect of mentoring is not only related to coding, but also to leadership skills. Preparing people to take roles like Project Team Lead, joining the Technical Committee, and so on is crucial if we intend to see the community grow even when we're not around anymore.
+
+Needless to say, mentoring is also an important skill for climbing the engineering ladder in most companies. Consider that another motivation.
+
+### To conclude
+
+Open source should not be treated as only the means to an end. Collaboration is a crucial part of these projects, and alongside mentoring, should always be treated as a first citizen in any open source community. And, of course, we will fix the unfinished spec used as this article's example.
+
+If you are part of an open source community, it is your responsibility to be focusing on sharing your knowledge while you are still around. Chances are that no one is going to tell you to do so, it should be part of the routine of any open source collaborator.
+
+What are other ways of sharing knowledge? What are your thoughts and ideas about the issue?
+
+_This original article was posted on[rodrigods][20]._
+
+--------------------------------------------------------------------------------
+
+via: https://opensource.com/article/19/5/code-missing-community-management
+
+作者:[Rodrigo Duarte Sousa][a]
+选题:[lujun9972][b]
+译者:[译者ID](https://github.com/译者ID)
+校对:[校对者ID](https://github.com/校对者ID)
+
+本文由 [LCTT](https://github.com/LCTT/TranslateProject) 原创编译,[Linux中国](https://linux.cn/) 荣誉推出
+
+[a]: https://opensource.com/users/rodrigods/users/tellesnobrega
+[b]: https://github.com/lujun9972
+[1]: https://opensource.com/sites/default/files/styles/image-full-size/public/lead-images/BIZ_question_B.png?itok=f88cyt00
+[2]: https://en.wikipedia.org/wiki/Version_control
+[3]: https://en.wikipedia.org/wiki/Unit_testing
+[4]: https://en.wikipedia.org/wiki/Integration_testing
+[5]: https://en.wikipedia.org/wiki/Continuous_delivery
+[6]: https://en.wikipedia.org/wiki/Code_review
+[7]: https://www.agilealliance.org/glossary/sprint-planning/
+[8]: https://www.softwaretestinghelp.com/how-to-write-good-bug-report/
+[9]: https://en.wikipedia.org/wiki/Bus_factor
+[10]: https://www.openstack.org/
+[11]: /resources/what-is-openstack
+[12]: https://review.opendev.org/#/c/148730/35
+[13]: https://blueprints.launchpad.net/keystone/+spec/project-tree-deletion
+[14]: https://bugs.launchpad.net/keystone/+bug/1816105
+[15]: https://github.com/openstack/keystone/blob/master/keystone/resource/core.py#L475-L519
+[16]: https://github.com/openstack/keystone/blob/master/keystone/api/projects.py#L202-L214
+[17]: https://launchpad.net
+[18]: https://www.outreachy.org/
+[19]: https://summerofcode.withgoogle.com/
+[20]: https://blog.rodrigods.com/knowledge-legacy-the-issue-of-passing-the-baton/
diff --git a/sources/tech/20190510 Learn to change history with git rebase.md b/sources/tech/20190510 Learn to change history with git rebase.md
new file mode 100644
index 0000000000..be1d265d8a
--- /dev/null
+++ b/sources/tech/20190510 Learn to change history with git rebase.md
@@ -0,0 +1,594 @@
+[#]: collector: (lujun9972)
+[#]: translator: (zhang5788)
+[#]: reviewer: ( )
+[#]: publisher: ( )
+[#]: url: ( )
+[#]: subject: (Learn to change history with git rebase!)
+[#]: via: (https://git-rebase.io/)
+[#]: author: (git-rebase https://git-rebase.io/)
+
+Learn to change history with git rebase!
+======
+One of Git 's core value-adds is the ability to edit history. Unlike version control systems that treat the history as a sacred record, in git we can change history to suit our needs. This gives us a lot of powerful tools and allows us to curate a good commit history in the same way we use refactoring to uphold good software design practices. These tools can be a little bit intimidating to the novice or even intermediate git user, but this guide will help to demystify the powerful git-rebase .
+
+```
+A word of caution : changing the history of public, shared, or stable branches is generally advised against. Editing the history of feature branches and personal forks is fine, and editing commits that you haven't pushed yet is always okay. Use git push -f to force push your changes to a personal fork or feature branch after editing your commits.
+```
+
+Despite the scary warning, it's worth mentioning that everything mentioned in this guide is a non-destructive operation. It's actually pretty difficult to permanently lose data in git. Fixing things when you make mistakes is covered at the end of this guide.
+
+### Setting up a sandbox
+
+We don't want to mess up any of your actual repositories, so throughout this guide we'll be working with a sandbox repo. Run these commands to get started:
+
+```
+git init /tmp/rebase-sandbox
+cd /tmp/rebase-sandbox
+git commit --allow-empty -m"Initial commit"
+```
+
+If you run into trouble, just run rm -rf /tmp/rebase-sandbox and run these steps again to start over. Each step of this guide can be run on a fresh sandbox, so it's not necessary to re-do every task.
+
+
+### Amending your last commit
+
+Let's start with something simple: fixing your most recent commit. Let's add a file to our sandbox - and make a mistake:
+
+```
+echo "Hello wrold!" >greeting.txt
+ git add greeting.txt
+ git commit -m"Add greeting.txt"
+```
+
+Fixing this mistake is pretty easy. We can just edit the file and commit with `--amend`, like so:
+
+```
+echo "Hello world!" >greeting.txt
+ git commit -a --amend
+```
+
+Specifying `-a` automatically stages (i.e. `git add`'s) all files that git already knows about, and `--amend` will squash the changes into the most recent commit. Save and quit your editor (you have a chance to change the commit message now if you'd like). You can see the fixed commit by running `git show`:
+
+```
+commit f5f19fbf6d35b2db37dcac3a55289ff9602e4d00 (HEAD -> master)
+Author: Drew DeVault
+Date: Sun Apr 28 11:09:47 2019 -0400
+
+ Add greeting.txt
+
+diff --git a/greeting.txt b/greeting.txt
+new file mode 100644
+index 0000000..cd08755
+--- /dev/null
++++ b/greeting.txt
+@@ -0,0 +1 @@
++Hello world!
+```
+
+### Fixing up older commits
+
+Amending only works for the most recent commit. What happens if you need to correct an older commit? Let's start by setting up our sandbox accordingly:
+
+```
+echo "Hello!" >greeting.txt
+git add greeting.txt
+git commit -m"Add greeting.txt"
+
+echo "Goodbye world!" >farewell.txt
+git add farewell.txt
+git commit -m"Add farewell.txt"
+```
+
+Looks like `greeting.txt` is missing "world". Let's write a commit normally which fixes that:
+
+```
+echo "Hello world!" >greeting.txt
+git commit -a -m"fixup greeting.txt"
+```
+
+So now the files look correct, but our history could be better - let's use the new commit to "fixup" the last one. For this, we need to introduce a new tool: the interactive rebase. We're going to edit the last three commits this way, so we'll run `git rebase -i HEAD~3` (`-i` for interactive). This'll open your text editor with something like this:
+
+```
+pick 8d3fc77 Add greeting.txt
+pick 2a73a77 Add farewell.txt
+pick 0b9d0bb fixup greeting.txt
+
+# Rebase f5f19fb..0b9d0bb onto f5f19fb (3 commands)
+#
+# Commands:
+# p, pick = use commit
+# f, fixup = like "squash", but discard this commit's log message
+```
+
+This is the rebase plan, and by editing this file you can instruct git on how to edit history. I've trimmed the summary to just the details relevant to this part of the rebase guide, but feel free to skim the full summary in your text editor.
+
+When we save and close our editor, git is going to remove all of these commits from its history, then execute each line one at a time. By default, it's going to pick each commit, summoning it from the heap and adding it to the branch. If we don't edit this file at all, we'll end up right back where we started, picking every commit as-is. We're going to use one of my favorite features now: fixup. Edit the third line to change the operation from "pick" to "fixup" and move it to immediately after the commit we want to "fix up":
+
+```
+pick 8d3fc77 Add greeting.txt
+fixup 0b9d0bb fixup greeting.txt
+pick 2a73a77 Add farewell.txt
+```
+
+**Tip** : We can also abbreviate this with just "f" to speed things up next time.
+
+Save and quit your editor - git will run these commands. We can check the log to verify the result:
+
+```
+$ git log -2 --oneline
+fcff6ae (HEAD -> master) Add farewell.txt
+a479e94 Add greeting.txt
+```
+
+### Squashing several commits into one
+
+As you work, you may find it useful to write lots of commits as you reach small milestones or fix bugs in previous commits. However, it may be useful to "squash" these commits together, to make a cleaner history before merging your work into master. For this, we'll use the "squash" operation. Let's start by writing a bunch of commits - just copy and paste this if you want to speed it up:
+
+```
+git checkout -b squash
+for c in H e l l o , ' ' w o r l d; do
+ echo "$c" >>squash.txt
+ git add squash.txt
+ git commit -m"Add '$c' to squash.txt"
+done
+```
+
+That's a lot of commits to make a file that says "Hello, world"! Let's start another interactive rebase to squash them together. Note that we checked out a branch to try this on, first. Because of that, we can quickly rebase all of the commits since we branched by using `git rebase -i master`. The result:
+
+```
+pick 1e85199 Add 'H' to squash.txt
+pick fff6631 Add 'e' to squash.txt
+pick b354c74 Add 'l' to squash.txt
+pick 04aaf74 Add 'l' to squash.txt
+pick 9b0f720 Add 'o' to squash.txt
+pick 66b114d Add ',' to squash.txt
+pick dc158cd Add ' ' to squash.txt
+pick dfcf9d6 Add 'w' to squash.txt
+pick 7a85f34 Add 'o' to squash.txt
+pick c275c27 Add 'r' to squash.txt
+pick a513fd1 Add 'l' to squash.txt
+pick 6b608ae Add 'd' to squash.txt
+
+# Rebase 1af1b46..6b608ae onto 1af1b46 (12 commands)
+#
+# Commands:
+# p, pick = use commit
+# s, squash = use commit, but meld into previous commit
+```
+
+**Tip** : your local master branch evolves independently of the remote master branch, and git stores the remote branch as `origin/master`. Combined with this trick, `git rebase -i origin/master` is often a very convenient way to rebase all of the commits which haven't been merged upstream yet!
+
+We're going to squash all of these changes into the first commit. To do this, change every "pick" operation to "squash", except for the first line, like so:
+
+```
+pick 1e85199 Add 'H' to squash.txt
+squash fff6631 Add 'e' to squash.txt
+squash b354c74 Add 'l' to squash.txt
+squash 04aaf74 Add 'l' to squash.txt
+squash 9b0f720 Add 'o' to squash.txt
+squash 66b114d Add ',' to squash.txt
+squash dc158cd Add ' ' to squash.txt
+squash dfcf9d6 Add 'w' to squash.txt
+squash 7a85f34 Add 'o' to squash.txt
+squash c275c27 Add 'r' to squash.txt
+squash a513fd1 Add 'l' to squash.txt
+squash 6b608ae Add 'd' to squash.txt
+```
+
+When you save and close your editor, git will think about this for a moment, then open your editor again to revise the final commit message. You'll see something like this:
+
+```
+# This is a combination of 12 commits.
+# This is the 1st commit message:
+
+Add 'H' to squash.txt
+
+# This is the commit message #2:
+
+Add 'e' to squash.txt
+
+# This is the commit message #3:
+
+Add 'l' to squash.txt
+
+# This is the commit message #4:
+
+Add 'l' to squash.txt
+
+# This is the commit message #5:
+
+Add 'o' to squash.txt
+
+# This is the commit message #6:
+
+Add ',' to squash.txt
+
+# This is the commit message #7:
+
+Add ' ' to squash.txt
+
+# This is the commit message #8:
+
+Add 'w' to squash.txt
+
+# This is the commit message #9:
+
+Add 'o' to squash.txt
+
+# This is the commit message #10:
+
+Add 'r' to squash.txt
+
+# This is the commit message #11:
+
+Add 'l' to squash.txt
+
+# This is the commit message #12:
+
+Add 'd' to squash.txt
+
+# Please enter the commit message for your changes. Lines starting
+# with '#' will be ignored, and an empty message aborts the commit.
+#
+# Date: Sun Apr 28 14:21:56 2019 -0400
+#
+# interactive rebase in progress; onto 1af1b46
+# Last commands done (12 commands done):
+# squash a513fd1 Add 'l' to squash.txt
+# squash 6b608ae Add 'd' to squash.txt
+# No commands remaining.
+# You are currently rebasing branch 'squash' on '1af1b46'.
+#
+# Changes to be committed:
+# new file: squash.txt
+#
+```
+
+This defaults to a combination of all of the commit messages which were squashed, but leaving it like this is almost always not what you want. The old commit messages may be useful for reference when writing the new one, though.
+
+**Tip** : the "fixup" command you learned about in the previous section can be used for this purpose, too - but it discards the messages of the squashed commits.
+
+Let's delete everything and replace it with a better commit message, like this:
+
+```
+Add squash.txt with contents "Hello, world"
+
+# Please enter the commit message for your changes. Lines starting
+# with '#' will be ignored, and an empty message aborts the commit.
+#
+# Date: Sun Apr 28 14:21:56 2019 -0400
+#
+# interactive rebase in progress; onto 1af1b46
+# Last commands done (12 commands done):
+# squash a513fd1 Add 'l' to squash.txt
+# squash 6b608ae Add 'd' to squash.txt
+# No commands remaining.
+# You are currently rebasing branch 'squash' on '1af1b46'.
+#
+# Changes to be committed:
+# new file: squash.txt
+#
+```
+
+Save and quit your editor, then examine your git log - success!
+
+```
+commit c785f476c7dff76f21ce2cad7c51cf2af00a44b6 (HEAD -> squash)
+Author: Drew DeVault
+Date: Sun Apr 28 14:21:56 2019 -0400
+
+ Add squash.txt with contents "Hello, world"
+```
+
+Before we move on, let's pull our changes into the master branch and get rid of this scratch one. We can use `git rebase` like we use `git merge`, but it avoids making a merge commit:
+
+```
+git checkout master
+git rebase squash
+git branch -D squash
+```
+
+We generally prefer to avoid using git merge unless we're actually merging unrelated histories. If you have two divergent branches, a git merge is useful to have a record of when they were... merged. In the course of your normal work, rebase is often more appropriate.
+
+### Splitting one commit into several
+
+Sometimes the opposite problem happens - one commit is just too big. Let's look into splitting it up. This time, let's write some actual code. Start with a simple C program2 (you can still copy+paste this snippet into your shell to do this quickly):
+
+```
+cat <main.c
+int main(int argc, char *argv[]) {
+ return 0;
+}
+EOF
+```
+
+We'll commit this first.
+
+```
+git add main.c
+git commit -m"Add C program skeleton"
+```
+
+Next, let's extend the program a bit:
+
+```
+cat <main.c
+#include <stdio.h>
+
+const char *get_name() {
+ static char buf[128];
+ scanf("%s", buf);
+ return buf;
+}
+
+int main(int argc, char *argv[]) {
+ printf("What's your name? ");
+ const char *name = get_name();
+ printf("Hello, %s!\n", name);
+ return 0;
+}
+EOF
+```
+
+After we commit this, we'll be ready to learn how to split it up.
+
+```
+git commit -a -m"Flesh out C program"
+```
+
+The first step is to start an interactive rebase. Let's rebase both commits with `git rebase -i HEAD~2`, giving us this rebase plan:
+
+```
+pick 237b246 Add C program skeleton
+pick b3f188b Flesh out C program
+
+# Rebase c785f47..b3f188b onto c785f47 (2 commands)
+#
+# Commands:
+# p, pick = use commit
+# e, edit = use commit, but stop for amending
+```
+
+Change the second commit's command from "pick" to "edit", then save and close your editor. Git will think about this for a second, then present you with this:
+
+```
+Stopped at b3f188b... Flesh out C program
+You can amend the commit now, with
+
+ git commit --amend
+
+Once you are satisfied with your changes, run
+
+ git rebase --continue
+```
+
+We could follow these instructions to add new changes to the commit, but instead let's do a "soft reset"3 by running `git reset HEAD^`. If you run `git status` after this, you'll see that it un-commits the latest commit and adds its changes to the working tree:
+
+```
+Last commands done (2 commands done):
+ pick 237b246 Add C program skeleton
+ edit b3f188b Flesh out C program
+No commands remaining.
+You are currently splitting a commit while rebasing branch 'master' on 'c785f47'.
+ (Once your working directory is clean, run "git rebase --continue")
+
+Changes not staged for commit:
+ (use "git add ..." to update what will be committed)
+ (use "git checkout -- ..." to discard changes in working directory)
+
+ modified: main.c
+
+no changes added to commit (use "git add" and/or "git commit -a")
+```
+
+To split this up, we're going to do an interactive commit. This allows us to selectively commit only specific changes from the working tree. Run `git commit -p` to start this process, and you'll be presented with the following prompt:
+
+```
+diff --git a/main.c b/main.c
+index b1d9c2c..3463610 100644
+--- a/main.c
++++ b/main.c
+@@ -1,3 +1,14 @@
++#include <stdio.h>
++
++const char *get_name() {
++ static char buf[128];
++ scanf("%s", buf);
++ return buf;
++}
++
+ int main(int argc, char *argv[]) {
++ printf("What's your name? ");
++ const char *name = get_name();
++ printf("Hello, %s!\n", name);
+ return 0;
+ }
+Stage this hunk [y,n,q,a,d,s,e,?]?
+```
+
+Git has presented you with just one "hunk" (i.e. a single change) to consider committing. This one is too big, though - let's use the "s" command to "split" up the hunk into smaller parts.
+
+```
+Split into 2 hunks.
+@@ -1 +1,9 @@
++#include
++
++const char *get_name() {
++ static char buf[128];
++ scanf("%s", buf);
++ return buf;
++}
++
+ int main(int argc, char *argv[]) {
+Stage this hunk [y,n,q,a,d,j,J,g,/,e,?]?
+```
+
+**Tip** : If you're curious about the other options, press "?" to summarize them.
+
+This hunk looks better - a single, self-contained change. Let's hit "y" to answer the question (and stage that "hunk"), then "q" to "quit" the interactive session and proceed with the commit. Your editor will pop up to ask you to enter a suitable commit message.
+
+```
+Add get_name function to C program
+
+# Please enter the commit message for your changes. Lines starting
+# with '#' will be ignored, and an empty message aborts the commit.
+#
+# interactive rebase in progress; onto c785f47
+# Last commands done (2 commands done):
+# pick 237b246 Add C program skeleton
+# edit b3f188b Flesh out C program
+# No commands remaining.
+# You are currently splitting a commit while rebasing branch 'master' on 'c785f47'.
+#
+# Changes to be committed:
+# modified: main.c
+#
+# Changes not staged for commit:
+# modified: main.c
+#
+```
+
+Save and close your editor, then we'll make the second commit. We could do another interactive commit, but since we just want to include the rest of the changes in this commit we'll just do this:
+
+```
+git commit -a -m"Prompt user for their name"
+git rebase --continue
+```
+
+That last command tells git that we're done editing this commit, and to continue to the next rebase command. That's it! Run `git log` to see the fruits of your labor:
+
+```
+$ git log -3 --oneline
+fe19cc3 (HEAD -> master) Prompt user for their name
+659a489 Add get_name function to C program
+237b246 Add C program skeleton
+```
+
+### Reordering commits
+
+This one is pretty easy. Let's start by setting up our sandbox:
+
+```
+echo "Goodbye now!" >farewell.txt
+git add farewell.txt
+git commit -m"Add farewell.txt"
+
+echo "Hello there!" >greeting.txt
+git add greeting.txt
+git commit -m"Add greeting.txt"
+
+echo "How're you doing?" >inquiry.txt
+git add inquiry.txt
+git commit -m"Add inquiry.txt"
+```
+
+The git log should now look like this:
+
+```
+f03baa5 (HEAD -> master) Add inquiry.txt
+a4cebf7 Add greeting.txt
+90bb015 Add farewell.txt
+```
+
+Clearly, this is all out of order. Let's do an interactive rebase of the past 3 commits to resolve this. Run `git rebase -i HEAD~3` and this rebase plan will appear:
+
+```
+pick 90bb015 Add farewell.txt
+pick a4cebf7 Add greeting.txt
+pick f03baa5 Add inquiry.txt
+
+# Rebase fe19cc3..f03baa5 onto fe19cc3 (3 commands)
+#
+# Commands:
+# p, pick = use commit
+#
+# These lines can be re-ordered; they are executed from top to bottom.
+```
+
+The fix is now straightforward: just reorder these lines in the order you wish for the commits to appear. Should look something like this:
+
+```
+pick a4cebf7 Add greeting.txt
+pick f03baa5 Add inquiry.txt
+pick 90bb015 Add farewell.txt
+```
+
+Save and close your editor and git will do the rest for you. Note that it's possible to end up with conflicts when you do this in practice - click here for help resolving conflicts.
+
+### git pull --rebase
+
+If you've been writing some commits on a branch which has been updated upstream, normally `git pull` will create a merge commit. In this respect, `git pull`'s behavior by default is equivalent to:
+
+```
+git fetch origin
+git merge origin/master
+```
+
+There's another option, which is often more useful and leads to a much cleaner history: `git pull --rebase`. Unlike the merge approach, this is equivalent to the following:
+
+```
+git fetch origin
+git rebase origin/master
+```
+
+The merge approach is simpler and easier to understand, but the rebase approach is almost always what you want to do if you understand how to use git rebase. If you like, you can set it as the default behavior like so:
+
+```
+git config --global pull.rebase true
+```
+
+When you do this, technically you're applying the procedure we discuss in the next section... so let's explain what it means to do that deliberately, too.
+
+### Using git rebase to... rebase
+
+Ironically, the feature of git rebase that I use the least is the one it's named for: rebasing branches. Say you have the following branches:
+
+```
+o--o--o--o--> master
+ \--o--o--> feature-1
+ \--o--> feature-2
+```
+
+It turns out feature-2 doesn't depend on any of the changes in feature-1, so you can just base it off of master. The fix is thus:
+
+```
+git checkout feature-2
+git rebase master
+```
+
+The non-interactive rebase does the default operation for all implicated commits ("pick")4, which simply rolls your history back to the last common anscestor and replays the commits from both branches. Your history now looks like this:
+
+```
+o--o--o--o--> master
+ | \--o--> feature-2
+ \--o--o--> feature-1
+```
+
+### Resolving conflicts
+
+The details on resolving merge conflicts are beyond the scope of this guide - keep your eye out for another guide for this in the future. Assuming you're familiar with resolving conflicts in general, here are the specifics that apply to rebasing.
+
+The details on resolving merge conflicts are beyond the scope of this guide - keep your eye out for another guide for this in the future. Assuming you're familiar with resolving conflicts in general, here are the specifics that apply to rebasing.
+
+Sometimes you'll get a merge conflict when doing a rebase, which you can handle just like any other merge conflict. Git will set up the conflict markers in the affected files, `git status` will show you what you need to resolve, and you can mark files as resolved with `git add` or `git rm`. However, in the context of a git rebase, there are two options you should be aware of.
+
+The first is how you complete the conflict resolution. Rather than `git commit` like you'll use when addressing conflicts that arise from `git merge`, the appropriate command for rebasing is `git rebase --continue`. However, there's another option available to you: `git rebase --skip`. This will skip the commit you're working on, and it won't be included in the rebase. This is most common when doing a non-interactive rebase, when git doesn't realize that a commit it's pulled from the "other" branch is an updated version of the commit that it conflicts with on "our" branch.
+
+### Help! I broke it!
+
+No doubt about it - rebasing can be hard sometimes. If you've made a mistake and in so doing lost commits which you needed, then `git reflog` is here to save the day. Running this command will show you every operation which changed a ref, or reference - that is, branches and tags. Each line shows you what the old reference pointed to, and you can `git cherry-pick`, `git checkout`, `git show`, or use any other operation on git commits once thought lost.
+
+
+--------------------------------------------------------------------------------
+
+via: https://git-rebase.io/
+
+作者:[git-rebase][a]
+选题:[lujun9972][b]
+译者:[译者ID](https://github.com/译者ID)
+校对:[校对者ID](https://github.com/校对者ID)
+
+本文由 [LCTT](https://github.com/LCTT/TranslateProject) 原创编译,[Linux中国](https://linux.cn/) 荣誉推出
+
+[a]: https://git-rebase.io/
+[b]: https://github.com/lujun9972
diff --git a/sources/tech/20190513 Blockchain 2.0 - Introduction To Hyperledger Fabric -Part 10.md b/sources/tech/20190513 Blockchain 2.0 - Introduction To Hyperledger Fabric -Part 10.md
new file mode 100644
index 0000000000..c685af487c
--- /dev/null
+++ b/sources/tech/20190513 Blockchain 2.0 - Introduction To Hyperledger Fabric -Part 10.md
@@ -0,0 +1,81 @@
+[#]: collector: (lujun9972)
+[#]: translator: ( )
+[#]: reviewer: ( )
+[#]: publisher: ( )
+[#]: url: ( )
+[#]: subject: (Blockchain 2.0 – Introduction To Hyperledger Fabric [Part 10])
+[#]: via: (https://www.ostechnix.com/blockchain-2-0-introduction-to-hyperledger-fabric/)
+[#]: author: (sk https://www.ostechnix.com/author/sk/)
+
+Blockchain 2.0 – Introduction To Hyperledger Fabric [Part 10]
+======
+
+![Hyperledger Fabric][1]
+
+### Hyperledger Fabric
+
+The [**Hyperledger project**][2] is an umbrella organization of sorts featuring many different modules and systems under development. Among the most popular among these individual sub-projects is the **Hyperledger Fabric**. This post will explore the features that would make the Fabric almost indispensable in the near future once blockchain systems start proliferating into main stream use. Towards the end we will also take a quick look at what developers and enthusiasts need to know regarding the technicalities of the Hyperledger Fabric.
+
+### Inception
+
+In the usual fashion for the Hyperledger project, Fabric was “donated” to the organization by one of its core members, **IBM** , who was previously the principle developer of the same. The technology platform shared by IBM was put to joint development at the Hyperledger project with contributions from over a 100 member companies and institutions.
+
+Currently running on **v1.4** of the LTS version, Fabric has come a long way and is currently seen as the go to enterprise solution for managing business data. The core vision that surrounds the Hyperledger project inevitably permeates into the Fabric as well. The Hyperledger Fabric system carries forward all the enterprise ready and scalable features that are hard coded into all projects under the Hyperledger organization.
+
+### Highlights Of Hyperledger Fabric
+
+Hyperledger Fabric offers a wide variety of features and standards that are built around the mission of supporting fast development and modular architectures. Furthermore, compared to its competitors (primarily **Ripple** and [**Ethereum**][3]), Fabric takes an explicit stance toward closed and [**permissioned blockchains**][4]. Their core objective here is to develop a set of tools which will aid blockchain developers in creating customized solutions and not to create a standalone ecosystem or a product.
+
+Some of the highlights of the Hyperledger Fabric are given below:
+
+ * **Permissioned blockchain systems**
+
+
+
+This is a category where other platforms such as Ethereum and Ripple differ quite a lot with Hyperledger Fabric. The Fabric by default is a tool designed to implement a private permissioned blockchain. Such blockchains cannot be accessed by everyone and the nodes working to offer consensus or to verify transactions are chosen by a central authority. This might be important for some applications such as banking and insurance, where transactions have to be verified by the central authority rather than participants.
+
+ * **Confidential and controlled information flow**
+
+
+
+The Fabric has built in permission systems that will restrict information flow within a specific group or certain individuals as the case may be. Unlike a public blockchain where anyone and everyone who runs a node will have a copy and selective access to data stored in the blockchain, the admin of the system can choose how to and who to share access to the information. There are also subsystems which will encrypt the stored data at better security standards compared to existing competition.
+
+ * **Plug and play architecture**
+
+
+
+Hyperledger Fabric has a plug and play type architecture. Individual components of the system may be chosen to be implemented and components of the system that developers don’t see a use for maybe discarded. The Fabric takes a highly modular and customizable route to development rather than a one size fits all approach taken by its competitors. This is especially attractive for firms and companies looking to build a lean system fast. This combined with the interoperability of the Fabric with other Hyperledger components implies that developers and designers now have access to a diverse set of standardized tools instead of having to pull code from different sources and integrate them afterwards. It also presents a rather fail-safe way to build robust modular systems.
+
+ * **Smart contracts and chaincode**
+
+
+
+A distributed application running on a blockchain is called a [**Smart contract**][5]. While the smart contract term is more or less associated with the Ethereum platform, chaincode is the name given to the same in the Hyperledger camp. Apart from possessing all the benefits of **DApps** being present in chaincode applications, what sets Hyperledger apart is the fact that the code for the same may be written in multiple high-level programming language. It supports [**Go**][6] and **JavaScript** out of the box and supports many other after integration with appropriate compiler modules as well. Though this fact might not mean much at this point, the fact remains that if existing talent can be used for ongoing projects involving blockchain that has the potential to save companies billions of dollars in personnel training and management in the long run. Developers can code in languages they’re comfortable in to start building applications on the Hyperledger Fabric and need not learn nor train in platform specific languages and syntax. This presents flexibility which current competitors of the Hyperledger Fabric do not offer.
+
+ * The Hyperledger Fabric is a back-end driver platform and is mainly aimed at integration projects where a blockchain or another distributed ledger technology is required. As such it does not provide any user facing services except for minor scripting capabilities. (Think of it to be more like a scripting language.)
+ * Hyperledger Fabric supports building sidechains for specific use-cases. In case, the developer wishes to isolate a set of users or participants to a specific part or functionality of the application, they may do so by implementing side-chains. Side-chains are blockchains that derive from a main parent, but form a different chain after their initial block. This block which gives rise to the new chain will stay immune to further changes in the new chain and the new chain remains immutable even if new information is added to the original chain. This functionality will aid in scaling the platform being developed and usher in user specific and case specific processing capabilities.
+ * The previous feature also means that not all users will have an “exact” copy of all the data in the blockchain as is expected usually from public chains. Participating nodes will have a copy of data that is only relevant to them. For instance, consider an application similar to PayTM in India. The app has wallet functionality as well as an e-commerce end. However, not all its wallet users use PayTM to shop online. In this scenario, only active shoppers will have the corresponding chain of transactions on the PayTM e-commerce site, whereas the wallet users will just have a copy of the chain that stores wallet transactions. This flexible architecture for data storage and retrieval is important while scaling, since massive singular blockchains have been shown to increase lead times for processing transactions. The chain can be kept lean and well categorised this way.
+
+
+
+We will look at other modules under the Hyperledger Project in detail in upcoming posts.
+
+--------------------------------------------------------------------------------
+
+via: https://www.ostechnix.com/blockchain-2-0-introduction-to-hyperledger-fabric/
+
+作者:[sk][a]
+选题:[lujun9972][b]
+译者:[译者ID](https://github.com/译者ID)
+校对:[校对者ID](https://github.com/校对者ID)
+
+本文由 [LCTT](https://github.com/LCTT/TranslateProject) 原创编译,[Linux中国](https://linux.cn/) 荣誉推出
+
+[a]: https://www.ostechnix.com/author/sk/
+[b]: https://github.com/lujun9972
+[1]: data:image/gif;base64,R0lGODlhAQABAIAAAAAAAP///yH5BAEAAAAALAAAAAABAAEAAAIBRAA7
+[2]: https://www.ostechnix.com/blockchain-2-0-an-introduction-to-hyperledger-project-hlp/
+[3]: https://www.ostechnix.com/blockchain-2-0-what-is-ethereum/
+[4]: https://www.ostechnix.com/blockchain-2-0-public-vs-private-blockchain-comparison/
+[5]: https://www.ostechnix.com/blockchain-2-0-explaining-smart-contracts-and-its-types/
+[6]: https://www.ostechnix.com/install-go-language-linux/
diff --git a/sources/tech/20190513 How To Check Whether The Given Package Is Installed Or Not On Debian-Ubuntu System.md b/sources/tech/20190513 How To Check Whether The Given Package Is Installed Or Not On Debian-Ubuntu System.md
new file mode 100644
index 0000000000..dfc3e62dce
--- /dev/null
+++ b/sources/tech/20190513 How To Check Whether The Given Package Is Installed Or Not On Debian-Ubuntu System.md
@@ -0,0 +1,141 @@
+[#]: collector: (lujun9972)
+[#]: translator: ( )
+[#]: reviewer: ( )
+[#]: publisher: ( )
+[#]: url: ( )
+[#]: subject: (How To Check Whether The Given Package Is Installed Or Not On Debian/Ubuntu System?)
+[#]: via: (https://www.2daygeek.com/how-to-check-whether-the-given-package-is-installed-or-not-on-ubuntu-debian-system/)
+[#]: author: (Magesh Maruthamuthu https://www.2daygeek.com/author/magesh/)
+
+How To Check Whether The Given Package Is Installed Or Not On Debian/Ubuntu System?
+======
+
+We have recently published an article about bulk package installation.
+
+While doing that, i was struggled to get the installed package information and did a small google search and found few methods about it.
+
+I would like to share it in our website so, that it will be helpful for others too.
+
+There are numerous ways we can achieve this.
+
+I have add seven ways to achieve this. However, you can choose the preferred method for you.
+
+Those methods are listed below.
+
+ * **`apt-cache Command:`** apt-cache command is used to query the APT cache or package metadata.
+ * **`apt Command:`** APT is a powerful command-line tool for installing, downloading, removing, searching and managing packages on Debian based systems.
+ * **`dpkg-query Command:`** dpkg-query is a tool to query the dpkg database.
+ * **`dpkg Command:`** dpkg is a package manager for Debian based systems.
+ * **`which Command:`** The which command returns the full path of the executable that would have been executed when the command had been entered in terminal.
+ * **`whereis Command:`** The whereis command used to search the binary, source, and man page files for a given command.
+ * **`locate Command:`** locate command works faster than the find command because it uses updatedb database, whereas the find command searches in the real system.
+
+
+
+### Method-1 : How To Check Whether The Given Package Is Installed Or Not On Ubuntu System Using apt-cache Command?
+
+apt-cache command is used to query the APT cache or package metadata from APT’s internal database.
+
+It will search and display an information about the given package. It shows whether the package is installed or not, installed package version, source repository information.
+
+The below output clearly showing that `nano` package has already installed in the system. Since installed part is showing the installed version of nano package.
+
+```
+# apt-cache policy nano
+nano:
+ Installed: 2.9.3-2
+ Candidate: 2.9.3-2
+ Version table:
+ *** 2.9.3-2 500
+ 500 http://in.archive.ubuntu.com/ubuntu bionic/main amd64 Packages
+ 100 /var/lib/dpkg/status
+```
+
+### Method-2 : How To Check Whether The Given Package Is Installed Or Not On Ubuntu System Using apt Command?
+
+APT is a powerful command-line tool for installing, downloading, removing, searching and managing as well as querying information about packages as a low-level access to all features of the libapt-pkg library. It’s contains some less used command-line utilities related to package management.
+
+```
+# apt -qq list nano
+nano/bionic,now 2.9.3-2 amd64 [installed]
+```
+
+### Method-3 : How To Check Whether The Given Package Is Installed Or Not On Ubuntu System Using dpkg-query Command?
+
+dpkg-query is a tool to show information about packages listed in the dpkg database.
+
+In the below output first column showing `ii`. It means, the given package has already installed in the system.
+
+```
+# dpkg-query --list | grep -i nano
+ii nano 2.9.3-2 amd64 small, friendly text editor inspired by Pico
+```
+
+### Method-4 : How To Check Whether The Given Package Is Installed Or Not On Ubuntu System Using dpkg Command?
+
+DPKG stands for Debian Package is a tool to install, build, remove and manage Debian packages, but unlike other package management systems, it cannot automatically download and install packages or their dependencies.
+
+In the below output first column showing `ii`. It means, the given package has already installed in the system.
+
+```
+# dpkg -l | grep -i nano
+ii nano 2.9.3-2 amd64 small, friendly text editor inspired by Pico
+```
+
+### Method-5 : How To Check Whether The Given Package Is Installed Or Not On Ubuntu System Using which Command?
+
+The which command returns the full path of the executable that would have been executed when the command had been entered in terminal.
+
+It’s very useful when you want to create a desktop shortcut or symbolic link for executable files.
+
+Which command searches the directories listed in the current user’s PATH environment variable not for all the users. I mean, when you are logged in your own account and you can’t able to search for root user file or directory.
+
+If the following output shows the given package binary or executable file location then the given package has already installed in the system. If not, the package is not installed in system.
+
+```
+# which nano
+/bin/nano
+```
+
+### Method-6 : How To Check Whether The Given Package Is Installed Or Not On Ubuntu System Using whereis Command?
+
+The whereis command used to search the binary, source, and man page files for a given command.
+
+If the following output shows the given package binary or executable file location then the given package has already installed in the system. If not, the package is not installed in system.
+
+```
+# whereis nano
+nano: /bin/nano /usr/share/nano /usr/share/man/man1/nano.1.gz /usr/share/info/nano.info.gz
+```
+
+### Method-7 : How To Check Whether The Given Package Is Installed Or Not On Ubuntu System Using locate Command?
+
+locate command works faster than the find command because it uses updatedb database, whereas the find command searches in the real system.
+
+It uses a database rather than hunting individual directory paths to get a given file.
+
+locate command doesn’t pre-installed in most of the distributions so, use your distribution package manager to install it.
+
+The database is updated regularly through cron. Even, we can update it manually.
+
+If the following output shows the given package binary or executable file location then the given package has already installed in the system. If not, the package is not installed in system.
+
+```
+# locate --basename '\nano'
+/usr/bin/nano
+/usr/share/nano
+/usr/share/doc/nano
+```
+--------------------------------------------------------------------------------
+
+via: https://www.2daygeek.com/how-to-check-whether-the-given-package-is-installed-or-not-on-ubuntu-debian-system/
+
+作者:[Magesh Maruthamuthu][a]
+选题:[lujun9972][b]
+译者:[译者ID](https://github.com/译者ID)
+校对:[校对者ID](https://github.com/校对者ID)
+
+本文由 [LCTT](https://github.com/LCTT/TranslateProject) 原创编译,[Linux中国](https://linux.cn/) 荣誉推出
+
+[a]: https://www.2daygeek.com/author/magesh/
+[b]: https://github.com/lujun9972
diff --git a/sources/tech/20190513 How To Set Password Complexity On Linux.md b/sources/tech/20190513 How To Set Password Complexity On Linux.md
new file mode 100644
index 0000000000..e9a3171c6b
--- /dev/null
+++ b/sources/tech/20190513 How To Set Password Complexity On Linux.md
@@ -0,0 +1,243 @@
+[#]: collector: (lujun9972)
+[#]: translator: ( )
+[#]: reviewer: ( )
+[#]: publisher: ( )
+[#]: url: ( )
+[#]: subject: (How To Set Password Complexity On Linux?)
+[#]: via: (https://www.2daygeek.com/how-to-set-password-complexity-policy-on-linux/)
+[#]: author: (Magesh Maruthamuthu https://www.2daygeek.com/author/magesh/)
+
+How To Set Password Complexity On Linux?
+======
+
+User management is one of the important task of Linux system administration.
+
+There are many aspect is involved in this and implementing the strong password policy is one of them.
+
+Navigate to the following URL, if you would like to **[generate a strong password on Linux][1]**.
+
+It will Restrict unauthorized access to systems.
+
+By default Linux is secure that everybody know. however, we need to make necessary tweak on this to make it more secure.
+
+Insecure password will leads to breach security. So, take additional care on this.
+
+Navigate to the following URL, if you would like to see the **[password strength and score][2]** of the generated strong password.
+
+In this article, we will teach you, how to implement the best security policy on Linux.
+
+We can use PAM (the “pluggable authentication module”) to enforce password policy On most Linux systems.
+
+The file can be found in the following location.
+
+For Redhat based systems @ `/etc/pam.d/system-auth` and Debian based systems @ `/etc/pam.d/common-password`.
+
+The default password aging details can be found in the `/etc/login.defs` file.
+
+I have trimmed this file for better understanding.
+
+```
+# vi /etc/login.defs
+
+PASS_MAX_DAYS 99999
+PASS_MIN_DAYS 0
+PASS_MIN_LEN 5
+PASS_WARN_AGE 7
+```
+
+**Details:**
+
+ * **`PASS_MAX_DAYS:`**` ` Maximum number of days a password may be used.
+ * **`PASS_MIN_DAYS:`**` ` Minimum number of days allowed between password changes.
+ * **`PASS_MIN_LEN:`**` ` Minimum acceptable password length.
+ * **`PASS_WARN_AGE:`**` ` Number of days warning given before a password expires.
+
+
+
+We will show you, how to implement the below eleven password policies in Linux.
+
+ * Password Max days
+ * Password Min days
+ * Password warning days
+ * Password history or Deny Re-Used Passwords
+ * Password minimum length
+ * Minimum upper case characters
+ * Minimum lower case characters
+ * Minimum digits in password
+ * Minimum other characters (Symbols)
+ * Account lock – retries
+ * Account unlock time
+
+
+
+### What Is Password Max days?
+
+This parameter limits the maximum number of days a password can be used. It’s mandatory for user to change his/her account password before expiry.
+
+If they forget to change, they are not allowed to login into the system. They need to work with admin team to get rid of it.
+
+It can be set in `/etc/login.defs` file. I’m going to set `90 days`.
+
+```
+# vi /etc/login.defs
+
+PASS_MAX_DAYS 90
+```
+
+### What Is Password Min days?
+
+This parameter limits the minimum number of days after password can be changed.
+
+Say for example, if this parameter is set to 15 and user changed password today. Then he won’t be able to change the password again before 15 days from now.
+
+It can be set in `/etc/login.defs` file. I’m going to set `15 days`.
+
+```
+# vi /etc/login.defs
+
+PASS_MIN_DAYS 15
+```
+
+### What Is Password Warning Days?
+
+This parameter controls the password warning days and it will warn the user when the password is going to expires.
+
+A warning will be given to the user regularly until the warning days ends. This can helps user to change their password before expiry. Otherwise we need to work with admin team for unlock the password.
+
+It can be set in `/etc/login.defs` file. I’m going to set `10 days`.
+
+```
+# vi /etc/login.defs
+
+PASS_WARN_AGE 10
+```
+
+**Note:** All the above parameters only applicable for new accounts and not for existing accounts.
+
+### What Is Password History Or Deny Re-Used Passwords?
+
+This parameter keep controls of the password history. Keep history of passwords used (the number of previous passwords which cannot be reused).
+
+When the users try to set a new password, it will check the password history and warn the user when they set the same old password.
+
+It can be set in `/etc/pam.d/system-auth` file. I’m going to set `5` for history of password.
+
+```
+# vi /etc/pam.d/system-auth
+
+password sufficient pam_unix.so md5 shadow nullok try_first_pass use_authtok remember=5
+```
+
+### What Is Password Minimum Length?
+
+This parameter keeps the minimum password length. When the users set a new password, it will check against this parameter and warn the user if they try to set the password length less than that.
+
+It can be set in `/etc/pam.d/system-auth` file. I’m going to set `12` character for minimum password length.
+
+```
+# vi /etc/pam.d/system-auth
+
+password requisite pam_cracklib.so try_first_pass retry=3 minlen=12
+```
+
+**try_first_pass retry=3** : Allow users to set a good password before the passwd command aborts.
+
+### Set Minimum Upper Case Characters?
+
+This parameter keeps, how many upper case characters should be added in the password. These are password strengthening parameters ,which increase the password strength.
+
+When the users set a new password, it will check against this parameter and warn the user if they are not including any upper case characters in the password.
+
+It can be set in `/etc/pam.d/system-auth` file. I’m going to set `1` character for minimum password length.
+
+```
+# vi /etc/pam.d/system-auth
+
+password requisite pam_cracklib.so try_first_pass retry=3 minlen=12 ucredit=-1
+```
+
+### Set Minimum Lower Case Characters?
+
+This parameter keeps, how many lower case characters should be added in the password. These are password strengthening parameters ,which increase the password strength.
+
+When the users set a new password, it will check against this parameter and warn the user if they are not including any lower case characters in the password.
+
+It can be set in `/etc/pam.d/system-auth` file. I’m going to set `1` character.
+
+```
+# vi /etc/pam.d/system-auth
+
+password requisite pam_cracklib.so try_first_pass retry=3 minlen=12 lcredit=-1
+```
+
+### Set Minimum Digits In Password?
+
+This parameter keeps, how many digits should be added in the password. These are password strengthening parameters ,which increase the password strength.
+
+When the users set a new password, it will check against this parameter and warn the user if they are not including any digits in the password.
+
+It can be set in `/etc/pam.d/system-auth` file. I’m going to set `1` character.
+
+```
+# vi /etc/pam.d/system-auth
+
+password requisite pam_cracklib.so try_first_pass retry=3 minlen=12 dcredit=-1
+```
+
+### Set Minimum Other Characters (Symbols) In Password?
+
+This parameter keeps, how many Symbols should be added in the password. These are password strengthening parameters ,which increase the password strength.
+
+When the users set a new password, it will check against this parameter and warn the user if they are not including any Symbol in the password.
+
+It can be set in `/etc/pam.d/system-auth` file. I’m going to set `1` character.
+
+```
+# vi /etc/pam.d/system-auth
+
+password requisite pam_cracklib.so try_first_pass retry=3 minlen=12 ocredit=-1
+```
+
+### Set Account Lock?
+
+This parameter controls users failed attempts. It locks user account after reaches the given number of failed login attempts.
+
+It can be set in `/etc/pam.d/system-auth` file.
+
+```
+# vi /etc/pam.d/system-auth
+
+auth required pam_tally2.so onerr=fail audit silent deny=5
+account required pam_tally2.so
+```
+
+### Set Account Unlock Time?
+
+This parameter keeps users unlock time. If the user account is locked after consecutive failed authentications.
+
+It’s unlock the locked user account after reaches the given time. Sets the time (900 seconds = 15 minutes) for which the account should remain locked.
+
+It can be set in `/etc/pam.d/system-auth` file.
+
+```
+# vi /etc/pam.d/system-auth
+
+auth required pam_tally2.so onerr=fail audit silent deny=5 unlock_time=900
+account required pam_tally2.so
+```
+
+--------------------------------------------------------------------------------
+
+via: https://www.2daygeek.com/how-to-set-password-complexity-policy-on-linux/
+
+作者:[Magesh Maruthamuthu][a]
+选题:[lujun9972][b]
+译者:[译者ID](https://github.com/译者ID)
+校对:[校对者ID](https://github.com/校对者ID)
+
+本文由 [LCTT](https://github.com/LCTT/TranslateProject) 原创编译,[Linux中国](https://linux.cn/) 荣誉推出
+
+[a]: https://www.2daygeek.com/author/magesh/
+[b]: https://github.com/lujun9972
+[1]: https://www.2daygeek.com/5-ways-to-generate-a-random-strong-password-in-linux-terminal/
+[2]: https://www.2daygeek.com/how-to-check-password-complexity-strength-and-score-in-linux/
diff --git a/sources/tech/20190513 Manage business documents with OpenAS2 on Fedora.md b/sources/tech/20190513 Manage business documents with OpenAS2 on Fedora.md
new file mode 100644
index 0000000000..c8e82151ef
--- /dev/null
+++ b/sources/tech/20190513 Manage business documents with OpenAS2 on Fedora.md
@@ -0,0 +1,153 @@
+[#]: collector: (lujun9972)
+[#]: translator: ( )
+[#]: reviewer: ( )
+[#]: publisher: ( )
+[#]: url: ( )
+[#]: subject: (Manage business documents with OpenAS2 on Fedora)
+[#]: via: (https://fedoramagazine.org/manage-business-documents-with-openas2-on-fedora/)
+[#]: author: (Stuart D Gathman https://fedoramagazine.org/author/sdgathman/)
+
+Manage business documents with OpenAS2 on Fedora
+======
+
+![][1]
+
+Business documents often require special handling. Enter Electronic Document Interchange, or **EDI**. EDI is more than simply transferring files using email or http (or ftp), because these are documents like orders and invoices. When you send an invoice, you want to be sure that:
+
+1\. It goes to the right destination, and is not intercepted by competitors.
+2\. Your invoice cannot be forged by a 3rd party.
+3\. Your customer can’t claim in court that they never got the invoice.
+
+The first two goals can be accomplished by HTTPS or email with S/MIME, and in some situations, a simple HTTPS POST to a web API is sufficient. What EDI adds is the last part.
+
+This article does not cover the messy topic of formats for the files exchanged. Even when using a standardized format like ANSI or EDIFACT, it is ultimately up to the business partners. It is not uncommon for business partners to use an ad-hoc CSV file format. This article shows you how to configure Fedora to send and receive in an EDI setup.
+
+### Centralized EDI
+
+The traditional solution is to use a Value Added Network, or **VAN**. The VAN is a central hub that transfers documents between their customers. Most importantly, it keeps a secure record of the documents exchanged that can be used as evidence in disputes. The VAN can use different transfer protocols for each of its customers
+
+### AS Protocols and MDN
+
+The AS protocols are a specification for adding a digital signature with optional encryption to an electronic document. What it adds over HTTPS or S/MIME is the Message Disposition Notification, or **MDN**. The MDN is a signed and dated response that says, in essence, “We got your invoice.” It uses a secure hash to identify the specific document received. This addresses point #3 without involving a third party.
+
+The [AS2 protocol][2] uses HTTP or HTTPS for transport. Other AS protocols target [FTP][3] and [SMTP][4]. AS2 is used by companies big and small to avoid depending on (and paying) a VAN.
+
+### OpenAS2
+
+OpenAS2 is an open source Java implemention of the AS2 protocol. It is available in Fedora since 28, and installed with:
+
+```
+$ sudo dnf install openas2
+$ cd /etc/openas2
+```
+
+Configuration is done with a text editor, and the config files are in XML. The first order of business before starting OpenAS2 is to change the factory passwords.
+
+Edit _/etc/openas2/config.xml_ and search for _ChangeMe_. Change those passwords. The default password on the certificate store is _testas2_ , but that doesn’t matter much as anyone who can read the certificate store can read _config.xml_ and get the password.
+
+### What to share with AS2 partners
+
+There are 3 things you will exchange with an AS2 peer.
+
+#### AS2 ID
+
+Don’t bother looking up the official AS2 standard for legal AS2 IDs. While OpenAS2 implements the standard, your partners will likely be using a proprietary product which doesn’t. While AS2 allows much longer IDs, many implementations break with more than 16 characters. Using otherwise legal AS2 ID chars like ‘:’ that can appear as path separators on a proprietary OS is also a problem. Restrict your AS2 ID to upper and lower case alpha, digits, and ‘_’ with no more than 16 characters.
+
+#### SSL certificate
+
+For real use, you will want to generate a certificate with SHA256 and RSA. OpenAS2 ships with two factory certs to play with. Don’t use these for anything real, obviously. The certificate file is in PKCS12 format. Java ships with _keytool_ which can maintain your PKCS12 “keystore,” as Java calls it. This article skips using _openssl_ to generate keys and certificates. Simply note that _sudo keytool -list -keystore as2_certs.p12_ will list the two factory practice certs.
+
+#### AS2 URL
+
+This is an HTTP URL that will access your OpenAS2 instance. HTTPS is also supported, but is redundant. To use it you have to uncomment the https module configuration in _config.xml_ , and supply a certificate signed by a public CA. This requires another article and is entirely unnecessary here.
+
+By default, OpenAS2 listens on 10080 for HTTP and 10443 for HTTPS. OpenAS2 can talk to itself, so it ships with two partnerships using __ as the AS2 URL. If you don’t find this a convincing demo, and can install a second instance (on a VM, for instance), you can use private IPs for the AS2 URLs. Or install [Cjdns][5] to get IPv6 mesh addresses that can be used anywhere, resulting in AS2 URLs like _http://[fcbf:fc54:e597:7354:8250:2b2e:95e6:d6ba]:10080_.
+
+Most businesses will also want a list of IPs to add to their firewall. This is actually [bad practice][6]. An AS2 server has the same security risk as a web server, meaning you should isolate it in a VM or container. Also, the difficulty of keeping mutual lists of IPs up to date grows with the list of partners. The AS2 server rejects requests not signed by a configured partner.
+
+### OpenAS2 Partners
+
+With that in mind, open _partnerships.xml_ in your editor. At the top is a list of “partners.” Each partner has a name (referenced by the partnerships below as “sender” or “receiver”), AS2 ID, certificate, and email. You need a partner definition for yourself and those you exchange documents with. You can define multiple partners for yourself. OpenAS2 ships with two partners, OpenAS2A and OpenAS2B, which you’ll use to send a test document.
+
+### OpenAS2 Partnerships
+
+Next is a list of “partnerships,” one for each direction. Each partnership configuration includes the sender, receiver, and the AS2 URL used to send the documents. By default, partnerships use synchronous MDN. The MDN is returned on the same HTTP transaction. You could uncomment the _as2_receipt_option_ for asynchronous MDN, which is sent some time later. Use synchronous MDN whenever possible, as tracking pending MDNs adds complexity to your application.
+
+The other partnership options select encryption, signature hash, and other protocol options. A fully implemented AS2 receiver can handle any combination of options, but AS2 partners may have incomplete implementations or policy requirements. For example, DES3 is a comparatively weak encryption algorithm, and may not be acceptable. It is the default because it is almost universally implemented.
+
+If you went to the trouble to set up a second physical or virtual machine for this test, designate one as OpenAS2A and the other as OpenAS2B. Modify the _as2_url_ on the OpenAS2A-to-OpenAS2B partnership to use the IP (or hostname) of OpenAS2B, and vice versa for the OpenAS2B-to-OpenAS2A partnership. Unless they are using the FedoraWorkstation firewall profile, on both machines you’ll need:
+
+```
+# sudo firewall-cmd --zone=public --add-port=10080/tcp
+```
+
+Now start the _openas2_ service (on both machines if needed):
+
+```
+# sudo systemctl start openas2
+```
+
+### Resetting the MDN password
+
+This initializes the MDN log database with the factory password, not the one you changed it to. This is a packaging bug to be fixed in the next release. To avoid frustration, here’s how to change the h2 database password:
+
+```
+$ sudo systemctl stop openas2
+$ cat >h2passwd <<'DONE'
+#!/bin/bash
+AS2DIR="/var/lib/openas2"
+java -cp "$AS2DIR"/lib/h2* org.h2.tools.Shell \
+ -url jdbc:h2:"$AS2DIR"/db/openas2 \
+ -user sa -password "$1" <testdoc <<'DONE'
+This is not a real EDI format, but is nevertheless a document.
+DONE
+$ sudo chown openas2 testdoc
+$ sudo mv testdoc /var/spool/openas2/toOpenAS2B
+$ sudo journalctl -f -u openas2
+... log output of sending file, Control-C to stop following log
+^C
+```
+
+OpenAS2 does not send a document until it is writable by the _openas2_ user or group. As a consequence, your actual business application will copy, or generate in place, the document. Then it changes the group or permissions to send it on its way, to avoid sending a partial document.
+
+Now, on the OpenAS2B machine, _/var/spool/openas2/OpenAS2A_OID-OpenAS2B_OID/inbox_ shows the message received. That should get you started!
+
+* * *
+
+_Photo by _[ _Beatriz Pérez Moya_][7]_ on _[_Unsplash_][8]_._
+
+--------------------------------------------------------------------------------
+
+via: https://fedoramagazine.org/manage-business-documents-with-openas2-on-fedora/
+
+作者:[Stuart D Gathman][a]
+选题:[lujun9972][b]
+译者:[译者ID](https://github.com/译者ID)
+校对:[校对者ID](https://github.com/校对者ID)
+
+本文由 [LCTT](https://github.com/LCTT/TranslateProject) 原创编译,[Linux中国](https://linux.cn/) 荣誉推出
+
+[a]: https://fedoramagazine.org/author/sdgathman/
+[b]: https://github.com/lujun9972
+[1]: https://fedoramagazine.org/wp-content/uploads/2019/05/openas2-816x345.jpg
+[2]: https://en.wikipedia.org/wiki/AS2
+[3]: https://en.wikipedia.org/wiki/AS3_(networking)
+[4]: https://en.wikipedia.org/wiki/AS1_(networking)
+[5]: https://fedoramagazine.org/decentralize-common-fedora-apps-cjdns/
+[6]: https://www.ld.com/as2-part-2-best-practices/
+[7]: https://unsplash.com/photos/XN4T2PVUUgk?utm_source=unsplash&utm_medium=referral&utm_content=creditCopyText
+[8]: https://unsplash.com/search/photos/documents?utm_source=unsplash&utm_medium=referral&utm_content=creditCopyText
diff --git a/sources/tech/20190513 When to be concerned about memory levels on Linux.md b/sources/tech/20190513 When to be concerned about memory levels on Linux.md
new file mode 100644
index 0000000000..c42d417e9e
--- /dev/null
+++ b/sources/tech/20190513 When to be concerned about memory levels on Linux.md
@@ -0,0 +1,121 @@
+[#]: collector: (lujun9972)
+[#]: translator: (luuming)
+[#]: reviewer: ( )
+[#]: publisher: ( )
+[#]: url: ( )
+[#]: subject: (When to be concerned about memory levels on Linux)
+[#]: via: (https://www.networkworld.com/article/3394603/when-to-be-concerned-about-memory-levels-on-linux.html)
+[#]: author: (Sandra Henry-Stocker https://www.networkworld.com/author/Sandra-Henry_Stocker/)
+
+When to be concerned about memory levels on Linux
+======
+Memory management on Linux systems is complicated. Seeing high usage doesn’t necessarily mean there’s a problem. There are other things you should also consider.
+![Qfamily \(CC BY 2.0\)][1]
+
+Running out of memory on a Linux system is generally _not_ a sign that there's a serious problem. Why? Because a healthy Linux system will cache disk activity in memory, basically gobbling memory that isn't being used, which is a very good thing.
+
+In other words, it doesn't allow memory to go to waste. It uses the spare memory to increase disk access speed, and it does this _without_ taking memory away from running applications. This memory caching, as you might well imagine, is hundreds of times faster than working directly with the hard-disk drives (HDD) and significantly faster than solid-state drives. Full or near full memory normally means that a system is running as efficiently as it can — not that it's running into problems.
+
+**[ Also see:[Must-know Linux Commands][2] ]**
+
+### How caching works
+
+Disk caching simply means that a system is taking advantage of unused resources (free memory) to speed up disk reads and writes. Applications don't lose anything and most of the time can acquire more memory whenever they need it. In addition, disk caching does not cause applications to resort to using swap. Instead, memory used for disk caching is always returned immediately when needed and disk content updated.
+
+### Major and minor page faults
+
+Linux systems allocate memory to processes by breaking physical memory into chunks called "pages" and then mapping those pages into process virtual memory. Pages that appear to no longer be used may be removed from memory — even if the related process is still running. When a process needs a page that is no longer mapped or no longer in memory, a fault is generated. So, "fault" does not mean "error" but instead means "unavailable," and faults play an important role in memory management.
+
+A minor fault means the page is in memory but not allocated to the requesting process or not marked as present in the memory management unit. A major fault means the page in no longer in memory.
+
+If you'd like to get a feel for how often minor and major page faults occur, try a **ps** command like this one. Note that we're asking for the fields related to page faults and the commands to be listed. Numerous lines were omitted from the output. The MINFL displays the number of minor faults, while MAJFL represents the number of major faults.
+
+```
+$ ps -eo min_flt,maj_flt,cmd
+ MINFL MAJFL CMD
+230760 150 /usr/lib/systemd/systemd --switched-root --system --deserialize 18
+ 0 0 [kthreadd]
+ 0 0 [rcu_gp]
+ 0 0 [rcu_par_gp]
+ 0 0 [kworker/0:0H-kblockd]
+ ...
+ 166 20 gpg-agent --homedir /var/lib/fwupd/gnupg --use-standard-socket --daemon
+ 525 1 /usr/libexec/gvfsd-trash --spawner :1.16 /org/gtk/gvfs/exec_spaw/0
+ 4966 4 /usr/libexec/gnome-terminal-server
+ 3617 0 bash
+ 0 0 [kworker/1:0H-kblockd]
+ 927 0 gdm-session-worker [pam/gdm-password]
+```
+
+To report on a single process, you might try a command like this:
+
+```
+$ ps -o min_flt,maj_flt 1
+ MINFL MAJFL
+230064 150
+```
+
+You can also add other fields such as the process owner's UID and GID.
+
+```
+$ ps -o min_flt,maj_flt,cmd,args,uid,gid 1
+ MINFL MAJFL CMD COMMAND UID GID
+230064 150 /usr/lib/systemd/systemd -- /usr/lib/systemd/systemd -- 0 0
+```
+
+### How full is full?
+
+One way to get a better handle on how memory is being used is with the **free -m** command. The **-m** option reports the numbers in mebibytes (MiBs) instead of bytes.
+
+```
+$ free -m
+ total used free shared buff/cache available
+Mem: 3244 3069 35 49 140 667
+Swap: 3535 0 3535
+```
+
+Note that "free" (unused) memory can be running low while "available" (available for starting new applications) might report a larger number. The distinction between these two fields is well worth paying attention to. Available means that it can be recovered and used when needed, while free means that it's available now.
+
+### When to worry
+
+If performance on a Linux systems appears to be good — applications are responsive, the command line shows no indications of a problem — chances are the system's in good shape. Keep in mind that some application might be slowed down for some reason that doesn't affect the overall system.
+
+An excessive number of hard faults may indeed indicate a problem, but balance this with observed performance.
+
+A good rule of thumb is to worry when available memory is close to zero or when the "swap used" field grows or fluctuates noticeably. Don't worry if the "available" figure is a reasonable percentage of the total memory available as it is in the example from above repeated here:
+
+```
+$ free -m
+ total used free shared buff/cache available
+Mem: 3244 3069 35 49 140 667
+Swap: 3535 0 3535
+```
+
+### Linux performance is complicated
+
+All that aside, memory on a Linux system can fill up and performance can slow down. Just don't take one report on memory usage as an indication that your system's in trouble.
+
+Memory management on Linux systems is complicated because of the measures taken to ensure the best use of system resources. Don't let the initial appearance of full memory trick you into believing that your system is in trouble when it isn't.
+
+**[ Two-Minute Linux Tips:[Learn how to master a host of Linux commands in these 2-minute video tutorials][3] ]**
+
+Join the Network World communities on [Facebook][4] and [LinkedIn][5] to comment on topics that are top of mind.
+
+--------------------------------------------------------------------------------
+
+via: https://www.networkworld.com/article/3394603/when-to-be-concerned-about-memory-levels-on-linux.html
+
+作者:[Sandra Henry-Stocker][a]
+选题:[lujun9972][b]
+译者:[译者ID](https://github.com/译者ID)
+校对:[校对者ID](https://github.com/校对者ID)
+
+本文由 [LCTT](https://github.com/LCTT/TranslateProject) 原创编译,[Linux中国](https://linux.cn/) 荣誉推出
+
+[a]: https://www.networkworld.com/author/Sandra-Henry_Stocker/
+[b]: https://github.com/lujun9972
+[1]: https://images.idgesg.net/images/article/2019/05/full-swimming-pool-100796221-large.jpg
+[2]: https://www.networkworld.com/article/3391029/must-know-linux-commands.html
+[3]: https://www.youtube.com/playlist?list=PL7D2RMSmRO9J8OTpjFECi8DJiTQdd4hua
+[4]: https://www.facebook.com/NetworkWorld/
+[5]: https://www.linkedin.com/company/network-world
diff --git a/sources/tech/20190515 How to manage access control lists with Ansible.md b/sources/tech/20190515 How to manage access control lists with Ansible.md
new file mode 100644
index 0000000000..692dd70599
--- /dev/null
+++ b/sources/tech/20190515 How to manage access control lists with Ansible.md
@@ -0,0 +1,139 @@
+[#]: collector: (lujun9972)
+[#]: translator: ( )
+[#]: reviewer: ( )
+[#]: publisher: ( )
+[#]: url: ( )
+[#]: subject: (How to manage access control lists with Ansible)
+[#]: via: (https://opensource.com/article/19/5/manage-access-control-lists-ansible)
+[#]: author: (Taz Brown https://opensource.com/users/heronthecli)
+
+How to manage access control lists with Ansible
+======
+Automating ACL management with Ansible's ACL module is a smart way to
+strengthen your security strategy.
+![Data container block with hexagons][1]
+
+Imagine you're a new DevOps engineer in a growing agile environment, and recently your company has experienced phenomenal growth. To support expansion, the company increased hiring by 25% over the last quarter and added 5,000 more servers and network devices to its infrastructure. The company now has over 13,000 users, and you need a tool to scale the existing infrastructure and manage your large number of users and their thousands of files and directories. The company decided to adopt [Ansible][2] company-wide to manage [access control lists (ACLs)][3] and answer the call of effectively managing files and directories and permissions.
+
+Ansible can be used for a multitude of administration and maintenance tasks and, as a DevOps engineer or administrator, it's likely you've been tasked with using it to manage ACLs.
+
+### About managing ACLs
+
+ACLs allow regular users to share their files and directories selectively with other users and groups. With ACLs, a user can grant others the ability to read, write, and execute files and directories without leaving those filesystem elements open.
+
+ACLs are set and removed at the command line using the **setfacl** utility. The command is usually followed by the name of a file or directory. To set permissions, you would use the Linux command **setfacl -m d ⭕rx ** (e.g., **setfacl -m d ⭕rx Music/**). To view the current permissions on a directory, you would use the command **getfacl ** (e.g., **getfacl Music/** ). To remove an ACL from a file or directory, you would type the command, **# setfacl -x ** (to remove only the specified ACL from the file/directory) or **# setfacl -b ** (to remove all ACLs from the file/directory).
+
+Only the owner assigned to the file or directory can set ACLs. (It's important to understand this before you, as the admin, take on Ansible to manage your ACLs.) There are also default ACLs, which control directory access; if a file inside a directory has no ACL, then the default ACL is applied.
+
+
+```
+sudo setfacl -m d⭕rx Music
+getfacl Music/
+# file: Music/
+# owner: root
+# group: root
+user::rwx
+group::---
+other::---
+default:user::rwx
+default:group::---
+default:other::r-x
+```
+
+### Enter Ansible
+
+So how can Ansible, in all its wisdom, tackle the task of applying permissions to users, files, directories, and more? Ansible can play nicely with ACLs, just as it does with a lot of features, utilities, APIs, etc. Ansible has an out-of-the-box [ACL module][3] that allows you to create playbooks/roles around granting a user access to a file, removing ACLs for users on a specific file, setting default ACLs for users on files, or obtaining ACLs on particular files.
+
+Anytime you are administering ACLs, you should use the best practice of "least privilege," meaning you should give a user access only to what they need to perform their role or execute a task, and no more. Restraint and minimizing the attack surface are critical. The more access extended, the higher the risk of unauthorized access to company assets.
+
+Here's an example Ansible playbook:
+
+![Ansible playbook][4]
+
+As an admin, automating ACL management demands that your Ansible playbooks can scale across your infrastructure to increase speed, improve efficiency, and reduce the time it takes to achieve your goals. There will be times when you need to determine the ACL for a specific file. This is essentially the same as using **getfacl ** in Linux. If you want to determine the ACLs of many, specific files, start with a playbook that looks like this:
+
+
+```
+\---
+\- hosts: all
+tasks:
+\- name: obtain the acl for a specific file
+acl:
+path: /etc/logrotate.d
+user_nfsv4_acls: true
+register: acl_info
+```
+
+You can use the following playbook to set permissions on files/directories:
+
+![Ansible playbook][5]
+
+This playbook grants user access to a file:
+
+
+```
+\- hosts:
+become: yes
+gather_facts: no
+tasks:
+\- name: Grant user Shirley read access to a file
+acl:
+path: /etc/foo.conf
+entity: shirley
+etype: user
+permissions: r
+state: present
+```
+
+And this playbook grants user access to a directory:
+
+
+```
+\---
+\- hosts: all
+become: yes
+gather_facts: no
+tasks:
+\- name: setting permissions on directory and user
+acl:
+path: /path/to/scripts/directory
+entity: "{{ item }}"
+etype: user
+permissions: rwx
+state: present
+loop:
+\- www-data
+\- root
+```
+
+### Security realized?
+
+Applying ACLs to files and users is a practice you should take seriously in your role as a DevOps engineer. Security best practices and formal compliance often get little or no attention. When you allow access to files with sensitive data, you are always risking that the data will be tampered with, stolen, or deleted. Therefore, data protection must be a focal point in your security strategy. Ansible can be part of your security automation strategy, as demonstrated here, and your ACL application is as good a place to start as any.
+
+Automating your security practices will, of course, go beyond just managing ACLs; it might also involve [SELinux][6] configuration, cryptography, security, and compliance. Remember that Ansible also allows you to define your systems for security, whether it's locking down users and groups (e.g., managing ACLs), setting firewall rules, or applying custom security policies.
+
+Your security strategy should start with a baseline plan. As a DevOps engineer or admin, you should examine the current security strategy (or the lack thereof), then chart your plan for automating security in your environment.
+
+### Conclusion
+
+Using Ansible to manage your ACLs as part of your overall security automation strategy depends on the size of both the company you work for and the infrastructure you manage. Permissions, users, and files can quickly get out of control, potentially placing your security in peril and putting the company in a position you definitely don't want to it be.
+
+--------------------------------------------------------------------------------
+
+via: https://opensource.com/article/19/5/manage-access-control-lists-ansible
+
+作者:[Taz Brown ][a]
+选题:[lujun9972][b]
+译者:[译者ID](https://github.com/译者ID)
+校对:[校对者ID](https://github.com/校对者ID)
+
+本文由 [LCTT](https://github.com/LCTT/TranslateProject) 原创编译,[Linux中国](https://linux.cn/) 荣誉推出
+
+[a]: https://opensource.com/users/heronthecli
+[b]: https://github.com/lujun9972
+[1]: https://opensource.com/sites/default/files/styles/image-full-size/public/lead-images/data_container_block.png?itok=S8MbXEYw (Data container block with hexagons)
+[2]: https://opensource.com/article/19/2/quickstart-guide-ansible
+[3]: https://docs.ansible.com/ansible/latest/modules/acl_module.html
+[4]: https://opensource.com/sites/default/files/images/acl.yml_.png (Ansible playbook)
+[5]: https://opensource.com/sites/default/files/images/set_filedir_permissions.png (Ansible playbook)
+[6]: https://opensource.com/article/18/8/cheat-sheet-selinux
diff --git a/sources/tech/20190516 Create flexible web content with a headless management system.md b/sources/tech/20190516 Create flexible web content with a headless management system.md
new file mode 100644
index 0000000000..df58e96d0d
--- /dev/null
+++ b/sources/tech/20190516 Create flexible web content with a headless management system.md
@@ -0,0 +1,113 @@
+[#]: collector: (lujun9972)
+[#]: translator: ( )
+[#]: reviewer: ( )
+[#]: publisher: ( )
+[#]: url: ( )
+[#]: subject: (Create flexible web content with a headless management system)
+[#]: via: (https://opensource.com/article/19/5/headless-cms)
+[#]: author: (Sam Bocetta https://opensource.com/users/sambocetta)
+
+Create flexible web content with a headless management system
+======
+Get the versatility and freedom to deliver content however you think is
+best.
+![Browser of things][1]
+
+In recent years, we’ve witnessed an explosion in the number of technological devices that deliver web-based content to users. Smartphones, tablets, smartwatches, and more—all with progressively advancing technical capabilities and support for an ever-widening list of operating systems and web browsers—swarm anew onto the market each year.
+
+What does this trend have to do with web development and headless versus traditional Content Management Systems (CMS)? Quite a lot.
+
+### CMS creates the internet
+
+A CMS is an application or set of computer programs used to manage digital content like images, videos, blog posts—essentially anything you would post on a website. An obvious example of a CMS is [WordPress][2].
+
+The word "manage" is used broadly here. It can refer to creating, editing, or updating any kind of digital content on a website, as well as indexing the site to make it easily searchable.
+
+So, a CMS essentially separates the content displayed on a website from how that content is displayed. It also allows you, the website administrator, to set permissions on who can access, edit, modify, or otherwise manage that content.
+
+Suppose you want to post a new blog entry, update or correct something in an old post, write on your Facebook page, share a social media link to a video or article, or embed a video, music file, or pre-written set of text into a page on your website. If you have ever done anything like this, you have made use of CMS features.
+
+### Traditional CMS architecture: Benefits and flaws
+
+There are two major components that make up a CMS: the Content Management Application (CMA) and the Content Delivery Application (CDA). The CMA pertains to the front-end portion of the website. This is what allows authors or other content managers to edit and create content without help from a web developer. The CDA pertains to the back end portion of a website. By organizing and compiling content to make website content updates possible, it automates the function of a website administrator.
+
+Traditionally, these two pieces are joined into a single unit as a "coupled" CMS architecture. A **coupled CMS** uses a specific front-end delivery system (CMA) built into the application itself. The term "coupled" comes from the fact that the front-end framework—the templates and layout of the pages and how those pages respond to being opened in certain browsers—is coupled to the website’s content. In other words, in a coupled CMS architecture the Content Management Application (CMA) and Content Delivery Application (CDA) are inseparably merged.
+
+#### Benefits of the traditional CMS
+
+Coupled architecture does offer advantages, mainly in simplicity and ease of use for those who are not technically sophisticated. This fact explains why a platform like WordPress, which retains a traditional CMS setup, [remains so popular][3] for those who create websites or blogs.
+
+Further simplifying the web development process [are website builder applications][4], such as [Wix][5] and [Squarespace][6], which allow you to build drag-and-drop websites. The most popular of these builders use open source libraries but are themselves closed source. These sites allow almost anyone who can find the internet to put a website together without wading through the relatively short weeds of a CMS environment. While builder applications were [the object of derision][7] not so long ago amongst many in the open source community—mainly because they tended to give websites a generic and pre-packaged look and feel—they have grown increasingly functional and variegated.
+
+#### Security is an issue
+
+However, for all but the simplest web apps, a traditional CMS architecture results in inflexible technology. Modifying a static website or web app with a traditional CMS requires tremendous time and effort to produce updates, patches, and installations, preventing developers from keeping up with the growing number of devices and browsers.
+
+Furthermore, coupled CMSs have two built-in security flaws:
+
+**Risk #1** : Since content management and delivery are bound together, hackers who breach your website through the front end automatically gain access to the back-end database. This lack of separation between data and its presentation increases the likelihood that data will be stolen. Depending on the kind of user data stored on your website’s servers, a large-scale theft could be catastrophic.
+
+**Risk #2** : The risk of successful [Distributed Denial of Service][8] (DDoS) attacks increases without a separate system for delivering content to your website. DDoS attacks flood content delivery networks with so many traffic requests that they become overwhelmed and go offline. If your content delivery network is separated from your actual web servers, attackers will be less able to bring down your site.
