There are several reasons to[restrict a SSH user session][1]to a particular directory, especially on web servers, but the obvious one is a system security. In order to lock SSH users in a certain directory, we can usechrootmechanism.
change root (chroot) in Unix-like systems such as Linux, is a means of separating specific user operations from the rest of the Linux system; changes the apparent root directory for the current running user process and its child process with new root directory called achrooted jail.
In this tutorial, we’ll show you how to restrict a SSH user access to a given directory in Linux. Note that we’ll run the all the commands as root, use the[sudo command][2]if you are logged into server as a normal user.
### Step 1: Create SSH Chroot Jail
1.Start by creating the chroot jail using the mkdir command below:
```
# mkdir -p /home/test
```
2.Next, identify required files, according to thesshd_configman page, the`ChrootDirectory`option specifies the pathname of the directory to chroot to after authentication. The directory must contain the necessary files and directories to support a user’s session.
For an interactive session, this requires at least a shell, commonly`sh`, and basic`/dev`nodes such as null, zero, stdin, stdout, stderr, and tty devices:
```
# ls -l /dev/{null,zero,stdin,stdout,stderr,random,tty}
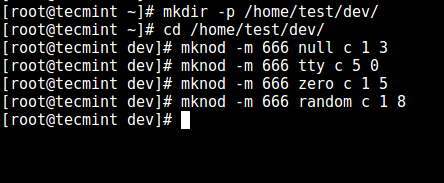
3.Now, create the`/dev`files as follows using themknod command. In the command below, the`-m`flag is used to specify the file permissions bits,`c`means character file and the two numbers are major and minor numbers that the files point to.
```
# mkdir -p /home/test/dev/
# cd /home/test/dev/
# mknod -m 666 null c 1 3
# mknod -m 666 tty c 5 0
# mknod -m 666 zero c 1 5
# mknod -m 666 random c 1 8
```
[
][4]
Create /dev and Required Files
4.Afterwards, set the appropriate permission on the chroot jail. Note that the chroot jail and its subdirectories and subfiles must be owned byrootuser, and not writable by any normal user or group:
```
# chown root:root /home/test
# chmod 0755 /home/test
# ls -ld /home/test
```
[

][5]
Set Permissions on Directory
### Step 2: Setup Interactive Shell for SSH Chroot Jail
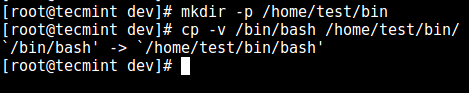
5.First, create the`bin`directory and then copy the`/bin/bash`files into the`bin`directory as follows:
```
# mkdir -p /home/test/bin
# cp -v /bin/bash /home/test/bin/
```
[
][6]
Copy Files to bin Directory
6.Now, identify bash required shared`libs`, as below and copy them into the`lib`directory:
7.Now, create the SSH user with the[useradd command][8]and set a secure password for the user:
```
# useradd tecmint
# passwd tecmint
```
8.Create the chroot jail general configurations directory,`/home/test/etc`and copy the updated account files (/etc/passwdand/etc/group) into this directory as follows:
### Step 6\. Create SSH User’s Home Directory and Add Linux Commands
11.From the previous step, we can notice that the user is locked in the root directory, we can create a home directory for the the SSH user like so (do this for all future users):
**Suggested Read:**[Restrict SFTP Users to Home Directories Using chroot Jail][18]
That’s it for now!. In this article, we showed you how to restrict a SSH user in a given directory (chrooted jail) in Linux. Use the comment section below to offer us your thoughts about this guide.
Aaron Kili is a Linux and F.O.S.S enthusiast, an upcoming Linux SysAdmin, web developer, and currently a content creator for TecMint who loves working with computers and strongly believes in sharing knowledge.