+
+To avoid these problems, developers have introduced headless and decoupled CMSs.
+
+### Comparing headless and decoupled CMSs
+
+The "head" of a CMS is a catch-all term for the Content Delivery Application. Therefore, a CMS without one—and so with no way of delivering content to a user—is called "headless."
+
+This lack of an established delivery method gives headless CMSs enormous versatility. Without a CDA there is no pre-established delivery method, so developers can design separate frameworks as the need arises. The problem of constantly patching your website, web apps, and other code to guarantee compatibility disappears.
+
+Another option, a **decoupled CMS** , includes many of the same features and benefits as a headless CMS, but there is one crucial difference. Where a headless CMS leaves it entirely to the developer to deliver and present content to their users, a decoupled CMS offers pre-established delivery tools that developers can either take or leave. Decoupled CMSs thus offer both the simplicity of the traditional CMS and the versatility of the headless ones.
+
+In short, a decoupled CMS is sometimes called a **hybrid CMS ****since it's a hybrid of the coupled and headless designs. Decoupled CMSs are not a new concept. As far back as 2015, PHP core repository developer David Buchmann was [calling on devs][9] to decouple their CMSs to meet a wider set of challenges.
+
+### Security improvements with a headless CMS
+
+Perhaps the most important point to make about headless versus decoupled content management architectures, and how they both differ from traditional architecture, is the added security benefit. In both the headless and decoupled designs, content and user data are located on a separate back-end system protected by a firewall. The user can’t access the content management application itself.
+
+However, it's important to keep in mind that the major consequence of this change in architectures is that since the architecture is fragmented, developers have to fill in the gaps and design content delivery and presentation mechanisms on their own. This means that whether you opt to go headless or decoupled, your developer needs to understand security. While separating content management and content delivery gives hackers one fewer vector through which to attack, this isn’t a security benefit in itself. The burden will be on your devs to properly secure your resulting CDA.
+
+A firewall protecting the back end provides a [crucial layer of security][10]. Headless and decoupled architectures can distribute your content among multiple databases, so if you take advantage of this possibility you can lower the chance of successful DDoS attacks even further. Open source headless CMS can also benefit from the installation of a [Linux VPN][11] or Linux kernel firewall management tool like [iptables][12]. All of these options combine to provide the added security developers need to create no matter what kind of CDA or back end setup they choose.
+
+Benefits aside, keep in mind that headless CMS platforms are a fairly new tech. Before making the switch to headless or decoupled, consider whether the host you’re using can support your added security so that you can host your application behind network security systems to block attempts at unauthorized access. If they cannot, a host change might be in order. When evaluating new hosts, also consider any existing contracts or security and compliance restrictions in place (GDPR, CCPA, etc.) which could cause migration troubles.
+
+### Open source options
+
+As you can see, headless architecture offers designers the versatility and freedom to deliver content however they think best. This spirit of freedom fits naturally with the open source paradigm in software design, in which all source code is available to public view and may be taken and modified by anyone for any reason.
+
+There are a number of open source headless CMS platforms that allow developers to do just that: [Mura,][13] [dotCMS][14], and [Cockpit CMS][15] to name a few. For a deeper dive into the world of open source headless CMS platforms, [check out this article][16].
+
+### Final thoughts
+
+For web designers and developers, the idea of a headless CMS marks a significant rethinking of how sites are built and delivered. Moving to this architecture is a great way to future-proof your website against changing preferences and whatever tricks future hackers may cook up, while at the same time creating a seamless user experience no matter what device or browser is used. You might also take a look at [this guide][17] for UX tips on designing your website in a way that meshes with headless and decoupled architectures.
+
+--------------------------------------------------------------------------------
+
+via: https://opensource.com/article/19/5/headless-cms
+
+作者:[Sam Bocetta][a]
+选题:[lujun9972][b]
+译者:[译者ID](https://github.com/译者ID)
+校对:[校对者ID](https://github.com/校对者ID)
+
+本文由 [LCTT](https://github.com/LCTT/TranslateProject) 原创编译,[Linux中国](https://linux.cn/) 荣誉推出
+
+[a]: https://opensource.com/users/sambocetta
+[b]: https://github.com/lujun9972
+[1]: https://opensource.com/sites/default/files/styles/image-full-size/public/lead-images/browser_desktop_website_checklist_metrics.png?itok=OKKbl1UR (Browser of things)
+[2]: https://wordpress.org/
+[3]: https://kinsta.com/wordpress-market-share/
+[4]: https://hostingcanada.org/website-builders/
+[5]: https://www.wix.com/
+[6]: https://www.squarespace.com
+[7]: https://arstechnica.com/information-technology/2016/11/wordpress-and-wix-trade-shots-over-alleged-theft-of-open-source-code/
+[8]: https://www.cloudflare.com/learning/ddos/what-is-a-ddos-attack/
+[9]: https://opensource.com/business/15/3/decoupling-your-cms
+[10]: https://www.hostpapa.com/blog/security/why-your-small-business-needs-a-firewall/
+[11]: https://surfshark.com/download/linux
+[12]: https://www.linode.com/docs/security/firewalls/control-network-traffic-with-iptables/
+[13]: https://www.getmura.com/
+[14]: https://dotcms.com/
+[15]: https://getcockpit.com/
+[16]: https://www.cmswire.com/web-cms/13-headless-cmss-to-put-on-your-radar/
+[17]: https://medium.com/@mat_walker/tips-for-content-modelling-with-the-headless-cms-contentful-7e886a911962
diff --git a/sources/tech/20190516 System76-s secret sauce for success.md b/sources/tech/20190516 System76-s secret sauce for success.md
new file mode 100644
index 0000000000..9409de535f
--- /dev/null
+++ b/sources/tech/20190516 System76-s secret sauce for success.md
@@ -0,0 +1,71 @@
+[#]: collector: (lujun9972)
+[#]: translator: ( )
+[#]: reviewer: ( )
+[#]: publisher: ( )
+[#]: url: ( )
+[#]: subject: (System76's secret sauce for success)
+[#]: via: (https://opensource.com/article/19/5/system76-secret-sauce)
+[#]: author: (Don Watkins https://opensource.com/users/don-watkins/users/don-watkins)
+
+System76's secret sauce for success
+======
+Linux computer maker's approach to community-informed software and
+hardware development embodies the open source way.
+![][1]
+
+In [_The Open Organization_][2], Jim Whitehurst says, "show passion for the purpose of your organization and constantly drive interest in it. People are drawn to and generally, want to follow passionate people." Carl Richell, the founder and CEO of Linux hardware maker [System76][3], pours that secret sauce to propel his company in the world of open hardware, Linux, and open source.
+
+Carl demonstrates quiet confidence and engages the team at System76 in a way that empowers their creative synergy. During a recent visit to System76's Denver factory, I could immediately tell that the employees love what they do, what they produce, and their interaction with each other and their customers, and Carl sets that example. They are as they [describe themselves][4]: a diverse team of creators, makers, and builders; a small company innovating the next big things; and a group of extremely hard-core nerds.
+
+### A revolutionary approach
+
+In 2005, Carl had a vision, which began as talk over some beers, to produce desktop and laptop computers that come installed with Linux. He's transformed that idea into a highly successful company founded on the [belief][5] that "the computer and operating system are the most powerful and versatile tools ever created." And by producing the best tools, System76 can inspire the curious to make their greatest discovery or complete their greatest project.
+
+![System 76 founder and CEO Carl Richell][6]
+
+Carl Richell's enthusiasm was obvious at System 76's [Thelio launch event][7].
+
+System76 lives up to its name, which was inspired by the American Revolution of 1776. The company views itself as a leader in the open source revolution, granting people freedom and independence from proprietary hardware and software.
+
+But the revolution does not end there; it continues with the company's business practices and diverse environment that aims to close the gender gap in technology leadership. Eight of the company's 28 employees are women, including vice president of marketing Louisa Bisio, creative manager Kate Hazen, purchasing manager May Liu, head of technical support Emma Marshall, and manufacturing control and logistics manager Sarah Zinger.
+
+### Community-informed design
+
+The staff members' passion and ingenuity for making the Linux experience enjoyable for customers creates an outstanding culture. Because the company believes the Linux desktop deserves a dedicated PC manufacturer, in 2018, it brought manufacturing in-house. This allows System76's engineers to make design changes more quickly, based on their frequent interactions with Linux users to learn about their needs and wants. It also opens up its parts and process to the public, including publishing design files under GPL on [GitHub][8], consistent with its commitment to openness and open source.
+
+For example, when System76 decided to create its own version of Linux, [Pop!_OS][9], it hosted online meetings to discuss and learn what features and software its customers wanted. This decision to work closely with the community has been instrumental in making Pop!_OS successful.
+
+System76 again turned to the community when it began developing [Thelio][10], its new line of desktop computers. Marketing VP Louisa Bisio says, "Taking a similar approach to open hardware has been great. We started in-house design in 2016, prototyping different desktop designs. Then we moved from prototyping acrylic to sheet metal. Then the first few prototypes of Thelio were presented to our [Superfan][11] attendees in 2017, and their feedback was really important in adjusting the desktop designs and progressing Thelio iterations forward."
+
+Thelio is the product of research and development focusing on high-quality components and design. It features a unique cabling layout, innovative airflow within the computer case, and the Thelio Io open hardware SATA controller. Many of System76's customers use platforms like [CUDA][12] to do their work; to support them, System76 works backward and pulls out proprietary functionality, piece by piece, until everything is open.
+
+### Open roads ahead
+
+Manufacturing open laptops are on the long-range roadmap, but the company is actively working on an open motherboard and maintaining Pop!_OS and System76 drivers, which are open. This commitment to openness, customer-driven design, and culture give System 76 a unique place in computer manufacturing. All of this stems from founder Carl Richell and his philosophy "that technology should be open and accessible to everyone." [As Carl says][13], "open hardware benefits all of us. It's how we further advance technology and make it more available to everyone."
+
+--------------------------------------------------------------------------------
+
+via: https://opensource.com/article/19/5/system76-secret-sauce
+
+作者:[Don Watkins ][a]
+选题:[lujun9972][b]
+译者:[译者ID](https://github.com/译者ID)
+校对:[校对者ID](https://github.com/校对者ID)
+
+本文由 [LCTT](https://github.com/LCTT/TranslateProject) 原创编译,[Linux中国](https://linux.cn/) 荣誉推出
+
+[a]: https://opensource.com/users/don-watkins/users/don-watkins
+[b]: https://github.com/lujun9972
+[1]: https://opensource.com/sites/default/files/styles/image-full-size/public/lead-images/bubblehands_fromRHT_520_0612LL.png?itok=_iQ2dO3S
+[2]: https://www.amazon.com/Open-Organization-Igniting-Passion-Performance/dp/1511392460
+[3]: https://system76.com/
+[4]: https://system76.com/about
+[5]: https://system76.com/pop
+[6]: https://opensource.com/sites/default/files/uploads/carl_richell.jpg (System 76 founder and CEO Carl Richell)
+[7]: https://trevgstudios.smugmug.com/System76/121418-Thelio-Press-Event/i-w6XNmKS
+[8]: https://github.com/system76
+[9]: https://opensource.com/article/18/1/behind-scenes-popos-linux
+[10]: https://system76.com/desktops
+[11]: https://system76.com/superfan
+[12]: https://en.wikipedia.org/wiki/CUDA
+[13]: https://opensource.com/article/19/4/system76-hardware
diff --git a/sources/tech/20190517 Announcing Enarx for running sensitive workloads.md b/sources/tech/20190517 Announcing Enarx for running sensitive workloads.md
new file mode 100644
index 0000000000..81d021f7d7
--- /dev/null
+++ b/sources/tech/20190517 Announcing Enarx for running sensitive workloads.md
@@ -0,0 +1,83 @@
+[#]: collector: (lujun9972)
+[#]: translator: ( )
+[#]: reviewer: ( )
+[#]: publisher: ( )
+[#]: url: ( )
+[#]: subject: (Announcing Enarx for running sensitive workloads)
+[#]: via: (https://opensource.com/article/19/5/enarx-security)
+[#]: author: (Mike Bursell https://opensource.com/users/mikecamel/users/wgarry155)
+
+Announcing Enarx for running sensitive workloads
+======
+Enarx leverages the capabilities of a TEE to change the trust model for
+your application.
+![cubes coming together to create a larger cube][1]
+
+Running software is something that most of us do without thinking about it. We run in "on premises"—our own machines—or we run it in the cloud - on somebody else's machines. We don't always think about what those differences mean, or about what assumptions we're making about the securtiy of the data that's being processed, or even of the software that's doing that processing. Specifically, when you run software (a "workload") on a system (a "host") on the cloud or on your own premises, there are lots and lots of layers. You often don't see those layers, but they're there.
+
+Here's an example of the layers that you might see in a standard cloud virtualisation architecture. The different colours represent different entities that "own" different layers or sets of layers.
+
+![Layers in a standard cloud virtualisation architecture][2]
+
+Here's a similar diagram depicting a standard cloud container architecture. As before, each different colour represents a different "owner" of a layer or set of layers.
+
+![Standard cloud container architecture][3]
+
+These owners may be of very different types, from hardware vendors to OEMs to cloud service providers (CSPs) to middleware vendors to operating system vendors to application vendors to you, the workload owner. And for each workload that you run, on each host, the exact list of layers is likely to be different. And even when they're the same, the versions of the layers instances may be different, whether it's a different BIOS version, a different bootloader, a different kernel version, or whatever else.
+
+Now, in many contexts, you might not worry about this, and your CSP goes out of its way to abstract these layers and their version details away from you. But this is a security article, for security people, and that means that anybody who's reading this probably does care.
+
+The reason we care is not just the different versions and the different layers, but the number of different things—and different entities—that we need to trust if we're going to be happy running any sort of sensitive workload on these types of stacks. I need to trust every single layer, and the owner of every single layer, not only to do what they say they will do, but also not to be compromised. This is a _big_ stretch when it comes to running my sensitive workloads.
+
+### What's Enarx?
+
+Enarx is a new project that is trying to address this problem of having to trust all of those layers. A few of us at Red Hat have been working on it for a few months now. My colleague Nathaniel McCallum demoed an early incarnation of it at [Red Hat Summit 2019][4] in Boston, and we're ready to start announcing it to the world. We have code, we have a demo, we have a GitHub repository, we have a logo: what more could a project want? Well, people—but we'll get to that.
+
+![Enarx logo][5]
+
+With Enarx, we made the decision that we wanted to allow people running workloads to be able to reduce the number of layers—and owners—that they need to trust to the absolute minimum. We plan to use trusted execution environments ("TEEs"—see "[Oh, how I love my TEE (or do I?)][6]") to provide an architecture that looks a little more like this:
+
+![Enarx architecture][7]
+
+In a world like this, you have to trust the CPU and firmware, and you need to trust some middleware—of which Enarx is part—but you don't need to trust all of the other layers, because we will leverage the capabilities of the TEE to ensure the integrity and confidentiality of your application. The Enarx project will provide attestation of the TEE, so that you know you're running on a true and trusted TEE, and will provide open source, auditable code to help you trust the layer directly beneath your application.
+
+The initial code is out there—working on AMD's SEV TEE at the momen—and enough of it works now that we're ready to tell you about it.
+
+Making sure that your application meets your own security requirements is down to you. :-)
+
+### How do I find out more?
+
+The easiest way to learn more is to visit the [Enarx GitHub][8].
+
+We'll be adding more information there—it's currently just code—but bear with us: there are only a few of us on the project at the moment. A blog is on the list of things we'd like to have, but we wanted to get things started.
+
+We'd love to have people in the community getting involved in the project. It's currently quite low-level and requires quite a lot of knowledge to get running, but we'll work on that. You will need some specific hardware to make it work, of course. Oh, and if you're an early boot or a low-level KVM hacker, we're _particularly_ interested in hearing from you.
+
+I will, of course, respond to comments on this article.
+
+* * *
+
+_This article was originally published on[Alice, Eve, and Bob][9] and is reprinted with the author's permission._
+
+--------------------------------------------------------------------------------
+
+via: https://opensource.com/article/19/5/enarx-security
+
+作者:[Mike Bursell ][a]
+选题:[lujun9972][b]
+译者:[译者ID](https://github.com/译者ID)
+校对:[校对者ID](https://github.com/校对者ID)
+
+本文由 [LCTT](https://github.com/LCTT/TranslateProject) 原创编译,[Linux中国](https://linux.cn/) 荣誉推出
+
+[a]: https://opensource.com/users/mikecamel/users/wgarry155
+[b]: https://github.com/lujun9972
+[1]: https://opensource.com/sites/default/files/styles/image-full-size/public/lead-images/cube_innovation_process_block_container.png?itok=vkPYmSRQ (cubes coming together to create a larger cube)
+[2]: https://opensource.com/sites/default/files/uploads/classic-cloud-virt-arch-1.png (Layers in a standard cloud virtualisation architecture)
+[3]: https://opensource.com/sites/default/files/uploads/cloud-container-arch.png (Standard cloud container architecture)
+[4]: https://www.redhat.com/en/summit/2019
+[5]: https://opensource.com/sites/default/files/uploads/enarx.png (Enarx logo)
+[6]: https://aliceevebob.com/2019/02/26/oh-how-i-love-my-tee-or-do-i/
+[7]: https://opensource.com/sites/default/files/uploads/reduced-arch.png (Enarx architecture)
+[8]: https://github.com/enarx
+[9]: https://aliceevebob.com/2019/05/07/announcing-enarx/
diff --git a/sources/tech/20190520 Blockchain 2.0 - Explaining Distributed Computing And Distributed Applications -Part 11.md b/sources/tech/20190520 Blockchain 2.0 - Explaining Distributed Computing And Distributed Applications -Part 11.md
new file mode 100644
index 0000000000..c34effe6be
--- /dev/null
+++ b/sources/tech/20190520 Blockchain 2.0 - Explaining Distributed Computing And Distributed Applications -Part 11.md
@@ -0,0 +1,88 @@
+[#]: collector: (lujun9972)
+[#]: translator: ( )
+[#]: reviewer: ( )
+[#]: publisher: ( )
+[#]: url: ( )
+[#]: subject: (Blockchain 2.0 – Explaining Distributed Computing And Distributed Applications [Part 11])
+[#]: via: (https://www.ostechnix.com/blockchain-2-0-explaining-distributed-computing-and-distributed-applications/)
+[#]: author: (editor https://www.ostechnix.com/author/editor/)
+
+Blockchain 2.0 – Explaining Distributed Computing And Distributed Applications [Part 11]
+======
+
+![Explaining Distributed Computing And Distributed Applications][1]
+
+### How DApps serve the purpose of [Blockchain 2.0][2]
+
+**Blockchain 1.0** was about introducing the “blockchain” into the list of modern buzzwords along with the advent of **bitcoin**. Multiple white papers detailing bitcoin’s underlying blockchain network specified the use of the blockchain for other uses as well. Although most of the said uses was around the basic concept of using the blockchain as a **decentralized medium** for storage, a use that stems from this property is utilizing it for carrying out **Distributed computing** on top of this layer.
+
+**DApps** or **Distributed Applications** are computer programs that are stored and run on a distributed storage system such as the [**Ethereum**][3] blockchain for instance. To understand how DApps function and how they’re different from traditional applications on your desktop or phone, we’ll need to delve into what distributed computing is. This post will explore some fundamental concepts of distributed computing and the role of blockchains in executing the said objective. Furthermore, well also look at a few applications or DApps, in blockchain lingo, to get a hang of things.
+
+### What is Distributed Computing?
+
+We’re assuming many readers are familiar with multi-threaded applications and multi-threading in general. Multi-threading is the reason why processor manufacturers are forever hell bent on increasing the core count on their products. Fundamentally speaking, some applications such as video rendering software suites are capable of dividing their work (in this case rendering effects and video styles) into multiple chunks and parallelly get them processed from a supporting computing system. This reduces the lead time on getting the work done and is generally more efficient in terms of time, money and energy usage. Applications such as some games however, cannot make use of this system since processing and responses need to be obtained real time based on user inputs rather than via planned execution. Nonetheless, the fact that more processing power may be exploited from existing hardware using these computing methods remains true and significant.
+
+Even supercomputers are basically a bunch of powerful CPUs all tied up together in a circuit to enable faster processing as mentioned above. The average core count on flagship CPUs from the lead manufacturers AMD and Intel have in fact gone up in the last few years, because increasing core count has recently been the only method to claim better processing and claim upgrades to their product lines. This information notwithstanding, the fact remains that distributed computing and related concepts of parallel computing are the only legitimate ways to improve processing capabilities in the near future. There are minor differences between distributed and parallel computing models as well, however that is beyond the scope off this post.
+
+Another method to get many computers executing programs simultaneously is to connect them through the internet and have a cloud-based program to be implemented in parts by all of the participating systems. This is the basic fundamental behind distributed applications.
+
+For a more detailed account and primer regarding what and how parallel computing works, interested readers may visit [this][4] webpage. For a more detailed study of the topic, for people who have a background in computer science, you may refer to [this][5] website and the accompanying book.
+
+### What are DApps or Distributed Applications
+
+Application that can make use of the capabilities offered by a distributed computing system is called a **distributed application**. The execution and structure of such an application’s back end needs to be carefully designed in order to be compatible with the system.
+
+The blockchain presents an opportunity to store data in a distributed system of participating nodes. Stepping up from this opportunity we can logically build systems and applications running on such a network (think about how you used to download files via the Torrent protocol).
+
+Such decentralized applications present a lot of benefits over conventional applications that typically run from a central server. Some highlights are:
+
+ * DApps run on a network of such participating nodes and any user request is parsed through such network nodes to provide the user with the requested functionality. _**Program is executed on the network instead of a single computer or a server**_.
+ * DApps will have codified methods of filtering through requests and executing them so as to always be fair and transparent when users interact with it. To create a new block of data in the chain, the same has to be approved via a **consensus algorithm** by the participating nodes. This fundamental idea of peer to peer approval applies for DApps as well. This essentially means that DApps cannot by extension of this principle provide different outputs to the same query or input. All users will be given the same priority unless it is explicitly mentioned and all users will receive similar results from the DApp as well. This will prove to be important in developing better industry practices for insurance and finance companies for instance. A DApp that specializes in microlending, for instance, cannot differentiate and offer different interest rates for different borrowers other than their credit history. This also means that all users will eventually end up paying for their required operations uniformly depending on the computational complexity of the task they passed on to the application. For instance, combing through 10000 entries of data will cost proportionately more than combing through say 100. The payment or incentivisation system might be different for different applications and blockchain protocols though.
+ * Most DApps are by default redundant and fail safe. If you’re using a service which is run on a central server, a failure from the server end will freeze the application. Think of a service such as PayPal for instance. If the PayPal server in your immediate region fails due to some reason and somehow the central server cannot re route your request, your payment will not go through. However, even in case multiple participating nodes in the blockchain dies, you will still find the application live and running provided at least one node is live. This presents a use case for applications which are by definition supposed to be live all the time. Emergency services, insurance, communications etc., are some key areas where investors hope such DApps will bring in much needed reliability.
+ * DApps are usually cost-effective owing to them not requiring a central server to be maintained for their functionality. Once they become mainstream, the mean computing cost of running tasks on the same is also supposed to decrease.
+ * DApps will as mentioned exist till eternity at least until one participant is live on the chain. This essentially means that DApps cannot be censored or hacked into bowing and shutting down.
+
+
+
+The above list of features seems very few, however, combine that with all the other capabilities of the blockchain, the advancement of wireless network access, and, the increasing capabilities of millions of smartphones and here we have in our hands nothing less than a paradigm shift in how the apps that we rely on work.
+
+We will look deeper into how DApps function and how you can make your own DApps on the Ethereum blockchain in a proceeding post. To give you an idea of the DApp environment right now, we present 4 carefully chosen examples that are fairly advanced and popular.
+
+##### 1\. BITCOIN (or any Cryptocurrency)
+
+We’re very sure that readers did not expect BITCOIN to be one among a list of applications in this post. The point we’re trying to make here however, is that any cryptocurrency currently running on a blockchain backbone can be termed as a DApp. Cryptocurrencies are in fact the most popular DApp format out there and a revolutionary one at that too.
+
+##### 2\. [MELON][6]
+
+We’ve talked about how asset management can be an easier task utilizing blockchain and [**smart contracts**][7]. **Melon** is a company that aims to provide its users with usable relevant tools to manage and maximize their returns from the assets they own. They specialize in cryptographic assets as of now with plans to turn to real digitized assets in the future.
+
+##### 3\. [Request][8]
+
+**Request** is primarily a ledger system that handles financial transactions, invoicing, and taxation among other things. Working with other compatible databases and systems it is also capable of verifying payer data and statistics. Large corporations which typically have a significant number of defaulting customers will find it easier to handle their operations with a system such as this.
+
+##### 4\. [CryptoKitties][9]
+
+Known the world over as the video game that broke the Ethereum blockchain, **CryptoKitties** is a video game that runs on the Ethereum blockchain. The video game identifies each user individually by building your own digital profiles and gives you unique **virtual cats** in return. The game went viral and due to the sheer number of users it actually managed to slow down the Ethereum blockchain and its transaction capabilities. Transactions took longer than usual with users having to pay significantly extra money for simple transactions even. Concerns regarding scalability of the Ethereum blockchain have been raised by several stakeholders since then.
+
+--------------------------------------------------------------------------------
+
+via: https://www.ostechnix.com/blockchain-2-0-explaining-distributed-computing-and-distributed-applications/
+
+作者:[editor][a]
+选题:[lujun9972][b]
+译者:[译者ID](https://github.com/译者ID)
+校对:[校对者ID](https://github.com/校对者ID)
+
+本文由 [LCTT](https://github.com/LCTT/TranslateProject) 原创编译,[Linux中国](https://linux.cn/) 荣誉推出
+
+[a]: https://www.ostechnix.com/author/editor/
+[b]: https://github.com/lujun9972
+[1]: https://www.ostechnix.com/wp-content/uploads/2019/05/Distributed-Computing-720x340.png
+[2]: https://www.ostechnix.com/blockchain-2-0-an-introduction/
+[3]: https://www.ostechnix.com/blockchain-2-0-what-is-ethereum/
+[4]: https://www.techopedia.com/definition/7/distributed-computing-system
+[5]: https://www.distributed-systems.net/index.php/books/distributed-systems-3rd-edition-2017/
+[6]: https://melonport.com/
+[7]: https://www.ostechnix.com/blockchain-2-0-explaining-smart-contracts-and-its-types/
+[8]: https://request.network/en/use-cases/
+[9]: https://www.cryptokitties.co/
diff --git a/sources/tech/20190520 How To Map Oracle ASM Disk Against Physical Disk And LUNs In Linux.md b/sources/tech/20190520 How To Map Oracle ASM Disk Against Physical Disk And LUNs In Linux.md
new file mode 100644
index 0000000000..4e9df8a0ff
--- /dev/null
+++ b/sources/tech/20190520 How To Map Oracle ASM Disk Against Physical Disk And LUNs In Linux.md
@@ -0,0 +1,229 @@
+[#]: collector: (lujun9972)
+[#]: translator: ( )
+[#]: reviewer: ( )
+[#]: publisher: ( )
+[#]: url: ( )
+[#]: subject: (How To Map Oracle ASM Disk Against Physical Disk And LUNs In Linux?)
+[#]: via: (https://www.2daygeek.com/shell-script-map-oracle-asm-disks-physical-disk-lun-in-linux/)
+[#]: author: (Magesh Maruthamuthu https://www.2daygeek.com/author/magesh/)
+
+How To Map Oracle ASM Disk Against Physical Disk And LUNs In Linux?
+======
+
+You might already know about ASM, Device Mapper Multipathing (DM-Multipathing) if you are working quit long time as a Linux administrator.
+
+There are multiple ways to check these information. However, you will be getting part of the information when you use the default commands.
+
+It doesn’t show you all together in the single output.
+
+If you want to check all together in the single output then we need to write a small shell script to achieve this.
+
+We have added two shell script to get those information and you can use which one is suitable for you.
+
+Major and Minor numbers can be used to match the physical devices in Linux system.
+
+This tutorial helps you to find which ASM disk maps to which Linux partition or DM Device.
+
+If you want to **[manage Oracle ASM disks][1]** (such as start, enable, stop, list, query and etc) then navigate to following URL.
+
+### What Is ASMLib?
+
+ASMLib is an optional support library for the Automatic Storage Management feature of the Oracle Database.
+
+Automatic Storage Management (ASM) simplifies database administration and greatly reduces kernel resource usage (e.g. the number of open file descriptors).
+
+It eliminates the need for the DBA to directly manage potentially thousands of Oracle database files, requiring only the management of groups of disks allocated to the Oracle Database.
+
+ASMLib allows an Oracle Database using ASM more efficient and capable access to the disk groups it is using.
+
+### What Is Device Mapper Multipathing (DM-Multipathing)?
+
+Device Mapper Multipathing or DM-multipathing is a Linux host-side native multipath tool, which allows us to configure multiple I/O paths between server nodes and storage arrays into a single device by utilizing device-mapper.
+
+### Method-1 : Shell Script To Map ASM Disks To Physical Devices?
+
+In this shell script we are using for loop to achieve the results.
+
+Also, we are not using any ASM related commands.
+
+```
+# vi asm_disk_mapping.sh
+
+#!/bin/bash
+
+ls -lh /dev/oracleasm/disks > /tmp/asmdisks1.txt
+
+for ASMdisk in `cat /tmp/asmdisks1.txt | tail -n +2 | awk '{print $10}'`
+
+do
+
+minor=$(grep -i "$ASMdisk" /tmp/asmdisks1.txt | awk '{print $6}')
+
+major=$(grep -i "$ASMdisk" /tmp/asmdisks1.txt | awk '{print $5}' | cut -d"," -f1)
+
+phy_disk=$(ls -l /dev/* | grep ^b | grep "$major, *$minor" | awk '{print $10}')
+
+echo "ASM disk $ASMdisk is associated on $phy_disk [$major, $minor]"
+
+done
+```
+
+Set an executable permission to port_scan.sh file.
+
+```
+$ chmod +x asm_disk_mapping.sh
+```
+
+Finally run the script to achieve this.
+
+```
+# sh asm_disk_mapping.sh
+
+ASM disk MP4E6D_DATA01 is associated on /dev/dm-1
+3600a0123456789012345567890234q11 [253, 1]
+ASM disk MP4E6E_DATA02 is associated on /dev/dm-2
+3600a0123456789012345567890234q12 [253, 2]
+ASM disk MP4E6F_DATA03 is associated on /dev/dm-3
+3600a0123456789012345567890234q13 [253, 3]
+ASM disk MP4E70_DATA04 is associated on /dev/dm-4
+3600a0123456789012345567890234q14 [253, 4]
+ASM disk MP4E71_DATA05 is associated on /dev/dm-5
+3600a0123456789012345567890234q15 [253, 5]
+ASM disk MP4E72_DATA06 is associated on /dev/dm-6
+3600a0123456789012345567890234q16 [253, 6]
+ASM disk MP4E73_DATA07 is associated on /dev/dm-7
+3600a0123456789012345567890234q17 [253, 7]
+```
+
+### Method-2 : Shell Script To Map ASM Disks To Physical Devices?
+
+In this shell script we are using while loop to achieve the results.
+
+Also, we are using ASM related commands.
+
+```
+# vi asm_disk_mapping_1.sh
+
+#!/bin/bash
+
+/etc/init.d/oracleasm listdisks > /tmp/asmdisks.txt
+
+while read -r ASM_disk
+
+do
+
+major="$(/etc/init.d/oracleasm querydisk -d $ASM_disk | awk -F[ '{ print $2 }'| awk -F] '{ print $1 }' | cut -d"," -f1)"
+
+minor="$(/etc/init.d/oracleasm querydisk -d $ASM_disk | awk -F[ '{ print $2 }'| awk -F] '{ print $1 }' | cut -d"," -f2)"
+
+phy_disk="$(ls -l /dev/* | grep ^b | grep "$major, *$minor" | awk '{ print $10 }')"
+
+echo "ASM disk $ASM_disk is associated on $phy_disk [$major, $minor]"
+
+done < /tmp/asmdisks.txt
+```
+
+Set an executable permission to port_scan.sh file.
+
+```
+$ chmod +x asm_disk_mapping_1.sh
+```
+
+Finally run the script to achieve this.
+
+```
+# sh asm_disk_mapping_1.sh
+
+ASM disk MP4E6D_DATA01 is associated on /dev/dm-1
+3600a0123456789012345567890234q11 [253, 1]
+ASM disk MP4E6E_DATA02 is associated on /dev/dm-2
+3600a0123456789012345567890234q12 [253, 2]
+ASM disk MP4E6F_DATA03 is associated on /dev/dm-3
+3600a0123456789012345567890234q13 [253, 3]
+ASM disk MP4E70_DATA04 is associated on /dev/dm-4
+3600a0123456789012345567890234q14 [253, 4]
+ASM disk MP4E71_DATA05 is associated on /dev/dm-5
+3600a0123456789012345567890234q15 [253, 5]
+ASM disk MP4E72_DATA06 is associated on /dev/dm-6
+3600a0123456789012345567890234q16 [253, 6]
+ASM disk MP4E73_DATA07 is associated on /dev/dm-7
+3600a0123456789012345567890234q17 [253, 7]
+```
+
+### How To List Oracle ASM Disks?
+
+If you would like to list only Oracle ASM disk then use the below command to List available/created Oracle ASM disks in Linux.
+
+```
+# oracleasm listdisks
+
+ASM_Disk1
+ASM_Disk2
+ASM_Disk3
+ASM_Disk4
+ASM_Disk5
+ASM_Disk6
+ASM_Disk7
+```
+
+### How To List Oracle ASM Disks Against Major And Minor Number?
+
+If you would like to map Oracle ASM disks against major and minor number then use the below commands to List available/created Oracle ASM disks in Linux.
+
+```
+# for ASMdisk in `oracleasm listdisks`; do /etc/init.d/oracleasm querydisk -d $ASMdisk; done
+
+Disk "ASM_Disk1" is a valid Disk on device [253, 1]
+Disk "ASM_Disk2" is a valid Disk on device [253, 2]
+Disk "ASM_Disk3" is a valid Disk on device [253, 3]
+Disk "ASM_Disk4" is a valid Disk on device [253, 4]
+Disk "ASM_Disk5" is a valid Disk on device [253, 5]
+Disk "ASM_Disk6" is a valid Disk on device [253, 6]
+Disk "ASM_Disk7" is a valid Disk on device [253, 7]
+```
+
+Alternatively, we can get the same results using the ls command.
+
+```
+# ls -lh /dev/oracleasm/disks
+
+total 0
+brw-rw---- 1 oracle oinstall 253, 1 May 19 14:44 ASM_Disk1
+brw-rw---- 1 oracle oinstall 253, 2 May 19 14:44 ASM_Disk2
+brw-rw---- 1 oracle oinstall 253, 3 May 19 14:44 ASM_Disk3
+brw-rw---- 1 oracle oinstall 253, 4 May 19 14:44 ASM_Disk4
+brw-rw---- 1 oracle oinstall 253, 5 May 19 14:44 ASM_Disk5
+brw-rw---- 1 oracle oinstall 253, 6 May 19 14:44 ASM_Disk6
+brw-rw---- 1 oracle oinstall 253, 7 May 19 14:44 ASM_Disk7
+```
+
+### How To List Physical Disks Against LUNs?
+
+If you would like to map physical disks against LUNs then use the below command.
+
+```
+# multipath -ll | grep NETAPP
+
+3600a0123456789012345567890234q11 dm-1 NETAPP,LUN C-Mode
+3600a0123456789012345567890234q12 dm-2 NETAPP,LUN C-Mode
+3600a0123456789012345567890234q13 dm-3 NETAPP,LUN C-Mode
+3600a0123456789012345567890234q14 dm-4 NETAPP,LUN C-Mode
+3600a0123456789012345567890234q15 dm-5 NETAPP,LUN C-Mode
+3600a0123456789012345567890234q16 dm-6 NETAPP,LUN C-Mode
+3600a0123456789012345567890234q17 dm-7 NETAPP,LUN C-Mode
+```
+
+--------------------------------------------------------------------------------
+
+via: https://www.2daygeek.com/shell-script-map-oracle-asm-disks-physical-disk-lun-in-linux/
+
+作者:[Magesh Maruthamuthu][a]
+选题:[lujun9972][b]
+译者:[译者ID](https://github.com/译者ID)
+校对:[校对者ID](https://github.com/校对者ID)
+
+本文由 [LCTT](https://github.com/LCTT/TranslateProject) 原创编译,[Linux中国](https://linux.cn/) 荣誉推出
+
+[a]: https://www.2daygeek.com/author/magesh/
+[b]: https://github.com/lujun9972
+[1]: https://www.2daygeek.com/start-stop-restart-enable-reload-oracleasm-service-linux-create-scan-list-query-rename-delete-configure-oracleasm-disk/
diff --git a/sources/tech/20190521 How to Disable IPv6 on Ubuntu Linux.md b/sources/tech/20190521 How to Disable IPv6 on Ubuntu Linux.md
new file mode 100644
index 0000000000..d25298583c
--- /dev/null
+++ b/sources/tech/20190521 How to Disable IPv6 on Ubuntu Linux.md
@@ -0,0 +1,219 @@
+[#]: collector: (lujun9972)
+[#]: translator: (arrowfeng)
+[#]: reviewer: ( )
+[#]: publisher: ( )
+[#]: url: ( )
+[#]: subject: (How to Disable IPv6 on Ubuntu Linux)
+[#]: via: (https://itsfoss.com/disable-ipv6-ubuntu-linux/)
+[#]: author: (Sergiu https://itsfoss.com/author/sergiu/)
+
+How to Disable IPv6 on Ubuntu Linux
+======
+
+Are you looking for a way to **disable IPv6** connections on your Ubuntu machine? In this article, I’ll teach you exactly how to do it and why you would consider this option. I’ll also show you how to **enable or re-enable IPv6** in case you change your mind.
+
+### What is IPv6 and why would you want to disable IPv6 on Ubuntu?
+
+**[Internet Protocol version 6][1]** [(][1] **[IPv6][1]**[)][1] is the most recent version of the Internet Protocol (IP), the communications protocol that provides an identification and location system for computers on networks and routes traffic across the Internet. It was developed in 1998 to replace the **IPv4** protocol.
+
+**IPv6** aims to improve security and performance, while also making sure we don’t run out of addresses. It assigns unique addresses globally to every device, storing them in **128-bits** , compared to just 32-bits used by IPv4.
+
+![Disable IPv6 Ubuntu][2]
+
+Although the goal is for IPv4 to be replaced by IPv6, there is still a long way to go. Less than **30%** of the sites on the Internet makes IPv6 connectivity available to users (tracked by Google [here][3]). IPv6 can also cause [problems with some applications at time][4].
+
+Since **VPNs** provide global services, the fact that IPv6 uses globally routed addresses (uniquely assigned) and that there (still) are ISPs that don’t offer IPv6 support shifts this feature lower down their priority list. This way, they can focus on what matters the most for VPN users: security.
+
+Another possible reason you might want to disable IPv6 on your system is not wanting to expose yourself to various threats. Although IPv6 itself is safer than IPv4, the risks I am referring to are of another nature. If you aren’t actively using IPv6 and its features, [having IPv6 enabled leaves you vulnerable to various attacks][5], offering the hacker another possible exploitable tool.
+
+On the same note, configuring basic network rules is not enough. You have to pay the same level of attention to tweaking your IPv6 configuration as you do for IPv4. This can prove to be quite a hassle to do (and also to maintain). With IPv6 comes a suite of problems different to those of IPv4 (many of which can be referenced online, given the age of this protocol), giving your system another layer of complexity.
+
+[][6]
+
+Suggested read How To Remove Drive Icons From Unity Launcher In Ubuntu 14.04 [Beginner Tips]
+
+### Disabling IPv6 on Ubuntu [For Advanced Users Only]
+
+In this section, I’ll be covering how you can disable IPv6 protocol on your Ubuntu machine. Open up a terminal ( **default:** CTRL+ALT+T) and let’s get to it!
+
+**Note:** _For most of the commands you are going to input in the terminal_ _you are going to need root privileges ( **sudo** )._
+
+Warning!
+
+If you are a regular desktop Linux user and prefer a stable working system, please avoid this tutorial. This is for advanced users who know what they are doing and why they are doing so.
+
+#### 1\. Disable IPv6 using Sysctl
+
+First of all, you can **check** if you have IPv6 enabled with:
+
+```
+ip a
+```
+
+You should see an IPv6 address if it is enabled (the name of your internet card might be different):
+
+![IPv6 Address Ubuntu][7]
+
+You have see the sysctl command in the tutorial about [restarting network in Ubuntu][8]. We are going to use it here as well. To **disable IPv6** you only have to input 3 commands:
+
+```
+sudo sysctl -w net.ipv6.conf.all.disable_ipv6=1
+sudo sysctl -w net.ipv6.conf.default.disable_ipv6=1
+sudo sysctl -w net.ipv6.conf.lo.disable_ipv6=1
+```
+
+You can check if it worked using:
+
+```
+ip a
+```
+
+You should see no IPv6 entry:
+
+![IPv6 Disabled Ubuntu][9]
+
+However, this only **temporarily disables IPv6**. The next time your system boots, IPv6 will be enabled again.
+
+One method to make this option persist is modifying **/etc/sysctl.conf**. I’ll be using vim to edit the file, but you can use any editor you like. Make sure you have **administrator rights** (use **sudo** ):
+
+![Sysctl Configuration][10]
+
+Add the following lines to the file:
+
+```
+net.ipv6.conf.all.disable_ipv6=1
+net.ipv6.conf.default.disable_ipv6=1
+net.ipv6.conf.lo.disable_ipv6=1
+```
+
+For the settings to take effect use:
+
+```
+sudo sysctl -p
+```
+
+If IPv6 is still enabled after rebooting, you must create (with root privileges) the file **/etc/rc.local** and fill it with:
+
+```
+#!/bin/bash
+# /etc/rc.local
+
+/etc/sysctl.d
+/etc/init.d/procps restart
+
+exit 0
+```
+
+Now use [chmod command][11] to make the file executable:
+
+```
+sudo chmod 755 /etc/rc.local
+```
+
+What this will do is manually read (during the boot time) the kernel parameters from your sysctl configuration file.
+
+[][12]
+
+Suggested read 3 Ways to Check Linux Kernel Version in Command Line
+
+#### 2\. Disable IPv6 using GRUB
+
+An alternative method is to configure **GRUB** to pass kernel parameters at boot time. You’ll have to edit **/etc/default/grub**. Once again, make sure you have administrator privileges:
+
+![GRUB Configuration][13]
+
+Now you need to modify **GRUB_CMDLINE_LINUX_DEFAULT** and **GRUB_CMDLINE_LINUX** to disable IPv6 on boot:
+
+```
+GRUB_CMDLINE_LINUX_DEFAULT="quiet splash ipv6.disable=1"
+GRUB_CMDLINE_LINUX="ipv6.disable=1"
+```
+
+Save the file and run:
+
+```
+sudo update-grub
+```
+
+The settings should now persist on reboot.
+
+### Re-enabling IPv6 on Ubuntu
+
+To re-enable IPv6, you’ll have to undo the changes you made. To enable IPv6 until reboot, enter:
+
+```
+sudo sysctl -w net.ipv6.conf.all.disable_ipv6=0
+sudo sysctl -w net.ipv6.conf.default.disable_ipv6=0
+sudo sysctl -w net.ipv6.conf.lo.disable_ipv6=0
+```
+
+Otherwise, if you modified **/etc/sysctl.conf** you can either remove the lines you added or change them to:
+
+```
+net.ipv6.conf.all.disable_ipv6=0
+net.ipv6.conf.default.disable_ipv6=0
+net.ipv6.conf.lo.disable_ipv6=0
+```
+
+You can optionally reload these values:
+
+```
+sudo sysctl -p
+```
+
+You should once again see a IPv6 address:
+
+![IPv6 Reenabled in Ubuntu][14]
+
+Optionally, you can remove **/etc/rc.local** :
+
+```
+sudo rm /etc/rc.local
+```
+
+If you modified the kernel parameters in **/etc/default/grub** , go ahead and delete the added options:
+
+```
+GRUB_CMDLINE_LINUX_DEFAULT="quiet splash"
+GRUB_CMDLINE_LINUX=""
+```
+
+Now do:
+
+```
+sudo update-grub
+```
+
+**Wrapping Up**
+
+In this guide I provided you ways in which you can **disable IPv6** on Linux, as well as giving you an idea about what IPv6 is and why you would want to disable it.
+
+Did you find this article useful? Do you disable IPv6 connectivity? Let us know in the comment section!
+
+--------------------------------------------------------------------------------
+
+via: https://itsfoss.com/disable-ipv6-ubuntu-linux/
+
+作者:[Sergiu][a]
+选题:[lujun9972][b]
+译者:[译者ID](https://github.com/译者ID)
+校对:[校对者ID](https://github.com/校对者ID)
+
+本文由 [LCTT](https://github.com/LCTT/TranslateProject) 原创编译,[Linux中国](https://linux.cn/) 荣誉推出
+
+[a]: https://itsfoss.com/author/sergiu/
+[b]: https://github.com/lujun9972
+[1]: https://en.wikipedia.org/wiki/IPv6
+[2]: https://i0.wp.com/itsfoss.com/wp-content/uploads/2019/05/disable_ipv6_ubuntu.png?fit=800%2C450&ssl=1
+[3]: https://www.google.com/intl/en/ipv6/statistics.html
+[4]: https://whatismyipaddress.com/ipv6-issues
+[5]: https://www.internetsociety.org/blog/2015/01/ipv6-security-myth-1-im-not-running-ipv6-so-i-dont-have-to-worry/
+[6]: https://itsfoss.com/remove-drive-icons-from-unity-launcher-in-ubuntu/
+[7]: https://i2.wp.com/itsfoss.com/wp-content/uploads/2019/05/ipv6_address_ubuntu.png?fit=800%2C517&ssl=1
+[8]: https://itsfoss.com/restart-network-ubuntu/
+[9]: https://i1.wp.com/itsfoss.com/wp-content/uploads/2019/05/ipv6_disabled_ubuntu.png?fit=800%2C442&ssl=1
+[10]: https://i1.wp.com/itsfoss.com/wp-content/uploads/2019/05/sysctl_configuration.jpg?fit=800%2C554&ssl=1
+[11]: https://linuxhandbook.com/chmod-command/
+[12]: https://itsfoss.com/find-which-kernel-version-is-running-in-ubuntu/
+[13]: https://i0.wp.com/itsfoss.com/wp-content/uploads/2019/05/grub_configuration-1.jpg?fit=800%2C565&ssl=1
+[14]: https://i2.wp.com/itsfoss.com/wp-content/uploads/2019/05/ipv6_address_ubuntu-1.png?fit=800%2C517&ssl=1
diff --git a/sources/tech/20190521 I don-t know how CPUs work so I simulated one in code.md b/sources/tech/20190521 I don-t know how CPUs work so I simulated one in code.md
new file mode 100644
index 0000000000..3b9be98d2f
--- /dev/null
+++ b/sources/tech/20190521 I don-t know how CPUs work so I simulated one in code.md
@@ -0,0 +1,174 @@
+[#]: collector: (lujun9972)
+[#]: translator: ( )
+[#]: reviewer: ( )
+[#]: publisher: ( )
+[#]: url: ( )
+[#]: subject: (I don't know how CPUs work so I simulated one in code)
+[#]: via: (https://djhworld.github.io/post/2019/05/21/i-dont-know-how-cpus-work-so-i-simulated-one-in-code/)
+[#]: author: (daniel harper https://djhworld.github.io)
+
+I don't know how CPUs work so I simulated one in code
+======
+
+![][1]
+
+A few months ago it dawned on me that I didn’t really understand how computers work under the hood. I still don’t understand how modern computers work.
+
+However, after making my way through [But How Do It Know?][2] by J. Clark Scott, a book which describes the bits of a simple 8-bit computer from the NAND gates, through to the registers, RAM, bits of the CPU, ALU and I/O, I got a hankering to implement it in code.
+
+While I’m not that interested in the physics of the circuitry, the book just about skims the surface of those waters and gives a neat overview of the wiring and how bits move around the system without the requisite electrical engineering knowledge. For me though I can’t get comfortable with book descriptions, I have to see things in action and learn from my inevitable mistakes, which led me to chart a course on the rough seas of writing a circuit in code and getting a bit weepy about it.
+
+The fruits of my voyage can be seen in [simple-computer][3]; a simple computer that’s simple and computes things.
+
+[![][4]][5] [![][6]][7] [![][8]][9]
+Example programs
+
+It is quite a neat little thing, the CPU code is implemented [as a horrific splurge of gates turning on and off][10] but it works, I’ve [unit tested it][11], and we all know unit tests are irrefutable proof that something works.
+
+It handles [keyboard inputs][12], and renders text [to a display][13] using a painstakingly crafted set of glyphs for a professional font I’ve named “Daniel Code Pro”. The only cheat bit is to get the keyboard input and display output working I had to hook up go channels to speak to the outside world via [GLFW][14], but the rest of it is a simulated circuit.
+
+I even wrote a [crude assembler][15] which was eye opening to say the least. It’s not perfect. Actually it’s a bit crap, but it highlighted to me the problems that other people have already solved many, many years ago and I think I’m a better person for it. Or worse, depending who you ask.
+
+### But why you do that?
+
+> “I’ve seen thirteen year old children do this in Minecraft, come back to me when you’ve built a REAL CPU out of telegraph relays”
+
+My mental model of computing is stuck in beginner computer science textbooks, and the CPU that powers the [gameboy emulator I wrote back in 2013][16] is really nothing like the CPUs that are running today. Even saying that, the emulator is just a state machine, it doesn’t describe the stuff at the logic gate level. You can implement most of it using just a `switch` statement and storing the state of the registers.
+
+So I’m trying to get a better understanding of this stuff because I don’t know what L1/L2 caches are, I don’t know what pipelining means, I’m not entirely sure I understand the Meltdown and Spectre vulnerability papers. Someone told me they were optimising their code to make use of CPU caches, I don’t know how to verify that other than taking their word for it. I’m not really sure what all the x86 instructions mean. I don’t understand how people off-load work to a GPU or TPU. I don’t know what a TPU is. I don’t know how to make use of SIMD instructions.
+
+But all that is built on a foundation of knowledge you need to earn your stripes for, so I ain’t gonna get there without reading the map first. Which means getting back to basics and getting my hands dirty with something simple. The “Scott Computer” described in the book is simple. That’s the reason.
+
+### Great Scott! It’s alive!
+
+The Scott computer is an 8-bit processor attached to 256 bytes of RAM, all connected via an 8-bit system bus. It has 4 general purpose registers and can execute [17 machine instructions][17]. Someone built a visual simulator [for the web here][18], which is really cool, I dread to think how long it took to track all the wiring states!
+
+[![][19]][20]
+A diagram outlining all the components that make up the Scott CPU
+Copyright © 2009 - 2016 by Siegbert Filbinger and John Clark Scott.
+
+The book takes you on a journey from the humble NAND gate, onto a Bit of memory, onto a register and then keeps layering on components until you end up with something resembling the above. I really recommend reading it, even if you are already familiar with the concepts because it’s quite a good overview. I don’t recommend the Kindle version though because the diagrams are sometimes hard to zoom in and decipher on a screen. A perennial problem for the Kindle in my experience.
+
+The only thing that’s different about my computer is I upgraded it to 16-bit to have more memory to play with, as storing even just the glyphs for the [ASCII table][21] would have dwarfed most of the 8-bit machine described in the book, with not much room left for useful code.
+
+### My development journey
+
+During development it really was just a case of reading the text, scouring the diagrams and then attempting to translate that using a general purpose programming language code and definitely not using something that’s designed for integrated circuit development. The reason why I wrote it in Go, is well, I know a bit of Go. Naysayers might chime in and say, you blithering idiot! I can’t believe you didn’t spend all your time learning [VHDL][22] or [Verilog][23] or [LogSim][24] or whatever but I’d already written my bits and bytes and NANDs by that point, I was in too deep. Maybe I’ll learn them next and weep about my time wasted, but that’s my cross to bear.
+
+In the grand scheme of things most of the computer is just passing around a bunch of booleans, so any boolean friendly language will do the job.
+
+Applying a schema to those booleans is what helps you (the programmer) derive its meaning, and the biggest decision anyone needs to make is decide what [endianness][25] your system is going to use and make sure all the components transfer things to and from the bus in the right order.
+
+This was an absolute pain in the backside to implement. From the offset I opted for little endian but when testing the ALU my hair took a beating trying to work out why the numbers were coming out wrong. Many, many print statements took place on this one.
+
+Development did take a while, maybe about a month or two during some of my free time, but once the CPU was done and successfully able to execute 2 + 2 = 5, I was happy.
+
+Well, until the book discussed the I/O features, with designs for a simple keyboard and display interface so you can get things in and out of the machine. Well I’ve already gotten this far, no point in leaving it in a half finished state. I set myself a goal of being able to type something on a keyboard and render the letters on a display.
+
+### Peripherals
+
+The peripherals use the [adapter pattern][26] to act as a hardware interface between the CPU and the outside world. It’s probably not a huge leap to guess this was what the software design pattern took inspiration from.
+
+![][27]
+How the I/O adapters connect to a GLFW window
+
+With this separation of concerns it was actually pretty simple to hook the other end of the keyboard and display to a window managed by GLFW. In fact I just pulled most of the code from my [emulator][28] and reshaped it a bit, using go channels to act as the signals in and out of the machine.
+
+### Bringing it to life
+
+![][29]
+
+This was probably the most tricky part, or at least the most cumbersome. Writing assembly with such a limited instruction set sucks. Writing assembly using a crude assembler I wrote sucks even more because you can’t shake your fist at someone other than yourself.
+
+The biggest problem was juggling the 4 registers and keeping track of them, pulling and putting stuff in memory as a temporary store. Whilst doing this I remembered the Gameboy CPU having a stack pointer register so you could push and pop state. Unfortunately this computer doesn’t have such a luxury, so I was mostly moving stuff in and out of memory on a bespoke basis.
+
+The only pseudo instruction I took the time to implement was `CALL` to help calling functions, this allows you to run a function and then return to the point after the function was called. Without that stack though you can only call one level deep.
+
+Also as the machine does not support interrupts, you have to implement awful polling code for functions like getting keyboard state. The book does discuss the steps needed to implement interrupts, but it would involve a lot more wiring.
+
+But anyway enough of the moaning, I ended up writing [four programs][30] and most of them make use of some shared code for drawing fonts, getting keyboard input etc. Not exactly operating system material but it did make me appreciate some of the services a simple operating system might provide.
+
+It wasn’t easy though, the trickiest part of the text-writer program was getting the maths right to work out when to go to a newline, or what happens when you hit the enter key.
+
+```
+main-getInput:
+ CALL ROUTINE-io-pollKeyboard
+ CALL ROUTINE-io-drawFontCharacter
+ JMP main-getInput
+```
+
+The main loop for the text-writer program
+
+I didn’t get round to implementing the backspace key either, or any of the modifier keys. Made me appreciate how much work must go in to making text editors and how tedious that probably is.
+
+### On reflection
+
+This was a fun and very rewarding project for me. In the midst of programming in the assembly language I’d largely forgotten about the NAND, AND and OR gates firing underneath. I’d ascended into the layers of abstraction above.
+
+While the CPU in the is very simple and a long way from what’s sitting in my laptop, I think this project has taught me a lot, namely:
+
+ * How bits move around between all components using a bus
+ * How a simple ALU works
+ * What a simple Fetch-Decode-Execute cycle looks like
+ * That a machine without a stack pointer register + concept of a stack sucks
+ * That a machine without interrupts sucks
+ * What an assembler is and does
+ * How a peripherals communicate with a simple CPU
+ * How simple fonts work and an approach to rendering them on a display
+ * What a simple operating system might start to look like
+
+
+
+So what’s next? The book said that no-one has built a computer like this since 1952, meaning I’ve got 67 years of material to brush up on, so that should keep me occupied for a while. I see the [x86 manual is 4800 pages long][31], enough for some fun, light reading at bedtime.
+
+Maybe I’ll have a brief dalliance with operating system stuff, a flirtation with the C language, a regrettable evening attempting to [solder up a PiDP-11 kit][32] then probably call it quits. I dunno, we’ll see.
+
+With all seriousness though I think I’m going to start looking into RISC based stuff next, maybe RISC-V, but probably start with early RISC processors to get an understanding of the lineage. Modern CPUs have a lot more features like caches and stuff so I want to understand them as well. A lot of stuff out there to learn.
+
+Do I need to know any of this stuff in my day job? Probably helps, but not really, but I’m enjoying it, so whatever, thanks for reading xxxx
+
+--------------------------------------------------------------------------------
+
+via: https://djhworld.github.io/post/2019/05/21/i-dont-know-how-cpus-work-so-i-simulated-one-in-code/
+
+作者:[daniel harper][a]
+选题:[lujun9972][b]
+译者:[译者ID](https://github.com/译者ID)
+校对:[校对者ID](https://github.com/校对者ID)
+
+本文由 [LCTT](https://github.com/LCTT/TranslateProject) 原创编译,[Linux中国](https://linux.cn/) 荣誉推出
+
+[a]: https://djhworld.github.io
+[b]: https://github.com/lujun9972
+[1]: https://djhworld.github.io/img/simple-computer/text-writer.gif (Hello World)
+[2]: http://buthowdoitknow.com/
+[3]: https://github.com/djhworld/simple-computer
+[4]: https://djhworld.github.io/img/simple-computer/ascii1.png (ASCII)
+[5]: https://djhworld.github.io/img/simple-computer/ascii.png
+[6]: https://djhworld.github.io/img/simple-computer/brush1.png (brush)
+[7]: https://djhworld.github.io/img/simple-computer/brush.png
+[8]: https://djhworld.github.io/img/simple-computer/text-writer1.png (doing the typesin')
+[9]: https://djhworld.github.io/img/simple-computer/text-writer.png
+[10]: https://github.com/djhworld/simple-computer/blob/master/cpu/cpu.go#L763
+[11]: https://github.com/djhworld/simple-computer/blob/master/cpu/cpu_test.go
+[12]: https://github.com/djhworld/simple-computer/blob/master/io/keyboard.go#L20
+[13]: https://github.com/djhworld/simple-computer/blob/master/io/display.go#L13
+[14]: https://github.com/djhworld/simple-computer/blob/master/cmd/simulator/glfw_io.go
+[15]: https://github.com/djhworld/simple-computer/blob/master/asm/assembler.go
+[16]: https://github.com/djhworld/gomeboycolor
+[17]: https://github.com/djhworld/simple-computer#instructions
+[18]: http://www.buthowdoitknow.com/but_how_do_it_know_cpu_model.html
+[19]: https://djhworld.github.io/img/simple-computer/scott-cpu.png (The Scott CPU)
+[20]: https://djhworld.github.io/img/simple-computer/scott-cpu.png
+[21]: https://github.com/djhworld/simple-computer/blob/master/_programs/ascii.asm#L27
+[22]: https://en.wikipedia.org/wiki/VHDL
+[23]: https://en.wikipedia.org/wiki/Verilog
+[24]: http://www.cburch.com/logisim/
+[25]: https://en.wikipedia.org/wiki/Endianness
+[26]: https://en.wikipedia.org/wiki/Adapter_pattern
+[27]: https://djhworld.github.io/img/simple-computer/io.png (i couldn't be bothered to do the corners around the CPU for the system bus)
+[28]: https://github.com/djhworld/gomeboycolor-glfw
+[29]: https://djhworld.github.io/img/simple-computer/brush.gif (brush.bin)
+[30]: https://github.com/djhworld/simple-computer/blob/master/_programs/README.md
+[31]: https://software.intel.com/sites/default/files/managed/39/c5/325462-sdm-vol-1-2abcd-3abcd.pdf
+[32]: https://obsolescence.wixsite.com/obsolescence/pidp-11
diff --git a/sources/tech/20190522 Convert Markdown files to word processor docs using pandoc.md b/sources/tech/20190522 Convert Markdown files to word processor docs using pandoc.md
new file mode 100644
index 0000000000..8fab8bfcae
--- /dev/null
+++ b/sources/tech/20190522 Convert Markdown files to word processor docs using pandoc.md
@@ -0,0 +1,119 @@
+[#]: collector: (lujun9972)
+[#]: translator: ( )
+[#]: reviewer: ( )
+[#]: publisher: ( )
+[#]: url: ( )
+[#]: subject: (Convert Markdown files to word processor docs using pandoc)
+[#]: via: (https://opensource.com/article/19/5/convert-markdown-to-word-pandoc)
+[#]: author: (Scott Nesbitt https://opensource.com/users/scottnesbitt/users/jason-van-gumster/users/kikofernandez)
+
+Convert Markdown files to word processor docs using pandoc
+======
+Living that plaintext life? Here's how to create the word processor
+documents people ask for without having to work in a word processor
+yourself.
+![][1]
+
+If you live your life in [plaintext][2], there invariably comes a time when someone asks for a word processor document. I run into this issue frequently, especially at the Day JobTM. Although I've introduced one of the development teams I work with to a [Docs Like Code][3] workflow for writing and reviewing release notes, there are a small number of people who have no interest in GitHub or working with [Markdown][4]. They prefer documents formatted for a certain proprietary application.
+
+The good news is that you're not stuck copying and pasting unformatted text into a word processor document. Using **[pandoc][5]** , you can quickly give people what they want. Let's take a look at how to convert a document from Markdown to a word processor format in [Linux][6] using **pandoc.**
+
+Note that **pandoc** is also available for a wide variety of operating systems, ranging from two flavors of BSD ([NetBSD][7] and [FreeBSD][8]) to Chrome OS, MacOS, and Windows.
+
+### Converting basics
+
+To begin, [install **pandoc**][9] on your computer. Then, crack open a console terminal window and navigate to the directory containing the file that you want to convert.
+
+Type this command to create an ODT file (which you can open with a word processor like [LibreOffice Writer][10] or [AbiWord][11]):
+
+**pandoc -t odt filename.md -o filename.odt**
+
+Remember to replace **filename** with the file's actual name. And if you need to create a file for that other word processor (you know the one I mean), replace **odt** on the command line with **docx**. Here's what this article looks like when converted to an ODT file:
+
+![Basic conversion results with pandoc.][12]
+
+These results are serviceable, but a bit bland. Let's look at how to add a bit more style to the converted documents.
+
+### Converting with style
+
+**pandoc** has a nifty feature enabling you to specify a style template when converting a marked-up plaintext file to a word processor format. In this file, you can edit a small number of styles in the document, including those that control the look of paragraphs, headings, captions, titles and subtitles, a basic table, and hyperlinks.
+
+Let's look at the possibilities.
+
+#### Creating a template
+
+In order to style your documents, you can't just use _any_ template. You need to generate what **pandoc** calls a _reference_ template, which is the template it uses when converting text files to word processor documents. To create this file, type the following in a terminal window:
+
+**pandoc -o custom-reference.odt --print-default-data-file reference.odt**
+
+This command creates a file called **custom-reference.odt**. If you're using that other word processor, change the references to **odt** on the command line to **docx**.
+
+Open the template file in LibreOffice Writer, and then press **F11** to open LibreOffice Writer's **Styles** pane. Although the [pandoc manual][13] advises against making other changes to the file, I change the page size and add headers and footers when necessary.
+
+#### Using the template
+
+So, how do you use that template you just created? There are two ways to do this.
+
+The easiest way is to drop the template in your **/home** directory's **.pandoc** folder—you might have to create the folder first if it doesn't exist. When it's time to convert a document, **pandoc** uses this template file. See the next section on how to choose from multiple templates if you need more than one.
+
+The other way to use your template is to type this set of conversion options at the command line:
+
+**pandoc -t odt file-name.md --reference-doc=path-to-your-file/reference.odt -o file-name.odt**
+
+If you're wondering what a converted file looks like with a customized template, here's an example:
+
+![A document converted using a pandoc style template.][14]
+
+#### Choosing from multiple templates
+
+Many people only need one **pandoc** template. Some people, however, need more than one.
+
+At my day job, for example, I use several templates—one with a DRAFT watermark, one with a watermark stating FOR INTERNAL USE, and one for a document's final versions. Each type of document needs a different template.
+
+If you have similar needs, start the same way you do for a single template, by creating the file **custom-reference.odt**. Rename the resulting file—for example, to **custom-reference-draft.odt** —then open it in LibreOffice Writer and modify the styles. Repeat this process for each template you need.
+
+Next, copy the files into your **/home** directory. You can even put them in the **.pandoc** folder if you want to.
+
+To select a specific template at conversion time, you'll need to run this command in a terminal:
+
+**pandoc -t odt file-name.md --reference-doc=path-to-your-file/custom-template.odt -o file-name.odt**
+
+Change **custom-template.odt** to your template file's name.
+
+### Wrapping up
+
+To avoid having to remember a set of options I don't regularly use, I cobbled together some simple, very lame one-line scripts that encapsulate the options for each template. For example, I run the script **todraft.sh** to create a word processor document using the template with a DRAFT watermark. You might want to do the same.
+
+Here's an example of a script using the template containing a DRAFT watermark:
+
+`pandoc -t odt $1.md -o $1.odt --reference-doc=~/Documents/pandoc-templates/custom-reference-draft.odt`
+
+Using **pandoc** is a great way to provide documents in the format that people ask for, without having to give up the command line life. This tool doesn't just work with Markdown, either. What I've discussed in this article also allows you to create and convert documents between a wide variety of markup languages. See the **pandoc** site linked earlier for more details.
+
+--------------------------------------------------------------------------------
+
+via: https://opensource.com/article/19/5/convert-markdown-to-word-pandoc
+
+作者:[Scott Nesbitt][a]
+选题:[lujun9972][b]
+译者:[译者ID](https://github.com/译者ID)
+校对:[校对者ID](https://github.com/校对者ID)
+
+本文由 [LCTT](https://github.com/LCTT/TranslateProject) 原创编译,[Linux中国](https://linux.cn/) 荣誉推出
+
+[a]: https://opensource.com/users/scottnesbitt/users/jason-van-gumster/users/kikofernandez
+[b]: https://github.com/lujun9972
+[1]: https://opensource.com/sites/default/files/styles/image-full-size/public/lead-images/computer_keyboard_laptop_development_code_woman.png?itok=vbYz6jjb
+[2]: https://plaintextproject.online/
+[3]: https://www.docslikecode.com/
+[4]: https://en.wikipedia.org/wiki/Markdown
+[5]: https://pandoc.org/
+[6]: /resources/linux
+[7]: https://www.netbsd.org/
+[8]: https://www.freebsd.org/
+[9]: https://pandoc.org/installing.html
+[10]: https://www.libreoffice.org/discover/writer/
+[11]: https://www.abisource.com/
+[12]: https://opensource.com/sites/default/files/uploads/pandoc-wp-basic-conversion_600_0.png (Basic conversion results with pandoc.)
+[13]: https://pandoc.org/MANUAL.html
+[14]: https://opensource.com/sites/default/files/uploads/pandoc-wp-conversion-with-tpl_600.png (A document converted using a pandoc style template.)
diff --git a/sources/tech/20190522 Damn- Antergos Linux has been Discontinued.md b/sources/tech/20190522 Damn- Antergos Linux has been Discontinued.md
new file mode 100644
index 0000000000..38c11508bf
--- /dev/null
+++ b/sources/tech/20190522 Damn- Antergos Linux has been Discontinued.md
@@ -0,0 +1,103 @@
+[#]: collector: (lujun9972)
+[#]: translator: ( )
+[#]: reviewer: ( )
+[#]: publisher: ( )
+[#]: url: ( )
+[#]: subject: (Damn! Antergos Linux has been Discontinued)
+[#]: via: (https://itsfoss.com/antergos-linux-discontinued/)
+[#]: author: (Abhishek Prakash https://itsfoss.com/author/abhishek/)
+
+Damn! Antergos Linux has been Discontinued
+======
+
+_**Beginner-friendly Arch Linux based distribution Antergos has announced that the project is being discontinued.**_
+
+Arch Linux has always been considered a no-go zone for the beginners. Antergos challenged this status quo and made Arch Linux accessible to everyone by providing easier installation method. People who wouldn’t dare [installing Arch Linux][1], opted for Antergos.
+
+![Antergos provided easy access to Arch with its easy to use GUI tools][2]
+
+The project started in 2012-13 and started gaining popularity around 2014. I used Antergos, liked it and covered it here on It’s FOSS and perhaps (slightly) contributed to its popularity. In last five years, Antergos was downloaded close to a million times.
+
+But for past year or so, I felt that this project was stagnating. Antergos hardly made any news. Neither the forum nor the social media handles were active. The community around Antergos grew thinner though a few dedicated users still remain.
+
+### The end of Antergos Linux project
+
+![][3]
+
+On May 21, 2019, Antergos [announced][4] its discontinuation. Lack of free time cited as the main reason behind this decision.
+
+> Today, we are announcing the end of this project. As many of you probably noticed over the past several months, we no longer have enough free time to properly maintain Antergos. We came to this decision because we believe that continuing to neglect the project would be a huge disservice to the community.
+>
+> Antergos Team
+
+Antergos developers also mentioned that since the project’s code still works, it’s an opportunity for interested developers to take what they find useful and start their own projects.
+
+#### What happens to Existing Antergos users?
+
+If you are an Antergos user, you don’t have to worry a lot. It’s not that your system will be unusable from today. Your system will continue to get updates directly from Arch Linux.
+
+Antergos team plans to release an update to remove the Antergos repositories from your system along with any Antergos-specific packages that no longer serve a purpose as the project is ending. After that any packages installed from the Antergos repo that are in the AUR will begin to receive updates from [AUR][5].
+
+[][6]
+
+Suggested read Peppermint 8 Released. Download Now!
+
+The Antergos forum and wiki will be functional but only for some time.
+
+If you think using an ‘unmaintained’ project is not a good idea, you should switch your distribution. The most appropriate choice would be [Manjaro Linux][7].
+
+Manjaro Linux started around the same time as Antergos. Both Antergos and Manjaro were sort of competitors as both of them tried to make Arch Linux accessible for everyone.
+
+Manjaro gained a huge userbase in the last few years and its community is thriving. If you want to remain in Arch domain but don’t want to install Arch Linux itself, Manjaro is the best choice for you.
+
+Just note that Manjaro Linux doesn’t provide all the updates immediately as Arch or Antergos. It is a rolling release but with stability in mind. So the updates are tested first.
+
+#### Inevitable fate for smaller distributions?
+
+_Here’s my opinion on the discontinuation on Antergos and other similar open source projects._
+
+Antergos was a niche distribution. It had a smaller but dedicated userbase. The developers cited lack of free time as the main reason for their decision. However, I believe that lack of motivation plays a bigger role in such cases.
+
+What motivates the people behind a project? They start it mostly as a side project and if the project is good, they start gaining users. This growth of userbase drives their motivation to work on the project.
+
+If the userbase starts declining or gets stagnated, the motivation takes a hit.
+
+If the userbase keeps on growing, the motivation increases but only to a certain point. More users require more effort in various tasks around the project. Keeping the wiki and forum along with social media itself is a challenging part, leave aside the actual code development. The situation becomes overwhelming.
+
+When a project grows in considerable size, project owners have two choices. First choice is to form a community of volunteers and start delegating tasks that could be delegated. Having volunteers dedicated to project is not easy but it can surely be achieved as Debian and Manjaro have done it already.
+
+[][8]
+
+Suggested read Lightweight Distribution Linux Lite 4.0 Released With Brand New Look
+
+Second choice is to create some revenue generation channel around the project. The additional revenue may ‘justify’ those extra hours and in some cases, it could drive the developer to work full time on the project. [elementary OS][9] is trying to achieve something similar by developing an ecosystem of ‘payable apps’ in their software center.
+
+You may argue that money should not be a factor in Free and Open Source Software culture but the unfortunate truth is that money is always a factor, in every aspect of our life. I am not saying that a project should be purely driven by money but a project must be sustainable in every aspect.
+
+We have see how other smaller but moderately popular Linux distributions like Korora has been discontinued due to lack of free time. [Solus creator Ikey Doherty had to leave the project][10] to focus on his personal life. Developing and maintaining a successful open source project is not an easy task.
+
+That’s just my opinion. Please feel free to disagree with it and voice your opinion in the comment section.
+
+--------------------------------------------------------------------------------
+
+via: https://itsfoss.com/antergos-linux-discontinued/
+
+作者:[Abhishek Prakash][a]
+选题:[lujun9972][b]
+译者:[译者ID](https://github.com/译者ID)
+校对:[校对者ID](https://github.com/校对者ID)
+
+本文由 [LCTT](https://github.com/LCTT/TranslateProject) 原创编译,[Linux中国](https://linux.cn/) 荣誉推出
+
+[a]: https://itsfoss.com/author/abhishek/
+[b]: https://github.com/lujun9972
+[1]: https://itsfoss.com/install-arch-linux/
+[2]: https://i0.wp.com/itsfoss.com/wp-content/uploads/2015/08/Installing_Antergos_Linux_7.png?ssl=1
+[3]: https://i1.wp.com/itsfoss.com/wp-content/uploads/2019/05/antergos-linux-dead.jpg?resize=800%2C450&ssl=1
+[4]: https://antergos.com/blog/antergos-linux-project-ends/
+[5]: https://itsfoss.com/best-aur-helpers/
+[6]: https://itsfoss.com/peppermint-8-released/
+[7]: https://manjaro.org/
+[8]: https://itsfoss.com/linux-lite-4/
+[9]: https://elementary.io/
+[10]: https://itsfoss.com/ikey-leaves-solus/
diff --git a/sources/tech/20190523 Hardware bootstrapping with Ansible.md b/sources/tech/20190523 Hardware bootstrapping with Ansible.md
new file mode 100644
index 0000000000..94842453cc
--- /dev/null
+++ b/sources/tech/20190523 Hardware bootstrapping with Ansible.md
@@ -0,0 +1,223 @@
+[#]: collector: (lujun9972)
+[#]: translator: ( )
+[#]: reviewer: ( )
+[#]: publisher: ( )
+[#]: url: ( )
+[#]: subject: (Hardware bootstrapping with Ansible)
+[#]: via: (https://opensource.com/article/19/5/hardware-bootstrapping-ansible)
+[#]: author: (Mark Phillips https://opensource.com/users/markp/users/feeble/users/markp)
+
+Hardware bootstrapping with Ansible
+======
+
+![computer servers processing data][1]
+
+At a recent [Ansible London Meetup][2], I got chatting with somebody about automated hardware builds. _"It's all cloud now!"_ I hear you say. Ah, but for many large organisations it's not—they still have massive data centres full of hardware. Almost regularly somebody pops up on our internal mail list and asks, *"can Ansible do hardware provisioning?" *Well yes, you can provision hardware with Ansible…
+
+### Requirements
+
+Bootstrapping hardware is mostly about network services. Before we do any operating system (OS) installing then, we must set up some services. We will need:
+
+ * DHCP
+ * PXE
+ * TFTP
+ * Operating system media
+ * Web server
+
+
+
+### Setup
+
+Besides the DHCP configuration, everything else in this article is handled by the Ansible plays included in [this repository][3].
+
+#### DHCP server
+
+I'm writing here on the assumption you can control your DHCP configuration. If you don't have access to your DHCP server, you'll need to ask the owner to set two options. DHCP option 67 needs to be set to **pxelinux.0** and **next-server** (which is option 66—but you may not need to know that; often a DHCP server will have a field/option for 'next server') needs to be set to the IP address of your TFTP server.
+
+If you can own the DHCP server, I'd suggest using dnsmasq. It's small and simple. I will not cover configuring it here, but look at [the man page][4] and the **\--enable-tftp** option.
+
+#### TFTP
+
+The **next-server** setting for our DHCP server, above, will point to a machine serving [TFTP][5]. Here I've used a [CentOS Linux][6] virtual machine, as it only takes one package (syslinux-tftpboot) and a service to start to have TFTP up and running. We'll stick with the default path, **/var/lib/tftpboot**.
+
+#### PXE
+
+If you're not already familiar with PXE, you might like to take a quick look at [the Wikipedia page][7]. For this article I'll keep it short—we will serve some files over TFTP, which DHCP guides our hardware to.
+
+You'll want **images/pxeboot/{initrd.img,vmlinuz}** from the OS distribution media for pxeboot. These need to be copied to **/var/lib/tftpboot/pxeboot**. The referenced Ansible plays **do not do this step, **so you need to copy them over yourself.
+
+We'll also need to serve the OS installation files. There are two approaches to this: 1) install, via HTTP, from the internet or 2) install, again via HTTP, from a local server. For my testing, since I'm on a private LAN (and I guess you are too), the fastest installation method is the second. The easiest way to prepare this is to mount the DVD image and rsync the `images`, **`Packages` **and `repodata` directories to your webserver location. The referenced Ansible plays will install **httpd** but won't copy over these files, so don't forget to do that after running [the play][8]. For this article, we'll once again stick with defaults for simplicity—so files need to be copied to Apache's standard docroot, **/var/www/html**.
+
+#### Directories
+
+We should end up with directory structures like this:
+
+##### PXE/TFTP
+
+
+```
+[root@c7 ~]# tree /var/lib/tftpboot/pxe{b*,l*cfg}
+/var/lib/tftpboot/pxeboot
+└── 6
+├── initrd.img
+└── vmlinuz
+```
+
+##### httpd
+
+
+```
+[root@c7 ~]# tree -d /var/www/html/
+/var/www/html/
+├── 6 -> centos/6
+├── 7 -> centos/7
+├── centos
+│ ├── 6
+│ │ └── os
+│ │ └── x86_64
+│ │ ├── images
+│ │ │ └── pxeboot
+│ │ ├── Packages
+│ │ └── repodata
+│ └── 7
+│ └── os
+│ └── x86_64
+│ ├── images
+│ │ └── pxeboot
+│ ├── Packages
+│ └── repodata
+└── ks
+```
+
+You'll notice my web setup appears a little less simple than the words above! I've pasted my actual structure to give you some ideas. The hardware I'm using is really old, and even getting CentOS 7 to work was horrible (if you're interested, it's due to the lack of [cciss][9] drivers for the HP Smart Array controller—yes, [there is an answer][10], but it takes a lot of faffing to make work), so all examples are of CentOS 6. I also wanted a flexible setup that could install many versions. Here I've done that using symlinks—this arrangement will work just fine for RHEL too, for example. The basic structure is present though—note the images, Packages and repodata directories.
+
+These paths relate directly to [the PXE menu][11] file we'll serve up and [the kickstart file][12] too.
+
+#### If you don't have DHCP
+
+If you can't manage your own DHCP server or the owners of your infrastructure can't help, there is another option. In the past, I've used [iPXE][13] to create a boot image that I've loaded as virtual media. A lot of out-of-band/lights-out-management (LOM) interfaces on modern hardware support this functionality. You can make a custom embedded PXE menu in seconds with iPXE. I won't cover that here, but if it turns out to be a problem for you, then drop me a line [on Twitter][14] and I'll look at doing a follow-up blog post if enough people request it.
+
+### Installing hardware
+
+We've got our structure in place now, and we can [kickstart][15] a server. Before we do, we have to add some configuration to the TFTP setup to enable a given piece of hardware to pick up the PXE boot menu.
+
+It's here we come across a small chicken/egg problem. We need a host's MAC address to create a link to the specific piece of hardware we want to kickstart. If the hardware is already running and we can access it with Ansible, that's great—we have a way of finding out the boot interface MAC address via the setup module (see [the reinstall play][16]). If it's a new piece of tin, however, we need to get the MAC address and tell our setup what to do with it. This probably means some manual intervention—booting the server and looking at a screen or maybe getting the MAC from a manifest or such like. Whichever way you get hold of it, we can tell our play about it via the inventory.
+
+Let's put a custom variable into our simple INI format [inventory file][17], but run a play to set up TFTP…
+
+
+```
+(pip)iMac:ansible-hw-bootstrap$ ansible-inventory --host hp.box
+{
+"ilo_ip": "192.168.1.68",
+"ilo_password": "administrator"
+}
+(pip)iMac:ansible-hw-bootstrap$ ansible-playbook plays/install.yml
+
+PLAY [kickstart] *******************************************************************************************************
+
+TASK [Host inventory entry has a MAC address] **************************************************************************
+failed: [ks.box] (item=hp.box) => {
+"assertion": "hostvars[item]['mac'] is defined",
+"changed": false,
+"evaluated_to": false,
+"item": "hp.box",
+"msg": "Assertion failed"
+}
+
+PLAY RECAP *************************************************************************************************************
+ks.box : ok=0 changed=0 unreachable=0 failed=1
+```
+
+Uh oh, play failed. It [contains a check][18] that the host we're about to install actually has a MAC address added. Let's fix that and run the play again…
+
+
+```
+(pip)iMac:ansible-hw-bootstrap$ ansible-inventory --host hp.box
+{
+"ilo_ip": "192.168.1.68",
+"ilo_password": "administrator",
+"mac": "00:AA:BB:CC:DD:EE"
+}
+(pip)iMac:ansible-hw-bootstrap$ ansible-playbook plays/install.yml
+
+PLAY [kickstart] *******************************************************************************************************
+
+TASK [Host inventory entry has a MAC address] **************************************************************************
+ok: [ks.box] => (item=hp.box) => {
+"changed": false,
+"item": "hp.box",
+"msg": "All assertions passed"
+}
+
+TASK [Set PXE menu to install] *****************************************************************************************
+ok: [ks.box] => (item=hp.box)
+
+TASK [Reboot target host for PXE boot] *********************************************************************************
+skipping: [ks.box] => (item=hp.box)
+
+PLAY RECAP *************************************************************************************************************
+ks.box : ok=2 changed=0 unreachable=0 failed=0
+```
+
+That worked! What did it do? Looking at the pxelinux.cfg directory under our TFTP root, we can see a symlink…
+
+
+```
+[root@c7 pxelinux.cfg]# pwd
+/var/lib/tftpboot/pxelinux.cfg
+[root@c7 pxelinux.cfg]# l
+total 12
+drwxr-xr-x. 2 root root 65 May 13 14:23 ./
+drwxr-xr-x. 4 root root 4096 May 2 22:13 ../
+-r--r--r--. 1 root root 515 May 2 12:22 00README
+lrwxrwxrwx. 1 root root 7 May 13 14:12 01-00-aa-bb-cc-dd-ee -> install
+-rw-r--r--. 1 root root 682 May 2 22:07 install
+```
+
+The **install** file is symlinked to a file named after our MAC address. This is the key, useful piece. It will ensure our hardware with MAC address **00-aa-bb-cc-dd-ee** is served a PXE menu when it boots from its network card.
+
+So let's boot our machine.
+
+Usefully, Ansible has some [remote management modules][19]. We're working with an HP server here, so we can use the [hpilo_boot][20] module to save us from having to interact directly with the LOM web interface.
+
+Let's run the reinstall play on a booted server…
+
+The neat thing about the **hpilo_boot** module, you'll notice, is it sets the boot medium to be the network. When the installation completes, the server restarts and boots from its hard drive. The eagle-eyed amongst you will have spotted the critical problem with this—what happens if the server boots to its network card again? It will pick up the PXE menu and promptly reinstall itself. I would suggest removing the symlink as a "belt and braces" step then. I will leave that as an exercise for you, dear reader. Hint: I would make the new server do a 'phone home' on boot, to somewhere, which runs a clean-up job. Since you wouldn't need the console open, as I had here to demonstrate what's going on in the background, a 'phone home' job would also give a nice indication that the process completed. Ansible, [naturally][21]. Good luck!
+
+If you've any thoughts or comments on this process, please let me know.
+
+--------------------------------------------------------------------------------
+
+via: https://opensource.com/article/19/5/hardware-bootstrapping-ansible
+
+作者:[Mark Phillips][a]
+选题:[lujun9972][b]
+译者:[译者ID](https://github.com/译者ID)
+校对:[校对者ID](https://github.com/校对者ID)
+
+本文由 [LCTT](https://github.com/LCTT/TranslateProject) 原创编译,[Linux中国](https://linux.cn/) 荣誉推出
+
+[a]: https://opensource.com/users/markp/users/feeble/users/markp
+[b]: https://github.com/lujun9972
+[1]: https://opensource.com/sites/default/files/styles/image-full-size/public/lead-images/server_data_system_admin.png?itok=q6HCfNQ8 (computer servers processing data)
+[2]: https://www.meetup.com/Ansible-London/
+[3]: https://github.com/phips/ansible-hw-bootstrap
+[4]: http://www.thekelleys.org.uk/dnsmasq/docs/dnsmasq-man.html
+[5]: https://en.m.wikipedia.org/wiki/Trivial_File_Transfer_Protocol
+[6]: https://www.centos.org
+[7]: https://en.m.wikipedia.org/wiki/Preboot_Execution_Environment
+[8]: https://github.com/phips/ansible-hw-bootstrap/blob/master/plays/kickstart.yml
+[9]: https://linux.die.net/man/4/cciss
+[10]: https://serverfault.com/questions/611182/centos-7-x64-and-hp-proliant-dl360-g5-scsi-controller-compatibility
+[11]: https://github.com/phips/ansible-hw-bootstrap/blob/master/roles/kickstart/templates/pxe_install.j2#L10
+[12]: https://github.com/phips/ansible-hw-bootstrap/blob/master/roles/kickstart/templates/local6.ks.j2#L3
+[13]: https://ipxe.org
+[14]: https://twitter.com/thismarkp
+[15]: https://access.redhat.com/documentation/en-us/red_hat_enterprise_linux/6/html/installation_guide/ch-kickstart2
+[16]: https://github.com/phips/ansible-hw-bootstrap/blob/master/plays/reinstall.yml
+[17]: https://docs.ansible.com/ansible/latest/user_guide/intro_inventory.html
+[18]: https://github.com/phips/ansible-hw-bootstrap/blob/master/plays/install.yml#L9
+[19]: https://docs.ansible.com/ansible/latest/modules/list_of_remote_management_modules.html
+[20]: https://docs.ansible.com/ansible/latest/modules/hpilo_boot_module.html#hpilo-boot-module
+[21]: https://github.com/phips/ansible-demos/tree/master/roles/phone_home
diff --git a/sources/tech/20190523 Run your blog on GitHub Pages with Python.md b/sources/tech/20190523 Run your blog on GitHub Pages with Python.md
new file mode 100644
index 0000000000..4763e5e215
--- /dev/null
+++ b/sources/tech/20190523 Run your blog on GitHub Pages with Python.md
@@ -0,0 +1,235 @@
+[#]: collector: (lujun9972)
+[#]: translator: (QiaoN)
+[#]: reviewer: ( )
+[#]: publisher: ( )
+[#]: url: ( )
+[#]: subject: (Run your blog on GitHub Pages with Python)
+[#]: via: (https://opensource.com/article/19/5/run-your-blog-github-pages-python)
+[#]: author: (Erik O'Shaughnessy https://opensource.com/users/jnyjny/users/jasperzanjani/users/jasperzanjani/users/jasperzanjani/users/jnyjny/users/jasperzanjani)
+
+Run your blog on GitHub Pages with Python
+======
+Create a blog with Pelican, a Python-based blogging platform that works
+well with GitHub.
+![Raspberry Pi and Python][1]
+
+[GitHub][2] is a hugely popular web service for source code control that uses [Git][3] to synchronize local files with copies kept on GitHub's servers so you can easily share and back up your work.
+
+In addition to providing a user interface for code repositories, GitHub also enables users to [publish web pages][4] directly from a repository. The website generation package GitHub recommends is [Jekyll][5], written in Ruby. Since I'm a bigger fan of [Python][6], I prefer [Pelican][7], a Python-based blogging platform that works well with GitHub.
+
+Pelican and Jekyll both transform content written in [Markdown][8] or [reStructuredText][9] into HTML to generate static websites, and both generators support themes that allow unlimited customization.
+
+In this article, I'll describe how to install Pelican, set up your GitHub repository, run a quickstart helper, write some Markdown files, and publish your first page. I'll assume that you have a [GitHub account][10], are comfortable with [basic Git commands][11], and want to publish a blog using Pelican.
+
+### Install Pelican and create the repo
+
+First things first, Pelican (and **ghp-import** ) must be installed on your local machine. This is super easy with [pip][12], the Python package installation tool (you have pip right?):
+
+
+```
+`$ pip install pelican ghp-import`
+```
+
+Next, open a browser and create a new repository on GitHub for your sweet new blog. Name it as follows (substituting your GitHub username for here and throughout this tutorial):
+
+
+```
+`https://GitHub.com/username/username.github.io`
+```
+
+Leave it empty; we will fill it with compelling blog content in a moment.
+
+Using a command line (you command line right?), clone your empty Git repository to your local machine:
+
+
+```
+$ git clone blog
+$ cd blog
+```
+
+### That one weird trick…
+
+Here's a not-super-obvious trick about publishing web content on GitHub. For user pages (pages hosted in repos named _username.github.io_ ), the content is served from the **master** branch.
+
+I strongly prefer not to keep all the Pelican configuration files and raw Markdown files in **master** , rather just the web content. So I keep the Pelican configuration and the raw content in a separate branch I like to call **content**. (You can call it whatever you want, but the following instructions will call it **content**.) I like this structure since I can throw away all the files in **master** and re-populate it with the **content** branch.
+
+
+```
+$ git checkout -b content
+Switched to a new branch 'content'
+```
+
+### Configure Pelican
+
+Now it's time for content configuration. Pelican provides a great initialization tool called **pelican-quickstart** that will ask you a series of questions about your blog.
+
+
+```
+$ pelican-quickstart
+Welcome to pelican-quickstart v3.7.1.
+
+This script will help you create a new Pelican-based website.
+
+Please answer the following questions so this script can generate the files
+needed by Pelican.
+
+> Where do you want to create your new web site? [.]
+> What will be the title of this web site? Super blog
+> Who will be the author of this web site? username
+> What will be the default language of this web site? [en]
+> Do you want to specify a URL prefix? e.g., (Y/n) n
+> Do you want to enable article pagination? (Y/n)
+> How many articles per page do you want? [10]
+> What is your time zone? [Europe/Paris] US/Central
+> Do you want to generate a Fabfile/Makefile to automate generation and publishing? (Y/n) y
+> Do you want an auto-reload & simpleHTTP script to assist with theme and site development? (Y/n) y
+> Do you want to upload your website using FTP? (y/N) n
+> Do you want to upload your website using SSH? (y/N) n
+> Do you want to upload your website using Dropbox? (y/N) n
+> Do you want to upload your website using S3? (y/N) n
+> Do you want to upload your website using Rackspace Cloud Files? (y/N) n
+> Do you want to upload your website using GitHub Pages? (y/N) y
+> Is this your personal page (username.github.io)? (y/N) y
+Done. Your new project is available at /Users/username/blog
+```
+
+You can take the defaults on every question except:
+
+ * Website title, which should be unique and special
+ * Website author, which can be a personal username or your full name
+ * Time zone, which may not be in Paris
+ * Upload to GitHub Pages, which is a "y" in our case
+
+
+
+After answering all the questions, Pelican leaves the following in the current directory:
+
+
+```
+$ ls
+Makefile content/ develop_server.sh*
+fabfile.py output/ pelicanconf.py
+publishconf.py
+```
+
+You can check out the [Pelican docs][13] to find out how to use those files, but we're all about getting things done _right now_. No, I haven't read the docs yet either.
+
+### Forge on
+
+Add all the Pelican-generated files to the **content** branch of the local Git repo, commit the changes, and push the local changes to the remote repo hosted on GitHub by entering:
+
+
+```
+$ git add .
+$ git commit -m 'initial pelican commit to content'
+$ git push origin content
+```
+
+This isn't super exciting, but it will be handy if we need to revert edits to one of these files.
+
+### Finally getting somewhere
+
+OK, now you can get bloggy! All of your blog posts, photos, images, PDFs, etc., will live in the **content** directory, which is initially empty. To begin creating a first post and an About page with a photo, enter:
+
+
+```
+$ cd content
+$ mkdir pages images
+$ cp /Users/username/SecretStash/HotPhotoOfMe.jpg images
+$ touch first-post.md
+$ touch pages/about.md
+```
+
+Next, open the empty file **first-post.md** in your favorite text editor and add the following:
+
+
+```
+title: First Post on My Sweet New Blog
+date:
+author: Your Name Here
+
+# I am On My Way To Internet Fame and Fortune!
+
+This is my first post on my new blog. While not super informative it
+should convey my sense of excitement and eagerness to engage with you,
+the reader!
+```
+
+The first three lines contain metadata that Pelican uses to organize things. There are lots of different metadata you can put there; again, the docs are your best bet for learning more about the options.
+
+Now, open the empty file **pages/about.md** and add this text:
+
+
+```
+title: About
+date:
+
+![So Schmexy][my_sweet_photo]
+
+Hi, I am and I wrote this epic collection of Interweb
+wisdom. In days of yore, much of this would have been deemed sorcery
+and I would probably have been burned at the stake.
+
+😆
+
+[my_sweet_photo]: {filename}/images/HotPhotoOfMe.jpg
+```
+
+You now have three new pieces of web content in your content directory. Of the content branch. That's a lot of content.
+
+### Publish
+
+Don't worry; the payoff is coming!
+
+All that's left to do is:
+
+ * Run Pelican to generate the static HTML files in **output** : [code]`$ pelican content -o output -s publishconf.py`
+```
+* Use **ghp-import** to add the contents of the **output** directory to the **master** branch: [code]`$ ghp-import -m "Generate Pelican site" --no-jekyll -b master output`
+```
+ * Push the local master branch to the remote repo: [code]`$ git push origin master`
+```
+ * Commit and push the new content to the **content** branch: [code] $ git add content
+$ git commit -m 'added a first post, a photo and an about page'
+$ git push origin content
+```
+
+
+
+### OMG, I did it!
+
+Now the exciting part is here, when you get to view what you've published for everyone to see! Open your browser and enter:
+
+
+```
+`https://username.github.io`
+```
+
+Congratulations on your new blog, self-published on GitHub! You can follow this pattern whenever you want to add more pages or articles. Happy blogging.
+
+--------------------------------------------------------------------------------
+
+via: https://opensource.com/article/19/5/run-your-blog-github-pages-python
+
+作者:[Erik O'Shaughnessy][a]
+选题:[lujun9972][b]
+译者:[QiaoN](https://github.com/QiaoN)
+校对:[校对者ID](https://github.com/校对者ID)
+
+本文由 [LCTT](https://github.com/LCTT/TranslateProject) 原创编译,[Linux中国](https://linux.cn/) 荣誉推出
+
+[a]: https://opensource.com/users/jnyjny/users/jasperzanjani/users/jasperzanjani/users/jasperzanjani/users/jnyjny/users/jasperzanjani
+[b]: https://github.com/lujun9972
+[1]: https://opensource.com/sites/default/files/styles/image-full-size/public/lead-images/getting_started_with_python.png?itok=MFEKm3gl (Raspberry Pi and Python)
+[2]: https://github.com/
+[3]: https://git-scm.com
+[4]: https://help.github.com/en/categories/github-pages-basics
+[5]: https://jekyllrb.com
+[6]: https://python.org
+[7]: https://blog.getpelican.com
+[8]: https://guides.github.com/features/mastering-markdown
+[9]: http://docutils.sourceforge.net/docs/user/rst/quickref.html
+[10]: https://github.com/join?source=header-home
+[11]: https://git-scm.com/docs
+[12]: https://pip.pypa.io/en/stable/
+[13]: https://docs.getpelican.com
diff --git a/sources/tech/20190523 Testing a Go-based S2I builder image.md b/sources/tech/20190523 Testing a Go-based S2I builder image.md
new file mode 100644
index 0000000000..a6facd515d
--- /dev/null
+++ b/sources/tech/20190523 Testing a Go-based S2I builder image.md
@@ -0,0 +1,222 @@
+[#]: collector: (lujun9972)
+[#]: translator: ( )
+[#]: reviewer: ( )
+[#]: publisher: ( )
+[#]: url: ( )
+[#]: subject: (Testing a Go-based S2I builder image)
+[#]: via: (https://opensource.com/article/19/5/source-image-golang-part-3)
+[#]: author: (Chris Collins https://opensource.com/users/clcollins)
+
+Testing a Go-based S2I builder image
+======
+In the third article in this series on Source-to-Image for Golang
+applications, build your application image and take it out for a spin.
+![gopher illustrations][1]
+
+In the first two articles in this series, we explored the general [requirements of a Source To Image (S2I) system][2] and [prepared an environment][3] specifically for a Go (Golang) application. Now let's give it a spin.
+
+### Building the builder image
+
+Once the Dockerfile and Source-to-Image (S2I) scripts are ready, the Golang builder image can be created with the **docker build** command:
+
+
+```
+`docker build -t golang-builder .`
+```
+
+This will produce a builder image named **golang-builder** with the context of our current directory.
+
+### Building the application image
+
+The golang-builder image is not much use without an application to build. For this exercise, we will build a simple **hello-world** application.
+
+#### GoHelloWorld
+
+Let's meet our test app, [GoHelloWorld][4]. Download the latest [version of Go][5] if you want to follow along. There are two important (for this exercise) files in this repository:
+
+
+```
+// goHelloWorld.go
+package main
+
+import "fmt"
+
+func main() {
+fmt.Println("Hello World!")
+}
+```
+
+This is a very basic app, but it will work fine for testing the builder image. We also have a basic test for GoHelloWorld:
+
+
+```
+// goHelloWorld_test.go
+package main
+
+import "testing"
+
+func TestMain(t *testing.T) {
+t.Log("Hello World!")
+}
+```
+
+#### Build the application image
+
+Building the application image entails running the **s2i build** command with arguments for the repository containing the code to build (or **.** to build with code from the current directory), the name of the builder image to use, and the name of the resulting application image to create.
+
+
+```
+`$ s2i build https://github.com/clcollins/goHelloWorld.git golang-builder go-hello-world`
+```
+
+To build from a local directory on a filesystem, replace the Git URL with a period to represent the current directory. For example:
+
+
+```
+`$ s2i build . golang-builder go-hello-world`
+```
+
+_Note:_ If a Git repository is initialized in the current directory, S2I will fetch the code from the repository URL rather than using the local code. This results in local, uncommitted changes not being used when building the image (if you're unfamiliar with what I mean by "uncommitted changes," brush up on your [Git terminology over here][6]). Directories that are not Git-initialized repositories behave as expected.
+
+#### Run the application image
+
+Once the application image is built, it can be tested by running it with the **Docker** command. Source-to-Image has replaced the **CMD** in the image with the run script created earlier so it will execute the **/go/src/app/app** binary created during the build process:
+
+
+```
+$ docker run go-hello-world
+Hello World!
+```
+
+Success! We now have a compiled Go application inside a Docker image created by passing the contents of a Git repo to S2I and without needing a special Dockerfile for our application.
+
+The application image we just built includes not only the application, but also its source code, test code, the S2I scripts, Golang libraries, and _much of the Debian Linux distribution_ (because the Golang image is based on the Debian base image). The resulting image is not small:
+
+
+```
+$ docker images | grep go-hello-world
+go-hello-world latest 75a70c79a12f 4 minutes ago 789 MB
+```
+
+For applications written in languages that are interpreted at runtime and depend on linked libraries, like Ruby or Python, having all the source code and operating system are necessary to run. The build images will be pretty large as a result, but at least we know it will be able to run. With these languages, we could stop here with our S2I builds.
+
+There is the option, however, to more explicitly define the production requirements for the application.
+
+Since the resulting application image would be the same image that would run the production app, I want to assure the required ports, volumes, and environment variables are added to the Dockerfile for the builder image. By writing these in a declarative way, our app is closer to the [Twelve-Factor App][7] recommended practice. For example, if we were to use the builder image to create application images for a Ruby on Rails application running [Puma][8], we would want to open a port to access the webserver. We should add the line **PORT 3000** in the builder Dockerfile so it can be inherited by all the images generated from it.
+
+But for the Go app, we can do better.
+
+### Build a runtime image
+
+Since our builder image created a statically compiled Go binary with our application, we can create a final "runtime" image containing _only_ the binary and none of the other cruft.
+
+Once the application image is created, the compiled GoHelloWorld app can be extracted and put into a new, empty image using the save-artifacts script.
+
+#### Runtime files
+
+Only the application binary and a Dockerfile are required to create the runtime image.
+
+##### Application binary
+
+Inside of the application image, the save-artifacts script is written to stream a tar archive of the app binary to stdout. We can check the files included in the tar archive created by save-artifacts with the **-vt** flags for tar:
+
+
+```
+$ docker run go-hello-world /usr/libexec/s2i/save-artifacts | tar -tvf -
+-rwxr-xr-x 1001/root 1997502 2019-05-03 18:20 app
+```
+
+If this results in errors along the lines of "This does not appear to be a tar archive," the save-artifacts script is probably outputting other data in addition to the tar stream, as mentioned above. We must make sure to suppress all output other than the tar stream.
+
+If everything looks OK, we can use **save-artifacts** to copy the binary out of the application image:
+
+
+```
+`$ docker run go-hello-world /usr/libexec/s2i/save-artifacts | tar -xf -`
+```
+
+This will copy the app file into the current directory, ready to be added to its own image.
+
+##### Dockerfile
+
+The Dockerfile is extremely simple, with only three lines. The **FROM scratch** source denotes that it uses an empty, blank parent image. The rest of the Dockerfile specifies copying the app binary into **/app** in the image and using that binary as the image **ENTRYPOINT** :
+
+
+```
+FROM scratch
+COPY app /app
+ENTRYPOINT ["/app"]
+```
+
+Save this Dockerfile as **Dockerfile-runtime**.
+
+Why **ENTRYPOINT** and not **CMD**? We could do either, but since there is nothing else in the image (no filesystem, no shell), we couldn't run anything else anyway.
+
+#### Building the runtime image
+
+With the Dockerfile and binary ready to go, we can build the new runtime image:
+
+
+```
+`$ docker build -f Dockerfile-runtime -t go-hello-world:slim .`
+```
+
+The new runtime image is considerably smaller—just 2MB!
+
+
+```
+$ docker images | grep -e 'go-hello-world *slim'
+go-hello-world slim 4bd091c43816 3 minutes ago 2 MB
+```
+
+We can test that it still works as expected with **docker run** :
+
+
+```
+$ docker run go-hello-world:slim
+Hello World!
+```
+
+### Bootstrapping s2i with s2i create
+
+While we hand-created all the S2I files in this example, the **s2i** command has a sub-command to help scaffold all the files we might need for a Source-to-Image build: **s2i create**.
+
+Using the **s2i create** command, we can generate a new project, creatively named **go-hello-world-2** in the **./ghw2** directory:
+
+
+```
+$ s2i create go-hello-world-2 ./ghw2
+$ ls ./ghw2/
+Dockerfile Makefile README.md s2i test
+```
+
+The **create** sub-command creates a placeholder Dockerfile, a README.md with information about how to use Source-to-Image, some example S2I scripts, a basic test framework, and a Makefile. The Makefile is a great way to automate building and testing the Source-to-Image builder image. Out of the box, running **make** will build our image, and it can be extended to do more. For example, we could add steps to build a base application image, run tests, or generate a runtime Dockerfile.
+
+### Conclusion
+
+In this tutorial, we have learned how to use Source-to-Image to build a custom Golang builder image, create an application image using **s2i build** , and extract the application binary to create a super-slim runtime image.
+
+In a future extension to this series, I would like to look at how to use the builder image we created with [OKD][9] to automatically deploy our Golang apps with **buildConfigs** , **imageStreams** , and **deploymentConfigs**. Please let me know in the comments if you are interested in me continuing the series, and thanks for reading.
+
+--------------------------------------------------------------------------------
+
+via: https://opensource.com/article/19/5/source-image-golang-part-3
+
+作者:[Chris Collins][a]
+选题:[lujun9972][b]
+译者:[译者ID](https://github.com/译者ID)
+校对:[校对者ID](https://github.com/校对者ID)
+
+本文由 [LCTT](https://github.com/LCTT/TranslateProject) 原创编译,[Linux中国](https://linux.cn/) 荣誉推出
+
+[a]: https://opensource.com/users/clcollins
+[b]: https://github.com/lujun9972
+[1]: https://opensource.com/sites/default/files/styles/image-full-size/public/lead-images/go-golang.png?itok=OAW9BXny (gopher illustrations)
+[2]: https://opensource.com/article/19/5/source-image-golang-part-1
+[3]: https://opensource.com/article/19/5/source-image-golang-part-2
+[4]: https://github.com/clcollins/goHelloWorld.git
+[5]: https://golang.org/doc/install
+[6]: /article/19/2/git-terminology
+[7]: https://12factor.net/
+[8]: http://puma.io/
+[9]: https://okd.io/
diff --git a/sources/tech/20190524 Choosing the right model for maintaining and enhancing your IoT project.md b/sources/tech/20190524 Choosing the right model for maintaining and enhancing your IoT project.md
new file mode 100644
index 0000000000..06b8fd6de3
--- /dev/null
+++ b/sources/tech/20190524 Choosing the right model for maintaining and enhancing your IoT project.md
@@ -0,0 +1,96 @@
+[#]: collector: (lujun9972)
+[#]: translator: ( )
+[#]: reviewer: ( )
+[#]: publisher: ( )
+[#]: url: ( )
+[#]: subject: (Choosing the right model for maintaining and enhancing your IoT project)
+[#]: via: (https://opensource.com/article/19/5/model-choose-embedded-iot-development)
+[#]: author: (Drew Moseley https://opensource.com/users/drewmoseley)
+
+Choosing the right model for maintaining and enhancing your IoT project
+======
+Learn more about these two models: Centralized Golden Master and
+Distributed Build System
+![][1]
+
+In today's connected embedded device market, driven by the [Internet of things (IoT)][2], a large share of devices in development are based on Linux of one form or another. The prevalence of low-cost boards with ready-made Linux distributions is a key driver in this. Acquiring hardware, building your custom code, connecting the devices to other hardware peripherals and the internet as well as device management using commercial cloud providers has never been easier. A developer or development team can quickly prototype a new application and get the devices in the hands of potential users. This is a good thing and results in many interesting new applications, as well as many questionable ones.
+
+When planning a system design for beyond the prototyping phase, things get a little more complex. In this post, we want to consider mechanisms for developing and maintaining your base [operating system (OS) image][3]. There are many tools to help with this but we won't be discussing individual tools; of interest here is the underlying model for maintaining and enhancing this image and how it will make your life better or worse.
+
+There are two primary models for generating these images:
+
+ 1. Centralized Golden Master
+ 2. Distributed Build System
+
+
+
+These categories mirror the driving models for [Source Code Management (SCM)][4] systems, and many of the arguments regarding centralized vs. distributed are applicable when discussing OS images.
+
+### Centralized Golden Master
+
+Hobbyist and maker projects primarily use the Centralized Golden Master method of creating and maintaining application images. This fact gives this model the benefit of speed and familiarity, allowing developers to quickly set up such a system and get it running. The speed comes from the fact that many device manufacturers provide canned images for their off-the-shelf hardware. For example, boards from such families as the [BeagleBone][5] and [Raspberry Pi][6] offer ready-to-use OS images and [flashing][7]. Relying on these images means having your system up and running in just a few mouse clicks. The familiarity is due to the fact that these images are generally based on a desktop distro many device developers have already used, such as [Debian][8]. Years of using Linux can then directly transfer to the embedded design, including the fact that the packaging utilities remain largely the same, and it is simple for designers to get the extra software packages they need.
+
+There are a few downsides of such an approach. The first is that the [golden master image][9] is generally a choke point, resulting in lost developer productivity after the prototyping stage since everyone must wait for their turn to access the latest image and make their changes. In the SCM realm, this practice is equivalent to a centralized system with individual [file locking][10]. Only the developer with the lock can work on any given file.
+
+![Development flow with the Centralized Golden Master model.][11]
+
+The second downside with this approach is image reproducibility. This issue is usually managed by manually logging into the target systems, installing packages using the native package manager, configuring applications and dot files, and then modifying the system configuration files in place. Once this process is completed, the disk is imaged using the **dd** utility, or an equivalent, and then distributed.
+
+Again, this approach creates a minefield of potential issues. For example, network-based package feeds may cease to exist, and the base software provided by the vendor image may change. Scripting can help mitigate these issues. However, these scripts tend to be fragile and break when changes are made to configuration file formats or the vendor's base software packages.
+
+The final issue that arises with this development model is reliance on third parties. If the hardware vendor's image changes don't work for your design, you may need to invest significant time to adapt. To make matters even more complicated, as mentioned before, the hardware vendors often based their images on an upstream project such as Debian or Ubuntu. This situation introduces even more third parties who can affect your design.
+
+### Distributed Build System
+
+This method of creating and maintaining an image for your application relies on the generation of target images separate from the target hardware. The developer workflow here is similar to standard software development using an SCM system; the image is fully buildable by tooling and each developer can work independently. Changes to the system are made via edits to metadata files (scripting, recipes, configuration files, etc) and then the tooling is rerun to generate an updated image. These metadata files are then managed using an SCM system. Individual developers can merge the latest changes into their working copies to produce their development images. In this case, no golden master image is needed and developers can avoid the associated bottleneck.
+
+Release images are then produced by a build system using standard SCM techniques to pull changes from all the developers.
+
+![Development flow with the Distributed Build System model.][12]
+
+Working in this fashion allows the size of your development team to increase without reducing productivity of individual developers. All engineers can work independently of the others. Additionally, this build setup ensures that your builds can be reproduced. Using standard SCM workflows can ensure that, at any future time, you can regenerate a specific build allowing for long term maintenance, even if upstream providers are no longer available. Similar to working with distributed SCM tools however, there is additional policy that needs to be in place to enable reproducible, release candidate images. Individual developers have their own copies of the source and can build their own test images but for a proper release engineering effort, development teams will need to establish merging and branching standards and ensure that all changes targeted for release eventually get merged into a well-defined branch. Many upstream projects already have well-defined processes for this kind of release strategy (for instance, using *-stable and *-next branches).
+
+The primary downside of this approach is the lack of familiarity. For example, adding a package to the image normally requires creating a recipe of some kind and then updating the definitions so that the package binaries are included in the image. This is very different from running apt while logged into a running system. The learning curve of these systems can be daunting but the results are more predictable and scalable and are likely a better choice when considering a design for a product that will be mass produced.
+
+Dedicated build systems such as [OpenEmbedded][13] and [Buildroot][14] use this model as do distro packaging tools such as [debootstrap][15] and [multistrap][16]. Newer tools such as [Isar][17], [debos][18], and [ELBE][19] also use this basic model. Choices abound, and it is worth the investment to learn one or more of these packages for your designs. The long term maintainability and reproducibility of these systems will reduce risk in your design by allowing you to generate reproducible builds, track all the source code, and remove your dependency on third-party providers continued existence.
+
+#### Conclusion
+
+To be clear, the distributed model does suffer some of the same issues as mentioned for the Golden Master Model; especially the reliance on third parties. This is a consequence of using systems designed by others and cannot be completely avoided unless you choose a completely roll-your-own approach which comes with a significant cost in development and maintenance.
+
+For prototyping and proof-of-concept level design, and a team of just a few developers, the Golden Master Model may well be the right choice given restrictions in time and budget that are present at this stage of development. For low volume, high touch designs, this may be an acceptable trade-off for production use.
+
+For general production use, the benefits in terms of team size scalability, image reproducibility and developer productivity greatly outweigh the learning curve and overhead of systems implementing the distributed model. Support from board and chip vendors is also widely available in these systems reducing the upfront costs of developing with them. For your next product, I strongly recommend starting the design with a serious consideration of the model being used to generate the base OS image. If you choose to prototype with the golden master model with the intention of migrating to the distributed model, make sure to build sufficient time in your schedule for this effort; the estimates will vary widely depending on the specific tooling you choose as well as the scope of the requirements and the out-of-the-box availability of software packages your code relies on.
+
+--------------------------------------------------------------------------------
+
+via: https://opensource.com/article/19/5/model-choose-embedded-iot-development
+
+作者:[Drew Moseley][a]
+选题:[lujun9972][b]
+译者:[译者ID](https://github.com/译者ID)
+校对:[校对者ID](https://github.com/校对者ID)
+
+本文由 [LCTT](https://github.com/LCTT/TranslateProject) 原创编译,[Linux中国](https://linux.cn/) 荣誉推出
+
+[a]: https://opensource.com/users/drewmoseley
+[b]: https://github.com/lujun9972
+[1]: https://opensource.com/sites/default/files/styles/image-full-size/public/lead-images/LAW-Internet_construction_9401467_520x292_0512_dc.png?itok=RPkPPtDe
+[2]: https://en.wikipedia.org/wiki/Internet_of_things
+[3]: https://en.wikipedia.org/wiki/System_image
+[4]: https://en.wikipedia.org/wiki/Version_control
+[5]: http://beagleboard.org/
+[6]: https://www.raspberrypi.org/
+[7]: https://en.wikipedia.org/wiki/Flash_memory
+[8]: https://www.debian.org/
+[9]: https://en.wikipedia.org/wiki/Software_release_life_cycle#RTM
+[10]: https://en.wikipedia.org/wiki/File_locking
+[11]: https://opensource.com/sites/default/files/uploads/cgm1_500.png (Development flow with the Centralized Golden Master model.)
+[12]: https://opensource.com/sites/default/files/uploads/cgm2_500.png (Development flow with the Distributed Build System model.)
+[13]: https://www.openembedded.org/
+[14]: https://buildroot.org/
+[15]: https://wiki.debian.org/Debootstrap
+[16]: https://wiki.debian.org/Multistrap
+[17]: https://github.com/ilbers/isar
+[18]: https://github.com/go-debos/debos
+[19]: https://elbe-rfs.org/
diff --git a/sources/tech/20190524 Dual booting Windows and Linux using UEFI.md b/sources/tech/20190524 Dual booting Windows and Linux using UEFI.md
new file mode 100644
index 0000000000..b281b6036b
--- /dev/null
+++ b/sources/tech/20190524 Dual booting Windows and Linux using UEFI.md
@@ -0,0 +1,104 @@
+[#]: collector: (lujun9972)
+[#]: translator: ( )
+[#]: reviewer: ( )
+[#]: publisher: ( )
+[#]: url: ( )
+[#]: subject: (Dual booting Windows and Linux using UEFI)
+[#]: via: (https://opensource.com/article/19/5/dual-booting-windows-linux-uefi)
+[#]: author: (Alan Formy-Duval https://opensource.com/users/alanfdoss/users/ckrzen)
+
+Dual booting Windows and Linux using UEFI
+======
+A quick rundown of setting up Linux and Windows to dual boot on the same
+machine, using the Unified Extensible Firmware Interface (UEFI).
+![Linux keys on the keyboard for a desktop computer][1]
+
+Rather than doing a step-by-step how-to guide to configuring your system to dual boot, I’ll highlight the important points. As an example, I will refer to my new laptop that I purchased a few months ago. I first installed [Ubuntu Linux][2] onto the entire hard drive, which destroyed the pre-installed [Windows 10][3] installation. After a few months, I decided to install a different Linux distribution, and so also decided to re-install Windows 10 alongside [Fedora Linux][4] in a dual boot configuration. I’ll highlight some essential facts to get started.
+
+### Firmware
+
+Dual booting is not just a matter of software. Or, it is, but it involves changing your firmware, which among other things tells your machine how to begin the boot process. Here are some firmware-related issues to keep in mind.
+
+#### UEFI vs. BIOS
+
+Before attempting to install, make sure your firmware configuration is optimal. Most computers sold today have a new type of firmware known as [Unified Extensible Firmware Interface (UEFI)][5], which has pretty much replaced the other firmware known as [Basic Input Output System (BIOS)][6], which is often included through the mode many providers call Legacy Boot.
+
+I had no need for BIOS, so I chose UEFI mode.
+
+#### Secure Boot
+
+One other important setting is Secure Boot. This feature detects whether the boot path has been tampered with, and stops unapproved operating systems from booting. For now, I disabled this option to ensure that I could install Fedora Linux. According to the Fedora Project Wiki [Features/Secure Boot ][7] Fedora Linux will work with it enabled. This may be different for other Linux distributions —I plan to revisit this setting in the future.
+
+In short, if you find that you cannot install your Linux OS with this setting active, disable Secure Boot and try again.
+
+### Partitioning the boot drive
+
+If you choose to dual boot and have both operating systems on the same drive, you have to break it into partitions. Even if you dual boot using two different drives, most Linux installations are best broken into a few basic partitions for a variety of reasons. Here are some options to consider.
+
+#### GPT vs MBR
+
+If you decide to manually partition your boot drive in advance, I recommend using the [GUID Partition Table (GPT)][8] rather than the older [Master Boot Record (MBR)][9]. Among the reasons for this change, there are two specific limitations of MBR that GPT doesn’t have:
+
+ * MBR can hold up to 15 partitions, while GPT can hold up to 128.
+ * MBR only supports up to 2 terabytes, while GPT uses 64-bit addresses which allows it to support disks up to 8 million terabytes.
+
+
+
+If you have shopped for hard drives recently, then you know that many of today’s drives exceed the 2 terabyte limit.
+
+#### The EFI system partition
+
+If you are doing a fresh installation or using a new drive, there are probably no partitions to begin with. In this case, the OS installer will create the first one, which is the [EFI System Partition (ESP)][10]. If you choose to manually partition your drive using a tool such as [gdisk][11], you will need to create this partition with several parameters. Based on the existing ESP, I set the size to around 500MB and assigned it the ef00 (EFI System) partition type. The UEFI specification requires the format to be FAT32/msdos, most likely because it is supportable by a wide range of operating systems.
+
+![Partitions][12]
+
+### Operating System Installation
+
+Once you accomplish the first two tasks, you can install your operating systems. While I focus on Windows 10 and Fedora Linux here, the process is fairly similar when installing other combinations as well.
+
+#### Windows 10
+
+I started the Windows 10 installation and created a 20 Gigabyte Windows partition. Since I had previously installed Linux on my laptop, the drive had an ESP, which I chose to keep. I deleted all existing Linux and swap partitions to start fresh, and then started my Windows installation. The Windows installer automatically created another small partition—16 Megabytes—called the [Microsoft Reserved Partition (MSR)][13]. Roughly 400 Gigabytes of unallocated space remained on the 512GB boot drive once this was finished.
+
+I then proceeded with and completed the Windows 10 installation process. I then rebooted into Windows to make sure it was working, created my user account, set up wi-fi, and completed other tasks that need to be done on a first-time OS installation.
+
+#### Fedora Linux
+
+I next moved to install Linux. I started the process, and when it reached the disk configuration steps, I made sure not to change the Windows NTFS and MSR partitions. I also did not change the EPS, but I did set its mount point to **/boot/efi**. I then created the usual ext4 formatted partitions, **/** (root), **/boot** , and **/home**. The last partition I created was Linux **swap**.
+
+As with Windows, I continued and completed the Linux installation, and then rebooted. To my delight, at boot time the [GRand][14] [Unified Boot Loader (GRUB)][14] menu provided the choice to select either Windows or Linux, which meant I did not have to do any additional configuration. I selected Linux and completed the usual steps such as creating my user account.
+
+### Conclusion
+
+Overall, the process was painless. In past years, there has been some difficulty navigating the changes from UEFI to BIOS, plus the introduction of features such as Secure Boot. I believe that we have now made it past these hurdles and can reliably set up multi-boot systems.
+
+I don’t miss the [Linux LOader (LILO)][15] anymore!
+
+--------------------------------------------------------------------------------
+
+via: https://opensource.com/article/19/5/dual-booting-windows-linux-uefi
+
+作者:[Alan Formy-Duval][a]
+选题:[lujun9972][b]
+译者:[译者ID](https://github.com/译者ID)
+校对:[校对者ID](https://github.com/校对者ID)
+
+本文由 [LCTT](https://github.com/LCTT/TranslateProject) 原创编译,[Linux中国](https://linux.cn/) 荣誉推出
+
+[a]: https://opensource.com/users/alanfdoss/users/ckrzen
+[b]: https://github.com/lujun9972
+[1]: https://opensource.com/sites/default/files/styles/image-full-size/public/lead-images/linux_keyboard_desktop.png?itok=I2nGw78_ (Linux keys on the keyboard for a desktop computer)
+[2]: https://www.ubuntu.com
+[3]: https://www.microsoft.com/en-us/windows
+[4]: https://getfedora.org
+[5]: https://en.wikipedia.org/wiki/Unified_Extensible_Firmware_Interface
+[6]: https://en.wikipedia.org/wiki/BIOS
+[7]: https://fedoraproject.org/wiki/Features/SecureBoot
+[8]: https://en.wikipedia.org/wiki/GUID_Partition_Table
+[9]: https://en.wikipedia.org/wiki/Master_boot_record
+[10]: https://en.wikipedia.org/wiki/EFI_system_partition
+[11]: https://sourceforge.net/projects/gptfdisk/
+[12]: /sites/default/files/u216961/gdisk_screenshot_s.png
+[13]: https://en.wikipedia.org/wiki/Microsoft_Reserved_Partition
+[14]: https://en.wikipedia.org/wiki/GNU_GRUB
+[15]: https://en.wikipedia.org/wiki/LILO_(boot_loader)
diff --git a/sources/tech/20190527 4 open source mobile apps for Nextcloud.md b/sources/tech/20190527 4 open source mobile apps for Nextcloud.md
new file mode 100644
index 0000000000..c97817e3c1
--- /dev/null
+++ b/sources/tech/20190527 4 open source mobile apps for Nextcloud.md
@@ -0,0 +1,140 @@
+[#]: collector: (lujun9972)
+[#]: translator: ( )
+[#]: reviewer: ( )
+[#]: publisher: ( )
+[#]: url: ( )
+[#]: subject: (4 open source mobile apps for Nextcloud)
+[#]: via: (https://opensource.com/article/19/5/mobile-apps-nextcloud)
+[#]: author: (Scott Nesbitt https://opensource.com/users/scottnesbitt)
+
+4 open source mobile apps for Nextcloud
+======
+Increase Nextcloud's value by turning it into an on-the-go information
+hub.
+![][1]
+
+I've been using [Nextcloud][2] (and before that, ownCloud), an open source alternative to file syncing and storage services like Dropbox and Google Drive, for many years. It's been both reliable and useful, and it respects my privacy.
+
+While Nextcloud is great at both syncing and storage, it's much more than a place to dump your files. Thanks to applications that you can fold into Nextcloud, it becomes more of an information hub than a storage space.
+
+While I usually interact with Nextcloud using the desktop client or in a browser, I'm not always at my computer (or any computer that I trust). So it's important that I can work with Nextcloud using my [LineageOS][3]-powered smartphone or tablet.
+
+To do that, I use several open source apps that work with Nextcloud. Let's take a look at four of them.
+
+As you've probably guessed, this article looks at the Android version of those apps. I grabbed mine from [F-Droid][4], although you get them from other Android app markets. You might be able to get some or all of them from Apple's App Store if you're an iOS person.
+
+### Working with files and folders
+
+The obvious app to start with is the [Nextcloud sync client][5]. This little app links your phone or tablet to your Nextcloud account.
+
+![Nextcloud mobile app][6]
+
+Using the app, you can:
+
+ * Create folders
+ * Upload one or more files
+ * Sync files between your device and server
+ * Rename or remove files
+ * Make files available offline
+
+
+
+You can also tap a file to view or edit it. If your device doesn't have an app that can open the file, then you're out of luck. You can still download it to your phone or tablet though.
+
+### Reading news feeds
+
+Remember all the whining that went on when Google pulled the plug on Google Reader in 2013? This despite Google giving users several months to find an alternative. And, yes, there are alternatives. One of them, believe it or not, is Nextcloud.
+
+Nextcloud has a built-in RSS reader. All you need to do to get started is upload an [OPML][7] file containing your feeds or manually add a site's RSS feed to Nextcloud.
+
+Going mobile is easy, too, with the Nextcloud [News Reader app][8].
+
+![Nextcloud News app][9]
+
+Unless you configure the app to sync when you start it up, you'll need to swipe down from the top of the app to load updates to your feeds. Depending on how many feeds you have, and how many unread items are in those feeds, syncing takes anywhere from a few seconds to half a minute.
+
+From there, tap an item to read it in the News app.
+
+![Nextcloud News app][10]
+
+You can also add feeds or open what you're reading in your device's default web browser.
+
+### Reading and writing notes
+
+I don't use Nextcloud's [Notes][11] app all that often (I'm more of a [Standard Notes][12] person). That said, you might find the Notes app comes in handy.
+
+How? By giving you a lightweight way to take [plain text][13] notes on your mobile device. The Notes app syncs any notes you have in your Nextcloud account and displays them in chronological order—newest or last-edited notes first.
+
+![Nextcloud Notes app][14]
+
+Tap a note to read or edit it. You can also create a note by tapping the **+** button, then typing what you need to type.
+
+![Nextcloud Notes app][15]
+
+There's no formatting, although you can add markup (like Markdown) to the note. Once you're done editing, the app syncs your note with Nextcloud.
+
+### Accessing your bookmarks
+
+Nextcloud has a decent bookmarking tool, and its [Bookmarks][16] app makes it easy to work with the tool on your phone or tablet.
+
+![Nextcloud Bookmarks app][17]
+
+Like the Notes app, Bookmarks displays your bookmarks in chronological order, with the newest appearing first in the list.
+
+If you tagged your bookmarks in Nextcloud, you can swipe left in the app to see a list of those tags rather than a long list of bookmarks. Tap a tag to view the bookmarks under it.
+
+![Nextcloud Bookmarks app][18]
+
+From there, just tap a bookmark. It opens in your device's default browser.
+
+You can also add a bookmark within the app. To do that, tap the **+** menu and add the bookmark.
+
+![Nextcloud Bookmarks app][19]
+
+You can include:
+
+ * The URL
+ * A title for the bookmark
+ * A description
+ * One or more tags
+
+
+
+### Is that all?
+
+Definitely not. There are apps for [Nextcloud Deck][20] (a personal kanban tool) and [Nextcloud Talk][21] (a voice and video chat app). There are also a number of third-party apps that work with Nextcloud. Just do a search for _Nextcloud_ or _ownCloud_ in your favorite app store to track them down.
+
+--------------------------------------------------------------------------------
+
+via: https://opensource.com/article/19/5/mobile-apps-nextcloud
+
+作者:[Scott Nesbitt][a]
+选题:[lujun9972][b]
+译者:[译者ID](https://github.com/译者ID)
+校对:[校对者ID](https://github.com/校对者ID)
+
+本文由 [LCTT](https://github.com/LCTT/TranslateProject) 原创编译,[Linux中国](https://linux.cn/) 荣誉推出
+
+[a]: https://opensource.com/users/scottnesbitt
+[b]: https://github.com/lujun9972
+[1]: https://opensource.com/sites/default/files/styles/image-full-size/public/lead-images/OSDC_BUS_cloudagenda_20140341_jehb.png?itok=1NGs3_n4
+[2]: https://nextcloud.com/
+[3]: https://lineageos.org/
+[4]: https://opensource.com/life/15/1/going-open-source-android-f-droid
+[5]: https://f-droid.org/en/packages/com.nextcloud.client/
+[6]: https://opensource.com/sites/default/files/uploads/nextcloud-app.png (Nextcloud mobile app)
+[7]: http://en.wikipedia.org/wiki/OPML
+[8]: https://f-droid.org/en/packages/de.luhmer.owncloudnewsreader/
+[9]: https://opensource.com/sites/default/files/uploads/nextcloud-news.png (Nextcloud News app)
+[10]: https://opensource.com/sites/default/files/uploads/nextcloud-news-reading.png (Nextcloud News app)
+[11]: https://f-droid.org/en/packages/it.niedermann.owncloud.notes
+[12]: https://opensource.com/article/18/12/taking-notes-standard-notes
+[13]: https://plaintextproject.online
+[14]: https://opensource.com/sites/default/files/uploads/nextcloud-notes.png (Nextcloud Notes app)
+[15]: https://opensource.com/sites/default/files/uploads/nextcloud-notes-add.png (Nextcloud Notes app)
+[16]: https://f-droid.org/en/packages/org.schabi.nxbookmarks/
+[17]: https://opensource.com/sites/default/files/uploads/nextcloud-bookmarks.png (Nextcloud Bookmarks app)
+[18]: https://opensource.com/sites/default/files/uploads/nextcloud-bookmarks-tags.png (Nextcloud Bookmarks app)
+[19]: https://opensource.com/sites/default/files/uploads/nextcloud-bookmarks-add.png (Nextcloud Bookmarks app)
+[20]: https://f-droid.org/en/packages/it.niedermann.nextcloud.deck
+[21]: https://f-droid.org/en/packages/com.nextcloud.talk2
diff --git a/sources/tech/20190527 5 GNOME keyboard shortcuts to be more productive.md b/sources/tech/20190527 5 GNOME keyboard shortcuts to be more productive.md
new file mode 100644
index 0000000000..989d69e524
--- /dev/null
+++ b/sources/tech/20190527 5 GNOME keyboard shortcuts to be more productive.md
@@ -0,0 +1,86 @@
+[#]: collector: (lujun9972)
+[#]: translator: ( )
+[#]: reviewer: ( )
+[#]: publisher: ( )
+[#]: url: ( )
+[#]: subject: (5 GNOME keyboard shortcuts to be more productive)
+[#]: via: (https://fedoramagazine.org/5-gnome-keyboard-shortcuts-to-be-more-productive/)
+[#]: author: (Clément Verna https://fedoramagazine.org/author/cverna/)
+
+5 GNOME keyboard shortcuts to be more productive
+======
+
+![][1]
+
+For some people, using GNOME Shell as a traditional desktop manager may be frustrating since it often requires more action of the mouse. In fact, GNOME Shell is also a [desktop manager][2] designed for and meant to be driven by the keyboard. Learn how to be more efficient with GNOME Shell with these 5 ways to use the keyboard instead of the mouse.
+
+### GNOME activities overview
+
+The activities overview can be easily opened using the **Super** key from the keyboard. (The **Super** key usually has a logo on it.) This is really useful when it comes to start an application. For example, it’s easy to start the Firefox web browser with the following key sequence **Super + f i r + Enter.**
+
+![][3]
+
+### Message tray
+
+In GNOME, notifications are available in the message tray. This is also the place where the calendar and world clocks are available. To open the message tray using the keyboard use the **Super+m** shortcut. To close the message tray simply use the same shortcut again.
+
+ * ![][4]
+
+
+
+### Managing workspaces in GNOME
+
+Gnome Shell uses dynamic workspaces, meaning it creates additional workspaces as they are needed. A great way to be more productive using Gnome is to use one workspace per application or per dedicated activity, and then use the keyboard to navigate between these workspaces.
+
+Let’s look at a practical example. To open a Terminal in the current workspace press the following keys: **Super + t e r + Enter.** Then, to open a new workspace press **Super + PgDn**. Open Firefox ( **Super + f i r + Enter)**. To come back to the terminal, use **Super + PgUp**.
+
+![][5]
+
+### Managing an application window
+
+Using the keyboard it is also easy to manage the size of an application window. Minimizing, maximizing and moving the application to the left or the right of the screen can be done with only a few key strokes. Use **Super+**🠝 to maximize, **Super+**🠟 to minimize, **Super+**🠜 and **Super+**🠞 to move the window left and right.
+
+![][6]
+
+### Multiple windows from the same application
+
+Using the activities overview to start an application is very efficient. But trying to open a new window from an application already running only results in focusing on the open window. To create a new window, instead of simply hitting **Enter** to start the application, use **Ctrl+Enter**.
+
+So for example, to start a second instance of the terminal using the application overview, **Super + t e r + (Ctrl+Enter)**.
+
+![][7]
+
+Then you can use **Super+`** to switch between windows of the same application.
+
+![][8]
+
+As shown, GNOME Shell is a really powerful desktop environment when controlled from the keyboard. Learning to use these shortcuts and train your muscle memory to not use the mouse will give you a better user experience, and make you more productive when using GNOME. For other useful shortcuts, check out [this page on the GNOME wiki][9].
+
+* * *
+
+_Photo by _[ _1AmFcS_][10]_ on _[_Unsplash_][11]_._
+
+--------------------------------------------------------------------------------
+
+via: https://fedoramagazine.org/5-gnome-keyboard-shortcuts-to-be-more-productive/
+
+作者:[Clément Verna][a]
+选题:[lujun9972][b]
+译者:[译者ID](https://github.com/译者ID)
+校对:[校对者ID](https://github.com/校对者ID)
+
+本文由 [LCTT](https://github.com/LCTT/TranslateProject) 原创编译,[Linux中国](https://linux.cn/) 荣誉推出
+
+[a]: https://fedoramagazine.org/author/cverna/
+[b]: https://github.com/lujun9972
+[1]: https://fedoramagazine.org/wp-content/uploads/2019/05/5-gnome-keycombos-816x345.jpg
+[2]: https://fedoramagazine.org/gnome-3-32-released-coming-to-fedora-30/
+[3]: https://fedoramagazine.org/wp-content/uploads/2019/05/Peek-2019-05-23-10-50.gif
+[4]: https://fedoramagazine.org/wp-content/uploads/2019/05/Peek-2019-05-23-11-01.gif
+[5]: https://fedoramagazine.org/wp-content/uploads/2019/05/Peek-2019-05-23-12-57.gif
+[6]: https://fedoramagazine.org/wp-content/uploads/2019/05/Peek-2019-05-23-13-06.gif
+[7]: https://fedoramagazine.org/wp-content/uploads/2019/05/Peek-2019-05-23-13-19.gif
+[8]: https://fedoramagazine.org/wp-content/uploads/2019/05/Peek-2019-05-23-13-22.gif
+[9]: https://wiki.gnome.org/Design/OS/KeyboardShortcuts
+[10]: https://unsplash.com/photos/MuTWth_RnEs?utm_source=unsplash&utm_medium=referral&utm_content=creditCopyText
+[11]: https://unsplash.com/search/photos/keyboard?utm_source=unsplash&utm_medium=referral&utm_content=creditCopyText
diff --git a/sources/tech/20190527 Blockchain 2.0 - Introduction To Hyperledger Sawtooth -Part 12.md b/sources/tech/20190527 Blockchain 2.0 - Introduction To Hyperledger Sawtooth -Part 12.md
new file mode 100644
index 0000000000..8ab4b5b0b8
--- /dev/null
+++ b/sources/tech/20190527 Blockchain 2.0 - Introduction To Hyperledger Sawtooth -Part 12.md
@@ -0,0 +1,103 @@
+[#]: collector: (lujun9972)
+[#]: translator: ( )
+[#]: reviewer: ( )
+[#]: publisher: ( )
+[#]: url: ( )
+[#]: subject: (Blockchain 2.0 – Introduction To Hyperledger Sawtooth [Part 12])
+[#]: via: (https://www.ostechnix.com/blockchain-2-0-introduction-to-hyperledger-sawtooth/)
+[#]: author: (editor https://www.ostechnix.com/author/editor/)
+
+Blockchain 2.0 – Introduction To Hyperledger Sawtooth [Part 12]
+======
+
+![Introduction To Hyperledger Sawtooth][1]
+
+After having discussed the [**Hyperledger Fabric**][2] project in detail on this blog, its time we moved on to the next project of interest at the Hyperledger camp. **Hyperledger Sawtooth** is Intel’s contribution to the [**Blockchain**][3] consortium mission to develop enterprise ready modular distributed ledgers and applications. Sawtooth is another attempt at creating an easy to roll out blockchain ledger for businesses keeping their resource constraints and security requirements in mind. While platforms such as [**Ethereum**][4] will in theory offer similar functionality when placed in capable hands, Sawtooth readily provides a lot of customizability and is built from the ground up for specific enterprise level use cases.
+
+The Hyperledger project page has an introductory video detailing the Sawtooth architecture and platform. We’re attaching it here for readers to get a quick round-up about the product.
+
+Moving to the intricacies of the Sawtooth project, there are **five primary and significant differences** between Sawtooth and its alternatives. The post from now and on will explore these differences and at the end will mention an example real world use case for Hyperledger Sawtooth in managing supply chains.
+
+### Distinction 1: The consensus algorithm – PoET
+
+This is perhaps amongst the most notable and significant changes that Sawtooth brings to the fore. While exploring all the different consensus algorithms that exist for blockchain platforms these days is out of the scope of this post, what is to be noted is that Sawtooth uses a **Proof Of Elapsed Time** (POET) based consensus algorithm. Such a system for validating transactions and blocks on the blockchain is considered to be resources efficient unlike other computation heavy systems which use the likes of **Proof of work** or **Proof of stake** algorithms.
+
+POET is designed to utilize the security and tamper proof features of modern processors with reference implementations utilizing **Intel’s trusted execution environment** (TEE) architecture on its modern CPUs. The fact that the execution of the validating program takes use of a TEE along with a **“lottery”** system that is implemented to choose the **validator** or **node** to fulfill the request makes the process of creating blocks on the Sawtooth architecture secure and resource efficient at the same time.
+
+The POET algorithm basically elects a validator randomly based on a stochastic process. The probability of a particular node being selected depends on a host of pointers one of which depends on the amount of computing resources the said node has contributed to the ledger so far. The chosen validator then proceeds to timestamp the said block of data and shares it with the permissioned nodes in the network so that there remains a reliable record of the blockchains immutability. This method of electing the “validator” node was developed by **Intel** and so far, has been shown to exhibit zero bias and or error in executing its function.
+
+### Distinction 2: A fully separated level of abstraction between the application level and core system
+
+As mentioned, the Sawtooth platform takes modularity to the next level. Here in the reference implementation that is shared by the [**Hyperledger project**][5] foundation, the core system that enables users to create a distributed ledger, and, the application run-time environment (the virtual environment where applications developed to run on the blockchain otherwise known as [**smart contracts**][6] or **chaincode** ) are separated by a full level of abstraction. This essentially means that developers can separately code applications in any programming language of their choice instead of having to conform to and follow platform specific languages. The Sawtooth platform provides support for the following contract languages out of the box: **Java** , **Python** , **C++** , **Go** , **JavaScript** and **Rust**. This distinction between the core system and application levels are obtained by defining a custom transaction family for each application that is developed on the platform.
+
+A transaction family contains the following:
+
+ * **A transaction processor** : basically, your applications logic or business logic.
+ * **Data model** : a system that defines and handles data storage and processing at the system level.
+ * **Client-side handler** to handle the end user side of your application.
+
+
+
+Multiple low-level transaction families such as this may be defined in a permissioned blockchain and used in a modular fashion throughout the network. For instance, if a consortium of banks chose to implement it, they could come together and define common functionalities or rules for their applications and then plug and play the transaction families they need in their respective systems without having to develop everything on their own.
+
+### Distinction 3: SETH
+
+It is without doubt that a blockchain future would for sure have Ethereum as one of the key players. People at the Hyperledger foundation know this well. The **Hyperledger Burrow project** is in fact meant to address the existence of entities working on multiple platforms by providing a way for developers to use Ethereum blockchain specifications to build custom distributed applications using the **EVM** (Ethereum virtual machine).
+
+Basically speaking, Burrow lets you customize and deploy Ethereum based [**DApps**][7] (written in **solidity** ) in non-public blockchains (the kind developed for use at the Hyperledger foundation). The Burrow and Sawtooth projects teamed up and created **SETH**. **Sawtooth-Ethereum Integration project** (SETH) is meant to add Ethereum (solidity) smart contract functionality and compatibility to Sawtooth based distributed ledger networks. A much-less known agenda to SETH is the fact that applications (DApps) and smart contracts written for EVM can now be easily ported to Sawtooth.
+
+### Distinction 4: ACID principle and ability to batch process
+
+A rather path breaking feature of Sawtooth is its ability to batch transactions together and then package them into a block. The blocks and transactions will still be subject to the **ACID** principle ( **A** tomicity, **C** onsistency, **I** solation and **D** urability). The implication of these two facts are highlighted using an example as follows.
+
+Let’s say you have **6 transactions** to be packaged into **two blocks (4+2)**. Block A has 4 transactions which individually needs to succeed in order for the next block of 2 transactions to be timestamped and validated. Assuming they succeed, the next block of 2 transactions is processed and assuming even they are successful the entire package of 6 transactions are deemed successful and the overall business logic is deemed successful. For instance, assume you’re selling a car. Different transactions at the ends of the buyer (block A) and the seller (block B) will need be completed in order for the trade to be deemed valid. Ownership is transferred only if both the sides are successful in carrying out their individual transactions.
+
+Such a feature will improve accountability on individual ends by separating responsibilities and improve the recognizability of faults and errors by the same principle. The ACID principle is implemented by coding for a custom transaction processor and defining a transaction family that will store data in the said block structure.
+
+### Distinction 5: Parallel transaction execution
+
+Blockchain platforms usually follow a serial **first come first serve route** to executing transactions and follow a queueing system for the same. Sawtooth provides support for both **serial** and **parallel execution** of transactions. Parallel transaction processing offers significant performance gains for even faster transactions by reducing overall transaction latencies. More faster transactions will be processed along with slower and bigger transactions at the same time on the platform instead of transactions of all types to be kept waiting.
+
+The methodology followed to implement the parallel transaction paradigm efficiently takes care of the double spending problems and errors due to multiple changes being made to the same state by defining a custom scheduler for the network which can identity processes and their predecessors.
+
+Real world use case: Supply Chain Management using Sawtooth applied with IoT
+
+The Sawtooth **official website** lists seafood traceability as an example use case for the Sawtooth platform. The basic template is applicable for almost all supply chain related use cases.
+
+![][8]
+
+Figure 1 From the Hyperledger Sawtooth Official Website
+
+Traditional supply chain management solutions in this space work majorly through manual record keeping which leaves room for massive frauds, errors, and significant quality control issues. IoT has been cited as a solution to overcome such issues with supply chains in day to day use. Inexpensive GPS enabled RFID-tags can be attached to fresh catch or produce as the case may be and can be scanned for updating at the individual processing centres automatically. Buyers or middle men can verify and or track the information easily using a client on their mobile device to know the route their dinner has taken before arriving on their plates.
+
+While tracking seafood seems to be a first world problem in countries like India, the change an IoT enabled system can bring to public delivery systems in developing countries can be a welcome change. The application is available for demo at this **[link][9]** and users are encouraged to fiddle with it and adopt it to suit their needs.
+
+**Reference:**
+
+ * [**The Official Hyperledger Sawtooth Docs**][10]
+
+
+
+--------------------------------------------------------------------------------
+
+via: https://www.ostechnix.com/blockchain-2-0-introduction-to-hyperledger-sawtooth/
+
+作者:[editor][a]
+选题:[lujun9972][b]
+译者:[译者ID](https://github.com/译者ID)
+校对:[校对者ID](https://github.com/校对者ID)
+
+本文由 [LCTT](https://github.com/LCTT/TranslateProject) 原创编译,[Linux中国](https://linux.cn/) 荣誉推出
+
+[a]: https://www.ostechnix.com/author/editor/
+[b]: https://github.com/lujun9972
+[1]: https://www.ostechnix.com/wp-content/uploads/2019/05/Hyperledger-Sawtooth-720x340.png
+[2]: https://www.ostechnix.com/blockchain-2-0-introduction-to-hyperledger-fabric/
+[3]: https://www.ostechnix.com/blockchain-2-0-an-introduction/
+[4]: https://www.ostechnix.com/blockchain-2-0-what-is-ethereum/
+[5]: https://www.ostechnix.com/blockchain-2-0-an-introduction-to-hyperledger-project-hlp/
+[6]: https://www.ostechnix.com/blockchain-2-0-explaining-smart-contracts-and-its-types/
+[7]: https://www.ostechnix.com/blockchain-2-0-explaining-distributed-computing-and-distributed-applications/
+[8]: http://www.ostechnix.com/wp-content/uploads/2019/05/Sawtooth.png
+[9]: https://sawtooth.hyperledger.org/examples/seafood.html
+[10]: https://sawtooth.hyperledger.org/docs/core/releases/1.0/contents.html
diff --git a/sources/tech/20190527 How To Enable Or Disable SSH Access For A Particular User Or Group In Linux.md b/sources/tech/20190527 How To Enable Or Disable SSH Access For A Particular User Or Group In Linux.md
new file mode 100644
index 0000000000..a717d05ed8
--- /dev/null
+++ b/sources/tech/20190527 How To Enable Or Disable SSH Access For A Particular User Or Group In Linux.md
@@ -0,0 +1,300 @@
+[#]: collector: (lujun9972)
+[#]: translator: ( )
+[#]: reviewer: ( )
+[#]: publisher: ( )
+[#]: url: ( )
+[#]: subject: (How To Enable Or Disable SSH Access For A Particular User Or Group In Linux?)
+[#]: via: (https://www.2daygeek.com/allow-deny-enable-disable-ssh-access-user-group-in-linux/)
+[#]: author: (2daygeek http://www.2daygeek.com/author/2daygeek/)
+
+How To Enable Or Disable SSH Access For A Particular User Or Group In Linux?
+======
+
+As per your organization standard policy, you may need to allow only the list of users that are allowed to access the Linux system.
+
+Or you may need to allow only few groups, which are allowed to access the Linux system.
+
+How to achieve this? What is the best way? How to achieve this in a simple way?
+
+Yes, there are many ways are available to perform this.
+
+However, we need to go with simple and easy method.
+
+If so, it can be done by making the necessary changes in `/etc/ssh/sshd_config` file.
+
+In this article we will show you, how to perform this in details.
+
+Why are we doing this? due to security reason. Navigate to the following URL to know more about **[openSSH][1]** usage.
+
+### What Is SSH?
+
+openssh stands for OpenBSD Secure Shell. Secure Shell (ssh) is a free open source networking tool which allow us to access remote system over an unsecured network using Secure Shell (SSH) protocol.
+
+It’s a client-server architecture. It handles user authentication, encryption, transferring files between computers and tunneling.
+
+These can be accomplished via traditional tools such as telnet or rcp, these are insecure and use transfer password in cleartext format while performing any action.
+
+### How To Allow A User To Access SSH In Linux?
+
+We can allow/enable the ssh access for a particular user or list of the users using the following method.
+
+If you would like to allow more than one user then you have to add the users with space in the same line.
+
+To do so, just append the following value into `/etc/ssh/sshd_config` file. In this example, we are going to allow ssh access for `user3`.
+
+```
+# echo "AllowUsers user3" >> /etc/ssh/sshd_config
+```
+
+You can double check this by running the following command.
+
+```
+# cat /etc/ssh/sshd_config | grep -i allowusers
+AllowUsers user3
+```
+
+That’s it. Just bounce the ssh service and see the magic.
+
+```
+# systemctl restart sshd
+
+# service restart sshd
+```
+
+Simple open a new terminal or session and try to access the Linux system with different user. Yes, `user2` isn’t allowed for SSH login and will be getting an error message as shown below.
+
+```
+# ssh [email protected]
+[email protected]'s password:
+Permission denied, please try again.
+```
+
+Output:
+
+```
+Mar 29 02:00:35 CentOS7 sshd[4900]: User user2 from 192.168.1.6 not allowed because not listed in AllowUsers
+Mar 29 02:00:35 CentOS7 sshd[4900]: input_userauth_request: invalid user user2 [preauth]
+Mar 29 02:00:40 CentOS7 unix_chkpwd[4902]: password check failed for user (user2)
+Mar 29 02:00:40 CentOS7 sshd[4900]: pam_unix(sshd:auth): authentication failure; logname= uid=0 euid=0 tty=ssh ruser= rhost=192.168.1.6 user=user2
+Mar 29 02:00:43 CentOS7 sshd[4900]: Failed password for invalid user user2 from 192.168.1.6 port 42568 ssh2
+```
+
+At the same time `user3` is allowed to login into the system because it’s in allowed users list.
+
+```
+# ssh [email protected]
+[email protected]'s password:
+[[email protected] ~]$
+```
+
+Output:
+
+```
+Mar 29 02:01:13 CentOS7 sshd[4939]: Accepted password for user3 from 192.168.1.6 port 42590 ssh2
+Mar 29 02:01:13 CentOS7 sshd[4939]: pam_unix(sshd:session): session opened for user user3 by (uid=0)
+```
+
+### How To Deny Users To Access SSH In Linux?
+
+We can deny/disable the ssh access for a particular user or list of the users using the following method.
+
+If you would like to disable more than one user then you have to add the users with space in the same line.
+
+To do so, just append the following value into `/etc/ssh/sshd_config` file. In this example, we are going to disable ssh access for `user1`.
+
+```
+# echo "DenyUsers user1" >> /etc/ssh/sshd_config
+```
+
+You can double check this by running the following command.
+
+```
+# cat /etc/ssh/sshd_config | grep -i denyusers
+DenyUsers user1
+```
+
+That’s it. Just bounce the ssh service and see the magic.
+
+```
+# systemctl restart sshd
+
+# service restart sshd
+```
+
+Simple open a new terminal or session and try to access the Linux system with Deny user. Yes, `user1` is in denyusers list. So, you will be getting an error message as shown below when you are try to login.
+
+```
+# ssh [email protected]
+[email protected]'s password:
+Permission denied, please try again.
+```
+
+Output:
+
+```
+Mar 29 01:53:42 CentOS7 sshd[4753]: User user1 from 192.168.1.6 not allowed because listed in DenyUsers
+Mar 29 01:53:42 CentOS7 sshd[4753]: input_userauth_request: invalid user user1 [preauth]
+Mar 29 01:53:46 CentOS7 unix_chkpwd[4755]: password check failed for user (user1)
+Mar 29 01:53:46 CentOS7 sshd[4753]: pam_unix(sshd:auth): authentication failure; logname= uid=0 euid=0 tty=ssh ruser= rhost=192.168.1.6 user=user1
+Mar 29 01:53:48 CentOS7 sshd[4753]: Failed password for invalid user user1 from 192.168.1.6 port 42522 ssh2
+```
+
+### How To Allow Groups To Access SSH In Linux?
+
+We can allow/enable the ssh access for a particular group or groups using the following method.
+
+If you would like to allow more than one group then you have to add the groups with space in the same line.
+
+To do so, just append the following value into `/etc/ssh/sshd_config` file. In this example, we are going to disable ssh access for `2g-admin` group.
+
+```
+# echo "AllowGroups 2g-admin" >> /etc/ssh/sshd_config
+```
+
+You can double check this by running the following command.
+
+```
+# cat /etc/ssh/sshd_config | grep -i allowgroups
+AllowGroups 2g-admin
+```
+
+Run the following command to know the list of the users are belongs to this group.
+
+```
+# getent group 2g-admin
+2g-admin:x:1005:user1,user2,user3
+```
+
+That’s it. Just bounce the ssh service and see the magic.
+
+```
+# systemctl restart sshd
+
+# service restart sshd
+```
+
+Yes, `user3` is allowed to login into the system because user3 is belongs to `2g-admin` group.
+
+```
+# ssh [email protected]
+[email protected]'s password:
+[[email protected] ~]$
+```
+
+Output:
+
+```
+Mar 29 02:10:21 CentOS7 sshd[5165]: Accepted password for user1 from 192.168.1.6 port 42640 ssh2
+Mar 29 02:10:22 CentOS7 sshd[5165]: pam_unix(sshd:session): session opened for user user1 by (uid=0)
+```
+
+Yes, `user2` is allowed to login into the system because user2 is belongs to `2g-admin` group.
+
+```
+# ssh [email protected]
+[email protected]'s password:
+[[email protected] ~]$
+```
+
+Output:
+
+```
+Mar 29 02:10:38 CentOS7 sshd[5225]: Accepted password for user2 from 192.168.1.6 port 42642 ssh2
+Mar 29 02:10:38 CentOS7 sshd[5225]: pam_unix(sshd:session): session opened for user user2 by (uid=0)
+```
+
+When you are try to login into the system with other users which are not part of this group then you will be getting an error message as shown below.
+
+```
+# ssh [email protected]
+[email protected]'s password:
+Permission denied, please try again.
+```
+
+Output:
+
+```
+Mar 29 02:12:36 CentOS7 sshd[5306]: User ladmin from 192.168.1.6 not allowed because none of user's groups are listed in AllowGroups
+Mar 29 02:12:36 CentOS7 sshd[5306]: input_userauth_request: invalid user ladmin [preauth]
+Mar 29 02:12:56 CentOS7 unix_chkpwd[5310]: password check failed for user (ladmin)
+Mar 29 02:12:56 CentOS7 sshd[5306]: pam_unix(sshd:auth): authentication failure; logname= uid=0 euid=0 tty=ssh ruser= rhost=192.168.1.6 user=ladmin
+Mar 29 02:12:58 CentOS7 sshd[5306]: Failed password for invalid user ladmin from 192.168.1.6 port 42674 ssh2
+```
+
+### How To Deny Group To Access SSH In Linux?
+
+We can deny/disable the ssh access for a particular group or groups using the following method.
+
+If you would like to disable more than one group then you need to add the group with space in the same line.
+
+To do so, just append the following value into `/etc/ssh/sshd_config` file.
+
+```
+# echo "DenyGroups 2g-admin" >> /etc/ssh/sshd_config
+```
+
+You can double check this by running the following command.
+
+```
+# # cat /etc/ssh/sshd_config | grep -i denygroups
+DenyGroups 2g-admin
+
+# getent group 2g-admin
+2g-admin:x:1005:user1,user2,user3
+```
+
+That’s it. Just bounce the ssh service and see the magic.
+
+```
+# systemctl restart sshd
+
+# service restart sshd
+```
+
+Yes `user3` isn’t allowed to login into the system because it’s not part of `2g-admin` group. It’s in Denygroups.
+
+```
+# ssh [email protected]
+[email protected]'s password:
+Permission denied, please try again.
+```
+
+Output:
+
+```
+Mar 29 02:17:32 CentOS7 sshd[5400]: User user1 from 192.168.1.6 not allowed because a group is listed in DenyGroups
+Mar 29 02:17:32 CentOS7 sshd[5400]: input_userauth_request: invalid user user1 [preauth]
+Mar 29 02:17:38 CentOS7 unix_chkpwd[5402]: password check failed for user (user1)
+Mar 29 02:17:38 CentOS7 sshd[5400]: pam_unix(sshd:auth): authentication failure; logname= uid=0 euid=0 tty=ssh ruser= rhost=192.168.1.6 user=user1
+Mar 29 02:17:41 CentOS7 sshd[5400]: Failed password for invalid user user1 from 192.168.1.6 port 42710 ssh2
+```
+
+Anyone can login into the system except `2g-admin` group. Hence, `ladmin` user is allowed to login into the system.
+
+```
+# ssh [email protected]
+[email protected]'s password:
+[[email protected] ~]$
+```
+
+Output:
+
+```
+Mar 29 02:19:13 CentOS7 sshd[5432]: Accepted password for ladmin from 192.168.1.6 port 42716 ssh2
+Mar 29 02:19:13 CentOS7 sshd[5432]: pam_unix(sshd:session): session opened for user ladmin by (uid=0)
+```
+
+--------------------------------------------------------------------------------
+
+via: https://www.2daygeek.com/allow-deny-enable-disable-ssh-access-user-group-in-linux/
+
+作者:[2daygeek][a]
+选题:[lujun9972][b]
+译者:[译者ID](https://github.com/译者ID)
+校对:[校对者ID](https://github.com/校对者ID)
+
+本文由 [LCTT](https://github.com/LCTT/TranslateProject) 原创编译,[Linux中国](https://linux.cn/) 荣誉推出
+
+[a]: http://www.2daygeek.com/author/2daygeek/
+[b]: https://github.com/lujun9972
+[1]: https://www.2daygeek.com/category/ssh-tutorials/
diff --git a/sources/tech/20190528 A Quick Look at Elvish Shell.md b/sources/tech/20190528 A Quick Look at Elvish Shell.md
new file mode 100644
index 0000000000..778965d442
--- /dev/null
+++ b/sources/tech/20190528 A Quick Look at Elvish Shell.md
@@ -0,0 +1,106 @@
+[#]: collector: (lujun9972)
+[#]: translator: ( )
+[#]: reviewer: ( )
+[#]: publisher: ( )
+[#]: url: ( )
+[#]: subject: (A Quick Look at Elvish Shell)
+[#]: via: (https://itsfoss.com/elvish-shell/)
+[#]: author: (John Paul https://itsfoss.com/author/john/)
+
+A Quick Look at Elvish Shell
+======
+
+Everyone who comes to this site has some knowledge (no matter how slight) of the Bash shell that comes default of so many systems. There have been several attempts to create shells that solve some of the shortcomings of Bash that have appeared over the years. One such shell is Elvish, which we will look at today.
+
+### What is Elvish Shell?
+
+![Pipelines In Elvish][1]
+
+[Elvish][2] is more than just a shell. It is [also][3] “an expressive programming language”. It has a number of interesting features including:
+
+ * Written in Go
+ * Built-in file manager, inspired by the [Ranger file manager][4] (`Ctrl + N`)
+ * Searchable command history (`Ctrl + R`)
+ * History of directories visited (`Ctrl + L`)
+ * Powerful pipelines that support structured data, such as lists, maps, and functions
+ * Includes a “standard set of control structures: conditional control with `if`, loops with `for` and `while`, and exception handling with `try`“
+ * Support for [third-party modules via a package manager to extend Elvish][5]
+ * Licensed under the BSD 2-Clause license
+
+
+
+“Why is it named Elvish?” I hear you shout. Well, according to [their website][6], they chose their current name because:
+
+> In roguelikes, items made by the elves have a reputation of high quality. These are usually called elven items, but “elvish” was chosen because it ends with “sh”, a long tradition of Unix shells. It also rhymes with fish, one of the shells that influenced the philosophy of Elvish.
+
+### How to Install Elvish Shell
+
+Elvish is available in several mainstream distributions.
+
+Note that the software is very young. The most recent version is 0.12. According to the project’s [GitHub page][3]: “Despite its pre-1.0 status, it is already suitable for most daily interactive use.”
+
+![Elvish Control Structures][7]
+
+#### Debian and Ubuntu
+
+Elvish packages were introduced into Debian Buster and Ubuntu 17.10. Unfortunately, those packages are out of date and you will need to use a [PPA][8] to install the latest version. You will need to use the following commands:
+
+```
+sudo add-apt-repository ppa:zhsj/elvish
+sudo apt update
+sudo apt install elvish
+```
+
+#### Fedora
+
+Elvish is not available in the main Fedora repos. You will need to add the [FZUG Repository][9] to install Evlish. To do so, you will need to use these commands:
+
+```
+sudo dnf config-manager --add-repo=http://repo.fdzh.org/FZUG/FZUG.repol
+sudo dnf install elvish
+```
+
+#### Arch
+
+Elvish is available in the [Arch User Repository][10].
+
+I believe you know [how to change shell in Linux][11] so after installing you can switch to Elvish to use it.
+
+### Final Thoughts on Elvish Shell
+
+Personally, I have no reason to install Elvish on any of my systems. I can get most of its features by installing a couple of small command line programs or using already installed programs.
+
+For example, the search past commands feature already exists in Bash and it works pretty well. If you want to improve your ability to search past commands, I would recommend installing [fzf][12] instead. Fzf uses fuzzy search, so you don’t need to remember the exact command you are looking for. Fzf also allows you to preview and open files.
+
+I do think that the fact that Elvish is also a programming language is neat, but I’ll stick with Bash shell scripting until Elvish matures a little more.
+
+Have you every used Elvish? Do you think it would be worthwhile to install Elvish? What is your favorite Bash replacement? Please let us know in the comments below.
+
+If you found this article interesting, please take a minute to share it on social media, Hacker News or [Reddit][13].
+
+--------------------------------------------------------------------------------
+
+via: https://itsfoss.com/elvish-shell/
+
+作者:[John Paul][a]
+选题:[lujun9972][b]
+译者:[译者ID](https://github.com/译者ID)
+校对:[校对者ID](https://github.com/校对者ID)
+
+本文由 [LCTT](https://github.com/LCTT/TranslateProject) 原创编译,[Linux中国](https://linux.cn/) 荣誉推出
+
+[a]: https://itsfoss.com/author/john/
+[b]: https://github.com/lujun9972
+[1]: https://i2.wp.com/itsfoss.com/wp-content/uploads/2019/05/pipelines-in-elvish.png?fit=800%2C421&ssl=1
+[2]: https://elv.sh/
+[3]: https://github.com/elves/elvish
+[4]: https://ranger.github.io/
+[5]: https://github.com/elves/awesome-elvish
+[6]: https://elv.sh/ref/name.html
+[7]: https://i0.wp.com/itsfoss.com/wp-content/uploads/2019/05/Elvish-control-structures.png?fit=800%2C425&ssl=1
+[8]: https://launchpad.net/%7Ezhsj/+archive/ubuntu/elvish
+[9]: https://github.com/FZUG/repo/wiki/Add-FZUG-Repository
+[10]: https://aur.archlinux.org/packages/elvish/
+[11]: https://linuxhandbook.com/change-shell-linux/
+[12]: https://github.com/junegunn/fzf
+[13]: http://reddit.com/r/linuxusersgroup
diff --git a/sources/tech/20190529 Packit - packaging in Fedora with minimal effort.md b/sources/tech/20190529 Packit - packaging in Fedora with minimal effort.md
new file mode 100644
index 0000000000..ad431547da
--- /dev/null
+++ b/sources/tech/20190529 Packit - packaging in Fedora with minimal effort.md
@@ -0,0 +1,244 @@
+[#]: collector: (lujun9972)
+[#]: translator: ( )
+[#]: reviewer: ( )
+[#]: publisher: ( )
+[#]: url: ( )
+[#]: subject: (Packit – packaging in Fedora with minimal effort)
+[#]: via: (https://fedoramagazine.org/packit-packaging-in-fedora-with-minimal-effort/)
+[#]: author: (Petr Hracek https://fedoramagazine.org/author/phracek/)
+
+Packit – packaging in Fedora with minimal effort
+======
+
+![][1]
+
+### What is packit
+
+Packit ([https://packit.dev/)][2] is a CLI tool that helps you auto-maintain your upstream projects into the Fedora operating system. But what does it really mean?
+
+As a developer, you might want to update your package in Fedora. If you’ve done it in the past, you know it’s no easy task. If you haven’t let me reiterate: it’s no easy task.
+
+And this is exactly where packit can help: once you have your package in Fedora, you can maintain your SPEC file upstream and, with just one additional configuration file, packit will help you update your package in Fedora when you update your source code upstream.
+
+Furthermore, packit can synchronize downstream changes to a SPEC file back into the upstream repository. This could be useful if the SPEC file of your package is changed in Fedora repositories and you would like to synchronize it into your upstream project.
+
+Packit also provides a way to build an SRPM package based on an upstream repository checkout, which can be used for building RPM packages in COPR.
+
+Last but not least, packit provides a status command. This command provides information about upstream and downstream repositories, like pull requests, release and more others.
+
+Packit provides also another two commands: _build_ and _create-update_.
+
+The command _packit build_ performs a production build of your project in Fedora build system – koji. You can Fedora version you want to build against using an option _–dist-git-branch_. The command _packit create-updates_ creates a Bodhi update for the specific branch using the option — _dist-git-branch_.
+
+### Installation
+
+You can install packit on Fedora using dnf:
+
+```
+sudo dnf install -y packit
+```
+
+### Configuration
+
+For demonstration use case, I have selected the upstream repository of **colin** ([https://github.com/user-cont/colin)][3]. Colin is a tool to check generic rules and best-practices for containers, dockerfiles, and container images.
+
+First of all, clone **colin** git repository:
+
+```
+$ git clone https://github.com/user-cont/colin.git
+$ cd colin
+```
+
+Packit expects to run in the root of your git repository.
+
+Packit ([https://github.com/packit-service/packit/)][4] needs information about your project, which has to be stored in the upstream repository in the _.packit.yaml_ file ().
+
+See colin’s packit configuration file:
+
+```
+$ cat .packit.yaml
+specfile_path: colin.spec
+synced_files:
+ -.packit.yaml
+ - colin.spec
+upstream_project_name: colin
+downstream_package_name: colin
+```
+
+What do the values mean?
+
+ * _specfile_path_ – a relative path to a spec file within the upstream repository (mandatory)
+ * _synced_files_ – a list of relative paths to files in the upstream repo which are meant to be copied to dist-git during an update
+ * _upstream_project_name_ – name of the upstream repository (e.g. in PyPI); this is used in %prep section
+ * _downstream_package_name_ – name of the package in Fedora (mandatory)
+
+
+
+For more information see the packit configuration documentation ()
+
+### What can packit do?
+
+Prerequisite for using packit is that you are in a working directory of a git checkout of your upstream project.
+
+Before running any packit command, you need to do several actions. These actions are mandatory for filing a PR into the upstream or downstream repositories and to have access into the Fedora dist-git repositories.
+
+Export GitHub token taken from :
+
+```
+$ export GITHUB_TOKEN=
+```
+
+Obtain your Kerberos ticket needed for Fedora Account System (FAS) :
+
+```
+$ kinit @FEDORAPROJECT.ORG
+```
+
+Export your Pagure API keys taken from :
+
+```
+$ export PAGURE_USER_TOKEN=
+```
+
+Packit also needs a fork token to create a pull request. The token is taken from
+
+Do it by running:
+
+```
+$ export PAGURE_FORK_TOKEN=
+```
+
+Or store these tokens in the **~/.config/packit.yaml** file:
+
+```
+$ cat ~/.config/packit.yaml
+
+github_token:
+pagure_user_token:
+pagure_fork_token:
+```
+
+#### Propose a new upstream release in Fedora
+
+The command for this first use case is called _**propose-update**_ (). The command creates a new pull request in Fedora dist-git repository using a selected or the latest upstream release.
+
+```
+$ packit propose-update
+
+INFO: Running 'anitya' versioneer
+Version in upstream registries is '0.3.1'.
+Version in spec file is '0.3.0'.
+WARNING Version in spec file is outdated
+Picking version of the latest release from the upstream registry.
+Checking out upstream version 0.3.1
+Using 'master' dist-git branch
+Copying /home/vagrant/colin/colin.spec to /tmp/tmptfwr123c/colin.spec.
+Archive colin-0.3.0.tar.gz found in lookaside cache (skipping upload).
+INFO: Downloading file from URL https://files.pythonhosted.org/packages/source/c/colin/colin-0.3.0.tar.gz
+100%[=============================>] 3.18M eta 00:00:00
+Downloaded archive: '/tmp/tmptfwr123c/colin-0.3.0.tar.gz'
+About to upload to lookaside cache
+won't be doing kinit, no credentials provided
+PR created: https://src.fedoraproject.org/rpms/colin/pull-request/14
+```
+
+Once the command finishes, you can see a PR in the Fedora Pagure instance which is based on the latest upstream release. Once you review it, it can be merged.
+
+![][5]
+
+#### Sync downstream changes back to the upstream repository
+
+Another use case is to sync downstream changes into the upstream project repository.
+
+The command for this purpose is called _**sync-from-downstream**_ (). Files synced into the upstream repository are mentioned in the _packit.yaml_ configuration file under the _synced_files_ value.
+
+```
+$ packit sync-from-downstream
+
+upstream active branch master
+using "master" dist-git branch
+Copying /tmp/tmplvxqtvbb/colin.spec to /home/vagrant/colin/colin.spec.
+Creating remote fork-ssh with URL git@github.com:phracek/colin.git.
+Pushing to remote fork-ssh using branch master-downstream-sync.
+PR created: https://github.com/user-cont/colin/pull/229
+```
+
+As soon as packit finishes, you can see the latest changes taken from the Fedora dist-git repository in the upstream repository. This can be useful, e.g. when Release Engineering performs mass-rebuilds and they update your SPEC file in the Fedora dist-git repository.
+
+![][6]
+
+#### Get the status of your upstream project
+
+If you are a developer, you may want to get all the information about the latest releases, tags, pull requests, etc. from the upstream and the downstream repository. Packit provides the _**status**_ command for this purpose.
+
+```
+$ packit status
+Downstream PRs:
+ ID Title URL
+---- -------------------------------- ---------------------------------------------------------
+ 14 Update to upstream release 0.3.1 https://src.fedoraproject.org//rpms/colin/pull-request/14
+ 12 Upstream pr: 226 https://src.fedoraproject.org//rpms/colin/pull-request/12
+ 11 Upstream pr: 226 https://src.fedoraproject.org//rpms/colin/pull-request/11
+ 8 Upstream pr: 226 https://src.fedoraproject.org//rpms/colin/pull-request/8
+
+Dist-git versions:
+f27: 0.2.0
+f28: 0.2.0
+f29: 0.2.0
+f30: 0.2.0
+master: 0.2.0
+
+GitHub upstream releases:
+0.3.1
+0.3.0
+0.2.1
+0.2.0
+0.1.0
+
+Latest builds:
+f27: colin-0.2.0-1.fc27
+f28: colin-0.3.1-1.fc28
+f29: colin-0.3.1-1.fc29
+f30: colin-0.3.1-2.fc30
+
+Latest bodhi updates:
+Update Karma status
+------------------ ------- --------
+colin-0.3.1-1.fc29 1 stable
+colin-0.3.1-1.fc28 1 stable
+colin-0.3.0-2.fc28 0 obsolete
+```
+
+#### Create an SRPM
+
+The last packit use case is to generate an SRPM package based on a git checkout of your upstream project. The packit command for SRPM generation is _**srpm**_.
+
+```
+$ packit srpm
+Version in spec file is '0.3.1.37.g00bb80e'.
+SRPM: /home/phracek/work/colin/colin-0.3.1.37.g00bb80e-1.fc29.src.rpm
+```
+
+### Packit as a service
+
+In the summer, the people behind packit would like to introduce packit as a service (). In this case, the packit GitHub application will be installed into the upstream repository and packit will perform all the actions automatically, based on the events it receives from GitHub or fedmsg.
+
+--------------------------------------------------------------------------------
+
+via: https://fedoramagazine.org/packit-packaging-in-fedora-with-minimal-effort/
+
+作者:[Petr Hracek][a]
+选题:[lujun9972][b]
+译者:[译者ID](https://github.com/译者ID)
+校对:[校对者ID](https://github.com/校对者ID)
+
+本文由 [LCTT](https://github.com/LCTT/TranslateProject) 原创编译,[Linux中国](https://linux.cn/) 荣誉推出
+
+[a]: https://fedoramagazine.org/author/phracek/
+[b]: https://github.com/lujun9972
+[1]: https://fedoramagazine.org/wp-content/uploads/2019/05/packit3-816x345.png
+[2]: https://packit.dev/
+[3]: https://github.com/user-cont/colin
+[4]: https://github.com/packit-service/packit/
+[5]: https://fedoramagazine.org/wp-content/uploads/2019/05/colin_pr-1024x781.png
+[6]: https://fedoramagazine.org/wp-content/uploads/2019/05/colin_upstream_pr-1-1024x677.png
diff --git a/sources/tech/20190530 A short primer on assemblers, compilers, and interpreters.md b/sources/tech/20190530 A short primer on assemblers, compilers, and interpreters.md
new file mode 100644
index 0000000000..cb242f5e1f
--- /dev/null
+++ b/sources/tech/20190530 A short primer on assemblers, compilers, and interpreters.md
@@ -0,0 +1,145 @@
+[#]: collector: (lujun9972)
+[#]: translator: (chen-ni)
+[#]: reviewer: ( )
+[#]: publisher: ( )
+[#]: url: ( )
+[#]: subject: (A short primer on assemblers, compilers, and interpreters)
+[#]: via: (https://opensource.com/article/19/5/primer-assemblers-compilers-interpreters)
+[#]: author: (Erik O'Shaughnessy https://opensource.com/users/jnyjny/users/shawnhcorey/users/jnyjny/users/jnyjny)
+
+A short primer on assemblers, compilers, and interpreters
+======
+A gentle introduction to the historical evolution of programming
+practices.
+![keyboard with connected dots][1]
+
+In the early days of computing, hardware was expensive and programmers were cheap. In fact, programmers were so cheap they weren't even called "programmers" and were in fact usually mathematicians or electrical engineers. Early computers were used to solve complex mathematical problems quickly, so mathematicians were a natural fit for the job of "programming."
+
+### What is a program?
+
+First, a little background. Computers can't do anything by themselves, so they require programs to drive their behavior. Programs can be thought of as very detailed recipes that take an input and produce an output. The steps in the recipe are composed of instructions that operate on data. While that sounds complicated, you probably know how this statement works:
+
+
+```
+`1 + 2 = 3`
+```
+
+The plus sign is the "instruction" while the numbers 1 and 2 are the data. Mathematically, the equal sign indicates that both sides of an equation are "equivalent," however most computer languages use some variant of equals to mean "assignment." If a computer were executing that statement, it would store the results of the addition (the "3") somewhere in memory.
+
+Computers know how to do math with numbers and move data around the machine's memory hierarchy. I won't say too much about memory except that it generally comes in two different flavors: fast/small and slow/big. CPU registers are very fast, very small and act as scratch pads. Main memory is typically very big and not nearly as fast as register memory. CPUs shuffle the data they are working with from main memory to registers and back again while a program executes.
+
+### Assemblers
+
+Computers were very expensive and people were cheap. Programmers spent endless hours translating hand-written math into computer instructions that the computer could execute. The very first computers had terrible user interfaces, some only consisting of toggle switches on the front panel. The switches represented 1s and 0s in a single "word" of memory. The programmer would configure a word, indicate where to store it, and commit the word to memory. It was time-consuming and error-prone.
+
+![Programmers operate the ENIAC computer][2]
+
+_Programmers[Betty Jean Jennings][3] (left) and [Fran Bilas][4] (right) operate [ENIAC's][5] main control panel._
+
+Eventually, an [electrical engineer][6] decided his time wasn't cheap and wrote a program with input written as a "recipe" expressed in terms people could read that output a computer-readable version. This was the first "assembler" and it was very controversial. The people that owned the expensive machines didn't want to "waste" compute time on a task that people were already doing; albeit slowly and with errors. Over time, people came to appreciate the speed and accuracy of the assembler versus a hand-assembled program, and the amount of "real work" done with the computer increased.
+
+While assembler programs were a big step up from toggling bit patterns into the front panel of a machine, they were still pretty specialized. The addition example above might have looked something like this:
+
+
+```
+01 MOV R0, 1
+02 MOV R1, 2
+03 ADD R0, R1, R2
+04 MOV 64, R0
+05 STO R2, R0
+```
+
+Each line is a computer instruction, beginning with a shorthand name of the instruction followed by the data the instruction works on. This little program will first "move" the value 1 into a register called R0, then 2 into register R1. Line 03 adds the contents of registers R0 and R1 and stores the resulting value into register R2. Finally, lines 04 and 05 identify where the result should be stored in main memory (address 64). Managing where data is stored in memory is one of the most time-consuming and error-prone parts of writing computer programs.
+
+### Compilers
+
+Assembly was much better than writing computer instructions by hand; however, early programmers yearned to write programs like they were accustomed to writing mathematical formulae. This drove the development of higher-level compiled languages, some of which are historical footnotes and others are still in use today. [ALGO][7] is one such footnote, while real problems continue to be solved today with languages like [Fortran][8] and [C][9].
+
+![Genealogy tree of ALGO and Fortran][10]
+
+Genealogy tree of ALGO and Fortran programming languages
+
+The introduction of these "high-level" languages allowed programmers to write their programs in simpler terms. In the C language, our addition assembly program would be written:
+
+
+```
+int x;
+x = 1 + 2;
+```
+
+The first statement describes a piece of memory the program will use. In this case, the memory should be the size of an integer and its name is **x** The second statement is the addition, although written "backward." A C programmer would read that as "X is assigned the result of one plus two." Notice the programmer doesn't need to say where to put **x** in memory, as the compiler takes care of that.
+
+A new type of program called a "compiler" would turn the program written in a high-level language into an assembly language version and then run it through the assembler to produce a machine-readable version of the program. This composition of programs is often called a "toolchain," in that one program's output is sent directly to another program's input.
+
+The huge advantage of compiled languages over assembly language programs was porting from one computer model or brand to another. In the early days of computing, there was an explosion of different types of computing hardware from companies like IBM, Digital Equipment Corporation, Texas Instruments, UNIVAC, Hewlett Packard, and others. None of these computers shared much in common besides needing to be plugged into an electrical power supply. Memory and CPU architectures differed wildly, and it often took man-years to translate programs from one computer to another.
+
+With high-level languages, the compiler toolchain only had to be ported to the new platform. Once the compiler was available, high-level language programs could be recompiled for a new computer with little or no modification. Compilation of high-level languages was truly revolutionary.
+
+![IBM PC XT][11]
+
+IBM PC XT released in 1983, is an early example of the decreasing cost of hardware.
+
+Life became very good for programmers. It was much easier to express the problems they wanted to solve using high-level languages. The cost of computer hardware was falling dramatically due to advances in semiconductors and the invention of integrated chips. Computers were getting faster and more capable, as well as much less expensive. At some point, possibly in the late '80s, there was an inversion and programmers became more expensive than the hardware they used.
+
+### Interpreters
+
+Over time, a new programming model rose where a special program called an "interpreter" would read a program and turn it into computer instructions to be executed immediately. The interpreter takes the program as input and interprets it into an intermediate form, much like a compiler. Unlike a compiler, the interpreter then executes the intermediate form of the program. This happens every time an interpreted program runs, whereas a compiled program is compiled just one time and the computer executes the machine instructions "as written."
+
+As a side note, when people say "interpreted programs are slow," this is the main source of the perceived lack of performance. Modern computers are so amazingly capable that most people can't tell the difference between compiled and interpreted programs.
+
+Interpreted programs, sometimes called "scripts," are even easier to port to different hardware platforms. Because the script doesn't contain any machine-specific instructions, a single version of a program can run on many different computers without changes. The catch, of course, is the interpreter must be ported to the new machine to make that possible.
+
+One example of a very popular interpreted language is [perl][12]. A complete perl expression of our addition problem would be:
+
+
+```
+`$x = 1 + 2`
+```
+
+While it looks and acts much like the C version, it lacks the variable initialization statement. There are other differences (which are beyond the scope of this article), but you can see that we can write a computer program that is very close to how a mathematician would write it by hand with pencil and paper.
+
+### Virtual Machines
+
+The latest craze in programming models is the virtual machine, often abbreviated as VM. There are two flavors of virtual machine; system virtual machines and process virtual machines. Both types of VMs provide a level of abstraction from the "real" computing hardware, though they have different scopes. A system virtual machine is software that offers a substitute for the physical hardware, while a process virtual machine is designed to execute a program in a system-independent manner. So in this case, a process virtual machine (virtual machine from here on) is similar in scope to an interpreter in that a program is first compiled into an intermediated form before the virtual machine executes it.
+
+The main difference between an interpreter and a virtual machine is the virtual machine implements an idealized CPU accessed through its virtual instruction set. This abstraction makes it possible to write front-end language tools that compile programs written in different languages and target the virtual machine. Probably the most popular and well known virtual machine is the Java Virtual Machine (JVM). The JVM was initially only for the Java programming language back in the 1990s, but it now hosts [many][13] popular computer languages: Scala, Jython, JRuby, Clojure, and Kotlin to list just a few. There are other examples that may not be common knowledge. I only recently learned that my favorite language, [Python][14], is not an interpreted language, but a [language hosted on a virtual machine][15]!
+
+Virtual machines continue the historical trend of reducing the amount of platform-specific knowledge a programmer needs to express their problem in a language that supports their domain-specific needs.
+
+### That's a wrap
+
+I hope you enjoy this primer on some of the less visible parts of software. Are there other topics you want me to dive into next? Let me know in the comments.
+
+* * *
+
+_This article was originally published on[PyBites][16] and is reprinted with permission._
+
+--------------------------------------------------------------------------------
+
+via: https://opensource.com/article/19/5/primer-assemblers-compilers-interpreters
+
+作者:[Erik O'Shaughnessy][a]
+选题:[lujun9972][b]
+译者:[译者ID](https://github.com/译者ID)
+校对:[校对者ID](https://github.com/校对者ID)
+
+本文由 [LCTT](https://github.com/LCTT/TranslateProject) 原创编译,[Linux中国](https://linux.cn/) 荣誉推出
+
+[a]: https://opensource.com/users/jnyjny/users/shawnhcorey/users/jnyjny/users/jnyjny
+[b]: https://github.com/lujun9972
+[1]: https://opensource.com/sites/default/files/styles/image-full-size/public/lead-images/programming_keyboard_coding.png?itok=E0Vvam7A (keyboard with connected dots)
+[2]: https://opensource.com/sites/default/files/uploads/two_women_operating_eniac.gif (Programmers operate the ENIAC computer)
+[3]: https://en.wikipedia.org/wiki/Jean_Bartik (Jean Bartik)
+[4]: https://en.wikipedia.org/wiki/Frances_Spence (Frances Spence)
+[5]: https://en.wikipedia.org/wiki/ENIAC
+[6]: https://en.wikipedia.org/wiki/Nathaniel_Rochester_%28computer_scientist%29
+[7]: https://en.wikipedia.org/wiki/ALGO
+[8]: https://en.wikipedia.org/wiki/Fortran
+[9]: https://en.wikipedia.org/wiki/C_(programming_language)
+[10]: https://opensource.com/sites/default/files/uploads/algolfortran_family-by-borkowski.png (Genealogy tree of ALGO and Fortran)
+[11]: https://opensource.com/sites/default/files/uploads/639px-ibm_px_xt_color.jpg (IBM PC XT)
+[12]: www.perl.org
+[13]: https://en.wikipedia.org/wiki/List_of_JVM_languages
+[14]: /resources/python
+[15]: https://opensource.com/article/18/4/introduction-python-bytecode
+[16]: https://pybit.es/python-interpreters.html
diff --git a/sources/tech/20190530 Creating a Source-to-Image build pipeline in OKD.md b/sources/tech/20190530 Creating a Source-to-Image build pipeline in OKD.md
new file mode 100644
index 0000000000..713d117cb3
--- /dev/null
+++ b/sources/tech/20190530 Creating a Source-to-Image build pipeline in OKD.md
@@ -0,0 +1,484 @@
+[#]: collector: (lujun9972)
+[#]: translator: ( )
+[#]: reviewer: ( )
+[#]: publisher: ( )
+[#]: url: ( )
+[#]: subject: (Creating a Source-to-Image build pipeline in OKD)
+[#]: via: (https://opensource.com/article/19/5/creating-source-image-build-pipeline-okd)
+[#]: author: (Chris Collins https://opensource.com/users/clcollins)
+
+Creating a Source-to-Image build pipeline in OKD
+======
+S2I is an ideal way to build and compile Go applications in a repeatable
+way, and it just gets better when paired with OKD BuildConfigs.
+![][1]
+
+In the first three articles in this series, we explored the general [requirements][2] of a Source-to-Image (S2I) system and [prepared][3] and [tested][4] an environment specifically for a Go (Golang) application. This S2I build is perfect for local development or maintaining a builder image with a code pipeline, but if you have access to an [OKD][5] or OpenShift cluster (or [Minishift][6]), you can set up the entire workflow using OKD BuildConfigs, not only to build and maintain the builder image but also to use the builder image to create the application image and subsequent runtime image automatically. This way, the images can be rebuilt automatically when downstream images change and can trigger OKD deploymentConfigs to redeploy applications running from these images.
+
+### Step 1: Build the builder image in OKD
+
+As in local S2I usage, the first step is to create the builder image to build the GoHelloWorld test application that we can reuse to compile other Go-based applications. This first build step will be a Docker build, just like before, that pulls the Dockerfile and S2I scripts from a Git repository to build the image. Therefore, those files must be committed and available in a public Git repo (or you can use the companion [GitHub repo][7] for this article).
+
+_Note:_ OKD BuildConfigs do not require that source Git repos are public. To use a private repo, you must set up deploy keys and link the keys to a builder service account. This is not difficult, but for simplicity's sake, this exercise will use a public repository.
+
+#### Create an image stream for the builder image
+
+The BuildConfig will create a builder image for us to compile the GoHelloWorld app, but first, we need a place to store the image. In OKD, that place is an image stream.
+
+An [image stream][8] and its tags are like a manifest or list of related images and image tags. It serves as an abstraction layer that allows you to reference an image, even if the image changes. Think of it as a collection of aliases that reference specific images and, as images are updated, automatically points to the new image version. The image stream is nothing except these aliases—just metadata about real images stored in a registry.
+
+An image stream can be created with the **oc create imagestream ** command, or it can be created from a YAML file with **oc create -f **. Either way, a brand-new image stream is a small placeholder object that is empty until it is populated with image references, either manually (who wants to do things manually?) or with a BuildConfig.
+
+Our golang-builder image stream looks like this:
+
+
+```
+# imageStream-golang-builder.yaml
+\---
+apiVersion: image.openshift.io/v1
+kind: ImageStream
+metadata:
+generation: 1
+name: golang-builder
+spec:
+lookupPolicy:
+local: false
+```
+
+Other than a name, and a (mostly) empty spec, there is nothing really there.
+
+_Note:_ The **lookupPolicy** has to do with allowing Kubernetes-native components to resolve image stream references since image streams are OKD-native and not a part of the Kubernetes core. This topic is out of scope for this article, but you can read more about how it works in OKD's documentation [Using Image Streams with Kubernetes Resources][9].
+
+Create an image stream for the builder image and its progeny.
+
+
+```
+$ oc create -f imageStream-golangBuilder.yaml
+
+# Check the ImageStream
+$ oc get imagestream golang-builder
+NAME DOCKER REPO TAGS UPDATED
+imagestream.image.openshift.io/golang-builder docker-registry.default.svc:5000/golang-builder/golang-builder
+```
+
+Note that the newly created image stream has no tags and has never been updated.
+
+#### Create a BuildConfig for the builder image
+
+In OKD, a [BuildConfig][10] describes how to build container images from a specific source and triggers for when they build. Don't be thrown off by the language—just as you might say you build and re-build the same image from a Dockerfile, but in reality, you have built multiple images, a BuildConfig builds and rebuilds the same image, but in reality, it creates multiple images. (And suddenly the reason for image streams becomes much clearer!)
+
+Our builder image BuildConfig describes how to build and re-build our builder image(s). The BuildConfig's core is made up of four important parts:
+
+ 1. Build source
+ 2. Build strategy
+ 3. Build output
+ 4. Build triggers
+
+
+
+The _build source_ (predictably) describes where the thing that runs the build comes from. The builds described by the golang-builder BuildConfig will use the Dockerfile and S2I scripts we created previously and, using the Git-type build source, clone a Git repository to get the files to do the builds.
+
+
+```
+source:
+type: Git
+git:
+ref: master
+uri:
+```
+
+The _build strategy_ describes what the build will do with the source files from the build source. The golang-builder BuildConfig mimics the **docker build** we used previously to build our local builder image by using the Docker-type build strategy.
+
+
+```
+strategy:
+type: Docker
+dockerStrategy: {}
+```
+
+The **dockerStrategy** build type tells OKD to build a Docker image from the Dockerfile contained in the source specified by the build source.
+
+The _build output_ tells the BuildConfig what to do with the resulting image. In this case, we specify the image stream we created above and a tag to give to the image. As with our local build, we're tagging it with **golang-builder:1.12** as a reference to the Go version inherited from the parent image.
+
+
+```
+output:
+to:
+kind: ImageStreamTag
+name: golang-builder:1.12
+```
+
+Finally, the BuildConfig defines a set of _build triggers_ —events that will cause the image to be rebuilt automatically. For this BuildConfig, a change to the BuildConfig configuration or an update to the upstream image (golang:1.12) will trigger a new build.
+
+
+```
+triggers:
+\- type: ConfigChange
+\- imageChange:
+type: ImageChange
+```
+
+Using the [builder image BuildConfig][11] from the GitHub repo as a reference (or just using that file), create a BuildConfig YAML file and use it to create the BuildConfig.
+
+
+```
+$ oc create -f buildConfig-golang-builder.yaml
+
+# Check the BuildConfig
+$ oc get bc golang-builder
+NAME TYPE FROM LATEST
+golang-builder Docker Git@master 1
+```
+
+Because the BuildConfig included the "ImageChange" trigger, it immediately kicks off a new build. You can check that the build was created with the **oc get builds** command.
+
+
+```
+# Check the Builds
+$ oc get builds
+NAME TYPE FROM STATUS STARTED DURATION
+golang-builder-1 Docker Git@8eff001 Complete About a minute ago 13s
+```
+
+While the build is running and after it has completed, you can view its logs with **oc logs -f ** and see the Docker build output as you would locally.
+
+
+```
+$ oc logs -f golang-builder-1-build
+Step 1/11 : FROM docker.io/golang:1.12
+\---> 7ced090ee82e
+Step 2/11 : LABEL maintainer "Chris Collins <[collins.christopher@gmail.com][12]>"
+\---> 7ad989b765e4
+Step 3/11 : ENV CGO_ENABLED 0 GOOS linux GOCACHE /tmp STI_SCRIPTS_PATH /usr/libexec/s2i SOURCE_DIR /go/src/app
+\---> 2cee2ce6757d
+
+<...>
+```
+
+If you did not include any build triggers (or did not have them in the right place), your build may not start automatically. You can manually kick off a new build with the **oc start-build** command.
+
+
+```
+$ oc start-build golang-builder
+
+# Or, if you want to automatically tail the build log
+$ oc start-build golang-builder --follow
+```
+
+When the build completes, the resulting image is tagged and pushed to the integrated image registry and the image stream is updated with the new image's information. Check the image stream with the **oc get imagestream** command to see that the new tag exists.
+
+
+```
+$ oc get imagestream golang-builder
+NAME DOCKER REPO TAGS UPDATED
+golang-builder docker-registry.default.svc:5000/golang-builder/golang-builder 1.12 33 seconds ago
+```
+
+### Step 2: Build the application image in OKD
+
+Now that we have a builder image for our Golang applications created and stored within OKD, we can use this builder image to compile all of our Go apps. First on the block is the example GoHelloWorld app from our [local build example][4]. GoHelloWorld is a simple Go app that just outputs **Hello World!** when it's run.
+
+Just as we did in the local example with the **s2i build** command, we can tell OKD to use our builder image and S2I to build the application image for GoHelloWorld, compiling the Go binary from the source code in the [GoHelloWorld GitHub repository][13]. This can be done with a BuildConfig with a **sourceStrategy** build.
+
+#### Create an image stream for the application image
+
+First things first, we need to create an image stream to manage the image created by the BuildConfig. The image stream is just like the golang-builder image stream, just with a different name. Create it with **oc create is** or using a YAML file from the [GitHub repo][7].
+
+
+```
+$ oc create -f imageStream-goHelloWorld-appimage.yaml
+imagestream.image.openshift.io/go-hello-world-appimage created
+```
+
+#### Create a BuildConfig for the application image
+
+Just as we did with the builder image BuildConfig, this BuildConfig will use the Git source option to clone our source code from the GoHelloWorld repository.
+
+
+```
+source:
+type: Git
+git:
+uri:
+```
+
+Instead of using a DockerStrategy build to create an image from a Dockerfile, this BuildConfig will use the sourceStrategy definition to build the image using S2I.
+
+
+```
+strategy:
+type: Source
+sourceStrategy:
+from:
+kind: ImageStreamTag
+name: golang-builder:1.12
+```
+
+Note the **from:** hash in sourceStrategy. This tells OKD to use the **golang-builder:1.12** image we created previously for the S2I build.
+
+The BuildConfig will output to the new **appimage** image stream we created, and we'll include config- and image-change triggers to kick off new builds automatically if anything updates.
+
+
+```
+output:
+to:
+kind: ImageStreamTag
+name: go-hello-world-appimage:1.0
+triggers:
+\- type: ConfigChange
+\- imageChange:
+type: ImageChange
+```
+
+Once again, create a BuildConfig or use the one from the GitHub repo.
+
+
+```
+`$ oc create -f buildConfig-goHelloWorld-appimage.yaml`
+```
+
+The new build shows up alongside the golang-builder build and, because image-change triggers are specified, the build starts immediately.
+
+
+```
+$ oc get builds
+NAME TYPE FROM STATUS STARTED DURATION
+golang-builder-1 Docker Git@8eff001 Complete 8 minutes ago 13s
+go-hello-world-appimage-1 Source Git@99699a6 Running 44 seconds ago
+```
+
+If you want to watch the build logs, use the **oc logs -f** command. Once the application image build completes, it is pushed to the image stream we specified, then the new image stream tag is created.
+
+
+```
+$ oc get is go-hello-world-appimage
+NAME DOCKER REPO TAGS UPDATED
+go-hello-world-appimage docker-registry.default.svc:5000/golang-builder/go-hello-world-appimage 1.0 10 minutes ago
+```
+
+Success! The GoHelloWorld app was cloned from source into a new image and compiled and tested using our S2I scripts. We can use the image as-is but, as with our local S2I builds, we can do better and create an image with just the new Go binary in it.
+
+### Step 3: Build the runtime image in OKD
+
+Now that the application image has been created with a compiled Go binary for the GoHelloWorld app, we can use something called chain builds to mimic when we extracted the binary from our local application image and created a new runtime image with just the binary in it.
+
+#### Create an image stream for the runtime image
+
+Once again, the first step is to create an image stream image for the new runtime image.
+
+
+```
+# Create the ImageStream
+$ oc create -f imageStream-goHelloWorld.yaml
+imagestream.image.openshift.io/go-hello-world created
+
+# Get the ImageStream
+$ oc get imagestream go-hello-world
+NAME DOCKER REPO TAGS UPDATED
+go-hello-world docker-registry.default.svc:5000/golang-builder/go-hello-world
+```
+
+#### Chain builds
+
+Chain builds are when one or more BuildConfigs are used to compile software or assemble artifacts for an application, and those artifacts are saved and used by a subsequent BuildConfig to generate a runtime image without re-compiling the code.
+
+![Chain Build workflow][14]
+
+Chain build workflow
+
+#### Create a BuildConfig for the runtime image
+
+The runtime BuildConfig uses the DockerStrategy build to build the image from a Dockerfile—the same thing we did with the builder image BuildConfig. This time, however, the source is not a Git source, but a Dockerfile source.
+
+What is the Dockerfile source? It's an inline Dockerfile! Instead of cloning a repo with a Dockerfile in it and building that, we specify the Dockerfile in the BuildConfig. This is especially appropriate with our runtime Dockerfile because it's just three lines long.
+
+
+```
+source:
+type: Dockerfile
+dockerfile: |-
+FROM scratch
+COPY app /app
+ENTRYPOINT ["/app"]
+images:
+\- from:
+kind: ImageStreamTag
+name: go-hello-world-appimage:1.0
+paths:
+\- sourcePath: /go/src/app/app
+destinationDir: "."
+```
+
+Note that the Dockerfile in the Dockerfile source definition above is the same as the Dockerfile we used in the [third article][4] in this series when we built the slim GoHelloWorld image locally using the binary we extracted with the S2I **save-artifacts** script.
+
+Something else to note: **scratch** is a reserved word in Dockerfiles. Unlike other **FROM** statements, it does not define an _actual_ image, but rather that the first layer of this image will be nothing. It is defined with **kind: DockerImage** but does not have a registry or group/namespace/project string. Learn more about this behavior in this excellent [container best practices][15] reference.
+
+The **images** section of the Dockerfile source describes the source of the artifact(s) to be used in the build; in this case, from the appimage generated earlier. The **paths** subsection describes where to get the binary (i.e., in the **/go/src/app** directory of the app image, get the **app** binary) and where to save it (i.e., in the current working directory of the build itself: **"."** ). This allows the **COPY app /app** to grab the binary from the current working directory and add it to **/app** in the runtime image.
+
+_Note:_ **paths** is an array of source and the destination path _pairs_. Each entry in the list consists of a source and destination. In the example above, there is just one entry because there is just a single binary to copy.
+
+The Docker strategy is then used to build the inline Dockerfile.
+
+
+```
+strategy:
+type: Docker
+dockerStrategy: {}
+```
+
+Once again, it is output to the image stream created earlier and includes build triggers to automatically kick off new builds.
+
+
+```
+output:
+to:
+kind: ImageStreamTag
+name: go-hello-world:1.0
+triggers:
+\- type: ConfigChange
+\- imageChange:
+type: ImageChange
+```
+
+Create a BuildConfig YAML or use the runtime BuildConfig from the GitHub repo.
+
+
+```
+$ oc create -f buildConfig-goHelloWorld.yaml
+buildconfig.build.openshift.io/go-hello-world created
+```
+
+If you watch the logs, you'll notice the first step is **FROM scratch** , which confirms we're adding the compiled binary to a blank image.
+
+
+```
+$ oc logs -f pod/go-hello-world-1-build
+Step 1/5 : FROM scratch
+\--->
+Step 2/5 : COPY app /app
+\---> 9e70e6c710f8
+Removing intermediate container 4d0bd9cef0a7
+Step 3/5 : ENTRYPOINT /app
+\---> Running in 7a2dfeba28ca
+\---> d697577910fc
+
+<...>
+```
+
+Once the build is completed, check the image stream tag to validate that the new image was pushed to the registry and image stream was updated.
+
+
+```
+$ oc get imagestream go-hello-world
+NAME DOCKER REPO TAGS UPDATED
+go-hello-world docker-registry.default.svc:5000/golang-builder/go-hello-world 1.0 4 minutes ago
+```
+
+Make a note of the **DOCKER REPO** string for the image. It will be used in the next section to run the image.
+
+### Did we create a tiny, binary-only image?
+
+Finally, let's validate that we did, indeed, build a tiny image with just the binary.
+
+Check out the image details. First, get the image's name from the image stream.
+
+
+```
+$ oc describe imagestream go-hello-world
+Name: go-hello-world
+Namespace: golang-builder
+Created: 42 minutes ago
+Labels:
+Annotations:
+Docker Pull Spec: docker-registry.default.svc:5000/golang-builder/go-hello-world
+Image Lookup: local=false
+Unique Images: 1
+Tags: 1
+
+1.0
+no spec tag
+
+* docker-registry.default.svc:5000/golang-builder/go-hello-world@sha256:eb11e0147a2917312f5e0e9da71109f0cb80760e945fdc1e2db6424b91bc9053
+13 minutes ago
+```
+
+The image is listed at the bottom, described with the SHA hash (e.g., **sha256:eb11e0147a2917312f5e0e9da71109f0cb80760e945fdc1e2db6424b91bc9053** ; yours will be different).
+
+Get the details of the image using the hash.
+
+
+```
+$ oc describe image sha256:eb11e0147a2917312f5e0e9da71109f0cb80760e945fdc1e2db6424b91bc9053
+Docker Image: docker-registry.default.svc:5000/golang-builder/go-hello-world@sha256:eb11e0147a2917312f5e0e9da71109f0cb80760e945fdc1e2db6424b91bc9053
+Name: sha256:eb11e0147a2917312f5e0e9da71109f0cb80760e945fdc1e2db6424b91bc9053
+Created: 15 minutes ago
+Annotations: image.openshift.io/dockerLayersOrder=ascending
+image.openshift.io/manifestBlobStored=true
+openshift.io/image.managed=true
+Image Size: 1.026MB
+Image Created: 15 minutes ago
+Author:
+Arch: amd64
+Entrypoint: /app
+Working Dir:
+User:
+Exposes Ports:
+Docker Labels: io.openshift.build.name=go-hello-world-1
+io.openshift.build.namespace=golang-builder
+Environment: PATH=/usr/local/sbin:/usr/local/bin:/usr/sbin:/usr/bin:/sbin:/bin
+OPENSHIFT_BUILD_NAME=go-hello-world-1
+OPENSHIFT_BUILD_NAMESPACE=golang-builder
+```
+
+Notice the image size, 1.026MB, is exactly as we want. The image is a scratch image with just the binary inside it!
+
+### Run a pod with the runtime image
+
+Using the runtime image we just created, let's create a pod on-demand and run it and validate that it still works.
+
+This almost never happens in Kubernetes/OKD, but we will run a pod, just a pod, by itself.
+
+
+```
+$ oc run -it go-hello-world --image=docker-registry.default.svc:5000/golang-builder/go-hello-world:1.0 --restart=Never
+Hello World!
+```
+
+Everything is working as expected—the image runs and outputs "Hello World!" just as it did in the previous, local S2I builds.
+
+By creating this workflow in OKD, we can use the golang-builder S2I image for any Go application. This builder image is in place and built for any other applications, and it will auto-update and rebuild itself anytime the upstream golang:1.12 image changes.
+
+New apps can be built automatically using the S2I build by creating a chain build strategy in OKD with an appimage BuildConfig to compile the source and the runtime BuildConfig to create the final image. Using the build triggers, any change to the source code in the Git repo will trigger a rebuild through the entire pipeline, rebuilding the appimage and the runtime image automatically.
+
+This is a great way to maintain updated images for any application. Paired with an OKD deploymentConfig with an image build trigger, long-running applications (e.g., webapps) will be automatically redeployed when new code is committed.
+
+Source-to-Image is an ideal way to develop builder images to build and compile Go applications in a repeatable way, and it just gets better when paired with OKD BuildConfigs.
+
+--------------------------------------------------------------------------------
+
+via: https://opensource.com/article/19/5/creating-source-image-build-pipeline-okd
+
+作者:[Chris Collins][a]
+选题:[lujun9972][b]
+译者:[译者ID](https://github.com/译者ID)
+校对:[校对者ID](https://github.com/校对者ID)
+
+本文由 [LCTT](https://github.com/LCTT/TranslateProject) 原创编译,[Linux中国](https://linux.cn/) 荣誉推出
+
+[a]: https://opensource.com/users/clcollins
+[b]: https://github.com/lujun9972
+[1]: https://opensource.com/sites/default/files/styles/image-full-size/public/lead-images/blocks_building.png?itok=eMOT-ire
+[2]: https://opensource.com/article/19/5/source-image-golang-part-1
+[3]: https://opensource.com/article/19/5/source-image-golang-part-2
+[4]: https://opensource.com/article/19/5/source-image-golang-part-3
+[5]: https://www.okd.io/
+[6]: https://github.com/minishift/minishift
+[7]: https://github.com/clcollins/golang-s2i.git
+[8]: https://docs.okd.io/latest/architecture/core_concepts/builds_and_image_streams.html#image-streams
+[9]: https://docs.okd.io/latest/dev_guide/managing_images.html#using-is-with-k8s
+[10]: https://docs.okd.io/latest/dev_guide/builds/index.html#defining-a-buildconfig
+[11]: https://github.com/clcollins/golang-s2i/blob/master/okd/buildConfig-golang-builder.yaml
+[12]: mailto:collins.christopher@gmail.com
+[13]: https://github.com/clcollins/goHelloWorld.git
+[14]: https://opensource.com/sites/default/files/uploads/chainingbuilds.png (Chain Build workflow)
+[15]: http://docs.projectatomic.io/container-best-practices/#_from_scratch
diff --git a/sources/tech/20190531 Learn Python with these awesome resources.md b/sources/tech/20190531 Learn Python with these awesome resources.md
new file mode 100644
index 0000000000..8bcd1d2bbf
--- /dev/null
+++ b/sources/tech/20190531 Learn Python with these awesome resources.md
@@ -0,0 +1,90 @@
+[#]: collector: (lujun9972)
+[#]: translator: ( )
+[#]: reviewer: ( )
+[#]: publisher: ( )
+[#]: url: ( )
+[#]: subject: (Learn Python with these awesome resources)
+[#]: via: (https://opensource.com/article/19/5/resources-learning-python)
+[#]: author: (Don Watkins https://opensource.com/users/don-watkins)
+
+Learn Python with these awesome resources
+======
+Expand your Python knowledge by adding these resources to your personal
+learning network.
+![Book list, favorites][1]
+
+I've been using and teaching Python for a long time now, but I'm always interested in increasing my knowledge about this practical and useful programming language. That's why I've been trying to expand my Python [personal learning network][2] (PLN), a concept that describes informal and mutually beneficial networks for sharing information.
+
+Educators [Kelly Paredes][3] and [Sean Tibor][4] recently talked about how to build your Python PLN on their podcast, [Teaching Python][5], which I subscribed to after meeting them at [PyCon 2019][6] in Cleveland (and adding them to my Python PLN). This podcast inspired me to think more about the people in my Python PLN, including those I met recently at PyCon.
+
+I'll share some of the places I've met members of my PLN; maybe they can become part of your Python PLN, too.
+
+### Young Coders mentors
+
+[Betsy Waliszewski][7], the event coordinator for the Python Foundation, is a member of my Python PLN. When we ran into each other at PyCon2019, because I'm a teacher, she recommended I check out the [Young Coders][8] workshop for kids ages 12 and up. There, I met [Katie Cunningham][9], who was running the program, which taught participants how to set up and configure a Raspberry Pi and use Python. The young students also received two books: _[Python for Kids][10]_ by Jason Briggs and _[Learn to Program with Minecraft][11]_ by Craig Richardson. I'm always looking for new ways to improve my teaching, so I quickly picked up two copies of the Minecraft book at [NoStarch Press][12]' booth at the conference. Katie is a great teacher and a prolific author with a wonderful [YouTube][13] channel full of Python training videos.
+
+I added Katie to my PLN, along with two other people I met at the Young Coders workshop: [Nat Dunn][14] and [Sean Valentine][15]. Like Katie, they were volunteering their time to introduce young programmers to Python. Nat is the president of [Webucator][16], an IT training company that has been a sponsor of the Python Software Foundation for several years and sponsored the PyCon 2018 Education Summit. He decided to teach at Young Coders after teaching Python to his 13-year-old son and 14-year-old nephew. Sean is the director of strategic initiatives at the [Hidden Genius Project][17], a technology and leadership mentoring program for black male youth. Sean said many Hidden Genius participants "built projects using Python, so we saw [Young Coders] as a great opportunity to partner." Learning about the Hidden Genius Project has inspired me to think deeper about the implications of coding and its power to change lives.
+
+### Open Spaces meetups
+
+I found PyCon's [Open Spaces][18], self-organizing, impromptu hour-long meetups, just as useful as the official programmed events. One of my favorites was about the [Circuit Playground Express][19] device, which was part of our conference swag bags. I am fascinated by this device, and the Open Space provided an avenue to learn more. The organizers offered a worksheet and a [GitHub][20] repo with all the tools we needed to be successful, as well as an opportunity for hands-on learning and direction to explore this unique hardware.
+
+This meetup whetted my appetite to learn even more about programming the Circuit Playground Express, so after PyCon, I reached out on Twitter to [Nina Zakharenko][21], who [presented a keynote][22] at the conference about programming the device. Nina has been in my Python PLN since last fall when I heard her talk at [All Things Open][23], and I recently signed up for her [Python Fundamentals][24] class to add to my learning. Nina recommended I add [Kattni Rembor][25], whose [code examples][26] are helping me learn to program with CircuitPython, to my Python PLN.
+
+### Other resources from my PLN
+
+I also met fellow [Opensource.com][27] Community Moderator [Moshe Zadka][28] at PyCon2019 and talked with him at length. He shared several new Python resources, including _[How to Think Like a Computer Scientist][29]_. Community Moderator [Seth Kenlon][30] is another member of my PLN; he has published many great [Python articles][31], and I recommend you follow him, too.
+
+My Python personal learning network continues to grow each day. Besides the folks I have already mentioned, I recommend you follow [Al Sweigart][32], [Eric Matthes][33], and [Adafruit][34] because they share great content. I also recommend the book _[Make: Getting Started with Adafruit Circuit Playground Express][35]_ and [Podcast.__init__][36], a podcast all about the Python community, both of which I learned about from my PLN.
+
+Who is in your Python PLN? Please share your favorites in the comments.
+
+--------------------------------------------------------------------------------
+
+via: https://opensource.com/article/19/5/resources-learning-python
+
+作者:[Don Watkins][a]
+选题:[lujun9972][b]
+译者:[译者ID](https://github.com/译者ID)
+校对:[校对者ID](https://github.com/校对者ID)
+
+本文由 [LCTT](https://github.com/LCTT/TranslateProject) 原创编译,[Linux中国](https://linux.cn/) 荣誉推出
+
+[a]: https://opensource.com/users/don-watkins
+[b]: https://github.com/lujun9972
+[1]: https://opensource.com/sites/default/files/styles/image-full-size/public/lead-images/reading_book_stars_list.png?itok=Iwa1oBOl (Book list, favorites)
+[2]: https://en.wikipedia.org/wiki/Personal_learning_network
+[3]: https://www.teachingpython.fm/hosts/kellypared
+[4]: https://twitter.com/smtibor
+[5]: https://www.teachingpython.fm/20
+[6]: https://us.pycon.org/2019/
+[7]: https://www.linkedin.com/in/betsywaliszewski
+[8]: https://us.pycon.org/2019/events/letslearnpython/
+[9]: https://www.linkedin.com/in/kcunning/
+[10]: https://nostarch.com/pythonforkids
+[11]: https://nostarch.com/programwithminecraft
+[12]: https://nostarch.com/
+[13]: https://www.youtube.com/c/KatieCunningham
+[14]: https://www.linkedin.com/in/natdunn/
+[15]: https://www.linkedin.com/in/sean-valentine-b370349b/
+[16]: https://www.webucator.com/
+[17]: http://www.hiddengeniusproject.org/
+[18]: https://us.pycon.org/2019/events/open-spaces/
+[19]: https://www.adafruit.com/product/3333
+[20]: https://github.com/adafruit/PyCon2019
+[21]: https://twitter.com/nnja
+[22]: https://www.youtube.com/watch?v=35mXD40SvXM
+[23]: https://allthingsopen.org/
+[24]: https://frontendmasters.com/courses/python/
+[25]: https://twitter.com/kattni
+[26]: https://github.com/kattni/ChiPy_2018
+[27]: http://Opensource.com
+[28]: https://opensource.com/users/moshez
+[29]: http://openbookproject.net/thinkcs/python/english3e/
+[30]: https://opensource.com/users/seth
+[31]: https://www.google.com/search?source=hp&ei=gVToXPq-FYXGsAW-mZ_YAw&q=site%3Aopensource.com+%22Seth+Kenlon%22+%2B+Python&oq=site%3Aopensource.com+%22Seth+Kenlon%22+%2B+Python&gs_l=psy-ab.12...627.15303..15584...1.0..0.176.2802.4j21......0....1..gws-wiz.....0..35i39j0j0i131j0i67j0i20i263.r2SAW3dxlB4
+[32]: http://alsweigart.com/
+[33]: https://twitter.com/ehmatthes?lang=en
+[34]: https://twitter.com/adafruit
+[35]: https://www.adafruit.com/product/3944
+[36]: https://www.pythonpodcast.com/episodes/
diff --git a/sources/tech/20190531 Use Firefox Send with ffsend in Fedora.md b/sources/tech/20190531 Use Firefox Send with ffsend in Fedora.md
new file mode 100644
index 0000000000..984fb771dc
--- /dev/null
+++ b/sources/tech/20190531 Use Firefox Send with ffsend in Fedora.md
@@ -0,0 +1,126 @@
+[#]: collector: (lujun9972)
+[#]: translator: ( )
+[#]: reviewer: ( )
+[#]: publisher: ( )
+[#]: url: ( )
+[#]: subject: (Use Firefox Send with ffsend in Fedora)
+[#]: via: (https://fedoramagazine.org/use-firefox-send-with-ffsend-in-fedora/)
+[#]: author: (Sylvia Sánchez https://fedoramagazine.org/author/lailah/)
+
+Use Firefox Send with ffsend in Fedora
+======
+
+![][1]
+
+_ffsend_ is the command line client of Firefox Send. This article will show how Firefox Send and _ffsend_ work. It’ll also detail how it can be installed and used in Fedora.
+
+### What are Firefox Send and ffsend ?
+
+Firefox Send is a file sharing tool from Mozilla that allows sending encrypted files to other users. You can install Send on your own server, or use the Mozilla-hosted link [send.firefox.com][2]. The hosted version officially supports files up to 1 GB, and links that expire after a configurable download count (default of 1) or 24 hours, and then all the files on the Send server are deleted. This tool is still _in experimental phase_ , and therefore shouldn’t be used in production or to share important or sensitive data.
+
+While Firefox Send is the tool itself and can be used with a web interface, _ffsend_ is a command-line utility you can use with scripts and arguments. It has a wide range of configuration options and can be left working in the background without any human intervention.
+
+### How does it work?
+
+FFSend can both upload and download files. The remote host can use either the Firefox tool or another web browser to download the file. Neither Firefox Send nor _ffsend_ require the use of Firefox.
+
+It’s important to highlight that _ffsend_ uses client-side encryption. This means that files are encrypted _before_ they’re uploaded. You share secrets together with the link, so be careful when sharing, because anyone with the link will be able to download the file. As an extra layer of protection, you can protect the file with a password by using the following argument:
+
+```
+ffsend password URL -p PASSWORD
+```
+
+### Other features
+
+There are a few other features worth mentioning. Here’s a list:
+
+ * Configurable download limit, between 1 and 20 times, before the link expires
+ * Built-in extract and archiving functions
+ * Track history of shared files
+ * Inspect or delete shared files
+ * Folders can be shared as well, either as they are or as compressed files
+ * Generate a QR code, for easier download on a mobile phone
+
+
+
+### How to install in Fedora
+
+While Fedora Send works with Firefox without installing anything extra, you’ll need to install the CLI tool to use _ffsend_. This tool is in the official repositories, so you only need a simple _dnf_ command [with][3] _[sudo][3]_.
+
+```
+$ sudo dnf install ffsend
+```
+
+After that, you can use _ffsend_ from the terminal .
+
+### Upload a file
+
+Uploading a file is a simple as
+
+```
+$ ffsend upload /etc/os-release
+Upload complete
+Share link: https://send.firefox.com/download/05826227d70b9a4b/#RM_HSBq6kuyeBem8Z013mg
+```
+
+The file now can be easily share using the Share link URL.
+
+## Downloading a file
+
+Downloading a file is as simple as uploading.
+
+```
+$ ffsend download https://send.firefox.com/download/05826227d70b9a4b/#RM_HSBq6kuyeBem8Z013mg
+Download complete
+```
+
+Before downloading a file it might be useful to check if the file exist and get information about it. _ffsend_ provides 2 handy commands for that.
+
+```
+$ ffsend exists https://send.firefox.com/download/88a6324e2a99ebb6/#YRJDh8ZDQsnZL2KZIA-PaQ
+Exists: true
+Password: false
+$ ffsend info https://send.firefox.com/download/88a6324e2a99ebb6/#YRJDh8ZDQsnZL2KZIA-PaQ
+ID: 88a6324e2a99ebb6
+Downloads: 0 of 1
+Expiry: 23h59m (86388s
+```
+
+## Upload history
+
+_ffsend_ also provides a way to check the history of the uploads made with the tools. This can be really useful if you upload a lot of files during a scripted tasks for example and you want to keep track of each files download status.
+
+```
+$ ffsend history
+LINK EXPIRY
+ 1 https://send.firefox.com/download/#8TJ9QNw 23h59m
+ 2 https://send.firefox.com/download/KZIA-PaQ 23h54m
+```
+
+## Delete a file
+
+Another useful feature is the possibility to delete a file.
+
+```
+ffsend delete https://send.firefox.com/download/2d9faa7f34bb1478/#phITKvaYBjCGSRI8TJ9QNw
+```
+
+Firefox Send is a great service and the _ffsend_ tools makes it really convenient to use from the terminal. More examples and documentation is available on _ffsend_ ‘s [Gitlab repository][4].
+
+--------------------------------------------------------------------------------
+
+via: https://fedoramagazine.org/use-firefox-send-with-ffsend-in-fedora/
+
+作者:[Sylvia Sánchez][a]
+选题:[lujun9972][b]
+译者:[译者ID](https://github.com/译者ID)
+校对:[校对者ID](https://github.com/校对者ID)
+
+本文由 [LCTT](https://github.com/LCTT/TranslateProject) 原创编译,[Linux中国](https://linux.cn/) 荣誉推出
+
+[a]: https://fedoramagazine.org/author/lailah/
+[b]: https://github.com/lujun9972
+[1]: https://fedoramagazine.org/wp-content/uploads/2019/04/firefox-send-816x345.png
+[2]: http://send.firefox.com/
+[3]: https://fedoramagazine.org/howto-use-sudo/
+[4]: https://gitlab.com/timvisee/ffsend
diff --git a/sources/tech/20190603 How many browser tabs do you usually have open.md b/sources/tech/20190603 How many browser tabs do you usually have open.md
new file mode 100644
index 0000000000..7777477029
--- /dev/null
+++ b/sources/tech/20190603 How many browser tabs do you usually have open.md
@@ -0,0 +1,44 @@
+[#]: collector: (lujun9972)
+[#]: translator: ( )
+[#]: reviewer: ( )
+[#]: publisher: ( )
+[#]: url: ( )
+[#]: subject: (How many browser tabs do you usually have open?)
+[#]: via: (https://opensource.com/article/19/6/how-many-browser-tabs)
+[#]: author: (Lauren Pritchett https://opensource.com/users/lauren-pritchett/users/sarahwall/users/ksonney/users/jwhitehurst)
+
+How many browser tabs do you usually have open?
+======
+Plus, get a few tips for browser productivity.
+![Browser of things][1]
+
+Here's a potentially loaded question: How many browser tabs do you usually have open at one time? Do you have multiple windows, each with multiple tabs? Or are you a minimalist, and only have a couple of tabs open at once. Another option is to move a 20-tabbed browser window to a different monitor so that it is out of the way while working on a particular task. Does your approach differ between work, personal, and mobile browsers? Is your browser strategy related to your [productivity habits][2]?
+
+### 4 tips for browser productivity
+
+ 1. Know your browser shortcuts to save clicks. Whether you use Firefox or Chrome, there are plenty of keyboard shortcuts to help make switching between tabs and performing certain functions a breeze. For example, Chrome makes it easy to open up a blank Google document. Use the shortcut **"Ctrl + t"** to open a new tab, then type **"doc.new"**. The same can be done for spreadsheets, slides, and forms.
+ 2. Organize your most frequent tasks with bookmark folders. When it's time to start a particular task, simply open all of the bookmarks in the folder **(Ctrl + click)** to check it off your list quickly.
+ 3. Get the right browser extensions for you. There are thousands of browser extensions out there all claiming to improve productivity. Before you install, make sure you're not just adding more distractions to your screen.
+ 4. Reduce screen time by using a timer. It doesn't matter if you use an old-fashioned egg timer or a fancy browser extension. To prevent eye strain, implement the 20/20/20 rule. Every 20 minutes, take a 20-second break from your screen and look at something 20 feet away.
+
+
+
+Take our poll to share how many browser tabs you like to have open at once. Be sure to tell us about your favorite browser tricks in the comments.
+
+There are two components of productivity—doing the right things and doing those things efficiently...
+
+--------------------------------------------------------------------------------
+
+via: https://opensource.com/article/19/6/how-many-browser-tabs
+
+作者:[Lauren Pritchett][a]
+选题:[lujun9972][b]
+译者:[译者ID](https://github.com/译者ID)
+校对:[校对者ID](https://github.com/校对者ID)
+
+本文由 [LCTT](https://github.com/LCTT/TranslateProject) 原创编译,[Linux中国](https://linux.cn/) 荣誉推出
+
+[a]: https://opensource.com/users/lauren-pritchett/users/sarahwall/users/ksonney/users/jwhitehurst
+[b]: https://github.com/lujun9972
+[1]: https://opensource.com/sites/default/files/styles/image-full-size/public/lead-images/browser_desktop_website_checklist_metrics.png?itok=OKKbl1UR (Browser of things)
+[2]: https://enterprisersproject.com/article/2019/1/5-time-wasting-habits-break-new-year
diff --git a/sources/tech/20190603 How to set up virtual environments for Python on MacOS.md b/sources/tech/20190603 How to set up virtual environments for Python on MacOS.md
new file mode 100644
index 0000000000..db01ada8d4
--- /dev/null
+++ b/sources/tech/20190603 How to set up virtual environments for Python on MacOS.md
@@ -0,0 +1,214 @@
+[#]: collector: (lujun9972)
+[#]: translator: (runningwater)
+[#]: reviewer: ( )
+[#]: publisher: ( )
+[#]: url: ( )
+[#]: subject: (How to set up virtual environments for Python on MacOS)
+[#]: via: (https://opensource.com/article/19/6/virtual-environments-python-macos)
+[#]: author: (Matthew Broberg https://opensource.com/users/mbbroberg/users/moshez/users/mbbroberg/users/moshez)
+
+How to set up virtual environments for Python on MacOS
+======
+Save yourself a lot of confusion by managing your virtual environments
+with pyenv and virtualwrapper.
+![][1]
+
+If you're a Python developer and a MacOS user, one of your first tasks upon getting a new computer is to set up your Python development environment. Here is the best way to do it (although we have written about [other ways to manage Python environments on MacOS][2]).
+
+### Preparation
+
+First, open a terminal and enter **xcode-select --install** at its cold, uncaring prompt. Click to confirm, and you'll be all set with a basic development environment. This step is required on MacOS to set up local development utilities, including "many commonly used tools, utilities, and compilers, including make, GCC, clang, perl, svn, git, size, strip, strings, libtool, cpp, what, and many other useful commands that are usually found in default Linux installations," according to [OS X Daily][3].
+
+Next, install [Homebrew][4] by executing the following Ruby script from the internet:
+
+
+```
+`ruby -e "$(curl -fsSL https://raw.githubusercontent.com/Homebrew/install/master/install)"`
+```
+
+If you, like me, have trust issues with arbitrarily running scripts from the internet, click on the script above and take a longer look to see what it does.
+
+Once this is done, congratulations, you have an excellent package management tool in Homebrew. Naively, you might think that you next **brew install python** or something. No, haha. Homebrew will give you a version of Python, but the version you get will be out of your control if you let the tool manage your environment for you. You want [pyenv][5], "a tool for simple Python version management," that can be installed on [many operating systems][6]. Run:
+
+
+```
+`$ brew install pyenv`
+```
+
+You want pyenv to run every time you open your prompt, so include the following in your configuration files (by default on MacOS, this is **.bash_profile** in your home directory):
+
+
+```
+$ cd ~/
+$ echo 'eval "$(pyenv init -)"' >> .bash_profile
+```
+
+By adding this line, every new terminal will initiate pyenv to manage the **PATH** environment variable in your terminal and insert the version of Python you want to run (as opposed to the first one that shows up in the environment. For more information, read "[How to set your $PATH variable in Linux][7].") Open a new terminal for the updated **.bash_profile** to take effect.
+
+Before installing your favorite version of Python, you'll want to install a couple of helpful tools:
+
+
+```
+`$ brew install zlib sqlite`
+```
+
+The [zlib][8] compression algorithm and the [SQLite][9] database are dependencies for pyenv and often [cause build problems][10] when not configured correctly. Add these exports to your current terminal window to ensure the installation completes:
+
+
+```
+$ export LDFLAGS="-L/usr/local/opt/zlib/lib -L/usr/local/opt/sqlite/lib"
+$ export CPPFLAGS="-I/usr/local/opt/zlib/include -I/usr/local/opt/sqlite/include"
+```
+
+Now that the preliminaries are done, it's time to install a version of Python that is fit for a modern person in the modern age:
+
+
+```
+`$ pyenv install 3.7.3`
+```
+
+Go have a cup of coffee. From beans you hand-roast. After you pick them. What I'm saying here is it's going to take some time.
+
+### Adding virtual environments
+
+Once it's finished, it's time to make your virtual environments pleasant to use. Without this next step, you will effectively be sharing one Python development environment for every project you work on. Using virtual environments to isolate dependency management on a per-project basis will give us more certainty and reproducibility than Python offers out of the box. For these reasons, install **virtualenvwrapper** into the Python environment:
+
+
+```
+$ pyenv global 3.7.3
+# Be sure to keep the $() syntax in this command so it can evaluate
+$ $(pyenv which python3) -m pip install virtualenvwrapper
+```
+
+Open your **.bash_profile** again and add the following to be sure it works each time you open a new terminal:
+
+
+```
+# We want to regularly go to our virtual environment directory
+$ echo 'export WORKON_HOME=~/.virtualenvs' >> .bash_profile
+# If in a given virtual environment, make a virtual environment directory
+# If one does not already exist
+$ echo 'mkdir -p $WORKON_HOME' >> .bash_profile
+# Activate the new virtual environment by calling this script
+# Note that $USER will substitute for your current user
+$ echo '. ~/.pyenv/versions/3.7.3/bin/virtualenvwrapper.sh' >> .bash_profile
+```
+
+Close the terminal and open a new one (or run **exec /bin/bash -l** to refresh the current terminal session), and you'll see **virtualenvwrapper** initializing the environment:
+
+
+```
+$ exec /bin/bash -l
+virtualenvwrapper.user_scripts creating /Users/moshe/.virtualenvs/premkproject
+virtualenvwrapper.user_scripts creating /Users/moshe/.virtualenvs/postmkproject
+virtualenvwrapper.user_scripts creating /Users/moshe/.virtualenvs/initialize
+virtualenvwrapper.user_scripts creating /Users/moshe/.virtualenvs/premkvirtualenv
+virtualenvwrapper.user_scripts creating /Users/moshe/.virtualenvs/postmkvirtualenv
+virtualenvwrapper.user_scripts creating /Users/moshe/.virtualenvs/prermvirtualenv
+virtualenvwrapper.user_scripts creating /Users/moshe/.virtualenvs/postrmvirtualenv
+virtualenvwrapper.user_scripts creating /Users/moshe/.virtualenvs/predeactivate
+virtualenvwrapper.user_scripts creating /Users/moshe/.virtualenvs/postdeactivate
+virtualenvwrapper.user_scripts creating /Users/moshe/.virtualenvs/preactivate
+virtualenvwrapper.user_scripts creating /Users/moshe/.virtualenvs/postactivate
+virtualenvwrapper.user_scripts creating /Users/moshe/.virtualenvs/get_env_details
+```
+
+From now on, all your work should be in a virtual environment, allowing you to use temporary environments to play around with development safely. With this toolchain, you can set up multiple projects and switch between them, depending upon what you're working on at that moment:
+
+
+```
+$ mkvirtualenv test1
+Using base prefix '/Users/moshe/.pyenv/versions/3.7.3'
+New python executable in /Users/moshe/.virtualenvs/test1/bin/python3
+Also creating executable in /Users/moshe/.virtualenvs/test1/bin/python
+Installing setuptools, pip, wheel...
+done.
+virtualenvwrapper.user_scripts creating /Users/moshe/.virtualenvs/test1/bin/predeactivate
+virtualenvwrapper.user_scripts creating /Users/moshe/.virtualenvs/test1/bin/postdeactivate
+virtualenvwrapper.user_scripts creating /Users/moshe/.virtualenvs/test1/bin/preactivate
+virtualenvwrapper.user_scripts creating /Users/moshe/.virtualenvs/test1/bin/postactivate
+virtualenvwrapper.user_scripts creating /Users/moshe/.virtualenvs/test1/bin/get_env_details
+(test1)$ mkvirtualenv test2
+Using base prefix '/Users/moshe/.pyenv/versions/3.7.3'
+New python executable in /Users/moshe/.virtualenvs/test2/bin/python3
+Also creating executable in /Users/moshe/.virtualenvs/test2/bin/python
+Installing setuptools, pip, wheel...
+done.
+virtualenvwrapper.user_scripts creating /Users/moshe/.virtualenvs/test2/bin/predeactivate
+virtualenvwrapper.user_scripts creating /Users/moshe/.virtualenvs/test2/bin/postdeactivate
+virtualenvwrapper.user_scripts creating /Users/moshe/.virtualenvs/test2/bin/preactivate
+virtualenvwrapper.user_scripts creating /Users/moshe/.virtualenvs/test2/bin/postactivate
+virtualenvwrapper.user_scripts creating /Users/moshe/.virtualenvs/test2/bin/get_env_details
+(test2)$ ls $WORKON_HOME
+get_env_details postmkvirtualenv premkvirtualenv
+initialize postrmvirtualenv prermvirtualenv
+postactivate preactivate test1
+postdeactivate predeactivate test2
+postmkproject premkproject
+(test2)$ workon test1
+(test1)$
+```
+
+The **deactivate** command exits you from the current environment.
+
+### Recommended practices
+
+You may already set up your long-term projects in a directory like **~/src**. When you start working on a new project, go into this directory, add a subdirectory for the project, then use the power of Bash interpretation to name the virtual environment based on your directory name. For example, for a project named "pyfun":
+
+
+```
+$ mkdir -p ~/src/pyfun && cd ~/src/pyfun
+$ mkvirtualenv $(basename $(pwd))
+# we will see the environment initialize
+(pyfun)$ workon
+pyfun
+test1
+test2
+(pyfun)$ deactivate
+$
+```
+
+Whenever you want to work on this project, go back to that directory and reconnect to the virtual environment by entering:
+
+
+```
+$ cd ~/src/pyfun
+(pyfun)$ workon .
+```
+
+Since initializing a virtual environment means taking a point-in-time copy of your Python version and the modules that are loaded, you will occasionally want to refresh the project's virtual environment, as dependencies can change dramatically. You can do this safely by deleting the virtual environment because the source code will remain unscathed:
+
+
+```
+$ cd ~/src/pyfun
+$ rmvirtualenv $(basename $(pwd))
+$ mkvirtualenv $(basename $(pwd))
+```
+
+This method of managing virtual environments with pyenv and virtualwrapper will save you from uncertainty about which version of Python you are running as you develop code locally. This is the simplest way to avoid confusion—especially when you're working with a larger team.
+
+If you are just beginning to configure your Python environment, read up on how to use [Python 3 on MacOS][2]. Do you have other beginner or intermediate Python questions? Leave a comment and we will consider them for the next article.
+
+--------------------------------------------------------------------------------
+
+via: https://opensource.com/article/19/6/virtual-environments-python-macos
+
+作者:[Matthew Broberg][a]
+选题:[lujun9972][b]
+译者:[runningwater](https://github.com/runningwater)
+校对:[校对者ID](https://github.com/校对者ID)
+
+本文由 [LCTT](https://github.com/LCTT/TranslateProject) 原创编译,[Linux中国](https://linux.cn/) 荣誉推出
+
+[a]: https://opensource.com/users/mbbroberg/users/moshez/users/mbbroberg/users/moshez
+[b]: https://github.com/lujun9972
+[1]: https://opensource.com/sites/default/files/styles/image-full-size/public/lead-images/python_snake_file_box.jpg?itok=UuDVFLX-
+[2]: https://opensource.com/article/19/5/python-3-default-macos
+[3]: http://osxdaily.com/2014/02/12/install-command-line-tools-mac-os-x/
+[4]: https://brew.sh/
+[5]: https://github.com/pyenv/pyenv
+[6]: https://github.com/pyenv/pyenv/wiki
+[7]: https://opensource.com/article/17/6/set-path-linux
+[8]: https://zlib.net/
+[9]: https://www.sqlite.org/index.html
+[10]: https://github.com/pyenv/pyenv/wiki/common-build-problems#build-failed-error-the-python-zlib-extension-was-not-compiled-missing-the-zlib
diff --git a/sources/tech/20190603 How to stream music with GNOME Internet Radio.md b/sources/tech/20190603 How to stream music with GNOME Internet Radio.md
new file mode 100644
index 0000000000..fc21d82d0b
--- /dev/null
+++ b/sources/tech/20190603 How to stream music with GNOME Internet Radio.md
@@ -0,0 +1,59 @@
+[#]: collector: (lujun9972)
+[#]: translator: ( )
+[#]: reviewer: ( )
+[#]: publisher: ( )
+[#]: url: ( )
+[#]: subject: (How to stream music with GNOME Internet Radio)
+[#]: via: (https://opensource.com/article/19/6/gnome-internet-radio)
+[#]: author: (Alan Formy-Duval https://opensource.com/users/alanfdoss/users/r3bl)
+
+How to stream music with GNOME Internet Radio
+======
+If you're looking for a simple, straightforward interface that gets your
+streams playing, try GNOME's Internet Radio plugin.
+![video editing dashboard][1]
+
+Internet radio is a great way to listen to stations from all over the world. Like many developers, I like to turn on a station as I code. You can listen to internet radio with a media player for the terminal like [MPlayer][2] or [mpv][3], which is what I use to listen via the Linux command line. However, if you prefer using a graphical user interface (GUI), you may want to try [GNOME Internet Radio][4], a nifty plugin for the GNOME desktop. You can find it in the package manager.
+
+![GNOME Internet Radio plugin][5]
+
+Listening to internet radio with a graphical desktop operating system generally requires you to launch an application such as [Audacious][6] or [Rhythmbox][7]. They have nice interfaces, plenty of options, and cool audio visualizers. But if you want a simple, straightforward interface that gets your streams playing, GNOME Internet Radio is for you.
+
+After installing it, a small icon appears in your toolbar, which is where you do all your configuration and management.
+
+![GNOME Internet Radio icons][8]
+
+The first thing I did was go to the Settings menu. I enabled the following two options: show title notifications and show volume adjustment.
+
+![GNOME Internet Radio Settings][9]
+
+GNOME Internet Radio includes a few pre-configured stations, and it is really easy to add others. Just click the ( **+** ) sign. You'll need to enter a channel name, which can be anything you prefer (including the station name), and the station address. For example, I like to listen to Synthetic FM. I enter the name, e.g., "Synthetic FM," and the stream address, i.e., .
+
+Then click the star next to the stream to add it to your menu.
+
+However you listen to music and whatever genre you choose, it is obvious—coders need their music! The GNOME Internet Radio plugin makes it simple to get your favorite internet radio station queued up.
+
+In honor of the Gnome desktop's 18th birthday on August 15, we've rounded up 18 reasons to toast...
+
+--------------------------------------------------------------------------------
+
+via: https://opensource.com/article/19/6/gnome-internet-radio
+
+作者:[Alan Formy-Duval][a]
+选题:[lujun9972][b]
+译者:[译者ID](https://github.com/译者ID)
+校对:[校对者ID](https://github.com/校对者ID)
+
+本文由 [LCTT](https://github.com/LCTT/TranslateProject) 原创编译,[Linux中国](https://linux.cn/) 荣誉推出
+
+[a]: https://opensource.com/users/alanfdoss/users/r3bl
+[b]: https://github.com/lujun9972
+[1]: https://opensource.com/sites/default/files/styles/image-full-size/public/lead-images/video_editing_folder_music_wave_play.png?itok=-J9rs-My (video editing dashboard)
+[2]: https://opensource.com/article/18/12/linux-toy-mplayer
+[3]: https://mpv.io/
+[4]: https://extensions.gnome.org/extension/836/internet-radio/
+[5]: https://opensource.com/sites/default/files/uploads/packagemanager_s.png (GNOME Internet Radio plugin)
+[6]: https://audacious-media-player.org/
+[7]: https://help.gnome.org/users/rhythmbox/stable/
+[8]: https://opensource.com/sites/default/files/uploads/titlebaricons.png (GNOME Internet Radio icons)
+[9]: https://opensource.com/sites/default/files/uploads/gnomeinternetradio_settings.png (GNOME Internet Radio Settings)
diff --git a/sources/tech/20190604 Aging in the open- How this community changed us.md b/sources/tech/20190604 Aging in the open- How this community changed us.md
new file mode 100644
index 0000000000..a03d49eca2
--- /dev/null
+++ b/sources/tech/20190604 Aging in the open- How this community changed us.md
@@ -0,0 +1,135 @@
+[#]: collector: (lujun9972)
+[#]: translator: ( )
+[#]: reviewer: ( )
+[#]: publisher: ( )
+[#]: url: ( )
+[#]: subject: (Aging in the open: How this community changed us)
+[#]: via: (https://opensource.com/open-organization/19/6/four-year-celebration)
+[#]: author: (Bryan Behrenshausen https://opensource.com/users/bbehrens)
+
+Aging in the open: How this community changed us
+======
+Our community dedicated to exploring open organizational culture and
+design turns four years old this week.
+![Browser window with birthday hats and a cake][1]
+
+A community will always surprise you.
+
+That's not an easy statement for someone like me to digest. I'm not one for surprises. I revel in predictability. I thrive on consistency.
+
+A passionate and dedicated community offers few of these comforts. Participating in something like [the open organization community at Opensource.com][2]—which [turns four years old this week][3]—means acquiescing to dynamism, to constant change. Every day brings novelty. Every correspondence is packed with possibility. Every interaction reveals undisclosed pathways.
+
+To [a certain type of person][4] (me again), it can be downright terrifying.
+
+But that unrelenting and genuine surprise is the [very source of a community's richness][5], its sheer abundance. If a community is the nucleus of all those reactions that catalyze innovations and breakthroughs, then unpredictability and serendipity are its fuel. I've learned to appreciate it—more accurately, perhaps, to stand in awe of it. Four years ago, when the Opensource.com team heeded [Jim Whitehurst's call][6] to build a space for others to "share your thoughts and opinions… on how you think we can all lead and work better in the future" (see the final page of _The Open Organization_ ), we had little more than a mandate, a platform, and a vision. We'd be an open organization [committed to studying, learning from, and propagating open organizations][7]. The rest was a surprise—or rather, a series of surprises:
+
+ * [Hundreds of articles, reviews, guides, and tutorials][2] on infusing open principles into organizations of all sizes across industries
+ * [A book series][8] spanning five volumes (with [another currently in production][9])
+ * A detailed, comprehensive, community-maintained [definition of the "open organization" concept][10]
+ * A [robust maturity model][11] for anyone seeking to understand how that definition might (or might not) support their own work
+
+
+
+All of that—everything you see there, [and more][12]—is the work of a community that never stopped conversing, never ceased creating, never failed to outsmart itself. No one could have predicted it. No one could have [planned for it][13]. We simply do our best to keep up with it.
+
+And after four years the work continues, more focused and impassioned than ever. Remaining involved with this bunch of writers, educators, consultants, coaches, leaders, and mentors—all united by their belief that openness is the surest source of hope for organizations struggling to address the challenges of our age—has made me appreciate the power of the utterly surprising. I'm even getting a little more comfortable with it.
+
+That's been its gift to me. But the gifts it has given each of its participants have been equally special.
+
+As we celebrate four years of challenges, collaboration, and camaraderie this week, let's recount those surprising gifts by hearing from some of the members:
+
+* * *
+
+Four years of the open organization community—congratulations to all!
+
+My first thought was to look at the five most-read articles over the past four years. Here they are:
+
+ * [5 laws every aspiring DevOps engineer should know][14]
+ * [What value do you bring to your company?][15]
+ * [8 answers to management questions from an open point of view][16]
+ * [What to do when you're feeling underutilized][17]
+ * [What's the point of DevOps?][18]
+
+
+
+All great articles. And then I started to think: Of all the great content over the past four years, which articles have impacted me the most?
+
+I remembered reading several great articles about meetings and how to make them more effective. So I typed "opensource.com meetings" into my search engine, and these two wonderful articles were at the top of the results list:
+
+ * [The secret to better one-on-one meetings][19]
+ * [Time to rethink your team's approach to meetings][20]
+
+
+
+Articles like that have inspired my favorite open organization management principle, which I've tried to apply and has made a huge difference: All meetings are optional.
+
+**—Jeff Mackanic, senior director, Marketing, Red Hat**
+
+* * *
+
+Being a member of the "open community" has reminded me of the power of getting things done via values and shared purpose without command and control—something that seems more important than ever in today's fragmented and often abusive management world, and at a time when truth and transparency themselves are under attack.
+
+Four years is a long journey for this kind of initiative—but there's still so much to learn and understand about what makes "open" work and what it will take to accelerate the embrace of its principles more widely through different domains of work and society. Congratulations on all you, your colleagues, partners, and other members of the community have done thus far!
+
+**—Brook Manville, Principal, Brook Manville LLC, author of _A Company of Citizens_ and co-author of _The Harvard Business Review Leader's Handbook_**
+
+* * *
+
+The Open Organization Ambassador program has, in the last four years, become an inspired community of experts. We have defined what it means to be a truly open organization. We've written books, guides, articles, and other resources for learning about, understanding, and implementing open principles. We've done this while bringing open principles to other communities, and we've done this together.
+
+For me, personally and professionally, the togetherness is the best part of this endeavor. I have learned so much from my colleagues. I'm absolutely ecstatic to be one of the idealists and activists in this community—committed to making our workplaces more equitable and open.
+
+**—Laura Hilliger, co-founder, We Are Open Co-Op, and[Open Organization Ambassador][21]**
+
+* * *
+
+Finding the open organization community opened me up to knowing that there are others out there who thought as I did. I wasn't alone. My ideas on leadership and the workplace were not crazy. This sense of belonging increased once I joined the Ambassador team. Our monthly meetings are never long enough. I don't like when we have to hang up because each session is full of laughter, sharpening each other, idea exchange, and joy. Humans seek community. We search for people who share values and ideals as we do but who also push back and help us expand. This is the gift of the open organization community—expansion, growth, and lifelong friendships. Thank you to all of those who contribute their time, intellect, content, and whole self to this awesome think tank that is changing the shape of how we organize to solve problems!
+
+**—Jen Kelchner, founder and Chief Change Architect, LDR21, and[Open Organization Ambassador][21]**
+
+* * *
+
+Happy fourth birthday, open organization community! Thank you for being an ever-present reminder in my life that being open is better than being closed, that listening is more fruitful than telling, and that together we can achieve more.
+
+**—Michael Doyle, professional coach and[Open Organization Ambassador][21]**
+
+* * *
+
+Wow, what a journey it's been exploring the world of open organizations. We're seeing more interest now than ever before. It's amazing to see what this community has done and I'm excited to see what the future holds for open organizations and open leadership.
+
+**—Jason Hibbets, senior community architect, Red Hat**
+
+--------------------------------------------------------------------------------
+
+via: https://opensource.com/open-organization/19/6/four-year-celebration
+
+作者:[Bryan Behrenshausen][a]
+选题:[lujun9972][b]
+译者:[译者ID](https://github.com/译者ID)
+校对:[校对者ID](https://github.com/校对者ID)
+
+本文由 [LCTT](https://github.com/LCTT/TranslateProject) 原创编译,[Linux中国](https://linux.cn/) 荣誉推出
+
+[a]: https://opensource.com/users/bbehrens
+[b]: https://github.com/lujun9972
+[1]: https://opensource.com/sites/default/files/styles/image-full-size/public/lead-images/happy_birthday_anniversary_celebrate_hats_cake.jpg?itok=Zfsv6DE_ (Browser window with birthday hats and a cake)
+[2]: https://opensource.com/open-organization
+[3]: https://opensource.com/open-organization/15/5/introducing-open-organization
+[4]: https://opensource.com/open-organization/18/11/design-communities-personality-types
+[5]: https://opensource.com/open-organization/18/1/why-build-community-1
+[6]: https://www.redhat.com/en/explore/the-open-organization-book
+[7]: https://opensource.com/open-organization/resources/ambassadors-program
+[8]: https://opensource.com/open-organization/resources/book-series
+[9]: https://opensource.com/open-organization/19/5/educators-guide-project
+[10]: https://opensource.com/open-organization/resources/open-org-definition
+[11]: https://opensource.com/open-organization/resources/open-org-maturity-model
+[12]: https://opensource.com/open-organization/resources
+[13]: https://opensource.com/open-organization/19/2/3-misconceptions-agile
+[14]: https://opensource.com/open-organization/17/5/5-devops-laws
+[15]: https://opensource.com/open-organization/15/7/what-value-do-you-bring-your-company
+[16]: https://opensource.com/open-organization/16/5/open-questions-and-answers-about-open-management
+[17]: https://opensource.com/open-organization/17/4/feeling-underutilized
+[18]: https://opensource.com/open-organization/17/5/what-is-the-point-of-DevOps
+[19]: https://opensource.com/open-organization/18/5/open-one-on-one-meetings-guide
+[20]: https://opensource.com/open-organization/18/3/open-approaches-meetings
+[21]: https://opensource.com/open-organization/resources/meet-ambassadors
diff --git a/sources/tech/20190604 Create a CentOS homelab in an hour.md b/sources/tech/20190604 Create a CentOS homelab in an hour.md
new file mode 100644
index 0000000000..039af752db
--- /dev/null
+++ b/sources/tech/20190604 Create a CentOS homelab in an hour.md
@@ -0,0 +1,224 @@
+[#]: collector: (lujun9972)
+[#]: translator: ( )
+[#]: reviewer: ( )
+[#]: publisher: ( )
+[#]: url: ( )
+[#]: subject: (Create a CentOS homelab in an hour)
+[#]: via: (https://opensource.com/article/19/6/create-centos-homelab-hour)
+[#]: author: (Bob Murphy https://opensource.com/users/murph)
+
+Create a CentOS homelab in an hour
+======
+Set up a self-sustained set of basic Linux servers with nothing more
+than a system with virtualization software, a CentOS ISO, and about an
+hour of your time.
+![metrics and data shown on a computer screen][1]
+
+When working on new Linux skills (or, as I was, studying for a Linux certification), it is helpful to have a few virtual machines (VMs) available on your laptop so you can do some learning on the go.
+
+But what happens if you are working somewhere without a good internet connection and you want to work on a web server? What about using other software that you don't already have installed? If you were depending on downloading it from the distribution's repositories, you may be out of luck. With a bit of preparation, you can set up a [homelab][2] that will allow you to install anything you need wherever you are, with or without a network connection.
+
+The requirements are:
+
+ * A downloaded ISO file of the Linux distribution you intend to use (for example, CentOS, Red Hat, etc.)
+ * A host computer with virtualization. I use [Fedora][3] with [KVM][4] and [virt-manager][5], but any Linux will work similarly. You could even use Windows or Mac with virtualization, with some difference in implementation
+ * About an hour of time
+
+
+
+### 1\. Create a VM for your repo host
+
+Use virt-manager to create a VM with modest specs; 1GB RAM, one CPU, and 16GB of disk space are plenty.
+
+Install [CentOS 7][6] on the VM.
+
+![Installing a CentOS homelab][7]
+
+Select your language and continue.
+
+Click _Installation Destination_ , select your local disk, mark the _Automatically Configure Partitioning_ checkbox, and click *Done *in the upper-left corner.
+
+Under _Software Selection_ , select _Infrastructure Server_ , mark the _FTP Server_ checkbox, and click _Done_.
+
+![Installing a CentOS homelab][8]
+
+Select _Network and Host Name_ , enable Ethernet in the upper-right, then click _Done_ in the upper-left corner.
+
+Click _Begin Installation_ to start installing the OS.
+
+You must create a root password, then you can create a user with a password as it installs.
+
+### 2\. Start the FTP service
+
+The next step is to start and set the FTP service to run and allow it through the firewall.
+
+Log in with your root password, then start the FTP server:
+
+
+```
+`systemctl start vsftpd`
+```
+
+Enable it to work on every start:
+
+
+```
+`systemctl enable vsftpd`
+```
+
+Set the port as allowed through the firewall:
+
+
+```
+`firewall-cmd --add-service=ftp --perm`
+```
+
+Enable this change immediately:
+
+
+```
+`firewall-cmd --reload`
+```
+
+Get your IP address:
+
+
+```
+`ip a`
+```
+
+(it's probably **eth0** ). You'll need it in a minute.
+
+### 3\. Copy the files for your local repository
+
+Mount the CD you installed from to your VM through your virtualization software.
+
+Create a directory for the CD to be mounted to temporarily:
+
+
+```
+`mkdir /root/temp`
+```
+
+Mount the install CD:
+
+
+```
+`mount /dev/cdrom /root/temp`
+```
+
+Copy all the files to the FTP server directory:
+
+
+```
+`rsync -avhP /root/temp/ /var/ftp/pub/`
+```
+
+### 4\. Point the server to the local repository
+
+Red Hat-based systems use files that end in **.repo** to identify where to get updates and new software. Those files can be found at
+
+
+```
+`cd /etc/yum.repos.d`
+```
+
+You need to get rid of the repo files that point your server to look to the CentOS repositories on the internet. I prefer to copy them to root's home directory to get them out of the way:
+
+
+```
+`mv * ~`
+```
+
+Then create a new repo file to point to your server. Use your favorite text editor to create a file named **network.repo** with the following lines (substituting the IP address you got in step 2 for _< your IP>_), then save it:
+
+
+```
+[network]
+name=network
+baseurl=/pub
+gpgcheck=0
+```
+
+When that's done, we can test it out with the following:
+
+
+```
+`yum clean all; yum install ftp`
+```
+
+If your FTP client installs as expected from the "network" repository, your local repo is set up!
+
+![Installing a CentOS homelab][9]
+
+### 5\. Install a new VM with the repository you set up
+
+Go back to the virtual machine manager, and create another VM—but this time, select _Network Install_ with a URL of:
+
+
+```
+`ftp://192.168.122./pub`
+```
+
+If you're using a different host OS or virtualization manager, install your VM similarly as before, and skip to the next section.
+
+### 6\. Set the new VM to use your existing network repository
+
+You can copy the repo file from your existing server to use here.
+
+As in the first server example, enter:
+
+
+```
+cd /etc/yum.repos.d
+mv * ~
+```
+
+Then:
+
+
+```
+`scp root@192.168.122.:/etc/yum.repos.d/network.repo /etc/yum.repos.d`
+```
+
+Now you should be ready to work with your new VM and get all your software from your local repository.
+
+Test this again:
+
+
+```
+`yum clean all; yum install screen`
+```
+
+This will install your software from your local repo server.
+
+This setup, which gives you independence from the network with the ability to install software, can create a much more dependable environment for expanding your skills on the road.
+
+* * *
+
+_Bob Murphy will present this topic as well as an introduction to[GNU Screen][10] at [Southeast Linux Fest][11], June 15-16 in Charlotte, N.C._
+
+--------------------------------------------------------------------------------
+
+via: https://opensource.com/article/19/6/create-centos-homelab-hour
+
+作者:[Bob Murphy][a]
+选题:[lujun9972][b]
+译者:[译者ID](https://github.com/译者ID)
+校对:[校对者ID](https://github.com/校对者ID)
+
+本文由 [LCTT](https://github.com/LCTT/TranslateProject) 原创编译,[Linux中国](https://linux.cn/) 荣誉推出
+
+[a]: https://opensource.com/users/murph
+[b]: https://github.com/lujun9972
+[1]: https://opensource.com/sites/default/files/styles/image-full-size/public/lead-images/metrics_data_dashboard_system_computer_analytics.png?itok=oxAeIEI- (metrics and data shown on a computer screen)
+[2]: https://opensource.com/article/19/3/home-lab
+[3]: https://getfedora.org/
+[4]: https://en.wikipedia.org/wiki/Kernel-based_Virtual_Machine
+[5]: https://virt-manager.org/
+[6]: https://www.centos.org/download/
+[7]: https://opensource.com/sites/default/files/uploads/homelab-3b_0.png (Installing a CentOS homelab)
+[8]: https://opensource.com/sites/default/files/uploads/homelab-5b.png (Installing a CentOS homelab)
+[9]: https://opensource.com/sites/default/files/uploads/homelab-14b.png (Installing a CentOS homelab)
+[10]: https://opensource.com/article/17/3/introduction-gnu-screen
+[11]: https://southeastlinuxfest.org/
diff --git a/sources/tech/20190604 ExamSnap Guide- 6 Excellent Resources for Microsoft 98-366- Networking Fundamentals Exam.md b/sources/tech/20190604 ExamSnap Guide- 6 Excellent Resources for Microsoft 98-366- Networking Fundamentals Exam.md
new file mode 100644
index 0000000000..97414f530f
--- /dev/null
+++ b/sources/tech/20190604 ExamSnap Guide- 6 Excellent Resources for Microsoft 98-366- Networking Fundamentals Exam.md
@@ -0,0 +1,103 @@
+[#]: collector: (lujun9972)
+[#]: translator: ( )
+[#]: reviewer: ( )
+[#]: publisher: ( )
+[#]: url: ( )
+[#]: subject: (ExamSnap Guide: 6 Excellent Resources for Microsoft 98-366: Networking Fundamentals Exam)
+[#]: via: (https://www.2daygeek.com/examsnap-guide-6-excellent-resources-for-microsoft-98-366-networking-fundamentals-exam/)
+[#]: author: (2daygeek http://www.2daygeek.com/author/2daygeek/)
+
+ExamSnap Guide: 6 Excellent Resources for Microsoft 98-366: Networking Fundamentals Exam
+======
+
+The Microsoft 98-366 exam is almost similar to the CompTIA Network+ certification test when it comes to its content.
+
+It is also known as Networking Fundamentals, and its purpose is to assess your knowledge of switches, routers, OSI models, wide area and local area networks, wireless networking, and IP addressing.
+
+Those who pass the exam earn the MTA (Microsoft Technology Associate) certificate. This certifications an ideal entry-level credential to help you begin your IT career.
+
+### 6 Resources for Microsoft MTA 98-366 Exam
+
+Using approved training materials is the best method to prepare for your certification exam. Most candidates are fond of shortcuts and often use PDFs and brain dumps to prepare for the test.
+
+It is important to note that these materials need additional study methods. They will not help you gain better knowledge that is meant to make you perform better at work.
+
+When you take your time to master the course contents of a certification exam, you are not only getting ready for the test but also developing your skills, expertise, and knowledge in the topics covered there.
+
+ * **[ExamSnap][1]**
+
+
+
+Another important point to note is that you shouldn’t rely only on brain dumps. Microsoft can withhold or withdraw your certification if it is discovered that you have cheated.
+
+This may also result in the situation when a person is not allowed to earn the credentials any more. Thus, use only verified platforms such as Examsnap.
+
+Most people tend to believe that there is no way they can get discovered. However, you need to know that Microsoft has been offering professional certification exams for years and they know what they are doing.
+
+Now when we have established the importance of using legal materials to prepare for your certification exam, we need to highlight the top resources you can use to prepare for the Microsoft 98-366 test.
+
+### 1\. Microsoft Video Academy
+
+The MVA (Microsoft Video Academy) provides you with introductory lessons on the 98-366 certification exam.This is not sufficient for your study although it is a great way to begin your preparation for the test. The materials in the video do not cover everything you need to know before taking the exam.
+
+In fact, it is introductory series that is meant to lay down the foundation for your study. You will have to explore other materials for you to get an in-depth knowledge of the topics.
+
+These videos are available without payment, so you can easily access them and use whenever you want.
+
+ * [Microsoft Certification Overview][2]
+
+
+
+### 2\. Examsnap
+
+If you have been looking for material that can help you prepare for the Microsoft Networking Fundamentals exam, look no further because you will know about Examsnap now.
+
+It is an online platform that provides you with exam dumps and video series of various certification courses. All you need to do is to register on the website and pay a fee for you to be able to access various tools that will help you prepare for the test.
+
+Examsnap will enable you to pass your exams with confidence by providing you with the most accurate and comprehensive preparation materials on the Internet. The platform also has training courses to help you improve your study.
+
+Before making any payment on the site, you can complete the trial course to establish whether the site is suitable for your exam preparation needs.
+
+### 3\. Exam 98-366: MTA Networking Fundamentals
+
+This is a study resource that is a book. It provides you with a comprehensive approach to the various topics. It is important for you to note that this study guide is critical to your success.
+
+It offers you more detailed material than the introductory lectures by the MVA. It is advisable that you do not focus on the sample questions in each part when using this book.
+
+You should not concentrate on the sample questions because they are not so informative. You can make up for this shortcoming by checking out other practice test options. Overall, this book is a top resource that will contribute greatly to your certification exam success.
+
+### 4\. Measure-Up
+
+Measure-Up is the official Microsoft practice test provider whereby you can access different materials. You can get a lab and hands-on practice with networking software tools, which are very beneficial for your preparation. The site also has study questions that you can purchase.
+
+### 5\. U-Certify
+
+The U-Certify platform is a reputable organization that offers video courses that are considered to be more understandable than those offered by the MVA. In addition to video courses, the site presents flashcards at the end of the videos.
+
+You can also access a series of practice tests, which contain several hundreds of study questions on the platform. There are more contents in videos and tests that you can access the moment you subscribe. Depending on what you are looking for, you can choose to buy the tests or the videos.
+
+### 6\. Networking Essentials – Wiki
+
+There are several posts that are linked to the Networking Essentials page on Wiki, and you can be sure that these articles are greatly detailed with information that will be helpful for your exam preparation.
+
+It is important to note that they are not meant to be studied as the only resource materials. You should only use them as additional means for the purpose of getting more information on specific topics but not as an individual study tool.
+
+### Conclusion
+
+You may not be able to access all the top resources available. However, you can access some of them. In addition to the resources mentioned, there are also some others that are very good. Visit the Microsoft official website to get the list of reliable resource platforms you can use. Study and be well-prepared for the 98-366 certification exam!
+
+--------------------------------------------------------------------------------
+
+via: https://www.2daygeek.com/examsnap-guide-6-excellent-resources-for-microsoft-98-366-networking-fundamentals-exam/
+
+作者:[2daygeek][a]
+选题:[lujun9972][b]
+译者:[译者ID](https://github.com/译者ID)
+校对:[校对者ID](https://github.com/校对者ID)
+
+本文由 [LCTT](https://github.com/LCTT/TranslateProject) 原创编译,[Linux中国](https://linux.cn/) 荣誉推出
+
+[a]: http://www.2daygeek.com/author/2daygeek/
+[b]: https://github.com/lujun9972
+[1]: https://www.examsnap.com/
+[2]: https://www.microsoft.com/en-us/learning/certification-overview.aspx
diff --git a/sources/tech/20190604 Four Ways To Install Security Updates On Red Hat (RHEL) And CentOS Systems.md b/sources/tech/20190604 Four Ways To Install Security Updates On Red Hat (RHEL) And CentOS Systems.md
new file mode 100644
index 0000000000..ebe841dbcb
--- /dev/null
+++ b/sources/tech/20190604 Four Ways To Install Security Updates On Red Hat (RHEL) And CentOS Systems.md
@@ -0,0 +1,174 @@
+[#]: collector: (lujun9972)
+[#]: translator: ( )
+[#]: reviewer: ( )
+[#]: publisher: ( )
+[#]: url: ( )
+[#]: subject: (Four Ways To Install Security Updates On Red Hat (RHEL) And CentOS Systems?)
+[#]: via: (https://www.2daygeek.com/install-security-updates-on-redhat-rhel-centos-system/)
+[#]: author: (Magesh Maruthamuthu https://www.2daygeek.com/author/magesh/)
+
+Four Ways To Install Security Updates On Red Hat (RHEL) And CentOS Systems?
+======
+
+Patching of the Linux server is one of important and routine task of Linux admin.
+
+Keeping the system with latest patch level is must. It protects your system against unnecessary attack.
+
+There are three kind of erratas available in the RHEL/CentOS repository, these are Security, Bug Fix and Product Enhancement.
+
+Now, you have two options to handle this.
+
+Either install only security updates or all the errata packages.
+
+We have already written an article in the past **[to check available security updates?][1]**.
+
+Also, **[check the installed security updates on your system][2]** using this link.
+
+You can navigate to the above link, if you would like to verify available security updates before installing them.
+
+In this article, we will show your, how to install security updates in multiple ways on RHEL and CentOS system.
+
+### 1) How To Install Entire Errata Updates In Red Hat And CentOS System?
+
+Run the following command to download and apply all available security updates on your system.
+
+Make a note, this command will install the last available version of any package with at least one security errata.
+
+Also, install non-security erratas if they provide a more updated version of the package.
+
+```
+# yum update --security
+
+Loaded plugins: changelog, package_upload, product-id, search-disabled-repos, subscription-manager, verify, versionlock
+RHEL7-Server-DVD | 4.3 kB 00:00:00
+rhel-7-server-rpms | 2.0 kB 00:00:00
+--> 1:grub2-tools-extra-2.02-0.76.el7.1.x86_64 from rhel-7-server-rpms removed (updateinfo)
+--> nss-pem-1.0.3-5.el7_6.1.x86_64 from rhel-7-server-rpms removed (updateinfo)
+.
+35 package(s) needed (+0 related) for security, out of 115 available
+Resolving Dependencies
+--> Running transaction check
+---> Package NetworkManager.x86_64 1:1.12.0-6.el7 will be updated
+---> Package NetworkManager.x86_64 1:1.12.0-10.el7_6 will be an update
+```
+
+Once you ran the above command, it will check all the available updates and its dependency satisfaction.
+
+```
+--> Finished Dependency Resolution
+--> Running transaction check
+---> Package kernel.x86_64 0:3.10.0-514.26.1.el7 will be erased
+---> Package kernel-devel.x86_64 0:3.10.0-514.26.1.el7 will be erased
+--> Finished Dependency Resolution
+
+Dependencies Resolved
+=====================================================================================================================================================================
+Package Arch Version Repository Size
+=====================================================================================================================================================================
+Installing:
+kernel x86_64 3.10.0-957.10.1.el7 rhel-7-server-rpms 48 M
+kernel-devel x86_64 3.10.0-957.10.1.el7 rhel-7-server-rpms 17 M
+Updating:
+NetworkManager x86_64 1:1.12.0-10.el7_6 rhel-7-server-rpms 1.7 M
+NetworkManager-adsl x86_64 1:1.12.0-10.el7_6 rhel-7-server-rpms 157 k
+.
+Removing:
+kernel x86_64 3.10.0-514.26.1.el7 @rhel-7-server-rpms 148 M
+kernel-devel x86_64 3.10.0-514.26.1.el7 @rhel-7-server-rpms 34 M
+```
+
+If these dependencies were satisfied, which finally gives you a total summary about it.
+
+The transaction summary shows, how many packages will be getting Installed, upgraded and removed from the system.
+
+```
+Transaction Summary
+=====================================================================================================================================================================
+Install 2 Packages
+Upgrade 33 Packages
+Remove 2 Packages
+
+Total download size: 124 M
+Is this ok [y/d/N]:
+```
+
+### How To Install Only Security Updates In Red Hat And CentOS System?
+
+Run the following command to install only the packages that have a security errata.
+
+```
+# yum update-minimal --security
+
+Loaded plugins: changelog, package_upload, product-id, search-disabled-repos, subscription-manager, verify, versionlock
+rhel-7-server-rpms | 2.0 kB 00:00:00
+Resolving Dependencies
+--> Running transaction check
+---> Package NetworkManager.x86_64 1:1.12.0-6.el7 will be updated
+---> Package NetworkManager.x86_64 1:1.12.0-8.el7_6 will be an update
+.
+--> Finished Dependency Resolution
+--> Running transaction check
+---> Package kernel.x86_64 0:3.10.0-514.26.1.el7 will be erased
+---> Package kernel-devel.x86_64 0:3.10.0-514.26.1.el7 will be erased
+--> Finished Dependency Resolution
+
+Dependencies Resolved
+=====================================================================================================================================================================
+Package Arch Version Repository Size
+=====================================================================================================================================================================
+Installing:
+kernel x86_64 3.10.0-957.10.1.el7 rhel-7-server-rpms 48 M
+kernel-devel x86_64 3.10.0-957.10.1.el7 rhel-7-server-rpms 17 M
+Updating:
+NetworkManager x86_64 1:1.12.0-8.el7_6 rhel-7-server-rpms 1.7 M
+NetworkManager-adsl x86_64 1:1.12.0-8.el7_6 rhel-7-server-rpms 157 k
+.
+Removing:
+kernel x86_64 3.10.0-514.26.1.el7 @rhel-7-server-rpms 148 M
+kernel-devel x86_64 3.10.0-514.26.1.el7 @rhel-7-server-rpms 34 M
+
+Transaction Summary
+=====================================================================================================================================================================
+Install 2 Packages
+Upgrade 33 Packages
+Remove 2 Packages
+
+Total download size: 124 M
+Is this ok [y/d/N]:
+```
+
+### How To Install Security Update Using CVE reference In Red Hat And CentOS System?
+
+If you would like to install a security update using a CVE reference, run the following command.
+
+```
+# yum update --cve
+
+# yum update --cve CVE-2008-0947
+```
+
+### How To Install Security Update Using Specific Advisory In Red Hat And CentOS System?
+
+Run the following command, if you want to apply only a specific advisory.
+
+```
+# yum update --advisory=
+
+# yum update --advisory=RHSA-2014:0159
+```
+
+--------------------------------------------------------------------------------
+
+via: https://www.2daygeek.com/install-security-updates-on-redhat-rhel-centos-system/
+
+作者:[Magesh Maruthamuthu][a]
+选题:[lujun9972][b]
+译者:[译者ID](https://github.com/译者ID)
+校对:[校对者ID](https://github.com/校对者ID)
+
+本文由 [LCTT](https://github.com/LCTT/TranslateProject) 原创编译,[Linux中国](https://linux.cn/) 荣誉推出
+
+[a]: https://www.2daygeek.com/author/magesh/
+[b]: https://github.com/lujun9972
+[1]: https://www.2daygeek.com/check-list-view-find-available-security-updates-on-redhat-rhel-centos-system/
+[2]: https://www.2daygeek.com/check-installed-security-updates-on-redhat-rhel-and-centos-system/
diff --git a/sources/tech/20190604 Linux Shell Script To Monitor CPU Utilization And Send Email.md b/sources/tech/20190604 Linux Shell Script To Monitor CPU Utilization And Send Email.md
new file mode 100644
index 0000000000..f1cb86573b
--- /dev/null
+++ b/sources/tech/20190604 Linux Shell Script To Monitor CPU Utilization And Send Email.md
@@ -0,0 +1,178 @@
+[#]: collector: (lujun9972)
+[#]: translator: ( )
+[#]: reviewer: ( )
+[#]: publisher: ( )
+[#]: url: ( )
+[#]: subject: (Linux Shell Script To Monitor CPU Utilization And Send Email)
+[#]: via: (https://www.2daygeek.com/linux-shell-script-to-monitor-cpu-utilization-usage-and-send-email/)
+[#]: author: (Magesh Maruthamuthu https://www.2daygeek.com/author/magesh/)
+
+Linux Shell Script To Monitor CPU Utilization And Send Email
+======
+
+There are many opensource monitoring tools are available to monitor Linux systems performance.
+
+It will send an email alert when the system reaches the given threshold limit.
+
+It monitors everything such as CPU utilization, Memory utilization, swap utilization, disk space utilization and much more.
+
+If you only have few systems and want to monitor them then writing a small shell script can achieve this.
+
+In this tutorial we have added two shell script to monitor CPU utilization on Linux system.
+
+When the system reaches the given threshold then it will trigger a mail to corresponding email id.
+
+### Method-1 : Linux Shell Script To Monitor CPU Utilization And Send an Email
+
+If you want to only get CPU utilization percentage through mail when the system reaches the given threshold, use the following script.
+
+This is very simple and straightforward and one line script.
+
+It will trigger an email when your system reaches `80%` CPU utilization.
+
+```
+*/5 * * * * /usr/bin/cat /proc/loadavg | awk '{print $1}' | awk '{ if($1 > 80) printf("Current CPU Utilization is: %.2f%\n"), $0;}' | mail -s "High CPU Alert" [email protected]
+```
+
+**Note:** You need to change the email id instead of ours. Also, you can change the CPU utilization threshold value as per your requirement.
+
+**Output:** You will be getting an email alert similar to below.
+
+```
+Current CPU Utilization is: 80.40%
+```
+
+We had added many useful shell scripts in the past. If you want to check those, navigate to the below link.
+
+ * **[How to automate day to day activities using shell scripts?][1]**
+
+
+
+### Method-2 : Linux Shell Script To Monitor CPU Utilization And Send an Email
+
+If you want to get more information about the CPU utilization in the mail alert.
+
+Then use the following script, which includes top CPU utilization process details based on the top Command and ps Command.
+
+This will inconstantly gives you an idea what is going on your system.
+
+It will trigger an email when your system reaches `80%` CPU utilization.
+
+**Note:** You need to change the email id instead of ours. Also, you can change the CPU utilization threshold value as per your requirement.
+
+```
+# vi /opt/scripts/cpu-alert.sh
+
+#!/bin/bash
+cpuuse=$(cat /proc/loadavg | awk '{print $1}')
+
+if [ "$cpuuse" > 80 ]; then
+
+SUBJECT="ATTENTION: CPU Load Is High on $(hostname) at $(date)"
+
+MESSAGE="/tmp/Mail.out"
+
+TO="[email protected]"
+
+ echo "CPU Current Usage is: $cpuuse%" >> $MESSAGE
+
+ echo "" >> $MESSAGE
+
+ echo "+------------------------------------------------------------------+" >> $MESSAGE
+
+ echo "Top CPU Process Using top command" >> $MESSAGE
+
+ echo "+------------------------------------------------------------------+" >> $MESSAGE
+
+ echo "$(top -bn1 | head -20)" >> $MESSAGE
+
+ echo "" >> $MESSAGE
+
+ echo "+------------------------------------------------------------------+" >> $MESSAGE
+
+ echo "Top CPU Process Using ps command" >> $MESSAGE
+
+ echo "+------------------------------------------------------------------+" >> $MESSAGE
+
+ echo "$(ps -eo pcpu,pid,user,args | sort -k 1 -r | head -10)" >> $MESSAGE
+
+ mail -s "$SUBJECT" "$TO" < $MESSAGE
+
+ rm /tmp/Mail.out
+
+ fi
+```
+
+Finally add a **[cronjob][2]** to automate this. It will run every 5 minutes.
+
+```
+# crontab -e
+*/10 * * * * /bin/bash /opt/scripts/cpu-alert.sh
+```
+
+**Note:** You will be getting an email alert 5 mins later since the script has scheduled to run every 5 minutes (But it's not exactly 5 mins and it depends the timing).
+
+Say for example. If your system reaches the limit at 8.25 then you will get an email alert in another 5 mins. Hope it's clear now.
+
+**Output:** You will be getting an email alert similar to below.
+
+```
+CPU Current Usage is: 80.51%
+
++------------------------------------------------------------------+
+Top CPU Process Using top command
++------------------------------------------------------------------+
+top - 13:23:01 up 1:43, 1 user, load average: 2.58, 2.58, 1.51
+Tasks: 306 total, 3 running, 303 sleeping, 0 stopped, 0 zombie
+%Cpu0 : 6.2 us, 6.2 sy, 0.0 ni, 87.5 id, 0.0 wa, 0.0 hi, 0.0 si, 0.0 st
+%Cpu1 : 18.8 us, 0.0 sy, 0.0 ni, 81.2 id, 0.0 wa, 0.0 hi, 0.0 si, 0.0 st
+%Cpu2 : 50.0 us, 37.5 sy, 0.0 ni, 12.5 id, 0.0 wa, 0.0 hi, 0.0 si, 0.0 st
+%Cpu3 : 5.9 us, 5.9 sy, 0.0 ni, 88.2 id, 0.0 wa, 0.0 hi, 0.0 si, 0.0 st
+%Cpu4 : 0.0 us, 5.9 sy, 0.0 ni, 94.1 id, 0.0 wa, 0.0 hi, 0.0 si, 0.0 st
+%Cpu5 : 29.4 us, 23.5 sy, 0.0 ni, 47.1 id, 0.0 wa, 0.0 hi, 0.0 si, 0.0 st
+%Cpu6 : 0.0 us, 5.9 sy, 0.0 ni, 94.1 id, 0.0 wa, 0.0 hi, 0.0 si, 0.0 st
+%Cpu7 : 5.9 us, 0.0 sy, 0.0 ni, 94.1 id, 0.0 wa, 0.0 hi, 0.0 si, 0.0 st
+KiB Mem : 16248588 total, 223436 free, 5816924 used, 10208228 buff/cache
+KiB Swap: 17873388 total, 17871340 free, 2048 used. 7440884 avail Mem
+
+ PID USER PR NI VIRT RES SHR S %CPU %MEM TIME+ COMMAND
+ 8867 daygeek 20 2743884 440420 360952 R 100.0 2.7 1:07.25 /usr/lib/virtualbox/VirtualBoxVM --comment CentOS7 --startvm 002f47b8-2af2-48f5-be1d-67b67e03514c --no-startvm-errormsgbox
+ 9119 daygeek 20 36136 784 R 46.7 0.0 0:00.07 /usr/bin/CROND -n
+ 1057 daygeek 20 889808 487692 461692 S 13.3 3.0 4:21.12 /usr/lib/Xorg vt2 -displayfd 3 -auth /run/user/1000/gdm/Xauthority -nolisten tcp -background none -noreset -keeptty -verbose 3
+ 3098 daygeek 20 1929012 351412 120532 S 13.3 2.2 16:42.51 /usr/lib/firefox/firefox -contentproc -childID 6 -isForBrowser -prefsLen 9236 -prefMapSize 184485 -parentBuildID 20190521202118 -greomni /us+
+ 1 root 20 188820 10144 7708 S 6.7 0.1 0:06.92 /sbin/init
+ 818 gdm 20 199836 25120 15876 S 6.7 0.2 0:01.85 /usr/lib/Xorg vt1 -displayfd 3 -auth /run/user/120/gdm/Xauthority -nolisten tcp -background none -noreset -keeptty -verbose 3
+ 1170 daygeek 9 -11 2676516 16516 12520 S 6.7 0.1 1:28.30 /usr/bin/pulseaudio --daemonize=no
+ 8271 root 20 I 6.7 0:00.21 [kworker/u16:4-i915]
+ 9117 daygeek 20 13528 4036 3144 R 6.7 0.0 0:00.01 top -bn1
+
++------------------------------------------------------------------+
+Top CPU Process Using ps command
++------------------------------------------------------------------+
+%CPU PID USER COMMAND
+ 8.8 8522 daygeek /usr/lib/virtualbox/VirtualBox
+86.2 8867 daygeek /usr/lib/virtualbox/VirtualBoxVM --comment CentOS7 --startvm 002f47b8-2af2-48f5-be1d-67b67e03514c --no-startvm-errormsgbox
+76.1 8921 daygeek /usr/lib/virtualbox/VirtualBoxVM --comment Ubuntu-18.04 --startvm e8c32dbb-8b01-41b0-977a-bf28b9db1117 --no-startvm-errormsgbox
+ 5.5 8080 daygeek /usr/bin/nautilus --gapplication-service
+ 4.7 4575 daygeek /usr/lib/firefox/firefox -contentproc -childID 12 -isForBrowser -prefsLen 9375 -prefMapSize 184485 -parentBuildID 20190521202118 -greomni /usr/lib/firefox/omni.ja -appomni /usr/lib/firefox/browser/omni.ja -appdir /usr/lib/firefox/browser 1525 true tab
+ 4.4 3511 daygeek /usr/lib/firefox/firefox -contentproc -childID 8 -isForBrowser -prefsLen 9308 -prefMapSize 184485 -parentBuildID 20190521202118 -greomni /usr/lib/firefox/omni.ja -appomni /usr/lib/firefox/browser/omni.ja -appdir /usr/lib/firefox/browser 1525 true tab
+ 4.4 3190 daygeek /usr/lib/firefox/firefox -contentproc -childID 7 -isForBrowser -prefsLen 9237 -prefMapSize 184485 -parentBuildID 20190521202118 -greomni /usr/lib/firefox/omni.ja -appomni /usr/lib/firefox/browser/omni.ja -appdir /usr/lib/firefox/browser 1525 true tab
+ 4.4 1612 daygeek /usr/lib/firefox/firefox -contentproc -childID 1 -isForBrowser -prefsLen 1 -prefMapSize 184485 -parentBuildID 20190521202118 -greomni /usr/lib/firefox/omni.ja -appomni /usr/lib/firefox/browser/omni.ja -appdir /usr/lib/firefox/browser 1525 true tab
+ 4.2 3565 daygeek /usr/bin/../lib/notepadqq/notepadqq-bin
+```
+
+--------------------------------------------------------------------------------
+
+via: https://www.2daygeek.com/linux-shell-script-to-monitor-cpu-utilization-usage-and-send-email/
+
+作者:[Magesh Maruthamuthu][a]
+选题:[lujun9972][b]
+译者:[译者ID](https://github.com/译者ID)
+校对:[校对者ID](https://github.com/校对者ID)
+
+本文由 [LCTT](https://github.com/LCTT/TranslateProject) 原创编译,[Linux中国](https://linux.cn/) 荣誉推出
+
+[a]: https://www.2daygeek.com/author/magesh/
+[b]: https://github.com/lujun9972
+[1]: https://www.2daygeek.com/category/shell-script/
+[2]: https://www.2daygeek.com/crontab-cronjob-to-schedule-jobs-in-linux/
diff --git a/sources/tech/20190605 Tweaking the look of Fedora Workstation with themes.md b/sources/tech/20190605 Tweaking the look of Fedora Workstation with themes.md
new file mode 100644
index 0000000000..441415925f
--- /dev/null
+++ b/sources/tech/20190605 Tweaking the look of Fedora Workstation with themes.md
@@ -0,0 +1,140 @@
+[#]: collector: (lujun9972)
+[#]: translator: ( )
+[#]: reviewer: ( )
+[#]: publisher: ( )
+[#]: url: ( )
+[#]: subject: (Tweaking the look of Fedora Workstation with themes)
+[#]: via: (https://fedoramagazine.org/tweaking-the-look-of-fedora-workstation-with-themes/)
+[#]: author: (Ryan Lerch https://fedoramagazine.org/author/ryanlerch/)
+
+Tweaking the look of Fedora Workstation with themes
+======
+
+![][1]
+
+Changing the theme of a desktop environment is a common way to customize your daily experience with Fedora Workstation. This article discusses the 4 different types of visual themes you can change and how to change to a new theme. Additionally, this article will cover how to install new themes from both the Fedora repositories and 3rd party theme sources.
+
+### Theme Types
+
+When changing the theme of Fedora Workstation, there are 4 different themes that can be changed independently of each other. This allows a user to mix and match the theme types to customize their desktop in a multitude of combinations. The 4 theme types are the **Application** (GTK) theme, the **shell** theme, the **icon** theme, and the **cursor** theme.
+
+#### Application (GTK) themes
+
+As the name suggests, Application themes change the styling of the applications that are displayed on a user’s desktop. Application themes control the style of the window borders and the window titlebar. Additionally, they also control the style of the widgets in the windows — like dropdowns, text inputs, and buttons. One point to note is that an application theme does not change the icons that are displayed in an application — this is achieved using the icon theme.
+
+![Two application windows with two different application themes. The default Adwaita theme on the left, the Adapta theme on the right.][2]
+
+Application themes are also known as GTK themes, as GTK ( **G** IMP **T** ool **k** it) is the underlying technology that is used to render the windows and user interface widgets in those windows on Fedora Workstation.
+
+#### Shell Themes
+
+Shell themes change the appearance of the GNOME Shell. The GNOME Shell is the technology that displays the top bar (and the associated widgets like drop downs), as well as the overview screen and the applications list it contains.
+
+![Comparison of two Shell themes, with the Fedora Workstation default on top, and the Adapta shell theme on the bottom.][3]
+
+#### Icon Themes
+
+As the name suggests, icon themes change the icons used in the desktop. Changing the icon theme will change the icons displayed both in the Shell, and in applications.
+
+![Comparison of two icon themes, with the Fedora 30 Workstation default Adwaita on the left, and the Yaru icon theme on the right][4]
+
+One important item to note with icon themes is that all icon themes will not have customized icons for all application icons. Consequently, changing the icon theme will not change all the icons in the applications list in the overview.
+
+![Comparison of two icon themes, with the Fedora 30 Workstation default Adwaita on the top, and the Yaru icon theme on the bottom][5]
+
+#### Cursor Theme
+
+The cursor theme allows a user to change how the mouse pointer is displayed. Most cursor themes change all the common cursors, including the pointer, drag handles and the loading cursor.
+
+![Comparison of multiple cursors of two different cursor themes. Fedora 30 default is on the left, the Breeze Snow theme on the right.][6]
+
+### Changing the themes
+
+Changing themes on Fedora Workstation is a simple process. To change all 4 types of themes, use the **Tweaks** application. Tweaks is a tool used to change a range of different options in Fedora Workstation. It is not installed by default, and is installed using the Software application:
+
+![][7]
+
+Alternatively, install Tweaks from the command line with the command:
+
+```
+sudo dnf install gnome-tweak-tool
+```
+
+In addition to Tweaks, to change the Shell theme, the **User Themes** GNOME Shell Extension needs to be installed and enabled. [Check out this post for more details on installing extensions][8].
+
+Next, launch Tweaks, and switch to the Appearance pane. The Themes section in the Appearance pane allows the changing of the multiple theme types. Simply choose the theme from the dropdown, and the new theme will apply automatically.
+
+![][9]
+
+### Installing themes
+
+Armed with the knowledge of the types of themes, and how to change themes, it is time to install some themes. Broadly speaking, there are two ways to install new themes to your Fedora Workstation — installing theme packages from the Fedora repositories, or manually installing a theme. One point to note when installing themes, is that you may need to close and re-open the Tweaks application to make a newly installed theme appear in the dropdowns.
+
+#### Installing from the Fedora repositories
+
+The Fedora repositories contain a small selection of additional themes that once installed are available to we chosen in Tweaks. Theme packages are not available in the Software application, and have to be searched for and installed via the command line. Most theme packages have a consistent naming structure, so listing available themes is pretty easy.
+
+To find Application (GTK) themes use the command:
+
+```
+dnf search gtk | grep theme
+```
+
+To find Shell themes:
+
+```
+dnf search shell-theme
+```
+
+Icon themes:
+
+```
+dnf search icon-theme
+```
+
+Cursor themes:
+
+```
+dnf search cursor-theme
+```
+
+Once you have found a theme to install, install the theme using dnf. For example:
+
+```
+sudo dnf install numix-gtk-theme
+```
+
+#### Installing themes manually
+
+For a wider range of themes, there are a plethora of places on the internet to find new themes to use on Fedora Workstation. Two popular places to find themes are [OpenDesktop][10] and [GNOMELook][11].
+
+Typically when downloading themes from these sites, the themes are encapsulated in an archive like a tar.gz or zip file. In most cases, to install these themes, simply extract the contents into the correct directory, and the theme will appear in Tweaks. Note too, that themes can be installed either globally (must be done using sudo) so all users on the system can use them, or can be installed just for the current user.
+
+For Application (GTK) themes, and GNOME Shell themes, extract the archive to the **.themes/** directory in your home directory. To install for all users, extract to **/usr/share/themes/**
+
+For Icon and Cursor themes, extract the archive to the **.icons/** directory in your home directory. To install for all users, extract to **/usr/share/icons/**
+
+--------------------------------------------------------------------------------
+
+via: https://fedoramagazine.org/tweaking-the-look-of-fedora-workstation-with-themes/
+
+作者:[Ryan Lerch][a]
+选题:[lujun9972][b]
+译者:[译者ID](https://github.com/译者ID)
+校对:[校对者ID](https://github.com/校对者ID)
+
+本文由 [LCTT](https://github.com/LCTT/TranslateProject) 原创编译,[Linux中国](https://linux.cn/) 荣誉推出
+
+[a]: https://fedoramagazine.org/author/ryanlerch/
+[b]: https://github.com/lujun9972
+[1]: https://fedoramagazine.org/wp-content/uploads/2019/06/themes.png-816x345.jpg
+[2]: https://fedoramagazine.org/wp-content/uploads/2019/06/application-theme-1024x514.jpg
+[3]: https://fedoramagazine.org/wp-content/uploads/2019/06/overview-theme-1024x649.jpg
+[4]: https://fedoramagazine.org/wp-content/uploads/2019/06/icon-theme-application-1024x441.jpg
+[5]: https://fedoramagazine.org/wp-content/uploads/2019/06/overview-icons-1024x637.jpg
+[6]: https://fedoramagazine.org/wp-content/uploads/2019/06/cursortheme-1024x467.jpg
+[7]: https://fedoramagazine.org/wp-content/uploads/2019/06/tweaks-in-software-1024x725.png
+[8]: https://fedoramagazine.org/install-extensions-via-software-application/
+[9]: https://fedoramagazine.org/wp-content/uploads/2019/06/tweaks-choose-themes.png
+[10]: https://www.opendesktop.org/
+[11]: https://www.gnome-look.org/
diff --git a/sources/tech/20190606 Examples of blameless culture outside of DevOps.md b/sources/tech/20190606 Examples of blameless culture outside of DevOps.md
new file mode 100644
index 0000000000..b78722f3ef
--- /dev/null
+++ b/sources/tech/20190606 Examples of blameless culture outside of DevOps.md
@@ -0,0 +1,65 @@
+[#]: collector: (lujun9972)
+[#]: translator: ( )
+[#]: reviewer: ( )
+[#]: publisher: ( )
+[#]: url: ( )
+[#]: subject: (Examples of blameless culture outside of DevOps)
+[#]: via: (https://opensource.com/article/19/6/everyday-blameless)
+[#]: author: (Patrick Housley https://opensource.com/users/patrickhousley)
+
+Examples of blameless culture outside of DevOps
+======
+Is blameless culture just a matter of postmortems and top-down change?
+Or are there things individuals can do to promote it?
+![people in different locations who are part of the same team][1]
+
+A blameless culture is not a new concept in the technology industry. In fact, in 2012, [John Allspaw][2] wrote about how [Etsy uses blameless postmortems][3] to dive to the heart of problems when they arise. Other technology giants, like Google, have also worked hard to implement a blameless culture. But what is a blameless culture? Is it just a matter of postmortems? Does it take a culture change to make blameless a reality? And what about flagrant misconduct?
+
+### Exploring blameless culture
+
+In 2009, [Mike Rother][4] wrote an [award-winning book][5] on the culture of Toyota, in which he broke down how the automaker became so successful in the 20th century when most other car manufacturers were either stagnant or losing ground. Books on Toyota were nothing new, but how Mike approached Toyota's success was unique. Instead of focusing on the processes and procedures Toyota implements, he explains in exquisite detail the company's culture, including its focus on blameless failure and continuous improvement.
+
+Mike explains that Toyota, in the face of failure, focuses on the system where the failure occurred instead of who is at fault. Furthermore, the company treats failure as a learning opportunity, not a chance to chastise the operator. This is the very definition of a blameless culture and one that the technology field can still learn much from.
+
+### It's not a culture shift
+
+It shouldn't take an executive initiative to attain blamelessness. It's not so much the company's culture that we need to change, but our attitudes towards fault and failure. Sure, the company's culture should change, but, even in a blameless culture, some people still have the undying urge to point fingers and call others out for their shortcomings.
+
+I was once contracted to work with a company on developing and improving its digital footprint. This company employed its own developers, and, as you might imagine, there was tension at times. If a bug was found in production, the search began immediately for the person responsible. I think it's just human nature to want to find someone to blame. But there is a better way, and it will take practice.
+
+### Blamelessness at the microscale
+
+When I talk about implementing blamelessness, I'm not talking about doing it at the scale of companies and organizations. That's too large for most of us. Instead, focus your attention on the smallest scale: the code commit, review, and pull request. Focus on your actions and the actions of your peers and those you lead. You may find that you have the biggest impact in this area.
+
+How often do you or one of your peers get a bug report, dig in to find out what is wrong, and stop once you determine who made the breaking change? Do you immediately assume that a pull request or code commit needs to be reverted? Do you contact that individual and tell them what they broke and which commit it was? If this is happening within your team, you're the furthest from blamelessness you could be. But it can be remedied.
+
+Obviously, when you find a bug, you need to understand what broke, where, and who did it. But don't stop there. Attempt to fix the issue. The chances are high that patching the code will be a faster resolution than trying to figure out which code to back out. Too many times, I have seen people try to back out code only to find that they broke something else.
+
+If you're not confident that you can fix the issue, politely ask the individual who made the breaking change to assist. Yes, assist! My mom always said, "you can catch more flies with honey than vinegar." You will typically get a more positive response if you ask people for help instead of pointing out what they broke.
+
+Finally, once you have a fix, make sure to ask the individual who caused the bug to review your change. This isn't about rubbing it in their face. Remember that failure represents a learning opportunity, and the person who created the failure will learn if they have a chance to review the fix you created. Furthermore, that individual may have unique details and reasoning that suggests your change may fix the immediate issue but may not solve the original problem.
+
+### Catch flagrant misconduct and abuse sooner
+
+A blameless culture doesn't provide blanket protection if someone is knowingly attempting to do wrong. That also doesn't mean the system is not faulty. Remember how Toyota focuses on the system where failure occurs? If an individual can knowingly create havoc within the software they are working on, they should be held accountable—but so should the system.
+
+When reviewing failure, no matter how small, always ask, "How could we have caught this sooner?" Chances are you could improve some part of your software development lifecycle (SDLC) to make failures less likely to happen. Maybe you need to add more tests. Or run your tests more often. Whatever the solution, remember that fixing the bug is only part of a complete fix.
+
+--------------------------------------------------------------------------------
+
+via: https://opensource.com/article/19/6/everyday-blameless
+
+作者:[Patrick Housley][a]
+选题:[lujun9972][b]
+译者:[译者ID](https://github.com/译者ID)
+校对:[校对者ID](https://github.com/校对者ID)
+
+本文由 [LCTT](https://github.com/LCTT/TranslateProject) 原创编译,[Linux中国](https://linux.cn/) 荣誉推出
+
+[a]: https://opensource.com/users/patrickhousley
+[b]: https://github.com/lujun9972
+[1]: https://opensource.com/sites/default/files/styles/image-full-size/public/lead-images/connection_people_team_collaboration.png?itok=0_vQT8xV (people in different locations who are part of the same team)
+[2]: https://twitter.com/allspaw
+[3]: https://codeascraft.com/2012/05/22/blameless-postmortems/
+[4]: http://www-personal.umich.edu/~mrother/Homepage.html
+[5]: https://en.wikipedia.org/wiki/Toyota_Kata
diff --git a/sources/tech/20190606 Why hypothesis-driven development is key to DevOps.md b/sources/tech/20190606 Why hypothesis-driven development is key to DevOps.md
new file mode 100644
index 0000000000..766393dc3f
--- /dev/null
+++ b/sources/tech/20190606 Why hypothesis-driven development is key to DevOps.md
@@ -0,0 +1,152 @@
+[#]: collector: (lujun9972)
+[#]: translator: ( )
+[#]: reviewer: ( )
+[#]: publisher: ( )
+[#]: url: ( )
+[#]: subject: (Why hypothesis-driven development is key to DevOps)
+[#]: via: (https://opensource.com/article/19/6/why-hypothesis-driven-development-devops)
+[#]: author: (Brent Aaron Reed https://opensource.com/users/brentaaronreed/users/wpschaub)
+
+Why hypothesis-driven development is key to DevOps
+======
+A hypothesis-driven development mindset harvests the core value of
+feature flags: experimentation in production.
+![gears and lightbulb to represent innovation][1]
+
+The definition of DevOps, offered by [Donovan Brown][2] * _is_ "The union of **people** , **process** , and **products** to enable continuous delivery of **value** to our customers.*" It accentuates the importance of continuous delivery of value. Let's discuss how experimentation is at the heart of modern development practices.
+
+![][3]
+
+### Reflecting on the past
+
+Before we get into hypothesis-driven development, let's quickly review how we deliver value using waterfall, agile, deployment rings, and feature flags.
+
+In the days of _**waterfall**_ , we had predictable and process-driven delivery. However, we only delivered value towards the end of the development lifecycle, often failing late as the solution drifted from the original requirements, or our killer features were outdated by the time we finally shipped.
+
+![][4]
+
+Here, we have one release X and eight features, which are all deployed and exposed to the patiently waiting user. We are continuously delivering value—but with a typical release cadence of six months to two years, _the value of the features declines as the world continues to move on_. It worked well enough when there was time to plan and a lower expectation to react to more immediate needs.
+
+The introduction of _**agile**_ allowed us to create and respond to change so we could continuously deliver working software, sense, learn, and respond.
+
+![][5]
+
+Now, we have three releases: X.1, X.2, and X.3. After the X.1 release, we improved feature 3 based on feedback and re-deployed it in release X.3. This is a simple example of delivering features more often, focused on working software, and responding to user feedback. _We are on the path of continuous delivery, focused on our key stakeholders: our users._
+
+Using _**deployment rings**_ and/or _**feature flags**_ , we can decouple release deployment and feature exposure, down to the individual user, to control the exposure—the blast radius—of features. We can conduct experiments; progressively expose, test, enable, and hide features; fine-tune releases, and continuously pivot on learnings and feedback.
+
+When we add feature flags to the previous workflow, we can toggle features to be ON (enabled and exposed) or OFF (hidden).
+
+![][6]
+
+Here, feature flags for features 2, 4, and 8 are OFF, which results in the user being exposed to fewer of the features. All features have been deployed but are not exposed (yet). _We can fine-tune the features (value) of each release after deploying to production._
+
+_**Ring-based deployment**_ limits the impact (blast) on users while we gradually deploy and evaluate one or more features through observation. Rings allow us to deploy features progressively and have multiple releases (v1, v1.1, and v1.2) running in parallel.
+
+![Ring-based deployment][7]
+
+Exposing features in the canary and early-adopter rings enables us to evaluate features without the risk of an all-or-nothing big-bang deployment.
+
+_**Feature flags**_ decouple release deployment and feature exposure. You "flip the flag" to expose a new feature, perform an emergency rollback by resetting the flag, use rules to hide features, and allow users to toggle preview features.
+
+![Toggling feature flags on/off][8]
+
+When you combine deployment rings and feature flags, you can progressively deploy a release through rings and use feature flags to fine-tune the deployed release.
+
+> See [deploying new releases: Feature flags or rings][9], [what's the cost of feature flags][10], and [breaking down walls between people, process, and products][11] for discussions on feature flags, deployment rings, and related topics.
+
+### Adding hypothesis-driven development to the mix
+
+_**Hypothesis-driven development**_ is based on a series of experiments to validate or disprove a hypothesis in a [complex problem domain][12] where we have unknown-unknowns. We want to find viable ideas or fail fast. Instead of developing a monolithic solution and performing a big-bang release, we iterate through hypotheses, evaluating how features perform and, most importantly, how and if customers use them.
+
+> **Template:** _**We believe**_ {customer/business segment} _**wants**_ {product/feature/service} _**because**_ {value proposition}.
+>
+> **Example:** _**We believe**_ that users _**want**_ to be able to select different themes _**because**_ it will result in improved user satisfaction. We expect 50% or more users to select a non-default theme and to see a 5% increase in user engagement.
+
+Every experiment must be based on a hypothesis, have a measurable conclusion, and contribute to feature and overall product learning. For each experiment, consider these steps:
+
+ * Observe your user
+ * Define a hypothesis and an experiment to assess the hypothesis
+ * Define clear success criteria (e.g., a 5% increase in user engagement)
+ * Run the experiment
+ * Evaluate the results and either accept or reject the hypothesis
+ * Repeat
+
+
+
+Let's have another look at our sample release with eight hypothetical features.
+
+![][13]
+
+When we deploy each feature, we can observe user behavior and feedback, and prove or disprove the hypothesis that motivated the deployment. As you can see, the experiment fails for features 2 and 6, allowing us to fail-fast and remove them from the solution. _**We do not want to carry waste that is not delivering value or delighting our users!**_ The experiment for feature 3 is inconclusive, so we adapt the feature, repeat the experiment, and perform A/B testing in Release X.2. Based on observations, we identify the variant feature 3.2 as the winner and re-deploy in release X.3. _**We only expose the features that passed the experiment and satisfy the users.**_
+
+### Hypothesis-driven development lights up progressive exposure
+
+When we combine hypothesis-driven development with progressive exposure strategies, we can vertically slice our solution, incrementally delivering on our long-term vision. With each slice, we progressively expose experiments, enable features that delight our users and hide those that did not make the cut.
+
+But there is more. When we embrace hypothesis-driven development, we can learn how technology works together, or not, and what our customers need and want. We also complement the test-driven development (TDD) principle. TDD encourages us to write the test first (hypothesis), then confirm our features are correct (experiment), and succeed or fail the test (evaluate). _**It is all about quality and delighting our users** , as outlined in principles 1, 3, and 7_ of the [Agile Manifesto][14]:
+
+ * Our highest priority is to satisfy the customers through early and continuous delivery of value.
+ * Deliver software often, from a couple of weeks to a couple of months, with a preference to the shorter timescale.
+ * Working software is the primary measure of progress.
+
+
+
+More importantly, we introduce a new mindset that breaks down the walls between development, business, and operations to view, design, develop, deliver, and observe our solution in an iterative series of experiments, adopting features based on scientific analysis, user behavior, and feedback in production. We can evolve our solutions in thin slices through observation and learning in production, a luxury that other engineering disciplines, such as aerospace or civil engineering, can only dream of.
+
+The good news is that hypothesis-driven development supports the empirical process theory and its three pillars: **Transparency** , **Inspection** , and **Adaption**.
+
+![][15]
+
+But there is more. Based on lean principles, we must pivot or persevere after we measure and inspect the feedback. Using feature toggles in conjunction with hypothesis-driven development, we get the best of both worlds, as well as the ability to use A|B testing to make decisions on feedback, such as likes/dislikes and value/waste.
+
+### Remember:
+
+Hypothesis-driven development:
+
+ * Is about a series of experiments to confirm or disprove a hypothesis. Identify value!
+ * Delivers a measurable conclusion and enables continued learning.
+ * Enables continuous feedback from the key stakeholder—the user—to understand the unknown-unknowns!
+ * Enables us to understand the evolving landscape into which we progressively expose value.
+
+
+
+Progressive exposure:
+
+ * Is not an excuse to hide non-production-ready code. _**Always ship quality!**_
+ * Is about deploying a release of features through rings in production. _**Limit blast radius!**_
+ * Is about enabling or disabling features in production. _**Fine-tune release values!**_
+ * Relies on circuit breakers to protect the infrastructure from implications of progressive exposure. _**Observe, sense, act!**_
+
+
+
+What have you learned about progressive exposure strategies and hypothesis-driven development? We look forward to your candid feedback.
+
+--------------------------------------------------------------------------------
+
+via: https://opensource.com/article/19/6/why-hypothesis-driven-development-devops
+
+作者:[Brent Aaron Reed][a]
+选题:[lujun9972][b]
+译者:[译者ID](https://github.com/译者ID)
+校对:[校对者ID](https://github.com/校对者ID)
+
+本文由 [LCTT](https://github.com/LCTT/TranslateProject) 原创编译,[Linux中国](https://linux.cn/) 荣誉推出
+
+[a]: https://opensource.com/users/brentaaronreed/users/wpschaub
+[b]: https://github.com/lujun9972
+[1]: https://opensource.com/sites/default/files/styles/image-full-size/public/lead-images/innovation_lightbulb_gears_devops_ansible.png?itok=TSbmp3_M (gears and lightbulb to represent innovation)
+[2]: http://donovanbrown.com/post/what-is-devops
+[3]: https://opensource.com/sites/default/files/hypo-1_copy.png
+[4]: https://opensource.com/sites/default/files/uploads/hyp0-2-trans.png
+[5]: https://opensource.com/sites/default/files/uploads/hypo-3-trans.png
+[6]: https://opensource.com/sites/default/files/uploads/hypo-4_0.png
+[7]: https://opensource.com/sites/default/files/uploads/hypo-6-trans.png
+[8]: https://opensource.com/sites/default/files/uploads/hypo-7-trans.png
+[9]: https://opensource.com/article/18/2/feature-flags-ring-deployment-model
+[10]: https://opensource.com/article/18/7/does-progressive-exposure-really-come-cost
+[11]: https://opensource.com/article/19/3/breaking-down-walls-between-people-process-and-products
+[12]: https://en.wikipedia.org/wiki/Cynefin_framework
+[13]: https://opensource.com/sites/default/files/uploads/hypo-5-trans.png
+[14]: https://agilemanifesto.org/principles.html
+[15]: https://opensource.com/sites/default/files/uploads/adapt-transparent-inspect.png
diff --git a/sources/tech/20190607 4 tools to help you drive Kubernetes.md b/sources/tech/20190607 4 tools to help you drive Kubernetes.md
new file mode 100644
index 0000000000..bb45fb0bea
--- /dev/null
+++ b/sources/tech/20190607 4 tools to help you drive Kubernetes.md
@@ -0,0 +1,219 @@
+[#]: collector: (lujun9972)
+[#]: translator: ( )
+[#]: reviewer: ( )
+[#]: publisher: ( )
+[#]: url: ( )
+[#]: subject: (4 tools to help you drive Kubernetes)
+[#]: via: (https://opensource.com/article/19/6/tools-drive-kubernetes)
+[#]: author: (Scott McCarty https://opensource.com/users/fatherlinux/users/fatherlinux/users/fatherlinux/users/fatherlinux)
+
+4 tools to help you drive Kubernetes
+======
+Learning to drive Kubernetes is more important that knowing how to build
+it, and these tools will get you on the road fast.
+![Tools in a workshop][1]
+
+In the third article in this series, _[Kubernetes basics: Learn how to drive first][2]_ , I emphasized that you should learn to drive Kubernetes, not build it. I also explained that there is a minimum set of primitives that you have to learn to model an application in Kubernetes. I want to emphasize this point: the set of primitives that you _need_ to learn are the easiest set of primitives that you _can_ learn to achieve production-quality application deployments (i.e., high-availability [HA], multiple containers, multiple applications). Stated another way, learning the set of primitives built into Kubernetes is easier than learning clustering software, clustered file systems, load balancers, crazy Apache configs, crazy Nginx configs, routers, switches, firewalls, and storage backends—all the things you would need to model a simple HA application in a traditional IT environment (for virtual machines or bare metal).
+
+In this fourth article, I'll share some tools that will help you learn to drive Kubernetes quickly.
+
+### 1\. Katacoda
+
+[Katacoda][3] is the easiest way to test-drive a Kubernetes cluster, hands-down. With one click and five seconds of time, you have a web-based terminal plumbed straight into a running Kubernetes cluster. It's magnificent for playing and learning. I even use it for demos and testing out new ideas. Katacoda provides a completely ephemeral environment that is recycled when you finish using it.
+
+![OpenShift Playground][4]
+
+[OpenShift playground][5]
+
+![Kubernetes Playground][6]
+
+[Kubernetes playground][7]
+
+Katacoda provides ephemeral playgrounds and deeper lab environments. For example, the [Linux Container Internals Lab][3], which I have run for the last three or four years, is built in Katacoda.
+
+Katacoda maintains a bunch of [Kubernetes and cloud tutorials][8] on its main site and collaborates with Red Hat to support a [dedicated learning portal for OpenShift][9]. Explore them both—they are excellent learning resources.
+
+When you first learn to drive a dump truck, it's always best to watch how other people drive first.
+
+### 2\. Podman generate kube
+
+The **podman generate kube** command is a brilliant little subcommand that helps users naturally transition from a simple container engine running simple containers to a cluster use case running many containers (as I described in the [last article][2]). [Podman][10] does this by letting you start a few containers, then exporting the working Kube YAML, and firing them up in Kubernetes. Check this out (pssst, you can run it in this [Katacoda lab][3], which already has Podman and OpenShift).
+
+First, notice the syntax to run a container is strikingly similar to Docker:
+
+
+```
+`podman run -dtn two-pizza quay.io/fatherlinux/two-pizza`
+```
+
+But this is something other container engines don't do:
+
+
+```
+`podman generate kube two-pizza`
+```
+
+The output:
+
+
+```
+# Generation of Kubernetes YAML is still under development!
+#
+# Save the output of this file and use kubectl create -f to import
+# it into Kubernetes.
+#
+# Created with podman-1.3.1
+apiVersion: v1
+kind: Pod
+metadata:
+creationTimestamp: "2019-06-07T08:08:12Z"
+labels:
+app: two-pizza
+name: two-pizza
+spec:
+containers:
+\- command:
+\- /bin/sh
+\- -c
+\- bash -c 'while true; do /usr/bin/nc -l -p 3306 < /srv/hello.txt; done'
+env:
+\- name: PATH
+value: /usr/local/sbin:/usr/local/bin:/usr/sbin:/usr/bin:/sbin:/bin
+\- name: TERM
+value: xterm
+\- name: HOSTNAME
+\- name: container
+value: oci
+image: quay.io/fatherlinux/two-pizza:latest
+name: two-pizza
+resources: {}
+securityContext:
+allowPrivilegeEscalation: true
+capabilities: {}
+privileged: false
+readOnlyRootFilesystem: false
+tty: true
+workingDir: /
+status: {}
+\---
+apiVersion: v1
+kind: Service
+metadata:
+creationTimestamp: "2019-06-07T08:08:12Z"
+labels:
+app: two-pizza
+name: two-pizza
+spec:
+selector:
+app: two-pizza
+type: NodePort
+status:
+loadBalancer: {}
+```
+
+You now have some working Kubernetes YAML, which you can use as a starting point for mucking around and learning, tweaking, etc. The **-s** flag created a service for you. [Brent Baude][11] is even working on new features like [adding Volumes/Persistent Volume Claims][12]. For a deeper dive, check out Brent's amazing work in his blog post "[Podman can now ease the transition to Kubernetes and CRI-O][13]."
+
+### 3\. oc new-app
+
+The **oc new-app** command is extremely powerful. It's OpenShift-specific, so it's not available in default Kubernetes, but it's really useful when you're starting to learn Kubernetes. Let's start with a quick command to create a fairly sophisticated application:
+
+
+```
+oc new-project -n example
+oc new-app -f
+```
+
+With **oc new-app** , you can literally steal templates from the OpenShift developers and have a known, good starting point when developing primitives to describe your own applications. After you run the above command, your Kubernetes namespace (in OpenShift) will be populated by a bunch of new, defined resources.
+
+
+```
+`oc get all`
+```
+
+The output:
+
+
+```
+NAME READY STATUS RESTARTS AGE
+pod/cakephp-mysql-example-1-build 0/1 Completed 0 4m
+pod/cakephp-mysql-example-1-gz65l 1/1 Running 0 1m
+pod/mysql-1-nkhqn 1/1 Running 0 4m
+
+NAME DESIRED CURRENT READY AGE
+replicationcontroller/cakephp-mysql-example-1 1 1 1 1m
+replicationcontroller/mysql-1 1 1 1 4m
+
+NAME TYPE CLUSTER-IP EXTERNAL-IP PORT(S) AGE
+service/cakephp-mysql-example ClusterIP 172.30.234.135 8080/TCP 4m
+service/mysql ClusterIP 172.30.13.195 3306/TCP 4m
+
+NAME REVISION DESIRED CURRENT TRIGGERED BY
+deploymentconfig.apps.openshift.io/cakephp-mysql-example 1 1 1 config,image(cakephp-mysql-example:latest)
+deploymentconfig.apps.openshift.io/mysql 1 1 1 config,image(mysql:5.7)
+
+NAME TYPE FROM LATEST
+buildconfig.build.openshift.io/cakephp-mysql-example Source Git 1
+
+NAME TYPE FROM STATUS STARTED DURATION
+build.build.openshift.io/cakephp-mysql-example-1 Source Git@47a951e Complete 4 minutes ago 2m27s
+
+NAME DOCKER REPO TAGS UPDATED
+imagestream.image.openshift.io/cakephp-mysql-example docker-registry.default.svc:5000/example/cakephp-mysql-example latest About aminute ago
+
+NAME HOST/PORT PATH SERVICES PORT TERMINATION WILDCARD
+route.route.openshift.io/cakephp-mysql-example cakephp-mysql-example-example.2886795271-80-rhsummit1.environments.katacoda.com cakephp-mysql-example None
+```
+
+The beauty of this is that you can delete Pods, watch the replication controllers recreate them, scale Pods up, and scale them down. You can play with the template and change it for other applications (which is what I did when I first started).
+
+### 4\. Visual Studio Code
+
+I saved one of my favorites for last. I use [vi][14] for most of my work, but I have never found a good syntax highlighter and code completion plugin for Kubernetes (if you have one, let me know). Instead, I have found that Microsoft's [VS Code][15] has a killer set of plugins that complete the creation of Kubernetes resources and provide boilerplate.
+
+![VS Code plugins UI][16]
+
+First, install Kubernetes and YAML plugins shown in the image above.
+
+![Autocomplete in VS Code][17]
+
+Then, you can create a new YAML file from scratch and get auto-completion of Kubernetes resources. The example above shows a Service.
+
+![VS Code autocomplete filling in boilerplate for an object][18]
+
+When you use autocomplete and select the Service resource, it fills in some boilerplate for the object. This is magnificent when you are first learning to drive Kubernetes. You can build Pods, Services, Replication Controllers, Deployments, etc. This is a really nice feature when you are building these files from scratch or even modifying the files you create with **Podman generate kube**.
+
+### Conclusion
+
+These four tools (six if you count the two plugins) will help you learn to drive Kubernetes, instead of building or equipping it. In my final article in the series, I will talk about why Kubernetes is so exciting for running so many different workloads.
+
+--------------------------------------------------------------------------------
+
+via: https://opensource.com/article/19/6/tools-drive-kubernetes
+
+作者:[Scott McCarty][a]
+选题:[lujun9972][b]
+译者:[译者ID](https://github.com/译者ID)
+校对:[校对者ID](https://github.com/校对者ID)
+
+本文由 [LCTT](https://github.com/LCTT/TranslateProject) 原创编译,[Linux中国](https://linux.cn/) 荣誉推出
+
+[a]: https://opensource.com/users/fatherlinux/users/fatherlinux/users/fatherlinux/users/fatherlinux
+[b]: https://github.com/lujun9972
+[1]: https://opensource.com/sites/default/files/styles/image-full-size/public/lead-images/tools_workshop_blue_mechanic.jpg?itok=4YXkCU-J (Tools in a workshop)
+[2]: https://opensource.com/article/19/6/kubernetes-basics
+[3]: https://learn.openshift.com/subsystems/container-internals-lab-2-0-part-1
+[4]: https://opensource.com/sites/default/files/uploads/openshift-playground.png (OpenShift Playground)
+[5]: https://learn.openshift.com/playgrounds/openshift311/
+[6]: https://opensource.com/sites/default/files/uploads/kubernetes-playground.png (Kubernetes Playground)
+[7]: https://katacoda.com/courses/kubernetes/playground
+[8]: https://katacoda.com/learn
+[9]: http://learn.openshift.com/
+[10]: https://podman.io/
+[11]: https://developers.redhat.com/blog/author/bbaude/
+[12]: https://github.com/containers/libpod/issues/2303
+[13]: https://developers.redhat.com/blog/2019/01/29/podman-kubernetes-yaml/
+[14]: https://en.wikipedia.org/wiki/Vi
+[15]: https://code.visualstudio.com/
+[16]: https://opensource.com/sites/default/files/uploads/vscode_-_kubernetes_red_hat_-_plugins.png (VS Code plugins UI)
+[17]: https://opensource.com/sites/default/files/uploads/vscode_-_kubernetes_service_-_autocomplete.png (Autocomplete in VS Code)
+[18]: https://opensource.com/sites/default/files/uploads/vscode_-_kubernetes_service_-_boiler_plate.png (VS Code autocomplete filling in boilerplate for an object)
diff --git a/sources/tech/20190607 An Introduction to Kubernetes Secrets and ConfigMaps.md b/sources/tech/20190607 An Introduction to Kubernetes Secrets and ConfigMaps.md
new file mode 100644
index 0000000000..7d28e67ea4
--- /dev/null
+++ b/sources/tech/20190607 An Introduction to Kubernetes Secrets and ConfigMaps.md
@@ -0,0 +1,608 @@
+[#]: collector: (lujun9972)
+[#]: translator: ( )
+[#]: reviewer: ( )
+[#]: publisher: ( )
+[#]: url: ( )
+[#]: subject: (An Introduction to Kubernetes Secrets and ConfigMaps)
+[#]: via: (https://opensource.com/article/19/6/introduction-kubernetes-secrets-and-configmaps)
+[#]: author: (Chris Collins https://opensource.com/users/clcollins)
+
+An Introduction to Kubernetes Secrets and ConfigMaps
+======
+Kubernetes Secrets and ConfigMaps separate the configuration of
+individual container instances from the container image, reducing
+overhead and adding flexibility.
+![Kubernetes][1]
+
+Kubernetes has two types of objects that can inject configuration data into a container when it starts up: Secrets and ConfigMaps. Secrets and ConfigMaps behave similarly in [Kubernetes][2], both in how they are created and because they can be exposed inside a container as mounted files or volumes or environment variables.
+
+To explore Secrets and ConfigMaps, consider the following scenario:
+
+> You're running the [official MariaDB container image][3] in Kubernetes and must do some configuration to get the container to run. The image requires an environment variable to be set for **MYSQL_ROOT_PASSWORD** , **MYSQL_ALLOW_EMPTY_PASSWORD** , or **MYSQL_RANDOM_ROOT_PASSWORD** to initialize the database. It also allows for extensions to the MySQL configuration file **my.cnf** by placing custom config files in **/etc/mysql/conf.d**.
+
+You could build a custom image, setting the environment variables and copying the configuration files into it to create a bespoke container image. However, it is considered a best practice to create and use generic images and add configuration to the containers created from them, instead. This is a perfect use-case for ConfigMaps and Secrets. The **MYSQL_ROOT_PASSWORD** can be set in a Secret and added to the container as an environment variable, and the configuration files can be stored in a ConfigMap and mounted into the container as a file on startup.
+
+Let's try it out!
+
+### But first: A quick note about Kubectl
+
+Make sure that your version of the **kubectl** client command is the same or newer than the Kubernetes cluster version in use.
+
+An error along the lines of:
+
+
+```
+`error: SchemaError(io.k8s.api.admissionregistration.v1beta1.ServiceReference): invalid object doesn't have additional properties`
+```
+
+may mean the client version is too old and needs to be upgraded. The [Kubernetes Documentation for Installing Kubectl][4] has instructions for installing the latest client on various platforms.
+
+If you're using Docker for Mac, it also installs its own version of **kubectl** , and that may be the issue. You can install a current client with **brew install** , replacing the symlink to the client shipped by Docker:
+
+
+```
+$ rm /usr/local/bin/kubectl
+$ brew link --overwrite kubernetes-cli
+```
+
+The newer **kubectl** client should continue to work with Docker's Kubernetes version.
+
+### Secrets
+
+Secrets are a Kubernetes object intended for storing a small amount of sensitive data. It is worth noting that Secrets are stored base64-encoded within Kubernetes, so they are not wildly secure. Make sure to have appropriate [role-based access controls][5] (RBAC) to protect access to Secrets. Even so, extremely sensitive Secrets data should probably be stored using something like [HashiCorp Vault][6]. For the root password of a MariaDB database, however, base64 encoding is just fine.
+
+#### Create a Secret manually
+
+To create the Secret containing the **MYSQL_ROOT_PASSWORD** , choose a password and convert it to base64:
+
+
+```
+# The root password will be "KubernetesRocks!"
+$ echo -n 'KubernetesRocks!' | base64
+S3ViZXJuZXRlc1JvY2tzIQ==
+```
+
+Make a note of the encoded string. You need it to create the YAML file for the Secret:
+
+
+```
+apiVersion: v1
+kind: Secret
+metadata:
+name: mariadb-root-password
+type: Opaque
+data:
+password: S3ViZXJuZXRlc1JvY2tzIQ==
+```
+
+Save that file as **mysql-secret.yaml** and create the Secret in Kubernetes with the **kubectl apply** command:
+
+
+```
+$ kubectl apply -f mysql-secret.yaml
+secret/mariadb-root-password created
+```
+
+#### View the newly created Secret
+
+Now that you've created the Secret, use **kubectl describe** to see it:
+
+
+```
+$ kubectl describe secret mariadb-root-password
+Name: mariadb-root-password
+Namespace: secrets-and-configmaps
+Labels:
+Annotations:
+Type: Opaque
+
+Data
+====
+password: 16 bytes
+```
+
+Note that the **Data** field contains the key you set in the YAML: **password**. The value assigned to that key is the password you created, but it is not shown in the output. Instead, the value's size is shown in its place, in this case, 16 bytes.
+
+You can also use the **kubectl edit secret ** command to view and edit the Secret. If you edit the Secret, you'll see something like this:
+
+
+```
+# Please edit the object below. Lines beginning with a '#' will be ignored,
+# and an empty file will abort the edit. If an error occurs while saving this file will be
+# reopened with the relevant failures.
+#
+apiVersion: v1
+data:
+password: S3ViZXJuZXRlc1JvY2tzIQ==
+kind: Secret
+metadata:
+annotations:
+kubectl.kubernetes.io/last-applied-configuration: |
+{"apiVersion":"v1","data":{"password":"S3ViZXJuZXRlc1JvY2tzIQ=="},"kind":"Secret","metadata":{"annotations":{},"name":"mariadb-root-password","namespace":"secrets-and-configmaps"},"type":"Opaque"}
+creationTimestamp: 2019-05-29T12:06:09Z
+name: mariadb-root-password
+namespace: secrets-and-configmaps
+resourceVersion: "85154772"
+selfLink: /api/v1/namespaces/secrets-and-configmaps/secrets/mariadb-root-password
+uid: 2542dadb-820a-11e9-ae24-005056a1db05
+type: Opaque
+```
+
+Again, the **data** field with the **password** key is visible, and this time you can see the base64-encoded Secret.
+
+#### Decode the Secret
+
+Let's say you need to view the Secret in plain text, for example, to verify that the Secret was created with the correct content. You can do this by decoding it.
+
+It is easy to decode the Secret by extracting the value and piping it to base64. In this case, you will use the output format **-o jsonpath= ** to extract only the Secret value using a JSONPath template.
+
+
+```
+# Returns the base64 encoded secret string
+$ kubectl get secret mariadb-root-password -o jsonpath='{.data.password}'
+S3ViZXJuZXRlc1JvY2tzIQ==
+
+# Pipe it to `base64 --decode -` to decode:
+$ kubectl get secret mariadb-root-password -o jsonpath='{.data.password}' | base64 --decode -
+KubernetesRocks!
+```
+
+#### Another way to create Secrets
+
+You can also create Secrets directly using the **kubectl create secret** command. The MariaDB image permits setting up a regular database user with a password by setting the **MYSQL_USER** and **MYSQL_PASSWORD** environment variables. A Secret can hold more than one key/value pair, so you can create a single Secret to hold both strings. As a bonus, by using **kubectl create secret** , you can let Kubernetes mess with base64 so that you don't have to.
+
+
+```
+$ kubectl create secret generic mariadb-user-creds \
+\--from-literal=MYSQL_USER=kubeuser\
+\--from-literal=MYSQL_PASSWORD=kube-still-rocks
+secret/mariadb-user-creds created
+```
+
+Note the **\--from-literal** , which sets the key name and the value all in one. You can pass as many **\--from-literal** arguments as you need to create one or more key/value pairs in the Secret.
+
+Validate that the username and password were created and stored correctly with the **kubectl get secrets** command:
+
+
+```
+# Get the username
+$ kubectl get secret mariadb-user-creds -o jsonpath='{.data.MYSQL_USER}' | base64 --decode -
+kubeuser
+
+# Get the password
+$ kubectl get secret mariadb-user-creds -o jsonpath='{.data.MYSQL_PASSWORD}' | base64 --decode -
+kube-still-rocks
+```
+
+### ConfigMaps
+
+ConfigMaps are similar to Secrets. They can be created and shared in the containers in the same ways. The only big difference between them is the base64-encoding obfuscation. ConfigMaps are intended for non-sensitive data—configuration data—like config files and environment variables and are a great way to create customized running services from generic container images.
+
+#### Create a ConfigMap
+
+ConfigMaps can be created in the same ways as Secrets. You can write a YAML representation of the ConfigMap manually and load it into Kubernetes, or you can use the **kubectl create configmap** command to create it from the command line. The following example creates a ConfigMap using the latter method but, instead of passing literal strings (as with **\--from-literal= =** in the Secret above), it creates a ConfigMap from an existing file—a MySQL config intended for **/etc/mysql/conf.d** in the container. This config file overrides the **max_allowed_packet** setting that MariaDB sets to 16M by default.
+
+First, create a file named **max_allowed_packet.cnf** with the following content:
+
+
+```
+[mysqld]
+max_allowed_packet = 64M
+```
+
+This will override the default setting in the **my.cnf** file and set **max_allowed_packet** to 64M.
+
+Once the file is created, you can create a ConfigMap named **mariadb-config** using the **kubectl create configmap** command that contains the file:
+
+
+```
+$ kubectl create configmap mariadb-config --from-file=max_allowed_packet.cnf
+configmap/mariadb-config created
+```
+
+Just like Secrets, ConfigMaps store one or more key/value pairs in their Data hash of the object. By default, using **\--from-file= ** (as above) will store the contents of the file as the value, and the name of the file will be stored as the key. This is convenient from an organization viewpoint. However, the key name can be explicitly set, too. For example, if you used **\--from-file=max-packet=max_allowed_packet.cnf** when you created the ConfigMap, the key would be **max-packet** rather than the file name. If you had multiple files to store in the ConfigMap, you could add each of them with an additional **\--from-file= ** argument.
+
+#### View the new ConfigMap and read the data
+
+As mentioned, ConfigMaps are not meant to store sensitive data, so the data is not encoded when the ConfigMap is created. This makes it easy to view and validate the data and edit it directly.
+
+First, validate that the ConfigMap was, indeed, created:
+
+
+```
+$ kubectl get configmap mariadb-config
+NAME DATA AGE
+mariadb-config 1 9m
+```
+
+The contents of the ConfigMap can be viewed with the **kubectl describe** command. Note that the full contents of the file are visible and that the key name is, in fact, the file name, **max_allowed_packet.cnf**.
+
+
+```
+$ kubectl describe cm mariadb-config
+Name: mariadb-config
+Namespace: secrets-and-configmaps
+Labels:
+Annotations:
+
+Data
+====
+max_allowed_packet.cnf:
+\----
+[mysqld]
+max_allowed_packet = 64M
+
+Events:
+```
+
+A ConfigMap can be edited live within Kubernetes with the **kubectl edit** command. Doing so will open a buffer with the default editor showing the contents of the ConfigMap as YAML. When changes are saved, they will immediately be live in Kubernetes. While not really the _best_ practice, it can be handy for testing things in development.
+
+Say you want a **max_allowed_packet** value of 32M instead of the default 16M or the 64M in the **max_allowed_packet.cnf** file. Use **kubectl edit configmap mariadb-config** to edit the value:
+
+
+```
+$ kubectl edit configmap mariadb-config
+
+# Please edit the object below. Lines beginning with a '#' will be ignored,
+# and an empty file will abort the edit. If an error occurs while saving this file will be
+# reopened with the relevant failures.
+#
+apiVersion: v1
+
+data:
+max_allowed_packet.cnf: |
+[mysqld]
+max_allowed_packet = 32M
+kind: ConfigMap
+metadata:
+creationTimestamp: 2019-05-30T12:02:22Z
+name: mariadb-config
+namespace: secrets-and-configmaps
+resourceVersion: "85609912"
+selfLink: /api/v1/namespaces/secrets-and-configmaps/configmaps/mariadb-config
+uid: c83ccfae-82d2-11e9-832f-005056a1102f
+```
+
+After saving the change, verify the data has been updated:
+
+
+```
+# Note the '.' in max_allowed_packet.cnf needs to be escaped
+$ kubectl get configmap mariadb-config -o "jsonpath={.data['max_allowed_packet\\.cnf']}"
+
+[mysqld]
+max_allowed_packet = 32M
+```
+
+### Using Secrets and ConfigMaps
+
+Secrets and ConfigMaps can be mounted as environment variables or as files within a container. For the MariaDB container, you will need to mount the Secrets as environment variables and the ConfigMap as a file. First, though, you need to write a Deployment for MariaDB so that you have something to work with. Create a file named **mariadb-deployment.yaml** with the following:
+
+
+```
+apiVersion: apps/v1
+kind: Deployment
+metadata:
+labels:
+app: mariadb
+name: mariadb-deployment
+spec:
+replicas: 1
+selector:
+matchLabels:
+app: mariadb
+template:
+metadata:
+labels:
+app: mariadb
+spec:
+containers:
+\- name: mariadb
+image: docker.io/mariadb:10.4
+ports:
+\- containerPort: 3306
+protocol: TCP
+volumeMounts:
+\- mountPath: /var/lib/mysql
+name: mariadb-volume-1
+volumes:
+\- emptyDir: {}
+name: mariadb-volume-1
+```
+
+This is a bare-bones Kubernetes Deployment of the official MariaDB 10.4 image from Docker Hub. Now, add your Secrets and ConfigMap.
+
+#### Add the Secrets to the Deployment as environment variables
+
+You have two Secrets that need to be added to the Deployment:
+
+ 1. **mariadb-root-password** (with one key/value pair)
+ 2. **mariadb-user-creds** (with two key/value pairs)
+
+
+
+For the **mariadb-root-password** Secret, specify the Secret and the key you want by adding an **env** list/array to the container spec in the Deployment and setting the environment variable value to the value of the key in your Secret. In this case, the list contains only a single entry, for the variable **MYSQL_ROOT_PASSWORD**.
+
+
+```
+env:
+\- name: MYSQL_ROOT_PASSWORD
+valueFrom:
+secretKeyRef:
+name: mariadb-root-password
+key: password
+```
+
+Note that the name of the object is the name of the environment variable that is added to the container. The **valueFrom** field defines **secretKeyRef** as the source from which the environment variable will be set; i.e., it will use the value from the **password** key in the **mariadb-root-password** Secret you set earlier.
+
+Add this section to the definition for the **mariadb** container in the **mariadb-deployment.yaml** file. It should look something like this:
+
+
+```
+spec:
+containers:
+\- name: mariadb
+image: docker.io/mariadb:10.4
+env:
+\- name: MYSQL_ROOT_PASSWORD
+valueFrom:
+secretKeyRef:
+name: mariadb-root-password
+key: password
+ports:
+\- containerPort: 3306
+protocol: TCP
+volumeMounts:
+\- mountPath: /var/lib/mysql
+name: mariadb-volume-1
+```
+
+In this way, you have explicitly set the variable to the value of a specific key from your Secret. This method can also be used with ConfigMaps by using **configMapRef** instead of **secretKeyRef**.
+
+You can also set environment variables from _all_ key/value pairs in a Secret or ConfigMap to automatically use the key name as the environment variable name and the key's value as the environment variable's value. By using **envFrom** rather than **env** in the container spec, you can set the **MYSQL_USER** and **MYSQL_PASSWORD** from the **mariadb-user-creds** Secret you created earlier, all in one go:
+
+
+```
+envFrom:
+\- secretRef:
+name: mariadb-user-creds
+```
+
+**envFrom** is a list of sources for Kubernetes to take environment variables. Use **secretRef** again, this time to specify **mariadb-user-creds** as the source of the environment variables. That's it! All the keys and values in the Secret will be added as environment variables in the container.
+
+The container spec should now look like this:
+
+
+```
+spec:
+containers:
+\- name: mariadb
+image: docker.io/mariadb:10.4
+env:
+\- name: MYSQL_ROOT_PASSWORD
+valueFrom:
+secretKeyRef:
+name: mariadb-root-password
+key: password
+envFrom:
+\- secretRef:
+name: mariadb-user-creds
+ports:
+\- containerPort: 3306
+protocol: TCP
+volumeMounts:
+\- mountPath: /var/lib/mysql
+name: mariadb-volume-1
+```
+
+_Note:_ You could have just added the **mysql-root-password** Secret to the **envFrom** list and let it be parsed as well, as long as the **password** key was named **MYSQL_ROOT_PASSWORD** instead. There is no way to manually specify the environment variable name with **envFrom** as with **env**.
+
+#### Add the max_allowed_packet.cnf file to the Deployment as a volumeMount
+
+As mentioned, both **env** and **envFrom** can be used to share ConfigMap key/value pairs with a container as well. However, in the case of the **mariadb-config** ConfigMap, your entire file is stored as the value to your key, and the file needs to exist in the container's filesystem for MariaDB to be able to use it. Luckily, both Secrets and ConfigMaps can be the source of Kubernetes "volumes" and mounted into the containers instead of using a filesystem or block device as the volume to be mounted.
+
+The **mariadb-deployment.yaml** already has a volume and volumeMount specified, an **emptyDir** (effectively a temporary or ephemeral) volume mounted to **/var/lib/mysql** to store the MariaDB data:
+
+
+```
+<...>
+
+volumeMounts:
+\- mountPath: /var/lib/mysql
+name: mariadb-volume-1
+
+<...>
+
+volumes:
+\- emptyDir: {}
+name: mariadb-volume-1
+
+<...>
+```
+
+_Note:_ This is not a production configuration. When the Pod restarts, the data in the **emptyDir** volume is lost. This is primarily used for development or when the contents of the volume don't need to be persistent.
+
+You can add your ConfigMap as a source by adding it to the volume list and then adding a volumeMount for it to the container definition:
+
+
+```
+<...>
+
+volumeMounts:
+\- mountPath: /var/lib/mysql
+name: mariadb-volume-1
+\- mountPath: /etc/mysql/conf.d
+name: mariadb-config
+
+<...>
+
+volumes:
+\- emptyDir: {}
+name: mariadb-volume-1
+\- configMap:
+name: mariadb-config
+items:
+\- key: max_allowed_packet.cnf
+path: max_allowed_packet.cnf
+name: mariadb-config-volume
+
+<...>
+```
+
+The **volumeMount** is pretty self-explanatory—create a volume mount for the **mariadb-config-volume** (specified in the **volumes** list below it) to the path **/etc/mysql/conf.d**.
+
+Then, in the **volumes** list, **configMap** tells Kubernetes to use the **mariadb-config** ConfigMap, taking the contents of the key **max_allowed_packet.cnf** and mounting it to the path **max_allowed_packed.cnf**. The name of the volume is **mariadb-config-volume** , which was referenced in the **volumeMounts** above.
+
+_Note:_ The **path** from the **configMap** is the name of a file that will contain the contents of the key's value. In this case, your key was a file name, too, but it doesn't have to be. Note also that **items** is a list, so multiple keys can be referenced and their values mounted as files. These files will all be created in the **mountPath** of the **volumeMount** specified above: **/etc/mysql/conf.d**.
+
+### Create a MariaDB instance from the Deployment
+
+At this point, you should have enough to create a MariaDB instance. You have two Secrets, one holding the **MYSQL_ROOT_PASSWORD** and another storing the **MYSQL_USER** , and the **MYSQL_PASSWORD** environment variables to be added to the container. You also have a ConfigMap holding the contents of a MySQL config file that overrides the **max_allowed_packed** value from its default setting.
+
+You also have a **mariadb-deployment.yaml** file that describes a Kubernetes deployment of a Pod with a MariaDB container and adds the Secrets as environment variables and the ConfigMap as a volume-mounted file in the container. It should look like this:
+
+
+```
+apiVersion: apps/v1
+kind: Deployment
+metadata:
+labels:
+app: mariadb
+name: mariadb-deployment
+spec:
+replicas: 1
+selector:
+matchLabels:
+app: mariadb
+template:
+metadata:
+labels:
+app: mariadb
+spec:
+containers:
+\- image: docker.io/mariadb:10.4
+name: mariadb
+env:
+\- name: MYSQL_ROOT_PASSWORD
+valueFrom:
+secretKeyRef:
+name: mariadb-root-password
+key: password
+envFrom:
+\- secretRef:
+name: mariadb-user-creds
+ports:
+\- containerPort: 3306
+protocol: TCP
+volumeMounts:
+\- mountPath: /var/lib/mysql
+name: mariadb-volume-1
+\- mountPath: /etc/mysql/conf.d
+name: mariadb-config-volume
+volumes:
+\- emptyDir: {}
+name: mariadb-volume-1
+\- configMap:
+name: mariadb-config
+items:
+\- key: max_allowed_packet.cnf
+path: max_allowed_packet.cnf
+name: mariadb-config-volume
+```
+
+#### Create the MariaDB instance
+
+Create a new MariaDB instance from the YAML file with the **kubectl create** command:
+
+
+```
+$ kubectl create -f mariadb-deployment.yaml
+deployment.apps/mariadb-deployment created
+```
+
+Once the deployment has been created, use the **kubectl get** command to view the running MariaDB pod:
+
+
+```
+$ kubectl get pods
+NAME READY STATUS RESTARTS AGE
+mariadb-deployment-5465c6655c-7jfqm 1/1 Running 0 3m
+```
+
+Make a note of the Pod name (in this example, it's **mariadb-deployment-5465c6655c-7jfqm** ). Note that the Pod name will differ from this example.
+
+#### Verify the instance is using the Secrets and ConfigMap
+
+Use the **kubectl exec** command (with your Pod name) to validate that the Secrets and ConfigMaps are in use. For example, check that the environment variables are exposed in the container:
+
+
+```
+$ kubectl exec -it mariadb-deployment-5465c6655c-7jfqm env |grep MYSQL
+MYSQL_PASSWORD=kube-still-rocks
+MYSQL_USER=kubeuser
+MYSQL_ROOT_PASSWORD=KubernetesRocks!
+```
+
+Success! All three environment variables—the one using the **env** setup to specify the Secret, and two using **envFrom** to mount all the values from the Secret—are available in the container for MariaDB to use.
+
+Spot check that the **max_allowed_packet.cnf** file was created in **/etc/mysql/conf.d** and that it contains the expected content:
+
+
+```
+$ kubectl exec -it mariadb-deployment-5465c6655c-7jfqm ls /etc/mysql/conf.d
+max_allowed_packet.cnf
+
+$ kubectl exec -it mariadb-deployment-5465c6655c-7jfqm cat /etc/mysql/conf.d/max_allowed_packet.cnf
+[mysqld]
+max_allowed_packet = 32M
+```
+
+Finally, validate that MariaDB used the environment variable to set the root user password and read the **max_allowed_packet.cnf** file to set the **max_allowed_packet** configuration variable. Use the **kubectl exec** command again, this time to get a shell inside the running container and use it to run some **mysql** commands:
+
+
+```
+$ kubectl exec -it mariadb-deployment-5465c6655c-7jfqm /
+bin/sh
+
+# Check that the root password was set correctly
+$ mysql -uroot -p${MYSQL_ROOT_PASSWORD} -e 'show databases;'
++--------------------+
+| Database |
++--------------------+
+| information_schema |
+| mysql |
+| performance_schema |
++--------------------+
+
+# Check that the max_allowed_packet.cnf was parsed
+$ mysql -uroot -p${MYSQL_ROOT_PASSWORD} -e "SHOW VARIABLES LIKE 'max_allowed_packet';"
++--------------------+----------+
+| Variable_name | Value |
++--------------------+----------+
+| max_allowed_packet | 33554432 |
++--------------------+----------+
+```
+
+### Advantages of Secrets and ConfigMaps
+
+This exercise explained how to create Kubernetes Secrets and ConfigMaps and how to use those Secrets and ConfigMaps by adding them as environment variables or files inside of a running container instance. This makes it easy to keep the configuration of individual instances of containers separate from the container image. By separating the configuration data, overhead is reduced to maintaining only a single image for a specific type of instance while retaining the flexibility to create instances with a wide variety of configurations.
+
+--------------------------------------------------------------------------------
+
+via: https://opensource.com/article/19/6/introduction-kubernetes-secrets-and-configmaps
+
+作者:[Chris Collins][a]
+选题:[lujun9972][b]
+译者:[译者ID](https://github.com/译者ID)
+校对:[校对者ID](https://github.com/校对者ID)
+
+本文由 [LCTT](https://github.com/LCTT/TranslateProject) 原创编译,[Linux中国](https://linux.cn/) 荣誉推出
+
+[a]: https://opensource.com/users/clcollins
+[b]: https://github.com/lujun9972
+[1]: https://opensource.com/sites/default/files/styles/image-full-size/public/lead-images/kubernetes.png?itok=PqDGb6W7 (Kubernetes)
+[2]: https://opensource.com/resources/what-is-kubernetes
+[3]: https://hub.docker.com/_/mariadb
+[4]: https://kubernetes.io/docs/tasks/tools/install-kubectl/
+[5]: https://kubernetes.io/docs/reference/access-authn-authz/rbac/
+[6]: https://www.vaultproject.io/
diff --git a/sources/tech/20190610 5 Easy Ways To Free Up Space (Remove Unwanted or Junk Files) on Ubuntu.md b/sources/tech/20190610 5 Easy Ways To Free Up Space (Remove Unwanted or Junk Files) on Ubuntu.md
new file mode 100644
index 0000000000..9d5df1605a
--- /dev/null
+++ b/sources/tech/20190610 5 Easy Ways To Free Up Space (Remove Unwanted or Junk Files) on Ubuntu.md
@@ -0,0 +1,177 @@
+[#]: collector: (lujun9972)
+[#]: translator: ( )
+[#]: reviewer: ( )
+[#]: publisher: ( )
+[#]: url: ( )
+[#]: subject: (5 Easy Ways To Free Up Space (Remove Unwanted or Junk Files) on Ubuntu)
+[#]: via: (https://www.2daygeek.com/linux-remove-delete-unwanted-junk-files-free-up-space-ubuntu-mint-debian/)
+[#]: author: (Magesh Maruthamuthu https://www.2daygeek.com/author/magesh/)
+
+5 Easy Ways To Free Up Space (Remove Unwanted or Junk Files) on Ubuntu
+======
+
+Most of us may perform this action whenever we fall into out of disk space on system.
+
+Most of us may perform this action whenever we are running out of space on Linux system
+
+It should be performed frequently, to make space for installing a new application and dealing with other files.
+
+Housekeeping is one of the routine task of Linux administrator, which allow them to maintain the disk utilization is in under threshold.
+
+There are several ways we can clean up our system space.
+
+There is no need to clean up your system when you have TB of storage capacity.
+
+But if your have limited space then freeing up disk space becomes a necessity.
+
+In this article, I’ll show you some of the easiest or simple ways to clean up your Ubuntu system and get more space.
+
+### How To Check Free Space On Ubuntu Systems?
+
+Use **[df Command][1]** to check current disk utilization on your system.
+
+```
+$ df -h
+Filesystem Size Used Avail Use% Mounted on
+udev 975M 0 975M 0% /dev
+tmpfs 200M 1.7M 198M 1% /run
+/dev/sda1 30G 16G 13G 55% /
+tmpfs 997M 0 997M 0% /dev/shm
+tmpfs 5.0M 4.0K 5.0M 1% /run/lock
+tmpfs 997M 0 997M 0% /sys/fs/cgroup
+```
+
+GUI users can use “Disk Usage Analyzer tool” to view current usage.
+[![][2]![][2]][3]
+
+### 1) Remove The Packages That Are No Longer Required
+
+The following command removes the dependency libs and packages that are no longer required by the system.
+
+These packages were installed automatically to satisfy the dependencies of an installed package.
+
+Also, it removes old Linux kernels that were installed in the system.
+
+It removes orphaned packages which are not longer needed from the system, but not purges them.
+
+```
+$ sudo apt-get autoremove
+[sudo] password for daygeek:
+Reading package lists... Done
+Building dependency tree
+Reading state information... Done
+The following packages will be REMOVED:
+ apache2-bin apache2-data apache2-utils galera-3 libaio1 libapr1 libaprutil1
+ libaprutil1-dbd-sqlite3 libaprutil1-ldap libconfig-inifiles-perl libdbd-mysql-perl
+ libdbi-perl libjemalloc1 liblua5.2-0 libmysqlclient20 libopts25
+ libterm-readkey-perl mariadb-client-10.1 mariadb-client-core-10.1 mariadb-common
+ mariadb-server-10.1 mariadb-server-core-10.1 mysql-common sntp socat
+0 upgraded, 0 newly installed, 25 to remove and 23 not upgraded.
+After this operation, 189 MB disk space will be freed.
+Do you want to continue? [Y/n]
+```
+
+To purge them, use the `--purge` option together with the command for that.
+
+```
+$ sudo apt-get autoremove --purge
+Reading package lists... Done
+Building dependency tree
+Reading state information... Done
+The following packages will be REMOVED:
+ apache2-bin* apache2-data* apache2-utils* galera-3* libaio1* libapr1* libaprutil1*
+ libaprutil1-dbd-sqlite3* libaprutil1-ldap* libconfig-inifiles-perl*
+ libdbd-mysql-perl* libdbi-perl* libjemalloc1* liblua5.2-0* libmysqlclient20*
+ libopts25* libterm-readkey-perl* mariadb-client-10.1* mariadb-client-core-10.1*
+ mariadb-common* mariadb-server-10.1* mariadb-server-core-10.1* mysql-common* sntp*
+ socat*
+0 upgraded, 0 newly installed, 25 to remove and 23 not upgraded.
+After this operation, 189 MB disk space will be freed.
+Do you want to continue? [Y/n]
+```
+
+### 2) Empty The Trash Can
+
+There might a be chance, that you may have a large amount of useless data residing in your trash can.
+
+It takes up your system space. This is one of the best way to clear up those and get some free space on your system.
+
+To clean up this, simple use the file manager to empty your trash can.
+[![][2]![][2]][4]
+
+### 3) Clean up the APT cache
+
+Ubuntu uses **[APT Command][5]** (Advanced Package Tool) for package management like installing, removing, searching, etc,.
+
+By default every Linux operating system keeps a cache of downloaded and installed packages on their respective directory.
+
+Ubuntu also does the same, it keeps every updates it downloads and installs in a cache on your disk.
+
+Ubuntu system keeps a cache of DEB packages in /var/cache/apt/archives directory.
+
+Over time, this cache can quickly grow and hold a lot of space on your system.
+
+Run the following command to check the current utilization of APT cache.
+
+```
+$ sudo du -sh /var/cache/apt
+147M /var/cache/apt
+```
+
+It cleans obsolete deb-packages. I mean to say, less than clean.
+
+```
+$ sudo apt-get autoclean
+```
+
+It removes all packages kept in the apt cache.
+
+```
+$ sudo apt-get clean
+```
+
+### 4) Uninstall the unused applications
+
+I would request you to check the installed packages and games on your system and delete them if you are using rarely.
+
+This can be easily done via “Ubuntu Software Center”.
+[![][2]![][2]][6]
+
+### 5) Clean up the thumbnail cache
+
+The cache folder is a place where programs stored data they may need again, it is kept for speed but is not essential to keep. It can be generated again or downloaded again.
+
+If it’s really filling up your hard drive then you can delete things without worrying.
+
+Run the following command to check the current utilization of APT cache.
+
+```
+$ du -sh ~/.cache/thumbnails/
+412K /home/daygeek/.cache/thumbnails/
+```
+
+Run the following command to delete them permanently from your system.
+
+```
+$ rm -rf ~/.cache/thumbnails/*
+```
+
+--------------------------------------------------------------------------------
+
+via: https://www.2daygeek.com/linux-remove-delete-unwanted-junk-files-free-up-space-ubuntu-mint-debian/
+
+作者:[Magesh Maruthamuthu][a]
+选题:[lujun9972][b]
+译者:[译者ID](https://github.com/译者ID)
+校对:[校对者ID](https://github.com/校对者ID)
+
+本文由 [LCTT](https://github.com/LCTT/TranslateProject) 原创编译,[Linux中国](https://linux.cn/) 荣誉推出
+
+[a]: https://www.2daygeek.com/author/magesh/
+[b]: https://github.com/lujun9972
+[1]: https://www.2daygeek.com/how-to-check-disk-space-usage-using-df-command/
+[2]: data:image/gif;base64,R0lGODlhAQABAIAAAAAAAP///yH5BAEAAAAALAAAAAABAAEAAAIBRAA7
+[3]: https://www.2daygeek.com/wp-content/uploads/2019/06/remove-delete-Unwanted-Junk-Files-free-up-space-ubuntu-mint-debian-1.jpg
+[4]: https://www.2daygeek.com/wp-content/uploads/2019/06/remove-delete-Unwanted-Junk-Files-free-up-space-ubuntu-mint-debian-2.jpg
+[5]: https://www.2daygeek.com/apt-command-examples-manage-packages-debian-ubuntu-systems/
+[6]: https://www.2daygeek.com/wp-content/uploads/2019/06/remove-delete-Unwanted-Junk-Files-free-up-space-ubuntu-mint-debian-3.jpg
diff --git a/sources/tech/20190610 Applications for writing Markdown.md b/sources/tech/20190610 Applications for writing Markdown.md
new file mode 100644
index 0000000000..782ee8a0ee
--- /dev/null
+++ b/sources/tech/20190610 Applications for writing Markdown.md
@@ -0,0 +1,76 @@
+[#]: collector: (lujun9972)
+[#]: translator: (murphyzhao)
+[#]: reviewer: ( )
+[#]: publisher: ( )
+[#]: url: ( )
+[#]: subject: (Applications for writing Markdown)
+[#]: via: (https://fedoramagazine.org/applications-for-writing-markdown/)
+[#]: author: (Ryan Lerch https://fedoramagazine.org/author/ryanlerch/)
+
+Applications for writing Markdown
+======
+
+![][1]
+
+Markdown is a lightweight markup language that is useful for adding formatting while still maintaining readability when viewing as plain text. Markdown (and Markdown derivatives) are used extensively as the priumary form of markup of documents on services like GitHub and pagure. By design, Markdown is easily created and edited in a text editor, however, there are a multitude of editors available that provide a formatted preview of Markdown markup, and / or provide a text editor that highlights the markdown syntax.
+
+This article covers 3 desktop applications for Fedora Workstation that help out when editing Markdown.
+
+### UberWriter
+
+[UberWriter][2] is a minimal Markdown editor and previewer that allows you to edit in text, and preview the rendered document.
+
+![][3]
+
+The editor itself has inline previews built in, so text marked up as bold is displayed bold. The editor also provides inline previews for images, formulas, footnotes, and more. Ctrl-clicking one of these items in the markup provides an instant preview of that element to appear.
+
+In addition to the editor features, UberWriter also features a full screen mode and a focus mode to help minimise distractions. Focus mode greys out all but the current paragraph to help you focus on that element in your document
+
+Install UberWriter on Fedora from the 3rd-party Flathub repositories. It can be installed directly from the Software application after [setting up your system to install from Flathub][4]
+
+### Marker
+
+Marker is a Markdown editor that provides a simple text editor to write Markdown in, and provides a live preview of the rendered document. The interface is designed with a split screen layout with the editor on the left, and the live preview on the right.
+
+![][5]
+
+Additionally, Marker allows you to export you document in a range of different formats, including HTML, PDF, and the Open Document Format (ODF).
+
+Install Marker on Fedora from the 3rd-party Flathub repositories. It can be installed directly from the Software application after [setting up your system to install from Flathub][4]
+
+### Ghostwriter
+
+Where the previous editors are more focussed on a minimal user experice, Ghostwriter provides many more features and options to play with. Ghostwriter provides a text editor that is partially styled as you write in Markdown format. Bold text is bold, and headings are in a larger font to assist in writing the markup.
+
+![][6]
+
+It also provides a split screen with a live updating preview of the rendered document.
+
+![][7]
+
+Ghostwriter also includes a range of other features, including the ability to choose the Markdown flavour that the preview is rendered in, as well as the stylesheet used to render the preview too.
+
+Additionally, it provides a format menu (and keyboard shortcuts) to insert some of the frequent markdown ‘tags’ like bold, bullets, and italics.
+
+Install Ghostwriter on Fedora from the 3rd-party Flathub repositories. It can be installed directly from the Software application after [setting up your system to install from Flathub][4]
+
+--------------------------------------------------------------------------------
+
+via: https://fedoramagazine.org/applications-for-writing-markdown/
+
+作者:[Ryan Lerch][a]
+选题:[lujun9972][b]
+译者:[译者ID](https://github.com/译者ID)
+校对:[校对者ID](https://github.com/校对者ID)
+
+本文由 [LCTT](https://github.com/LCTT/TranslateProject) 原创编译,[Linux中国](https://linux.cn/) 荣誉推出
+
+[a]: https://fedoramagazine.org/author/ryanlerch/
+[b]: https://github.com/lujun9972
+[1]: https://fedoramagazine.org/wp-content/uploads/2019/06/markdownapps.png-816x345.jpg
+[2]: https://uberwriter.github.io/uberwriter/#1
+[3]: https://fedoramagazine.org/wp-content/uploads/2019/06/uberwriter-editor-1.png
+[4]: https://fedoramagazine.org/install-flathub-apps-fedora/
+[5]: https://fedoramagazine.org/wp-content/uploads/2019/06/marker-screenshot-1024x500.png
+[6]: https://fedoramagazine.org/wp-content/uploads/2019/06/ghostwriter-1024x732.png
+[7]: https://fedoramagazine.org/wp-content/uploads/2019/06/ghostwriter2-1024x566.png
diff --git a/sources/tech/20190610 Blockchain 2.0 - EOS.IO Is Building Infrastructure For Developing DApps -Part 13.md b/sources/tech/20190610 Blockchain 2.0 - EOS.IO Is Building Infrastructure For Developing DApps -Part 13.md
new file mode 100644
index 0000000000..a44ceeb105
--- /dev/null
+++ b/sources/tech/20190610 Blockchain 2.0 - EOS.IO Is Building Infrastructure For Developing DApps -Part 13.md
@@ -0,0 +1,88 @@
+[#]: collector: (lujun9972)
+[#]: translator: ( )
+[#]: reviewer: ( )
+[#]: publisher: ( )
+[#]: url: ( )
+[#]: subject: (Blockchain 2.0 – EOS.IO Is Building Infrastructure For Developing DApps [Part 13])
+[#]: via: (https://www.ostechnix.com/blockchain-2-0-eos-io-is-building-infrastructure-for-developing-dapps/)
+[#]: author: (editor https://www.ostechnix.com/author/editor/)
+
+Blockchain 2.0 – EOS.IO Is Building Infrastructure For Developing DApps [Part 13]
+======
+
+![Building infrastructure for Developing DApps][1]
+
+When a blockchain startup makes over **$4 billion** through an ICO without having a product or service to show for it, that is newsworthy. It becomes clear at this point that people invested these billions on this project because it seemed to promise a lot. This post will seek to demystify this mystical and seemingly powerful platform.
+
+**EOS.IO** is a [**blockchain**][2] platform that aims to develop standardized infrastructure including an application protocol and operating system for developing DApps ([ **distributed applications**][3]). **Block.one** the lead developer and investor in the project envisions **EOS.IO as the world’s’ first distributed operating system** providing a developing environment for decentralized applications. The system is meant to mirror a real computer by simulating hardware such as its CPUs, GPUs, and even RAM, apart from the obvious storage solutions courtesy of the blockchain database system.
+
+### Who is block.one?
+
+Block.one is the company behind EOS.IO. They developed the platform from the ground up based on a white paper published on GitHub. Block.one also spearheaded the yearlong “continuous” ICO that eventually made them a whopping $4 billion. They have one of the best teams of backers and advisors any company in the blockchain space can hope for with partnerships from **Bitmain** , **Louis Bacon** and **Alan Howard** among others. Not to mention **Peter Thiel** being one of the lead investors in the company. The expectations from their purported platform the EOS.IO and their crypto VC fund **EOS.VC** are high indeed.
+
+### What is EOS.IO?
+
+It is difficult to arrive at a short description for EOS.IO. The platform aims to position itself as a world wide computer with virtually simulated resources, hence creating a virtual environment for distributed applications to be built and run. The team behind EOS.IO aims achieve the following by directly quoting [**Ethereum**][4] as competition.
+
+ * Increase transaction throughput to millions per second,
+
+ * Reduce transaction costs to insignificant sums or remove them altogether.
+
+
+
+
+Though EOS.IO is not anywhere near solving any of these problems, the platform has a few capabilities that make it noteworthy as an alternative to Ethereum for DApp enthusiasts and developers.
+
+ 1. **Scalability** : EOS.IO uses a different consensus algorithm for handling blocks called **DPoS**. We’ve described it briefly below. The DPoS system basically allows the system to handle far more requests at better speeds than Ethereum is capable of with its **PoW** algorithm. The claim is that because they’ll be able to handle such massive throughputs they’ll be able to afford transactions at insignificant or even zero charges if need be.
+ 2. **Governance capabilities** : The consensus algorithm allows EOS.IO to dynamically understand malicious user (or node) behaviour to penalize or deactivate the user. The elected delegate feature of the delegated proof of stake system also ensures faster amendments to the rules that govern the network and its users.
+ 3. **Parallel processing** : Touted to another major feature. This will basically allow programs on the EOS.IO blockchain to utilize multiple computers or processors or even computing resources such as GPUs to parallelly processes large chunks of data and blocks. This is not yet seen in a roll out ready form. (This however is not a unique feature of EOS.IO. [**Hyperledger Sawtooth**][5] and Burrow for instance support the same at the moment).
+ 4. **Self-sufficiency** : The system has a built-in grievance system along with well defined incentive and penal systems for providing feedback for acceptable and non-acceptable behaviour. This means that the platform has a governance system without actually having a central governing body.
+
+
+
+All or at least most of the selling points of the system is based on the consensus algorithm it follows, DPoS. We explore more about the same below.
+
+### What is the delegated Proof of Stake (DPoS) consensus algorithm?
+
+As far as blockchains are concerned consensus algorithms are what gives them the strength and the selling point they need. However, as a general rule of thumb, as the “openness” and immutability of the ledger increases so does the computational power that is required to run it. For instance, if a blockchain intends to be secure against intrusion, be safe and immutable with respect to data, while being accessible to a lot of users, it will use up a lot of computing power in creating and maintaining itself. Think of it as a number lock. A 6-digit pin code is safer than a 3-digit pin code, but the latter will be easier and faster to open, now consider a million of these locks but with limited manpower to open them, and you get the scale at which blockchains operate and how much these consensus algorithms matter.
+
+In fact, this is a major area where competing platforms differ from each other. Hyperledger Sawtooth uses a proof of elapsed time algorithm (PoET), while ethereum uses a slightly modified proof of work (PoW) algorithm. Each of these have their own pros and cons which we will cover in a detailed post later on. However, for now, to be noted is that EOS.IO uses a delegated proof of stake mechanism for attesting and validating blocks under it. This has the following implications for users.
+
+Only one node can actively change the status of data written on the blockchain. In the case of a DPoS based system, this validator node is selected as part of a delegation by all the token holders of the blockchain. Every token holder gets to vote and have a say in who should be a validator. The weight the vote carries is usually proportional to the number of tokens the user carries. This is seen as a democratic way to ensure centralized accountability in terms of running the network. Furthermore, the validator is given additional monetary incentives to keep the network running smoothly and without friction. In case a validator or delegate member who is elected appears to be malicious, the system automatically votes out the said node member.
+
+DPoS system is efficient as it requires fewer computing resources to cast a vote and select a leader to validate. Further, it incentivizes good behaviour and penalizes bad ones leading to self-correction and maintenance of the blockchain. **The average transaction time for PoW vs DPoS is 10 minutes vs 10 seconds**. The downside to this paradigm being centralized operations, weighted voting systems, lack of redundancy, and possible malicious behaviour from the validator.
+
+To understand the difference between PoW and DPoS, imagine this: Let’s say your network has 100 participants out of which 10 are capable of handling validator duties and you need to choose one to do the same. In PoW, you give each of them a tough problem to solve to know who’s the fastest and smartest. You give the validator position to the winner and reward them for the same. In the DPoS system, the rest of the members vote for the person they think should hold the position. This is a simple matter of choosing based on arithmetic performance data based on the past. The node with the most votes win, and if the winner tries to do something fishy, the same electorate votes him out for the next transaction.
+
+### So does Ethereum lose out?
+
+While EOS.IO has miles to go before it even steps into the same ballpark as Ethereum with respect to the market cap and user base, EOS.IO targets specific shortfalls with Ethereum and solves them. We conclude this post by summarising some findings based on a 2017 [**paper**][6] written and published by **Ian Grigg**.
+
+ 1. The consensus algorithm used in the Ethereum (proof of work) platform uses far more computing resources and time to process transactions. This is true even for small block sizes. This limits its scaling potential and throughput. A meagre 15 transactions per second globally is no match for the over 2000 that payments network Visa manages. If the platform is to be adopted on a global scale based on a large scale roll out this is not acceptable.
+
+ 2. The reliance on proprietary languages, tool kits and protocols (including **Solidity** for instance) limits developer capability. Interoperability between platforms is also severely hurt due to this fact.
+
+ 3. This is rather subjective, however, the fact that Ethereum foundation refuses to acknowledge even the need for governance on the platform instead choosing to intervene on an ad-hoc manner when things turn sour on the network is not seen by many industry watchers as a sustainable model to be emulated in the future.
+
+
+
+
+--------------------------------------------------------------------------------
+
+via: https://www.ostechnix.com/blockchain-2-0-eos-io-is-building-infrastructure-for-developing-dapps/
+
+作者:[editor][a]
+选题:[lujun9972][b]
+译者:[译者ID](https://github.com/译者ID)
+校对:[校对者ID](https://github.com/校对者ID)
+
+本文由 [LCTT](https://github.com/LCTT/TranslateProject) 原创编译,[Linux中国](https://linux.cn/) 荣誉推出
+
+[a]: https://www.ostechnix.com/author/editor/
+[b]: https://github.com/lujun9972
+[1]: https://www.ostechnix.com/wp-content/uploads/2019/05/Developing-DApps-720x340.png
+[2]: https://www.ostechnix.com/blockchain-2-0-an-introduction/
+[3]: https://www.ostechnix.com/blockchain-2-0-explaining-distributed-computing-and-distributed-applications/
+[4]: https://www.ostechnix.com/blockchain-2-0-what-is-ethereum/
+[5]: https://www.ostechnix.com/blockchain-2-0-introduction-to-hyperledger-sawtooth/
+[6]: http://iang.org/papers/EOS_An_Introduction.pdf
diff --git a/sources/tech/20190610 Graviton- A Minimalist Open Source Code Editor.md b/sources/tech/20190610 Graviton- A Minimalist Open Source Code Editor.md
new file mode 100644
index 0000000000..2349f8b1c7
--- /dev/null
+++ b/sources/tech/20190610 Graviton- A Minimalist Open Source Code Editor.md
@@ -0,0 +1,94 @@
+[#]: collector: (lujun9972)
+[#]: translator: (geekpi)
+[#]: reviewer: ( )
+[#]: publisher: ( )
+[#]: url: ( )
+[#]: subject: (Graviton: A Minimalist Open Source Code Editor)
+[#]: via: (https://itsfoss.com/graviton-code-editor/)
+[#]: author: (Abhishek Prakash https://itsfoss.com/author/abhishek/)
+
+Graviton: A Minimalist Open Source Code Editor
+======
+
+[Graviton][1] is a free and open source, cross-platform code editor in development. The sixteen years old developer, Marc Espin, emphasizes that it is a ‘minimalist’ code editor. I am not sure about that but it does have a clean user interface like other [modern code editors like Atom][2].
+
+![Graviton Code Editor Interface][3]
+
+The developer also calls it a lightweight code editor despite the fact that Graviton is based on [Electron][4].
+
+Graviton comes with features you expect in any standard code editors like syntax highlighting, auto-completion etc. Since Graviton is still in the beta phase of development, more features will be added to it in the future releases.
+
+![Graviton Code Editor with Syntax Highlighting][5]
+
+### Feature of Graviton code editor
+
+Some of the main highlights of Graviton features are:
+
+ * Syntax highlighting for a number of programming languages using [CodeMirrorJS][6]
+ * Autocomplete
+ * Support for plugins and themes.
+ * Available in English, Spanish and a few other European languages.
+ * Available for Linux, Windows and macOS.
+
+
+
+I had a quick look at Graviton and it might not be as feature-rich as [VS Code][7] or [Brackets][8], but for some simple code editing, it’s not a bad tool.
+
+### Download and install Graviton
+
+![Graviton Code Editor][9]
+
+As mentioned earlier, Graviton is a cross-platform code editor available for Linux, Windows and macOS. It is still in beta stages which means that you more features will be added in future and you may encounter some bugs.
+
+You can find the latest version of Graviton on its release page. Debian and [Ubuntu users can install it from .deb file][10]. [AppImage][11] has been provided so that it could be used in other distributions. DMG and EXE files are also available for macOS and Windows respectively.
+
+[Download Graviton][12]
+
+If you are interested, you can find the source code of Graviton on its GitHub repository:
+
+[Graviton Source Code on GitHub][13]
+
+If you decided to use Graviton and find some issues, please open a bug report [here][14]. If you use GitHub, you may want to star the Graviton project. This boosts the morale of the developer as he would know that more users are appreciating his efforts.
+
+[][15]
+
+Suggested read Get Windows Style Sticky Notes For Ubuntu with Indicator Stickynotes
+
+I believe you know [how to install a software from source code][16] if you are taking that path.
+
+**In the end…**
+
+Sometimes, simplicity itself becomes a feature and the Graviton’s focus on being minimalist could help it form a niche for itself in the already crowded segment of code editors.
+
+At It’s FOSS, we try to highlight open source software. If you know some interesting open source software that you would like more people to know about, [do send us a note][17].
+
+--------------------------------------------------------------------------------
+
+via: https://itsfoss.com/graviton-code-editor/
+
+作者:[Abhishek Prakash][a]
+选题:[lujun9972][b]
+译者:[译者ID](https://github.com/译者ID)
+校对:[校对者ID](https://github.com/校对者ID)
+
+本文由 [LCTT](https://github.com/LCTT/TranslateProject) 原创编译,[Linux中国](https://linux.cn/) 荣誉推出
+
+[a]: https://itsfoss.com/author/abhishek/
+[b]: https://github.com/lujun9972
+[1]: https://graviton.ml/
+[2]: https://itsfoss.com/best-modern-open-source-code-editors-for-linux/
+[3]: https://i0.wp.com/itsfoss.com/wp-content/uploads/2019/06/graviton-code-editor-interface.jpg?resize=800%2C571&ssl=1
+[4]: https://electronjs.org/
+[5]: https://i0.wp.com/itsfoss.com/wp-content/uploads/2019/06/graviton-code-editor-interface-2.jpg?resize=800%2C522&ssl=1
+[6]: https://codemirror.net/
+[7]: https://itsfoss.com/install-visual-studio-code-ubuntu/
+[8]: https://itsfoss.com/install-brackets-ubuntu/
+[9]: https://i1.wp.com/itsfoss.com/wp-content/uploads/2019/06/graviton-code-editor-800x473.jpg?resize=800%2C473&ssl=1
+[10]: https://itsfoss.com/install-deb-files-ubuntu/
+[11]: https://itsfoss.com/use-appimage-linux/
+[12]: https://github.com/Graviton-Code-Editor/Graviton-App/releases
+[13]: https://github.com/Graviton-Code-Editor/Graviton-App
+[14]: https://github.com/Graviton-Code-Editor/Graviton-App/issues
+[15]: https://itsfoss.com/indicator-stickynotes-windows-like-sticky-note-app-for-ubuntu/
+[16]: https://itsfoss.com/install-software-from-source-code/
+[17]: https://itsfoss.com/contact-us/
diff --git a/sources/tech/20190610 Search Linux Applications On AppImage, Flathub And Snapcraft Platforms.md b/sources/tech/20190610 Search Linux Applications On AppImage, Flathub And Snapcraft Platforms.md
new file mode 100644
index 0000000000..dd0c986e72
--- /dev/null
+++ b/sources/tech/20190610 Search Linux Applications On AppImage, Flathub And Snapcraft Platforms.md
@@ -0,0 +1,91 @@
+[#]: collector: (lujun9972)
+[#]: translator: ( )
+[#]: reviewer: ( )
+[#]: publisher: ( )
+[#]: url: ( )
+[#]: subject: (Search Linux Applications On AppImage, Flathub And Snapcraft Platforms)
+[#]: via: (https://www.ostechnix.com/search-linux-applications-on-appimage-flathub-and-snapcraft-platforms/)
+[#]: author: (sk https://www.ostechnix.com/author/sk/)
+
+Search Linux Applications On AppImage, Flathub And Snapcraft Platforms
+======
+
+![Search Linux Applications On AppImage, Flathub And Snapcraft][1]
+
+Linux is evolving day by day. In the past, the developers had to build applications separately for different Linux distributions. Since there are several Linux variants exists, building apps for all distributions became tedious task and quite time consuming. Then some developers invented package converters and builders such as [**Checkinstall**][2], [**Debtap**][3] and [**Fpm**][4]. But they didn’t completely solved the problem. All of these tools will simply convert one package format to another. We still need to find and install the required dependencies the app needs to run.
+
+Well, the time has changed. We have now universal Linux apps. Meaning – we can install these applications on most Linux distributions. Be it Arch Linux, Debian, CentOS, Redhat, Ubuntu or any popular Linux distribution, the Universal apps will work just fine out of the box. These applications are packaged with all necessary libraries and dependencies in a single bundle. All we have to do is to download and run them on any Linux distributions of our choice. The popular universal app formats are **AppImages** , [**Flatpaks**][5] and [**Snaps**][6].
+
+The AppImages are created and maintained by **Simon peter**. Many popular applications, like Gimp, Firefox, Krita and a lot more, are available in these formats and available directly on their download pages.Just download them, make it executable and run it in no time. You don’t even root permissions to run AppImages.
+
+The developer of Flatpak is **Alexander Larsson** (a RedHat employee). The Flatpak apps are hosted in a central repository (store) called **“Flathub”**. If you’re a developer, you are encouraged to build your apps in Flatpak format and distribute them to the users via Flathub.
+
+The **Snaps** are created mainly for Ubuntu, by **Canonical**. However, the developers of other Linux distributions are started to contribute to Snap packing format. So, Snaps will work on other Linux distributions as well. The Snaps can be downloaded either directly from application’s download page or from **Snapcraft** store.
+
+Many popular Companies and developers have released their applications in AppImage, Flatpak and Snap formats. If you ever looking for an app, just head over to the respective store and grab the application of your choice and run it regardless of the Linux distribution you use.
+
+There is also a command line universal app search tool called **“Chob”** is available to easily search Linux Applications on AppImage, Flathub and Snapcraft platforms. This tool will only search for the given application and display official link in your default browser. It won’t install them. This guide will explain how to install Chob and use it to search AppImages, Flatpaks and Snaps on Linux.
+
+### Search Linux Applications On AppImage, Flathub And Snapcraft Platforms Using Chob
+
+Download the latest Chob binary file from the [**releases page**][7]. As of writing this guide, the latest version was **0.3.5**.
+
+```
+$ wget https://github.com/MuhammedKpln/chob/releases/download/0.3.5/chob-linux
+```
+
+Make it executable:
+
+```
+$ chmod +x chob-linux
+```
+
+Finally, search the applications you want. For example, I am going to search applications related to **Vim**.
+
+```
+$ ./chob-linux vim
+```
+
+Chob will search for the given application (and related) on AppImage, Flathub and Snapcraft platforms and display the results.
+
+![][8]
+
+Search Linux applications Using Chob
+
+Just choose the application you want by typing the appropriate number to open the official link of the selected app in your default web browser where you can read the details of the app.
+
+![][9]
+
+View Linux application’s Details In Browser
+
+For more details, have a look at the Chob official GitHub page given below.
+
+**Resource:**
+
+ * [**Chob GitHub Repository**][10]
+
+
+
+--------------------------------------------------------------------------------
+
+via: https://www.ostechnix.com/search-linux-applications-on-appimage-flathub-and-snapcraft-platforms/
+
+作者:[sk][a]
+选题:[lujun9972][b]
+译者:[译者ID](https://github.com/译者ID)
+校对:[校对者ID](https://github.com/校对者ID)
+
+本文由 [LCTT](https://github.com/LCTT/TranslateProject) 原创编译,[Linux中国](https://linux.cn/) 荣誉推出
+
+[a]: https://www.ostechnix.com/author/sk/
+[b]: https://github.com/lujun9972
+[1]: https://www.ostechnix.com/wp-content/uploads/2019/05/chob-720x340.png
+[2]: https://www.ostechnix.com/build-packages-source-using-checkinstall/
+[3]: https://www.ostechnix.com/convert-deb-packages-arch-linux-packages/
+[4]: https://www.ostechnix.com/build-linux-packages-multiple-platforms-easily/
+[5]: https://www.ostechnix.com/flatpak-new-framework-desktop-applications-linux/
+[6]: https://www.ostechnix.com/introduction-ubuntus-snap-packages/
+[7]: https://github.com/MuhammedKpln/chob/releases
+[8]: http://www.ostechnix.com/wp-content/uploads/2019/05/Search-Linux-applications-Using-Chob.png
+[9]: http://www.ostechnix.com/wp-content/uploads/2019/05/View-Linux-applications-Details.png
+[10]: https://github.com/MuhammedKpln/chob
diff --git a/sources/tech/20190610 Tmux Command Examples To Manage Multiple Terminal Sessions.md b/sources/tech/20190610 Tmux Command Examples To Manage Multiple Terminal Sessions.md
new file mode 100644
index 0000000000..d9ed871a10
--- /dev/null
+++ b/sources/tech/20190610 Tmux Command Examples To Manage Multiple Terminal Sessions.md
@@ -0,0 +1,296 @@
+[#]: collector: (lujun9972)
+[#]: translator: ( )
+[#]: reviewer: ( )
+[#]: publisher: ( )
+[#]: url: ( )
+[#]: subject: (Tmux Command Examples To Manage Multiple Terminal Sessions)
+[#]: via: (https://www.ostechnix.com/tmux-command-examples-to-manage-multiple-terminal-sessions/)
+[#]: author: (sk https://www.ostechnix.com/author/sk/)
+
+Tmux Command Examples To Manage Multiple Terminal Sessions
+======
+
+![tmux command examples][1]
+
+We’ve already learned to use [**GNU Screen**][2] to manage multiple Terminal sessions. Today, we will see yet another well-known command-line utility named **“Tmux”** to manage Terminal sessions. Similar to GNU Screen, Tmux is also a Terminal multiplexer that allows us to create number of terminal sessions and run more than one programs or processes at the same time inside a single Terminal window. Tmux is free, open source and cross-platform program that supports Linux, OpenBSD, FreeBSD, NetBSD and Mac OS X. In this guide, we will discuss most-commonly used Tmux commands in Linux.
+
+### Installing Tmux in Linux
+
+Tmux is available in the official repositories of most Linux distributions.
+
+On Arch Linux and its variants, run the following command to install it.
+
+```
+$ sudo pacman -S tmux
+```
+
+On Debian, Ubuntu, Linux Mint:
+
+```
+$ sudo apt-get install tmux
+```
+
+On Fedora:
+
+```
+$ sudo dnf install tmux
+```
+
+On RHEL and CentOS:
+
+```
+$ sudo yum install tmux
+```
+
+On SUSE/openSUSE:
+
+```
+$ sudo zypper install tmux
+```
+
+Well, we have just installed Tmux. Let us go ahead and see some examples to learn how to use Tmux.
+
+### Tmux Command Examples To Manage Multiple Terminal Sessions
+
+The default prefix shortcut to all commands in Tmux is **Ctrl+b**. Just remember this keyboard shortcut when using Tmux.
+
+* * *
+
+**Note:** The default prefix to all **Screen** commands is **Ctrl+a**.
+
+* * *
+
+##### Creating Tmux sessions
+
+To create a new Tmux session and attach to it, run the following command from the Terminal:
+
+```
+tmux
+```
+
+Or,
+
+```
+tmux new
+```
+
+Once you are inside the Tmux session, you will see a **green bar at the bottom** as shown in the screenshot below.
+
+![][3]
+
+New Tmux session
+
+It is very handy to verify whether you’re inside a Tmux session or not.
+
+##### Detaching from Tmux sessions
+
+To detach from a current Tmux session, just press **Ctrl+b** and **d**. You don’t need to press this both Keyboard shortcut at a time. First press “Ctrl+b” and then press “d”.
+
+Once you’re detached from a session, you will see an output something like below.
+
+```
+[detached (from session 0)]
+```
+
+##### Creating named sessions
+
+If you use multiple sessions, you might get confused which programs are running on which sessions. In such cases, you can just create named sessions. For example if you wanted to perform some activities related to web server in a session, just create the Tmux session with a custom name, for example **“webserver”** (or any name of your choice).
+
+```
+tmux new -s webserver
+```
+
+Here is the new named Tmux session.
+
+![][4]
+
+Tmux session with a custom name
+
+As you can see in the above screenshot, the name of the Tmux session is **webserver**. This way you can easily identify which program is running on which session.
+
+To detach, simply press **Ctrl+b** and **d**.
+
+##### List Tmux sessions
+
+To view the list of open Tmux sessions, run:
+
+```
+tmux ls
+```
+
+Sample output:
+
+![][5]
+
+List Tmux sessions
+
+As you can see, I have two open Tmux sessions.
+
+##### Creating detached sessions
+
+Sometimes, you might want to simply create a session and don’t want to attach to it automatically.
+
+To create a new detached session named **“ostechnix”** , run:
+
+```
+tmux new -s ostechnix -d
+```
+
+The above command will create a new Tmux session called “ostechnix”, but won’t attach to it.
+
+You can verify if the session is created using “tmux ls” command:
+
+![][6]
+
+Create detached Tmux sessions
+
+##### Attaching to Tmux sessions
+
+You can attach to the last created session by running this command:
+
+```
+tmux attach
+```
+
+Or,
+
+```
+tmux a
+```
+
+If you want to attach to any specific named session, for example “ostechnix”, run:
+
+```
+tmux attach -t ostechnix
+```
+
+Or, shortly:
+
+```
+tmux a -t ostechnix
+```
+
+##### Kill Tmux sessions
+
+When you’re done and no longer required a Tmux session, you can kill it at any time with command:
+
+```
+tmux kill-session -t ostechnix
+```
+
+To kill when attached, press **Ctrl+b** and **x**. Hit “y” to kill the session.
+
+You can verify if the session is closed with “tmux ls” command.
+
+To Kill Tmux server along with all Tmux sessions, run:
+
+```
+tmux kill-server
+```
+
+Be careful! This will terminate all Tmux sessions even if there are any running jobs inside the sessions without any warning.
+
+When there were no running Tmux sessions, you will see the following output:
+
+```
+$ tmux ls
+no server running on /tmp/tmux-1000/default
+```
+
+##### Split Tmux Session Windows
+
+Tmux has an option to split a single Tmux session window into multiple smaller windows called **Tmux panes**. This way we can run different programs on each pane and interact with all of them simultaneously. Each pane can be resized, moved and closed without affecting the other panes. We can split a Tmux window either horizontally or vertically or both at once.
+
+**Split panes horizontally**
+
+To split a pane horizontally, press **Ctrl+b** and **”** (single quotation mark).
+
+![][7]
+
+Split Tmux pane horizontally
+
+Use the same key combination to split the panes further.
+
+**Split panes vertically**
+
+To split a pane vertically, press **Ctrl+b** and **%**.
+
+![][8]
+
+Split Tmux panes vertically
+
+**Split panes horizontally and vertically**
+
+We can also split a pane horizontally and vertically at the same time. Take a look at the following screenshot.
+
+![][9]
+
+Split Tmux panes
+
+First, I did a horizontal split by pressing **Ctrl+b “** and then split the lower pane vertically by pressing **Ctrl+b %**.
+
+As you see in the above screenshot, I am running three different programs on each pane.
+
+**Switch between panes**
+
+To switch between panes, press **Ctrl+b** and **Arrow keys (Left, Right, Up, Down)**.
+
+**Send commands to all panes**
+
+In the previous example, we run three different commands on each pane. However, it is also possible to run send the same commands to all panes at once.
+
+To do so, press **Ctrl+b** and type the following command and hit ENTER:
+
+```
+:setw synchronize-panes
+```
+
+Now type any command on any pane. You will see that the same command is reflected on all panes.
+
+**Swap panes**
+
+To swap panes, press **Ctrl+b** and **o**.
+
+**Show pane numbers**
+
+Press **Ctrl+b** and **q** to show pane numbers.
+
+**Kill panes**
+
+To kill a pane, simply type **exit** and ENTER key. Alternatively, press **Ctrl+b** and **x**. You will see a confirmation message. Just press **“y”** to close the pane.
+
+![][10]
+
+Kill Tmux panes
+
+At this stage, you will get a basic idea of Tmux and how to use it to manage multiple Terminal sessions. For more details, refer man pages.
+
+```
+$ man tmux
+```
+
+Both GNU Screen and Tmux utilities can be very helpful when managing servers remotely via SSH. Learn Screen and Tmux commands thoroughly to manage your remote servers like a pro.
+
+--------------------------------------------------------------------------------
+
+via: https://www.ostechnix.com/tmux-command-examples-to-manage-multiple-terminal-sessions/
+
+作者:[sk][a]
+选题:[lujun9972][b]
+译者:[译者ID](https://github.com/译者ID)
+校对:[校对者ID](https://github.com/校对者ID)
+
+本文由 [LCTT](https://github.com/LCTT/TranslateProject) 原创编译,[Linux中国](https://linux.cn/) 荣誉推出
+
+[a]: https://www.ostechnix.com/author/sk/
+[b]: https://github.com/lujun9972
+[1]: https://www.ostechnix.com/wp-content/uploads/2019/06/Tmux-720x340.png
+[2]: https://www.ostechnix.com/screen-command-examples-to-manage-multiple-terminal-sessions/
+[3]: https://www.ostechnix.com/wp-content/uploads/2019/06/Tmux-session.png
+[4]: https://www.ostechnix.com/wp-content/uploads/2019/06/Named-Tmux-session.png
+[5]: https://www.ostechnix.com/wp-content/uploads/2019/06/List-Tmux-sessions.png
+[6]: https://www.ostechnix.com/wp-content/uploads/2019/06/Create-detached-sessions.png
+[7]: https://www.ostechnix.com/wp-content/uploads/2019/06/Horizontal-split.png
+[8]: https://www.ostechnix.com/wp-content/uploads/2019/06/Vertical-split.png
+[9]: https://www.ostechnix.com/wp-content/uploads/2019/06/Split-Panes.png
+[10]: https://www.ostechnix.com/wp-content/uploads/2019/06/Kill-panes.png
diff --git a/sources/tech/20190610 Welcoming Blockchain 3.0.md b/sources/tech/20190610 Welcoming Blockchain 3.0.md
new file mode 100644
index 0000000000..7c8579cd92
--- /dev/null
+++ b/sources/tech/20190610 Welcoming Blockchain 3.0.md
@@ -0,0 +1,113 @@
+[#]: collector: (lujun9972)
+[#]: translator: (murphyzhao)
+[#]: reviewer: ( )
+[#]: publisher: ( )
+[#]: url: ( )
+[#]: subject: (Welcoming Blockchain 3.0)
+[#]: via: (https://www.ostechnix.com/welcoming-blockchain-3-0/)
+[#]: author: (sk https://www.ostechnix.com/author/sk/)
+
+Welcoming Blockchain 3.0
+======
+
+![Welcoming blockchain 3.0][1]
+
+Image credit :
+
+The series of posts [**“Blockchain 2.0”**][2] discussed about the evolution of blockchain technology since the advent of cryptocurrencies since the Bitcoin in 2008. This post will seek to explore the future of blockchains. Lovably called **blockchain 3.0** , this new wave of DLT evolution will answer the issues faced with blockchains currently (each of which will be summarized here). The next version of the tech standard will also bring new applications and use cases. At the end of the post we will also look at a few examples of these principles currently applied.
+
+Few of the shortcomings of blockchain platforms in existence are listed below with some proposed solutions to those answered afterward.
+
+### Problem 1: Scalability[1]
+
+This is seen as the first major hurdle to mainstream adoption. As previously discussed, a lot of limiting factors contribute to the blockchain’s in-capacity to process a lot of transactions at the same time. Existing networks such as [**Ethereum**][3] are capable of measly 10-15 transactions per second (TPS) whereas mainstream networks such as those employed by Visa for instance are capable of more than 2000 TPS. **Scalability** is an issue that plagues all modern database systems. Improved consensus algorithms and better blockchain architecture designs are improving it though as we see here.
+
+**Solving scalability**
+
+Implementing leaner and more efficient consensus algorithms have been proposed for solving issues of scalability without disturbing the primary structure of the blockchain. While most cryptocurrencies and blockchain platforms use resource intensive PoW algorithms (For instance, Bitcoin & Ethereum) to generate blocks, newer DPoS and PoET algorithms exist to solve this issue. DPoS and PoET algorithms (there are some more in development) require less resources to maintain the blockchain and have shown to have throughputs ranging up to 1000s of TPS rivalling that of popular non-blockchain systems.
+
+The second solution to scalability is altering the blockchain structure[1] and functionality altogether. We won’t get into finer details of this, but alternative architectures such as **Directed Acyclic Graph** ( **DAG** ) have been proposed to handle this issue. Essentially, the assumption for this to work is that not all network nodes need to have a copy of the entire blockchain for the blockchain to work or the participants to reap the benefits of a DLT system. The system does not require transactions to be validated by the entirety of the participants and simply requires the transactions to happen in a common frame of reference and be linked to each other.
+
+The DAG[2] approach is implemented in the Bitcoin system using an implementation called the **Lightning network** and Ethereum implements the same using their **Sharding** [3] protocol. At its heart a DAG implementation is not technically a blockchain. It’s more like a tangled maze, but still retains the peer to peer and distributed database properties of the blockchain. We will explore DAG and Tangle networks in a separate post later.
+
+### Problem 2: Interoperability[4][5]
+
+**Interoperability** is called cross-chain interaction is basically different blockchains being able to talk to each other to exchange metrics and information. With so many platforms that is hard to keep a count on at the moment and different companies coming up with proprietary systems for all the myriad of applications, interoperability between platforms is key. For instance, at the moment, someone who owns digital identities on one platform will not be able to exploit features presented by other platforms because the individual blockchains do not understand or know each other. Problems pertaining to lack of credible verifications, token exchange etc. still persist. A global roll out of [**smart contracts**][4] is also not viable without platforms being able to communicate with each other.
+
+**Solving Interoperability**
+
+There are protocols and platforms designed just for enabling interoperability at the moment. Such platforms implement atomic swaps protocols and provide open stages for different blockchain systems to communicate and exchange information between them. An example would be **“0x (ZRX)”** which is described later on.
+
+### Problem 3: Governance[6]
+
+Not a limitation in its own, **governance** in a public blockchain needs to act as a community moral compass where everyone’s opinion is taken into account on the operation of the blockchain. Combined and seen with scale this presents a problem where in either the protocols change far too frequently or the protocols are changed at the whims of a “central” authority who holds the most tokens. This is not an issue that most public blockchains are working to avoid right now since the scale at their operating in and the nature of their operations don’t require stricter supervision.
+
+**Solving Governance issues**
+
+The Tangled framework or the DAG mentioned above would almost eliminate the need and use for global (platform wide) governance laws. Instead a program can automatically oversee the transaction and user type and decide on the laws that need to be implemented.
+
+### Problem 4: Sustainability
+
+**Sustainability** builds on the scalability issue again. Current blockchains and cryptocurrencies are notorious for being not sustainable in the long run owing to the significant oversight that is still required and the amount of resources required to keep the systems running. If you’ve read reports of how “mining cryptocurrencies” have not been so profitable lately, this is what it was. The amount of resources required to keep up existing platforms running is simply not practical at a global scale with mainstream use.
+
+**Solving non-sustainability**
+
+From a resources or economic point of view the answer to sustainability would be similar to the one for scalability. However, for the system to be implemented on a global scale, laws and regulations need to endorse it. This however depends on the governments of the world. Favourable moves from the American and European governments have however renewed hopes in this aspect.
+
+### Problem 5: User adoption[7]
+
+Currently a hindrance to widespread consumer adoption of blockchain based applications is consumer unfamiliarity with the platform and the tech underneath it. The fact that most applications require some sort of a tech and computing background to figure out how they work does not help in this aspect either. The third wave of blockchain developments seek to lessen the gap between consumer knowledge and platform usability.
+
+**Solving the user adoption issue**
+
+The internet took a lot of time to be the way it is now. A lot of work has been done on developing a standardized internet technology stack over the years that has allowed the web to function the way it is now. Developers are working on user facing front end distributed applications that should act as a layer on top of existing web 3.0 technology while being supported by blockchains and open protocols underneath. Such [**distributed applications**][5] will make the underlying technology more familiar to users, hence increasing mainstream adoption.
+
+We’ve discussed about the solutions to the above issues theoretically, and now we proceed to show these being applied in the present scenario.
+
+**[0x][6]** – is a decentralized token exchange where users from different platforms can exchange tokens without the need of a central authority to vet the same. Their breakthrough comes in how they’ve designed the system to record and vet the blocks only after transactions are settled and not in between (to verify context, blocks preceding the transaction order is also verified normally) as is normally done. This allows for a more liquid faster exchange of digitized assets online.
+
+**[Cardano][7]** – founded by one of the co-founders of Ethereum, Cardano boasts of being a truly “scientific” platform with multiple reviews and strict protocols for the developed code and algorithms. Everything out of Cardano is assumed to be mathematically as optimized as possible. Their consensus algorithm called **Ouroboros** , is a modified Proof of Stake algorithm. Cardano is developed in [**Haskell**][8] and the smart contract engine uses a derivative of Haskell called **Plutus** for operating. Both are functional programming languages which guarantee secure transactions without compromising efficiency.
+
+**EOS** – We’ve already described EOS here in [**this post**][9].
+
+**[COTI][10]** – a rather obscure architecture, COTI entails no mining, and next to zero power consumption in operating. It also stores assets in offline wallets localized on user’s devices rather than a pure peer to peer network. They also follow a DAG based architecture and claim of processing throughputs of up to 10000 TPS. Their platform allows enterprises to build their own cryptocurrency and digitized currency wallets without exploiting a blockchain.
+
+**References:**
+
+ * [1] **A. P. Paper, K. Croman, C. Decker, I. Eyal, A. E. Gencer, and A. Juels, “On Scaling Decentralized Blockchains | SpringerLink,” 2018.**
+ * [2] [**Going Beyond Blockchain with Directed Acyclic Graphs (DAG)**][11]
+ * [3] [**Ethreum/wiki – On sharding blockchains**][12]
+ * [4] [**Why is blockchain interoperability important**][13]
+ * [5] [**The Importance of Blockchain Interoperability**][14]
+ * [6] **R. Beck, C. Müller-Bloch, and J. L. King, “Governance in the Blockchain Economy: A Framework and Research Agenda,” J. Assoc. Inf. Syst., pp. 1020–1034, 2018.**
+ * [7] **J. M. Woodside, F. K. A. Jr, W. Giberson, F. K. J. Augustine, and W. Giberson, “Blockchain Technology Adoption Status and Strategies,” J. Int. Technol. Inf. Manag., vol. 26, no. 2, pp. 65–93, 2017.**
+
+
+
+--------------------------------------------------------------------------------
+
+via: https://www.ostechnix.com/welcoming-blockchain-3-0/
+
+作者:[sk][a]
+选题:[lujun9972][b]
+译者:[译者ID](https://github.com/译者ID)
+校对:[校对者ID](https://github.com/校对者ID)
+
+本文由 [LCTT](https://github.com/LCTT/TranslateProject) 原创编译,[Linux中国](https://linux.cn/) 荣誉推出
+
+[a]: https://www.ostechnix.com/author/sk/
+[b]: https://github.com/lujun9972
+[1]: https://www.ostechnix.com/wp-content/uploads/2019/06/blockchain-720x340.jpg
+[2]: https://www.ostechnix.com/blockchain-2-0-an-introduction/
+[3]: https://www.ostechnix.com/blockchain-2-0-what-is-ethereum/
+[4]: https://www.ostechnix.com/blockchain-2-0-explaining-smart-contracts-and-its-types/
+[5]: https://www.ostechnix.com/blockchain-2-0-explaining-distributed-computing-and-distributed-applications/
+[6]: https://0x.org/
+[7]: https://www.cardano.org/en/home/
+[8]: https://www.ostechnix.com/getting-started-haskell-programming-language/
+[9]: https://www.ostechnix.com/blockchain-2-0-eos-io-is-building-infrastructure-for-developing-dapps/
+[10]: https://coti.io/
+[11]: https://cryptoslate.com/beyond-blockchain-directed-acylic-graphs-dag/
+[12]: https://github.com/ethereum/wiki/wiki/Sharding-FAQ#introduction
+[13]: https://www.capgemini.com/2019/02/can-the-interoperability-of-blockchains-change-the-world/
+[14]: https://medium.com/wanchain-foundation/the-importance-of-blockchain-interoperability-b6a0bbd06d11
diff --git a/translated/talk/20190405 Blockchain 2.0 - Ongoing Projects (The State Of Smart Contracts Now) -Part 6.md b/translated/talk/20190405 Blockchain 2.0 - Ongoing Projects (The State Of Smart Contracts Now) -Part 6.md
new file mode 100644
index 0000000000..3748d28dd8
--- /dev/null
+++ b/translated/talk/20190405 Blockchain 2.0 - Ongoing Projects (The State Of Smart Contracts Now) -Part 6.md
@@ -0,0 +1,100 @@
+[#]: collector: (lujun9972)
+[#]: translator: (wxy)
+[#]: reviewer: ( )
+[#]: publisher: ( )
+[#]: url: ( )
+[#]: subject: (Blockchain 2.0 – Ongoing Projects (The State Of Smart Contracts Now) [Part 6])
+[#]: via: (https://www.ostechnix.com/blockchain-2-0-ongoing-projects-the-state-of-smart-contracts-now/)
+[#]: author: (editor https://www.ostechnix.com/author/editor/)
+
+区块链 2.0:智能合约如今的发展(六)
+======
+
+![The State Of Smart Contracts Now][1]
+
+继续我们的[前面的关于智能合约的文章][2],这篇文章旨在讨论智能合约的形势,重点介绍目前正在该领域进行开发的一些项目和公司。如本系列前一篇文章中讨论的,智能合约是在区块链网络上存在并执行的程序。我们探讨了智能合约的工作原理以及它们优于传统数字平台的原因。这里描述的公司分布于各种各样的行业中,但是大多涉及到身份管理系统、金融服务、众筹系统等,因为这些是被认为最适合切换到基于区块链的数据库系统的领域。
+
+### 开放平台
+
+诸如 [Counterparty][8] 和 Solidity(以太坊)等平台是完全公用的构建模块,开发者可以以之创建自己的智能合约。大量的开发人员参与此类项目使这些项目成为开发智能合约、设计自己的加密货币令牌系统以及为区块链创建协议以实现功能的事实标准。许多值得称赞的项目都来源于它们。摩根大通派生自以太坊的 [Quorum][9],就是一个例子。而瑞波是另一个例子。
+
+### 管理金融交易
+
+通过互联网转账加密货币被吹捧为在未来几年的常态。与此相关的不足之处是:
+
+* 身份和钱包地址是匿名的。如果接收方不履行交易,则付款人没有任何第一追索权。
+* 错误交易(如果无法追踪任何交易)。
+* 密码生成的哈希密钥很难用于人类,人为错误是主要关注点。
+
+在这种情况下,可以让其他人暂时接受该交易并在接受尽职调查后与接收方结算。
+
+[EscrowMyEther][10] 和 [PAYFAIR][11] 是两个这样的托管平台。基本上,托管公司采用商定的金额并向接收方发送令牌。一旦接收方通过相同的托管平台提供付款人想要的内容,两者都会确认并最终付款。 这些得到了自由职业者和业余爱好者收藏家广泛在线使用。
+
+### 金融服务
+
+小额融资和小额保险项目的发展将改善世界上大多数贫穷或没有银行账户的人的银行金融服务。据估计,社会中较贫穷的“无银行账户”人群可以为银行和机构的增加 3800 亿美元收入 [^5]。这一金额取代了通过银行切换到区块链 DLT 预期可以节省的运营费用。
+
+位于美国中西部的 BankQu Inc. 的口号是“通过身份而尊严”。他们的平台允许个人设置他们自己的数字身份记录,其中所有交易将在区块链上实时审查和处理。在底层代码上记录并为其用户构建唯一的在线标识,从而实现超快速的交易和结算。BankQu 案例研究探讨了他们如何以这种方式帮助个人和公司,可以在[这里][3]看到。
+
+[Stratumn][12] 正在帮助保险公司通过自动执行早期由人类微观管理的任务来提供更好的保险服务。通过自动化、端到端可追溯性和高效的数据隐私方法,他们彻底改变了保险索赔的结算方式。改善客户体验以及显著降低成本,为客户和相关公司带来双赢局面。
+
+法国保险公司 [AXA][14] 目前正在试行类似的努力。其产品 [fizzy][13] 允许用户以少量费用订阅其服务并输入他们的航班详细信息。如果航班延误或遇到其他问题,该程序会自动搜索在线数据库,检查保险条款并将保险金额记入用户的帐户。这样就消除了用户或客户在手动检查条款后提出索赔的要求,并且一旦这样的系统成为主流,就不需要长期提出索赔,增加了航空公司的责任。
+
+### 跟踪所有权
+
+理论上可以利用 DLT 中的带时间戳的数据块来跟踪从创建到最终用户消费的媒体。Peertracks 公司 和 Mycelia 公司目前正在帮助音乐家发布内容,而不必担心其内容被盗或被滥用。他们帮助艺术家直接向粉丝和客户销售,同时获得工作报酬,而无需通过权利和唱片公司 [^9]。
+
+### 身份管理平台
+
+基于区块链的身份管理平台可以将你的身份存储在分布式分类帐本中。设置帐户后,会对其进行安全加密,然后将其发送给所有参与节点。但是,作为数据块的所有者,只有该用户才能访问该数据。一旦你在网络上建立身份并开始交易,网络中的自动程序将验证与你的帐户关联的先前所有的交易,在检查要求后将其发送给监管备案,并在程序认为交易合法时自动执行结算。这里的好处是,由于区块链上的数据是防篡改的,而智能合约以零偏差(或主观性)检查输入,如前所述,交易不需要任何人的监督或批准,并且需要小心是即刻生效的。
+
+像 [ShoCard][15] 、[Credits][16] 和 [OneName][17] 这样的初创公司目前正在推出类似的服务,目前正在与政府和社会机构进行谈判,以便将它们整合到主流用途中。
+
+开发商的其他独立项目如 Chris Ellis 和 David Duccini 分别开发或提出了替代的身份管理系统,分别是 “[世界公民][4]”和 [IDCoin][5]。Ellis 先生甚至通过在区块链网络上创建护照来证明他的工作能力。
+
+### 资源共享
+
+[Share & Charge][18] ([Slock.It][19]) 是一家欧洲的区块链初创公司。他们的移动应用程序允许房主和其他个人投入资金建立充电站与其他正在寻找快速充电的人分享他们的资源。这不仅使业主能够收回他们的一些投资,而且还允许 EV 司机在其近地域获得更多的充电点,从而允许供应商以方便的方式满足需求。一旦“客户”完成对其车辆的充电,相关的硬件就会创建一个由数据组成的安全时间戳块,并且在该平台上工作的智能合约会自动将相应的金额记入所有者账户。记录所有此类交易的跟踪并保持适当的安全验证。有兴趣的读者可以看一下[这里][6],了解他们产品背后的技术角度。该公司的平台将逐步使用户能够与有需要的个人分享其他产品和服务,并从中获得被动收入。
+
+我们在这里看到的公司,以及一个很短的正在进行中的项目的清单,这些项目利用智能合约和区块链数据库系统。诸如此类的平台有助于构建一个安全的“盒子”,其中包含仅由用户自己和上面的代码或智能合约访问的信息。基于触发器对信息进行实时审查、检查,并且算法由系统执行。这样的平台具有最小化的人为监督,这是在安全数字自动化方面朝着正确方向迈出的急需的一步,这在以前从未被考虑过如此规模。
+
+下一篇文章将阐述不同类型的区块链。单击以下链接以了解有关此主题的更多信息。
+
+* [区块链 2.0:公有链与私有链的比较][7]
+
+
+[^5]: B. Pani, “Blockchain Powered Financial Inclusion,” 2016.
+[^9]: M. Gates, “Blockchain. Ultimate guide to understanding blockchain bitcoin cryptocurrencies smart-contracts and the future of money.pdf.” 2017.
+
+--------------------------------------------------------------------------------
+
+via: https://www.ostechnix.com/blockchain-2-0-ongoing-projects-the-state-of-smart-contracts-now/
+
+作者:[editor][a]
+选题:[lujun9972][b]
+译者:[wxy](https://github.com/wxy)
+校对:[校对者ID](https://github.com/校对者ID)
+
+本文由 [LCTT](https://github.com/LCTT/TranslateProject) 原创编译,[Linux中国](https://linux.cn/) 荣誉推出
+
+[a]: https://www.ostechnix.com/author/editor/
+[b]: https://github.com/lujun9972
+[1]: https://www.ostechnix.com/wp-content/uploads/2019/04/State-Of-Smart-Contracts-720x340.png
+[2]: https://linux.cn/article-10956-1.html
+[3]: https://banqu.co/case-study/
+[4]: https://github.com/MrChrisJ/World-Citizenship
+[5]: https://github.com/IDCoin/IDCoin
+[6]: https://blog.slock.it/share-charge-smart-contracts-the-technical-angle-58b93ce80f15
+[7]: https://www.ostechnix.com/blockchain-2-0-public-vs-private-blockchain-comparison/
+[8]: https://counterparty.io/platform/
+[9]: https://www.jpmorgan.com/global/Quorum
+[10]: http://escrowmyether.com/
+[11]: https://payfair.io/
+[12]: https://stratumn.com/business-case/insurance-claim-automation-across-europe/
+[13]: https://fizzy.axa/en-gb/
+[14]: https://group.axa.com/en/newsroom/news/axa-goes-blockchain-with-fizzy
+[15]: https://techcrunch.com/2015/05/05/shocard-is-a-digital-identity-card-on-the-blockchain/
+[16]: https://techcrunch.com/2014/10/31/your-next-passport-could-be-on-the-blockchain/
+[17]: https://wiki.namecoin.org/index.php?title=OneName
+[18]: https://blog.slock.it/share-charge-launches-its-app-on-boards-over-1-000-charging-stations-on-the-blockchain-ba8275390309
+[19]: https://slock.it/
diff --git a/sources/tech/20180604 BootISO - A Simple Bash Script To Securely Create A Bootable USB Device From ISO File.md b/translated/tech/20180604 BootISO - A Simple Bash Script To Securely Create A Bootable USB Device From ISO File.md
similarity index 54%
rename from sources/tech/20180604 BootISO - A Simple Bash Script To Securely Create A Bootable USB Device From ISO File.md
rename to translated/tech/20180604 BootISO - A Simple Bash Script To Securely Create A Bootable USB Device From ISO File.md
index f716a164a5..94bc351f7f 100644
--- a/sources/tech/20180604 BootISO - A Simple Bash Script To Securely Create A Bootable USB Device From ISO File.md
+++ b/translated/tech/20180604 BootISO - A Simple Bash Script To Securely Create A Bootable USB Device From ISO File.md
@@ -1,45 +1,46 @@
-BootISO – A Simple Bash Script To Securely Create A Bootable USB Device From ISO File
+BootISO – 一个简单的 Bash 脚本来安全地从 ISO 文件中创建一个可启动的 USB 设备
======
-Most of us (including me) very often create a bootable USB device from ISO file for OS installation.
+为操作系统安装,我们中的大多数人(包括我)非常经常地从 ISO 文件中创建一个可启动的 USB 设备。
-There are many applications freely available in Linux for this purpose. Even we wrote few of the utility in the past.
+为达到这个目的,在 Linux 中有很多自由可用的应用程序。甚至在过去我们写了几个实用程序。
-Every one uses different application and each application has their own features and functionality.
+每个人使用不同的应用程序,每个应用程序有它们自己的特色和功能。
-In that few of applications are belongs to CLI and few of them associated with GUI.
+在这些应用程序中,一些应用程序属于 CLI ,一些应用程序与 GUI 关联。
-Today we are going to discuss about similar kind of utility called BootISO. It’s a simple bash script, which allow users to create a USB device from ISO file.
+今天,我们将讨论相同类型的称为 BootISO 的实用程序。它是一个简单的 bash 脚本,允许用户来从 ISO 文件中创建一个可启动的 USB 设备。
-Many of the Linux admin uses dd command to create bootable ISO, which is one of the native and famous method but the same time, it’s one of the very dangerous command. So, be careful, when you performing any action with dd command.
+很多 Linux 管理员使用 dd 命令开创建可启动的 ISO ,它是一个本地的且著名的方法,但是与此同时,它也是一个非常危险的命令。因此,小心,当你执行一些带有 dd 命令的动作。
-**Suggested Read :**
-**(#)** [Etcher – Easy way to Create a bootable USB drive & SD card from an ISO image][1]
-**(#)** [Create a bootable USB drive from an ISO image using dd command on Linux][2]
+**建议阅读:**
+**(#)** [Etcher – 简单的方法来从一个 ISO 镜像中创建一个可启动的 USB 驱动器 & SD 卡][1]
-### What IS BootISO
+**(#)** [在 Linux 上使用 dd 命令来从一个 ISO 镜像中创建一个可启动的 USB 驱动器][2]
-[BootIOS][3] is a simple bash script, which allow users to securely create a bootable USB device from one ISO file. It’s written in bash.
+### BootISO 是什么
-It doesn’t offer any GUI but in the same time it has vast of options, which allow newbies to create a bootable USB device in Linux without any issues. Since it’s a intelligent tool that automatically choose if any USB device is connected on the system.
+[BootIOS][3] 是一个简单的 bash 脚本,允许用户来安全的从一个 ISO 文件中创建一个可启动的 USB 设备,它是用 bash 编写的。
-It will print the list when the system has more than one USB device connected. When you choose manually another hard disk manually instead of USB, this will safely exit without writing anything on it.
+它不提供任何图形用户界面,但是与此同时,它有大量的选项,允许初学者在 Linux 上来创建一个可启动的 USB 设备,而没有任何问题。因为它是一个智能工具,自动地选择是否一些 USB 设备被连接到系统上。
-This script will also check for dependencies and prompt user for installation, it works with all package managers such as apt-get, yum, dnf, pacman and zypper.
+当系统有多个 USB 设备连接,它将打印列表。当你手动选择另一个硬盘而不是 USB ,在这种情况下,它将安全地退出,而不在硬盘上写任何东西。
-### BootISO Features
+这个脚本也将检查依赖关系,并提示用户安装,它与所有的软件包管理器一起工作,例如 apt-get,yum,dnf,pacman 和 zypper。
- * It checks whether the selected ISO has the correct mime-type or not. If no then it exit.
- * BootISO will exit automatically, if you selected any other disks (local hard drive) except USB drives.
- * BootISO allow users to select the desired USB drives when you have more than one.
- * BootISO prompts the user for confirmation before erasing and paritioning USB device.
- * BootISO will handle any failure from a command properly and exit.
- * BootISO will call a cleanup routine on exit with trap.
+### BootISO 特色
+
+ * 它检查选择的 ISO 是否是正确的 mime 类型。如果不是,那么退出。.
+ * 如果你选择除 USB 设备以外的任何其它的磁盘(本地硬盘),BootISO 将自动地退出。
+ * 当你有多个驱动器时,BootISO 允许用户选择想要的 USB 驱动器。
+ * 在擦除和分区 USB 设备前,BootISO 提示用户确认。
+ * BootISO 将正确地处理来自一个命令的任何失灵,并退出。
+ * BootISO 在退出陷阱时将调用一个清理例行程序。
-### How To Install BootISO In Linux
+### 如果在 Linux 中安装 BootISO
-There are few ways are available to install BootISO in Linux but i would advise users to install using the following method.
+在 Linux 中安装 BootISO 有几个可用的方法,但是,我建议用户使用下面的方法安装。
```
$ curl -L https://git.io/bootiso -O
$ chmod +x bootiso
@@ -47,7 +48,7 @@ $ sudo mv bootiso /usr/local/bin/
```
-Once BootISO installed, run the following command to list the available USB devices.
+一旦 BootISO 已经安装,运行下面的命令来列出可用的 USB 设备。
```
$ bootiso -l
@@ -57,7 +58,7 @@ sdd 1 32G running disk
```
-If you have only one USB device, then simple run the following command to create a bootable USB device from ISO file.
+如果你仅有一个 USB 设备,那么简单地运行下面的命令来从一个 ISO 文件中创建一个可启动的 USB 设备。
```
$ bootiso /path/to/iso file
@@ -84,37 +85,37 @@ You can safely remove it !
```
-Mention your device name, when you have more than one USB device using `--device` option.
+提到你的设备名称,当你有多个 USB 设备时,使用 `--device` 选项。
```
$ bootiso -d /dev/sde /opt/iso_images/archlinux-2018.05.01-x86_64.iso
```
-By default bootios uses `rsync` command to perform all the action and if you want to use `dd` command instead of, use the following format.
+默认情况下,BootISO 使用 `rsync` 命令来执行所有的动作,如果你想使用 `dd` 命令代替它,使用下面的格式。
```
$ bootiso --dd -d /dev/sde /opt/iso_images/archlinux-2018.05.01-x86_64.iso
```
-If you want to skip `mime-type` check, include the following option with bootios utility.
+如果你想跳过 `mime-type` 检查,BootISO 实用程序带有下面的选项。
```
$ bootiso --no-mime-check -d /dev/sde /opt/iso_images/archlinux-2018.05.01-x86_64.iso
```
-Add the below option with bootios to skip user for confirmation before erasing and partitioning USB device.
+为 BootISO 添加下面的选项来跳过在擦除和分区 USB 设备前的用户确认。
```
$ bootiso -y -d /dev/sde /opt/iso_images/archlinux-2018.05.01-x86_64.iso
```
-Enable autoselecting USB devices in conjunction with -y option.
+连同 -y 选项一起,启用自动选择 USB 设备。
```
$ bootiso -y -a /opt/iso_images/archlinux-2018.05.01-x86_64.iso
```
-To know more all the available option for bootiso, run the following command.
+为知道更多全部可用的 BootISO 选项,运行下面的命令。
```
$ bootiso -h
Create a bootable USB from any ISO securely.
@@ -161,7 +162,7 @@ via: https://www.2daygeek.com/bootiso-a-simple-bash-script-to-securely-create-a-
作者:[Prakash Subramanian][a]
选题:[lujun9972](https://github.com/lujun9972)
-译者:[译者ID](https://github.com/译者ID)
+译者:[robsean](https://github.com/robsean)
校对:[校对者ID](https://github.com/校对者ID)
本文由 [LCTT](https://github.com/LCTT/TranslateProject) 原创编译,[Linux中国](https://linux.cn/) 荣誉推出
diff --git a/translated/tech/20180629 100 Best Ubuntu Apps.md b/translated/tech/20180629 100 Best Ubuntu Apps.md
new file mode 100644
index 0000000000..c82f5cc099
--- /dev/null
+++ b/translated/tech/20180629 100 Best Ubuntu Apps.md
@@ -0,0 +1,1195 @@
+warmfrog translating
+
+100 Best Ubuntu Apps
+======
+
+今年早些时候我们发布了一个 [2018 年最好的 20 个 Ubuntu 应用][1]列表,可能对很多用户来说都很有用。现在我们几乎到 2018 年下半年了,所以今天我们打算看一下 Ubuntu 上最好的 100 个应用,你可能会觉得有帮助。
+
+![100 Best Ubuntu Apps][2]
+
+很多用户最近从 Microsoft Windows 转换到了 Ubuntu,可能面临着这样一个困境:寻找它们之前使用了数年的操作系统上的应用软件的最好替代应用。Ubuntu 拥有上千个免费使用和开源应用软件比 Windows 和其它 OS 上的付费软件运行的更好。
+
+下列列表归纳了各种分类下很多应用软件的功能特点,因此,你可以找到匹配你的需求的最好的应用。
+
+### **1\. Google Chrome 浏览器**
+
+几乎所有 Linux 发行版默认安装了 Mozilla Firefox 网络浏览器,并且它是 Google Chrome 的强力竞争对手。但是 Chrome 相对 Firefox 有它自己的优点,给了你 Google 账户的入口,你可以通过它来同步你的书签,浏览历史,扩展。例如从其它操作系统和手机的 Chrome 浏览器同步。
+
+![Chrome][3]
+
+Google Chrome 为 Linux 集成了最新的 Flash 播放器,其它 Linux 上的浏览器像 Mozilla Firefox 和 Opera 网络浏览器则不是这样。如果你在 Windows 上经常使用 Chrome,那么在 Linux 上也用它是最好的选择。
+
+### 2\. **Steam**
+
+现在在 Linux 上玩游戏已经不是问题了,这在很多年前还是一个遥不可及的梦。在 2013 年,Valve 发布了 Linux 上的 Steam 游戏客户端,此后一切都变了。早期用户犹豫着从 Windows 转到 Linux,只是因为它们不能在 Ubuntu 上玩它们最喜欢的游戏,但是现在已经不是这样了。
+
+![Steam][4]
+
+一些用户可能发现在 Linux 上安装 Steam 有点棘手,但如果能在 Linux 上玩上千的 Steam 游戏时这么做就是值得的。一些流行的像 Counter Strike 这样的高端游戏:Global Offensive, Hitman, Dota 2 在 Linux 上都能获取,你只需要确保你满足玩这些游戏的最小硬件需求。
+
+```
+$ sudo add-apt-repository multiverse
+
+$ sudo apt-get update
+
+$ sudo apt-get install steam
+```
+
+### **3\. WordPress 桌面客户端**
+
+是的,没错,WordPress 有它专有的 Ubuntu 平台的客户端,你可以用来管理你的 WordPress 站点。你同样可以在桌面客户端上单独写和设计桌面客户端而不用转到浏览器。
+
+![][5]
+
+如果你有 WordPress 支持的站点,那么这个桌面客户端能够让你在单个窗口内追踪所有的 WordPress 通知。你同样可以检查站点的博客性能状态。桌面客户端可以在 Ubuntu 软件中心中获取,你可以在那里下载和安装。
+
+### **4\. VLC 媒体播放器**
+
+VLC 是一个非常流行的跨平台的开源媒体播放器,同样在 Ubuntu 中可以获取。使得 VLC 成为一个最好的媒体播放器的原因是它能够播放地球上能够获得的任何音频视频格式,而且不会出现任何问题。
+
+![][6]
+
+VLC 有一个平滑的用户界面,易于使用,除此之外,它提供了很多特点包括在线视频流,音频和视频自定义,等。
+
+```
+$ sudo add-apt-repository ppa:videolan/master-daily
+$ sudo apt update
+$ sudo apt-get install vlc qtwayland5
+```
+
+### **5\. Atom 文本编辑器**
+
+由 Github 开发,Atom 是一个免费和开源的文本编辑器,它同样能够被用做集成开发环境(IDE)来进行主流编程语言的编码和编辑。Atom 开发者声称它是 21 世纪的完全可控制的文本编辑器。
+
+![][7]
+
+Atom 文本编辑器属于最好的用户界面之一,它是一个富文本编辑器提供了自动补全,语法高亮、扩展与插件支持。
+
+```
+$ sudo add-apt-repository ppa:webupd8team/atom
+$ sudo apt-get update
+$ sudo apt-get install atom
+```
+
+### **6\. GIMP 图像编辑器**
+
+GIMP (GNU 图形操作程序)是 Ubuntu 上免费和开源的图像编辑器。有争议说它是 Windows 上 Adobe Photoshop 的最好替代品。如果你过去经常用 Adobe Photoshop,会觉得很难习惯 GIMP,但是你可以自定义 GIMP 使它看起来与 Photoshop 非常相似。
+
+![][8]
+
+GIMP 是一个功能丰富的图片编辑器,你可以随时通过安装扩展和插件来使用附加的功能。
+
+```
+$ sudo apt-get install gimp
+```
+
+### **7\. Google Play 音乐桌面播放器**
+
+Google Play 音乐桌面播放器是一个开源的音乐播放器,它是 Google Play Music 的一个替代品,或者说更好。Google 总是缺少桌面的音乐客户端,但第三方的应用完美的填充了空白。
+
+![][9]
+
+就像你在截屏里看到的,它的界面在外观和感觉上都是首屈一指的。你仅仅需要登录 Google 账户,之后会导入所有你的音乐和你的最爱到桌面客户端里。你可以从它的官方 [站点][10]下载安装文件并使用软件中心安装它。
+
+### **8\. Franz**
+
+Franz 是一个即时消息客户端,结合了聊天和信息服务到一个应用中。它是现代化的即时消息平台之一,在单个应用中支持 Facebook Messenger, WhatsApp, Telegram, 微信,Google Hangouts, Skype。
+
+![][11]
+
+Franz 是一个完整的消息平台,你同样可以在商业中用它来管理大量的客户服务。为了安装 Franz,你需要从它的[网站][12]下载安装包,在软件中心中打开。
+
+### **9\. Synaptic 包管理器**
+
+ Synaptic 包管理器是 Ubuntu 上必有工具之一,因为它为我们通常在命令行界面安装软件的 ‘apt-get’ 命令提供了用户图形界面。它是各种 Linux 发行版中默认的应用的强力对手。
+
+![][13]
+
+Synaptic 拥有非常简单的用户图形界面,相比其它的应用商店非常快并易于使用。左手边你可以浏览不同分类的各种应用,也可以轻松安装和卸载。
+
+```
+$ sudo apt-get install synaptic
+```
+
+### **10\. Skype**
+
+Skype 是一个非常流行的跨平台视频电话应用,如今在 Linux 系统的 Snap 应用中可以获取了。Skype 是一个即时通信应用,它提供了视频和音频通话,桌面共享等特点。
+
+![][14]
+
+Skype 有一个优秀的用户图形界面,与 Windows 上的桌面客户端非常相似,易于使用。它对于从 Windows 上转换来的用户来说非常有用。
+
+```
+$ sudo snap install skype
+```
+
+### **13\. VirtualBox**
+
+VirtualBox 是由 Oracle 公司开发的跨平台的虚拟化软件应用。如果你喜欢尝试新的操作系统,那么 VirtualBox 是为你准备的必备的 Ubuntu 应用。你可以尝试 Windows 内的 Linux,Mac 或者 Linux 系统中的 Windows 和 Mac。
+
+![][15]
+
+VB 实际做的是让你在宿机操作系统里可视化的运行顾客操作系统。它创建虚拟硬盘并在上面安装顾客操作系统。你可以在 Ubuntu 软件中心直接下载和安装。
+
+### **12\. Unity Tweak 工具**
+
+Unity Tweak 工具(Gnome Tweak 工具)对于每个 Linux 用户都是必须有的,因为它给了用户根据需要自定义桌面的能力。你可以尝试新的 GTK 主题,设置桌面角落,自定义图标集,改变 unity 启动器,等。
+
+![][16]
+
+Unity Tweak 工具对于用户来说可能非常有用,因为它包含了从基础到高级配置的所有内容。
+
+```
+$ sudo apt-get install unity-tweak-tool
+```
+
+### **13\. Ubuntu Cleaner**
+
+Ubuntu Cleaner是一个系统管理工具,尤其被设计为移除不再使用的包,移除不必要的应用和清理浏览器缓存的。Ubuntu Cleaner 有易于使用的简易用户界面。
+
+![][17]
+
+Ubuntu Cleaner是 BleachBit 最好的替代品之一,BleachBit 是 Linux 发行版上的相当好的清理工具。
+
+```
+$ sudo add-apt-repository ppa:gerardpuig/ppa
+$ sudo apt-get update
+$ sudo apt-get install ubuntu-cleaner
+```
+
+### 14\. Visual Studio Code
+
+Visual Studio Code 是一个代码编辑器,你会发现它与 Atom 文本编辑器和 Sublime Text 非常相似,如果你曾用过的话。Visual Studio Code 证明是非常好的教育工具,因为它解释了所有东西,从 HTML 标签到编程中的语法。
+
+![][18]
+
+Visual Studio 自身集成了 Git,它有优秀的用户界面,你会发现它与 Atom Text Editor 和 Sublime Text 非常相似。你可以从 Ubuntu 软件中心下载和安装它。
+
+### **15\. Corebird**
+
+如果你在找你可以用 Twitter 的桌面客户端,那 Corebird Twitter 客户端就是你在找的。它被争议是 Linux 发行版下可获得的最好的 Twitter 客户端,它提供了与你手机上的 Twitter 应用非常相似的功能。
+
+![][19]
+
+ 当有人喜欢或者转发你的 tweet 或者给你发消息时,Corebird Twitter 客户端同样会给你通知。你同样可以在这个客户端上添加多个 Twitter 账户。
+
+```
+$ sudo snap install corebird
+```
+
+### **16\. Pixbuf**
+
+Pixbuf 是来自 Pixbuf 图片社区中心的一个桌面客户端,让你上传,分享和出售你的相片。它支持图片共享到社交媒体像 Facebook,Pinterest,Instagram,Twitter,等等,也包括照相服务像 Flickr,500px and Youpic。
+
+![][20]
+
+Pixbuf提供了分析等功能,可以让你统计点击量、转发量、照片的回复、预定的帖子、专用的iOS 扩展。它同样有移动应用,因此你可以在任何地方连接到你的 Pixbuf 账户。 Pixbuf 在 Ubuntu 软件中心以 Snap 包的形式获得。
+
+### **17\. Clementine 音乐播放器**
+
+Clementine 是一个跨平台的音乐播放器,并且是 Ubuntu 上默认音乐播放器 Rhythmbox 的良好竞争者。多亏它的友好的界面,它很快速并易于使用。它支持所有音频文件格式的声音回放。
+
+![][21]
+
+除了播放本地库中的音乐,你也可以在线听 Spotify, SKY.fm, Soundcloud 等的广播。它也支持其它的功能像智能动态播放列表,从像 Dropbox,Google Drive 这样的云存储中同步音乐。
+
+```
+$ sudo add-apt-repository ppa:me-davidsansome/clementine
+$ sudo apt-get update
+$ sudo apt-get install clementine
+```
+
+### **18\. Blender**
+
+Blender 是一个免费和开源的 3D 创建应用软件,你可以用来创建 3D 打印模型,动画电影,视频游戏,等。它自身集成了游戏引擎,你可以用来开发和测试视频游戏。
+
+![blender][22]
+
+Blender 拥有赏心悦目的用户界面,易于使用,它包括了内置的渲染引擎,数字雕刻,仿真工具,动画工具,还有很多。考虑到它免费和它的特点,你甚至会认为它可能是 Ubuntu 上最好的应用之一。
+
+### **19\. Audacity**
+
+Audacity 是一个开源的音频编辑应用,你可以用来记录、编辑音频文件。你可以从各种输入中录入音频,包括麦克风,电子吉它,等等。根据你的需要,它提供了编辑和裁剪音频的能力。
+
+![][23]
+
+最近 Audacity 发布了 Ubuntu 上的新版本,新特点包括主题提升、放缩命令等。除了这些,它还提供了降噪等更多特点。
+
+```
+$ sudo add-apt-repository ppa:ubuntuhandbook1/audacity
+$ sudo apt-get update
+$ sudo apt-get install audacity
+```
+
+### **20\. Vim**
+
+Vim 是一个集成开发环境,你可以用作一个独立的应用或各种像 Python 等主流编程语言的命令行接口。
+
+![][24]
+
+大多数程序员喜欢在 Vim 中编代码,因为它快速并且是一个可高度定制的集成开发环境。最初你可能觉得有点难用,但你会很快习惯它。
+
+```
+$ sudo apt-get install vim
+```
+
+### **21\. Inkscape**
+
+Inkscape 是一个开源和跨平台的矢量图形编辑器,你会觉得它和 Corel Draw 和 Adobe Illustrator 很相似。用它可以创建和编辑矢量图形例如柱形图、logo、图表、插图等。
+
+![][25]
+
+Inkscape 使用规模矢量图形(SVG),一个基于 XML 的 W3C 标准格式。它只是各种格式包括 JPEG、PNG、GIF、PDF、AI(Adobe Illustrator 格式)、VSD 等等。
+
+```
+$ sudo add-apt-repository ppa:inkscape.dev/stable
+$ sudo apt-get update
+$ sudo apt-get install inkscape
+```
+
+### **22\. Shotcut**
+
+Shotcut 是一个免费、开源的跨平台的 Meltytech,LLC 在 MLT 多媒体框架下开发的视频编辑应用。你会发现它是 Linux 发行版上最强大的视频编辑器之一,因为它支持所有主要的音频,视频,图片格式。
+
+![][26]
+
+它给了非线性编辑的各种文件格式多轨道视频的能力。它支持 4K 视频分辨率和各种音频,视频过滤,语气生成、音频混合和很多其它的。
+
+```
+snap install shotcut -- classic
+```
+
+### **23\. SimpleScreenRecorder**
+
+SimpleScreenRecorder 是 Ubuntu 上的一个免费和轻量级的屏幕录制工具。屏幕录制非常有用,如果你是 YouTube 创作者或应用开发者。
+
+![][27]
+
+它可以捕获桌面屏幕的视频/音频记录或直接录制视频游戏。在屏幕录制前你可以设置视频分辨率、帧率等。它有简单的用户界面,你会发现非常易用。
+
+```
+$ sudo add-apt-repository ppa:marten-baert/simplescreenrecorder
+$ sudo apt-get update
+$ sudo apt-get install simplescreenrecorder
+```
+
+### **24\. Telegram**
+
+Telegram 是一个基于云的即时通信和网络电话平台,近年来非常流行。它是开源和跨平台的,用户可以用来发送消息,共享视频,图片,音频和其它文件。
+
+![][28]
+
+Telegram 中容易发现的特点是加密聊天,语音信息,远程视频通话,在线位置和社交登录。在 Telegram 中隐私和安全拥有最高优先级,因此,所有你发送和接收的是端对端加密的。
+
+```
+$ sudo snap install telegram-desktop
+```
+
+我们所知道的危害 Windows PC 的病毒不能危害 Ubuntu,因为在 Windows PC 中接收到的邮件的破坏性文件会破坏 Windows PC。因此,在 Linux 上有一些抗病毒应用是安全的。
+
+![][29]
+
+ClamTk 是一个轻量级的病毒扫描器,可以扫描系统中的文件和文件夹并清理发现的有害文件。ClamTk 可以 Snap 包的形式获得,可以从 Ubuntu 软件中心下载。
+
+### **26\. MailSpring**
+
+早期的 MailSpring 以 Nylas Mail 或 Nylas N1 而著名,是开源的邮件客户端。它保存所有的邮件在电脑本地,因此你可以在任何需要的时候访问它。它提供了高级搜索的功能,使用与或操作,因此你可以基于不同的参数搜索邮件。
+
+![][30]
+
+MailSpring 有着和其它易于上手的邮件客户端同样优秀的用户界面。MailSpring 同样提供了私密性、安全性、规划期、通讯录管理、日历等功能特点。
+
+### **27\. PyCharm**
+
+PyCharm 是我最喜欢的继 Vim 之后的 Python IDE 之一,因为它有优雅的用户界面,有很多扩展和插件支持。基本上,它有两个版本,一个是免费和开源的社区版,另一个是付费的专业版。
+
+![][31]
+
+PyCharm 是高度自定义的 IDE 并且有很多功能像错误高亮、代码分析、集成单元测试和 Python 调试器等。PyCharm 对于大多数 Python 程序员和开发者来说是首选的。
+
+### **28\. Caffeine**
+
+想象一下你在 Youtube 上看视频或阅读一篇新文章,突然你的 Ubuntu 锁屏了,我知道它很烦人。我们很多人都会遇到这种情况,所以 Caffeine 是一个阻止 Ubuntu 锁屏或屏幕保护程序的工具。
+
+![][32]
+
+Caffeine Inhibitor 是一个轻量级的工具,它在通知栏添加图标,你可以在那里轻松的激活或禁止它。不需要额外的设置。
+
+```
+$ sudo add-apt-repository ppa:eugenesan/ppa
+$ sudo apt-get update
+$ sudo apt-get install caffeine -y
+```
+
+### **29\. Etcher USB 镜像写入器**
+
+Etcher 是一个有 resin.io 开发的 USB 镜像写入器。它是一个跨平台的应用,帮助你将 ZIP、ISO、IMG 格式的镜像文件写入到 USB 存储中。如果你总是尝试新的操作系统,那么 Ethcher 是你必有的简单可靠的系统。
+
+![][33]
+
+Etcher 有干净的用户界面指导你在三步内烧录镜像到 USB 驱动或 SD 卡的过程。步骤包括选择镜像文件,选择 USB 驱动 和最终的 flash(写文件到 USB 驱动)。你可以从它的[官网][34]下载和安装 Etcher。
+
+### **30\. Neofetch**
+
+Neofetch 是一个酷炫的系统信息工具,通过在终端中运行 “neofetch” 命令,它会给你关于你的系统的所有信息。它酷是因为它给你关于桌面环境,内核版本,bash 版本和你正在运行的 GTK 主题信息。
+
+![][35]
+
+与其它系统信息工具比较,Nefetch 是高度自定义的工具。你可以使用命令行进行各种自定义。
+
+```
+$ sudo add-apt-repository ppa:dawidd0811/neofetch
+$ sudo apt-get update
+$ sudo apt-get update install neofetch
+```
+
+### 31\. Liferea
+
+Liferea(Linux 热点阅读器)是一个免费和开源的新闻聚集工具,用于在线新闻订阅。使用新的聚集工具非常快捷和简单,支持各种格式例如 RSS/RDF,Atom 等。
+
+![][36]
+Liferea 自带与 TinyTinyRSS 的同步支持,它给了你离线阅读的能力。你会发现,就可靠性和灵活性而言,它是 Linux 上最好的订阅工具之一。
+
+
+```
+$ sudo add-apt-repository ppa:ubuntuhandbook1/apps
+$ sudo apt-get update
+$ sudo apt-get install liferea
+```
+
+### 32\. Shutter
+
+在 Ubuntu 中很容易截屏,但当编辑截屏时 Shutter 是你必不可少的应用。它帮助你捕获,编辑和轻松的共享截屏。使用 Shutter 的选择工具,你可以选择屏幕的特定区域来截屏。
+
+![][37]
+
+Shutter 是一个功能强大的截图工具,提供了添加截图效果,画线等功能。它同样给你上传截屏到各种图像保存站点的选项。你可以直接在 Ubuntu 软件中心中下载和安装。
+
+### 33\. Weather
+
+Weather 是一个小的应用,给你关于你的城市或世界上其它位置的实时天气信息。它简单而且轻量级,给你超过 7 天的详细天气预报和今明两天的每个小时的细节信息。
+
+![][38]
+
+它集成在 GNOME shell 中,给你关于最近搜索位置的当前天气状态。它有最小的用户界面,在最小硬件需求下运行很顺畅。
+
+### 34\. Ramme
+
+Ramme 是一个很酷的非官方的 Instagram 桌面客户端,给你带来 Instagram 移动端的感觉。它是基于 Electron 的客户端,所以它替代了 Instagram 应用提供了主题自定义的功能。
+
+![][39]
+
+但是由于 Instagram 的 API 限制,你不能使用 Ramme 客户端上传图像,但你总是可以通过订阅 Instagram,喜欢和评论,给好友发消息。你可以从 [Github]][40] 下载 Ramme 安装文件。
+
+### **35\. Thunderbird**
+
+Thunderbird 是一个开源的邮件客户端,是很多 Linux 发行版的默认邮件客户端。尽管在 2017 年与 Mozilla 分离,Thunderbird 仍然是 Linux 平台非常流行的最好的邮件客户端。它自带特点像垃圾短信过滤,IMAP 和 POP 邮件同步,日历支持,通讯录集成和很多其它特定。
+
+![][41]
+
+它是一个跨平台的邮件客户端,在所有支持的平台上完全由社区提供支持。多亏它的高度自定义特点,你总是可以改变它的外观和观感。
+
+### **36\. Pidgin**
+
+Pidgin 是一个即时信息客户端,你能够在单个窗口下登录不同的即时网络。你可以登录到像 Google Talk,XMPP,AIM,Bonjour 等。
+
+![][42]
+
+Pidgin 拥有所有你期待的即时通信的特点,你总是可以通过安装额外的插件来提升它的性能。
+
+```
+$ sudo apt-get install pidgin
+```
+
+### **37\. Krita**
+
+Krita 是由 KDE 开发的免费和开源的数字打印,编辑和动画应用。它有优秀的用户界面,每个组件都放的很完美,因此你可以找到你需要的。
+
+![][43]
+
+它使用 OpenGL 画布,这提升了 Krita 的性能,并且提供了很多特点相不同的绘画工具、动画工具、矢量工具、层、罩等很多。可在 Ubuntu 软件中心获取 Krita 并下载。
+
+### **38\. Dropbox**
+
+Dropbox 是一个出色的云存储播放器,一旦安装,它在 Ubuntu 中运行得非常好。即使 Google Drive 在 Ubuntu 16.04 LTS 和以后的版本中运行得不错,就 Dropbox 提供的特点而言,Dropbox 仍然是 Linux 上的首选云存储工具。
+
+![][44]
+它总是在后台运行,备份你系统上的新文件到云存储,持续在你的电脑和云存储间同步。
+
+```
+$ sudo apt-get install nautilus-dropbox
+```
+
+### 39\. Kodi
+
+Kodi 的前身是人们熟知的 Xbox 媒体中心(XBMC),是一个开源的媒体播放器。你可以在线或离线播放音乐、视频、播客、视频游戏等。这个软件最初是为第一代的 Xbox 游戏控制台开发的,之后慢慢地面向了个人电脑。
+
+![][45]
+
+Kodi 有令人印象深刻的视频接口,快速而强大。它是可高度定制的媒体播放器,你可以通过安装插件,来获取在线流服务像 Pandora、 Spotify、Amazon Prime Video、Netflix and YouTube。
+
+### **40\. Spotify**
+
+Spotify 是最好的在线媒体流站点之一。它提供免费和付费音乐、播客、视频流服务。早期的 Spotify 不支持 Linux,但现在它有全功能的 Ubuntu 客户端。
+
+![][46]
+
+ 与 Google Play 音乐播放器一样,Spotify 是必不可少的媒体播放器。你只需要登录你的 Spotify 账户,就能在任何地方获取你最爱的在线内容。
+
+### 41\. Brackets
+
+Brackets 是一个有 Adobe 开发的开源的文本编辑器。它可被用来进行 web 开发和设计,例如 HTML,CSS 和 JavaScript。它随改变实时预览是一个很棒的特点,当你在脚本中修改时,你可以获得实时预览效果。
+
+![][47]
+
+它是 Ubuntu 上的现代文本编辑器之一,拥有平滑的用户界面,这将 web 开发任务带到新的水平。它同样提供行内编辑器的特点,支持流行的扩展像 Emmet、Beautify、Git、File Icons 等等。
+
+### 42\. Bitwarden
+
+现今,安全问题事件增加,用户密码被盗后,重要的数据受到连累,因此,账户安全性必须严肃对待。推荐你使用 Bitwarden,将你的所有账户和登录密码安全的存在一个地方。
+
+![][48]
+
+Bitwarden 使用 AES-256 加密技术来存储所有的登录细节,只有用户可以访问这些数据。它同样帮你创建健壮的密码,因为弱密码容易被黑。
+
+### 43\. Terminator
+
+Terminator 是一个开源终端模拟器,用 Java 语言开发的。它是一个跨平台的模拟器,允许你在单个窗口有多个终端,在 Linux 默认的终端模拟器中不是这样。
+
+![][49]
+
+Terminator 其它杰出的特点包括自动日志、拖、丢、智能垂直和水平滚动等。
+
+```
+$ sudo apt-get install terminator
+```
+
+### 44\. Yak Yak
+
+Yak Yak 是一个开源的非官方的 Google Hangouts 消息的桌面客户端。它可能是一个不错的 Microsort 的 Skype 的替代品,自身拥有很多让人吃惊的特点。你可以允许桌面通知,语言偏好,工作在最小内存或电源需求等。
+
+![][50]
+
+Yak Yak 拥有你期待的所有任何即时消息应用的所有特点,例如类型指示、拖、拽媒体文件,音/视频电话。
+
+### 45\. **Thonny**
+
+Thonny 是一个简单和轻量级的 IDE,尤其是为编程的初学者设计的。如果你是编程初学者,这是你必备的 IDE,因为当用 Python 编程的时候它会帮你学习。
+
+![][51]
+
+Thonny 同样是一个很棒的调试工具,它支持调试过程中的活变量,除此之外,它还提供了执行函数调用是分离窗口、简易用户界面的特点。
+
+```
+$ sudo apt-get install thonny
+```
+
+### **46\. Font Manager**
+
+Font Manager 是一个轻量级的工具,用于管理、添加、移除你的 Ubuntu 系统上的字体。尤其是为 Gnome 桌面环境构建的,当用户不知道如何在命令行管理字体的会发现这个工具非常有用。
+
+![][52]
+
+Gtk+ Font Manager 不是为专业用户准备的,它有简单的用户界面,你会发现很容易导航。你只需要从网上下载字体文件,并使用 Font Manager 添加它们。
+
+$ sudo add-apt-repository ppa:font-manager/staging
+$ sudo apt-get update
+$ sudo apt-get install font-manager
+
+### **47\. Atril Document Viewer**
+
+Atril 是一个简单的文件查看器,支持便携文件格式(PDF)、PostScript(PS)、Encapsulated PostScript(EPS)、DJVU 和 DVI。Atril 绑定在 MATE 桌面环境中,它比大多数 Linux 发行版中默认的文件查看器 Evince 更理想。
+
+![][53]
+
+Atril 用简单和轻量级的用户界面,可高度自定义,提供了搜索、书签、UI 左侧的缩略图等特点。
+
+```
+$ sudo apt-get install atril
+```
+
+### **48\. Notepadqq**
+
+如果你曾在 Windows 上用过 Notepad++,并且在 Linux 上寻找相似的程序,别担心,开发者们已经将它移植到 Linux,叫 Notepadqq。它是一个简单且强大的文本编辑器,你可以在日常生活中用它完成各种语言的任务。
+
+![][54]
+
+尽管作为一个简单的文本编辑器,它有一些令人惊奇的特点,例如,你可以设置主题为暗黑或明亮模式、多选、正则搜索和实时高亮。
+
+```
+$ sudo add-apt-repository ppa:notpadqq-team/notepadqq
+$ sudo apt-get update
+$ sudo apt-get install notepadqq
+```
+
+### **49\. Amarok**
+
+Amarok 是在 KDE 项目下开发的一个开源音乐播放器。它有直观的界面,让你感觉在家一样,因此你可以轻易的发现你最喜爱的音乐。除了 Clementine,当你在寻找 Ubuntu 上的完美的音乐播放器时,Amarok 是一个很棒的选择。
+
+![][55]
+
+Amarok 上的一些顶尖的特点包括智能播放列表支持,集成在线服务像 MP3tunes、Last.fm、 Magnatune 等。
+
+### **50\. Cheese**
+
+Cheese 是 Linux 默认的网络摄像头应用,在视频聊天或即时消息应用中非常有用。除了这些,你还可以用这个应用来照相或拍视频,附带一些迷人的特效。
+
+![][56]
+
+它同样提供闪拍模式,让你快速拍摄多张相片,并提供你共享给你的朋友和家人的选项。Cheese 预装在大多数的 Linux 发行版中,但是你同样可以在软件中心下载它。
+
+### **51\. MyPaint**
+
+MyPaint 是一个免费和开源的光栅图形编辑器,关注于数字绘画而不是图像操作和相片处理。它是跨平台的应用,与 Corel Painter 很相似。
+
+![][57]
+
+MyPaint 可能是 Windows 上的 Microsoft Paint 应用的很好的替代。它有简单的用户界面,快速而强大。MyPaint 可以软件中心下载。
+
+### **52\. PlayOnLinux**
+
+PlayOnLinux 是 WINE 模拟器的前端,允许你在 Linux 上运行 Windows 应用。你只需要在 WINE 中安装 Windows 应用,之后你就可以轻松的使用 PlayOnLinux 启动应用和游戏了。
+
+![][58]
+
+### **53\. Akregator**
+
+Akregator 是在 KDE 项目下为 KDE Plasma 环境开发的默认的 RSS 阅读器。它有简单的用户界面,自带了 KDE 的 Konqueror 浏览器,所以你不需要在阅读新闻提要时切换应用。
+
+Akregator 同样提供了桌面通知、自动提要等功能。你会发现在大多数 Linux 发行版中它是最好的提要阅读器。
+
+### **54\. Brave**
+
+Brave 是一个开源的 web 浏览器,阻挡了广告和追踪,所以你可以快速和安全的浏览你的内容。它实际做的是代表你像网站和油管主播支付了费用。如果你喜欢像网站和和油管主播共享而不是看广告,这个浏览器更适合你。
+
+![][60]
+
+对于那些想要安全浏览但有不想错过互联网上重要数据的人来说,这是一个新概念,一个不错的浏览器。
+
+### **55\. Bitcoin Core**
+
+Bitcoin Core 是一个官方的客户端,非常安全和可靠。它持续追踪你的所有交易以保证你的所有交易都是有效的。它限制比特币矿工和银行完全掌控你的比特币钱包。
+
+![][61]
+
+Bitcoin Core 同样提供了其它重要的特点像私钥备份、冷存储、安全通知等。
+
+```
+$ sudo add-apt-repository ppa:bitcoin/bitcoin
+$ sudo apt-get update
+$ sudo apt-get install bitcoin-qt
+```
+
+### **56\. Speedy Duplicate Finder**
+
+Speedy Duplicate Finder 是一个跨平台的文件查找工具,用来帮助你查找你的系统上的重复文件,清理磁盘空间。它是一个智能工具,在整个硬盘上搜索重复文件,同样提供智能过滤功能,根据文件类型、扩展或大小帮你找到文件。
+
+![][62]
+
+它有一个简单和整洁的用户界面,易于上手。从软件中心下载完后你就可以开始磁盘空间清理了。
+
+### **57\. Zulip**
+
+Zulip 是一个免费和开源的群聊应用,被 Dropbox 获得了。它是用 Python 写的,用 PostgreSQL 数据库。它被设计和开发为其它聊天应用像 Slack 和 HipChat 的好的替代品。
+
+![][63]
+
+Zulip 功能丰富,例如拖拽文件、群聊、私密聊天、图像预览等。它供养集成了 Github、JIRA、Sentry 和上百种其它服务。
+
+### **58\. Okular**
+
+Okular 是 KDE 为 KDE 桌面环境开发的跨平台的文件查看器。它是一个简单的文件查看器,支持 Portable Document Format (PDF), PostScript, DjVu, Microsoft Compiled HTML help 和很多其它文件格式。
+
+![][64]
+
+Okular 是在 Ubuntu 上你应该尝试的最好的文件查看器之一,它提供了 PDF 文件评论、画线、高亮等很多功能。你同样可以从 PDF 文件中提取文本文件。
+
+### **59\. FocusWriter**
+
+FocusWriter 是一个集中注意力的字处理工具,隐藏了你的桌面屏幕,因此你能够专注写作。正如你看到的屏幕截图,整个 Ubuntu 屏被隐藏了,只有你和你的字处理工具。但你总是可以进入 Ubuntu 屏幕,当你需要的时候,只需要将光标移动到屏幕的边缘。
+
+![][65]
+
+它是一个轻量级的字处理其,支持 TXT、RTF、ODT 文件格式。它同样提供可完全定制的用户界面,还有定时器、警报、每日目标、声音效果等特点,支持翻译为 20 种语言。
+
+### **60\. Guake**
+
+Guake 是为 GNOME 桌面环境准备的酷炫的下拉式终端。当你任务完成后,你需要它消失时, Guake 会闪一下。你只需要按 F12 按钮来启动或退出,这样启动 Guake 币启动一个新的终端窗口更快。
+
+![][66]
+
+Guake 是一个特点丰富的终端,支持多栏,只需要点击几下就能将你的终端内容保存到文件,并且有完全可定制的用户界面。
+
+```
+$ sudo apt-get install guake
+```
+### **61\. KDE Connect**
+
+KDE Connect 在 Ubuntu 上是一个很棒的应用,我很想在这篇马拉松文章中将它提早列出来,但是竞争激烈。总之 KDE Connect 可以将你的 Android 智能手机的通知直接转到 Ubuntu 桌面来。
+
+![][67]
+
+有了 KDE Connect,你可以做很多事,例如检查手机电池水平,在电脑和 Android 手机间交换文件,剪贴板同步,发送短信,你还可以将你的手机当作无线鼠标或键盘。
+
+```
+$ sudo add-apt-repository ppa:webupd8team/indicator-kedeconnect
+$ sudo apt-get update
+$ sudo apt-get install kdeconnect indicator-kdeconnect
+```
+
+### **62\. CopyQ**
+
+CopyQ 是一个简单但是非常有用的剪切板管理器,它保存你的系统剪切板内容,无论你做了什么改变,你都可以在你需要的时候恢复它。它是一个很棒的工具,支持文本、图像、HTML、和其它格式。
+
+![][68]
+
+CopyQ 自身有很多功能像拖拽、复制/拷贝、编辑、移除、排序、创建等。它同样支持集成文本编辑器,像 Vim,所以如果你是程序员,这非常有用。
+
+```
+$ sudo add-apt-repository ppa:hluk/copyq
+$ sudo apt-get update
+$ sudo apt-get install copyq
+```
+
+### **63\. Tilix**
+
+Tilix 是一个功能丰富的高级 GTX3 瓷砖终端模拟器。如果你使用 GNOME 桌面环境,那你会爱上 Tilix,因为它遵循了 GNOME 人类界面指导。Tilix 模拟器与大多数 Linux 发行版上默认终端模拟器相比,它给了你分离终端窗口为多个终端面板。
+
+![][69]
+
+Tilix 提供了自定义链接、图片支持、多面板、拖拽、持续布局等功能。它同样支持键盘快捷方式,你可以根据你的需要在偏好设置中自定义快捷方式。
+
+```
+$ sudo add-apt-repository ppa:webupd8team/terminix
+$ sudo apt-get update
+$ sudo apt-get install tilix
+```
+
+### **64\. Anbox**
+
+Anbox 是一个 Android 模拟器,让你在 Linux 系统中安装和运行 Android 应用。它是免费和开源的 Android 模拟器,通过使用 Linux 容器来执行 Android 运行时环境。它使用最新的 Linux 技术 和 Android 发布版,所以你可以运行任何原生的 Android 应用。
+
+![][70]
+
+Anbox 是现代和功能丰富的模拟器之一,提供的功能包括无限制的应用使用,强大的用户界面,与宿主系统无缝集成。
+
+首先你需要安装内核模块。
+
+```
+$ sudo add-apt-repository ppa:morphis/anbox-support
+$ sudo apt-get update
+$ sudo apt install anbox-modules-dkms Now install Anbox using snap
+$ snap install --devmode -- beta anbox
+```
+
+### **65\. OpenShot**
+
+你会发现 OpenShot 是 Linux 发行版中最好的开源视频编辑器。它是跨平台的视频编辑器,易于使用,不在性能方面妥协。它支持所有主流的音频、视频、图像格式。
+
+![][71]
+
+OpenShot 有干净的用户界面,功能有拖拽、裁剪大小调整、大小调整、裁剪、快照、实时预览、音频混合和编辑等多种功能。
+
+```
+$ sudo add-apt-repository ppa:openshot.developers/ppa
+$ sudo apt-get update
+$ sudo apt-get install openshot -qt
+```
+
+### **66\. Plank**
+
+如果你在为你的 Ubuntu 桌面寻找一个 Dock 导航栏,那 Plank 应该是一个选择。它是完美的,安装后你不需要任何的修改,除非你想这么做,它有内置的偏好面板,你可以自定义主题,Dock 大小和位置。
+
+![][72]
+
+尽管是一个简单的导航栏,Plank 提供了通过拖拽来重新安排的功能,固定和运行应用图标,转换主题支持。
+
+
+```
+$ sudo add-apt-repository ppa:ricotz/docky
+$ sudo apt-get update
+$ sudo apt-get install plank
+```
+
+### **67\. Filezilla**
+
+Filezilla 是一个免费和跨平台的 FTP 应用,包括 Filezilla 客户端和服务器。它让你使用 FTP 和加密的 FTP 像 FTPS 和 SFTP 传输文件,支持 IPv6 网络协议。
+
+![][73]
+
+它是一个简单的文件传输应用,支持拖拽,支持世界范围的各种语言,多任务的强大用户界面,控制和配置传输速度。
+
+### **68\. Stacer**
+
+Stacer 是一个开源的系统诊断和优化工具,使用 Electron 开发框架开发的。它有一个优秀的用户界面,你可以清理缓存内存,启动应用,卸载不需要的应用,掌控后台系统进程。
+
+![][74]
+
+它同样让你检查磁盘,内存和 CPU 使用情况,给你下载和上传的实时状态。它看起来像 Ubuntu clener 的强力竞争者,但是两者都有独特的特点。
+
+```
+$ sudo add-apt-repository ppa:oguzhaninan/stacer
+$ sudo apt-get update
+$ sudo apt-get install stacer
+```
+
+### **69\. 4K Video Downloader**
+
+4K Video Downloader 是一个简单的视频下载工具,你可以用来从 Vimeo、Facebook、YouTube 和其它在线视频流站点下载视频,播放列表,频道。它支持下载 YouTuBe 播放列表和频道,以 MP4, MKV, M4A, 3GP 和很多其它 音/视频格式。
+
+![][75]
+
+4K Video Downloader 不是你想的那么简单,除了正常的视频下载,它支持 3D 和 360 度 视频下载。它同样提供内置应用协议链接,直连 iTunes。你可以从[这里][76]下载。
+
+### 70\. **Qalculate**
+
+Qalculate 是一个多目的、跨平台的桌面计算器,简单但是强大。它可以用来解决复杂的数学问题和等式,货币汇率转换和很多其它日常计算。
+
+![][77]
+
+它有优秀的用户界面,提供了自定义功能,单元计算,符号计算,算数,画图,和很多你可以在科学计算器上发现的功能。
+
+### **71\. Hiri**
+
+Hiri 是一个跨平台的邮件客户端,使用 Python 语言开发的。它有平滑的用户界面,就它的功能和服务而言,是 Micorsoft Outlook 的很好的替代品。这是很棒的邮件客户端,可以用来发送和接收邮件,管理通讯录,日历和任务。
+
+![][78]
+
+它是一个丰富特点的邮件客户端,提供的功能有集成的任务管理器,邮件同步,邮件评分,邮件过滤等多种功能。
+
+
+```
+$ sudo snap install hiri
+```
+
+### **72\. Sublime Text**
+
+Sublime Text 是一个跨平台的源代码编辑器,用 C++ 和 Python 写的。它有 Python 语言编程接口(API),支持所有主流的编程语言和标记语言。它是简单轻量级的文本编辑器,可被用作 IDE,包含自动补全,语法高亮,分窗口编辑等功能。
+
+![][79]
+
+这个文本编辑器包括一些额外特点:去任何地方、去定义、多选、命令模板和完全定制的用户界面。
+
+```
+$ sudo apt-get install sublime-text
+```
+
+### **73\. TeXstudio**
+
+Texstudio 是一个创建和编辑 LaTex 文件的集成写作环境。它是开源的编辑器,提供了语法高亮、集成查看、交互式拼写检查、代码折叠、拖拽等特点。
+
+![][80]
+
+它是跨平台的编辑器,有简单轻量级的用户界面,易于使用。它集成了 BibTex和 BibLatex 目录管理器,同样有集成的 PDF 查看器。你可以从[官网][81]和 Ubuntu 软件中心下载 Texstudio。
+
+### **74\. QtQR**
+
+QtQR 是一个基于 Qt 的应用,让你在 Ubuntu 中创建和读取二维码。它是用 Python 和 Qt 开发的,有简单和轻量级的用户界面,你可以编码网站地址、邮件、文本、短消息等。你也可以用网络相机解码二维码。
+
+![][82]
+
+如果你经常处理产品销售和服务,QtQR 会证明是有用的工具,但是我不认为在最小硬件要求下有和 QtQR 这样相似并顺畅运行的应用了。
+
+```
+$ sudo add-apt-repository ppa: qr-tools-developers/qr-tools-stable
+$ sudo apt-get update
+$ sudo apt-get install qtqr
+```
+
+### **75\. Kontact**
+
+Kontact 是一个由 KDE 为 KDE 桌面环境开发的集成的个人信息管理器(PIM)。它集成了多个软件到一个集合中,集成了 KMail、KOrganizer和 KAddressBook 到一个用户界面,你可以管理所有的邮件、通讯录、日程表等。
+
+![][83]
+
+它可能是 Microsoft Outlook 的非常好的替代,因为它快速且高度高配置的消息管理工具。它有很好的用户界面,你会发现很容易上手。
+
+```
+$ sudo apt-get install kontact
+```
+
+### **76\. NitroShare**
+
+NitroShare 是一个跨平台、开源的网络文件共享应用。它让你轻松的在局域网的多个操作系统中共享文件。它简单而强大,当在局域网中运行 NitroShare 时,它会自动侦查其它设备。
+
+![][84]
+
+文件传输速度让 NitroShare 称为一个杰出的文件共享应用,它在能够胜任的硬件中能够达到 GB 级的传输速度。没有必要额外配置,安装完成后你就可以开始文件传输。
+
+```
+$ sudo apt-add-repository ppa:george-edison55/nitroshare
+$ sudo apt-get update
+$ sudo apt-get install nitroshare
+```
+
+### **77\. Konversation**
+
+Konversation 是一个为 KDE 桌面环境开发的开源的网络中继聊天(IRC)客户端。它给了到 Freenode 网络平岛的快速入口,你可以为大多数发行版找到支持。
+
+![][85]
+
+它是一个简单的聊天客户端,支持 IPv6 链接, SSL 服务器支持,书签,屏幕通知,UTF-8 检测和另外的主题。它易于使用的 GUI 是高度可配置的。
+
+```
+$ sudo apt-get install konversation
+```
+
+### **78\. Discord**
+
+如果你是硬核游戏玩家,经常玩在线游戏,我有一个很棒的应用推荐给你。Discord 是一个免费的网络电话应用,尤其是为在线游戏者们设计的。它是一个跨平台的应用,可用来文字或语音聊天。
+
+![][86]
+
+Discord 是一个非常流行的语音通话应用游戏社区,因为它是完全免费的,它是 Skype,Ventrilo,Teamspeak 的很好的竞争者。它同样提供清晰的语音质量,现代的文本聊天,你可以共享图片,视频和链接。
+
+### **79\. QuiteRSS**
+
+QuiteRSS是一个开源的 RSS 的新闻聚合和 Atom 新闻要点应用。它是跨平台的要点阅读器,用 Qt 和 C++ 写的。它有简单的用户界面,你可以改变为经典或者报纸模式。它集成了 webkit 浏览器,因此,你可以在单个窗口执行所有任务。
+
+![][87]
+
+QuiteRSS 自带了很多功能,像内容过滤,自动规划摘要,导入/到处 OPML,系统托盘集成和很多其它你期待任何要点阅读器有的特点。
+
+```
+$ sudo apt-get install quiterss
+```
+
+### **80\. MPV Media Player**
+
+MPV 是一个免费和开源的媒体播放器,基于 MPlayer 和 MPlayer 2。它有简单的用户界面,用户之需要拖拽音/视频文件来播放,因为在 GUI 上没有添加媒体文件的选项。
+
+![][88]
+
+关于 MPV 的一件事是它可以轻松播放 4K 视频,Linux 发行版中的其它媒体播放器可能不是这样。它同样给了用户播放在线视频流站点像 YouTube 和 Dailymotion 的能力。
+
+```
+$ sudo add-apt-repository ppa:mc3man/mpv-tests
+$ sudo apt-get update
+$ sudo apt-get install -y mpv
+```
+
+### **81\. Plume Creator**
+
+如果你是一个作家,那么 Plume Creator 是你必不可少的应用,因为你在 Ubuntu 上找不到其它应用像 Plume Creater 这样。写作和编辑故事、章节是繁重的任务,在 Plume Creator 这个令人惊奇的工具的帮助下,将大大帮你简化这个任务。
+
+![][89]
+
+它是一个开源的应用,拥有最小的用户界面,开始你可能觉得困惑,但不久你就会习惯的。它提供的功能有:编辑笔记,摘要,导出 HTML 和 ODT 格式支持,富文本编辑。
+
+```
+$ sudo apt-get install plume-creator
+```
+
+### **82\. Chromium Web Browser**
+
+Chromium 是一个由 Google 开发和发布的开源 web 浏览器。Chromium 就其外观和特点而言,很容易被误认为是 Chrome。它是轻量级和快速的网络浏览器,拥有最小用户界面。
+
+### **83\. Simple Weather Indicator**
+
+Simple Weather Indicator 是用 Python 开发的开源天气提示应用。它自动侦查你的位置,并显示你天气信息像温度,下雨的可能性,湿度,风速和可见度。
+
+![][91]
+
+Weather indicator 自带一些可配置项,例如位置检测,温度 SI 单元,位置可见度开关等等。它是一个酷应用,可以根据你的桌面来调整舒服。
+
+### **84\. SpeedCrunch**
+
+SpeedCrunch 是一个快速和高精度的科学计算器。它预置了数学函数,用户定义函数,复数和单位转换支持。它有简单的用户界面并易于使用。
+
+![][92]
+
+这个科学计算器有令人吃惊的特点像结果预览,语法高亮和自动补全。它是跨平台的,并有多语言支持。
+
+
+### **85\. Scribus**
+
+Scribus 是一个免费和开源的桌面出版应用,允许你创建宣传海报,杂志和图书。它是基于 Qt 工具器的跨平台英语,在 GNU 通用公共证书下发布。它是一个专业的应用,拥有 CMYK 和 ICC 颜色管理的功能,基于 Python 的脚本引擎,和 PDF 创建。
+
+![][93]
+
+Scribus 有相当好的用户界面,易于使用,轻松在低配置下使用。在所有的最新的 Linux 发行版的软件中心可以下载它。
+
+### **86.** **Cura**
+
+Cura 是一个由 David Braam 开发的开源的 3D 打印应用。Ultimaker Cura 是 3D 打印世界最流行的软件,并世界范围的百万用户使用。它遵守 3D 打印模型的 3 步:设计,准备,打印。
+
+![][94]
+
+它是功能丰富的 3D 打印应用,为 CAD 插件和扩展提供了无缝支持。它是一款简单易于使用的工具,新手艺术家可以马上开始了。它支持主流的文件格式像 STL,3MF,和 OBJ。
+
+### **87\. Nomacs**
+
+Nomacs 是一款开源、跨平台的图像浏览器,支持所有主流的图片格式包括 RAW 和 psd 图像。它可以浏览 zip 文件中的图像或者 Microsoft Office 文件并提取到目录。
+
+![][95]
+
+Nomacs 拥有非常简单的用户界面,图像缩略图在顶部,它提供了一些基本的图像操作特点像修改,调整大小,旋转,颜色纠正等。
+
+```
+$ sudo add-apt-repository ppa:nomacs/stable
+$ sudo apt-get update
+$ sudo apt-get install nomacs
+```
+
+### **88\. BitTicker**
+
+BitTicker 是一个 Ubuntu 上的在线比特币-USDT 收报。它是一个简单的工具,能够连接到 bittrex.com 市场,提取最新的 BTC-USDT 并在系统托盘显示 Ubuntu 时钟。
+
+![][96]
+
+它是简单但有用的工具,如果你经常有规律的投资比特币并且必须了解价格波动的话。
+
+### **89\. Organize My Files**
+
+Organize My Files 是一个跨平台的一键点击文件组织工具,它在 Ubuntu 中以 Snap 包的形式获得。它简单但是强大,帮助你找到未组织的文件,通过简单点击来掌控它们。
+
+![][97]
+
+它有易于理解的用户界面,强大且快速。它提供了很多功能:自动组织,递归组织,智能过滤和多层文件夹组织等。
+
+### **90\. GnuCash**
+
+GnuCash 是一个金融账户软件,在 GNU 公共证书下免费使用。它是个人和商业账户的理想软件。它有简单的用户界面允许你追踪银行账户,股票,收入和花费。
+
+![][98]
+
+GnuCash 实现了双入口记账系统,基于专业的账户原则来确保帐薄的平衡和报告的精确。
+
+v### **91\. Calibre**
+
+Calibre 是一个跨平台开源的面向你所有电子书需要的解决方案。它是一个简单的电子书管理器,提供显示、创建、编辑电子书、组织已存在的电子书到虚拟书库、同步和其它更多。
+
+![][99]
+
+Calibre 同样帮你转换电子书到你需要的格式并发送到你的电子书阅读设备。Calibre 是一个很棒的工具,如果你经常阅读和管理电子书的话。
+
+### **92\. MATE Dictionary**
+
+MATE Dictionary 是一个简单的词典,基本上是为 MATE 桌面环境开发的。你可以仅仅输入字然后这个字典会显示意思和引用。
+
+![][100]
+
+它简单和轻量级的在线词典,有最小的用户接口。
+
+### **93\. Converseen**
+
+Converseen 是免费的跨平台的批量图片处理应用,允许你转换、编辑、调整、旋转、裁剪大量图像,仅仅一次鼠标调集。它提供了图像批量重命名的功能,使用前缀或后缀,从一个 Windows 图标文件提取图像等。
+
+![][101]
+
+它有很好的用户界面,易于使用,即时你是一个新手。它也能够转换整个 PDF 文件为图像集合。
+
+### **94\. Tiled Map Editor**
+
+Tiled 是一个免费的水平映射图编辑器,允许你编辑各种形式的投影映射图,例如正交、等轴、和六角的。这个工具对于游戏开发者在游戏引擎开发周期内可能非常有用。
+
+![][102]
+
+Tiled 是一个通用的映射图编辑器,让你创建强大的促进位置,图布局,碰撞区域和敌人位置。它保存所有的数据为 tmx 格式。
+
+### **95.** **Qmmp**
+
+Qmmp 是一个免费和开源的音频播放器,用 C++ 和 Qt 开发的。它是跨平台的音频播放器,界面与 Winamp 很相似。 它有简单的直观的用户界面,Winamp 皮肤可替代默认的 UI。
+
+![][103]
+
+它提供了自动唱片集封面获取,多艺术家支持,另外的插件和扩展支持和其它与 Winamp 相似的特点。
+
+```
+$ sudo add-apt-repository ppa:forkotov02/ppa
+$ sudo apt-get update
+$ sudo apt-get install qmmp qmmp-q4 qmmp-plugin-pack-qt4
+```
+
+### **96\. Arora**
+
+Arora 是一个免费开源的 web 浏览器,提供了专有的下载管理器,书签,私密模式,选项卡式浏览。
+
+![][104]
+
+Arora web 浏览器由 Benjamin C. Meyer 开发,它由于它的轻量自然灵活的特点在 Linux 用户间很受欢迎。
+
+### **97\. XnSketch**
+
+XnSketch 是一个 Ubuntu 上的酷应用,只需要几次点击,就能帮你转换你的图片为卡通或素描图。它展现了 18 个不同的效果例如:锐化、白描、铅笔画和其它的。
+
+![][105]
+
+它有优秀的用户界面,易于使用。一些额外的特点包括容量和边缘强度调整,对比,亮度,饱和度调整。
+
+### **98\. Geany**
+
+Geany 是一个简单轻量级的文本编辑器,像一个集成开发环境。它是跨平台的文本编辑器,支持所有主流编程语言包括Python、C++、LaTex、Pascal、 C#、 etc。
+
+```
+$ sudo apt-get install geany
+```
+
+### **99\. Mumble**
+
+Mumble 是另一个 IP 上的语音应用相似与 Discord。Mumble 同样最初是为在线游戏者使用的,在端到端的聊天上用了客户端-服务器架构。声音质量在 Mumble 上非常好,它提供了端到端的加密来确保私密性。
+
+![][107]
+
+Mumble 是一个开源应用,有简单的用户界面,易于使用。Mumble 在 Ubuntu 软件中心可以下载。
+
+```
+$ sudo apt-get install mumble-server
+```
+
+### **100\. Deluge**
+
+Deluge 是一个跨平台的轻量级的 BitTorrent 客户端,能够用来在 Ubuntu 上下载文件。BitTorrent 客户端与很多 Linux 发行版一起发行,但 Deluge 是最好的 BitTorrent 客户端,界面简单,易于使用。
+
+![][108]
+
+Deluge 拥有你发现的其它 BitTorrent 客户端有的所有功能,但是一个功能特别突出,它给了用户从其它设备进入客户端的能力,这样你可以远程下载文件了。
+
+```
+$ sudo add-apt-repository ppa:deluge-team/ppa
+$ sudo apt-get update
+$ sudo apt-get install deluge
+```
+
+所以这些就是 2018 年我为大家选择的 Ubuntu 上最好的 100 个应用了。所有列出的应用都在 Ubuntu 18.04 上测试了,肯定在老版本上也能运行。请在 [@LinuxHint][109] 和 [@SwapTirthakar][110] 自由分享你的观点。
+
+--------------------------------------------------------------------------------
+
+via: https://linuxhint.com/100_best_ubuntu_apps/
+
+作者:[Swapnil Tirthakar][a]
+选题:[lujun9972](https://github.com/lujun9972)
+译者:[warmfrog](https://github.com/warmfrog)
+校对:[校对者ID](https://github.com/校对者ID)
+
+本文由 [LCTT](https://github.com/LCTT/TranslateProject) 原创编译,[Linux中国](https://linux.cn/) 荣誉推出
+
+[a]:https://linuxhint.com/author/swapnil/
+[1]:https://linuxhint.com/applications-2018-ubuntu/
+[2]:https://linuxhint.com/wp-content/uploads/2018/06/100-Best-Ubuntu-Apps.png
+[3]:https://linuxhint.com/wp-content/uploads/2018/06/Chrome.png
+[4]:https://linuxhint.com/wp-content/uploads/2018/06/Steam.png
+[5]:https://linuxhint.com/wp-content/uploads/2018/06/Wordpress.png
+[6]:https://linuxhint.com/wp-content/uploads/2018/06/VLC.png
+[7]:https://linuxhint.com/wp-content/uploads/2018/06/Atom-Text-Editor.png
+[8]:https://linuxhint.com/wp-content/uploads/2018/06/GIMP.png
+[9]:https://linuxhint.com/wp-content/uploads/2018/06/Google-Play.png
+[10]:https://www.googleplaymusicdesktopplayer.com/
+[11]:https://linuxhint.com/wp-content/uploads/2018/06/Franz.png
+[12]:https://meetfranz.com/#download
+[13]:https://linuxhint.com/wp-content/uploads/2018/06/Synaptic.png
+[14]:https://linuxhint.com/wp-content/uploads/2018/06/Skype.png
+[15]:https://linuxhint.com/wp-content/uploads/2018/06/VirtualBox.png
+[16]:https://linuxhint.com/wp-content/uploads/2018/06/Unity-Tweak-Tool.png
+[17]:https://linuxhint.com/wp-content/uploads/2018/06/Ubuntu-Cleaner.png
+[18]:https://linuxhint.com/wp-content/uploads/2018/06/Visual-Studio-Code.png
+[19]:https://linuxhint.com/wp-content/uploads/2018/06/Corebird.png
+[20]:https://linuxhint.com/wp-content/uploads/2018/06/Pixbuf.png
+[21]:https://linuxhint.com/wp-content/uploads/2018/06/Clementine.png
+[22]:https://linuxhint.com/wp-content/uploads/2016/06/blender.jpg
+[23]:https://linuxhint.com/wp-content/uploads/2018/06/Audacity.png
+[24]:https://linuxhint.com/wp-content/uploads/2018/06/Vim.png
+[25]:https://linuxhint.com/wp-content/uploads/2018/06/Inkscape-1.png
+[26]:https://linuxhint.com/wp-content/uploads/2018/06/ShotCut.png
+[27]:https://linuxhint.com/wp-content/uploads/2018/06/Simple-Screen-Recorder.png
+[28]:https://linuxhint.com/wp-content/uploads/2018/06/Telegram.png
+[29]:https://linuxhint.com/wp-content/uploads/2018/06/ClamTk.png
+[30]:https://linuxhint.com/wp-content/uploads/2018/06/Mailspring.png
+[31]:https://linuxhint.com/wp-content/uploads/2018/06/PyCharm.png
+[32]:https://linuxhint.com/wp-content/uploads/2018/06/Caffeine.png
+[33]:https://linuxhint.com/wp-content/uploads/2018/06/Etcher.png
+[34]:https://etcher.io/
+[35]:https://linuxhint.com/wp-content/uploads/2018/06/Neofetch.png
+[36]:https://linuxhint.com/wp-content/uploads/2018/06/Liferea.png
+[37]:https://linuxhint.com/wp-content/uploads/2018/06/Shutter.png
+[38]:https://linuxhint.com/wp-content/uploads/2018/06/Weather.png
+[39]:https://linuxhint.com/wp-content/uploads/2018/06/Ramme.png
+[40]:https://github.com/terkelg/ramme/releases
+[41]:https://linuxhint.com/wp-content/uploads/2018/06/Thunderbird.png
+[42]:https://linuxhint.com/wp-content/uploads/2018/06/Pidgin.png
+[43]:https://linuxhint.com/wp-content/uploads/2018/06/Krita.png
+[44]:https://linuxhint.com/wp-content/uploads/2018/06/Dropbox.png
+[45]:https://linuxhint.com/wp-content/uploads/2018/06/kodi.png
+[46]:https://linuxhint.com/wp-content/uploads/2018/06/Spotify.png
+[47]:https://linuxhint.com/wp-content/uploads/2018/06/Brackets.png
+[48]:https://linuxhint.com/wp-content/uploads/2018/06/Bitwarden.png
+[49]:https://linuxhint.com/wp-content/uploads/2018/06/Terminator.png
+[50]:https://linuxhint.com/wp-content/uploads/2018/06/Yak-Yak.png
+[51]:https://linuxhint.com/wp-content/uploads/2018/06/Thonny.png
+[52]:https://linuxhint.com/wp-content/uploads/2018/06/Font-Manager.png
+[53]:https://linuxhint.com/wp-content/uploads/2018/06/Atril.png
+[54]:https://linuxhint.com/wp-content/uploads/2018/06/Notepadqq.png
+[55]:https://linuxhint.com/wp-content/uploads/2018/06/Amarok.png
+[56]:https://linuxhint.com/wp-content/uploads/2018/06/Cheese.png
+[57]:https://linuxhint.com/wp-content/uploads/2018/06/MyPaint.png
+[58]:https://linuxhint.com/wp-content/uploads/2018/06/PlayOnLinux.png
+[59]:https://linuxhint.com/wp-content/uploads/2018/06/Akregator.png
+[60]:https://linuxhint.com/wp-content/uploads/2018/06/Brave.png
+[61]:https://linuxhint.com/wp-content/uploads/2018/06/Bitcoin-Core.png
+[62]:https://linuxhint.com/wp-content/uploads/2018/06/Speedy-Duplicate-Finder.png
+[63]:https://linuxhint.com/wp-content/uploads/2018/06/Zulip.png
+[64]:https://linuxhint.com/wp-content/uploads/2018/06/Okular.png
+[65]:https://linuxhint.com/wp-content/uploads/2018/06/Focus-Writer.png
+[66]:https://linuxhint.com/wp-content/uploads/2018/06/Guake.png
+[67]:https://linuxhint.com/wp-content/uploads/2018/06/KDE-Connect.png
+[68]:https://linuxhint.com/wp-content/uploads/2018/06/CopyQ.png
+[69]:https://linuxhint.com/wp-content/uploads/2018/06/Tilix.png
+[70]:https://linuxhint.com/wp-content/uploads/2018/06/Anbox.png
+[71]:https://linuxhint.com/wp-content/uploads/2018/06/OpenShot.png
+[72]:https://linuxhint.com/wp-content/uploads/2018/06/Plank.png
+[73]:https://linuxhint.com/wp-content/uploads/2018/06/FileZilla.png
+[74]:https://linuxhint.com/wp-content/uploads/2018/06/Stacer.png
+[75]:https://linuxhint.com/wp-content/uploads/2018/06/4K-Video-Downloader.png
+[76]:https://www.4kdownload.com/download
+[77]:https://linuxhint.com/wp-content/uploads/2018/06/Qalculate.png
+[78]:https://linuxhint.com/wp-content/uploads/2018/06/Hiri.png
+[79]:https://linuxhint.com/wp-content/uploads/2018/06/Sublime-text.png
+[80]:https://linuxhint.com/wp-content/uploads/2018/06/TeXstudio.png
+[81]:https://www.texstudio.org/
+[82]:https://linuxhint.com/wp-content/uploads/2018/06/QtQR.png
+[83]:https://linuxhint.com/wp-content/uploads/2018/06/Kontact.png
+[84]:https://linuxhint.com/wp-content/uploads/2018/06/Nitro-Share.png
+[85]:https://linuxhint.com/wp-content/uploads/2018/06/Konversation.png
+[86]:https://linuxhint.com/wp-content/uploads/2018/06/Discord.png
+[87]:https://linuxhint.com/wp-content/uploads/2018/06/QuiteRSS.png
+[88]:https://linuxhint.com/wp-content/uploads/2018/06/MPU-Media-Player.png
+[89]:https://linuxhint.com/wp-content/uploads/2018/06/Plume-Creator.png
+[90]:https://linuxhint.com/wp-content/uploads/2018/06/Chromium.png
+[91]:https://linuxhint.com/wp-content/uploads/2018/06/Simple-Weather-Indicator.png
+[92]:https://linuxhint.com/wp-content/uploads/2018/06/SpeedCrunch.png
+[93]:https://linuxhint.com/wp-content/uploads/2018/06/Scribus.png
+[94]:https://linuxhint.com/wp-content/uploads/2018/06/Cura.png
+[95]:https://linuxhint.com/wp-content/uploads/2018/06/Nomacs.png
+[96]:https://linuxhint.com/wp-content/uploads/2018/06/Bit-Ticker-1.png
+[97]:https://linuxhint.com/wp-content/uploads/2018/06/Organize-My-Files.png
+[98]:https://linuxhint.com/wp-content/uploads/2018/06/GNU-Cash.png
+[99]:https://linuxhint.com/wp-content/uploads/2018/06/Calibre.png
+[100]:https://linuxhint.com/wp-content/uploads/2018/06/MATE-Dictionary.png
+[101]:https://linuxhint.com/wp-content/uploads/2018/06/Converseen.png
+[102]:https://linuxhint.com/wp-content/uploads/2018/06/Tiled-Map-Editor.png
+[103]:https://linuxhint.com/wp-content/uploads/2018/06/Qmmp.png
+[104]:https://linuxhint.com/wp-content/uploads/2018/06/Arora.png
+[105]:https://linuxhint.com/wp-content/uploads/2018/06/XnSketch.png
+[106]:https://linuxhint.com/wp-content/uploads/2018/06/Geany.png
+[107]:https://linuxhint.com/wp-content/uploads/2018/06/Mumble.png
+[108]:https://linuxhint.com/wp-content/uploads/2018/06/Deluge.png
+[109]:https://twitter.com/linuxhint
+[110]:https://twitter.com/SwapTirthakar
+
+
+
+
+
+
+
+
+
+
+
+
+
+
+
+
+
+
diff --git a/translated/tech/20180902 Learning BASIC Like It-s 1983.md b/translated/tech/20180902 Learning BASIC Like It-s 1983.md
new file mode 100644
index 0000000000..5640ad3d95
--- /dev/null
+++ b/translated/tech/20180902 Learning BASIC Like It-s 1983.md
@@ -0,0 +1,184 @@
+学习 BASIC 像它的1983年
+======
+我没有生活在1983年.我偶尔有一些遗憾。我相当遗憾,我没有体验8位计算机时代的到来,因为我认为第一次遇到相对简单和过于受约束的计算机的人们,有超过我们的一些人的巨大的优势。
+
+今天,(大多数)每个人知道如何使用一台计算机,但是很少有人,甚至是在计算机工业中,明白在一些单台机器内部正在发生什么的全部。现在有[如此多软件层次][1]努力来识别必不可少的部分来做如此多不同的事情。在1983年,虽然,家用电脑足够简单,一个用功的人能学到一台特定计算机是如何工作的。现在这人可能比我通过所有堆积在硬件顶部的现代操作系统的抽象概念较少迷惑。我认为像他们采用的这些抽象概念的层次是容易一个接一个理解的;今天,新的程序员不得不通过自上而下的逆流时间上的工作来尝试理解它们。
+
+很多著名的程序员,尤其在计算机游戏工业,童年在8位计算机上开始编程游戏,像,苹果 II 和 Commodore 64。John Romero, Richard Garriott,和 Chris Roberts 都是例子。如何发生是容易看到的。在8位计算机时代,很多游戏仅可在计算机杂质和[书籍][2]中作为印刷的BASIC列表获得。如果你想玩这些游戏中其中一个,你不得手工不键入完整的程序。不可避免的,你可能得到一些错误,所以你可能不得不调试你的程序。等到你获得它工作, 你充分知道程序如何起作用来开始你自己修改它。如果你是一个着迷的游戏玩家,你不可避免地也成为一个好的程序员。
+
+在童年我也玩电脑游戏。但是我玩的游戏在只读光盘上。我有时发现我自己不得不搜索如何修复一个崩溃的安装器,这可能涉及编辑 Windows 注册表或一些像这样的事情。这类少数的使用计算机来考虑在大学中学习计算机科学的故障诊断可能使我足够舒适。但是在大学中从不教我一些关键性的关于计算机如何工作或如何控制它们的事。
+
+当然,现在我告诉计算机为了活动而做什么。尽管如此,我请不自觉地感到,我缺少一些基本的仅被给予这些成长为简单编程的计算机人的深刻见解。在20世纪80年代初,第一次偶然遇到计算机会是什么样子?与今天使用计算机的经验相比会有怎样的不同?
+
+这篇张贴文将与通常的二位历史贴文有一点不同,因为我将为这些问题尝试设想一个答案。
+
+### 1983
+
+仅仅是上周,你在电视上看到 [Commodore 64 广告][3] ,现在 M*A*S*H 结束了,在星期一晚上,你正在市场上采购没做过的一些东西。这个 Commodore 64 甚至看起来比 Apple II 更好,鲁迪(译者注:应该是拥有 Apple II 的人)的家人在他们的地下室。而且,广告承诺新的计算机将一会携带朋友们“击倒”你的门。你知道一些在学校的人们只要他们能在这里玩 Zork,他们宁愿在你的家里过把瘾,也不愿呆在鲁迪的家里。
+
+所以,你说服你的父母去买一台.你的妈妈说,她们可以考虑它,如果有一台家庭电脑,意味着你离开娱乐厅。你勉强同意。你的爸爸想,他可以开始在 MultiPlan (译注:电子表格程序)中跟踪家庭的资金。 MultiPlan 是他曾听到过的电子表格程序, 这是为什么计算机放在客厅的原因。然而,一年后,你将是唯一仍然使用它的人。你最终被允许把它放到你的卧室中的桌子上,正好在你的警察海报下面。
+
+(你的姐姐抗议这个决定,但是,它是在1983年,并且计算机[不是给她][4]。)
+
+父亲在从工作到回家的路上从 [ComputerLand][5] 处拿到它。你俩把盒子放置在电视机的旁边,并打开它。外包装上说“欢迎来到友好的计算机世界”。二十分钟以后,你不确信—你俩仍然试图来连接 Commodore 到电视机,并且想知道是否电视机的天线电缆是75欧姆或300欧姆同轴电缆。但是,你最终能够转到你的电视机到频道3,并看到一个粒状的,紫色的图像。
+
+![Commodore 64 启动屏幕][6]
+
+计算机报告,`READY`。你的爸爸把计算机推向你,标志着你应该第一个人来给它一个尝试。你小心翼翼地敲击每个字母,键入,`HELLO`。计算机的回应是令人困惑的。
+
+![Commodore 64 语法错误][7]
+
+你尝试输入一些很少变化的不同的单词,但是回应总是相同的。你的爸爸说,你最好通读手册的剩余部分。这可能不意味着是秘籍—[随 Commodore 64 一起提供的手册][8] 是一小本书。但是这不会困住你,因为手册的引进是奇迹的预兆。
+
+Commodore 64,它声称,有“微型计算机工业中最高级的图画制作器”,能允许“设计你拥有四种不同颜色的图画,就像你在看到的街机电子游戏”。Commodore 64 也有“内置的音乐和声音效果,比得上很多著名的语言音响合成器”。所有的这些工具将被放到你的手上,因为手册将陪伴你贯穿它全部:
+
+> 正像与所有可用的硬件重要一样,这本用户的指南将帮助你详尽阐述你的计算机的理解。它不会在这里告诉你有必要知道的关于计算机的任何事,但是它将谈及你到一个关于涉及的主题的详细情报方面的种类繁多的出版物。Commodore 希望你来真正地享受你的新 COMMODORE 64 。并且来玩得开心,记住:编程不是你能在一天内就学会的一种东西。你自己要有耐心,因为你将翻阅用户指南。
+
+那一夜,在床上,你通读整个前三个章节—“安装”,“入门”,和“开始 BASIC 编程”—在最终抵挡不住睡意前,手册被交叉放在胸前。
+
+### Commodore BASIC
+
+现在是星期六早上,你急于尝试你已经学到的什么。手册教你如何做的第一件事是更改在显示器上的颜色。你仿效指令,按下 `CTRL-9` 来进入相反的情况的类型模式,然后拖住空格键来创建长行。你可以使用 `CTRL-1` 到 `CTRL-8` 在不同的颜色之间交换,在电视机屏幕上陶醉于你的突然的新的力量。
+
+![Commodore 64 颜色带][9]
+
+尽管这很酷,你意识到它不算为编程。为了编程计算机,你昨晚已经学到,你必须以一种称为 BASIC 的语言与计算机交谈。对于你,BASIC 看起来像星球大战外的一些东西,但是,到1983年,BASIC 大约二十年了。它由两位达特茅斯教授,John Kemeny 和 Tom Kurtz 发明,他们想让社会科学和人文科学中的本科生可访问计算机。它在微型计算机上是普遍地可用的,并流行在大学数学课中。在比尔盖茨和保罗艾伦为 Altair 编写 MicroSoft BASIC 解释器后,在微型计算机上变成标准。但是手册没有任何解释这个,并且你很多年不会学到它。
+
+手册建议你尝试中的第一个 BASIC 命令是 `PRINT` 命令。你慢慢地键入 `PRINT "COMMODORE 64"`,因为你花费一点时间来在`2`按键上面找到引号符号。你单击 `RETURN` ,这一次,并不是抱怨,计算机准确地做你告诉它去做的事,并在下一行中显示 “COMMODORE 64” 。
+
+现在你尝试在各种各样不同的东西上使用 `PRINT` 命令:两个数字加在一起,两个数字乘在一起,甚至几个十进制数字。你停止输入 `PRINT` ,并使用 `?` 代替,因为手册已经正式告知你 `?` 是 `PRINT` 的一个缩写,通常被专业程序员使用。你感觉已经像一个专家,不过你想起你还没有看“开始 BASIC 编程”的三个章节。
+
+你不久达到目的。该章节开始催促你来写你的第一个真正的 BASIC 程序。你输入 `NEW` 并单击 `RETURN`,这给你一个干净黑板(slate)。然后你在其中输入你的程序:
+
+```
+10 ?"COMMODORE 64"
+20 GOTO 10
+```
+
+手册解释,10和20是行号。它们为计算机排序语句。它们也允许程序员来引用在某系命令中程序的其它行,正像你已经完成的 `GOTO` 命令, 它监督程序回到行10。“它是好的编程惯例”,手册认为,“以10的增量来编号行—以备你以后需要插入一些语句”。
+
+你输入 `RUN` ,并盯着用“COMMODORE 64”堵塞的屏幕 ,重复的一遍又一遍。
+
+![Commodore 64 显示反复打印 "Commodore 64" 的结果][10]
+
+你不确定这不会引爆你的计算机。它花费一秒钟才想起你应该单击 `RUN/STOP` 按键来打断循环。
+
+手册接下来的一些部分教你变量,手册告诉你变量像“在计算机中许多的暗盒,它们每个可以容纳一个数字或一个文本字符的字符串”。以一个 `%` 符号结尾的变量是一个整数,与此同时,以一个 `$` 符号结尾的变量是一个字符字符串。其余的所有变量是一些称为“浮点”变量的东西。手册警告你小心变量名称,因为计算机仅识别变量名称的前两个字母,尽管不阻止你想要的名称长度。(这并不是特别困扰你,但是你可能看到今后30年,这可能打击一些人像彻底地精神失常一样)。
+
+你接着学习 `IF... THEN...` 和 `FOR... NEXT...` 结构体。有所有的这些新的工具,你感觉有能力来解决的接下来的手册扔给你的大挑战。“如果你是有野心的人”,很好,“输入下面的程序,并查看会发生什么”。该程序比你目前已经看到的程序更长、更复杂,但是,你渴望知道它将做什么:
+
+```
+10 REM BOUNCING BALL
+20 PRINT "{CLR/HOME}"
+25 FOR X = 1 TO 10 : PRINT "{CRSR/DOWN}" : NEXT
+30 FOR BL = 1 TO 40
+40 PRINT " ●{CRSR LEFT}";:REM (● is a Shift-Q)
+50 FOR TM = 1 TO 5
+60 NEXT TM
+70 NEXT BL
+75 REM MOVE BALL RIGHT TO LEFT
+80 FOR BL = 40 TO 1 STEP -1
+90 PRINT " {CRSR LEFT}{CRSR LEFT}●{CRSR LEFT}";
+100 FOR TM = 1 TO 5
+110 NEXT TM
+120 NEXT BL
+130 GOTO 20
+```
+
+上面的程序利用 Commodore 64 最酷的特色之一。不可打印的命令字符,当传递到 `PRINT` 命令时,作为字符串的一部分,仅仅做它们通常执行的动作,而不是打印到屏幕。这允许你通过打印来自你程序中的字符串来重演任意的命令链。
+
+输入上面的程序花费很长时间。你犯一些错误,并不得不重新输入一些行。但是,你最终能够输入 `RUN` ,并看见一个杰作:
+
+![Commodore 64 反弹球][11]
+
+你认为这是你见过的最酷的事是一个主要的竞争者。不过你几乎立即忘记它,因为一旦你已经学习 BASIC 的内置的函数,像 `RND` (它返回一个随机数字) 和 `CHR$` (它返回匹配一个给定数字的字符),手册向你展示一个很多年的程序,到现在仍然足够著名,能够成为一个[论文选集][12]的题目
+
+```
+10 PRINT "{CLR/HOME}"
+20 PRINT CHR$(205.5 + RND(1));
+40 GOTO 20
+```
+
+当运行时,上面的程序产生一个随机的迷宫:
+
+![Commodore 64 迷宫程序][13]
+
+这肯定是你曾经见过最酷的事。
+
+### PEEK 和 POKE
+
+你现在看过 Commodore 64 手册的前四章节,包含标题为“高级的 BASIC” 的章节, 所以你觉得你自己十分自豪。这个星期六早上,你已经学习很多东西。但是这个下午(在一个快速午餐打断后),你继续去学习一些东西,这将使这个在你的客厅中奇妙的机器变得更不神秘。
+
+在手册中的下一个章节被标题为“高级颜色和图像命令”。以通过再次讨论颜色条开始,你能够输入我们这个早上的第一件事,并向你显示你如何能够从一个程序中做相同的事。然后它教你如何更改屏幕的背景颜色。
+
+为此,你需要使用最简单的 `PEEK` 和 `POKE` 命令。这些命令分别允许你来检查和写到存储器地址。Commodore 64 有一个主要背景颜色和一个边界背景颜色。每个颜色通过一个特定的内存地址控制。你可以写任何你喜欢的这些地址的颜色值到背景颜色或边界颜色。
+
+手册解释:
+
+> 正像变量可以被认为在机器中的一种放置你的信息的表现形式,你也可以认为在计算机中代表特殊内存位置的一些特殊定义的“容器”。
+>
+> Commodore 64 寻找这些内存位置来查看屏幕的背景和边界应该是什么样的颜色,什么样的字符能够被显示在屏幕上—在哪里—很多其它的任务。
+
+你写一个程序来循环所有可用的背景和边界的颜色的混合体:
+
+```
+10 FOR BA = 0 TO 15
+20 FOR BO = 0 TO 15
+30 POKE 53280, BA
+40 POKE 53281, BO
+50 FOR X = 1 TO 500 : NEXT X
+60 NEXT BO : NEXT BA
+```
+
+虽然 `POKE` 命令,带有它们的大量的运算数,开始时看起来很吓人,现在你看到数字的真实的值不是很要紧。明显地,你不得不获取正确的数字,但是所有的数字代表的是一个 Commodore 正好出现在存储在地址53280处的“容器”。这个容器有一个特殊的用途: Commodore 使用它来决定屏幕背景应该是什么颜色。
+
+![Commodore 64 更改背景颜色][14]
+
+你认为这是非常有条理的. 仅仅通过写入内存中一个特殊目的的容器中,你可以控制一台计算机的基础属性。你不确定 Commodore 64 的电路系统如何使用你写图内存中的值,并更改屏幕的颜色,但是,你不知道这些也没事。至少你理解到这点的每一件事。
+
+### 特殊容器
+
+那个周六,你没有读完整本手册,因为你现在开始精疲力尽。但是你终于读完它的全部。在这个过程中,你学到更多关于 Commodore 64 的特殊目的容器。它们是你可以写的容器来控制在屏幕上是什么—一个容器,事实上,每一个位置都可能出现一个角色f。在第六章节中,“小精灵图形”,你学到特殊目的容器允许你来定义能被四周移动和甚至缩放的图像。在第七章节中,“创建声音”,你学到你能写入的容器以便使你的 Commodore 64 歌唱 “Michael Row the Boat Ashore”。Commodore 64,转到外面,你可能以后学习一个称为 API 的非常有限的方法。控制 Commodore 64 大多涉及通过电路系统给定特殊意义来写到内存地址。
+
+你最终花费很多年写到这些粘住你的特殊容器。甚至几十年后,当你发现你自己用一组大量的图形或声音 API 编程一个机器时,你知道 API ,在隐蔽物的后面, API 最终是写到这些容器或一些像它们的东西。你有时会怀疑曾经使用过 API 的年轻程序员,他们一定会好奇并思考 API 正在为他们做什么。可能他们认为 API 正在调用一些其它隐藏的 API 。但是,随后思考隐藏的 API 正在调用什么?你同情这些年轻的程序员,因为他们一定非常迷惑。
+
+如果你喜欢这篇张贴文, 更喜欢它每两周出来一次!在Twitter上关注 [@TwoBitHistory][15] 或订阅[ RSS 源][16]来确保你知道新的张贴文出来的时间。
+
+先前关于TwoBitHistory…
+
+> 你曾经好奇一个19世纪计算机程序翻译到 C 语言程序的可能的样子吗?
+>
+> 这周帖子: 一个详细的说明查看,Ada Lovelace 的著名程序的工作,和它将尝试去做什么。
+>
+> — TwoBitHistory (@TwoBitHistory) [2018年8月19日][17]
+
+--------------------------------------------------------------------------------
+
+通过:https://twobithistory.org/2018/09/02/learning-basic.html
+
+作者:[Two-Bit History][a]
+选题:[lujun9972][b]
+译者:[robsean](https://github.com/robsean)
+校对:[校对者ID](https://github.com/校对者ID)
+
+本文由 [LCTT](https://github.com/LCTT/TranslateProject) 原创编译,[Linux中国](https://linux.cn/) 荣誉推出
+
+[a]: https://twobithistory.org
+[b]: https://github.com/lujun9972
+[1]: https://www.youtube.com/watch?v=kZRE7HIO3vk
+[2]: https://en.wikipedia.org/wiki/BASIC_Computer_Games
+[3]: https://www.youtube.com/watch?v=ZekAbt2o6Ms
+[4]: https://www.npr.org/sections/money/2014/10/21/357629765/when-women-stopped-coding
+[5]: https://www.youtube.com/watch?v=MA_XtT3VAVM
+[6]: https://twobithistory.org/images/c64_startup.png
+[7]: https://twobithistory.org/images/c64_error.png
+[8]: ftp://www.zimmers.net/pub/cbm/c64/manuals/C64_Users_Guide.pdf
+[9]: https://twobithistory.org/images/c64_colors.png
+[10]: https://twobithistory.org/images/c64_print_loop.png
+[11]: https://twobithistory.org/images/c64_ball.gif
+[12]: http://10print.org/
+[13]: https://twobithistory.org/images/c64_maze.gif
+[14]: https://twobithistory.org/images/c64_background.gif
+[15]: https://twitter.com/TwoBitHistory
+[16]: https://twobithistory.org/feed.xml
+[17]: https://twitter.com/TwoBitHistory/status/1030974776821665793?ref_src=twsrc%5Etfw
diff --git a/translated/tech/20180914 A day in the life of a log message.md b/translated/tech/20180914 A day in the life of a log message.md
new file mode 100644
index 0000000000..07b1c3b1fa
--- /dev/null
+++ b/translated/tech/20180914 A day in the life of a log message.md
@@ -0,0 +1,56 @@
+日志消息的一日之旅
+======
+
+> 从一条日志消息的角度来巡览现代分布式系统。
+
+
+
+混沌系统往往是不可预测的。在构建像分布式系统这样复杂的东西时,这一点尤其明显。如果不加以控制,这种不可预测性会无止境的浪费时间。这就是为什么分布式系统的每个组件,无论多小,都必须设计成以简化的方式组合在一起。
+
+[Kubernetes][1] 为抽象计算资源提供了一个很有前景的模型 —— 但即使是它也必须与 [Apache Kafka][2] 等其他分布式平台协调一致,以确保可靠的数据传输。如果有人要整合这两个平台,它会如何运作?此外,如果你通过这样的系统跟踪像日志消息这么简单的东西,它会是什么样子?本文将重点介绍来自[OKD][3] 内运行的应用程序的日志消息如何通过 Kafka 进入数据仓库(OKD 是为 Red Hat OpenShift 提供支持的 Kubernetes 的原初社区发行版)。
+
+### OKD 定义的环境
+
+这样的旅程始于 OKD,因为该容器平台完全覆盖了它抽象的硬件。这意味着日志消息等待由驻留在容器中的应用程序写入 stdout 或 stderr 流。从那里,日志消息被容器引擎(例如 [CRI-O][4])重定向到节点的文件系统。
+
+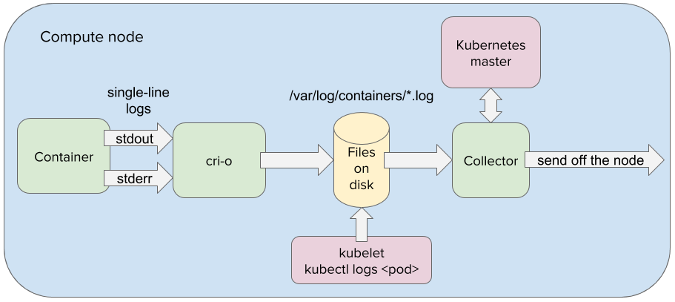
+
+在 OpenShift 中,一个或多个容器封装在称为 pod 的虚拟计算节点中。实际上,在 OKD 中运行的所有应用程序都被抽象为 pod(豆荚)。这允许应用程序以统一的方式操纵。这也大大简化了分布式组件之间的通信,因为 pod 可以通过 IP 地址和[负载均衡服务][5]系统地寻址。因此,当日志消息由日志收集器应用程序从节点的文件系统获取时,它可以很容易地传递到在 OpenShift 中运行的另一个 pod。
+
+### 在豆荚里的两个豌豆
+
+为了确保可以在整个分布式系统中无处不在地传播日志消息,日志收集器需要将日志消息传递到在 OpenShift 中运行的 Kafka 集群数据中心。通过 Kafka,日志消息可以以可靠且容错的方式低延迟传递给消费应用程序。但是,为了在 OKD 定义的环境中获得 Kafka 的好处,Kafka 需要完全集成到 OKD 中。
+
+运行 [Strimzi 操作子][6]将实例化所有 Kafka 组件为 pod,并将它们集成在 OKD 环境中运行。 这包括用于排队日志消息的 Kafka 代理,用于从 Kafka 代理读取和写入的 Kafka 连接器,以及用于管理 Kafka 集群状态的 Zookeeper 节点。Strimzi 还可以将日志收集器双实例化作为 Kafka 连接器,允许日志收集器将日志消息直接提供给在 OKD 中运行的 Kafka 代理 pod。
+
+### 在 OKD 内的 Kafka
+
+当日志收集器 pod 将日志消息传递给 Kafka 代理时,收集器会写到单个代理分区,并将日志消息附加到该分区的末尾。使用 Kafka 的一个优点是它将日志收集器与日志的最终目标分离。由于解耦,日志收集器不关心日志最后是放在 [Elasticsearch][7]、Hadoop、Amazon S3 中的某个还是全都。Kafka 与所有基础设施连接良好,因此 Kafka 连接器可以在任何需要的地方获取日志消息。
+
+一旦写入 Kafka 代理的分区,该日志消息就会在 Kafka 集群内的代理分区中复制。这是它的一个非常强大的概念;结合平台的自愈功能,它创建了一个非常灵活的分布式系统。例如,当节点变得不可用时,节点上运行的应用程序几乎立即在健康节点上生成。因此,即使带有 Kafka 代理的节点丢失或损坏,日志消息也能保证存活在必要多的节点上,并且新的 Kafka 代理将快速原位取代。
+
+### 存储起来
+
+在日志消息被提交到 Kafka 主题后,它将等待 Kafka 连接器接收器使用它,该接收器将日志消息中继到分析引擎或日志记录仓库。在传递到其最终目的地时,可以分析日志消息以进行异常检测,可以查询日志以立即进行根本原因分析,或用于其他目的。无论哪种方式,日志消息都由 Kafka 以安全可靠的方式传送到目的地。
+
+OKD 和 Kafka 是正在迅速发展的功能强大的分布式平台。创建能够在不影响性能的情况下抽象出分布式计算的复杂特性的系统至关重要。毕竟,如果我们不能简化单条日志消息的旅程,我们怎么能夸耀全系统的效率呢?
+
+--------------------------------------------------------------------------------
+
+via: https://opensource.com/article/18/9/life-log-message
+
+作者:[Josef Karásek][a]
+选题:[lujun9972](https://github.com/lujun9972)
+译者:[wxy](https://github.com/wxy)
+校对:[校对者ID](https://github.com/校对者ID)
+
+本文由 [LCTT](https://github.com/LCTT/TranslateProject) 原创编译,[Linux中国](https://linux.cn/) 荣誉推出
+
+[a]: https://opensource.com/users/jkarasek
+[1]: https://kubernetes.io/
+[2]: https://kafka.apache.org/
+[3]: https://www.okd.io/
+[4]: http://cri-o.io/
+[5]: https://kubernetes.io/docs/concepts/services-networking/service/
+[6]: http://strimzi.io/
+[7]: https://www.elastic.co/
diff --git a/translated/tech/20190219 5 Good Open Source Speech Recognition-Speech-to-Text Systems.md b/translated/tech/20190219 5 Good Open Source Speech Recognition-Speech-to-Text Systems.md
new file mode 100644
index 0000000000..0067324e41
--- /dev/null
+++ b/translated/tech/20190219 5 Good Open Source Speech Recognition-Speech-to-Text Systems.md
@@ -0,0 +1,127 @@
+[#]: collector: (lujun9972)
+[#]: translator: (luuming)
+[#]: reviewer: ( )
+[#]: publisher: ( )
+[#]: url: ( )
+[#]: subject: (5 Good Open Source Speech Recognition/Speech-to-Text Systems)
+[#]: via: (https://fosspost.org/lists/open-source-speech-recognition-speech-to-text)
+[#]: author: (Simon James https://fosspost.org/author/simonjames)
+
+5 款不错的开源语音识别/语音文字转换系统
+
+======
+
+
+
+语音文字转换(STT)系统就像它名字所蕴含的那样,是一种将说出的单词转换为文本文件以供后续用途的方式。
+
+语音文字转换技术非常有用。它可以用到许多应用中,例如自动转录,使用自己的声音写书籍或文本,用生成的文本文件和其他工具做复杂的分析等。
+
+在过去,语音文字转换技术以专有软件和库为主导,开源替代品并不存在或是有严格的限制并且没有社区。这一点正在发生改变,当今有许多开源语音文字转换工具和库可以让你立即使用。
+
+这里我列出了 5 个。
+
+### 开源语音识别库
+
+#### DeepSpeech 项目
+
+![5 Good Open Source Speech Recognition/Speech-to-Text Systems 15 open source speech recognition][1]
+
+该项目由 Firefox 浏览器背后的组织 Mozilla 团队开发。它 100% 自由并且使用 TensorFlow 机器学习框架实现。
+
+换句话说,你可以用它训练自己的模型获得更好的效果,甚至可以用它转换其它的语言。你也可以轻松的将它集成到自己的 Tensorflow 机器学习项目中。可惜的是项目当前默认仅支持英语。
+
+它也支持许多编程语言,例如 Python(3.6)。可以让你在数秒之内获取:
+
+```
+pip3 install deepspeech
+deepspeech --model models/output_graph.pbmm --alphabet models/alphabet.txt --lm models/lm.binary --trie models/trie --audio my_audio_file.wav
+```
+
+你也可以通过 npm 安装它:
+
+```
+npm install deepspeech
+```
+
+想要获得更多信息,请参考[项目主页][2]。
+
+#### Kaldi
+
+![5 Good Open Source Speech Recognition/Speech-to-Text Systems 17 open source speech recognition][3]
+
+Kaldi 是一个用 C++ 写的开源语音识别软件,并且在 Apache 公共许可下发布。它可以运行在 Windows,macOS 和 Linux 上。它的开发始于 2009。
+
+Kaldi 超过其他语音识别软件的主要特点是可扩展和模块化。社区提供了大量的三方模块可以用来完成你的任务。Kaldi 也支持深度神经网络,并且在它的网站上提供了[出色的文档][4]。
+
+虽然代码主要由 C++ 完成,但它通过 Bash 和 Python 脚本进行了封装。因此,如果你仅仅想使用基本的语音到文字转换功能,你就会发现通过 Python 或 Bash 能够轻易的完成。
+
+[Project’s homepage][5].
+
+#### Julius
+
+![5 Good Open Source Speech Recognition/Speech-to-Text Systems 19 open source speech recognition][6]
+
+可能是有史以来最古老的语音识别软件之一。它的发展始于 1991 年的京都大学,之后在 2005 年将所有权转移到了一个独立的项目组。
+
+Julius 的主要特点包括了执行实时 STT 的能力,低内存占用(20000 单词少于 64 MB),输出最优词/词图的能力,当作服务器单元运行的能力和很多东西。这款软件主要为学术和研究所设计。由 C 语言写成,并且可以运行在 Linux,Windows,macOS 甚至 Android(在智能手机上)。
+
+它当前仅支持英语和日语。软件或许易于从 Linux 发行版的仓库中安装。只要在软件包管理器中搜索 julius 即可。最新的版本[发布][7]于大约一个半月之前。
+
+[Project’s homepage][8].
+
+#### Wav2Letter++
+
+![5 Good Open Source Speech Recognition/Speech-to-Text Systems 21 open source speech recognition][9]
+
+如果你在寻找一个更加时髦的,那么这款一定适合。Wav2Letter++ 是一款由 Facebook 的 AI 研究团队于 2 个月之前发布的开源语言识别软件。代码在 BSD 许可下发布。
+
+Facebook 描述它的库是“最快最先进的语音识别系统”。构建它时的想法使其能在默认情况下对性能进行优化。Facebook 最新的机器学习库 [FlashLight][11] 也被用作 Wav2Letter++ 的底层核心。
+
+Wav2Letter++ 需要你先为所描述的语言建立一个模型来训练算法。没有任何一种语言(包括英语)的预训练模型,它仅仅是个机器学习驱动的文本语音转换工具,它用 C++ 写成,因此命名为 Wav2Letter++。
+
+[Project’s homepage][12].
+
+#### DeepSpeech2
+
+![5 Good Open Source Speech Recognition/Speech-to-Text Systems 23 open source speech recognition][13]
+
+中国巨头百度的研究人员也在开发他们自己的语音文字转换引擎,叫做“DeepSpeech2”。它是一个端对端的开源引擎,使用“PaddlePaddle”深度学习框架进行英语或汉语的文字转换。代码在 BSD 许可下发布。
+
+引擎可以训练在任何模型之上,并且可以用于任何想要的语言。模型并未随代码一同发布。你要像其他软件那样自己建立模型。DeepSpeech2 的源代码由 Python 写成,如果你使用过就会非常容易上手。
+
+[Project’s homepage][14].
+
+### 总结
+
+语音识别领域仍然主要地由专有软件巨头所占据,比如 Google 和 IBM(它们为此提供了闭源商业服务),但是开源同类软件很有前途。这 5 款开源语音识别引擎应当能够帮助你构建应用,随着时间推移,它们会不断地发展。在几年之后,我们希望开源成为这些技术中的常态,就像其他行业那样。
+
+如果你对清单有其他的建议或评论,我们很乐意在下面听到。
+
+--------------------------------------------------------------------------------
+
+via: https://fosspost.org/lists/open-source-speech-recognition-speech-to-text
+
+作者:[Simon James][a]
+选题:[lujun9972][b]
+译者:[译者ID](https://github.com/LuuMing)
+校对:[校对者ID](https://github.com/校对者ID)
+
+本文由 [LCTT](https://github.com/LCTT/TranslateProject) 原创编译,[Linux中国](https://linux.cn/) 荣誉推出
+
+[a]: https://fosspost.org/author/simonjames
+[b]: https://github.com/lujun9972
+[1]: https://i0.wp.com/fosspost.org/wp-content/uploads/2019/02/hero_speech-machine-learning2.png?resize=820%2C280&ssl=1 (5 Good Open Source Speech Recognition/Speech-to-Text Systems 16 open source speech recognition)
+[2]: https://github.com/mozilla/DeepSpeech
+[3]: https://i0.wp.com/fosspost.org/wp-content/uploads/2019/02/Screenshot-at-2019-02-19-1134.png?resize=591%2C138&ssl=1 (5 Good Open Source Speech Recognition/Speech-to-Text Systems 18 open source speech recognition)
+[4]: http://kaldi-asr.org/doc/index.html
+[5]: http://kaldi-asr.org
+[6]: https://i2.wp.com/fosspost.org/wp-content/uploads/2019/02/mic_web.png?resize=385%2C100&ssl=1 (5 Good Open Source Speech Recognition/Speech-to-Text Systems 20 open source speech recognition)
+[7]: https://github.com/julius-speech/julius/releases
+[8]: https://github.com/julius-speech/julius
+[9]: https://i2.wp.com/fosspost.org/wp-content/uploads/2019/02/fully_convolutional_ASR.png?resize=850%2C177&ssl=1 (5 Good Open Source Speech Recognition/Speech-to-Text Systems 22 open source speech recognition)
+[10]: https://code.fb.com/ai-research/wav2letter/
+[11]: https://github.com/facebookresearch/flashlight
+[12]: https://github.com/facebookresearch/wav2letter
+[13]: https://i2.wp.com/fosspost.org/wp-content/uploads/2019/02/ds2.png?resize=850%2C313&ssl=1 (5 Good Open Source Speech Recognition/Speech-to-Text Systems 24 open source speech recognition)
+[14]: https://github.com/PaddlePaddle/DeepSpeech
diff --git a/translated/tech/20190415 Inter-process communication in Linux- Shared storage.md b/translated/tech/20190415 Inter-process communication in Linux- Shared storage.md
deleted file mode 100644
index 3ee39094a6..0000000000
--- a/translated/tech/20190415 Inter-process communication in Linux- Shared storage.md
+++ /dev/null
@@ -1,435 +0,0 @@
-[#]: collector: (lujun9972)
-[#]: translator: (FSSlc)
-[#]: reviewer: ( )
-[#]: publisher: ( )
-[#]: url: ( )
-[#]: subject: (Inter-process communication in Linux: Shared storage)
-[#]: via: (https://opensource.com/article/19/4/interprocess-communication-linux-storage)
-[#]: author: (Marty Kalin https://opensource.com/users/mkalindepauledu)
-
-Linux 下的进程间通信:共享存储
-======
-
-学习在 Linux 中进程是如何与其他进程进行同步的。
-![Filing papers and documents][1]
-
-本篇是 Linux 下[进程间通信][2](IPC)系列的第一篇文章。这个系列将使用 C 语言代码示例来阐明以下 IPC 机制:
-
- * 共享文件
- * 共享内存(使用信号量)
- * 管道(命名的或非命名的管道)
- * 消息队列
- * 套接字
- * 信号
-
-在聚焦上面提到的共享文件和共享内存这两个机制之前,这篇文章将复习一些核心的概念。
-
-### 核心概念
-_进程_ 是运行着的程序,每个进程都有着它自己的地址空间,这些空间由进程被允许获取的内存地址组成。进程有一个或多个执行 _线程_,而线程是一系列执行指令的集合: _单线程_ 进程就只有一个线程,而 _多线程_ 的进程则有多个线程。一个进程中的线程共享各种资源,特别是地址空间。另外,一个进程中的线程可以直接通过共享内存来进行通信,尽管某些现代语言(例如 Go)鼓励一种更有序的方式例如使用线程安全的通道。当然对于不同的进程,默认情况下,它们 _不_ 能共享内存。
-
-启动进程后进行通信有多种方法,下面所举的例子中主要使用了下面的两种方法:
-
- * 一个终端被用来启动一个进程,另外一个不同的终端被用来启动另一个。
- * 在一个进程(父进程)中调用系统函数 **fork**,以此生发另一个进程(子进程)。
-
-第一个例子采用了上面使用终端的方法。这些[代码示例][3]的 ZIP 压缩包可以从我的网站下载到。
-
-### 共享文件
-
-程序员对文件获取问题应该都已经很熟识了,包括许多坑(不存在的文件、文件权限损坏等等),这些问题困扰着程序对文件的使用。尽管如此,共享文件可能是最为基础的 IPC 机制了。考虑一下下面这样一个相对简单的例子,其中一个进程(_生产者_)创建和写入一个文件,然后另一个进程(_消费者_)从这个相同的文件中进行读取:
-
-```
- writes +-----------+ reads
-producer-------->| disk file |<-------consumer
- +-----------+
-```
-
-在使用这个 IPC 机制时最明显的挑战是 _竞争条件_ 可能会发生:生产者和消费者可能恰好在同一时间访问该文件,从而使得输出结果不确定。为了避免竞争条件的发生,该文件在处于 _读_ 或 _写_ 状态时必须以某种方式处于被锁状态,从而阻止在 _写_ 操作执行时和其他操作的冲突。在标准系统库中与锁相关的 API 可以被总结如下:
-
- * 生产者应该在写入文件时获得一个文件的排斥锁。一个 _排斥_ 锁最多被一个进程所拥有。这样就可以排除掉竞争条件的发生,因为在锁被释放之前没有其他的进程可以访问这个文件。
- * 消费者应该在从文件中读取内容时得到至少一个共享锁。多个 _readers_ 可以同时保有一个 _共享_ 锁,但是没有 _writer_ 可以获取到文件内容,甚至在当一个单独的 _reader_ 保有一个共享锁时。
-
-共享锁可以提升效率。假如一个进程只是读入一个文件的内容,而不去改变它的内容,就没有什么原因阻止其他进程来做同样的事。但如果需要写入内容,则很显然需要文件有排斥锁。
-
-标准的 I/O 库中包含一个名为 **fcntl** 的实用函数,它可以被用来检查或者操作一个文件上的排斥锁和共享锁。该函数通过一个 _文件描述符_ (一个在进程中的非负整数值)来标记一个文件(在不同的进程中不同的文件描述符可能标记同一个物理文件)。对于文件的锁定, Linux 提供了名为 **flock** 的库函数,它是 **fcntl** 的一个精简包装。第一个例子中使用 **fcntl** 函数来暴露这些 API 细节。
-
-#### 示例 1. _生产者_ 程序
-
-```c
-#include
-#include
-#include
-#include
-
-#define FileName "data.dat"
-
-void report_and_exit(const char* msg) {
- [perror][4](msg);
- [exit][5](-1); /* EXIT_FAILURE */
-}
-
-int main() {
- struct flock lock;
- lock.l_type = F_WRLCK; /* read/write (exclusive) lock */
- lock.l_whence = SEEK_SET; /* base for seek offsets */
- lock.l_start = 0; /* 1st byte in file */
- lock.l_len = 0; /* 0 here means 'until EOF' */
- lock.l_pid = getpid(); /* process id */
-
- int fd; /* file descriptor to identify a file within a process */
- if ((fd = open(FileName, O_RDONLY)) < 0) /* -1 signals an error */
- report_and_exit("open to read failed...");
-
- /* If the file is write-locked, we can't continue. */
- fcntl(fd, F_GETLK, &lock); /* sets lock.l_type to F_UNLCK if no write lock */
- if (lock.l_type != F_UNLCK)
- report_and_exit("file is still write locked...");
-
- lock.l_type = F_RDLCK; /* prevents any writing during the reading */
- if (fcntl(fd, F_SETLK, &lock) < 0)
- report_and_exit("can't get a read-only lock...");
-
- /* Read the bytes (they happen to be ASCII codes) one at a time. */
- int c; /* buffer for read bytes */
- while (read(fd, &c, 1) > 0) /* 0 signals EOF */
- write(STDOUT_FILENO, &c, 1); /* write one byte to the standard output */
-
- /* Release the lock explicitly. */
- lock.l_type = F_UNLCK;
- if (fcntl(fd, F_SETLK, &lock) < 0)
- report_and_exit("explicit unlocking failed...");
-
- close(fd);
- return 0;
-}
-```
-
-上面 _生产者_ 程序的主要步骤可以总结如下:
-
- * 这个程序首先声明了一个类型为 **struct flock** 的变量,它代表一个锁,并对它的 5 个域做了初始化。第一个初始化
-```c
-lock.l_type = F_WRLCK; /* exclusive lock */
-````
-使得这个锁为排斥锁(_read-write_)而不是一个共享锁(_read-only_)。假如 _生产者_ 获得了这个锁,则其他的进程将不能够对文件做读或者写操作,直到 _生产者_ 释放了这个锁,或者显式地调用 **fcntl**,又或者隐式地关闭这个文件。(当进程终止时,所有被它打开的文件都会被自动关闭,从而释放了锁)
- * 上面的程序接着初始化其他的域。主要的效果是 _整个_ 文件都将被锁上。但是,有关锁的 API 允许特别指定的字节被上锁。例如,假如文件包含多个文本记录,则单个记录(或者甚至一个记录的一部分)可以被锁,而其余部分不被锁。
- * 第一次调用 **fcntl**
-```c
-if (fcntl(fd, F_SETLK, &lock) < 0)
-```
-尝试排斥性地将文件锁住,并检查调用是否成功。一般来说, **fcntl** 函数返回 **-1** (因此小于 0)意味着失败。第二个参数 **F_SETLK** 意味着 **fcntl** 的调用 _不是_ 堵塞的;函数立即做返回,要么获得锁,要么显示失败了。假如替换地使用 **F_SETLKW**(末尾的 **W** 代指 _等待_),那么对 **fcntl** 的调用将是阻塞的,直到有可能获得锁的时候。在调用 **fcntl** 函数时,它的第一个参数 **fd** 指的是文件描述符,第二个参数指定了将要采取的动作(在这个例子中,**F_SETLK** 指代设置锁),第三个参数为锁结构的地址(在本例中,指的是 **& lock**)。
- * 假如 _生产者_ 获得了锁,这个程序将向文件写入两个文本记录。
- * 在向文件写入内容后,_生产者_ 改变锁结构中的 **l_type** 域为 _unlock_ 值:
-```c
-lock.l_type = F_UNLCK;
-```
-并调用 **fcntl** 来执行解锁操作。最后程序关闭了文件并退出。
-
-#### 示例 2. _消费者_ 程序
-
-```c
-#include
-#include
-#include
-#include
-
-#define FileName "data.dat"
-
-void report_and_exit(const char* msg) {
- [perror][4](msg);
- [exit][5](-1); /* EXIT_FAILURE */
-}
-
-int main() {
- struct flock lock;
- lock.l_type = F_WRLCK; /* read/write (exclusive) lock */
- lock.l_whence = SEEK_SET; /* base for seek offsets */
- lock.l_start = 0; /* 1st byte in file */
- lock.l_len = 0; /* 0 here means 'until EOF' */
- lock.l_pid = getpid(); /* process id */
-
- int fd; /* file descriptor to identify a file within a process */
- if ((fd = open(FileName, O_RDONLY)) < 0) /* -1 signals an error */
- report_and_exit("open to read failed...");
-
- /* If the file is write-locked, we can't continue. */
- fcntl(fd, F_GETLK, &lock); /* sets lock.l_type to F_UNLCK if no write lock */
- if (lock.l_type != F_UNLCK)
- report_and_exit("file is still write locked...");
-
- lock.l_type = F_RDLCK; /* prevents any writing during the reading */
- if (fcntl(fd, F_SETLK, &lock) < 0)
- report_and_exit("can't get a read-only lock...");
-
- /* Read the bytes (they happen to be ASCII codes) one at a time. */
- int c; /* buffer for read bytes */
- while (read(fd, &c, 1) > 0) /* 0 signals EOF */
- write(STDOUT_FILENO, &c, 1); /* write one byte to the standard output */
-
- /* Release the lock explicitly. */
- lock.l_type = F_UNLCK;
- if (fcntl(fd, F_SETLK, &lock) < 0)
- report_and_exit("explicit unlocking failed...");
-
- close(fd);
- return 0;
-}
-```
-
-相比于着重解释锁的 API,_消费者_ 程序会相对复杂一点儿。特别的,_消费者_ 程序首先检查文件是否被排斥性的被锁,然后才尝试去获得一个共享锁。相关的代码为:
-
-```
-lock.l_type = F_WRLCK;
-...
-fcntl(fd, F_GETLK, &lock); /* sets lock.l_type to F_UNLCK if no write lock */
-if (lock.l_type != F_UNLCK)
- report_and_exit("file is still write locked...");
-```
-
-在 **fcntl** 调用中的 **F_GETLK** 操作指定检查一个锁,在本例中,上面代码的声明中给了一个 **F_WRLCK** 的排斥锁。假如特指的锁不存在,那么 **fcntl** 调用将会自动地改变锁类型域为 **F_UNLCK** 以此来显示当前的状态。假如文件是排斥性地被锁,那么 _消费者_ 将会终止。(一个更健壮的程序版本或许应该让 _消费者_ _睡_ 会儿,然后再尝试几次。)
-
-假如当前文件没有被锁,那么 _消费者_ 将尝试获取一个共享(_read-only_)锁(**F_RDLCK**)。为了缩短程序,**fcntl** 中的 **F_GETLK** 调用可以丢弃,因为假如其他进程已经保有一个 _读写_ 锁,**F_RDLCK** 的调用就可能会失败。重新调用一个 _只读_ 锁能够阻止其他进程向文件进行写的操作,但可以允许其他进程对文件进行读取。简而言之,共享锁可以被多个进程所保有。在获取了一个共享锁后,_消费者_ 程序将立即从文件中读取字节数据,然后在标准输出中打印这些字节的内容,接着释放锁,关闭文件并终止。
-
-下面的 **%** 为命令行提示符,下面展示的是从相同终端开启这两个程序的输出:
-
-```
-% ./producer
-Process 29255 has written to data file...
-
-% ./consumer
-Now is the winter of our discontent
-Made glorious summer by this sun of York
-```
-
-在本次的代码示例中,通过 IPC 传输的数据是文本:它们来自莎士比亚的戏剧《理查三世》中的两行台词。然而,共享文件的内容还可以是纷繁复杂的,任意的字节数据(例如一个电影)都可以,这使得文件共享变成了一个非常灵活的 IPC 机制。但它的缺点是文件获取速度较慢,因为文件的获取涉及到读或者写。同往常一样,编程总是伴随着折中。下面的例子将通过共享内存来做 IPC,而不是通过共享文件,在性能上相应的有极大的提升。
-
-### 共享内存
-
-对于共享内存,Linux 系统提供了两类不同的 API:传统的 System V API 和更新一点的 POSIX API。在单个应用中,这些 API 不能混用。但是, POSIX 方式的一个坏处是它的特性仍在发展中,并且依赖于安装的内核版本,这非常影响代码的可移植性。例如, 默认情况下,POSIX API 用 _内存映射文件_ 来实现共享内存:对于一个共享的内存段,系统为相应的内容维护一个 _备份文件_。在 POSIX 规范下共享内存可以被配置为不需要备份文件,但这可能会影响可移植性。我的例子中使用的是带有备份文件的 POSIX API,这既结合了内存获取的速度优势,又获得了文件存储的持久性。
-
-下面的共享内存例子中包含两个程序,分别名为 _memwriter_ 和 _memreader_,并使用 _信号量_ 来调整它们对共享内存的获取。在任何时候当共享内存进入一个 _writer_ 的版图时,无论是多进程还是多线程,都有遇到基于内存的竞争条件的风险,所以,需要引入信号量来协调(同步)对共享内存的获取。
-
-_memwriter_ 程序应当在它自己所处的终端首先启动,然后 _memreader_ 程序才可以在它自己所处的终端启动(在接着的十几秒内)。_memreader_ 的输出如下:
-
-```
-This is the way the world ends...
-```
-
-在每个源程序的最上方注释部分都解释了在编译它们时需要添加的链接参数。
-
-首先让我们复习一下信号量是如何作为一个同步机制工作的。一般的信号量也被叫做一个 _计数信号量_,因为带有一个可以增加的值(通常初始化为 0)。考虑一家租用自行车的商店,在它的库存中有 100 辆自行车,还有一个供职员用于租赁的程序。每当一辆自行车被租出去,信号量就增加 1;当一辆自行车被还回来,信号量就减 1。在信号量的值为 100 之前都还可以进行租赁业务,但如果等于 100 时,就必须停止业务,直到至少有一辆自行车被还回来,从而信号量减为 99。
-
-_二元信号量_ 是一个特例,它只有两个值: 0 和 1。在这种情况下,信号量的表现为 _互斥量_(一个互斥的构造)。下面的共享内存示例将把信号量用作互斥量。当信号量的值为 0 时,只有 _memwriter_ 可以获取共享内存,在写操作完成后,这个进程将增加信号量的值,从而允许 _memreader_ 来读取共享内存。
-
-#### 示例 3. _memwriter_ 进程的源程序
-
-```c
-/** Compilation: gcc -o memwriter memwriter.c -lrt -lpthread **/
-#include
-#include
-#include
-#include
-#include
-#include
-#include
-#include
-#include "shmem.h"
-
-void report_and_exit(const char* msg) {
- [perror][4](msg);
- [exit][5](-1);
-}
-
-int main() {
- int fd = shm_open(BackingFile, /* name from smem.h */
- O_RDWR | O_CREAT, /* read/write, create if needed */
- AccessPerms); /* access permissions (0644) */
- if (fd < 0) report_and_exit("Can't open shared mem segment...");
-
- ftruncate(fd, ByteSize); /* get the bytes */
-
- caddr_t memptr = mmap(NULL, /* let system pick where to put segment */
- ByteSize, /* how many bytes */
- PROT_READ | PROT_WRITE, /* access protections */
- MAP_SHARED, /* mapping visible to other processes */
- fd, /* file descriptor */
- 0); /* offset: start at 1st byte */
- if ((caddr_t) -1 == memptr) report_and_exit("Can't get segment...");
-
- [fprintf][7](stderr, "shared mem address: %p [0..%d]\n", memptr, ByteSize - 1);
- [fprintf][7](stderr, "backing file: /dev/shm%s\n", BackingFile );
-
- /* semahore code to lock the shared mem */
- sem_t* semptr = sem_open(SemaphoreName, /* name */
- O_CREAT, /* create the semaphore */
- AccessPerms, /* protection perms */
- 0); /* initial value */
- if (semptr == (void*) -1) report_and_exit("sem_open");
-
- [strcpy][8](memptr, MemContents); /* copy some ASCII bytes to the segment */
-
- /* increment the semaphore so that memreader can read */
- if (sem_post(semptr) < 0) report_and_exit("sem_post");
-
- sleep(12); /* give reader a chance */
-
- /* clean up */
- munmap(memptr, ByteSize); /* unmap the storage */
- close(fd);
- sem_close(semptr);
- shm_unlink(BackingFile); /* unlink from the backing file */
- return 0;
-}
-```
-
-下面是 _memwriter_ 和 _memreader_ 程序如何通过共享内存来通信的一个总结:
-
- * 上面展示的 _memwriter_ 程序调用 **shm_open** 函数来得到作为系统协调共享内存的备份文件的文件描述符。此时,并没有内存被分配。接下来调用的是令人误解的名为 **ftruncate** 的函数
-```c
-ftruncate(fd, ByteSize); /* get the bytes */
-```
-它将分配 **ByteSize** 字节的内存,在该情况下,一般为大小适中的 512 字节。_memwriter_ 和 _memreader_ 程序都只从共享内存中获取数据,而不是从备份文件。系统将负责共享内存和备份文件之间数据的同步。
- * 接着 _memwriter_ 调用 **mmap** 函数:
-```c
-caddr_t memptr = mmap(NULL, /* let system pick where to put segment */
- ByteSize, /* how many bytes */
- PROT_READ | PROT_WRITE, /* access protections */
- MAP_SHARED, /* mapping visible to other processes */
- fd, /* file descriptor */
- 0); /* offset: start at 1st byte */
-```
-来获得共享内存的指针。(_memreader_ 也做一次类似的调用。) 指针类型 **caddr_t** 以 **c** 开头,它代表 **calloc**,而这是动态初始化分配的内存为 0 的一个系统函数。_memwriter_ 通过库函数 **strcpy**(string copy)来获取后续 _写_ 操作的 **memptr**。
- * 到现在为止, _memwriter_ 已经准备好进行写操作了,但首先它要创建一个信号量来确保共享内存的排斥性。假如 _memwriter_ 正在执行写操作而同时 _memreader_ 在执行读操作,则有可能出现竞争条件。假如调用 **sem_open**
- 成功了:
-```c
-sem_t* semptr = sem_open(SemaphoreName, /* name */
- O_CREAT, /* create the semaphore */
- AccessPerms, /* protection perms */
- 0); /* initial value */
-```
-那么,接着写操作便可以执行。上面的 **SemaphoreName**(任意一个唯一的非空名称)用来在 _memwriter_ 和 _memreader_ 识别信号量。 初始值 0 将会传递给信号量的创建者,在这个例子中指的是 _memwriter_ 赋予它执行 _写_ 操作的权利。
- * 在写操作完成后,_memwriter_ 通过调用 **sem_post** 函数将信号量的值增加到 1:
-```c
-if (sem_post(semptr) < 0) ..
-```
-增加信号了将释放互斥锁,使得 _memreader_ 可以执行它的 _读_ 操作。为了更好地测量,_memwriter_ 也将从它自己的地址空间中取消映射,
-```c
-munmap(memptr, ByteSize); /* unmap the storage *
-```
-这将使得 _memwriter_ 不能进一步地访问共享内存。
-
-#### 示例 4. _memreader_ 进程的源代码
-
-```c
-/** Compilation: gcc -o memreader memreader.c -lrt -lpthread **/
-#include